| File name: | acer.exe |
| Full analysis: | https://app.any.run/tasks/ca9a2a47-090f-4c80-ad92-372c24cf7639 |
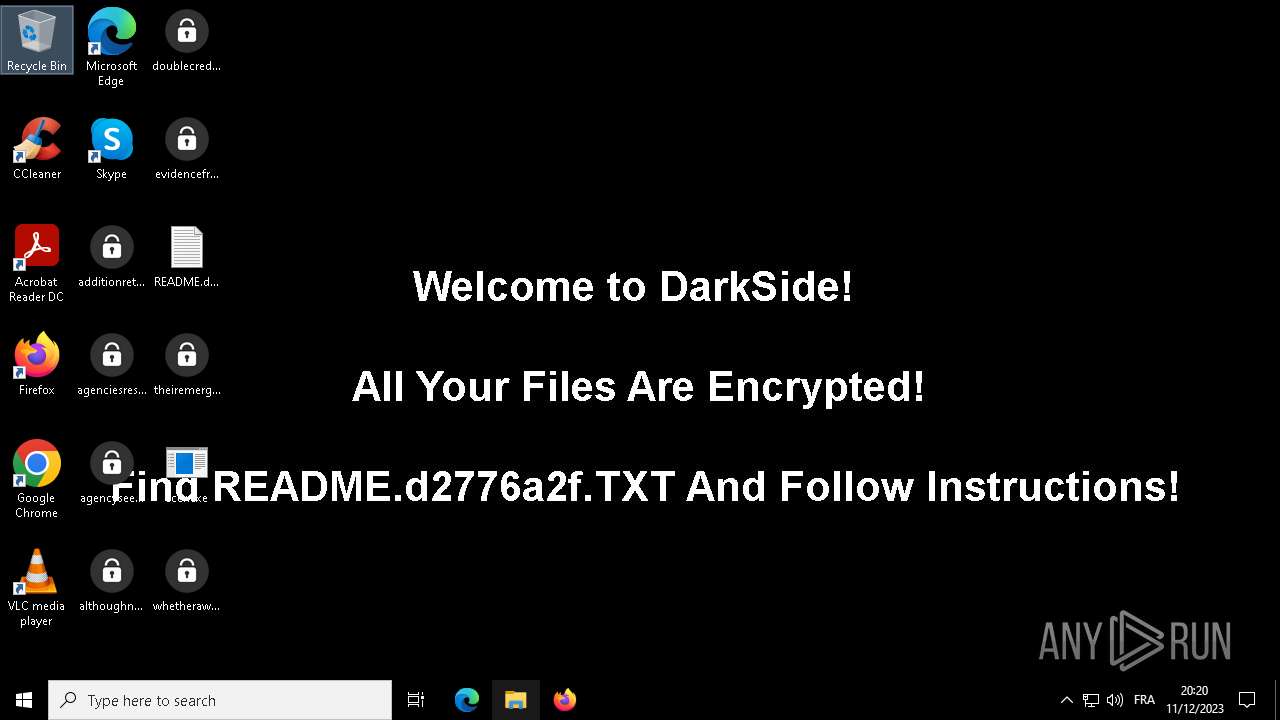
| Verdict: | Malicious activity |
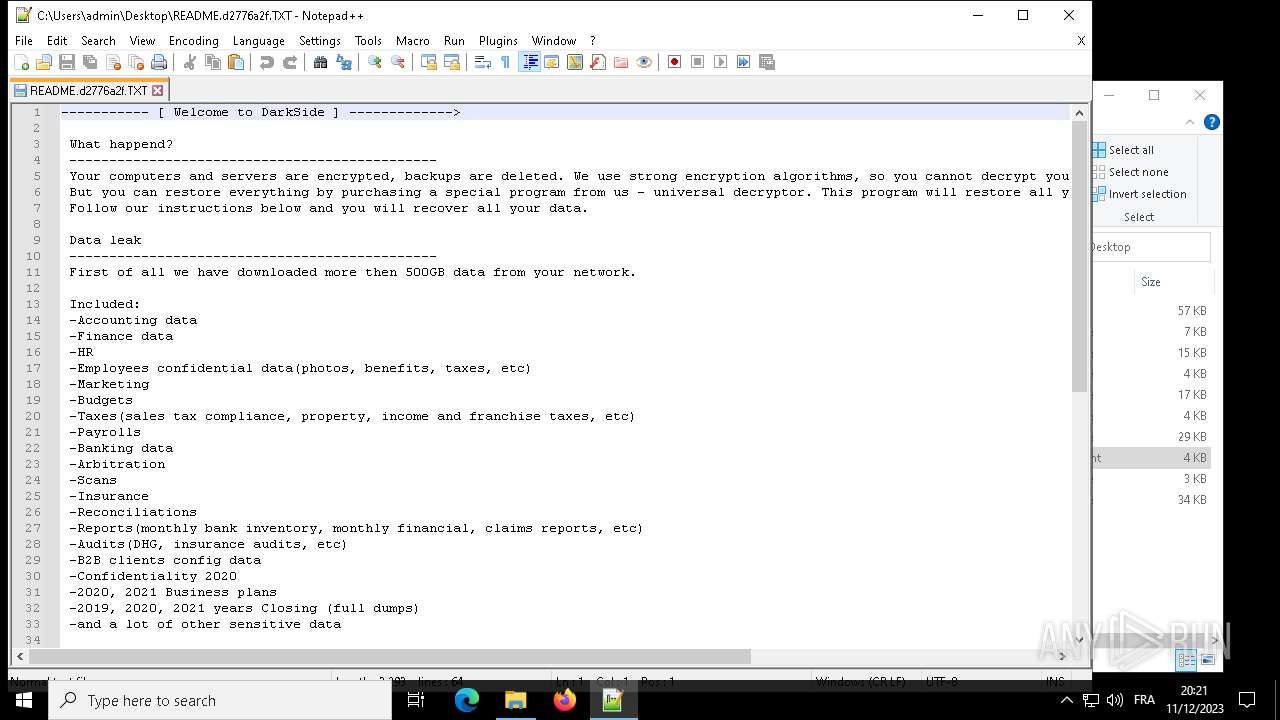
| Threats: | DarkSide ransomware is a novel ransomware strain involved in high-profile incidents. Its attacks lead to data theft and encryption, causing significant damage to victims. |
| Analysis date: | December 11, 2023, 19:20:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 979692CD7FC638BEEA6E9D68C752F360 |
| SHA1: | C511AE4D80AAA281C610190AA13630DE61CA714C |
| SHA256: | 0A0C225F0E5EE941A79F2B7701F1285E4975A2859EB4D025D96D9E366E81ABB9 |
| SSDEEP: | 768:piN4q1eksgR4SiI+rxQ3rjFrXRRWxXyw/Afy8fIaJ/ZB49j9xOOLd9kvAx0m:g4HHerjZX7pLjJKjSO5im |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 7036)
Renames files like ransomware
- acer.exe (PID: 3780)
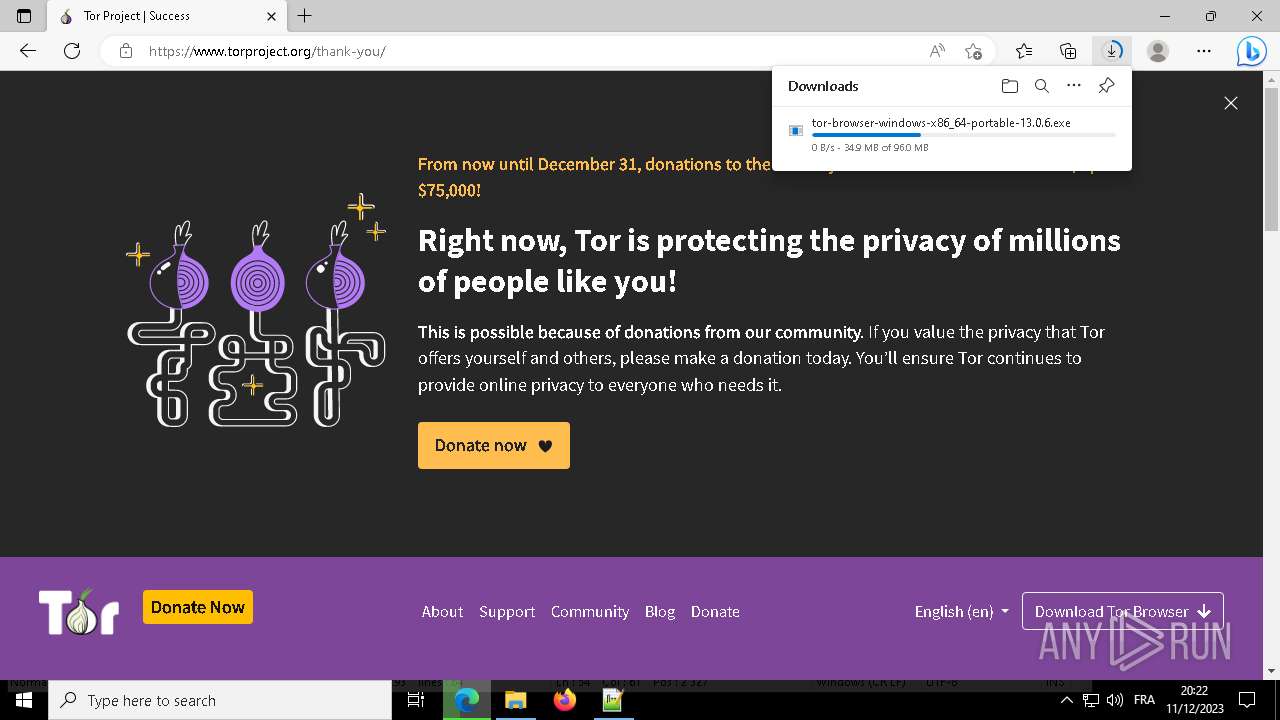
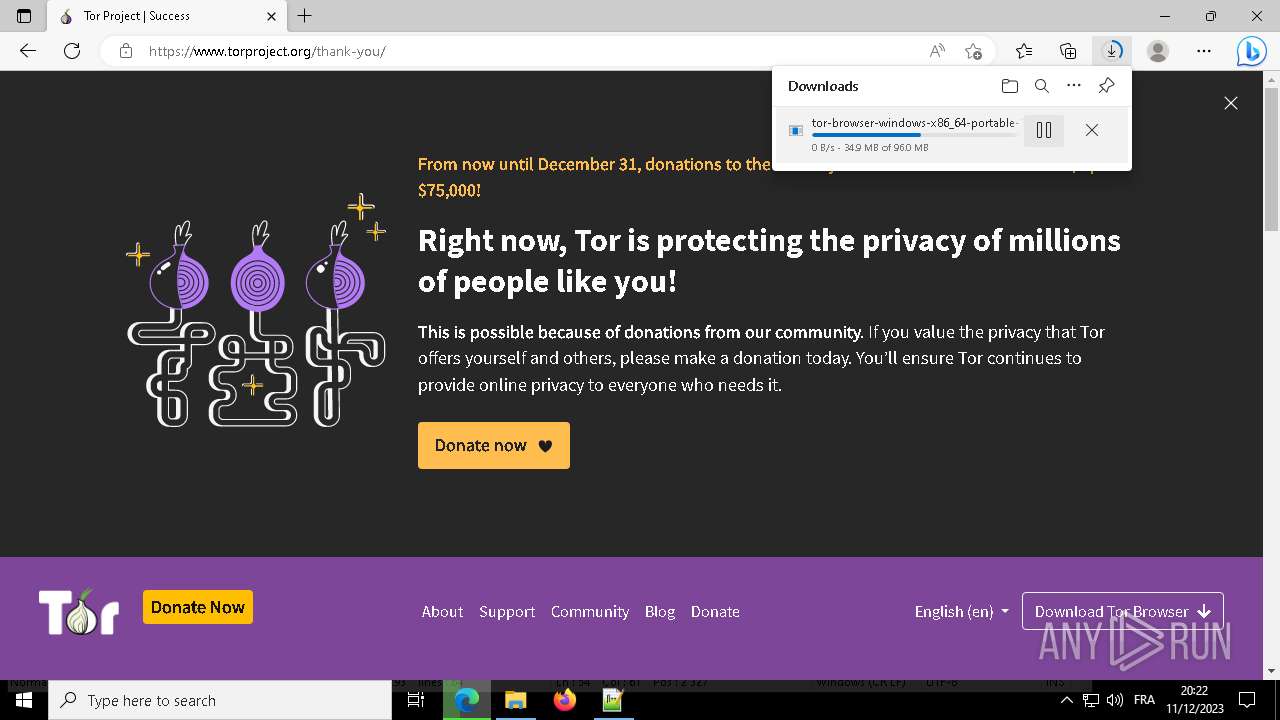
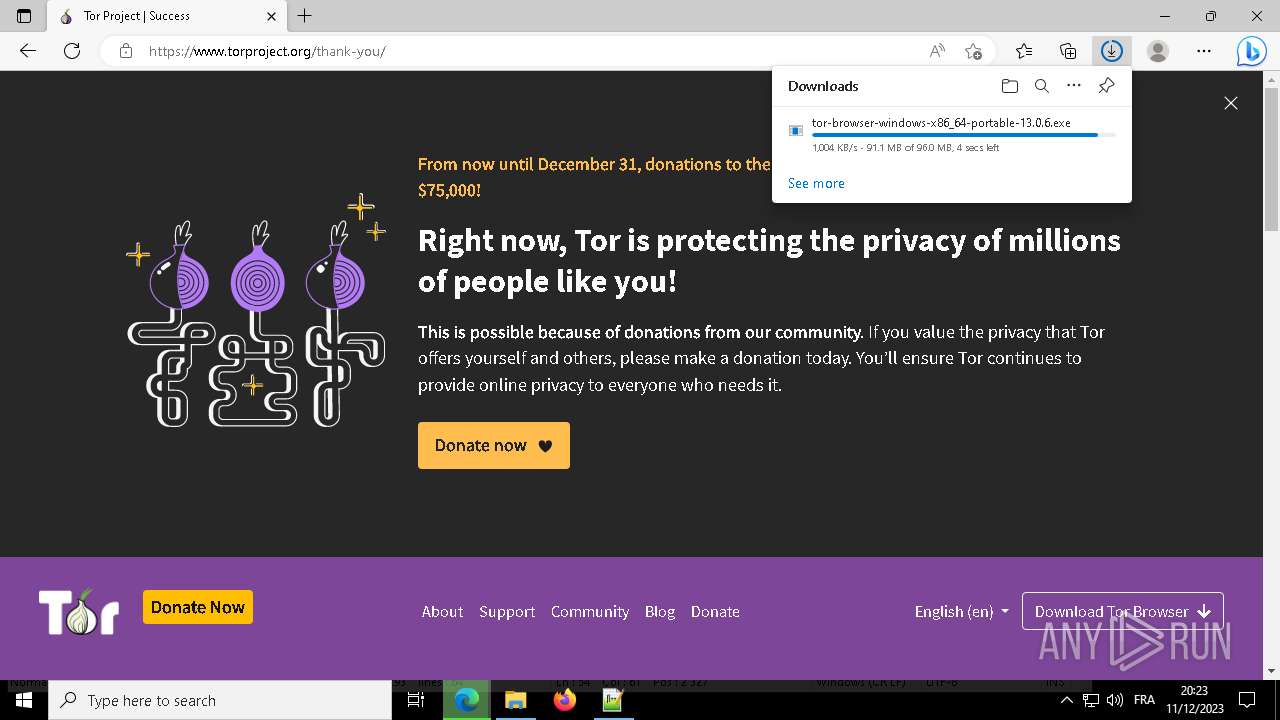
Drops the executable file immediately after the start
- acer.exe (PID: 3780)
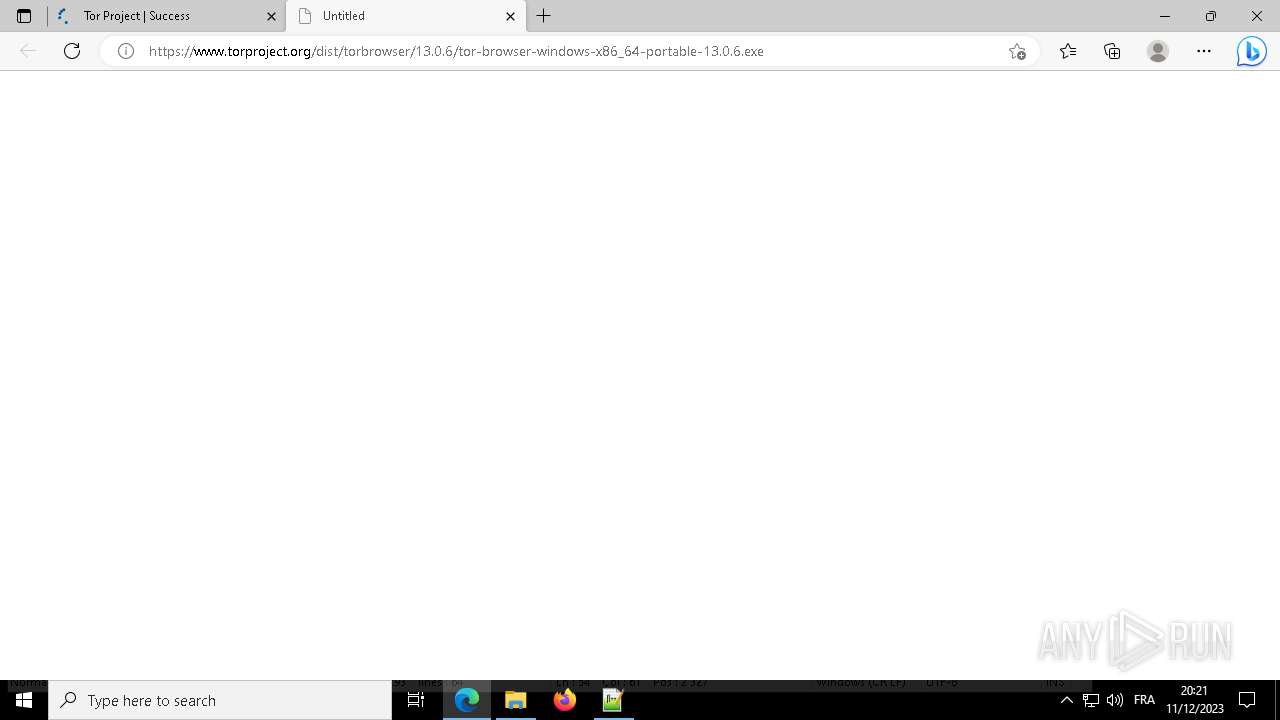
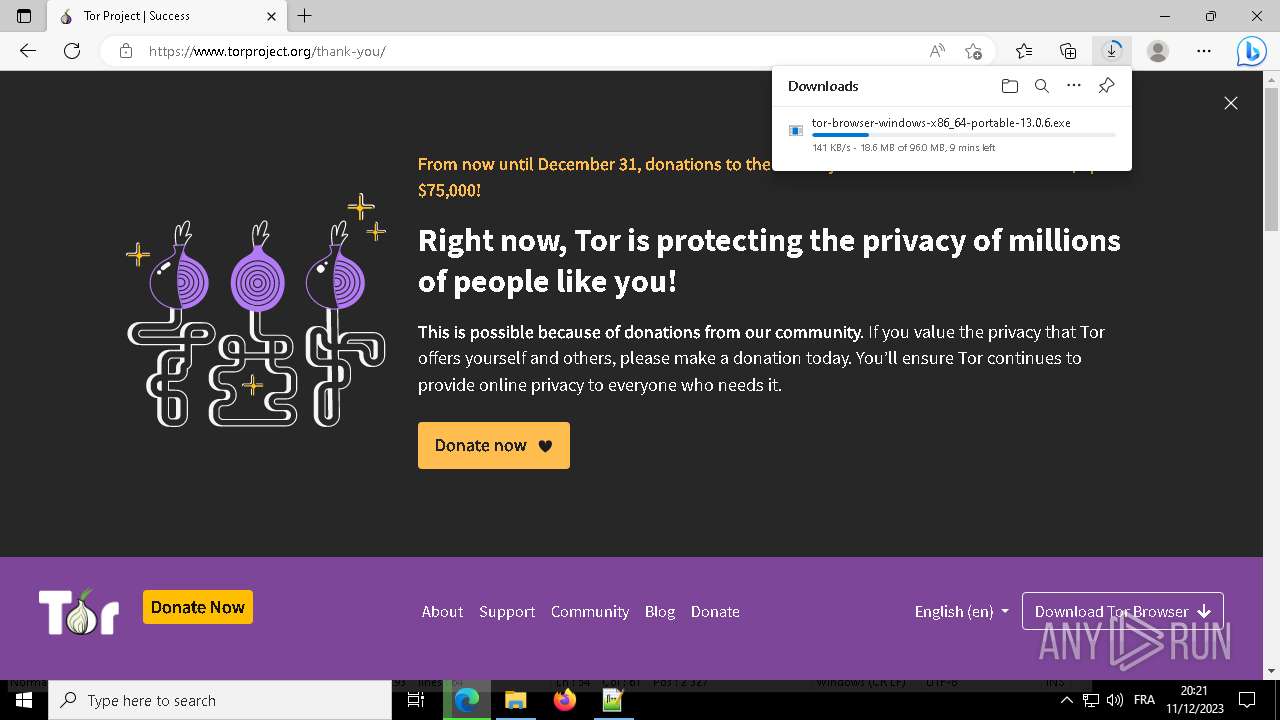
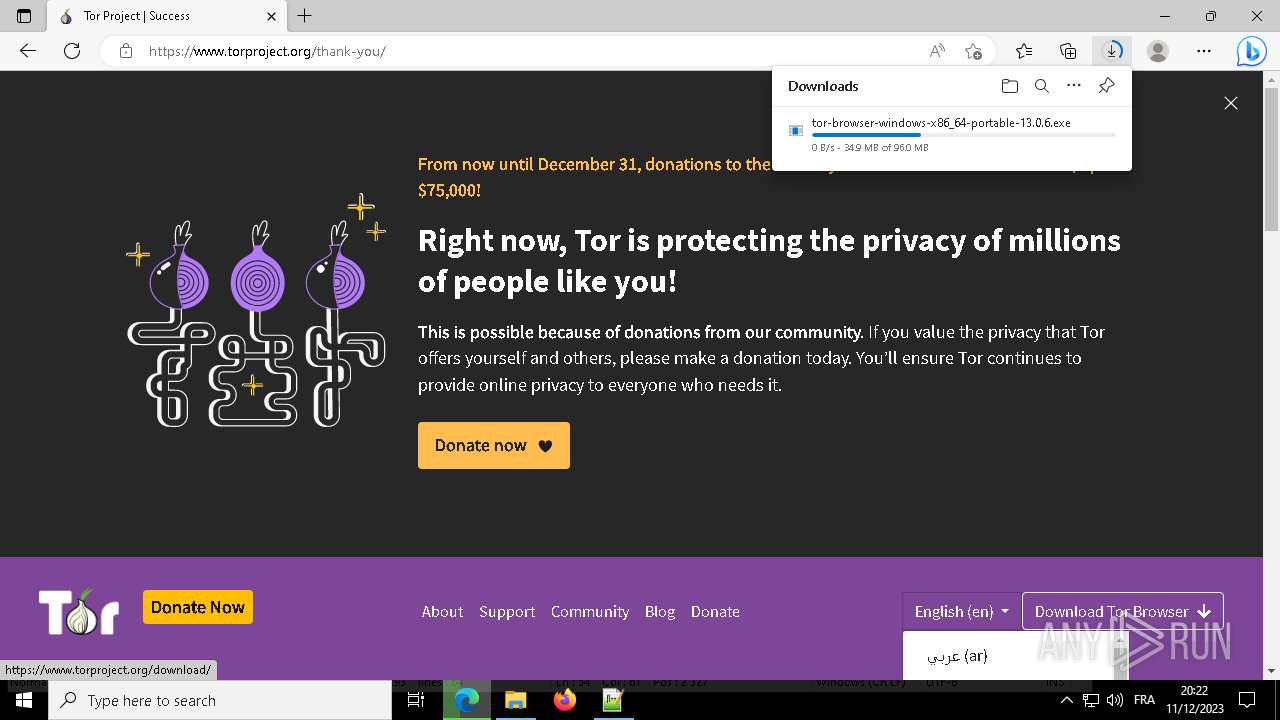
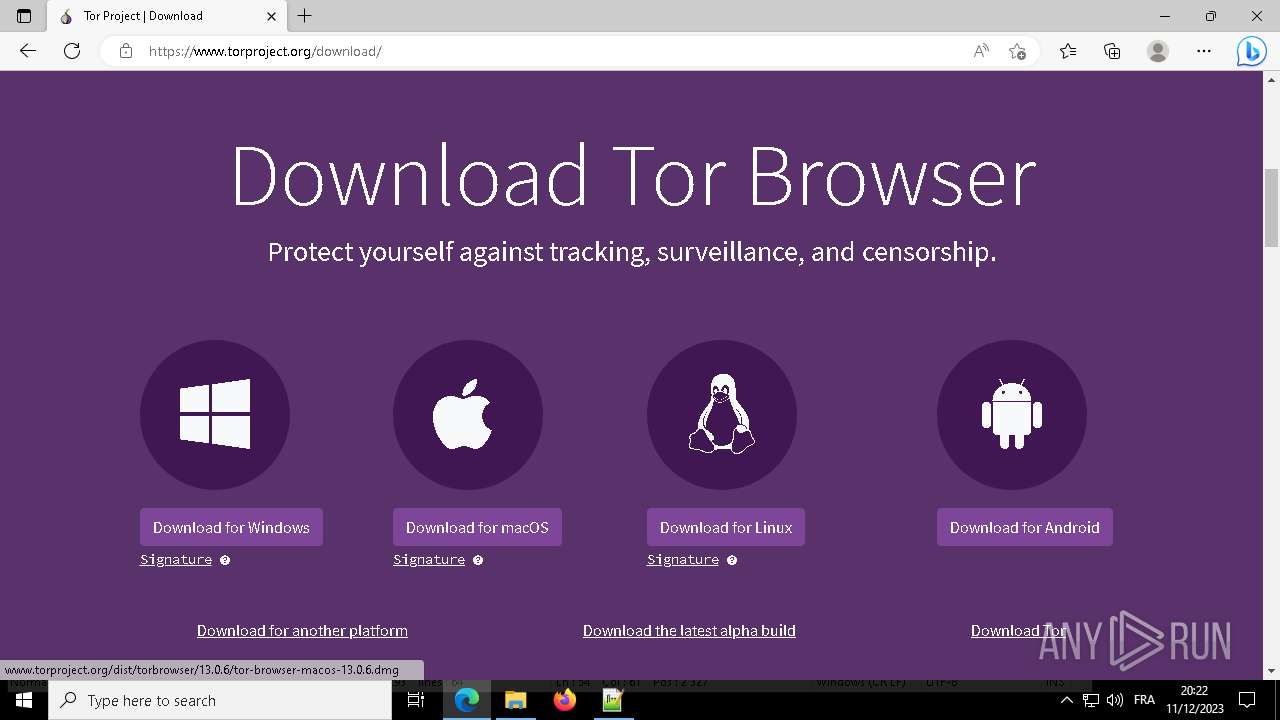
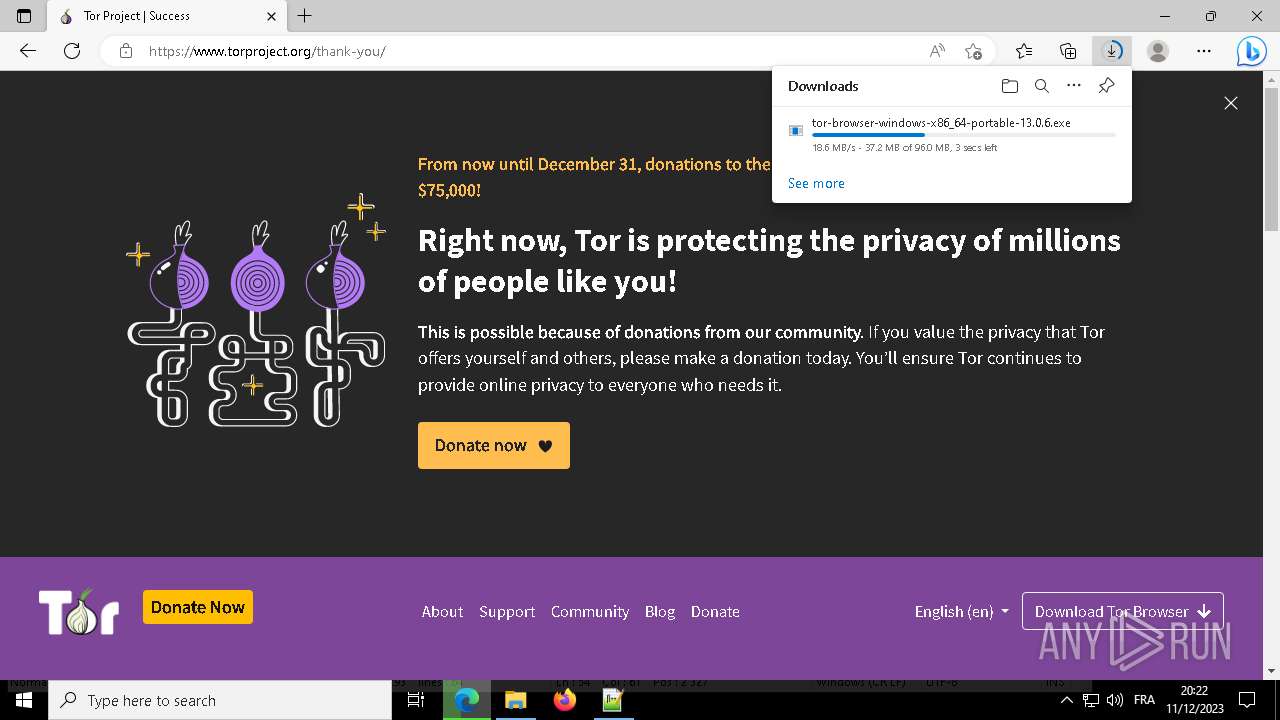
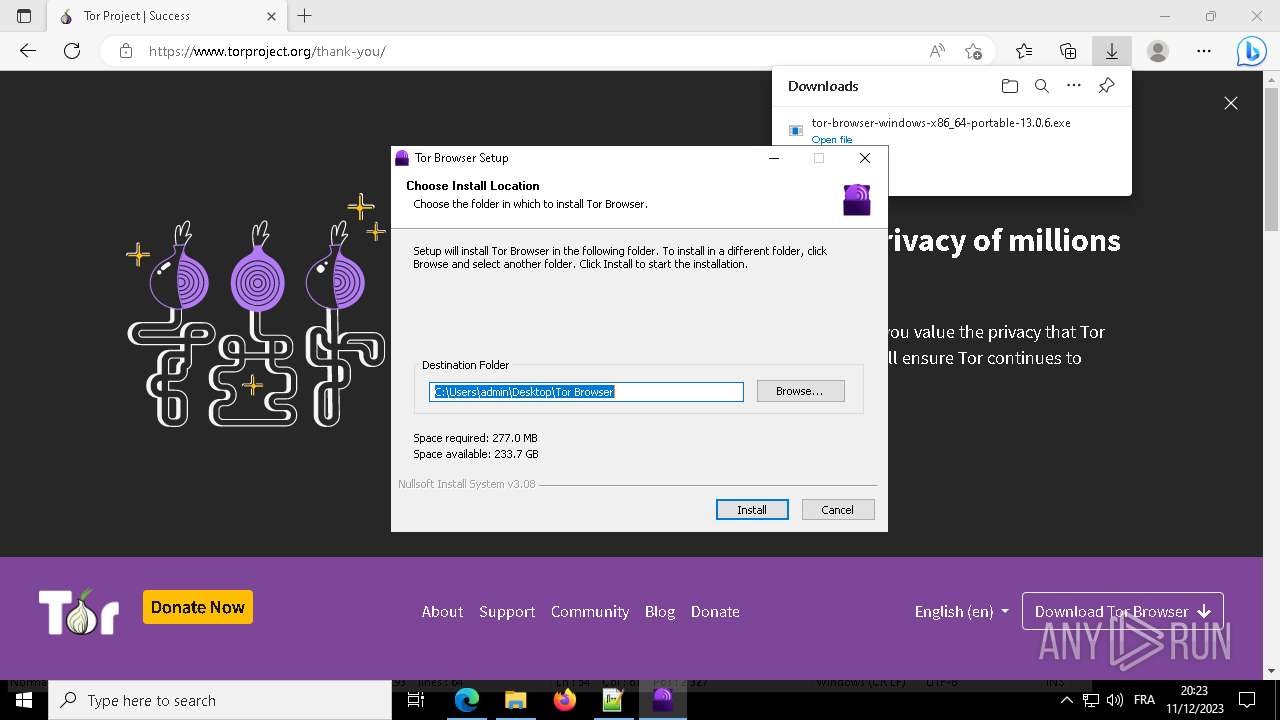
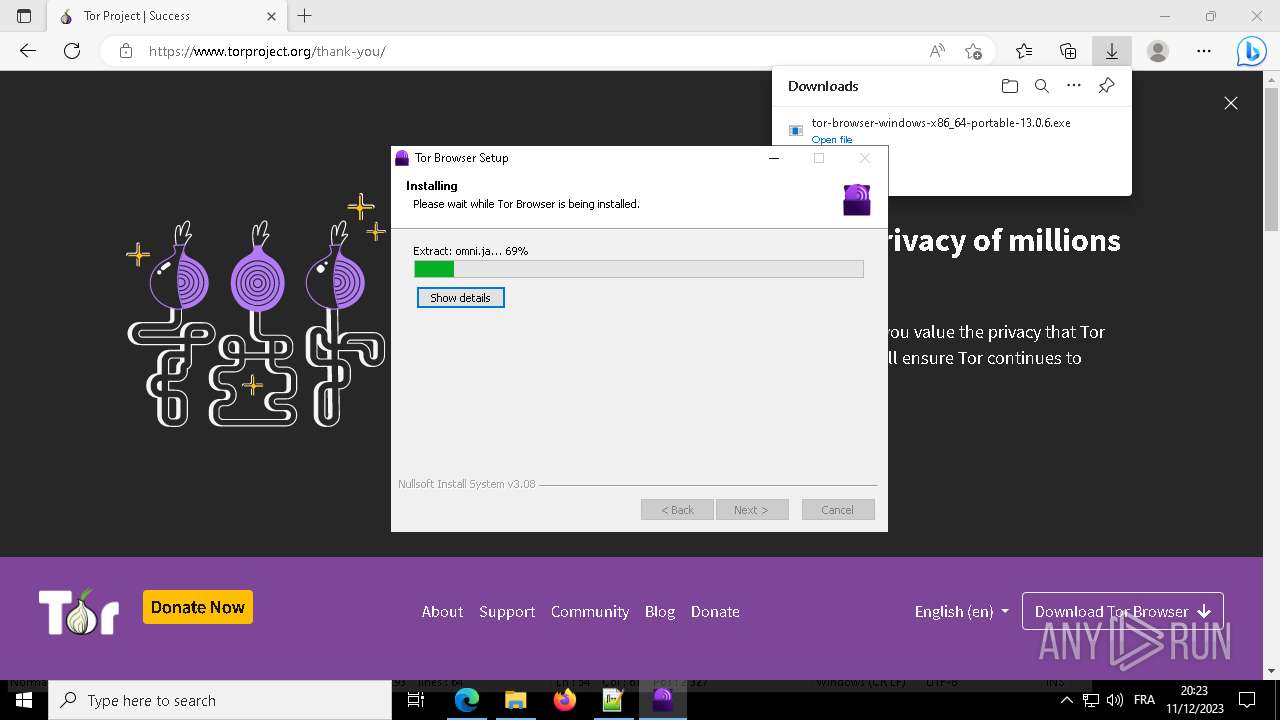
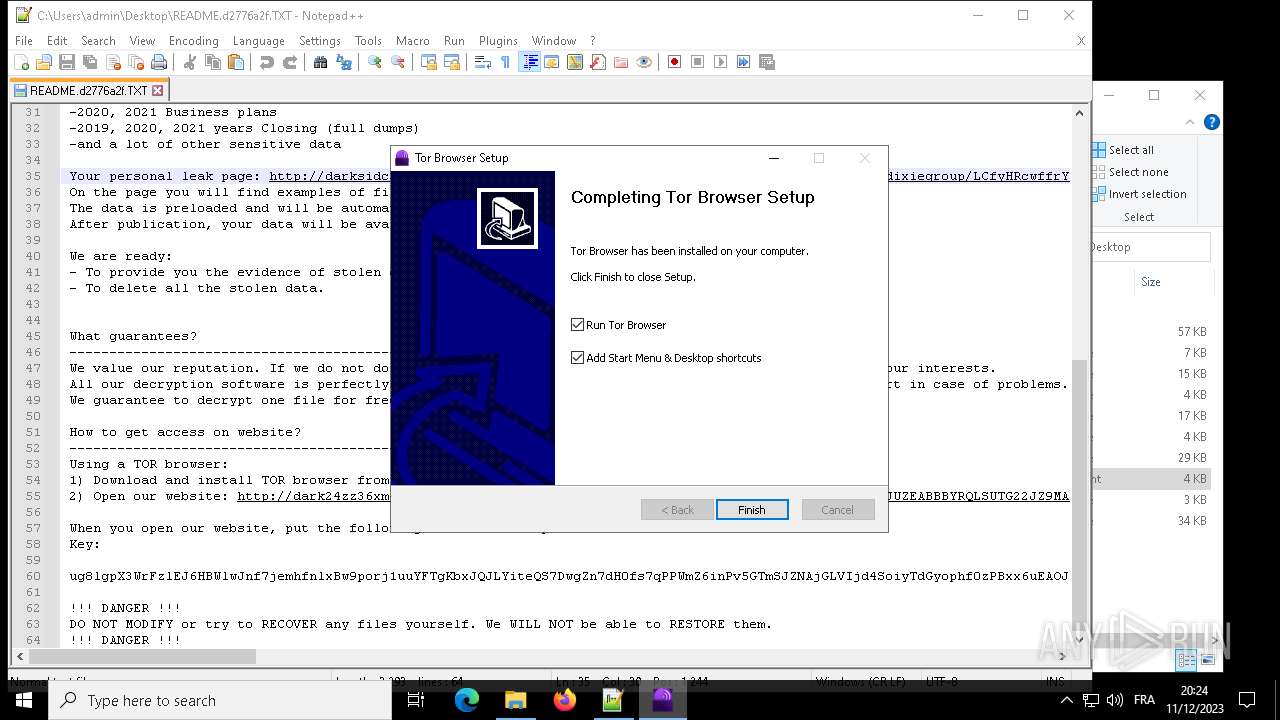
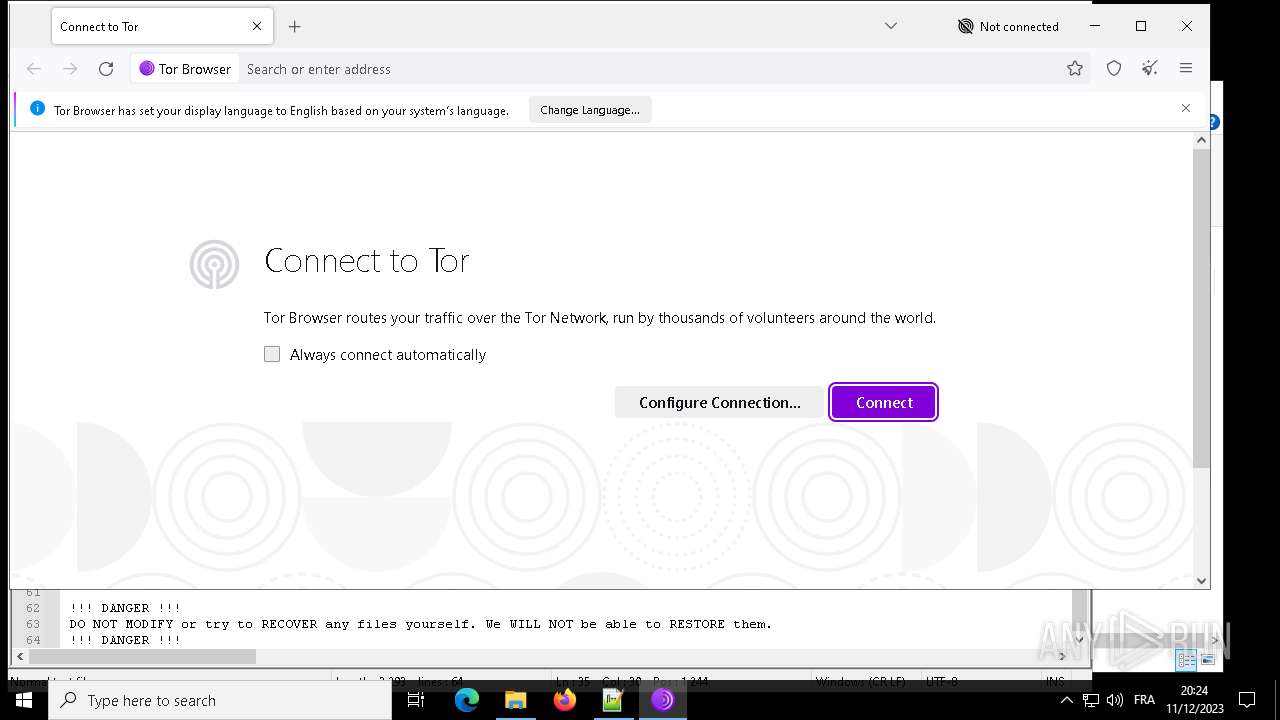
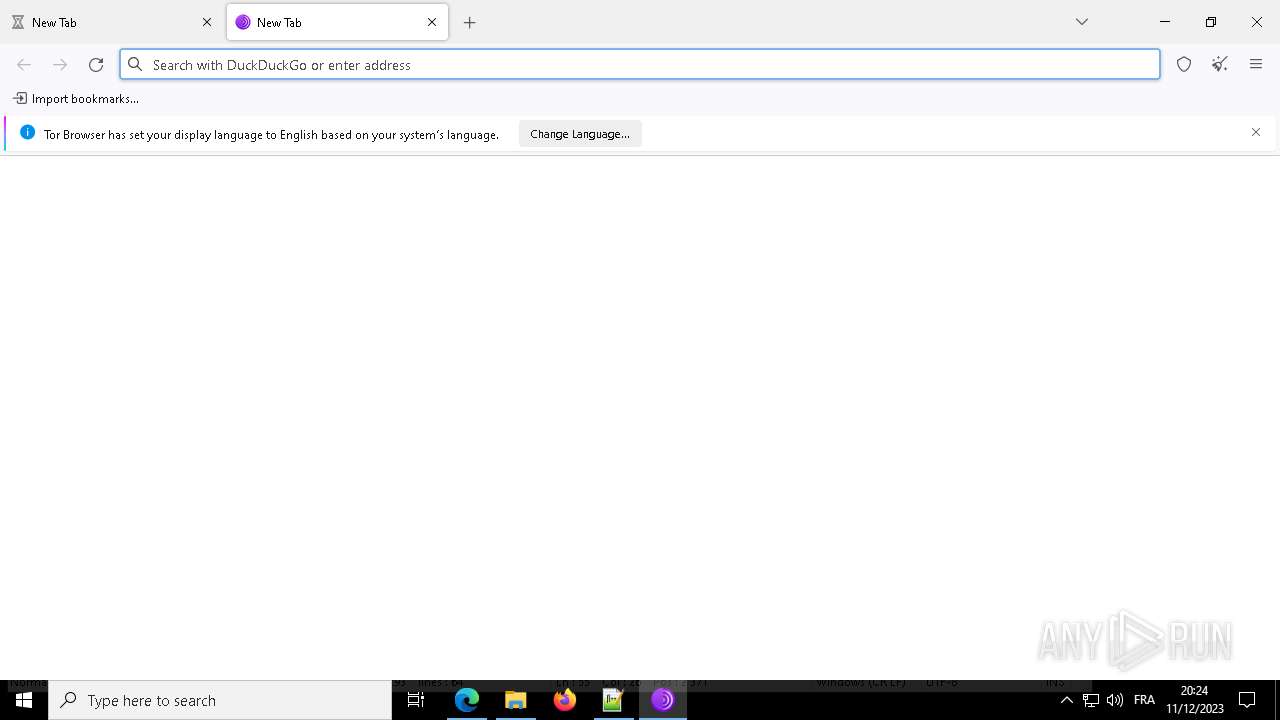
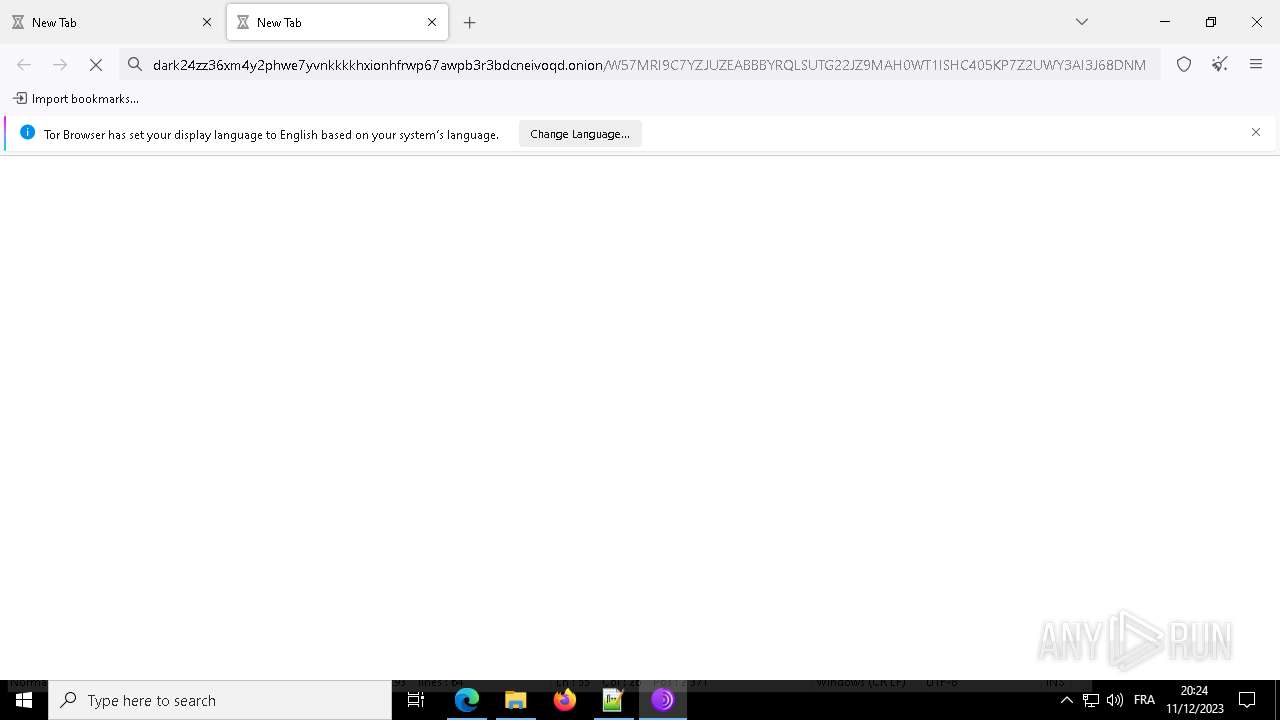
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
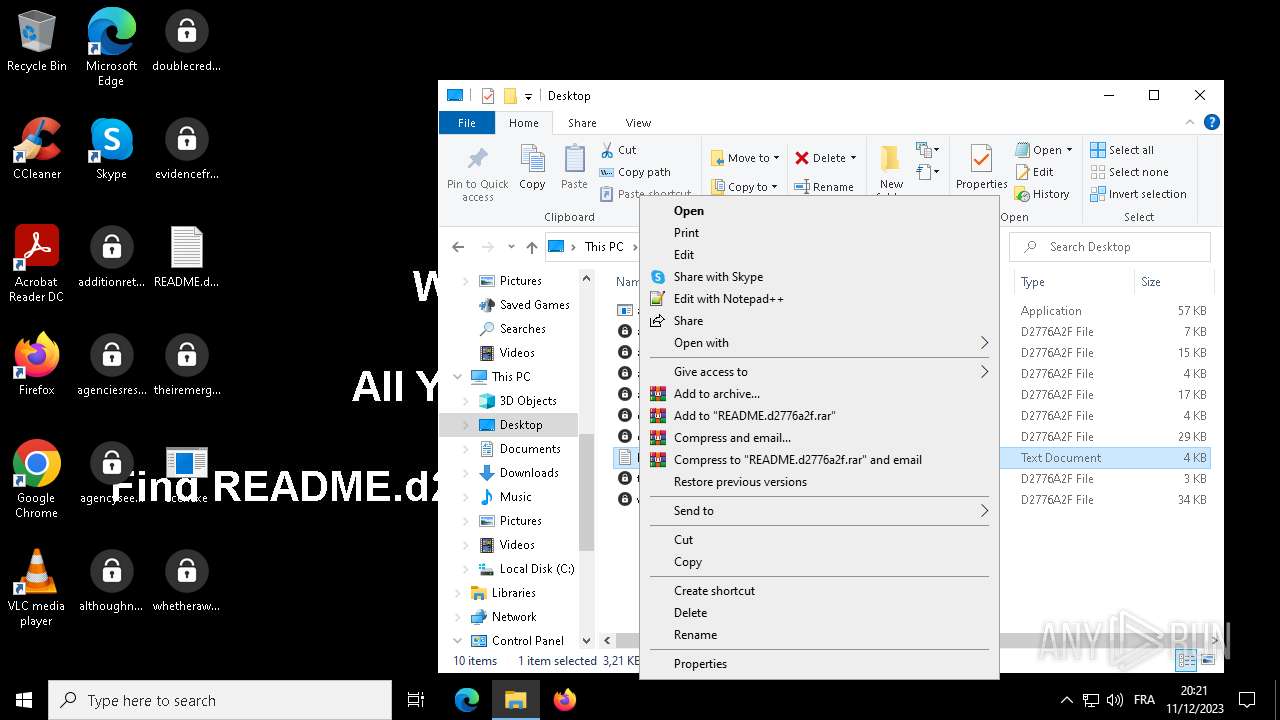
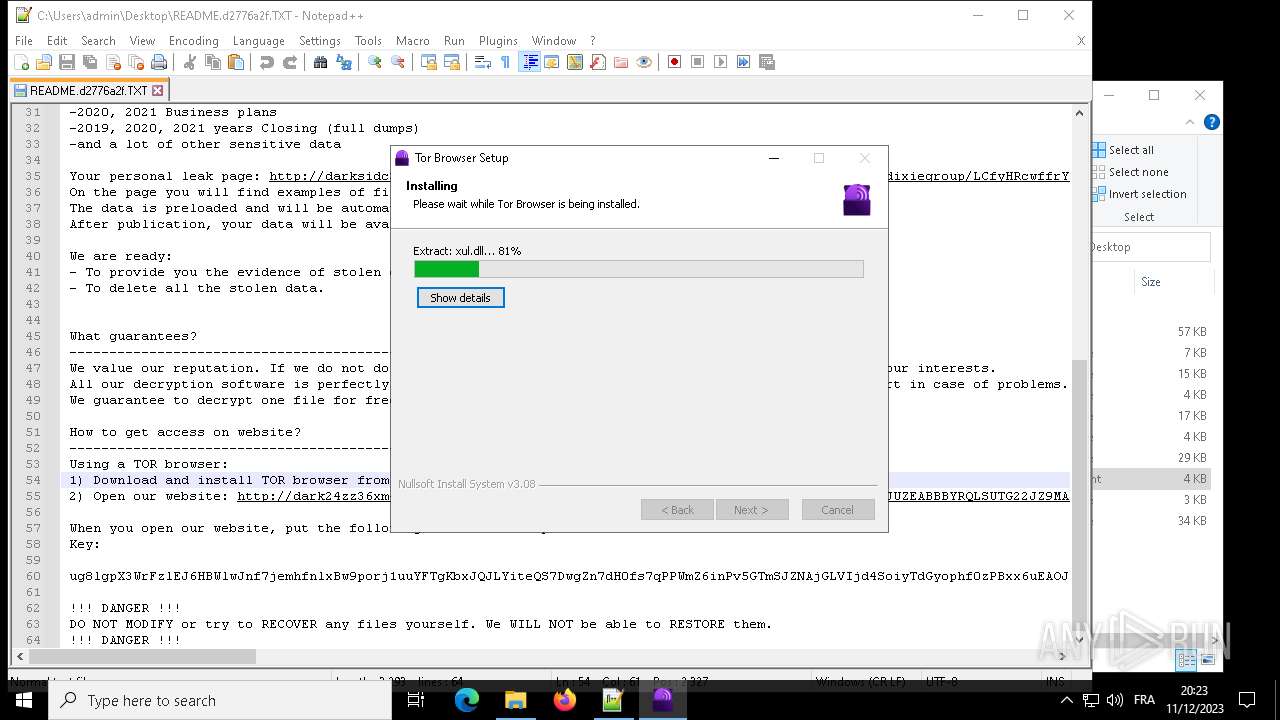
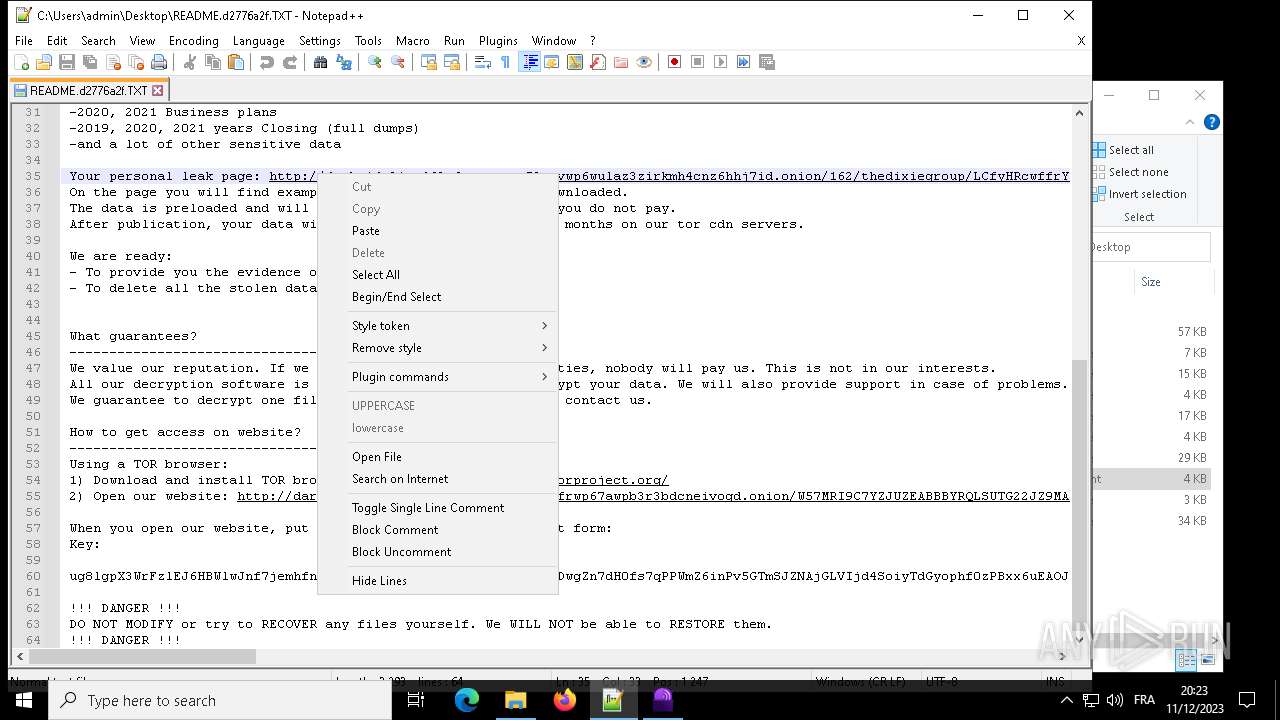
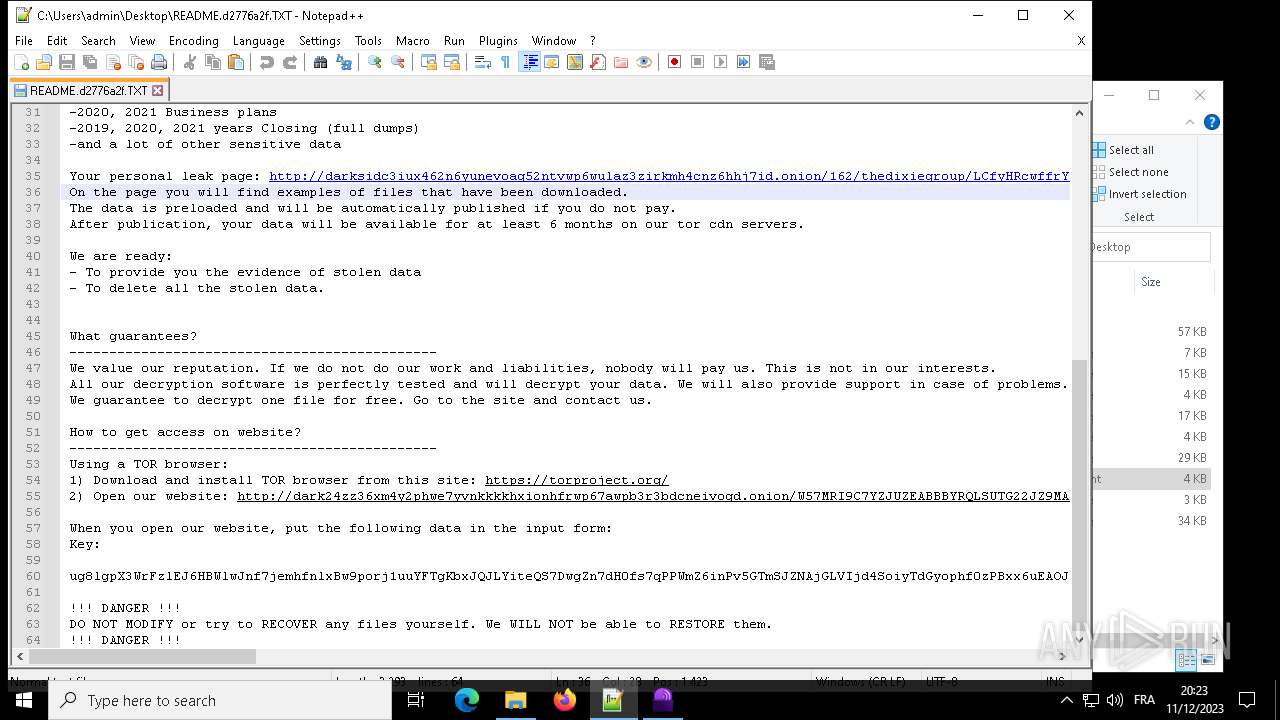
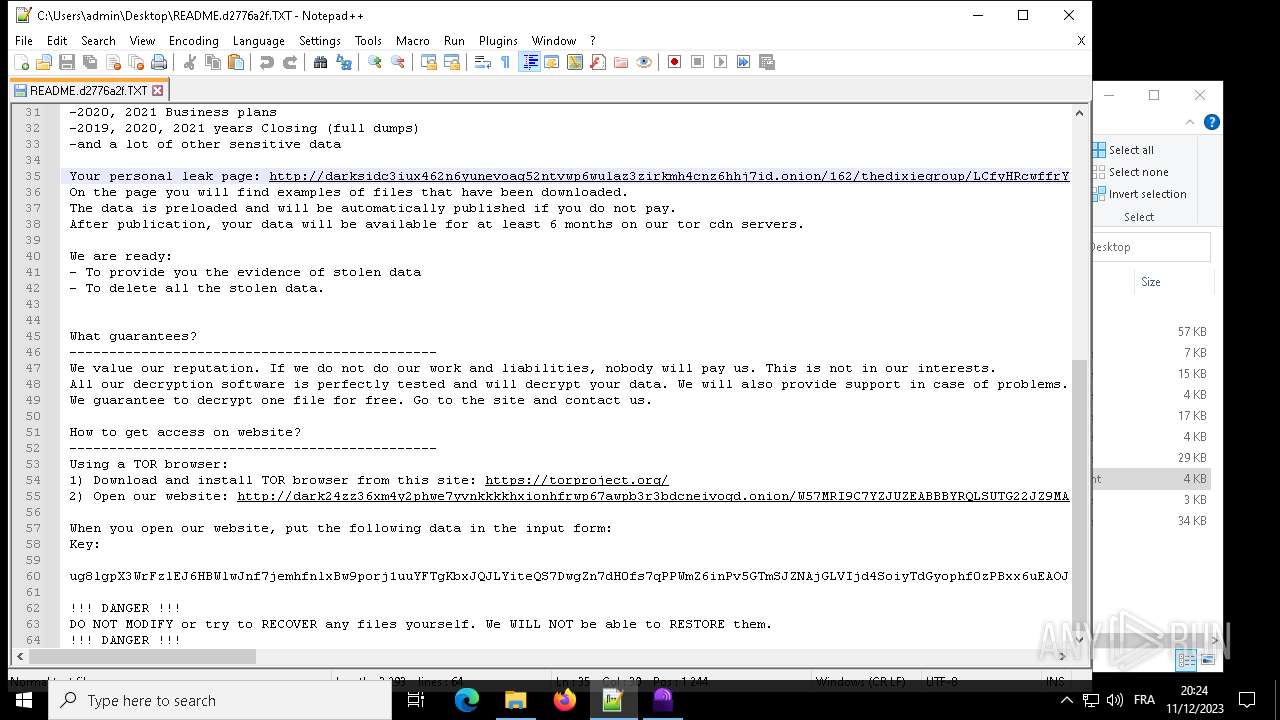
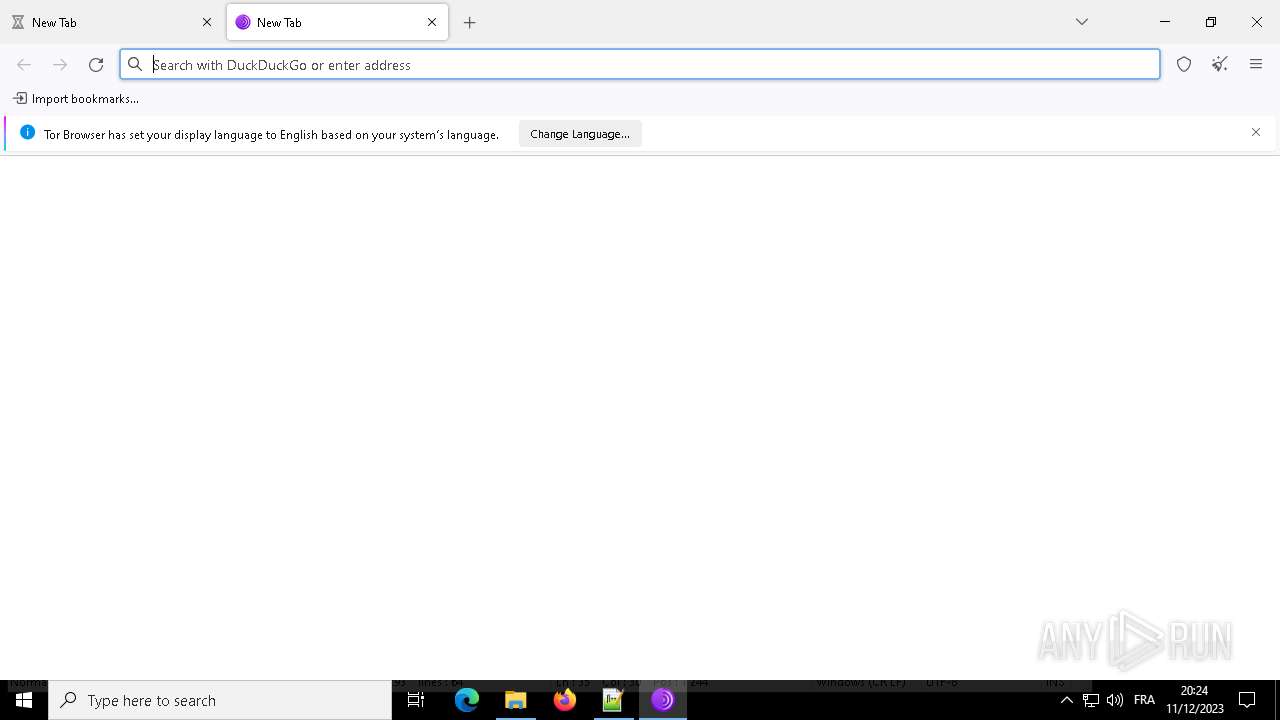
