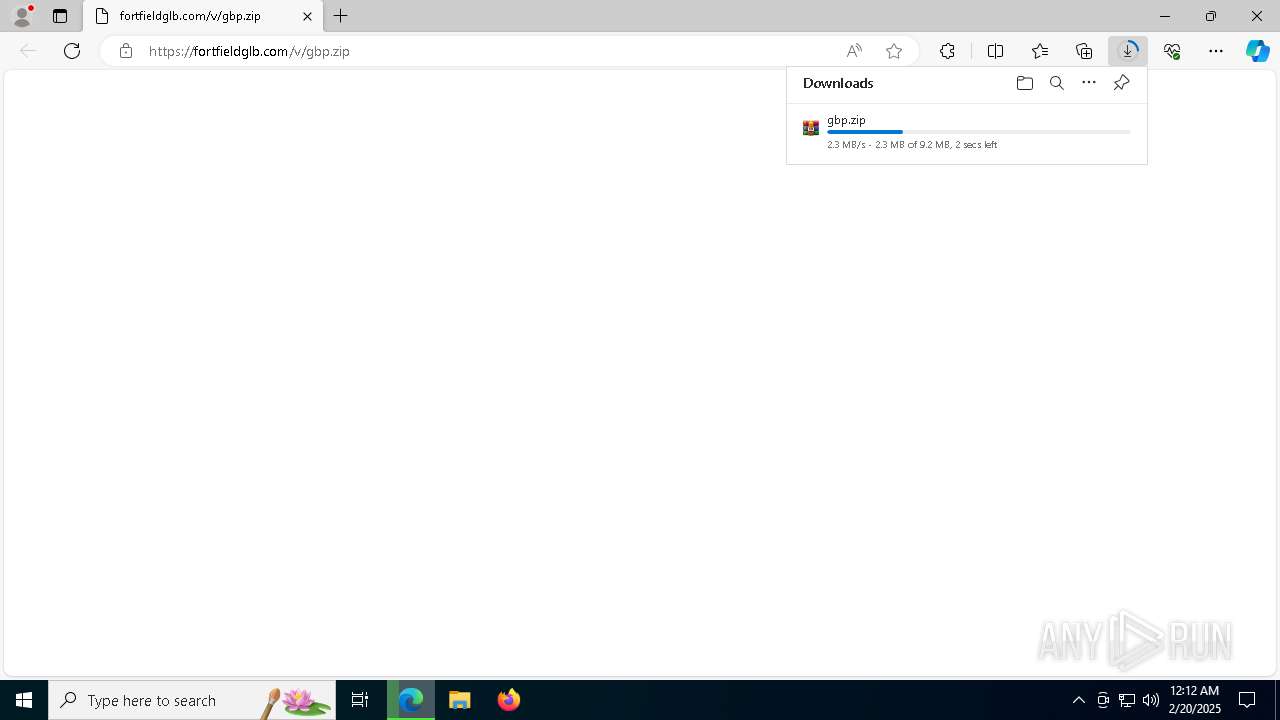
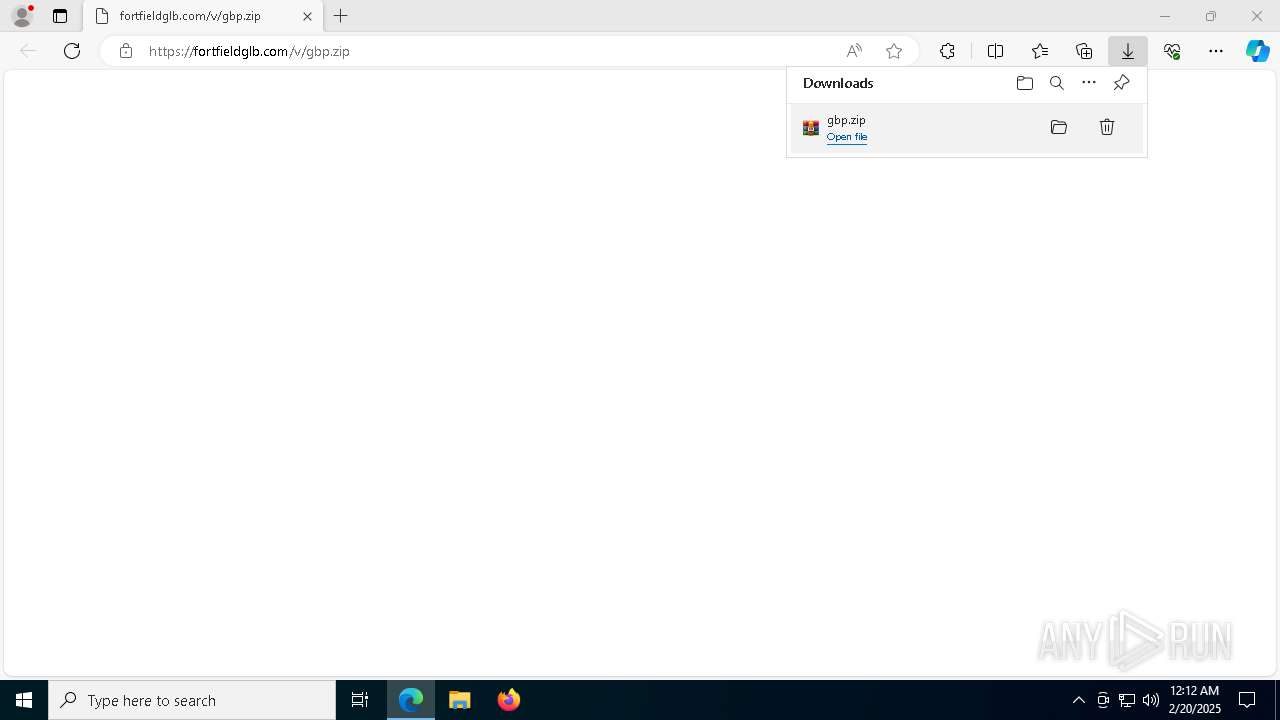
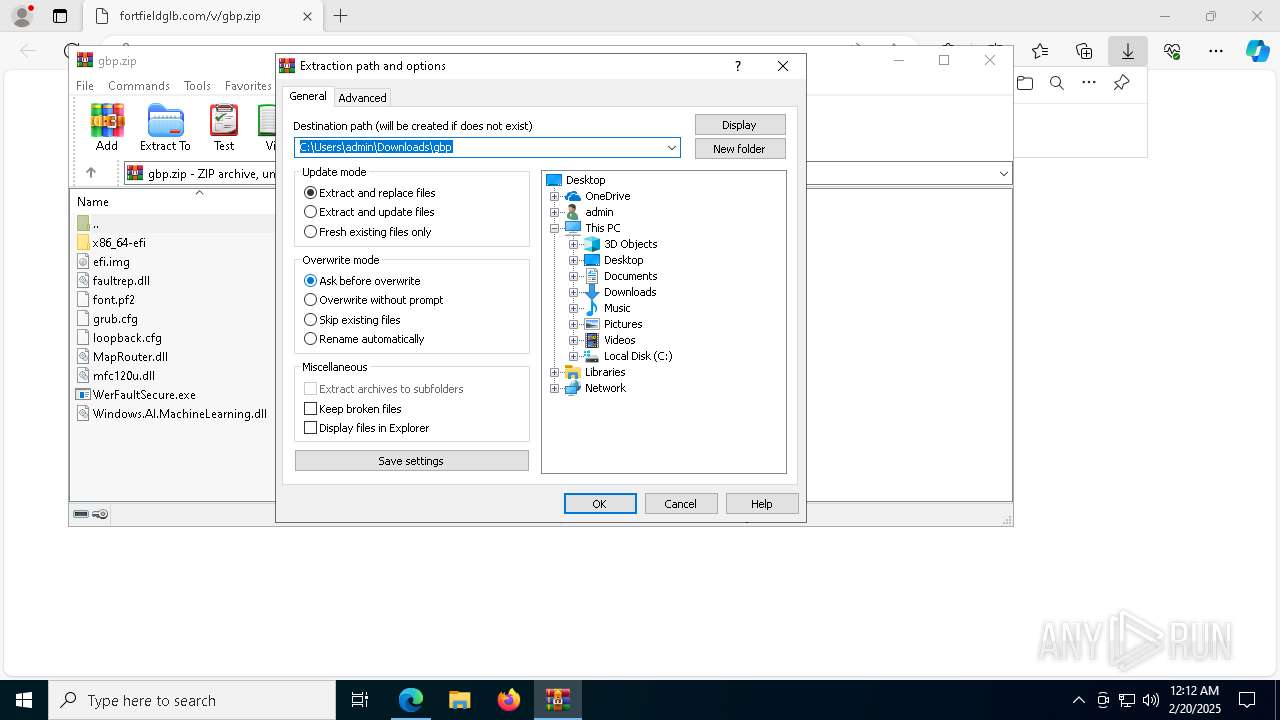
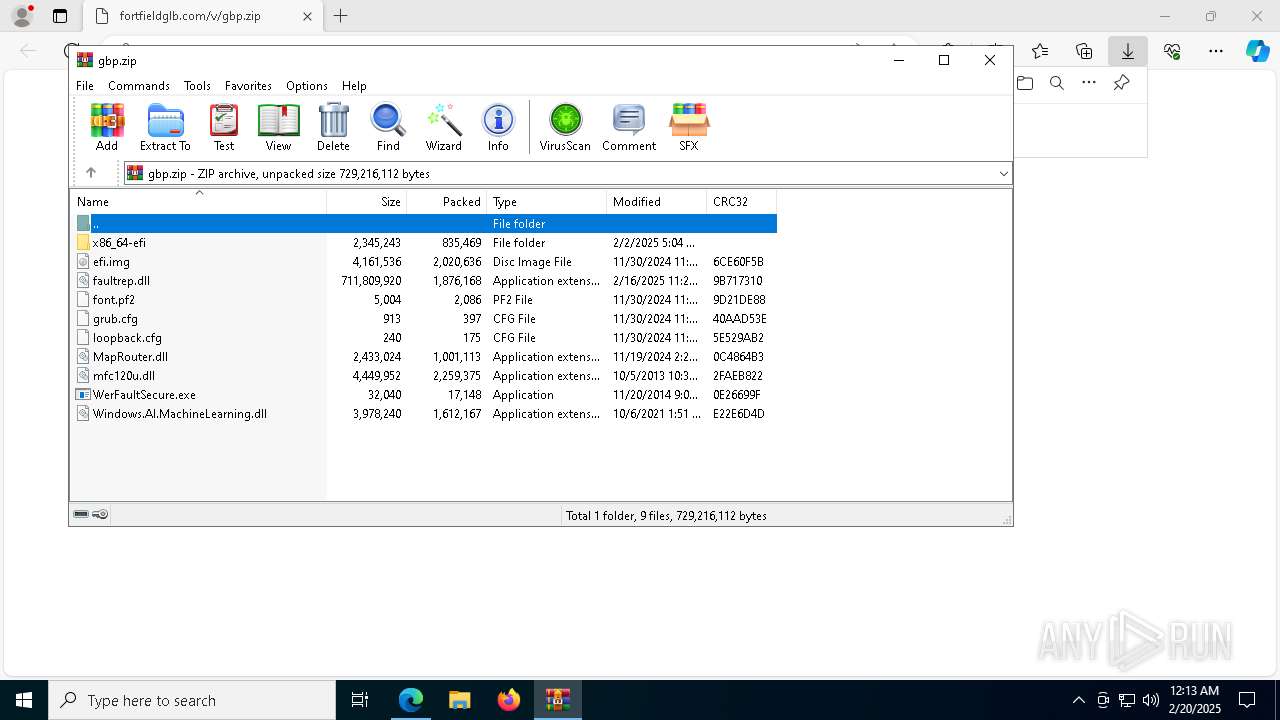
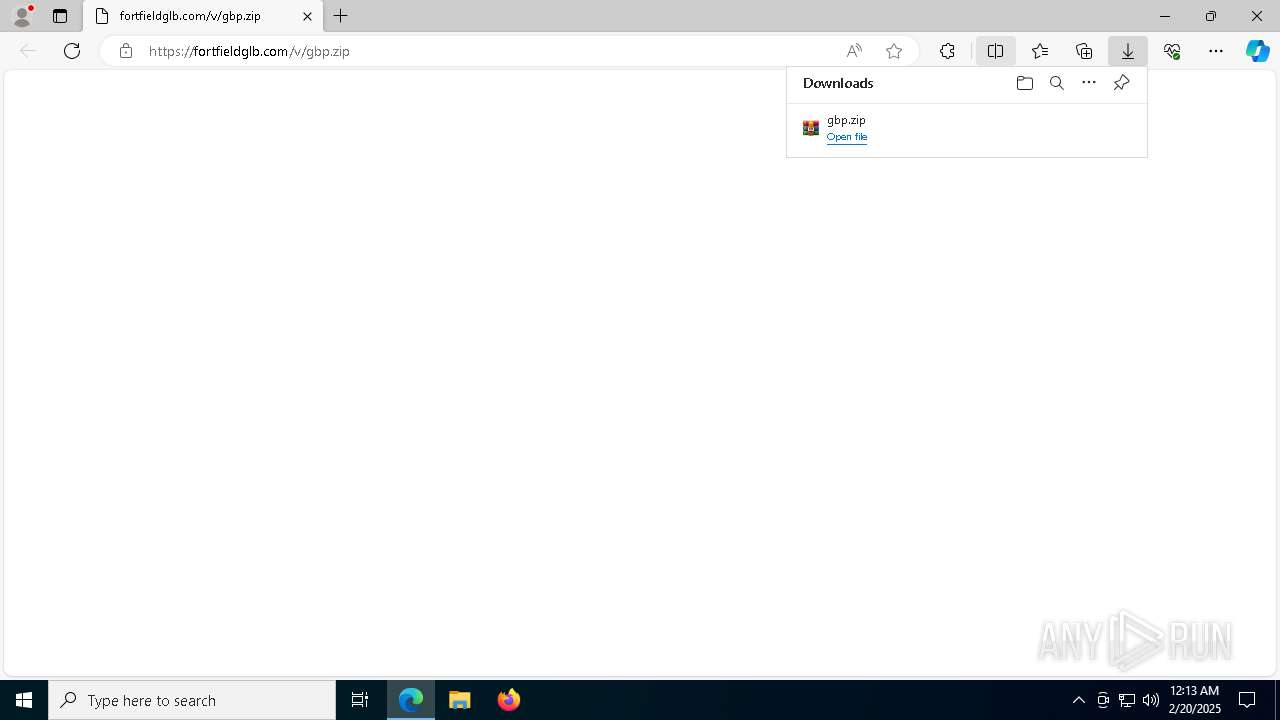
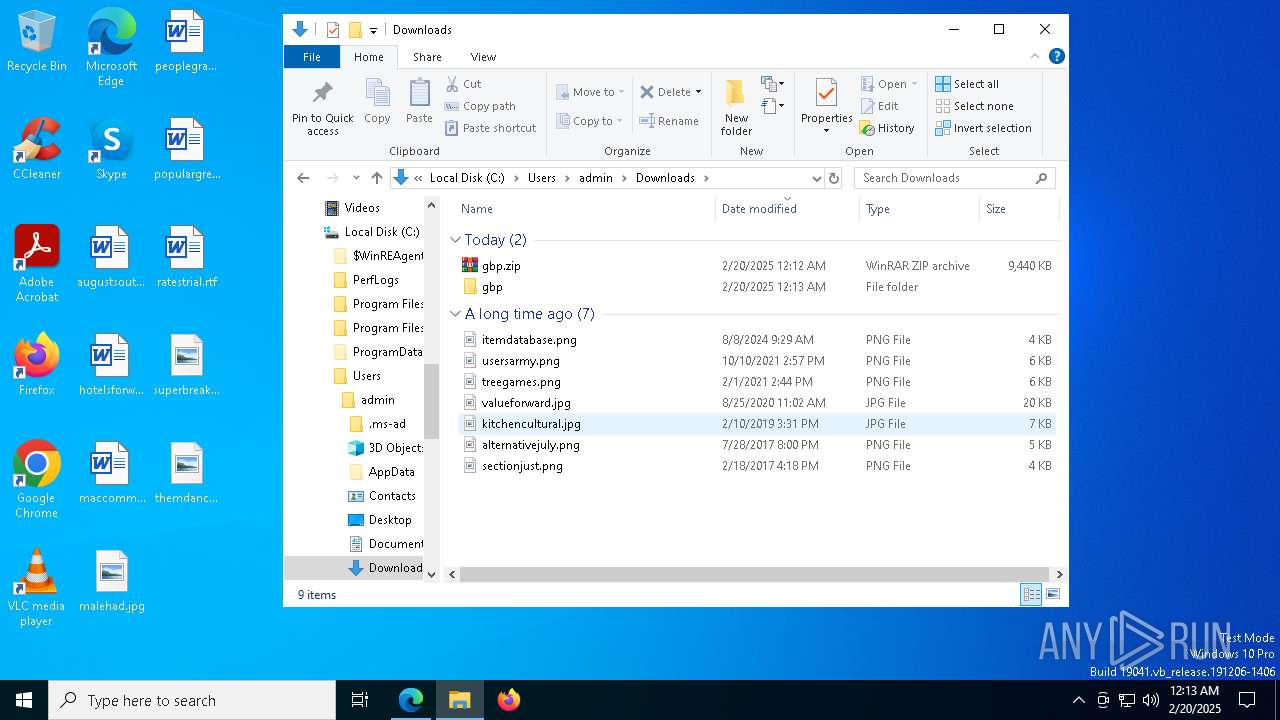
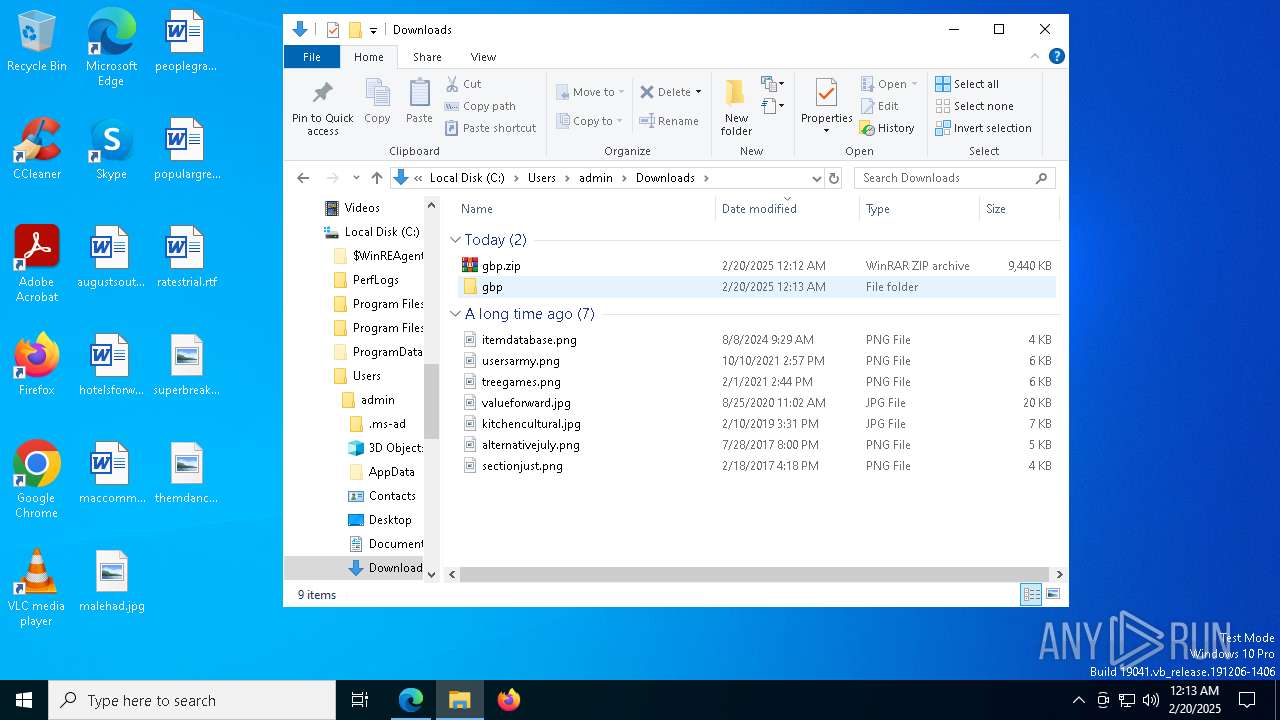
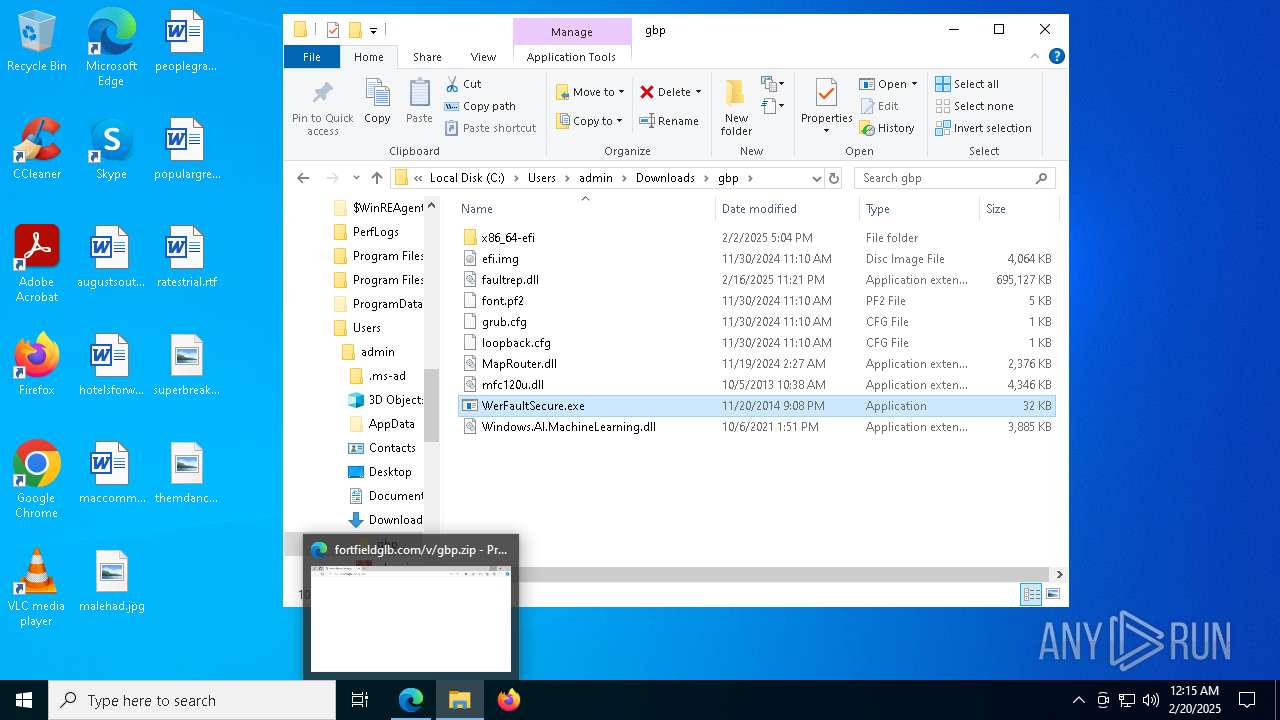
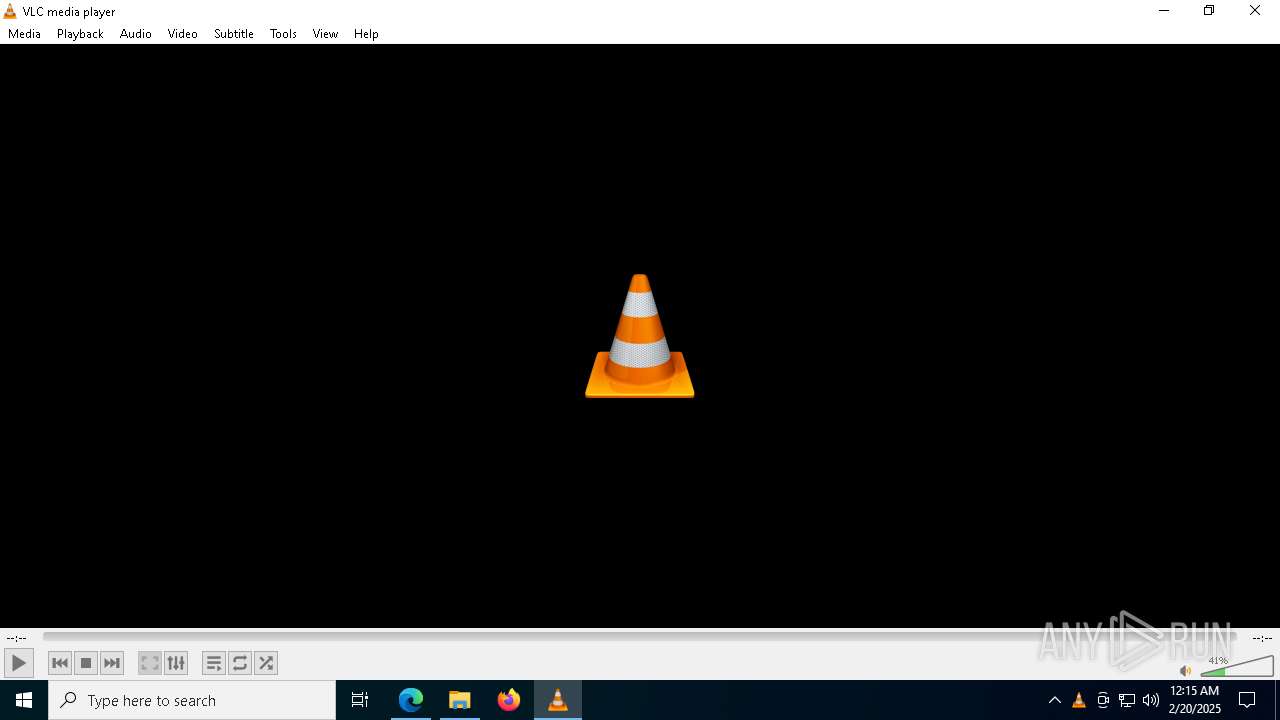
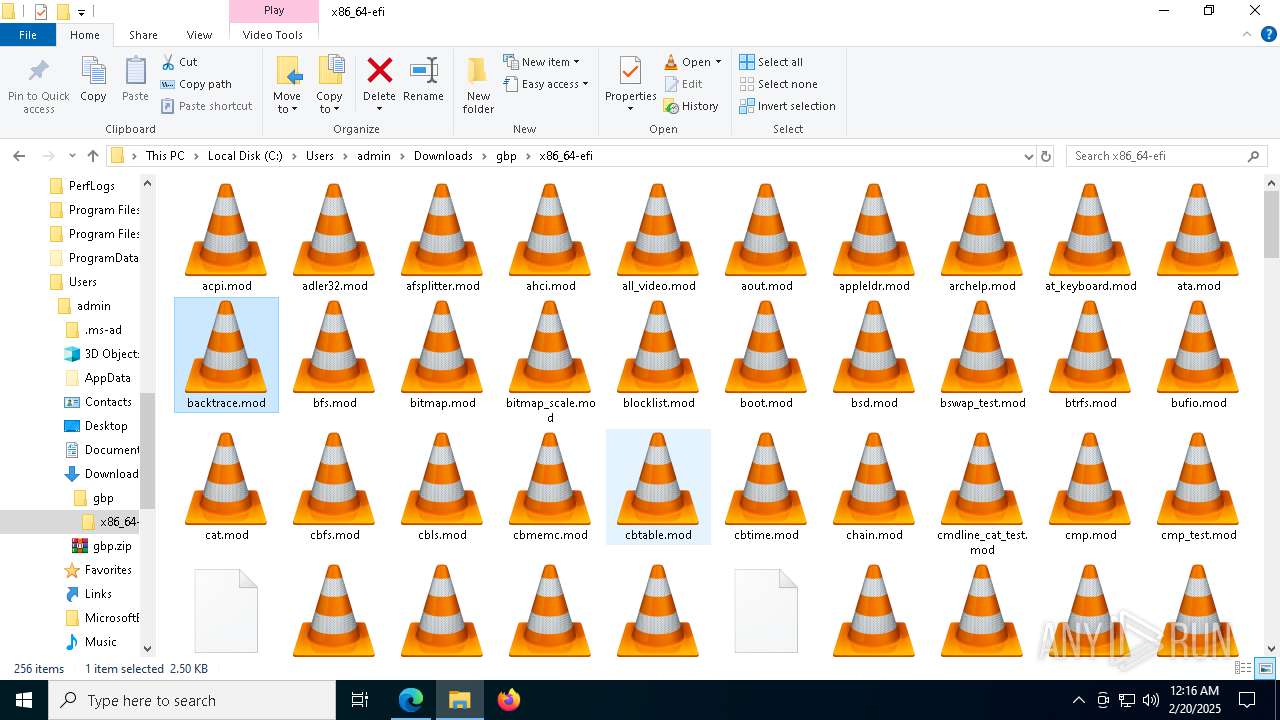
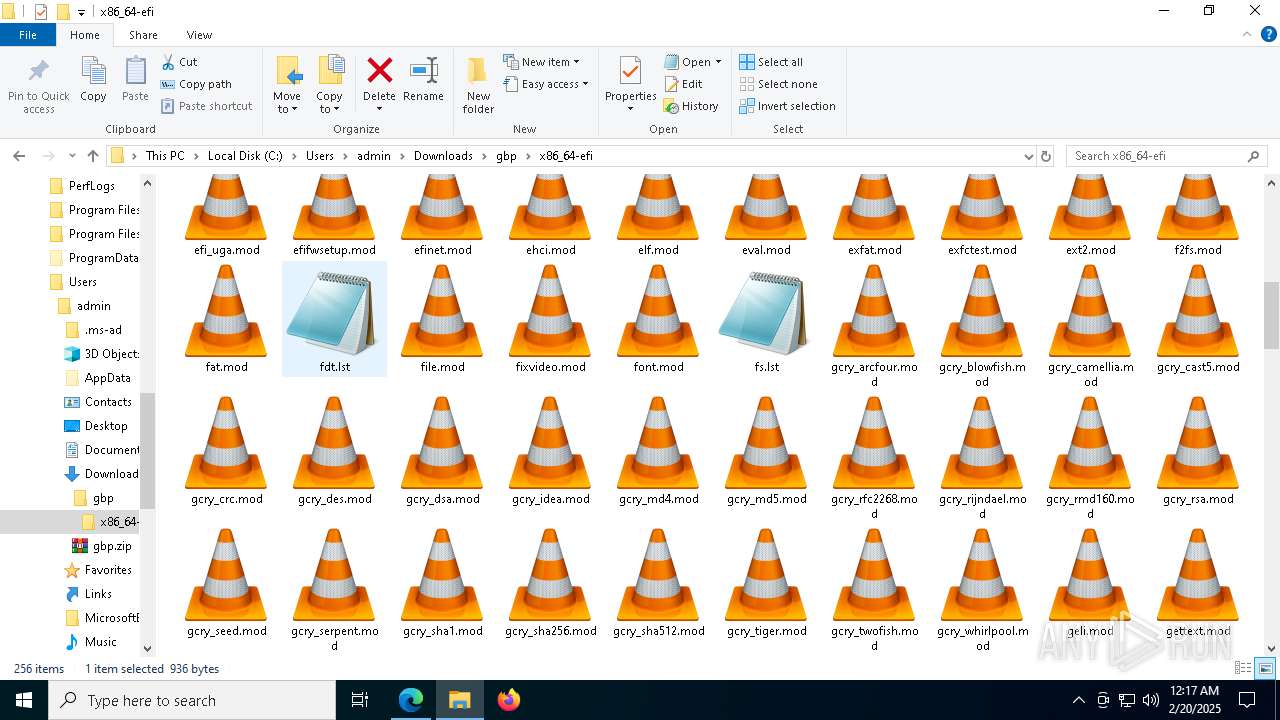
| URL: | https://fortfieldglb.com/v/gbp.zip |
| Full analysis: | https://app.any.run/tasks/c76b876d-ecd5-4d36-bdde-56752caf63c2 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 20, 2025, 00:12:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C4EF90BC46BD41B75FBDD9470B380EED |
| SHA1: | 6F279690C56DA73D601CCF225807C6EFB86C101D |
| SHA256: | 0F181D02595F45C22932DEC41D0DFDD9162F4F438AA9F1C307073D3250931D6F |
| SSDEEP: | 3:N8adIKEVYVn:2A/n |
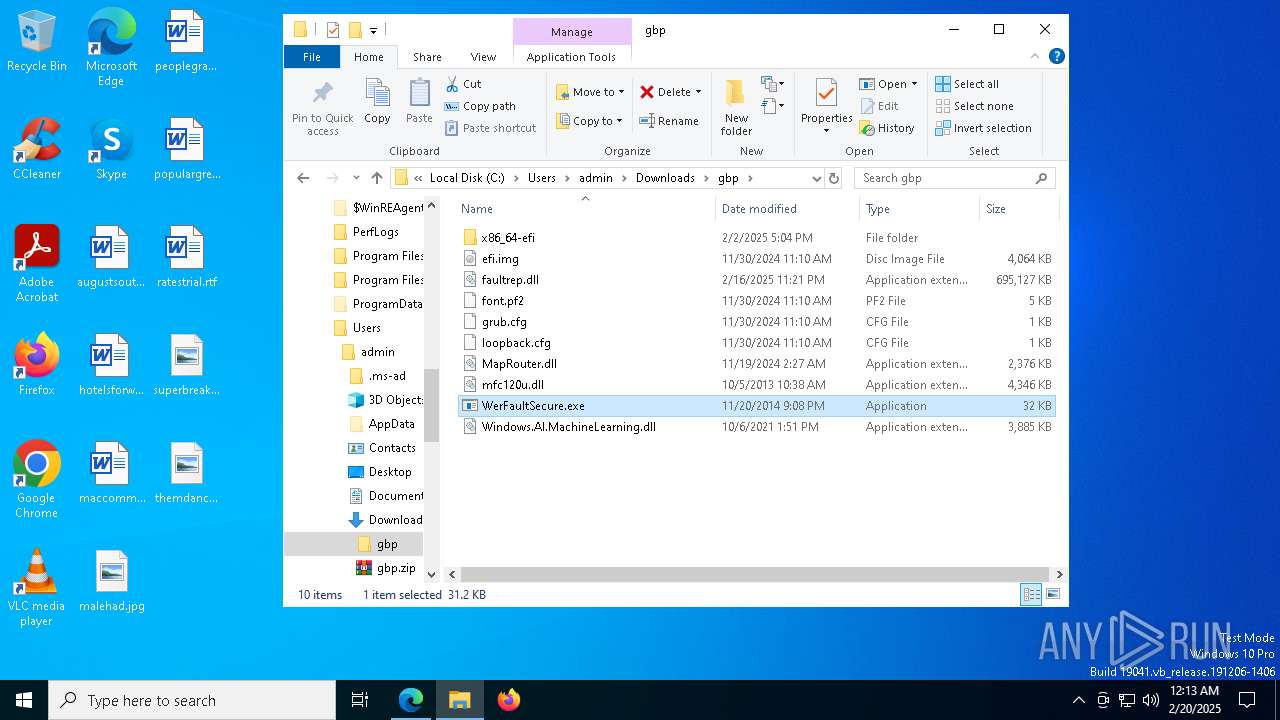
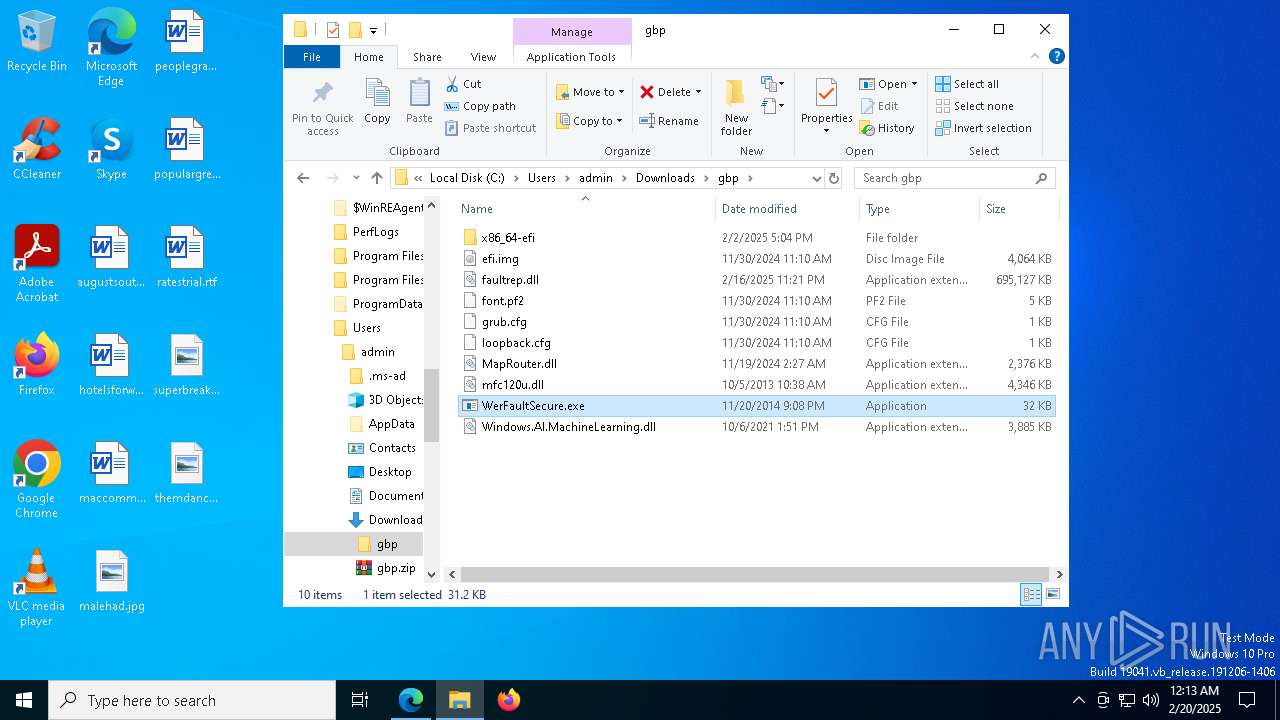
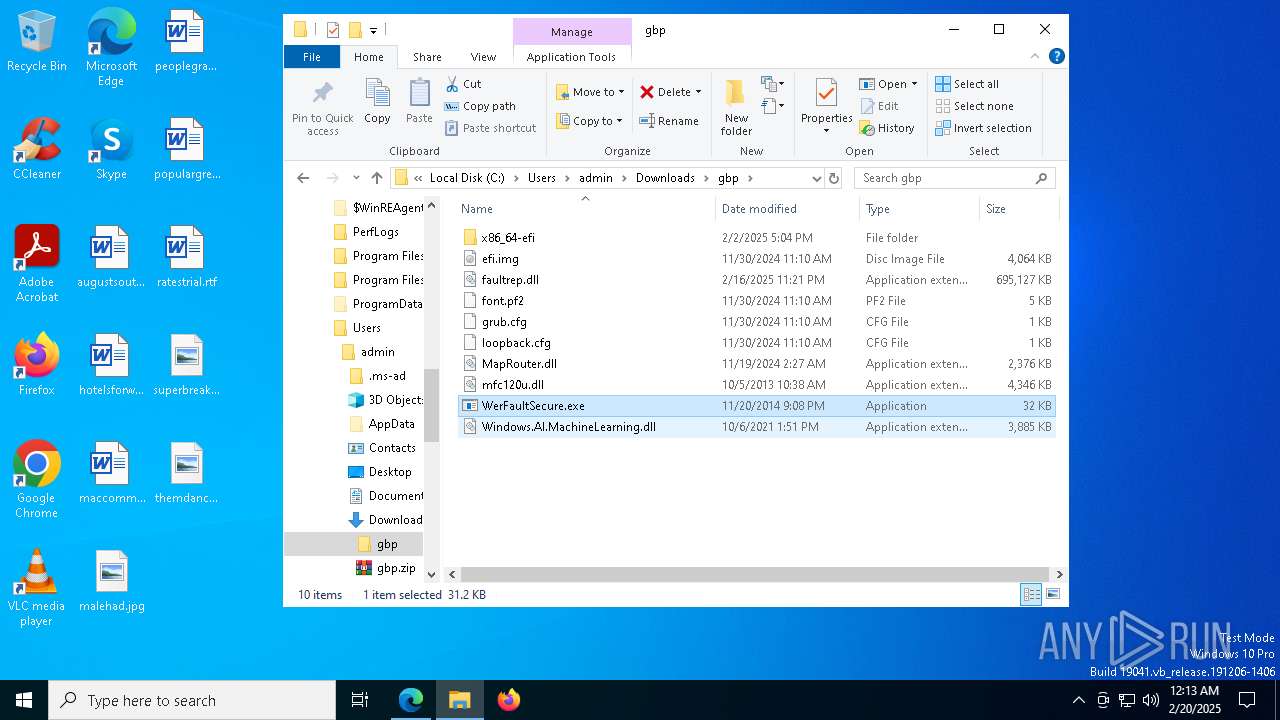
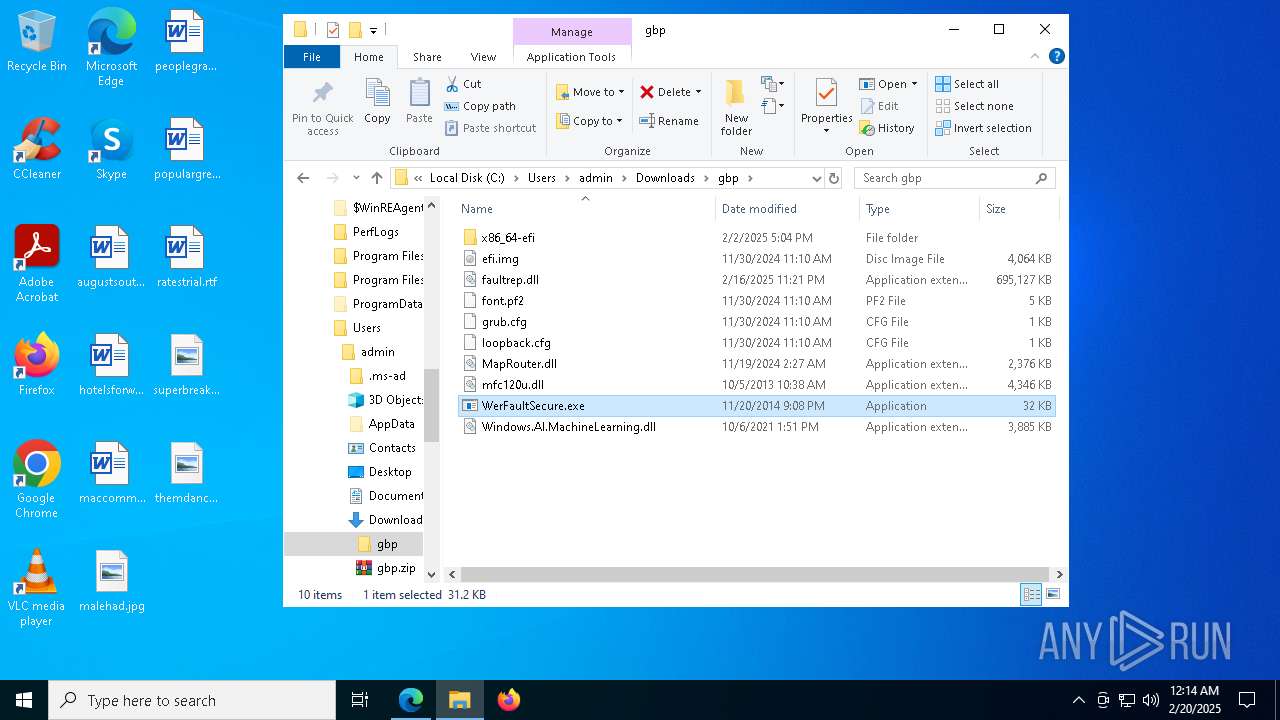
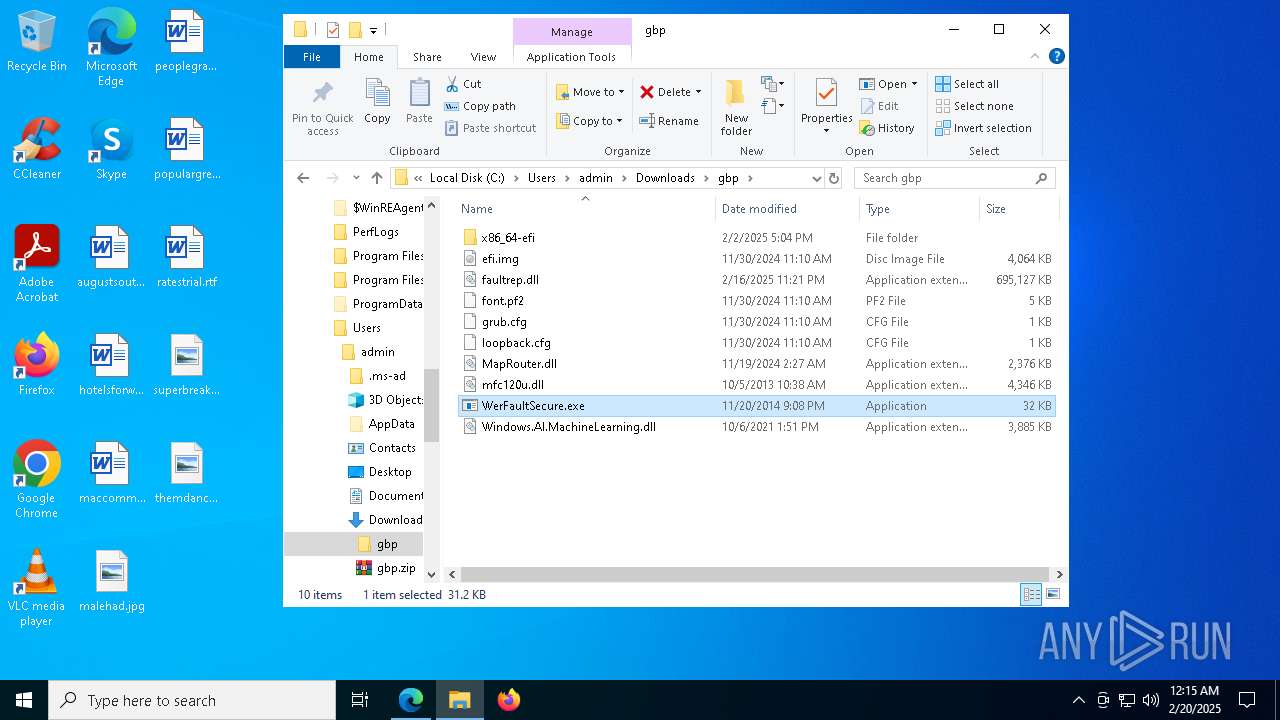
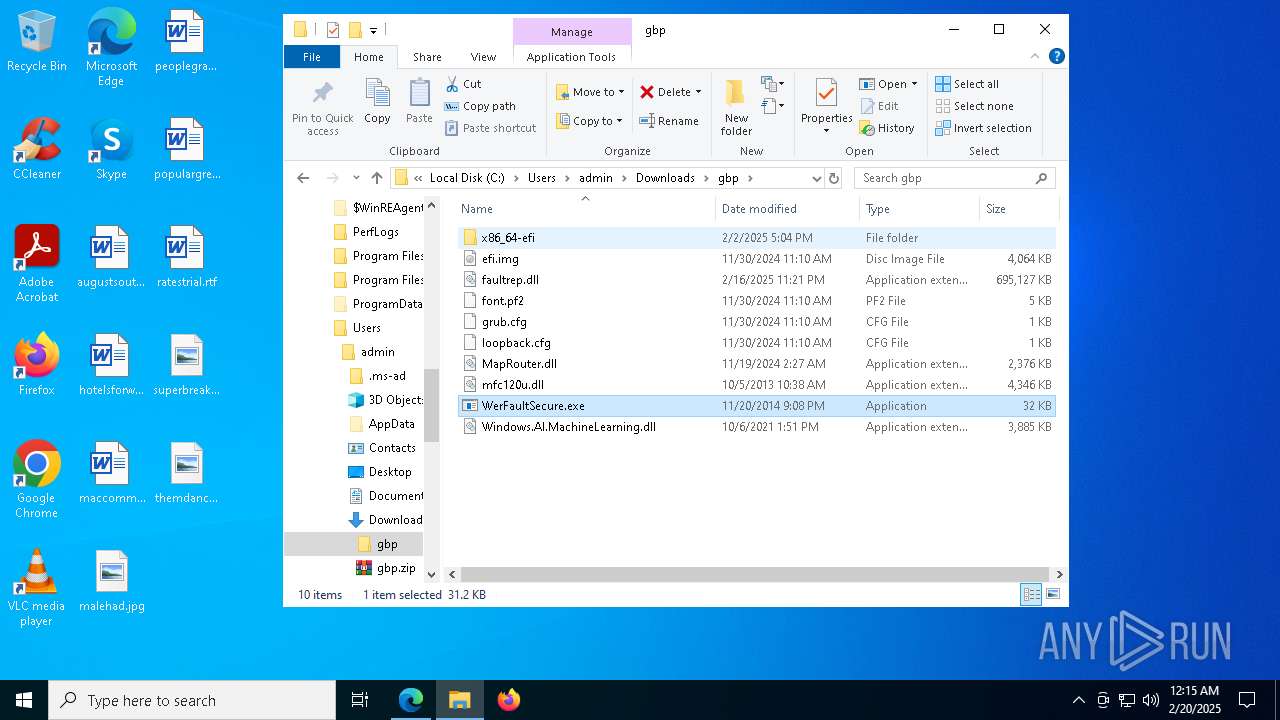
MALICIOUS
LUMMA mutex has been found
- WerFaultSecure.exe (PID: 7336)
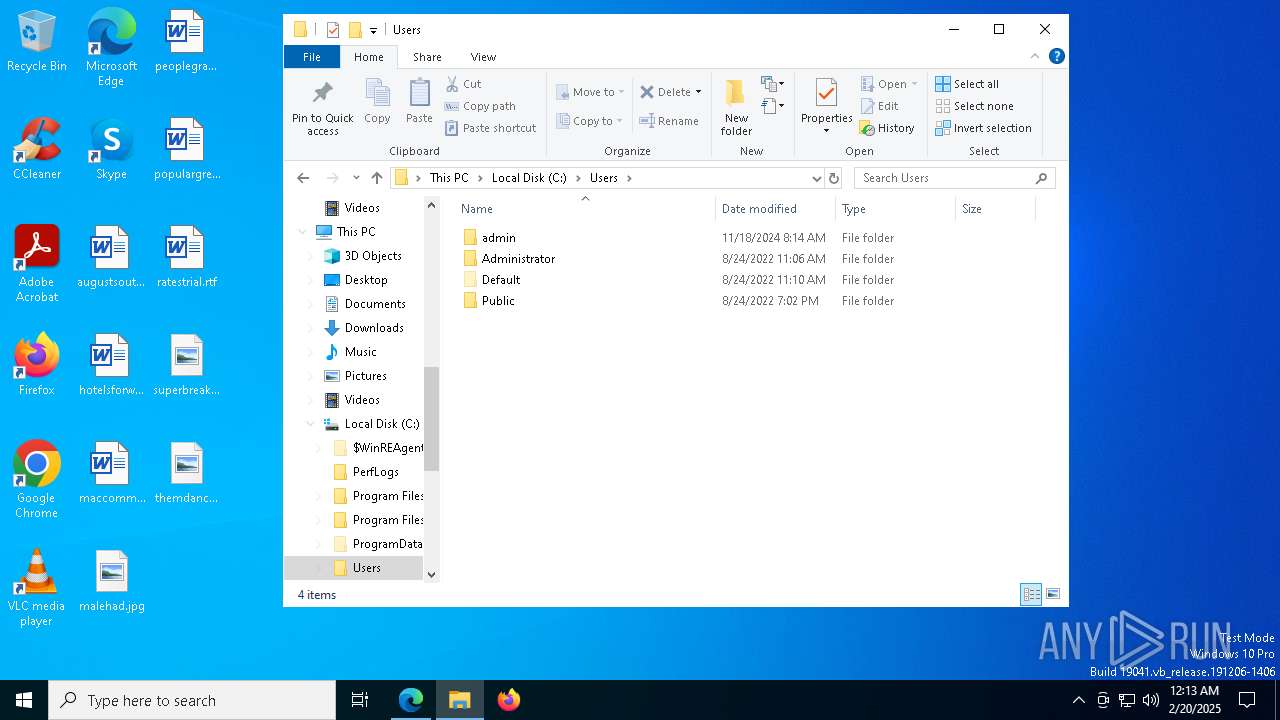
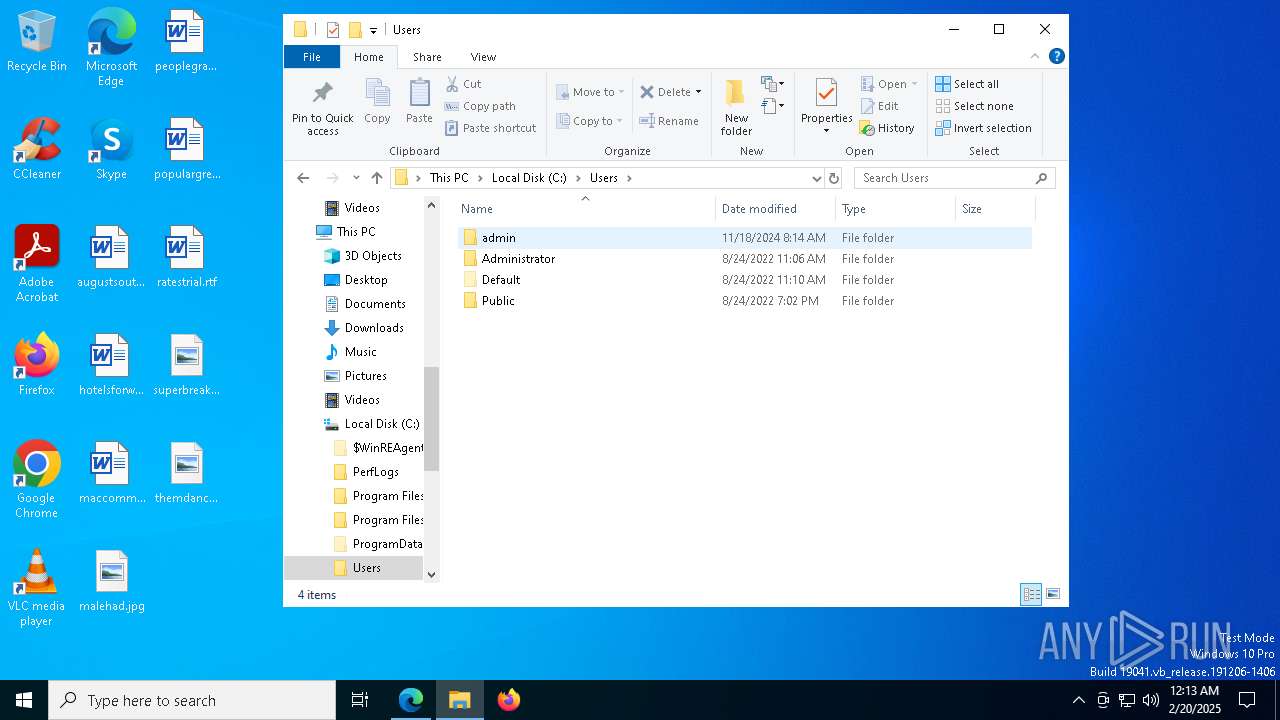
Actions looks like stealing of personal data
- WerFaultSecure.exe (PID: 7336)
Steals credentials from Web Browsers
- WerFaultSecure.exe (PID: 7336)
LUMMA has been detected (SURICATA)
- WerFaultSecure.exe (PID: 7336)
SUSPICIOUS
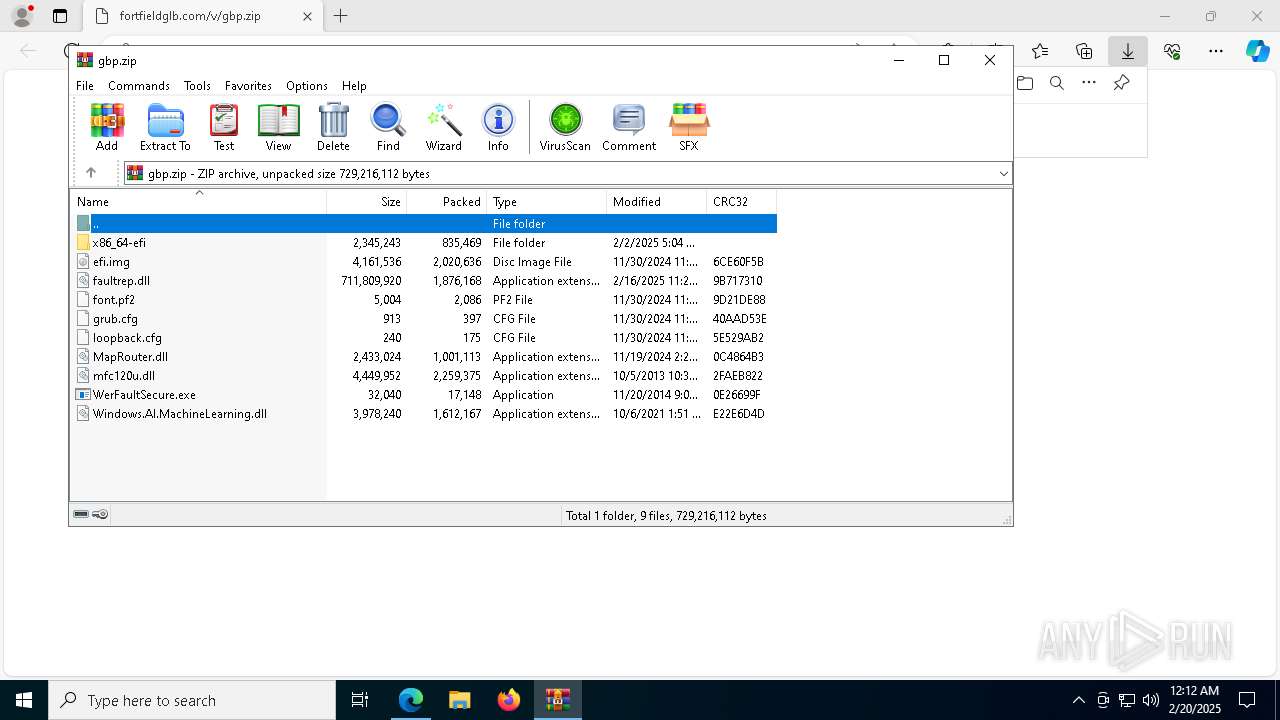
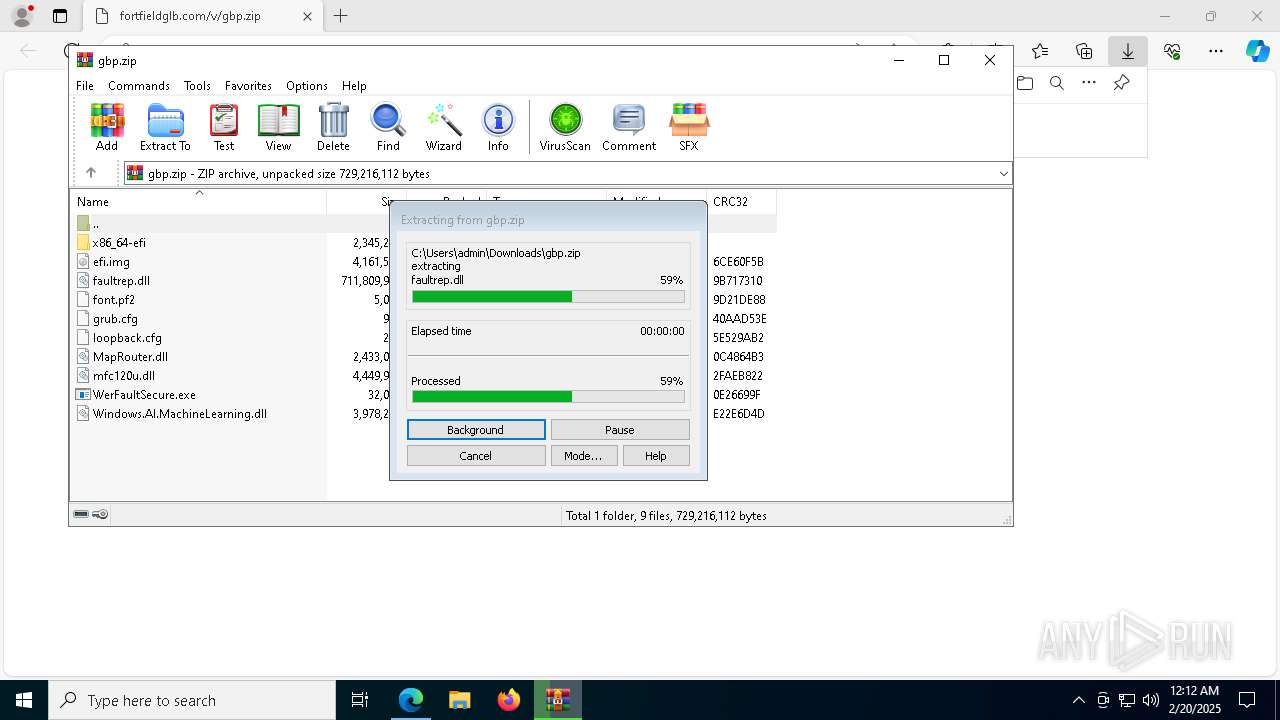
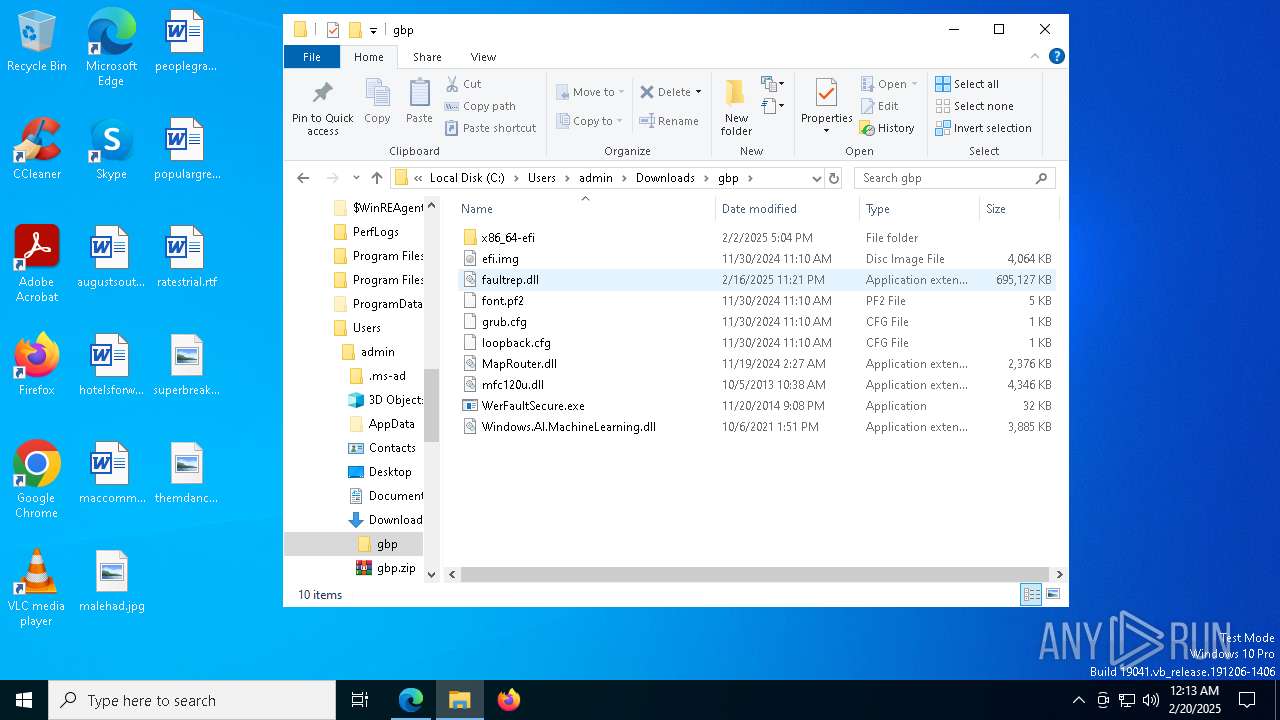
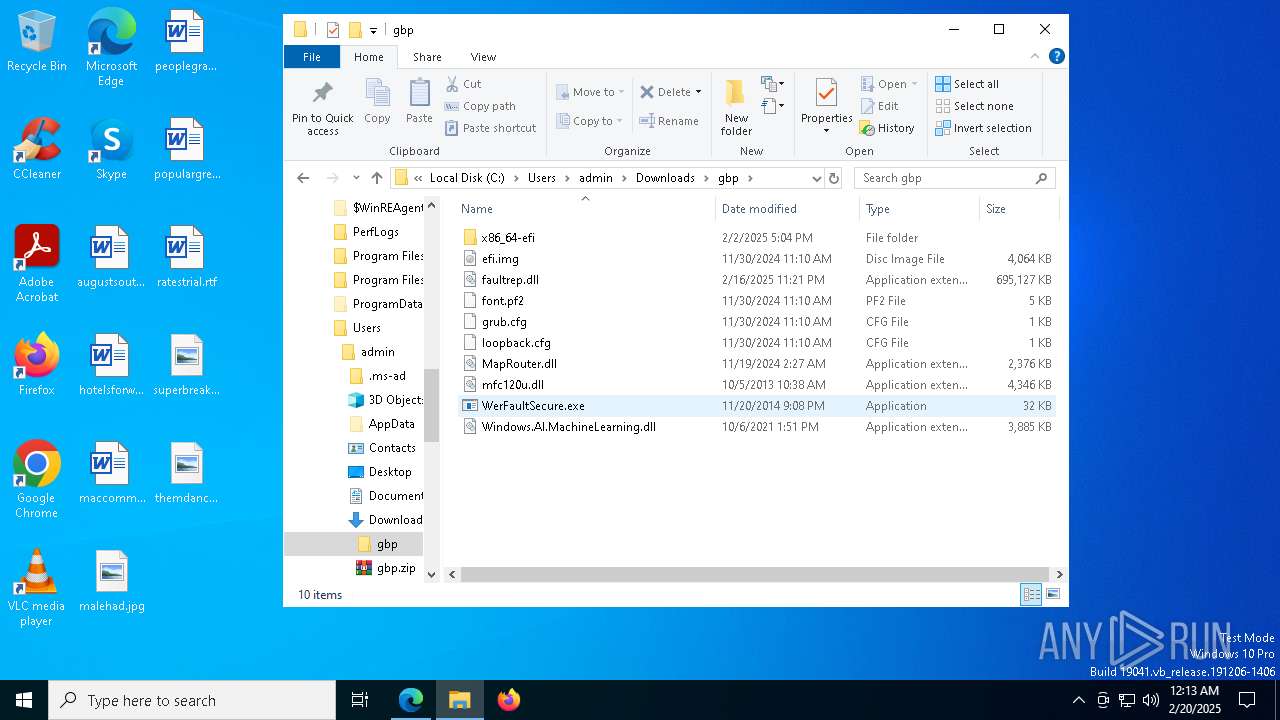
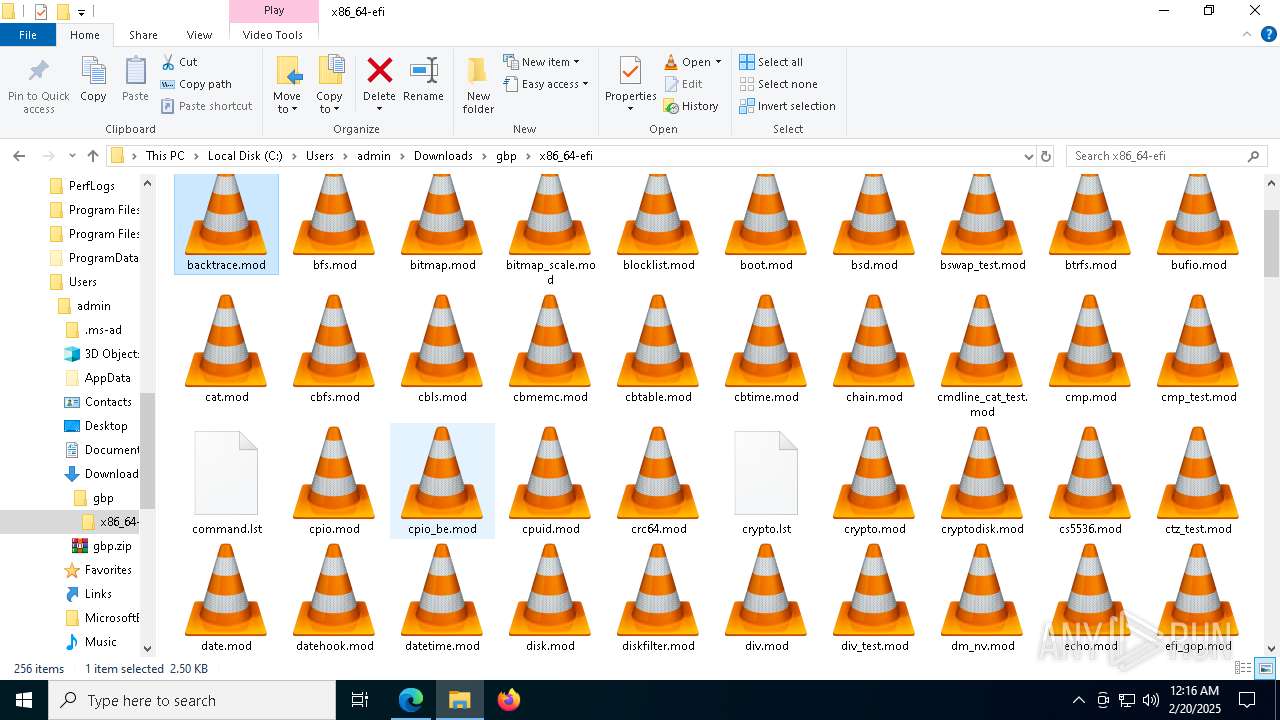
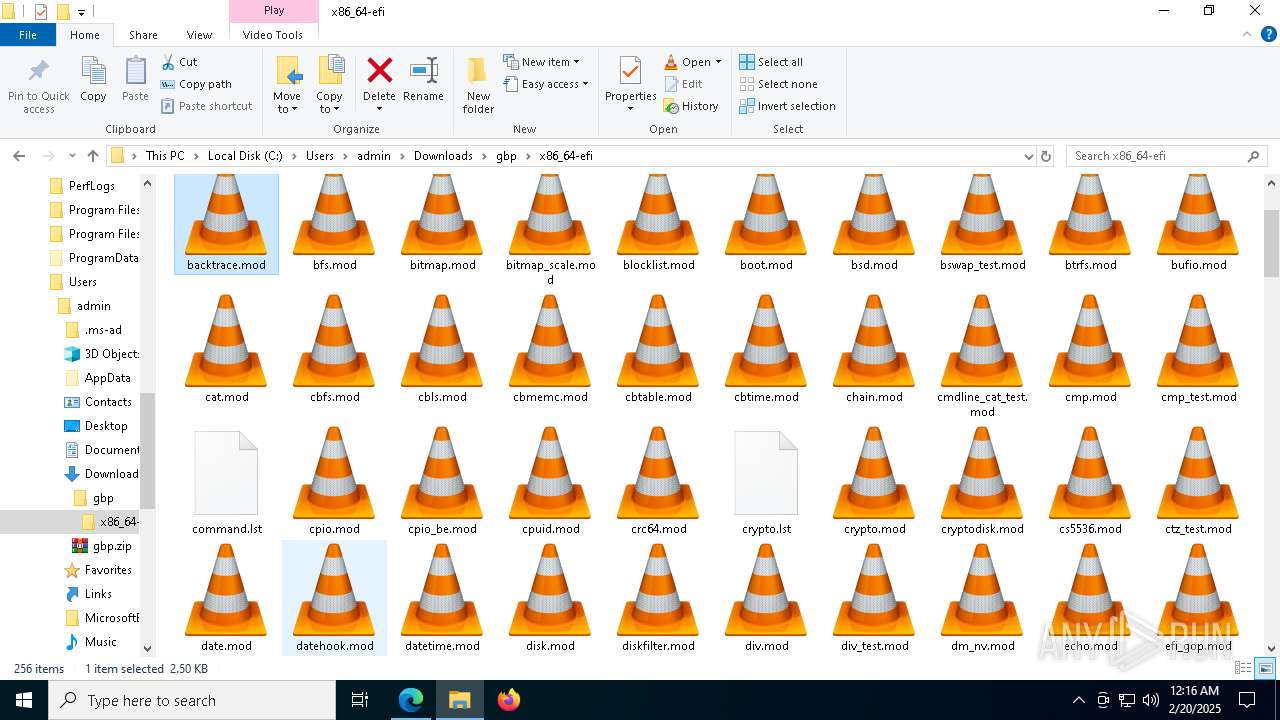
Process drops legitimate windows executable
- WinRAR.exe (PID: 7204)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- WerFaultSecure.exe (PID: 7336)
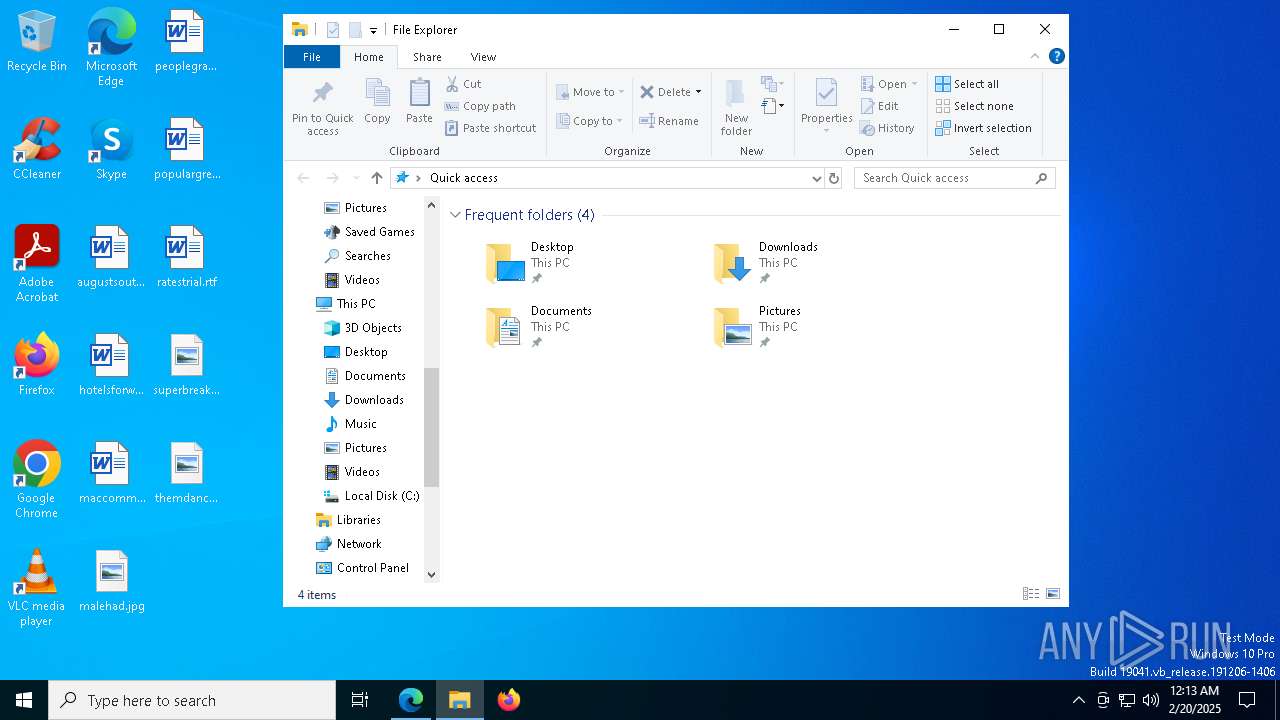
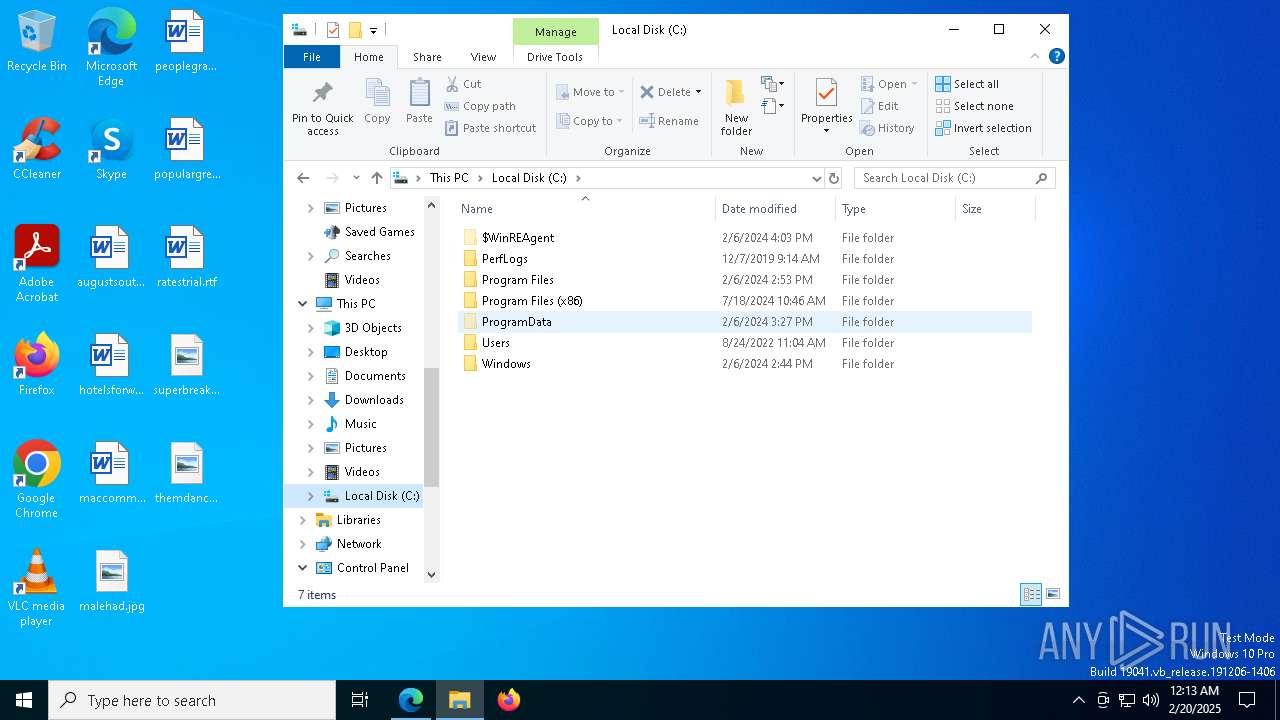
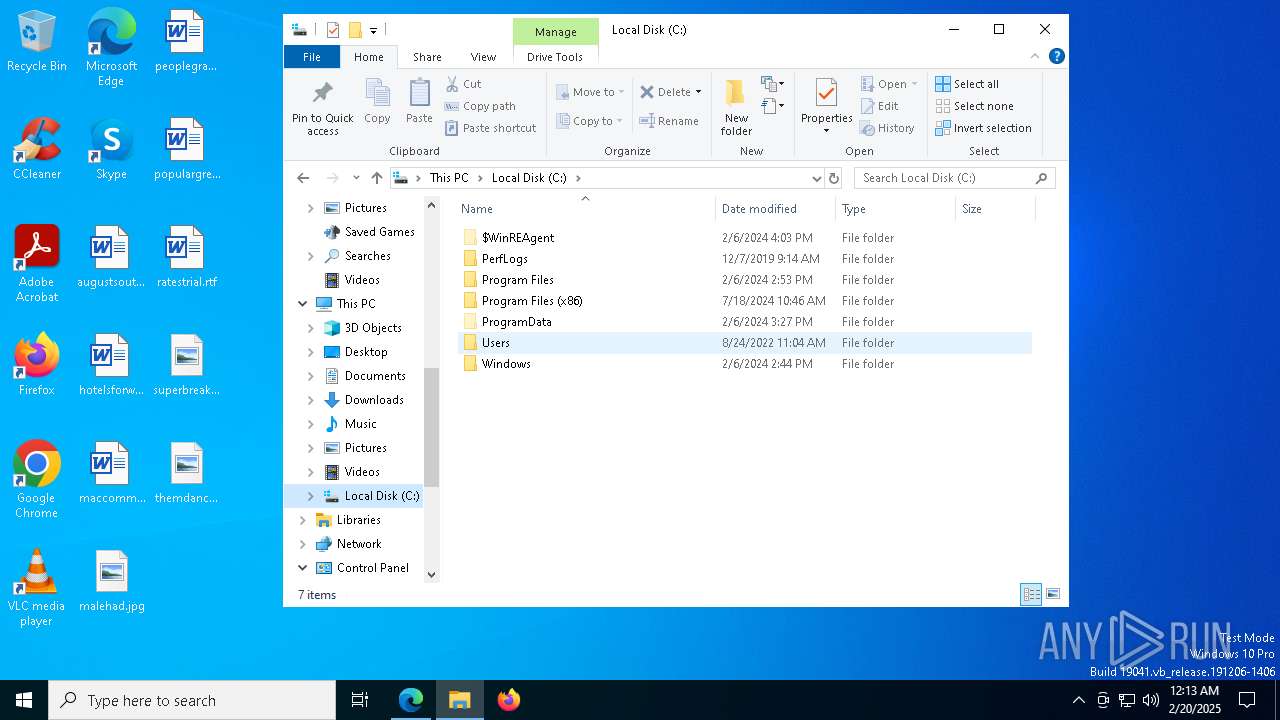
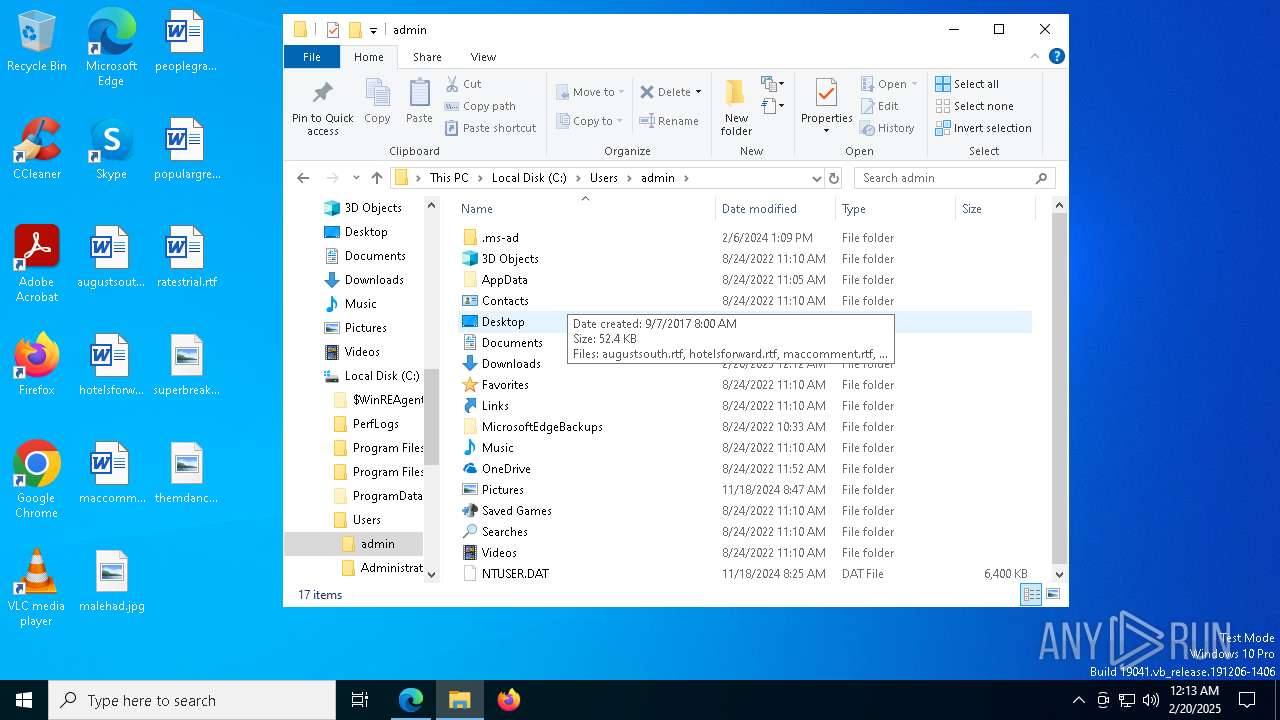
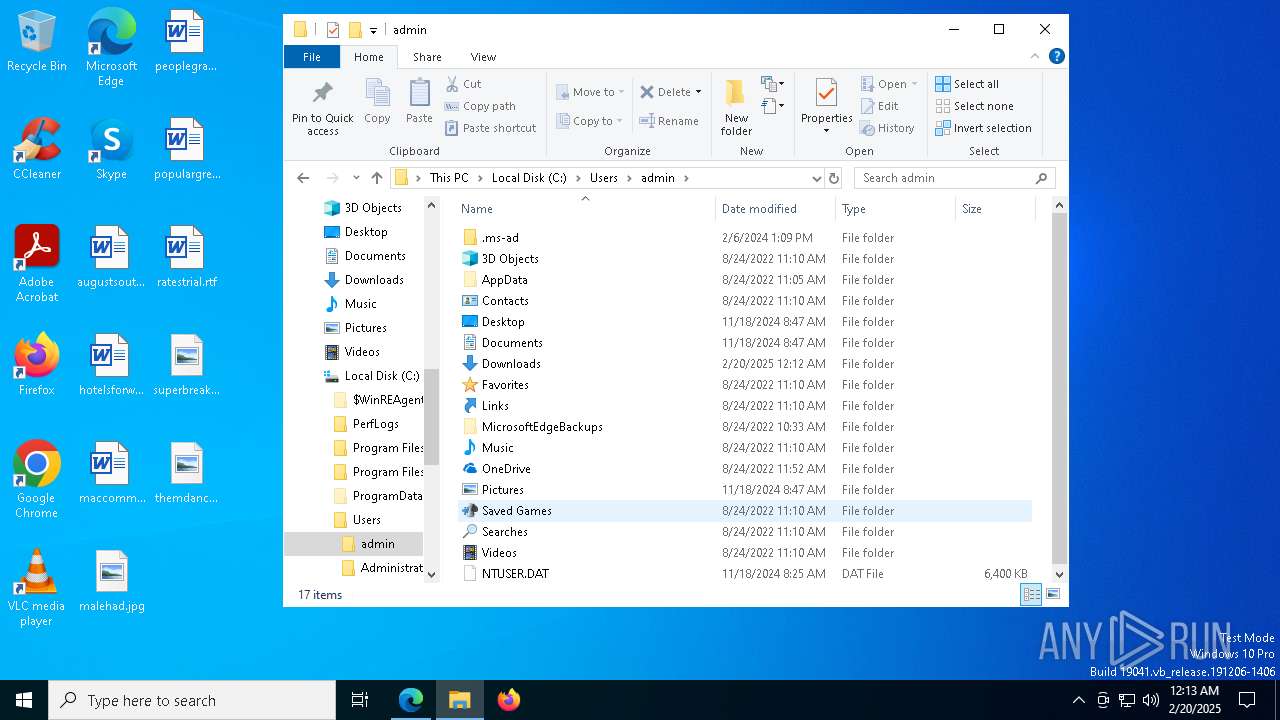
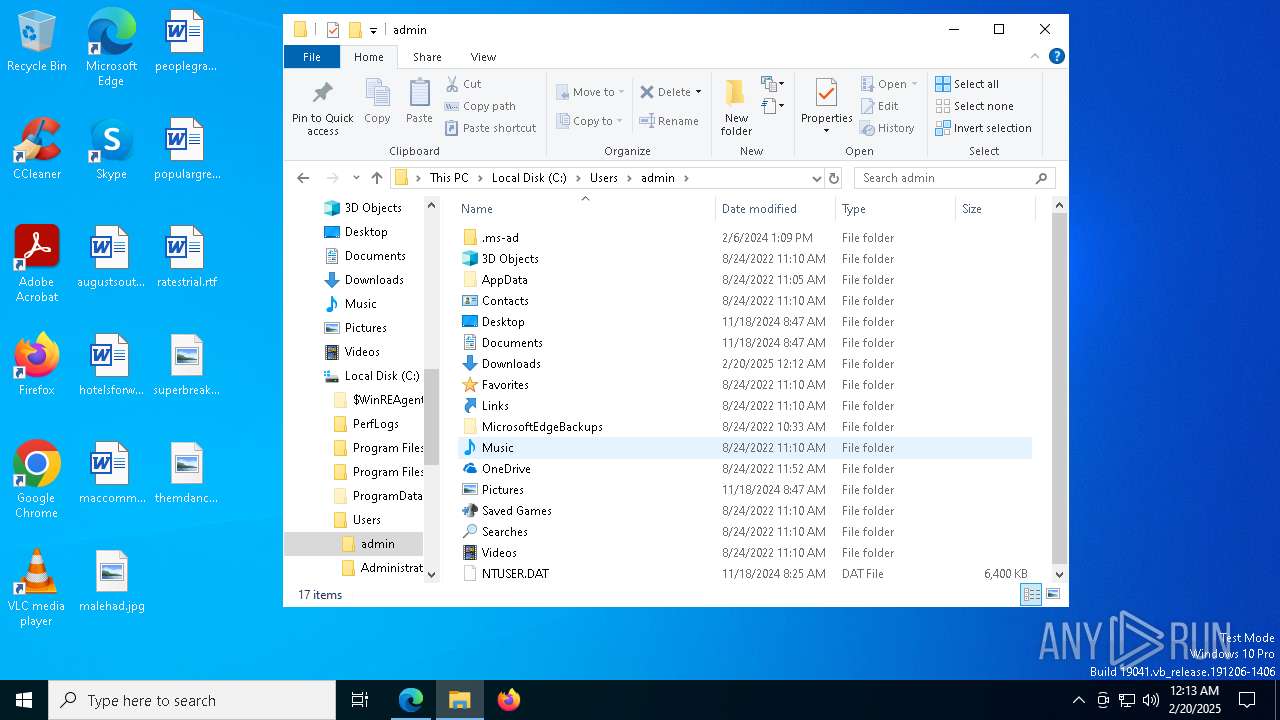
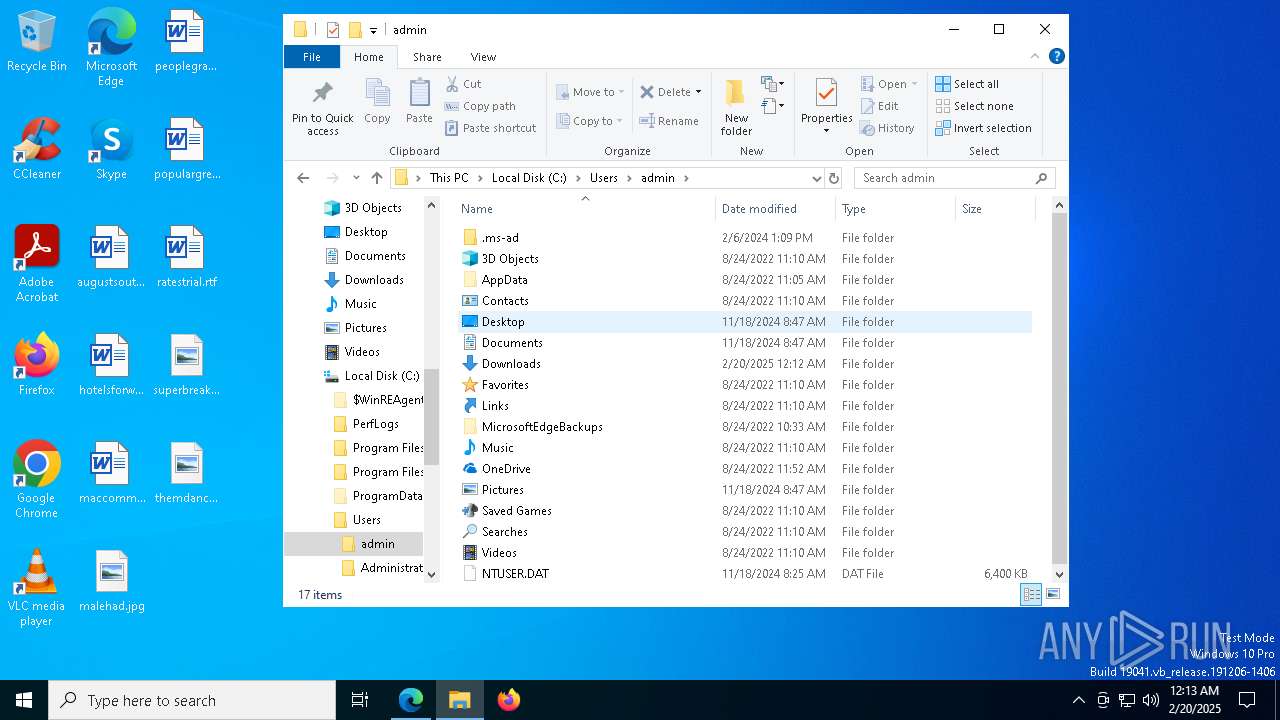
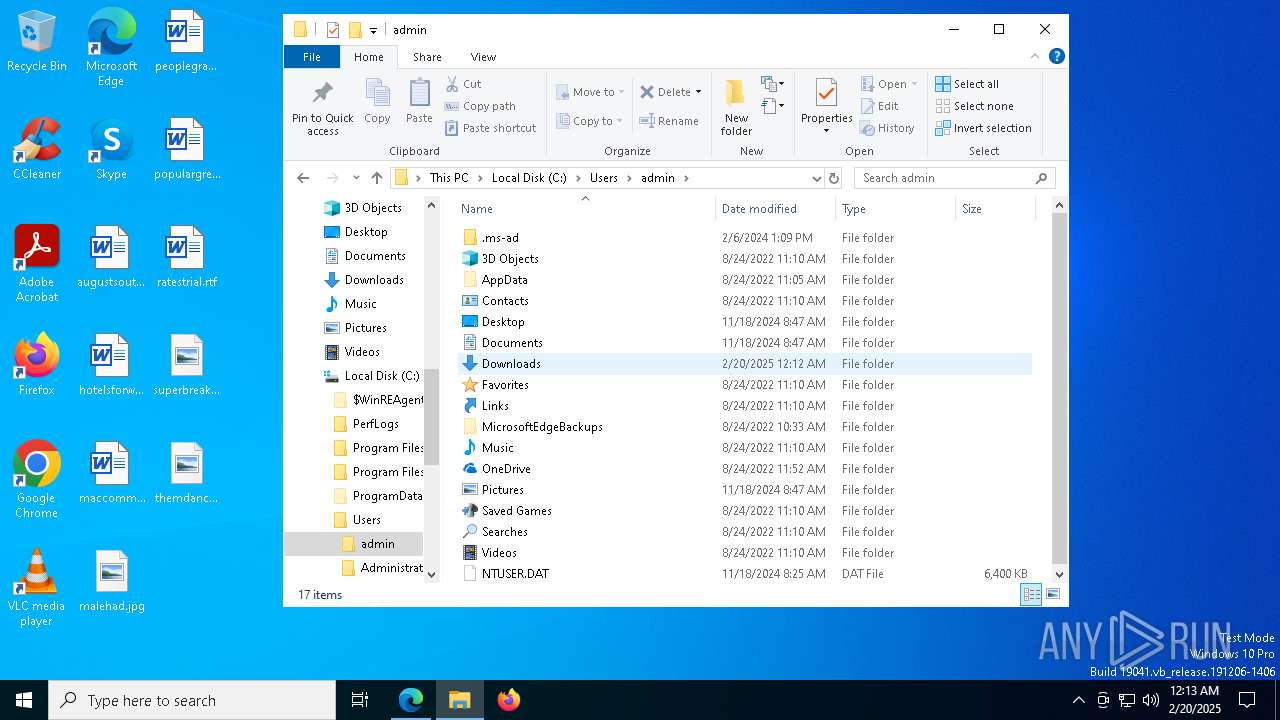
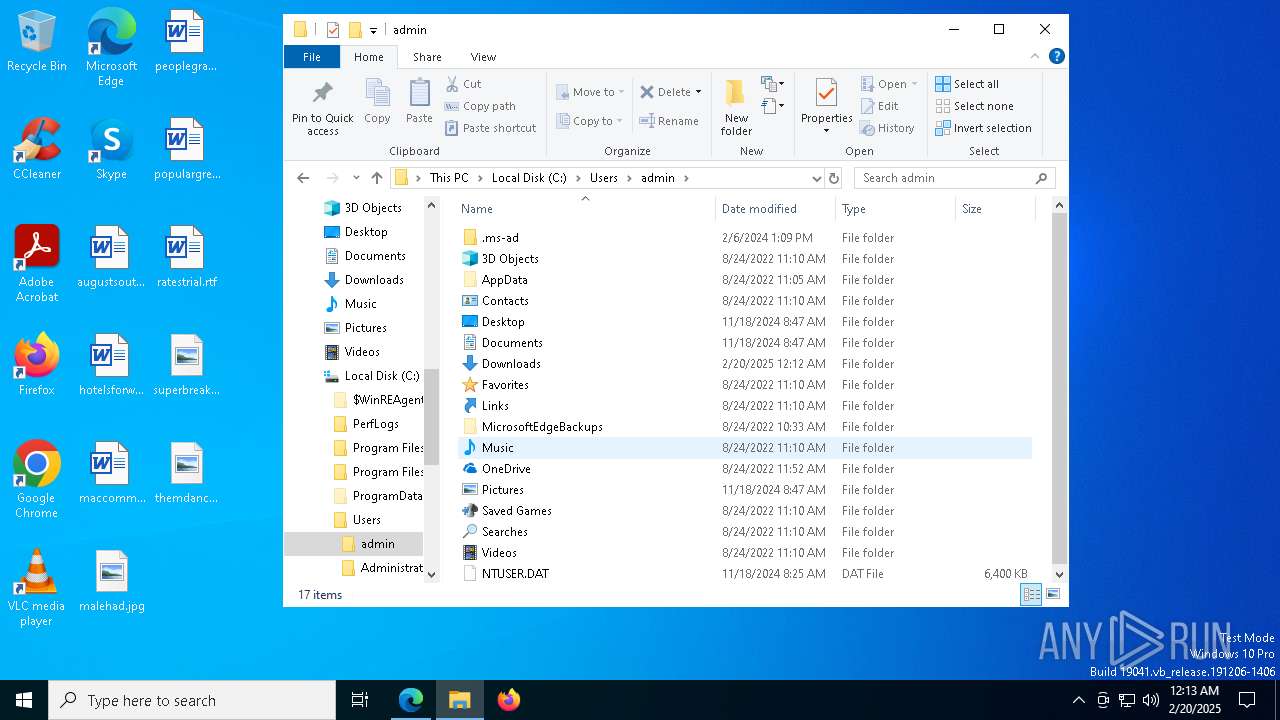
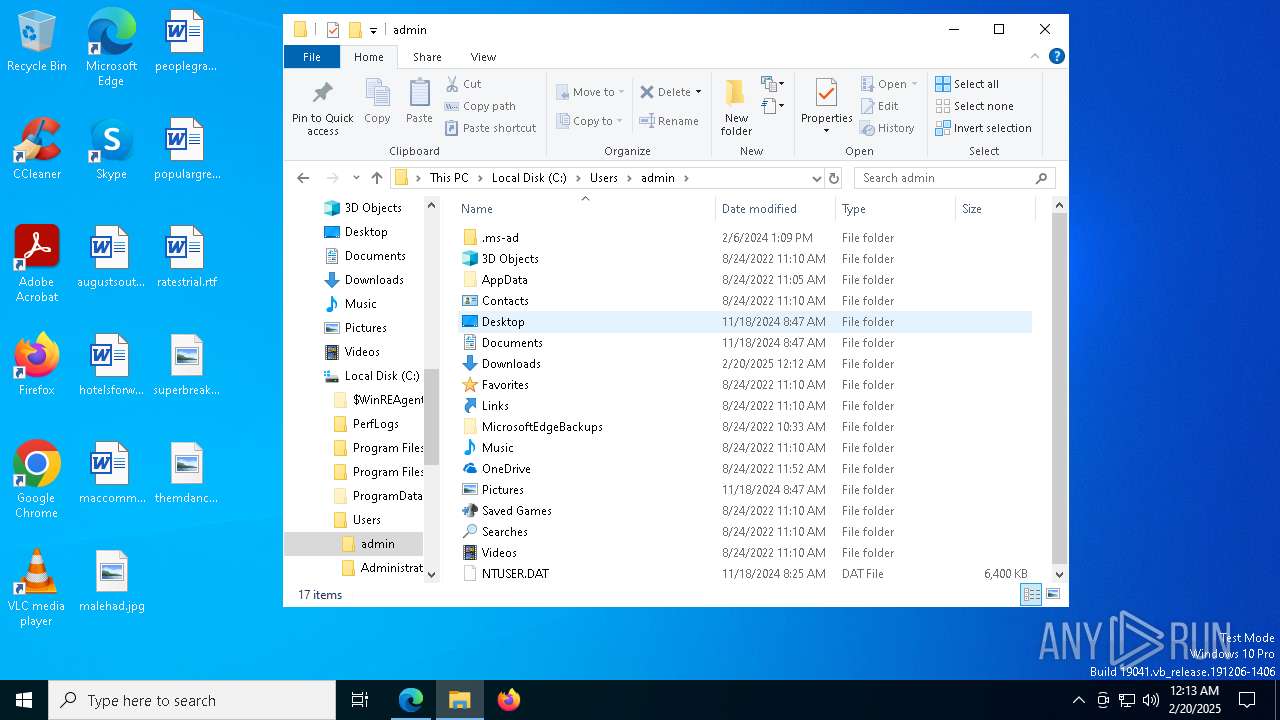
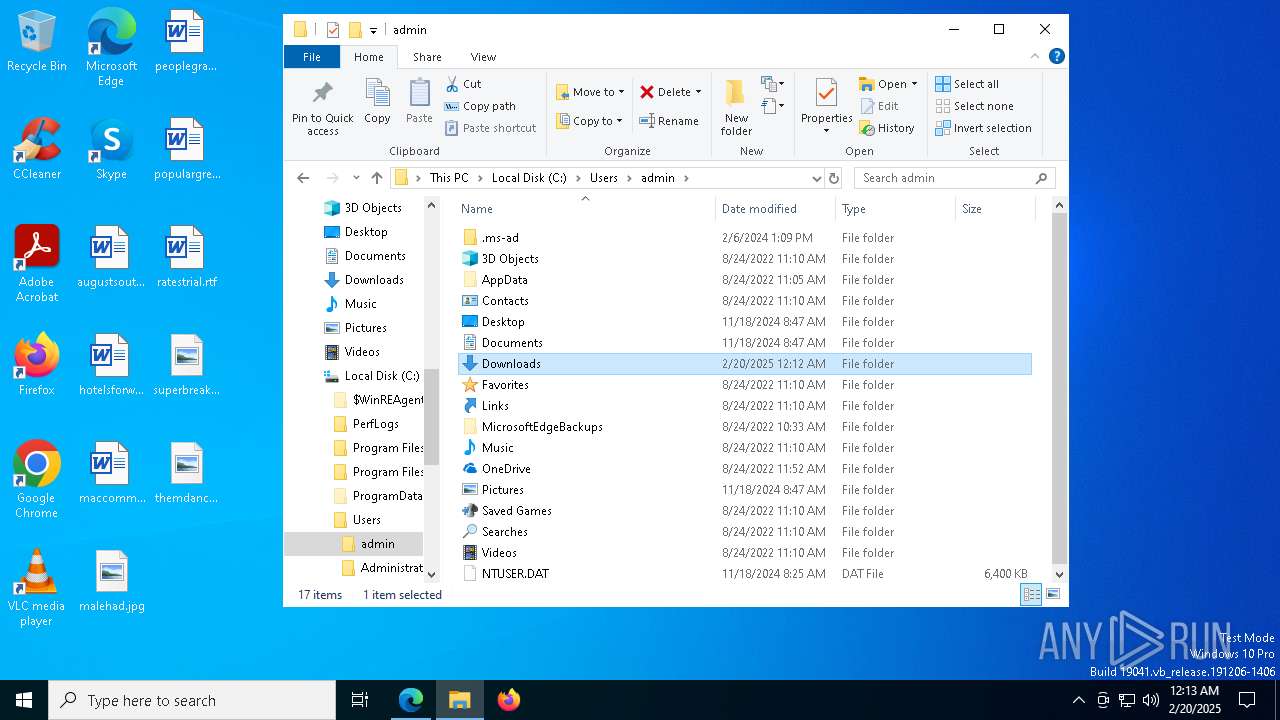
Searches for installed software
- WerFaultSecure.exe (PID: 7336)
INFO
Reads Environment values
- identity_helper.exe (PID: 6984)
Checks supported languages
- identity_helper.exe (PID: 6984)
- WerFaultSecure.exe (PID: 7336)
- vlc.exe (PID: 6084)
Application launched itself
- msedge.exe (PID: 5496)
Reads the computer name
- identity_helper.exe (PID: 6984)
- WerFaultSecure.exe (PID: 7336)
- vlc.exe (PID: 6084)
Reads the software policy settings
- WerFaultSecure.exe (PID: 7336)
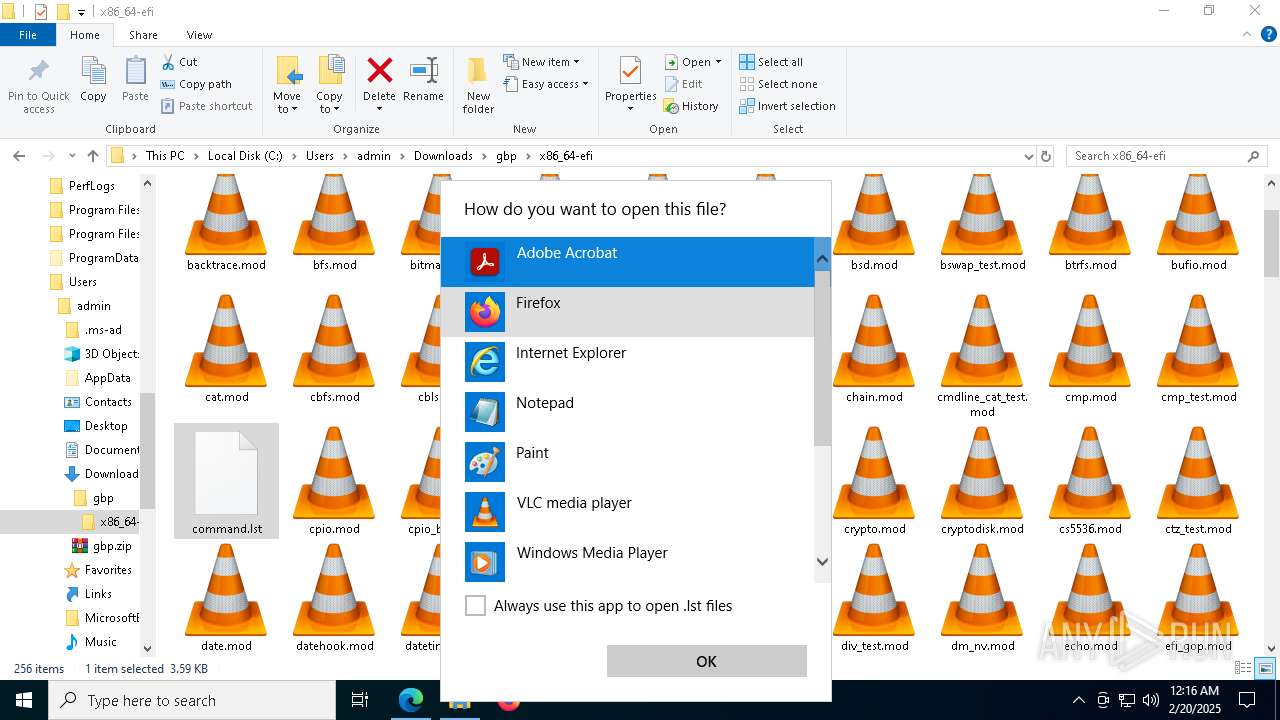
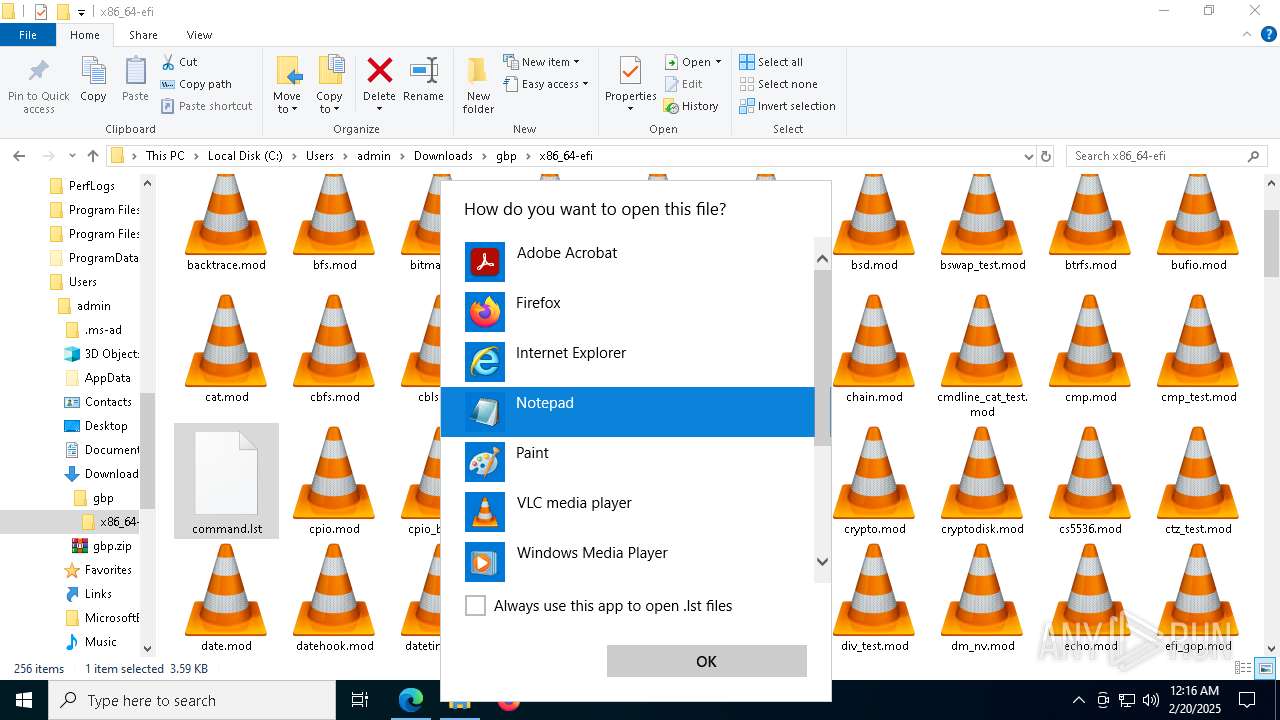
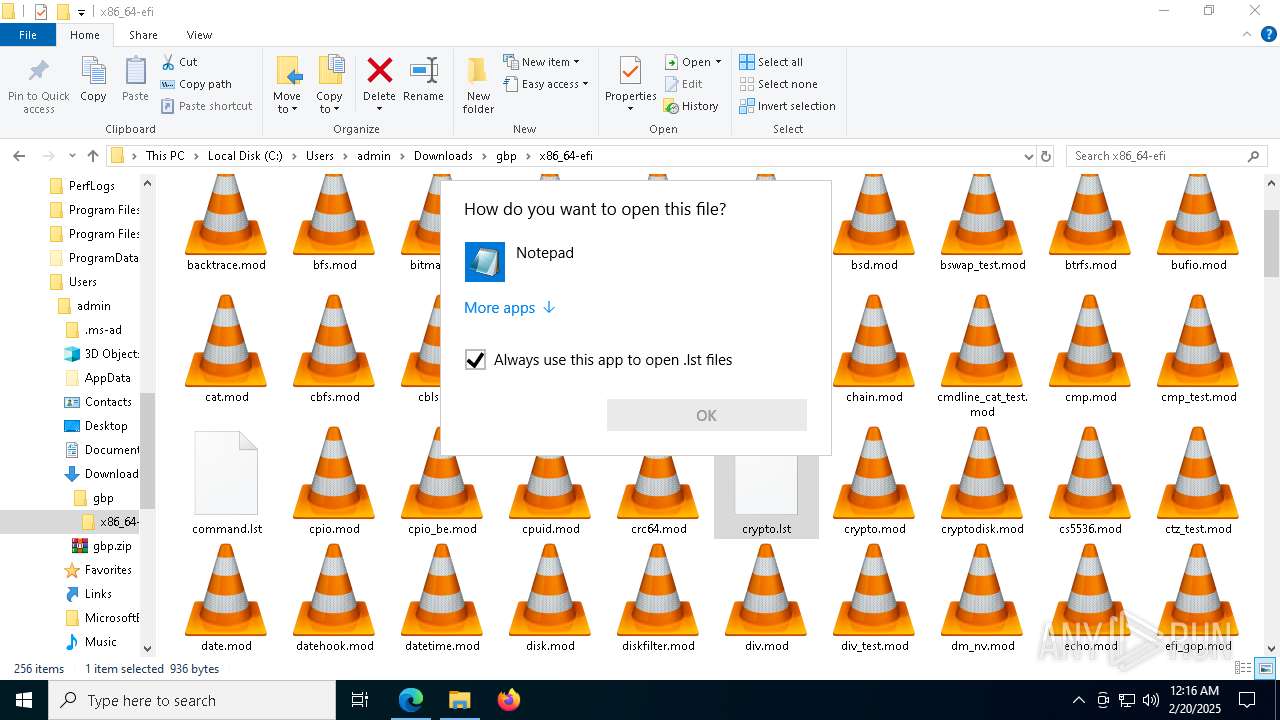
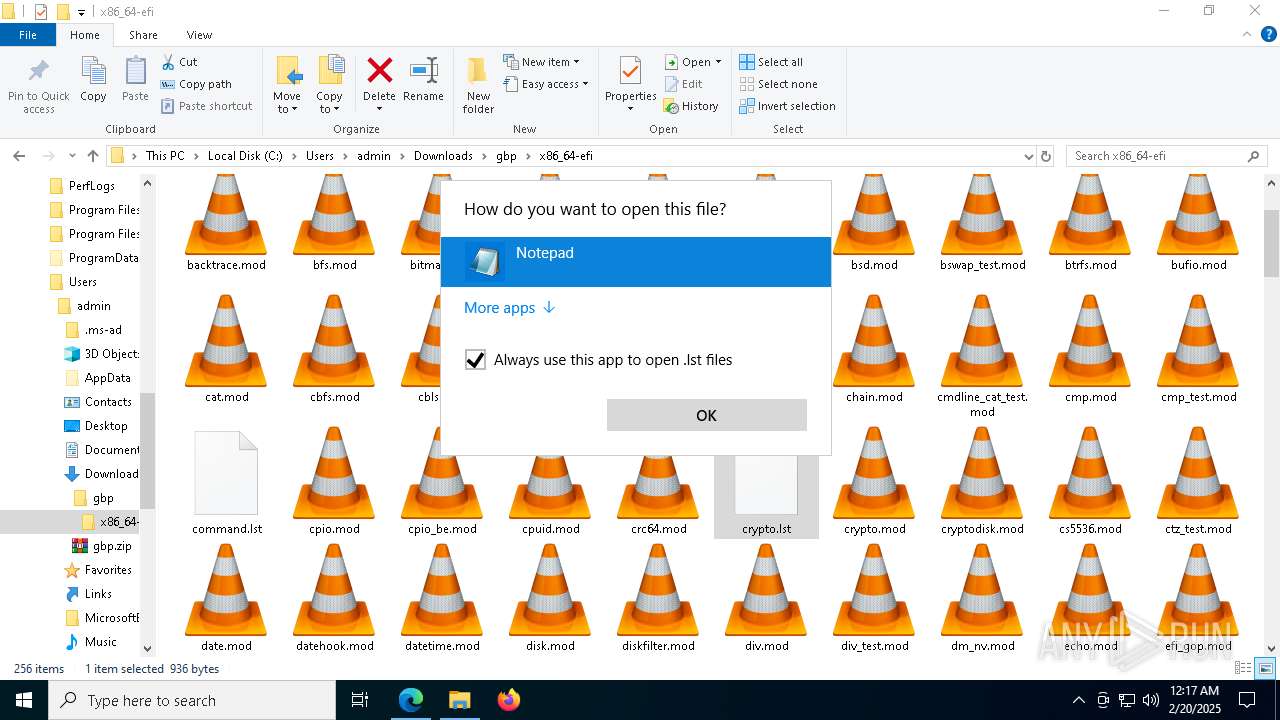
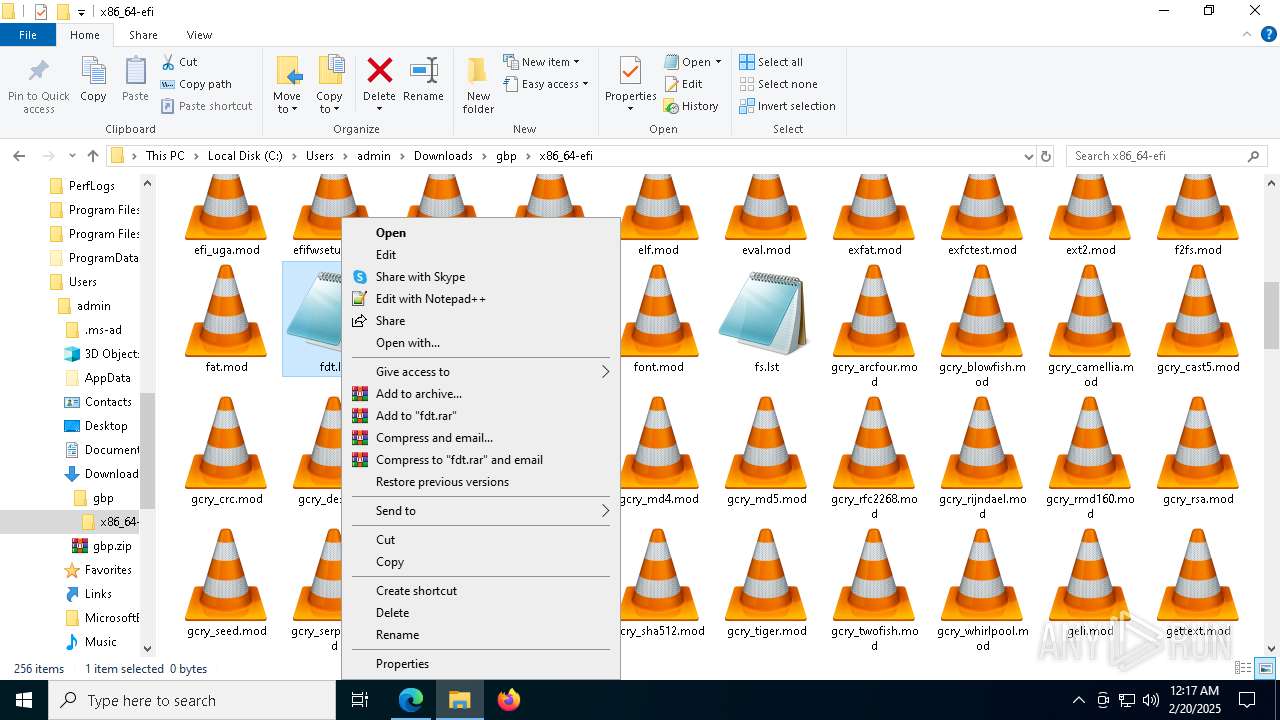
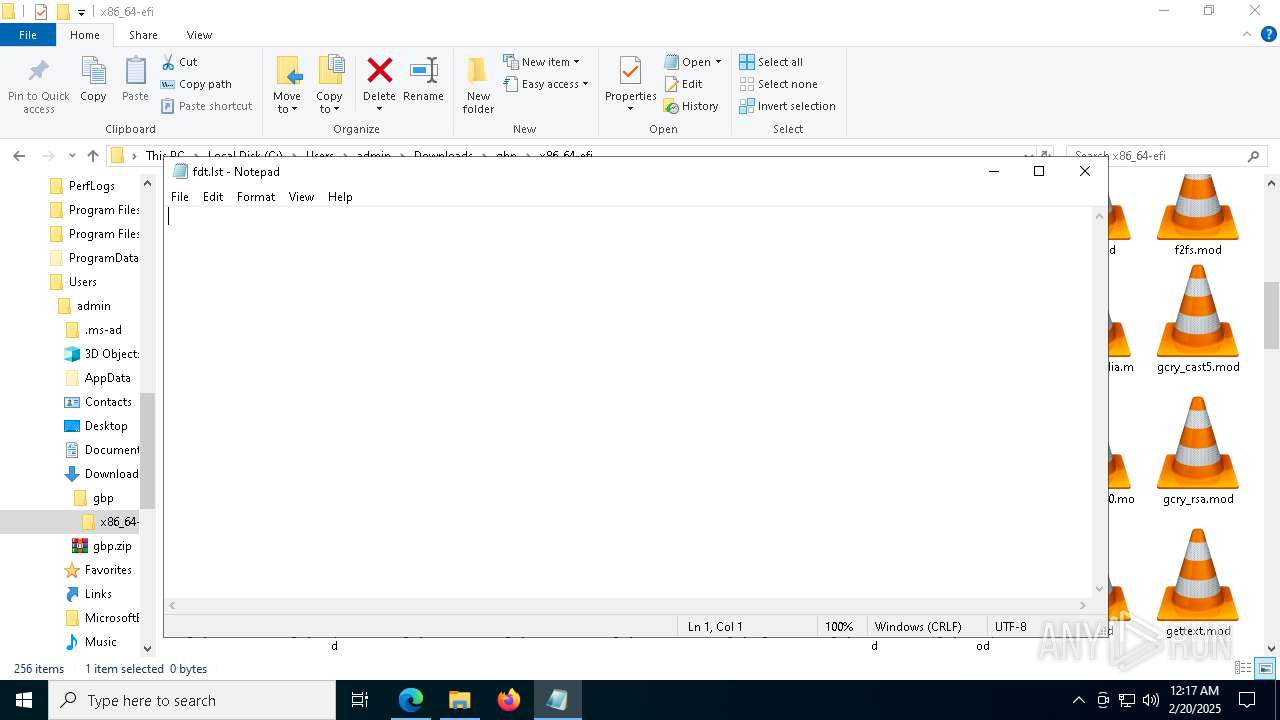
Manual execution by a user
- WerFaultSecure.exe (PID: 7336)
- vlc.exe (PID: 6084)
- notepad.exe (PID: 7464)
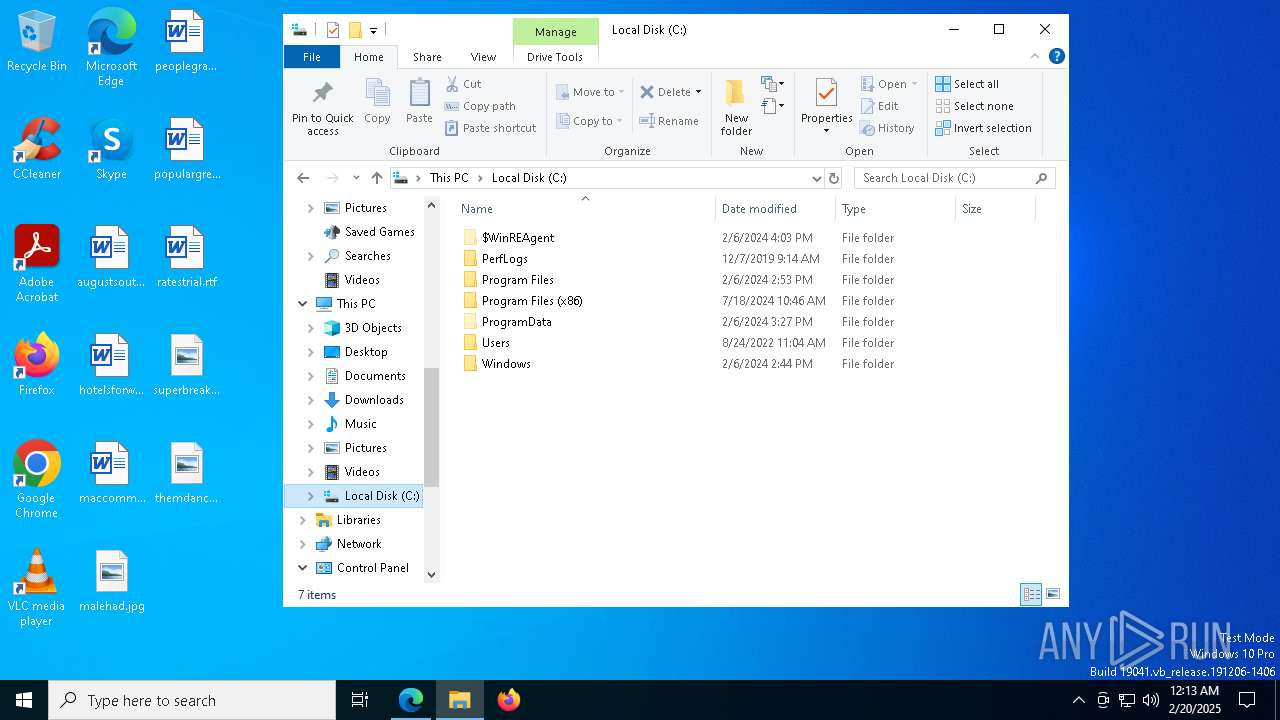
Creates files in the program directory
- WerFaultSecure.exe (PID: 7336)
Executable content was dropped or overwritten
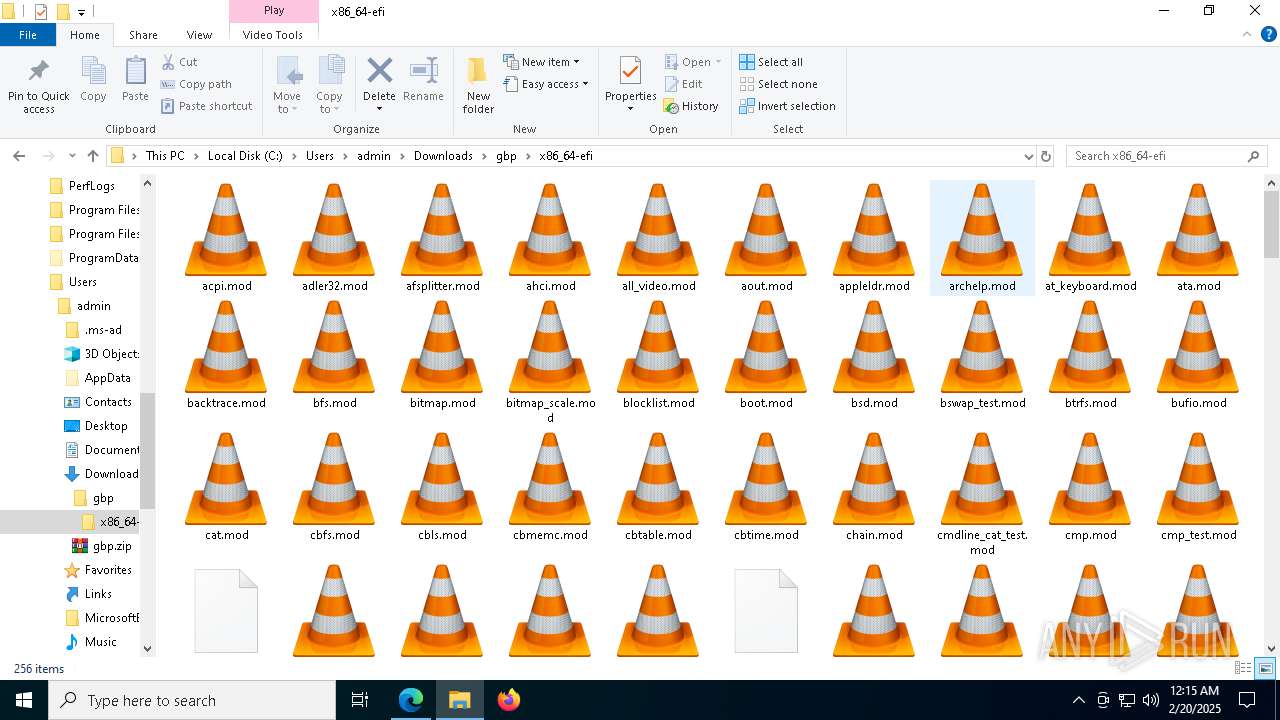
- WinRAR.exe (PID: 7204)
- msedge.exe (PID: 7636)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5496)
- OpenWith.exe (PID: 4840)
- OpenWith.exe (PID: 7364)
The sample compiled with english language support
- WinRAR.exe (PID: 7204)
- msedge.exe (PID: 7636)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7300)
- OpenWith.exe (PID: 7364)
- notepad.exe (PID: 1412)
- notepad.exe (PID: 7464)
- OpenWith.exe (PID: 4840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
191
Monitored processes
60
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6168 --field-trial-handle=2436,i,16586743651821535668,10141798116949154684,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6444 --field-trial-handle=2436,i,16586743651821535668,10141798116949154684,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ff8220f5fd8,0x7ff8220f5fe4,0x7ff8220f5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
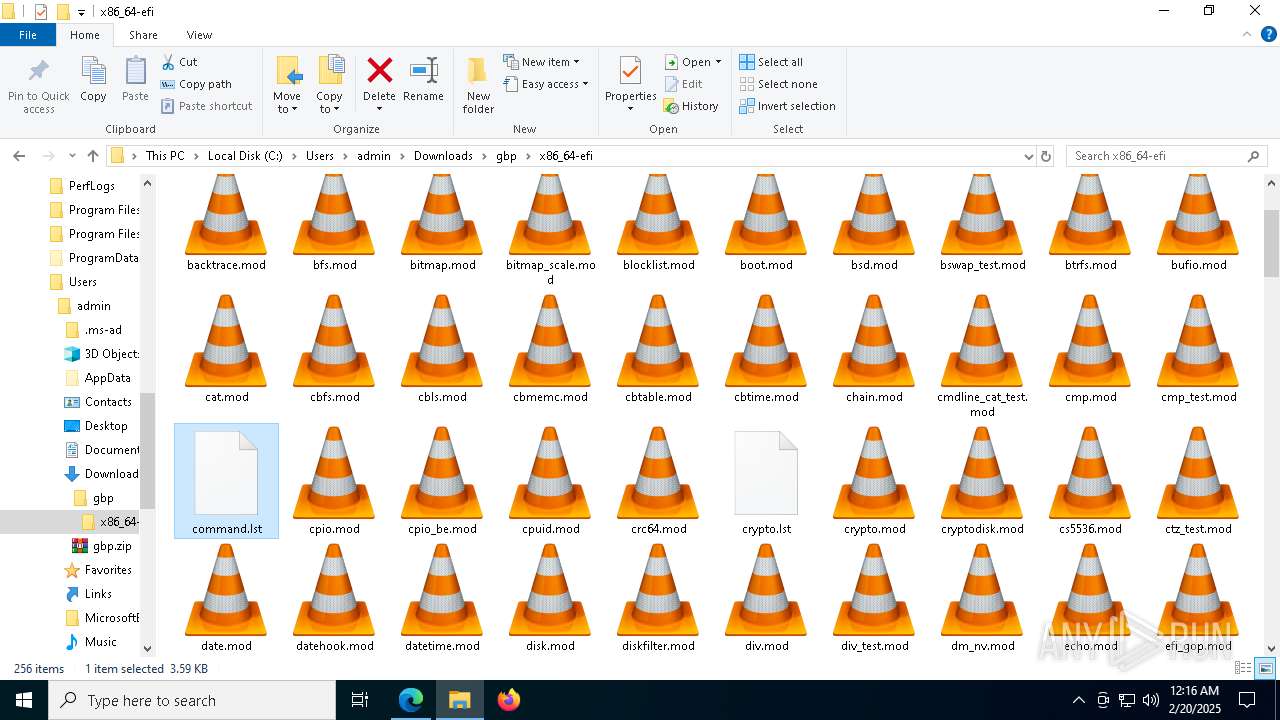
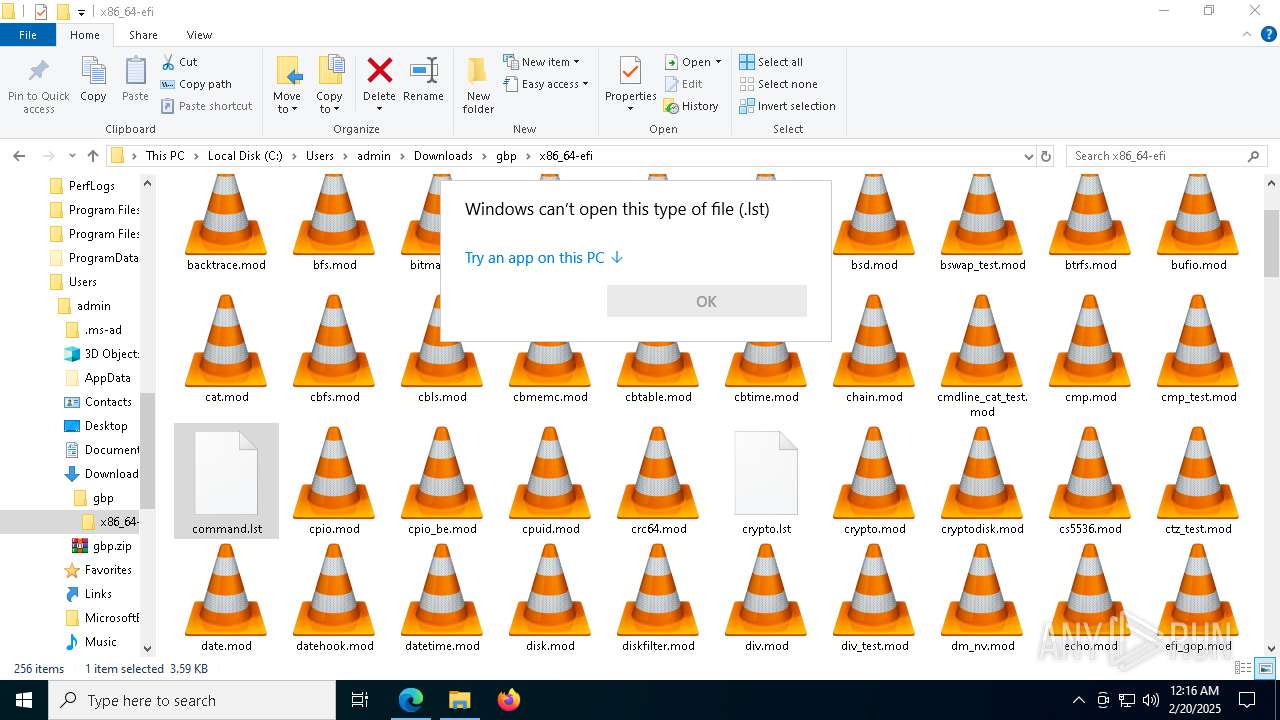
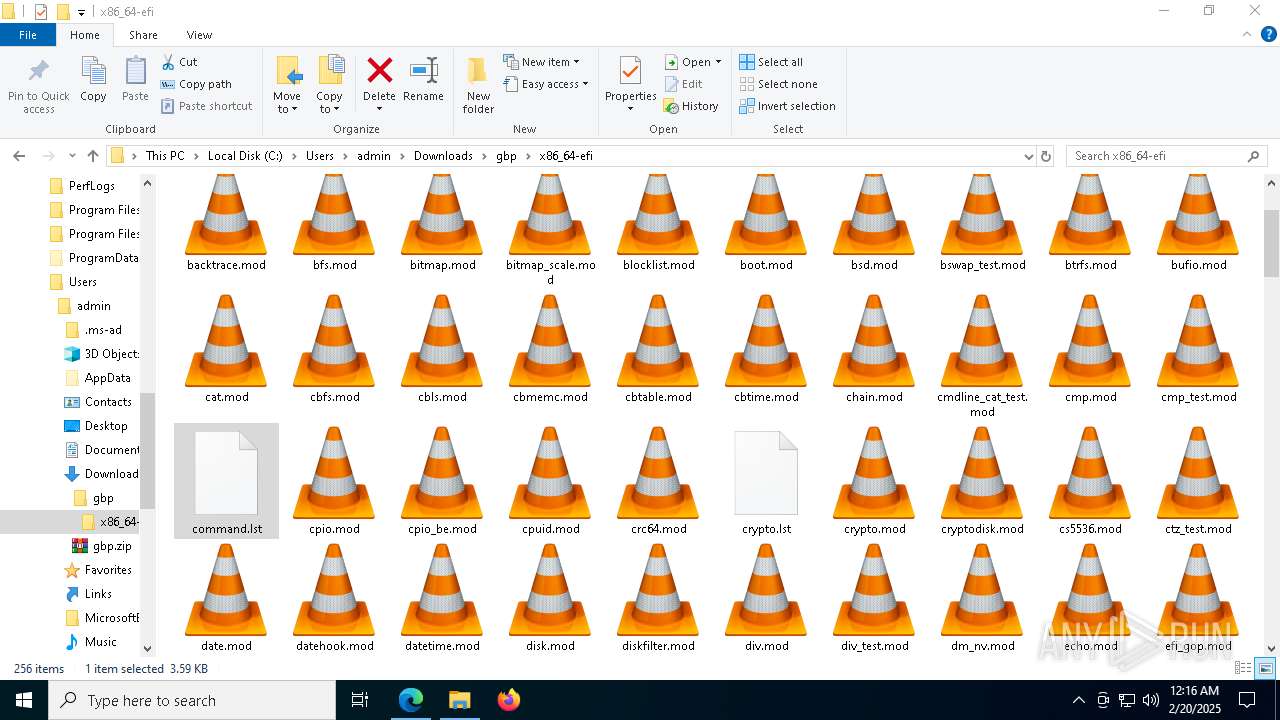
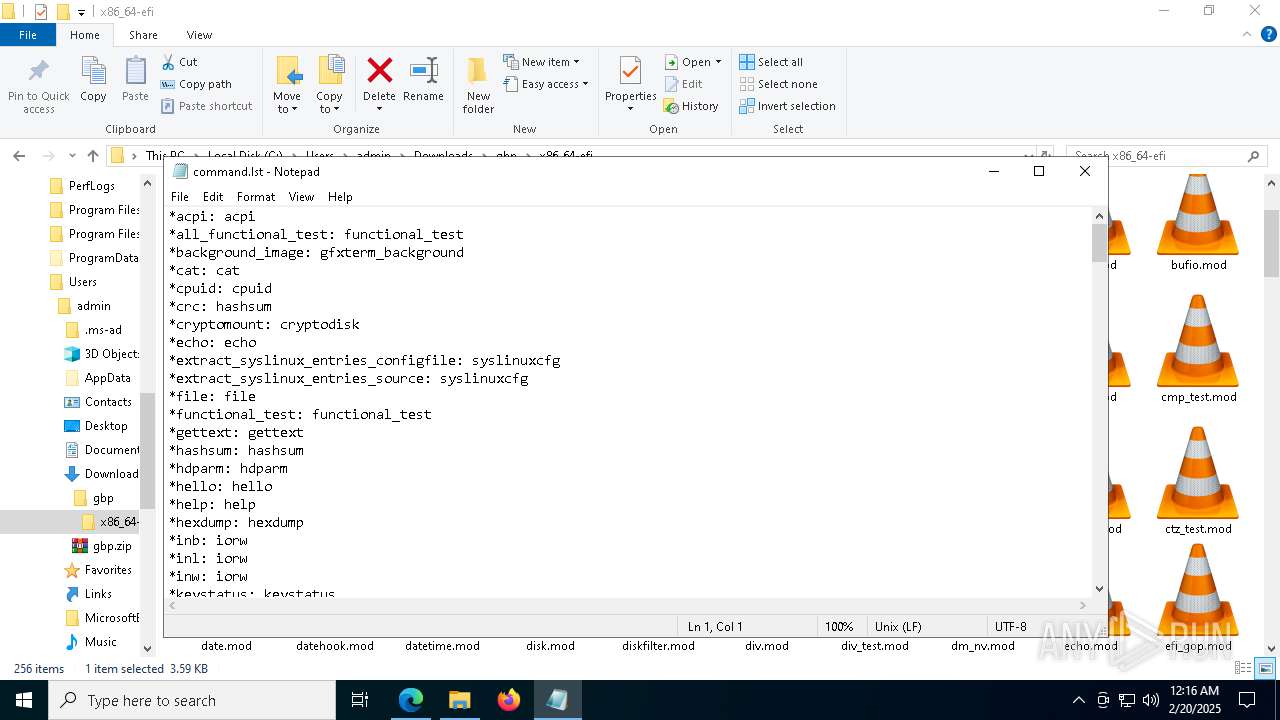
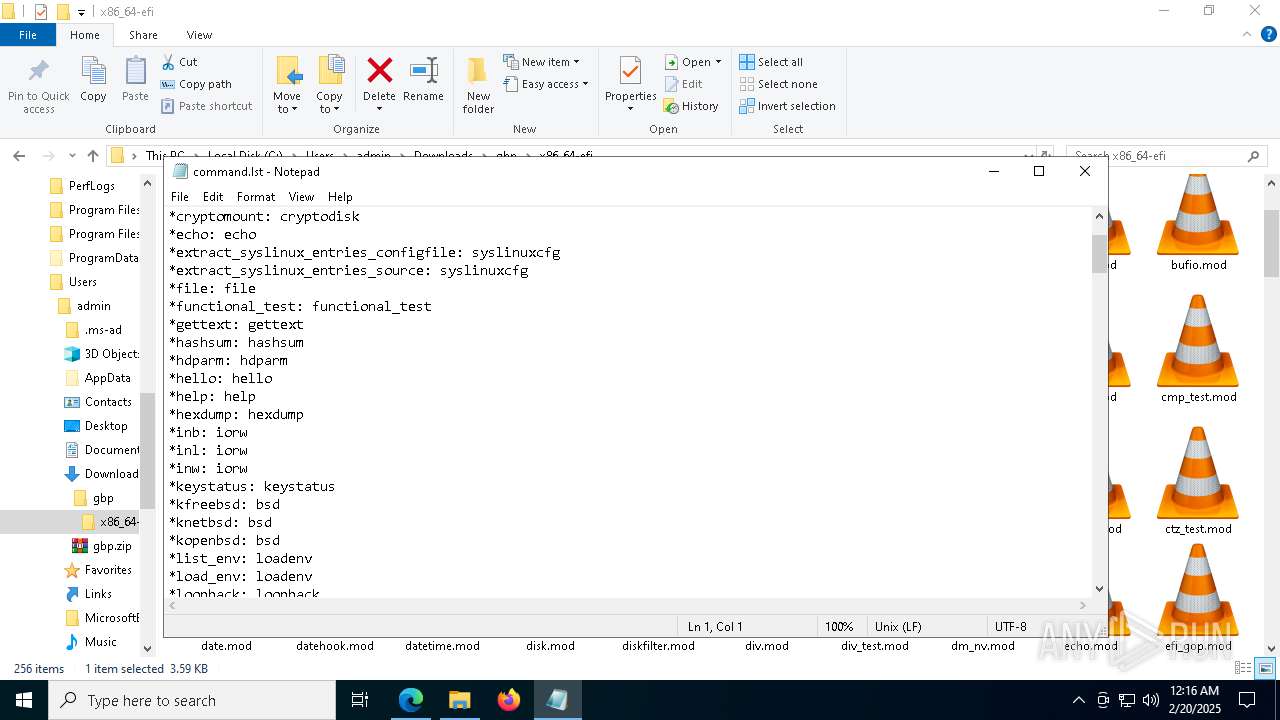
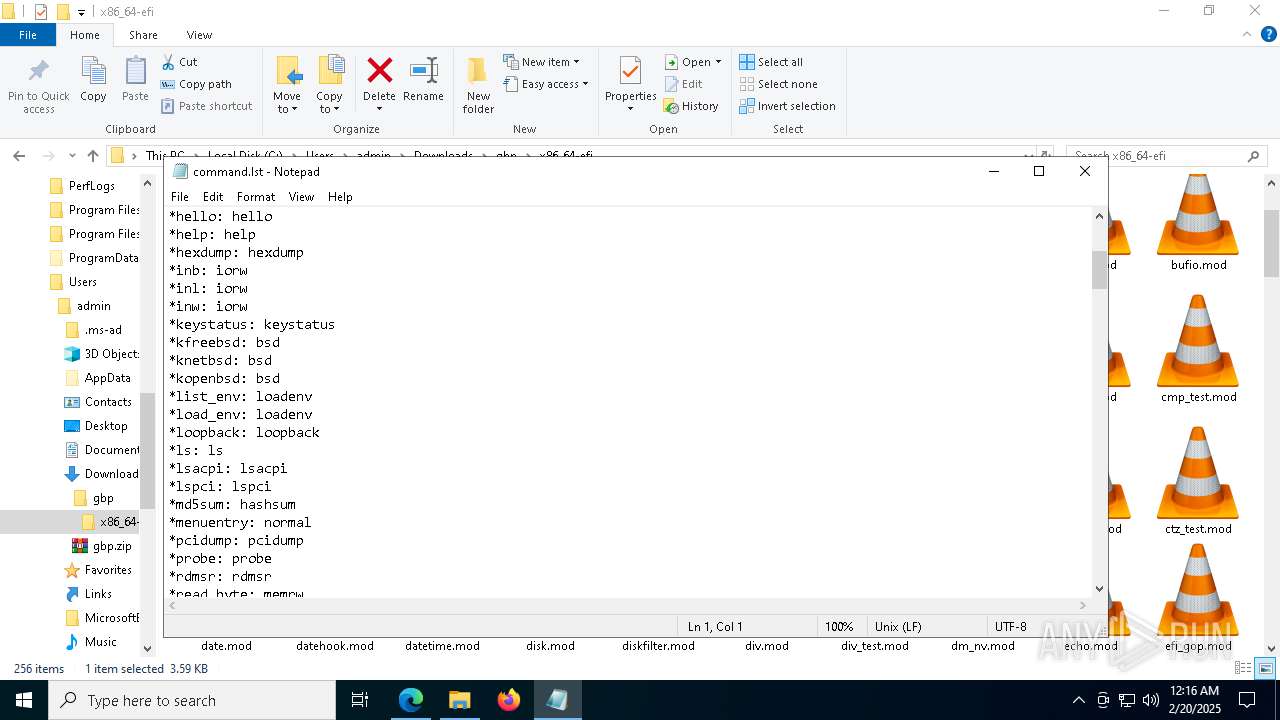
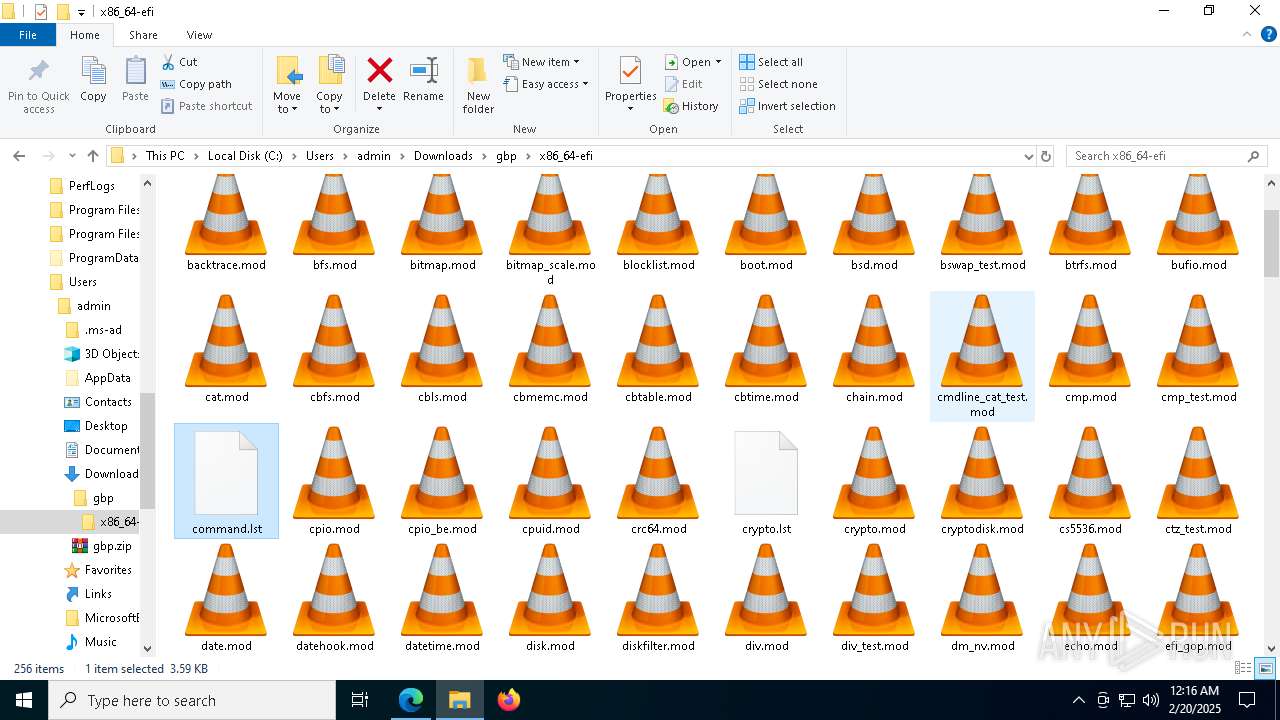
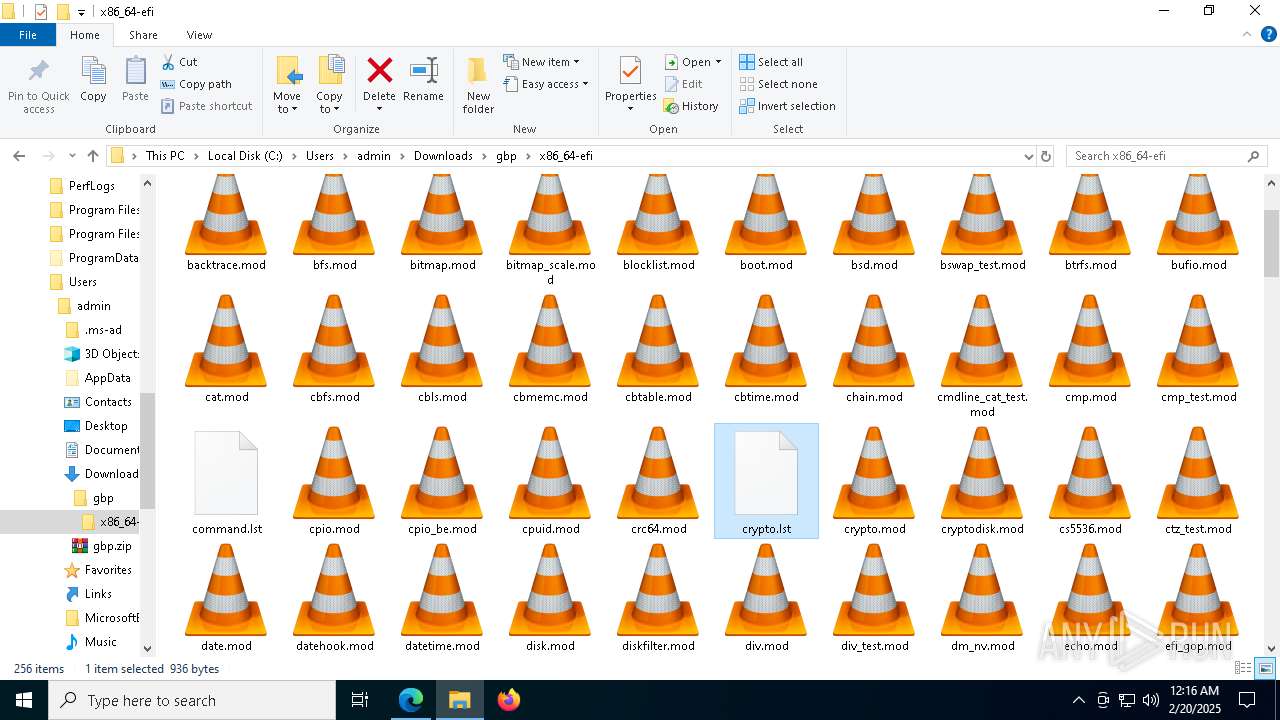
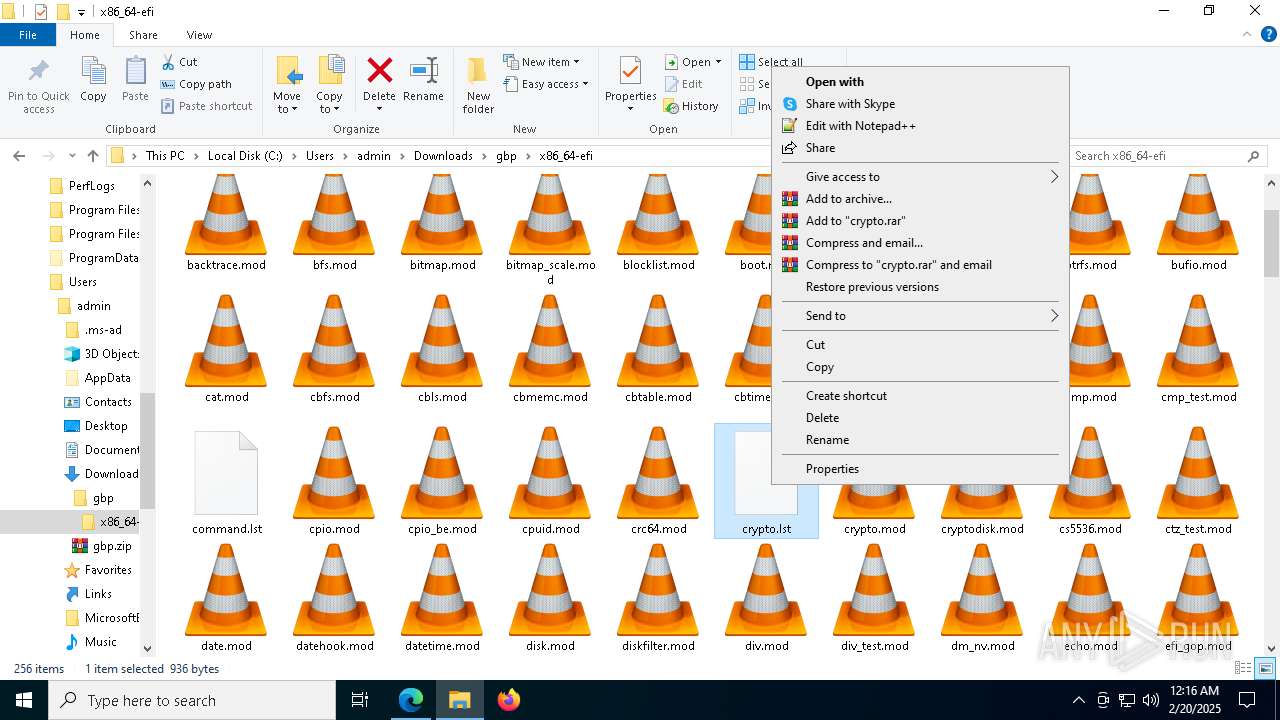
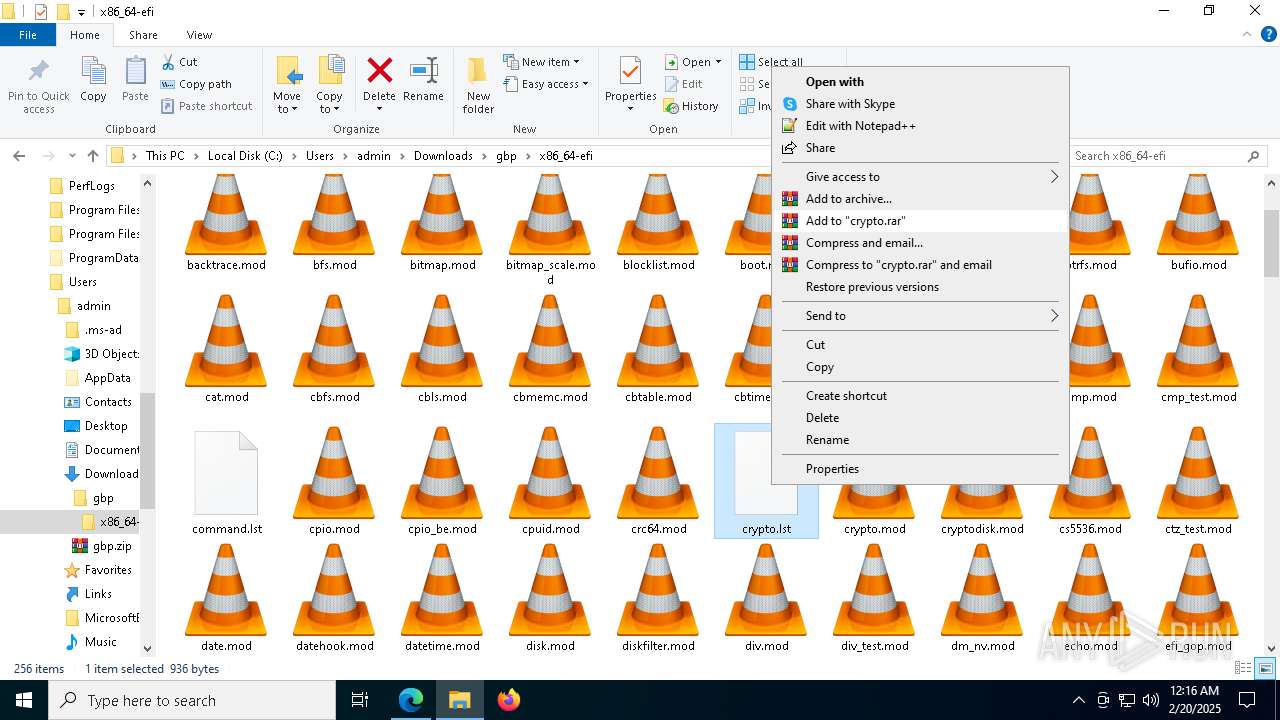
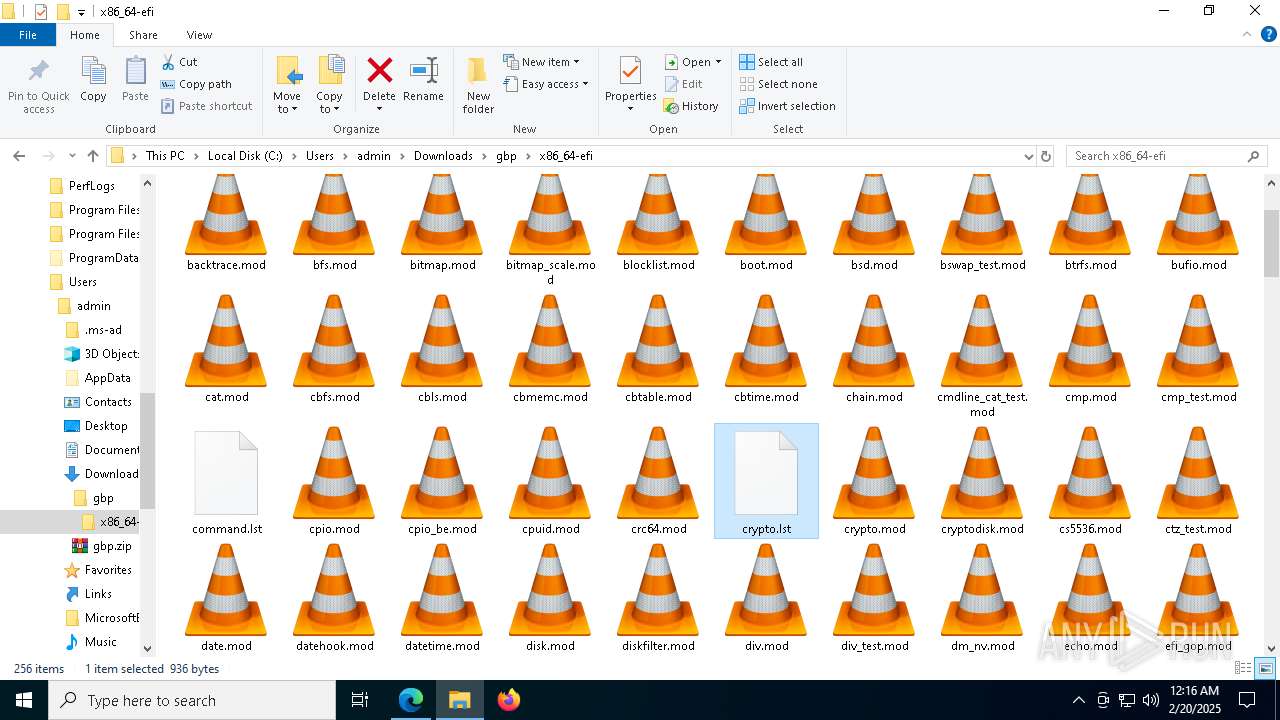
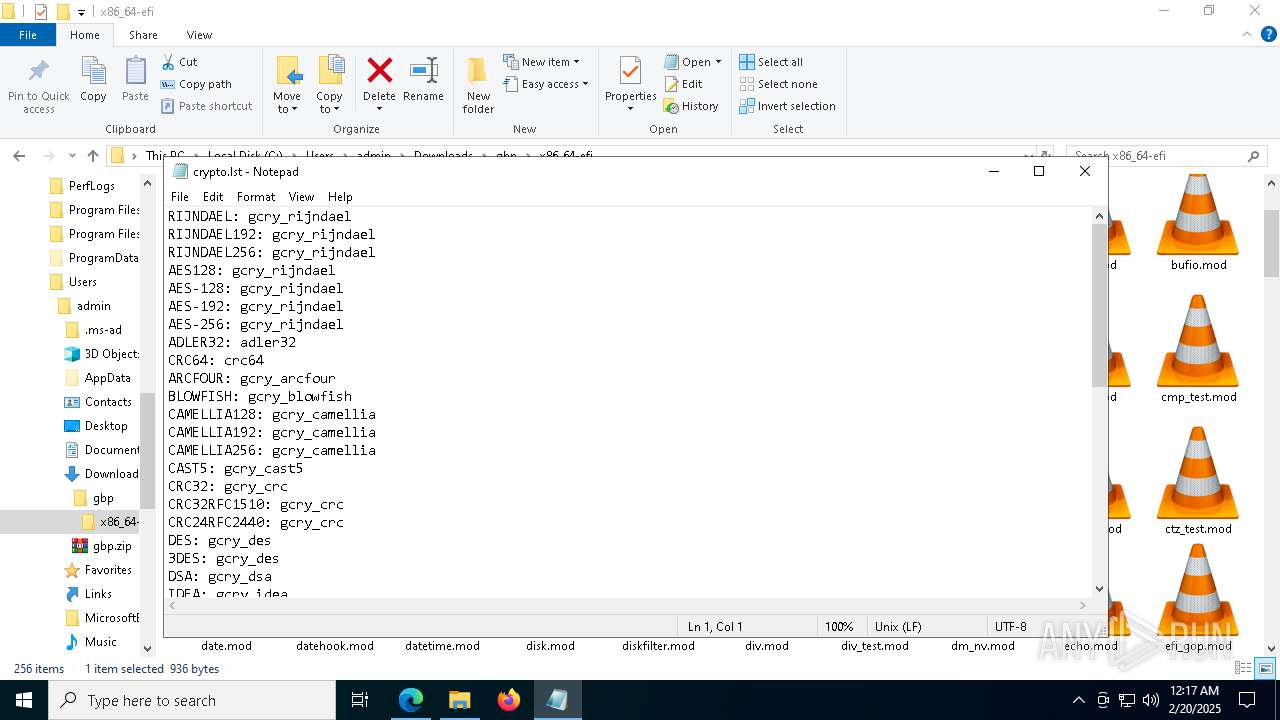
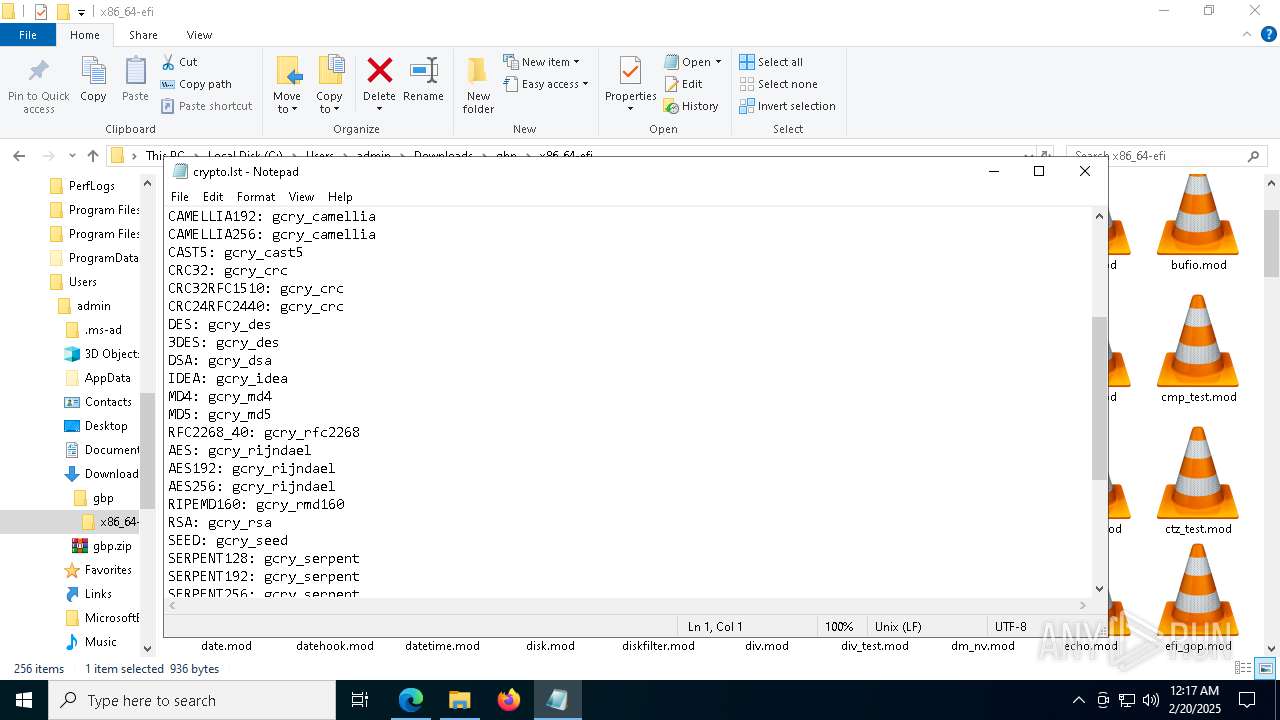
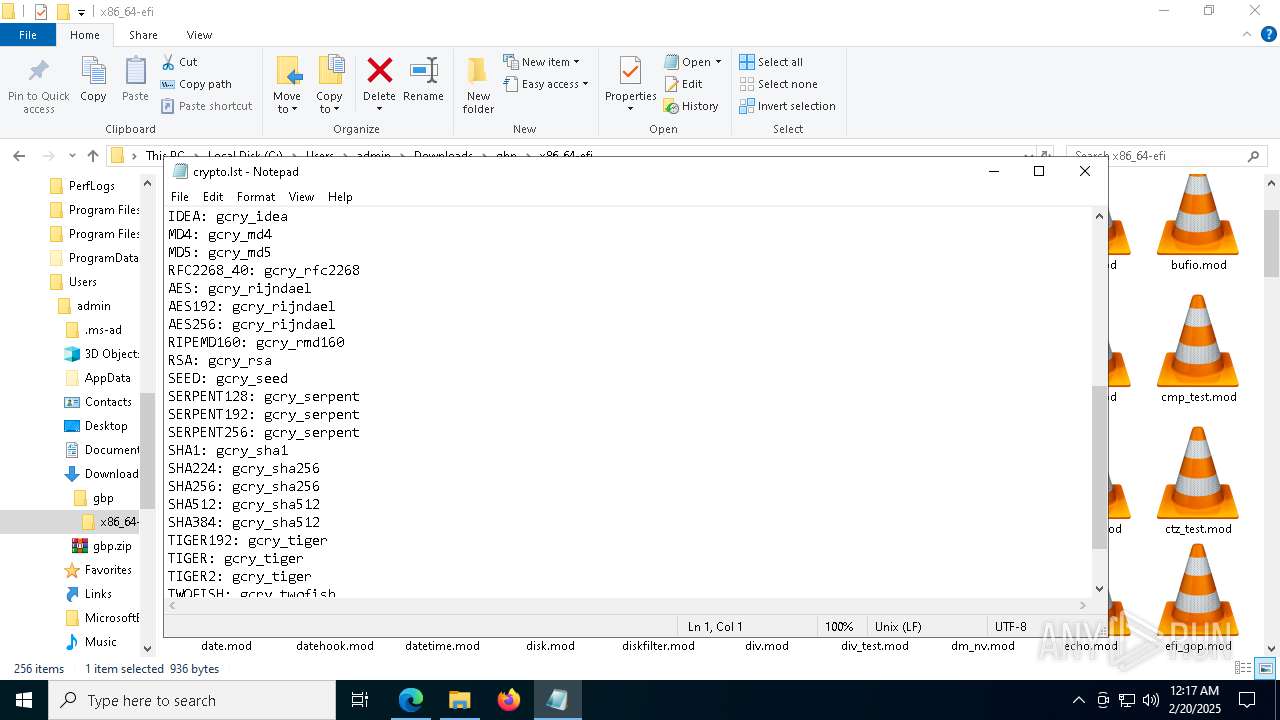
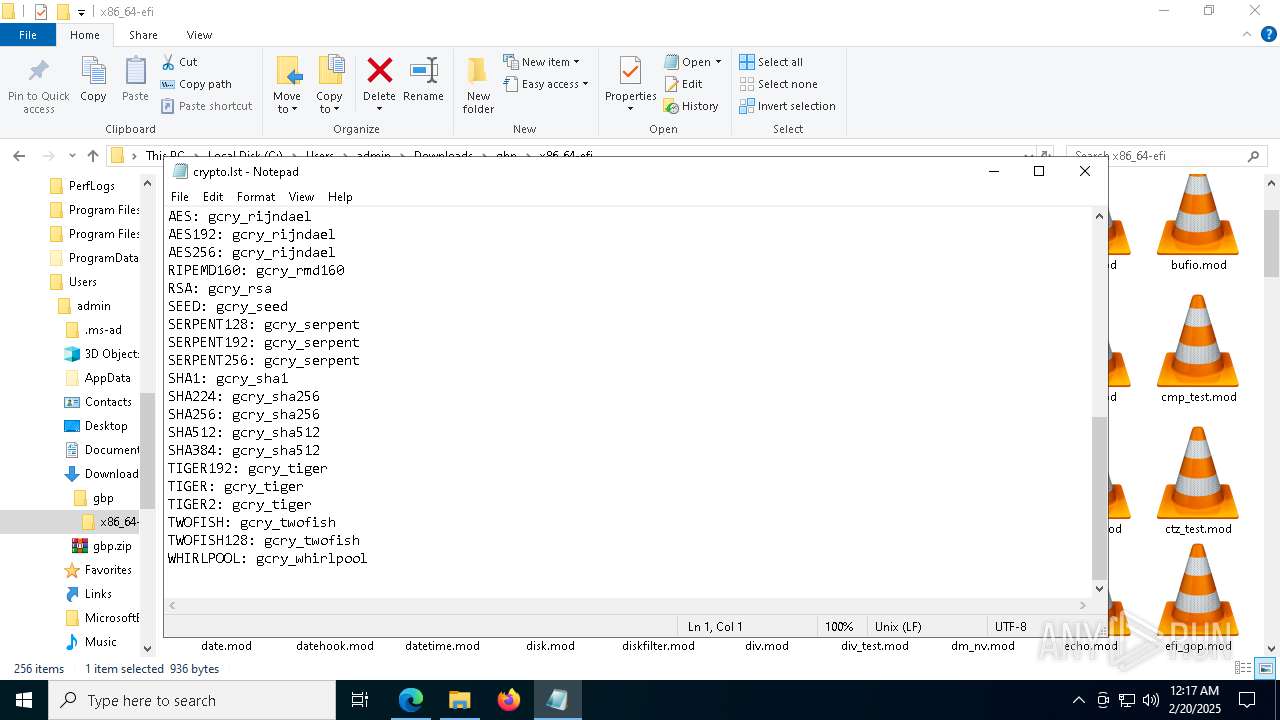
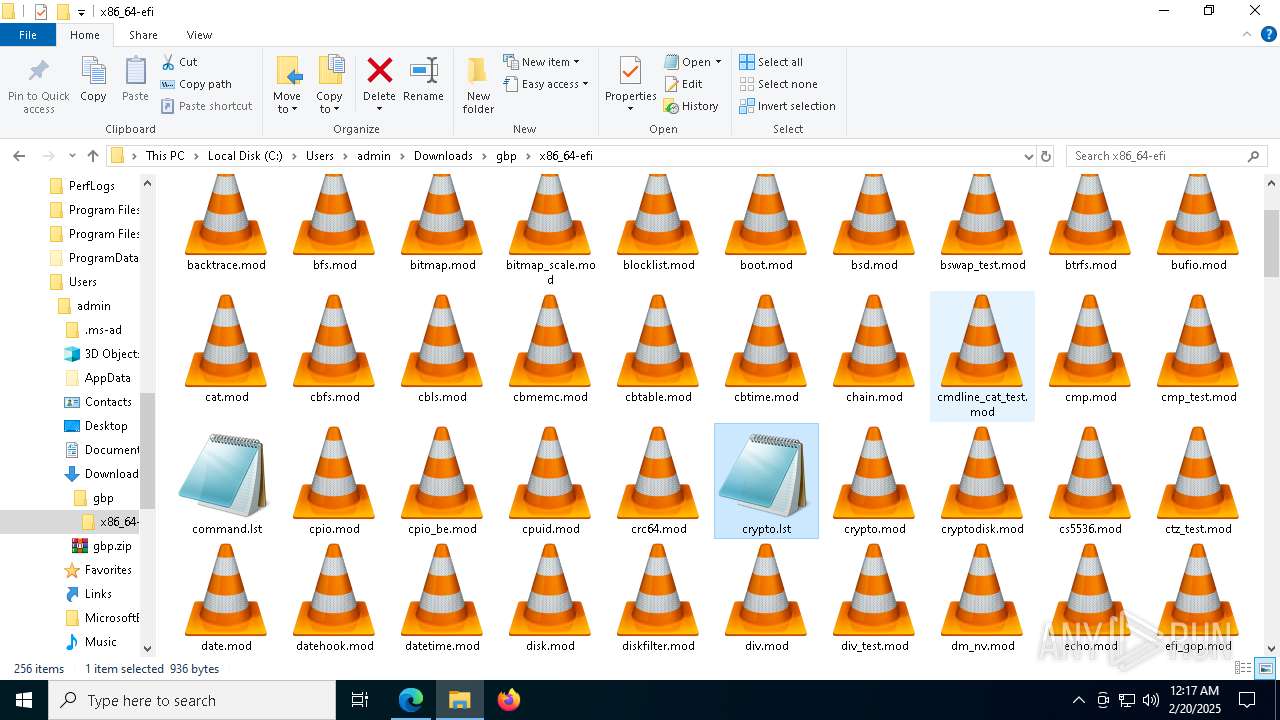
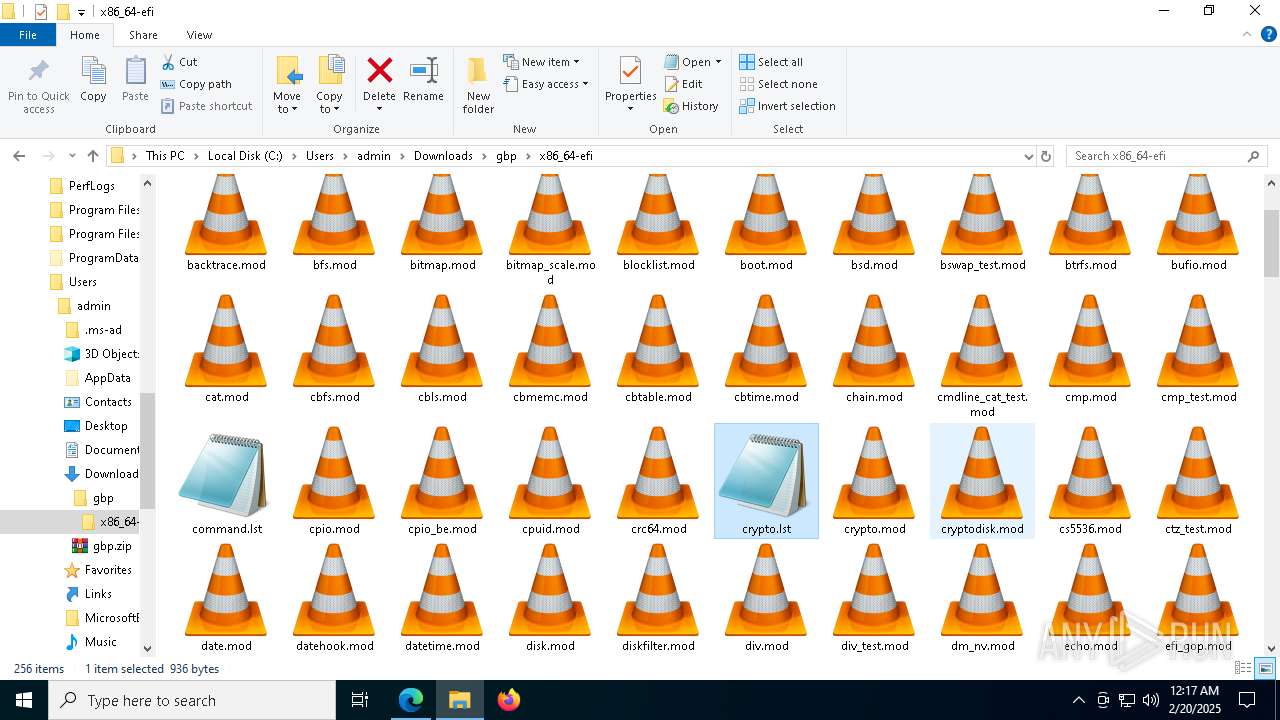
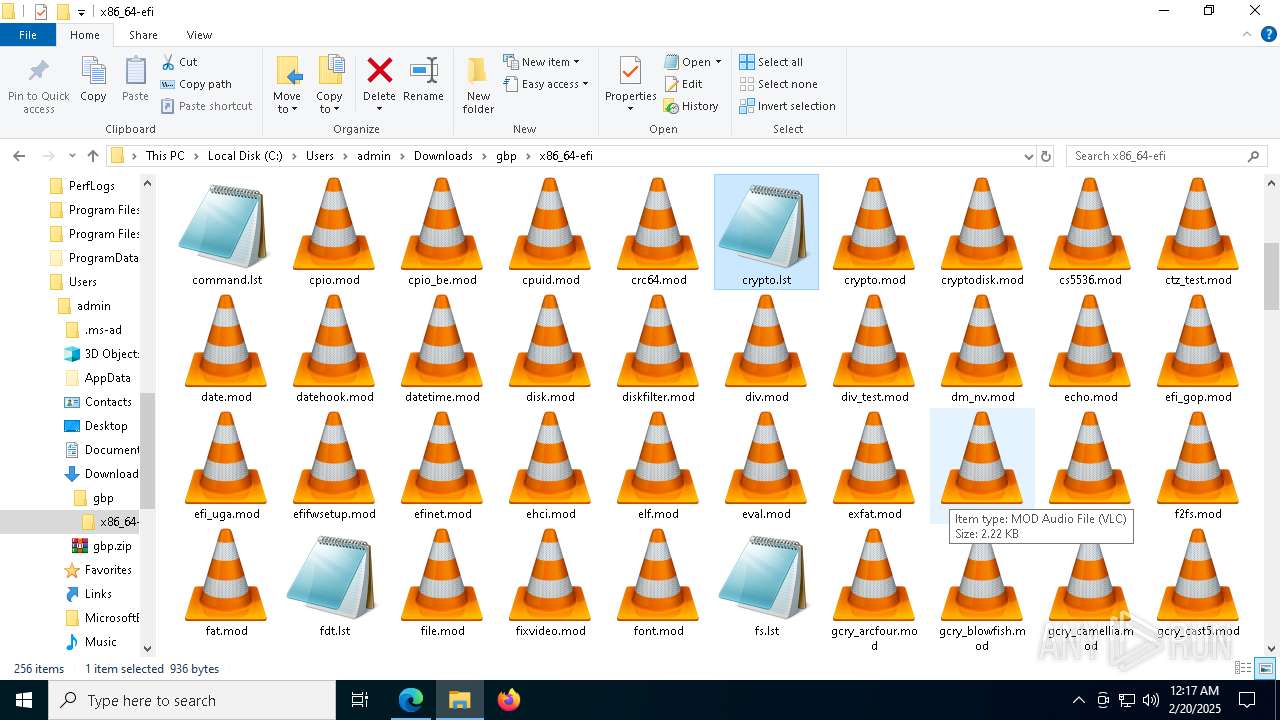
| 1412 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\gbp\x86_64-efi\crypto.lst | C:\Windows\System32\notepad.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4312 --field-trial-handle=2436,i,16586743651821535668,10141798116949154684,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6792 --field-trial-handle=2436,i,16586743651821535668,10141798116949154684,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2136 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5600 --field-trial-handle=2436,i,16586743651821535668,10141798116949154684,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3152 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6528 --field-trial-handle=2436,i,16586743651821535668,10141798116949154684,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3652 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3360 --field-trial-handle=2436,i,16586743651821535668,10141798116949154684,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
12 851
Read events
12 785
Write events
53
Delete events
13
Modification events
| (PID) Process: | (5092) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5092) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5092) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5092) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5092) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5092) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (5496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5496) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
25
Suspicious files
647
Text files
100
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135f88.TMP | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135f88.TMP | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135f98.TMP | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135fc7.TMP | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF135fc7.TMP | — | |
MD5:— | SHA256:— | |||
| 5496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
87
DNS requests
87
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2040 | svchost.exe | GET | 200 | 23.48.23.11:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7972 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3d821cc4-622c-4956-9fad-1a3107531878?P1=1740538477&P2=404&P3=2&P4=jHp3fh6VqIHgd0kbxryl%2bxWVVmNsGSXcUcZY%2f82W%2fLn6lFvjurfLERE93vTht55wkgZXerKJ%2fLgNq60RyrAGRQ%3d%3d | unknown | — | — | whitelisted |
7972 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3d821cc4-622c-4956-9fad-1a3107531878?P1=1740538477&P2=404&P3=2&P4=jHp3fh6VqIHgd0kbxryl%2bxWVVmNsGSXcUcZY%2f82W%2fLn6lFvjurfLERE93vTht55wkgZXerKJ%2fLgNq60RyrAGRQ%3d%3d | unknown | — | — | whitelisted |
7972 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3d821cc4-622c-4956-9fad-1a3107531878?P1=1740538477&P2=404&P3=2&P4=jHp3fh6VqIHgd0kbxryl%2bxWVVmNsGSXcUcZY%2f82W%2fLn6lFvjurfLERE93vTht55wkgZXerKJ%2fLgNq60RyrAGRQ%3d%3d | unknown | — | — | whitelisted |
7972 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3d821cc4-622c-4956-9fad-1a3107531878?P1=1740538477&P2=404&P3=2&P4=jHp3fh6VqIHgd0kbxryl%2bxWVVmNsGSXcUcZY%2f82W%2fLn6lFvjurfLERE93vTht55wkgZXerKJ%2fLgNq60RyrAGRQ%3d%3d | unknown | — | — | whitelisted |
7972 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3d821cc4-622c-4956-9fad-1a3107531878?P1=1740538477&P2=404&P3=2&P4=jHp3fh6VqIHgd0kbxryl%2bxWVVmNsGSXcUcZY%2f82W%2fLn6lFvjurfLERE93vTht55wkgZXerKJ%2fLgNq60RyrAGRQ%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7972 | svchost.exe | HEAD | 200 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3d821cc4-622c-4956-9fad-1a3107531878?P1=1740538477&P2=404&P3=2&P4=jHp3fh6VqIHgd0kbxryl%2bxWVVmNsGSXcUcZY%2f82W%2fLn6lFvjurfLERE93vTht55wkgZXerKJ%2fLgNq60RyrAGRQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2040 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5696 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6284 | msedge.exe | 142.250.186.132:443 | www.google.com | — | — | whitelisted |
6284 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5496 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6284 | msedge.exe | 185.151.30.211:443 | fortfieldglb.com | 20i Limited | GB | unknown |
6284 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6284 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
fortfieldglb.com |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6284 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6284 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6284 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6284 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7336 | WerFaultSecure.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
7336 | WerFaultSecure.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
Process | Message |
|---|---|
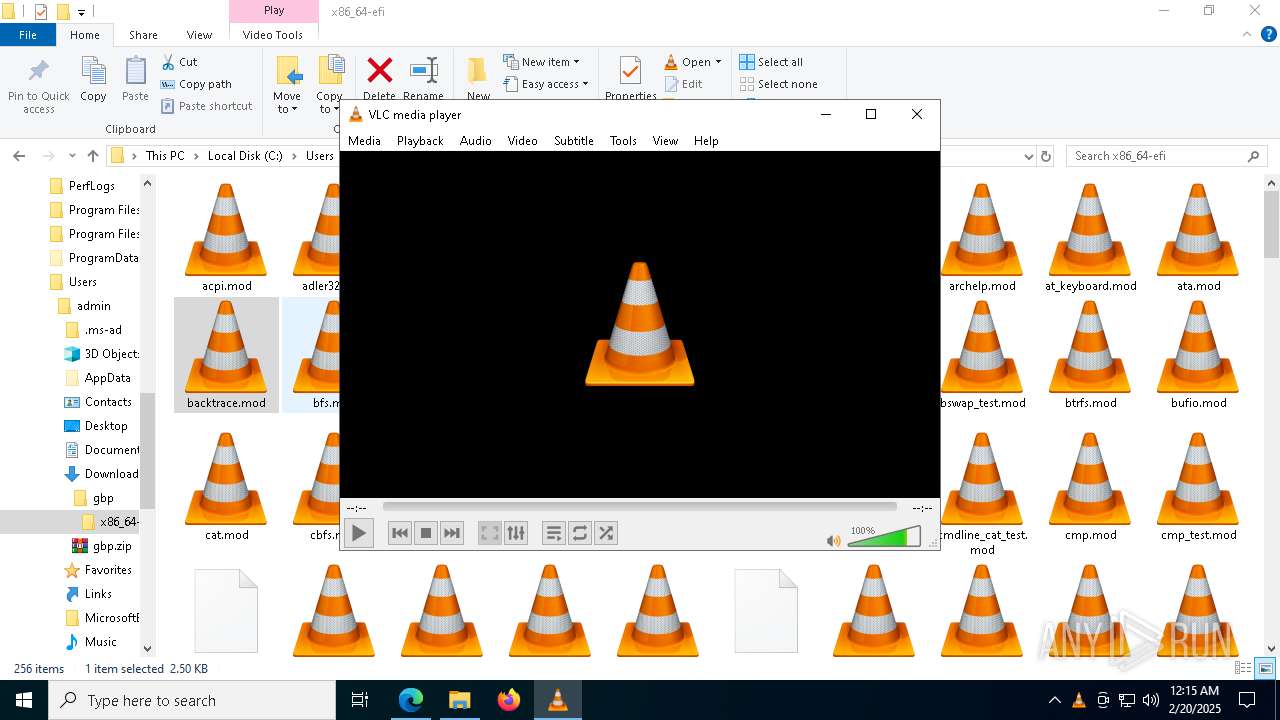
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
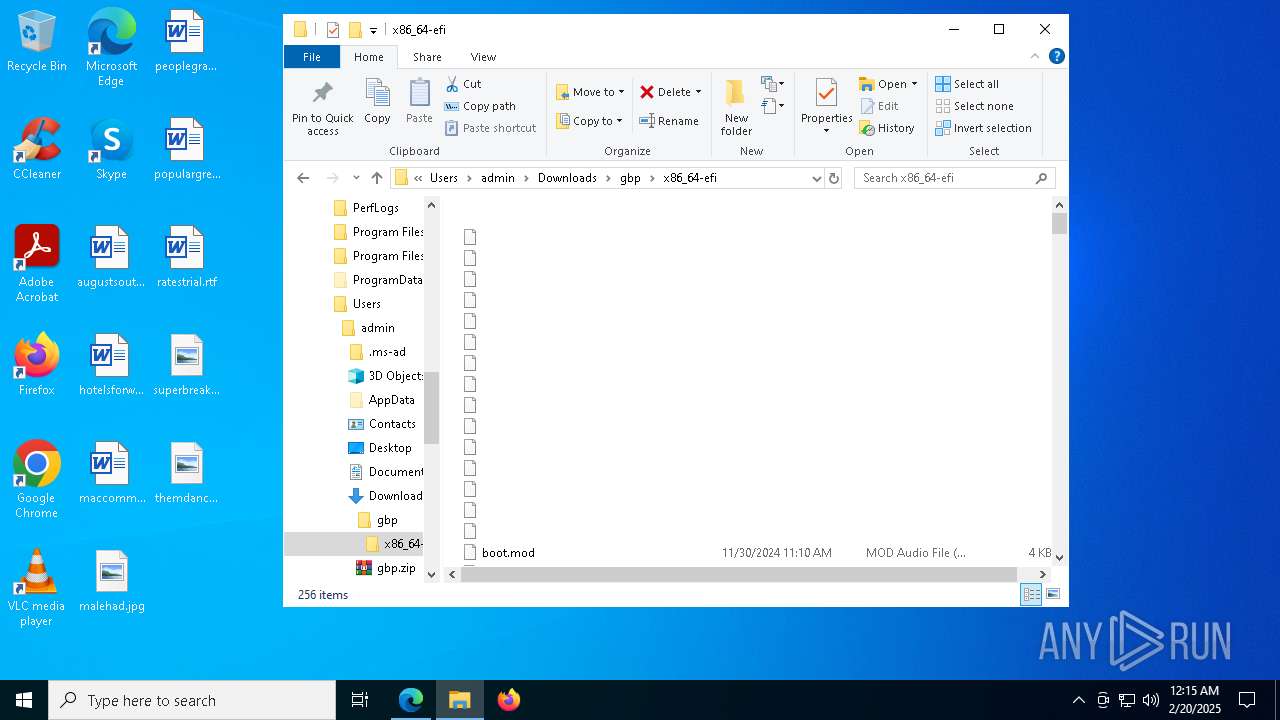
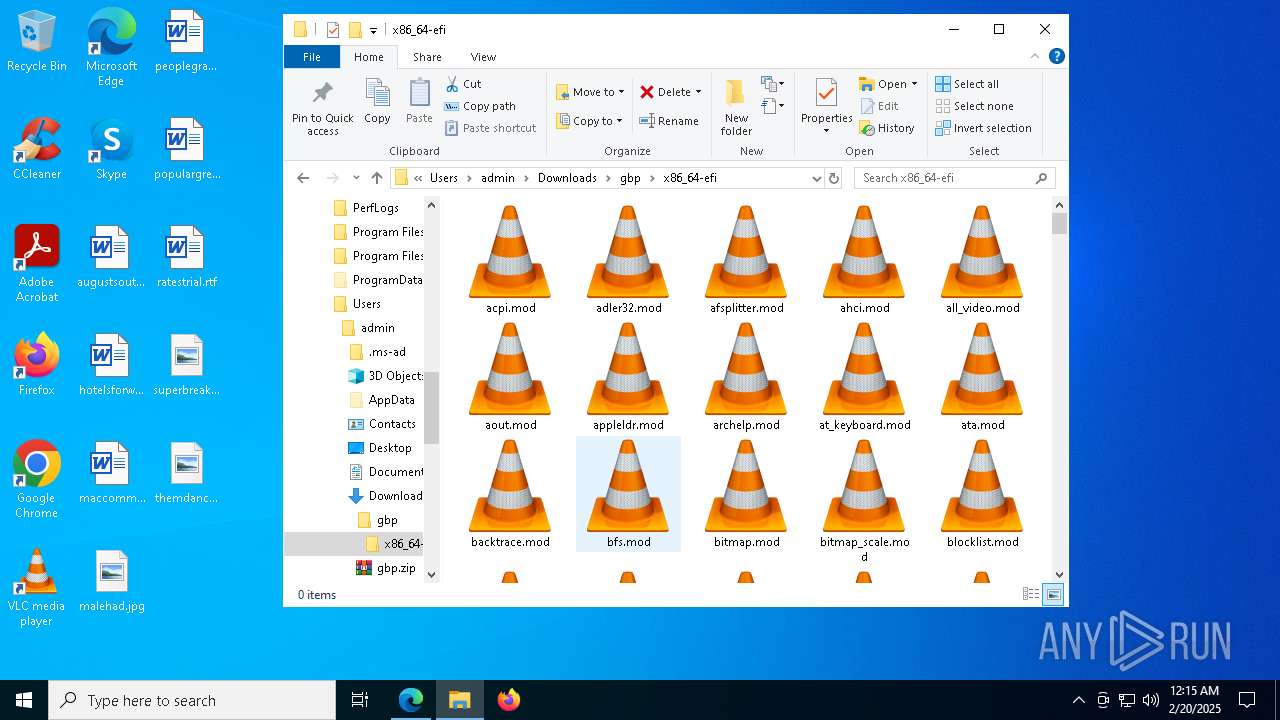
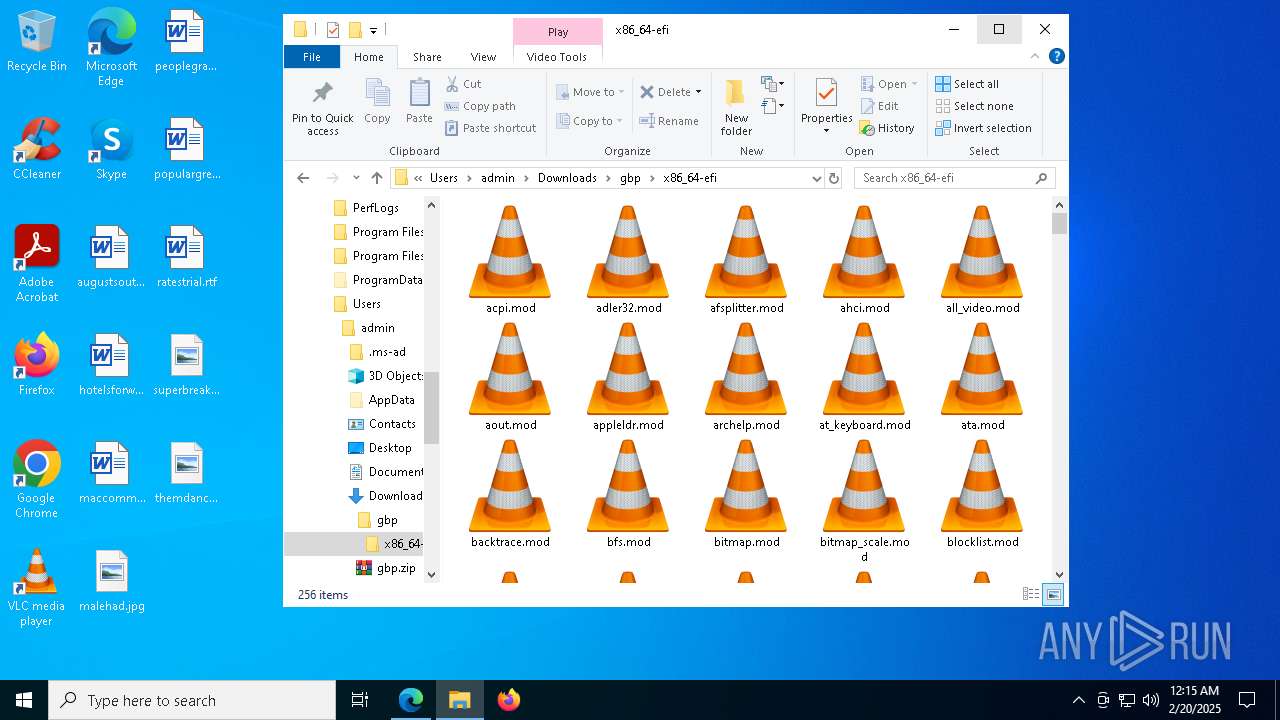
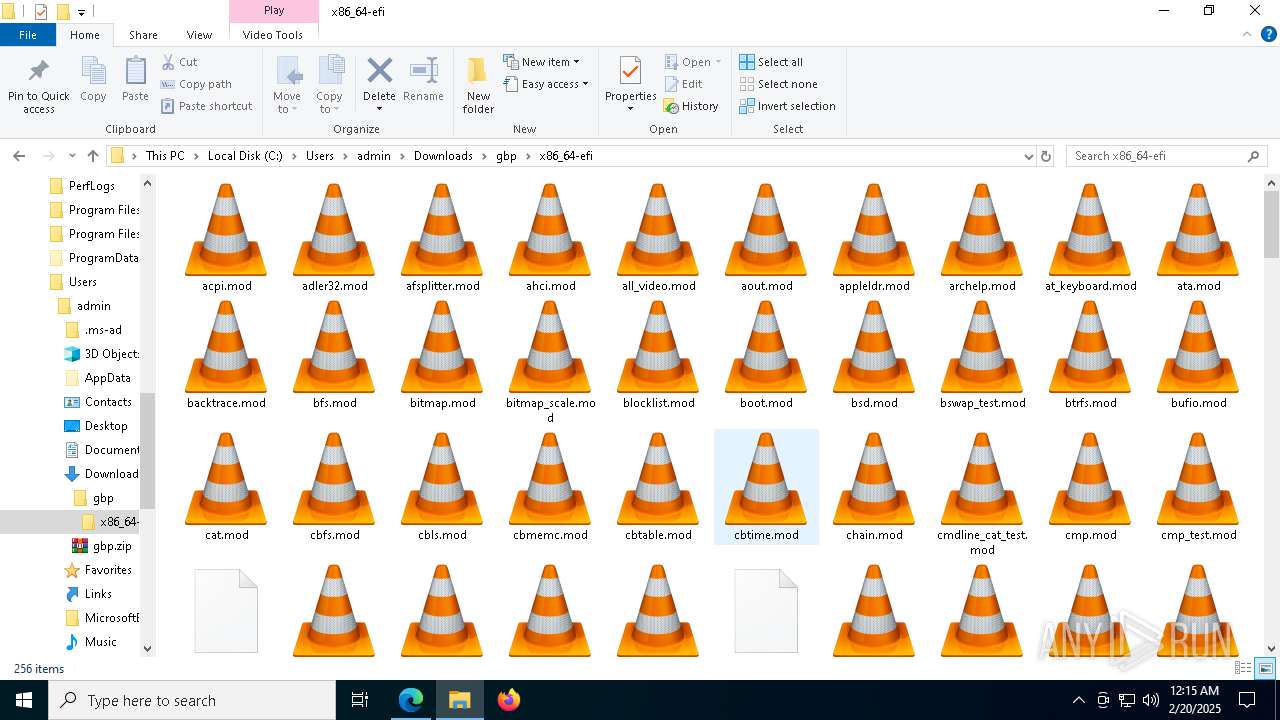
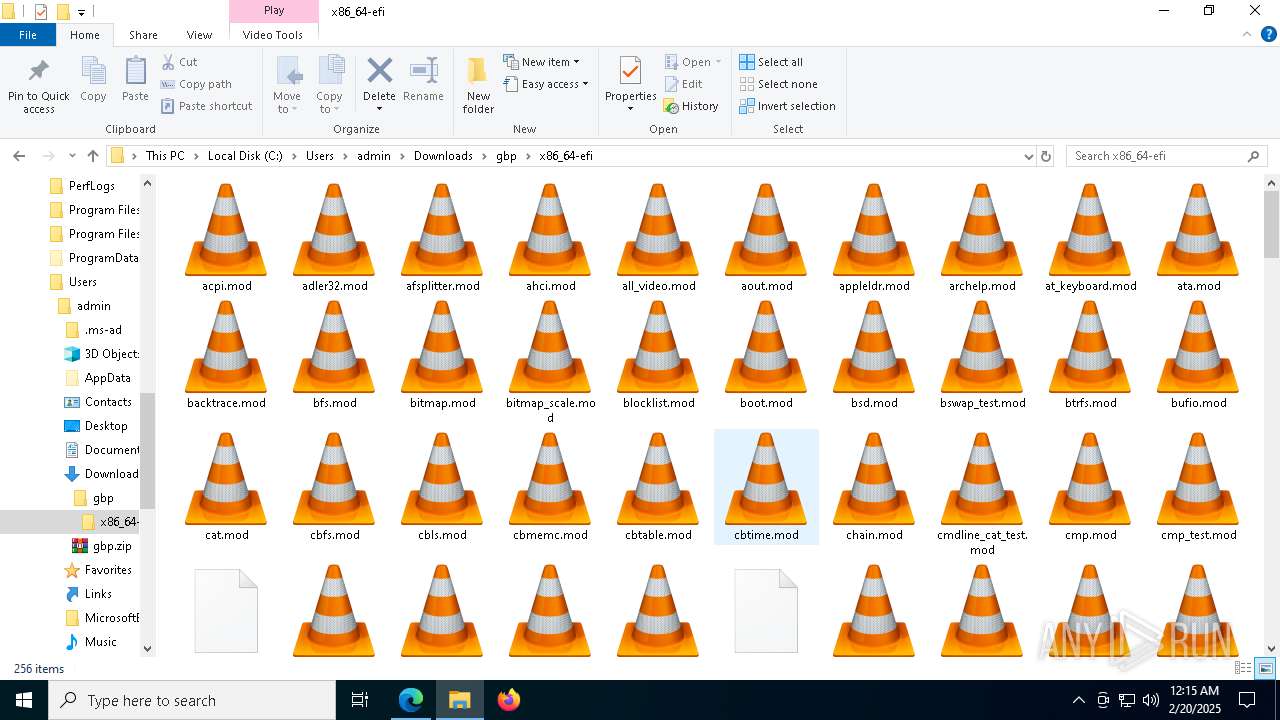
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|