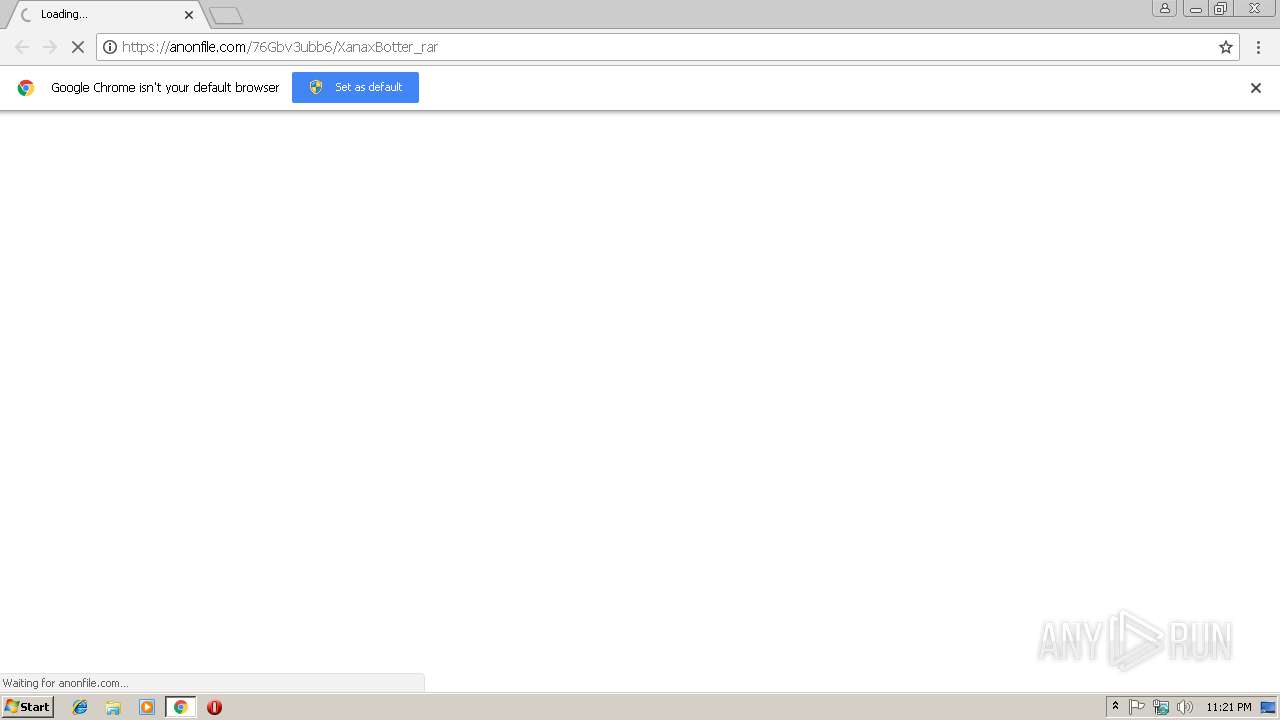
| URL: | https://anonfile.com/76Gbv3ubb6/XanaxBotter_rar |
| Full analysis: | https://app.any.run/tasks/236c1081-436a-4972-8be6-cdc9215ead58 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | February 18, 2019, 23:20:59 |
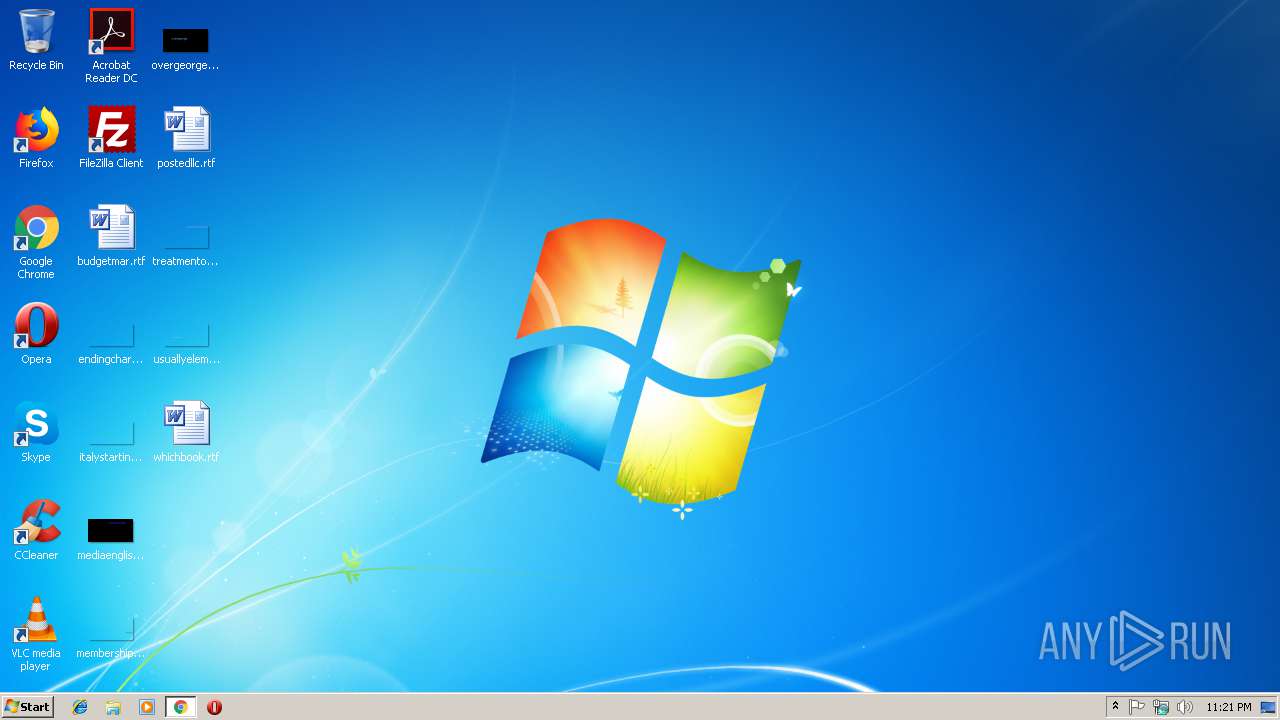
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 10F75EB0DD6CAFEF384E6AC0BD6463A1 |
| SHA1: | E7E5F6A30F2815A0DFCE93EB2DBED2412E0D7DCC |
| SHA256: | 0D2A1503F3B40FF1D4DE230B6AD852123AB4E79C4F83455215C1279B10941A73 |
| SSDEEP: | 3:N8RGpkTWSKEmqXEX:2gpkTW4sX |
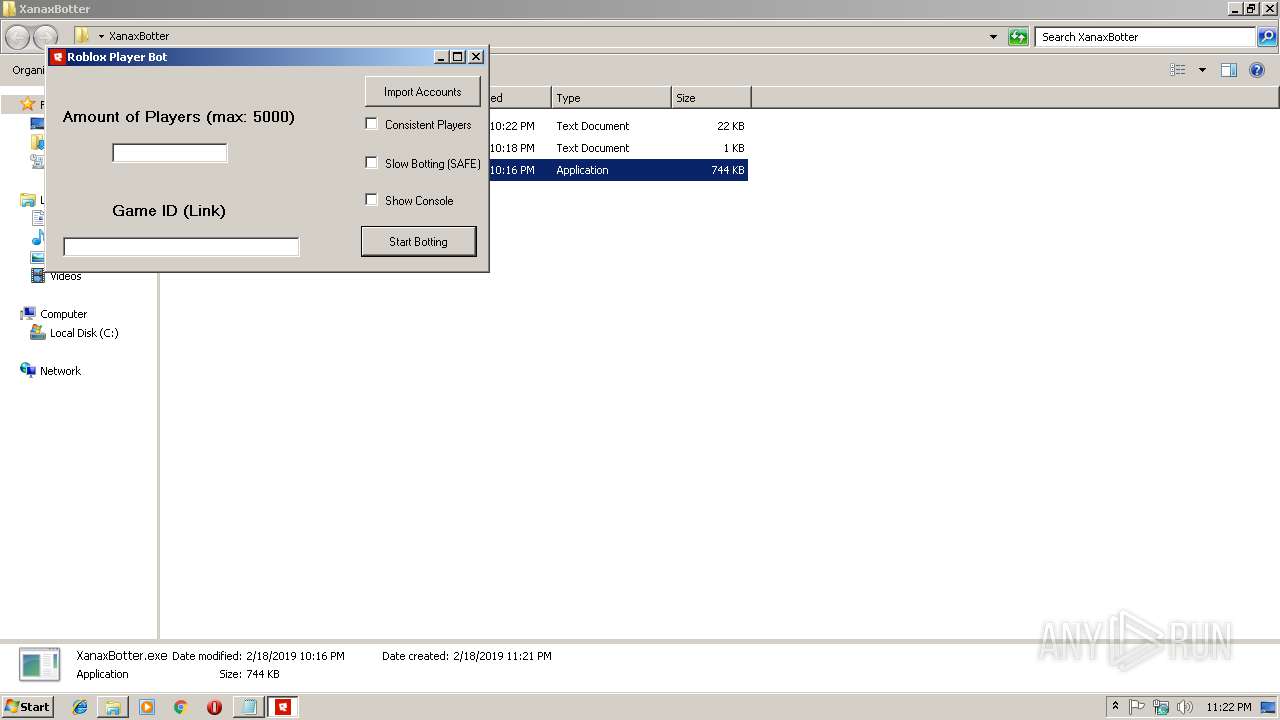
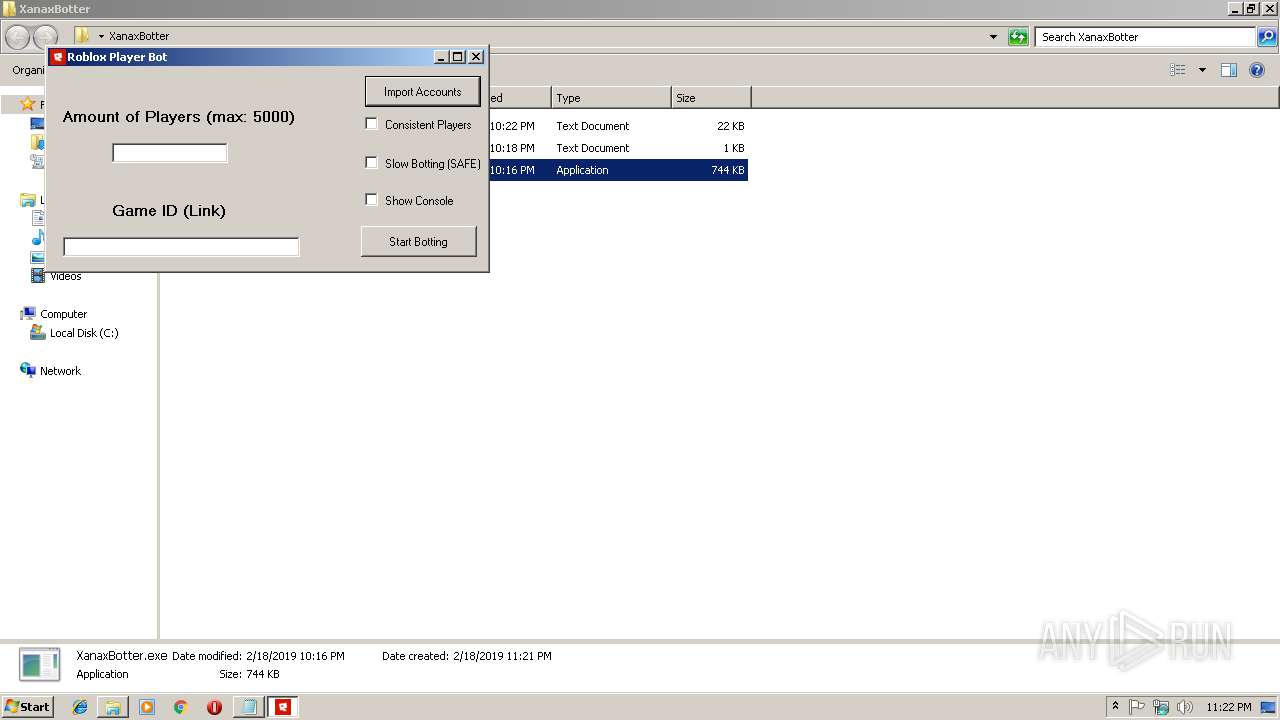
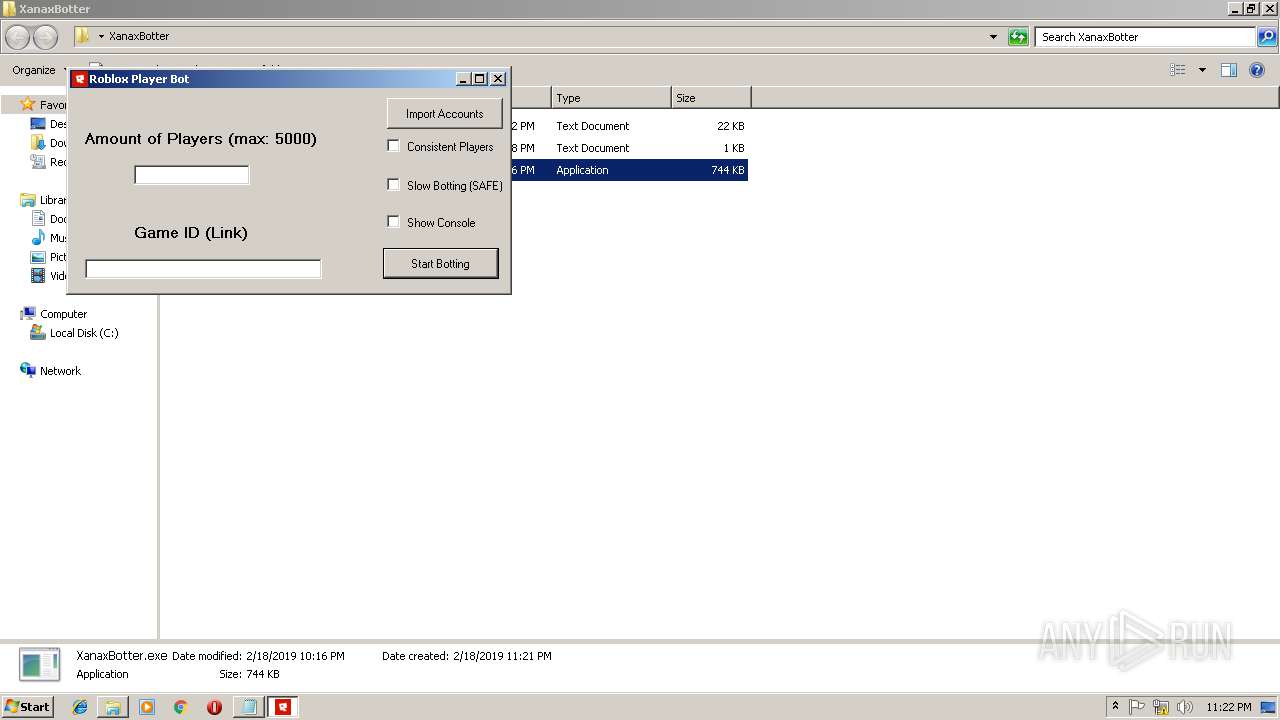
MALICIOUS
Application was dropped or rewritten from another process
- XanaxBotter.exe (PID: 2444)
- file174805.exe (PID: 3296)
- file173206.exe (PID: 2984)
- XanaxBotter.exe (PID: 3512)
- file85927.exe (PID: 936)
- file283769.exe (PID: 3912)
Actions looks like stealing of personal data
- file85927.exe (PID: 936)
Stealing of credential data
- file85927.exe (PID: 936)
QUASAR was detected
- file85927.exe (PID: 936)
Connects to CnC server
- file85927.exe (PID: 936)
SUSPICIOUS
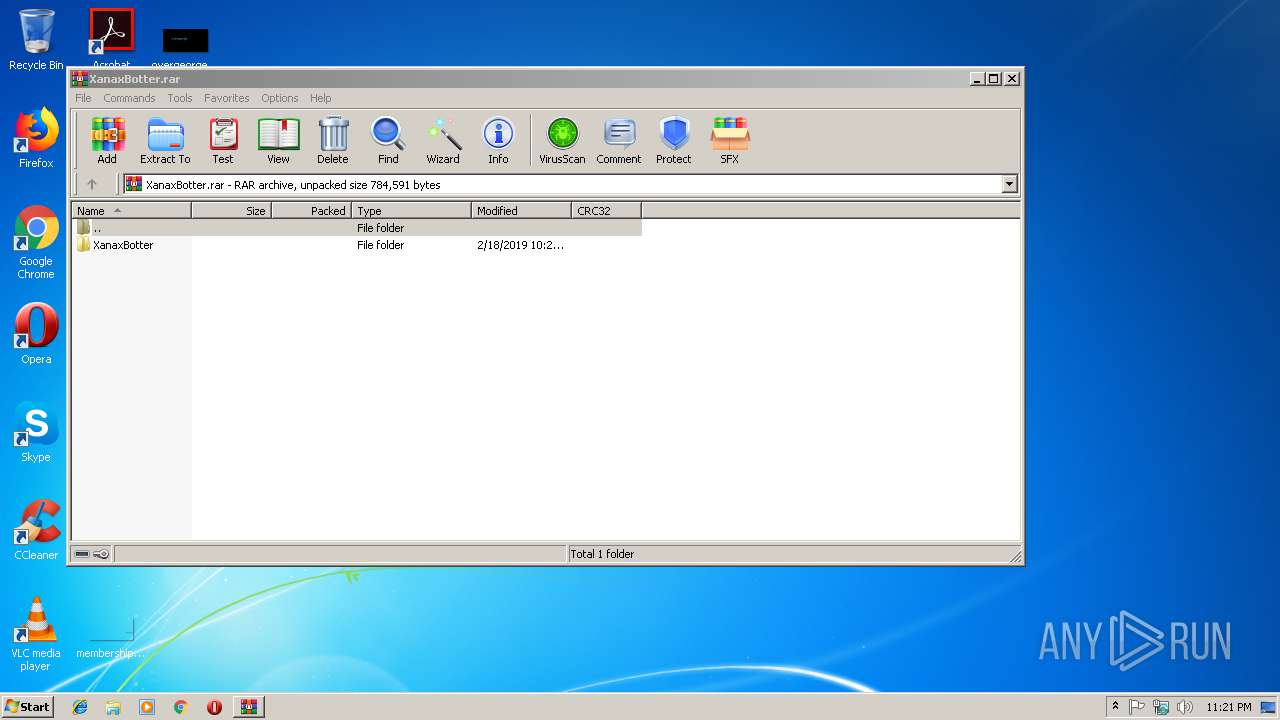
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2736)
- XanaxBotter.exe (PID: 2444)
- XanaxBotter.exe (PID: 3512)
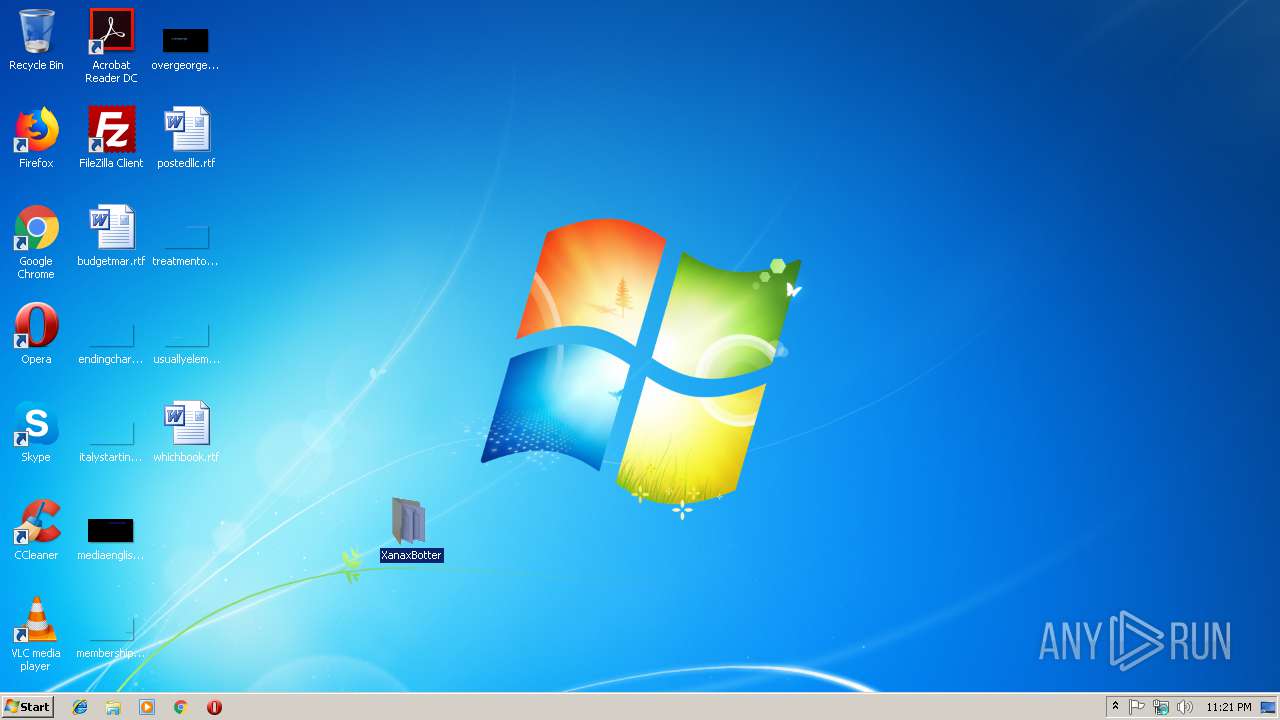
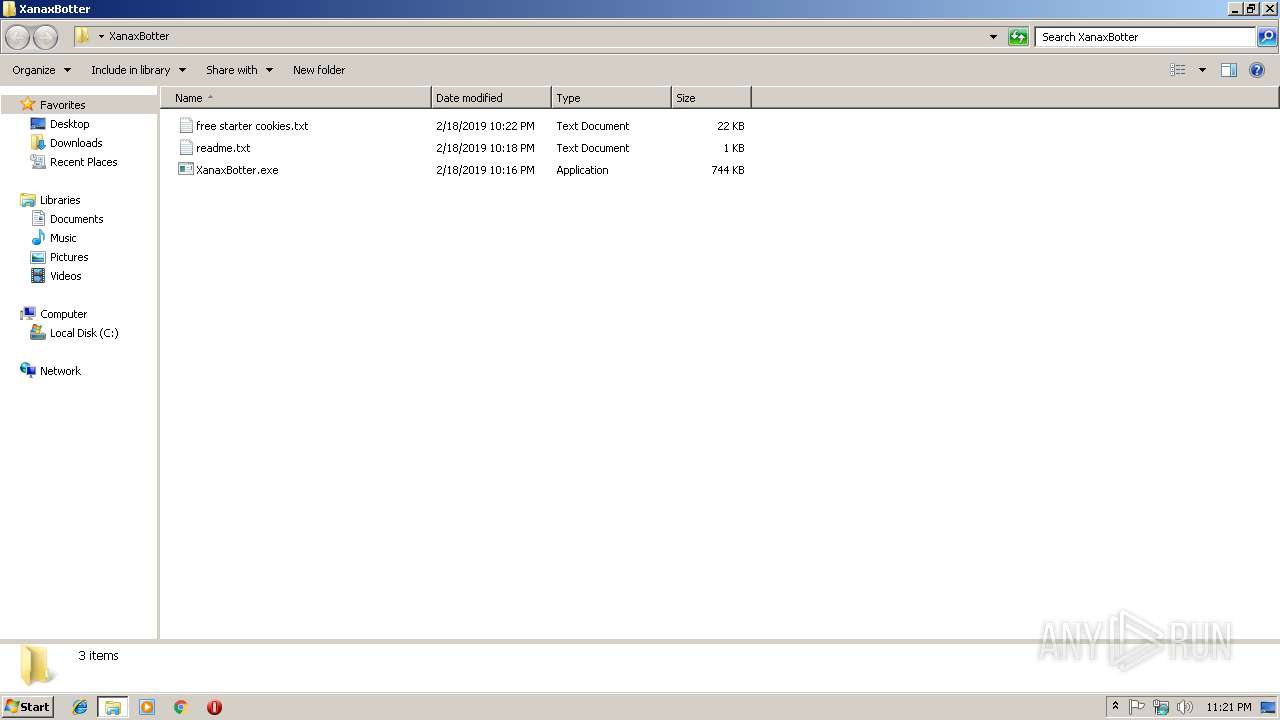
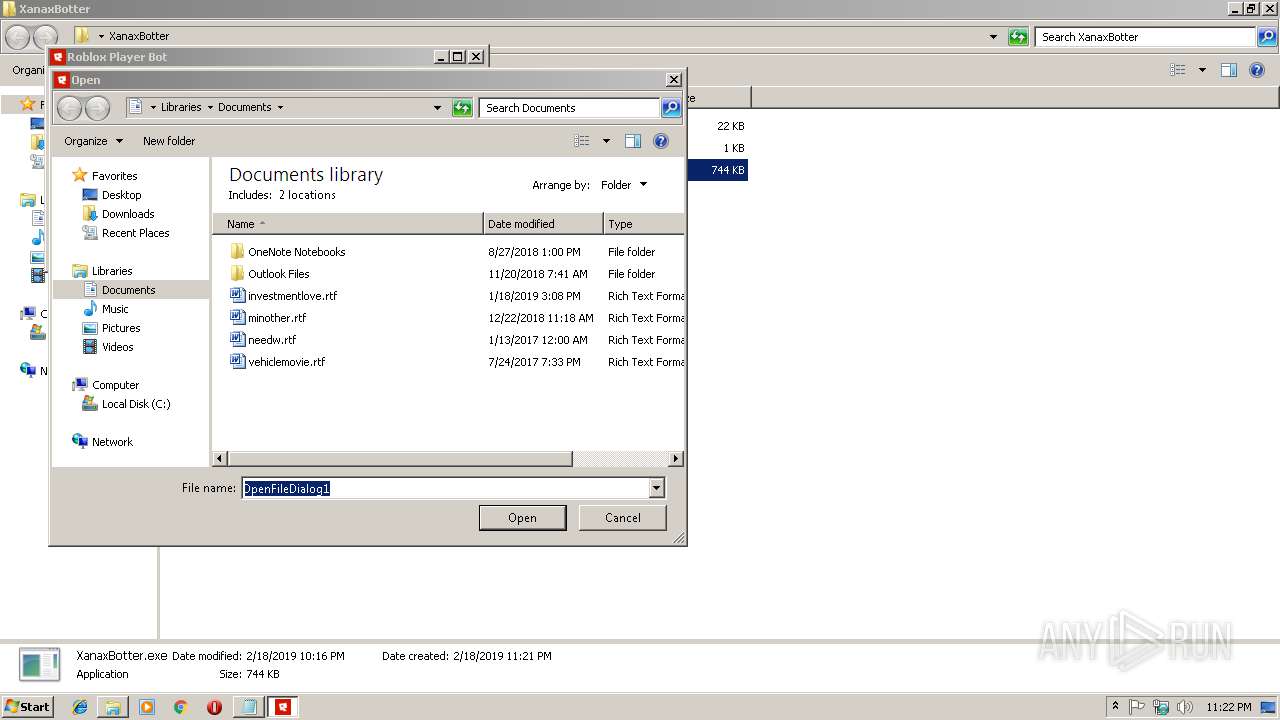
Creates files in the user directory
- XanaxBotter.exe (PID: 2444)
- XanaxBotter.exe (PID: 3512)
Reads Environment values
- file85927.exe (PID: 936)
Reads the cookies of Google Chrome
- file85927.exe (PID: 936)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3016)
Application launched itself
- chrome.exe (PID: 3016)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2736)
Reads settings of System Certificates
- chrome.exe (PID: 3016)
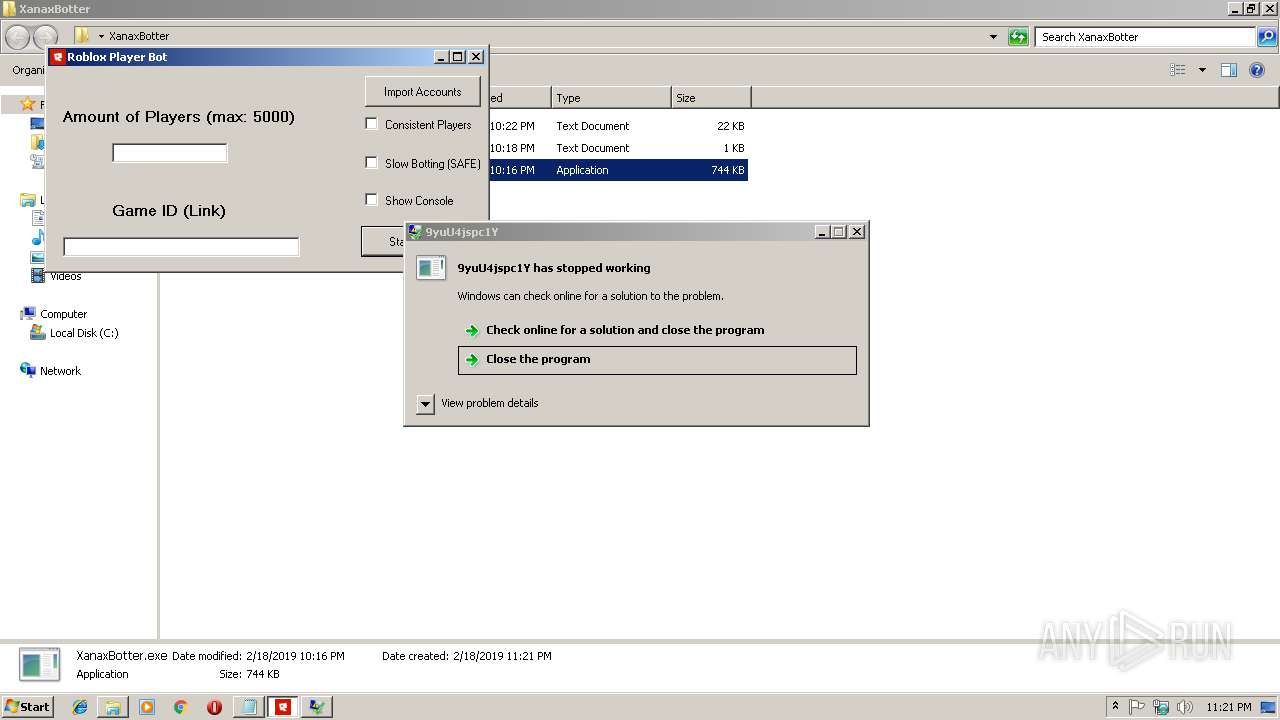
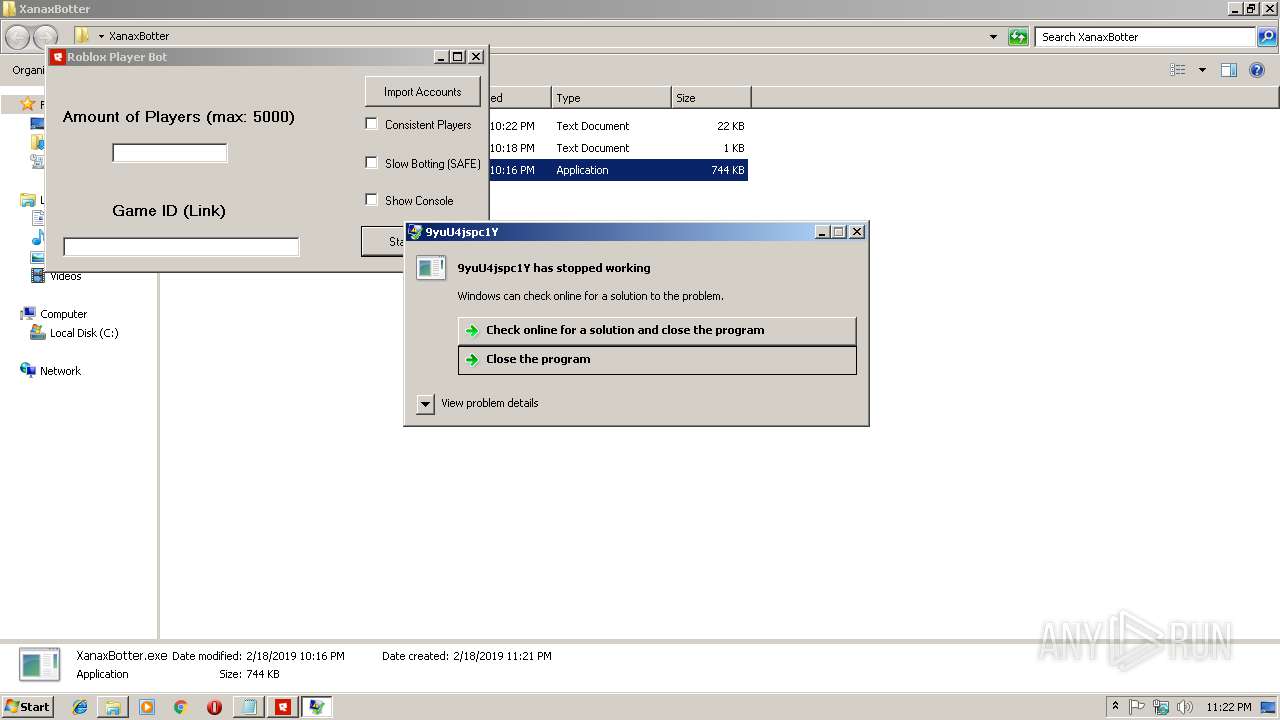
