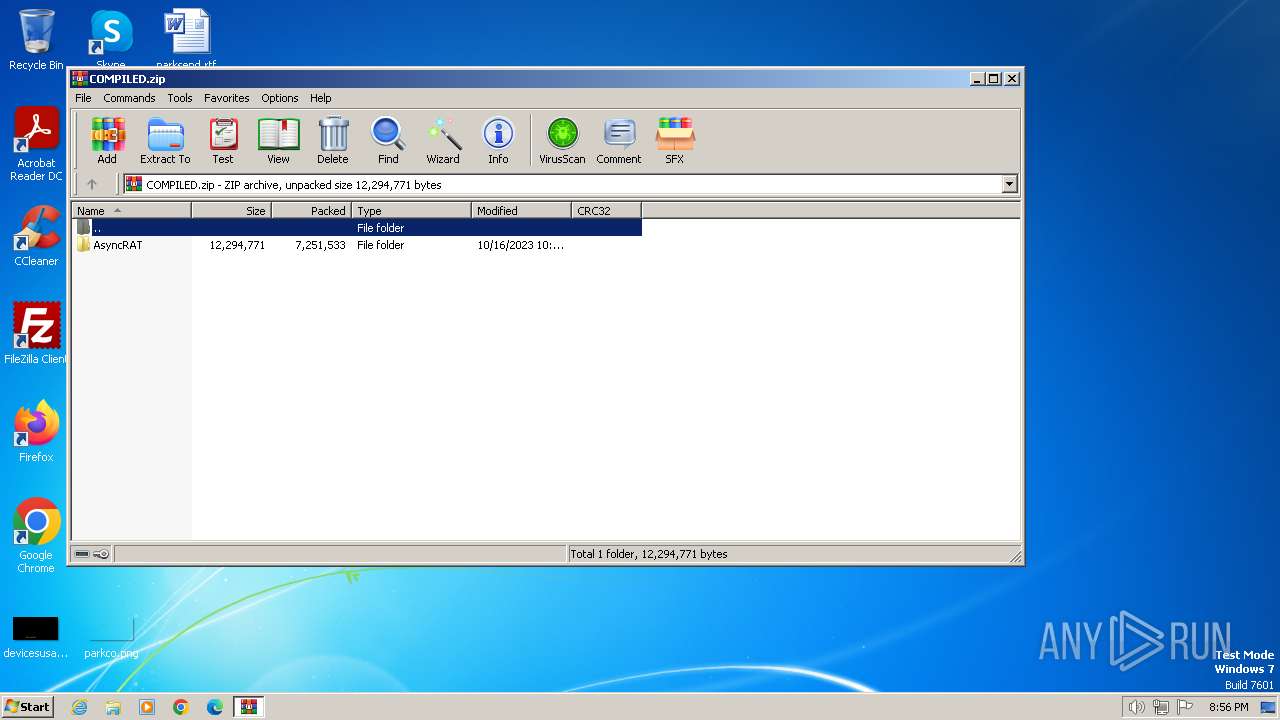
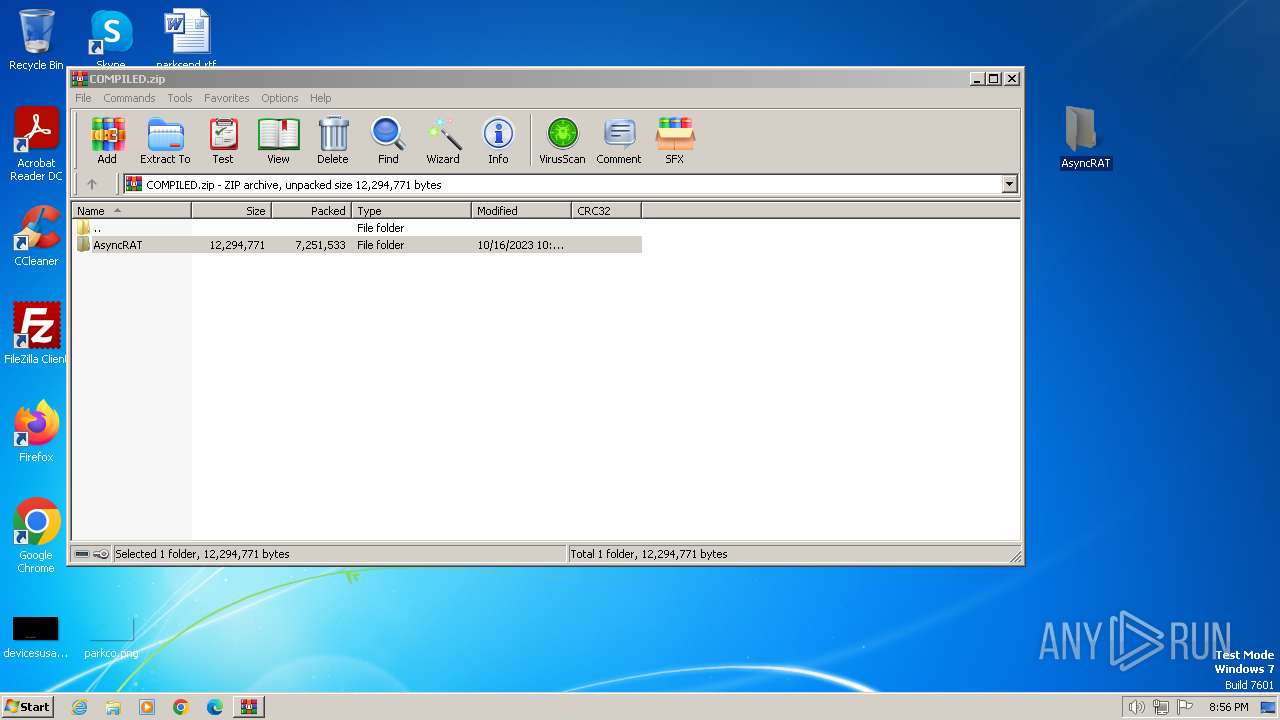
| download: | /NYAN-x-CAT/AsyncRAT-C-Sharp/releases/download/v0.5.8/COMPILED.zip |
| Full analysis: | https://app.any.run/tasks/acaf5eb4-8d9a-4ca0-9592-aa2998fb3e93 |
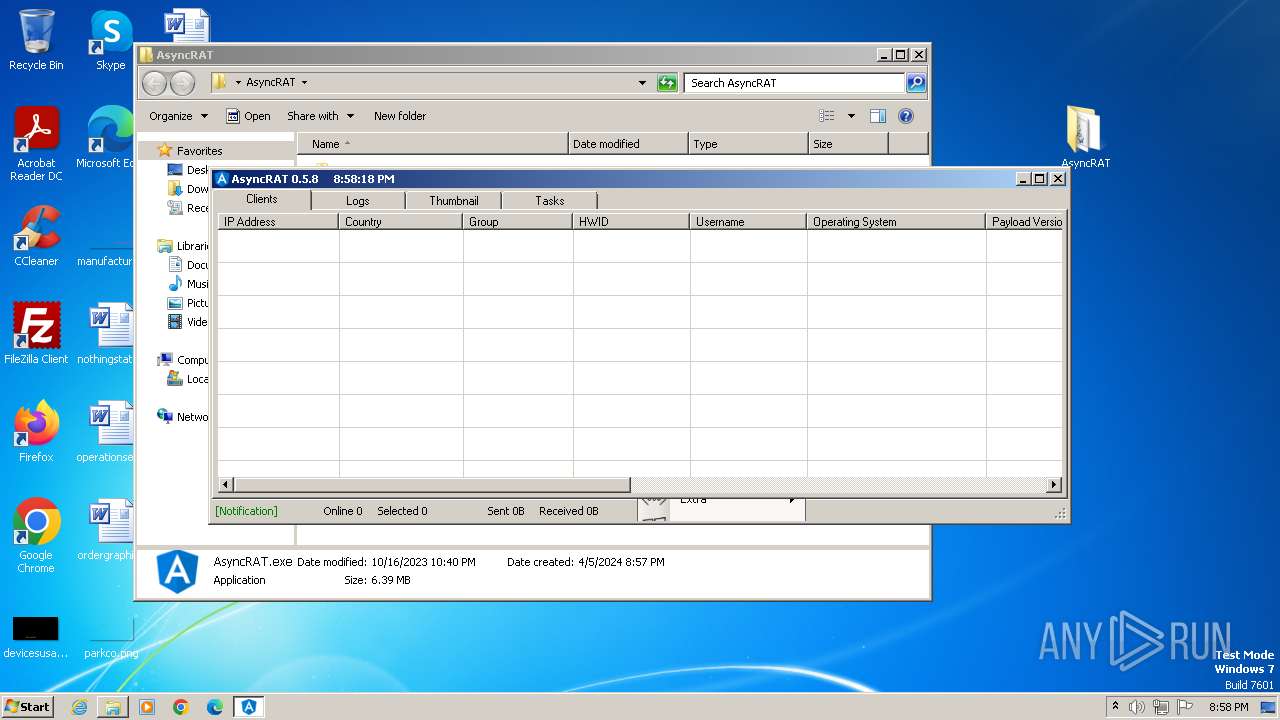
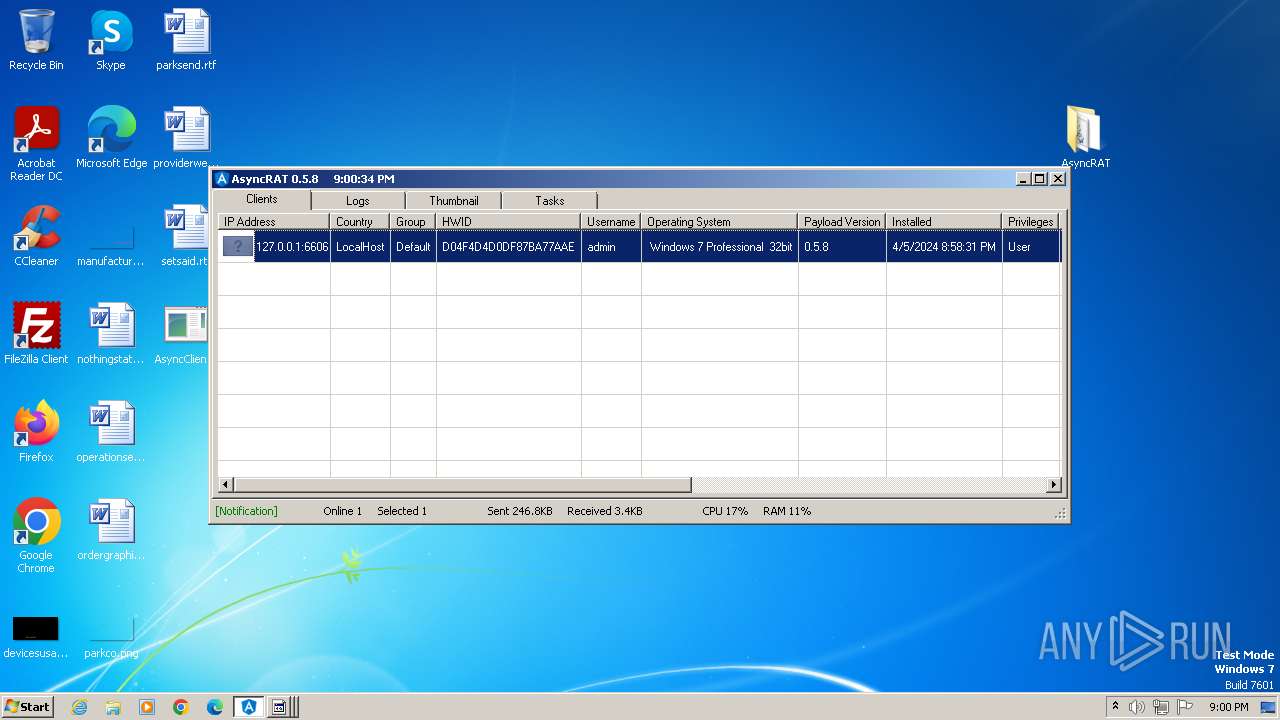
| Verdict: | Malicious activity |
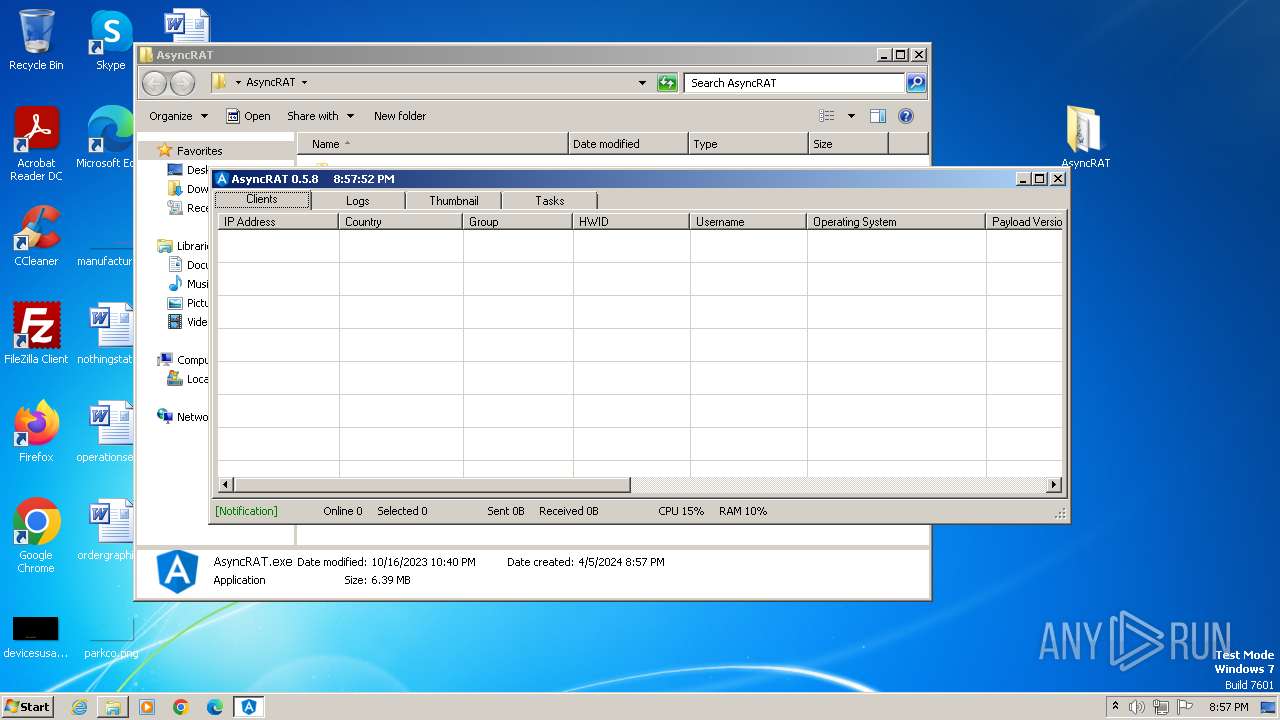
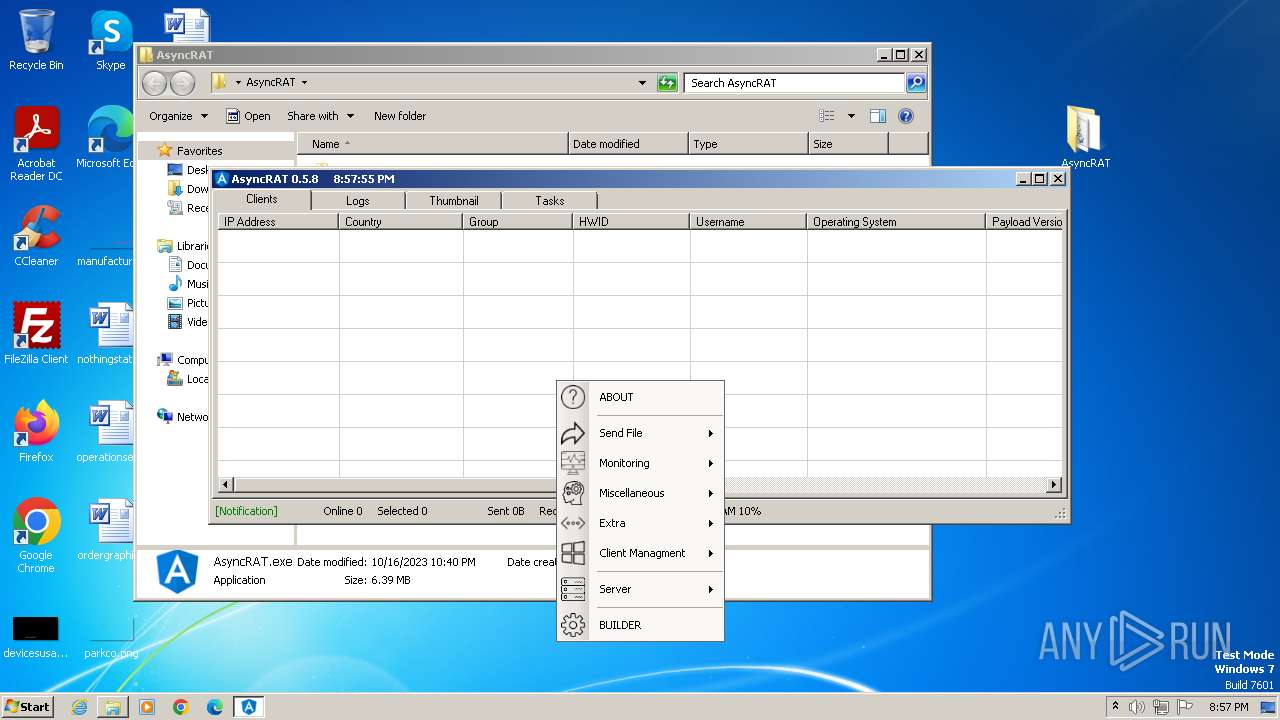
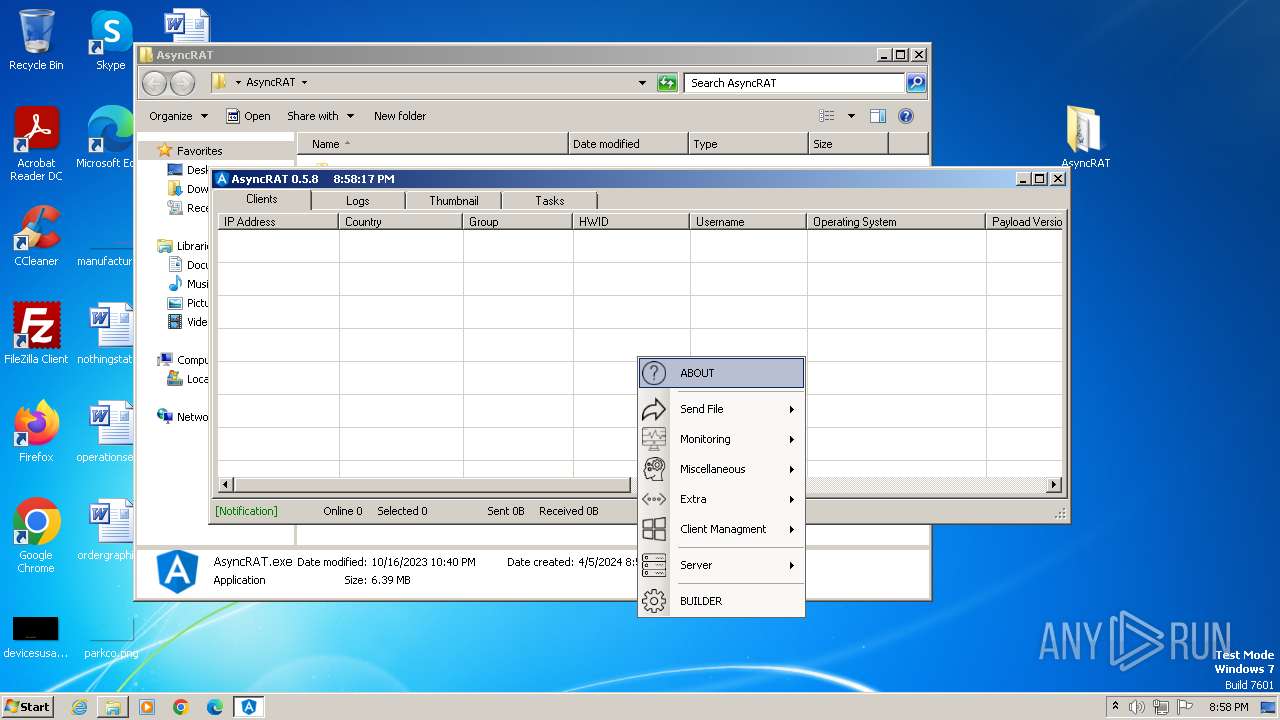
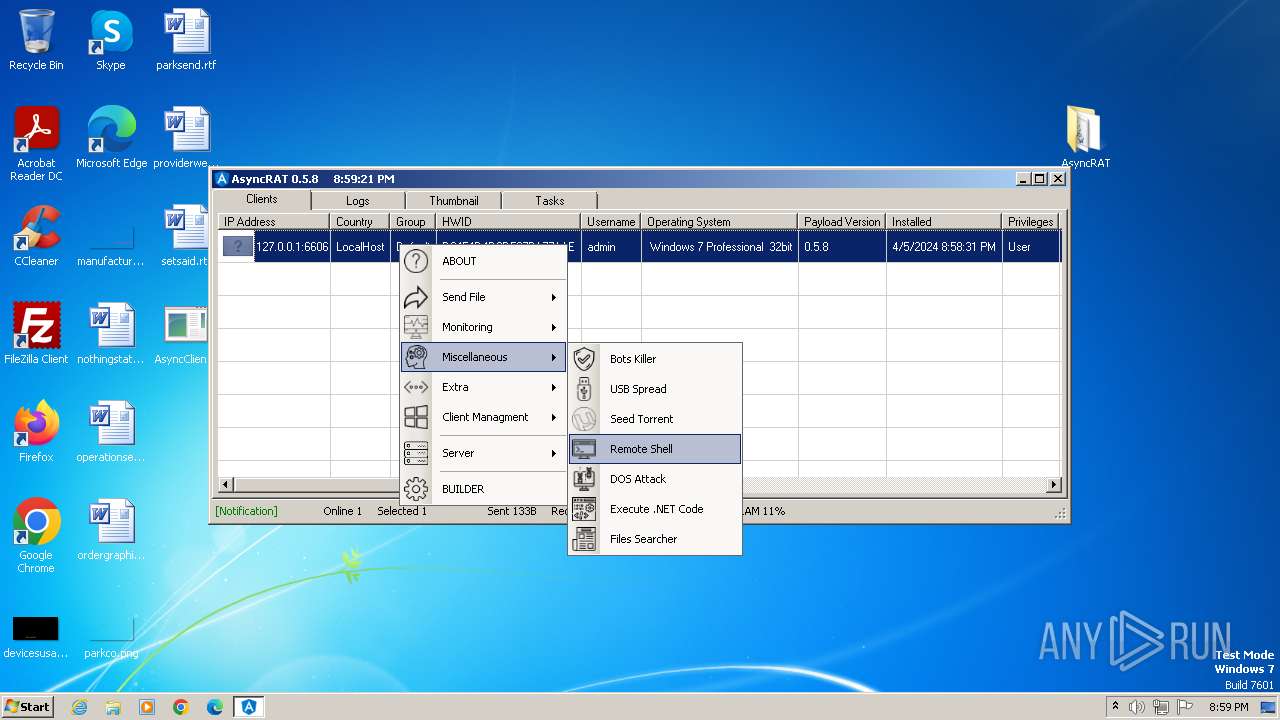
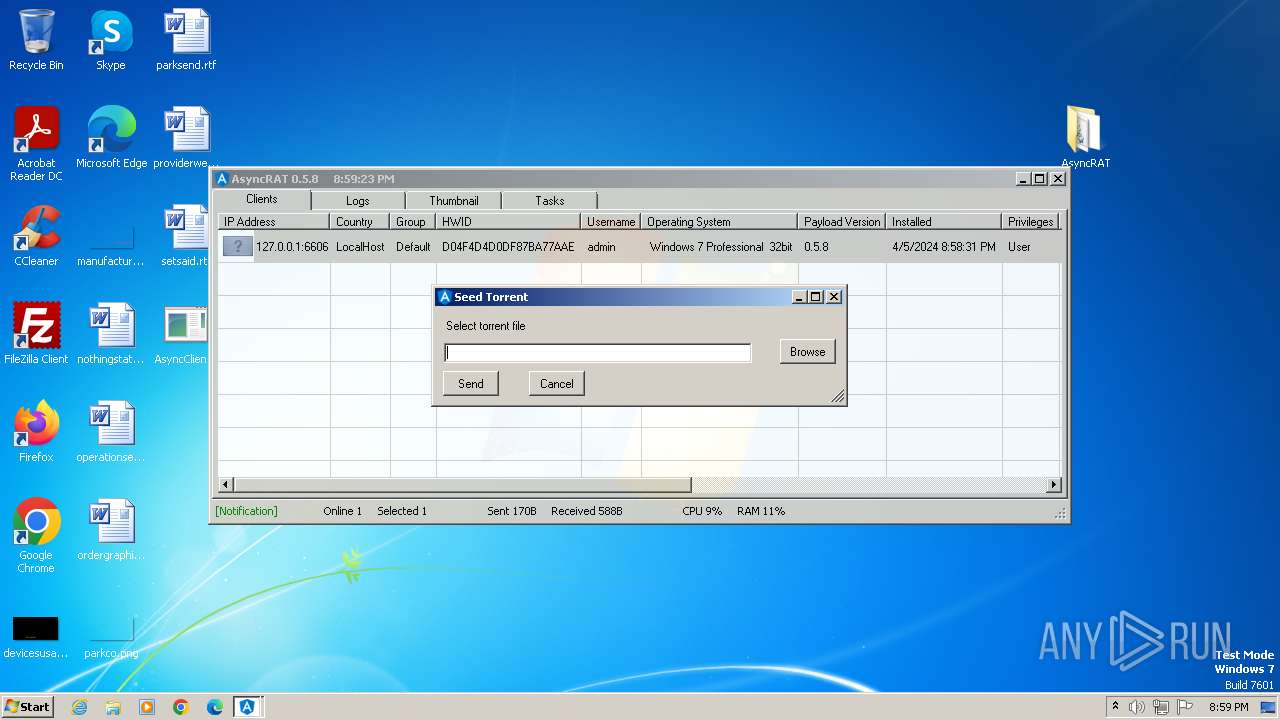
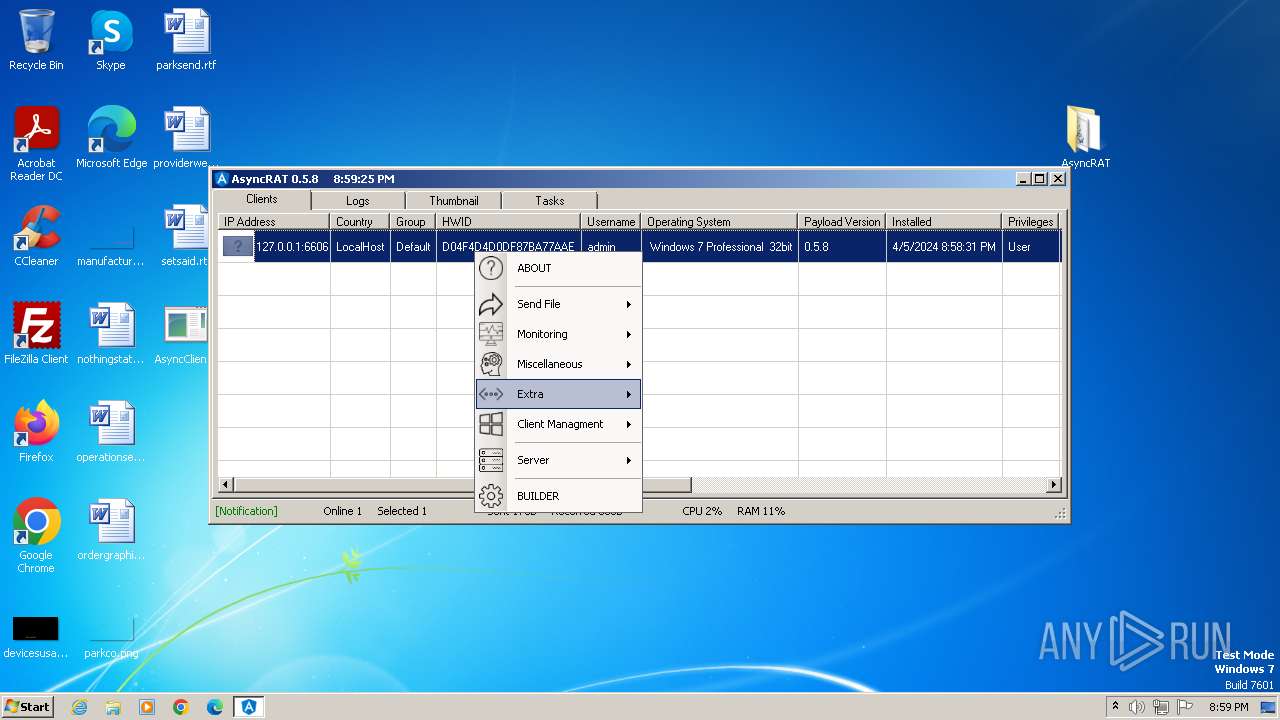
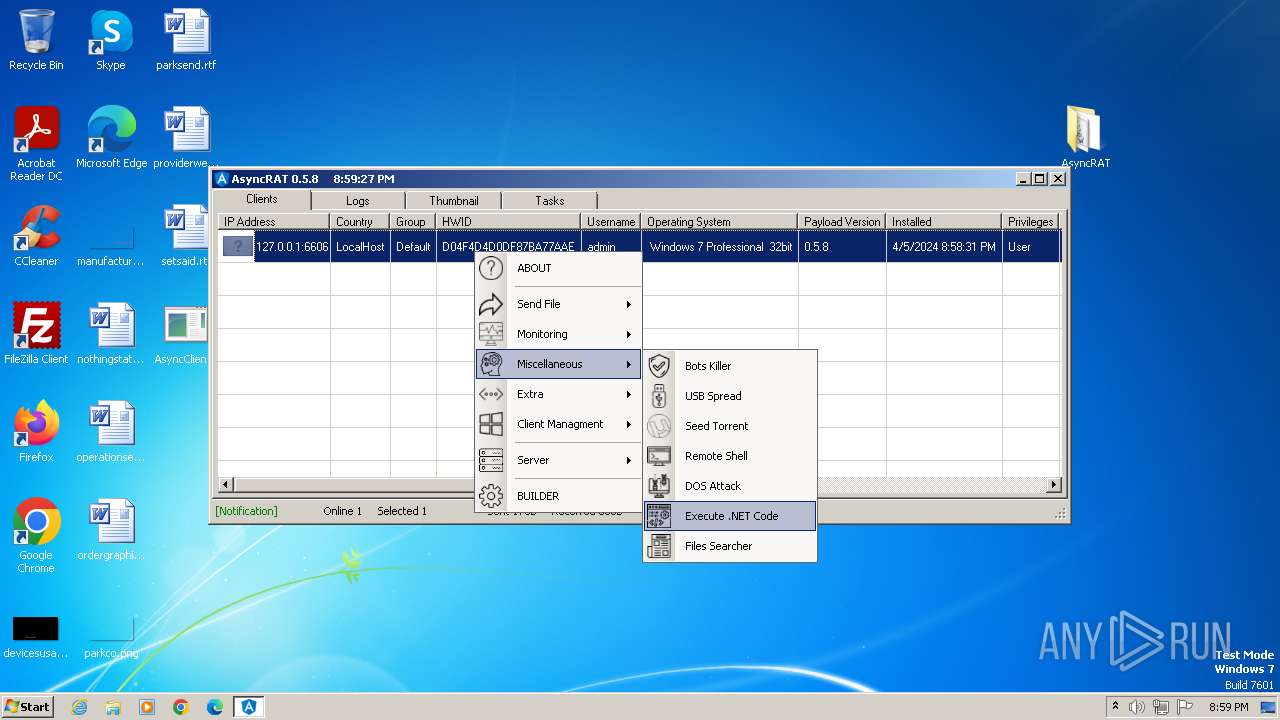
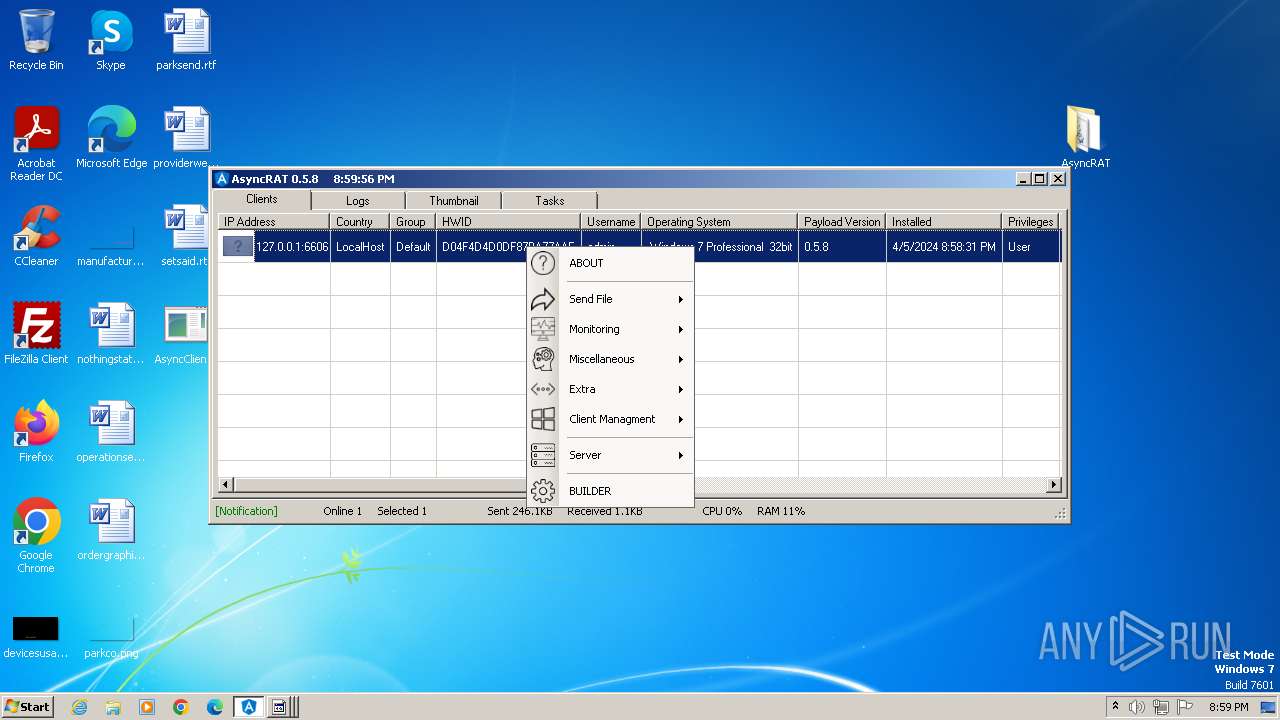
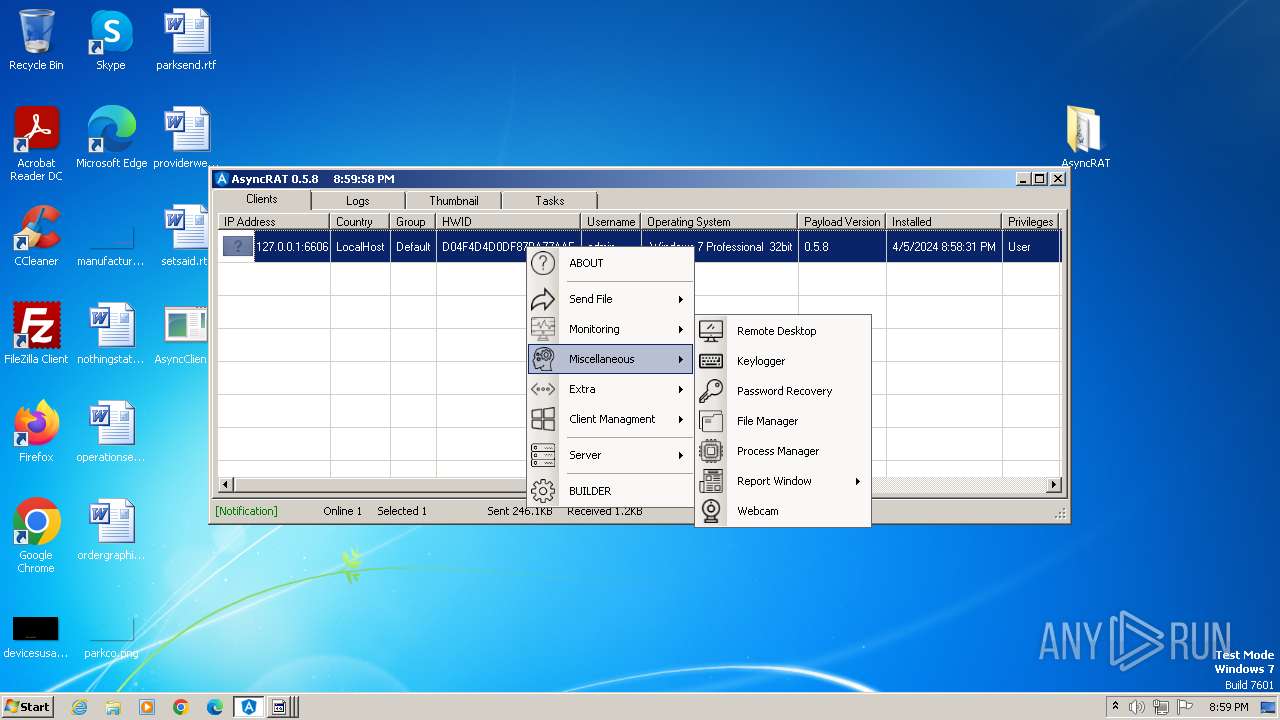
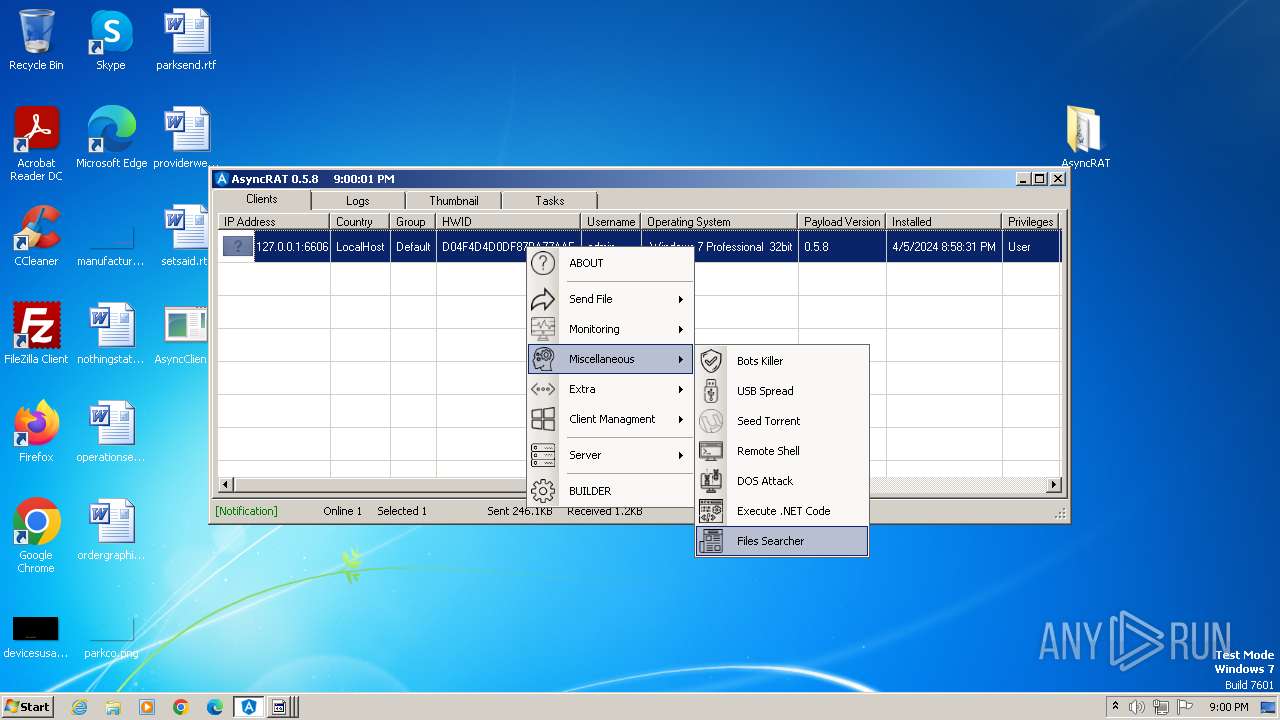
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 05, 2024, 19:56:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 30B1961A9B56972841A3806E716531D7 |
| SHA1: | 63C6880D936A60FEFC43A51715036C93265A4AE5 |
| SHA256: | 0B29711EC115C27F4CD6963B9EA1E4FEBF15624F1C17D1C018611EE3DF8C333C |
| SSDEEP: | 98304:5shr/UvjaKkkrapH/ykDAAvFMfMSsjEmNRP3V6JnS1RSlsg5qEUfZamMw2tThdyJ:7QqJJQR/8WIidOU |
MALICIOUS
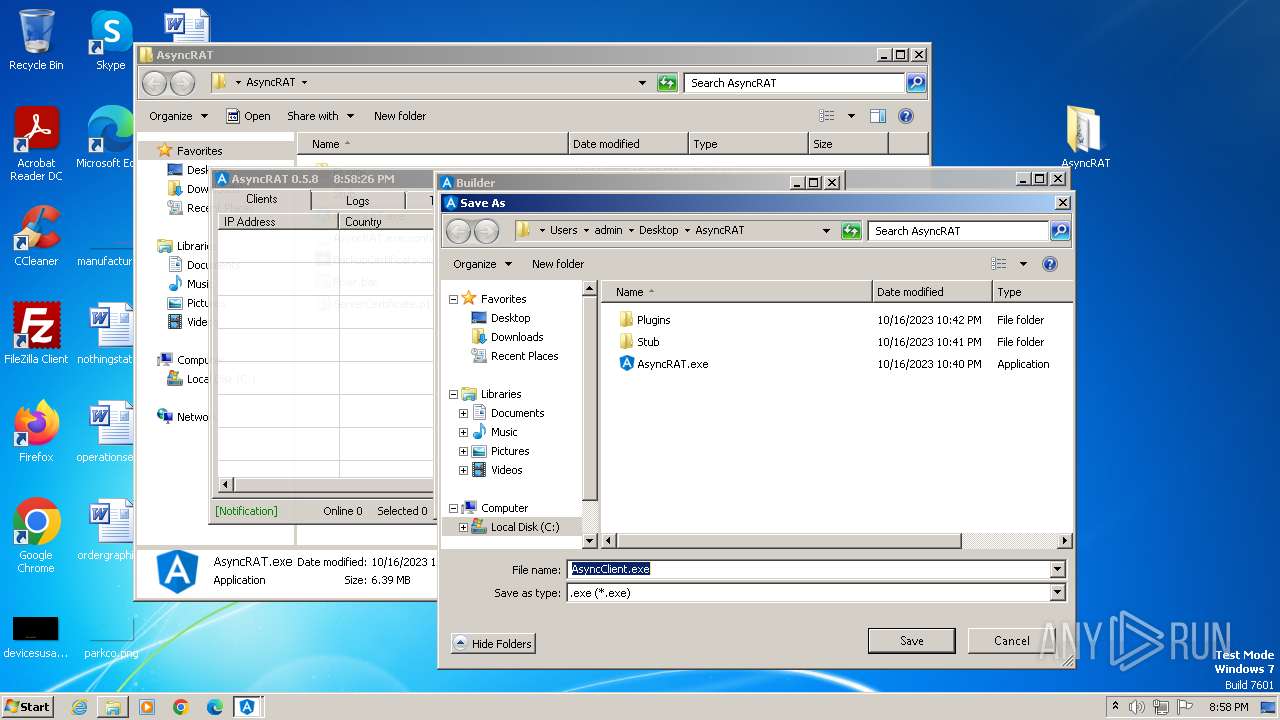
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3500)
- AsyncRAT.exe (PID: 3392)
- csc.exe (PID: 2588)
- csc.exe (PID: 920)
- csc.exe (PID: 2616)
- csc.exe (PID: 3152)
ASYNCRAT has been detected (YARA)
- AsyncRAT.exe (PID: 3392)
- AsyncClient.exe (PID: 1556)
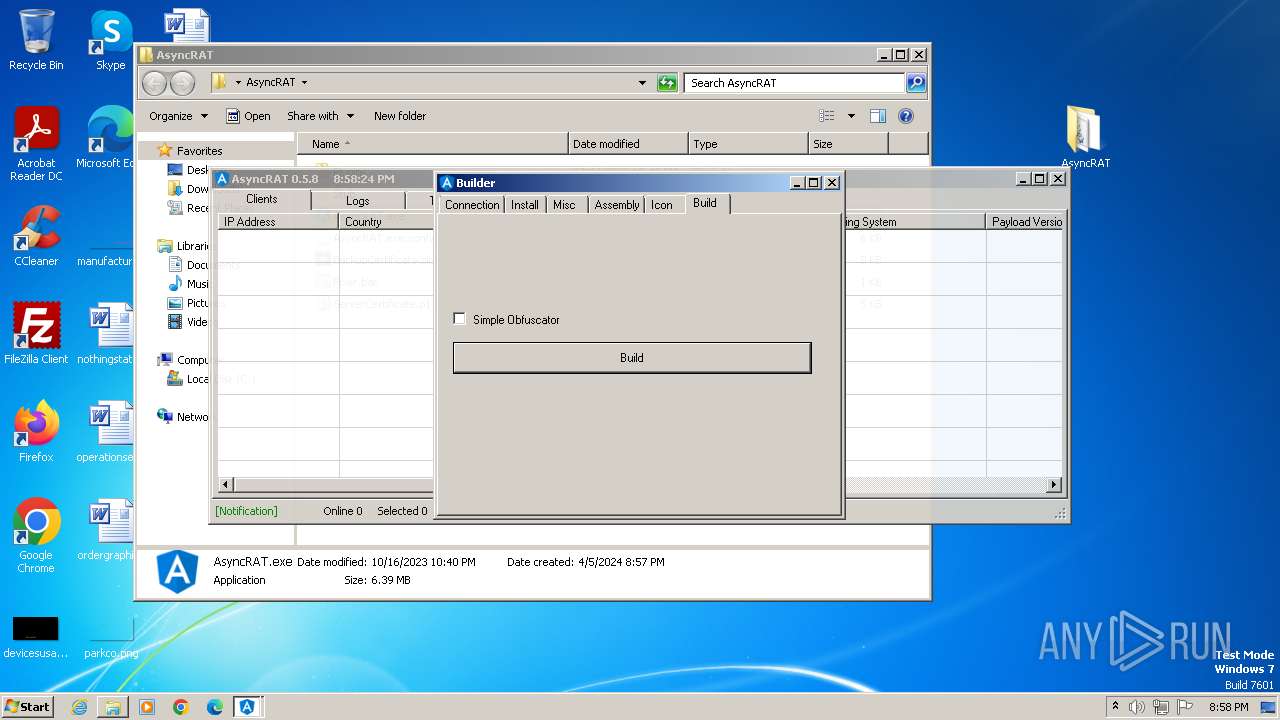
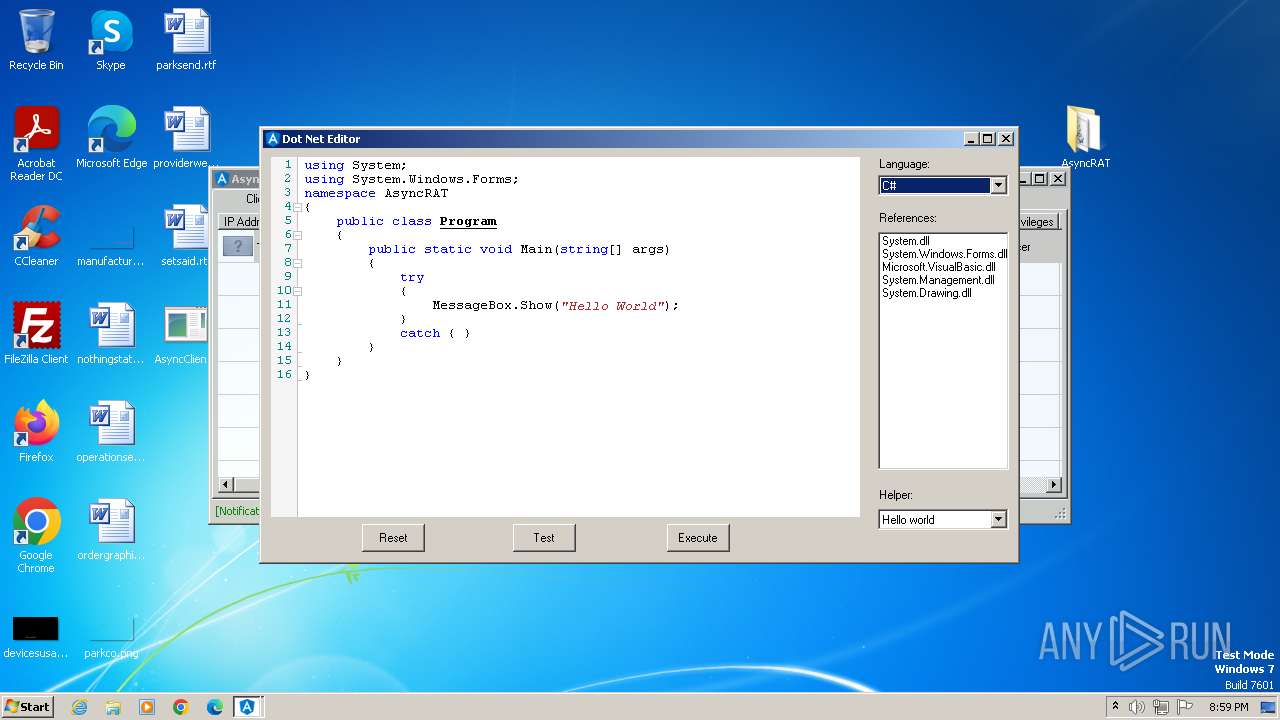
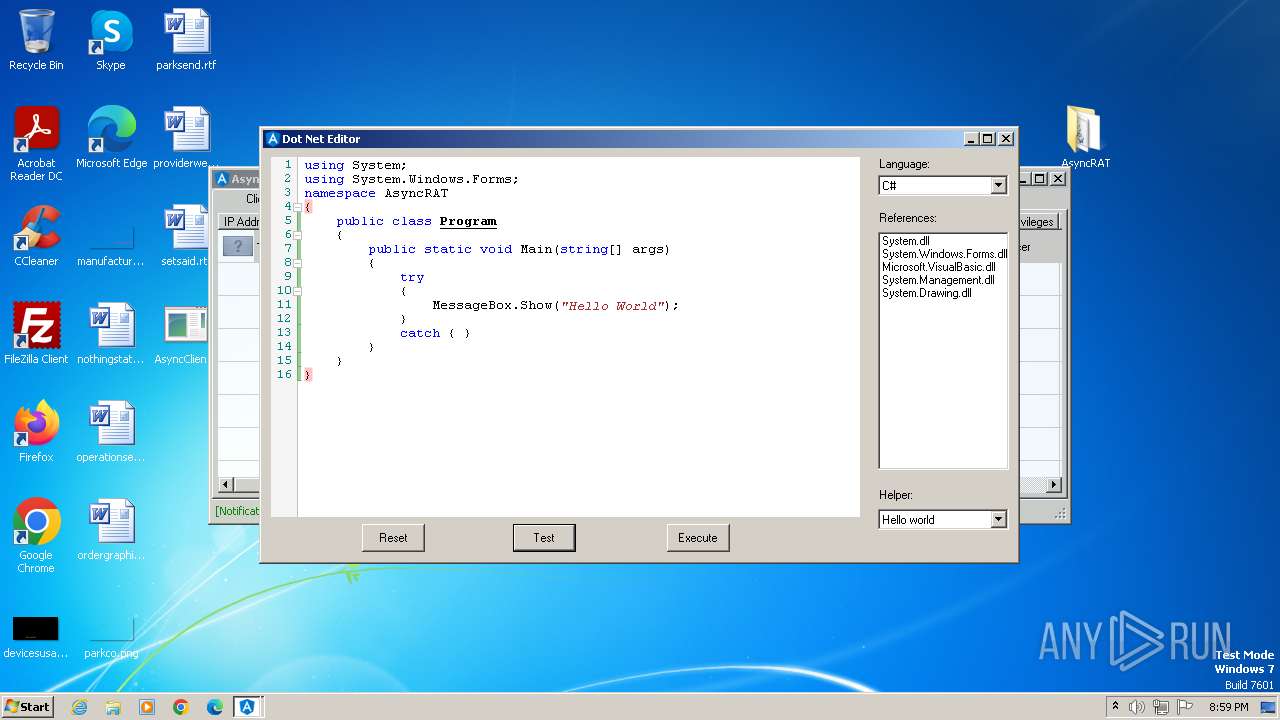
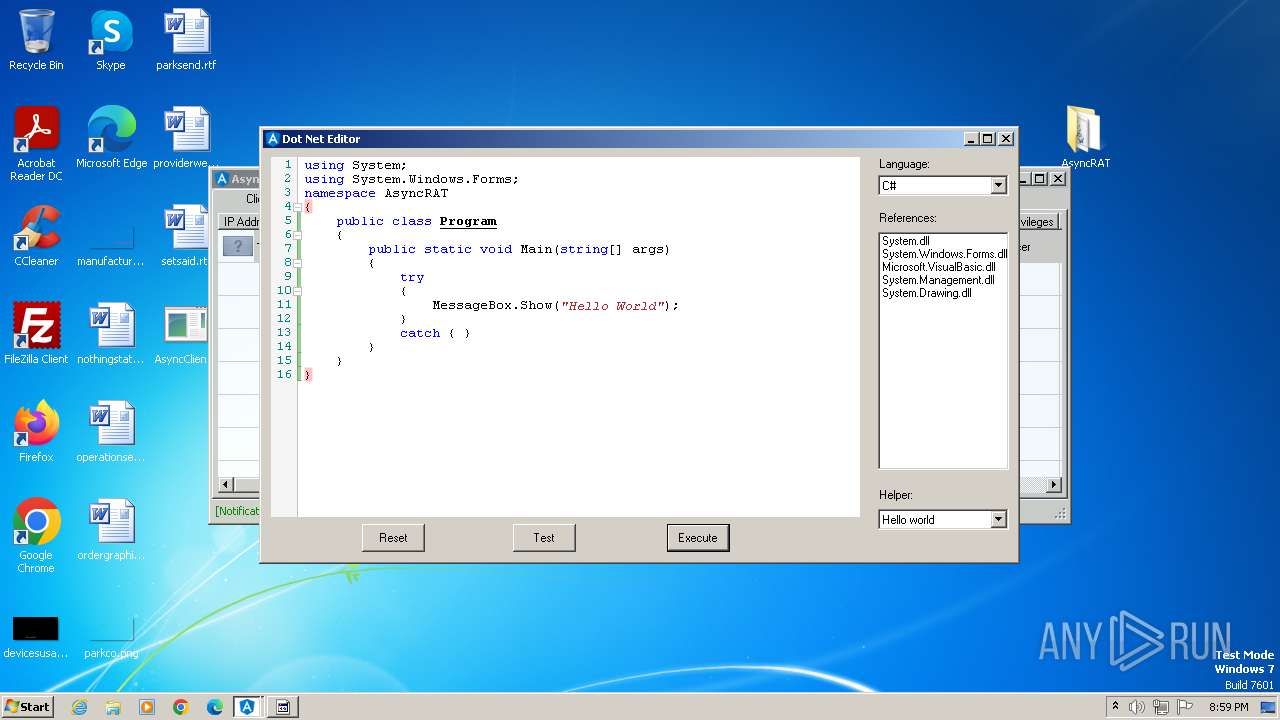
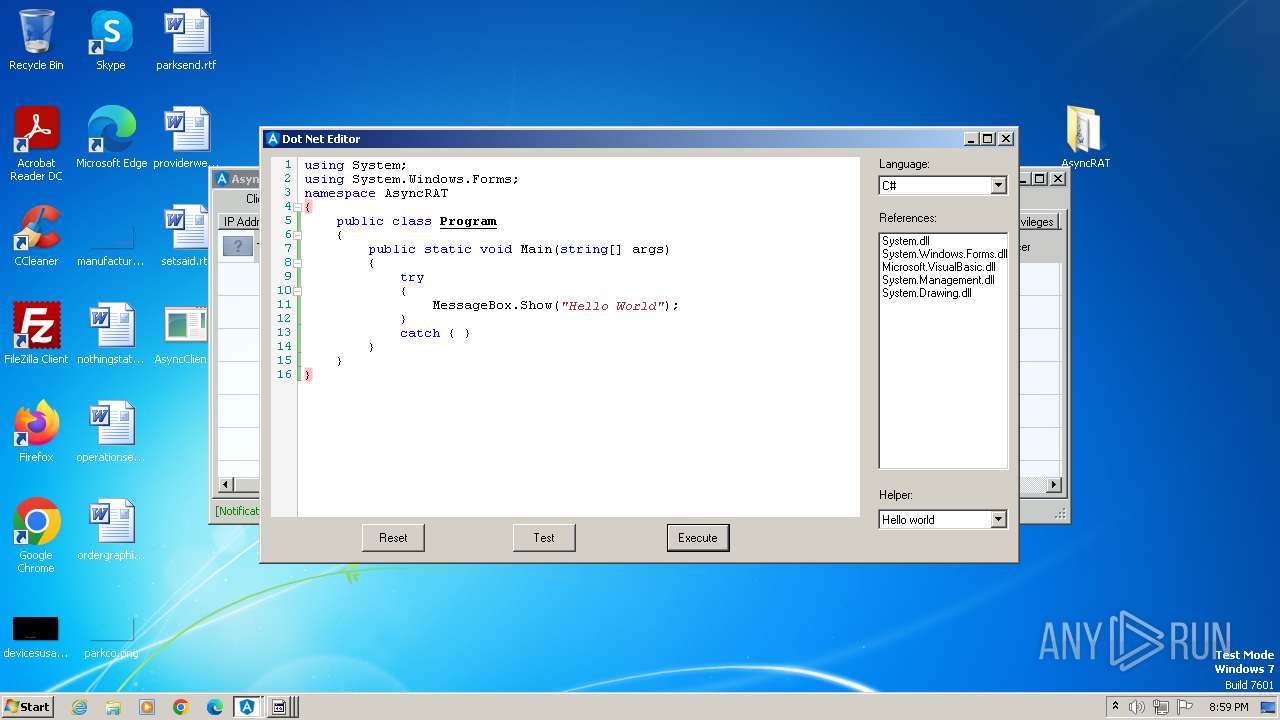
Starts Visual C# compiler
- AsyncClient.exe (PID: 1556)
- AsyncRAT.exe (PID: 3392)
SUSPICIOUS
Reads the Internet Settings
- AsyncRAT.exe (PID: 3392)
- AsyncClient.exe (PID: 1556)
Reads security settings of Internet Explorer
- AsyncRAT.exe (PID: 3392)
Reads settings of System Certificates
- AsyncClient.exe (PID: 1556)
Uses .NET C# to load dll
- AsyncRAT.exe (PID: 3392)
- AsyncClient.exe (PID: 1556)
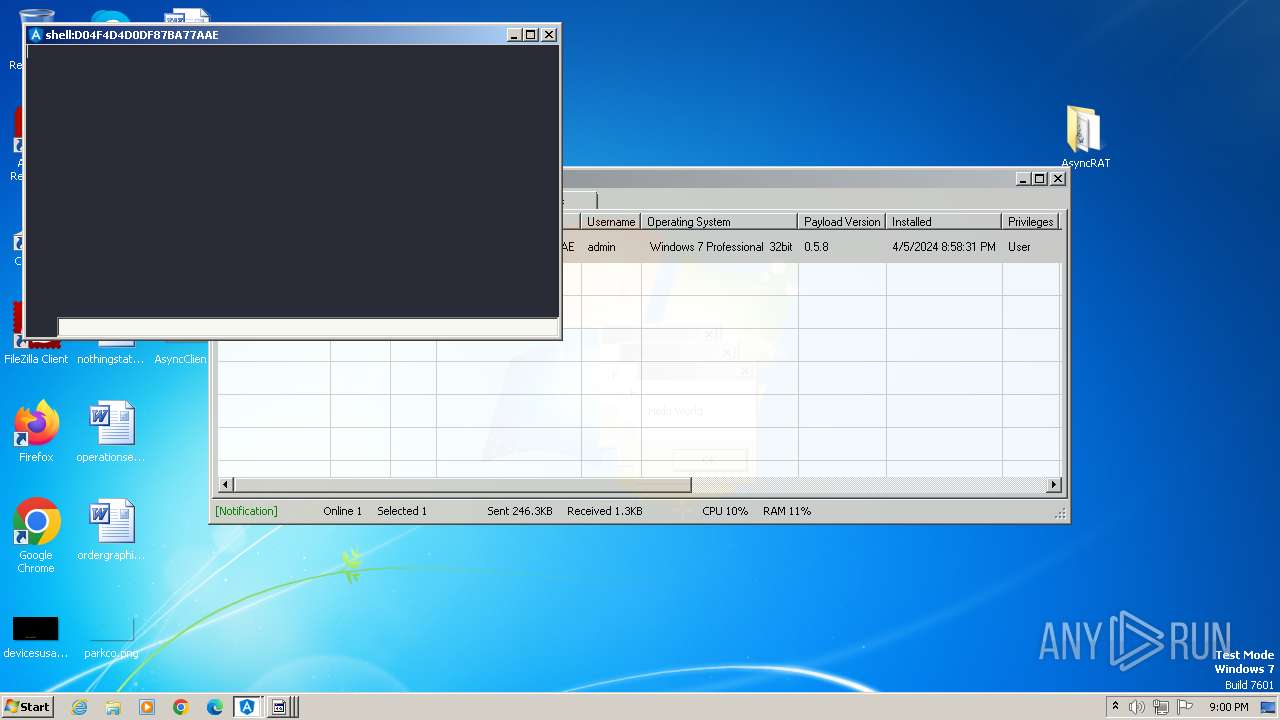
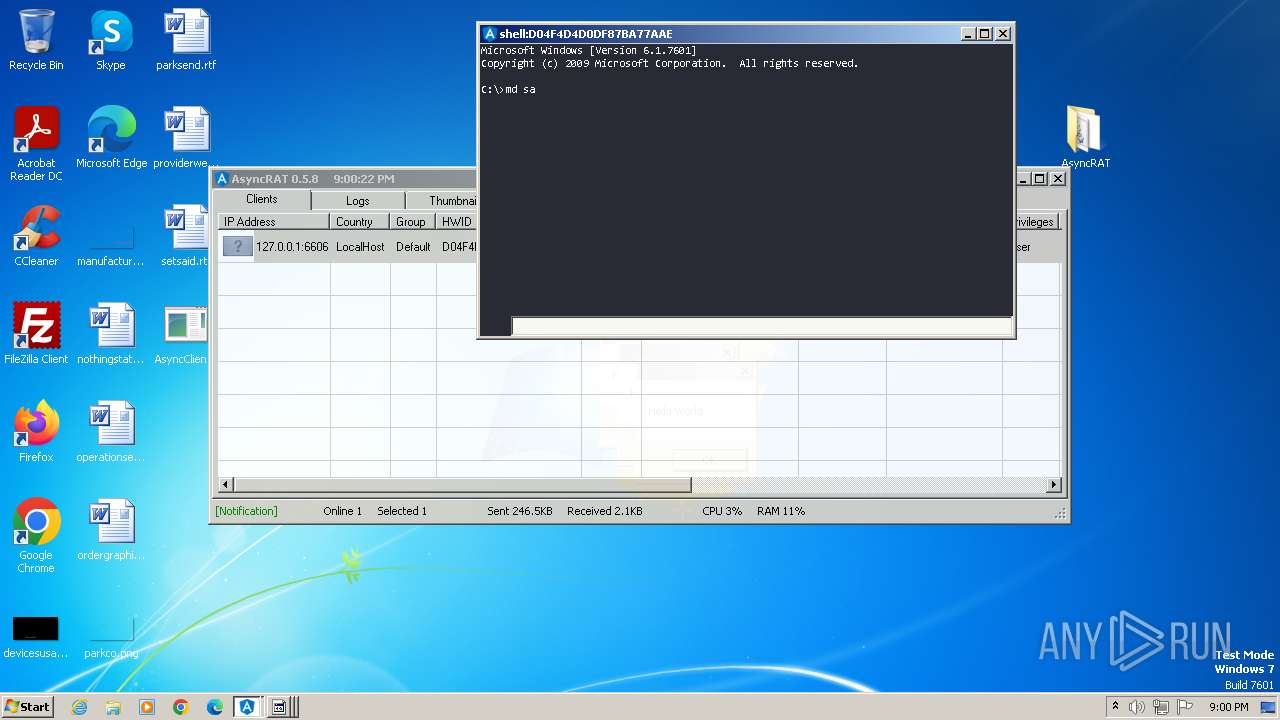
Starts CMD.EXE for commands execution
- AsyncClient.exe (PID: 1556)
INFO
Reads the computer name
- AsyncRAT.exe (PID: 3392)
- AsyncClient.exe (PID: 1556)
Checks supported languages
- AsyncRAT.exe (PID: 3392)
- AsyncClient.exe (PID: 1556)
- csc.exe (PID: 2588)
- cvtres.exe (PID: 2404)
- csc.exe (PID: 920)
- csc.exe (PID: 2616)
- csc.exe (PID: 3152)
- cvtres.exe (PID: 1592)
- cvtres.exe (PID: 3292)
- cvtres.exe (PID: 3112)
Manual execution by a user
- AsyncRAT.exe (PID: 3392)
- AsyncClient.exe (PID: 1556)
Reads the machine GUID from the registry
- AsyncRAT.exe (PID: 3392)
- AsyncClient.exe (PID: 1556)
- csc.exe (PID: 2588)
- cvtres.exe (PID: 2404)
- csc.exe (PID: 920)
- cvtres.exe (PID: 3292)
- csc.exe (PID: 3152)
- cvtres.exe (PID: 1592)
- csc.exe (PID: 2616)
- cvtres.exe (PID: 3112)
Reads Environment values
- AsyncRAT.exe (PID: 3392)
- AsyncClient.exe (PID: 1556)
Reads Microsoft Office registry keys
- AsyncRAT.exe (PID: 3392)
Creates files or folders in the user directory
- AsyncRAT.exe (PID: 3392)
Reads the software policy settings
- AsyncClient.exe (PID: 1556)
Create files in a temporary directory
- AsyncClient.exe (PID: 1556)
- AsyncRAT.exe (PID: 3392)
- cvtres.exe (PID: 2404)
- csc.exe (PID: 2588)
- cvtres.exe (PID: 3292)
- csc.exe (PID: 3152)
- csc.exe (PID: 920)
- cvtres.exe (PID: 1592)
- csc.exe (PID: 2616)
- cvtres.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
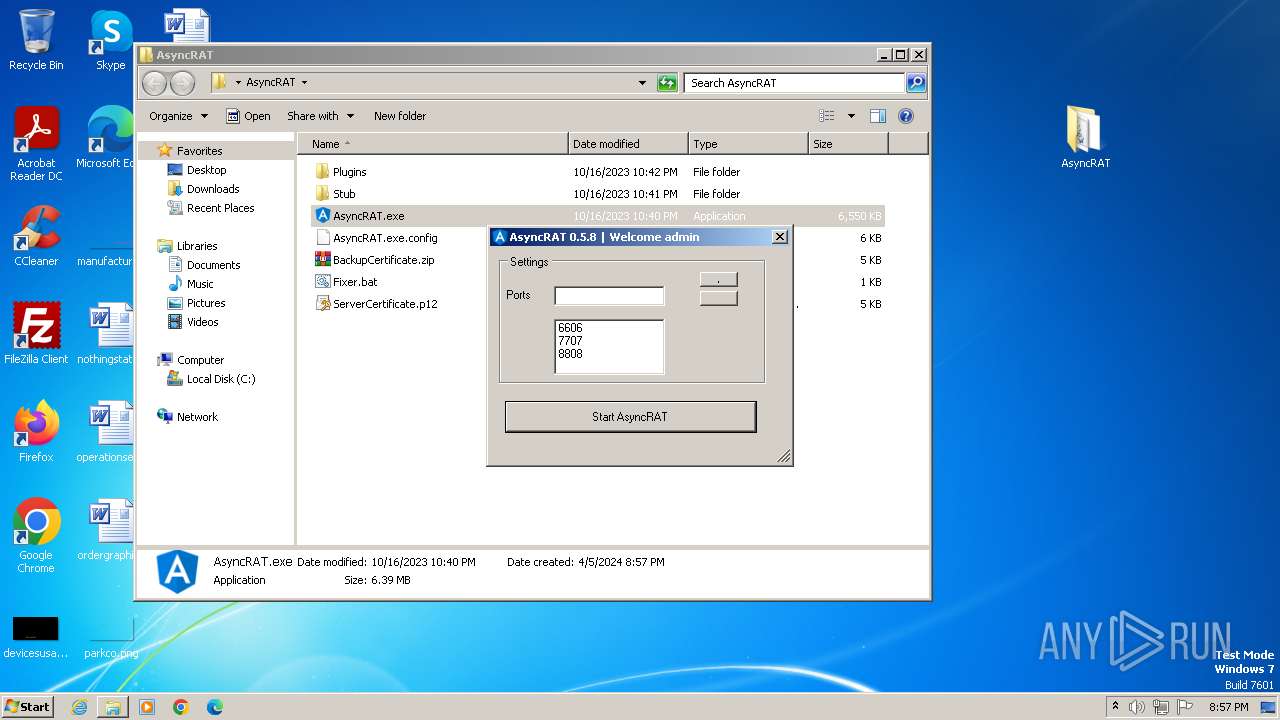
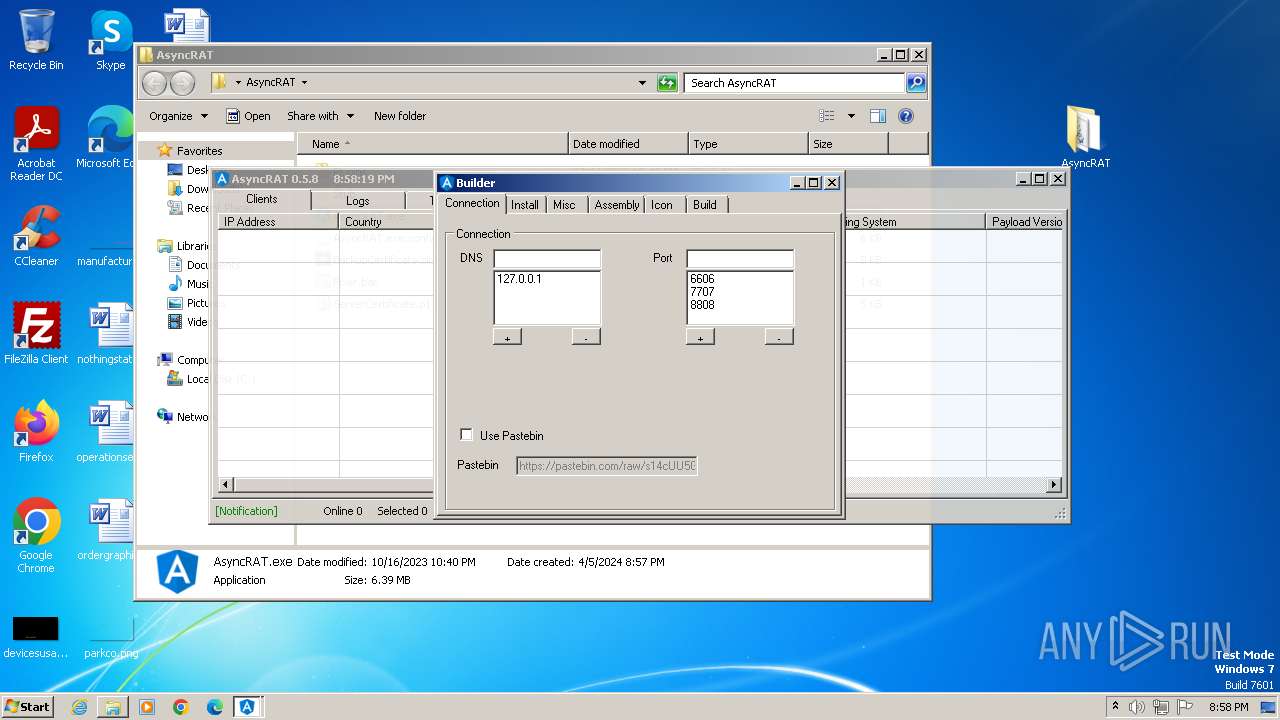
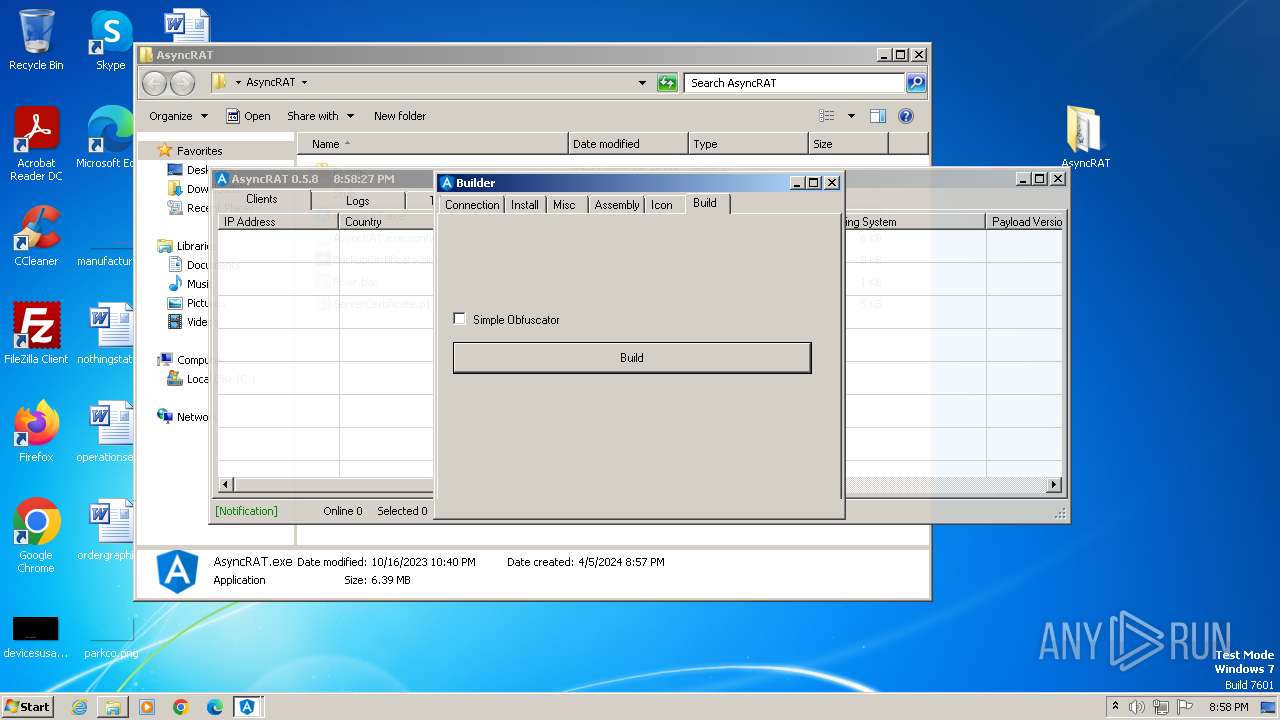
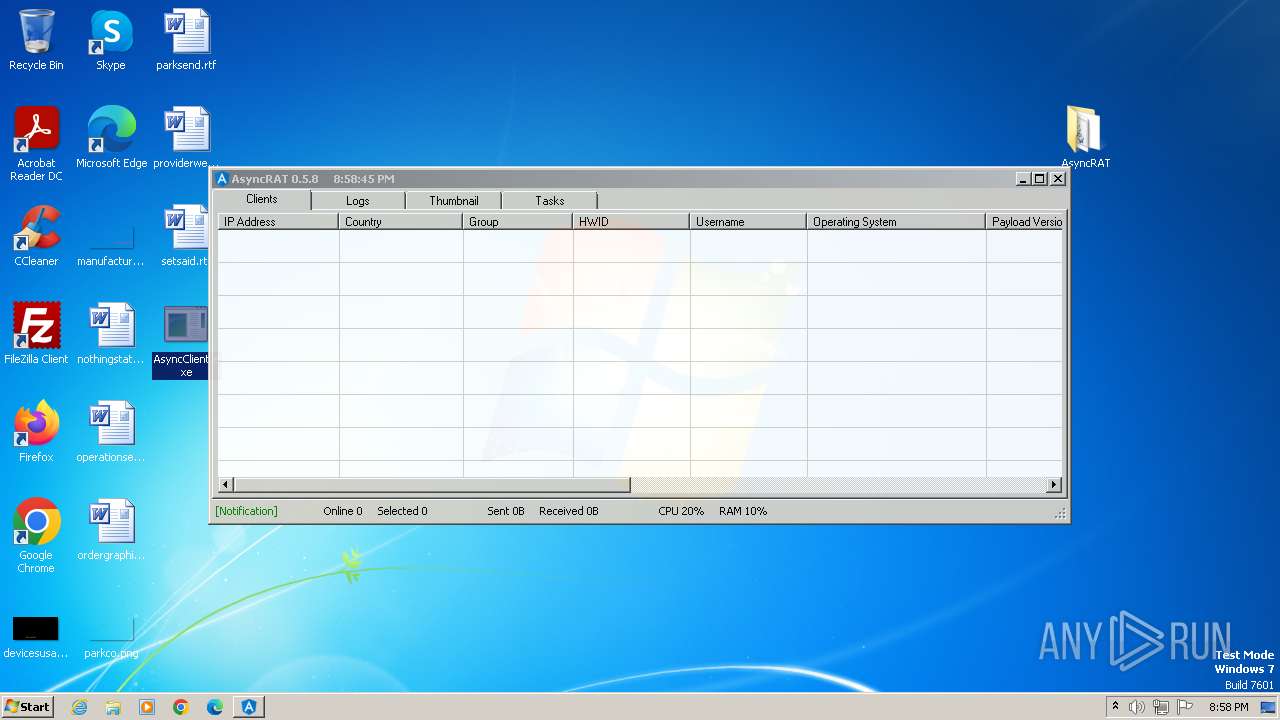
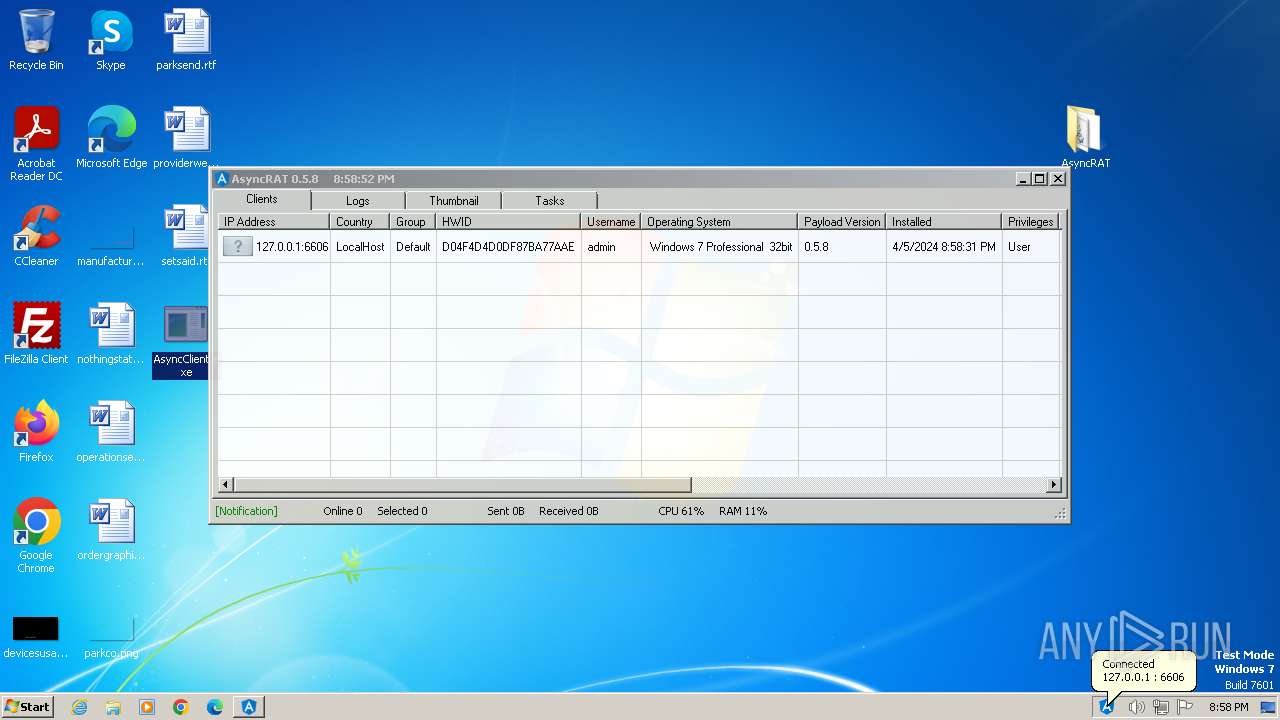
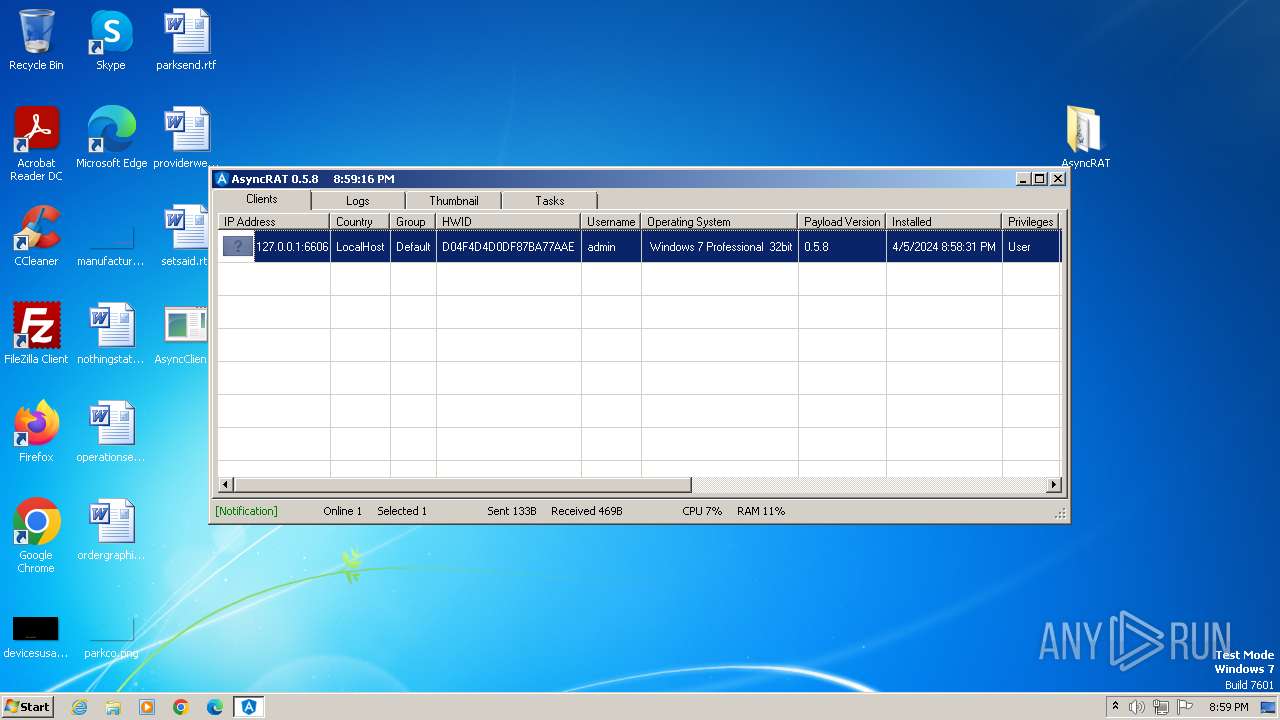
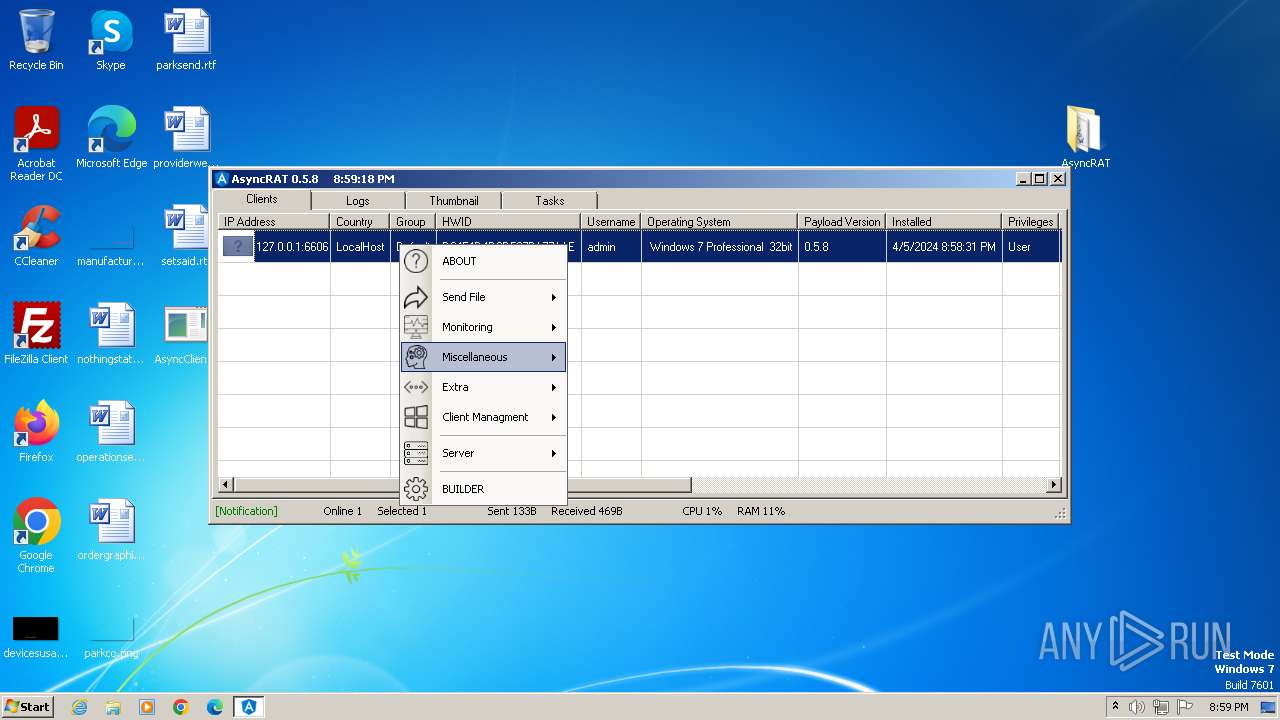
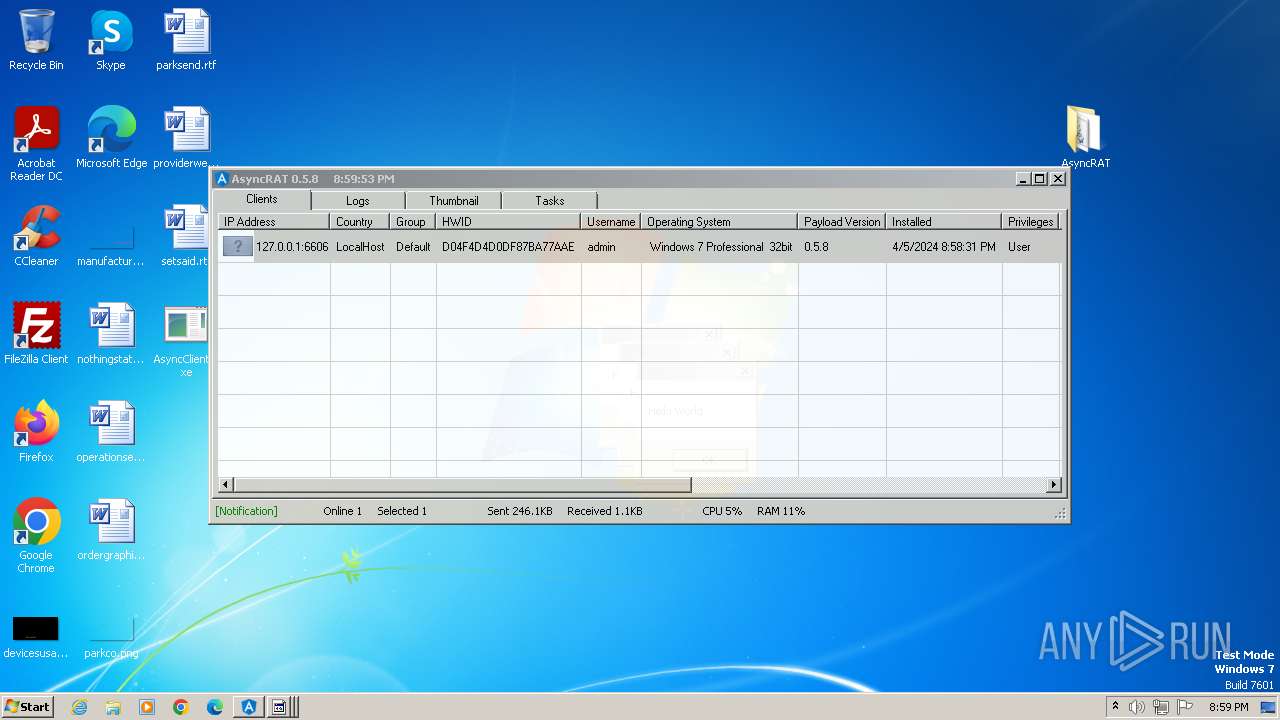
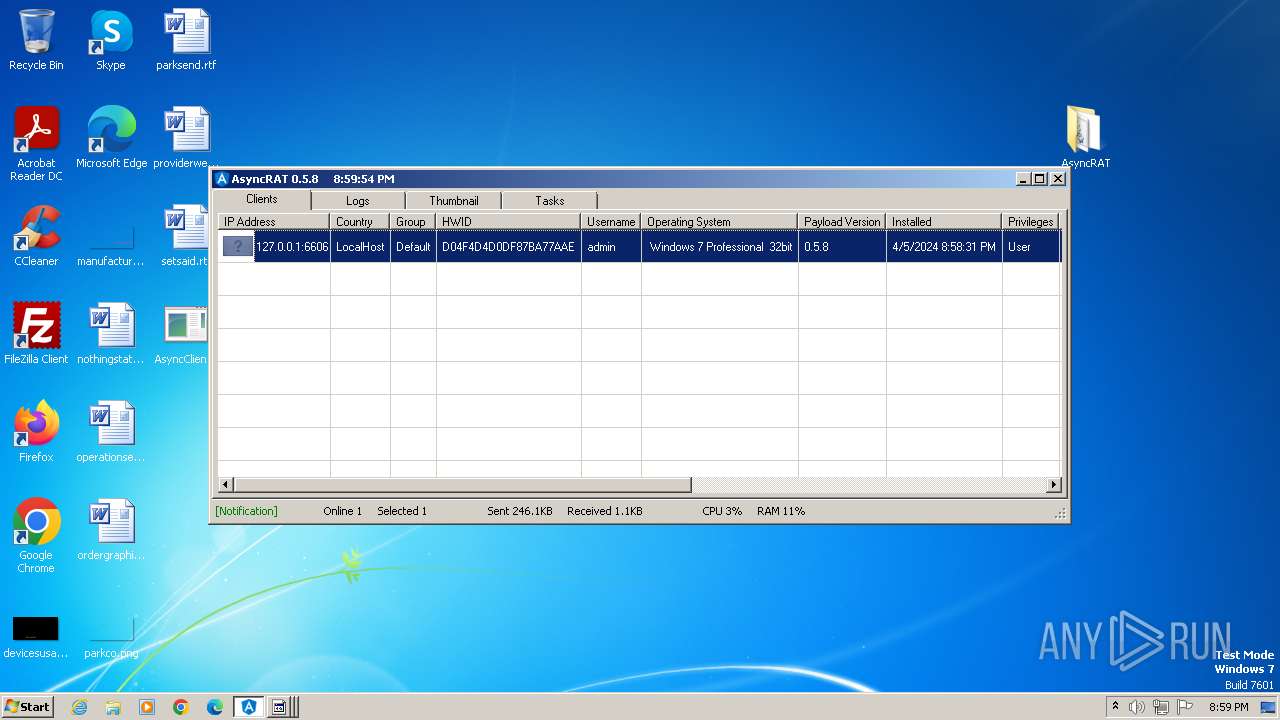
AsyncRat
(PID) Process(1556) AsyncClient.exe
C2 (1)127.0.0.1
Ports (3)6606
7707
8808
BotnetDefault
Version0.5.8
Options
AutoRunfalse
Mutexi6SwOR4Y6Lwv
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
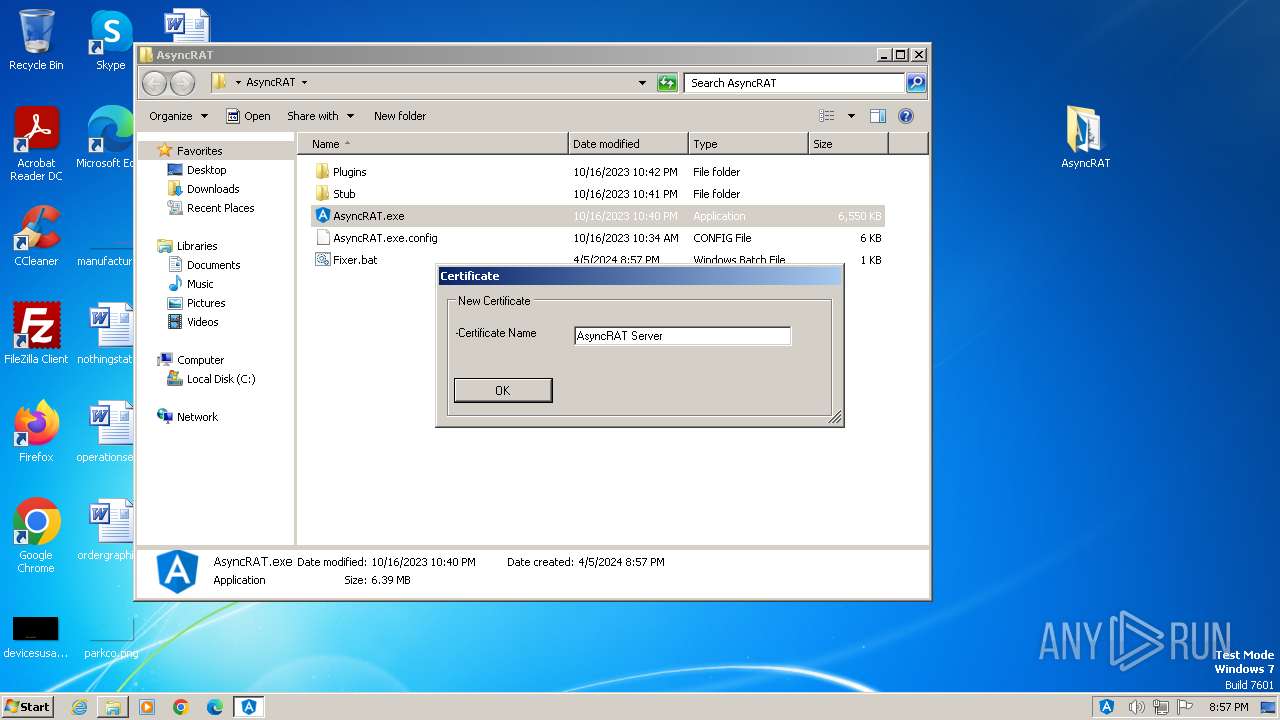
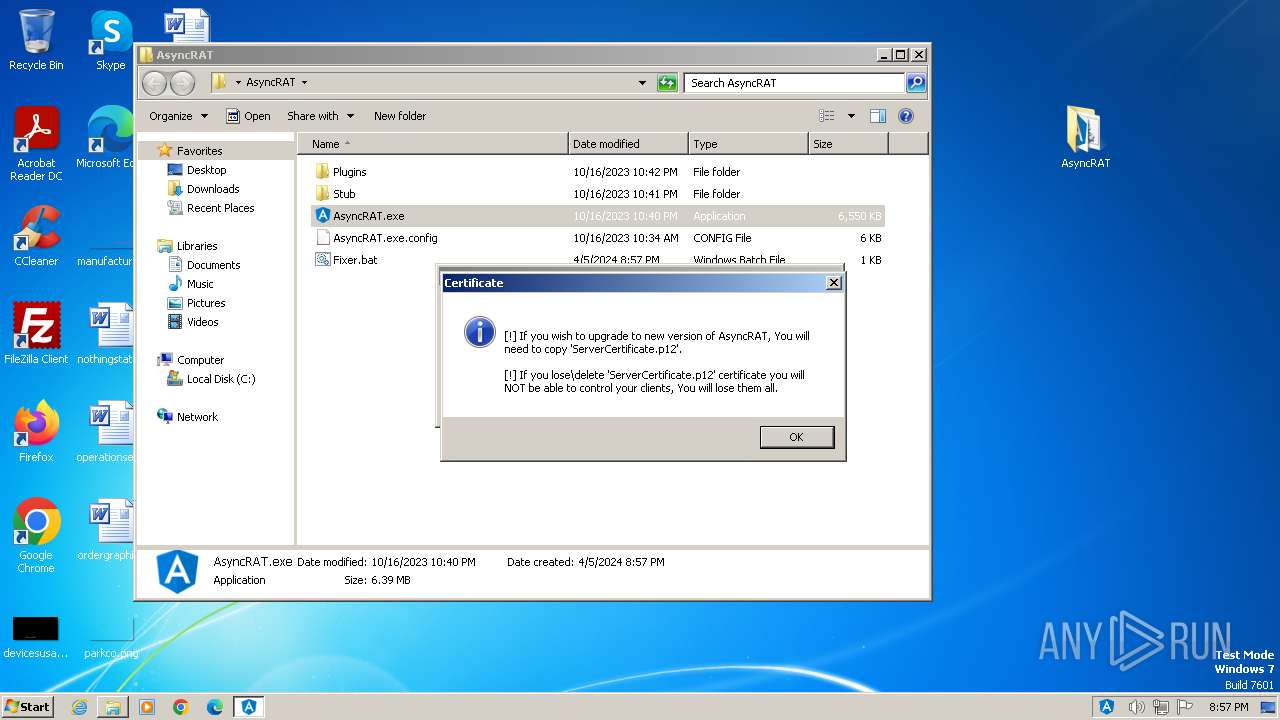
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAMwpQGFsRrLI/YLa7bNuXTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjQwNDAzMTk1NzQ3WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIZqb2cTPq8Hw6z1I0Z/733PS93Ahb8JC1ISQIV2YGsZRlcH1toYw6DXmxHK1pSb5l97FQR1H1jt...
Server_SignatureC/JNkntszrjJnqfe+WL/LO4p9tYYsiquDOqH8cFvUWiSspN0Y6fangPWTes5Gbnc21vJYBkXf89j6VVSfYXj34wvs4n1ZANoZrYDnZV0dx9GqKE4ginUOaHCPhXPQMMfMS6p6INiVXhoHInHpbWFK8VsJcUpI2pg56C46DKofGRqAjGEMTW1rVQQ3Awo2c0pFhuBpyYLIn1KGakvPUbgQV0tvHemks6qIK03rUdBr67QIOfbvKhbUq3pCNtnAlWEdltVwAagPd0VMQAqrIsmTCCzWzyhIokm/IRst7JnZ7NK...
Keys
AES1e9bcd87f2ceb88997d5ba38953928cb9333d975852011df20829bf9f1225e28
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:10:17 00:41:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | AsyncRAT/ |
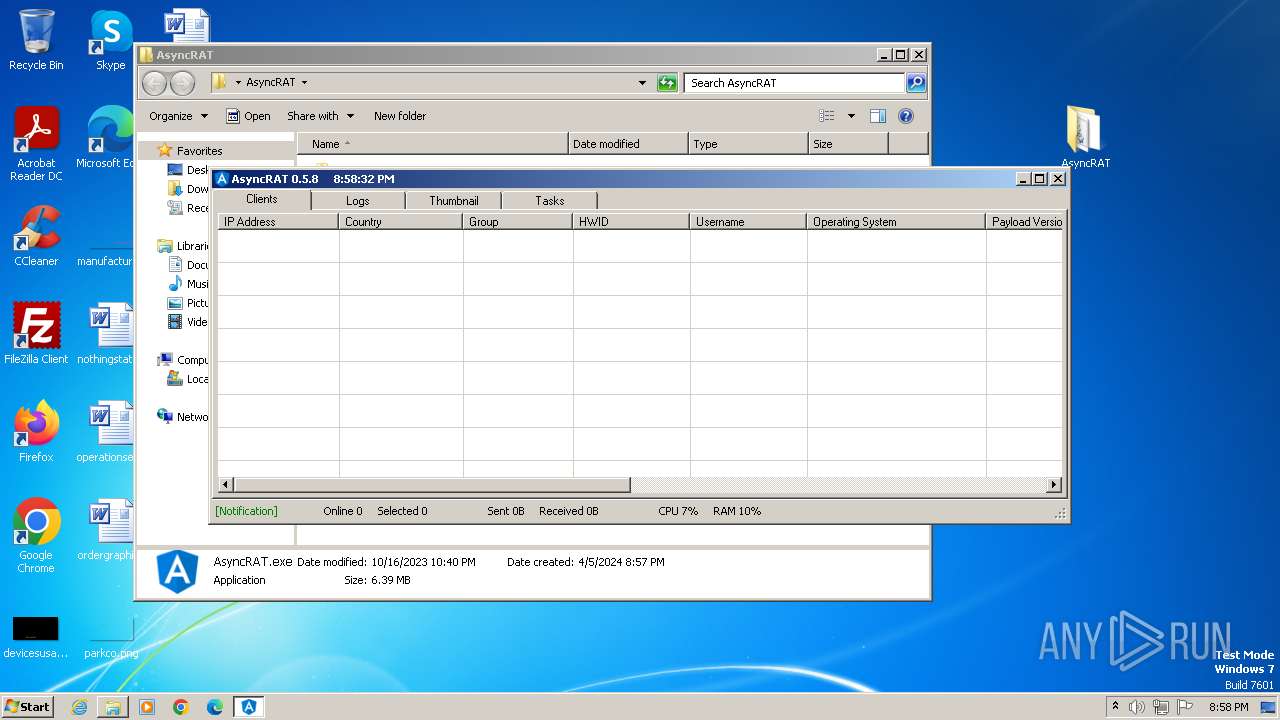
Total processes
58
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "cmd" | C:\Windows\System32\cmd.exe | — | AsyncClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 920 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\1hpf2rwf.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | AsyncClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
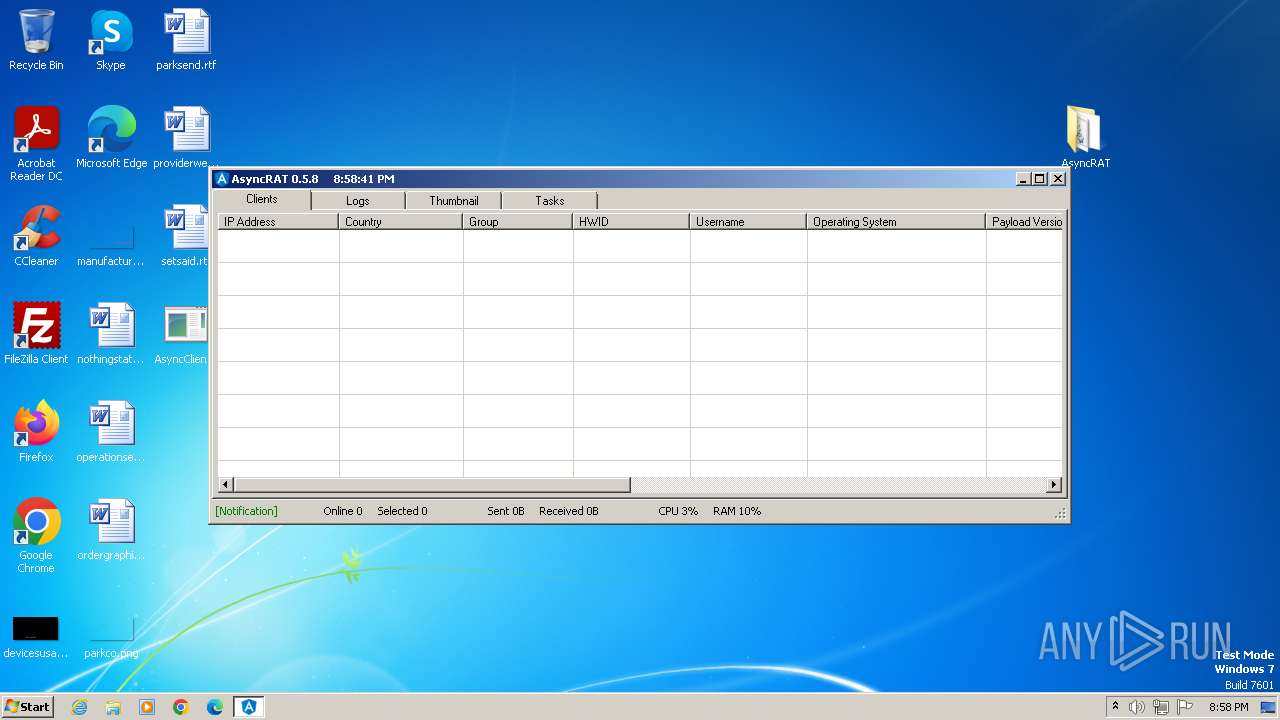
| 1556 | "C:\Users\admin\Desktop\AsyncClient.exe" | C:\Users\admin\Desktop\AsyncClient.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
AsyncRat(PID) Process(1556) AsyncClient.exe C2 (1)127.0.0.1 Ports (3)6606 7707 8808 BotnetDefault Version0.5.8 Options AutoRunfalse Mutexi6SwOR4Y6Lwv InstallFolder%AppData% BSoDfalse AntiVMfalse Certificates Cert1MIIE8jCCAtqgAwIBAgIQAMwpQGFsRrLI/YLa7bNuXTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjQwNDAzMTk1NzQ3WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIZqb2cTPq8Hw6z1I0Z/733PS93Ahb8JC1ISQIV2YGsZRlcH1toYw6DXmxHK1pSb5l97FQR1H1jt... Server_SignatureC/JNkntszrjJnqfe+WL/LO4p9tYYsiquDOqH8cFvUWiSspN0Y6fangPWTes5Gbnc21vJYBkXf89j6VVSfYXj34wvs4n1ZANoZrYDnZV0dx9GqKE4ginUOaHCPhXPQMMfMS6p6INiVXhoHInHpbWFK8VsJcUpI2pg56C46DKofGRqAjGEMTW1rVQQ3Awo2c0pFhuBpyYLIn1KGakvPUbgQV0tvHemks6qIK03rUdBr67QIOfbvKhbUq3pCNtnAlWEdltVwAagPd0VMQAqrIsmTCCzWzyhIokm/IRst7JnZ7NK... Keys AES1e9bcd87f2ceb88997d5ba38953928cb9333d975852011df20829bf9f1225e28 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 1592 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESC3DE.tmp" "c:\Users\admin\AppData\Local\Temp\CSCCD7CB416A4DF42C1825F6B8C6E17C195.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 2404 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESB1AD.tmp" "c:\Users\admin\AppData\Local\Temp\CSC13DD933FDBF3449F945FF539FE65E87C.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 2588 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\mjy0hpav.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | AsyncRAT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 2616 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\z5hm1jqr.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | AsyncClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 3112 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESE7C1.tmp" "c:\Users\admin\AppData\Local\Temp\CSC4BBFB3355BF6438EA66D3382D4B44AE.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 3152 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\tnhqfz5y.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | AsyncClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 3292 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESD35E.tmp" "c:\Users\admin\AppData\Local\Temp\CSC374C9F440C4469281D69EEB2F40FD2.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
Total events
21 040
Read events
20 897
Write events
135
Delete events
8
Modification events
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\COMPILED.zip | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
20
Suspicious files
15
Text files
18
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
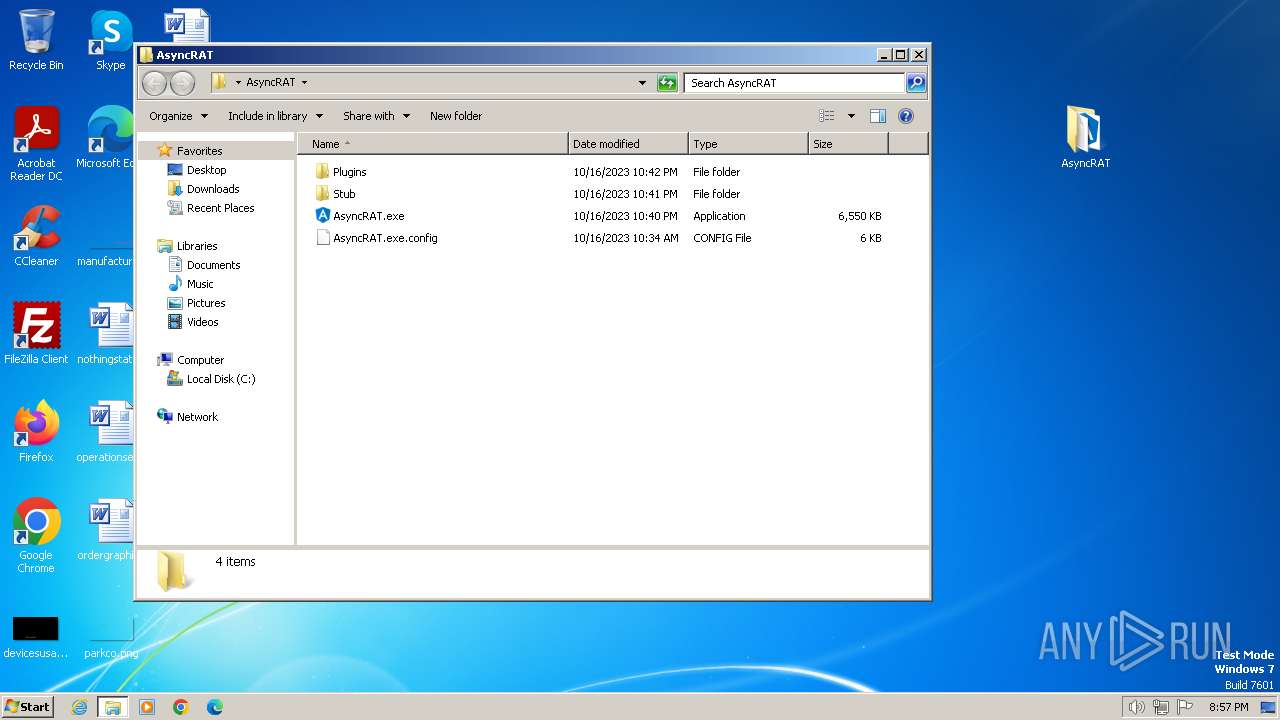
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\AsyncRAT.exe | executable | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\AsyncRAT.exe.config | xml | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\Plugins\Chat.dll | executable | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\Plugins\Extra.dll | executable | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\Plugins\FileManager.dll | executable | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\Plugins\FileSearcher.dll | executable | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\Plugins\LimeLogger.dll | executable | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\Plugins\Miscellaneous.dll | executable | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\Plugins\Options.dll | executable | |
MD5:— | SHA256:— | |||
| 3500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3500.188\AsyncRAT\Plugins\ProcessManager.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1556 | AsyncClient.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?826f55c0d4767c2c | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1556 | AsyncClient.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |