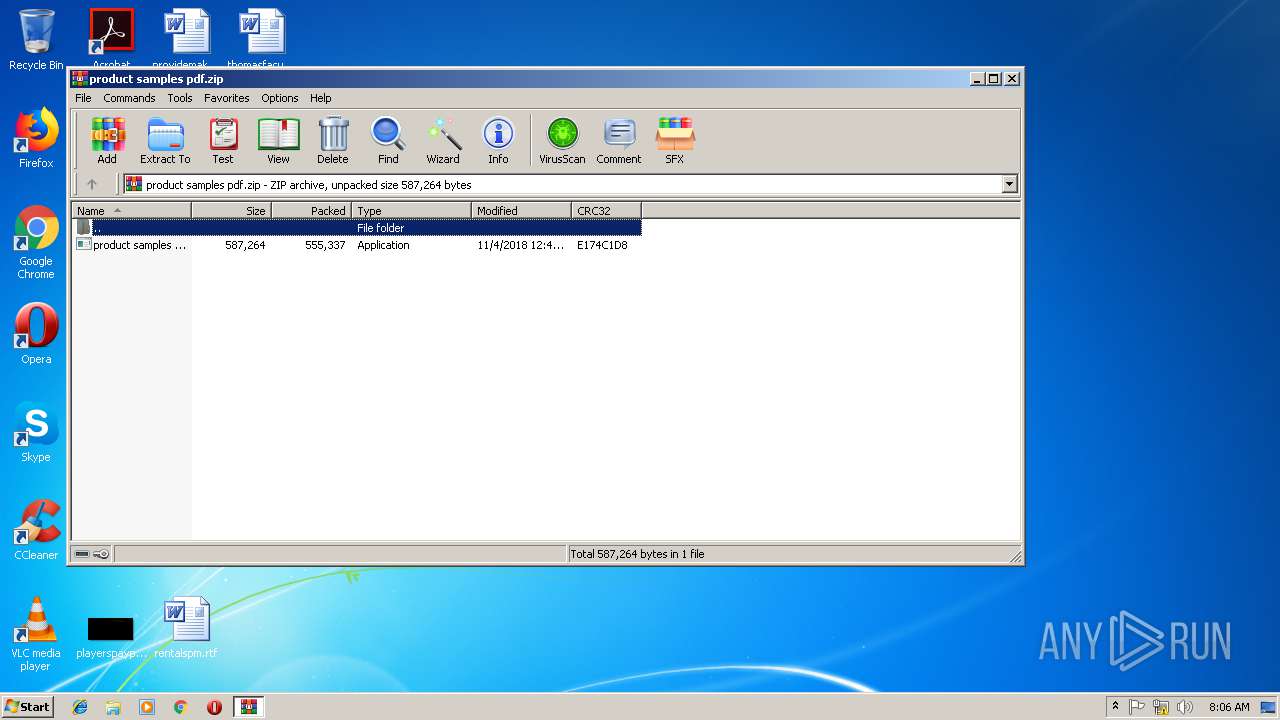
| File name: | product samples pdf.zip |
| Full analysis: | https://app.any.run/tasks/8e839f87-663d-49f6-84c5-55c451f4a1ad |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 15, 2018, 08:05:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | EFBA1B4A89830EAC4A1A31A97FC33B65 |
| SHA1: | DD7C071E1D8A5F4BF2C3D23122E082D1625434EF |
| SHA256: | 0C170B90F2AD6BD201820FA58902CF9D3B30B0D13E7D10E35908D74CB2032906 |
| SSDEEP: | 12288:eD0M6GnjjlojOkUS75WK8yavJs/wlf4VY5kyhIM8iMeQ3nx+:ew9GnjjlMU45W3yavJKjY5aiMeQ3nx+ |
MALICIOUS
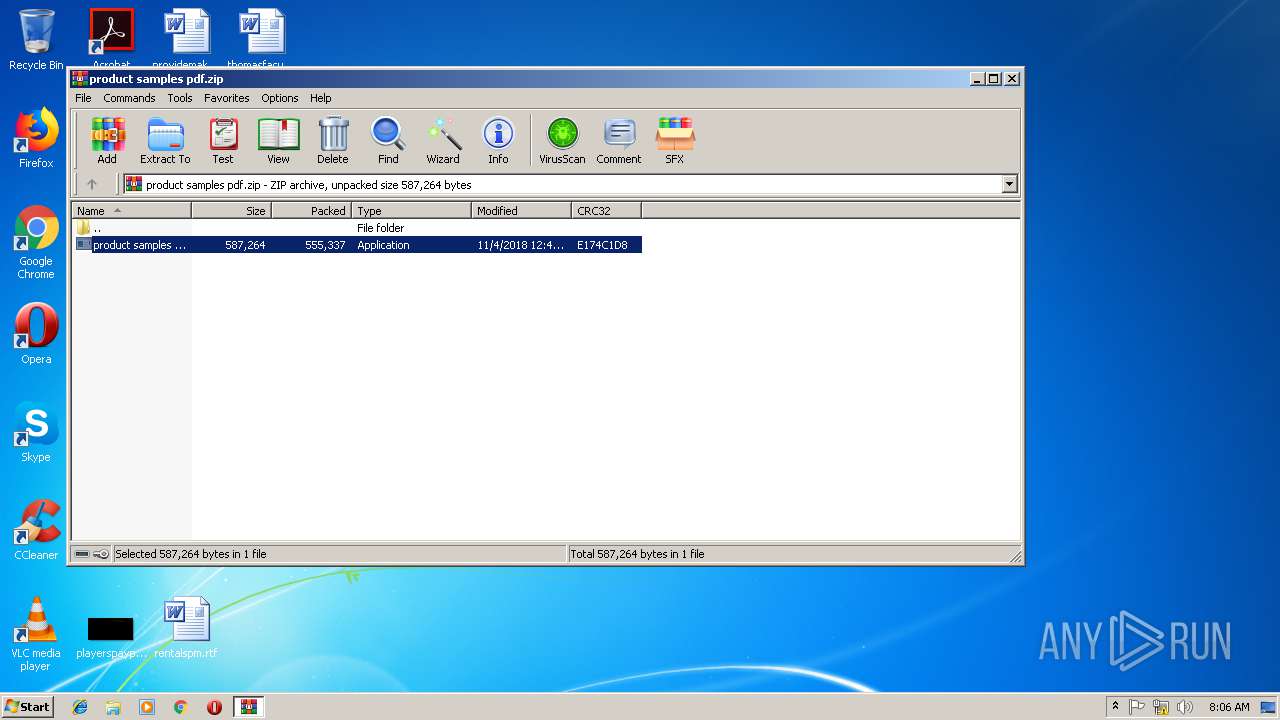
Application was dropped or rewritten from another process
- product samples pdf.exe (PID: 3412)
- frjpoz9ctjlef.exe (PID: 3740)
FORMBOOK was detected
- explorer.exe (PID: 1728)
Connects to CnC server
- explorer.exe (PID: 1728)
Changes the autorun value in the registry
- raserver.exe (PID: 1044)
Formbook was detected
- raserver.exe (PID: 1044)
- Firefox.exe (PID: 3080)
Actions looks like stealing of personal data
- raserver.exe (PID: 1044)
Uses SVCHOST.EXE for hidden code execution
- explorer.exe (PID: 1728)
Stealing of credential data
- raserver.exe (PID: 1044)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 1728)
- raserver.exe (PID: 1044)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3184)
- explorer.exe (PID: 1728)
- DllHost.exe (PID: 2844)
Reads Internet Cache Settings
- explorer.exe (PID: 1728)
Starts CMD.EXE for commands execution
- raserver.exe (PID: 1044)
Creates files in the program directory
- DllHost.exe (PID: 2844)
Loads DLL from Mozilla Firefox
- raserver.exe (PID: 1044)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 1728)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3164)
Creates files in the user directory
- WINWORD.EXE (PID: 3164)
- Firefox.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:04 12:43:17 |
| ZipCRC: | 0xe174c1d8 |
| ZipCompressedSize: | 555337 |
| ZipUncompressedSize: | 587264 |
| ZipFileName: | product samples pdf.exe |
Total processes
46
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Windows\System32\raserver.exe" | C:\Windows\System32\raserver.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Remote Assistance COM Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | raserver.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\thesevoice.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
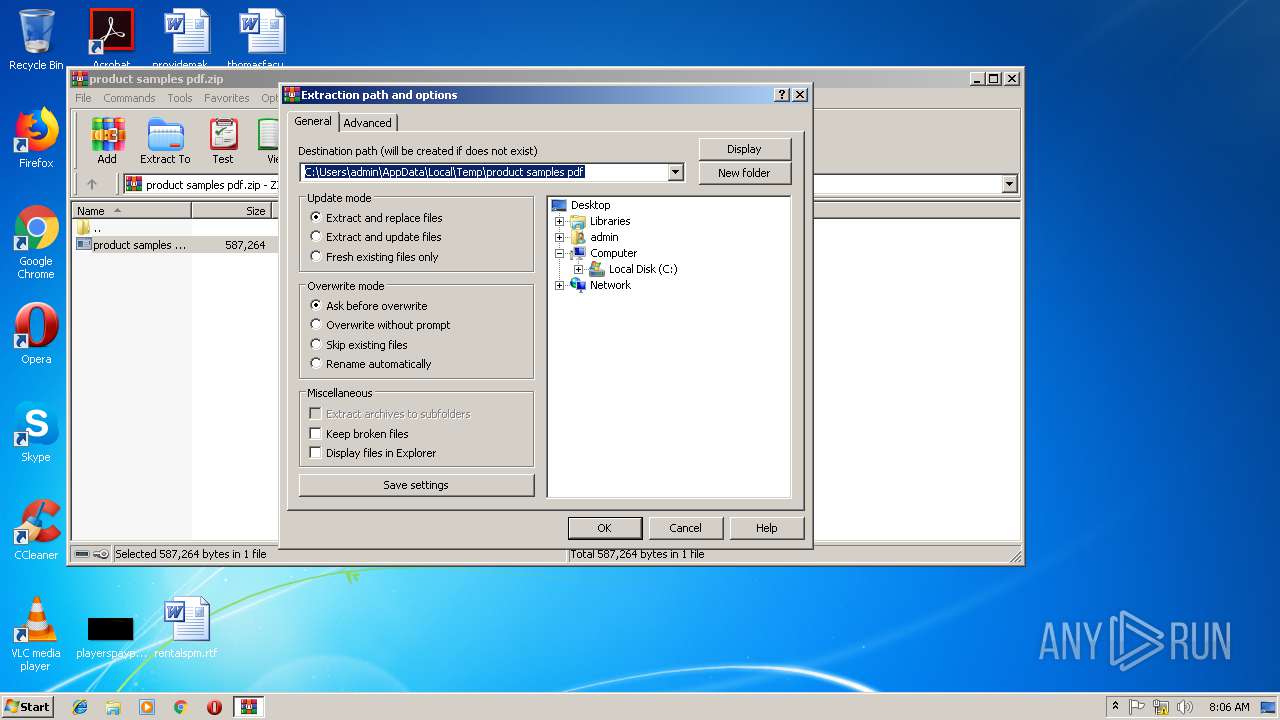
| 3184 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\product samples pdf.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3344 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\Desktop\product samples pdf.exe" | C:\Users\admin\Desktop\product samples pdf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: vidccleaner MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Zx46hzlcx\frjpoz9ctjlef.exe" | C:\Program Files\Zx46hzlcx\frjpoz9ctjlef.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: vidccleaner MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
5 193
Read events
4 770
Write events
409
Delete events
14
Modification events
| (PID) Process: | (3184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3184) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\product samples pdf.zip | |||
| (PID) Process: | (3184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1728) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (1728) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
3
Suspicious files
74
Text files
3
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9B4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3164 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{0C036E09-6622-4511-9A37-9EA931115D95}.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{77518F63-83BA-4729-9DD9-5D3D8F8890E7}.tmp | — | |
MD5:— | SHA256:— | |||
| 1728 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\a7bd71699cd38d1c.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1728 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1728 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018111520181116\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3164 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3164 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\thesevoice.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1728 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\stopending.jpg.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1728 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Zx46hzlcx\frjpoz9ctjlef.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
13
DNS requests
7
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1728 | explorer.exe | GET | 301 | 103.224.119.81:80 | http://www.pingsfarm.com/ca/?pRWtlDeX=Qe9RsRQYyVPhxLd6zT70/PwqWp+2t95AN96xFsYUgsXhdyiSlWgV16zYxUrYq5tHjqq9Cg==&4h=I20dJbTXel6Lx&sql=1 | SG | — | — | malicious |
1728 | explorer.exe | POST | 404 | 199.192.21.6:80 | http://www.daylleosin.info/ca/ | US | html | 293 b | malicious |
1728 | explorer.exe | POST | 404 | 199.192.21.6:80 | http://www.daylleosin.info/ca/ | US | html | 293 b | malicious |
1728 | explorer.exe | POST | — | 199.192.21.6:80 | http://www.daylleosin.info/ca/ | US | — | — | malicious |
1728 | explorer.exe | GET | 200 | 199.59.242.151:80 | http://www.ednconsulting.com/ca/?pRWtlDeX=zuy/pBpE11ZJeC83F1tYq4Olx3oqP71UPPx5YAeJGiwyZiDpLtjsqWQHeU7HX5DGS9eUzQ==&4h=I20dJbTXel6Lx&sql=1 | US | html | 3.84 Kb | malicious |
1728 | explorer.exe | POST | — | 199.59.242.151:80 | http://www.ednconsulting.com/ca/ | US | — | — | malicious |
1728 | explorer.exe | GET | 301 | 52.71.56.122:80 | http://www.blackmoorsociety.com/ca/?pRWtlDeX=HWEW/J+qHB1UXdpxUyp1UPiRD0Aus/XJ85i4XtkKJbjYb/mia0iAQ6rSe/3YGfWPic6bEg==&4h=I20dJbTXel6Lx | US | html | 438 b | malicious |
1728 | explorer.exe | POST | — | 199.59.242.151:80 | http://www.ednconsulting.com/ca/ | US | — | — | malicious |
1728 | explorer.exe | POST | — | 199.59.242.151:80 | http://www.ednconsulting.com/ca/ | US | — | — | malicious |
1728 | explorer.exe | POST | — | 103.224.119.81:80 | http://www.pingsfarm.com/ca/ | SG | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1728 | explorer.exe | 52.71.56.122:80 | www.blackmoorsociety.com | Amazon.com, Inc. | US | suspicious |
1728 | explorer.exe | 199.59.242.151:80 | www.ednconsulting.com | Bodis, LLC | US | malicious |
1728 | explorer.exe | 103.224.119.81:80 | www.pingsfarm.com | MyRepublic Ltd. | SG | malicious |
1728 | explorer.exe | 199.192.21.6:80 | www.daylleosin.info | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.blackmoorsociety.com |
| malicious |
www.52wjsp.com |
| unknown |
www.ednconsulting.com |
| malicious |
www.scholarshipsatm.com |
| unknown |
www.bulletcontracting.com |
| unknown |
www.pingsfarm.com |
| malicious |
www.daylleosin.info |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1728 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
1728 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1728 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
1728 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1728 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
1728 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1728 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1728 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
1728 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1728 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
10 ETPRO signatures available at the full report