| File name: | G9996757243586095_5678.zip |
| Full analysis: | https://app.any.run/tasks/dc6f942a-b3b8-48e0-84d9-dc038ae09084 |
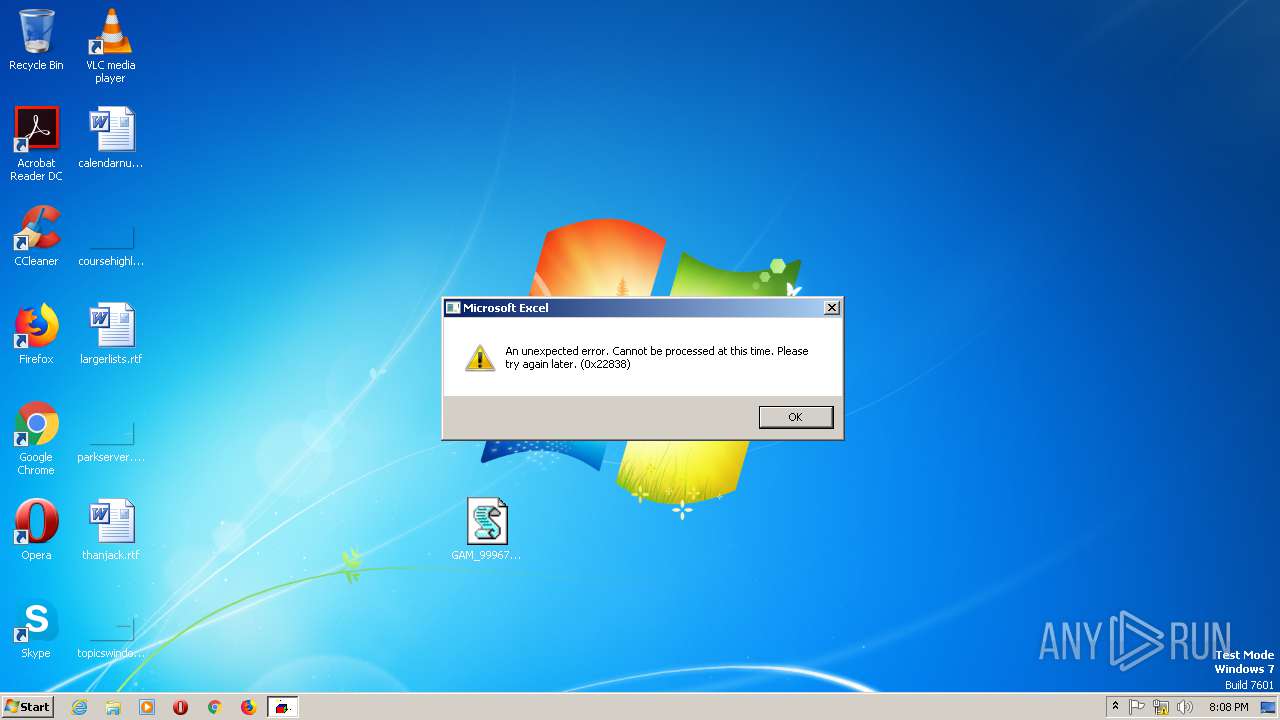
| Verdict: | Malicious activity |
| Threats: | Hancitor was created in 2014 to drop other malware on infected machines. It is also known as Tordal and Chanitor. This malware is available as a service which makes it accessible tools to criminals and contributes to the popularity of this virus. |
| Analysis date: | December 02, 2019, 20:08:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | AB8C2A1C3CEB5D3674C055CF7D644B8F |
| SHA1: | 909AB631E9303D805C5F28C19BA0BBBF77F6880B |
| SHA256: | 0A87EB9834F49DE095DF87CE3BE314772D34C95C7DA1A1846A313D58B430FB71 |
| SSDEEP: | 3072:hbqGgI895rrRpgCpRSWeOp2wLw5B6+Rsb/UekJxCZ6Eeby7vI:hbqi8/rrRpvTeOp2w6B6c0/UdJxCgtUQ |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 988)
HANCITOR was detected
- svchost.exe (PID: 2304)
Connects to CnC server
- svchost.exe (PID: 2304)
- IEXPLORE.EXE (PID: 2924)
- IEXPLORE.EXE (PID: 1084)
- IEXPLORE.EXE (PID: 1748)
- IEXPLORE.EXE (PID: 2448)
- IEXPLORE.EXE (PID: 2524)
- IEXPLORE.EXE (PID: 2844)
- IEXPLORE.EXE (PID: 3064)
- IEXPLORE.EXE (PID: 2584)
- IEXPLORE.EXE (PID: 2700)
- IEXPLORE.EXE (PID: 1504)
- IEXPLORE.EXE (PID: 1776)
- IEXPLORE.EXE (PID: 2168)
- IEXPLORE.EXE (PID: 592)
- IEXPLORE.EXE (PID: 2320)
- IEXPLORE.EXE (PID: 2120)
- IEXPLORE.EXE (PID: 344)
- IEXPLORE.EXE (PID: 3012)
- IEXPLORE.EXE (PID: 3068)
- IEXPLORE.EXE (PID: 2508)
- IEXPLORE.EXE (PID: 2600)
- IEXPLORE.EXE (PID: 3024)
- IEXPLORE.EXE (PID: 1696)
- IEXPLORE.EXE (PID: 1716)
- IEXPLORE.EXE (PID: 1640)
- IEXPLORE.EXE (PID: 3240)
- IEXPLORE.EXE (PID: 3716)
- IEXPLORE.EXE (PID: 3560)
- IEXPLORE.EXE (PID: 3536)
- IEXPLORE.EXE (PID: 3892)
- IEXPLORE.EXE (PID: 3096)
- IEXPLORE.EXE (PID: 864)
- IEXPLORE.EXE (PID: 3388)
- IEXPLORE.EXE (PID: 3332)
- IEXPLORE.EXE (PID: 3080)
- IEXPLORE.EXE (PID: 2720)
- IEXPLORE.EXE (PID: 3164)
- IEXPLORE.EXE (PID: 4012)
- IEXPLORE.EXE (PID: 3760)
Uses SVCHOST.EXE for hidden code execution
- regsvr32.exe (PID: 988)
Application was dropped or rewritten from another process
- BNBA83.tmp (PID: 2376)
URSNIF was detected
- IEXPLORE.EXE (PID: 2924)
- IEXPLORE.EXE (PID: 1084)
- IEXPLORE.EXE (PID: 1748)
- IEXPLORE.EXE (PID: 2448)
- IEXPLORE.EXE (PID: 2844)
- IEXPLORE.EXE (PID: 3064)
- IEXPLORE.EXE (PID: 2524)
- IEXPLORE.EXE (PID: 2700)
- IEXPLORE.EXE (PID: 2584)
- IEXPLORE.EXE (PID: 1504)
- IEXPLORE.EXE (PID: 1776)
- IEXPLORE.EXE (PID: 2168)
- IEXPLORE.EXE (PID: 592)
- IEXPLORE.EXE (PID: 2320)
- IEXPLORE.EXE (PID: 2120)
- IEXPLORE.EXE (PID: 344)
- IEXPLORE.EXE (PID: 3012)
- IEXPLORE.EXE (PID: 3068)
- IEXPLORE.EXE (PID: 2508)
- IEXPLORE.EXE (PID: 2600)
- IEXPLORE.EXE (PID: 3024)
- IEXPLORE.EXE (PID: 1696)
- IEXPLORE.EXE (PID: 1716)
- IEXPLORE.EXE (PID: 1640)
- IEXPLORE.EXE (PID: 3240)
- IEXPLORE.EXE (PID: 3560)
- IEXPLORE.EXE (PID: 3892)
- IEXPLORE.EXE (PID: 3536)
- IEXPLORE.EXE (PID: 3716)
- IEXPLORE.EXE (PID: 864)
- IEXPLORE.EXE (PID: 3388)
- IEXPLORE.EXE (PID: 3096)
- IEXPLORE.EXE (PID: 3332)
- IEXPLORE.EXE (PID: 3080)
- IEXPLORE.EXE (PID: 2720)
- IEXPLORE.EXE (PID: 4012)
- IEXPLORE.EXE (PID: 3164)
- IEXPLORE.EXE (PID: 3760)
SUSPICIOUS
Checks for external IP
- svchost.exe (PID: 2304)
Reads the machine GUID from the registry
- WScript.exe (PID: 1860)
- WinRAR.exe (PID: 2104)
Executed via WMI
- regsvr32.exe (PID: 2412)
Starts application with an unusual extension
- svchost.exe (PID: 2304)
Executable content was dropped or overwritten
- WScript.exe (PID: 1860)
- svchost.exe (PID: 2304)
Executed via COM
- iexplore.exe (PID: 328)
- iexplore.exe (PID: 1928)
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 148)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 1992)
- iexplore.exe (PID: 1088)
- iexplore.exe (PID: 2032)
- iexplore.exe (PID: 1476)
- iexplore.exe (PID: 1952)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 2656)
- iexplore.exe (PID: 1432)
- iexplore.exe (PID: 1644)
- iexplore.exe (PID: 772)
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 1360)
- iexplore.exe (PID: 1652)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 1092)
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 996)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 3816)
- iexplore.exe (PID: 1276)
- iexplore.exe (PID: 2940)
- iexplore.exe (PID: 1464)
- iexplore.exe (PID: 2224)
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 4032)
INFO
Reads the hosts file
- BNBA83.tmp (PID: 2376)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2924)
- IEXPLORE.EXE (PID: 1084)
- IEXPLORE.EXE (PID: 1748)
- IEXPLORE.EXE (PID: 2448)
- IEXPLORE.EXE (PID: 2524)
- IEXPLORE.EXE (PID: 3064)
- IEXPLORE.EXE (PID: 2844)
- IEXPLORE.EXE (PID: 2168)
- IEXPLORE.EXE (PID: 2584)
- IEXPLORE.EXE (PID: 2700)
- IEXPLORE.EXE (PID: 1504)
- IEXPLORE.EXE (PID: 1776)
- IEXPLORE.EXE (PID: 2120)
- IEXPLORE.EXE (PID: 592)
- IEXPLORE.EXE (PID: 2320)
- IEXPLORE.EXE (PID: 344)
- IEXPLORE.EXE (PID: 3068)
- IEXPLORE.EXE (PID: 3012)
- IEXPLORE.EXE (PID: 2600)
- IEXPLORE.EXE (PID: 2508)
- IEXPLORE.EXE (PID: 3024)
- IEXPLORE.EXE (PID: 1716)
- IEXPLORE.EXE (PID: 1696)
- IEXPLORE.EXE (PID: 3536)
- IEXPLORE.EXE (PID: 3240)
- IEXPLORE.EXE (PID: 1640)
- IEXPLORE.EXE (PID: 3716)
- IEXPLORE.EXE (PID: 3560)
- IEXPLORE.EXE (PID: 864)
- IEXPLORE.EXE (PID: 3096)
- IEXPLORE.EXE (PID: 3892)
- IEXPLORE.EXE (PID: 3388)
- IEXPLORE.EXE (PID: 2720)
- IEXPLORE.EXE (PID: 3080)
- IEXPLORE.EXE (PID: 3332)
- IEXPLORE.EXE (PID: 3164)
- IEXPLORE.EXE (PID: 4012)
- IEXPLORE.EXE (PID: 3760)
Reads Internet Cache Settings
- iexplore.exe (PID: 328)
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 1928)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 148)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 1992)
- iexplore.exe (PID: 1088)
- iexplore.exe (PID: 2032)
- iexplore.exe (PID: 1476)
- iexplore.exe (PID: 2656)
- iexplore.exe (PID: 1952)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 1432)
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 772)
- iexplore.exe (PID: 1360)
- iexplore.exe (PID: 1652)
- iexplore.exe (PID: 1644)
- iexplore.exe (PID: 1092)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 996)
- iexplore.exe (PID: 3816)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 2940)
- iexplore.exe (PID: 1276)
- iexplore.exe (PID: 1464)
- iexplore.exe (PID: 2224)
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 4032)
Changes internet zones settings
- iexplore.exe (PID: 328)
- iexplore.exe (PID: 1928)
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 148)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 1992)
- iexplore.exe (PID: 2032)
- iexplore.exe (PID: 1476)
- iexplore.exe (PID: 1088)
- iexplore.exe (PID: 1952)
- iexplore.exe (PID: 2656)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 1432)
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 772)
- iexplore.exe (PID: 1360)
- iexplore.exe (PID: 1644)
- iexplore.exe (PID: 1092)
- iexplore.exe (PID: 1652)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 996)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 3816)
- iexplore.exe (PID: 2940)
- iexplore.exe (PID: 1276)
- iexplore.exe (PID: 2224)
- iexplore.exe (PID: 1464)
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 4032)
Reads the machine GUID from the registry
- iexplore.exe (PID: 328)
- iexplore.exe (PID: 1928)
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 148)
- iexplore.exe (PID: 1992)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 2032)
- iexplore.exe (PID: 1476)
- iexplore.exe (PID: 1088)
- iexplore.exe (PID: 2656)
- iexplore.exe (PID: 1952)
- iexplore.exe (PID: 1432)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 2184)
- iexplore.exe (PID: 772)
- iexplore.exe (PID: 1360)
- iexplore.exe (PID: 1644)
- iexplore.exe (PID: 1092)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 1652)
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 3224)
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 996)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 3816)
- iexplore.exe (PID: 2940)
- iexplore.exe (PID: 1276)
- iexplore.exe (PID: 2224)
- iexplore.exe (PID: 1464)
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 4032)
Manual execution by user
- WScript.exe (PID: 1860)
Reads settings of System Certificates
- iexplore.exe (PID: 328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:02 22:09:28 |
| ZipCRC: | 0x9750ebde |
| ZipCompressedSize: | 180747 |
| ZipUncompressedSize: | 696209 |
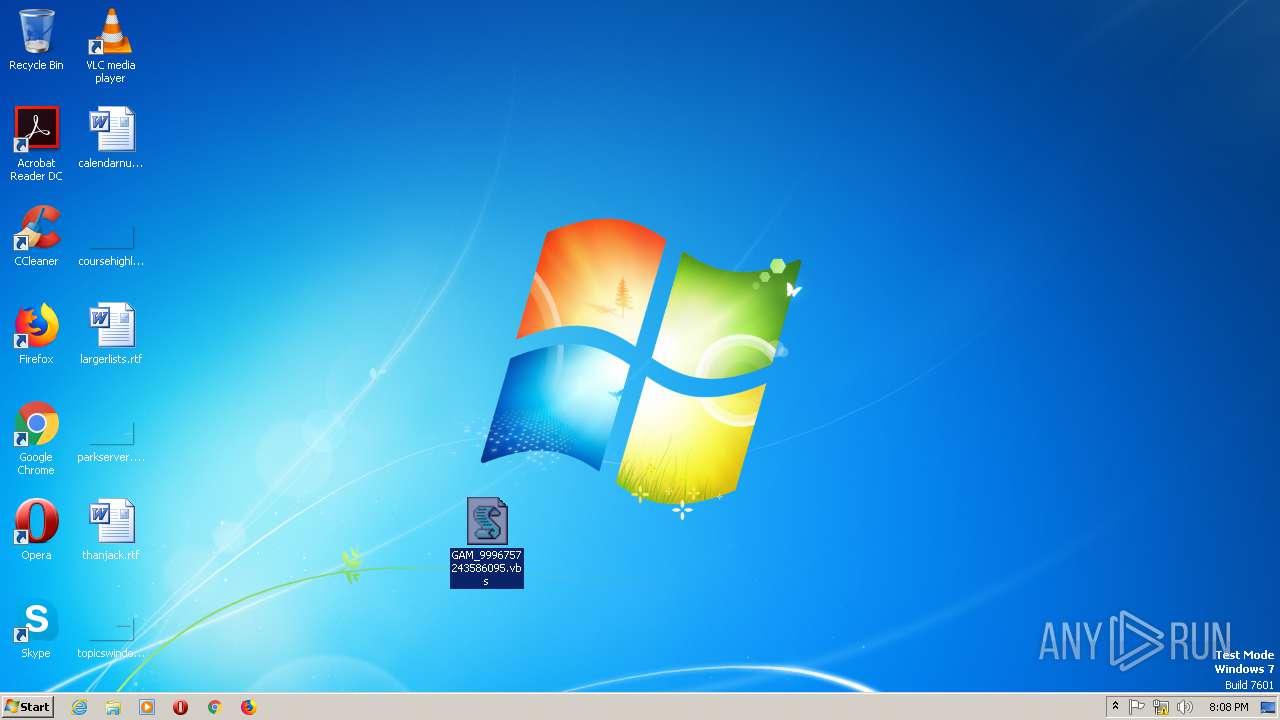
| ZipFileName: | GAM_9996757243586095.vbs |
Total processes
716
Monitored processes
82
Malicious processes
68
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 328 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 344 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:772 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2404 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 772 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3816 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 988 | -s C:\Users\admin\AppData\Local\Temp\PbzVeQP.txt | C:\Windows\SysWOW64\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1084 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:1928 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
14 028
Read events
12 539
Write events
1 451
Delete events
38
Modification events
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\G9996757243586095_5678.zip | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2104) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1600000016000000D60300000B020000 | |||
Executable files
2
Suspicious files
8
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2104.31507\GAM_9996757243586095.vbs | — | |
MD5:— | SHA256:— | |||
| 1860 | WScript.exe | C:\Users\admin\AppData\Local\Temp\FEN.txt | — | |
MD5:— | SHA256:— | |||
| 328 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1B3CEA71E2E7D8B5.TMP | — | |
MD5:— | SHA256:— | |||
| 328 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCF39638071B2824C.TMP | — | |
MD5:— | SHA256:— | |||
| 328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{97CAF642-153F-11EA-9C27-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 1928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5490426F5ABB25B4.TMP | — | |
MD5:— | SHA256:— | |||
| 1928 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{B13EF116-153F-11EA-9C27-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 1928 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF05657AA6B6FED584.TMP | — | |
MD5:— | SHA256:— | |||
| 1928 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{B13EF114-153F-11EA-9C27-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 2936 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2B8850A5B23021AF.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
136
DNS requests
46
Threats
94
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
328 | iexplore.exe | GET | — | 8.208.24.139:80 | http://8.208.24.139/favicon.ico | US | — | — | malicious |
2924 | IEXPLORE.EXE | GET | — | 8.208.24.139:80 | http://foo.fulldin.at/webstore/67nNBcPTc3bXzbkl_2Boi/7UmI4I4aidZLNNv3/yb2dMm0PgnuOCVy/3wmE0PLjh_2FhZ29_2/B8i58Stfx/5fHhoaxu_2FqvLK_2Fm3/7K6KB3HIh_2Faf01_2B/i3Uie511957PeWM_2FFr6v/5uvyyLKXyW4tf/pA2asl5n/Y0qz9o_2BkDYCNHD6IhHDiA/AyIZou7al_/2F_2ByCEiUY78_2Bo/FjRcMEFYN_2F/cSXbU9fs2yQ/wVuxmJy9aW76UU/_2BFrh0gzr7q01fLfsOza/VJhMwxTnd5U_0A_0/DAcMyoD_2BKgDIr/J_2FnjipUn/yKT_2F_2B/a | US | — | — | malicious |
1084 | IEXPLORE.EXE | GET | — | 8.208.24.139:80 | http://foo.fulldin.at/webstore/qpd_2B_2FnCiKEaRvUhB/FY_2BWrXmeb_2Fn5xa4/zKrPjkIcReyLfgsux99_2B/C1hv5MAs6sLjf/SKz7aLdl/s4DMW65KDd8OCpA2l9uEOHi/AGHKY6qxtK/Yckn0w9TiRAu4cPqD/CM1Pqe_2BU_2/FLw2dTI8ZEd/ZXOT0unmJCYzHJ/kV59Z23NzpbCRpz4E7WeS/PZHRzjGzmFcT88y0/TwFp2ERv0nM8ziX/1VFkEtdtmpkInuOIZJ/tfvlzq9Rd/scDgeT9EBKIMfApdYX_0/A_0DshcSOA9DQrvAK6n/Gw4TeGSC3V/y | US | — | — | malicious |
1928 | iexplore.exe | GET | — | 8.208.24.139:80 | http://8.208.24.139/favicon.ico | US | — | — | malicious |
1748 | IEXPLORE.EXE | GET | — | 8.208.24.139:80 | http://bat.fulldin.at/webstore/PEOn_2Bbpe/bye5ImGoRVobd7S1D/MoKmNdEf_2Fx/jxmmqVWTlPt/hX15ugakog2pCP/OjVZ6dEpC6Y1O9PEWzNrU/K5buxYZN7q5TPhmF/oph1PH4oaVb0ktt/IIc5o0CD1j1CotcCWr/g9j4gddtp/9zzpOt_2Bbf4oFqr44Ms/uCEgR_2Bvb2mm6_2Bei/w9E03_2FrMqKrKXohC_2B1/kc3EXLy81rOfz/zAAJ9QVF/sUfe2jj_2Fw1FwuQs8EgA_2/FhE5FYwBL4/tYUWg71bo_2FH4_0A/_0DST6sw0RML/3o9LDxBLYbZIxAzT/h | US | — | — | malicious |
2448 | IEXPLORE.EXE | GET | — | 8.208.24.139:80 | http://foo.fulldin.at/webstore/O8Q2OaQY1peh_2Bufy0/yJGkXQg_2FR6TR7mk9cF08/rCL_2F6I8vr_2/FS_2FNHs/bvDLtOXEGdcRJas9dwjE_2F/ttd_2BTMOr/W3v1EPm8tatLGBuYB/2lBRct9vZjp9/AF6vuakrO_2/BeA8b8iAw_2F_2/BN81iBg0RgdhmV2Xct_2B/uds5rSGQjgsMCNRy/JEp_2BcNuEj0pyY/Y1tExxE2BQNYbtqOXg/_2Fs6rgoR/CKorw7J_2FblJehEFnVz/xRuzi2zKj7zaueC1wDF/bYVJZ_2F29XVl11_0A_0Dl/biNGu3dL2EnTX/RhfM6b9c/jp4c | US | — | — | malicious |
2524 | IEXPLORE.EXE | GET | — | 8.208.24.139:80 | http://bat.fulldin.at/webstore/p0eWkshE/TavaUnqgs63kKVdLrVDVLZx/Lbo1jgQG0n/EuOTPj2mYU4RNcHE0/zr6o_2BCx945/9sJyZbAyv_2/BzuaaZGjNA_2Bp/VNxvM_2BQyLmOSVH626MY/CqdVJ6EBFnDk7cp1/zJ515AfCUH2wSrd/R7Tq9jD6oX7It5J673/BlbI9fGCc/XDrSJxxC1bTVfAVuR5MZ/MImDu0rih0KPcO263hL/w02YiWt_2FhjaAYS08tD9m/dcRtYAXvPh6_2/B952WGK3/4sQnmyul_0A_0D8VUYlBM_2/FRF76X_2BbxiFPV/KwAp4A | US | — | — | malicious |
2584 | IEXPLORE.EXE | GET | — | 8.208.24.139:80 | http://foo.fulldin.at/webstore/ZwTUp3FmAgu6uT/XvU0qAlV_2Ff9ERgYTjxZ/hYIUY145wUzLk0s9/bhzOUkYtmgxYDUQ/wVaw6ev8RTzZM_2FWj/IKP2kLJT6/UPOs0FmgyD5vwBSsz1mY/j0x8naGBPQmj1eayfDe/3lTZn6MPJcFknpfpYKDioW/IellS4rCAkZZn/uYPRroJX/6R53gT_2BYKtNq7rO0IHIu1/jKjx_2F8Mi/4WbSUCSM8YxjK898S/Rwei7i73PJot/20zlEc5X8lL/runRrzcdm5Bz_0/A_0DeUUZGKMDaqbJlnq8g/6QfG_2BD/TVe | US | — | — | malicious |
3064 | IEXPLORE.EXE | GET | — | 8.208.24.139:80 | http://bat.fulldin.at/webstore/079daTeWWh3UPB/l5a_2FD6WKtx4f8cPUcXn/WG9xWEtVctefS9Vi/iwvjQ1R5ohiHM_2/Fxbjxov8lMepP_2FuW/k9PdVmmpi/syzod_2BTK7OR4SuENvN/mFiqgtF1MYkr_2FPvLb/ky8zvi0eCpNF0vfiXaWm0Z/H_2FI72Q0FLsD/ovHNuRwr/GWjQ9snx0H5xOCNYNxsdN2K/cCJ74gRWgg/f8Rx8BZCvwo3IURR4/m4XYSY6WzKTP/mUSTucXTFnS/_2FphIfjMTiDYk/_2BBAE_0A_0DHpUB5F5g6/bu0niu1ubF4/iIt0To | US | — | — | malicious |
2844 | IEXPLORE.EXE | GET | — | 8.208.24.139:80 | http://foo.fulldin.at/webstore/keABF0EMOyLxt/EunGnqhC/bOJQ_2BSuuzEM3_2BFuH9e3/4cQp26j4tj/d3sYAW8HPL2_2FXJa/lymxZ2v74_2B/q_2BuEdi0p7/rZrBUnyifTox_2/FGYCuJN6BBz7WMeLJGr9k/kv36W8DS2PBUGK3Q/h1eawE_2F78jj9l/etKZXHHVQhtbDibGMw/c1urIJBnL/6xw5cFg_2B9Y8QX3_2Fl/WcHRrq1427bFqxv12KR/o_2BniX5mOLB2YjZSVtE23/7CID4xGjGvIWh/dqx8UD9a/gLn_0A_0DWBG1oYhRwy7Lhp/xnvzsbFei6/Xu | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2584 | IEXPLORE.EXE | 8.208.24.139:80 | foo.fulldin.at | Level 3 Communications, Inc. | US | malicious |
2168 | IEXPLORE.EXE | 8.208.24.139:80 | foo.fulldin.at | Level 3 Communications, Inc. | US | malicious |
1504 | IEXPLORE.EXE | 8.208.24.139:80 | foo.fulldin.at | Level 3 Communications, Inc. | US | malicious |
2304 | svchost.exe | 23.23.83.153:80 | api.ipify.org | Amazon.com, Inc. | US | malicious |
2304 | svchost.exe | 178.170.248.82:80 | laticivue.com | Electrics Ltd | RU | malicious |
2304 | svchost.exe | 2.57.89.115:80 | www.laadlifashionworld.com | — | — | malicious |
— | — | 8.8.8.8:53 | — | Google Inc. | US | malicious |
2924 | IEXPLORE.EXE | 8.208.24.139:80 | foo.fulldin.at | Level 3 Communications, Inc. | US | malicious |
328 | iexplore.exe | 8.208.24.139:80 | foo.fulldin.at | Level 3 Communications, Inc. | US | malicious |
2376 | BNBA83.tmp | 8.8.8.8:53 | — | Google Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
laticivue.com |
| malicious |
www.laadlifashionworld.com |
| malicious |
foo.fulldin.at |
| malicious |
bat.fulldin.at |
| malicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2304 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony/Hancitor Payload (Zeus) |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2304 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
84 ETPRO signatures available at the full report