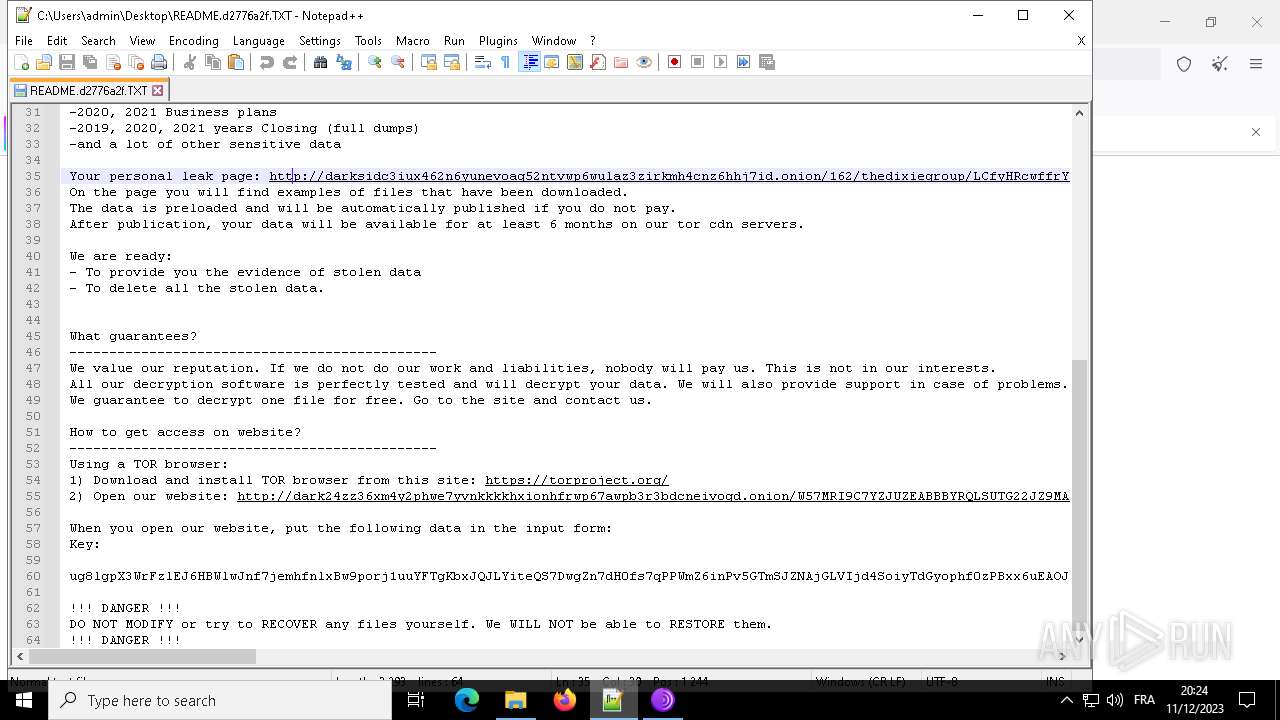
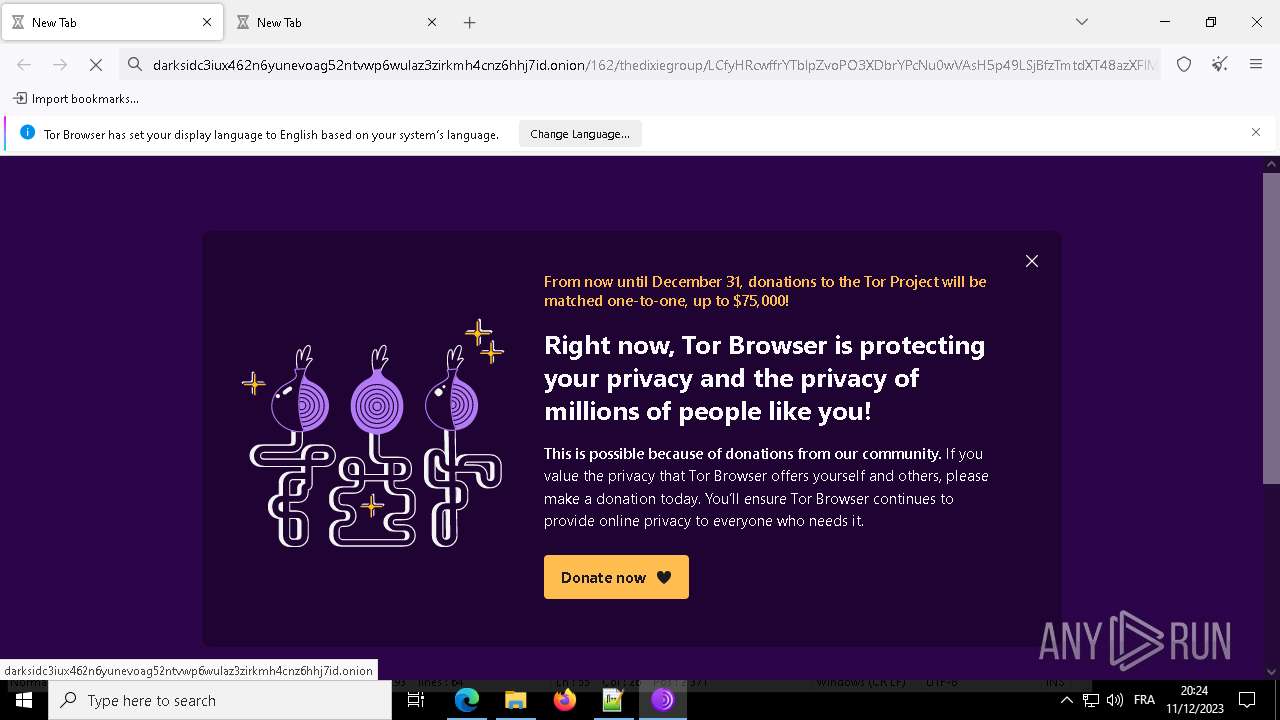
Darkside ransom note is found
- acer.exe (PID: 3780)
Creates a writable file in the system directory
- acer.exe (PID: 2544)
DARKSIDE has been detected (SURICATA)
- acer.exe (PID: 2544)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7012)
- acer.exe (PID: 6292)
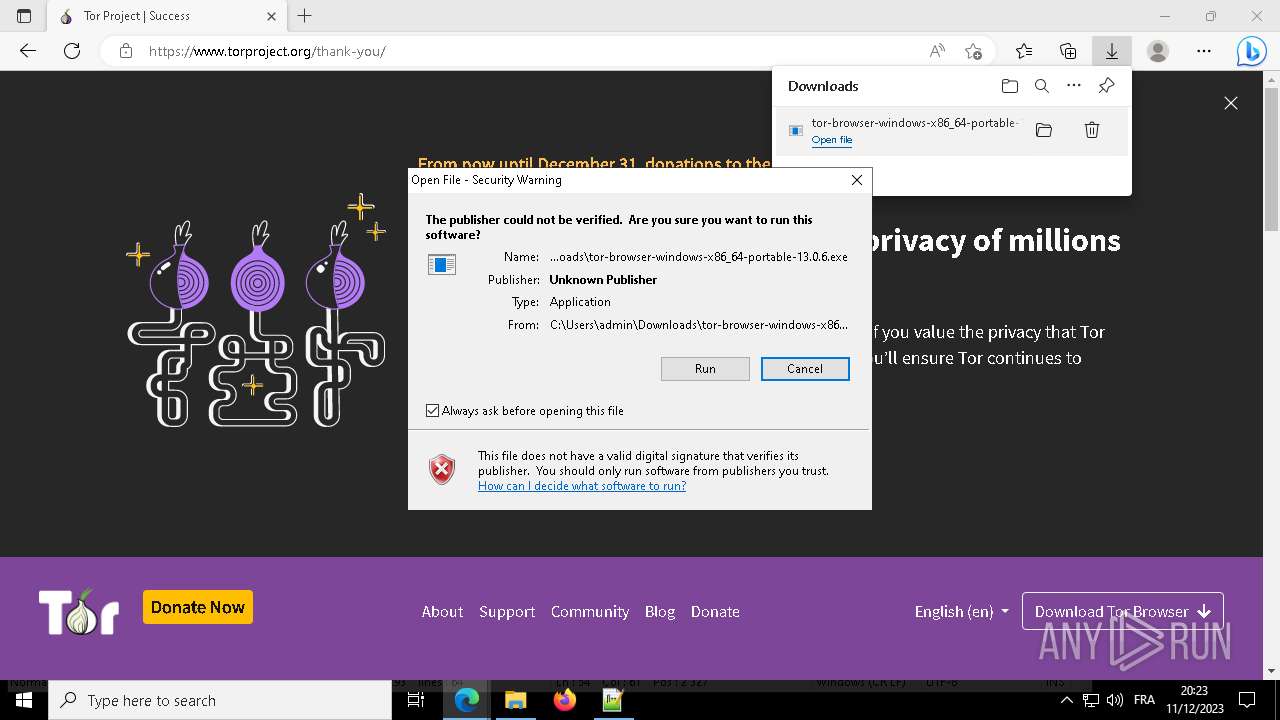
Checks Windows Trust Settings
- acer.exe (PID: 2544)
Application launched itself
- acer.exe (PID: 2544)
- firefox.exe (PID: 6364)
- firefox.exe (PID: 7100)
- acer.exe (PID: 6292)
Creates files like ransomware instruction
- acer.exe (PID: 3780)
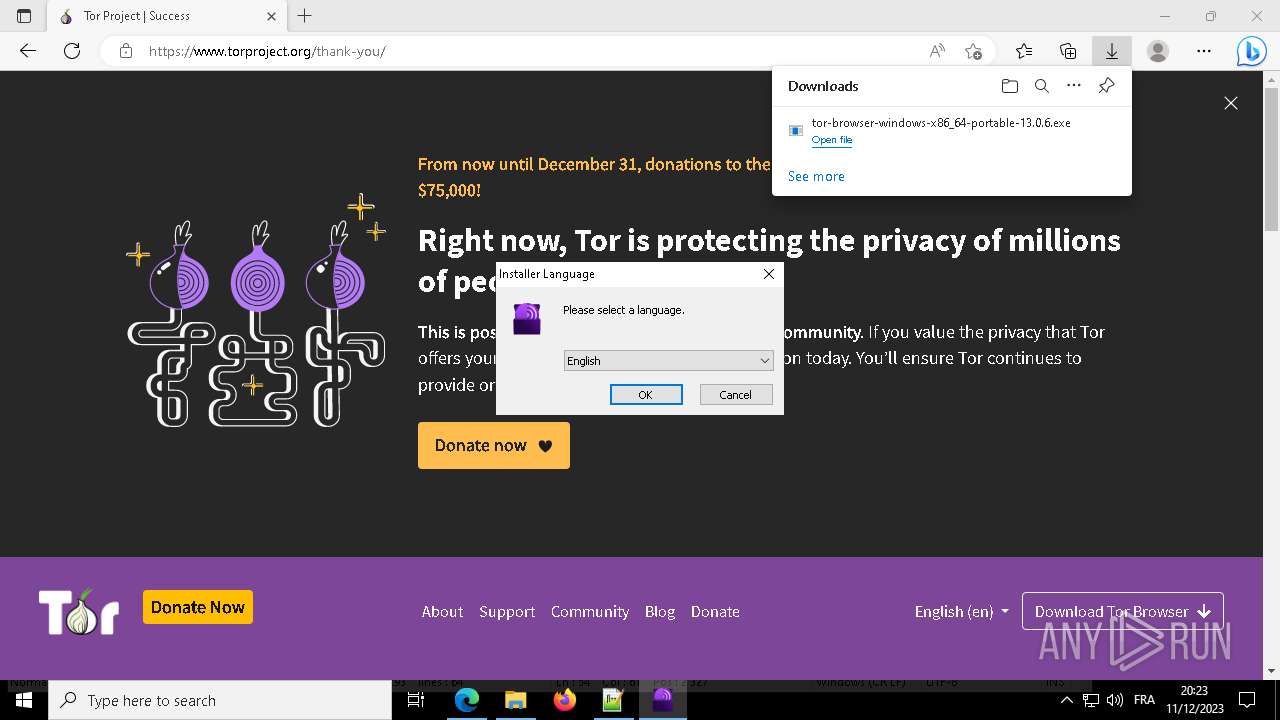
The process creates files with name similar to system file names
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
Malware-specific behavior (creating "System.dll" in Temp)
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
Process drops legitimate windows executable
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
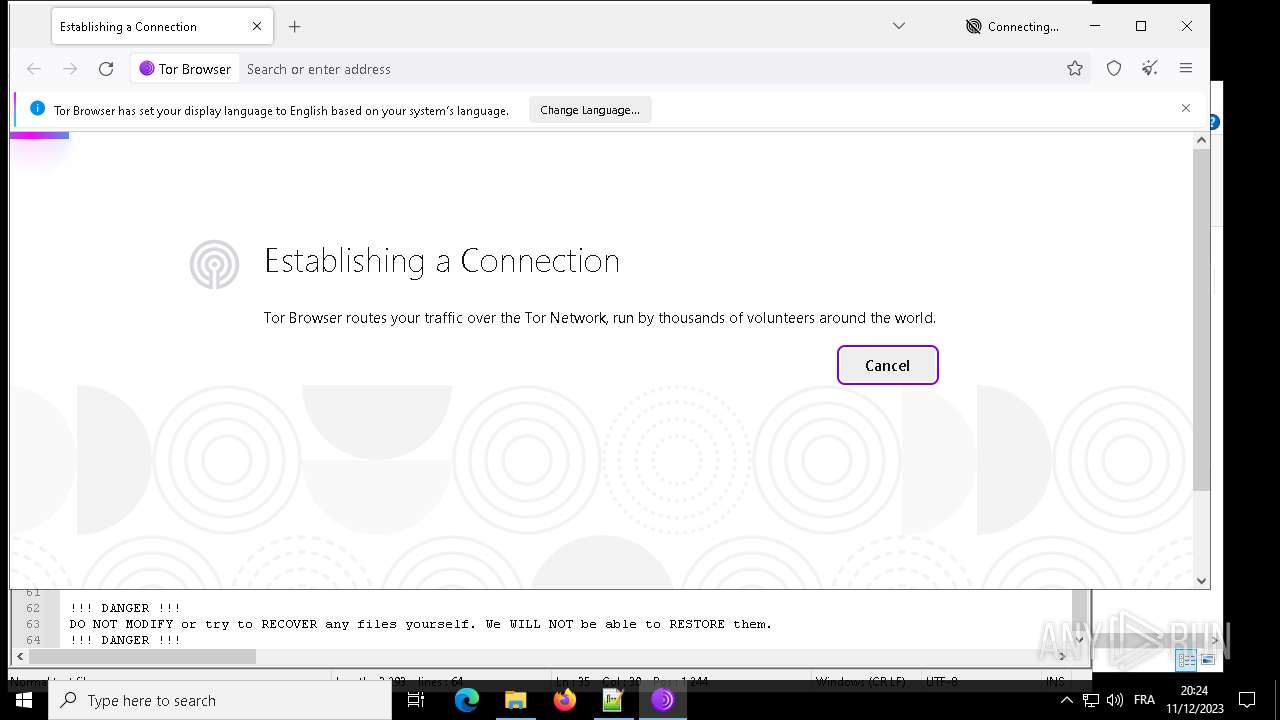
Connects to unusual port
- tor.exe (PID: 3968)
INFO
Reads the machine GUID from the registry
- acer.exe (PID: 6720)
- acer.exe (PID: 2544)
- acer.exe (PID: 5856)
- acer.exe (PID: 3780)
- tor.exe (PID: 3968)
- firefox.exe (PID: 7100)
- acer.exe (PID: 6292)
Checks supported languages
- acer.exe (PID: 6720)
- acer.exe (PID: 5856)
- acer.exe (PID: 6292)
- acer.exe (PID: 3780)
- identity_helper.exe (PID: 5892)
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
- identity_helper.exe (PID: 2252)
- identity_helper.exe (PID: 1500)
- firefox.exe (PID: 6364)
- firefox.exe (PID: 7100)
- firefox.exe (PID: 2468)
- firefox.exe (PID: 6788)
- tor.exe (PID: 3968)
- firefox.exe (PID: 6320)
- firefox.exe (PID: 7916)
- firefox.exe (PID: 7816)
- firefox.exe (PID: 6556)
- firefox.exe (PID: 8012)
- firefox.exe (PID: 7280)
- firefox.exe (PID: 2944)
- firefox.exe (PID: 2480)
- acer.exe (PID: 2544)
- firefox.exe (PID: 7260)
Reads Environment values
- acer.exe (PID: 2544)
Reads Windows Product ID
- acer.exe (PID: 2544)
Creates files in the program directory
- acer.exe (PID: 2544)
- firefox.exe (PID: 7100)
Reads the computer name
- acer.exe (PID: 2544)
- acer.exe (PID: 5856)
- acer.exe (PID: 6720)
- acer.exe (PID: 3780)
- identity_helper.exe (PID: 5892)
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
- identity_helper.exe (PID: 2252)
- identity_helper.exe (PID: 1500)
- firefox.exe (PID: 7100)
- firefox.exe (PID: 2468)
- firefox.exe (PID: 6320)
- firefox.exe (PID: 7816)
- firefox.exe (PID: 6788)
- firefox.exe (PID: 7916)
- firefox.exe (PID: 6556)
- firefox.exe (PID: 7280)
- tor.exe (PID: 3968)
- acer.exe (PID: 6292)
- firefox.exe (PID: 8012)
- firefox.exe (PID: 2944)
- firefox.exe (PID: 2480)
- firefox.exe (PID: 7260)
Manual execution by a user
- notepad++.exe (PID: 6992)
Reads the software policy settings
- acer.exe (PID: 2544)
Drops the executable file immediately after the start
- msedge.exe (PID: 1712)
Application launched itself
- msedge.exe (PID: 1712)
- msedge.exe (PID: 1224)
- msedge.exe (PID: 2656)
- msedge.exe (PID: 7728)
- msedge.exe (PID: 6264)
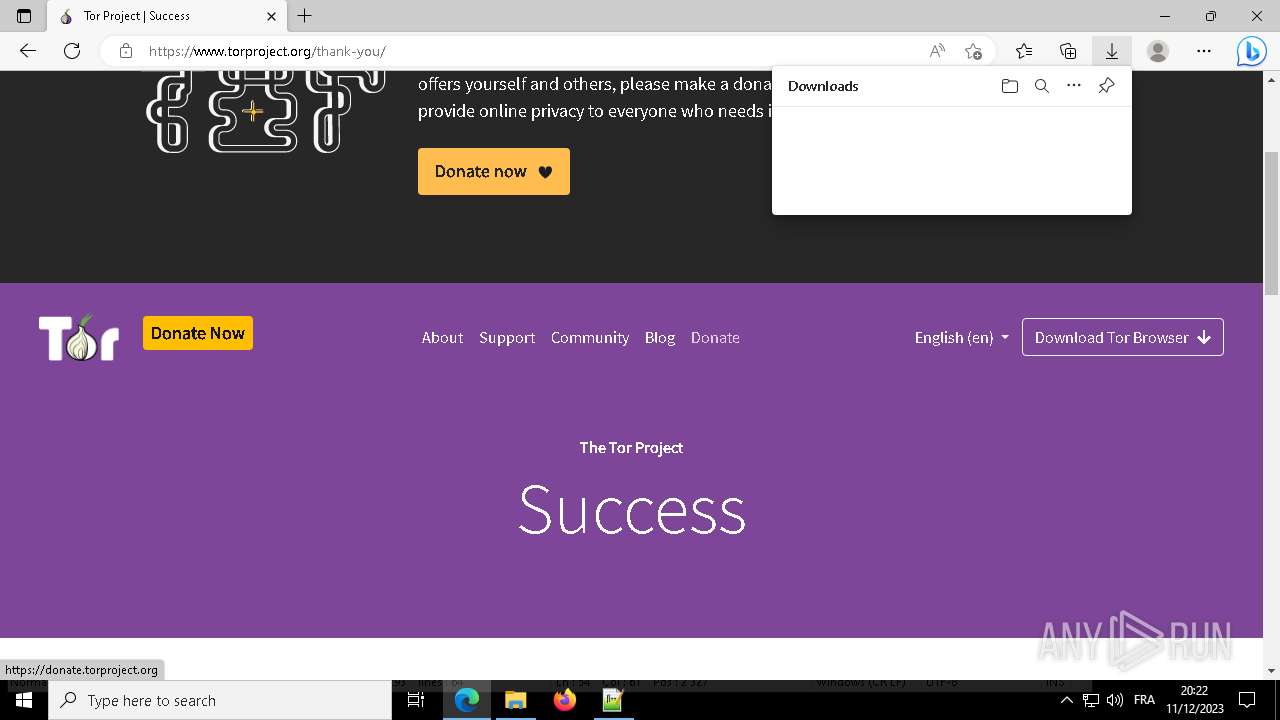
The process uses the downloaded file
- msedge.exe (PID: 8096)
- msedge.exe (PID: 1712)
Create files in a temporary directory
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
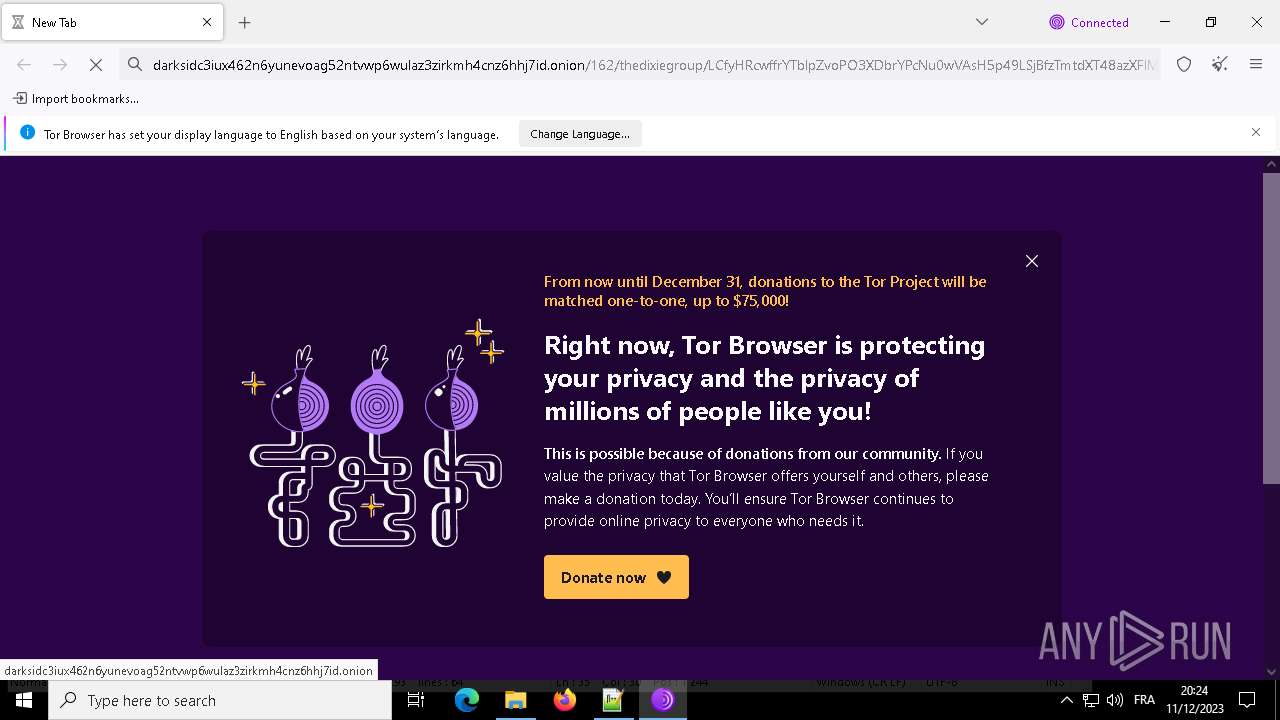
The dropped object may contain a URL to Tor Browser
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
- msedge.exe (PID: 1712)
- msedge.exe (PID: 1460)
- msedge.exe (PID: 1224)
Dropped object may contain TOR URL's
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
- acer.exe (PID: 3780)
- firefox.exe (PID: 7100)
Reads CPU info
- firefox.exe (PID: 7100)
Process checks computer location settings
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
- firefox.exe (PID: 7100)
- firefox.exe (PID: 8012)
- firefox.exe (PID: 7280)
Creates files or folders in the user directory
- tor-browser-windows-x86_64-portable-13.0.6.exe (PID: 6736)
Reads product name
- acer.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:04:06 00:09:09+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 38912 |
| InitializedDataSize: | 81920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb2bd |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
231
Monitored processes
105
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\111.0.1661.62\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4660 --field-trial-handle=1984,i,14931968374727737898,2647319038264339650,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\111.0.1661.62\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window /prefetch:5 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1460 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2020 --field-trial-handle=2164,i,6592508810880554217,10626810007443161095,131072 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1500 | "C:\Program Files (x86)\Microsoft\Edge\Application\111.0.1661.62\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4316 --field-trial-handle=1944,i,11601980975244602701,17683661026100419273,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\111.0.1661.62\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=5448 --field-trial-handle=1944,i,11601980975244602701,17683661026100419273,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
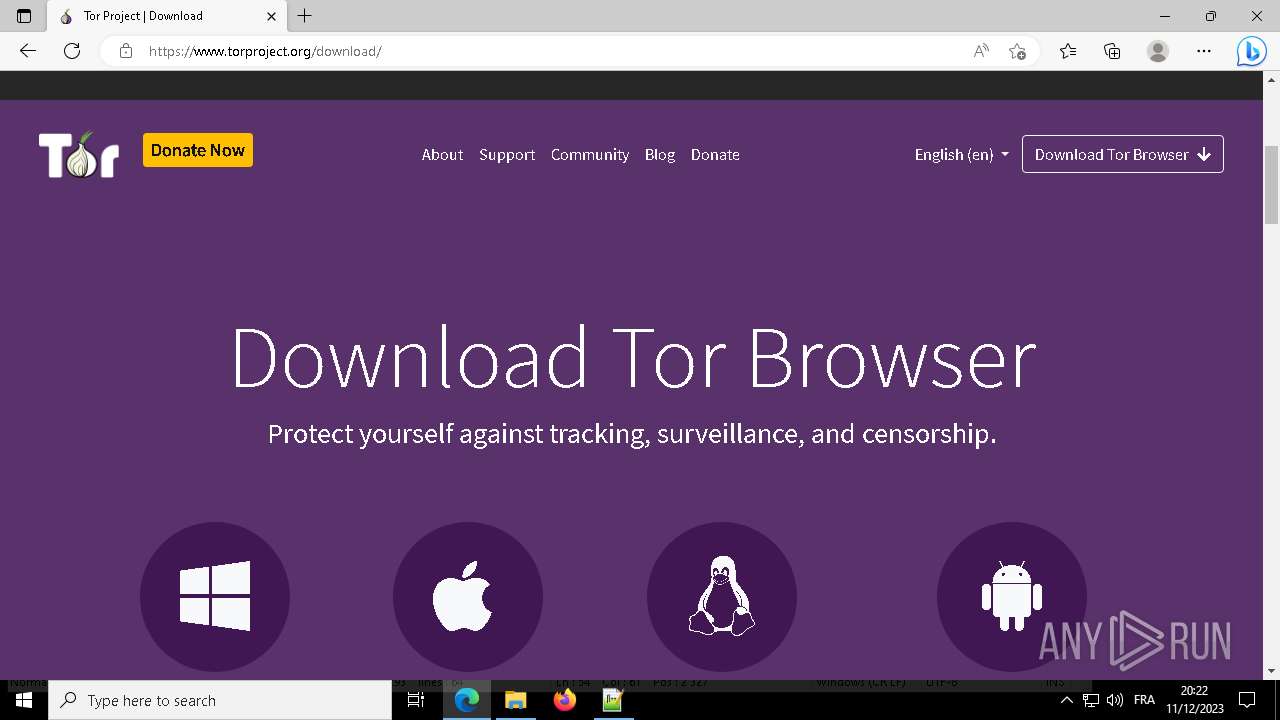
| 1712 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://torproject.org/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | notepad++.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=5296 --field-trial-handle=1984,i,14931968374727737898,2647319038264339650,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2252 | "C:\Program Files (x86)\Microsoft\Edge\Application\111.0.1661.62\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4660 --field-trial-handle=1984,i,14931968374727737898,2647319038264339650,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\111.0.1661.62\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\Desktop\Tor Browser\Browser\firefox.exe" -contentproc --channel="7100.0.1919211815\717211733" -parentBuildID 20231204122841 -prefsHandle 2056 -prefMapHandle 2044 -prefsLen 19245 -prefMapSize 243588 -appDir "C:\Users\admin\Desktop\Tor Browser\Browser\browser" - {308ee917-f273-41e8-9805-7cc33215838b} 7100 gpu | C:\Users\admin\Desktop\Tor Browser\Browser\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Tor Browser Exit code: 0 Version: 115.5.0 Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\Desktop\Tor Browser\Browser\firefox.exe" -contentproc --channel="7100.10.529172763\1184163923" -childID 9 -isForBrowser -prefsHandle 4828 -prefMapHandle 4932 -prefsLen 22800 -prefMapSize 243588 -jsInitHandle 1324 -jsInitLen 240916 -parentBuildID 20231204122841 -win32kLockedDown -appDir "C:\Users\admin\Desktop\Tor Browser\Browser\browser" - {da6fc5f4-bb59-46a8-bde6-d941fca2e3b9} 7100 tab | C:\Users\admin\Desktop\Tor Browser\Browser\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Tor Browser Exit code: 0 Version: 115.5.0 Modules
| |||||||||||||||
Total events
35 752
Read events
35 521
Write events
198
Delete events
33
Modification events
| (PID) Process: | (7036) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7036) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7036) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7036) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7036) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2544) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2544) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2544) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2544) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2544) acer.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
39
Suspicious files
659
Text files
337
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
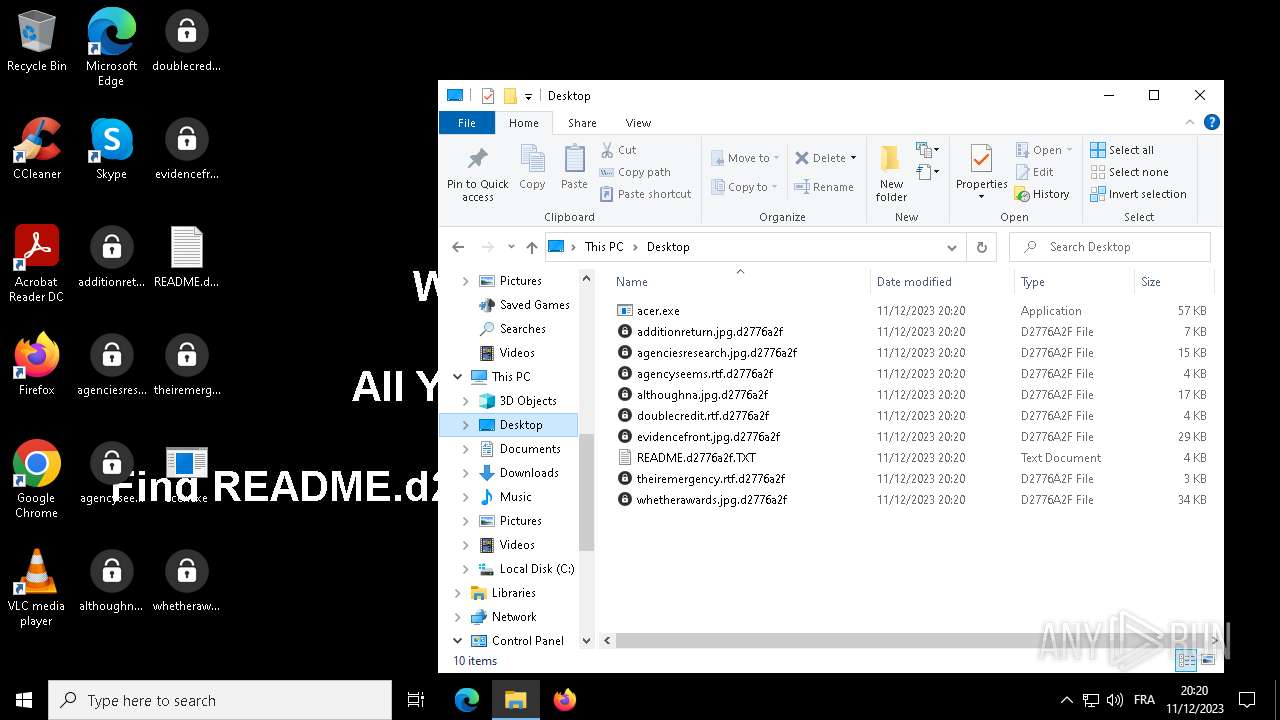
| 3780 | acer.exe | C:\BOOTNXT.d2776a2f | binary | |
MD5:93B885ADFE0DA089CDF634904FD59F71 | SHA256:6E340B9CFFB37A989CA544E6BB780A2C78901D3FB33738768511A30617AFA01D | |||
| 3780 | acer.exe | C:\found.000\dir0001.chk\WmiApRpl.h.d2776a2f | image | |
MD5:FE8831D8AE65666C08AB6CEB5734C6E3 | SHA256:3E4BDEB61C3386BEC9A0D78FA0FF108F3813B551E4A7D0C3B7B6461B4C9816B0 | |||
| 2544 | acer.exe | C:\ProgramData\d2776a2f.ico | image | |
MD5:4F57D54D01CCBDAF3EBFAC3EC0AC3FD7 | SHA256:28B6841AA125225CD01BE09FBD2F1D7B3C2102D9FFC7DC8546700E67C2A6E3BC | |||
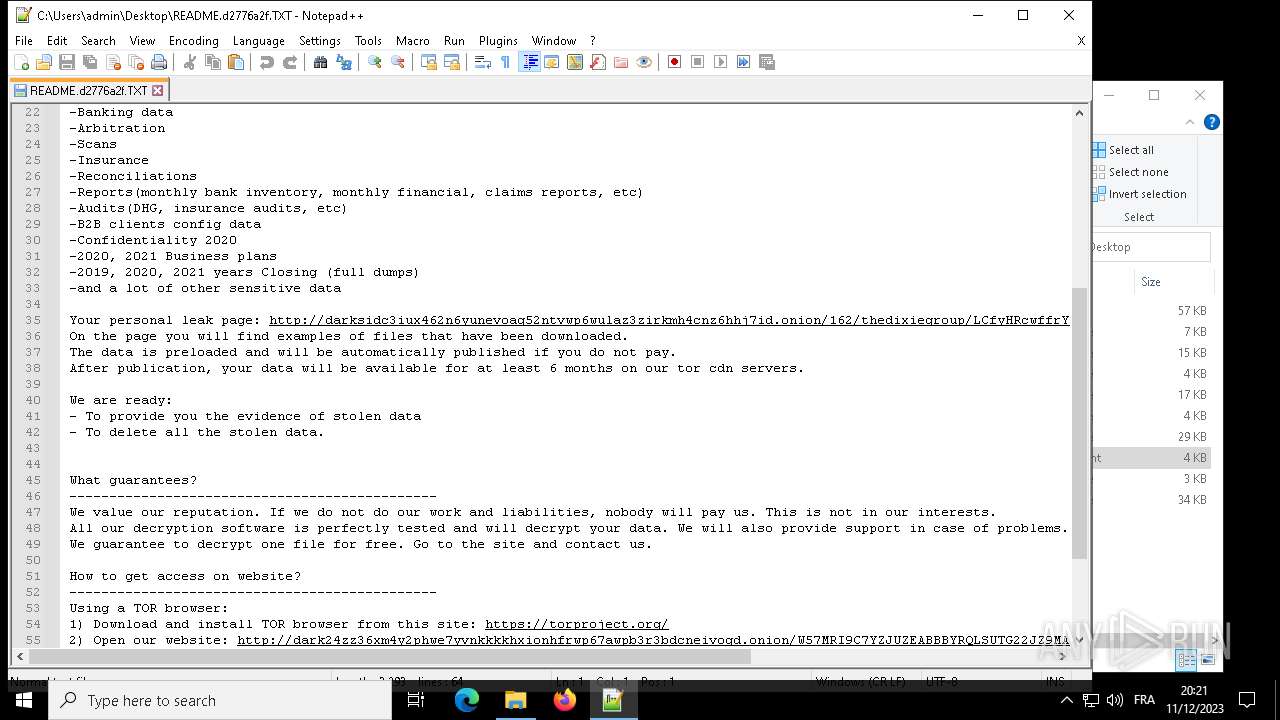
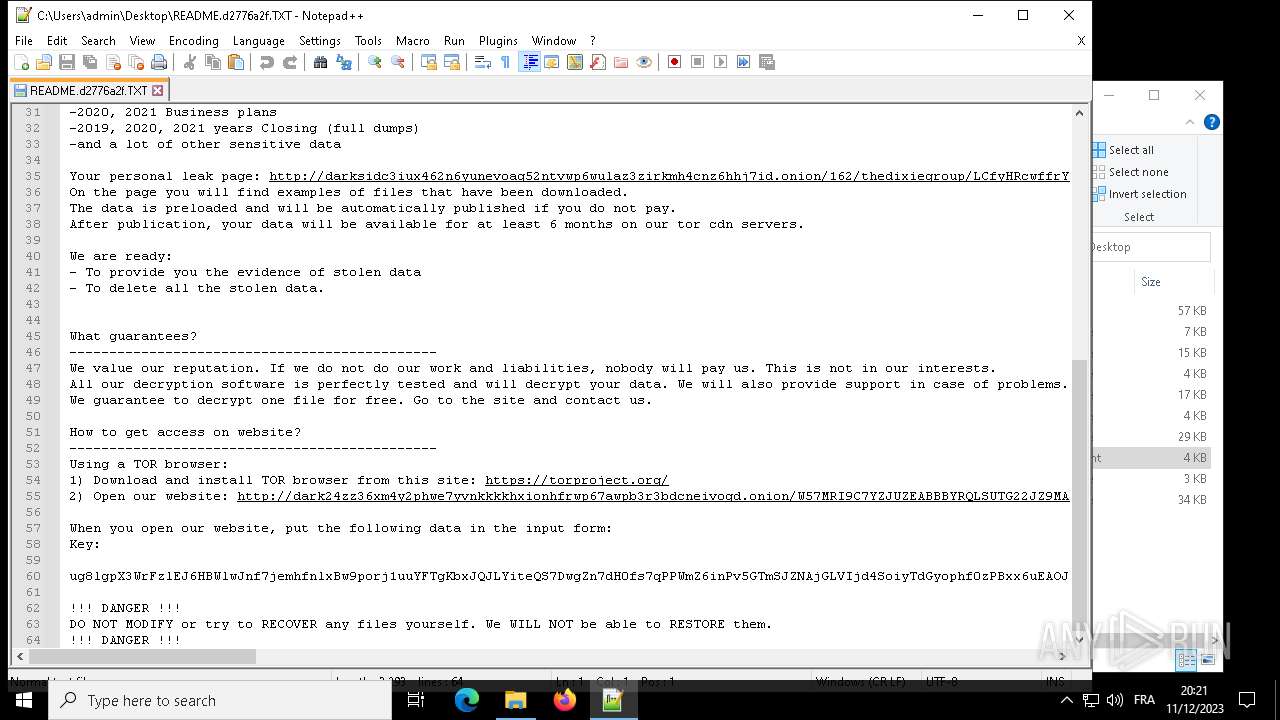
| 3780 | acer.exe | C:\found.000\README.d2776a2f.TXT | text | |
MD5:164AA420BE8E0C2BCDEF574355EDAA32 | SHA256:B326D11DD90C2E4EFB0A384981F71C2BD1A6FAA0553D6389ACB08945B699F73D | |||
| 3780 | acer.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.037.etl.d2776a2f | binary | |
MD5:80A56918B8F7CCD3D78BBC6D70DA8498 | SHA256:8703EF66931EFE9DD10ED7D5F4B88065A3B8FC2B23515FA61D21C49C52C38373 | |||
| 3780 | acer.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.058.etl.d2776a2f | binary | |
MD5:389F45A91E7FFC038CCCDB460AAD253D | SHA256:7C38AD8787A332AB2026A1C7516B5502842F8946E1D706ACCB9523BF6210F639 | |||
| 3780 | acer.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.061.etl.d2776a2f | binary | |
MD5:392C3F40C73E58132712E947AE9D371E | SHA256:03AB8771191D5FC774659228137C231421AABB0D48F9E46D94A5E73F6D8F2A30 | |||
| 3780 | acer.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.052.etl.d2776a2f | binary | |
MD5:1F3FD67433DAB64DA48D3F123968BB68 | SHA256:31E20FD59F30F4C9CED391F47E9D03961BC1D8B1DCA37CAB8F4E745E09708C17 | |||
| 3780 | acer.exe | C:\found.000\dir0000.chk\README.d2776a2f.TXT | text | |
MD5:164AA420BE8E0C2BCDEF574355EDAA32 | SHA256:B326D11DD90C2E4EFB0A384981F71C2BD1A6FAA0553D6389ACB08945B699F73D | |||
| 3780 | acer.exe | C:\found.000\dir0001.chk\README.d2776a2f.TXT | text | |
MD5:164AA420BE8E0C2BCDEF574355EDAA32 | SHA256:B326D11DD90C2E4EFB0A384981F71C2BD1A6FAA0553D6389ACB08945B699F73D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
112
DNS requests
145
Threats
70
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2876 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
2544 | acer.exe | GET | 200 | 184.24.77.58:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMzUhCmVMxflDqbVPDK4AyeLg%3D%3D | unknown | binary | 503 b | unknown |
2544 | acer.exe | GET | 200 | 23.56.202.135:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2544 | acer.exe | GET | 200 | 199.59.243.225:80 | http://ww25.baroquetees.com/iXmtcADB?subid1=20231212-0620-52f8-a937-78528b2e76f5 | unknown | html | 1.14 Kb | unknown |
6560 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
5008 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
7148 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | binary | 418 b | unknown |
2544 | acer.exe | GET | 200 | 199.59.243.225:80 | http://ww25.baroquetees.com/nmP8B1X9A?subid1=20231212-0621-0028-a249-f052568a7218 | unknown | html | 1.14 Kb | unknown |
7148 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | binary | 409 b | unknown |
2344 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | binary | 814 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2544 | acer.exe | 103.224.212.215:443 | baroquetees.com | Trellian Pty. Limited | AU | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2544 | acer.exe | 23.56.202.135:80 | — | AKAMAI-AS | GB | unknown |
2876 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2876 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2544 | acer.exe | 184.24.77.58:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2544 | acer.exe | 199.59.243.225:80 | ww25.baroquetees.com | AMAZON-02 | US | unknown |
5008 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5008 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
baroquetees.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
ww25.baroquetees.com |
| unknown |
rumahsia.com |
| unknown |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2544 | acer.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed DarkSide Ransomware Domain (baroquetees .com in TLS SNI) |
2544 | acer.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed DarkSide Ransomware Domain (baroquetees .com in TLS SNI) |
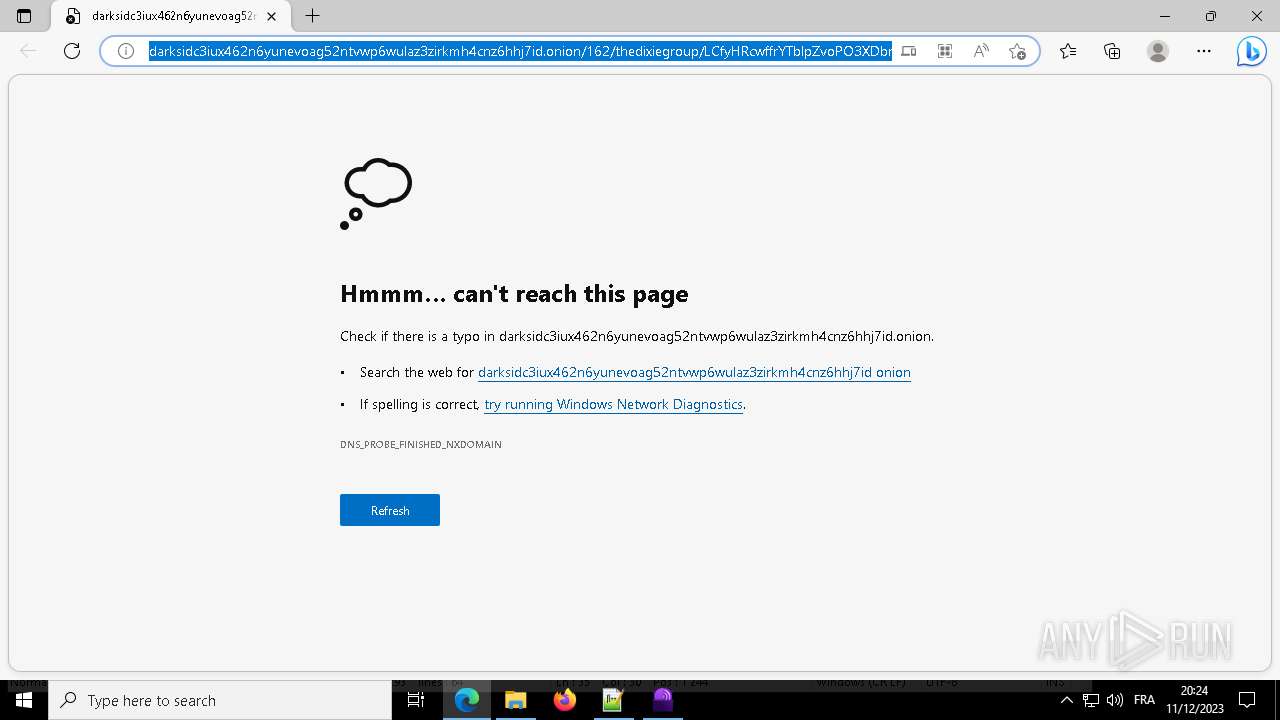
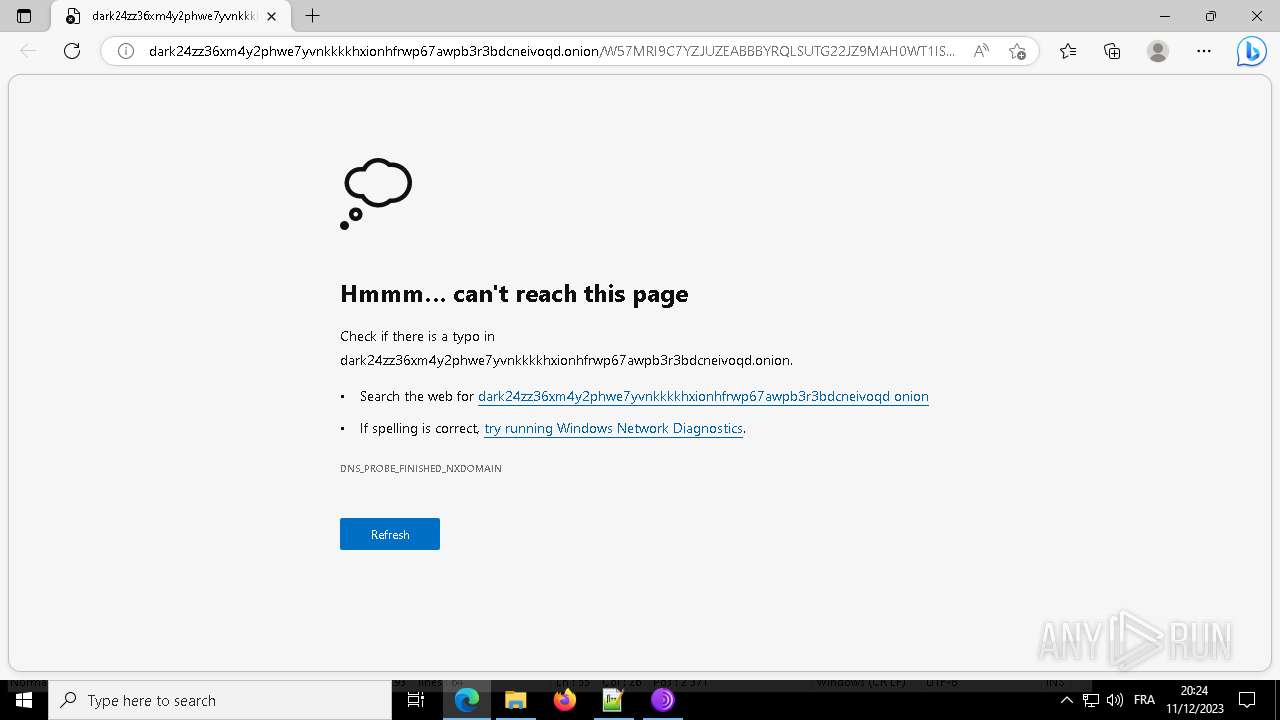
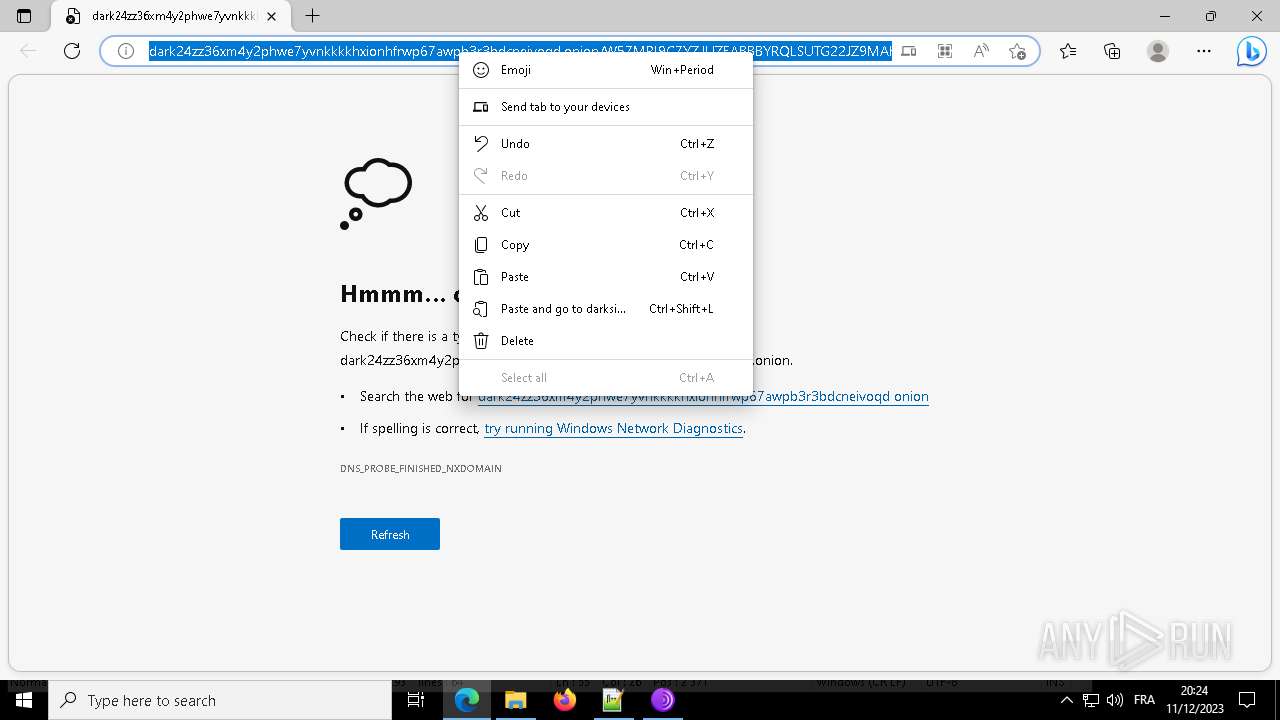
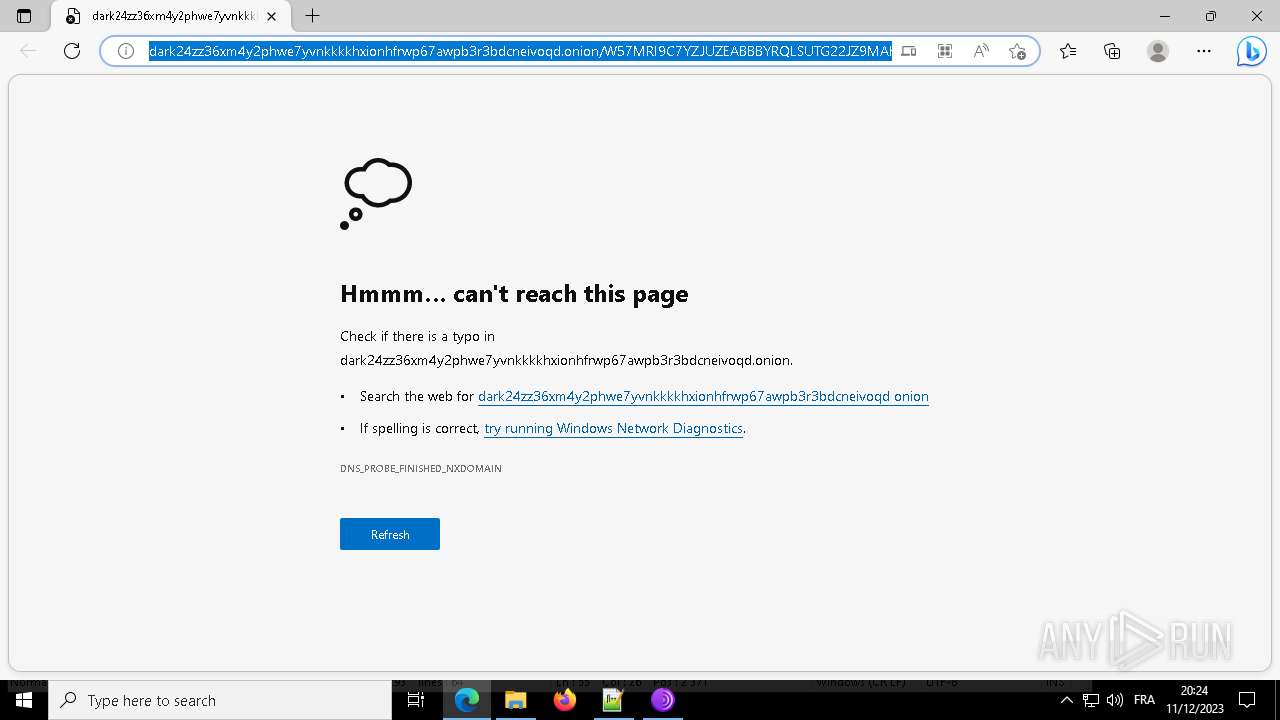
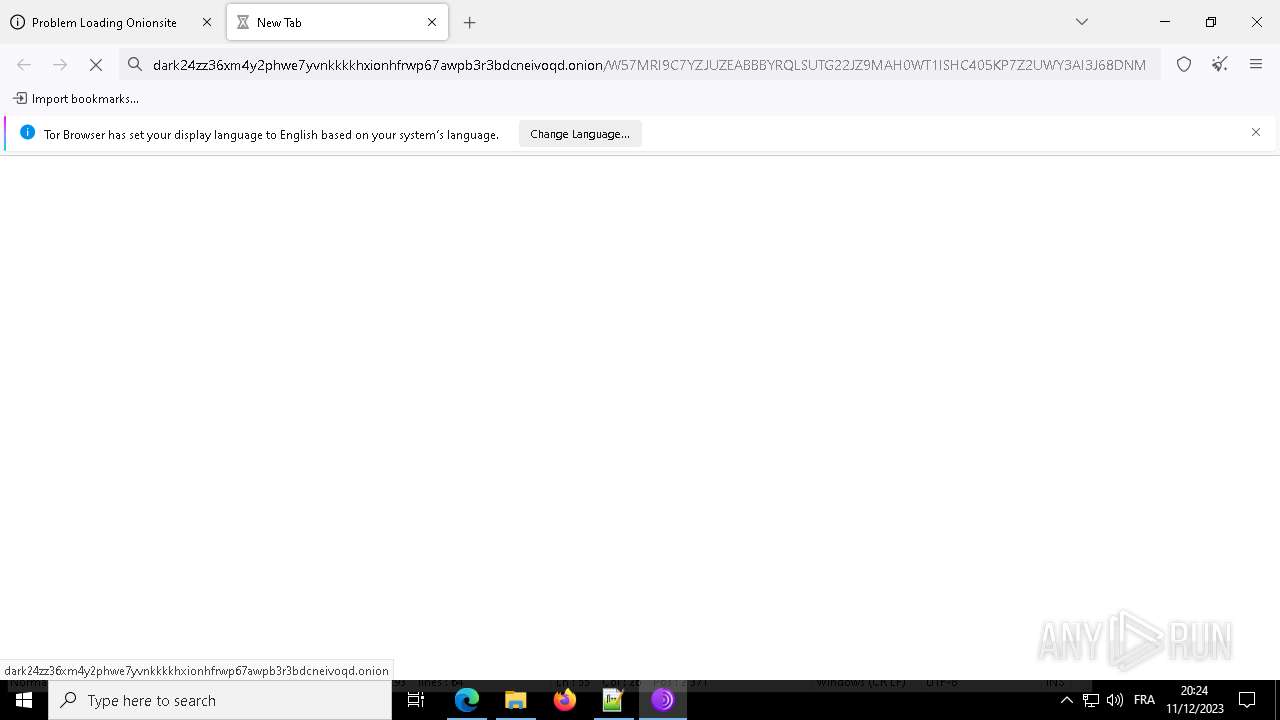
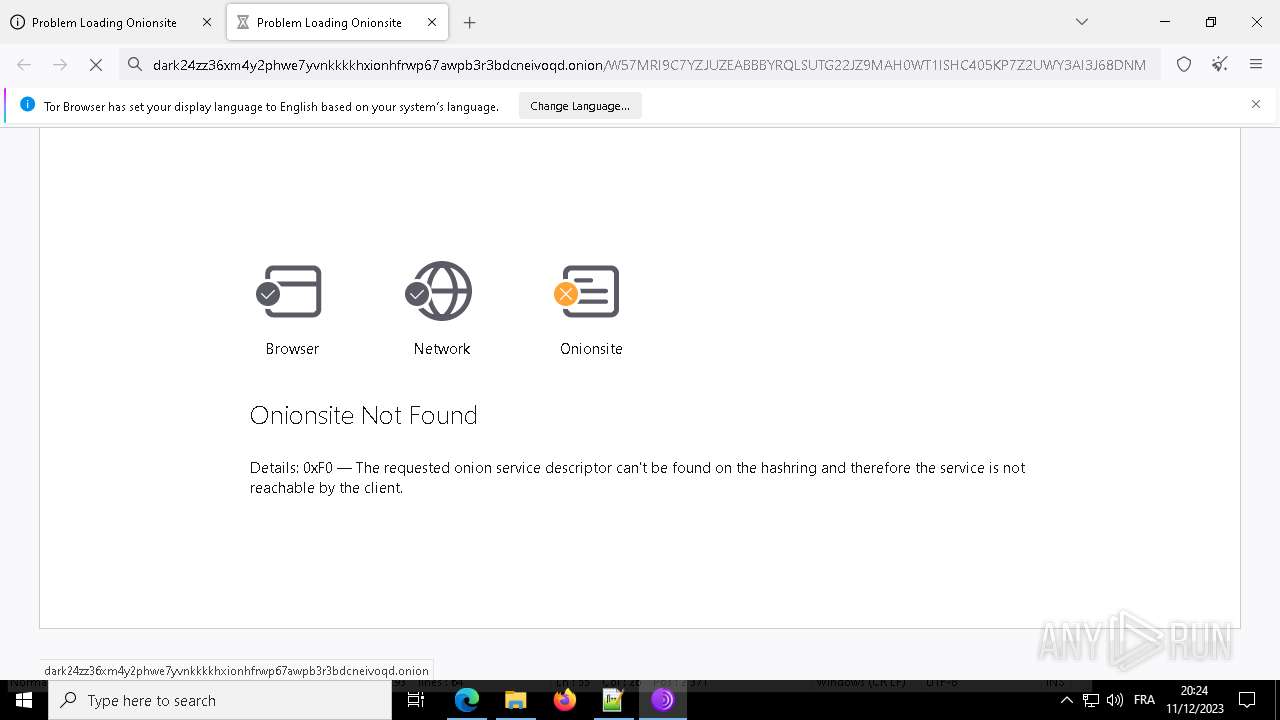
7276 | msedge.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
7276 | msedge.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
7276 | msedge.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
7276 | msedge.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
7276 | msedge.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
7276 | msedge.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
2092 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2092 | svchost.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|