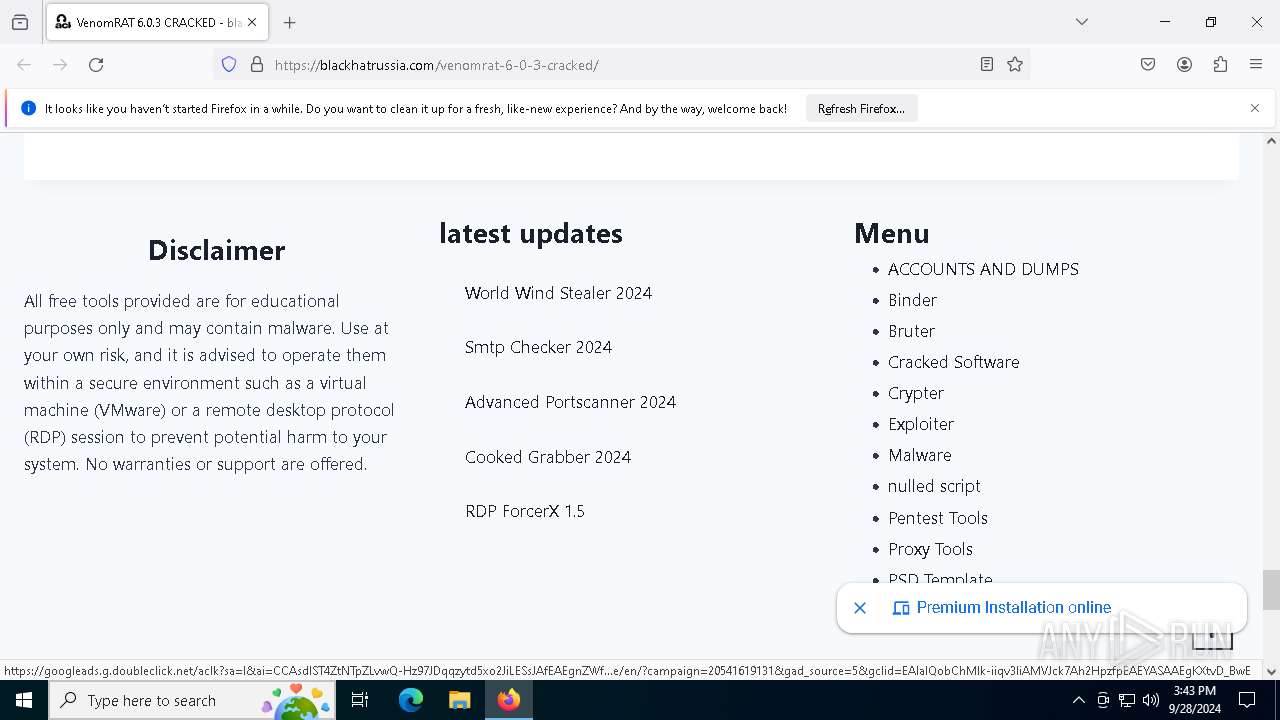
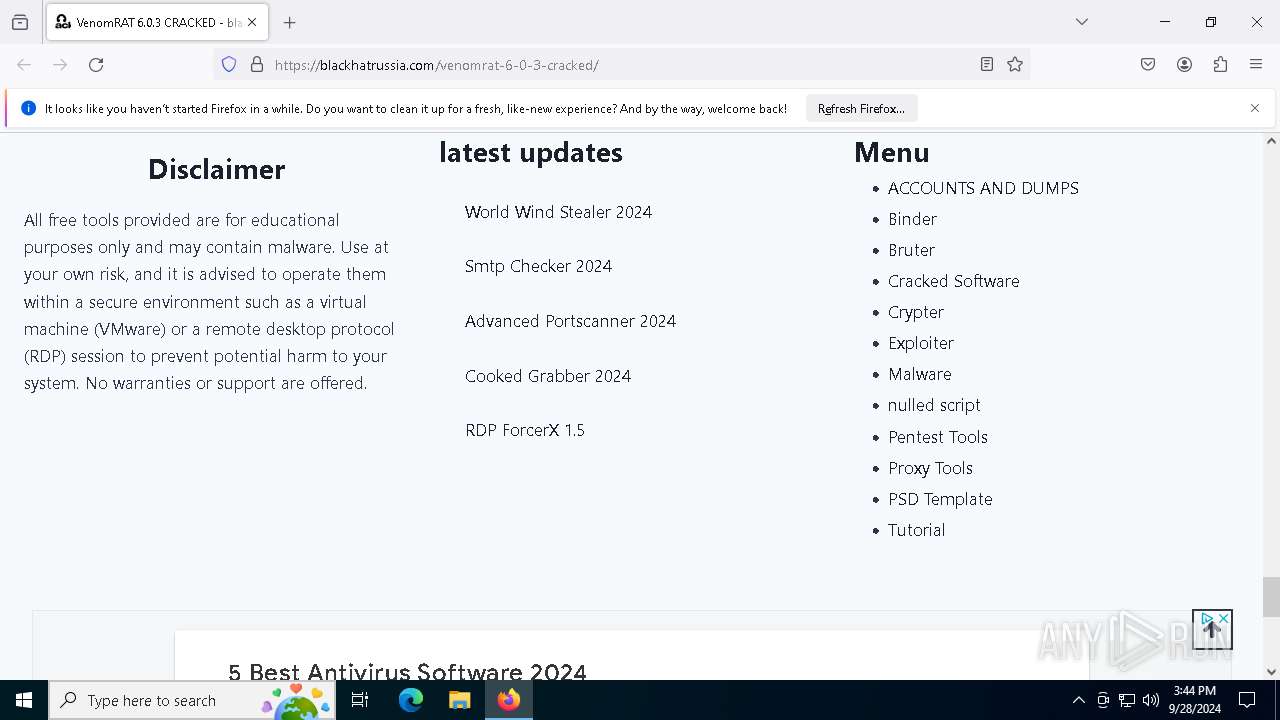
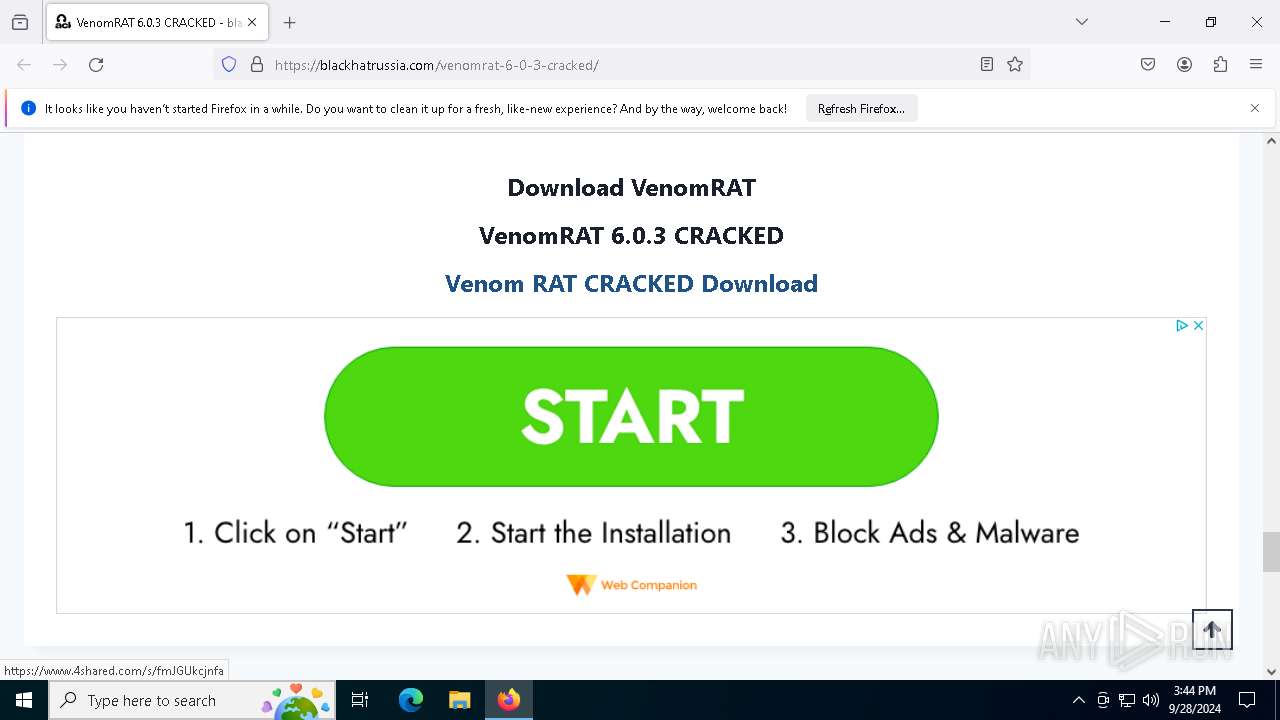
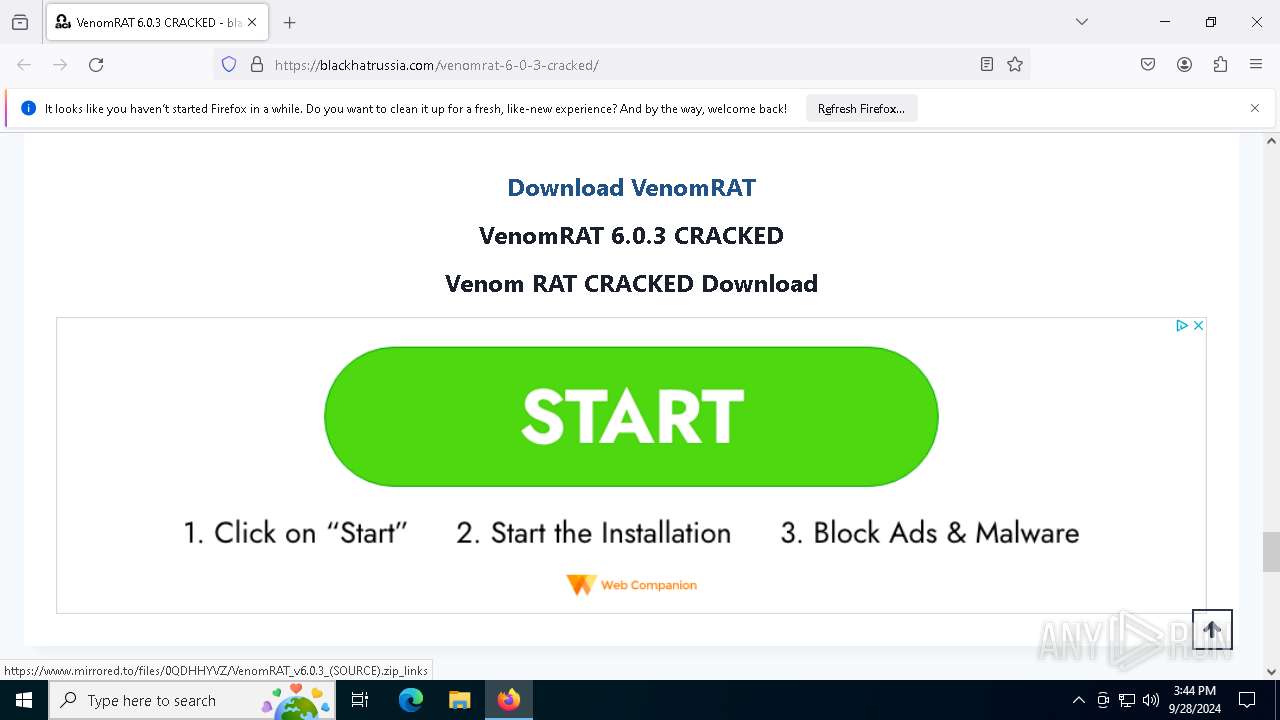
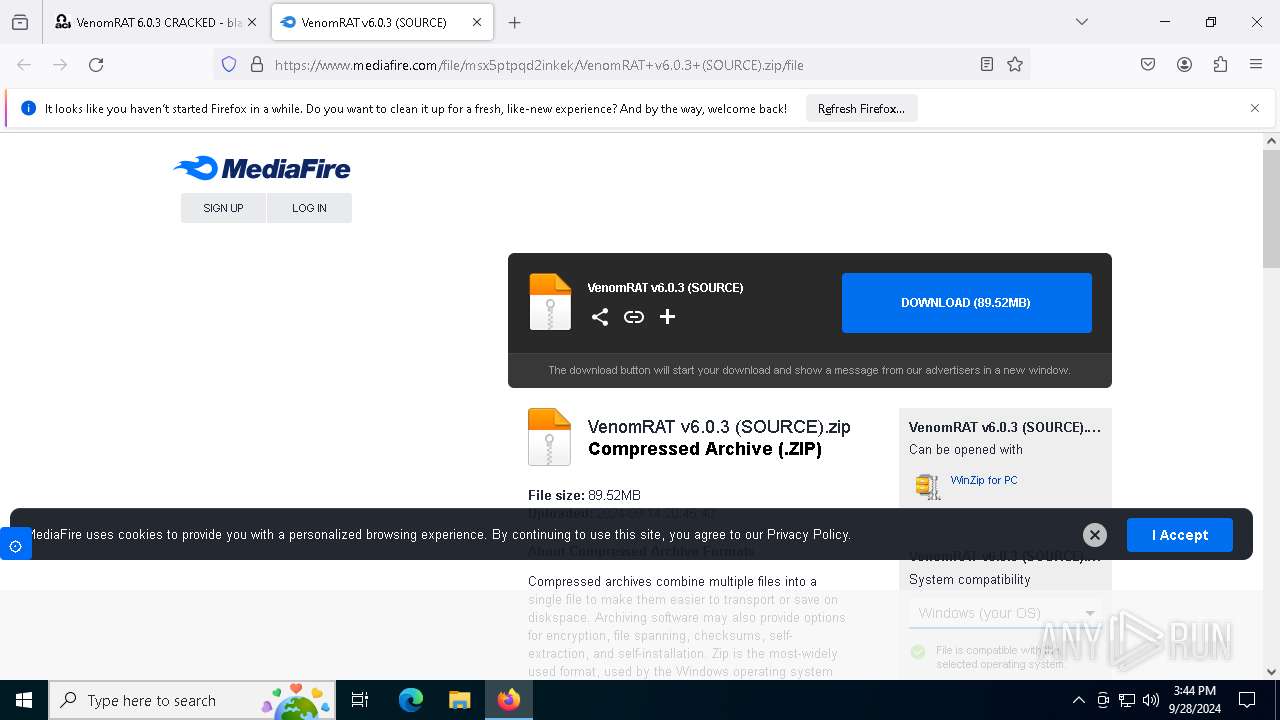
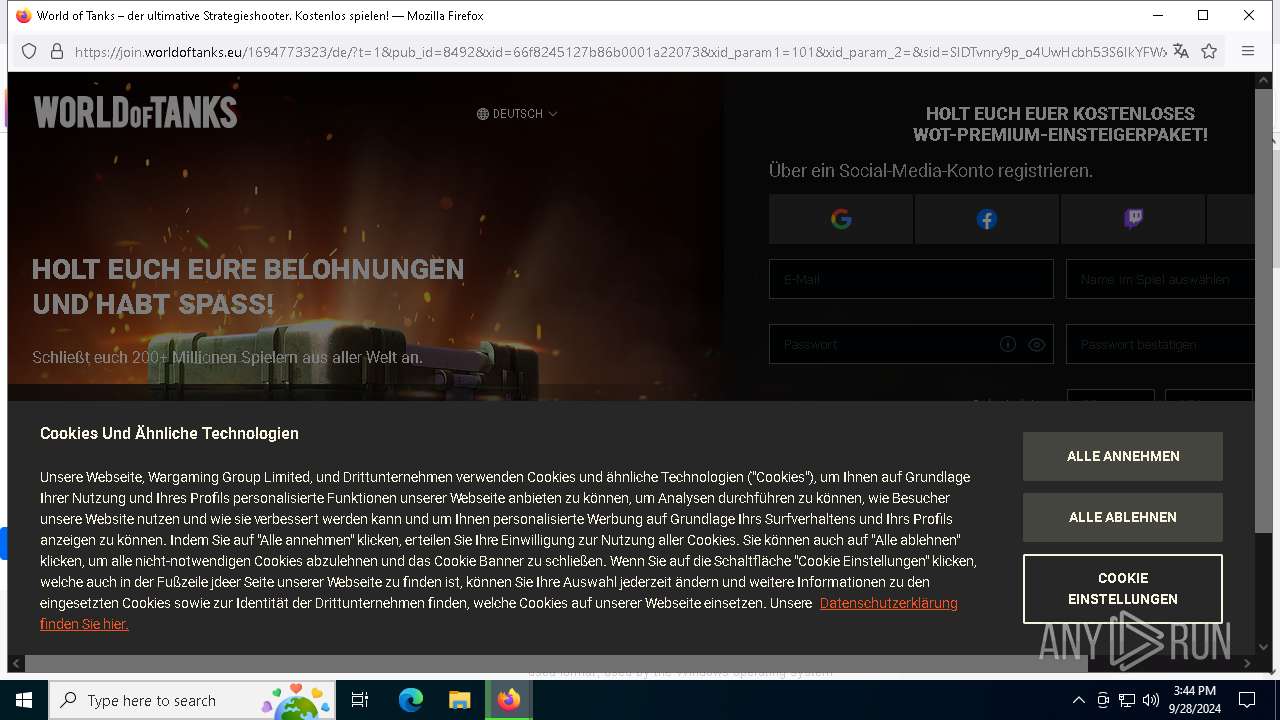
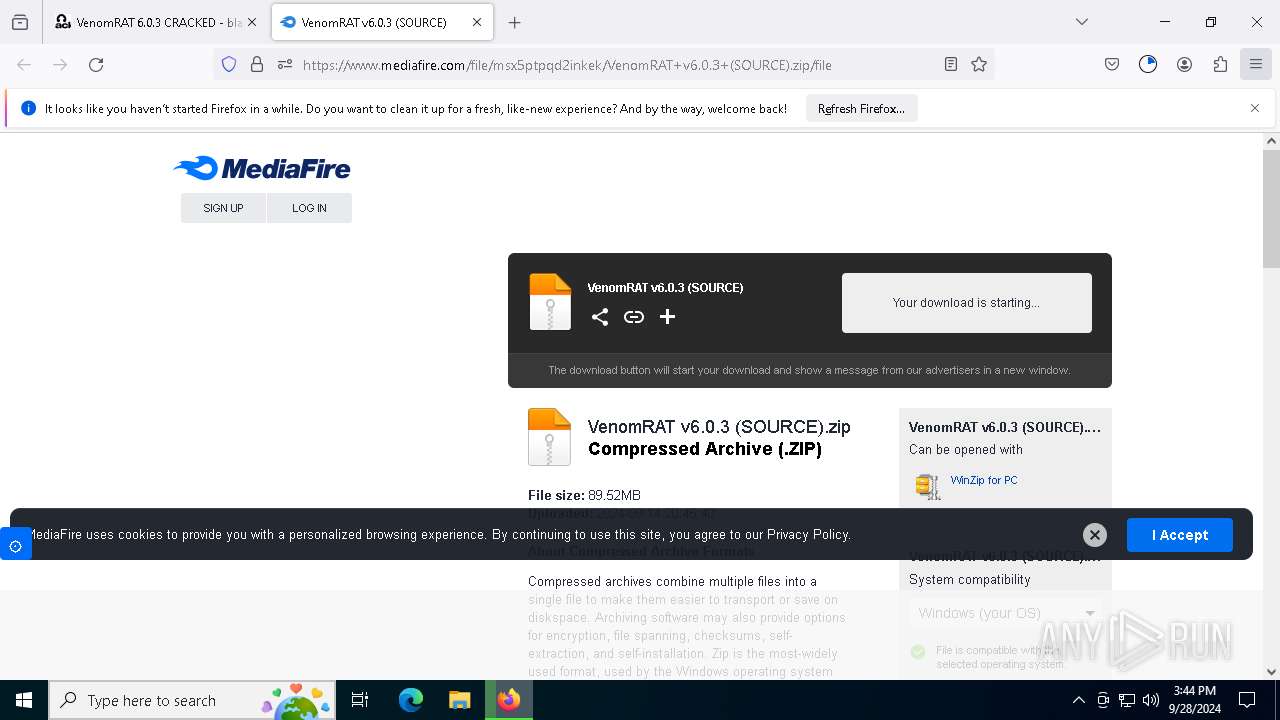
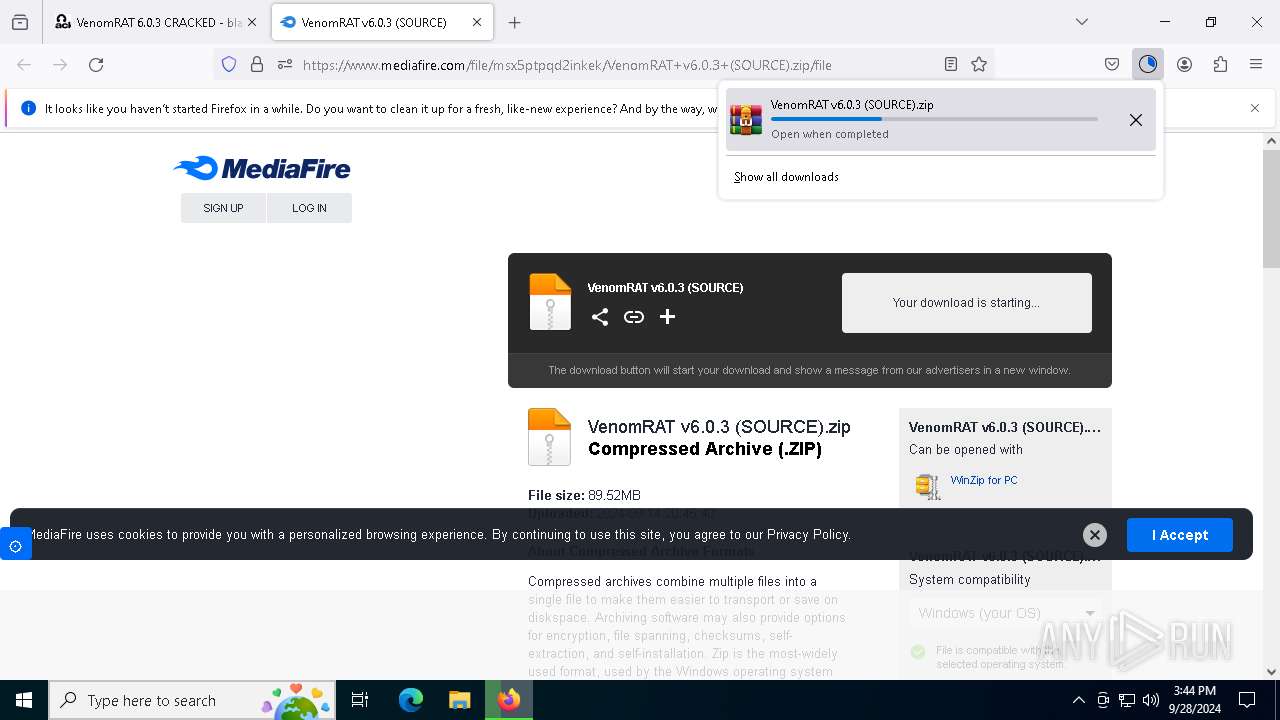
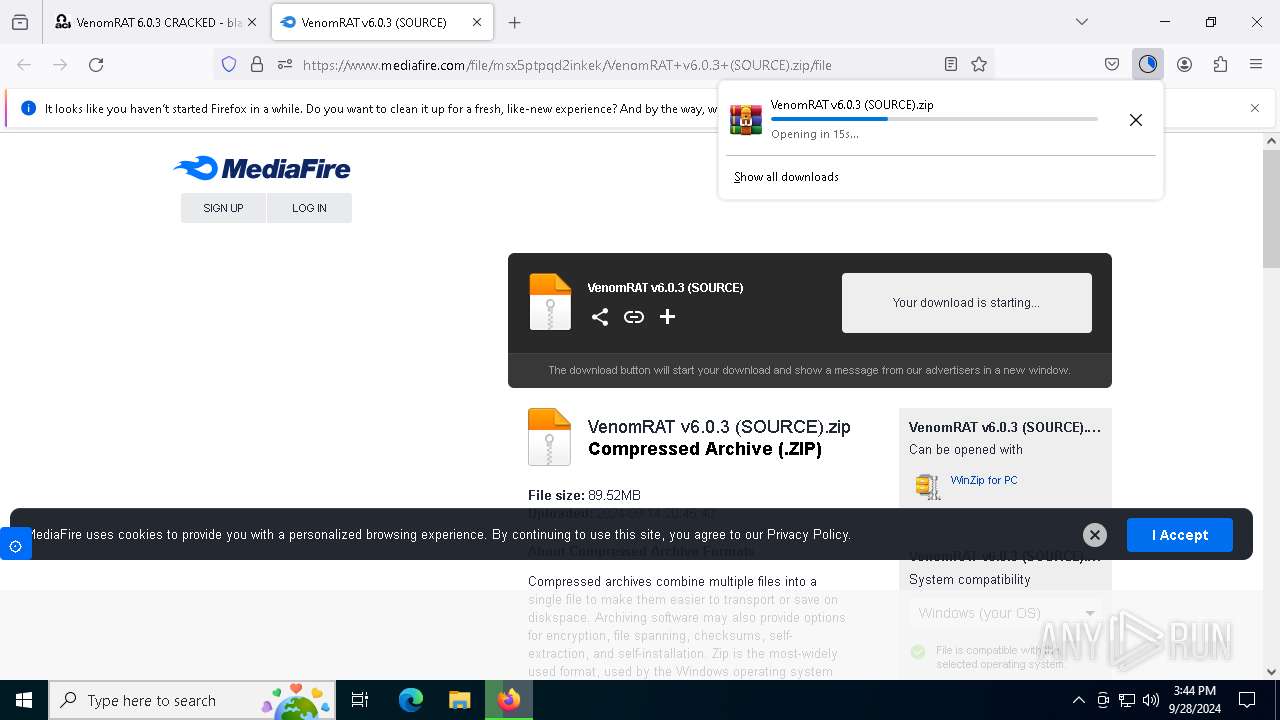
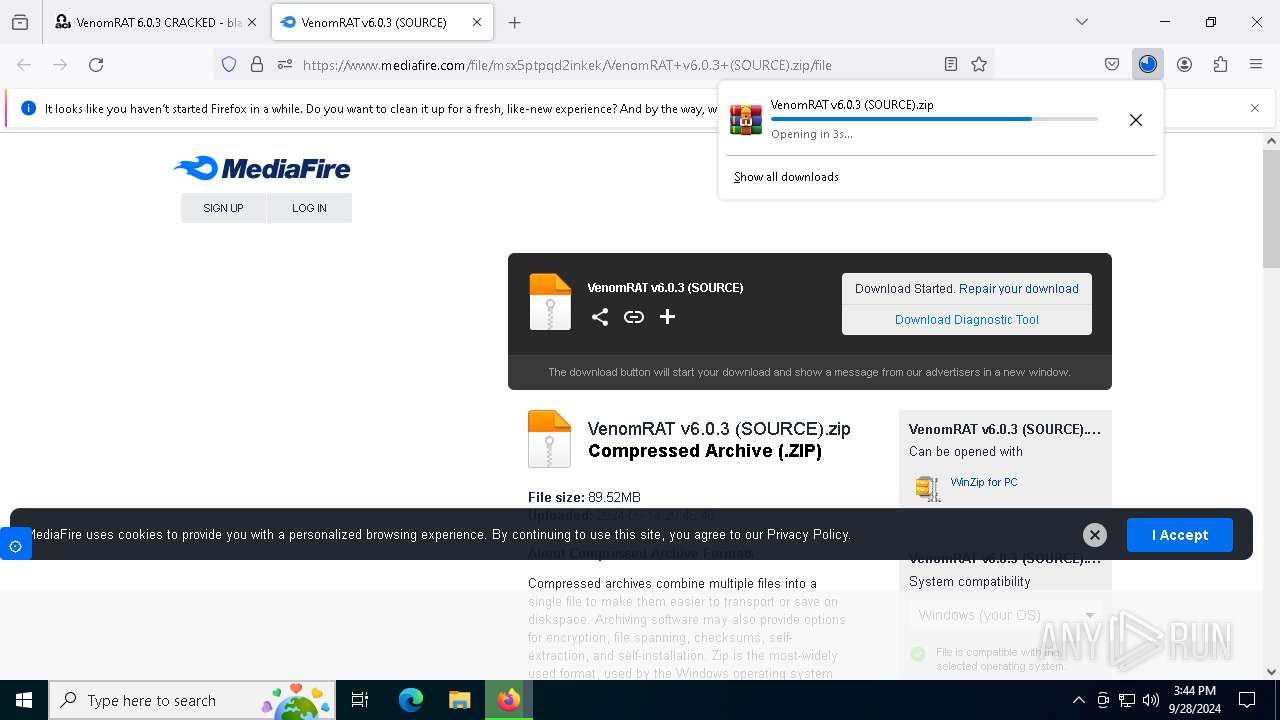
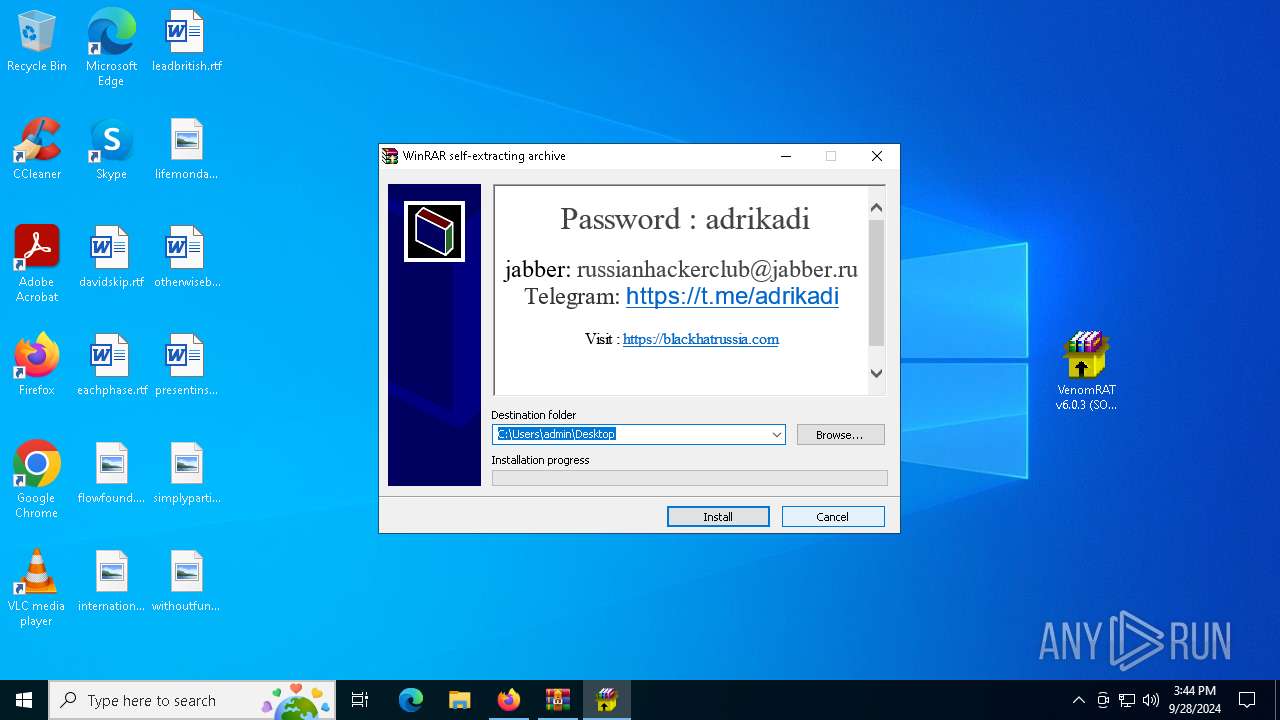
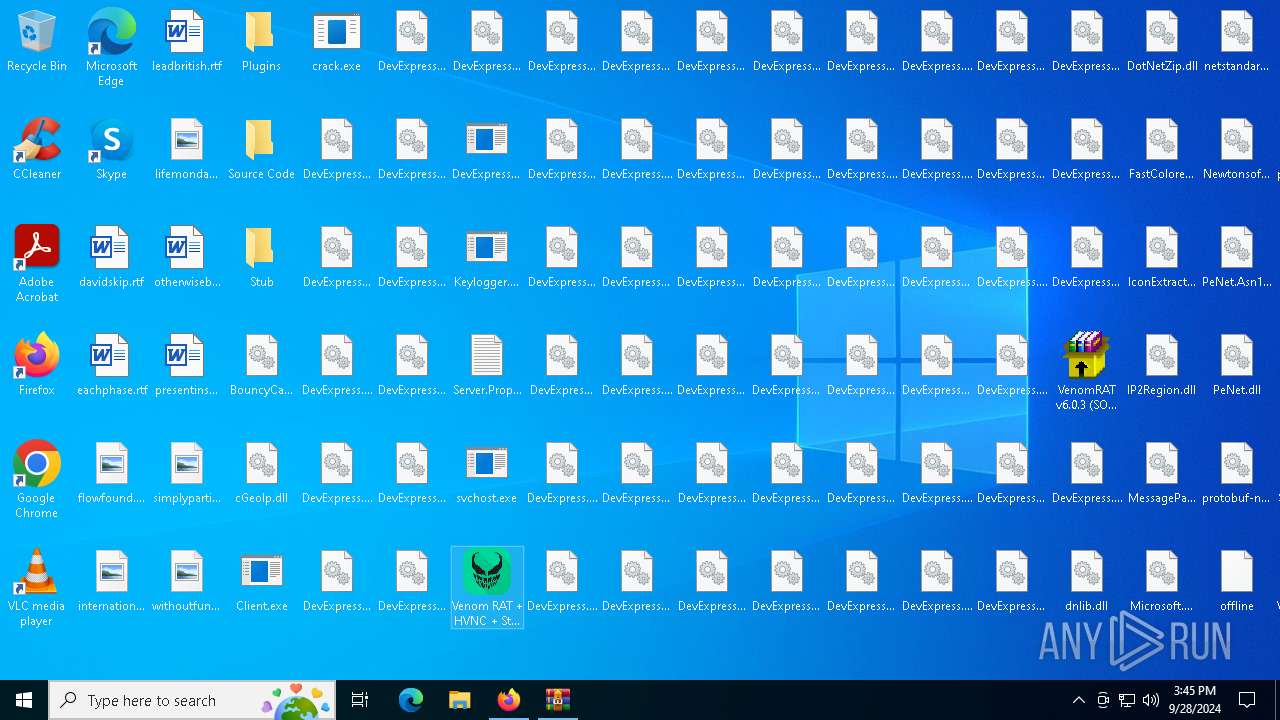
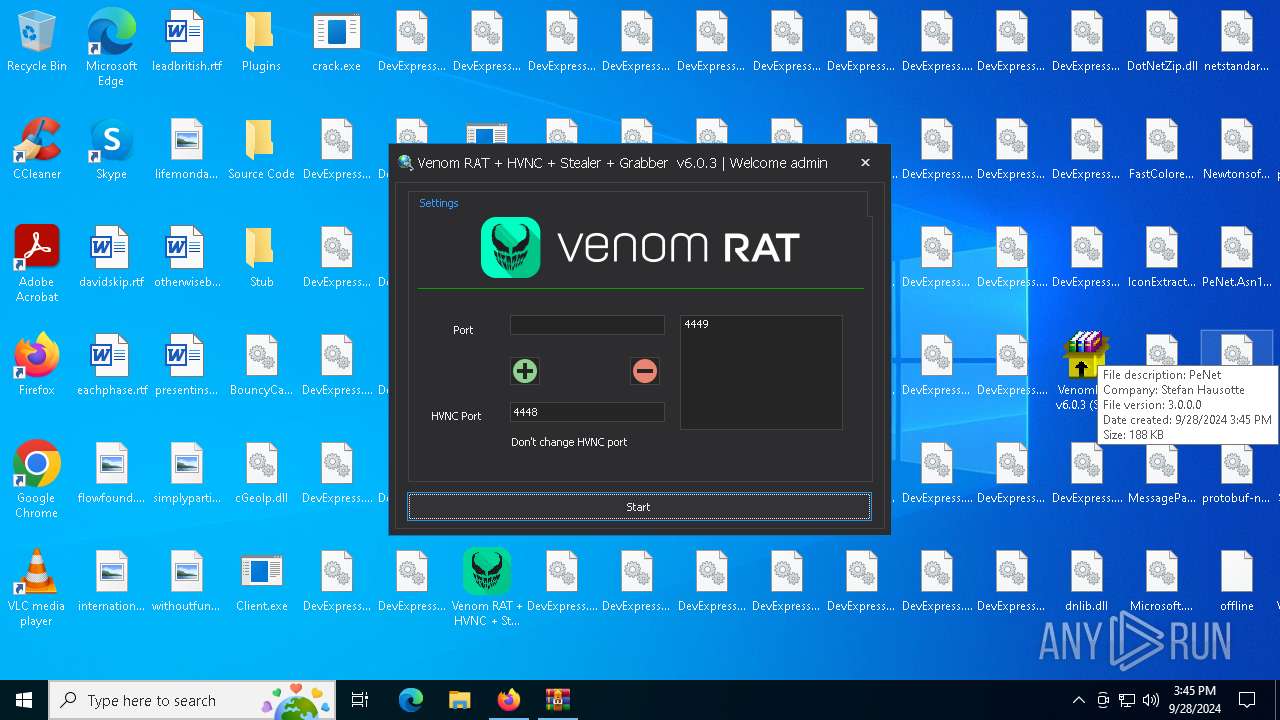
| URL: | https://blackhatrussia.com/venomrat-6-0-3-cracked/ |
| Full analysis: | https://app.any.run/tasks/9aa00d4a-dbb5-44f1-b0a6-b207d157793a |
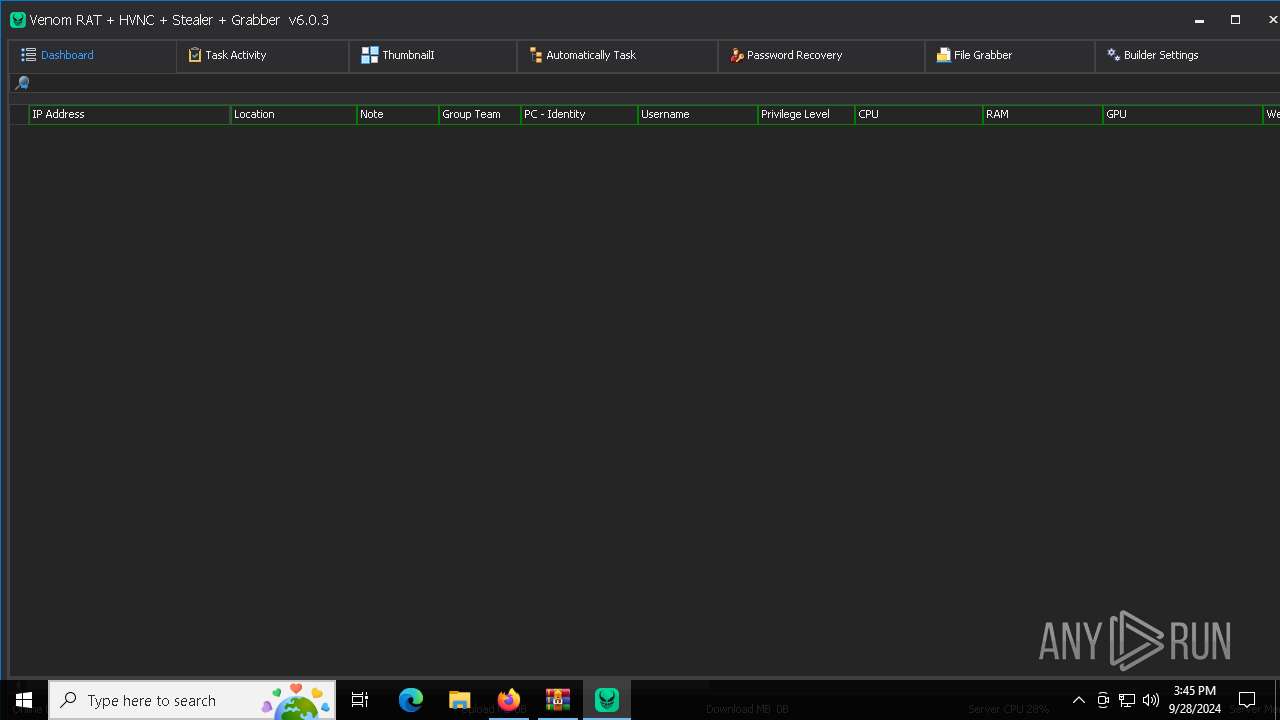
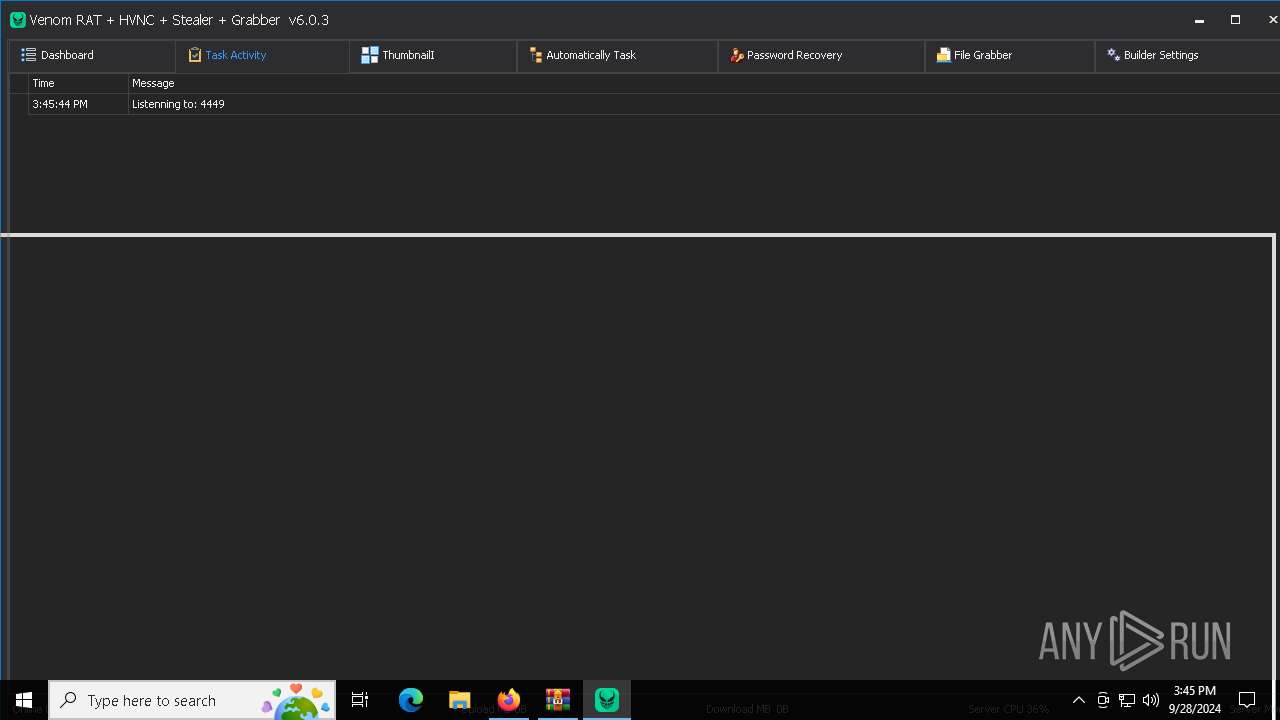
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | September 28, 2024, 15:42:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 190B612F0F6A99E35700A20D9C4A20A2 |
| SHA1: | 60612592BC74C7A1090D11EB01510E0AC4DA5C46 |
| SHA256: | 0A0935C7BAE5CA09E39012B1C38F76EF42007A7F39C0890067B074C113EC5D24 |
| SSDEEP: | 3:N8WFWWAKBIXFEzK:2WFRAVmm |
MALICIOUS
Adds path to the Windows Defender exclusion list
- svchost.exe (PID: 7436)
- cmd.exe (PID: 7208)
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 7212)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 7212)
- MpCmdRun.exe (PID: 8848)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7132)
Bypass execution policy to execute commands
- powershell.exe (PID: 8564)
GROWTOPIA has been detected (YARA)
- svchost.exe (PID: 7436)
DISCORDGRABBER has been detected (YARA)
- svchost.exe (PID: 7436)
UMBRALSTEALER has been detected (YARA)
- svchost.exe (PID: 7436)
Stealers network behavior
- svchost.exe (PID: 7436)
BLANKGRABBER has been detected (SURICATA)
- svchost.exe (PID: 7436)
ASYNCRAT has been detected (YARA)
- Venom RAT + HVNC + Stealer + Grabber.exe (PID: 7748)
SUSPICIOUS
Executable content was dropped or overwritten
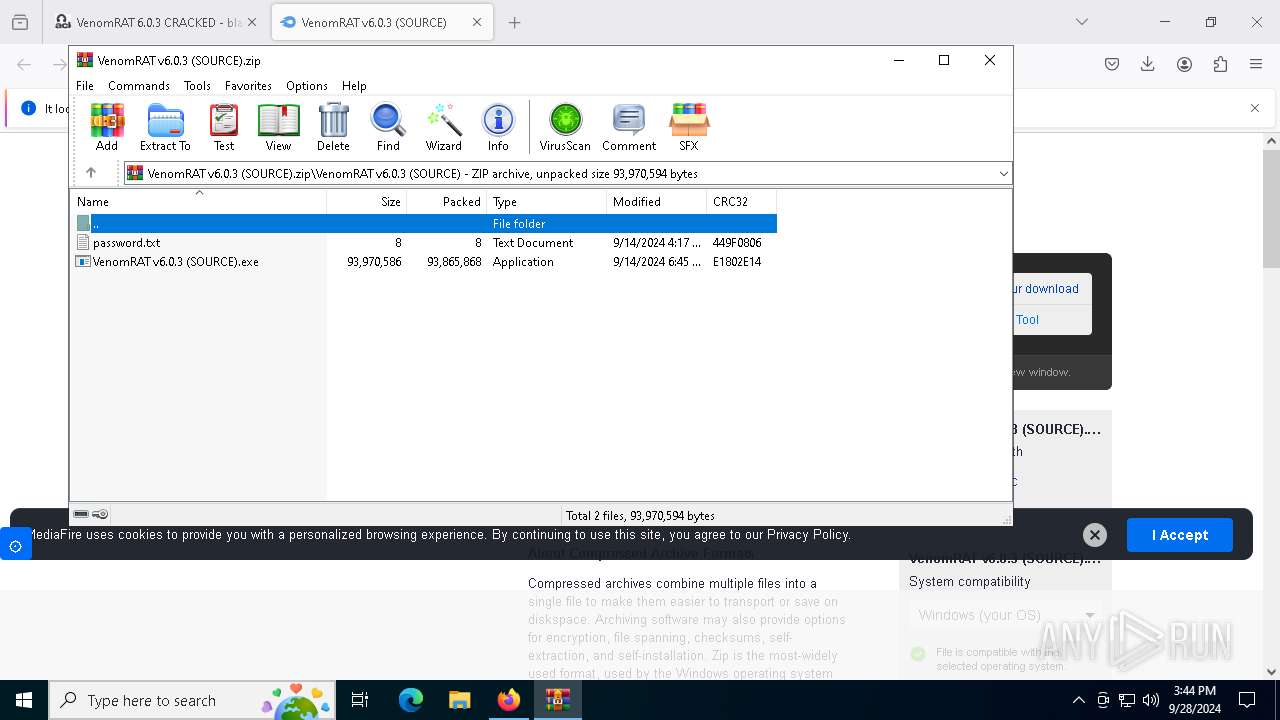
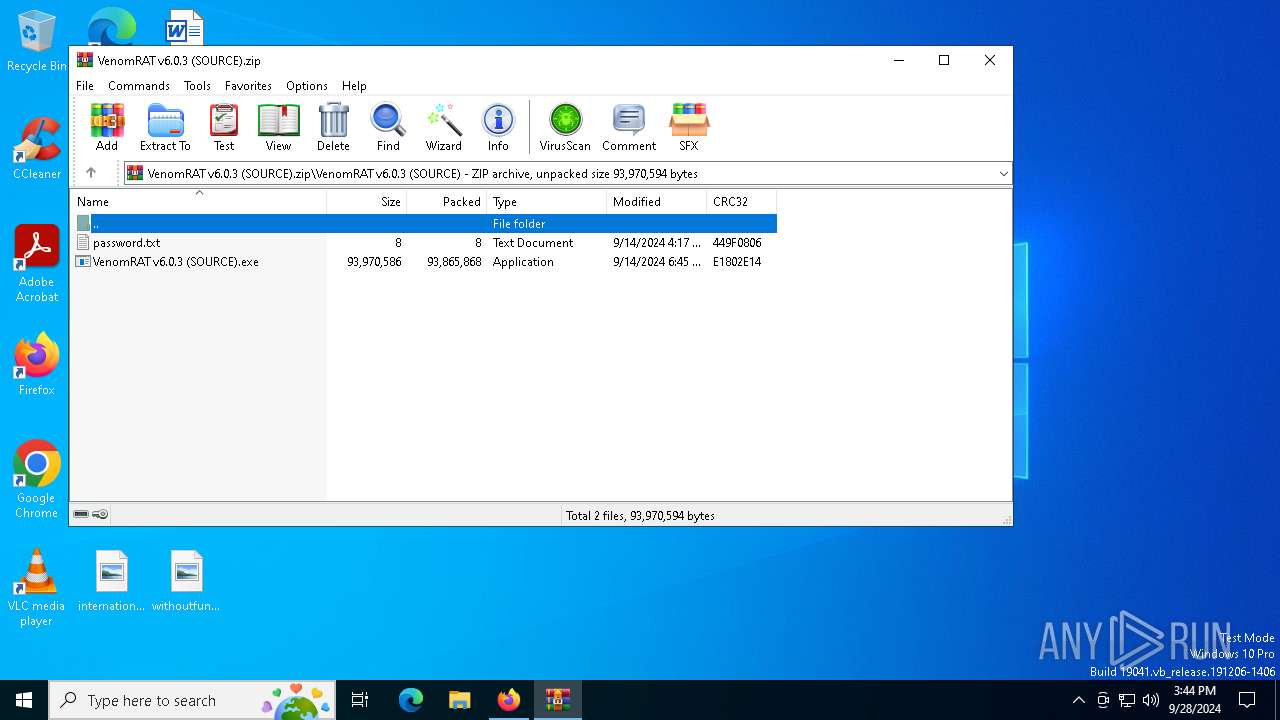
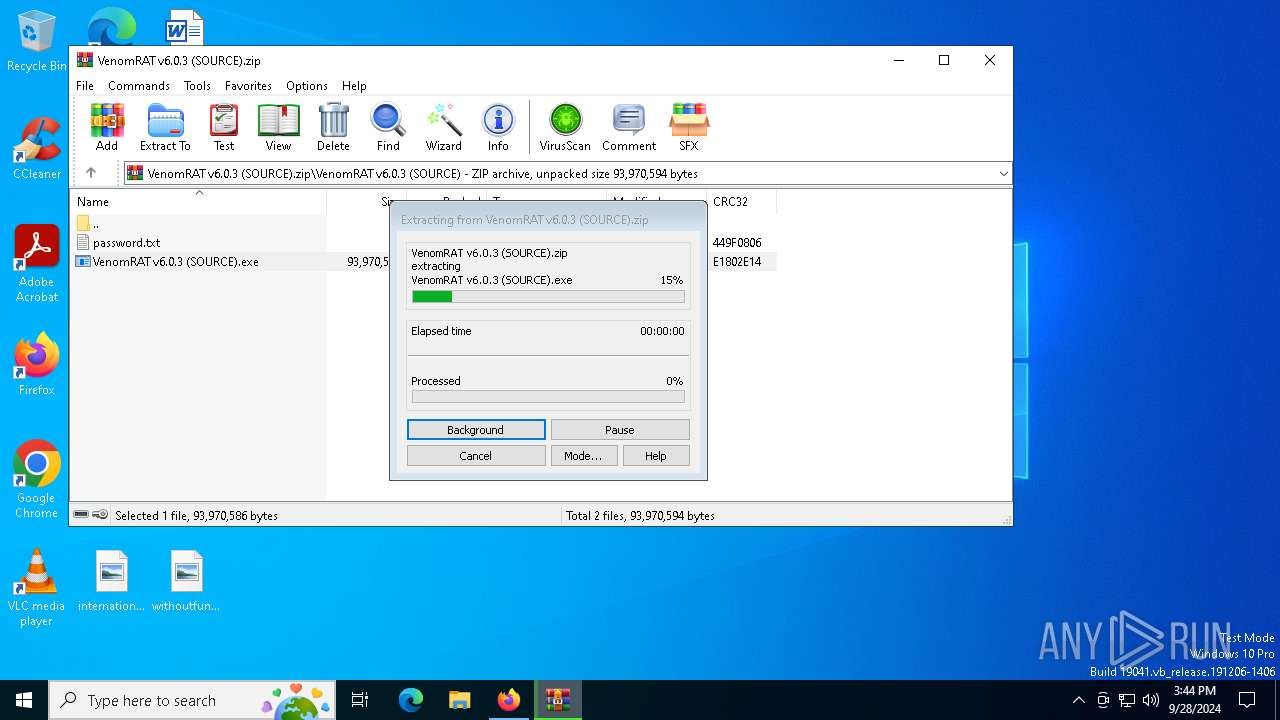
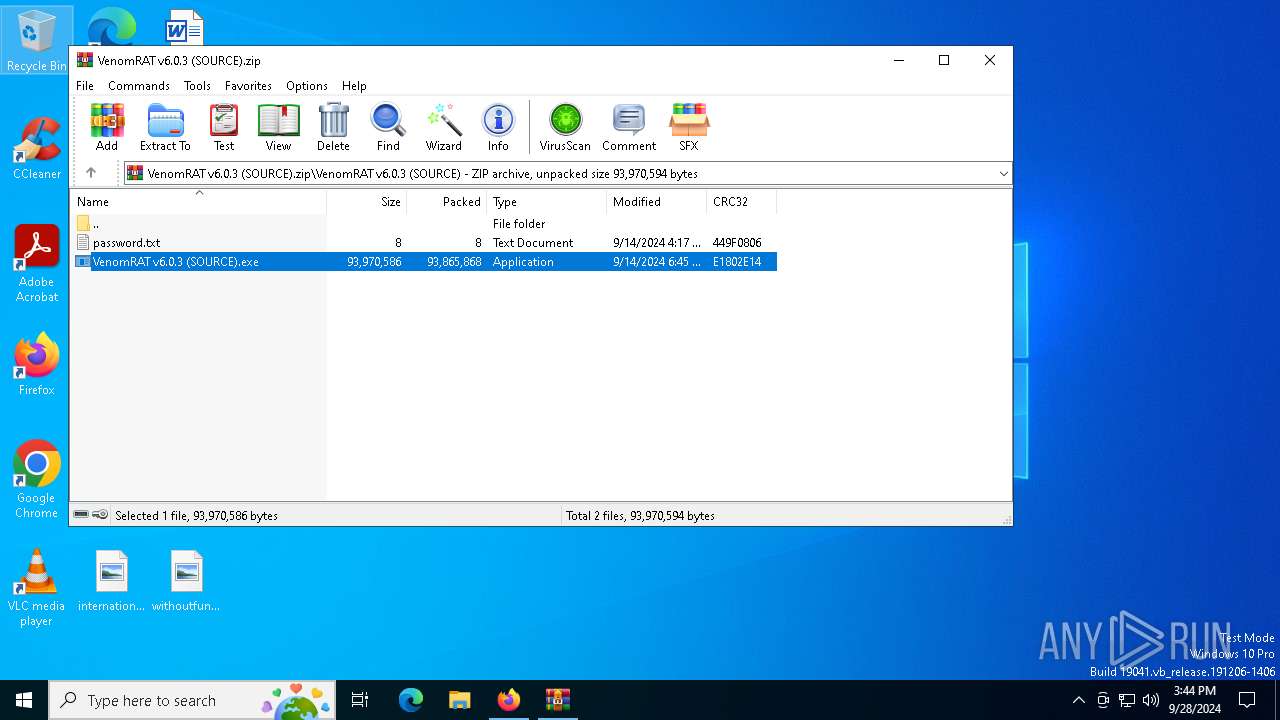
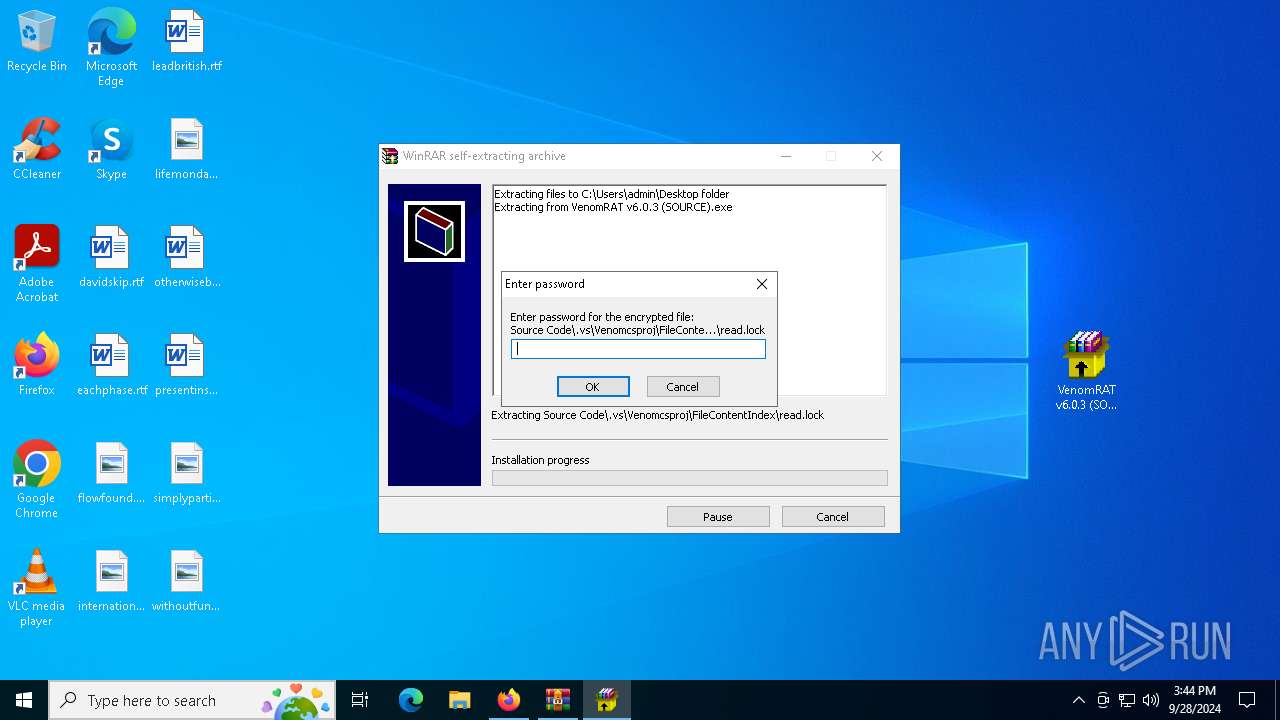
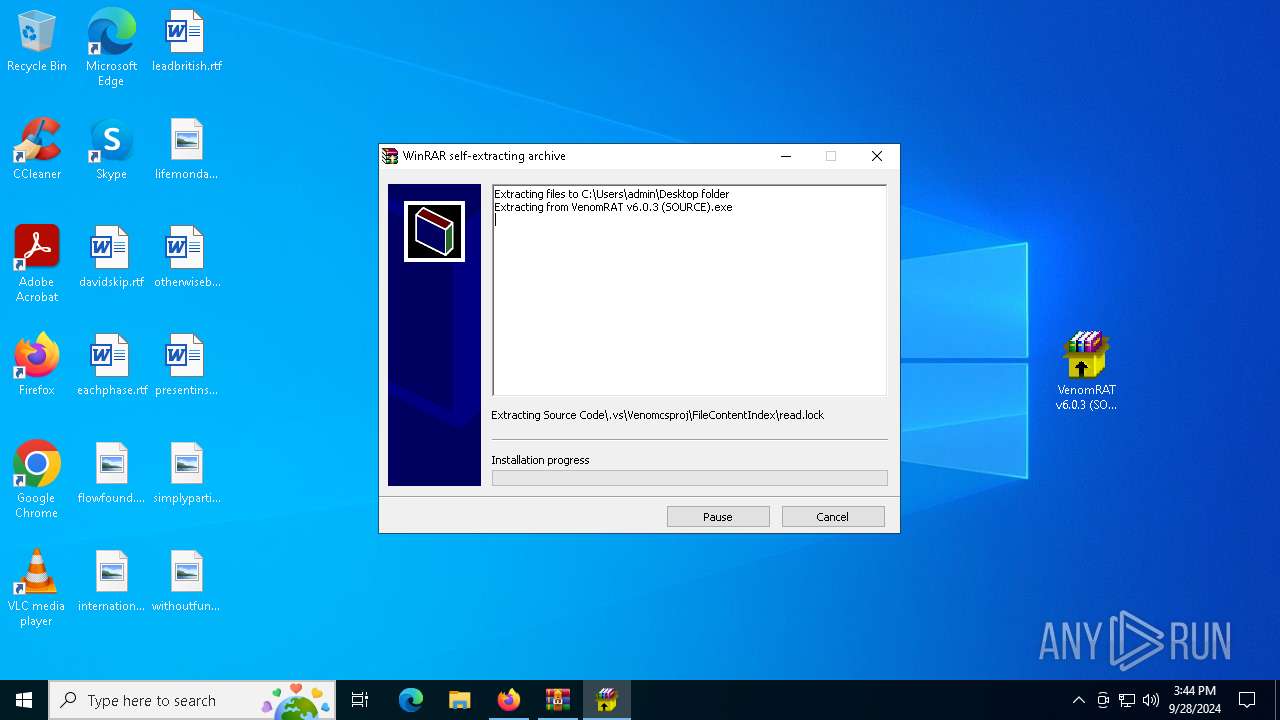
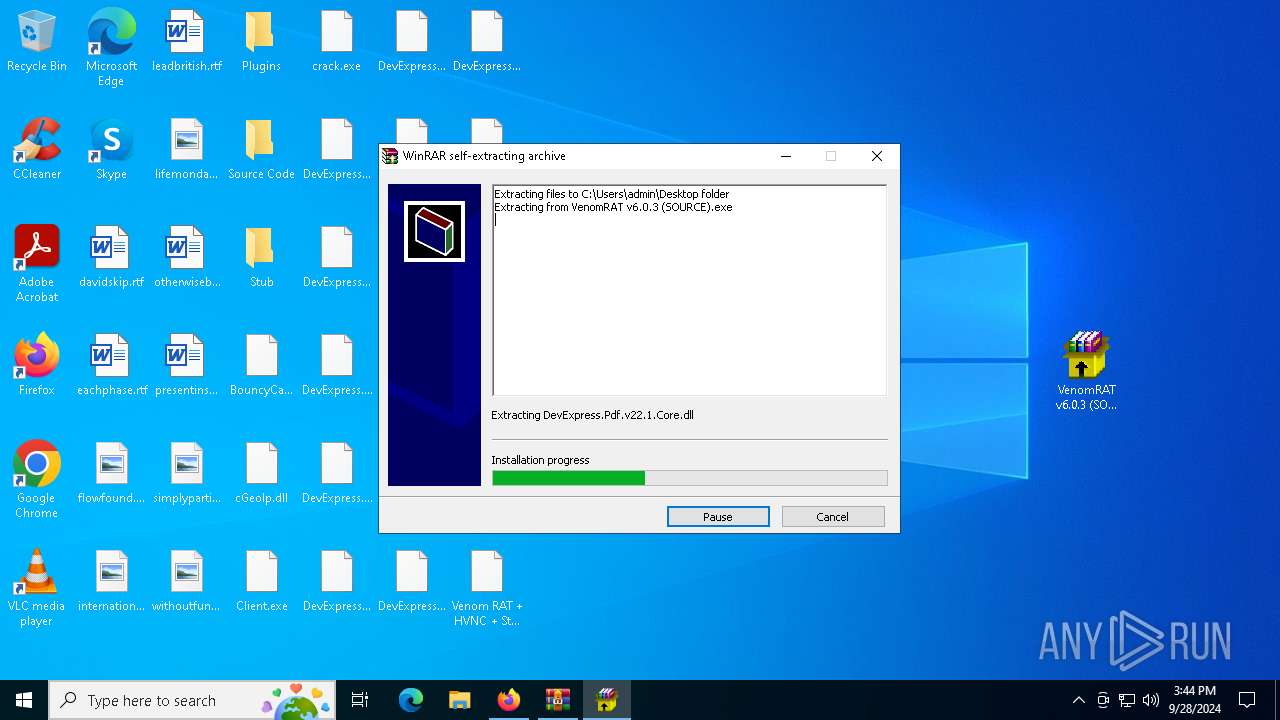
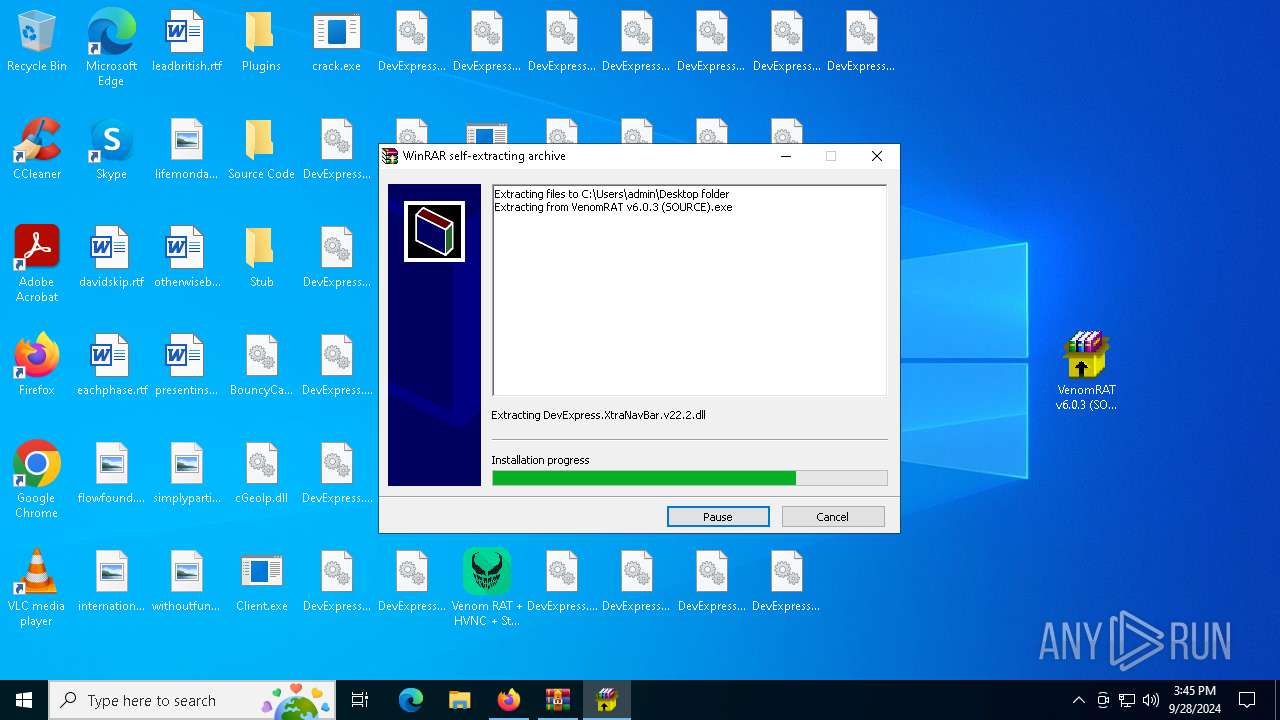
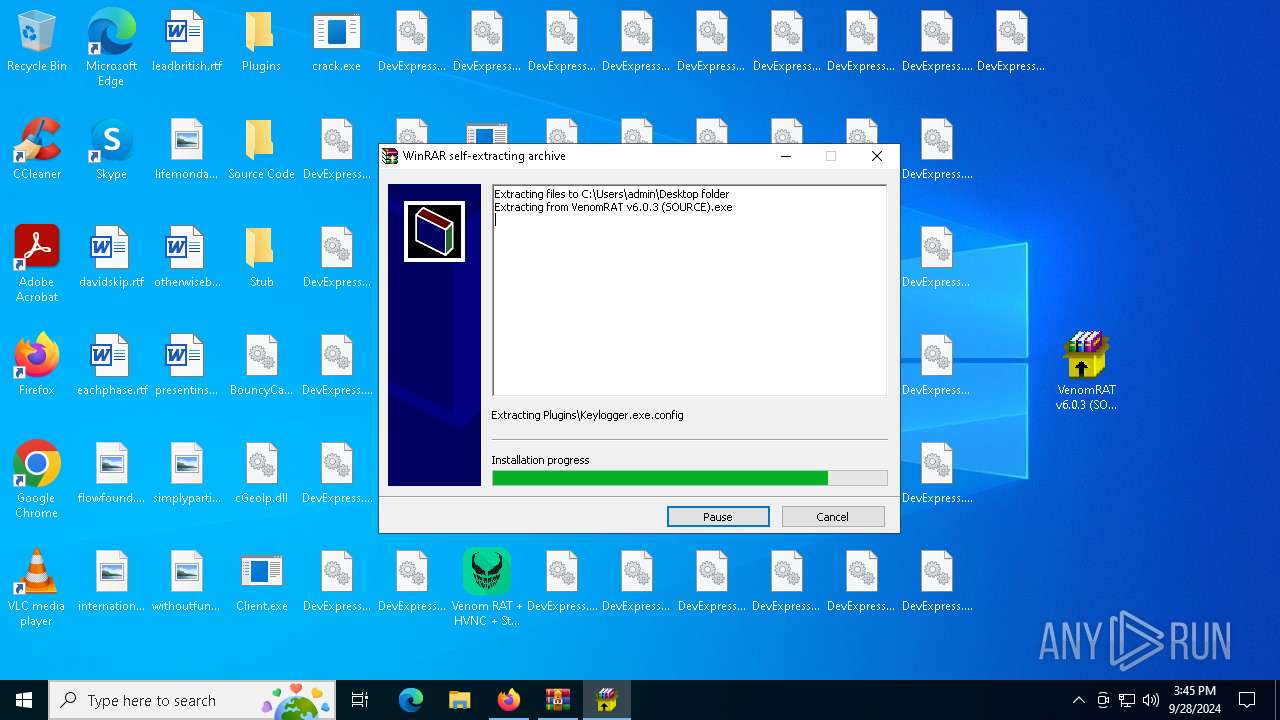
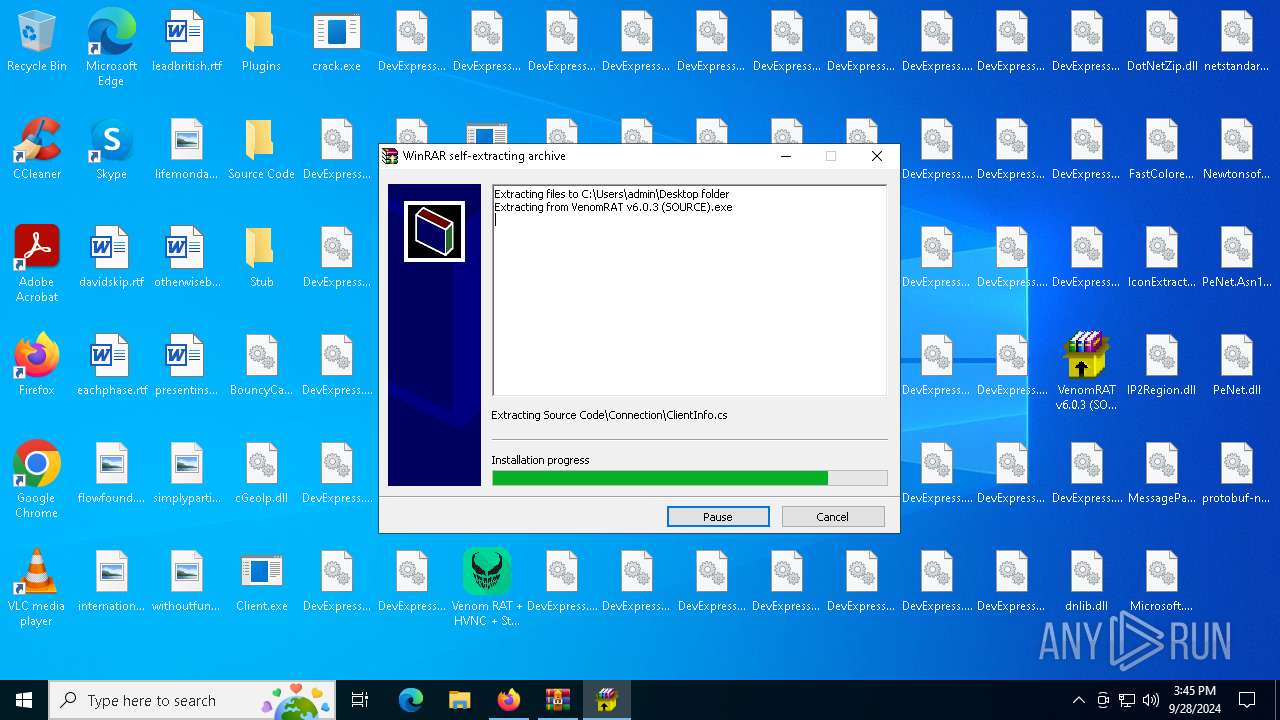
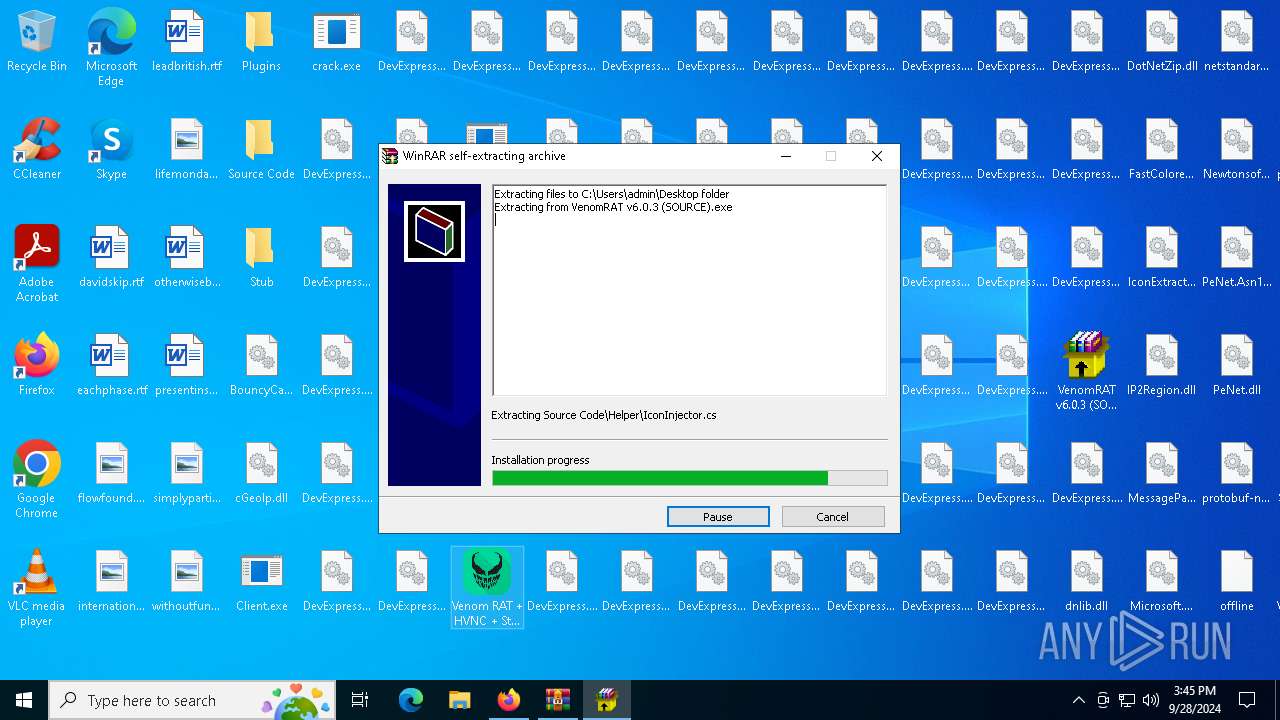
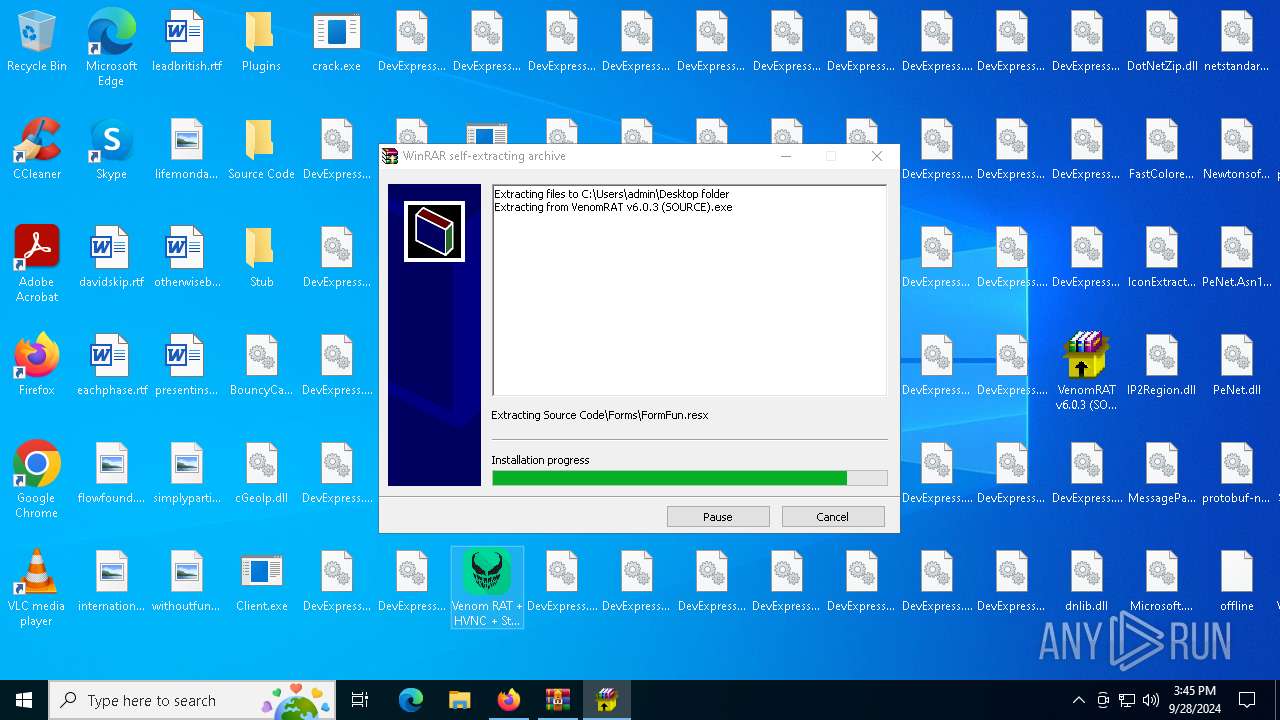
- VenomRAT v6.0.3 (SOURCE).exe (PID: 652)
- crack.exe (PID: 2776)
- svchost.exe (PID: 7924)
- svchost.exe (PID: 7424)
- svchost.exe (PID: 7436)
- csc.exe (PID: 8680)
- crack.exe (PID: 6204)
Starts a Microsoft application from unusual location
- svchost.exe (PID: 7924)
- svchost.exe (PID: 7456)
- svchost.exe (PID: 7424)
- svchost.exe (PID: 7436)
Process drops python dynamic module
- crack.exe (PID: 2776)
- svchost.exe (PID: 7924)
- svchost.exe (PID: 7424)
Process drops legitimate windows executable
- svchost.exe (PID: 7924)
- svchost.exe (PID: 7424)
- crack.exe (PID: 2776)
- VenomRAT v6.0.3 (SOURCE).exe (PID: 652)
The process drops C-runtime libraries
- svchost.exe (PID: 7924)
- svchost.exe (PID: 7424)
- crack.exe (PID: 2776)
Application launched itself
- svchost.exe (PID: 7924)
- svchost.exe (PID: 7456)
- svchost.exe (PID: 7424)
- crack.exe (PID: 2776)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 7436)
Found strings related to reading or modifying Windows Defender settings
- svchost.exe (PID: 7436)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7212)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 7132)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 9176)
- cmd.exe (PID: 6484)
- cmd.exe (PID: 8760)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7212)
Script disables Windows Defender's IPS
- cmd.exe (PID: 7212)
Get information on the list of running processes
- svchost.exe (PID: 7436)
- cmd.exe (PID: 3144)
- cmd.exe (PID: 1920)
- cmd.exe (PID: 5632)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6392)
- cmd.exe (PID: 9164)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7208)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 6296)
Starts application with an unusual extension
- cmd.exe (PID: 7236)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 9008)
- cmd.exe (PID: 8864)
- cmd.exe (PID: 8552)
- cmd.exe (PID: 9132)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7132)
Base64-obfuscated command line is found
- cmd.exe (PID: 7132)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 7132)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 6516)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8680)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 8740)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2624)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8432)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 5372)
Checks for external IP
- svchost.exe (PID: 2256)
- svchost.exe (PID: 7436)
- crack.exe (PID: 6204)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 7436)
Possible usage of Discord/Telegram API has been detected (YARA)
- svchost.exe (PID: 7436)
- Venom RAT + HVNC + Stealer + Grabber.exe (PID: 7748)
There is functionality for taking screenshot (YARA)
- Venom RAT + HVNC + Stealer + Grabber.exe (PID: 7748)
INFO
Executable content was dropped or overwritten
- firefox.exe (PID: 6292)
Application launched itself
- firefox.exe (PID: 6348)
- firefox.exe (PID: 6292)
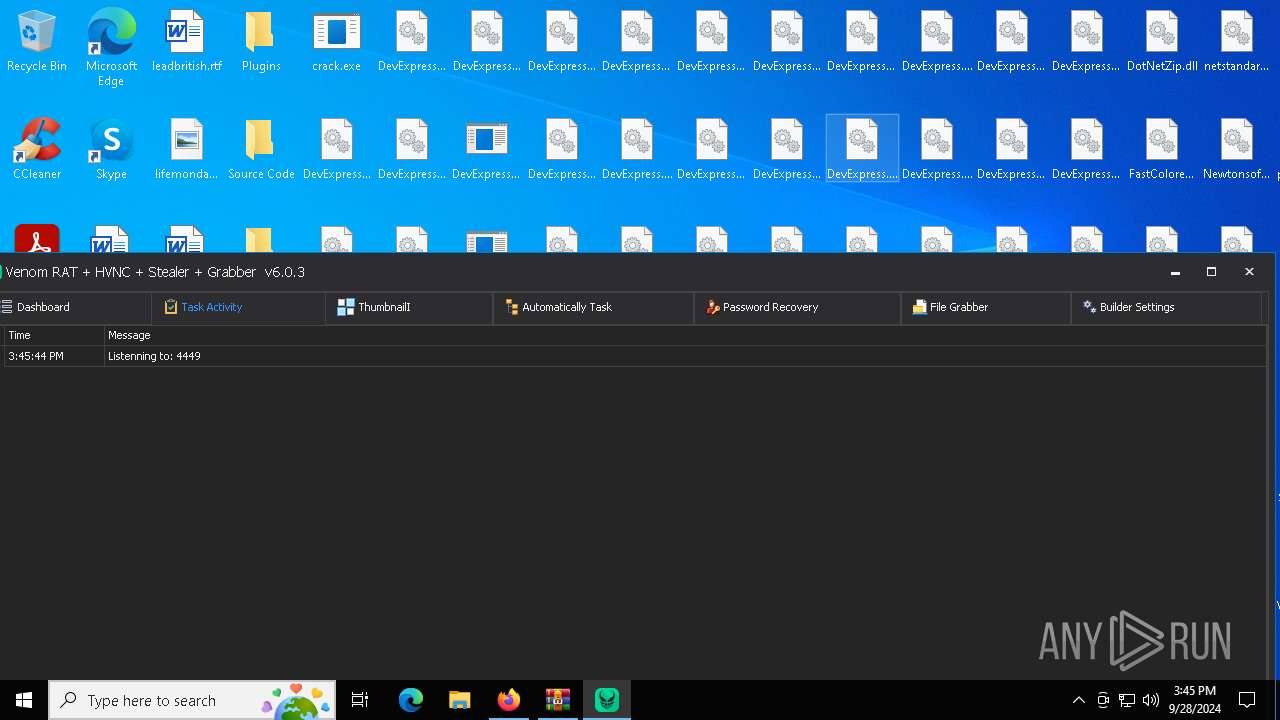
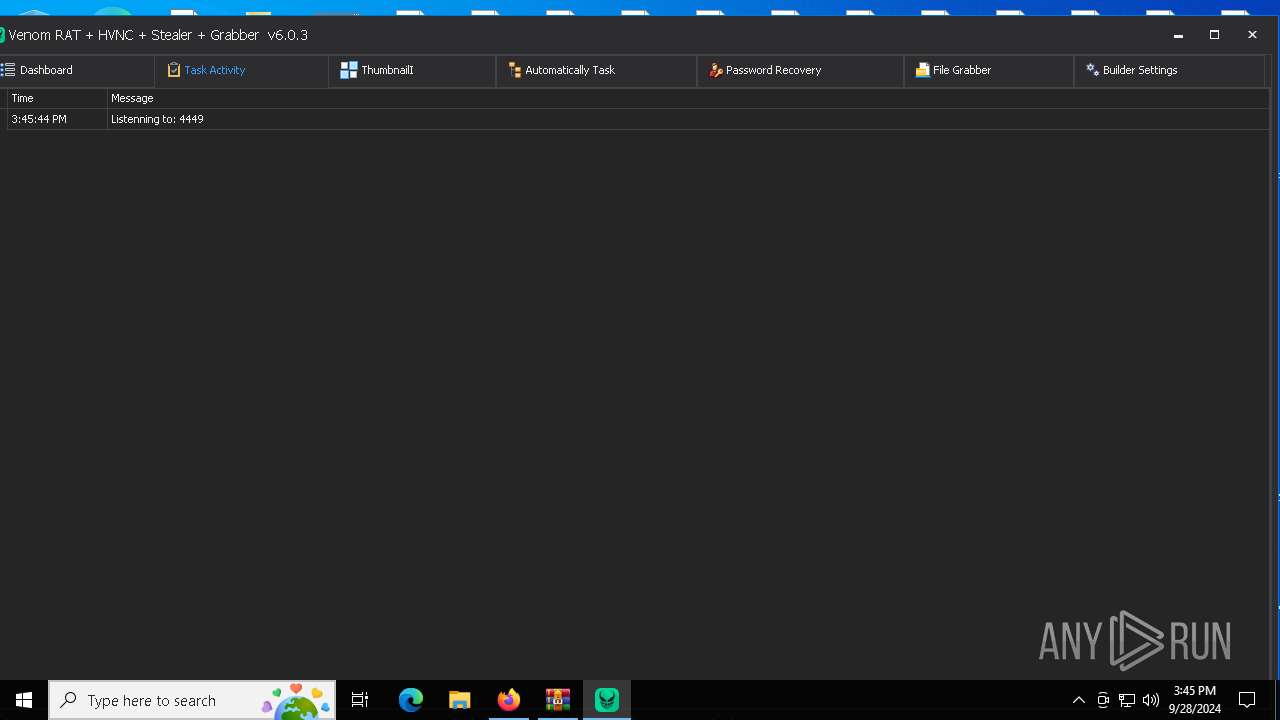
Manual execution by a user
- Venom RAT + HVNC + Stealer + Grabber.exe (PID: 7748)
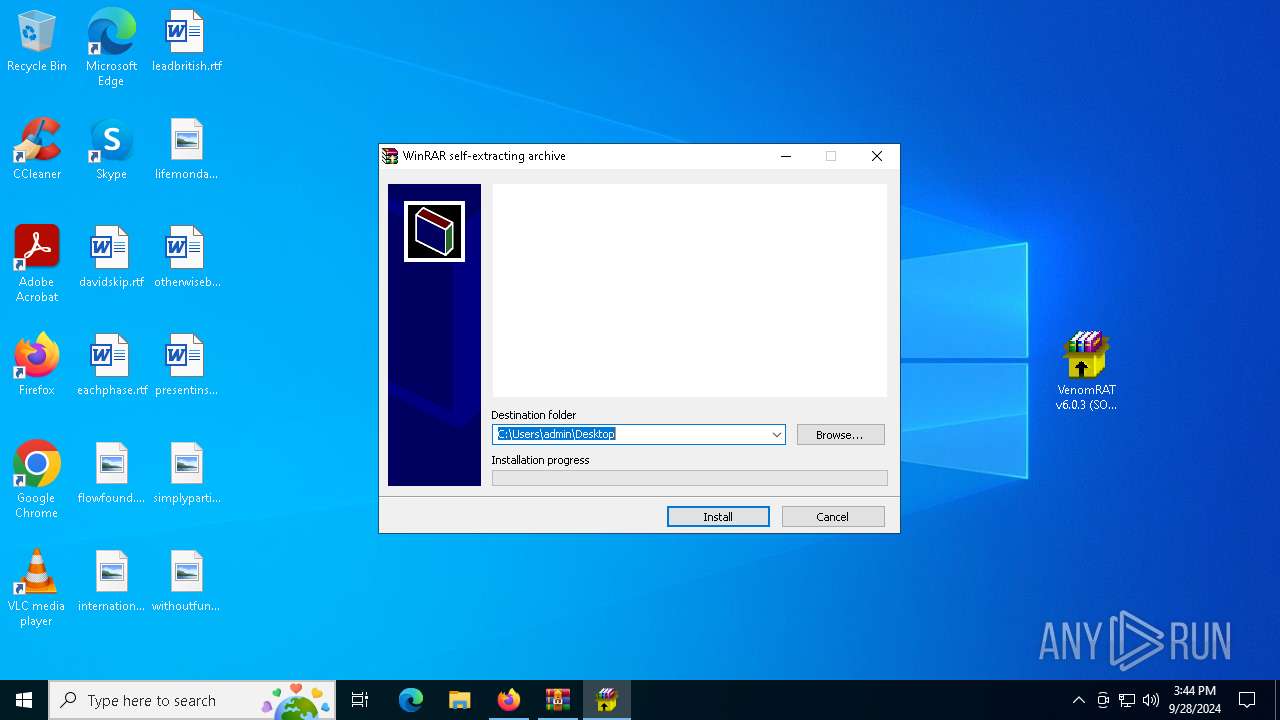
- WinRAR.exe (PID: 7052)
- VenomRAT v6.0.3 (SOURCE).exe (PID: 652)
The Powershell gets current clipboard
- powershell.exe (PID: 7712)
PyInstaller has been detected (YARA)
- crack.exe (PID: 2776)
- svchost.exe (PID: 7424)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 8224)
Found Base64 encoded reflection usage via PowerShell (YARA)
- svchost.exe (PID: 7436)
Attempting to use instant messaging service
- svchost.exe (PID: 2256)
- svchost.exe (PID: 7436)
Themida protector has been detected
- Venom RAT + HVNC + Stealer + Grabber.exe (PID: 7748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(7436) svchost.exe
Telegram-Tokens (1)7205168127:AAESPODoEWHkzAnT03lUQzuuqc_IjL7Fq7s
Telegram-Info-Links
7205168127:AAESPODoEWHkzAnT03lUQzuuqc_IjL7Fq7s
Get info about bothttps://api.telegram.org/bot7205168127:AAESPODoEWHkzAnT03lUQzuuqc_IjL7Fq7s/getMe
Get incoming updateshttps://api.telegram.org/bot7205168127:AAESPODoEWHkzAnT03lUQzuuqc_IjL7Fq7s/getUpdates
Get webhookhttps://api.telegram.org/bot7205168127:AAESPODoEWHkzAnT03lUQzuuqc_IjL7Fq7s/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7205168127:AAESPODoEWHkzAnT03lUQzuuqc_IjL7Fq7s/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7205168127:AAESPODoEWHkzAnT03lUQzuuqc_IjL7Fq7s/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7205168127:AAESPODoEWHkzAnT03lUQzuuqc_IjL7Fq7s
End-PointsendDocument
Args
(PID) Process(7748) Venom RAT + HVNC + Stealer + Grabber.exe
Telegram-Tokens (1)5819716395:AAEP-yuJ_QA22yswxx2C-lVY5yPkxnaxFMQ
Telegram-Info-Links
5819716395:AAEP-yuJ_QA22yswxx2C-lVY5yPkxnaxFMQ
Get info about bothttps://api.telegram.org/bot5819716395:AAEP-yuJ_QA22yswxx2C-lVY5yPkxnaxFMQ/getMe
Get incoming updateshttps://api.telegram.org/bot5819716395:AAEP-yuJ_QA22yswxx2C-lVY5yPkxnaxFMQ/getUpdates
Get webhookhttps://api.telegram.org/bot5819716395:AAEP-yuJ_QA22yswxx2C-lVY5yPkxnaxFMQ/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot5819716395:AAEP-yuJ_QA22yswxx2C-lVY5yPkxnaxFMQ/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot5819716395:AAEP-yuJ_QA22yswxx2C-lVY5yPkxnaxFMQ/deleteWebhook?drop_pending_updates=true
Discord-Webhook-Tokens (1)1016614786533969920/fMJOOjA1pZqjV8_s0JC86KN9Fa0FeGPEHaEak8WTADC18s5Xnk3vl2YBdVD37L0qTWnM
Discord-Info-Links
1016614786533969920/fMJOOjA1pZqjV8_s0JC86KN9Fa0FeGPEHaEak8WTADC18s5Xnk3vl2YBdVD37L0qTWnM
Get Webhook Infohttps://discord.com/api/webhooks/1016614786533969920/fMJOOjA1pZqjV8_s0JC86KN9Fa0FeGPEHaEak8WTADC18s5Xnk3vl2YBdVD37L0qTWnM
Total processes
255
Monitored processes
117
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | tree /A /F | C:\Windows\System32\tree.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Tree Walk Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 652 | "C:\Users\admin\Desktop\VenomRAT v6.0.3 (SOURCE).exe" | C:\Users\admin\Desktop\VenomRAT v6.0.3 (SOURCE).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 652 | powershell Get-ItemPropertyValue -Path HKLM:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | powershell Get-ItemPropertyValue -Path 'HKLM:System\CurrentControlSet\Control\Session Manager\Environment' -Name PROCESSOR_IDENTIFIER | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2888 -childID 1 -isForBrowser -prefsHandle 2880 -prefMapHandle 2876 -prefsLen 26706 -prefMapSize 244343 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {076256c1-4303-4382-86e3-355b3135858d} 6292 "\\.\pipe\gecko-crash-server-pipe.6292" 1ce42972150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1072 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7848 -childID 15 -isForBrowser -prefsHandle 5180 -prefMapHandle 7088 -prefsLen 32132 -prefMapSize 244343 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {fb1e1532-699a-44dc-9cf9-aaa8454b50b0} 6292 "\\.\pipe\gecko-crash-server-pipe.6292" 1ce48469f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5304 -childID 4 -isForBrowser -prefsHandle 5352 -prefMapHandle 5348 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f8b736ea-0e65-409b-9637-010a5c310876} 6292 "\\.\pipe\gecko-crash-server-pipe.6292" 1ce45d8ad90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=8560 -childID 16 -isForBrowser -prefsHandle 8516 -prefMapHandle 8100 -prefsLen 32174 -prefMapSize 244343 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e922aeb6-44dc-4644-b58f-25a92eba68b8} 6292 "\\.\pipe\gecko-crash-server-pipe.6292" 1ce502c3690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
84 701
Read events
84 685
Write events
14
Delete events
2
Modification events
| (PID) Process: | (6292) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
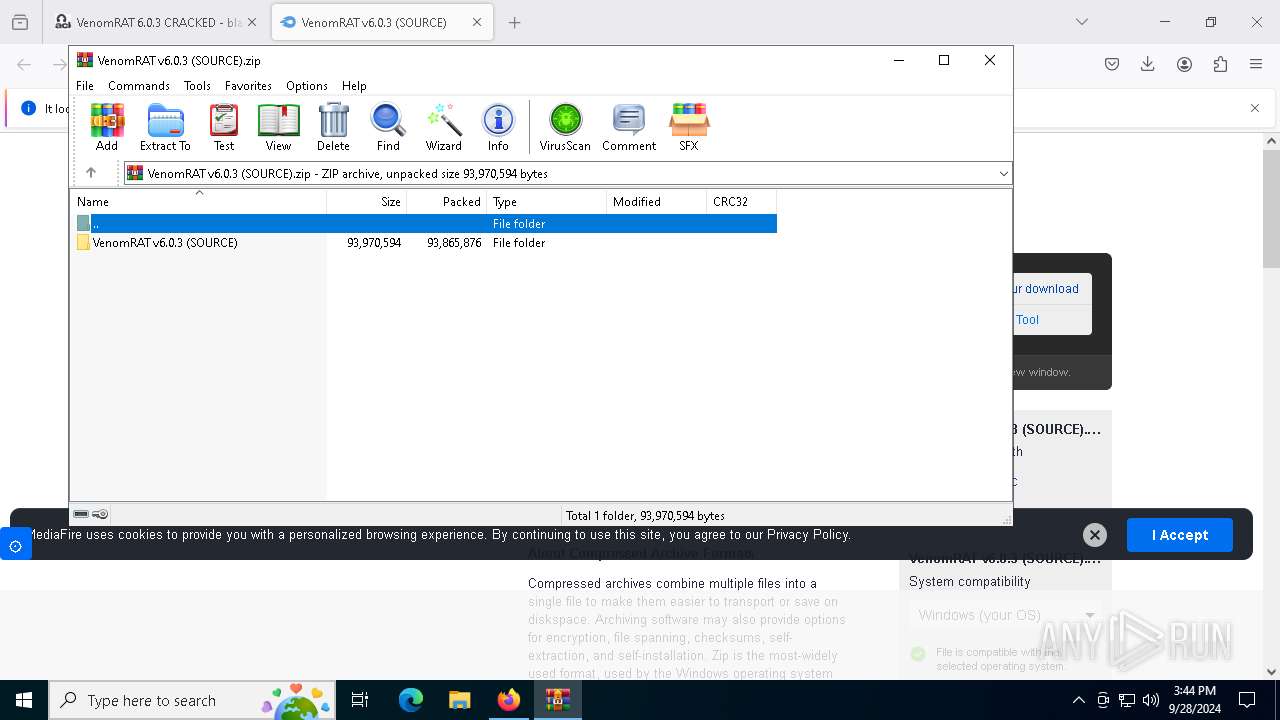
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
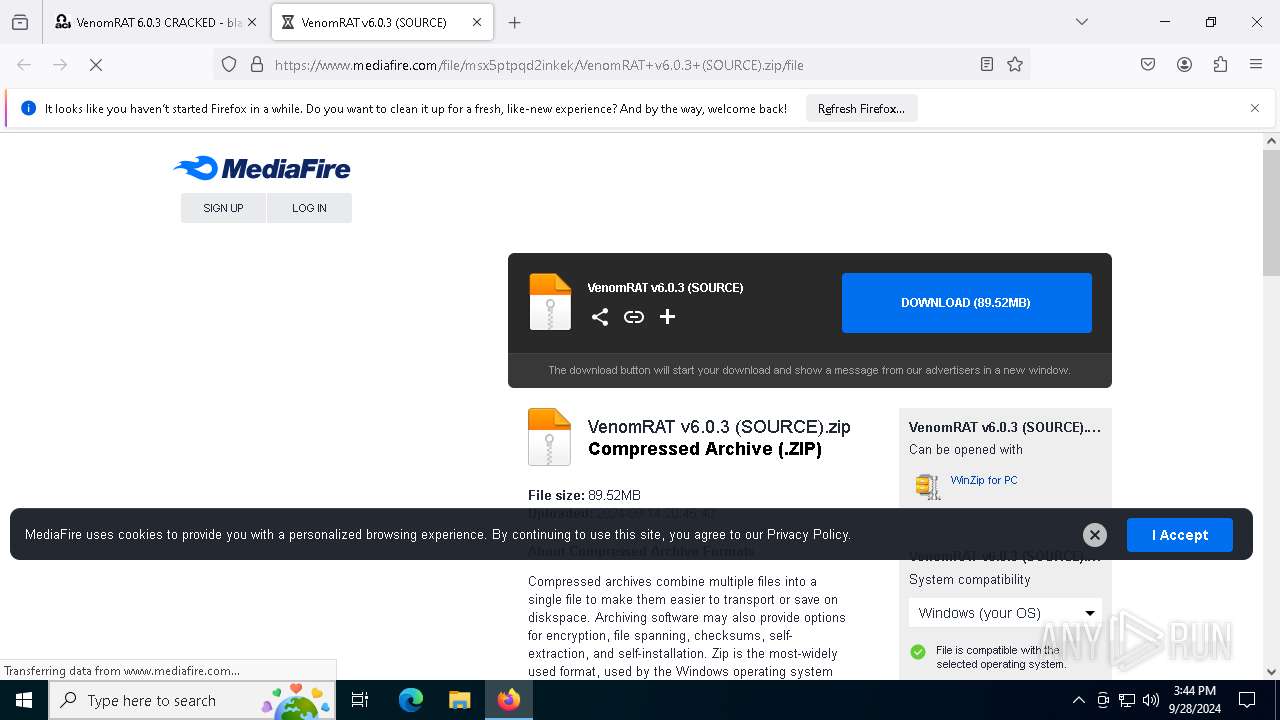
Value: C:\Users\admin\Downloads\VenomRAT v6.0.3 (SOURCE).zip | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (652) VenomRAT v6.0.3 (SOURCE).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (652) VenomRAT v6.0.3 (SOURCE).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (652) VenomRAT v6.0.3 (SOURCE).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
248
Suspicious files
257
Text files
1 171
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:BCCB4706FC3B2DBC581A95F650A02B6E | SHA256:EE052C1B0D7797AF892F3C76A03E61E71B5672FD8DBA76EB5AE7147D7F133F91 | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6292 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:EA2581F2EDABC819876860F3E84B69F1 | SHA256:6AB732B0FDFF2DFF8FCEF846243165A11D045D1ECFF1718C413D431C3B362E9E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
101
TCP/UDP connections
297
DNS requests
382
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6292 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6292 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.137:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/s/wr3/XjA | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.137:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.137:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.137:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6292 | firefox.exe | POST | 200 | 95.101.54.107:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3916 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6292 | firefox.exe | 104.21.78.120:443 | blackhatrussia.com | CLOUDFLARENET | — | malicious |
— | — | 34.117.188.166:443 | contile.services.mozilla.com | — | — | whitelisted |
— | — | 216.58.206.42:443 | safebrowsing.googleapis.com | — | — | whitelisted |
6292 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
blackhatrussia.com |
| malicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2256 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |