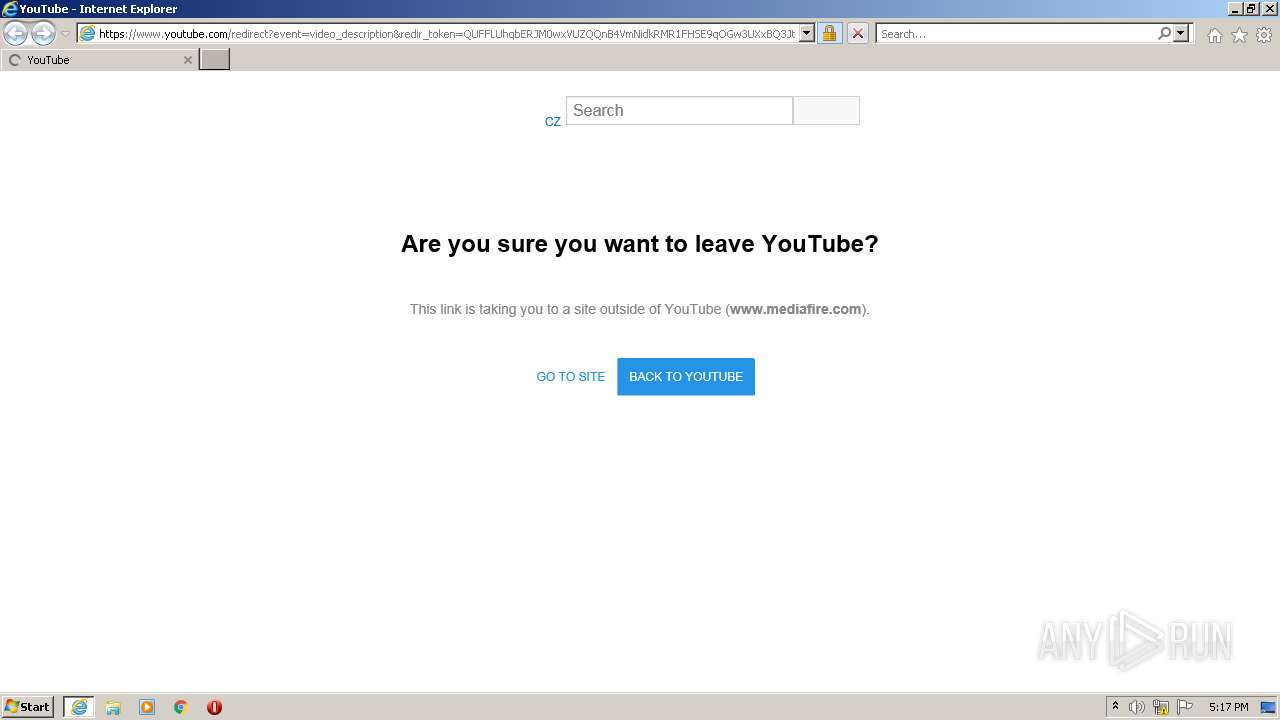
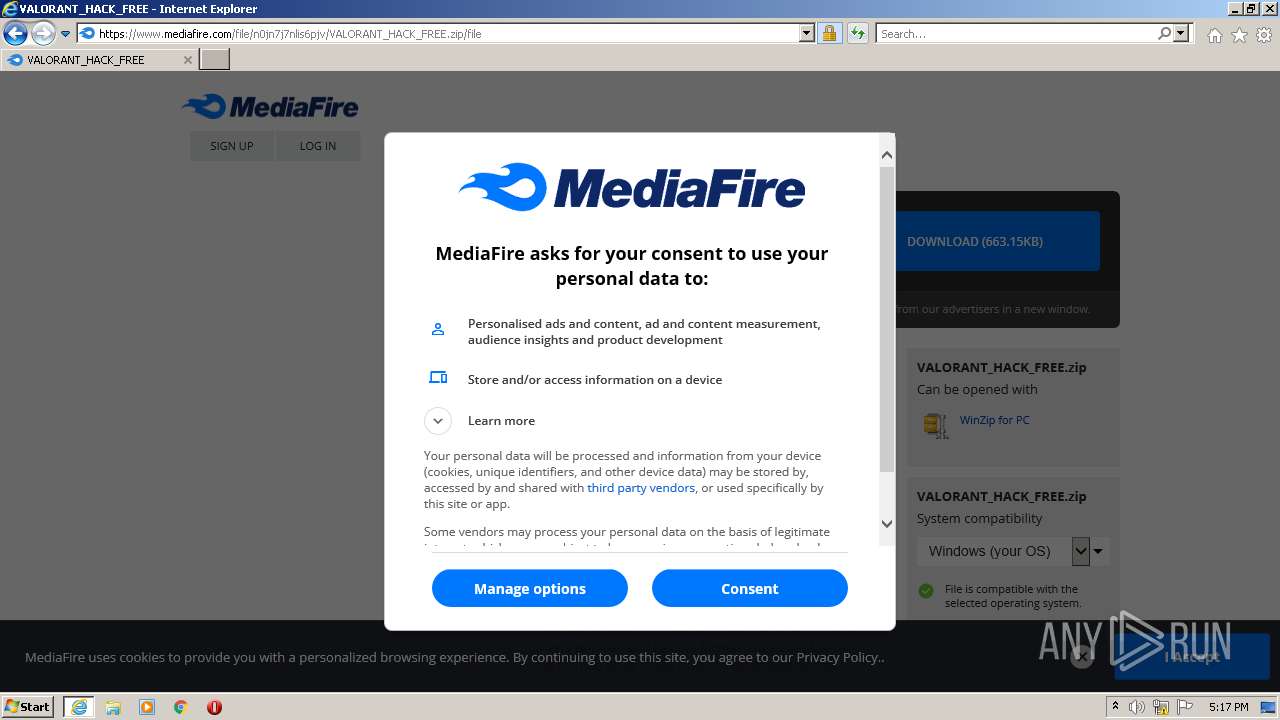
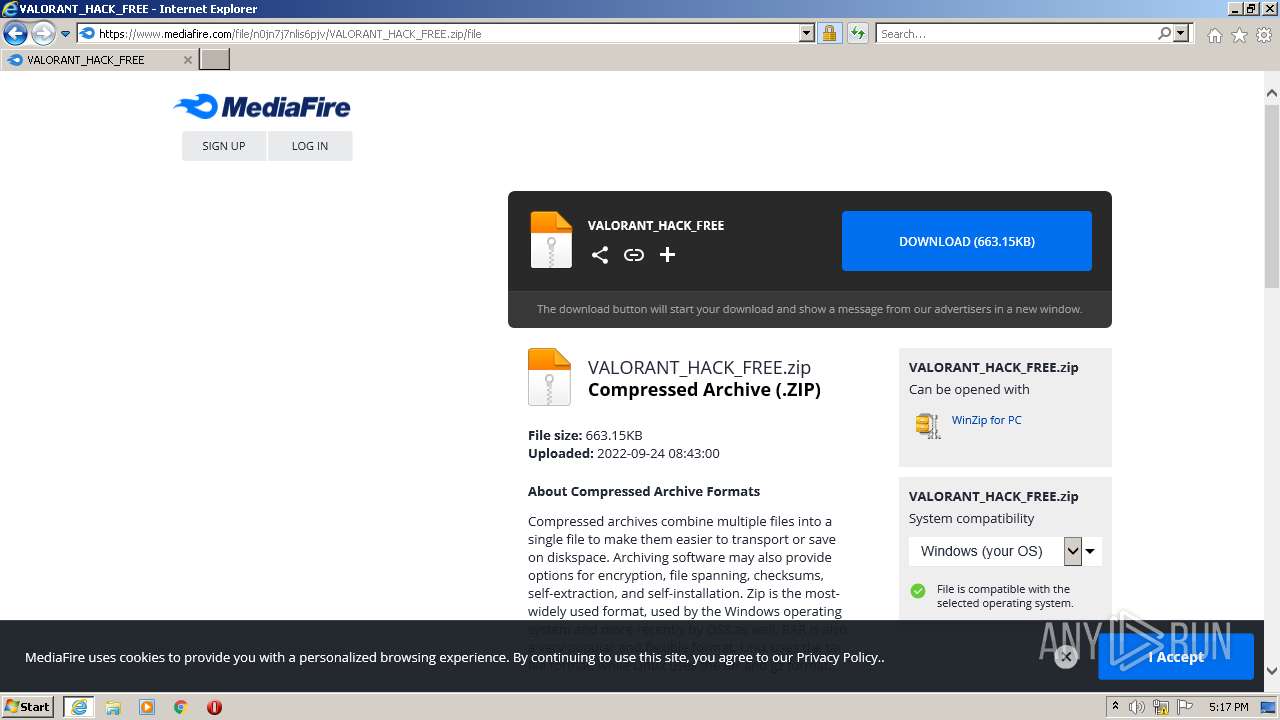
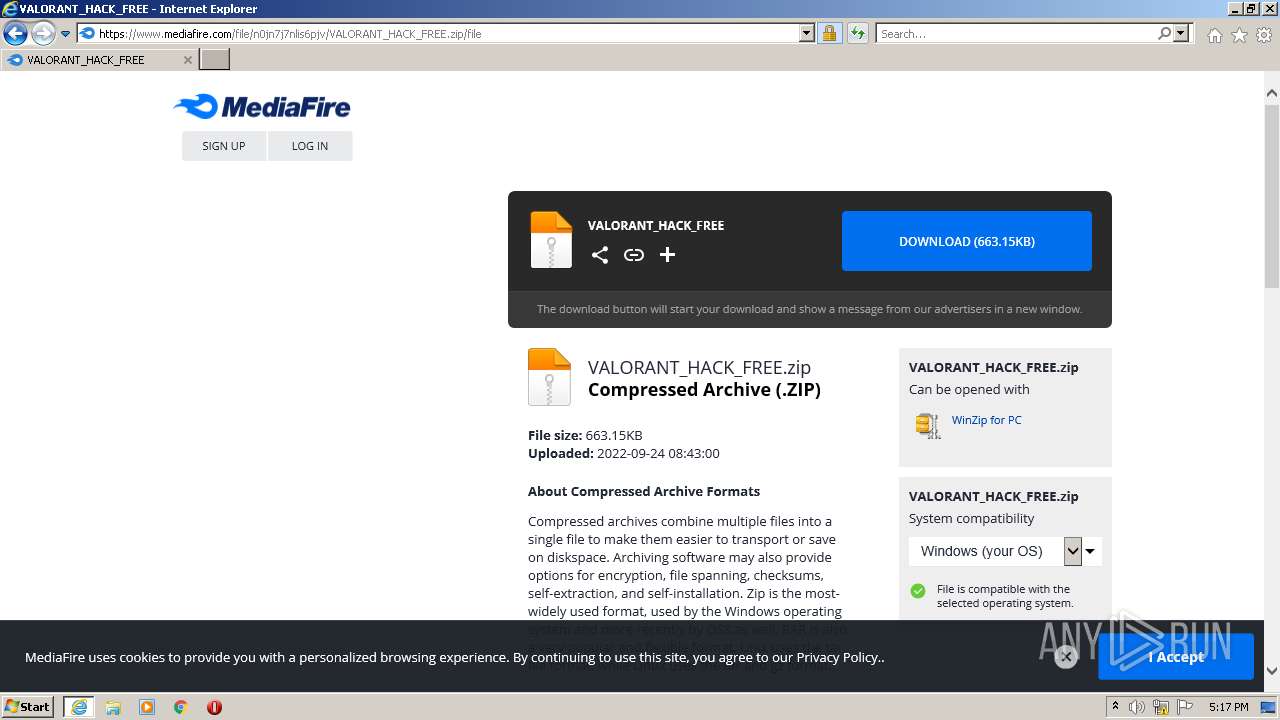
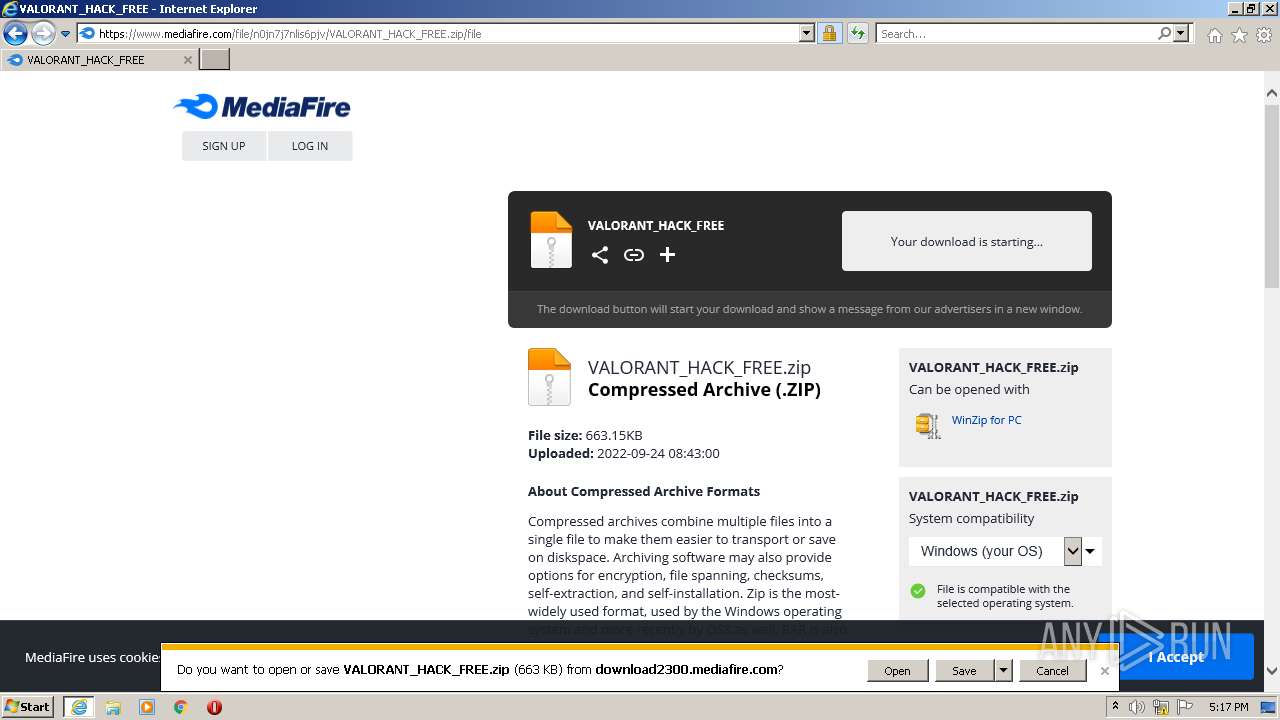
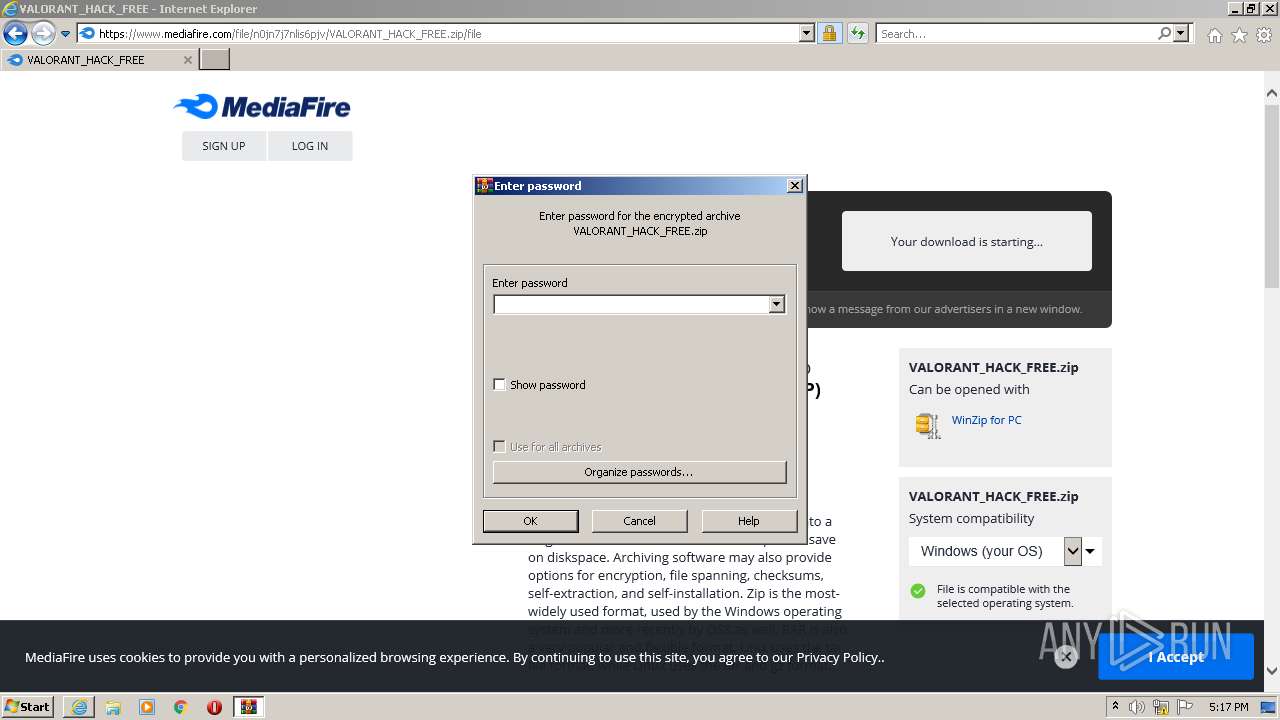
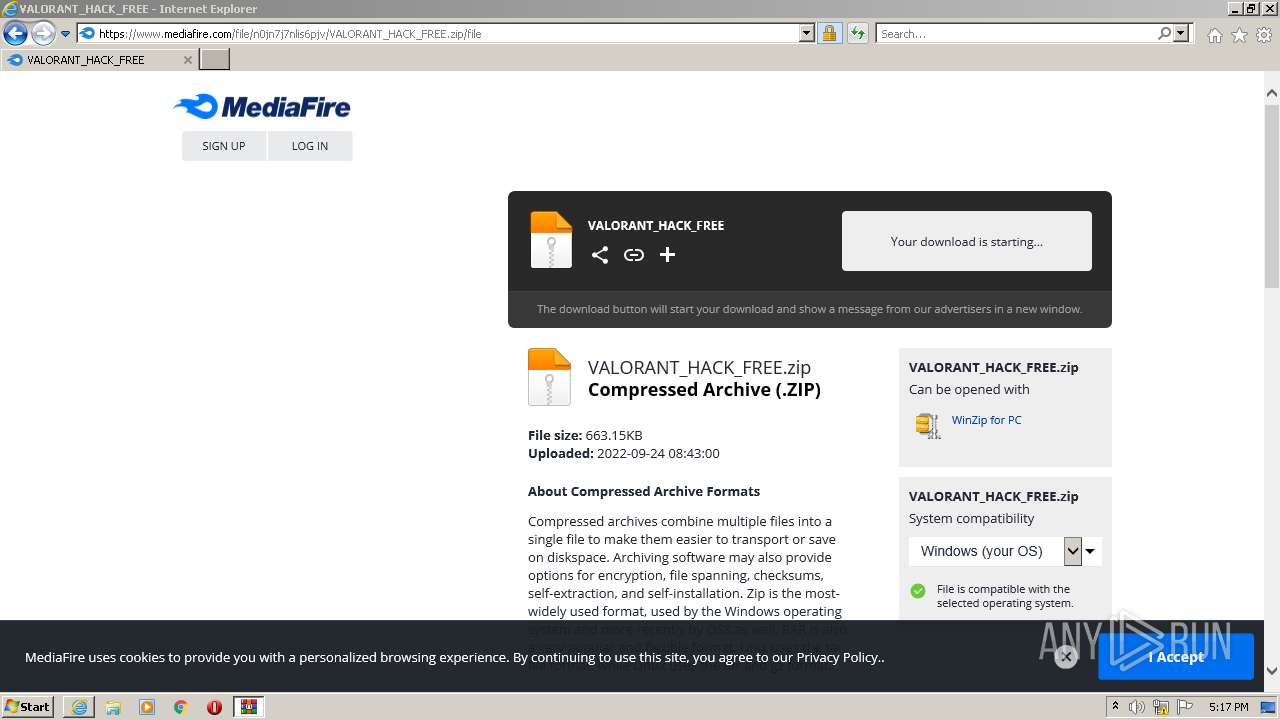
| URL: | https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqbERJM0wxVUZQQnB4VmNidkRMR1FHSE9qOGw3UXxBQ3Jtc0tsNGlvUkQ1c19jMm1acEVyYVpYaTFXdjA0QkR2X1FOa2JJTlJEamdtWWZEeFpobXEtYVpXb1VUc3pMUzBrV1hPOVVOQjROR21ZcXdTeU0zM1dWTzBmX0VIMGhUTTRGNENzOHp3NXNXUXVxWGFVblZabw&q=https%3A%2F%2Fwww.mediafire.com%2Ffile%2Fn0jn7j7nlis6pjv%2FVALORANT_HACK_FREE.zip%2Ffile&v=F9F-VuDPw3c |
| Full analysis: | https://app.any.run/tasks/0f309a86-251c-4744-8019-214a14eb6e90 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | September 24, 2022, 16:17:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C6E41F18B5CF3401896C4498AB19F531 |
| SHA1: | 3EE93819CDC1F7E0AA3261CCA18092EAAD888CE0 |
| SHA256: | 0BB3F966127A36A5E3C45485221F69CB15F6724649FF58AE3E5CC0BC70DFB31E |
| SSDEEP: | 6:2OLUxGKmKLqZAAH/rEY3UjISqCkl95c3D+gByW43Hw1kWSnlrJFII3zh3eG/l44Z:2jGRfZfrH6O56DGVdWSlr73F3ee2/03N |
MALICIOUS
REDLINE was detected
- AppLaunch.exe (PID: 99476)
REDLINE detected by memory dumps
- AppLaunch.exe (PID: 99476)
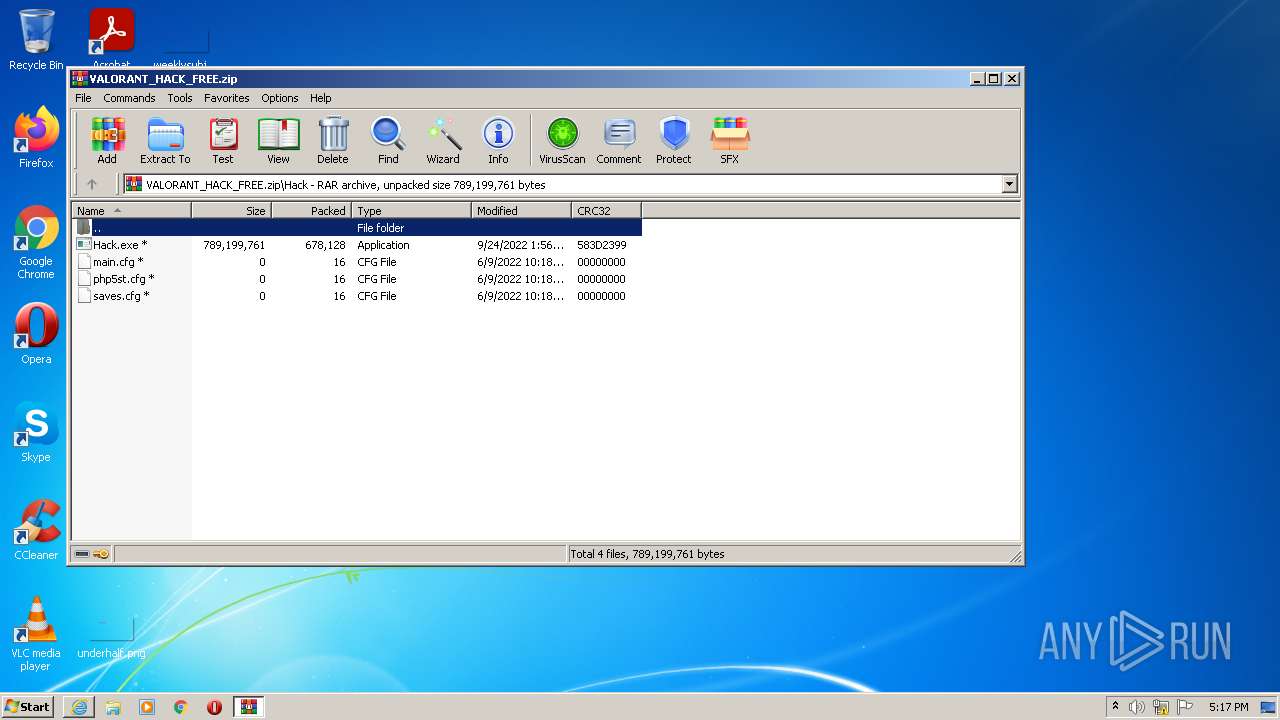
Drops executable file immediately after starts
- AppLaunch.exe (PID: 99476)
Actions looks like stealing of personal data
- AppLaunch.exe (PID: 99476)
Application was dropped or rewritten from another process
- Loader.exe (PID: 3028)
Steals credentials from Web Browsers
- AppLaunch.exe (PID: 99476)
Connects to CnC server
