| File name: | 14330000.exe.mal |
| Full analysis: | https://app.any.run/tasks/877c5718-df46-40e8-af49-4f9c139205ca |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | January 11, 2024, 10:19:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8F5310F4DFD2C55EB44273DFE985EEBC |
| SHA1: | 1AA941A272DA86667E81C7BB0AA7965FDEB8A309 |
| SHA256: | 0DB89DCB32A731BA535CCC4A5F92C1A6D28AAF47707CEF8B8164E9F7746092E6 |
| SSDEEP: | 12288:tc/eu8FVFDIDZwQsYZx7SleHgTj7W9XE2SR9Lp:tc/eu8FVFDIHDX7xej7WhEnN |
MALICIOUS
Actions looks like stealing of personal data
- OpenWith.exe (PID: 3680)
SUSPICIOUS
Searches for installed software
- OpenWith.exe (PID: 3680)
The process checks if it is being run in the virtual environment
- dialer.exe (PID: 2584)
Loads DLL from Mozilla Firefox
- OpenWith.exe (PID: 3680)
Reads the date of Windows installation
- 6_Sjz.exe (PID: 6296)
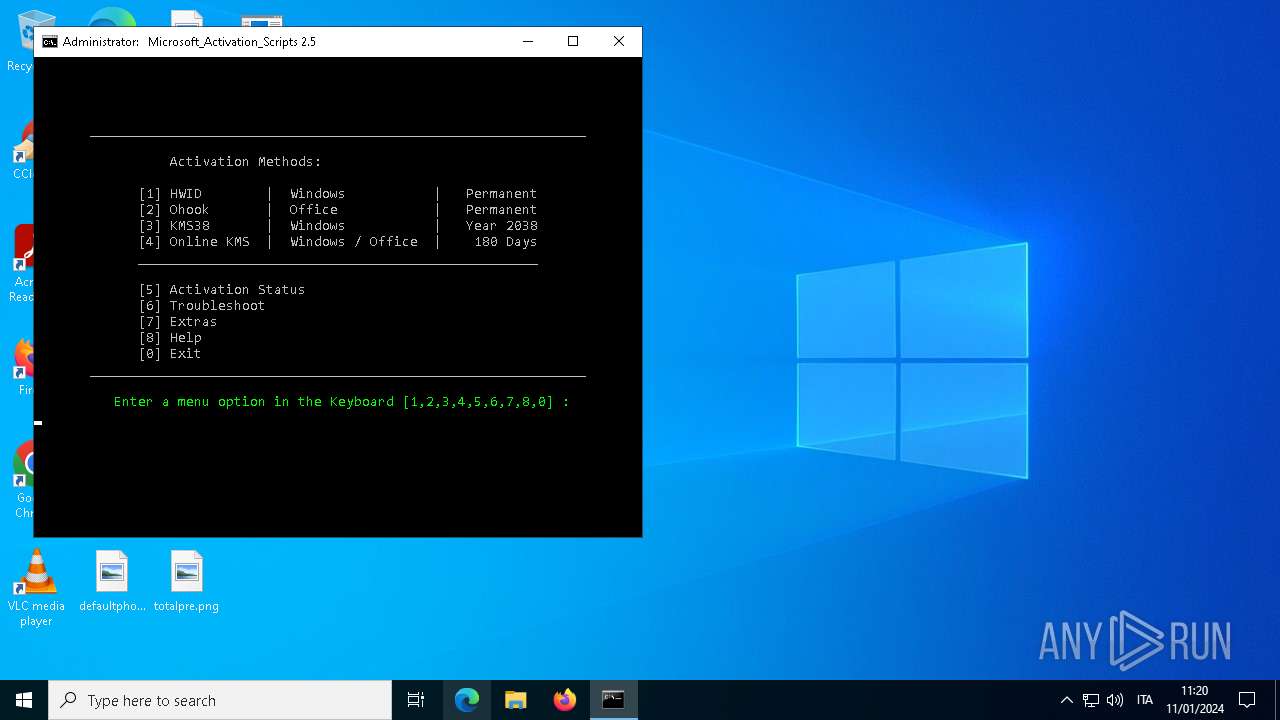
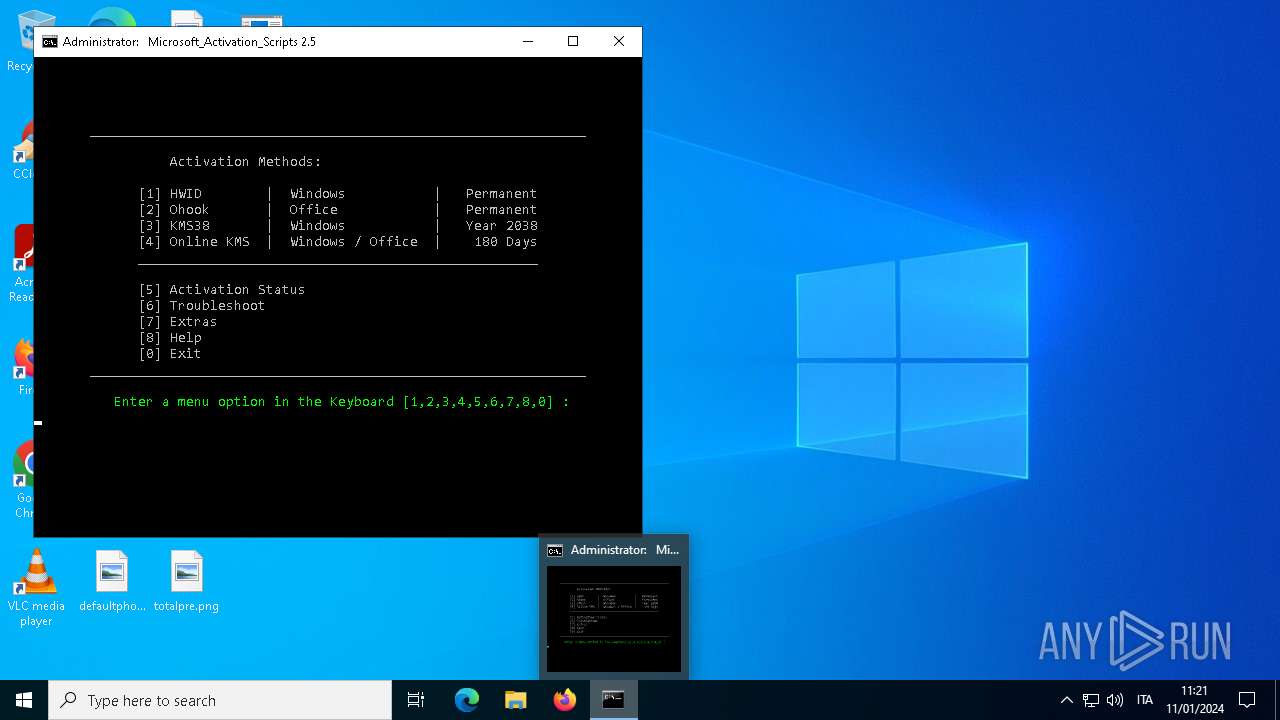
Starts CMD.EXE for commands execution
- 6_Sjz.exe (PID: 6296)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 6672)
- powershell.exe (PID: 6792)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 6548)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 4192)
Executing commands from ".cmd" file
- 6_Sjz.exe (PID: 6296)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 6436)
- powershell.exe (PID: 6792)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 4380)
Starts SC.EXE for service management
- cmd.exe (PID: 6436)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 4380)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6436)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 4380)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6436)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4380)
- cmd.exe (PID: 6980)
INFO
RHADAMANTHYS has been detected (SURICATA)
- dialer.exe (PID: 2584)
Drops the executable file immediately after the start
- 14330000.exe.mal.exe (PID: 2196)
- OpenWith.exe (PID: 3680)
Checks supported languages
- 14330000.exe.mal.exe (PID: 2196)
- 6_Sjz.exe (PID: 6296)
- mode.com (PID: 6844)
Manual execution by a user
- OpenWith.exe (PID: 3680)
- dialer.exe (PID: 2584)
Connects to unusual port
- dialer.exe (PID: 2584)
- OpenWith.exe (PID: 3680)
Creates files or folders in the user directory
- OpenWith.exe (PID: 3680)
- 6_Sjz.exe (PID: 6296)
Reads the computer name
- 6_Sjz.exe (PID: 6296)
Application launched itself
- cmd.exe (PID: 6436)
- cmd.exe (PID: 6672)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 6548)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 4192)
Checks operating system version
- cmd.exe (PID: 6436)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 6980)
Reads the software policy settings
- slui.exe (PID: 2624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:13 13:58:22+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 59392 |
| InitializedDataSize: | 415232 |
| UninitializedDataSize: | 65536 |
| EntryPoint: | 0xf576 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.0.0 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | FlashDevelop is an open source script editor. |
| CompanyName: | FlashDevelop.org |
| FileDescription: | FlashDevelop |
| FileVersion: | 5.0.0.0 |
| InternalName: | FlashDevelop.exe |
| LegalCopyright: | FlashDevelop.org 2005-2018 |
| LegalTrademarks: | - |
| OriginalFileName: | FlashDevelop.exe |
| ProductName: | FlashDevelop 5.3.3.1 for .NET 4.0 (master#436add6fc7) |
| ProductVersion: | 5.0.0.0 |
| AssemblyVersion: | 5.0.0.0 |
Total processes
196
Monitored processes
77
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | reg query "HKCU\Console" /v ForceV2 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | ping -4 -n 1 updatecheck.massgrave.dev | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | "C:\Users\admin\Desktop\14330000.exe.mal.exe" | C:\Users\admin\Desktop\14330000.exe.mal.exe | — | explorer.exe | |||||||||||
User: admin Company: FlashDevelop.org Integrity Level: MEDIUM Description: FlashDevelop Exit code: 0 Version: 5.0.0.0 Modules
| |||||||||||||||
| 2500 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2584 | "C:\WINDOWS\system32\dialer.exe" | C:\Windows\SysWOW64\dialer.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Phone Dialer Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2624 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3124 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3176 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3680 | "C:\WINDOWS\system32\openwith.exe" | C:\Windows\System32\OpenWith.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3868 | find /i "/S" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 246
Read events
6 228
Write events
18
Delete events
0
Modification events
| (PID) Process: | (6296) 6_Sjz.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6296) 6_Sjz.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6296) 6_Sjz.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6296) 6_Sjz.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6792) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6792) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6792) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6792) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6200) reg.exe | Key: | HKEY_CURRENT_USER\Console |
| Operation: | write | Name: | QuickEdit |
Value: 1 | |||
| (PID) Process: | (6316) reg.exe | Key: | HKEY_CURRENT_USER\Console |
| Operation: | write | Name: | QuickEdit |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\6_Sjz.exe | executable | |
MD5:C99A9FC14DAF7FDA75234789FCFA069B | SHA256:9B26CB4A160402A6ED7651C122A7BCE6A14220A6E1737685C13A246844D188D6 | |||
| 6792 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lp4hljhq.f4p.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6296 | 6_Sjz.exe | C:\Users\admin\Documents\cloud_bdc515c3-25ed-4dcb-b09f-f970e3db6833.cmd | text | |
MD5:721E3F8CACEDDB2BCB8CD85FA400F61A | SHA256:2AED5BB373191CB92B3284BE3DE8B2EE6DD746FF71ACC8AE10968CB6A514C95F | |||
| 6296 | 6_Sjz.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0_32\UsageLogs\6_Sjz.exe.log | binary | |
MD5:34F3599459082A5D4BBE6791ACAFDB19 | SHA256:4A414818A9077C12173EE4E94656CDA51E2B57BAFCB228F6E82C963D32A32C34 | |||
| 6792 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:25EC9407A3EFFD10E6DCF90208EFD65B | SHA256:77C5A53AC582883F6002A24AC592AE86FEB2980C91DFF92F63DA7FAE3A484624 | |||
| 6792 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_31bnhbwd.hen.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
35
DNS requests
13
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1092 | svchost.exe | POST | 302 | 23.213.166.81:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
1092 | svchost.exe | POST | 302 | 23.213.166.81:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
6244 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | binary | 418 b | unknown |
1092 | svchost.exe | POST | 302 | 23.213.166.81:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
6244 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | binary | 409 b | unknown |
2908 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1092 | svchost.exe | POST | 302 | 23.213.166.81:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
1092 | svchost.exe | POST | 302 | 23.213.166.81:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
1092 | svchost.exe | POST | 302 | 23.213.166.81:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
2644 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1092 | svchost.exe | 23.213.166.81:80 | go.microsoft.com | AKAMAI-AS | DE | unknown |
1092 | svchost.exe | 138.91.171.81:80 | dmd.metaservices.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5612 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2584 | dialer.exe | 141.105.68.140:9392 | — | Hostkey B.v. | RU | unknown |
6048 | svchost.exe | 40.126.32.76:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
784 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3680 | OpenWith.exe | 141.105.68.140:9392 | — | Hostkey B.v. | RU | unknown |
6244 | SIHClient.exe | 40.68.123.157:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
6244 | SIHClient.exe | 184.30.21.171:80 | — | AKAMAI-AS | DE | unknown |
6244 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
dmd.metaservices.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
updatecheck.massgrave.dev |
| unknown |
x1.c.lencr.org |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2584 | dialer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
6 ETPRO signatures available at the full report