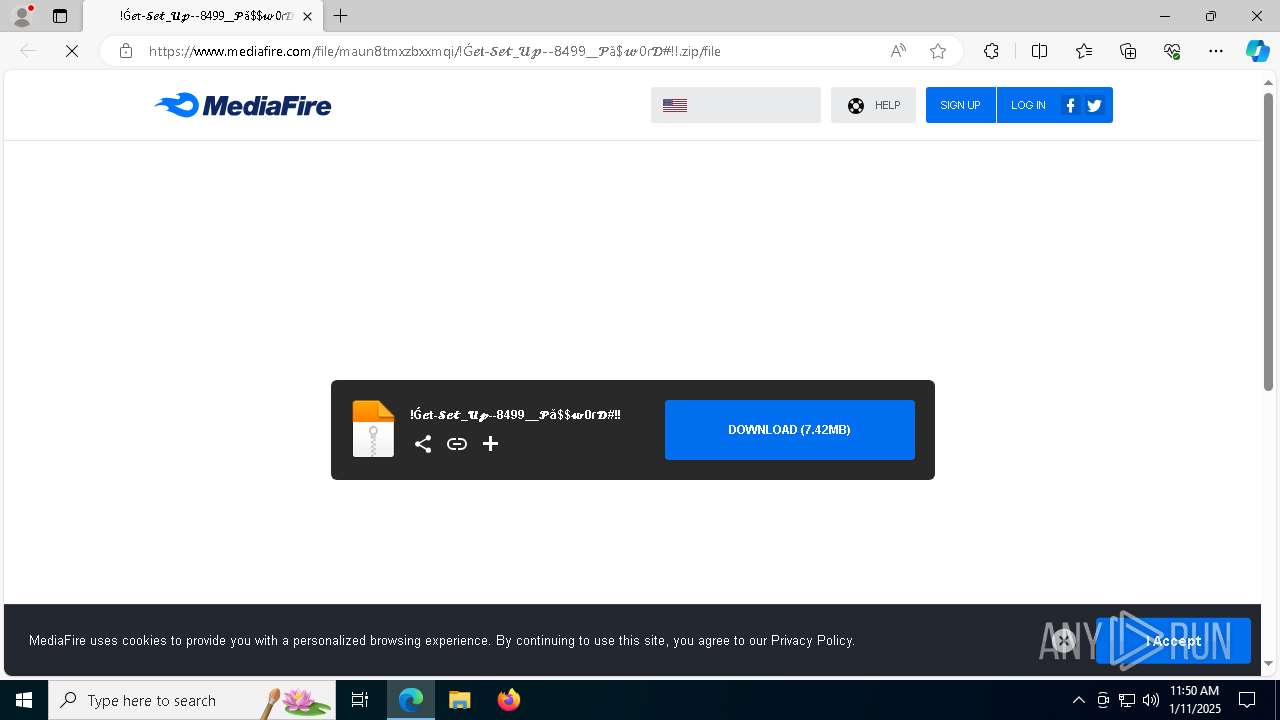
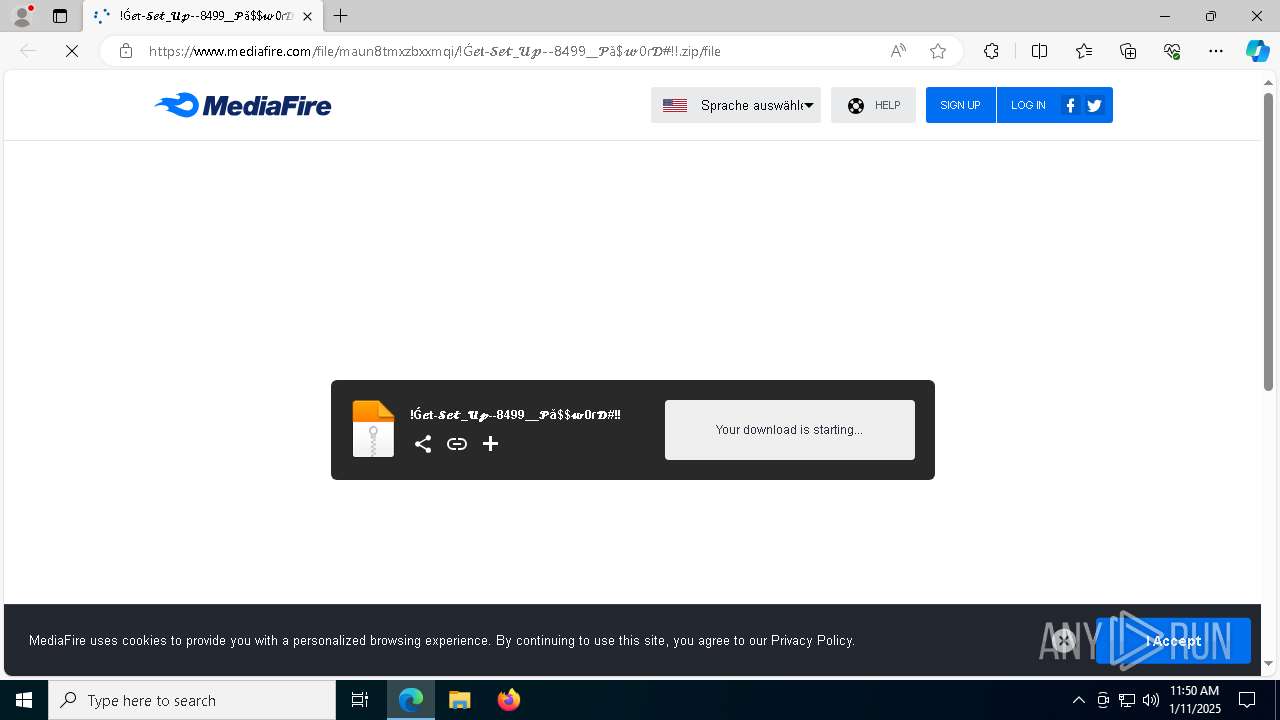
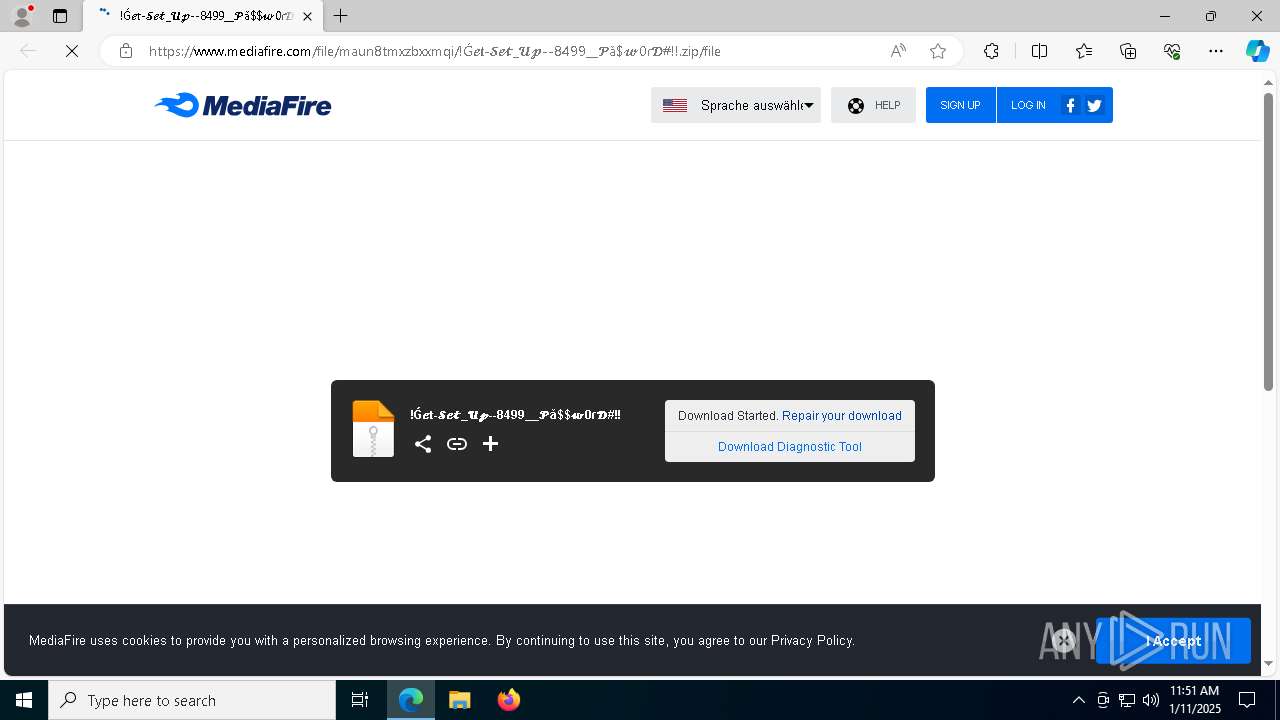
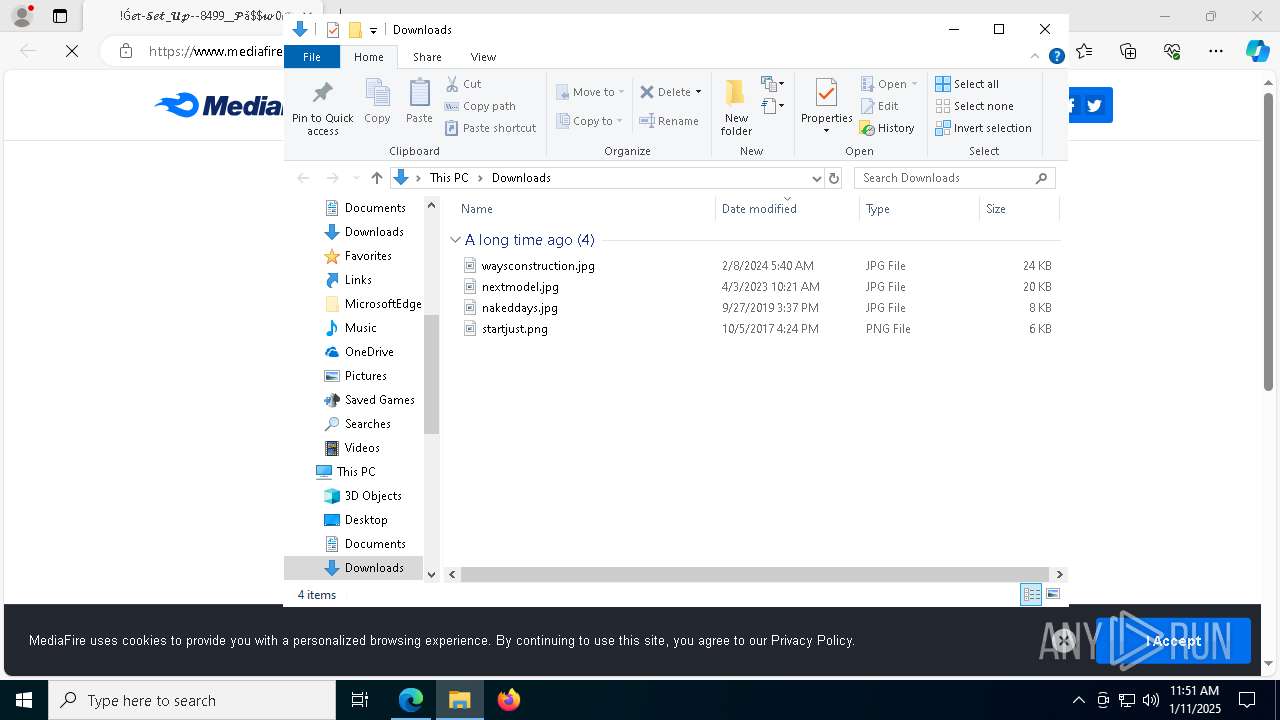
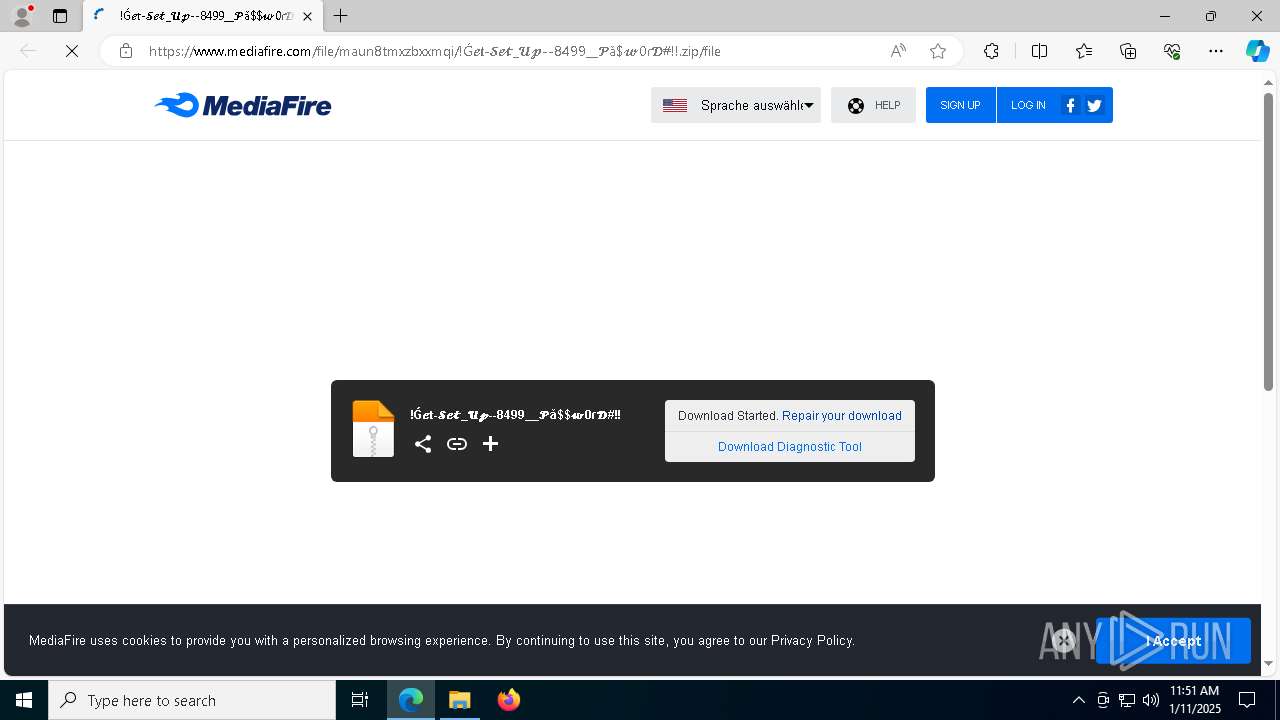
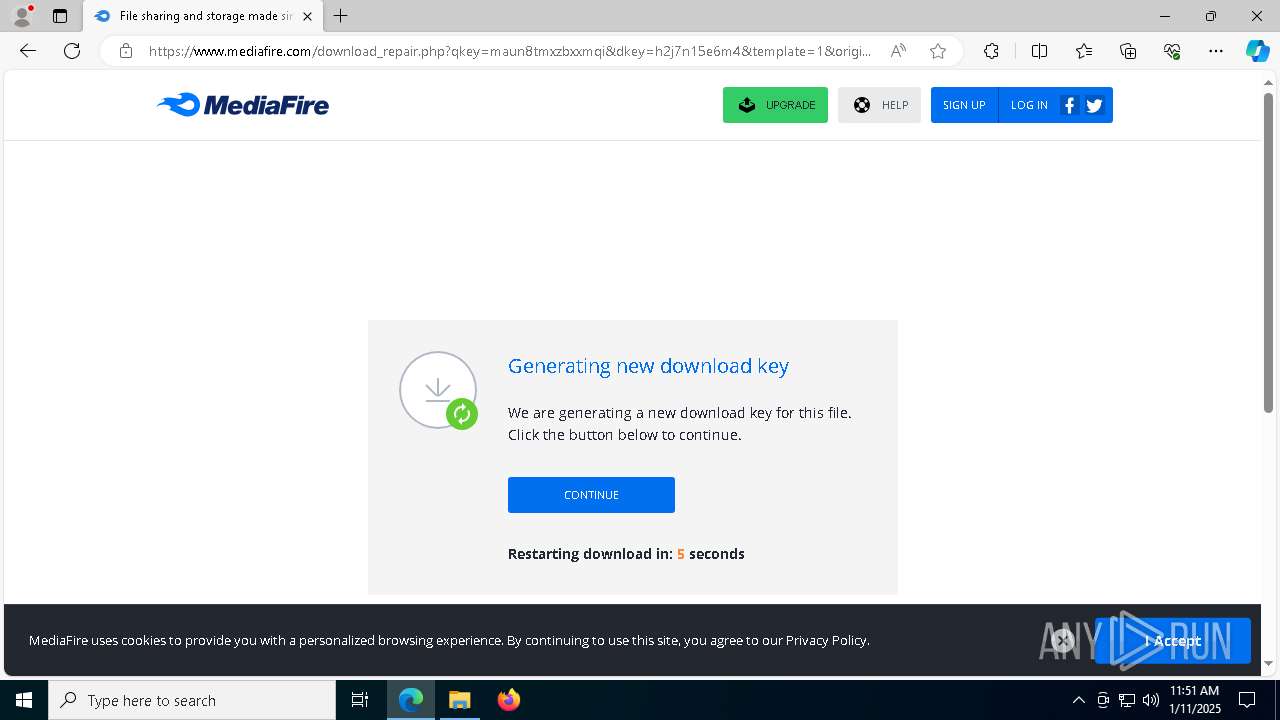
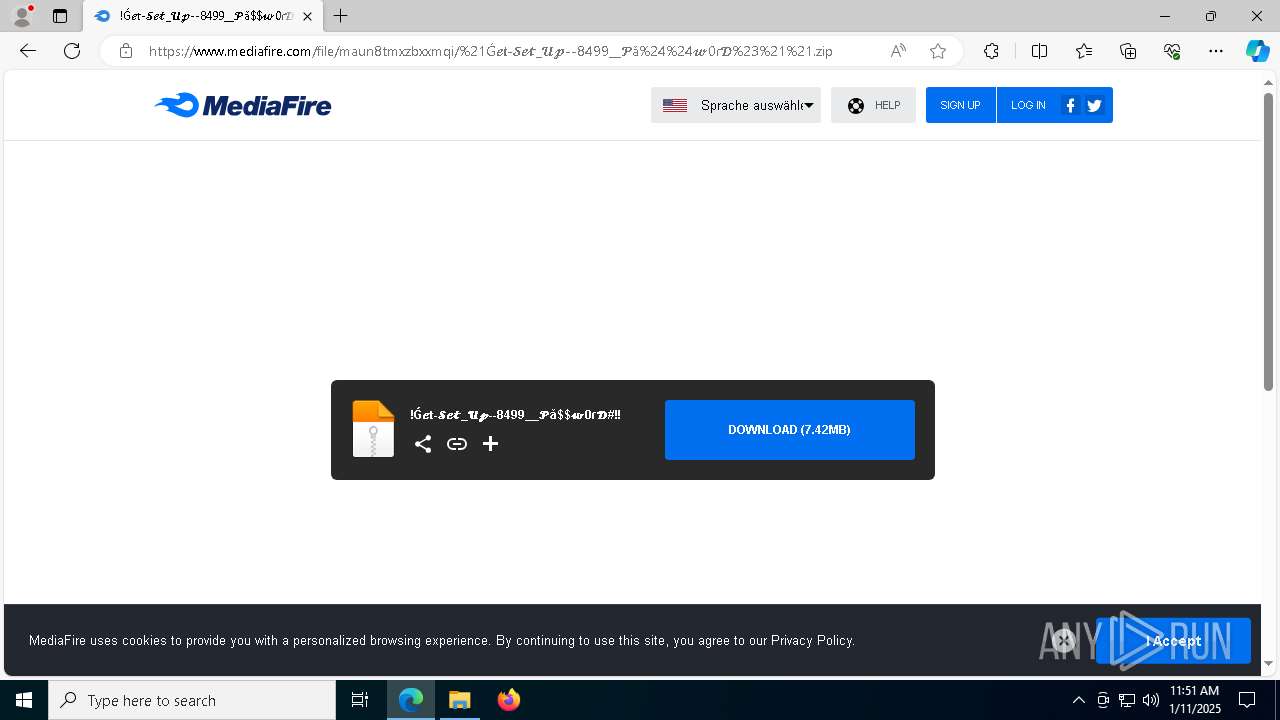
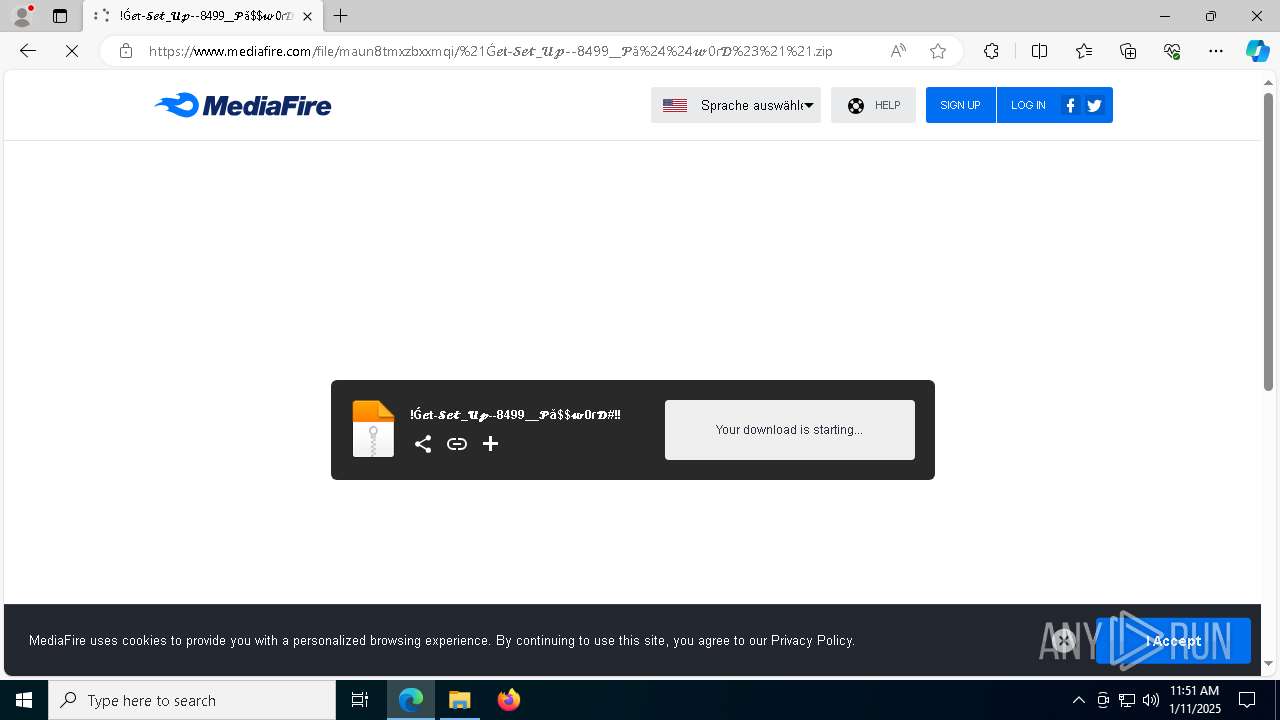
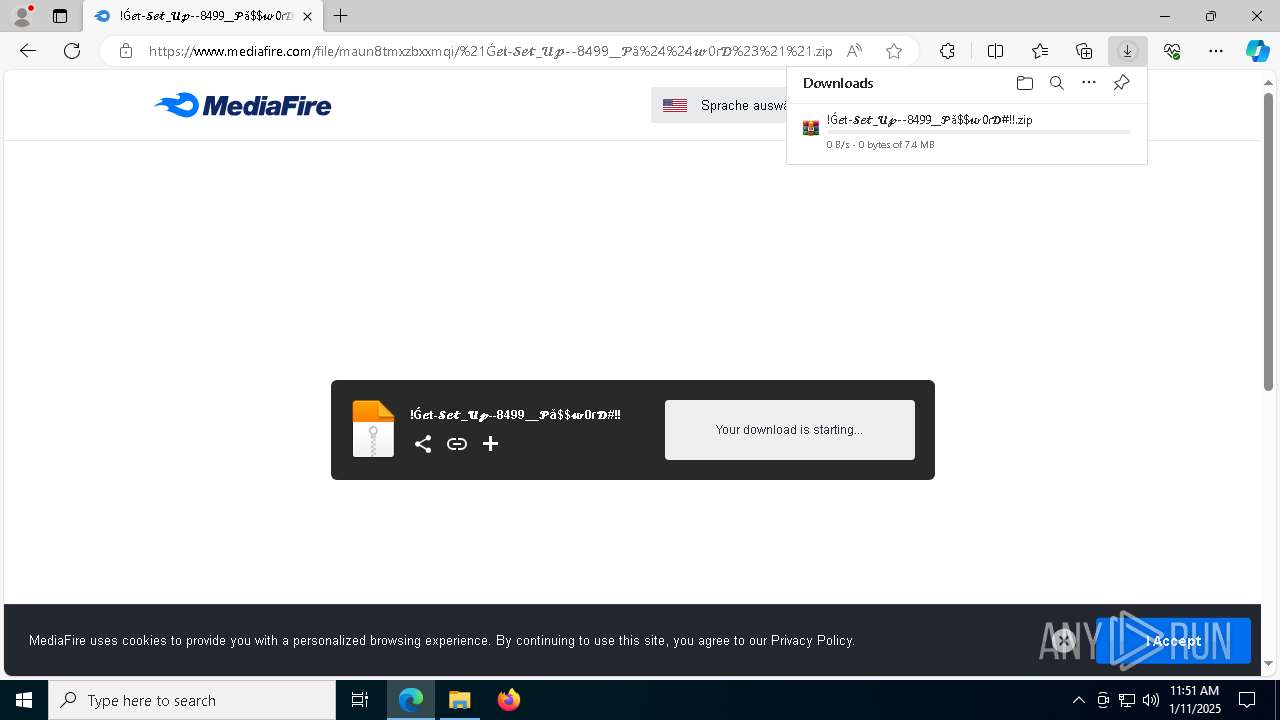
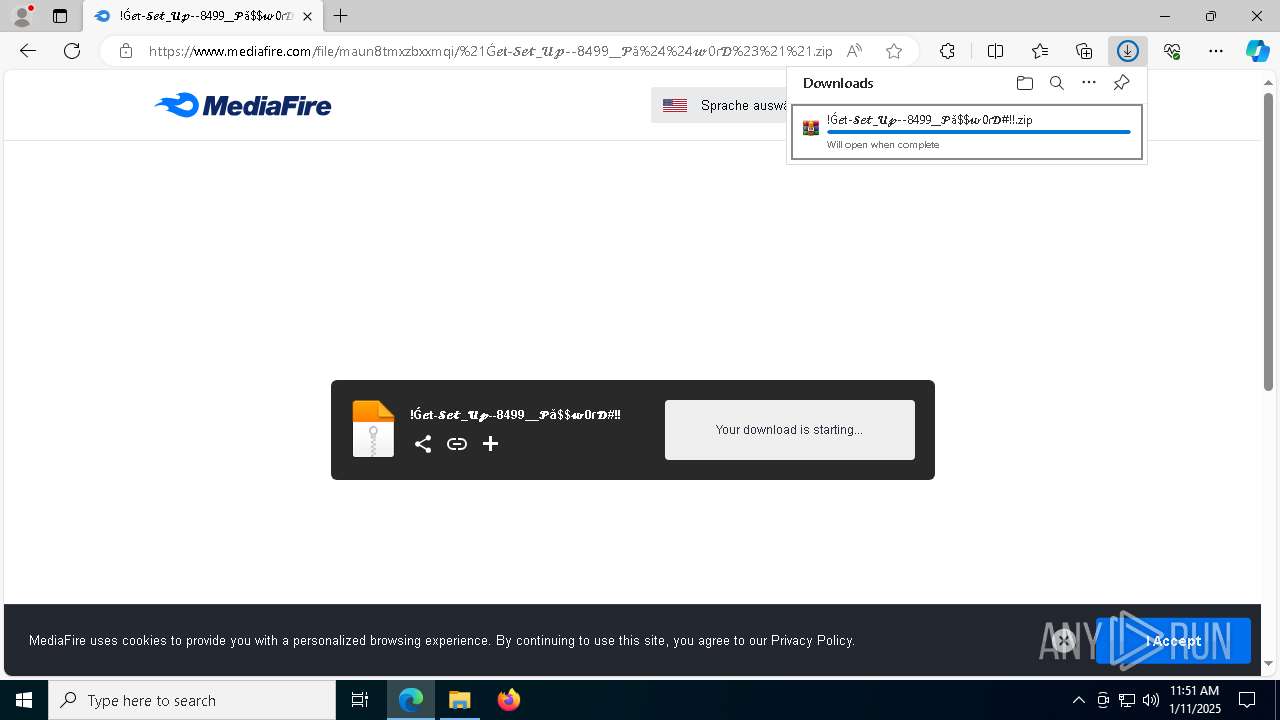
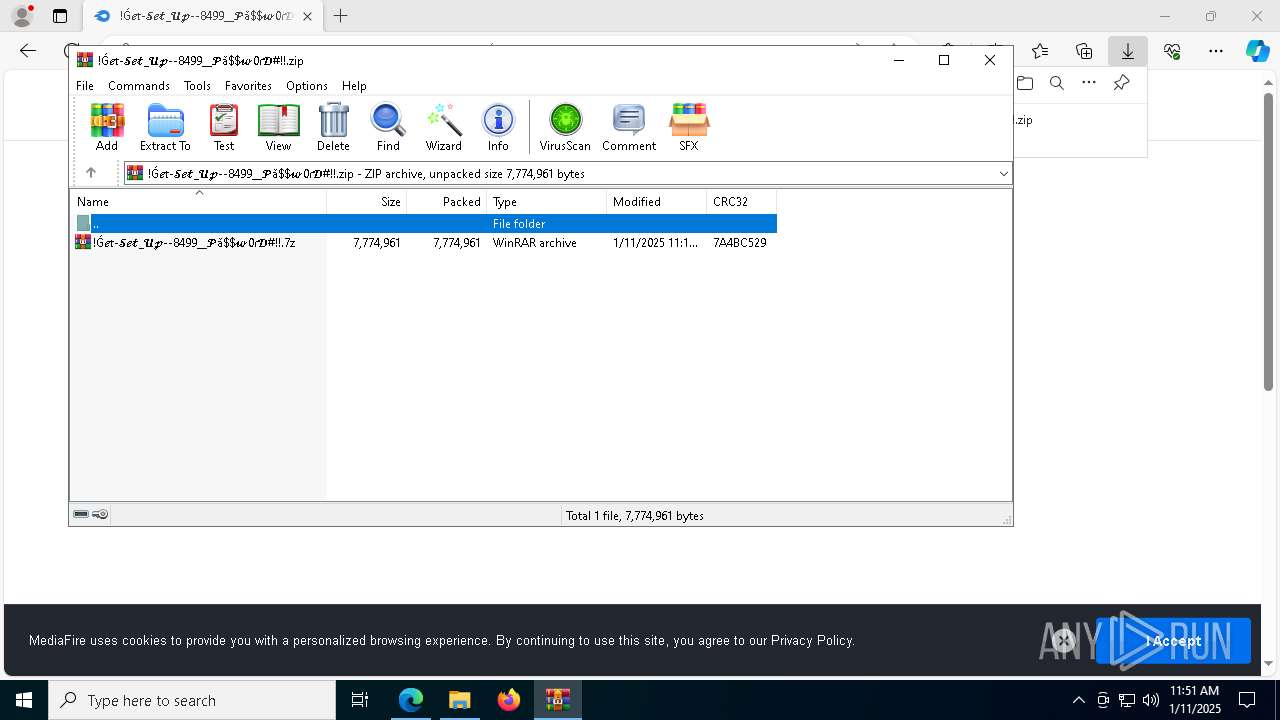
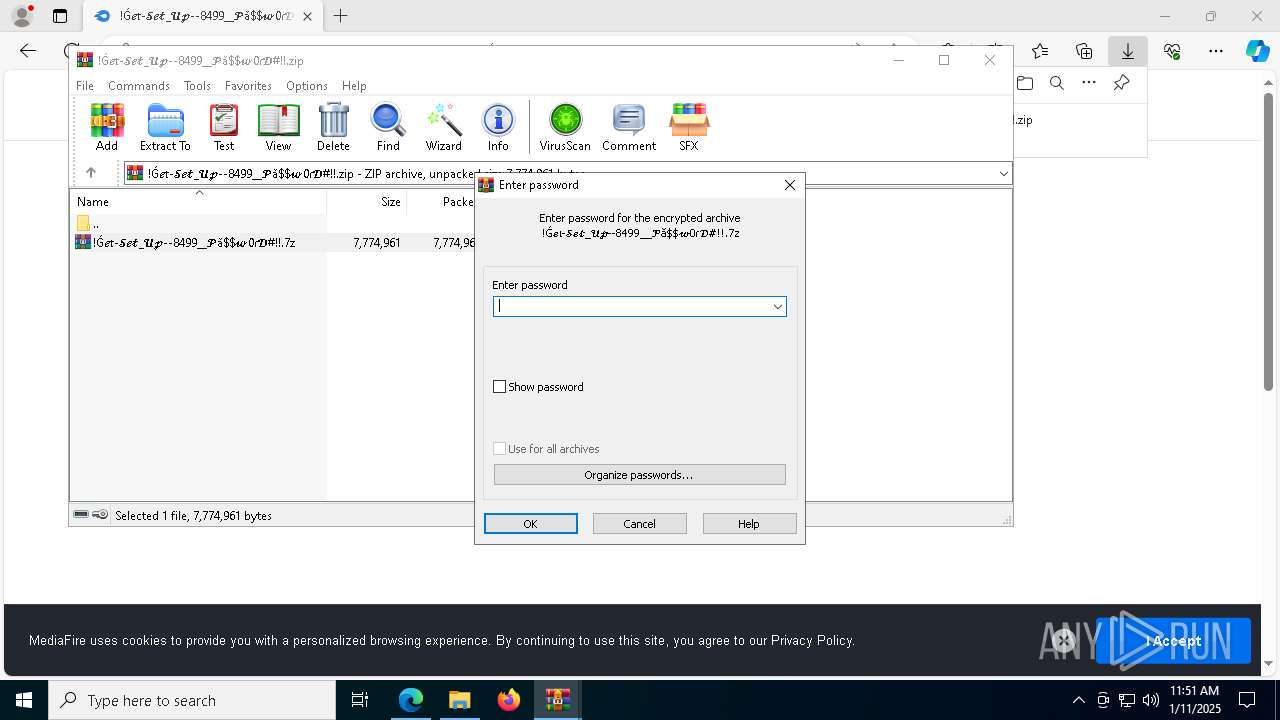
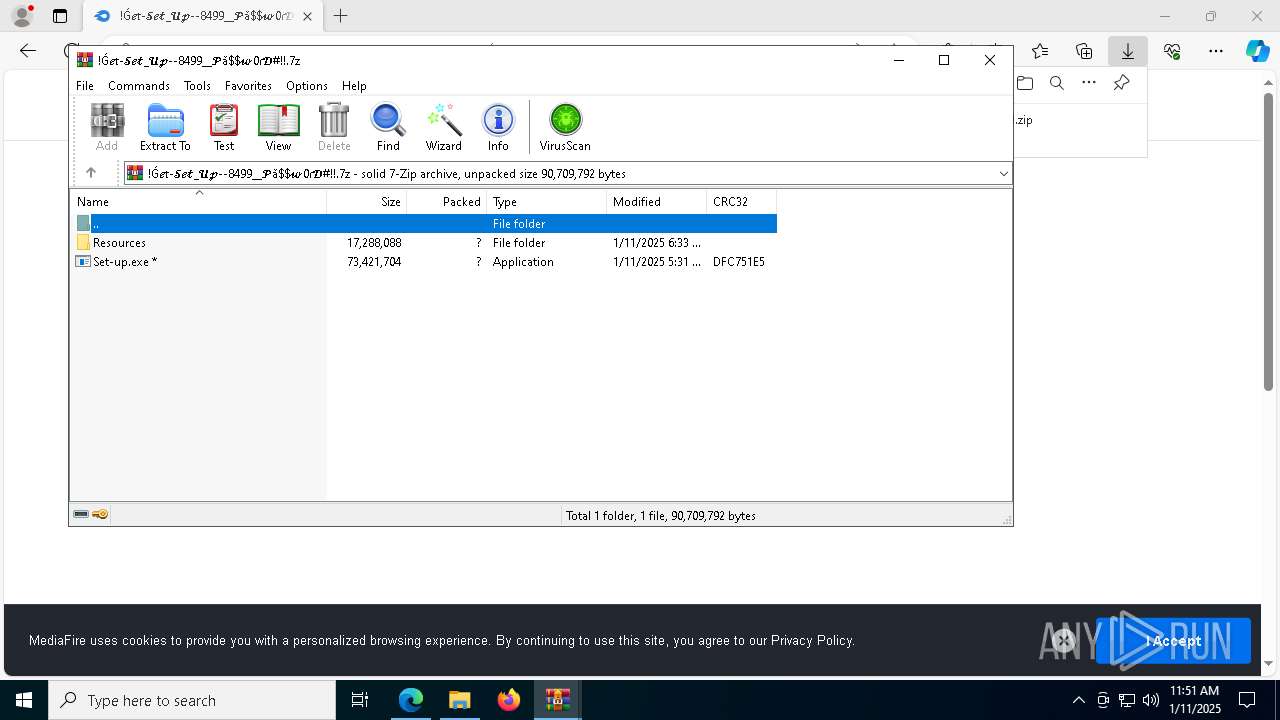
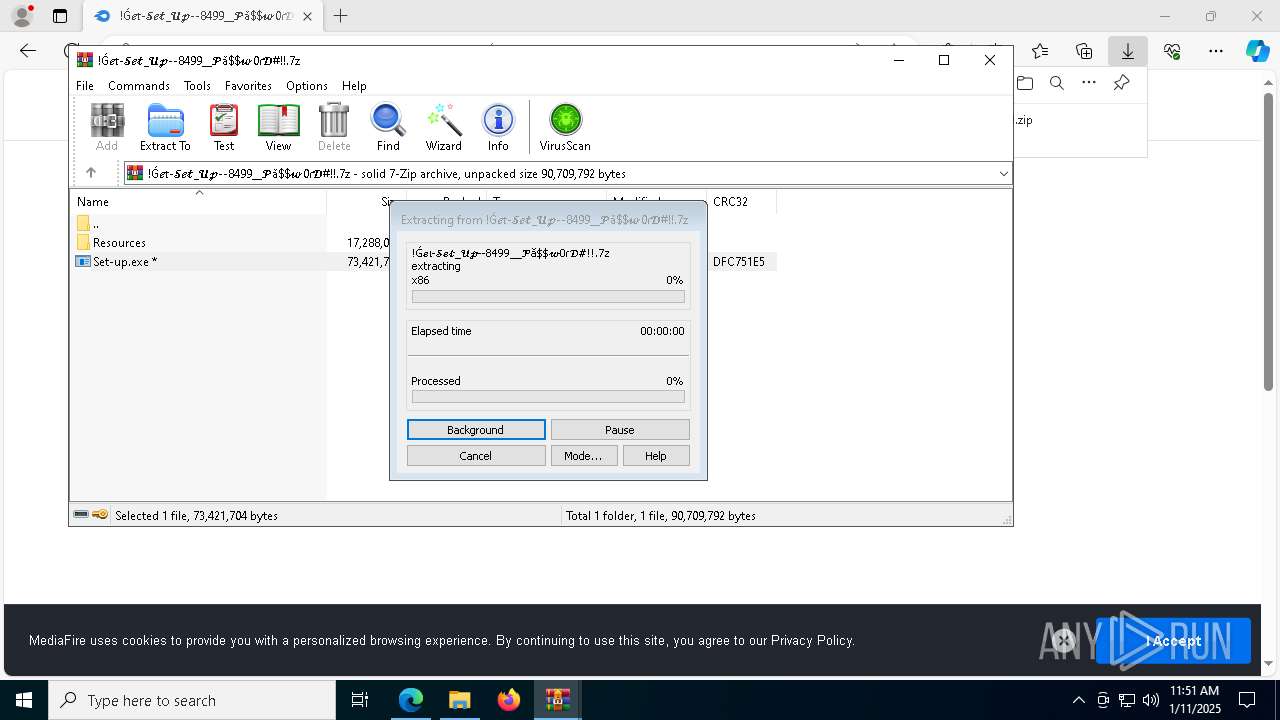
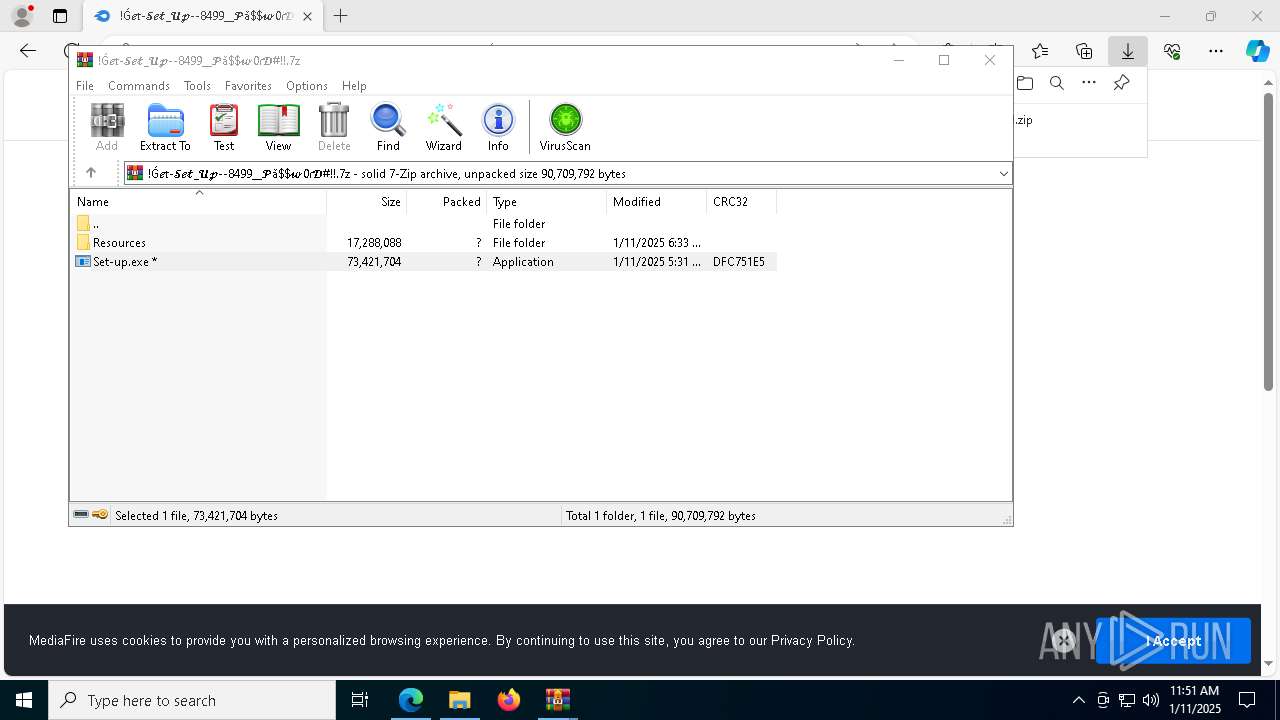
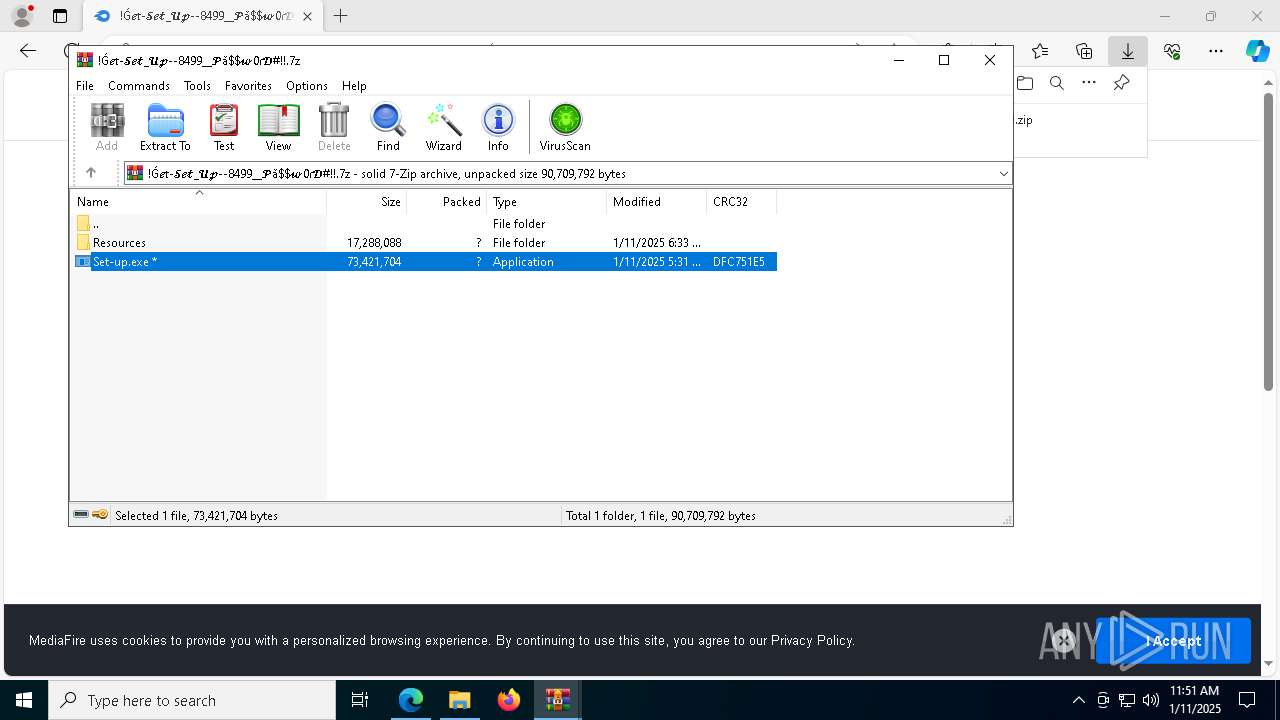
| URL: | https://www.mediafire.com/file/maun8tmxzbxxmqi/!Ǵ𝓮𝔱-𝓢𝓮𝓽_𝓤𝓹--8499__𝓟ǎ$𝔀0ɾ𝓓#!!.zip/file |
| Full analysis: | https://app.any.run/tasks/00020fde-fe5c-461b-922b-166d114b4694 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 11, 2025, 11:50:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7ED3D5B06371153235689F3646CA8CCB |
| SHA1: | 65E1A142FC52559B40039097685D09E88228929F |
| SHA256: | 0C75E77E796C64C83743AE5BEADBD86CE15A8C4465E8A61568F75AE6DA6072B1 |
| SSDEEP: | 3:N8DSLw3eGUo5edsKKUsVFoJ404/7T6cRFlBj44422GEdG9:2OLw3eGQr0Gnc/6cRhWGEdy |
MALICIOUS
Executing a file with an untrusted certificate
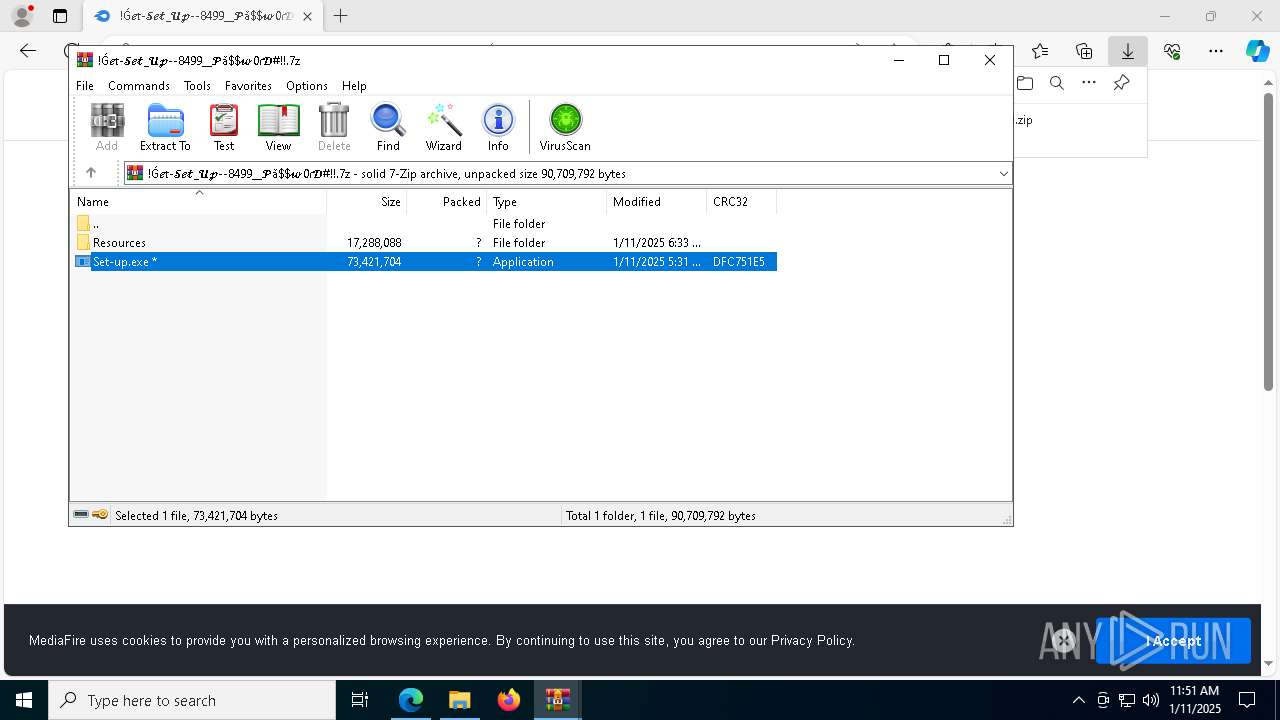
- Set-up.exe (PID: 4972)
LUMMA mutex has been found
- Token.com (PID: 2428)
Actions looks like stealing of personal data
- Token.com (PID: 2428)
Steals credentials from Web Browsers
- Token.com (PID: 2428)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5892)
- WinRAR.exe (PID: 3652)
- Set-up.exe (PID: 4972)
Application launched itself
- WinRAR.exe (PID: 5892)
- cmd.exe (PID: 1448)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3652)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3652)
Executing commands from ".cmd" file
- Set-up.exe (PID: 4972)
Starts CMD.EXE for commands execution
- Set-up.exe (PID: 4972)
- cmd.exe (PID: 1448)
Get information on the list of running processes
- cmd.exe (PID: 1448)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1448)
Starts the AutoIt3 executable file
- cmd.exe (PID: 1448)
Starts application with an unusual extension
- cmd.exe (PID: 1448)
The executable file from the user directory is run by the CMD process
- Token.com (PID: 2428)
Searches for installed software
- Token.com (PID: 2428)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 2744)
- msedge.exe (PID: 6244)
- WinRAR.exe (PID: 3652)
- msedge.exe (PID: 2928)
- WinRAR.exe (PID: 5892)
- Set-up.exe (PID: 4972)
Reads Environment values
- identity_helper.exe (PID: 4804)
Reads the computer name
- identity_helper.exe (PID: 4804)
- Set-up.exe (PID: 4972)
- extrac32.exe (PID: 2976)
- Token.com (PID: 2428)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3652)
The sample compiled with english language support
- WinRAR.exe (PID: 3652)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6244)
Checks supported languages
- identity_helper.exe (PID: 4804)
- Set-up.exe (PID: 4972)
- extrac32.exe (PID: 2976)
- Token.com (PID: 2428)
Creates files or folders in the user directory
- Set-up.exe (PID: 4972)
- extrac32.exe (PID: 2976)
Application launched itself
- msedge.exe (PID: 6244)
Process checks computer location settings
- Set-up.exe (PID: 4972)
Creates a new folder
- cmd.exe (PID: 5320)
Reads the software policy settings
- Token.com (PID: 2428)
Reads the machine GUID from the registry
- Token.com (PID: 2428)
Reads mouse settings
- Token.com (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
185
Monitored processes
59
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5116 --field-trial-handle=2396,i,362293370456008472,686111857946774239,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1448 | "C:\Windows\System32\cmd.exe" /c move Visibility Visibility.cmd & Visibility.cmd | C:\Windows\SysWOW64\cmd.exe | — | Set-up.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1888 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | findstr /V "Llp" Msgstr | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | Token.com Z | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\509038\Token.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 2572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6032 --field-trial-handle=2396,i,362293370456008472,686111857946774239,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.mediafire.com/file/maun8tmxzbxxmqi/!Ǵ𝓮𝔱-𝓢𝓮𝓽_𝓤𝓹--8499__𝓟ǎ$𝔀0ɾ𝓓#!!.zip/file" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2928 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3708 --field-trial-handle=2396,i,362293370456008472,686111857946774239,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2976 | extrac32 /Y /E Dictionary | C:\Windows\SysWOW64\extrac32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® CAB File Extract Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 474
Read events
14 423
Write events
51
Delete events
0
Modification events
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2744) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6244) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6244) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6244) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6244) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
19
Suspicious files
374
Text files
105
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135b04.TMP | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135b52.TMP | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135b33.TMP | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135b71.TMP | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135b81.TMP | — | |
MD5:— | SHA256:— | |||
| 6244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
150
DNS requests
124
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 204 | 216.58.206.46:443 | https://stats.g.doubleclick.net/g/collect?v=2&tid=G-K68XP6D85D&cid=673429614.1736596241>m=45je5190v887485693z86304663za200zb6304663&aip=1&dma=1&dma_cps=syphamo&gcd=13l3lPl2l1l1&npa=1&frm=0&tag_exp=101925629~102067555~102067808~102081485~102123608~102198178 | unknown | — | — | unknown |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
— | — | POST | 204 | 216.239.34.36:443 | https://region1.analytics.google.com/g/collect?v=2&tid=G-K68XP6D85D>m=45je5190v887485693z86304663za200zb6304663&_p=1736596238518&_gaz=1&gcd=13l3lPl2l1l1&npa=1&dma_cps=syphamo&dma=1&tag_exp=101925629~102067555~102067808~102081485~102123608~102198178&cid=673429614.1736596241&ul=en-us&sr=1280x720&uaa=x86&uab=64&uafvl=Chromium%3B122.0.6261.70%7CNot(A%253ABrand%3B24.0.0.0%7CMicrosoft%2520Edge%3B122.0.2365.59&uamb=0&uam=&uap=Windows&uapv=10.0.0&uaw=0&frm=0&pscdl=noapi&_s=1&sid=1736596240&sct=1&seg=0&dl=https%3A%2F%2Fwww.mediafire.com%2Ffile%2Fmaun8tmxzbxxmqi%2F!%C7%B4%F0%9D%93%AE%F0%9D%94%B1-%F0%9D%93%A2%F0%9D%93%AE%F0%9D%93%BD_%F0%9D%93%A4%F0%9D%93%B9--8499__%F0%9D%93%9F%C7%8E%24%F0%9D%94%800%C9%BE%F0%9D%93%93&dt=!%C7%B4%F0%9D%93%AE%F0%9D%94%B1-%F0%9D%93%A2%F0%9D%93%AE%F0%9D%93%BD_%F0%9D%93%A4%F0%9D%93%B9--8499__%F0%9D%93%9F%C7%8E%24%24%F0%9D%94%800%C9%BE%F0%9D%93%93%23!!&en=page_view&_fv=1&_nsi=1&_ss=1&up.page_url=https%3A%2F%2Fwww.mediafire.com%2Ffile%2Fmaun8tmxzbxxmqi%2F!%25C7%25B4%25F0%259D%2593%25AE%25F0%259D%2594%25B1-%25F0%259D%2593%25A2%25F0%259D%2593%25AE%25F0%259D%2593%25BD_%25F0%259D%2593%25A4%25F0%259D%2593%25B9--8499__%25F0%259D%2593%259F%25C7%258E%24%25F0%259D%2594%25800%25C9%25BE%25F0%259D%2593%2593&tfd=4527 | unknown | — | — | unknown |
— | — | GET | 200 | 13.107.21.239:443 | https://edge.microsoft.com/autofillservice/v1/pages/ChRDaHJvbWUvMTIyLjAuMjM2NS41ORIZCWOEHl3dj0hqEgUNZx3eyinovBQorxKFwA==?alt=proto | unknown | text | 20 b | whitelisted |
— | — | GET | 200 | 216.58.206.46:443 | https://www.google-analytics.com/analytics.js | unknown | binary | 51.6 Kb | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=topSite&IsStable=false | unknown | binary | 497 b | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=dafSite&IsStable=false | unknown | binary | 332 Kb | whitelisted |
— | — | POST | 200 | 52.26.98.66:443 | https://api.amplitude.com/ | unknown | text | 7 b | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=commonConfig&IsStable=false | unknown | binary | 481 b | whitelisted |
— | — | GET | 200 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/Edge/122.0.2365.59?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=44&mngd=0&installdate=1661339457&edu=0&bphint=2&soobedate=1504771245&fg=1 | unknown | binary | 768 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6244 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6476 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6476 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6476 | msedge.exe | 104.17.150.117:443 | www.mediafire.com | CLOUDFLARENET | — | shared |
6476 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6476 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.mediafire.com |
| shared |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6476 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6476 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6476 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6476 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6476 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6476 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6476 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |