| URL: | http://url4267.joincarma.com/ls/click?upn=u001.XT7M8389kHn5ypgXbdGEbA6-2FzdDv6E7L-2BXez5evFvRz202RE1upVKrOpH-2FYlprhJjUXb2vqgMegViRKkQvj9am8Gt4aIjqeWGX5hiO-2BR8IkqjdRZvGJvd8lI9yKby8ZehlAjoPN5bsEBg95BhFaTBmvJLGivhYXTapZMreTCybqgRQF-2BRA06UCWhxOPEyG7VnUZ6kHwYXok6BDtDSvzmUcDvkEqC1nP-2Fh83iI3Ua7jkp4BRb1PK2rrchf477KmqJNuocXrOlyWehwWWl-2F9FxQ-2BFbSSuXE2-2BrJK0AlHYJvtMslhYOPDdXdE1Vjgx-2BcDNuKE0sRtDoBRL1p6ZZYeI9qwsG3qUCMG6YUROVU5VdI4L97Io7Ng-2Bb050ioYKDKS67Ils7I8aTCThdl7y7FF3SYPDtj72Zo6JI1DcpTD9Qpptmm5nIPei5roMJF8GM5boy-2BkegMV49o9zvpe9gdWHVBH-2Bky8HfbjFY5HSPnpXqKOT6sppDGQ01Gucn-2FqNI5Im-2F-2F5AXsf2wibnvBBrFJBX96DSVY8LdUl5bncNvvTNexgM-3DC8hG_MjAhclRA0hH-2F1a1m8v8T4rJi-2BScc6AlQzsSSGVOBAwwtWN8L2P-2FngD-2Bz-2B9FEA4k9ZFamqMG0WnZ0pk0alMsZZ1rgTkzxVLJYQAgg2ppOO7C-2BVP-2FgiMdRz-2Fc8XDI-2FchGcoJKdXjhTei-2B3ussVDh-2F15gJwjdQNQRvI12w8396hooCgQjVlvRRaTtQbwC5j-2BN9BYwf0Dmk8vpWM6mkcCDSEWvc-2BcIR-2F3OVOcr7-2B7hb262c-3D |
| Full analysis: | https://app.any.run/tasks/2f0270cc-e989-4b9d-824b-4a0941085280 |
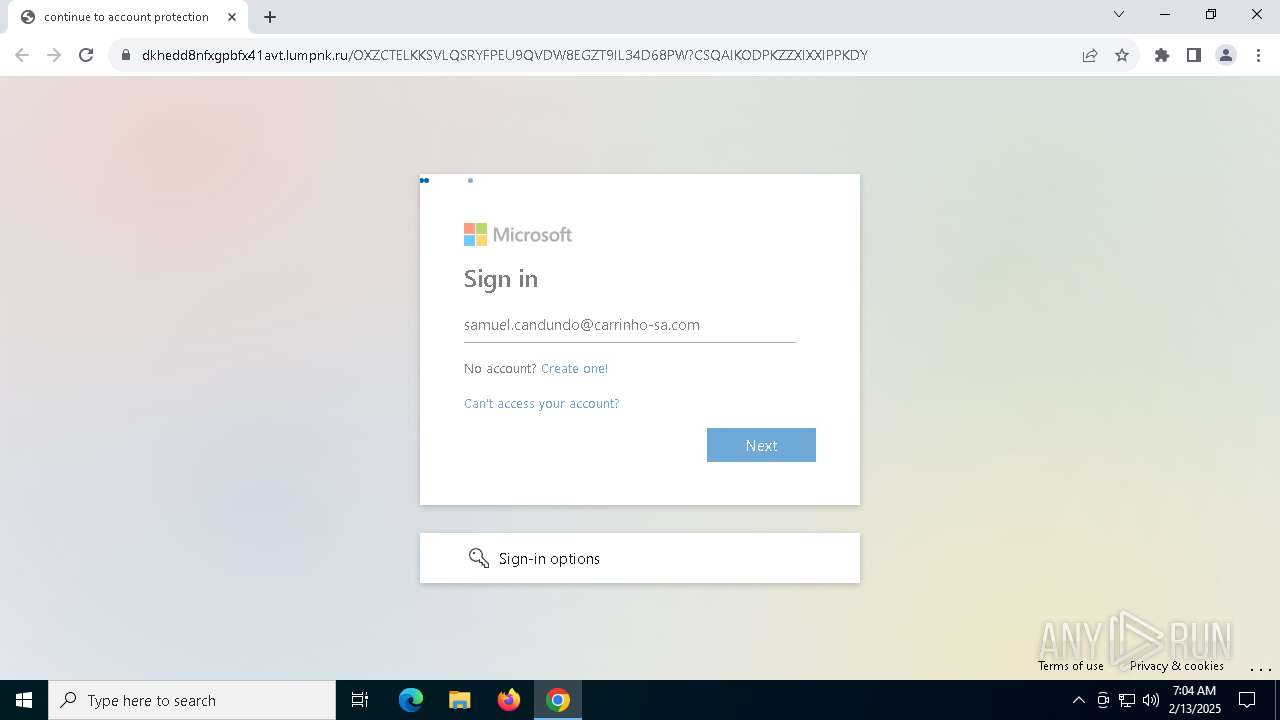
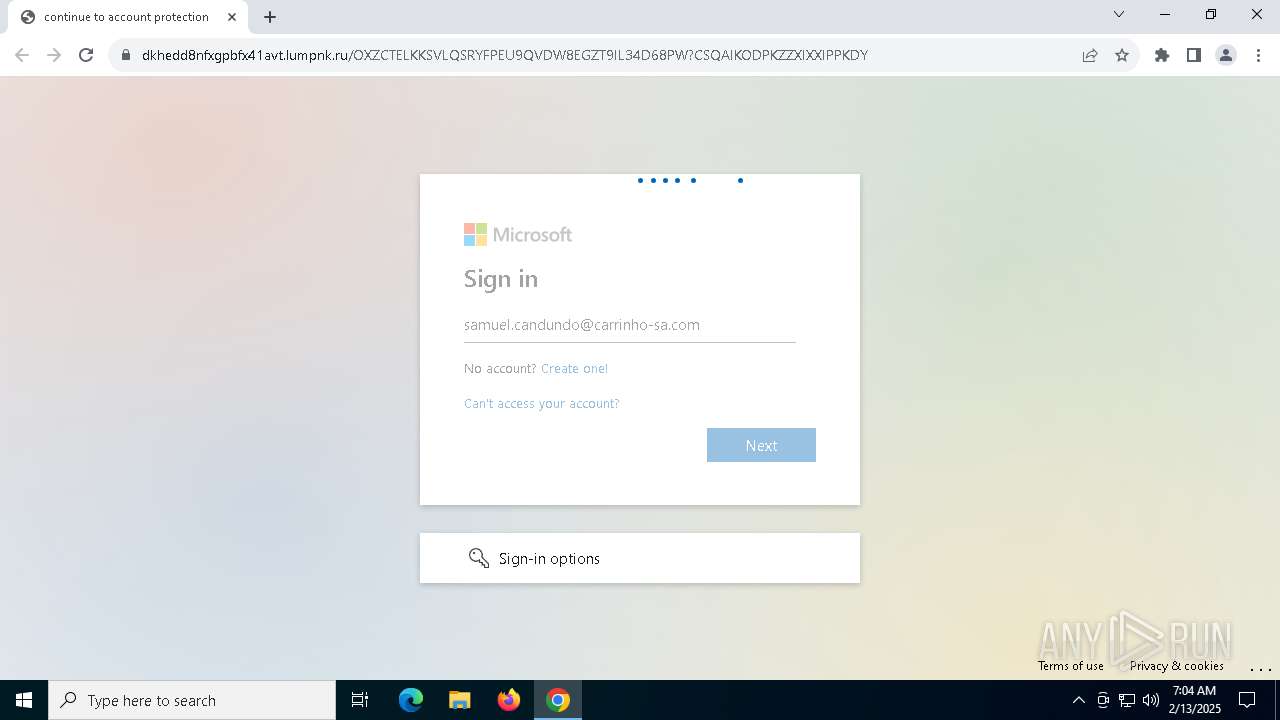
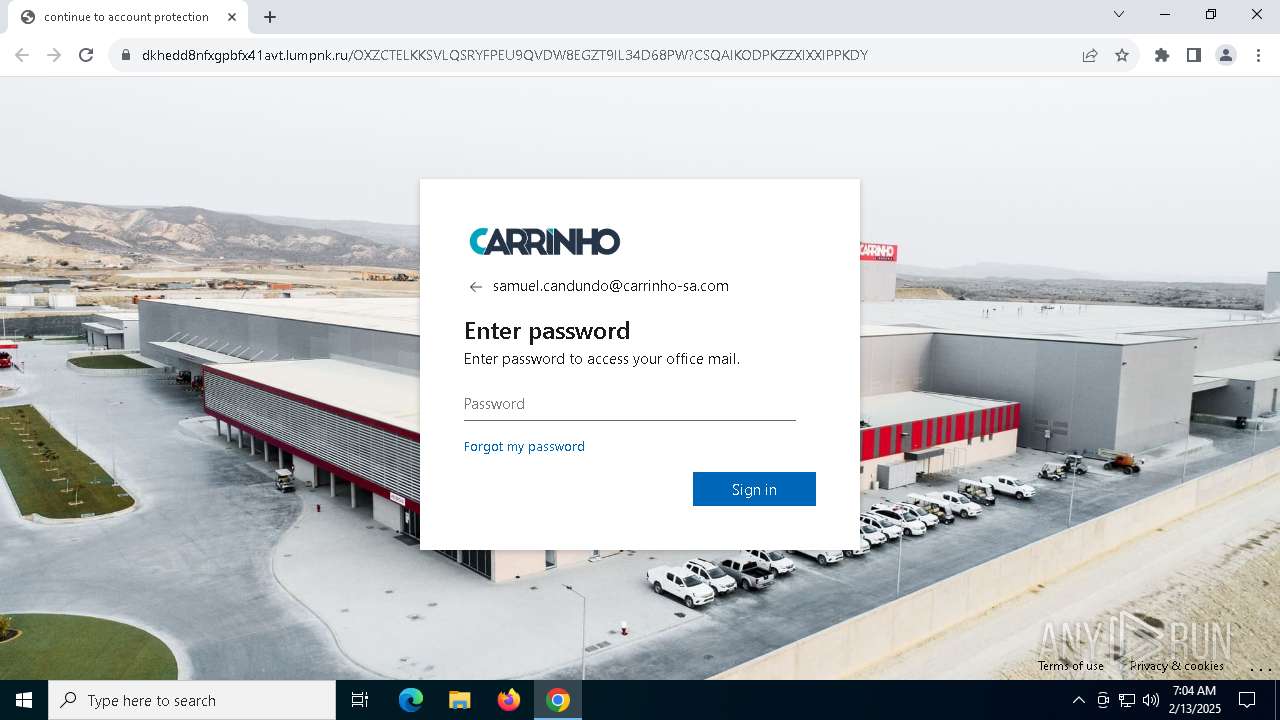
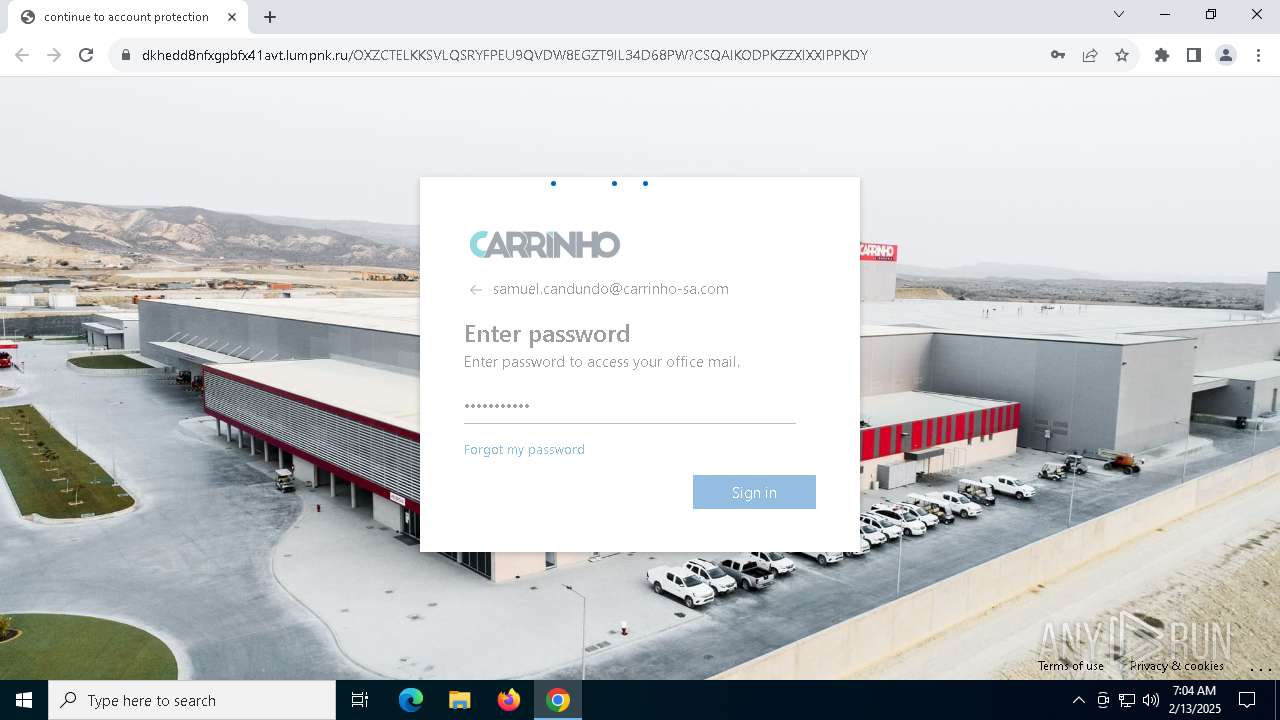
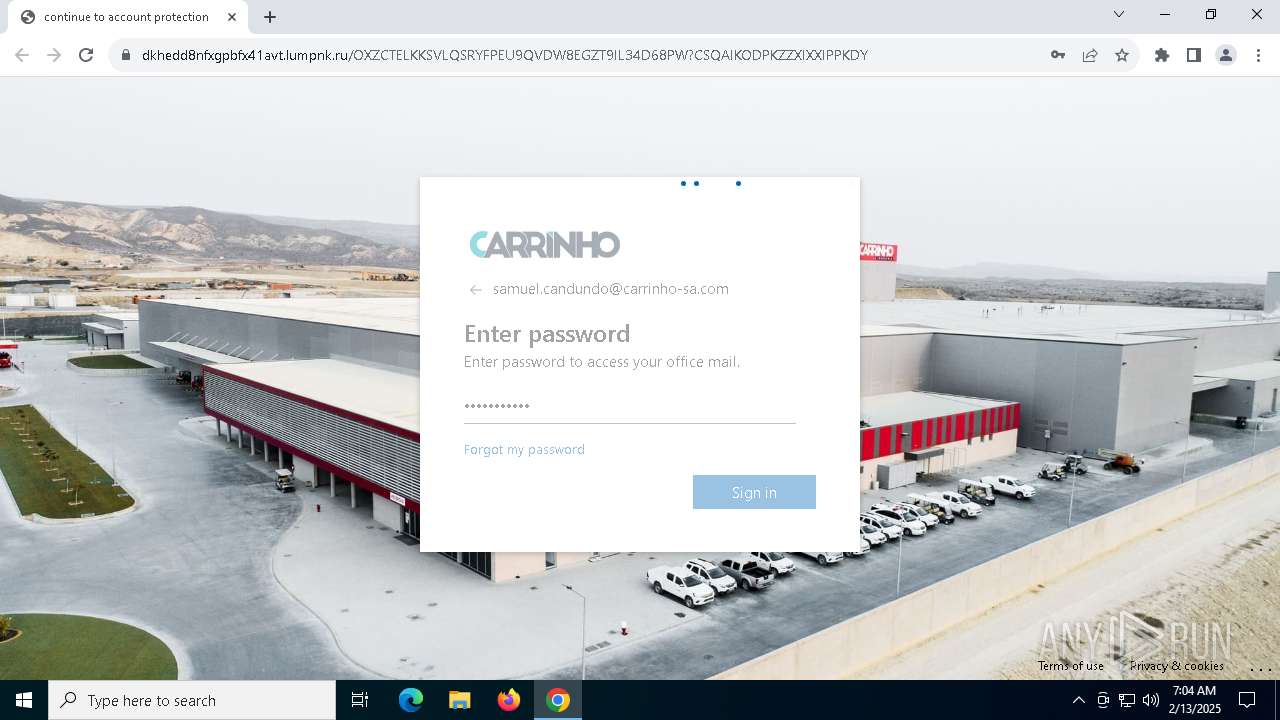
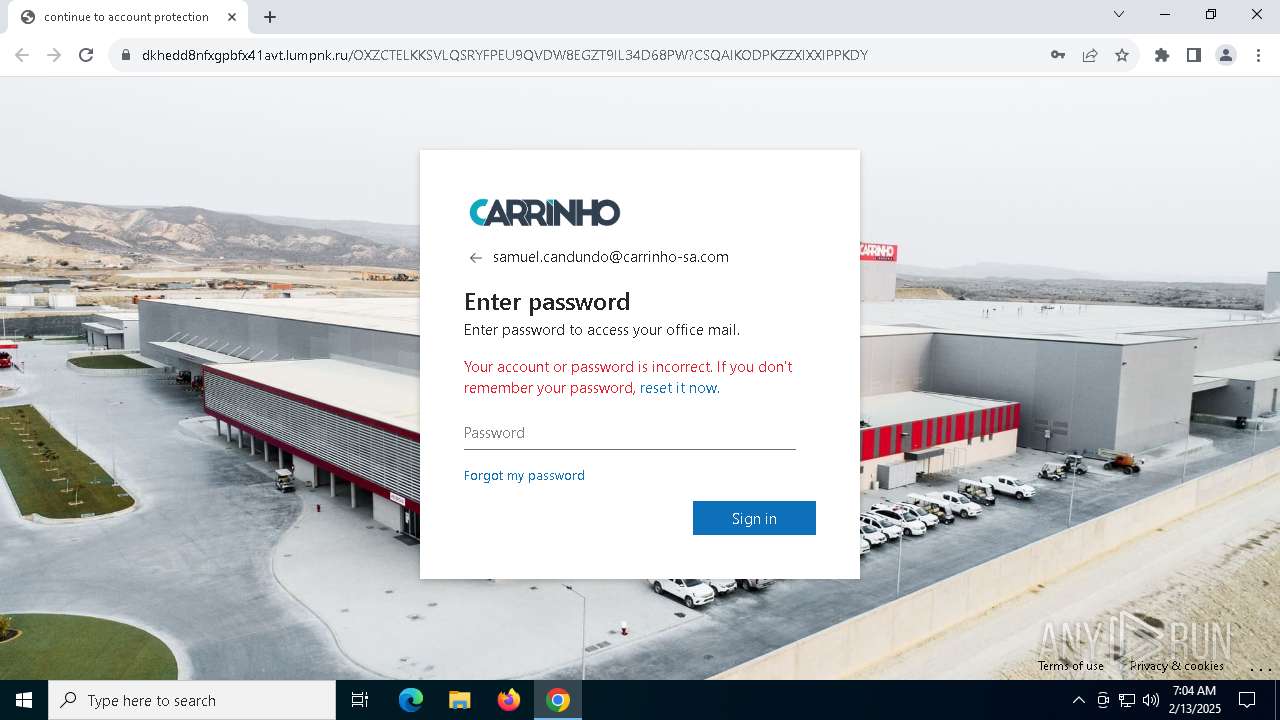
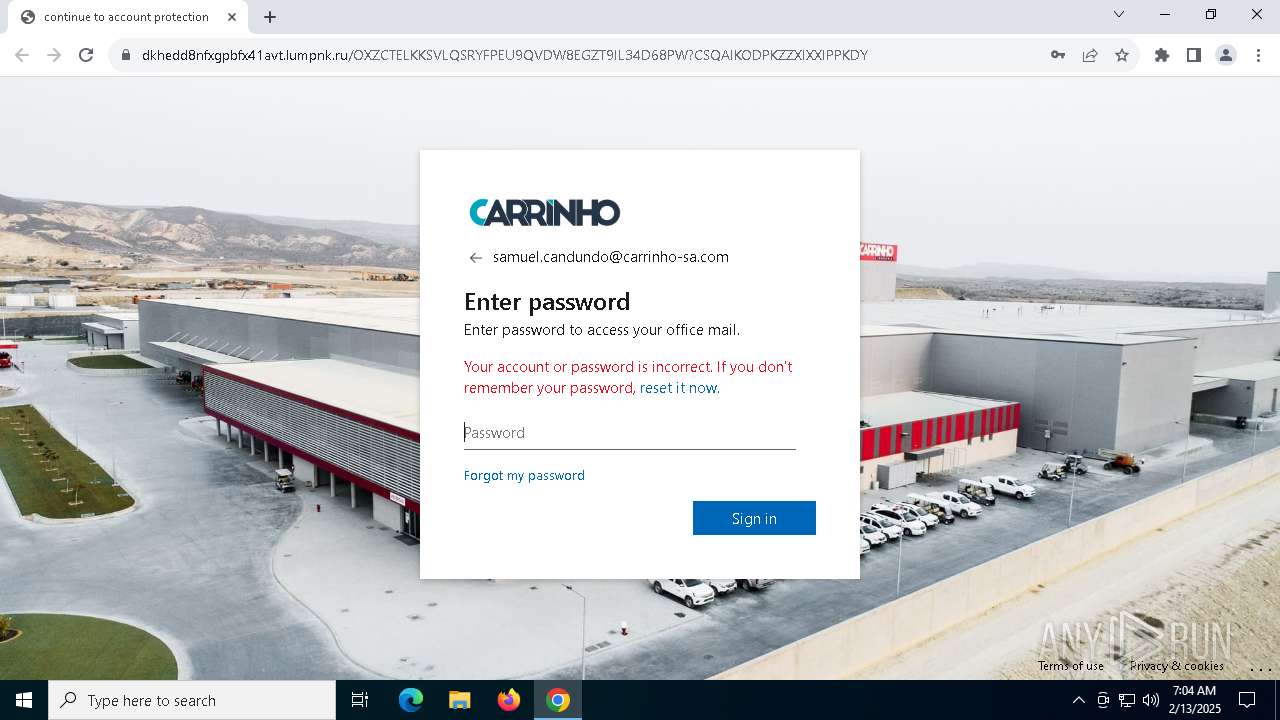
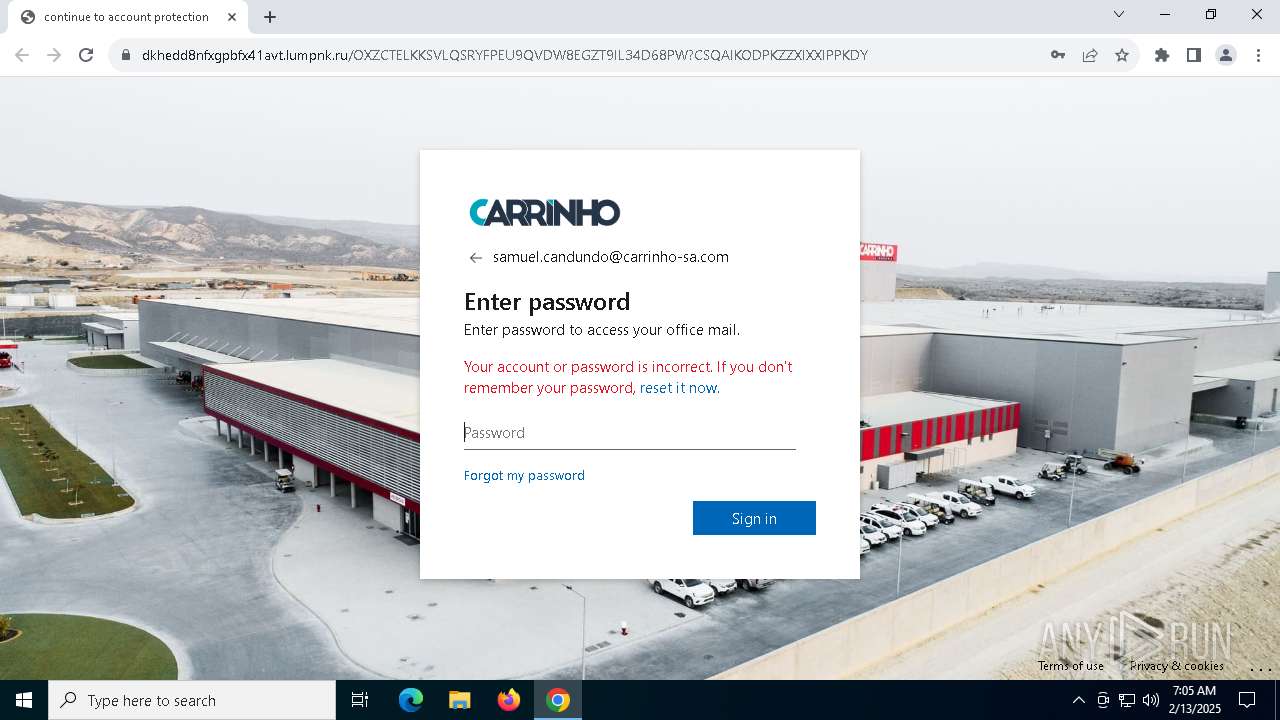
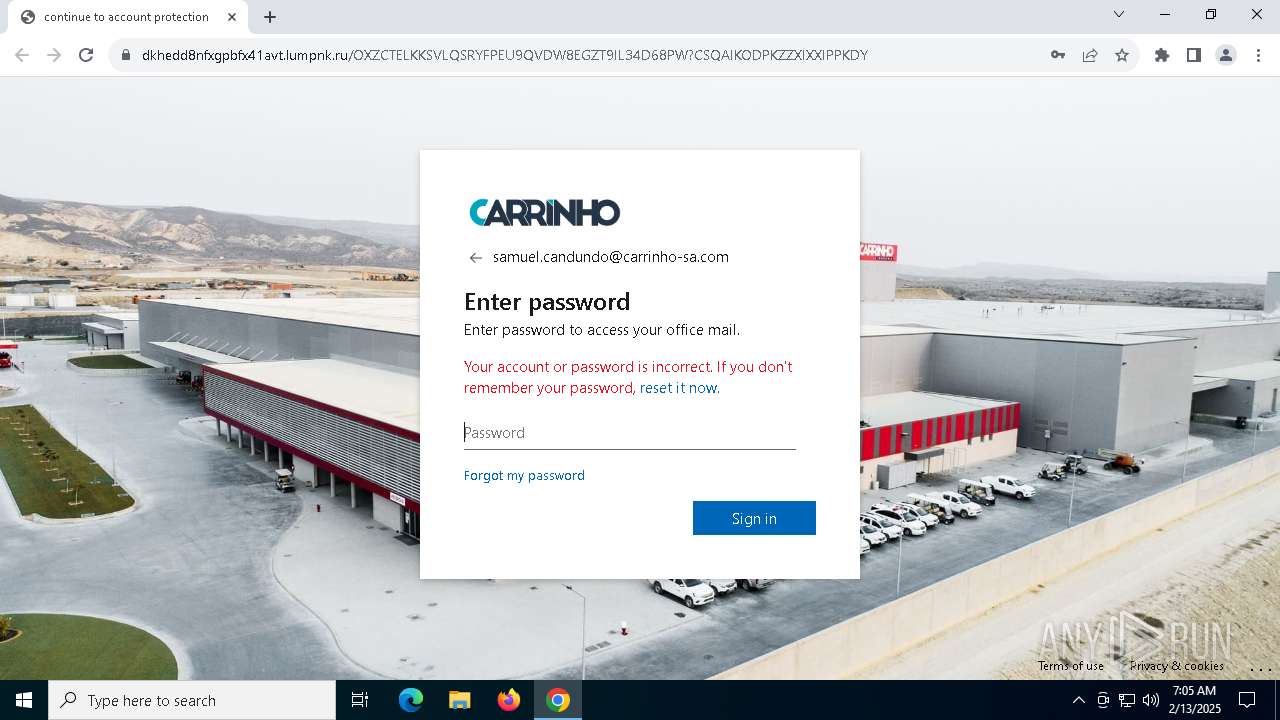
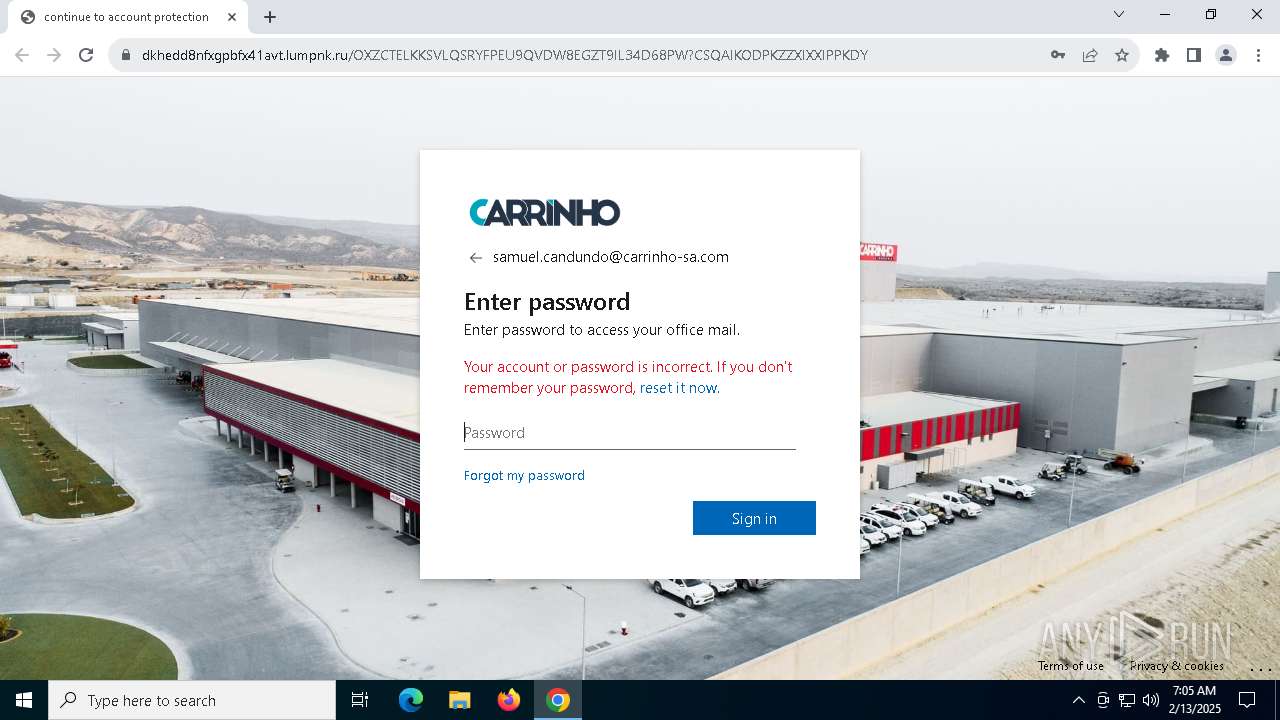
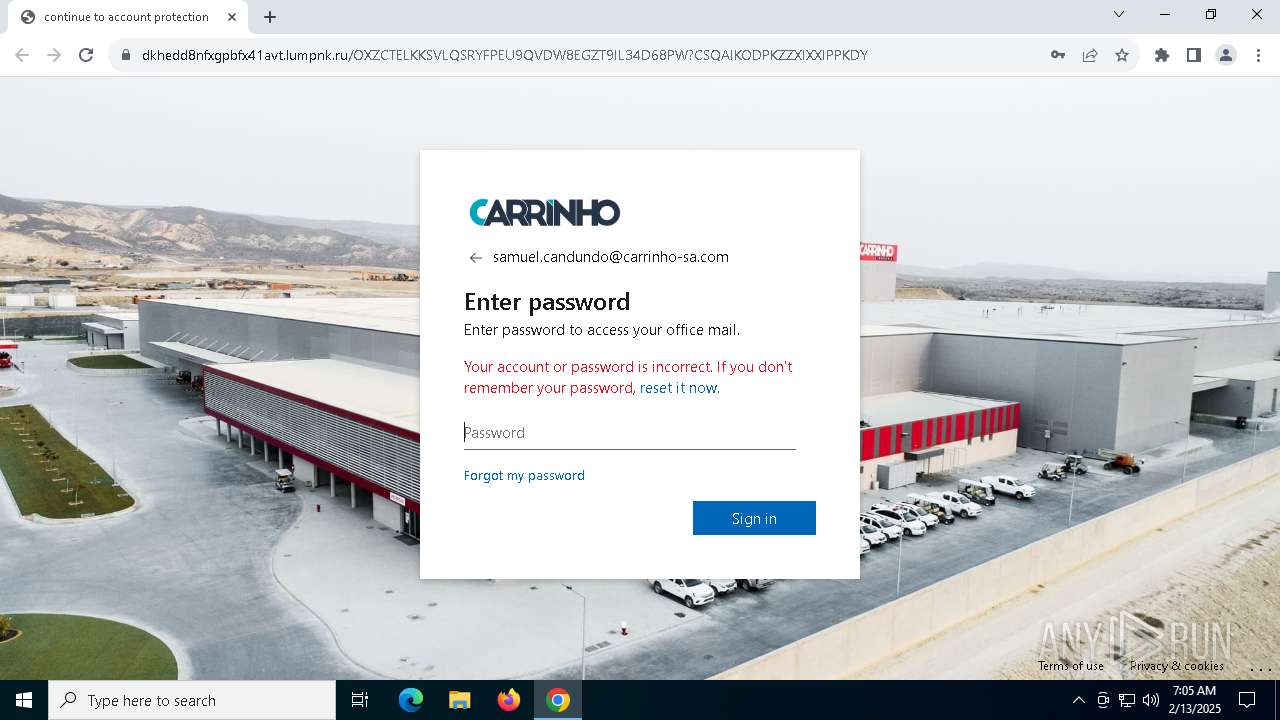
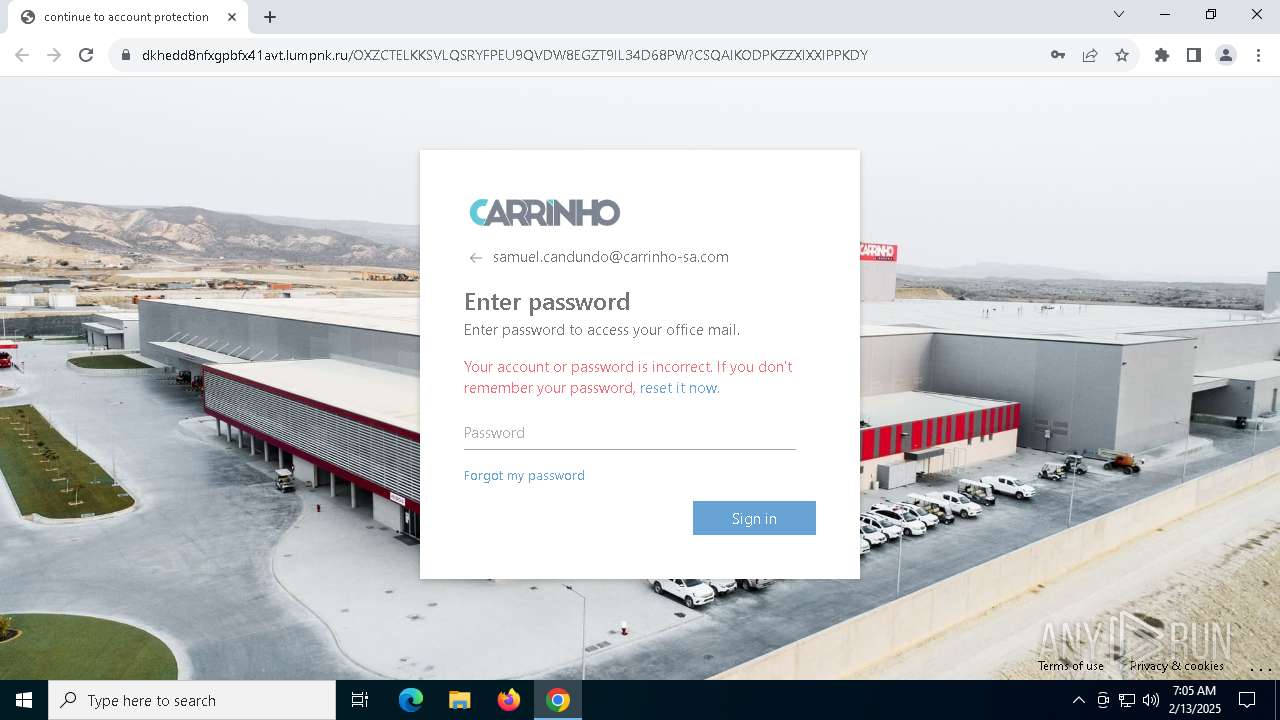
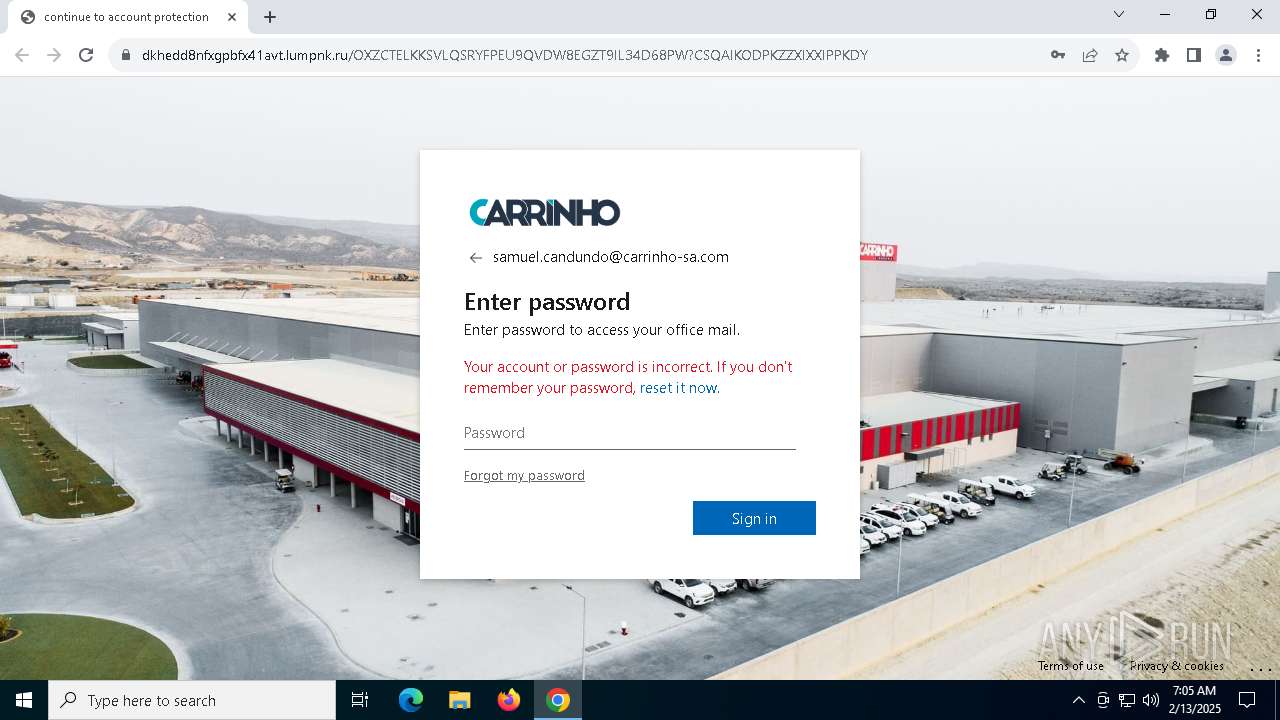
| Verdict: | Malicious activity |
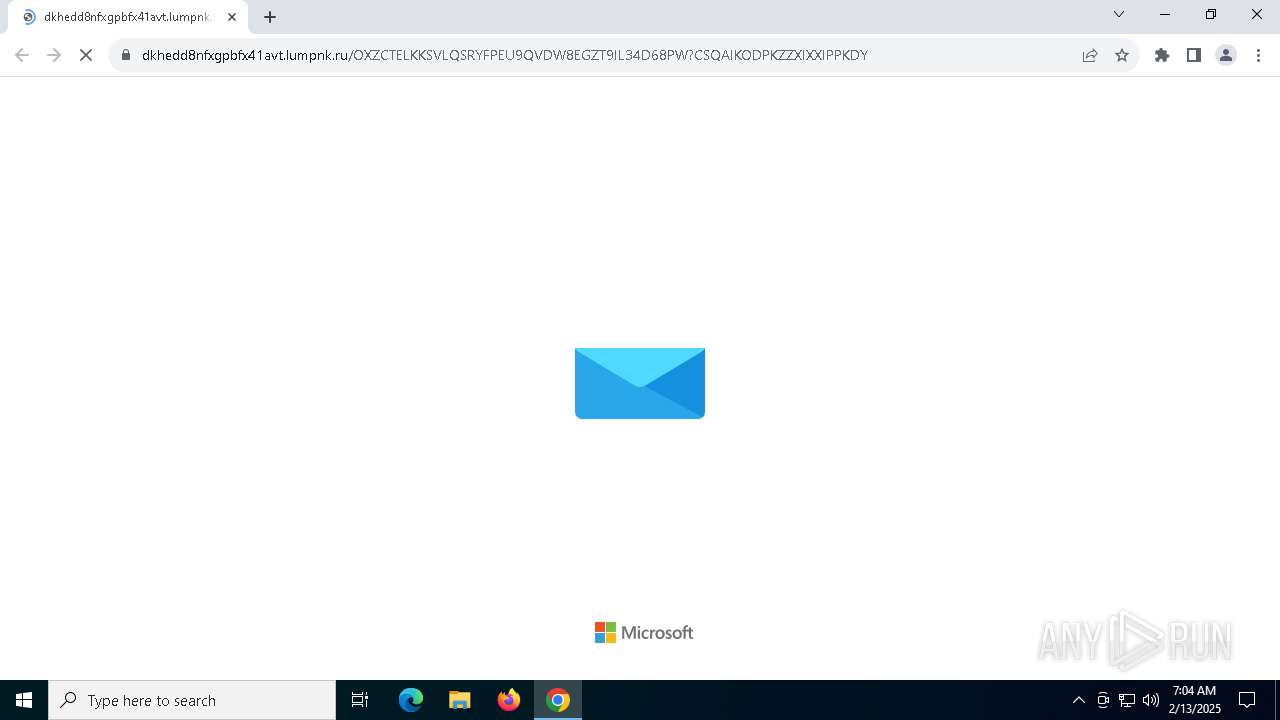
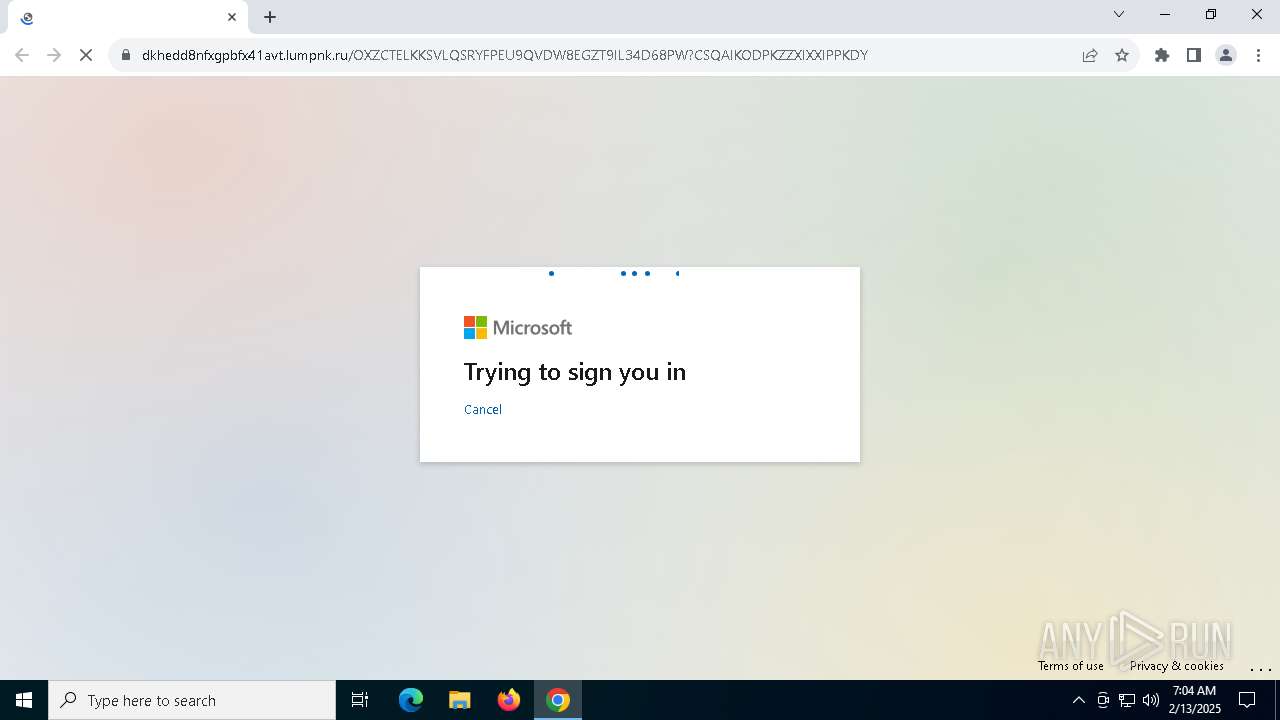
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | February 13, 2025, 07:04:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 09E7B8FC9477296EFEF3DE47399FECD8 |
| SHA1: | 3BFB5BA44A67F33CA575E67C187A09E2B8933136 |
| SHA256: | 0B976BD841C9A4A5E243E7DF44AFAF834BF9DD06A31B576CD8D5FD2A0AA07062 |
| SSDEEP: | 24:KXHmuqZWUrQH9F7YxU4xJ46hRqxV++3CYW:KXGFZWUroYq4t3qq+I |
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 6616)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 6328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
145
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=860 --field-trial-handle=1908,i,13460058730415403981,8649602043459441210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5164 --field-trial-handle=1908,i,13460058730415403981,8649602043459441210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "http://url4267.joincarma.com/ls/click?upn=u001.XT7M8389kHn5ypgXbdGEbA6-2FzdDv6E7L-2BXez5evFvRz202RE1upVKrOpH-2FYlprhJjUXb2vqgMegViRKkQvj9am8Gt4aIjqeWGX5hiO-2BR8IkqjdRZvGJvd8lI9yKby8ZehlAjoPN5bsEBg95BhFaTBmvJLGivhYXTapZMreTCybqgRQF-2BRA06UCWhxOPEyG7VnUZ6kHwYXok6BDtDSvzmUcDvkEqC1nP-2Fh83iI3Ua7jkp4BRb1PK2rrchf477KmqJNuocXrOlyWehwWWl-2F9FxQ-2BFbSSuXE2-2BrJK0AlHYJvtMslhYOPDdXdE1Vjgx-2BcDNuKE0sRtDoBRL1p6ZZYeI9qwsG3qUCMG6YUROVU5VdI4L97Io7Ng-2Bb050ioYKDKS67Ils7I8aTCThdl7y7FF3SYPDtj72Zo6JI1DcpTD9Qpptmm5nIPei5roMJF8GM5boy-2BkegMV49o9zvpe9gdWHVBH-2Bky8HfbjFY5HSPnpXqKOT6sppDGQ01Gucn-2FqNI5Im-2F-2F5AXsf2wibnvBBrFJBX96DSVY8LdUl5bncNvvTNexgM-3DC8hG_MjAhclRA0hH-2F1a1m8v8T4rJi-2BScc6AlQzsSSGVOBAwwtWN8L2P-2FngD-2Bz-2B9FEA4k9ZFamqMG0WnZ0pk0alMsZZ1rgTkzxVLJYQAgg2ppOO7C-2BVP-2FgiMdRz-2Fc8XDI-2FchGcoJKdXjhTei-2B3ussVDh-2F15gJwjdQNQRvI12w8396hooCgQjVlvRRaTtQbwC5j-2BN9BYwf0Dmk8vpWM6mkcCDSEWvc-2BcIR-2F3OVOcr7-2B7hb262c-3D" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x220,0x224,0x228,0x1f8,0x22c,0x7ff81772dc40,0x7ff81772dc4c,0x7ff81772dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1904 --field-trial-handle=1908,i,13460058730415403981,8649602043459441210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2080 --field-trial-handle=1908,i,13460058730415403981,8649602043459441210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2220 --field-trial-handle=1908,i,13460058730415403981,8649602043459441210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3008 --field-trial-handle=1908,i,13460058730415403981,8649602043459441210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3040 --field-trial-handle=1908,i,13460058730415403981,8649602043459441210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3484 --field-trial-handle=1908,i,13460058730415403981,8649602043459441210,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
2 862
Read events
2 850
Write events
11
Delete events
1
Modification events
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | ahfgeienlihckogmohjhadlkjgocpleb |
Value: 3B08F722C14555E595AF269F140EE426CE8DEBAD90D03EE9FF33B95CB34233F6 | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | bjbddleefiddlmdfdfbgodgacjjldihj |
Value: 5CFE6AD362B9AABBD07085580BC6C063CF1C79A0B22ECB6BCBA21EECA68BA07F | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | mhjfbmdgcfjbbpaeojofohoefgiehjai |
Value: F6EE482B70E472BD0FE04C8E130D7E2A0D87334BDC8F199AD874C100863BC5BE | |||
| (PID) Process: | (6328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | neajdppkdcdipfabeoofebfddakdcjhd |
Value: 856E0E73E6E37099A4C21DA68A6A10BD31001B9D36A3243EBC4814EC93C0BA43 | |||
Executable files
1
Suspicious files
48
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF137458.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF137458.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF137458.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF137468.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF137478.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
73
DNS requests
74
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6616 | chrome.exe | GET | 302 | 167.89.118.62:80 | http://url4267.joincarma.com/ls/click?upn=u001.XT7M8389kHn5ypgXbdGEbA6-2FzdDv6E7L-2BXez5evFvRz202RE1upVKrOpH-2FYlprhJjUXb2vqgMegViRKkQvj9am8Gt4aIjqeWGX5hiO-2BR8IkqjdRZvGJvd8lI9yKby8ZehlAjoPN5bsEBg95BhFaTBmvJLGivhYXTapZMreTCybqgRQF-2BRA06UCWhxOPEyG7VnUZ6kHwYXok6BDtDSvzmUcDvkEqC1nP-2Fh83iI3Ua7jkp4BRb1PK2rrchf477KmqJNuocXrOlyWehwWWl-2F9FxQ-2BFbSSuXE2-2BrJK0AlHYJvtMslhYOPDdXdE1Vjgx-2BcDNuKE0sRtDoBRL1p6ZZYeI9qwsG3qUCMG6YUROVU5VdI4L97Io7Ng-2Bb050ioYKDKS67Ils7I8aTCThdl7y7FF3SYPDtj72Zo6JI1DcpTD9Qpptmm5nIPei5roMJF8GM5boy-2BkegMV49o9zvpe9gdWHVBH-2Bky8HfbjFY5HSPnpXqKOT6sppDGQ01Gucn-2FqNI5Im-2F-2F5AXsf2wibnvBBrFJBX96DSVY8LdUl5bncNvvTNexgM-3DC8hG_MjAhclRA0hH-2F1a1m8v8T4rJi-2BScc6AlQzsSSGVOBAwwtWN8L2P-2FngD-2Bz-2B9FEA4k9ZFamqMG0WnZ0pk0alMsZZ1rgTkzxVLJYQAgg2ppOO7C-2BVP-2FgiMdRz-2Fc8XDI-2FchGcoJKdXjhTei-2B3ussVDh-2F15gJwjdQNQRvI12w8396hooCgQjVlvRRaTtQbwC5j-2BN9BYwf0Dmk8vpWM6mkcCDSEWvc-2BcIR-2F3OVOcr7-2B7hb262c-3D | US | html | 455 b | unknown |
— | — | GET | 200 | 2.18.244.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | whitelisted |
6156 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
— | — | GET | 200 | 96.6.17.223:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NO | binary | 973 b | whitelisted |
6156 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 1.09 Kb | whitelisted |
6156 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | compressed | 1.98 Kb | whitelisted |
1176 | svchost.exe | GET | 200 | 184.86.11.11:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | SE | binary | 471 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.86.11.11:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | SE | binary | 313 b | whitelisted |
6848 | backgroundTaskHost.exe | GET | 200 | 184.86.11.11:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | SE | binary | 471 b | whitelisted |
5464 | SIHClient.exe | GET | 200 | 96.6.17.223:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NO | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.18.244.211:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
— | — | 96.6.17.223:80 | www.microsoft.com | AKAMAI-AS | NO | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 95.101.136.223:443 | — | Akamai International B.V. | GB | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6616 | chrome.exe | 167.89.118.62:80 | url4267.joincarma.com | SENDGRID | US | unknown |
6328 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6616 | chrome.exe | 167.89.118.62:443 | url4267.joincarma.com | SENDGRID | US | unknown |
6616 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6616 | chrome.exe | 104.26.9.55:443 | link.shoppermeet.net | CLOUDFLARENET | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
url4267.joincarma.com |
| unknown |
accounts.google.com |
| whitelisted |
link.shoppermeet.net |
| unknown |
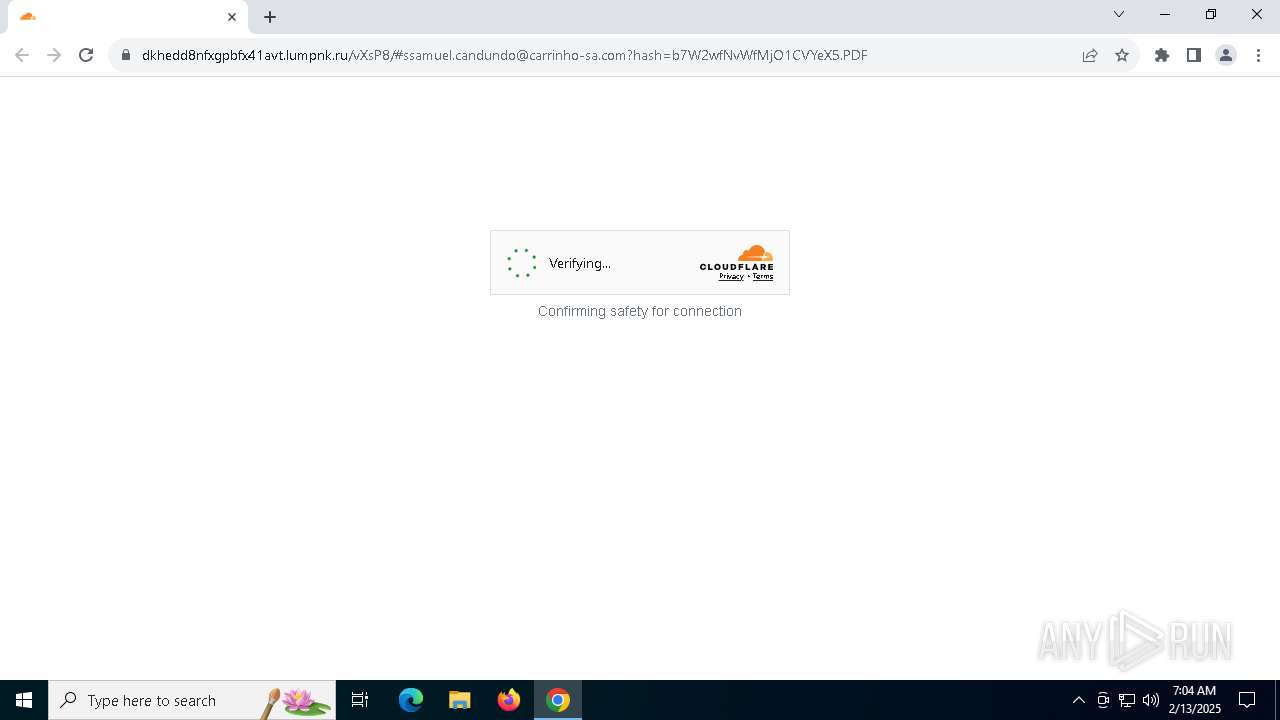
dkhedd8nfxgpbfx41avt.lumpnk.ru |
| unknown |
www.google.com |
| whitelisted |
code.jquery.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6616 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .lumpnk .ru) |
6616 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .lumpnk .ru) |
6616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |