| File name: | (VIRUS) !@Set-𝓤p__7599--!P𝕒$w0ɾ𝓓##.zip |
| Full analysis: | https://app.any.run/tasks/68fd8015-c471-4beb-9bac-4066ff0dbd80 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 03, 2025, 23:28:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | D31ACAB9AC06014062B524A81995F060 |
| SHA1: | 36A178802FB240EBD8C56DFC1C03B0FF661B2244 |
| SHA256: | 0D1121D7D38C0E1F193A3E8769E66A69608AEB2C825284CB7BE5D1BFEE30C2DA |
| SSDEEP: | 98304:0YZ/6mreFxBj3ywHGdw9h2Veupdn0d4qIYssCr7cYstMIM4hKk7+Gs2oslCcRyRO:YvEHeUBAwu |
MALICIOUS
Executing a file with an untrusted certificate
- setup.exe (PID: 3560)
- setup.exe (PID: 5592)
Actions looks like stealing of personal data
- setup.exe (PID: 3560)
- setup.exe (PID: 5592)
LUMMA mutex has been found
- setup.exe (PID: 3560)
- setup.exe (PID: 5592)
Steals credentials from Web Browsers
- setup.exe (PID: 3560)
- setup.exe (PID: 5592)
SUSPICIOUS
Searches for installed software
- setup.exe (PID: 3560)
INFO
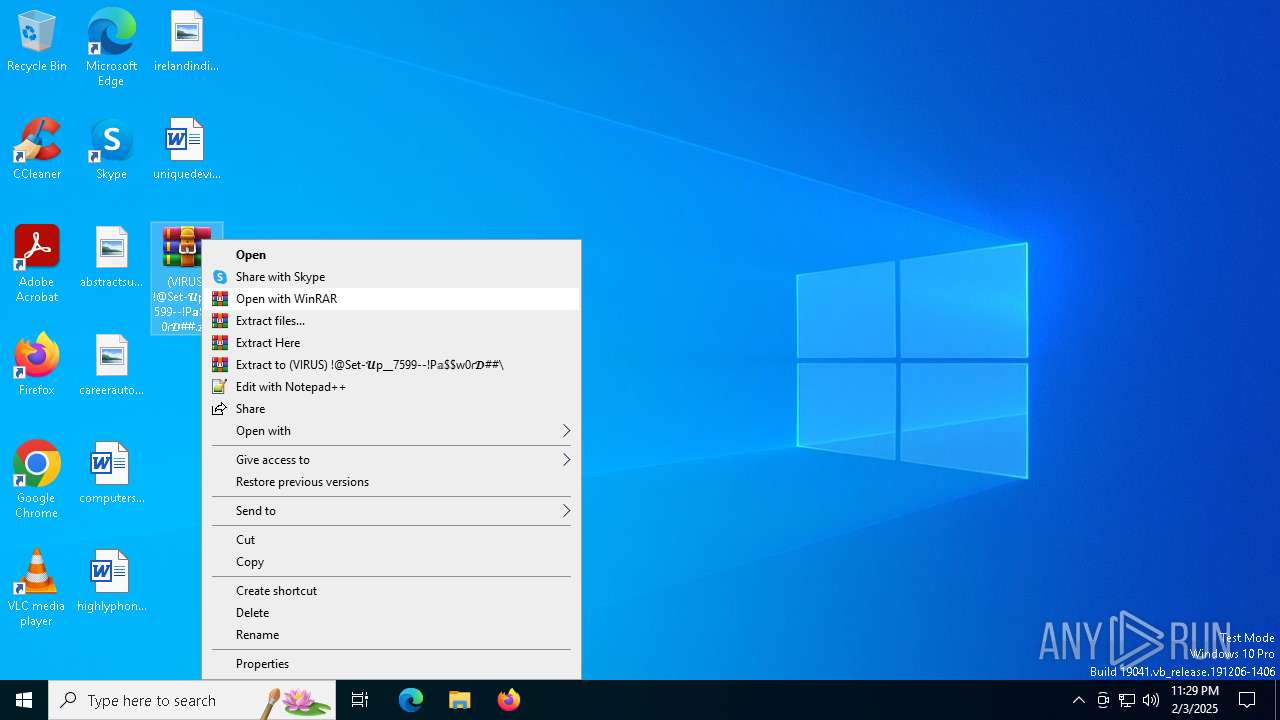
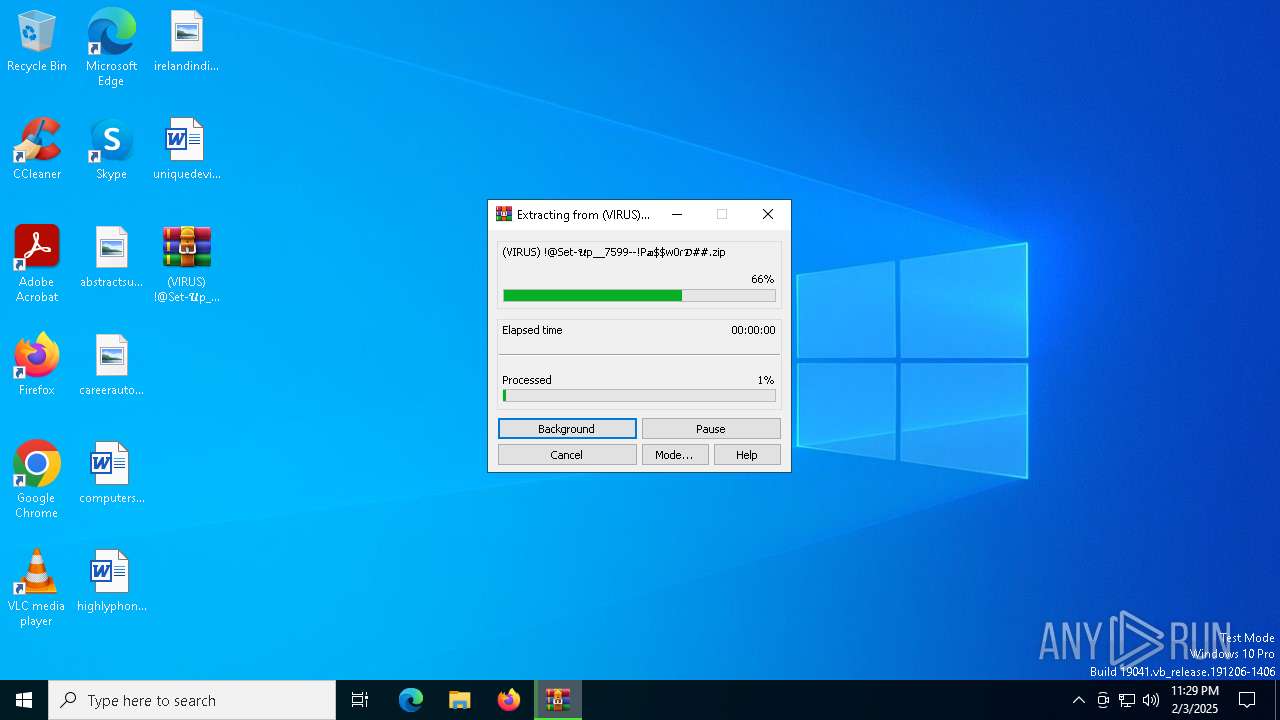
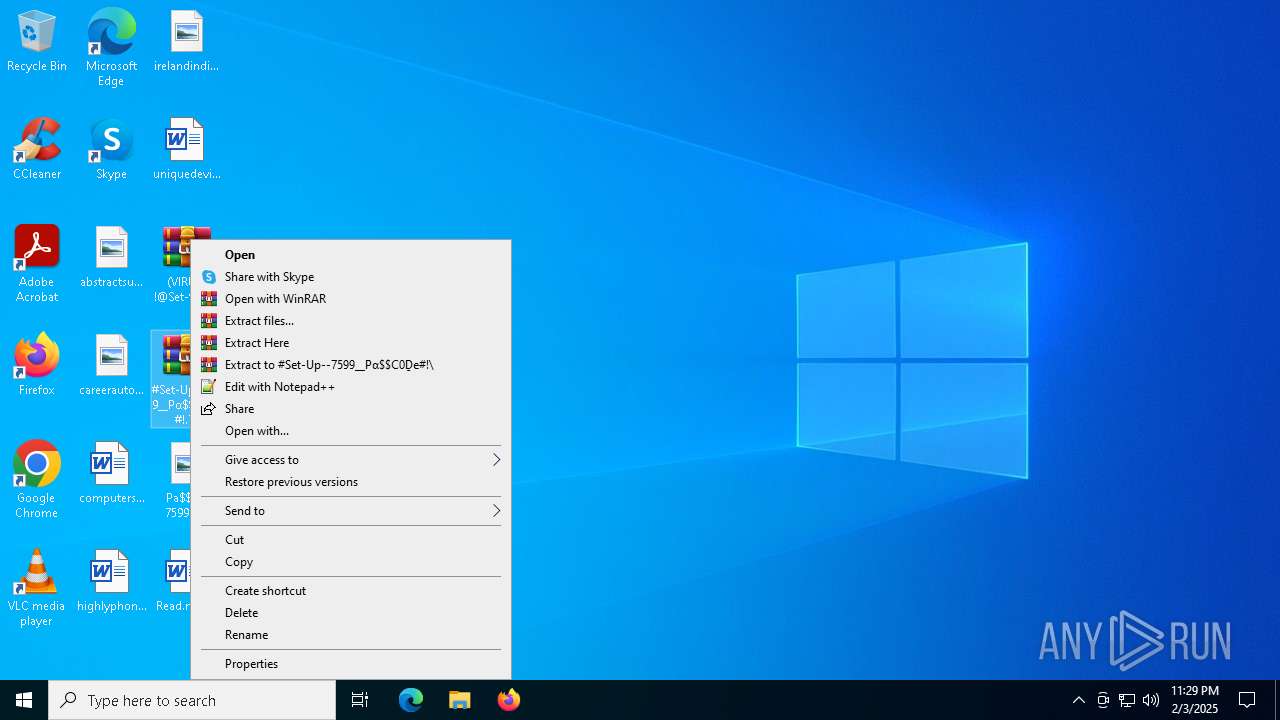
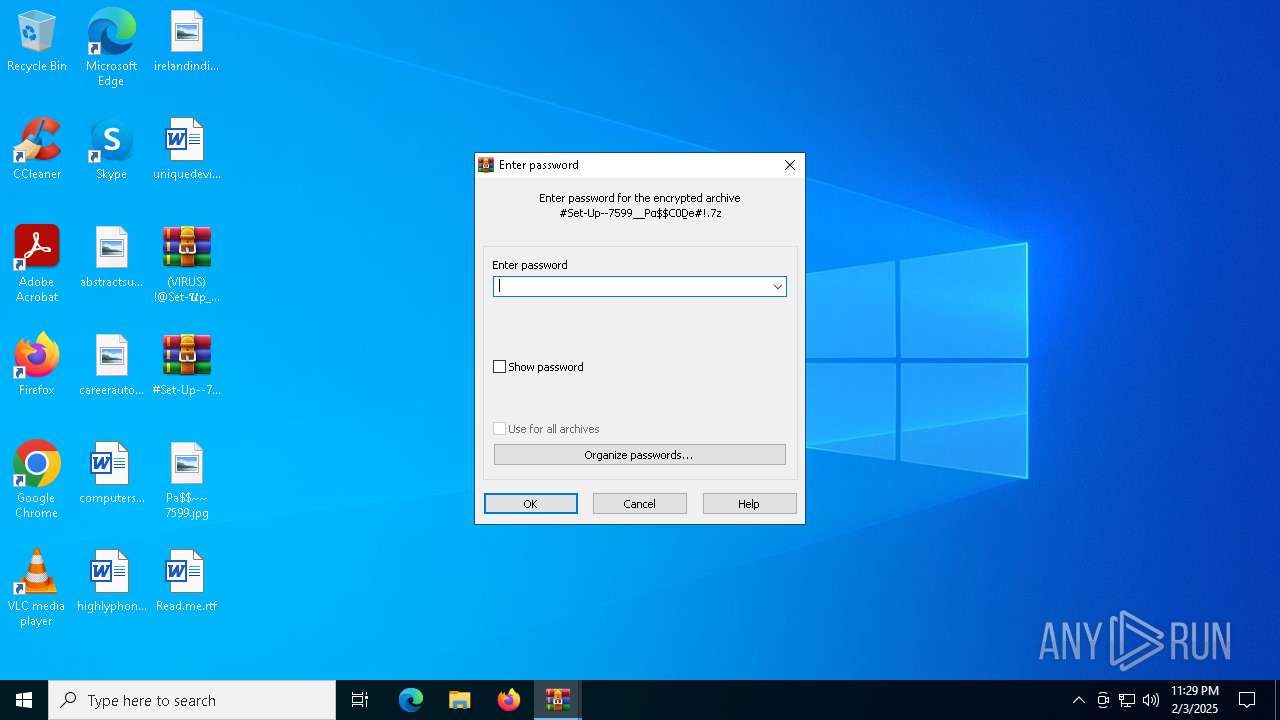
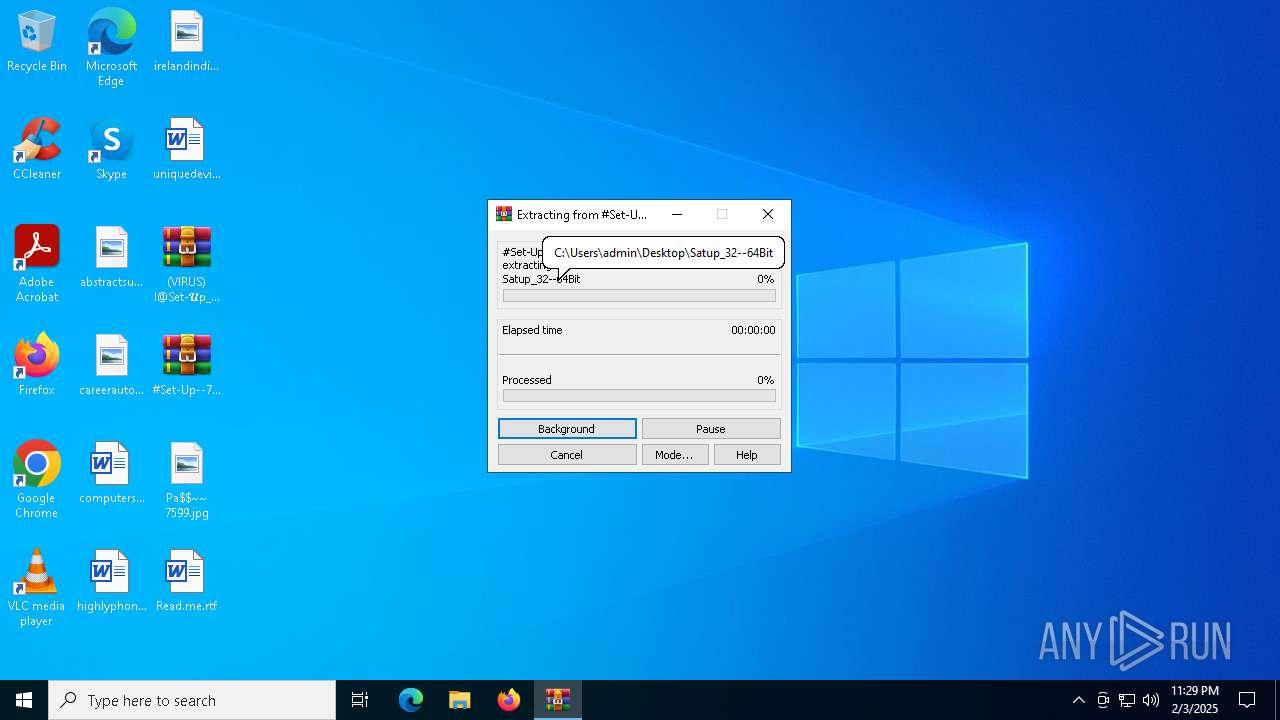
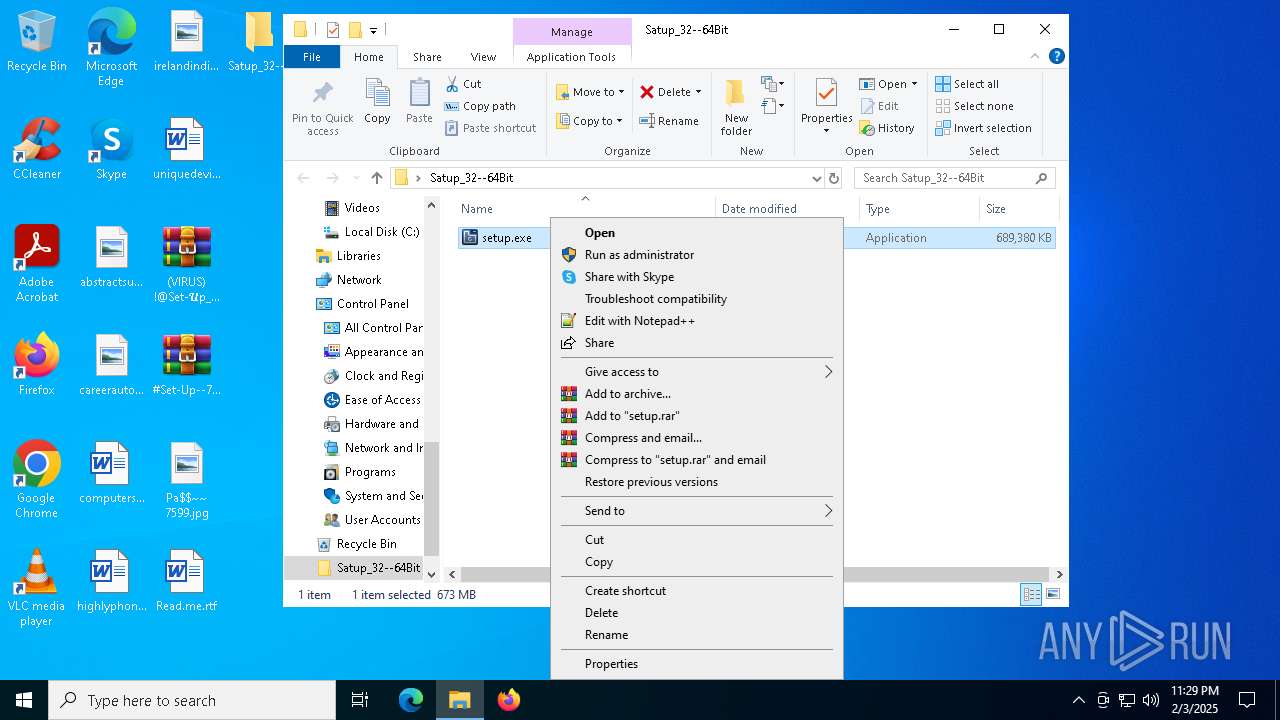
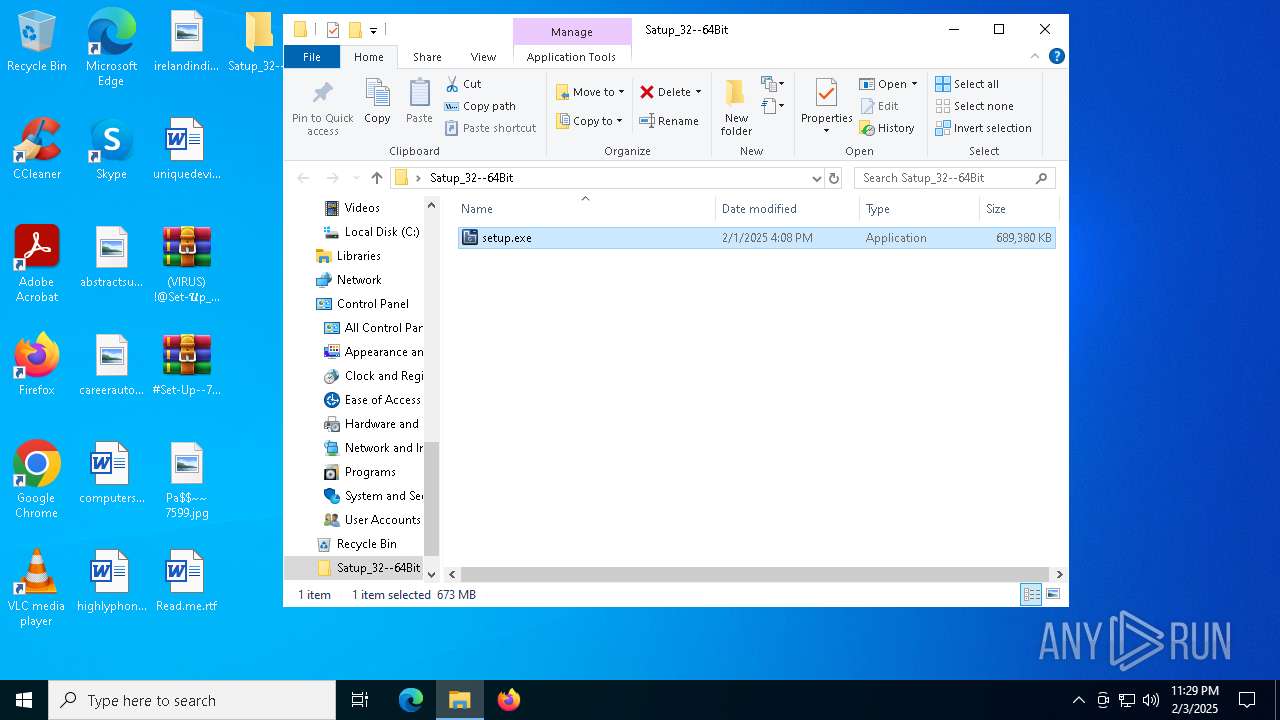
Manual execution by a user
- WinRAR.exe (PID: 6336)
- WinRAR.exe (PID: 6880)
- setup.exe (PID: 3560)
- setup.exe (PID: 5592)
Checks supported languages
- setup.exe (PID: 3560)
- setup.exe (PID: 5592)
Reads the software policy settings
- setup.exe (PID: 3560)
- setup.exe (PID: 5592)
Reads the computer name
- setup.exe (PID: 3560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2025:02:01 22:38:28 |
| ZipCRC: | 0x681bdd8a |
| ZipCompressedSize: | 7228673 |
| ZipUncompressedSize: | 7228673 |
| ZipFileName: | #Set-Up--7599__Pα$C0Ḏe#!.7z |
Total processes
130
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
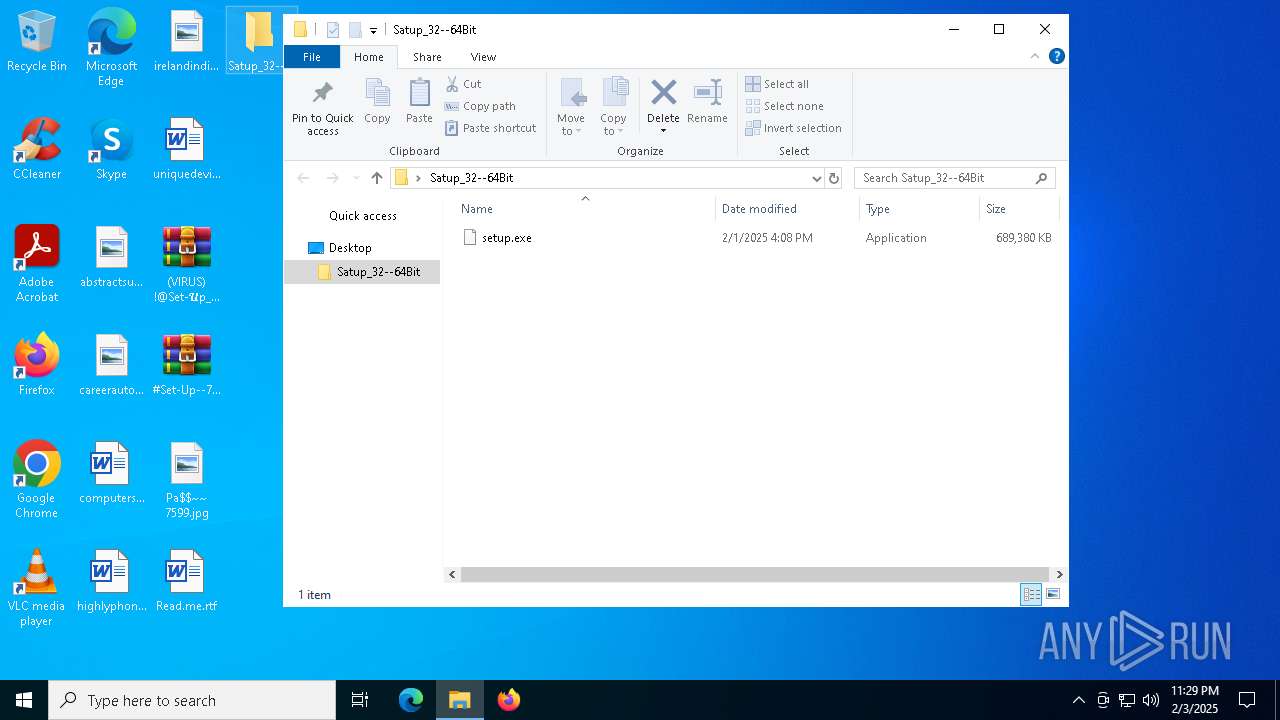
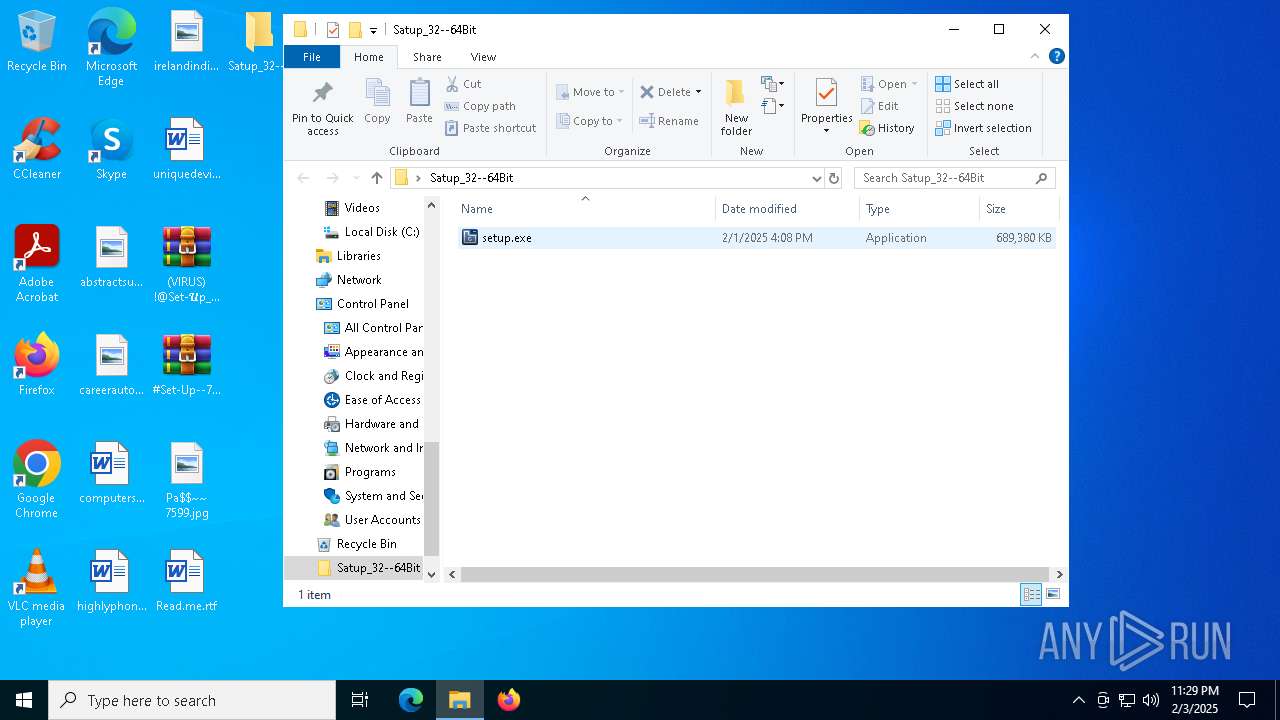
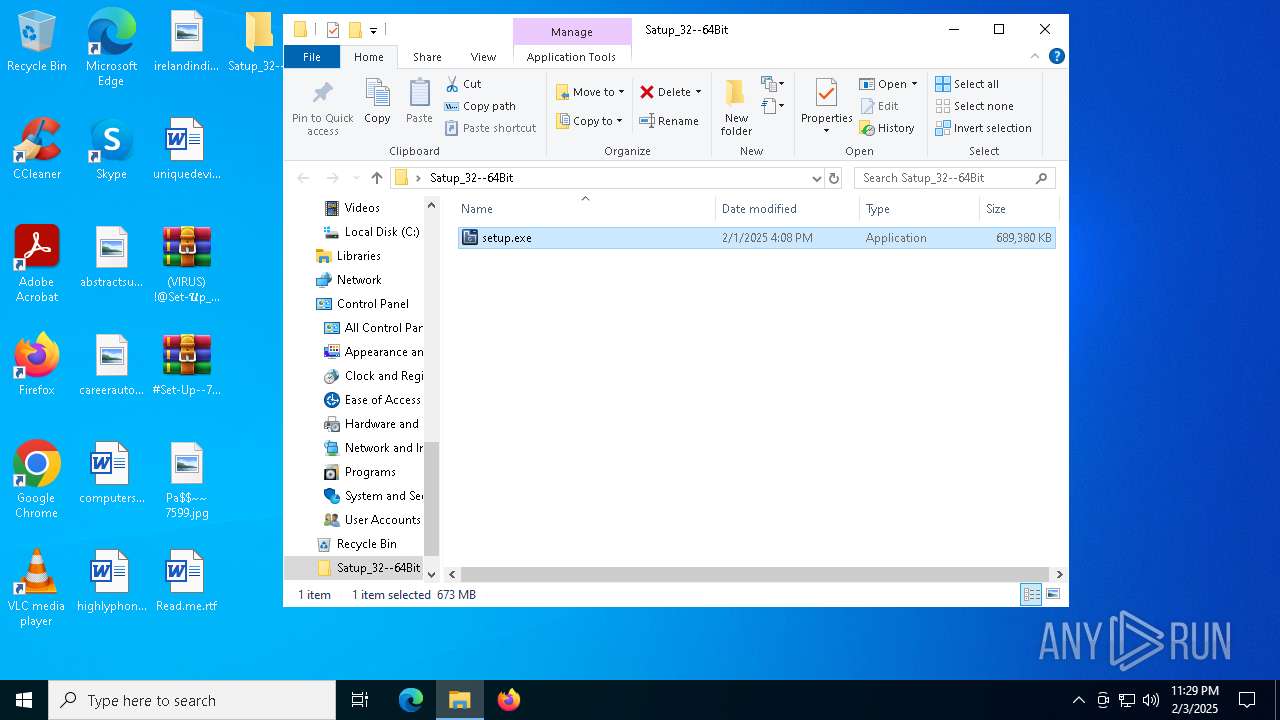
| 3560 | "C:\Users\admin\Desktop\Satup_32--64Bit\setup.exe" | C:\Users\admin\Desktop\Satup_32--64Bit\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Stardock Software Integrity Level: MEDIUM Description: Stardock Groupy 2 Configuration Utility Version: 2.2.0.1 Modules
| |||||||||||||||
| 5268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\(VIRUS) !@Set-𝓤p__7599--!P𝕒$w0ɾ𝓓##.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 5592 | "C:\Users\admin\Desktop\Satup_32--64Bit\setup.exe" | C:\Users\admin\Desktop\Satup_32--64Bit\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Stardock Software Integrity Level: HIGH Description: Stardock Groupy 2 Configuration Utility Version: 2.2.0.1 Modules
| |||||||||||||||
| 6336 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\(VIRUS) !@Set-𝓤p__7599--!P𝕒$w0ɾ𝓓##.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6880 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\#Set-Up--7599__Pα$C0Ḏe#!.7z" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 432
Read events
2 416
Write events
16
Delete events
0
Modification events
| (PID) Process: | (5268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000009E02060000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (5268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000EC0204000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (5268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F0000000000000000000000000000000000000000000CA0207000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6336 | WinRAR.exe | C:\Users\admin\Desktop\#Set-Up--7599__Pα$C0Ḏe#!.7z | — | |
MD5:— | SHA256:— | |||
| 6336 | WinRAR.exe | C:\Users\admin\Desktop\Read.me.rtf | — | |
MD5:— | SHA256:— | |||
| 6880 | WinRAR.exe | C:\Users\admin\Desktop\Satup_32--64Bit\setup.exe | — | |
MD5:— | SHA256:— | |||
| 6336 | WinRAR.exe | C:\Users\admin\Desktop\Pa$~~ 7599.jpg | image | |
MD5:C3811066B884D997E9B0C260D8AB652D | SHA256:C965F3A429719030E573420242B416213C39858F2DFA05CA4081BFF7DE5438F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
37
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.78.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7008 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6244 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7008 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 95.101.78.42:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.178:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious domain by CrossDomain ( .servicelandingkaraoke .shop) |