Application was crashed
- file174805.exe (PID: 3296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Users\admin\AppData\Roaming\file85927.exe" | C:\Users\admin\AppData\Roaming\file85927.exe | XanaxBotter.exe | ||||||||||||
User: admin Company: C1YsbcmJXJWFD2 Integrity Level: MEDIUM Description: 9yuU4jspc1Y Exit code: 0 Version: 4.3.4.7 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=924,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=27FA7F2C489BAE057CB7508B5C678935 --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
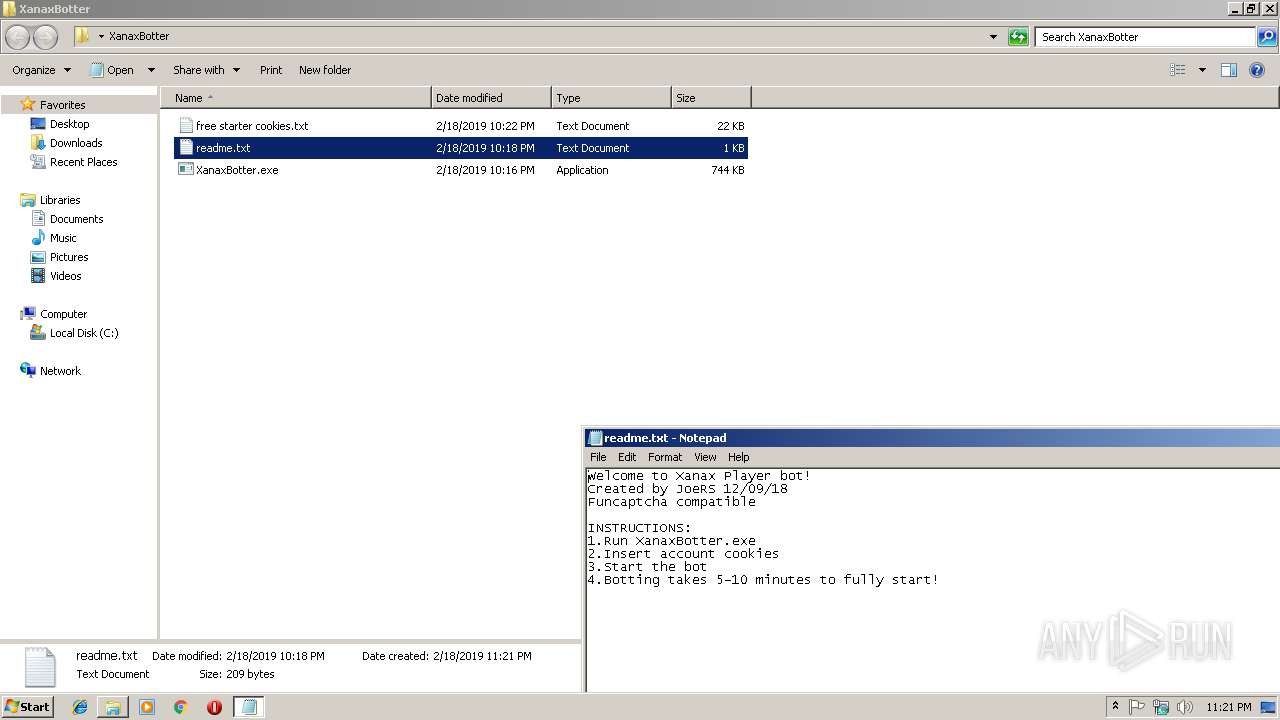
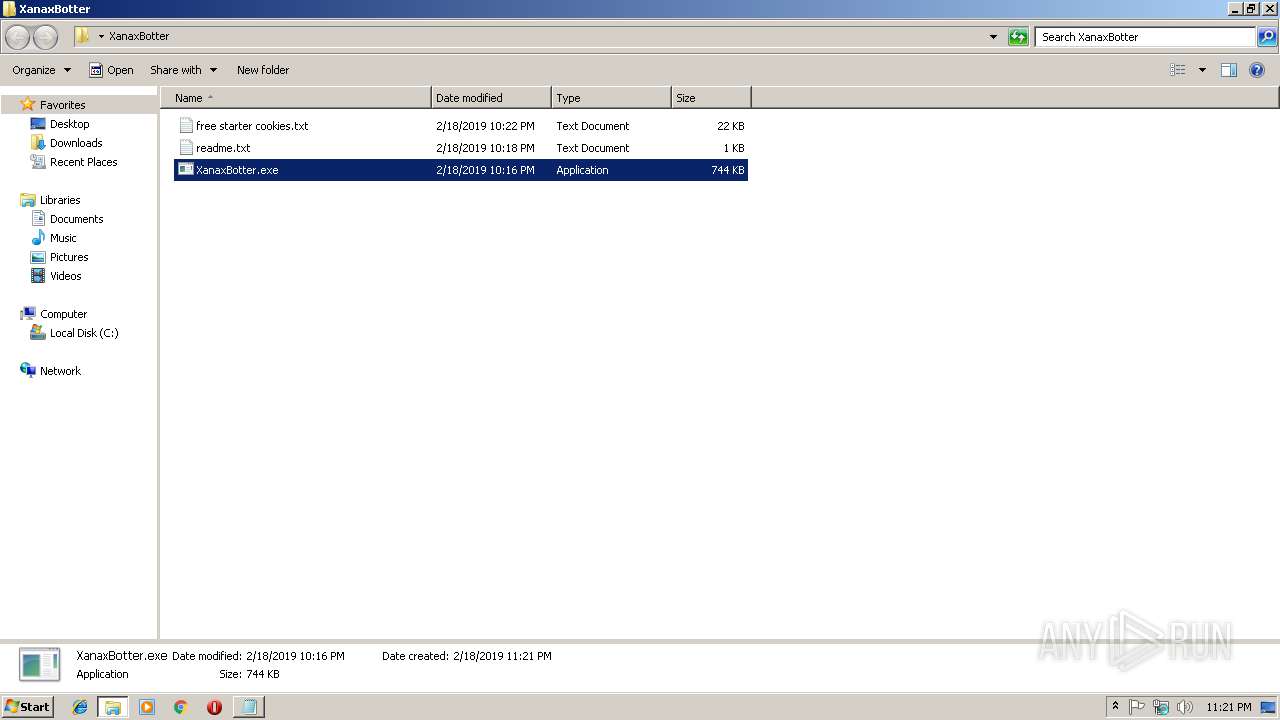
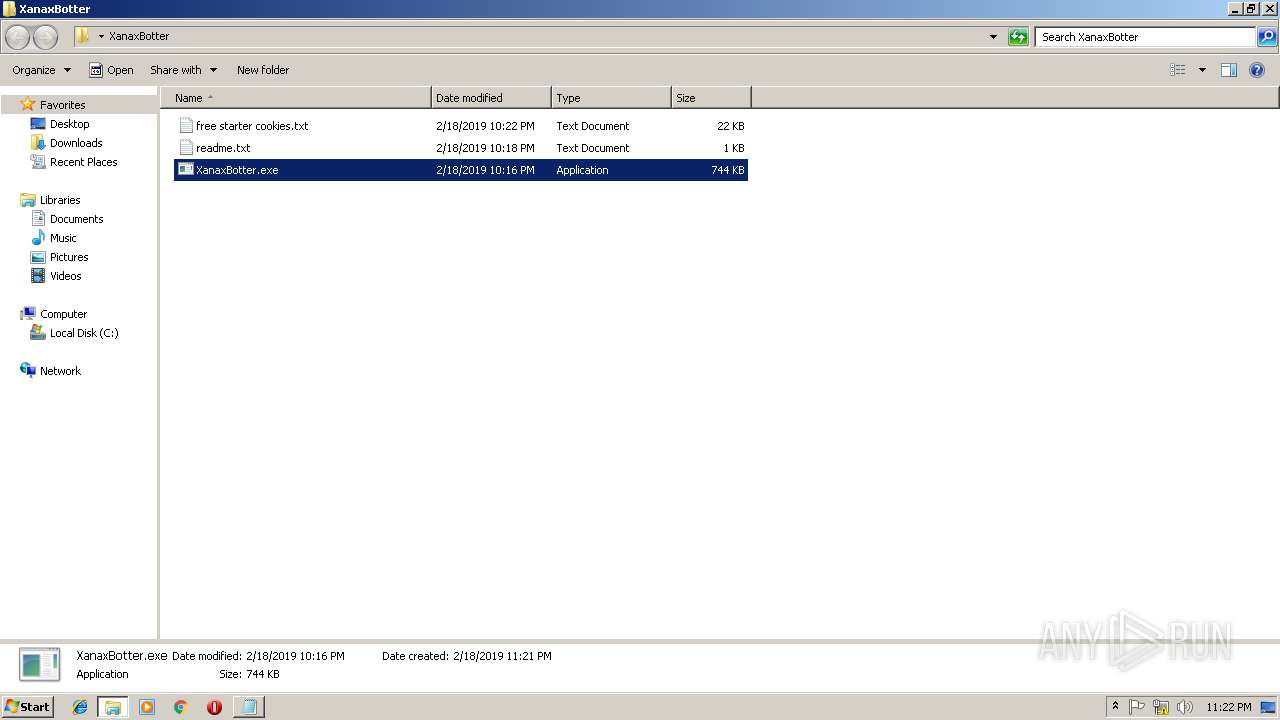
| 2444 | "C:\Users\admin\Desktop\XanaxBotter\XanaxBotter.exe" | C:\Users\admin\Desktop\XanaxBotter\XanaxBotter.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
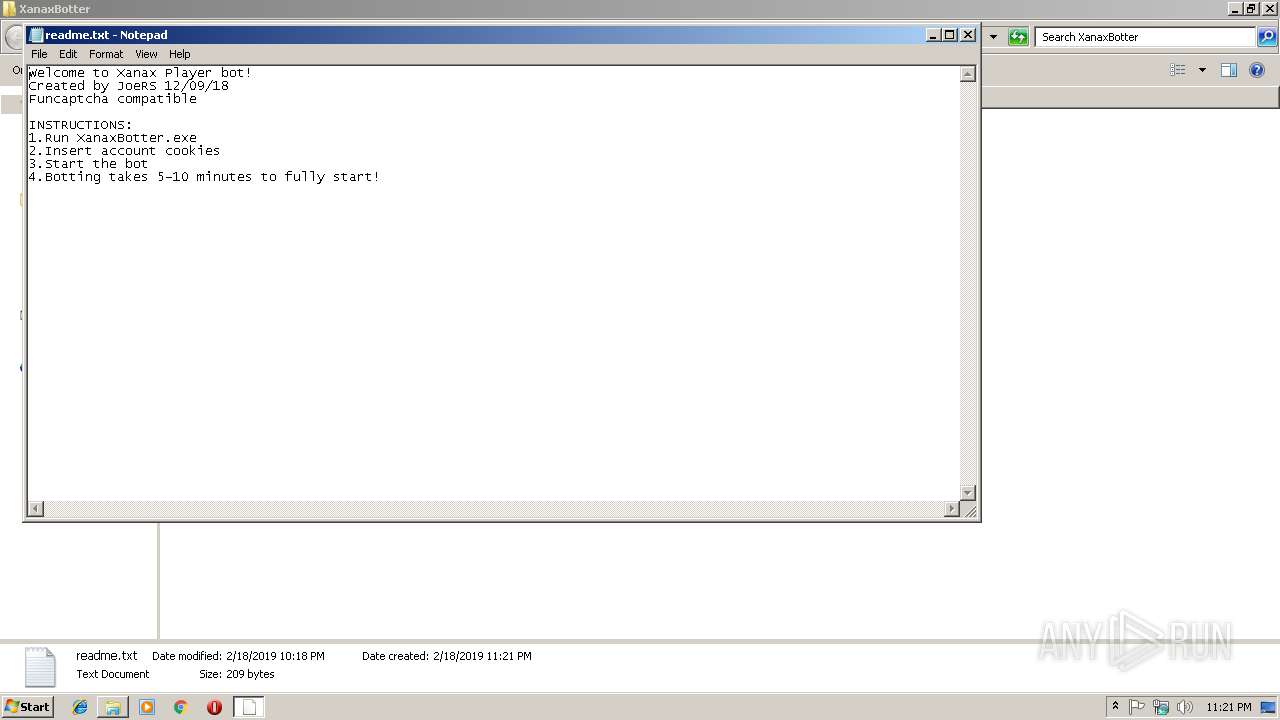
| 2476 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\XanaxBotter\readme.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --service-pipe-token=0CF2AC52FD55C275D6739839AA32877D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0CF2AC52FD55C275D6739839AA32877D --renderer-client-id=4 --mojo-platform-channel-handle=1876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
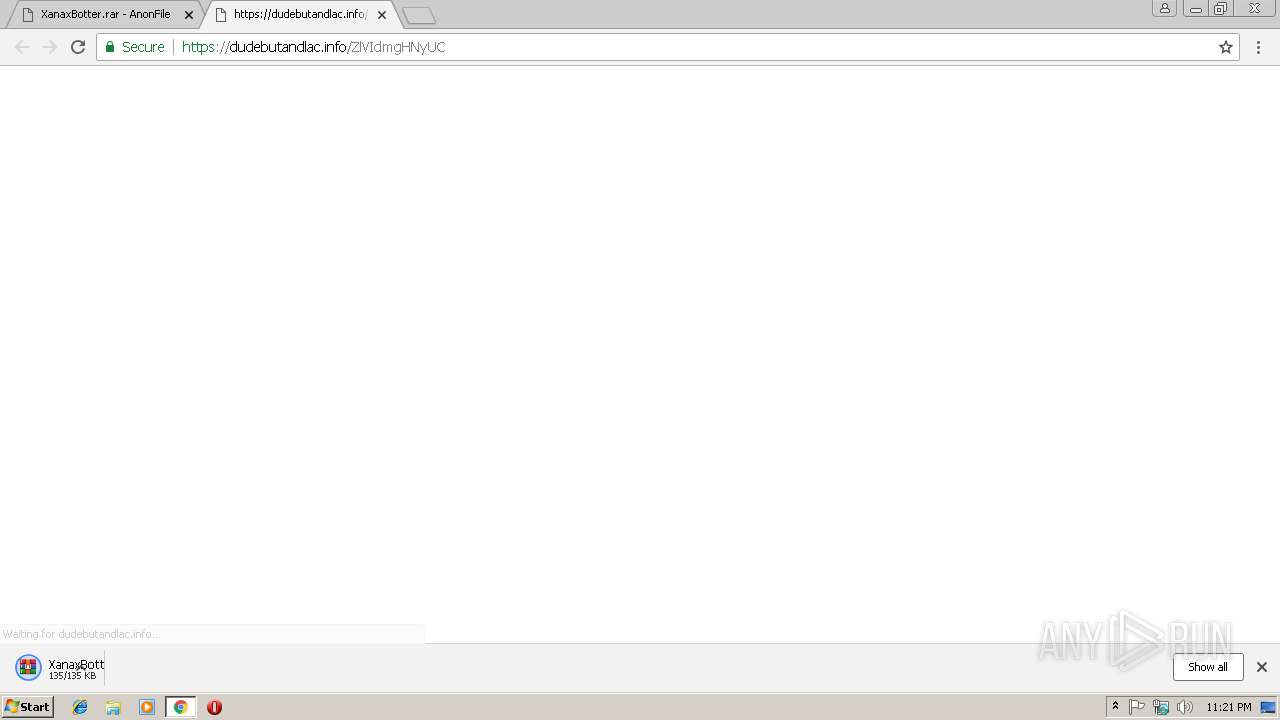
| 2736 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\XanaxBotter.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
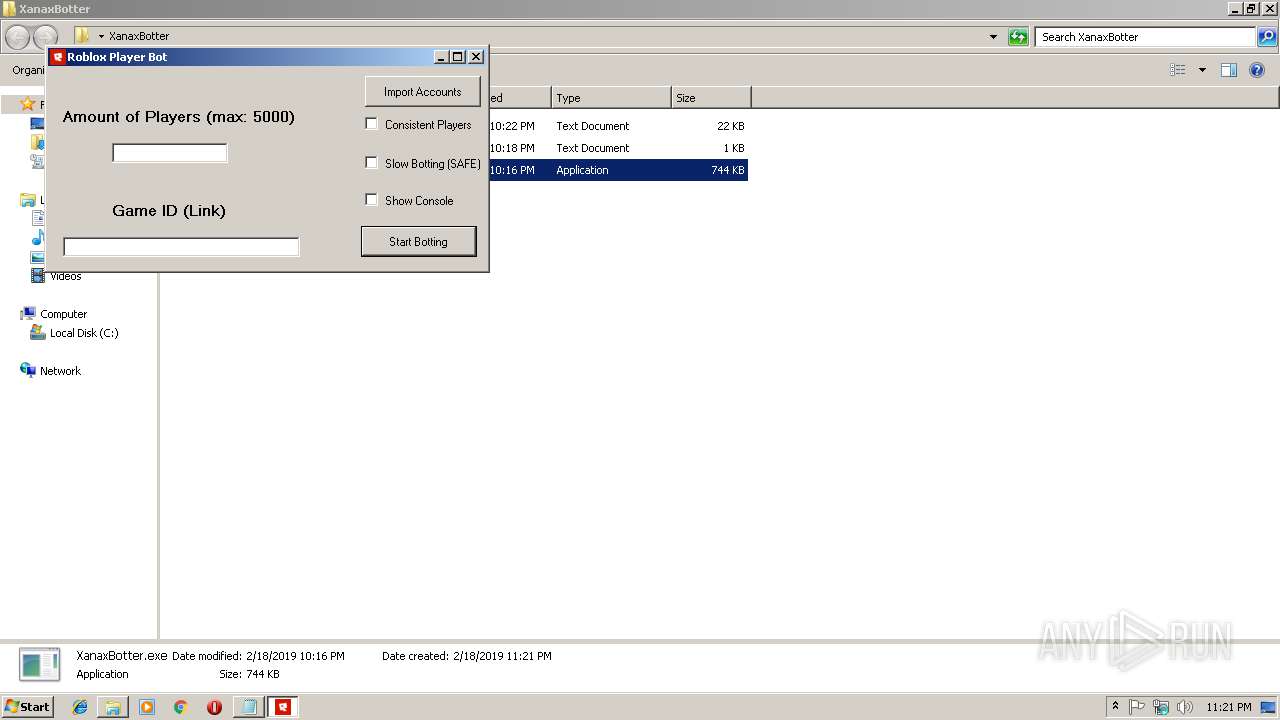
| 2984 | "C:\Users\admin\AppData\Roaming\file173206.exe" | C:\Users\admin\AppData\Roaming\file173206.exe | — | XanaxBotter.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Roblox Player Bot Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://anonfile.com/76Gbv3ubb6/XanaxBotter_rar | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3020 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --service-pipe-token=BAC0081CAD1CB12FADF0F1FED8E3F0F8 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BAC0081CAD1CB12FADF0F1FED8E3F0F8 --renderer-client-id=3 --mojo-platform-channel-handle=2068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 204
Read events
2 081
Write events
119
Delete events
4
Modification events
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3016-13195005674853250 |
Value: 259 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3016-13195005674853250 |
Value: 259 | |||
| (PID) Process: | (3016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
5
Suspicious files
48
Text files
99
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a20503db-345c-43d7-89ca-d3d2c1acdaa2.tmp | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0c8e05fe-79ec-422e-acc4-7e2e9472df20.tmp | — | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF246dbe.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
41
DNS requests
40
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
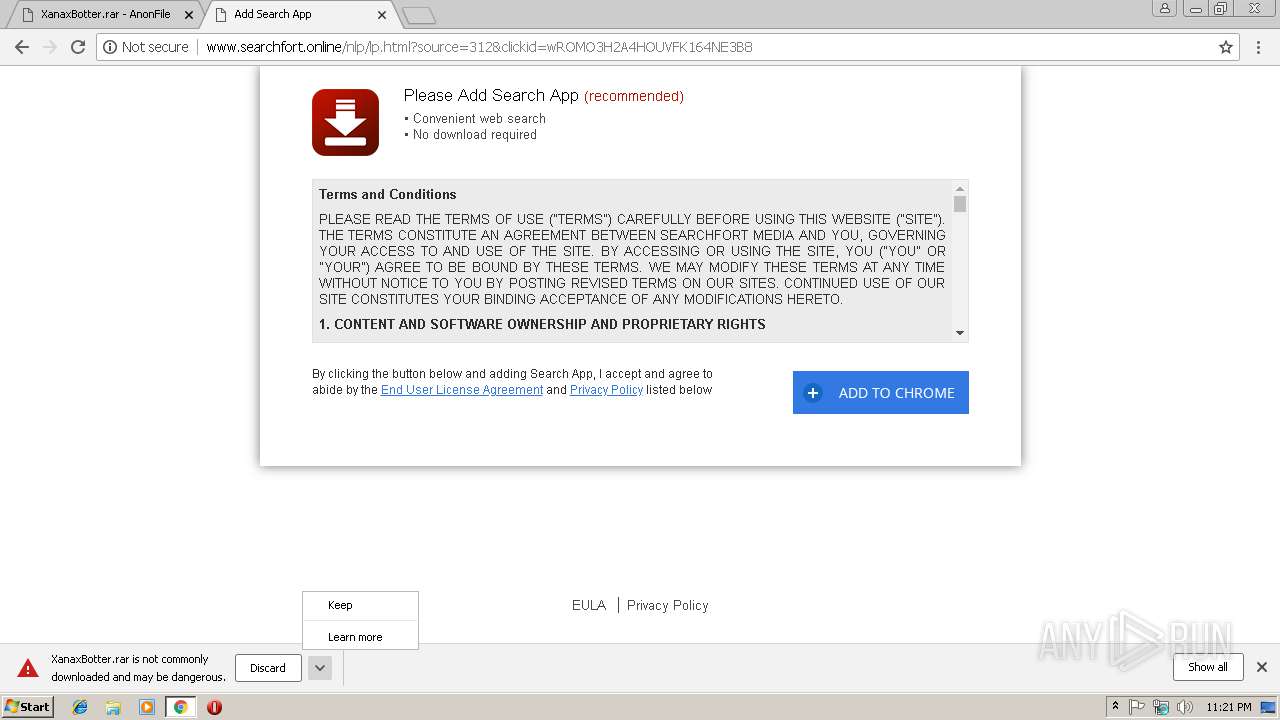
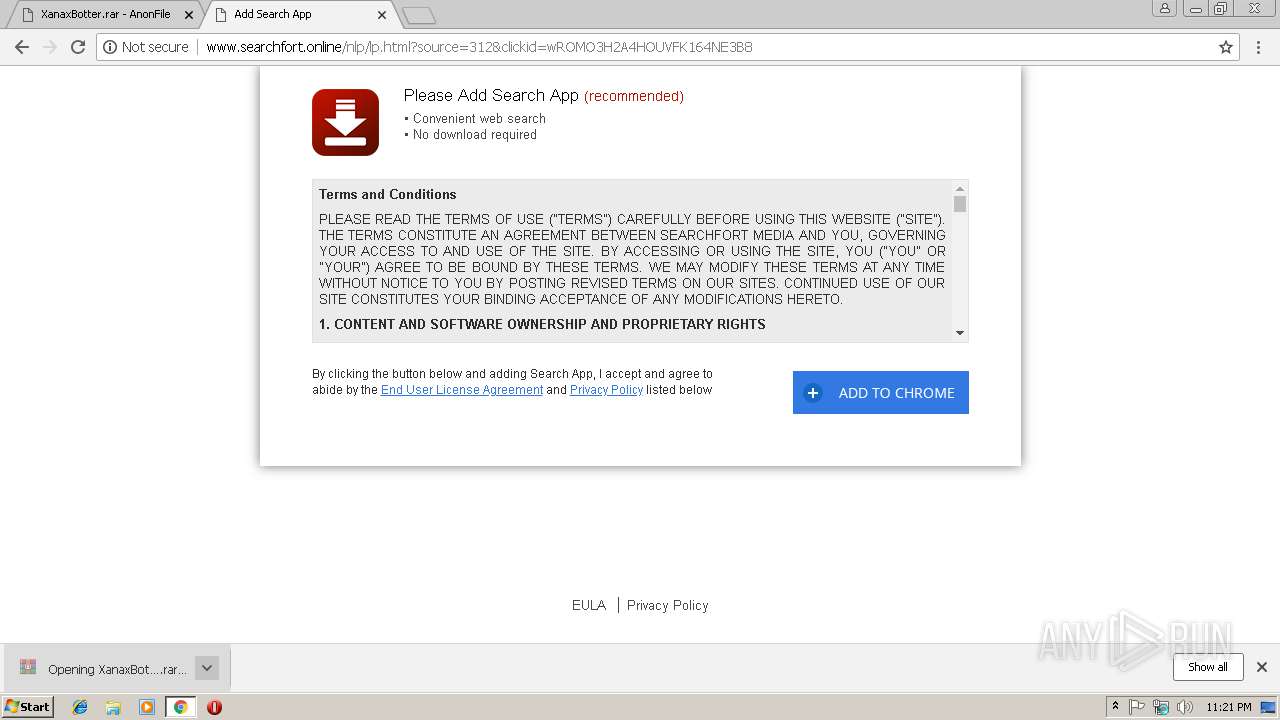
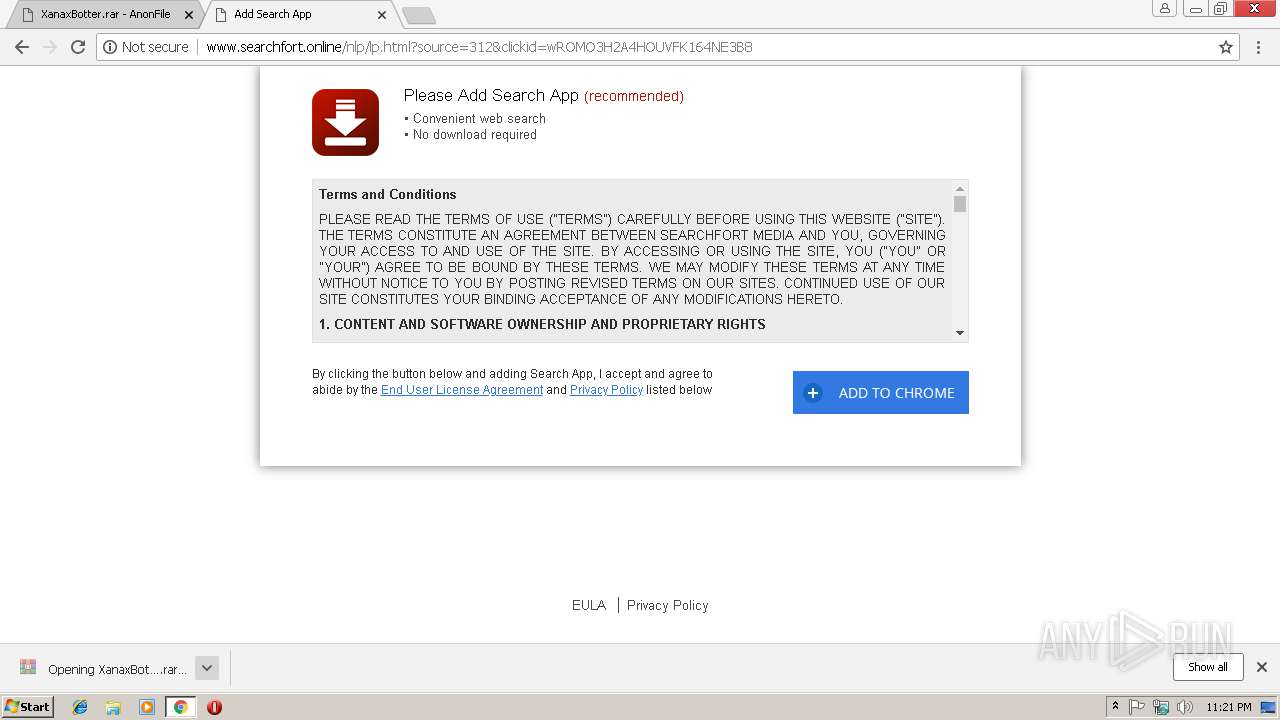
3016 | chrome.exe | GET | 302 | 18.195.71.253:80 | http://conityles-angths.com/733ffdca-83c0-41af-8c2d-450b460dba85?unique_req=-8332255289115197791&pubid=714041 | DE | — | — | shared |
936 | file85927.exe | GET | 301 | 104.31.76.103:80 | http://browserloot.rokey.xyz/api/get-ip.php | US | — | — | malicious |
3016 | chrome.exe | GET | 304 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
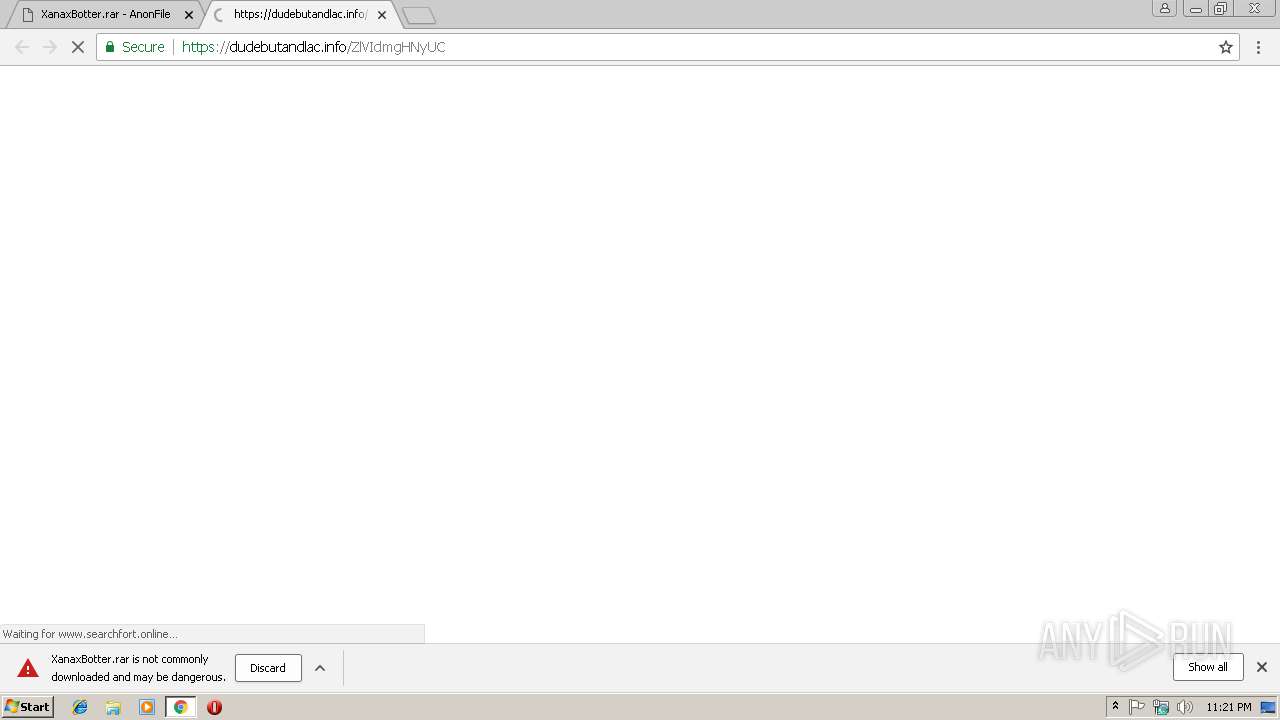
3016 | chrome.exe | GET | 200 | 104.28.0.62:80 | http://www.searchfort.online/nlp/lp.html?source=312&clickid=wROMO3H2A4HOUVFK164NE3B8 | US | html | 9.91 Kb | suspicious |
3016 | chrome.exe | GET | 200 | 104.28.0.62:80 | http://www.searchfort.online/nlp/images/add.png | US | image | 1.52 Kb | suspicious |
3016 | chrome.exe | GET | 200 | 104.28.0.62:80 | http://www.searchfort.online/nlp/images/download.png | US | image | 3.34 Kb | suspicious |
3016 | chrome.exe | GET | 200 | 104.28.0.62:80 | http://www.searchfort.online/nlp/images/bluearrow.gif | US | image | 64.6 Kb | suspicious |
3016 | chrome.exe | GET | 200 | 104.28.0.62:80 | http://www.searchfort.online/nlp/images/bluearrow-up.gif | US | image | 56.0 Kb | suspicious |
3016 | chrome.exe | GET | 404 | 104.28.0.62:80 | http://www.searchfort.online/nlp/images/confirm_dialog.png | US | xml | 132 b | suspicious |
3016 | chrome.exe | GET | 404 | 104.28.0.62:80 | http://www.searchfort.online/nlp/images/cancel.png | US | xml | 132 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3016 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3016 | chrome.exe | 104.31.156.7:443 | rattedropenrigh.info | Cloudflare Inc | US | shared |
3016 | chrome.exe | 54.230.93.248:443 | boudja.com | Amazon.com, Inc. | US | unknown |
3016 | chrome.exe | 52.85.188.197:80 | x.ss2.us | Amazon.com, Inc. | US | suspicious |
3016 | chrome.exe | 54.87.142.112:443 | dudebutandlac.info | Amazon.com, Inc. | US | unknown |
3016 | chrome.exe | 107.23.30.93:443 | emisedsaddamson.info | Amazon.com, Inc. | US | unknown |
3016 | chrome.exe | 54.230.93.230:443 | leguinge.info | Amazon.com, Inc. | US | unknown |
3016 | chrome.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3016 | chrome.exe | 185.147.237.15:443 | cdn-02.anonfile.com | Obenetwork AB | SE | unknown |
3016 | chrome.exe | 52.204.252.186:443 | p.adsymptotic.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfile.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
vjs.zencdn.net |
| whitelisted |
cdn-01.anonfile.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
cdn-02.anonfile.com |
| suspicious |
cdn-03.anonfile.com |
| unknown |
cdn-05.anonfile.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
936 | file85927.exe | A Network Trojan was detected | MALWARE [PTsecurity] BrowserLoot Stealer |
936 | file85927.exe | A Network Trojan was detected | MALWARE [PTsecurity] BrowserLoot Stealer Connection |
2 ETPRO signatures available at the full report