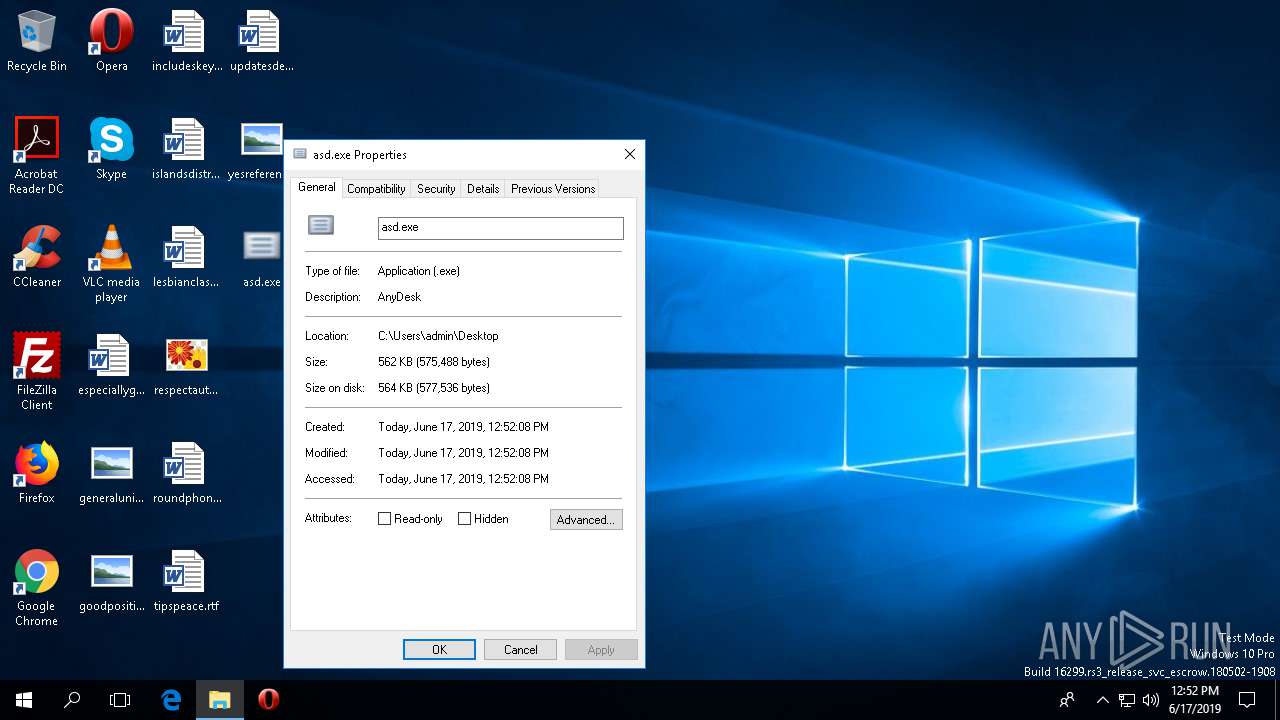
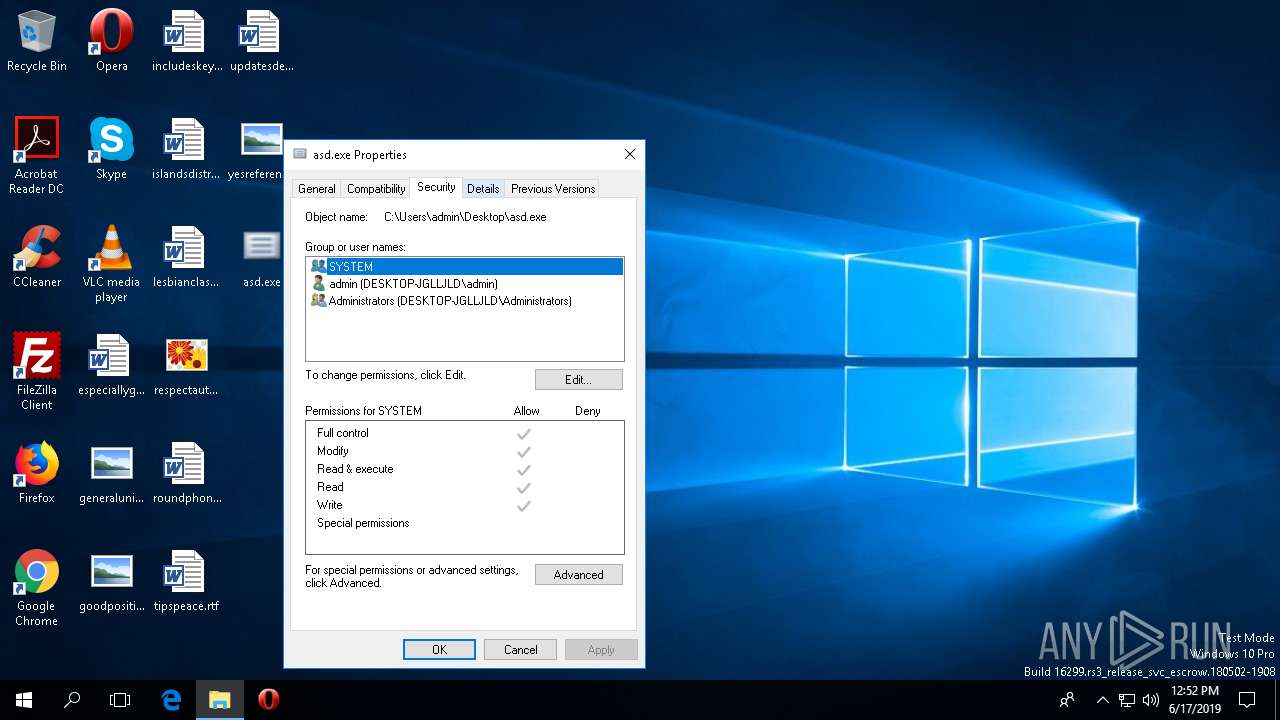
| File name: | asd.exe |
| Full analysis: | https://app.any.run/tasks/57ccb7e9-52b5-4a70-a9f9-85a8d2d46dea |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | June 17, 2019, 12:51:43 |
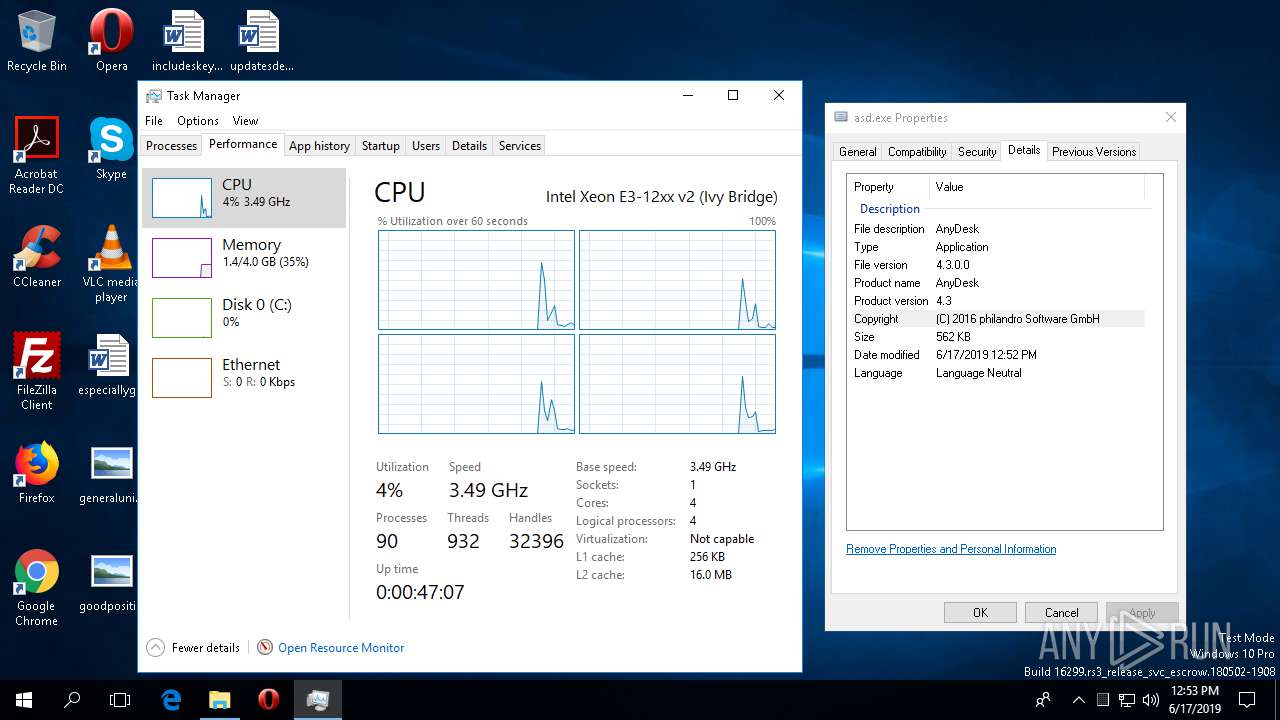
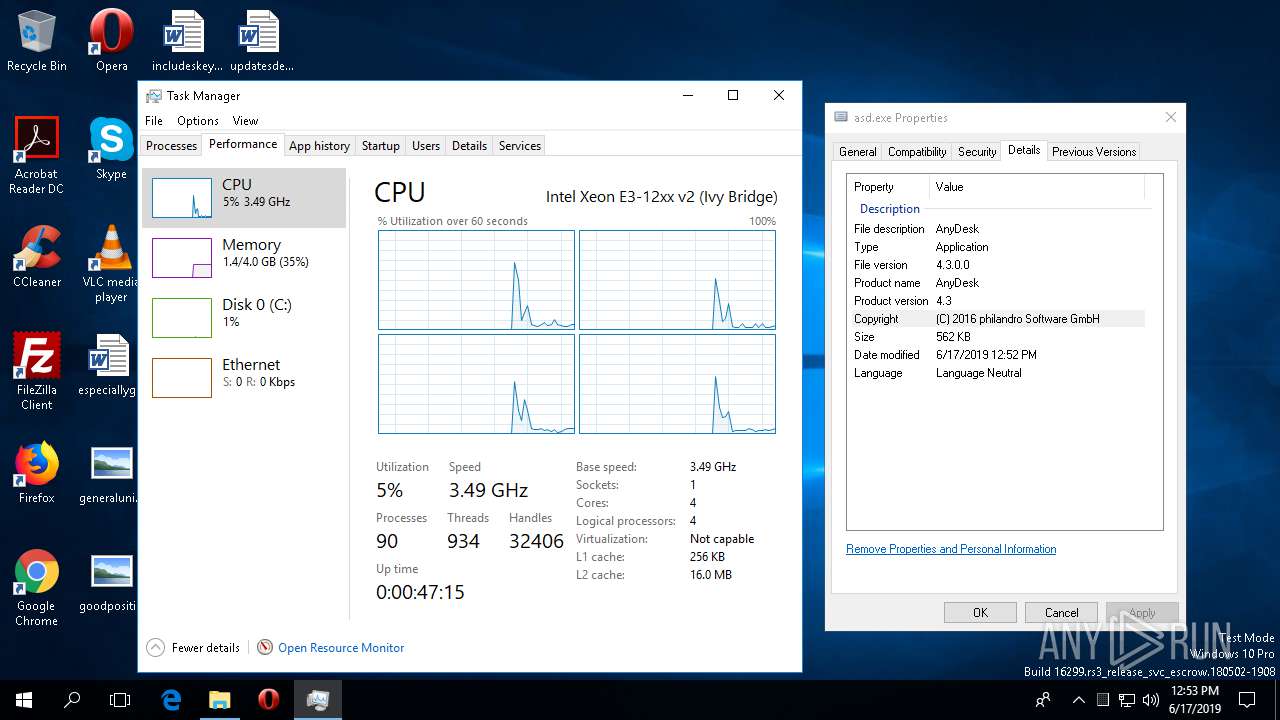
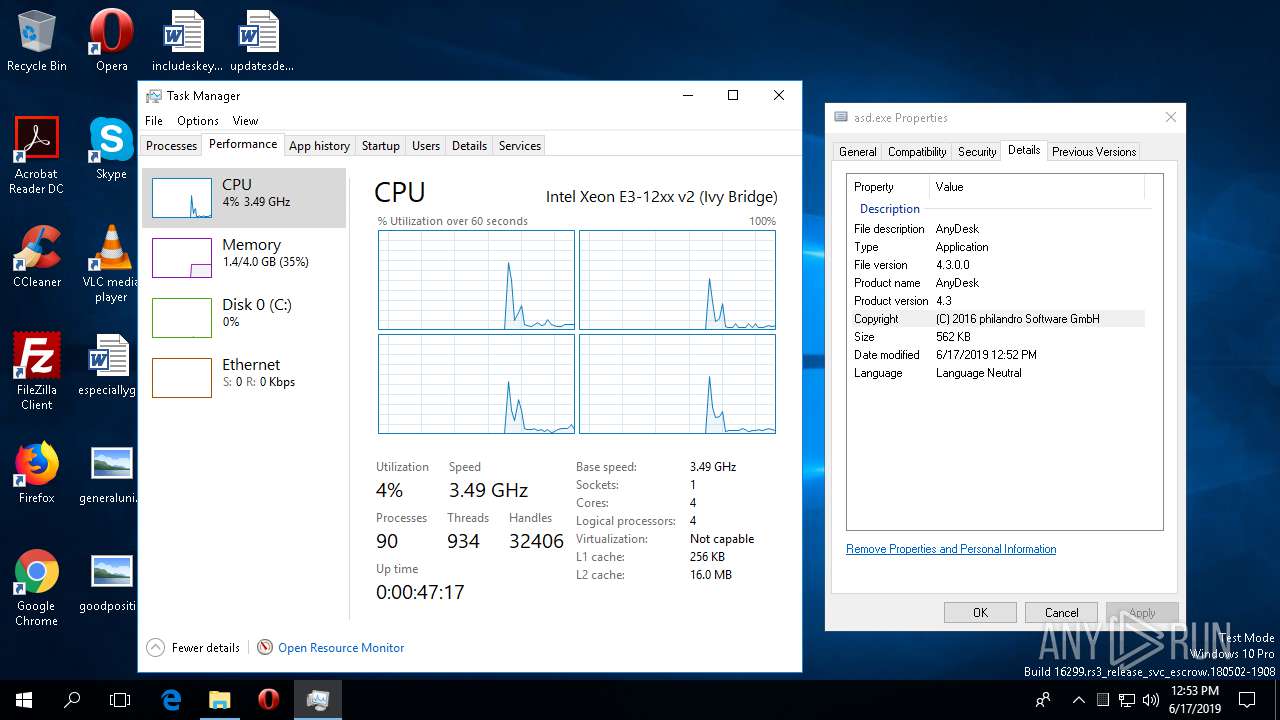
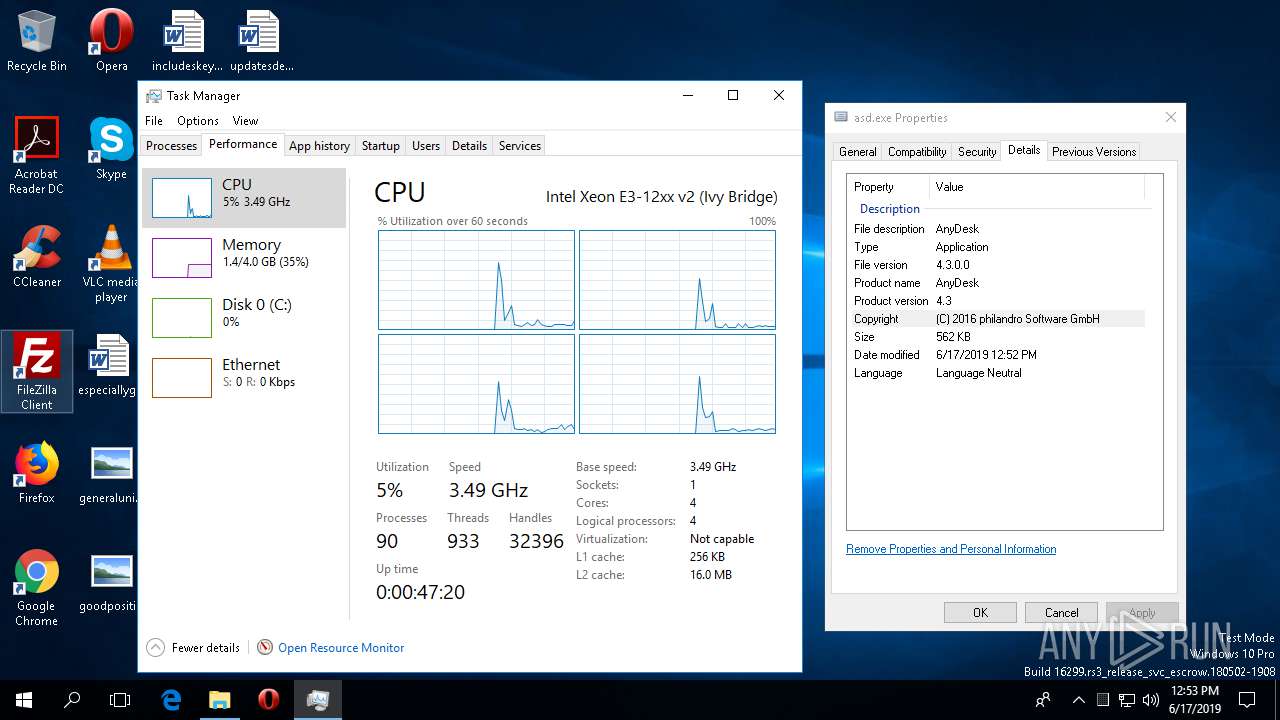
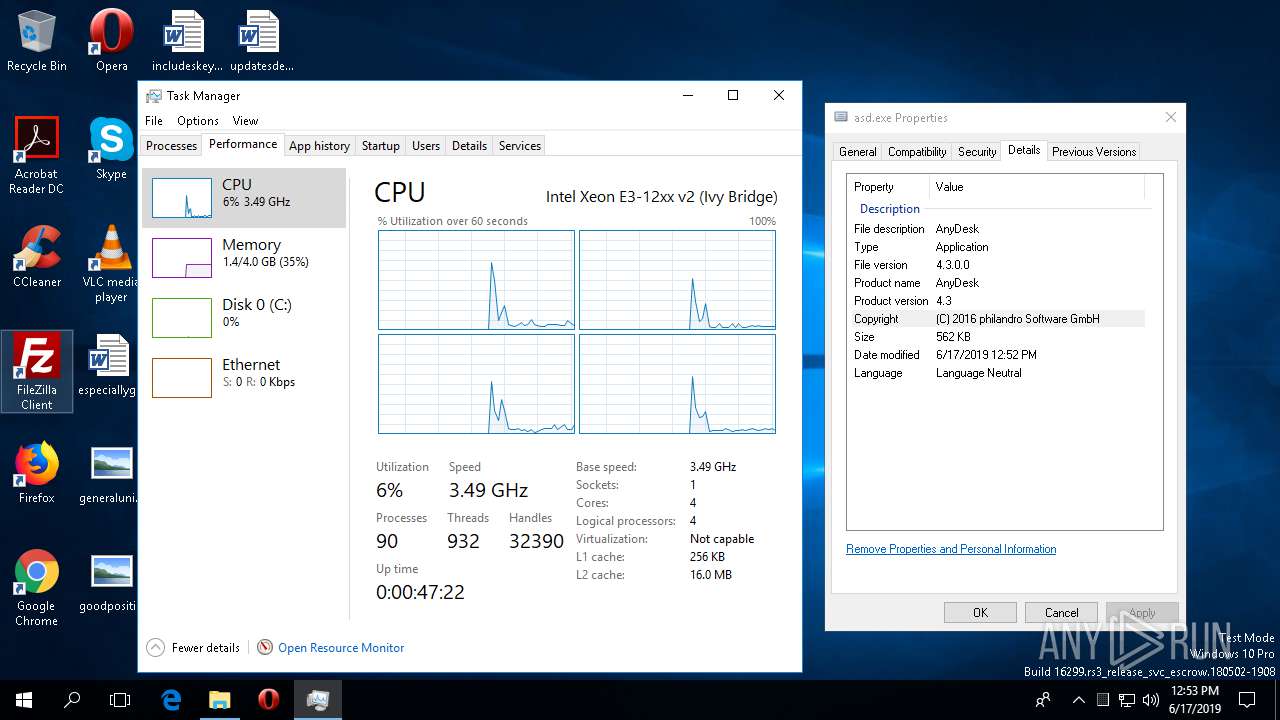
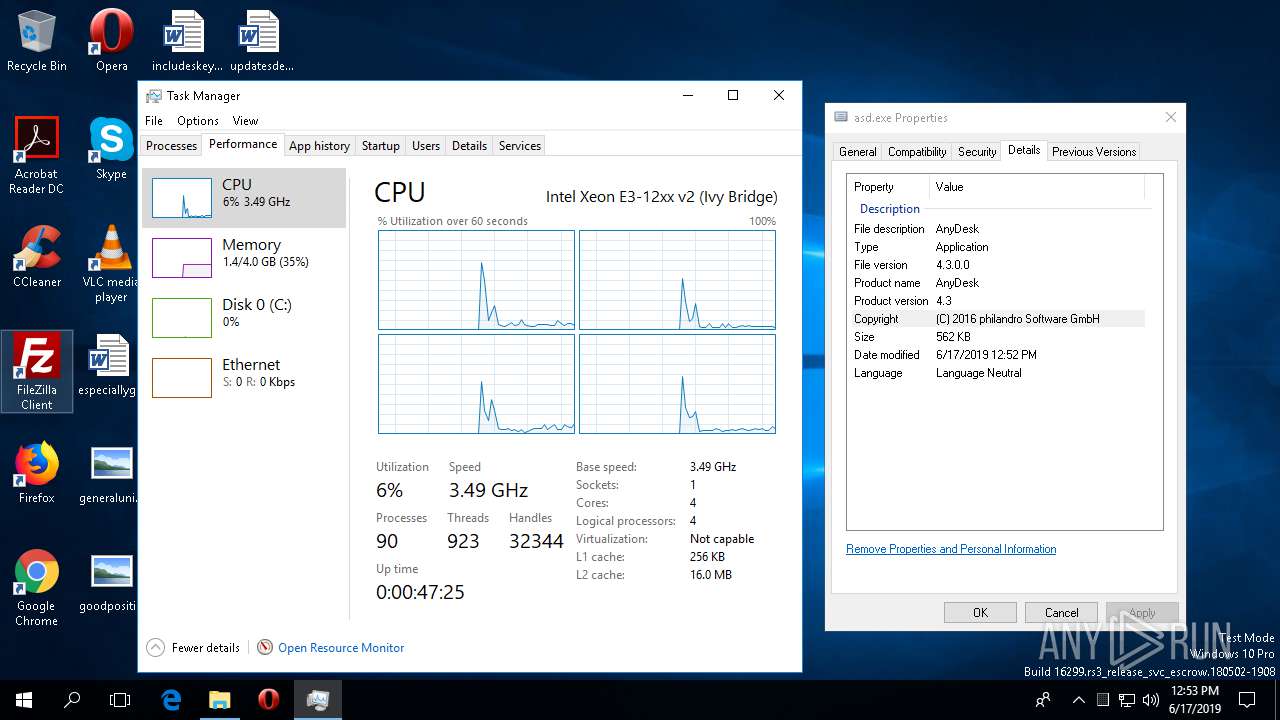
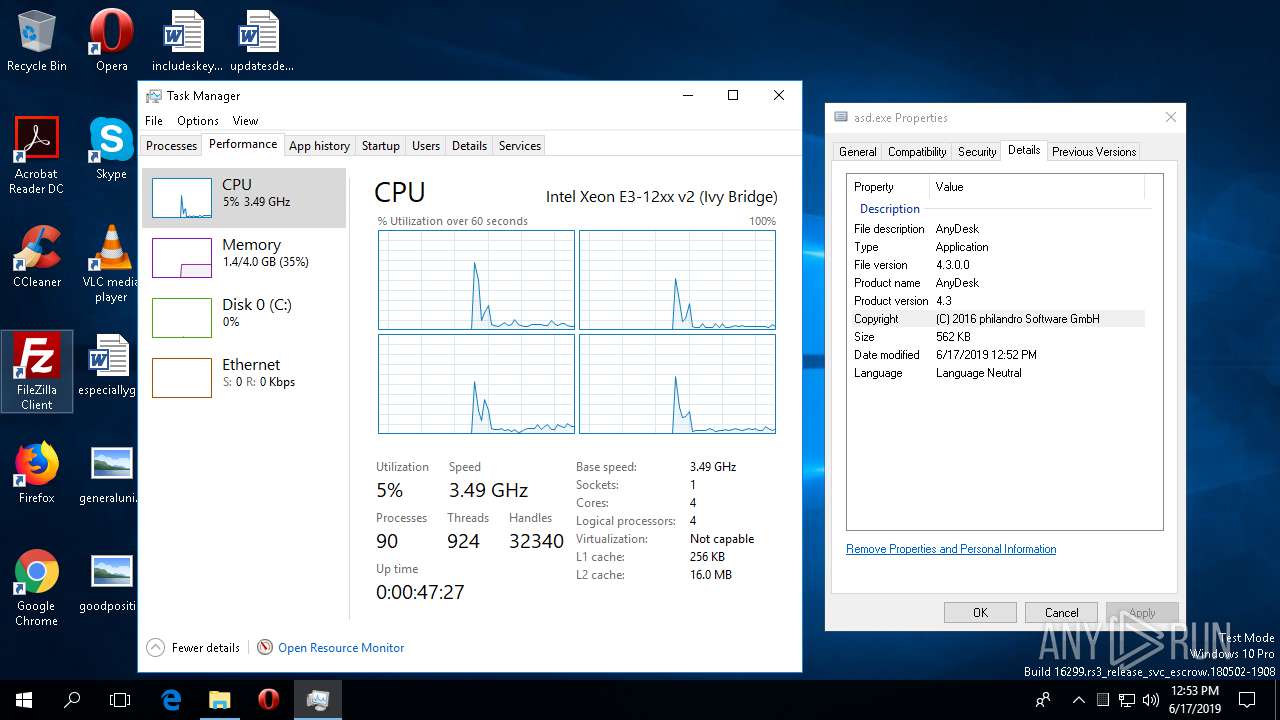
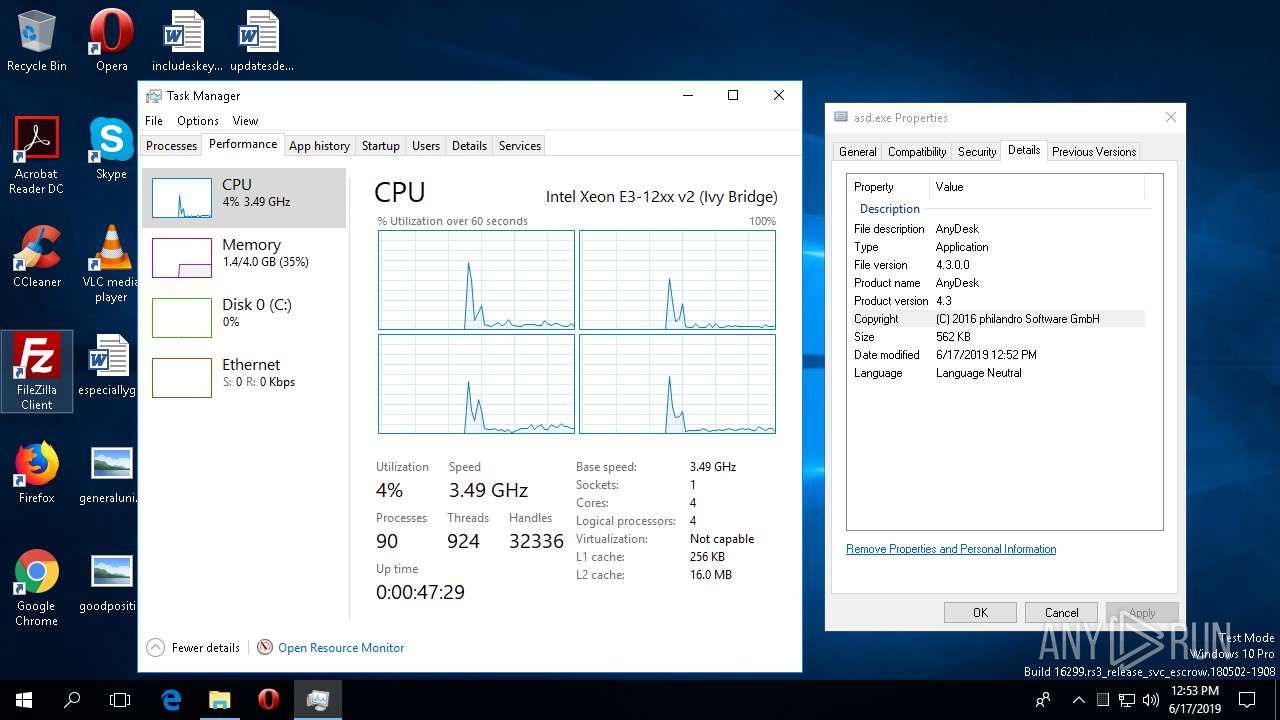
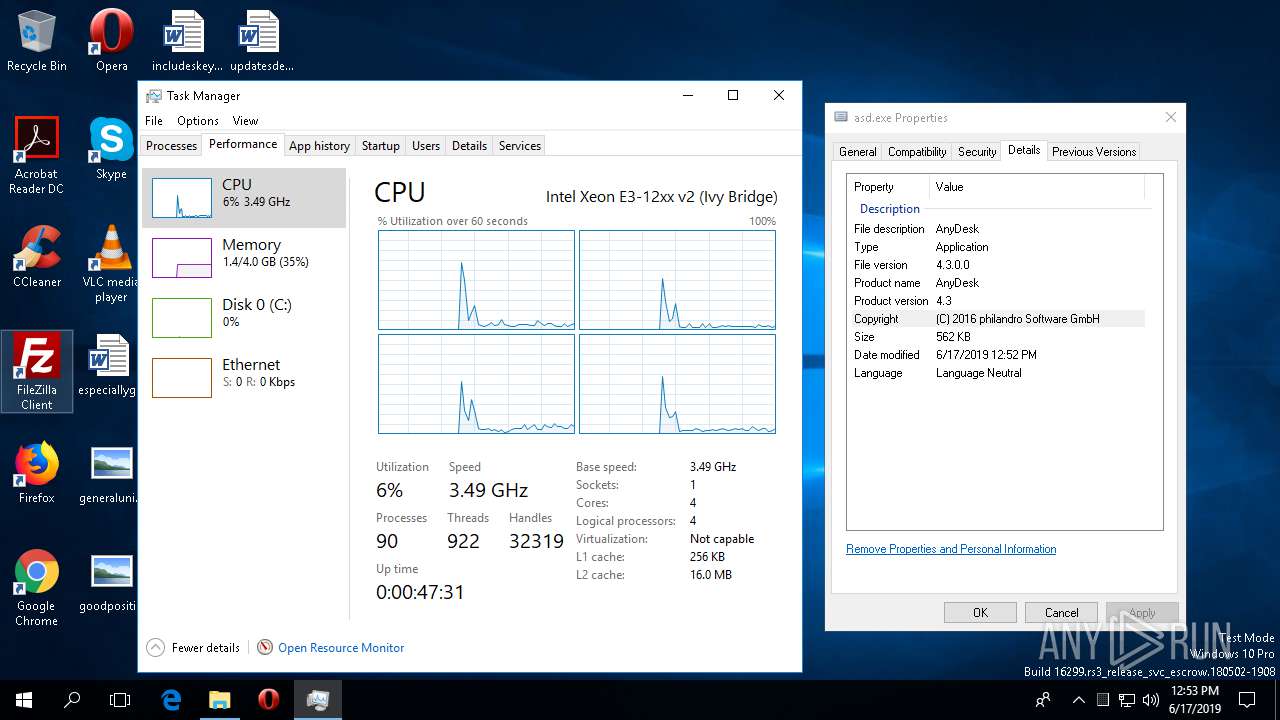
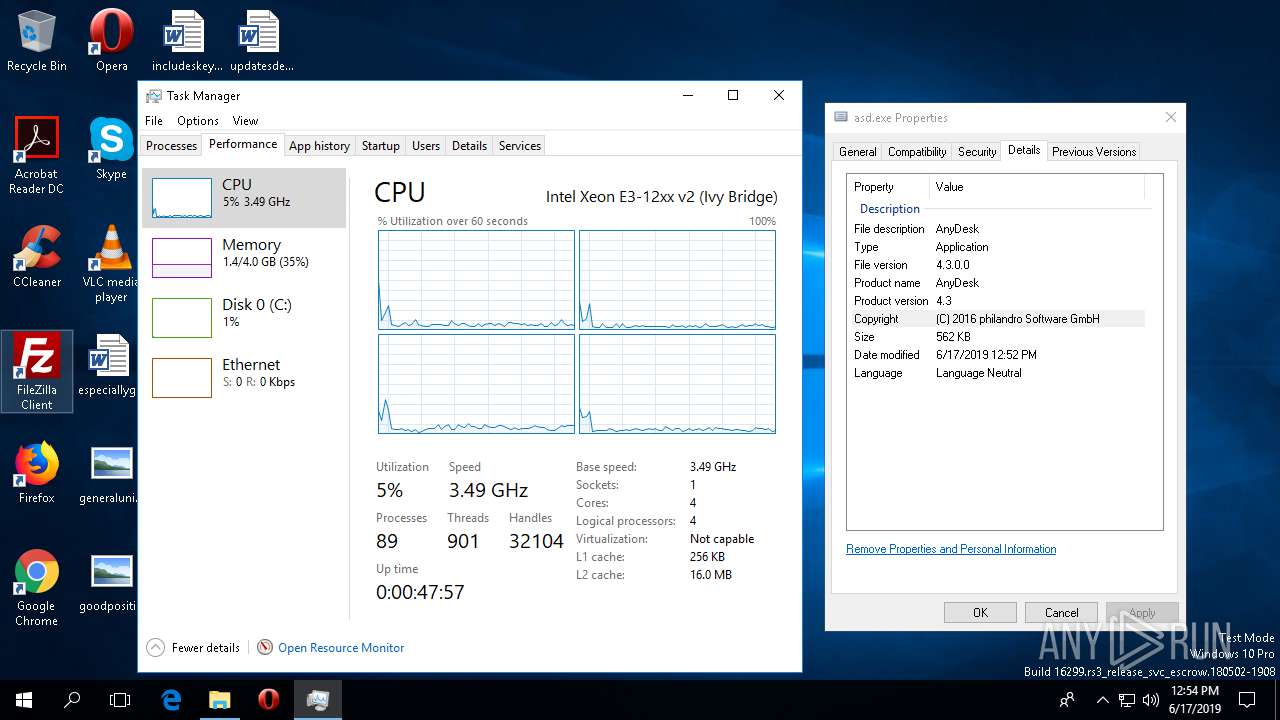
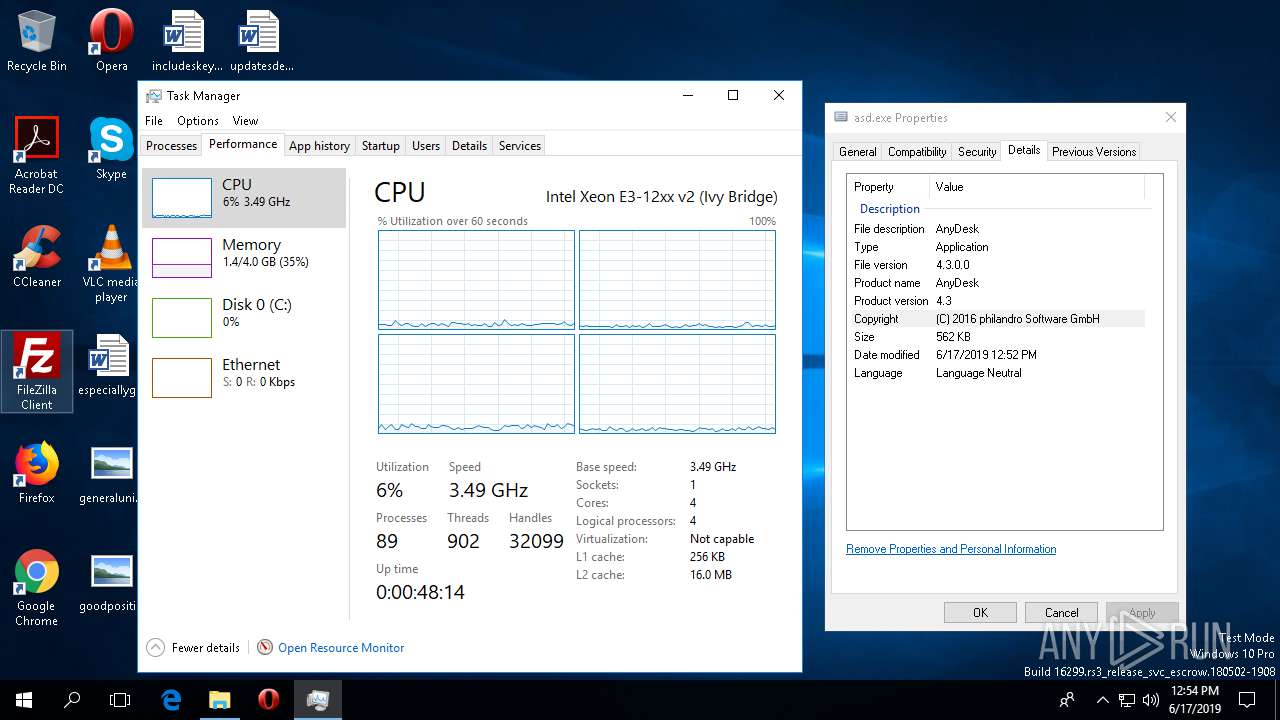
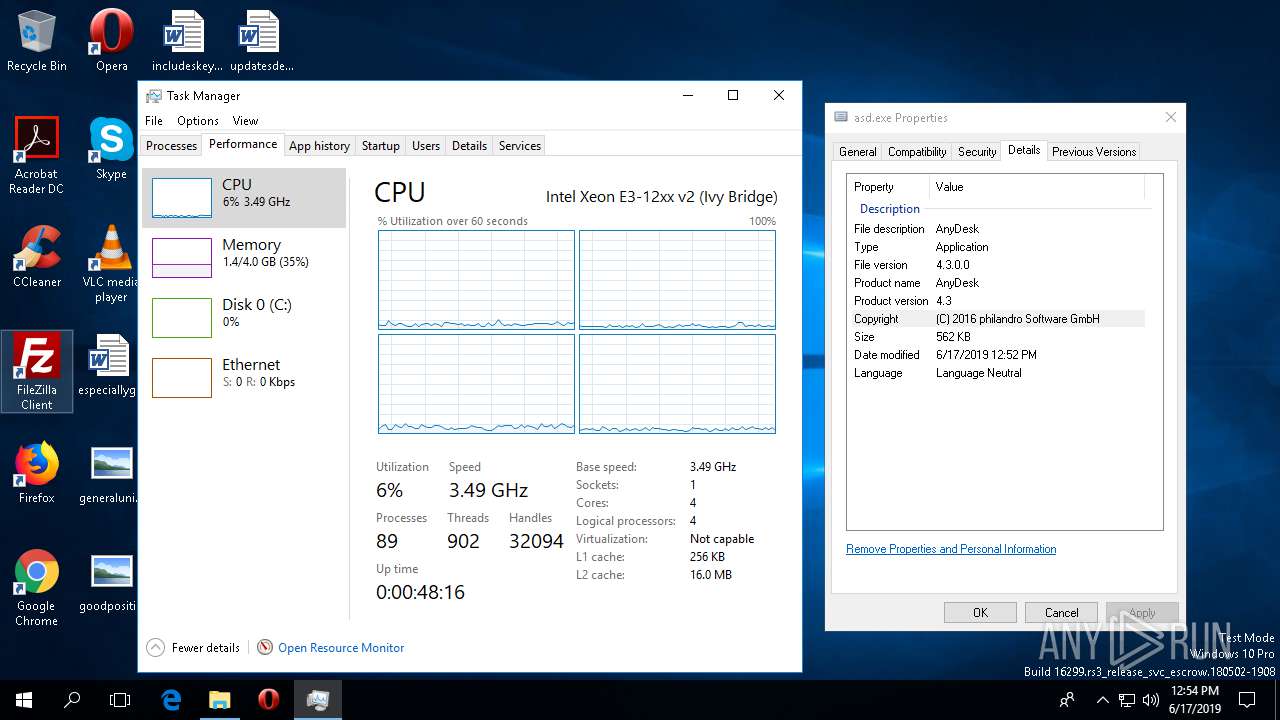
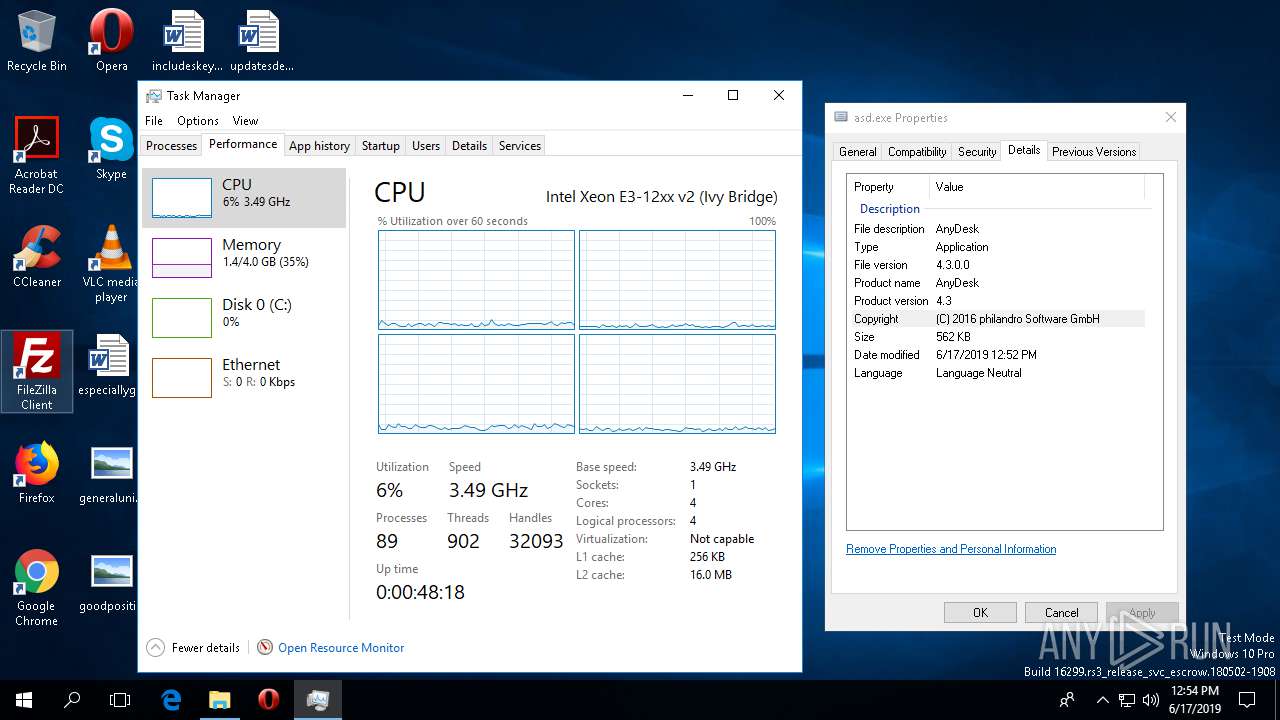
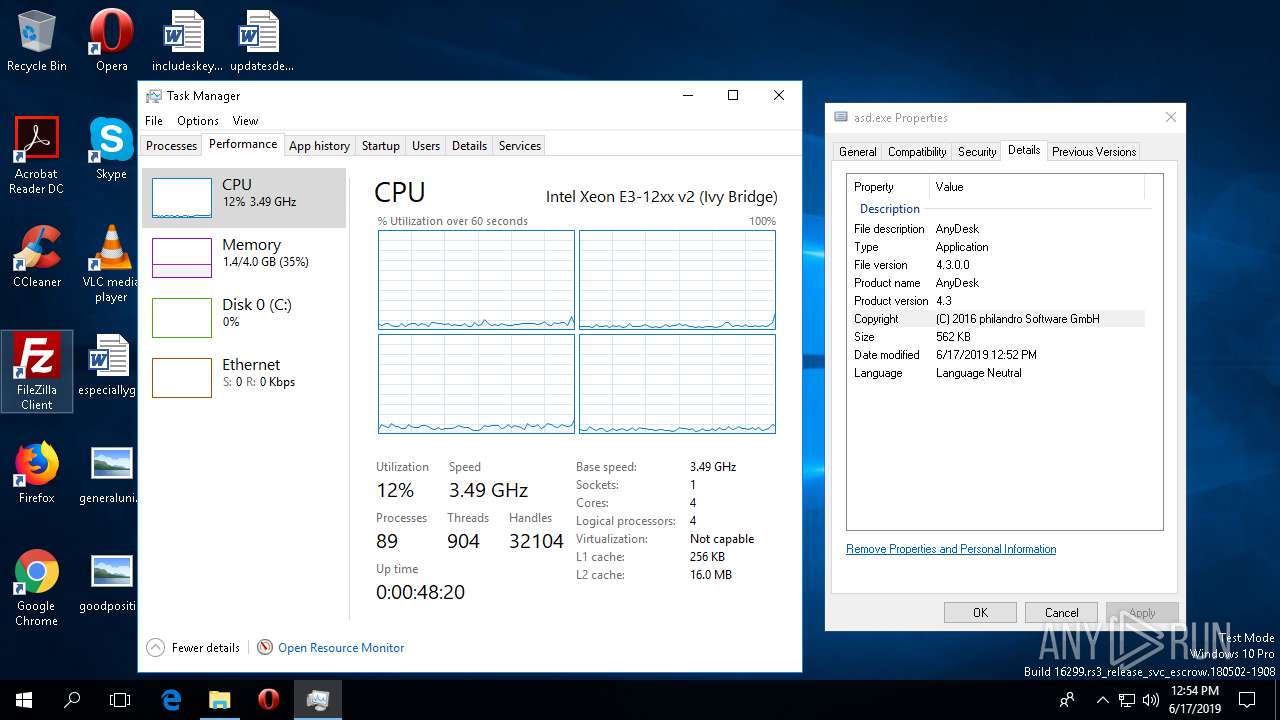
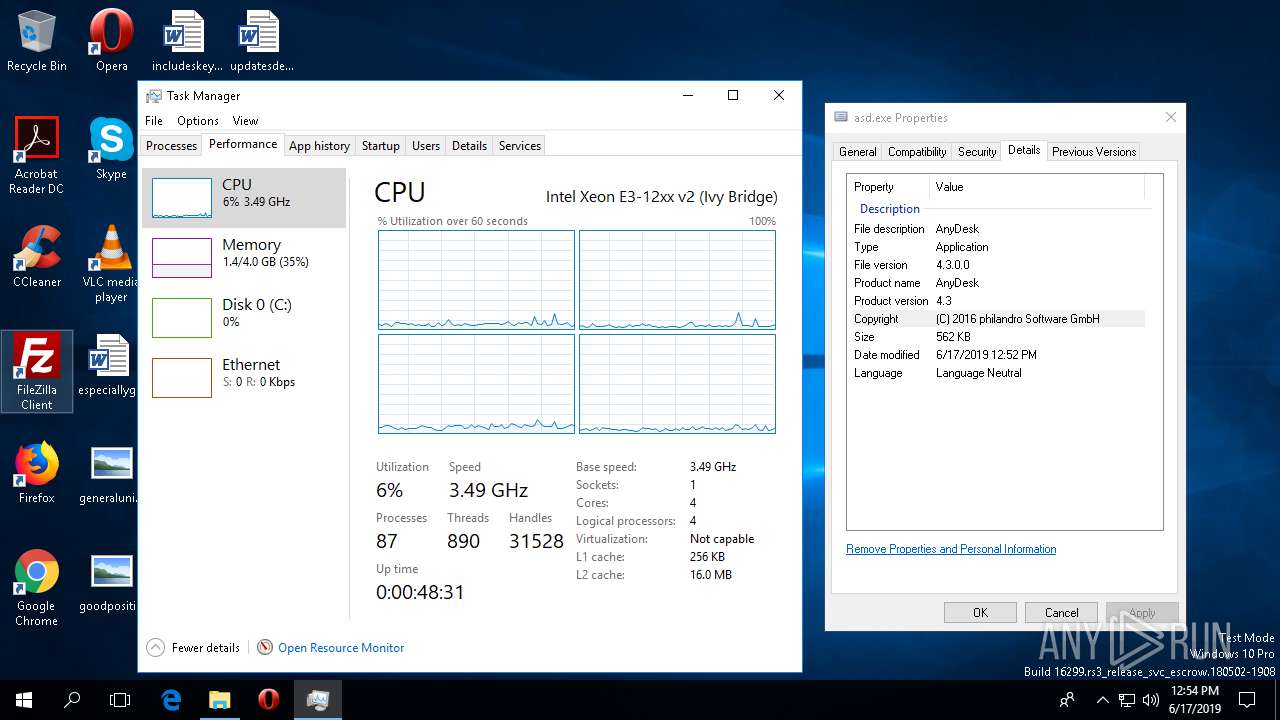
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F62F8C688B789D2DB52331DBE6C6C82B |
| SHA1: | 4AB2EC4234A50890D69E22D8F7285D7EC424795D |
| SHA256: | 0B5A148BF7714E06EF7545385F5659F041AC94E8004A919CA38D67A1A2FBBDB0 |
| SSDEEP: | 12288:uRHLLfdEQAj4NTRsiCxkjbIeTmM3+lt76BW/89Zwi8q8qkH2399+s:uFPd5TRsiCKhTmSutSWk9G8kH2Os |
MALICIOUS
Writes to a start menu file
- gsgf.exe (PID: 4508)
Connects to CnC server
- gsgf.exe (PID: 4444)
Detected artifacts of LokiBot
- gsgf.exe (PID: 4444)
Actions looks like stealing of personal data
- gsgf.exe (PID: 4444)
SUSPICIOUS
Creates files in the user directory
- asd.exe (PID: 1808)
- gsgf.exe (PID: 4508)
- gsgf.exe (PID: 4444)
Executed via COM
- sdiagnhost.exe (PID: 2256)
Executable content was dropped or overwritten
- msdt.exe (PID: 436)
- asd.exe (PID: 1808)
Reads the machine GUID from the registry
- msdt.exe (PID: 436)
- sdiagnhost.exe (PID: 2256)
- gsgf.exe (PID: 4444)
Starts itself from another location
- asd.exe (PID: 1808)
Application launched itself
- gsgf.exe (PID: 4508)
Connects to server without host name
- gsgf.exe (PID: 4444)
Checks supported languages
- taskmgr.exe (PID: 2580)
INFO
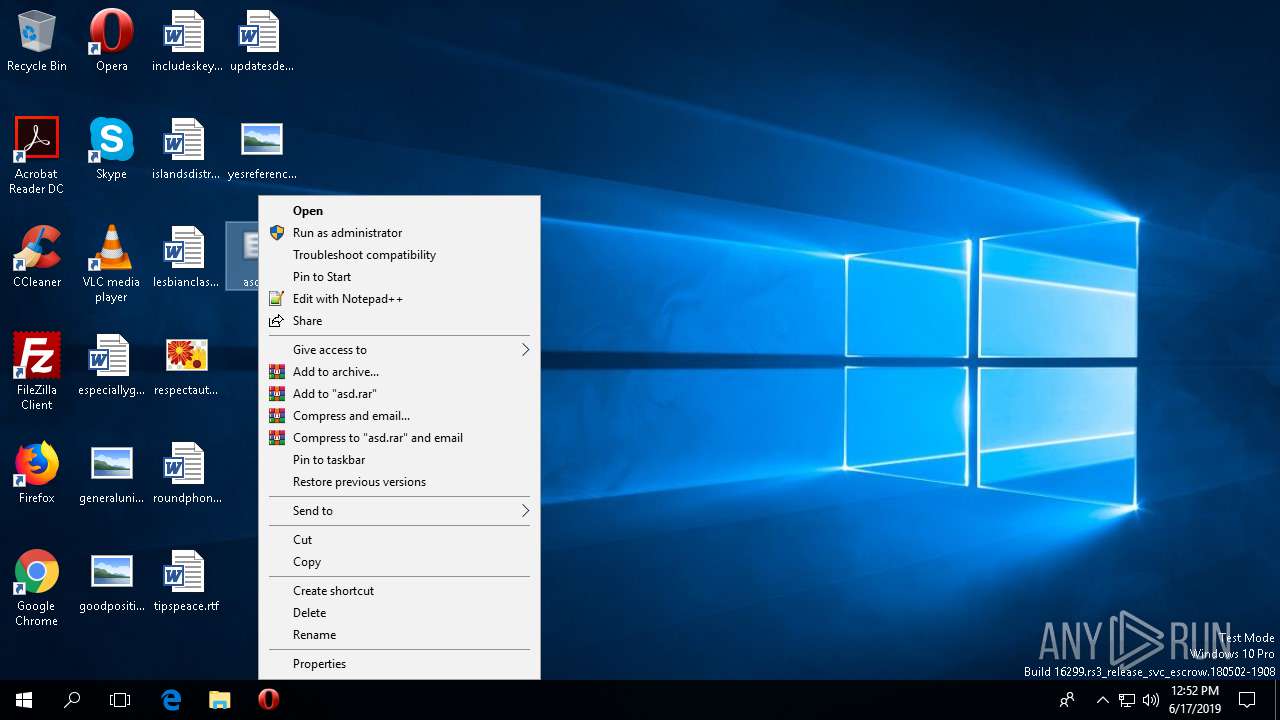
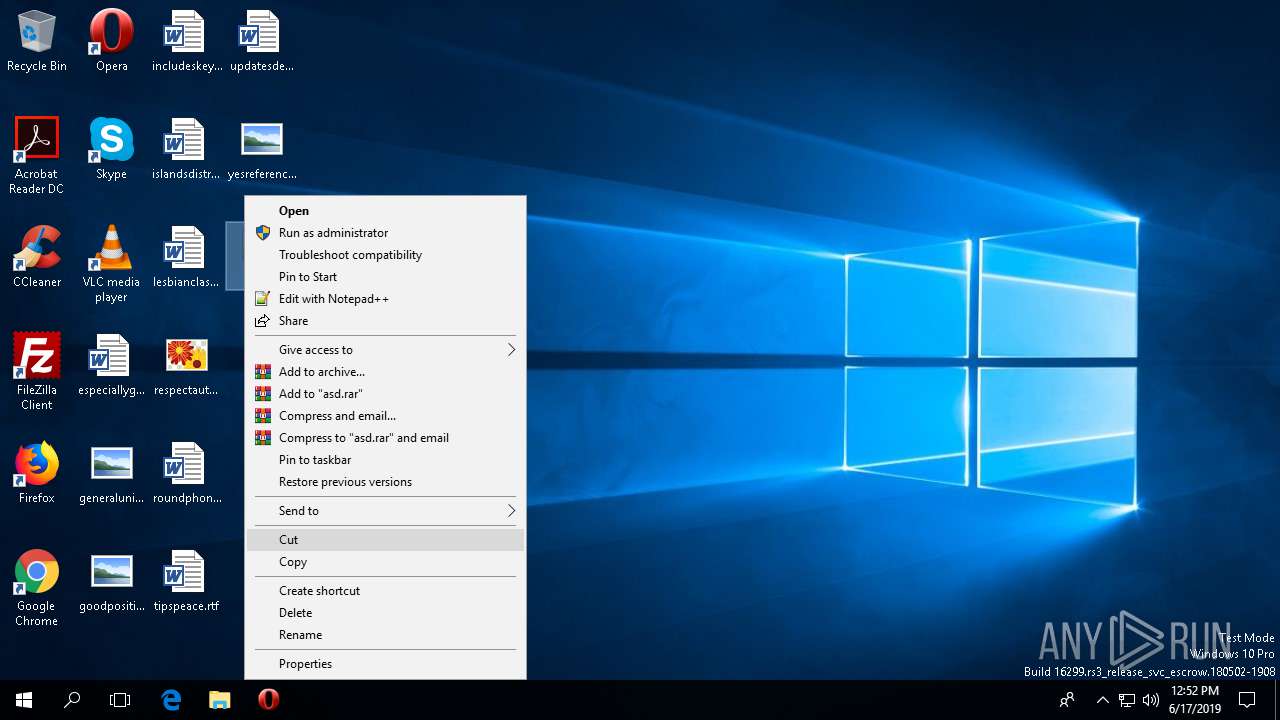
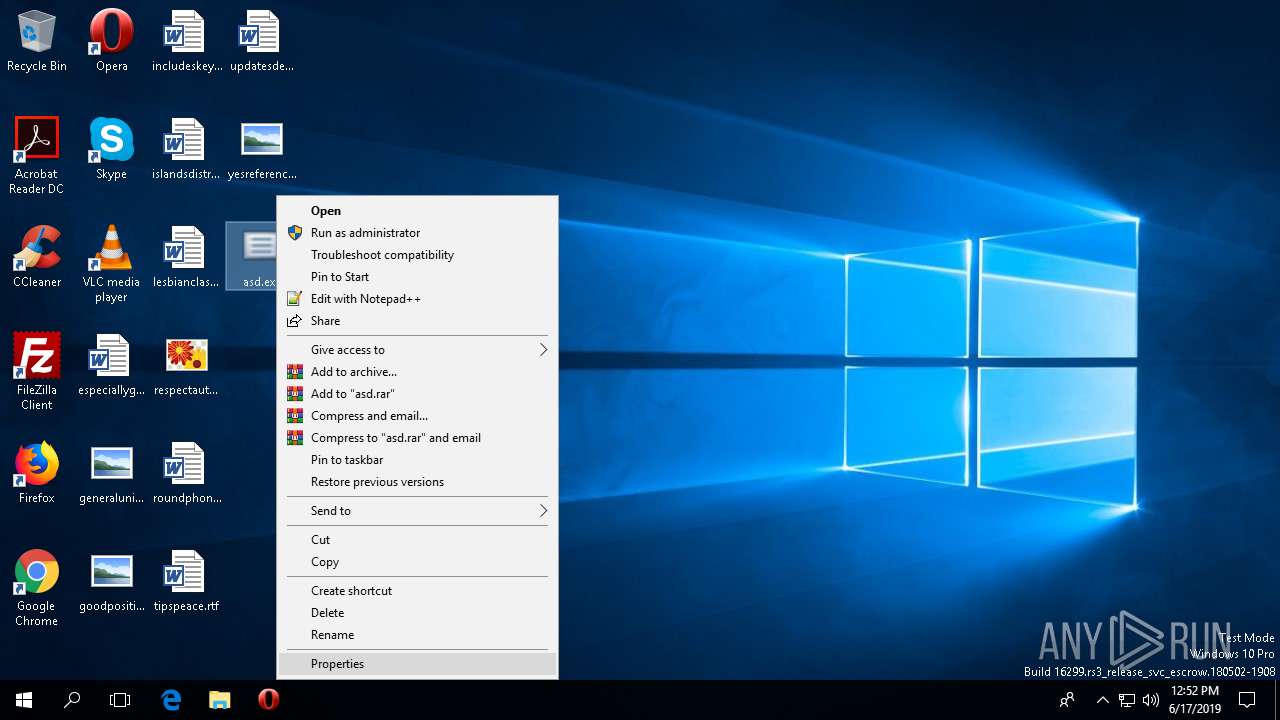
Manual execution by user
- pcwrun.exe (PID: 1640)
- taskmgr.exe (PID: 2504)
- taskmgr.exe (PID: 2580)
Reads the software policy settings
- msdt.exe (PID: 436)
Reads settings of System Certificates
- msdt.exe (PID: 436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:02:27 14:28:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 333312 |
| InitializedDataSize: | 241152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x524b4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.3.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
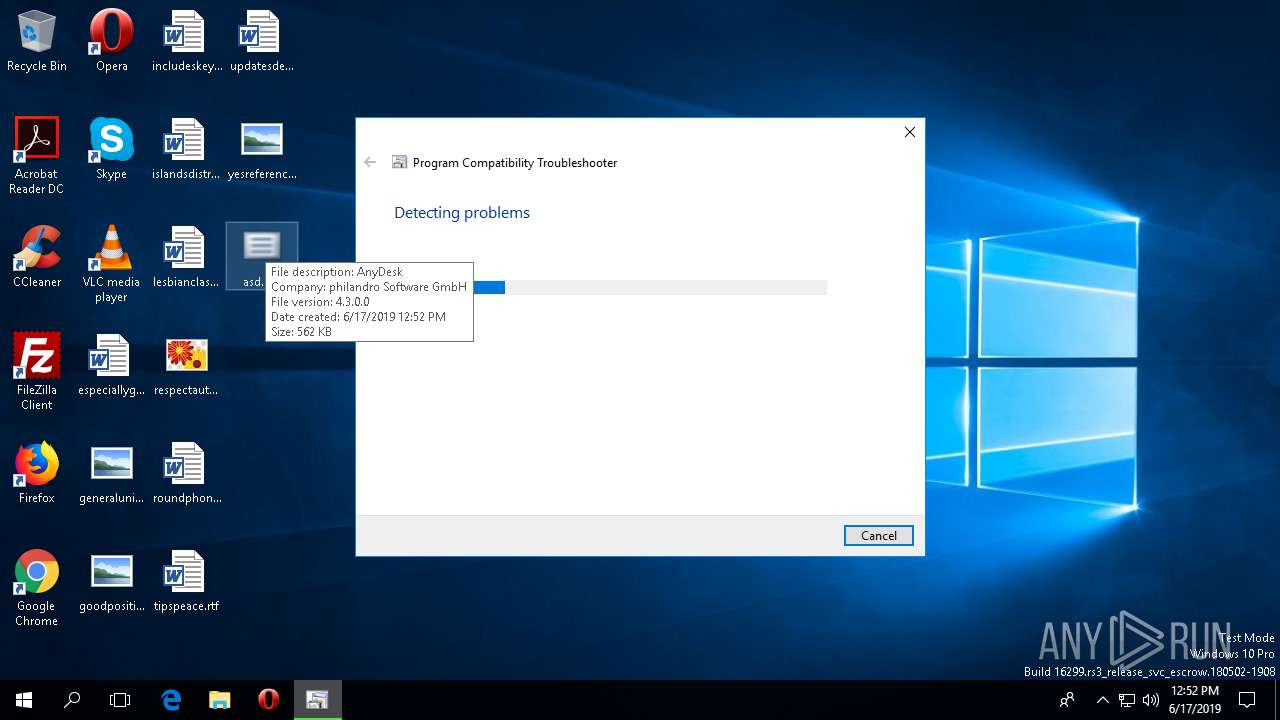
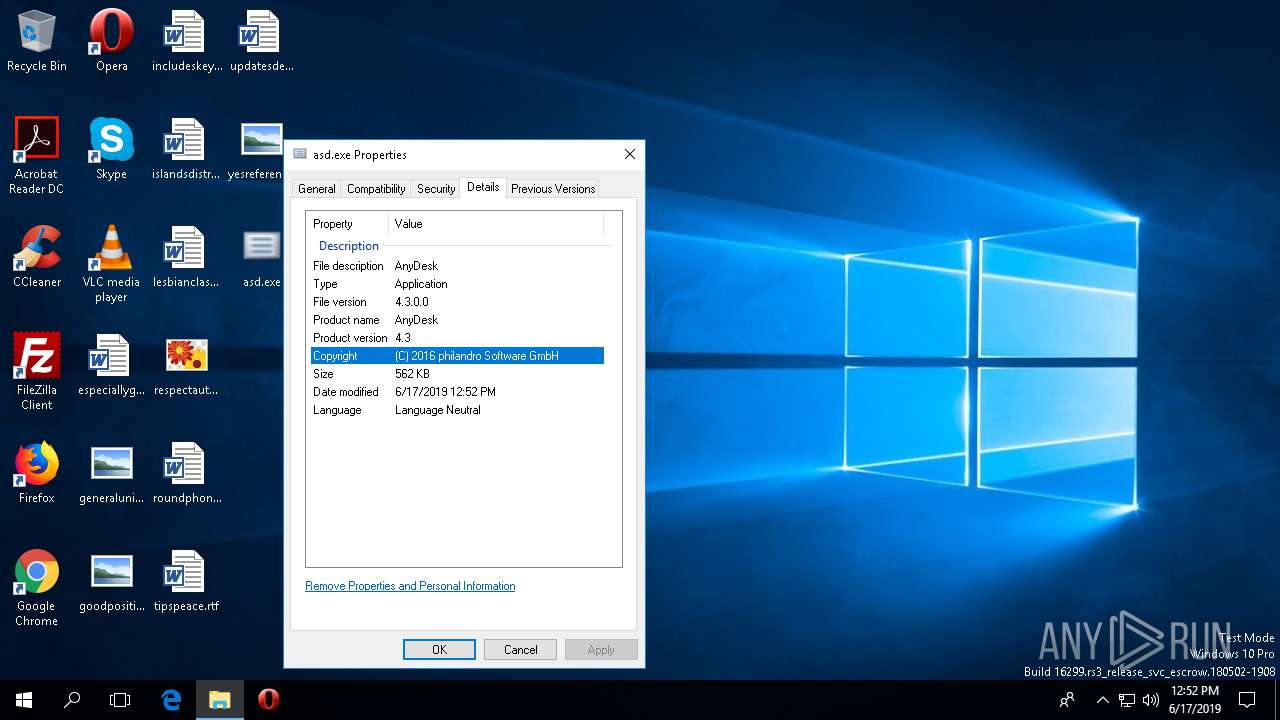
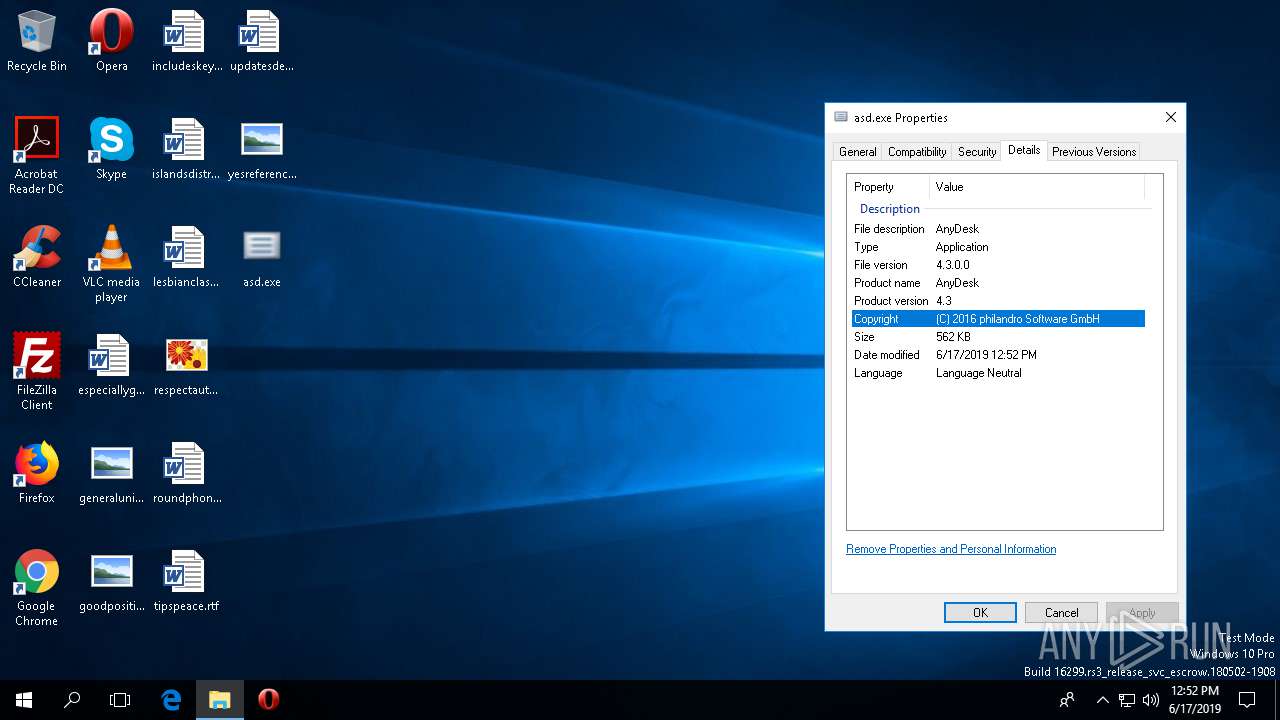
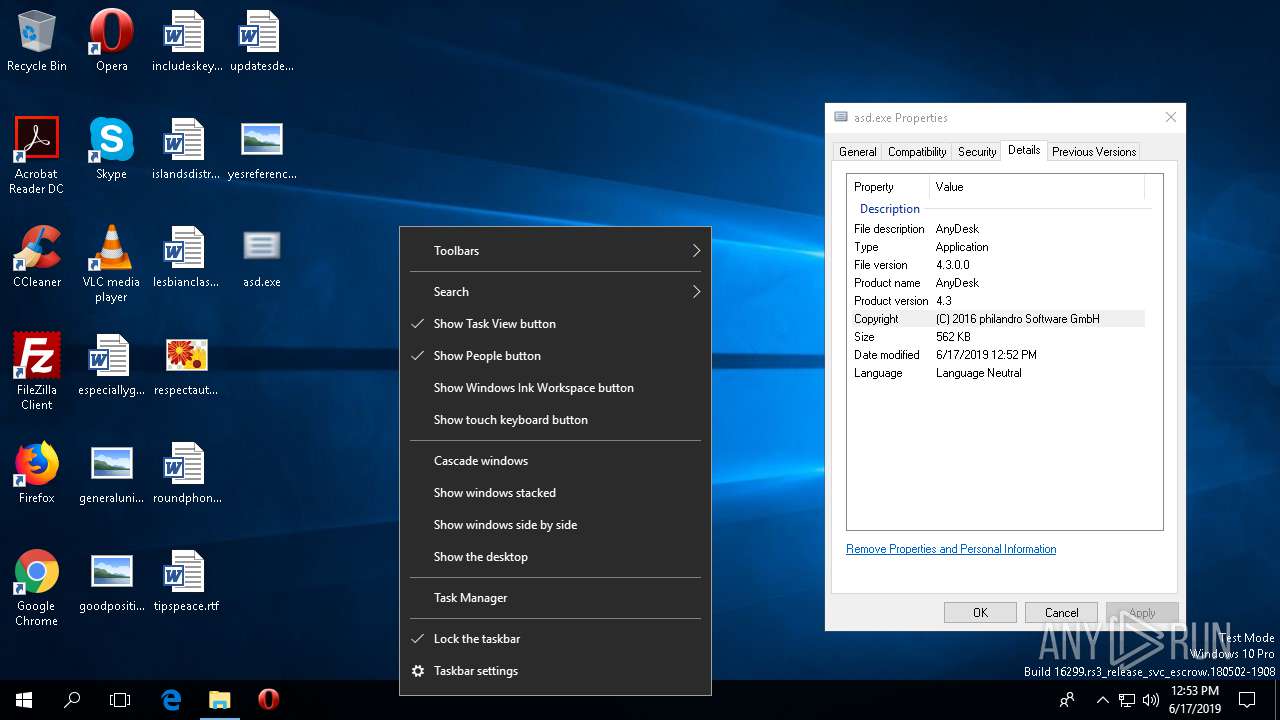
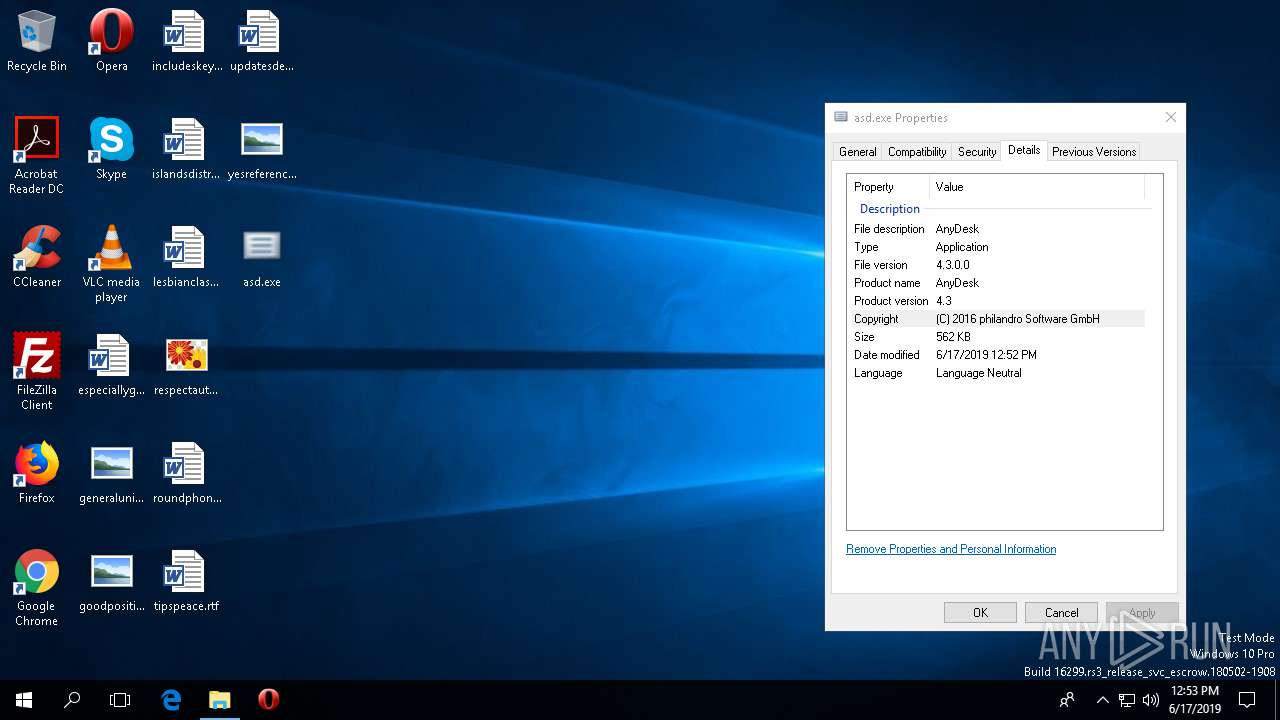
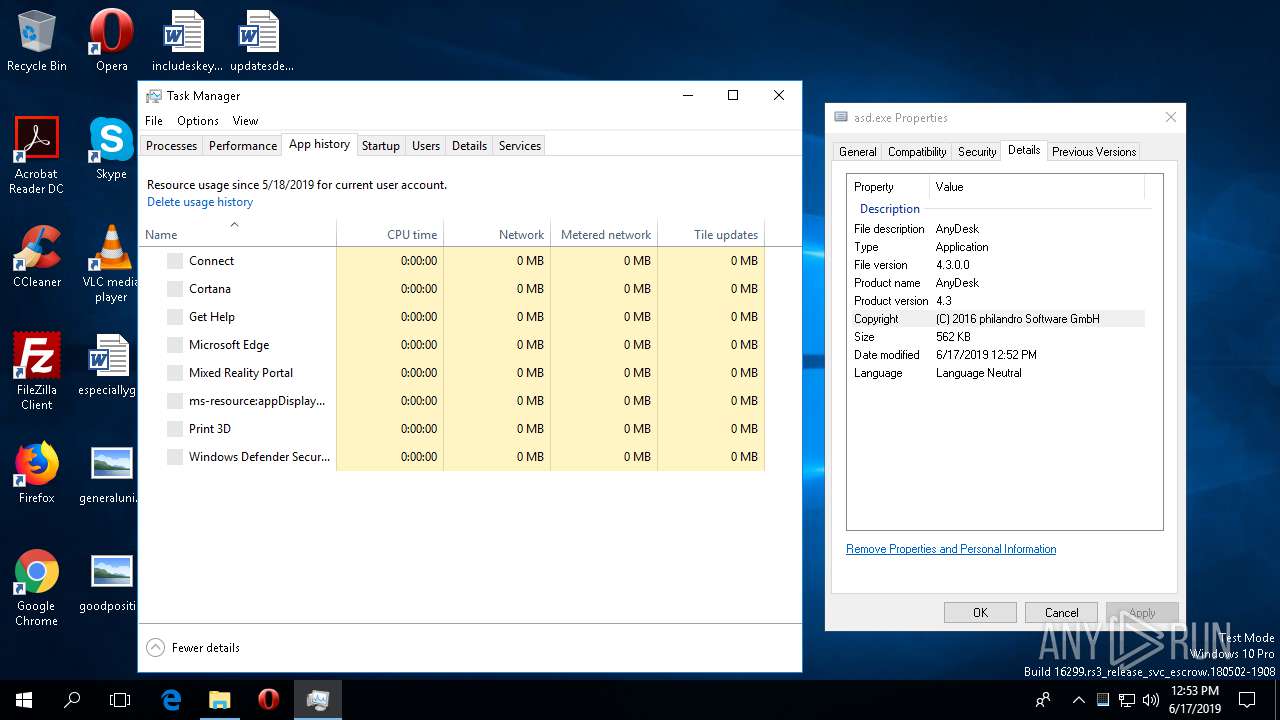
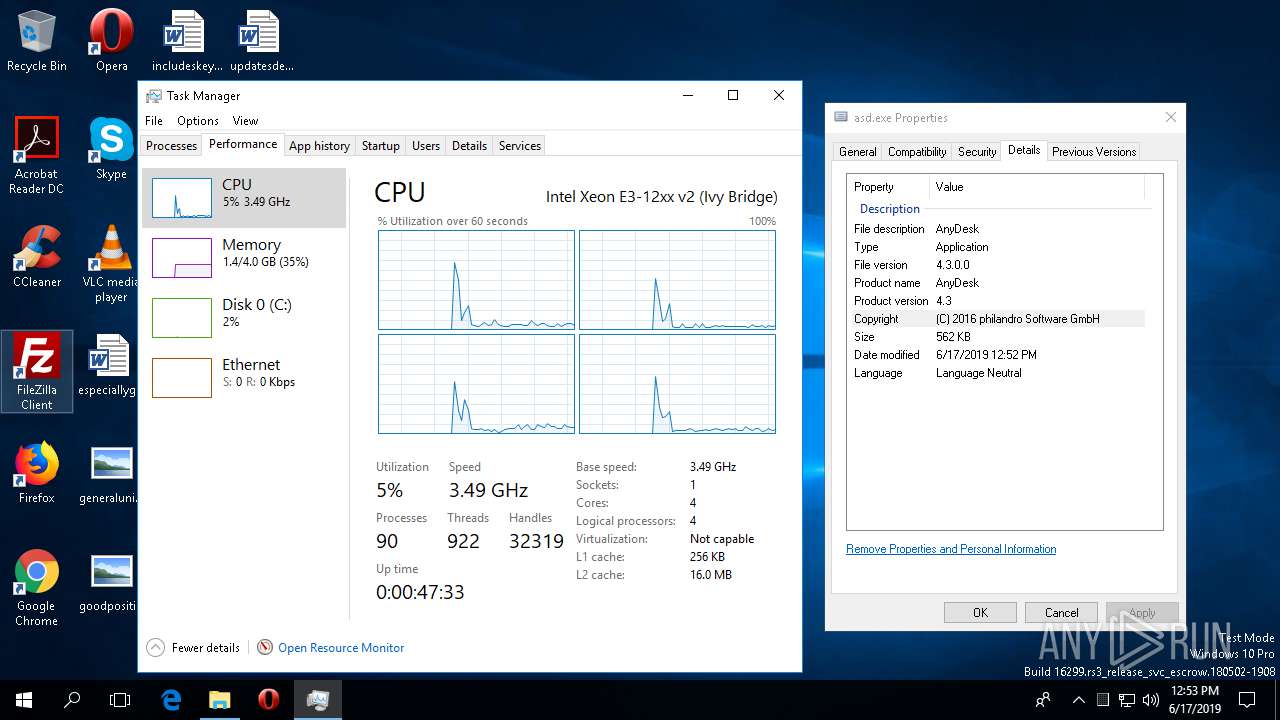
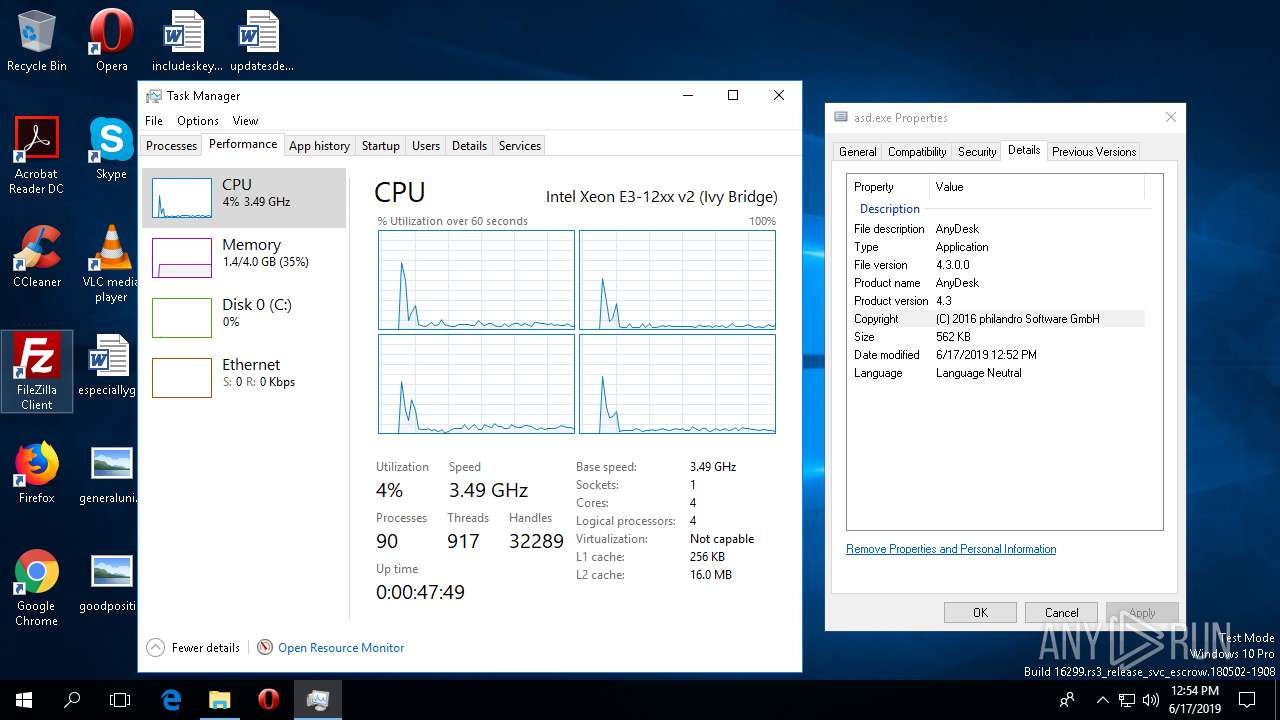
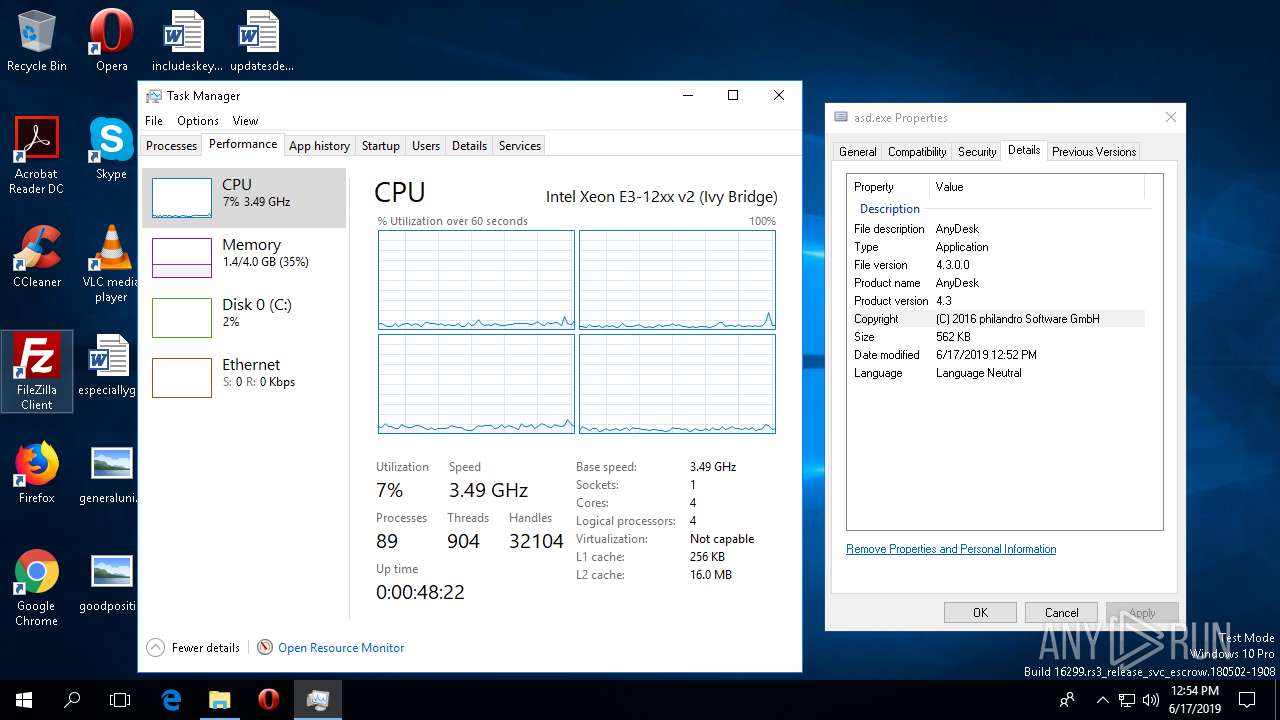
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 4.3.0.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 4.3 |
| LegalCopyright: | (C) 2016 philandro Software GmbH |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Feb-1992 13:28:50 |
| Detected languages: |
|
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 4.3.0.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 4.3 |
| LegalCopyright: | (C) 2016 philandro Software GmbH |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 27-Feb-1992 13:28:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000514FC | 0x00051600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51318 |
DATA | 0x00053000 | 0x000093A4 | 0x00009400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.95655 |
BSS | 0x0005D000 | 0x00000D01 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0005E000 | 0x00002010 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.86752 |
.tls | 0x00061000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00062000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 0x00063000 | 0x00005EF4 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.66092 |
.rsrc | 0x00069000 | 0x00029548 | 0x00029600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.89134 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.32229 | 600 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 2.81306 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.03061 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.17157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.57548 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
917 | 5.53142 | 892 | Latin 1 / Western European | English - United States | RT_BITMAP |
918 | 6.27806 | 892 | Latin 1 / Western European | English - United States | RT_BITMAP |
919 | 6.9758 | 892 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
version.dll |
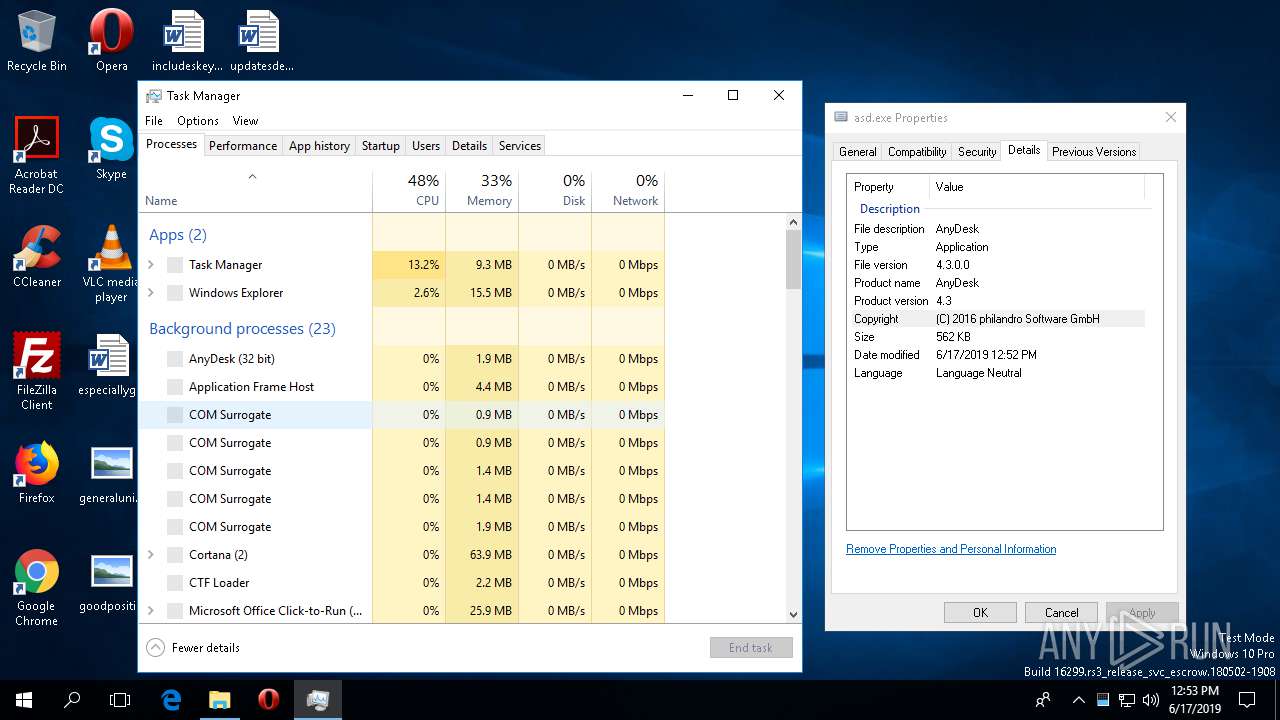
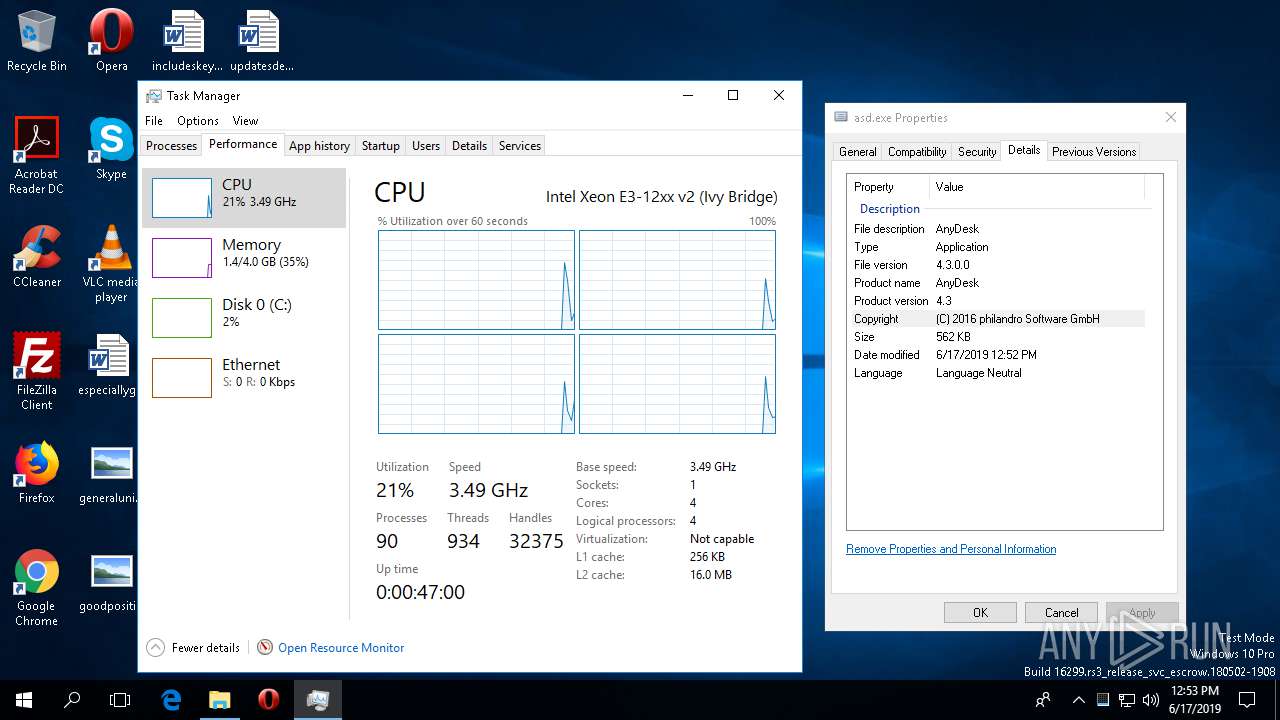
Total processes
100
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | C:\WINDOWS\System32\msdt.exe -path C:\WINDOWS\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCW91B.xml /skip TRUE | C:\WINDOWS\System32\msdt.exe | pcwrun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1640 | C:\WINDOWS\system32\pcwrun.exe "C:\Users\admin\Desktop\asd.exe" ContextMenu | C:\WINDOWS\system32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1808 | "C:\Users\admin\Desktop\asd.exe" | C:\Users\admin\Desktop\asd.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\System32\sdiagnhost.exe -Embedding | C:\WINDOWS\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
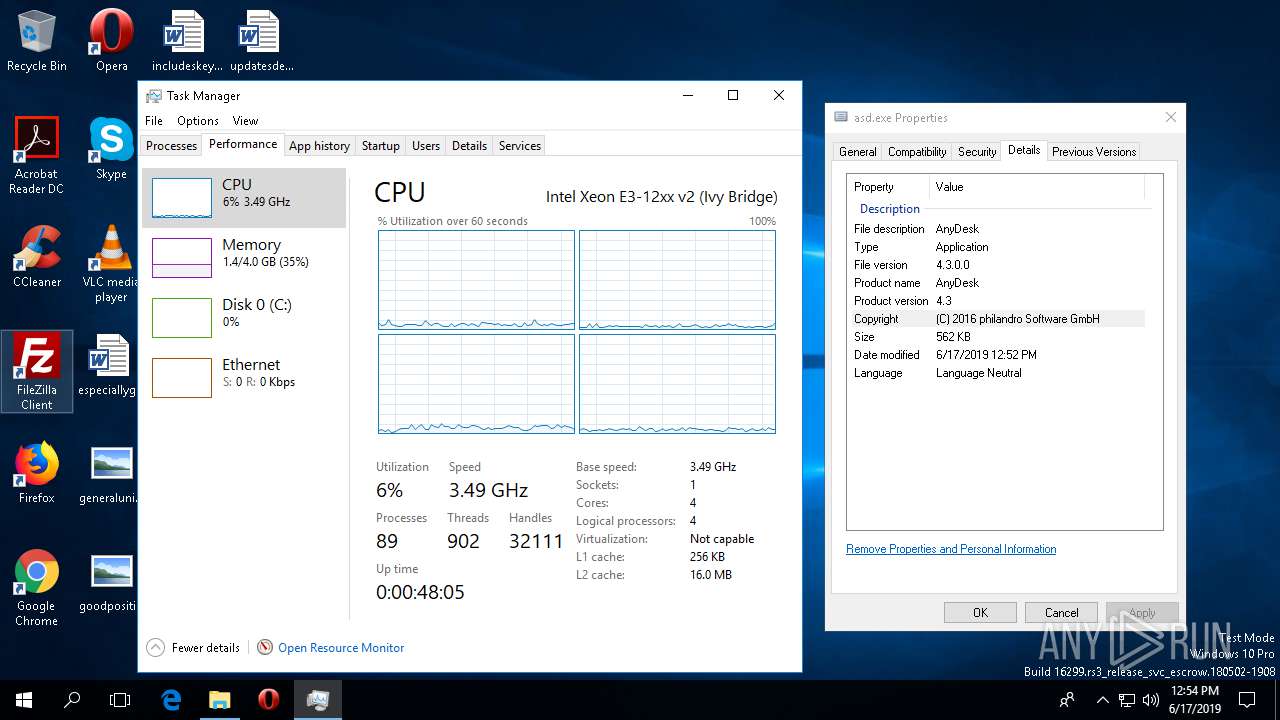
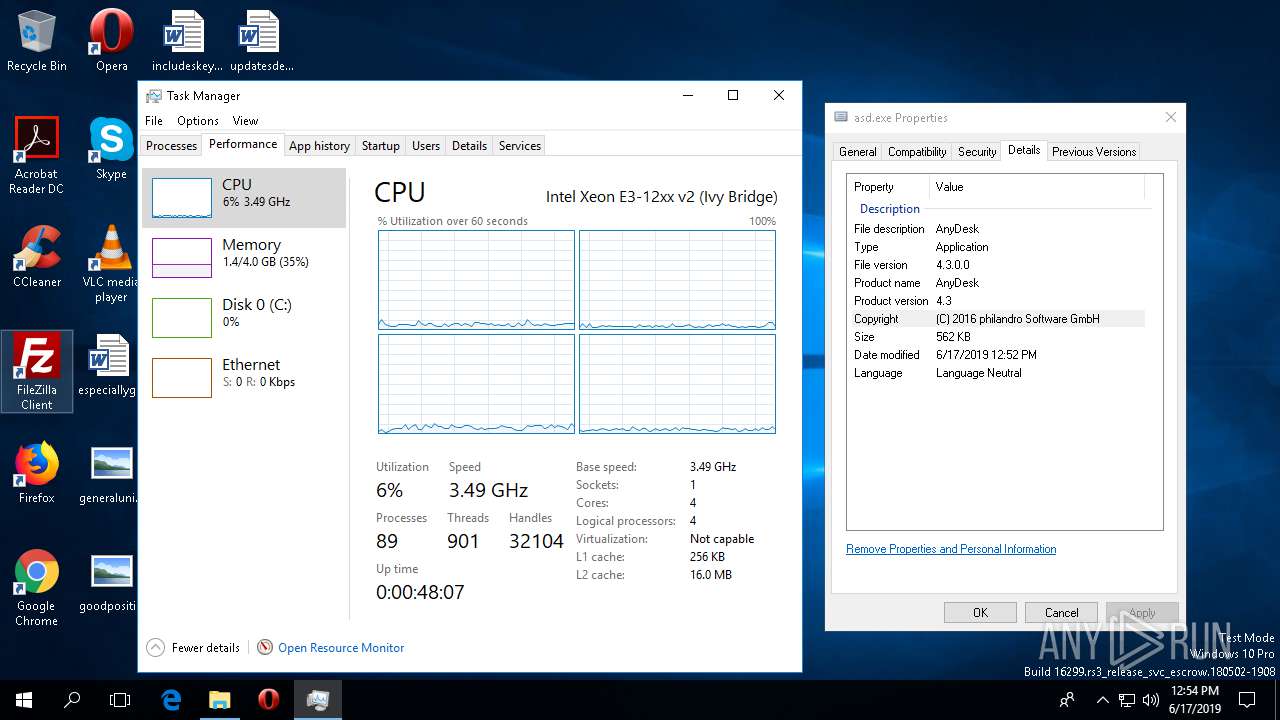
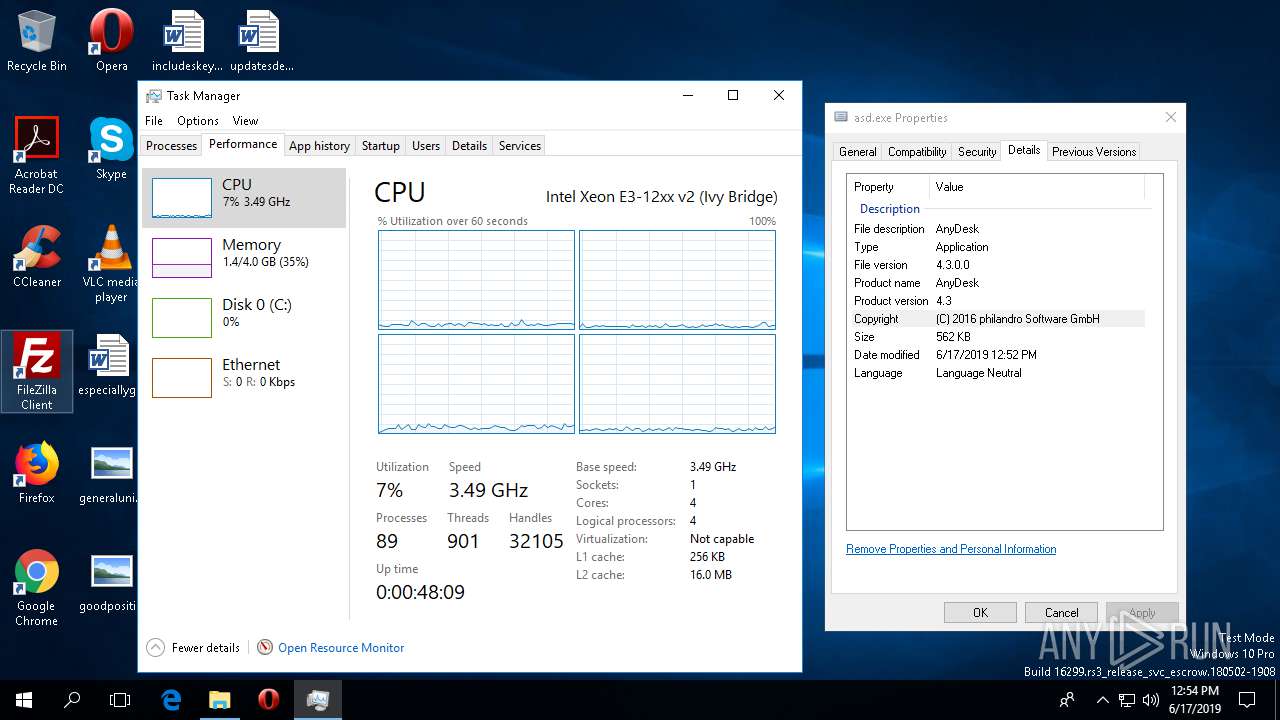
| 2504 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\WINDOWS\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\WINDOWS\system32\taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4444 | "C:\Users\admin\AppData\Roaming\vugjsw\gsgf.exe" | C:\Users\admin\AppData\Roaming\vugjsw\gsgf.exe | gsgf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4508 | "C:\Users\admin\AppData\Roaming\vugjsw\gsgf.exe" | C:\Users\admin\AppData\Roaming\vugjsw\gsgf.exe | asd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
961
Read events
941
Write events
20
Delete events
0
Modification events
| (PID) Process: | (436) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\22\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4444) gsgf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4444) gsgf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4444) gsgf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2580) taskmgr.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\22\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
3
Suspicious files
2
Text files
15
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1808 | asd.exe | C:\Users\admin\AppData\Roaming\vugjsw\gsgf.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 436 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_396243f1-f559-4e68-a8cb-4922d9caac8b\result\DebugReport.xml | — | |
MD5:— | SHA256:— | |||
| 436 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_396243f1-f559-4e68-a8cb-4922d9caac8b\result\ResultReport.xml | — | |
MD5:— | SHA256:— | |||
| 436 | msdt.exe | C:\Users\admin\AppData\Local\Diagnostics\733862231\2019061712.000\DebugReport.xml | — | |
MD5:— | SHA256:— | |||
| 436 | msdt.exe | C:\Users\admin\AppData\Local\Temp\PLA12A1.tmp | — | |
MD5:— | SHA256:— | |||
| 436 | msdt.exe | C:\Users\admin\AppData\Local\Temp\PLA544F.tmp | — | |
MD5:— | SHA256:— | |||
| 436 | msdt.exe | C:\Users\admin\AppData\Local\Temp\PLA1DF5.tmp | — | |
MD5:— | SHA256:— | |||
| 436 | msdt.exe | C:\Users\admin\AppData\Local\Temp\PLA3D65.tmp | — | |
MD5:— | SHA256:— | |||
| 436 | msdt.exe | C:\Users\admin\AppData\Local\Temp\PLA309F.tmp | — | |
MD5:— | SHA256:— | |||
| 1640 | pcwrun.exe | C:\Users\admin\AppData\Local\Temp\PCW91B.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4444 | gsgf.exe | POST | — | 93.126.60.184:80 | http://93.126.60.184/kas/4/cat.php | IR | — | — | malicious |
4444 | gsgf.exe | POST | — | 93.126.60.184:80 | http://93.126.60.184/kas/4/cat.php | IR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4444 | gsgf.exe | 93.126.60.184:80 | — | Asmanfaraz Sepahan Isdp (pjs) | IR | malicious |
— | — | 93.126.60.184:80 | — | Asmanfaraz Sepahan Isdp (pjs) | IR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nexusrules.officeapps.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4444 | gsgf.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
4444 | gsgf.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
4444 | gsgf.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
4444 | gsgf.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
4444 | gsgf.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
4444 | gsgf.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
4444 | gsgf.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |