| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/6961276f-0fff-4705-a621-4270f41611b3 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 11, 2025, 23:58:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | DAC017834309E13D06D298F109022CFC |
| SHA1: | E8FA6430A6D2E6A62F6071C4E9C30250F647C87A |
| SHA256: | 0ABB0DA913C388BC2BD315123D11C4DE4803EC59D8BCBE3CC7489B27612D3589 |
| SSDEEP: | 49152:xecnxWrwTnNX/hG0KxG1JAGIrGNRVFnF+FG18w4+R6wdI9TWttv:xecnxWkNXeo0byNRVFJSzpTitv |
MALICIOUS
Executing a file with an untrusted certificate
- setup.exe (PID: 2392)
- TransactorSmart.exe (PID: 5416)
- TransactorSmart.exe (PID: 6080)
- TransactorSmart.exe (PID: 5112)
Steals credentials from Web Browsers
- setup.exe (PID: 2392)
Actions looks like stealing of personal data
- setup.exe (PID: 2392)
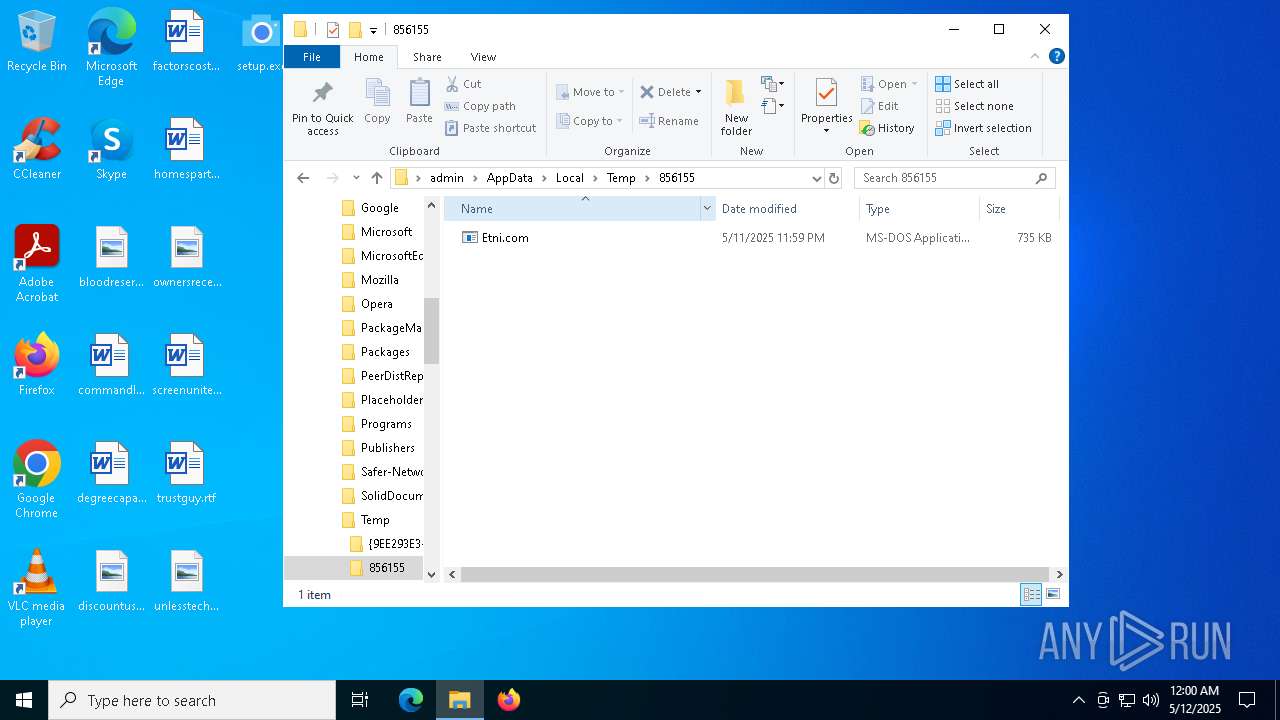
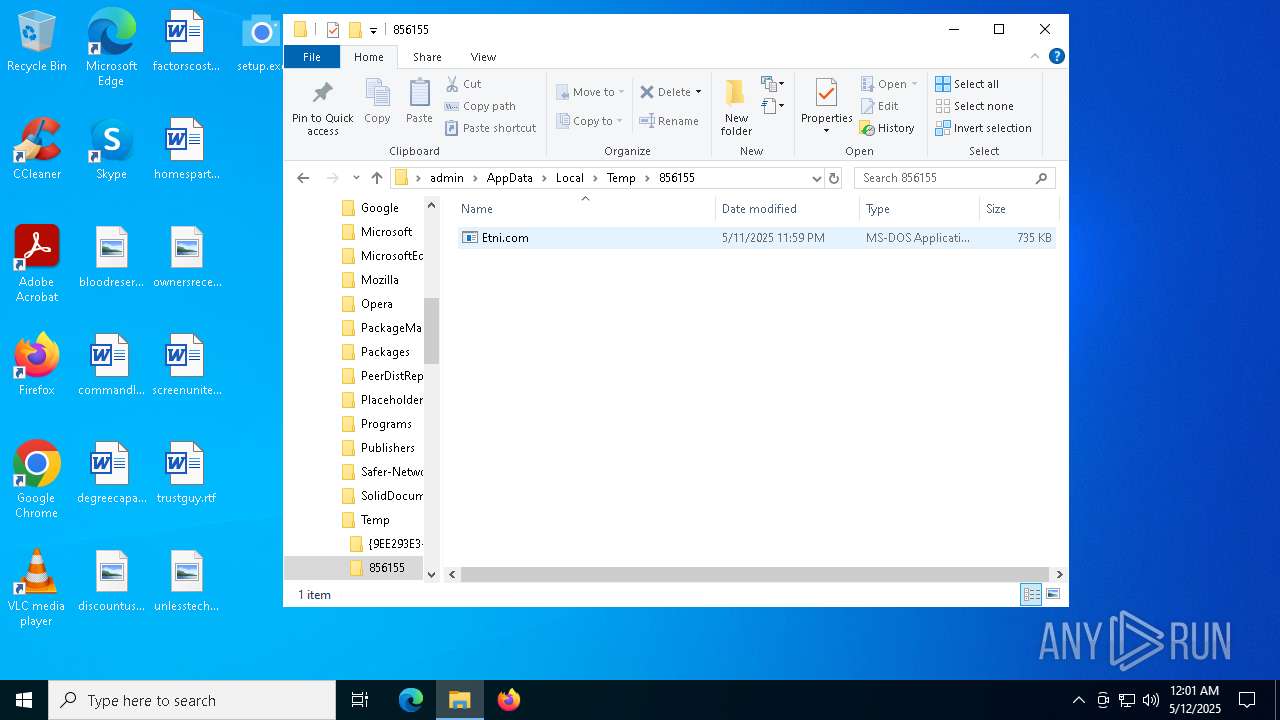
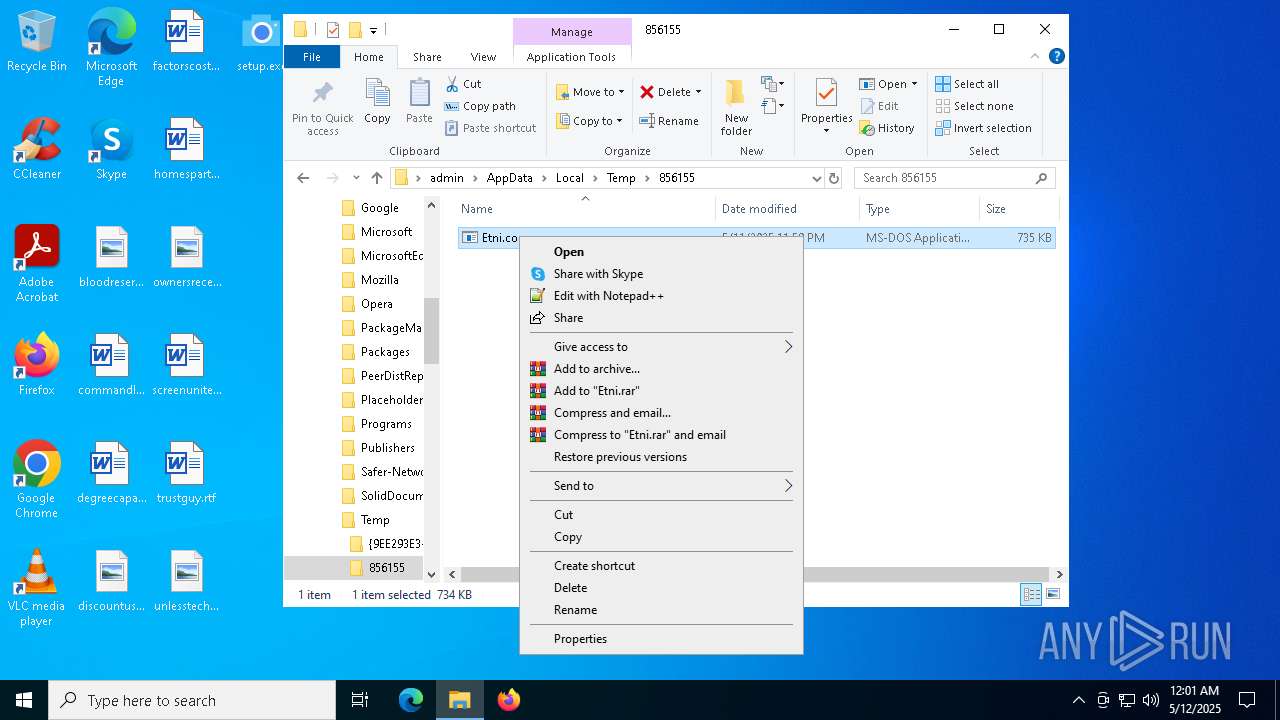
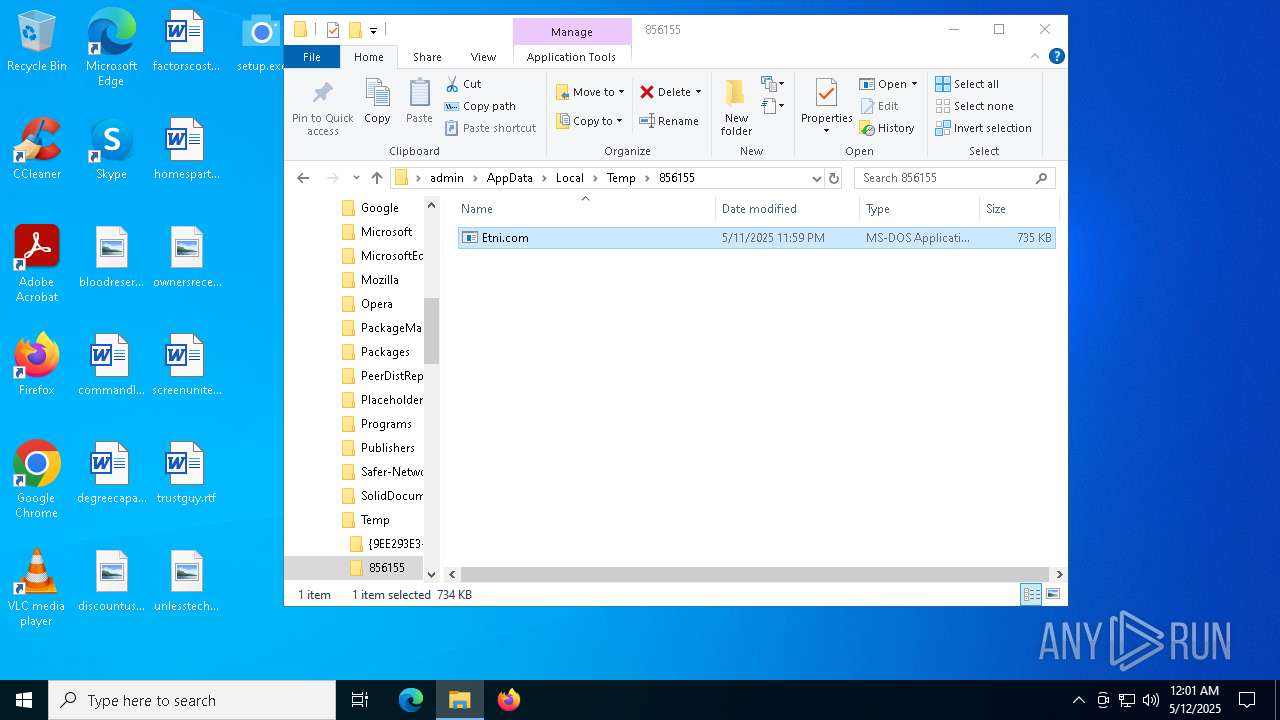
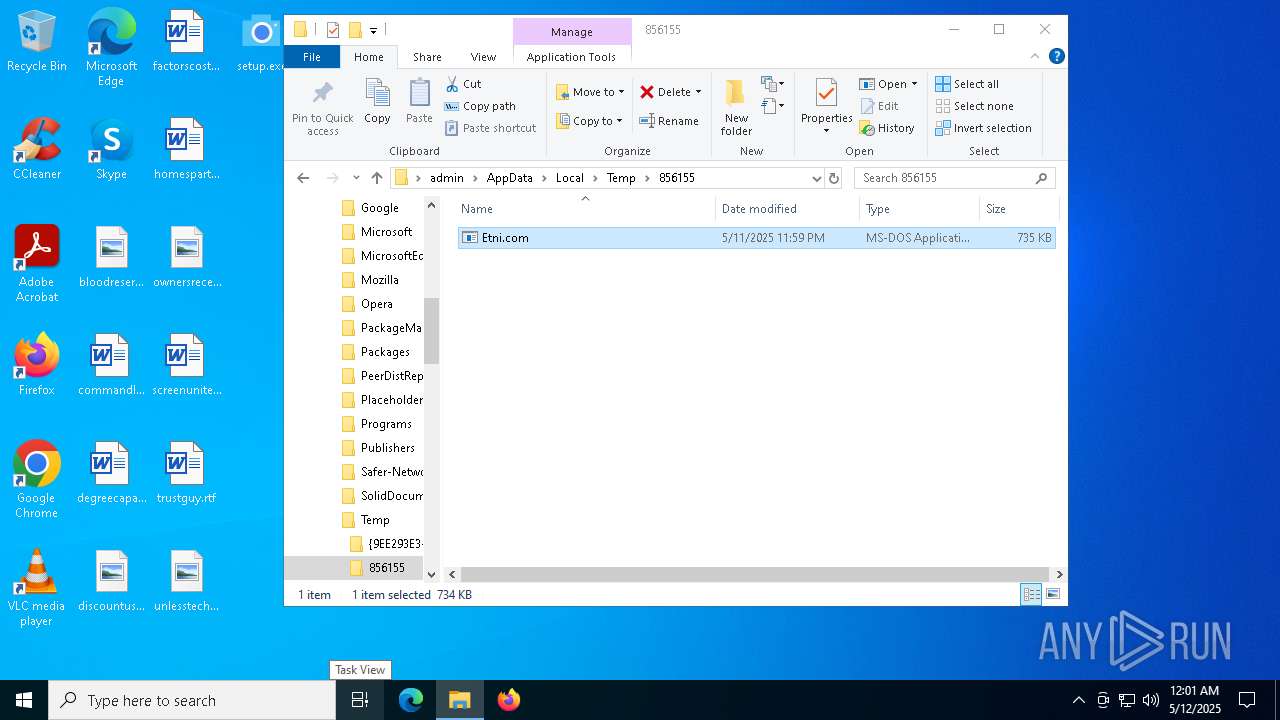
- Etni.com (PID: 7380)
GENERIC has been found (auto)
- setup.exe (PID: 2392)
- TransactorSmart.exe (PID: 5416)
Known privilege escalation attack
- dllhost.exe (PID: 4188)
LUMMA mutex has been found
- setup.exe (PID: 2392)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 2392)
Executable content was dropped or overwritten
- setup.exe (PID: 2392)
- TransactorSmart.exe (PID: 5416)
- TransactorSmart.exe (PID: 5112)
- TransactorSmart.exe (PID: 6080)
- Etni.com (PID: 7380)
- MicrosoftEdgeWebview2Setup.exe (PID: 7848)
Process drops legitimate windows executable
- setup.exe (PID: 2392)
- TransactorSmart.exe (PID: 5416)
- Etni.com (PID: 7380)
- MicrosoftEdgeWebview2Setup.exe (PID: 7848)
- MicrosoftEdgeUpdate.exe (PID: 7872)
Searches for installed software
- setup.exe (PID: 2392)
The process drops C-runtime libraries
- TransactorSmart.exe (PID: 5416)
- setup.exe (PID: 2392)
Starts itself from another location
- TransactorSmart.exe (PID: 5416)
Starts application with an unusual extension
- TransactorSmart.exe (PID: 6080)
Reads security settings of Internet Explorer
- Etni.com (PID: 7380)
- MicrosoftEdgeUpdate.exe (PID: 7872)
Connects to unusual port
- Etni.com (PID: 7380)
Starts process via Powershell
- powershell.exe (PID: 7720)
Starts POWERSHELL.EXE for commands execution
- Etni.com (PID: 7380)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 7872)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 7872)
INFO
Checks supported languages
- setup.exe (PID: 2392)
- TransactorSmart.exe (PID: 5416)
- TransactorSmart.exe (PID: 5112)
- tcpvcon.exe (PID: 6156)
- TransactorSmart.exe (PID: 6080)
- Etni.com (PID: 7380)
- MicrosoftEdgeWebview2Setup.exe (PID: 7848)
- MicrosoftEdgeUpdate.exe (PID: 7872)
- tcpvcon.exe (PID: 7564)
- Etni.com (PID: 5736)
Reads the computer name
- setup.exe (PID: 2392)
- TransactorSmart.exe (PID: 5416)
- tcpvcon.exe (PID: 6156)
- TransactorSmart.exe (PID: 5112)
- TransactorSmart.exe (PID: 6080)
- Etni.com (PID: 7380)
- MicrosoftEdgeUpdate.exe (PID: 7872)
- tcpvcon.exe (PID: 7564)
Reads the software policy settings
- setup.exe (PID: 2392)
- slui.exe (PID: 4880)
- Etni.com (PID: 7380)
- MicrosoftEdgeUpdate.exe (PID: 7872)
- wermgr.exe (PID: 7984)
- slui.exe (PID: 1912)
Create files in a temporary directory
- setup.exe (PID: 2392)
- TransactorSmart.exe (PID: 5112)
- TransactorSmart.exe (PID: 6080)
The sample compiled with english language support
- setup.exe (PID: 2392)
- TransactorSmart.exe (PID: 5416)
- TransactorSmart.exe (PID: 5112)
- Etni.com (PID: 7380)
- MicrosoftEdgeWebview2Setup.exe (PID: 7848)
- MicrosoftEdgeUpdate.exe (PID: 7872)
Creates files or folders in the user directory
- TransactorSmart.exe (PID: 5416)
- Etni.com (PID: 7380)
- wermgr.exe (PID: 7984)
Creates files in the program directory
- TransactorSmart.exe (PID: 5416)
- TransactorSmart.exe (PID: 5112)
- Etni.com (PID: 7380)
- MicrosoftEdgeWebview2Setup.exe (PID: 7848)
Reads the machine GUID from the registry
- tcpvcon.exe (PID: 6156)
- Etni.com (PID: 7380)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 4188)
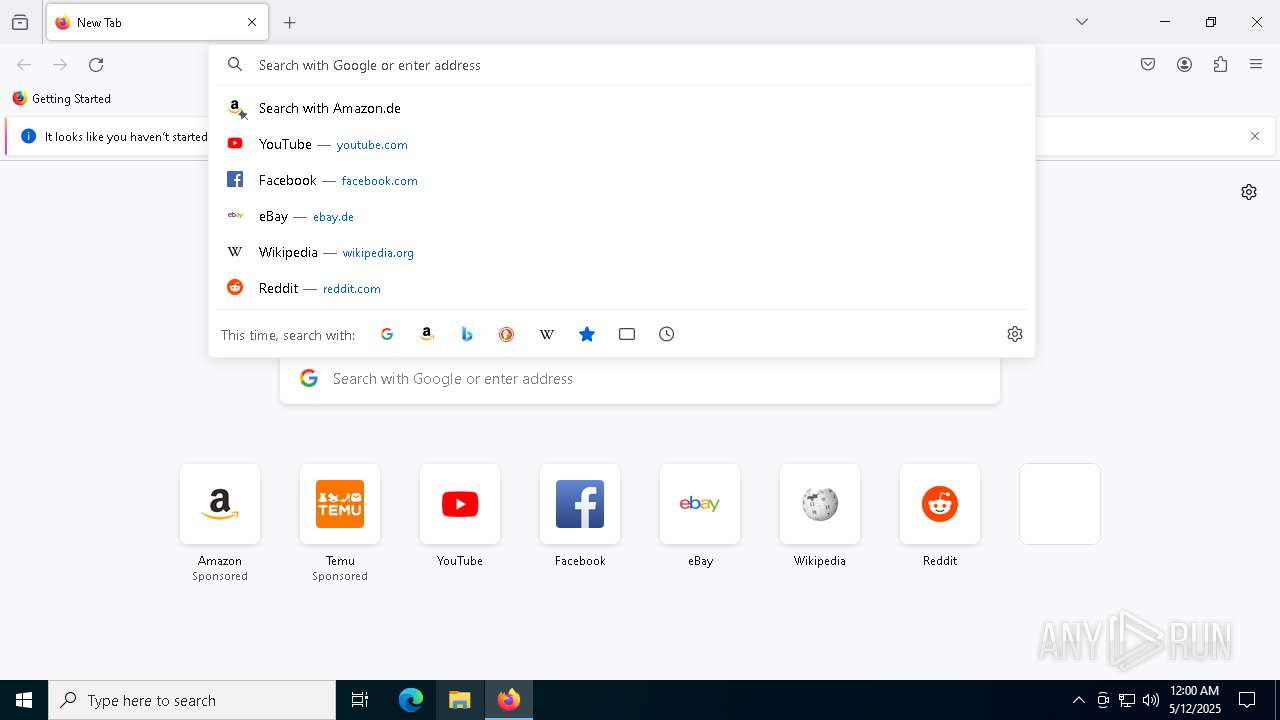
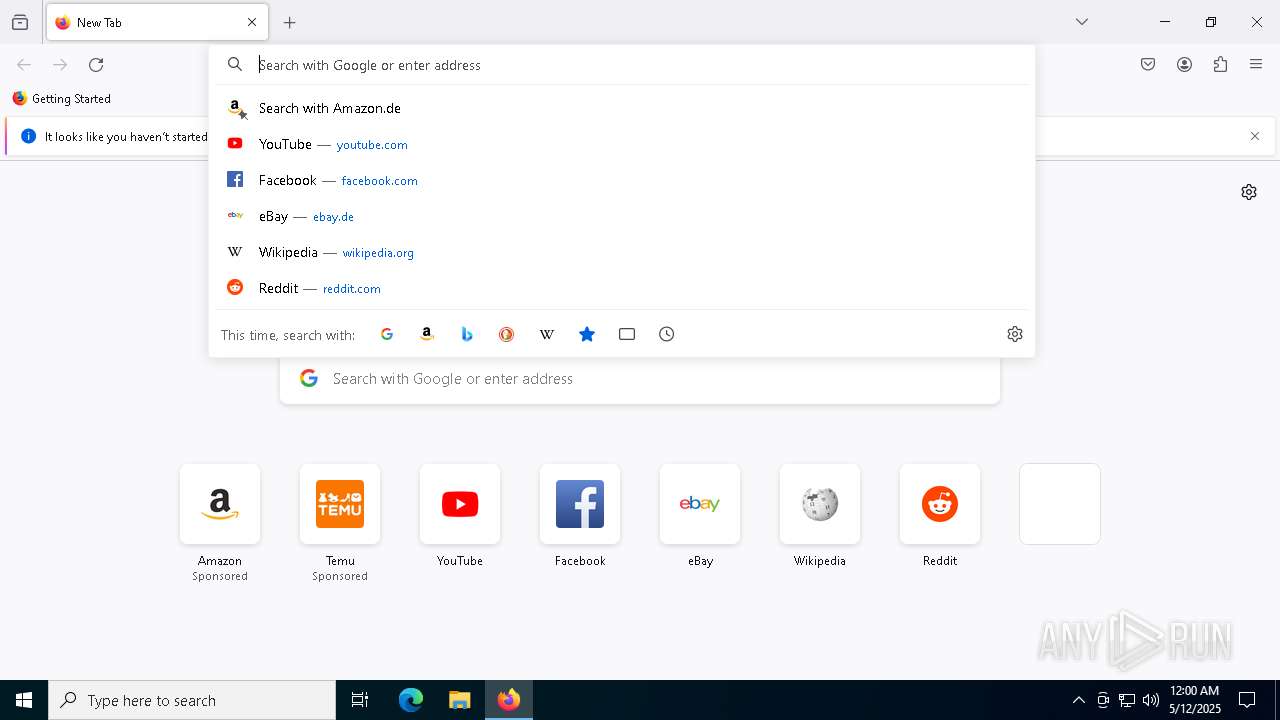
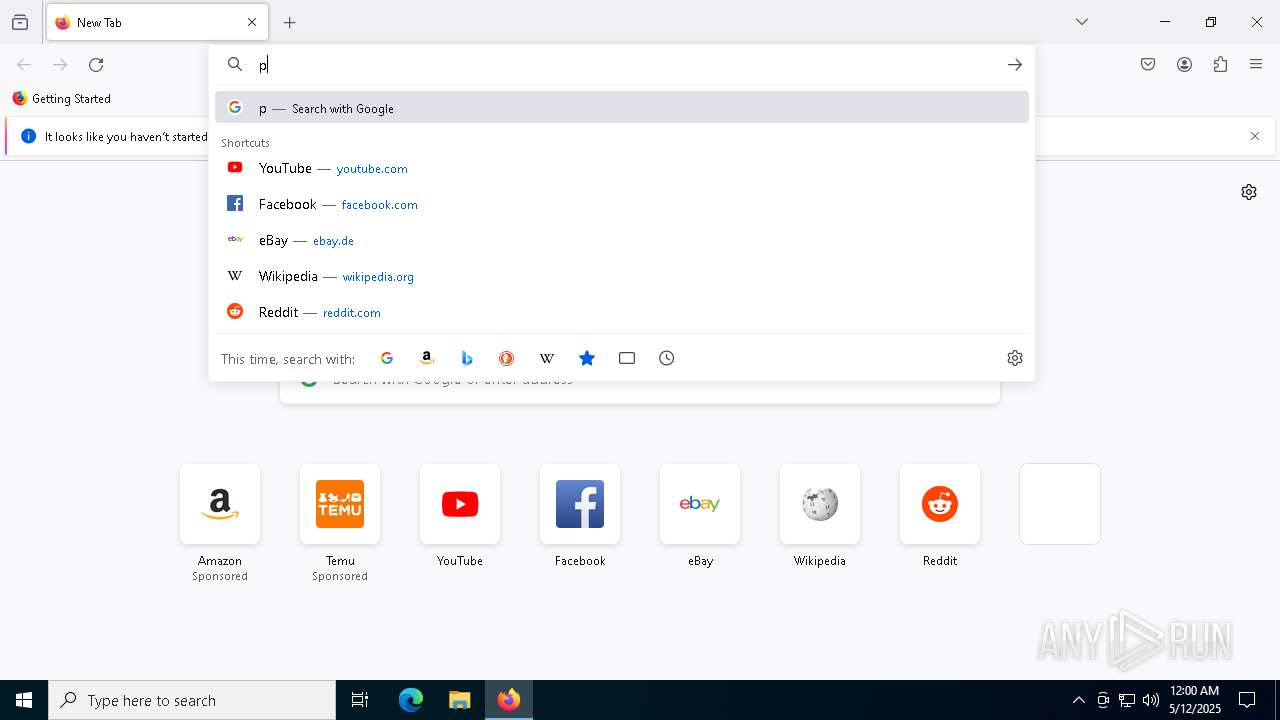
Manual execution by a user
- firefox.exe (PID: 536)
- Etni.com (PID: 5736)
Application launched itself
- firefox.exe (PID: 536)
- firefox.exe (PID: 6540)
Checks proxy server information
- Etni.com (PID: 7380)
- MicrosoftEdgeUpdate.exe (PID: 7872)
- wermgr.exe (PID: 7984)
- slui.exe (PID: 1912)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 7872)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 7872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:10:12 02:21:52+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.26 |
| CodeSize: | 342016 |
| InitializedDataSize: | 883712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xadcf |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.4 |
| ProductVersionNumber: | 1.0.0.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Process default |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.4 |
| LegalCopyright: | Copyright (C) 2022 Cent Studio |
| ProductName: | Screen Capture |
| ProductVersion: | 1.0.0.4 |
Total processes
164
Monitored processes
33
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1904 -parentBuildID 20240213221259 -prefsHandle 1840 -prefMapHandle 1832 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {24f97323-2f90-4d21-a24d-f4ab8aa90668} 6540 "\\.\pipe\gecko-crash-server-pipe.6540" 220405f0410 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 1912 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\Desktop\setup.exe" | C:\Users\admin\Desktop\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 3124 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5168 -childID 3 -isForBrowser -prefsHandle 5184 -prefMapHandle 4328 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1536 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c2a98056-fd4e-4ef1-8c86-b750108ab772} 6540 "\\.\pipe\gecko-crash-server-pipe.6540" 22049d7bd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4188 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4812 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4196 -childID 2 -isForBrowser -prefsHandle 4188 -prefMapHandle 4184 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1536 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {eba14735-6c31-4db3-9207-5e5b146da6ab} 6540 "\\.\pipe\gecko-crash-server-pipe.6540" 2204716b4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4880 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 944
Read events
22 905
Write events
37
Delete events
2
Modification events
| (PID) Process: | (4188) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6540) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7380) Etni.com | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7380) Etni.com | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7380) Etni.com | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7872) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\proxy |
| Operation: | write | Name: | source |
Value: auto | |||
| (PID) Process: | (7872) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MicrosoftEdgeUpdate.exe |
| Operation: | write | Name: | DisableExceptionChainValidation |
Value: 0 | |||
| (PID) Process: | (7872) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{38C7694F-7DD2-4744-B011-0CD3928BB707} |
| Operation: | write | Name: | PersistedPingString |
Value: <?xml version="1.0" encoding="UTF-8"?><request protocol="3.0" updater="Omaha" updaterversion="1.3.195.25" shell_version="1.3.147.37" ismachine="1" sessionid="{3DCFE76C-06D1-4667-8304-2321C62DD1BA}" userid="{FD984739-A122-4DB0-BE5B-46E3E09D84E4}" installsource="otherinstallcmd" requestid="{38C7694F-7DD2-4744-B011-0CD3928BB707}" dedup="cr" domainjoined="0"><hw logical_cpus="4" physmemory="4" disk_type="2" sse="1" sse2="1" sse3="1" ssse3="1" sse41="1" sse42="1" avx="1"/><os platform="win" version="10.0.19045.4046" sp="" arch="x64" product_type="48" is_wip="0" is_in_lockdown_mode="0"/><oem product_manufacturer="DELL" product_name="DELL"/><exp etag=""r452t1+k2Tgq/HXzjvFNBRhopBWR9sbjXxqeUDH9uX0=""/><app appid="{F3C4FE00-EFD5-403B-9569-398A20F1BA4A}" version="1.3.185.17" nextversion="1.3.195.25" lang="" brand="" client=""><event eventtype="2" eventresult="1" errorcode="0" extracode1="0" system_uptime_ticks="10639606388" install_time_ms="344"/></app></request> | |||
| (PID) Process: | (7872) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{38C7694F-7DD2-4744-B011-0CD3928BB707} |
| Operation: | write | Name: | PersistedPingTime |
Value: 133914816311963267 | |||
| (PID) Process: | (7872) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{38C7694F-7DD2-4744-B011-0CD3928BB707} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
211
Suspicious files
175
Text files
21
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6540 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5416 | TransactorSmart.exe | C:\ProgramData\asus\DivXDownloadManager.dll | executable | |
MD5:E1146619FC1DB71A1E3668371342E626 | SHA256:A39E5A8204F10AD32C0156569439624D744A4D504CBEF9925E94BCC7439FEC0E | |||
| 2392 | setup.exe | C:\Users\admin\AppData\Local\Temp\UZVFQ02X3EUGGPQJR\aurelian.torrent | binary | |
MD5:73051F1FED9D7F0B21D4CDC48224A32B | SHA256:C050D48792242351FD33A0375F262B8743EB61164D250D27758286C9083FE3FD | |||
| 5416 | TransactorSmart.exe | C:\ProgramData\asus\msvcp80.dll | executable | |
MD5:272A9E637ADCAF30B34EA184F4852836 | SHA256:35B15B78C31111DB4FA11D9C9CAD3A6F22C92DAA5E6F069DC455E72073266CC4 | |||
| 2392 | setup.exe | C:\Users\admin\AppData\Local\Temp\UZVFQ02X3EUGGPQJR\TransactorSmart.exe | executable | |
MD5:FF254C1778AEFE5AF06889F1F999DEE3 | SHA256:94BC0C01641801F258E207ECA8227845F3F1C686E7394CE3864A6B2538B8EADB | |||
| 5112 | TransactorSmart.exe | C:\ProgramData\asus\tcpvcon.exe | executable | |
MD5:1CF39530D557CE880D7F71984928384F | SHA256:198995FECC0E38A2749B7E48C54112A959B77878683B726EE36430C4BACEC196 | |||
| 2392 | setup.exe | C:\Users\admin\AppData\Local\Temp\UZVFQ02X3EUGGPQJR\msvcp80.dll | executable | |
MD5:272A9E637ADCAF30B34EA184F4852836 | SHA256:35B15B78C31111DB4FA11D9C9CAD3A6F22C92DAA5E6F069DC455E72073266CC4 | |||
| 6540 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5416 | TransactorSmart.exe | C:\ProgramData\asus\TransactorSmart.exe | executable | |
MD5:FF254C1778AEFE5AF06889F1F999DEE3 | SHA256:94BC0C01641801F258E207ECA8227845F3F1C686E7394CE3864A6B2538B8EADB | |||
| 5416 | TransactorSmart.exe | C:\ProgramData\asus\msvcr80.dll | executable | |
MD5:43143ABB001D4211FAB627C136124A44 | SHA256:CB8928FF2FAF2921B1EDDC267DCE1BB64E6FEE4D15B68CD32588E0F3BE116B03 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
87
DNS requests
107
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2148 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6540 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2148 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6540 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6540 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
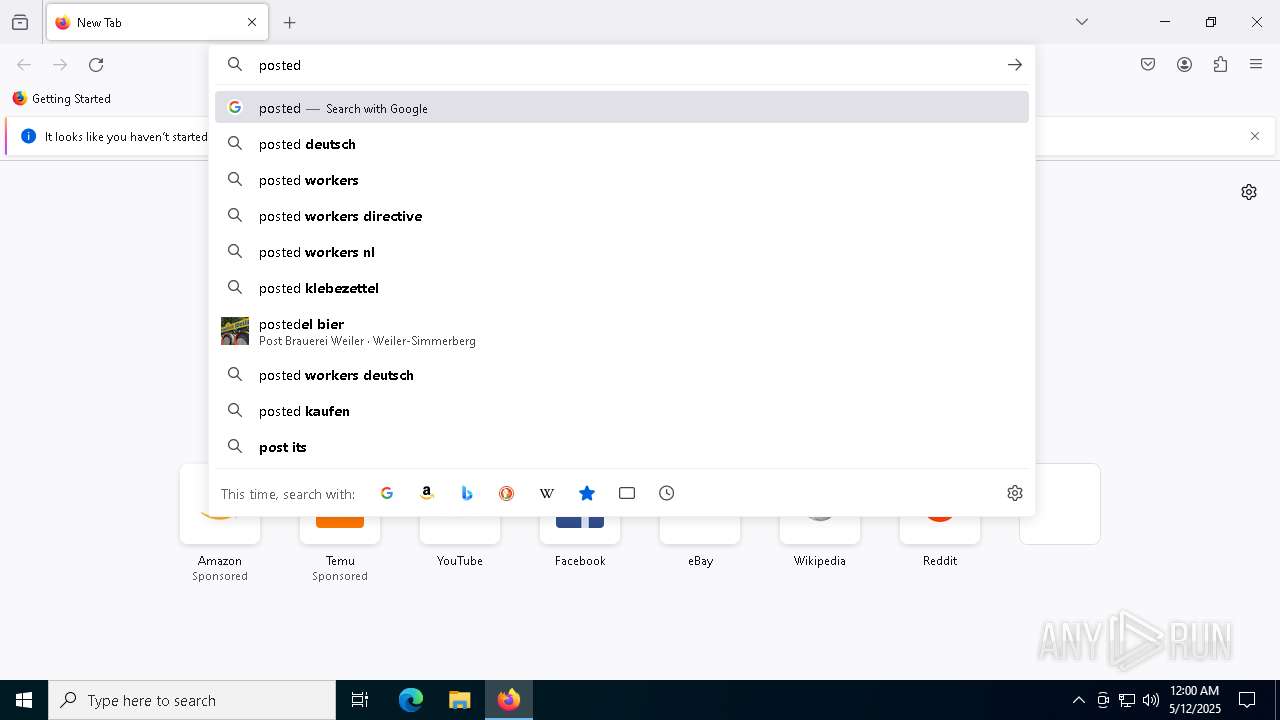
neutronryn.live |
| unknown |
unitech.x10.mx |
| unknown |
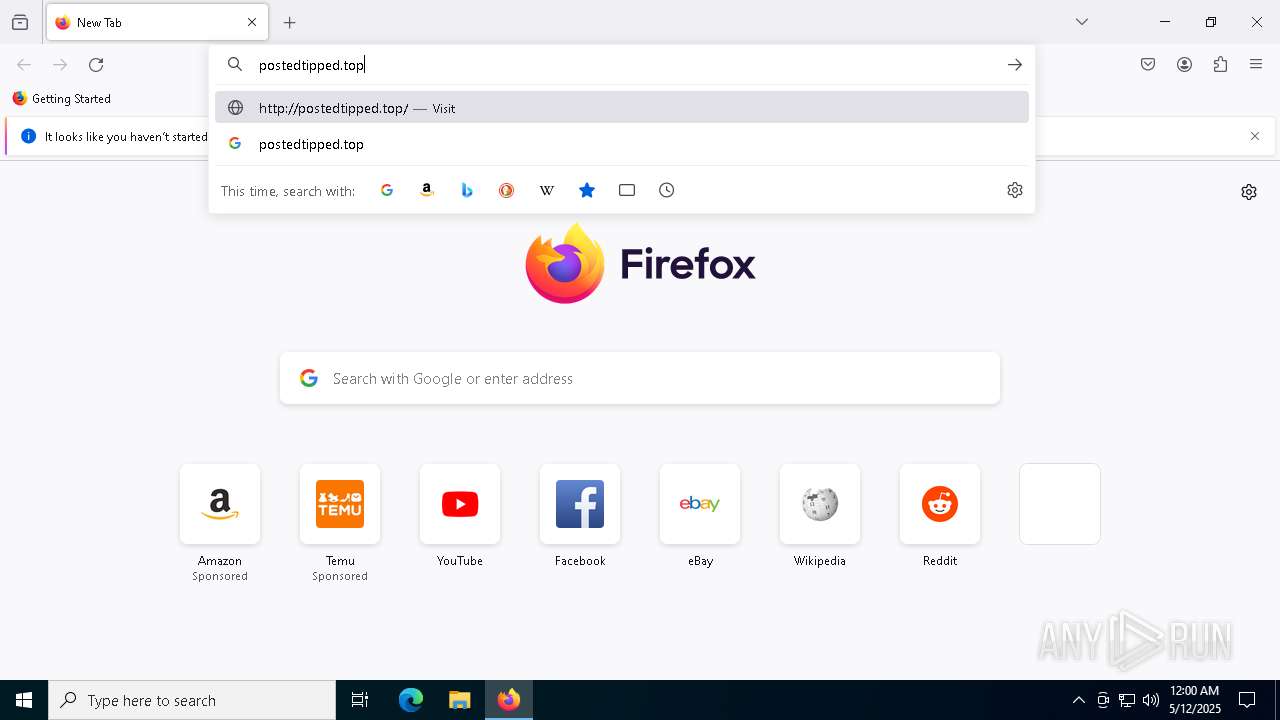
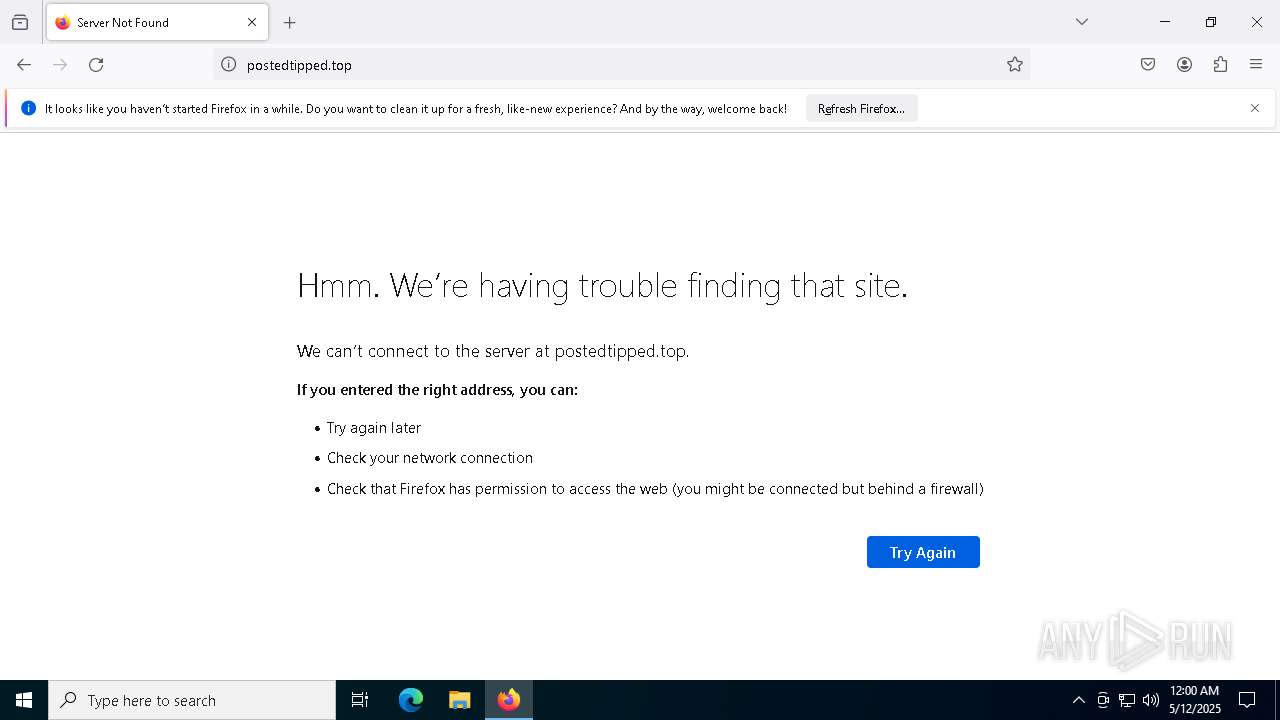
h1.postedtipped.top |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (postedtipped .top) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (postedtipped .top) |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (postedtipped .top) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES DNS Query to Commonly Actor Abused Online Service (data-seed-prebsc-1-s1 .binance .org) |
7380 | Etni.com | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (data-seed-prebsc-1-s1 .binance .org in TLS SNI) |