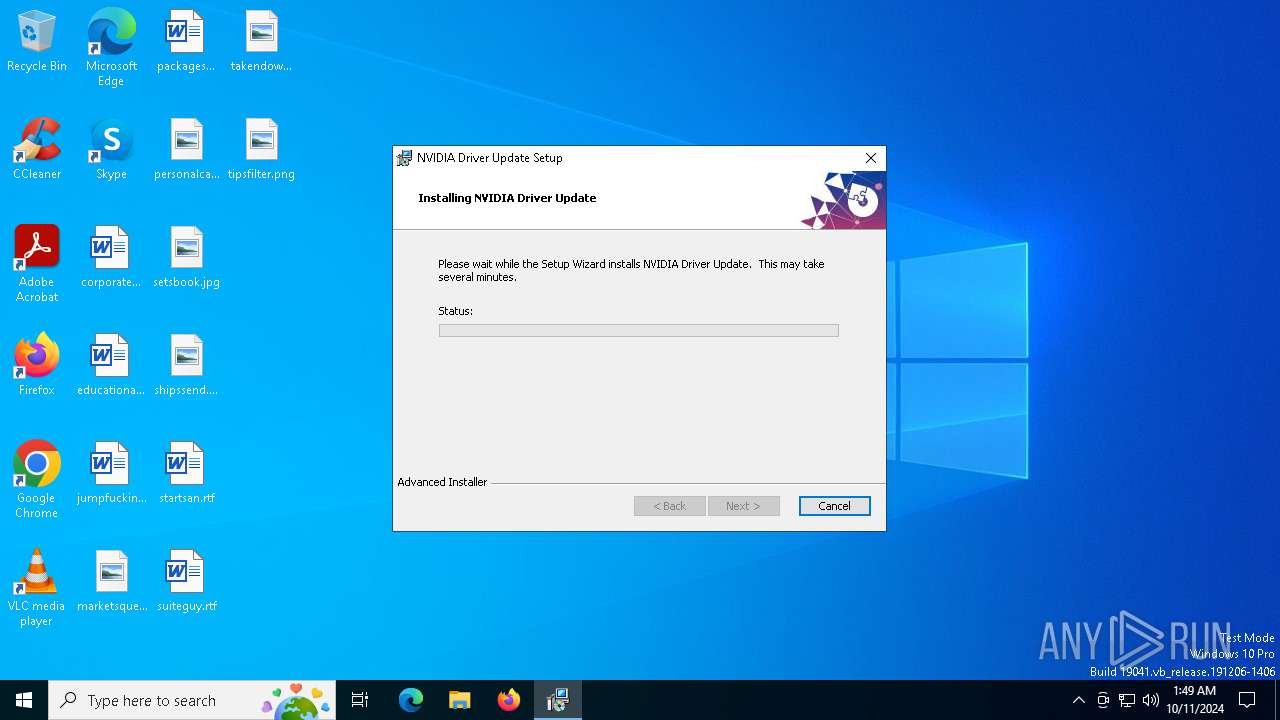
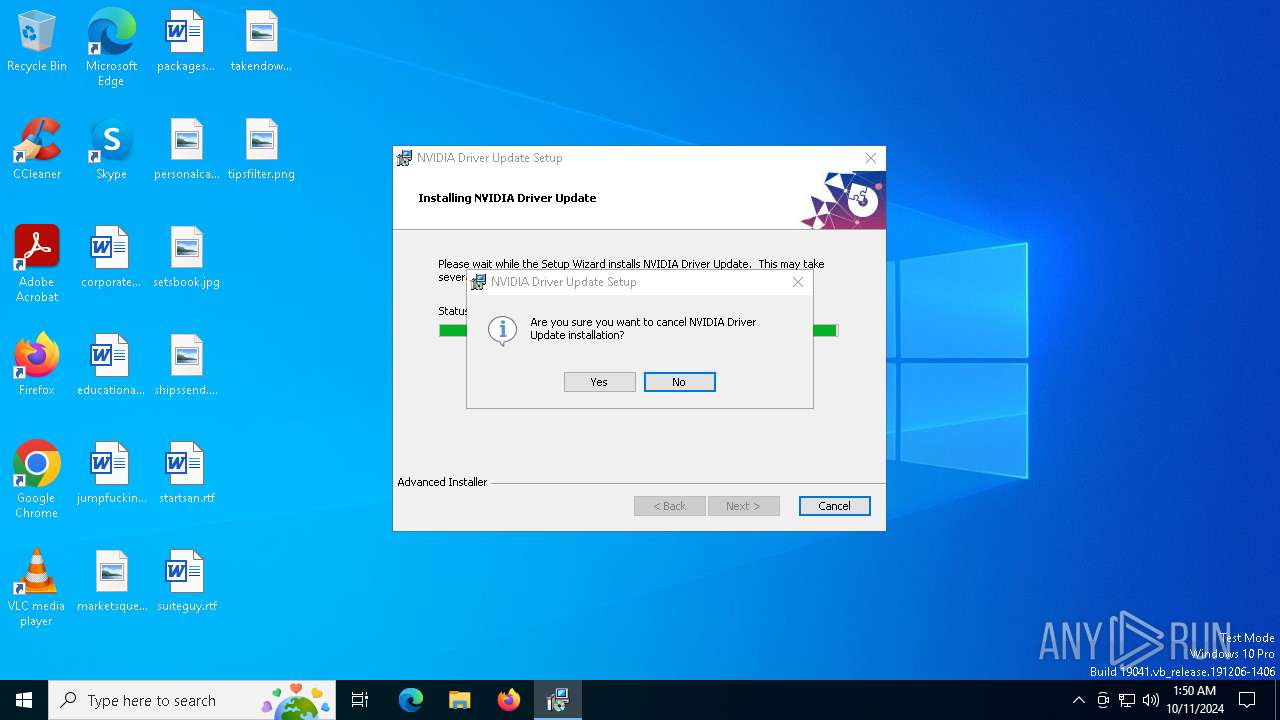
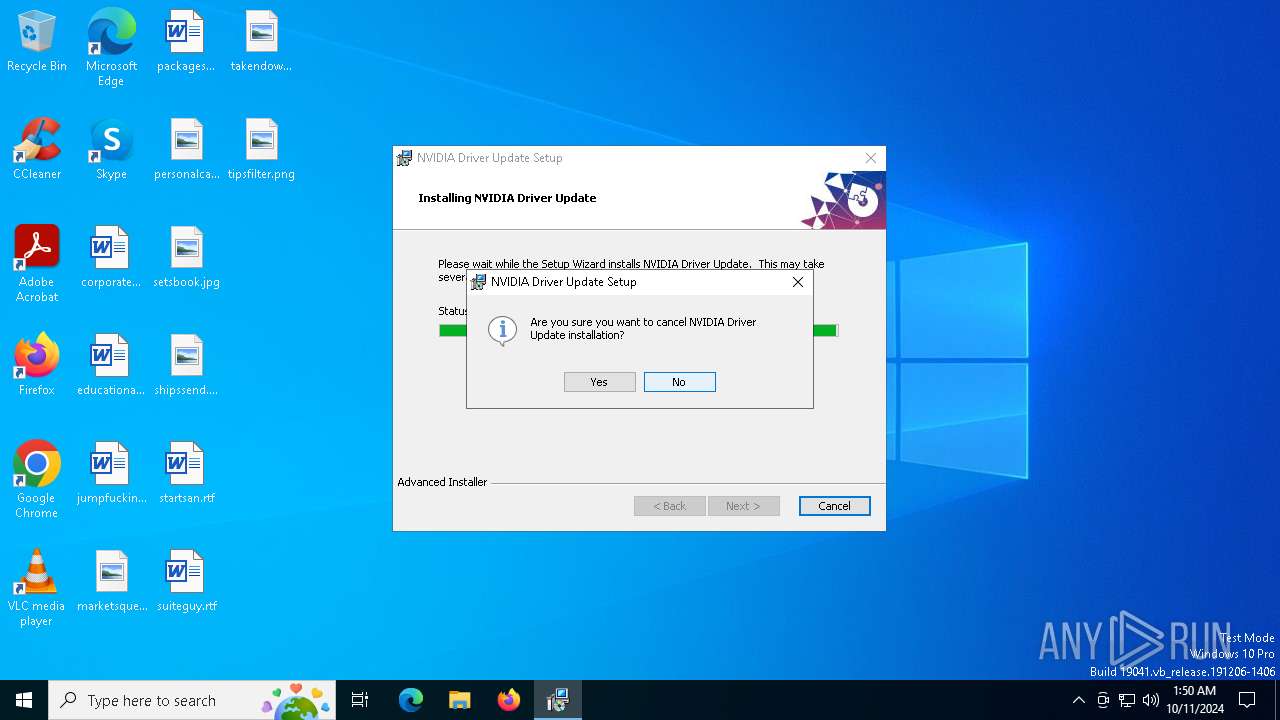
| File name: | nvinstall.msi |
| Full analysis: | https://app.any.run/tasks/16f7706e-2e87-4545-a9cd-ee52300d83ba |
| Verdict: | Malicious activity |
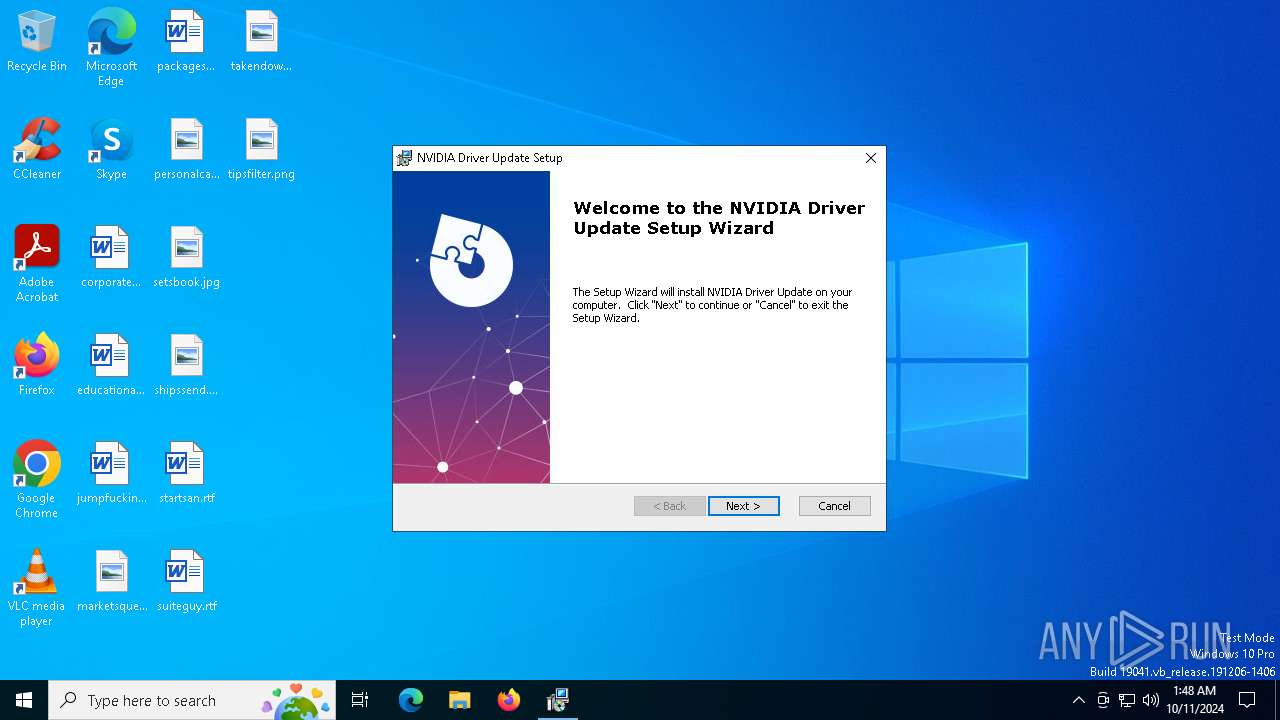
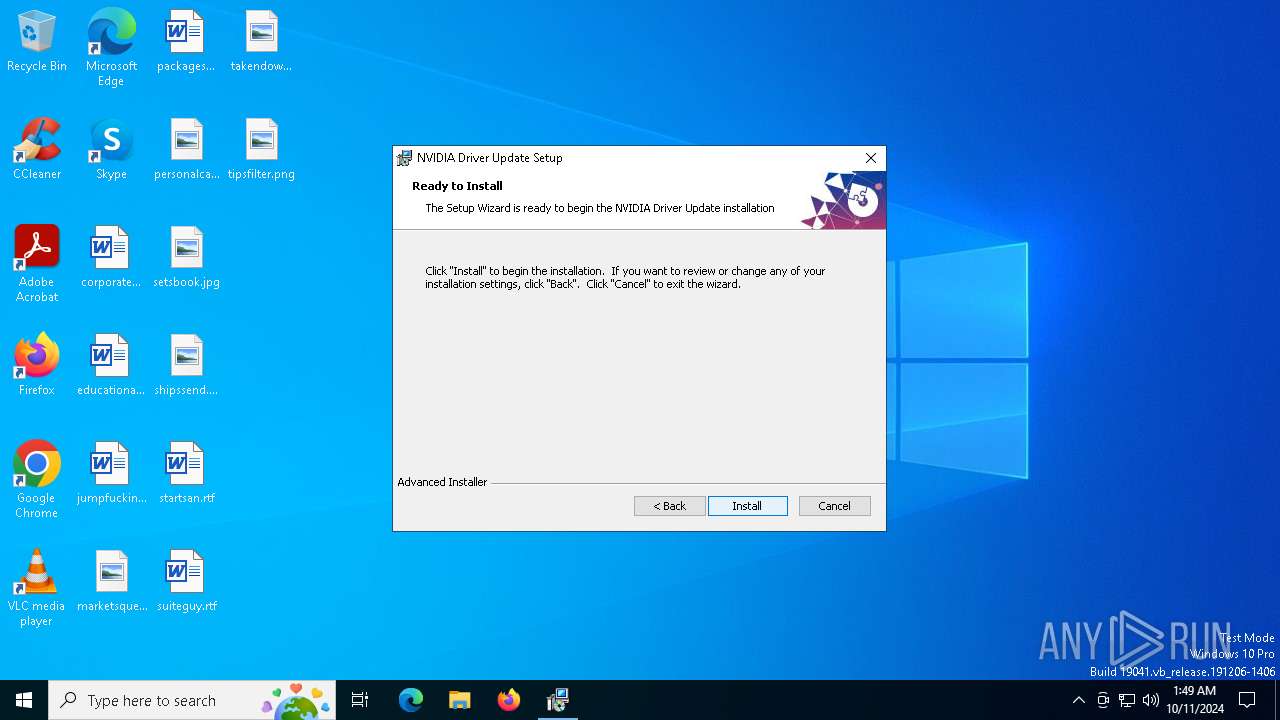
| Threats: | Bumblebee is a highly adaptable malware loader, often used by threat actors linked to the Conti and TrickBot cybercrime groups. Since its discovery in 2021, Bumblebee has been leveraged in phishing campaigns and email thread hijacking, primarily to distribute payloads like Cobalt Strike and ransomware. The malware employs obfuscation techniques, such as DLL injection and virtual environment detection, to avoid detection and sandbox analysis. Its command-and-control infrastructure and anti-analysis features allow it to persist on infected devices, where it enables further payload downloads and system compromise. |
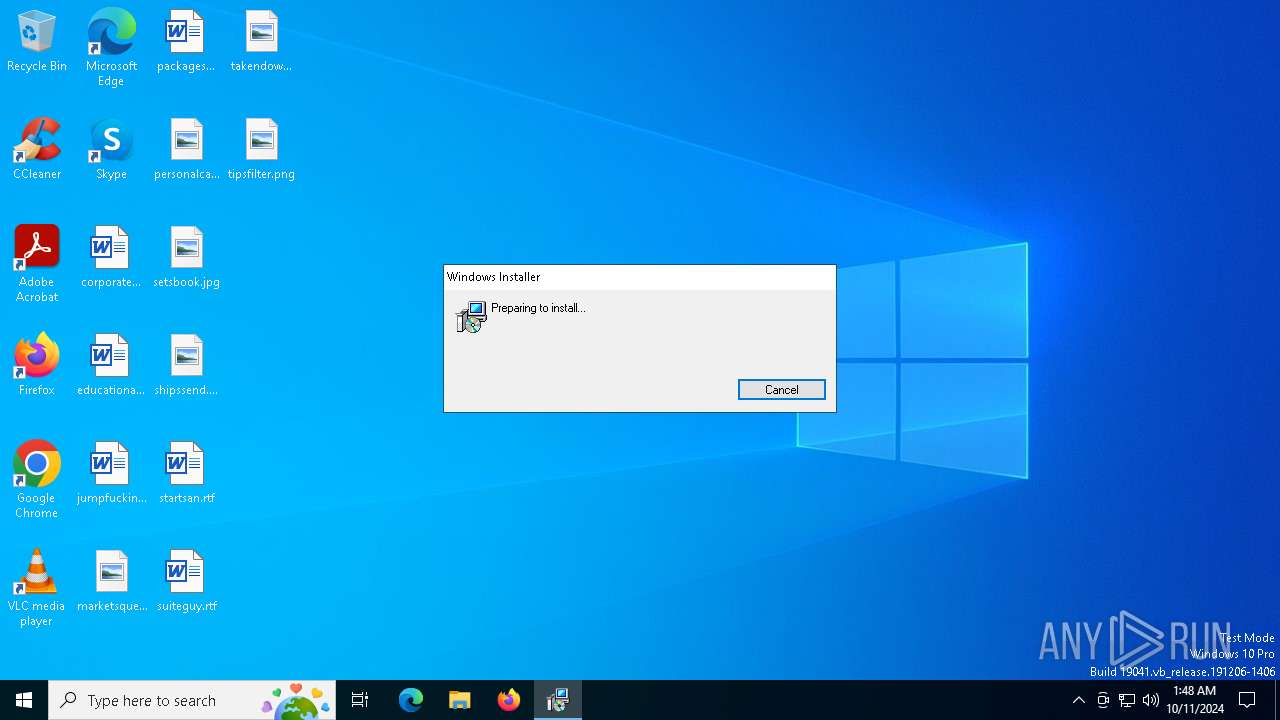
| Analysis date: | October 11, 2024, 01:48:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {96368533-618C-411D-9F0D-AA4591BE1161}, Number of Words: 10, Subject: NVIDIA Driver Update, Author: NVIDIA corp., Name of Creating Application: NVIDIA Driver Update, Template: ;1033, Comments: This installer database contains the logic and data required to install NVIDIA Driver Update., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Tue Oct 8 17:05:26 2024, Last Saved Time/Date: Tue Oct 8 17:05:26 2024, Last Printed: Tue Oct 8 17:05:26 2024, Number of Pages: 450 |
| MD5: | BC9F159C780F8092641FAA7CB0BA81A1 |
| SHA1: | 66D338E045B58295DE3657FA0EA1F491435837E1 |
| SHA256: | 0AB5B3E9790AA8ADA1BBADD5D22908B5BA7B9F078E8F5B4E8FCC27CC0011CCE7 |
| SSDEEP: | 98304:Y9ILo8oTiN0Rze47L5Tlhy2Trk7csqMLpaqTIFzb4kFWDab4N2e4m05U4F9rjGPj:KyW4IJUm |
MALICIOUS
BUMBLEBEE has been detected (YARA)
- msiexec.exe (PID: 5264)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 4040)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5984)
There is functionality for capture public ip (YARA)
- msiexec.exe (PID: 5264)
There is functionality for VM detection (VirtualBox)
- msiexec.exe (PID: 5264)
Checks for external IP
- msiexec.exe (PID: 5264)
INFO
Checks supported languages
- msiexec.exe (PID: 5984)
- msiexec.exe (PID: 916)
- msiexec.exe (PID: 3960)
Reads the computer name
- msiexec.exe (PID: 916)
- msiexec.exe (PID: 5984)
- msiexec.exe (PID: 3960)
An automatically generated document
- msiexec.exe (PID: 5616)
Reads Environment values
- msiexec.exe (PID: 916)
- msiexec.exe (PID: 3960)
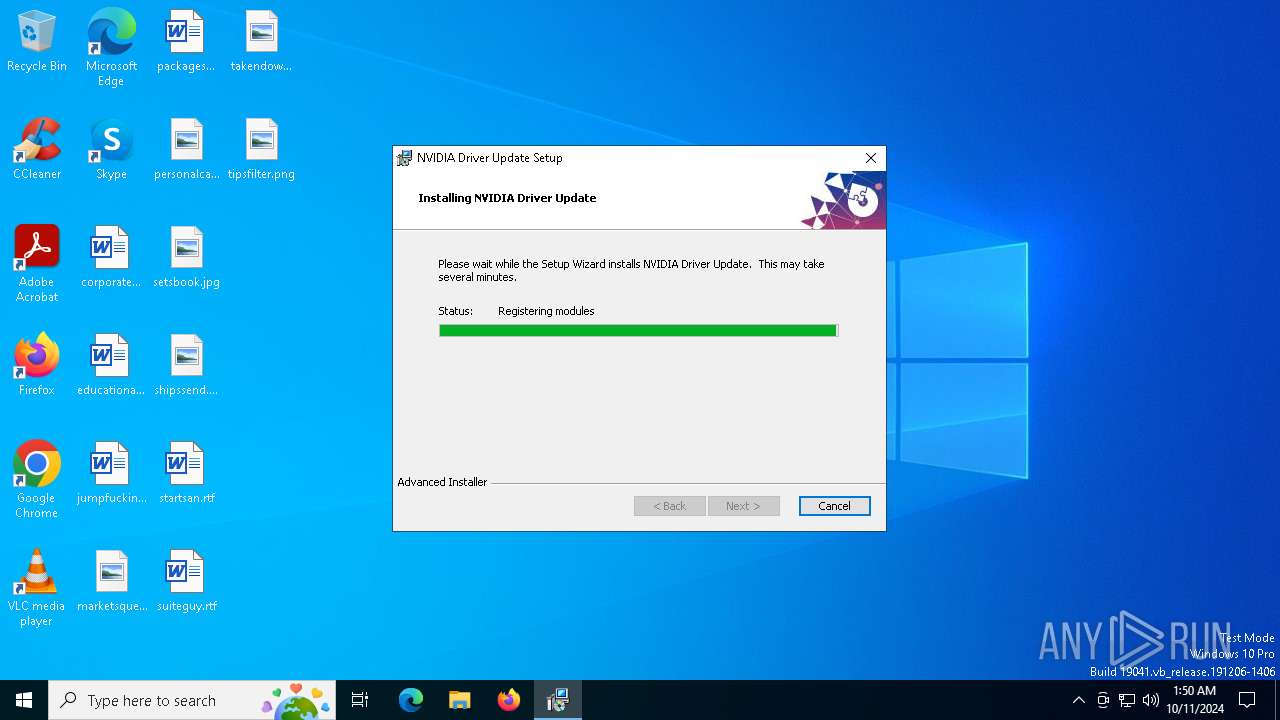
Executable content was dropped or overwritten
- msiexec.exe (PID: 5616)
- msiexec.exe (PID: 5984)
Manages system restore points
- SrTasks.exe (PID: 6216)
Application launched itself
- msiexec.exe (PID: 5984)
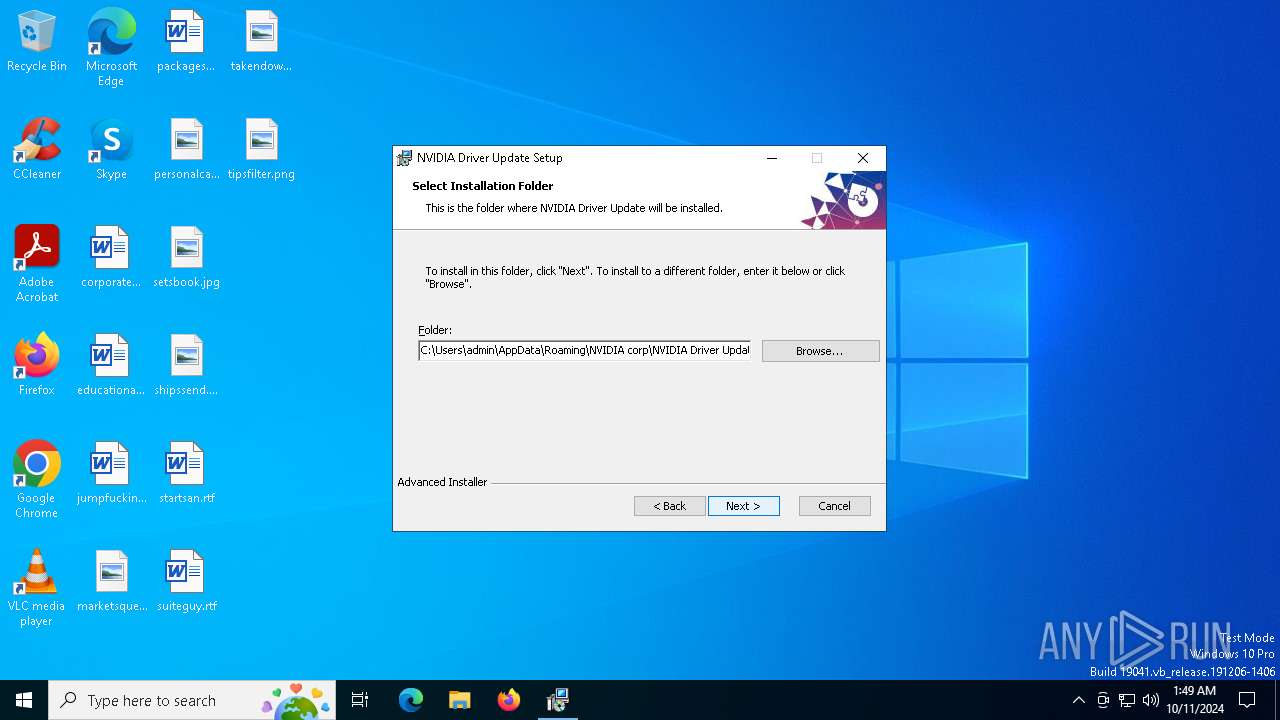
Creates files or folders in the user directory
- msiexec.exe (PID: 5984)
- msiexec.exe (PID: 5264)
Checks proxy server information
- msiexec.exe (PID: 5264)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5264)
Reads the software policy settings
- msiexec.exe (PID: 5264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {96368533-618C-411D-9F0D-AA4591BE1161} |
| Words: | 10 |
| Subject: | NVIDIA Driver Update |
| Author: | NVIDIA corp. |
| LastModifiedBy: | - |
| Software: | NVIDIA Driver Update |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install NVIDIA Driver Update. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:10:08 17:05:26 |
| ModifyDate: | 2024:10:08 17:05:26 |
| LastPrinted: | 2024:10:08 17:05:26 |
| Pages: | 450 |
Total processes
133
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | C:\Windows\syswow64\MsiExec.exe -Embedding 6F51903ACF76DB36AE40F0F1CEE4AF47 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3960 | C:\Windows\syswow64\MsiExec.exe -Embedding 3E2A98866086558BA60B414FA924CD4A | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5264 | "C:\Windows\System32\MsiExec.exe" /Y "C:\Users\admin\AppData\Roaming\zoHnNvuTkk.dll" | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5616 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\nvinstall.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5984 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6216 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 569
Read events
3 380
Write events
180
Delete events
9
Modification events
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000001C2B6EC17F1BDB016017000048120000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000001C2B6EC17F1BDB016017000048120000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000778FAEC17F1BDB016017000048120000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000778FAEC17F1BDB016017000048120000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000008358B3C17F1BDB016017000048120000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000007A1FB8C17F1BDB016017000048120000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000EC852AC27F1BDB016017000048120000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5984) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C4E92CC27F1BDB0160170000E8080000E803000001000000000000000000000044C3ADCF38DC7949961733FD3B1F284E00000000000000000000000000000000 | |||
| (PID) Process: | (4040) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000698D36C27F1BDB01C80F0000F0170000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
11
Suspicious files
10
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5984 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5984 | msiexec.exe | C:\Windows\Installer\91726.msi | — | |
MD5:— | SHA256:— | |||
| 5616 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIAF05.tmp | executable | |
MD5:AA88D8F40A286B6D40DE0F3ABC836CFA | SHA256:8D633EFEDA1249356B11BF8F46583242356E4F903056B53BD25A99511D1790A1 | |||
| 5984 | msiexec.exe | C:\Windows\Installer\MSI193A.tmp | executable | |
MD5:AA88D8F40A286B6D40DE0F3ABC836CFA | SHA256:8D633EFEDA1249356B11BF8F46583242356E4F903056B53BD25A99511D1790A1 | |||
| 5984 | msiexec.exe | C:\Windows\Installer\MSI1A26.tmp | binary | |
MD5:A939D3E3019605561ECB7C9399308C67 | SHA256:819FDBF3351DEDD1C97E077B9D5FC9F24D96C434B1AFCAA52A4D327CEB52DD41 | |||
| 5616 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB3BE.tmp | executable | |
MD5:AA88D8F40A286B6D40DE0F3ABC836CFA | SHA256:8D633EFEDA1249356B11BF8F46583242356E4F903056B53BD25A99511D1790A1 | |||
| 5616 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB08D.tmp | executable | |
MD5:AA88D8F40A286B6D40DE0F3ABC836CFA | SHA256:8D633EFEDA1249356B11BF8F46583242356E4F903056B53BD25A99511D1790A1 | |||
| 5984 | msiexec.exe | C:\Windows\Installer\MSI17A3.tmp | executable | |
MD5:AA88D8F40A286B6D40DE0F3ABC836CFA | SHA256:8D633EFEDA1249356B11BF8F46583242356E4F903056B53BD25A99511D1790A1 | |||
| 5984 | msiexec.exe | C:\Windows\Installer\MSI1979.tmp | executable | |
MD5:AA88D8F40A286B6D40DE0F3ABC836CFA | SHA256:8D633EFEDA1249356B11BF8F46583242356E4F903056B53BD25A99511D1790A1 | |||
| 5984 | msiexec.exe | C:\Windows\Temp\~DF7B690208481460EF.TMP | binary | |
MD5:43BF3345BFEB0637638148FBC93DFD1F | SHA256:C42EB3C1538265F3EC9AA16E2D18AFEF9806D380A30F4D7F30B17373B3CE6D58 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
48
DNS requests
39
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.10.249.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | CH | binary | 1.01 Kb | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.21.137.121:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 2.21.137.121:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
5264 | msiexec.exe | GET | 200 | 142.250.185.99:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
5264 | msiexec.exe | GET | 200 | 142.250.185.99:80 | http://c.pki.goog/r/r4.crl | US | binary | 436 b | whitelisted |
6212 | SIHClient.exe | GET | 200 | 2.21.137.121:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6212 | SIHClient.exe | GET | 200 | 2.21.137.121:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.10.249.24:80 | crl.microsoft.com | Akamai International B.V. | CH | whitelisted |
— | — | 2.21.133.195:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 2.21.133.195:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.21.137.121:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.21.137.121:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
tvx1ovdepj8.life |
| unknown |
acgr6r8zdot.life |
| unknown |
ilofx941igp.life |
| malicious |
8x2apo5m7ri.life |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5264 | msiexec.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |