| File name: | acer.exe |
| Full analysis: | https://app.any.run/tasks/e7a712f5-961a-45b4-a7e5-a0f7196113a5 |
| Verdict: | Malicious activity |
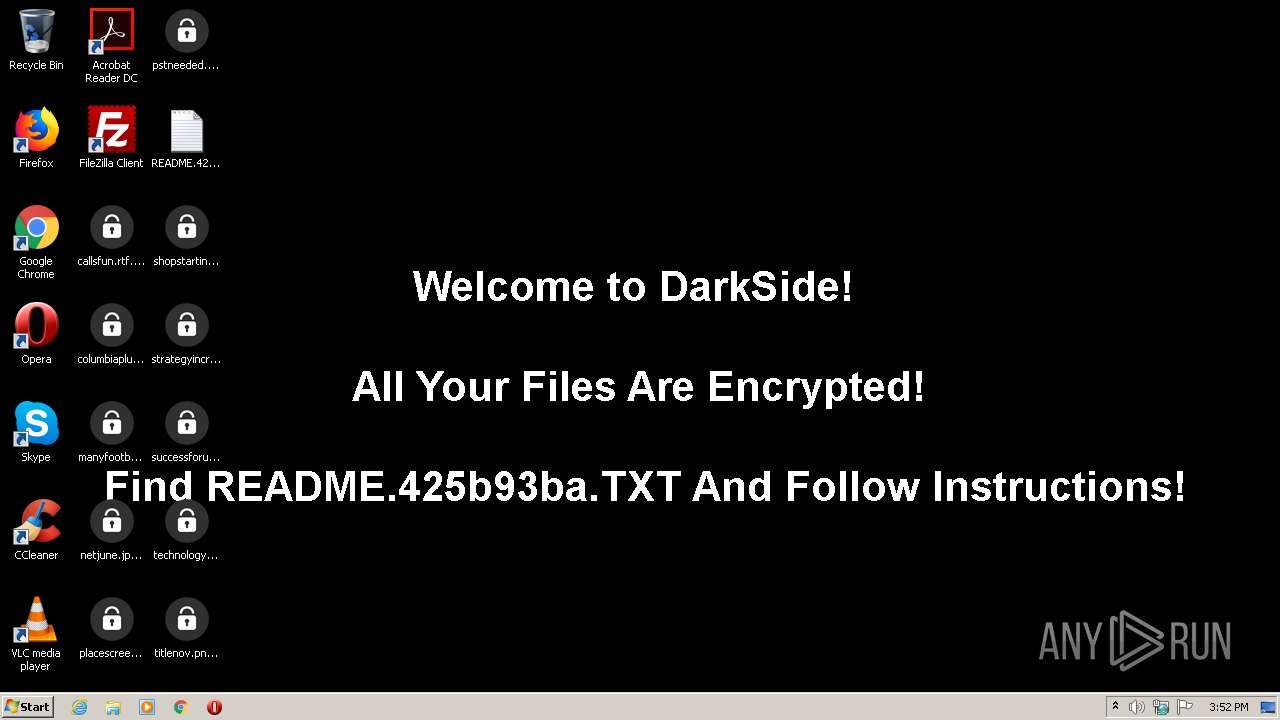
| Threats: | DarkSide ransomware is a novel ransomware strain involved in high-profile incidents. Its attacks lead to data theft and encryption, causing significant damage to victims. |
| Analysis date: | May 12, 2021, 14:52:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 979692CD7FC638BEEA6E9D68C752F360 |
| SHA1: | C511AE4D80AAA281C610190AA13630DE61CA714C |
| SHA256: | 0A0C225F0E5EE941A79F2B7701F1285E4975A2859EB4D025D96D9E366E81ABB9 |
| SSDEEP: | 768:piN4q1eksgR4SiI+rxQ3rjFrXRRWxXyw/Afy8fIaJ/ZB49j9xOOLd9kvAx0:g4HHerjZX7pLjJKjSO5i |
MALICIOUS
Known privilege escalation attack
- DllHost.exe (PID: 2108)
Renames files like Ransomware
- acer.exe (PID: 2856)
SUSPICIOUS
Application launched itself
- acer.exe (PID: 2424)
- acer.exe (PID: 3628)
Executed via COM
- DllHost.exe (PID: 2108)
Executed as Windows Service
- acer.exe (PID: 2424)
Creates files in the program directory
- acer.exe (PID: 3628)
Drops a file with a compile date too recent
- acer.exe (PID: 2856)
Creates files like Ransomware instruction
- acer.exe (PID: 2856)
Changes the desktop background image
- acer.exe (PID: 3628)
INFO
Dropped object may contain TOR URL's
- acer.exe (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0xb2bd |
| UninitializedDataSize: | - |
| InitializedDataSize: | 81920 |
| CodeSize: | 38912 |
| LinkerVersion: | 14.12 |
| PEType: | PE32 |
| TimeStamp: | 2021:04:06 00:09:09+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Apr-2021 22:09:09 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Apr-2021 22:09:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000093AB | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09567 |
.text1 | 0x0000B000 | 0x000002E0 | 0x00000400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.90376 |
.rdata | 0x0000C000 | 0x000001C0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.43189 |
.data | 0x0000D000 | 0x00013A28 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.59261 |
.ndata | 0x00021000 | 0x000011E3 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95371 |
Imports
KERNEL32.dll |
ntdll.dll |
Total processes
44
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1476 | "C:\Users\admin\AppData\Local\Temp\acer.exe" | C:\Users\admin\AppData\Local\Temp\acer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2108 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\AppData\Local\Temp\acer.exe" | C:\Users\admin\AppData\Local\Temp\acer.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2856 | "C:\Users\admin\AppData\Local\Temp\acer.exe" | C:\Users\admin\AppData\Local\Temp\acer.exe | — | DllHost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2856 | C:\Users\admin\AppData\Local\Temp\acer.exe -work worker0 job0-3628 | C:\Users\admin\AppData\Local\Temp\acer.exe | — | acer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3628 | "C:\Users\admin\AppData\Local\Temp\acer.exe" | C:\Users\admin\AppData\Local\Temp\acer.exe | acer.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
Total events
466
Read events
394
Write events
48
Delete events
24
Modification events
| (PID) Process: | (3628) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | DefaultConnectionSettings |
Value: 4600000002000000090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2108) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2108) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3628) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3628) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3628) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3628) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3628) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000002000000090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3628) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | DefaultConnectionSettings |
Value: 460000000300000009000000000000000000000000000000040000000000000000000000000000000000000000000000000000000100000002000000C0A8642F000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3628) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
101
Text files
46
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | acer.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.425b93ba | — | |
MD5:— | SHA256:— | |||
| 2856 | acer.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi.425b93ba | binary | |
MD5:17AE1E48A5CA3A6F89FE4EE871835BDB | SHA256:FE276868B98C74DABD55007CB260303A8107DD7E854316C587E1649074F6E5DE | |||
| 2856 | acer.exe | C:\Users\admin\Desktop\netjune.jpg.425b93ba | binary | |
MD5:B31258DDDCDCB0D4D8557142BE9FE512 | SHA256:0EEBD36E5C5651971A6CF7B32F3376E044C5905E375426EF6B97D71DE73223D8 | |||
| 2856 | acer.exe | C:\Users\admin\Desktop\placescreen.png.425b93ba | binary | |
MD5:CA3587EA468F928DE3D0A40439FEA5E2 | SHA256:74A93E86FD725E00632F98D07487CD2D4DCFDACFCBDFBAF4B87BB93CAA533124 | |||
| 2856 | acer.exe | C:\Users\admin\Contacts\admin.contact.425b93ba | ini | |
MD5:8C5D7561090D5C4BFD1E3D0ED9564A16 | SHA256:CA62525B6AA3B8E0E0002253D1CDFD899AD2608B63A5BD14769470B9CC17CF48 | |||
| 2856 | acer.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.425b93ba | binary | |
MD5:136D4457463999678C443CD1D9491F40 | SHA256:8A2ABE2AC5791E1F42E052CBECC5BF0EDF09215790149DF0744A0F975B09CC5B | |||
| 2856 | acer.exe | C:\Users\admin\Desktop\manyfootball.jpg.425b93ba | binary | |
MD5:03C269E04FAA6EFE324C641B80015B6B | SHA256:48C6F3AA4C712BA53A91A645B78CDCEE4C8AFE549B2DF504323AB4BCD2588B11 | |||
| 2856 | acer.exe | C:\Users\admin\Desktop\pstneeded.png.425b93ba | binary | |
MD5:528CCF4543011B467FD596612AAB59B7 | SHA256:CB5F6D2D4379D69EA8F8932CABEE5A1511677A9C522F47BE500ABE6A411FEB2A | |||
| 2856 | acer.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\README.425b93ba.TXT | text | |
MD5:164AA420BE8E0C2BCDEF574355EDAA32 | SHA256:B326D11DD90C2E4EFB0A384981F71C2BD1A6FAA0553D6389ACB08945B699F73D | |||
| 3628 | acer.exe | C:\ProgramData\425b93ba.ico | image | |
MD5:4F57D54D01CCBDAF3EBFAC3EC0AC3FD7 | SHA256:28B6841AA125225CD01BE09FBD2F1D7B3C2102D9FFC7DC8546700E67C2A6E3BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
3
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3628 | acer.exe | 176.103.62.217:443 | baroquetees.com | ITL Company | UA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
baroquetees.com |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3628 | acer.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3628 | acer.exe | A Network Trojan was detected | ET TROJAN Observed DarkSide Ransomware Domain (baroquetees .com in TLS SNI) |
3628 | acer.exe | A Network Trojan was detected | ET TROJAN Observed DarkSide Ransomware Domain (baroquetees .com in TLS SNI) |
3628 | acer.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3628 | acer.exe | A Network Trojan was detected | ET TROJAN Observed DarkSide Ransomware Domain (baroquetees .com in TLS SNI) |