- AppLaunch.exe (PID: 99476)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3328)
Reads the computer name
- WinRAR.exe (PID: 416)
- AppLaunch.exe (PID: 99476)
Checks supported languages
- Hack.exe (PID: 3992)
- WinRAR.exe (PID: 416)
- AppLaunch.exe (PID: 99476)
- Loader.exe (PID: 3028)
- AppLaunch.exe (PID: 448)
Reads Environment values
- AppLaunch.exe (PID: 99476)
Reads the cookies of Google Chrome
- AppLaunch.exe (PID: 99476)
Drops a file with a compile date too recent
- AppLaunch.exe (PID: 99476)
Executable content was dropped or overwritten
- AppLaunch.exe (PID: 99476)
Reads the cookies of Mozilla Firefox
- AppLaunch.exe (PID: 99476)
Searches for installed software
- AppLaunch.exe (PID: 99476)
INFO
Reads the computer name
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 3328)
Checks supported languages
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 3328)
Reads settings of System Certificates
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 2212)
- AppLaunch.exe (PID: 99476)
Application launched itself
- iexplore.exe (PID: 2212)
Changes internet zones settings
- iexplore.exe (PID: 2212)
Changes settings of System certificates
- iexplore.exe (PID: 2212)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2212)
Creates files in the user directory
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 2212)
Reads internet explorer settings
- iexplore.exe (PID: 3328)
Checks Windows Trust Settings
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 3328)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(99476) AppLaunch.exe
C2 (1)79.137.192.47:46759
Botnet@sedpoq
Err_msg
Auth_valueaf867af6143f51bd87083316b38e5a01
US (183)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
cookies.sqlite
GetDirectories
Entity12
EnumerateDirectories
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrhKeyyptDeshKeytroyKhKeyey
hKey
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
af867af6143f51bd87083316b38e5a01
Authorization
ns1
UNKNWON
GB8fGignG1Y4BSBGGwxAXysJOVU6BQZCGTRJUg==
@sedpoq
Vetoes
Yandex\YaAddon
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
.
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
1
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
Name
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
System.Text.RegularExpressions
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
The entered value cannot be less than 1 or greater than 20.
#F25D59
Segoe UI
#FFFFFF
#323A3D
Tahoma
#696969
#A0A0A0
−
Marlett
2
#C75050
⨉
#72767F
#FAFAFA
#DE5954
#F46662
#F68F84
#292C3D
#3C3F50
#747881
#2B3043
#7F838C
#AAABB0
Microsoft Sans Serif
Total processes
45
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
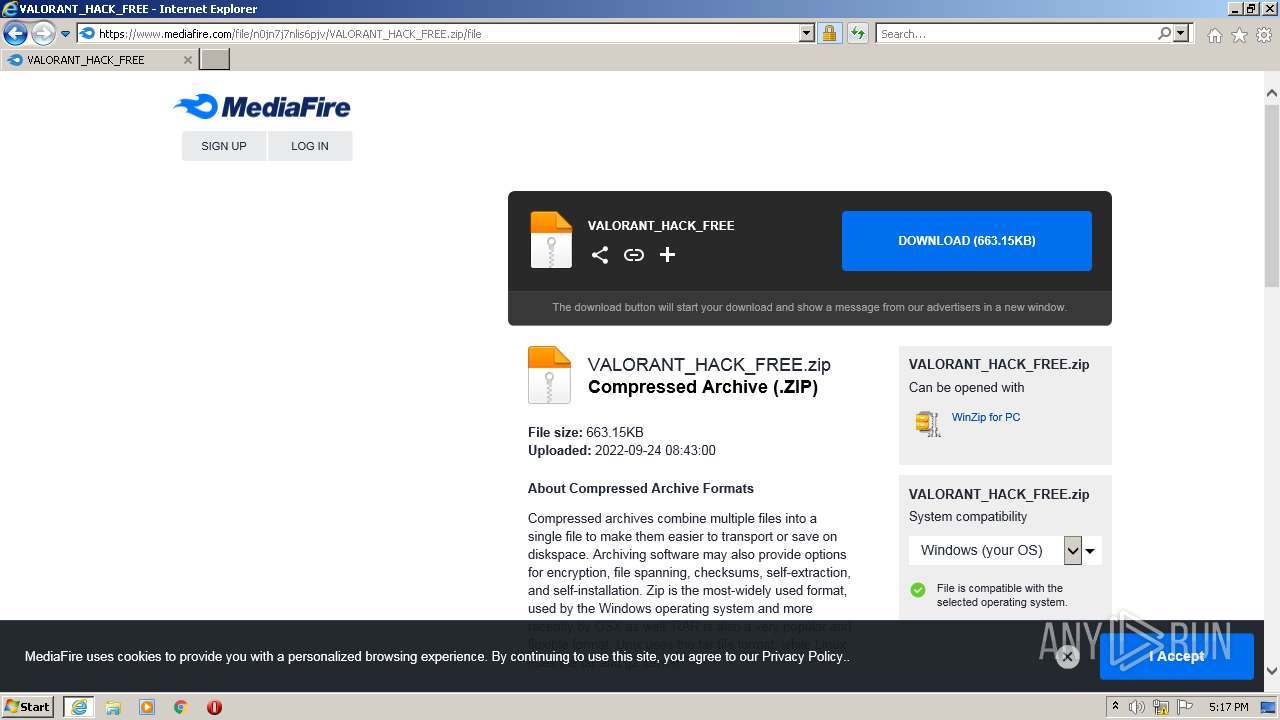
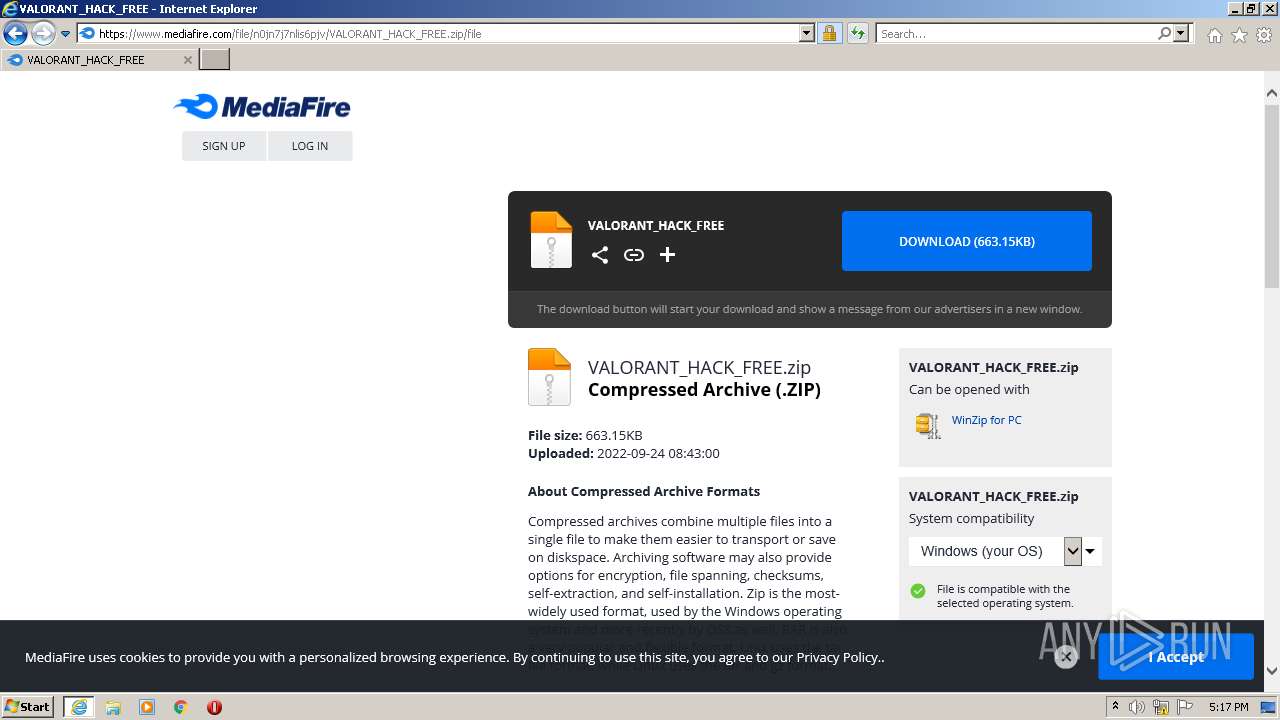
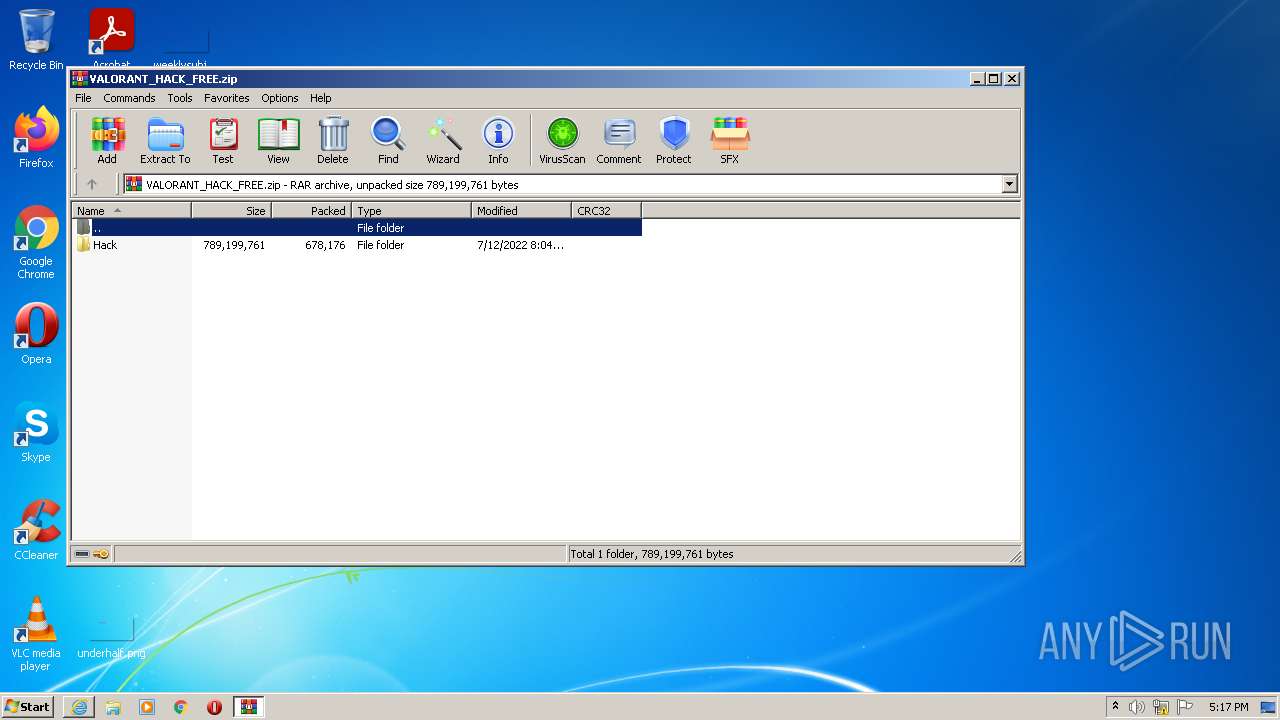
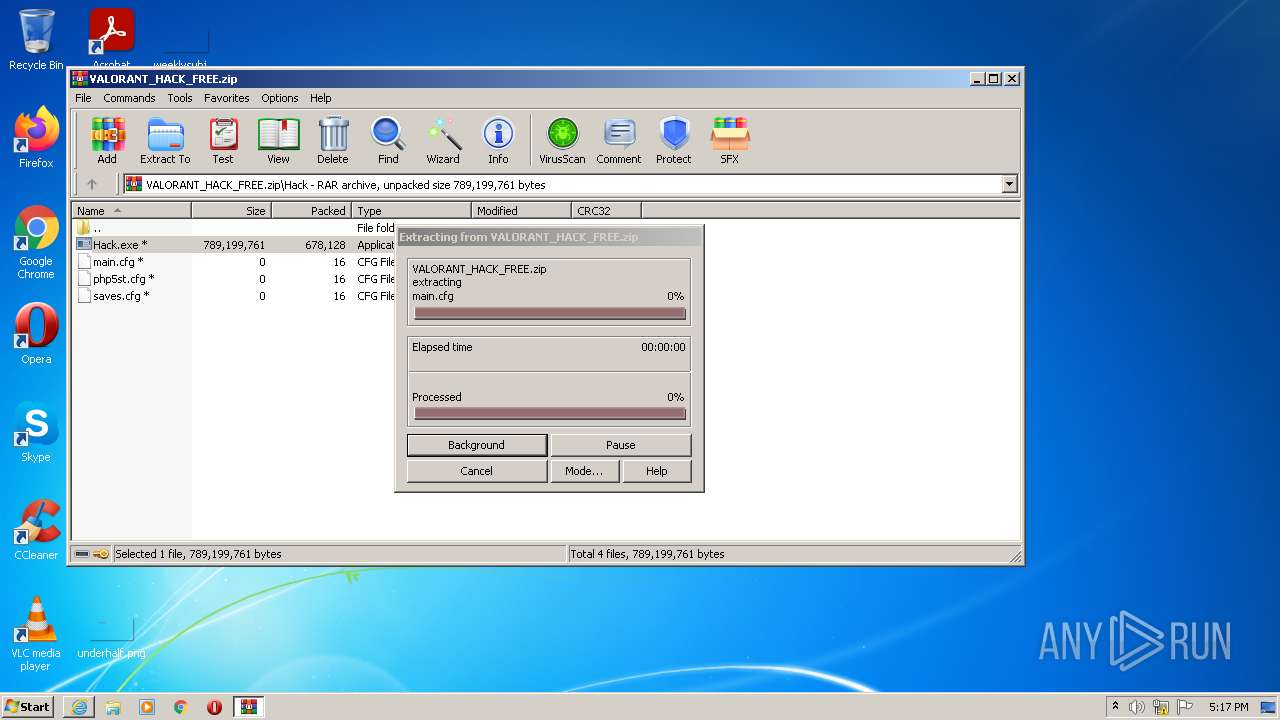
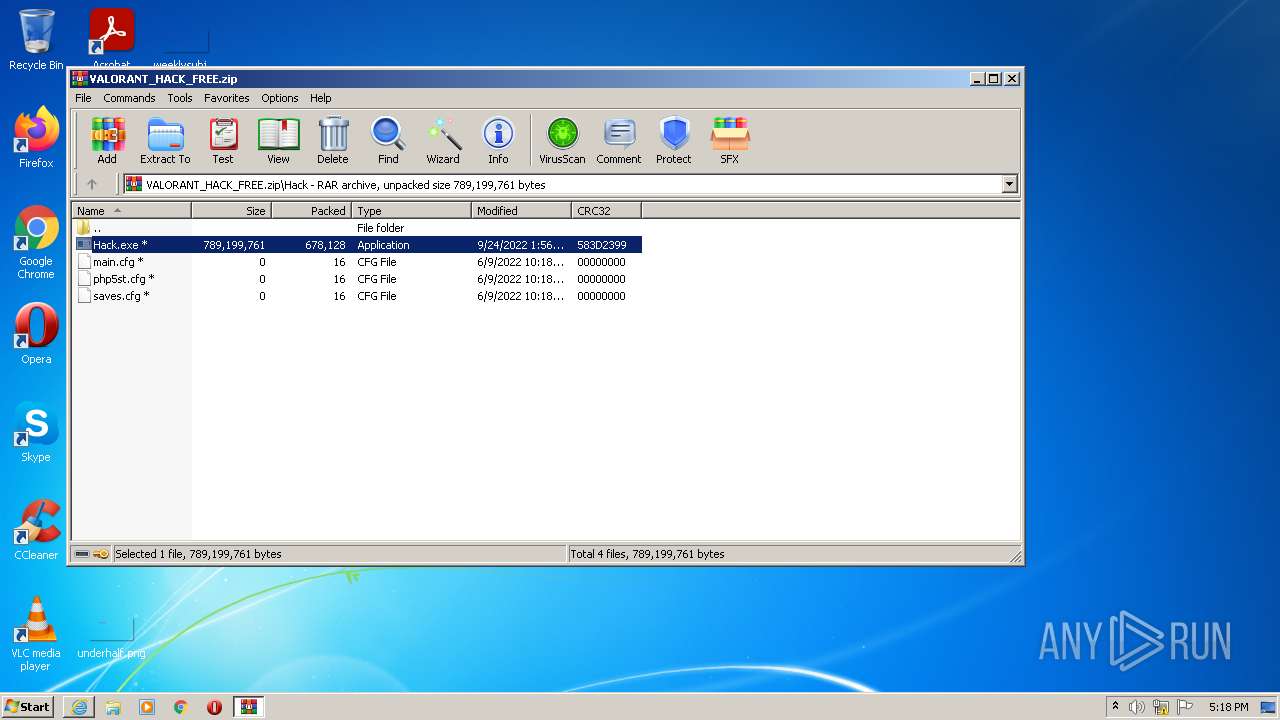
| 416 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\VALORANT_HACK_FREE.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 448 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET ClickOnce Launch Utility Exit code: 41 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqbERJM0wxVUZQQnB4VmNidkRMR1FHSE9qOGw3UXxBQ3Jtc0tsNGlvUkQ1c19jMm1acEVyYVpYaTFXdjA0QkR2X1FOa2JJTlJEamdtWWZEeFpobXEtYVpXb1VUc3pMUzBrV1hPOVVOQjROR21ZcXdTeU0zM1dWTzBmX0VIMGhUTTRGNENzOHp3NXNXUXVxWGFVblZabw&q=https%3A%2F%2Fwww.mediafire.com%2Ffile%2Fn0jn7j7nlis6pjv%2FVALORANT_HACK_FREE.zip%2Ffile&v=F9F-VuDPw3c" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\AppData\Local\Temp\Loader.exe" | C:\Users\admin\AppData\Local\Temp\Loader.exe | — | AppLaunch.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3328 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2212 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb416.43129\Hack\Hack.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb416.43129\Hack\Hack.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 99476 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe | Hack.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET ClickOnce Launch Utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
RedLine(PID) Process(99476) AppLaunch.exe C2 (1)79.137.192.47:46759 Botnet@sedpoq Err_msg Auth_valueaf867af6143f51bd87083316b38e5a01 US (183) LEnvironmentogiEnvironmentn DatEnvironmenta Environment WSystem.Texteb DatSystem.Texta System.Text CoCryptographyokieCryptographys Cryptography ExtGenericension CooGenerickies Generic OFileInfopeFileInfora GFileInfoX StabFileInfole FileInfo OpLinqera GLinqX Linq ApGenericpDaGenericta\RGenericoamiGenericng\ Network Extension UNKNOWN cFileStreamredFileStreamit_cFileStreamardFileStreams FileStream \ Network\ Host Port : User Pass cookies.sqlite GetDirectories Entity12 EnumerateDirectories String.Replace String.Remove bcrFileStream.IOypt.dFileStream.IOll FileStream.IO BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder string.Empty BCruintyptCloseAlgorituinthmProvuintider uint BCrUnmanagedTypeyptDecrUnmanagedTypeypt UnmanagedType BCrhKeyyptDeshKeytroyKhKeyey hKey BCpszPropertyryptGepszPropertytPropepszPropertyrty pszProperty BCEncodingryptSEncodingetPrEncodingoperEncodingty Encoding BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey bMasterKey windows-1251 AES Microsoft Primitive Provider ChainingModeGCM AuthTagLength ChainingMode ObjectLength KeyDataBlob - {0} net.tcp:// / localhost af867af6143f51bd87083316b38e5a01 Authorization ns1 UNKNWON GB8fGignG1Y4BSBGGwxAXysJOVU6BQZCGTRJUg== @sedpoq Vetoes Yandex\YaAddon asf *wallet* ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu... _ T e l gr am . ex \TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata 1 String Replace string.Replace %USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng File.Write Handler npvo* %USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl serviceInterface.Extension ProldCharotonVoldCharPN oldChar nSystem.CollectionspvoSystem.Collections* System.Collections ( UNIQUE cstringmstringd string /ProcessC Process Process | " Armenia Azerbaijan Belarus Kazakhstan Kyrgyzstan Moldova Tajikistan Uzbekistan Ukraine Russia https://api.ip.sb/ip 80 81 0.0.0.0 SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor System.Windows.Forms roSystem.Linqot\CISystem.LinqMV2 System.Linq SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller AdapterRAM Name SOFTWARE\WOW6432Node\Clients\StartMenuInternet SOFTWARE\Clients\StartMenuInternet shell\open\command Unknown Version SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente System.Management SerialNumber SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId=' System.Text.RegularExpressions ' FileSystem SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId=' System. ExecutablePath [ ] Concat0 MConcatb oConcatr Concat0 Concat SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem Memory {0}{1}{2} x32 x64 x86 SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CSDVersion Unknown _[ The entered value cannot be less than 1 or greater than 20. #F25D59 Segoe UI #FFFFFF #323A3D Tahoma #696969 #A0A0A0 − Marlett 2 #C75050 ⨉ #72767F #FAFAFA #DE5954 #F46662 #F68F84 #292C3D #3C3F50 #747881 #2B3043 #7F838C #AAABB0 Microsoft Sans Serif | |||||||||||||||
Total events
29 450
Read events
29 228
Write events
216
Delete events
6
Modification events
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 534785456 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30986289 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 834791706 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30986289 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2212) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
38
Text files
80
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_58589533BD741CABD9C6A1C2A7AAD4A1 | binary | |
MD5:568A0C92489C6B68932CEC73CB395114 | SHA256:4DCEF410F48E3015DE0EE224AF070A27CF4B0865FC7ACB162EE0BCEF4D0D9657 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:D0A17B670FADFD25DFD5D408405036C2 | SHA256:03FB29F18F68916465D7ACC76AB447819A9DE0A19F409F56D7B8C15CD1EEDE8B | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:5A11C6099B9E5808DFB08C5C9570C92F | SHA256:91291A5EDC4E10A225D3C23265D236ECC74473D9893BE5BD07E202D95B3FB172 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:3566F206E7A69C4615109E777DFF8F71 | SHA256:FB98C7D692A2CB04EFC73D7ECF9FF135A95527C052B7A54B5BD5C025A63AA757 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:0BCEBF949F50E2A7B284CB73B3889F24 | SHA256:BCDB1DCB252F704F7BFA816BD853D188244B6E3F903695D0F2A8AB0E2F42E292 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:E6FB9BAE0145FF7E879200DB14D4B51A | SHA256:977AE9D4D37CD8D629ADAFE4FFB73CCE3C0A2F148840F4DC08B5CB5482AFBF31 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_58589533BD741CABD9C6A1C2A7AAD4A1 | der | |
MD5:267300D587831DDA7559C30C40CC614E | SHA256:EC7AAD1A3116CE8EF5258B49DE87CF3456C8C4890206FA5D46C8E510DED80AC0 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\W6N2G3Z7.txt | text | |
MD5:81181367C8BF511BF123F80890A854C4 | SHA256:C211386C0181491B10766E77502FE571C122453E2EA52F2E31B1FB763AA156A9 | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\redirect[1].htm | html | |
MD5:F9D2E8F83C5E7D81B1E7CF4A786C201D | SHA256:43A8CE21939D6C7CF9C7A93CEBC603538B46C312D26DF422C1B90F27304A41FA | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E87CE99F124623F95572A696C80EFCAF_C52D0FE039A194FC3D7228557EE245E4 | der | |
MD5:DA681C2F112645651E5B32BE2CFCD052 | SHA256:302A7E1F8156051B7C793C61FBE3E81096374431E22BD9821B4AA38E1A5772F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
91
DNS requests
44
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3328 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEATCLupKMpUqEkLyWKtiuhk%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 65.9.58.56:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3328 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZEPRooQAkERIg4ut3zUOO | US | der | 472 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 99.86.1.91:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3328 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6eafe87802a5f092 | US | compressed | 4.70 Kb | whitelisted |
3328 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgGdnH2Si4qwpWql%2FWXvMR | US | der | 472 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDW1tEXOcnucS9%2F2dFgvl%2By | US | der | 472 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ad3a8252b74bf600 | US | compressed | 4.70 Kb | whitelisted |
3328 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 2.18 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3328 | iexplore.exe | 142.250.186.174:443 | www.youtube.com | GOOGLE | US | whitelisted |
3328 | iexplore.exe | 142.250.185.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3328 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2212 | iexplore.exe | 142.250.186.174:443 | www.youtube.com | GOOGLE | US | whitelisted |
3328 | iexplore.exe | 172.217.23.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3328 | iexplore.exe | 172.64.155.188:80 | ocsp.usertrust.com | CLOUDFLARENET | US | suspicious |
3328 | iexplore.exe | 104.16.54.48:443 | www.mediafire.com | CLOUDFLARENET | — | suspicious |
3328 | iexplore.exe | 104.18.32.68:80 | ocsp.usertrust.com | CLOUDFLARENET | — | suspicious |
3328 | iexplore.exe | 142.250.185.174:443 | www.youtube.com | GOOGLE | US | whitelisted |
3328 | iexplore.exe | 142.250.185.200:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.mediafire.com |
| shared |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
26 ETPRO signatures available at the full report