| File name: | 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe |
| Full analysis: | https://app.any.run/tasks/d423f999-8a07-416a-9c77-5d821eb8deb7 |
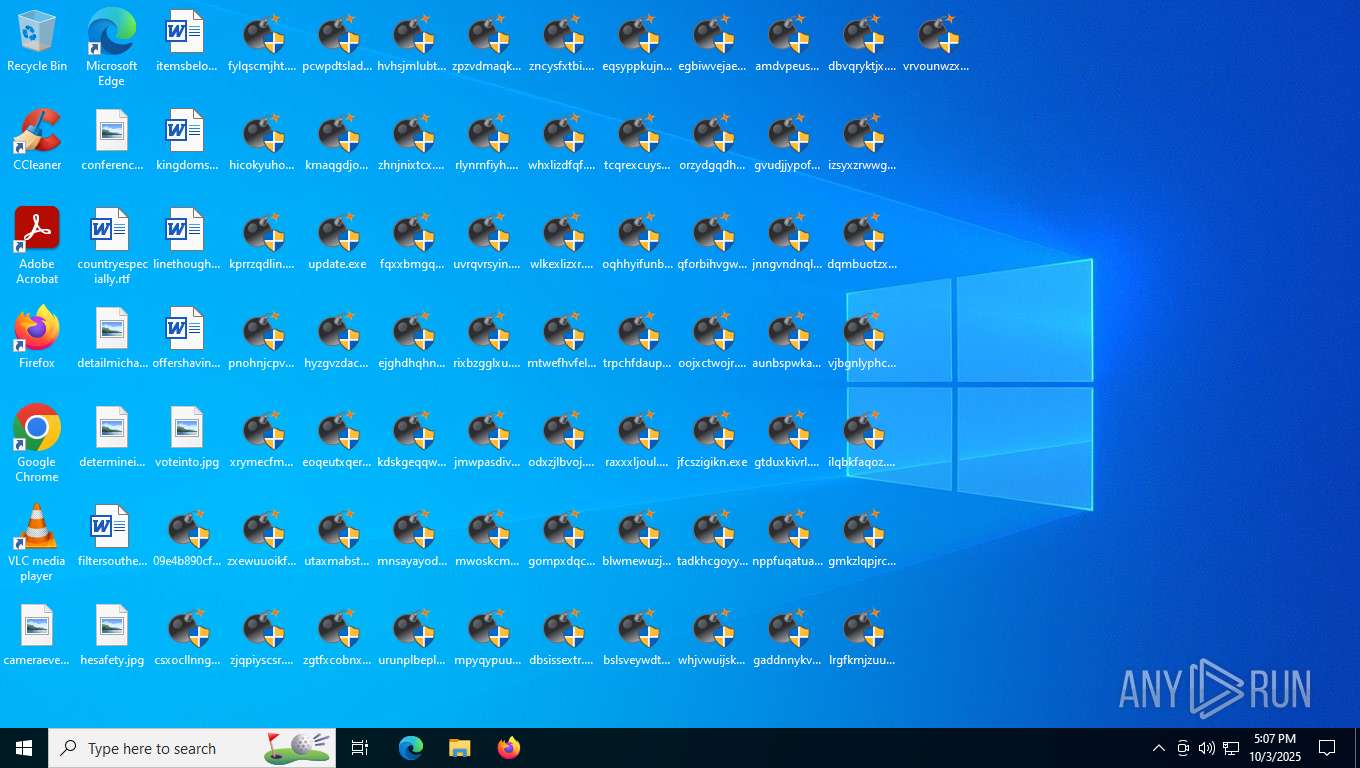
| Verdict: | Malicious activity |
| Threats: | BlackMoon also known as KrBanker is a trojan aimed at stealing payment credentials. It specializes in man-in-the-browser (MitB) attacks, web injection, and credential theft to compromise users' online banking accounts. It was first noticed in early 2014 attacking banks in South Korea and has impressively evolved since by adding a number of new infiltration techniques and information stealing methods. |
| Analysis date: | October 03, 2025, 17:06:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 127CDE97AD48B7EFEA0CE62EE1469964 |
| SHA1: | 325D7459D91CD2C1AA9361F73F1A6EB8CABBE4C7 |
| SHA256: | 09E4B890CFB48BD51937754512D22B96976A965965505B822E156697E5768AAF |
| SSDEEP: | 98304:vKOlBcIt0ML1CXN0RqfaSfS25QBWO7thGjLK/cVYRrs47iZEcF2W7rxLyDzsRncL:PoxjraHx |
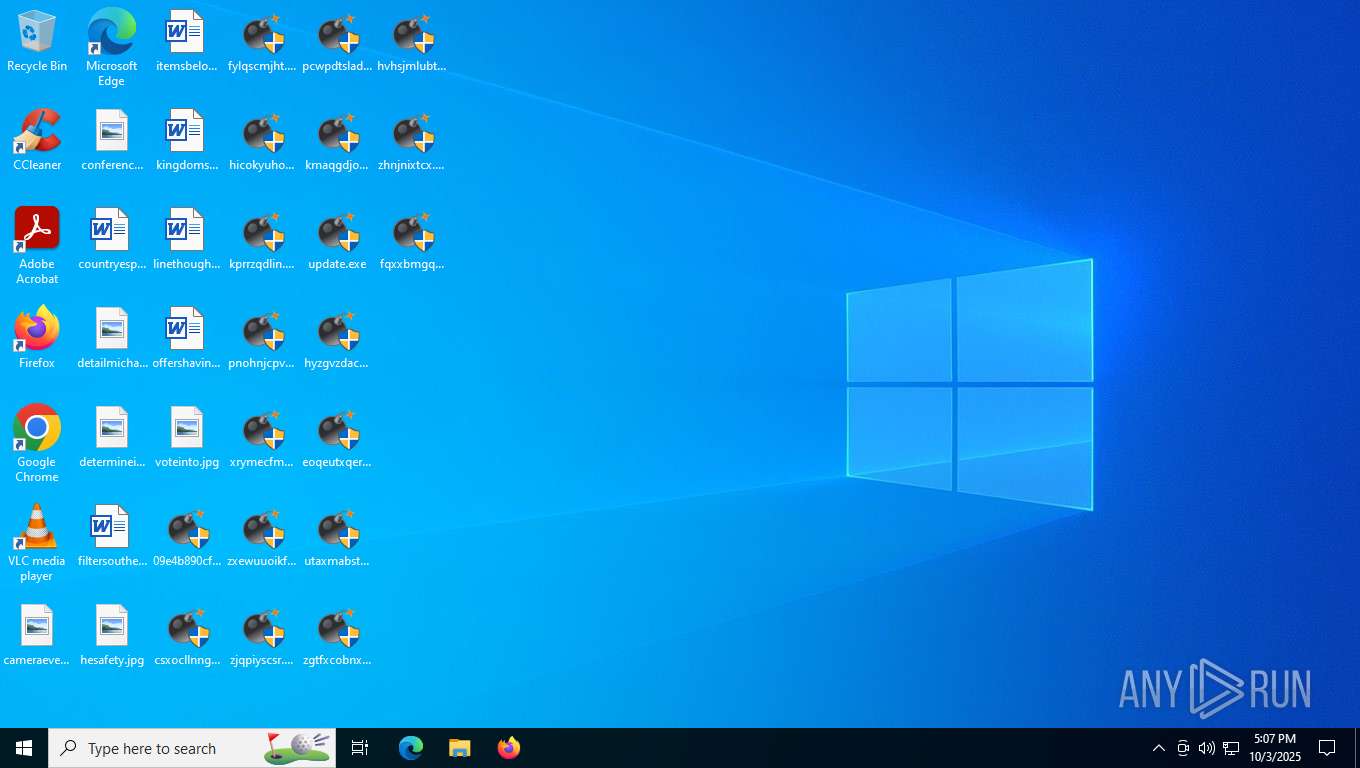
MALICIOUS
BLACKMOON has been detected (YARA)
- kmaqgdjokj.exe (PID: 7548)
- hqfbkvudsj.exe (PID: 8100)
SUSPICIOUS
Application launched itself
- csxocllnng.exe (PID: 8084)
- fylqscmjht.exe (PID: 2176)
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 1600)
- pnohnjcpvo.exe (PID: 8180)
- kprrzqdlin.exe (PID: 7244)
- hicokyuhob.exe (PID: 5708)
- zxewuuoikf.exe (PID: 8164)
- xrymecfmql.exe (PID: 4452)
- zjqpiyscsr.exe (PID: 3432)
- pcwpdtslad.exe (PID: 7416)
- eoqeutxqer.exe (PID: 7956)
- kmaqgdjokj.exe (PID: 7548)
- hyzgvzdacw.exe (PID: 4608)
- utaxmabstw.exe (PID: 560)
- zgtfxcobnx.exe (PID: 2600)
- fqxxbmgqhi.exe (PID: 2504)
- ejghdhqhnb.exe (PID: 2720)
- hvhsjmlubt.exe (PID: 8032)
- zhnjnixtcx.exe (PID: 7728)
- kdskgeqqwp.exe (PID: 2572)
- mnsayayodo.exe (PID: 5340)
- urunplbepl.exe (PID: 8116)
- zpzvdmaqku.exe (PID: 6752)
- uvrqvrsyin.exe (PID: 7360)
- rlynrnfiyh.exe (PID: 1320)
- rixbzgglxu.exe (PID: 4488)
- mwoskcmmxo.exe (PID: 2400)
- jmwpasdivy.exe (PID: 1924)
- zncysfxtbi.exe (PID: 7220)
- mpyqypuugx.exe (PID: 6156)
- whxlizdfqf.exe (PID: 2756)
- wlkexlizxr.exe (PID: 2360)
- mtwefhvfel.exe (PID: 2328)
- odxzjlbvoj.exe (PID: 8144)
- dbsissextr.exe (PID: 2876)
- gompxdqcvc.exe (PID: 6196)
- eqsyppkujn.exe (PID: 2188)
- tcqrexcuys.exe (PID: 6340)
- oqhhyifunb.exe (PID: 2172)
- trpchfdaup.exe (PID: 2080)
- raxxxljoul.exe (PID: 3056)
- blwmewuzju.exe (PID: 5292)
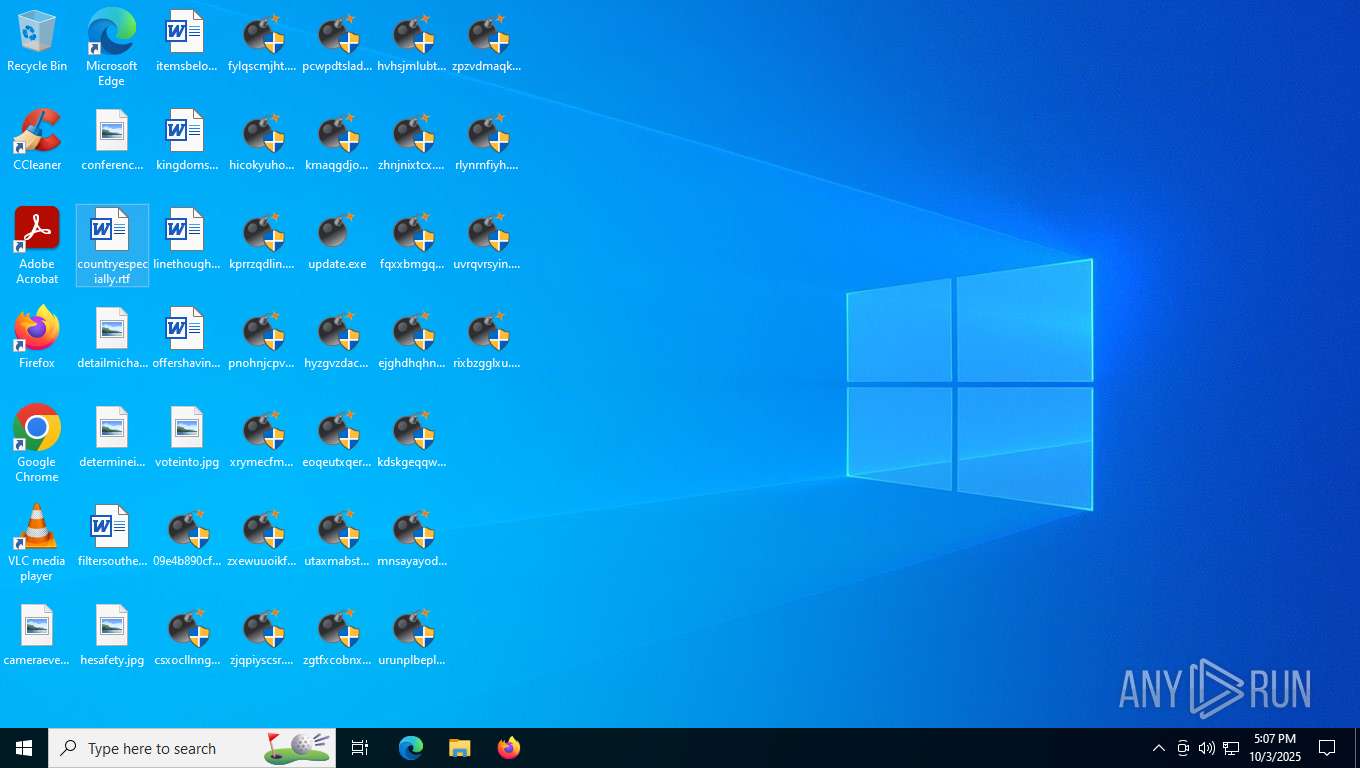
- bslsveywdt.exe (PID: 2856)
- egbiwvejae.exe (PID: 1432)
- orzydgqdhv.exe (PID: 5368)
- qforbihvgw.exe (PID: 2268)
- oojxctwojr.exe (PID: 2812)
- jfcszigikn.exe (PID: 7608)
- tadkhcgoyy.exe (PID: 3260)
- whjvwuijsk.exe (PID: 4584)
- gvudjjypof.exe (PID: 7956)
- amdvpeusmt.exe (PID: 5580)
- jnngvndnql.exe (PID: 1212)
- aunbspwkau.exe (PID: 2532)
- gtduxkivrl.exe (PID: 7068)
- nppfuqatua.exe (PID: 7792)
- gaddnnykva.exe (PID: 5440)
- dbvqryktjx.exe (PID: 2868)
- izsyxzrwwg.exe (PID: 6956)
- dqmbuotzxu.exe (PID: 8144)
- vjbgnlyphc.exe (PID: 2108)
- gmkzlqpjrc.exe (PID: 6868)
- ilqbkfaqoz.exe (PID: 7656)
- lrgfkmjzuu.exe (PID: 1740)
- vrvounwzxb.exe (PID: 2080)
- ngewcpuoup.exe (PID: 7416)
- aiaoihjpzf.exe (PID: 3056)
- lpowynuywa.exe (PID: 2672)
- fgqzncdaxw.exe (PID: 7084)
- lexngykmbg.exe (PID: 5372)
- ycisjlittj.exe (PID: 8016)
- icfsteusxx.exe (PID: 8088)
- snfjcegjph.exe (PID: 2268)
- yofqtukkgt.exe (PID: 1516)
- anfpcsiwsp.exe (PID: 7788)
- skfhycmpgc.exe (PID: 7472)
- nivcbzbogz.exe (PID: 4584)
- qokscracdj.exe (PID: 2884)
- viucigxcoi.exe (PID: 5232)
- cfevrgjeeg.exe (PID: 6416)
- soztejubgy.exe (PID: 2492)
- czaoqpodwr.exe (PID: 3000)
- njbxuzdgbg.exe (PID: 708)
- pirxplllek.exe (PID: 2028)
- pmeigbzvzh.exe (PID: 1380)
- keylvyjyad.exe (PID: 4108)
- caywraojoq.exe (PID: 7404)
- vlmbkfmhqy.exe (PID: 576)
- fzzhlgjvvl.exe (PID: 2816)
- zypigsazyh.exe (PID: 4960)
- hqfbkvudsj.exe (PID: 8100)
- psxgpipqhl.exe (PID: 7024)
- cuebmurspj.exe (PID: 1476)
- zgawcoxedg.exe (PID: 6292)
- sgmzncgjgn.exe (PID: 2176)
- pljbiomhzn.exe (PID: 1604)
- cuocxrzfaj.exe (PID: 1924)
- rzxpvjgivq.exe (PID: 7372)
- euzlwjcrpo.exe (PID: 3000)
- xipvivhfsi.exe (PID: 7220)
- eczuuiwbve.exe (PID: 6720)
- eukowlprtw.exe (PID: 708)
- bdsmjtncda.exe (PID: 532)
- uzsxfusvrv.exe (PID: 5404)
- mosqbwxfmq.exe (PID: 4016)
- jlavgkhmiz.exe (PID: 2996)
- hbagoozgbr.exe (PID: 6772)
- ueryyvrpsh.exe (PID: 7084)
- elocfqwuye.exe (PID: 7440)
- onvzbwiaun.exe (PID: 7032)
- hrdsgichmx.exe (PID: 6292)
- rfgabxtnjs.exe (PID: 6480)
- jruldodcef.exe (PID: 2832)
- jvgegzdsla.exe (PID: 560)
- bjgouiikhv.exe (PID: 2896)
- zwmnkfbpri.exe (PID: 6124)
- tjjutotxid.exe (PID: 2400)
- efgtzeuccn.exe (PID: 7196)
- bkdevtipzu.exe (PID: 2652)
- gxipnxzywl.exe (PID: 2480)
- yeisetohqr.exe (PID: 4960)
- wgoyrdxvcl.exe (PID: 7068)
- jezcurobuo.exe (PID: 2900)
- itvlxjniyf.exe (PID: 2156)
- lkmdvekdws.exe (PID: 5580)
- bftbkadpgy.exe (PID: 7736)
- dayxkinzxp.exe (PID: 2868)
- qreckkxgbk.exe (PID: 7788)
- letiqyvmxl.exe (PID: 2876)
- vadylndrtg.exe (PID: 8164)
- jnotcqhwce.exe (PID: 7672)
- neerqyggmi.exe (PID: 1020)
- omuukeryey.exe (PID: 5696)
- ypuhwbkstr.exe (PID: 3000)
- gibvdepsxj.exe (PID: 7360)
- dyktkxkhge.exe (PID: 5040)
- nrcocittiu.exe (PID: 2400)
- xucchfmvyn.exe (PID: 2288)
- nvifhdnajp.exe (PID: 1924)
- pxaauxccoh.exe (PID: 7908)
- ffwlailrtx.exe (PID: 2480)
- fjjojzzbou.exe (PID: 7068)
- dadbqfedcd.exe (PID: 5196)
- lxqsykutai.exe (PID: 6724)
- pdtxevsxel.exe (PID: 2156)
- cxkqobjgua.exe (PID: 3124)
- utyyljbzff.exe (PID: 6480)
- cmhwfkmvoz.exe (PID: 7740)
- cmibrrkujx.exe (PID: 8044)
- sogbmnsdrj.exe (PID: 4744)
- xtchtjmuuc.exe (PID: 708)
- sdsqzunocw.exe (PID: 2316)
- sdfaosdxwi.exe (PID: 7160)
- pywfoaybce.exe (PID: 4732)
- xxtbpyltyn.exe (PID: 4488)
- atychuwqkn.exe (PID: 7244)
- prrgtpskoe.exe (PID: 1020)
- enpqsmmnyu.exe (PID: 8116)
- pneqbfgmjb.exe (PID: 7084)
- pnoopaovkl.exe (PID: 6416)
- sfixedzcop.exe (PID: 3084)
- hkyfzgqkle.exe (PID: 5040)
- rzktpvrurt.exe (PID: 8180)
- cmgowgbywk.exe (PID: 2400)
- phwhwtwvnk.exe (PID: 7908)
- kkkczucsvr.exe (PID: 2980)
- mbrumwdich.exe (PID: 2436)
- zhlhxurvrq.exe (PID: 7580)
- koysbtwmln.exe (PID: 7460)
- eyclecnxvt.exe (PID: 1692)
- enlbmmdmah.exe (PID: 4228)
- wjmntlijzv.exe (PID: 7248)
- pnacwfqleo.exe (PID: 7396)
- eoxfwdqrpq.exe (PID: 7172)
- bpolhvgvcx.exe (PID: 8164)
- esswfjgpfd.exe (PID: 6196)
Executable content was dropped or overwritten
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 7548)
- fylqscmjht.exe (PID: 532)
- hicokyuhob.exe (PID: 4696)
- csxocllnng.exe (PID: 6780)
- kprrzqdlin.exe (PID: 4260)
- pnohnjcpvo.exe (PID: 5484)
- xrymecfmql.exe (PID: 2288)
- zxewuuoikf.exe (PID: 2188)
- zjqpiyscsr.exe (PID: 3516)
- pcwpdtslad.exe (PID: 4208)
- csxocllnng.exe (PID: 8084)
- hyzgvzdacw.exe (PID: 1924)
- kmaqgdjokj.exe (PID: 6176)
- eoqeutxqer.exe (PID: 332)
- utaxmabstw.exe (PID: 7440)
- hvhsjmlubt.exe (PID: 5424)
- zhnjnixtcx.exe (PID: 1212)
- fqxxbmgqhi.exe (PID: 3000)
- zgtfxcobnx.exe (PID: 2852)
- kdskgeqqwp.exe (PID: 7068)
- ejghdhqhnb.exe (PID: 708)
- mnsayayodo.exe (PID: 2008)
- urunplbepl.exe (PID: 3268)
- zpzvdmaqku.exe (PID: 7776)
- rlynrnfiyh.exe (PID: 2080)
- uvrqvrsyin.exe (PID: 3196)
- rixbzgglxu.exe (PID: 3160)
- mwoskcmmxo.exe (PID: 7556)
- jmwpasdivy.exe (PID: 6660)
- mpyqypuugx.exe (PID: 7608)
- zncysfxtbi.exe (PID: 7012)
- whxlizdfqf.exe (PID: 3552)
- wlkexlizxr.exe (PID: 1020)
- odxzjlbvoj.exe (PID: 4956)
- mtwefhvfel.exe (PID: 6416)
- gompxdqcvc.exe (PID: 7788)
- eqsyppkujn.exe (PID: 2392)
- dbsissextr.exe (PID: 764)
- oqhhyifunb.exe (PID: 5508)
- tcqrexcuys.exe (PID: 1604)
- raxxxljoul.exe (PID: 5196)
- trpchfdaup.exe (PID: 7736)
- blwmewuzju.exe (PID: 8000)
- bslsveywdt.exe (PID: 2164)
- egbiwvejae.exe (PID: 6868)
- orzydgqdhv.exe (PID: 4676)
- qforbihvgw.exe (PID: 7596)
- oojxctwojr.exe (PID: 5868)
- jfcszigikn.exe (PID: 6836)
- whjvwuijsk.exe (PID: 7276)
- tadkhcgoyy.exe (PID: 7012)
- amdvpeusmt.exe (PID: 4364)
- gvudjjypof.exe (PID: 1560)
- jnngvndnql.exe (PID: 2352)
- aunbspwkau.exe (PID: 2792)
- nppfuqatua.exe (PID: 2528)
- gtduxkivrl.exe (PID: 7220)
- gaddnnykva.exe (PID: 4708)
- dbvqryktjx.exe (PID: 2328)
- izsyxzrwwg.exe (PID: 7808)
- vjbgnlyphc.exe (PID: 796)
- dqmbuotzxu.exe (PID: 4432)
- ilqbkfaqoz.exe (PID: 572)
- gmkzlqpjrc.exe (PID: 7552)
- lrgfkmjzuu.exe (PID: 2172)
- aiaoihjpzf.exe (PID: 6184)
- vrvounwzxb.exe (PID: 600)
- lpowynuywa.exe (PID: 8056)
- ngewcpuoup.exe (PID: 7728)
- fgqzncdaxw.exe (PID: 7276)
- ycisjlittj.exe (PID: 5256)
- icfsteusxx.exe (PID: 8168)
- lexngykmbg.exe (PID: 7088)
- yofqtukkgt.exe (PID: 7744)
- anfpcsiwsp.exe (PID: 3708)
- skfhycmpgc.exe (PID: 2864)
- snfjcegjph.exe (PID: 1560)
- nivcbzbogz.exe (PID: 8100)
- viucigxcoi.exe (PID: 5684)
- qokscracdj.exe (PID: 6972)
- cfevrgjeeg.exe (PID: 7992)
- soztejubgy.exe (PID: 4016)
- njbxuzdgbg.exe (PID: 2572)
- czaoqpodwr.exe (PID: 5500)
- pirxplllek.exe (PID: 5552)
- keylvyjyad.exe (PID: 6396)
- pmeigbzvzh.exe (PID: 2176)
- caywraojoq.exe (PID: 7744)
- vlmbkfmhqy.exe (PID: 3552)
- hqfbkvudsj.exe (PID: 8016)
- fzzhlgjvvl.exe (PID: 2328)
- psxgpipqhl.exe (PID: 4016)
- zypigsazyh.exe (PID: 2284)
- zgawcoxedg.exe (PID: 7988)
- cuebmurspj.exe (PID: 2164)
- pljbiomhzn.exe (PID: 2652)
- sgmzncgjgn.exe (PID: 5208)
- cuocxrzfaj.exe (PID: 1764)
- rzxpvjgivq.exe (PID: 2492)
- xipvivhfsi.exe (PID: 7440)
- euzlwjcrpo.exe (PID: 5580)
- eukowlprtw.exe (PID: 7068)
- bdsmjtncda.exe (PID: 560)
- eczuuiwbve.exe (PID: 2832)
- uzsxfusvrv.exe (PID: 6924)
- mosqbwxfmq.exe (PID: 2652)
- hbagoozgbr.exe (PID: 7744)
- ueryyvrpsh.exe (PID: 2492)
- jlavgkhmiz.exe (PID: 7548)
- onvzbwiaun.exe (PID: 1764)
- elocfqwuye.exe (PID: 1476)
- hrdsgichmx.exe (PID: 5296)
- jruldodcef.exe (PID: 1924)
- rfgabxtnjs.exe (PID: 3116)
- bjgouiikhv.exe (PID: 2116)
- jvgegzdsla.exe (PID: 1688)
- tjjutotxid.exe (PID: 5232)
- zwmnkfbpri.exe (PID: 8164)
- efgtzeuccn.exe (PID: 7780)
- bkdevtipzu.exe (PID: 4284)
- yeisetohqr.exe (PID: 6156)
- gxipnxzywl.exe (PID: 4748)
- jezcurobuo.exe (PID: 4644)
- lkmdvekdws.exe (PID: 6752)
- wgoyrdxvcl.exe (PID: 7280)
- itvlxjniyf.exe (PID: 5500)
- dayxkinzxp.exe (PID: 4208)
- bftbkadpgy.exe (PID: 1924)
- qreckkxgbk.exe (PID: 2116)
- letiqyvmxl.exe (PID: 7032)
- vadylndrtg.exe (PID: 6724)
- jnotcqhwce.exe (PID: 7956)
- omuukeryey.exe (PID: 4868)
- neerqyggmi.exe (PID: 688)
- gibvdepsxj.exe (PID: 5192)
- ypuhwbkstr.exe (PID: 4488)
- dyktkxkhge.exe (PID: 6184)
- pxaauxccoh.exe (PID: 4432)
- xucchfmvyn.exe (PID: 1320)
- nrcocittiu.exe (PID: 6388)
- nvifhdnajp.exe (PID: 2492)
- fjjojzzbou.exe (PID: 7416)
- ffwlailrtx.exe (PID: 2268)
- dadbqfedcd.exe (PID: 5580)
- lxqsykutai.exe (PID: 8180)
- pdtxevsxel.exe (PID: 7420)
- cxkqobjgua.exe (PID: 7736)
- utyyljbzff.exe (PID: 2436)
- cmhwfkmvoz.exe (PID: 7596)
- cmibrrkujx.exe (PID: 4804)
- xtchtjmuuc.exe (PID: 7548)
- sogbmnsdrj.exe (PID: 7812)
- sdfaosdxwi.exe (PID: 7028)
- sdsqzunocw.exe (PID: 4016)
- xxtbpyltyn.exe (PID: 5404)
- pywfoaybce.exe (PID: 4956)
- atychuwqkn.exe (PID: 1604)
- enpqsmmnyu.exe (PID: 6320)
- pneqbfgmjb.exe (PID: 2896)
- prrgtpskoe.exe (PID: 144)
- pnoopaovkl.exe (PID: 6704)
- sfixedzcop.exe (PID: 2108)
- cmgowgbywk.exe (PID: 2288)
- hkyfzgqkle.exe (PID: 5580)
- phwhwtwvnk.exe (PID: 3948)
- rzktpvrurt.exe (PID: 5368)
- mbrumwdich.exe (PID: 7400)
- zhlhxurvrq.exe (PID: 4696)
- kkkczucsvr.exe (PID: 6064)
- koysbtwmln.exe (PID: 6328)
- eyclecnxvt.exe (PID: 4620)
- enlbmmdmah.exe (PID: 6340)
- pnacwfqleo.exe (PID: 8020)
- eoxfwdqrpq.exe (PID: 4608)
- wjmntlijzv.exe (PID: 7808)
- esswfjgpfd.exe (PID: 6124)
- bpolhvgvcx.exe (PID: 4956)
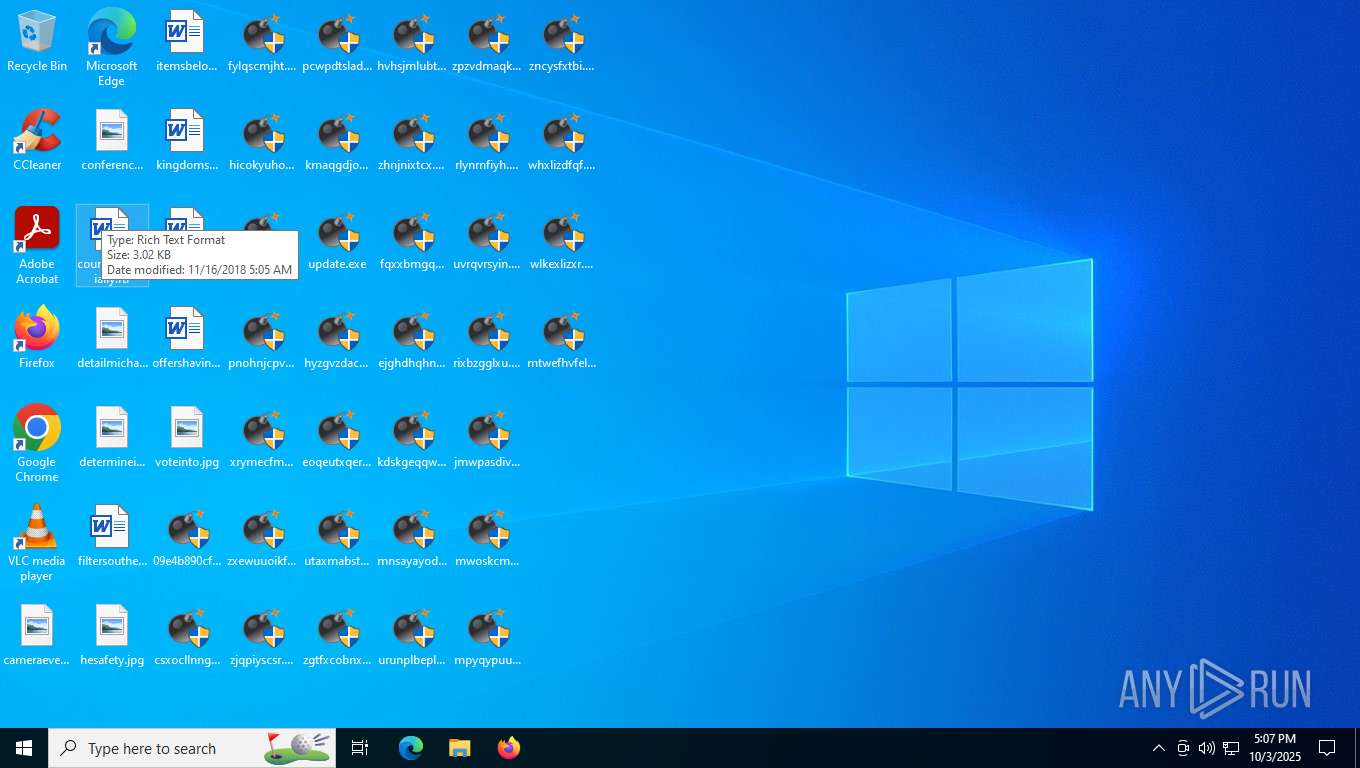
Starts itself from another location
- csxocllnng.exe (PID: 8084)
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 1600)
- hicokyuhob.exe (PID: 5708)
- kprrzqdlin.exe (PID: 7244)
- fylqscmjht.exe (PID: 2176)
- pnohnjcpvo.exe (PID: 8180)
- xrymecfmql.exe (PID: 4452)
- zxewuuoikf.exe (PID: 8164)
- pcwpdtslad.exe (PID: 7416)
- zjqpiyscsr.exe (PID: 3432)
- kmaqgdjokj.exe (PID: 7548)
- hyzgvzdacw.exe (PID: 4608)
- eoqeutxqer.exe (PID: 7956)
- zgtfxcobnx.exe (PID: 2600)
- utaxmabstw.exe (PID: 560)
- hvhsjmlubt.exe (PID: 8032)
- zhnjnixtcx.exe (PID: 7728)
- fqxxbmgqhi.exe (PID: 2504)
- kdskgeqqwp.exe (PID: 2572)
- ejghdhqhnb.exe (PID: 2720)
- mnsayayodo.exe (PID: 5340)
- urunplbepl.exe (PID: 8116)
- zpzvdmaqku.exe (PID: 6752)
- rlynrnfiyh.exe (PID: 1320)
- uvrqvrsyin.exe (PID: 7360)
- rixbzgglxu.exe (PID: 4488)
- jmwpasdivy.exe (PID: 1924)
- mwoskcmmxo.exe (PID: 2400)
- mpyqypuugx.exe (PID: 6156)
- whxlizdfqf.exe (PID: 2756)
- zncysfxtbi.exe (PID: 7220)
- wlkexlizxr.exe (PID: 2360)
- odxzjlbvoj.exe (PID: 8144)
- mtwefhvfel.exe (PID: 2328)
- gompxdqcvc.exe (PID: 6196)
- eqsyppkujn.exe (PID: 2188)
- dbsissextr.exe (PID: 2876)
- oqhhyifunb.exe (PID: 2172)
- tcqrexcuys.exe (PID: 6340)
- trpchfdaup.exe (PID: 2080)
- blwmewuzju.exe (PID: 5292)
- raxxxljoul.exe (PID: 3056)
- bslsveywdt.exe (PID: 2856)
- egbiwvejae.exe (PID: 1432)
- qforbihvgw.exe (PID: 2268)
- orzydgqdhv.exe (PID: 5368)
- jfcszigikn.exe (PID: 7608)
- oojxctwojr.exe (PID: 2812)
- whjvwuijsk.exe (PID: 4584)
- tadkhcgoyy.exe (PID: 3260)
- amdvpeusmt.exe (PID: 5580)
- gvudjjypof.exe (PID: 7956)
- jnngvndnql.exe (PID: 1212)
- aunbspwkau.exe (PID: 2532)
- nppfuqatua.exe (PID: 7792)
- gtduxkivrl.exe (PID: 7068)
- dbvqryktjx.exe (PID: 2868)
- gaddnnykva.exe (PID: 5440)
- izsyxzrwwg.exe (PID: 6956)
- vjbgnlyphc.exe (PID: 2108)
- dqmbuotzxu.exe (PID: 8144)
- ilqbkfaqoz.exe (PID: 7656)
- lrgfkmjzuu.exe (PID: 1740)
- gmkzlqpjrc.exe (PID: 6868)
- vrvounwzxb.exe (PID: 2080)
- aiaoihjpzf.exe (PID: 3056)
- lpowynuywa.exe (PID: 2672)
- ngewcpuoup.exe (PID: 7416)
- fgqzncdaxw.exe (PID: 7084)
- ycisjlittj.exe (PID: 8016)
- lexngykmbg.exe (PID: 5372)
- icfsteusxx.exe (PID: 8088)
- yofqtukkgt.exe (PID: 1516)
- anfpcsiwsp.exe (PID: 7788)
- snfjcegjph.exe (PID: 2268)
- nivcbzbogz.exe (PID: 4584)
- skfhycmpgc.exe (PID: 7472)
- viucigxcoi.exe (PID: 5232)
- qokscracdj.exe (PID: 2884)
- njbxuzdgbg.exe (PID: 708)
- cfevrgjeeg.exe (PID: 6416)
- soztejubgy.exe (PID: 2492)
- czaoqpodwr.exe (PID: 3000)
- pirxplllek.exe (PID: 2028)
- keylvyjyad.exe (PID: 4108)
- pmeigbzvzh.exe (PID: 1380)
- caywraojoq.exe (PID: 7404)
- vlmbkfmhqy.exe (PID: 576)
- hqfbkvudsj.exe (PID: 8100)
- fzzhlgjvvl.exe (PID: 2816)
- psxgpipqhl.exe (PID: 7024)
- zypigsazyh.exe (PID: 4960)
- cuebmurspj.exe (PID: 1476)
- zgawcoxedg.exe (PID: 6292)
- pljbiomhzn.exe (PID: 1604)
- sgmzncgjgn.exe (PID: 2176)
- cuocxrzfaj.exe (PID: 1924)
- rzxpvjgivq.exe (PID: 7372)
- xipvivhfsi.exe (PID: 7220)
- eukowlprtw.exe (PID: 708)
- euzlwjcrpo.exe (PID: 3000)
- bdsmjtncda.exe (PID: 532)
- eczuuiwbve.exe (PID: 6720)
- uzsxfusvrv.exe (PID: 5404)
- mosqbwxfmq.exe (PID: 4016)
- hbagoozgbr.exe (PID: 6772)
- jlavgkhmiz.exe (PID: 2996)
- ueryyvrpsh.exe (PID: 7084)
- onvzbwiaun.exe (PID: 7032)
- elocfqwuye.exe (PID: 7440)
- hrdsgichmx.exe (PID: 6292)
- jruldodcef.exe (PID: 2832)
- rfgabxtnjs.exe (PID: 6480)
- jvgegzdsla.exe (PID: 560)
- tjjutotxid.exe (PID: 2400)
- bjgouiikhv.exe (PID: 2896)
- zwmnkfbpri.exe (PID: 6124)
- bkdevtipzu.exe (PID: 2652)
- efgtzeuccn.exe (PID: 7196)
- yeisetohqr.exe (PID: 4960)
- gxipnxzywl.exe (PID: 2480)
- jezcurobuo.exe (PID: 2900)
- wgoyrdxvcl.exe (PID: 7068)
- itvlxjniyf.exe (PID: 2156)
- lkmdvekdws.exe (PID: 5580)
- bftbkadpgy.exe (PID: 7736)
- dayxkinzxp.exe (PID: 2868)
- qreckkxgbk.exe (PID: 7788)
- letiqyvmxl.exe (PID: 2876)
- vadylndrtg.exe (PID: 8164)
- jnotcqhwce.exe (PID: 7672)
- omuukeryey.exe (PID: 5696)
- neerqyggmi.exe (PID: 1020)
- gibvdepsxj.exe (PID: 7360)
- ypuhwbkstr.exe (PID: 3000)
- dyktkxkhge.exe (PID: 5040)
- xucchfmvyn.exe (PID: 2288)
- nrcocittiu.exe (PID: 2400)
- pxaauxccoh.exe (PID: 7908)
- nvifhdnajp.exe (PID: 1924)
- ffwlailrtx.exe (PID: 2480)
- dadbqfedcd.exe (PID: 5196)
- fjjojzzbou.exe (PID: 7068)
- lxqsykutai.exe (PID: 6724)
- utyyljbzff.exe (PID: 6480)
- pdtxevsxel.exe (PID: 2156)
- cmhwfkmvoz.exe (PID: 7740)
- cxkqobjgua.exe (PID: 3124)
- cmibrrkujx.exe (PID: 8044)
- xtchtjmuuc.exe (PID: 708)
- sogbmnsdrj.exe (PID: 4744)
- sdfaosdxwi.exe (PID: 7160)
- xxtbpyltyn.exe (PID: 4488)
- sdsqzunocw.exe (PID: 2316)
- atychuwqkn.exe (PID: 7244)
- pywfoaybce.exe (PID: 4732)
- enpqsmmnyu.exe (PID: 8116)
- pneqbfgmjb.exe (PID: 7084)
- prrgtpskoe.exe (PID: 1020)
- pnoopaovkl.exe (PID: 6416)
- sfixedzcop.exe (PID: 3084)
- cmgowgbywk.exe (PID: 2400)
- hkyfzgqkle.exe (PID: 5040)
- rzktpvrurt.exe (PID: 8180)
- phwhwtwvnk.exe (PID: 7908)
- mbrumwdich.exe (PID: 2436)
- kkkczucsvr.exe (PID: 2980)
- koysbtwmln.exe (PID: 7460)
- zhlhxurvrq.exe (PID: 7580)
- eyclecnxvt.exe (PID: 1692)
- enlbmmdmah.exe (PID: 4228)
- pnacwfqleo.exe (PID: 7396)
- wjmntlijzv.exe (PID: 7248)
- eoxfwdqrpq.exe (PID: 7172)
- bpolhvgvcx.exe (PID: 8164)
- esswfjgpfd.exe (PID: 6196)
There is functionality for taking screenshot (YARA)
- kmaqgdjokj.exe (PID: 7548)
- hqfbkvudsj.exe (PID: 8100)
INFO
Checks supported languages
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 1600)
- csxocllnng.exe (PID: 6780)
- fylqscmjht.exe (PID: 2176)
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 7548)
- fylqscmjht.exe (PID: 532)
- hicokyuhob.exe (PID: 5708)
- csxocllnng.exe (PID: 8084)
- pnohnjcpvo.exe (PID: 5484)
- kprrzqdlin.exe (PID: 4260)
- hicokyuhob.exe (PID: 4696)
- kprrzqdlin.exe (PID: 7244)
- xrymecfmql.exe (PID: 4452)
- xrymecfmql.exe (PID: 2288)
- zxewuuoikf.exe (PID: 8164)
- zjqpiyscsr.exe (PID: 3432)
- pnohnjcpvo.exe (PID: 8180)
- zxewuuoikf.exe (PID: 2188)
- zjqpiyscsr.exe (PID: 3516)
- pcwpdtslad.exe (PID: 7416)
- kmaqgdjokj.exe (PID: 7548)
- pcwpdtslad.exe (PID: 4208)
- kmaqgdjokj.exe (PID: 6176)
- eoqeutxqer.exe (PID: 7956)
- hyzgvzdacw.exe (PID: 1924)
- hyzgvzdacw.exe (PID: 4608)
- eoqeutxqer.exe (PID: 332)
- utaxmabstw.exe (PID: 7440)
- zgtfxcobnx.exe (PID: 2852)
- utaxmabstw.exe (PID: 560)
- hvhsjmlubt.exe (PID: 8032)
- zgtfxcobnx.exe (PID: 2600)
- zhnjnixtcx.exe (PID: 7728)
- zhnjnixtcx.exe (PID: 1212)
- hvhsjmlubt.exe (PID: 5424)
- fqxxbmgqhi.exe (PID: 3000)
- fqxxbmgqhi.exe (PID: 2504)
- kdskgeqqwp.exe (PID: 2572)
- kdskgeqqwp.exe (PID: 7068)
- mnsayayodo.exe (PID: 5340)
- ejghdhqhnb.exe (PID: 708)
- ejghdhqhnb.exe (PID: 2720)
- urunplbepl.exe (PID: 3268)
- urunplbepl.exe (PID: 8116)
- mnsayayodo.exe (PID: 2008)
- zpzvdmaqku.exe (PID: 7776)
- rlynrnfiyh.exe (PID: 1320)
- zpzvdmaqku.exe (PID: 6752)
- uvrqvrsyin.exe (PID: 7360)
- uvrqvrsyin.exe (PID: 3196)
- rlynrnfiyh.exe (PID: 2080)
- rixbzgglxu.exe (PID: 4488)
- rixbzgglxu.exe (PID: 3160)
- jmwpasdivy.exe (PID: 1924)
- mwoskcmmxo.exe (PID: 2400)
- mwoskcmmxo.exe (PID: 7556)
- mpyqypuugx.exe (PID: 6156)
- jmwpasdivy.exe (PID: 6660)
- zncysfxtbi.exe (PID: 7220)
- zncysfxtbi.exe (PID: 7012)
- mpyqypuugx.exe (PID: 7608)
- whxlizdfqf.exe (PID: 3552)
- wlkexlizxr.exe (PID: 2360)
- wlkexlizxr.exe (PID: 1020)
- whxlizdfqf.exe (PID: 2756)
- mtwefhvfel.exe (PID: 2328)
- mtwefhvfel.exe (PID: 6416)
- odxzjlbvoj.exe (PID: 8144)
- odxzjlbvoj.exe (PID: 4956)
- dbsissextr.exe (PID: 2876)
- dbsissextr.exe (PID: 764)
- gompxdqcvc.exe (PID: 7788)
- gompxdqcvc.exe (PID: 6196)
- eqsyppkujn.exe (PID: 2392)
- tcqrexcuys.exe (PID: 6340)
- tcqrexcuys.exe (PID: 1604)
- eqsyppkujn.exe (PID: 2188)
- oqhhyifunb.exe (PID: 5508)
- trpchfdaup.exe (PID: 2080)
- oqhhyifunb.exe (PID: 2172)
- raxxxljoul.exe (PID: 5196)
- raxxxljoul.exe (PID: 3056)
- trpchfdaup.exe (PID: 7736)
- bslsveywdt.exe (PID: 2856)
- blwmewuzju.exe (PID: 5292)
- blwmewuzju.exe (PID: 8000)
- egbiwvejae.exe (PID: 1432)
- bslsveywdt.exe (PID: 2164)
- orzydgqdhv.exe (PID: 5368)
- orzydgqdhv.exe (PID: 4676)
- egbiwvejae.exe (PID: 6868)
- qforbihvgw.exe (PID: 2268)
- qforbihvgw.exe (PID: 7596)
- oojxctwojr.exe (PID: 2812)
- oojxctwojr.exe (PID: 5868)
- tadkhcgoyy.exe (PID: 7012)
- jfcszigikn.exe (PID: 7608)
- jfcszigikn.exe (PID: 6836)
- tadkhcgoyy.exe (PID: 3260)
- whjvwuijsk.exe (PID: 7276)
- amdvpeusmt.exe (PID: 5580)
- whjvwuijsk.exe (PID: 4584)
- gvudjjypof.exe (PID: 7956)
- gvudjjypof.exe (PID: 1560)
- amdvpeusmt.exe (PID: 4364)
- jnngvndnql.exe (PID: 1212)
- jnngvndnql.exe (PID: 2352)
- gtduxkivrl.exe (PID: 7068)
- aunbspwkau.exe (PID: 2532)
- aunbspwkau.exe (PID: 2792)
- gtduxkivrl.exe (PID: 7220)
- nppfuqatua.exe (PID: 2528)
- gaddnnykva.exe (PID: 5440)
- nppfuqatua.exe (PID: 7792)
- dbvqryktjx.exe (PID: 2868)
- dbvqryktjx.exe (PID: 2328)
- izsyxzrwwg.exe (PID: 6956)
- izsyxzrwwg.exe (PID: 7808)
- gaddnnykva.exe (PID: 4708)
- dqmbuotzxu.exe (PID: 4432)
- dqmbuotzxu.exe (PID: 8144)
- ilqbkfaqoz.exe (PID: 7656)
- vjbgnlyphc.exe (PID: 2108)
- vjbgnlyphc.exe (PID: 796)
- gmkzlqpjrc.exe (PID: 6868)
- ilqbkfaqoz.exe (PID: 572)
- gmkzlqpjrc.exe (PID: 7552)
- lrgfkmjzuu.exe (PID: 2172)
- vrvounwzxb.exe (PID: 600)
- lrgfkmjzuu.exe (PID: 1740)
- vrvounwzxb.exe (PID: 2080)
- aiaoihjpzf.exe (PID: 3056)
- aiaoihjpzf.exe (PID: 6184)
- ngewcpuoup.exe (PID: 7416)
- ngewcpuoup.exe (PID: 7728)
- lpowynuywa.exe (PID: 2672)
- lpowynuywa.exe (PID: 8056)
- fgqzncdaxw.exe (PID: 7084)
- fgqzncdaxw.exe (PID: 7276)
- lexngykmbg.exe (PID: 5372)
- ycisjlittj.exe (PID: 8016)
- ycisjlittj.exe (PID: 5256)
- icfsteusxx.exe (PID: 8088)
- lexngykmbg.exe (PID: 7088)
- icfsteusxx.exe (PID: 8168)
- yofqtukkgt.exe (PID: 7744)
- snfjcegjph.exe (PID: 1560)
- snfjcegjph.exe (PID: 2268)
- yofqtukkgt.exe (PID: 1516)
- anfpcsiwsp.exe (PID: 7788)
- anfpcsiwsp.exe (PID: 3708)
- skfhycmpgc.exe (PID: 7472)
- skfhycmpgc.exe (PID: 2864)
- nivcbzbogz.exe (PID: 8100)
- viucigxcoi.exe (PID: 5232)
- nivcbzbogz.exe (PID: 4584)
- qokscracdj.exe (PID: 2884)
- qokscracdj.exe (PID: 6972)
- viucigxcoi.exe (PID: 5684)
- cfevrgjeeg.exe (PID: 6416)
- soztejubgy.exe (PID: 4016)
- soztejubgy.exe (PID: 2492)
- njbxuzdgbg.exe (PID: 708)
- njbxuzdgbg.exe (PID: 2572)
- cfevrgjeeg.exe (PID: 7992)
- czaoqpodwr.exe (PID: 3000)
- pirxplllek.exe (PID: 2028)
- pirxplllek.exe (PID: 5552)
- czaoqpodwr.exe (PID: 5500)
- pmeigbzvzh.exe (PID: 1380)
- pmeigbzvzh.exe (PID: 2176)
- keylvyjyad.exe (PID: 6396)
- caywraojoq.exe (PID: 7744)
- keylvyjyad.exe (PID: 4108)
- caywraojoq.exe (PID: 7404)
- vlmbkfmhqy.exe (PID: 576)
- vlmbkfmhqy.exe (PID: 3552)
- hqfbkvudsj.exe (PID: 8100)
- fzzhlgjvvl.exe (PID: 2816)
- fzzhlgjvvl.exe (PID: 2328)
- zypigsazyh.exe (PID: 2284)
- hqfbkvudsj.exe (PID: 8016)
- zypigsazyh.exe (PID: 4960)
- psxgpipqhl.exe (PID: 7024)
- psxgpipqhl.exe (PID: 4016)
- cuebmurspj.exe (PID: 1476)
- zgawcoxedg.exe (PID: 6292)
- zgawcoxedg.exe (PID: 7988)
- pljbiomhzn.exe (PID: 1604)
- cuebmurspj.exe (PID: 2164)
- sgmzncgjgn.exe (PID: 2176)
- sgmzncgjgn.exe (PID: 5208)
- pljbiomhzn.exe (PID: 2652)
- cuocxrzfaj.exe (PID: 1924)
- cuocxrzfaj.exe (PID: 1764)
- xipvivhfsi.exe (PID: 7220)
- rzxpvjgivq.exe (PID: 7372)
- rzxpvjgivq.exe (PID: 2492)
- euzlwjcrpo.exe (PID: 3000)
- euzlwjcrpo.exe (PID: 5580)
- xipvivhfsi.exe (PID: 7440)
- eczuuiwbve.exe (PID: 6720)
- eczuuiwbve.exe (PID: 2832)
- eukowlprtw.exe (PID: 708)
- eukowlprtw.exe (PID: 7068)
- bdsmjtncda.exe (PID: 532)
- bdsmjtncda.exe (PID: 560)
- uzsxfusvrv.exe (PID: 5404)
- mosqbwxfmq.exe (PID: 4016)
- mosqbwxfmq.exe (PID: 2652)
- hbagoozgbr.exe (PID: 6772)
- uzsxfusvrv.exe (PID: 6924)
- jlavgkhmiz.exe (PID: 2996)
- hbagoozgbr.exe (PID: 7744)
- ueryyvrpsh.exe (PID: 7084)
- ueryyvrpsh.exe (PID: 2492)
- jlavgkhmiz.exe (PID: 7548)
- onvzbwiaun.exe (PID: 1764)
- elocfqwuye.exe (PID: 7440)
- elocfqwuye.exe (PID: 1476)
- onvzbwiaun.exe (PID: 7032)
- hrdsgichmx.exe (PID: 6292)
- hrdsgichmx.exe (PID: 5296)
- rfgabxtnjs.exe (PID: 6480)
- rfgabxtnjs.exe (PID: 3116)
- jruldodcef.exe (PID: 1924)
- jvgegzdsla.exe (PID: 560)
- jvgegzdsla.exe (PID: 1688)
- jruldodcef.exe (PID: 2832)
- bjgouiikhv.exe (PID: 2896)
- bjgouiikhv.exe (PID: 2116)
- tjjutotxid.exe (PID: 5232)
- tjjutotxid.exe (PID: 2400)
- zwmnkfbpri.exe (PID: 6124)
- efgtzeuccn.exe (PID: 7196)
- efgtzeuccn.exe (PID: 7780)
- zwmnkfbpri.exe (PID: 8164)
- bkdevtipzu.exe (PID: 4284)
- gxipnxzywl.exe (PID: 2480)
- bkdevtipzu.exe (PID: 2652)
- yeisetohqr.exe (PID: 6156)
- gxipnxzywl.exe (PID: 4748)
- yeisetohqr.exe (PID: 4960)
- wgoyrdxvcl.exe (PID: 7068)
- wgoyrdxvcl.exe (PID: 7280)
- jezcurobuo.exe (PID: 2900)
- jezcurobuo.exe (PID: 4644)
- lkmdvekdws.exe (PID: 6752)
- itvlxjniyf.exe (PID: 2156)
- itvlxjniyf.exe (PID: 5500)
- lkmdvekdws.exe (PID: 5580)
- bftbkadpgy.exe (PID: 7736)
- bftbkadpgy.exe (PID: 1924)
- dayxkinzxp.exe (PID: 4208)
- dayxkinzxp.exe (PID: 2868)
- qreckkxgbk.exe (PID: 7788)
- qreckkxgbk.exe (PID: 2116)
- letiqyvmxl.exe (PID: 2876)
- vadylndrtg.exe (PID: 8164)
- letiqyvmxl.exe (PID: 7032)
- vadylndrtg.exe (PID: 6724)
- jnotcqhwce.exe (PID: 7672)
- omuukeryey.exe (PID: 5696)
- jnotcqhwce.exe (PID: 7956)
- neerqyggmi.exe (PID: 1020)
- neerqyggmi.exe (PID: 688)
- omuukeryey.exe (PID: 4868)
- ypuhwbkstr.exe (PID: 4488)
- ypuhwbkstr.exe (PID: 3000)
- dyktkxkhge.exe (PID: 5040)
- gibvdepsxj.exe (PID: 7360)
- gibvdepsxj.exe (PID: 5192)
- nrcocittiu.exe (PID: 2400)
- nrcocittiu.exe (PID: 6388)
- dyktkxkhge.exe (PID: 6184)
- xucchfmvyn.exe (PID: 2288)
- nvifhdnajp.exe (PID: 1924)
- pxaauxccoh.exe (PID: 7908)
- xucchfmvyn.exe (PID: 1320)
- nvifhdnajp.exe (PID: 2492)
- pxaauxccoh.exe (PID: 4432)
- ffwlailrtx.exe (PID: 2480)
- ffwlailrtx.exe (PID: 2268)
- fjjojzzbou.exe (PID: 7416)
- fjjojzzbou.exe (PID: 7068)
- lxqsykutai.exe (PID: 6724)
- dadbqfedcd.exe (PID: 5196)
- dadbqfedcd.exe (PID: 5580)
- pdtxevsxel.exe (PID: 2156)
- pdtxevsxel.exe (PID: 7420)
- lxqsykutai.exe (PID: 8180)
- utyyljbzff.exe (PID: 2436)
- cxkqobjgua.exe (PID: 3124)
- utyyljbzff.exe (PID: 6480)
- cxkqobjgua.exe (PID: 7736)
- cmhwfkmvoz.exe (PID: 7596)
- cmibrrkujx.exe (PID: 8044)
- cmhwfkmvoz.exe (PID: 7740)
- cmibrrkujx.exe (PID: 4804)
- sogbmnsdrj.exe (PID: 7812)
- sogbmnsdrj.exe (PID: 4744)
- xtchtjmuuc.exe (PID: 708)
- xtchtjmuuc.exe (PID: 7548)
- sdfaosdxwi.exe (PID: 7160)
- sdsqzunocw.exe (PID: 2316)
- sdsqzunocw.exe (PID: 4016)
- sdfaosdxwi.exe (PID: 7028)
- xxtbpyltyn.exe (PID: 5404)
- pywfoaybce.exe (PID: 4732)
- pywfoaybce.exe (PID: 4956)
- xxtbpyltyn.exe (PID: 4488)
- atychuwqkn.exe (PID: 7244)
- atychuwqkn.exe (PID: 1604)
- enpqsmmnyu.exe (PID: 8116)
- enpqsmmnyu.exe (PID: 6320)
- prrgtpskoe.exe (PID: 144)
- prrgtpskoe.exe (PID: 1020)
- pnoopaovkl.exe (PID: 6416)
- pneqbfgmjb.exe (PID: 2896)
- pneqbfgmjb.exe (PID: 7084)
- sfixedzcop.exe (PID: 3084)
- pnoopaovkl.exe (PID: 6704)
- hkyfzgqkle.exe (PID: 5580)
- sfixedzcop.exe (PID: 2108)
- hkyfzgqkle.exe (PID: 5040)
- cmgowgbywk.exe (PID: 2400)
- cmgowgbywk.exe (PID: 2288)
- rzktpvrurt.exe (PID: 8180)
- rzktpvrurt.exe (PID: 5368)
- phwhwtwvnk.exe (PID: 7908)
- phwhwtwvnk.exe (PID: 3948)
- mbrumwdich.exe (PID: 2436)
- kkkczucsvr.exe (PID: 2980)
- kkkczucsvr.exe (PID: 6064)
- mbrumwdich.exe (PID: 7400)
- zhlhxurvrq.exe (PID: 4696)
- zhlhxurvrq.exe (PID: 7580)
- koysbtwmln.exe (PID: 6328)
- eyclecnxvt.exe (PID: 1692)
- koysbtwmln.exe (PID: 7460)
- eyclecnxvt.exe (PID: 4620)
- enlbmmdmah.exe (PID: 6340)
- enlbmmdmah.exe (PID: 4228)
- pnacwfqleo.exe (PID: 7396)
- wjmntlijzv.exe (PID: 7248)
- wjmntlijzv.exe (PID: 7808)
- pnacwfqleo.exe (PID: 8020)
- eoxfwdqrpq.exe (PID: 4608)
- bpolhvgvcx.exe (PID: 8164)
- bpolhvgvcx.exe (PID: 4956)
- eoxfwdqrpq.exe (PID: 7172)
- esswfjgpfd.exe (PID: 6196)
- esswfjgpfd.exe (PID: 6124)
- rjxotlteoz.exe (PID: 5172)
The sample compiled with chinese language support
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 7548)
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 1600)
- csxocllnng.exe (PID: 6780)
- fylqscmjht.exe (PID: 532)
- kprrzqdlin.exe (PID: 4260)
- hicokyuhob.exe (PID: 4696)
- pnohnjcpvo.exe (PID: 5484)
- xrymecfmql.exe (PID: 2288)
- zxewuuoikf.exe (PID: 2188)
- zjqpiyscsr.exe (PID: 3516)
- pcwpdtslad.exe (PID: 4208)
- kmaqgdjokj.exe (PID: 6176)
- csxocllnng.exe (PID: 8084)
- hyzgvzdacw.exe (PID: 1924)
- eoqeutxqer.exe (PID: 332)
- utaxmabstw.exe (PID: 7440)
- hvhsjmlubt.exe (PID: 5424)
- zgtfxcobnx.exe (PID: 2852)
- fqxxbmgqhi.exe (PID: 3000)
- zhnjnixtcx.exe (PID: 1212)
- ejghdhqhnb.exe (PID: 708)
- kdskgeqqwp.exe (PID: 7068)
- mnsayayodo.exe (PID: 2008)
- urunplbepl.exe (PID: 3268)
- zpzvdmaqku.exe (PID: 7776)
- rlynrnfiyh.exe (PID: 2080)
- uvrqvrsyin.exe (PID: 3196)
- rixbzgglxu.exe (PID: 3160)
- jmwpasdivy.exe (PID: 6660)
- mwoskcmmxo.exe (PID: 7556)
- mpyqypuugx.exe (PID: 7608)
- zncysfxtbi.exe (PID: 7012)
- whxlizdfqf.exe (PID: 3552)
- wlkexlizxr.exe (PID: 1020)
- odxzjlbvoj.exe (PID: 4956)
- mtwefhvfel.exe (PID: 6416)
- gompxdqcvc.exe (PID: 7788)
- dbsissextr.exe (PID: 764)
- eqsyppkujn.exe (PID: 2392)
- oqhhyifunb.exe (PID: 5508)
- tcqrexcuys.exe (PID: 1604)
- raxxxljoul.exe (PID: 5196)
- trpchfdaup.exe (PID: 7736)
- blwmewuzju.exe (PID: 8000)
- bslsveywdt.exe (PID: 2164)
- orzydgqdhv.exe (PID: 4676)
- egbiwvejae.exe (PID: 6868)
- qforbihvgw.exe (PID: 7596)
- oojxctwojr.exe (PID: 5868)
- jfcszigikn.exe (PID: 6836)
- whjvwuijsk.exe (PID: 7276)
- tadkhcgoyy.exe (PID: 7012)
- amdvpeusmt.exe (PID: 4364)
- gvudjjypof.exe (PID: 1560)
- jnngvndnql.exe (PID: 2352)
- aunbspwkau.exe (PID: 2792)
- nppfuqatua.exe (PID: 2528)
- gtduxkivrl.exe (PID: 7220)
- gaddnnykva.exe (PID: 4708)
- dbvqryktjx.exe (PID: 2328)
- izsyxzrwwg.exe (PID: 7808)
- dqmbuotzxu.exe (PID: 4432)
- vjbgnlyphc.exe (PID: 796)
- ilqbkfaqoz.exe (PID: 572)
- gmkzlqpjrc.exe (PID: 7552)
- lrgfkmjzuu.exe (PID: 2172)
- aiaoihjpzf.exe (PID: 6184)
- vrvounwzxb.exe (PID: 600)
- ngewcpuoup.exe (PID: 7728)
- lpowynuywa.exe (PID: 8056)
- fgqzncdaxw.exe (PID: 7276)
- ycisjlittj.exe (PID: 5256)
- icfsteusxx.exe (PID: 8168)
- lexngykmbg.exe (PID: 7088)
- yofqtukkgt.exe (PID: 7744)
- anfpcsiwsp.exe (PID: 3708)
- skfhycmpgc.exe (PID: 2864)
- snfjcegjph.exe (PID: 1560)
- nivcbzbogz.exe (PID: 8100)
- viucigxcoi.exe (PID: 5684)
- qokscracdj.exe (PID: 6972)
- soztejubgy.exe (PID: 4016)
- czaoqpodwr.exe (PID: 5500)
- njbxuzdgbg.exe (PID: 2572)
- cfevrgjeeg.exe (PID: 7992)
- pirxplllek.exe (PID: 5552)
- keylvyjyad.exe (PID: 6396)
- pmeigbzvzh.exe (PID: 2176)
- caywraojoq.exe (PID: 7744)
- vlmbkfmhqy.exe (PID: 3552)
- hqfbkvudsj.exe (PID: 8016)
- fzzhlgjvvl.exe (PID: 2328)
- psxgpipqhl.exe (PID: 4016)
- zypigsazyh.exe (PID: 2284)
- zgawcoxedg.exe (PID: 7988)
- cuebmurspj.exe (PID: 2164)
- pljbiomhzn.exe (PID: 2652)
- sgmzncgjgn.exe (PID: 5208)
- cuocxrzfaj.exe (PID: 1764)
- rzxpvjgivq.exe (PID: 2492)
- xipvivhfsi.exe (PID: 7440)
- eukowlprtw.exe (PID: 7068)
- euzlwjcrpo.exe (PID: 5580)
- bdsmjtncda.exe (PID: 560)
- eczuuiwbve.exe (PID: 2832)
- mosqbwxfmq.exe (PID: 2652)
- uzsxfusvrv.exe (PID: 6924)
- hbagoozgbr.exe (PID: 7744)
- ueryyvrpsh.exe (PID: 2492)
- jlavgkhmiz.exe (PID: 7548)
- onvzbwiaun.exe (PID: 1764)
- elocfqwuye.exe (PID: 1476)
- hrdsgichmx.exe (PID: 5296)
- jruldodcef.exe (PID: 1924)
- rfgabxtnjs.exe (PID: 3116)
- bjgouiikhv.exe (PID: 2116)
- jvgegzdsla.exe (PID: 1688)
- tjjutotxid.exe (PID: 5232)
- zwmnkfbpri.exe (PID: 8164)
- bkdevtipzu.exe (PID: 4284)
- efgtzeuccn.exe (PID: 7780)
- yeisetohqr.exe (PID: 6156)
- gxipnxzywl.exe (PID: 4748)
- jezcurobuo.exe (PID: 4644)
- wgoyrdxvcl.exe (PID: 7280)
- lkmdvekdws.exe (PID: 6752)
- itvlxjniyf.exe (PID: 5500)
- bftbkadpgy.exe (PID: 1924)
- dayxkinzxp.exe (PID: 4208)
- qreckkxgbk.exe (PID: 2116)
- letiqyvmxl.exe (PID: 7032)
- vadylndrtg.exe (PID: 6724)
- jnotcqhwce.exe (PID: 7956)
- omuukeryey.exe (PID: 4868)
- neerqyggmi.exe (PID: 688)
- gibvdepsxj.exe (PID: 5192)
- ypuhwbkstr.exe (PID: 4488)
- dyktkxkhge.exe (PID: 6184)
- nrcocittiu.exe (PID: 6388)
- xucchfmvyn.exe (PID: 1320)
- pxaauxccoh.exe (PID: 4432)
- nvifhdnajp.exe (PID: 2492)
- ffwlailrtx.exe (PID: 2268)
- dadbqfedcd.exe (PID: 5580)
- fjjojzzbou.exe (PID: 7416)
- pdtxevsxel.exe (PID: 7420)
- lxqsykutai.exe (PID: 8180)
- utyyljbzff.exe (PID: 2436)
- cxkqobjgua.exe (PID: 7736)
- cmhwfkmvoz.exe (PID: 7596)
- cmibrrkujx.exe (PID: 4804)
- sogbmnsdrj.exe (PID: 7812)
- xtchtjmuuc.exe (PID: 7548)
- sdfaosdxwi.exe (PID: 7028)
- xxtbpyltyn.exe (PID: 5404)
- sdsqzunocw.exe (PID: 4016)
- pywfoaybce.exe (PID: 4956)
- atychuwqkn.exe (PID: 1604)
- enpqsmmnyu.exe (PID: 6320)
- prrgtpskoe.exe (PID: 144)
- pneqbfgmjb.exe (PID: 2896)
- pnoopaovkl.exe (PID: 6704)
- hkyfzgqkle.exe (PID: 5580)
- sfixedzcop.exe (PID: 2108)
- cmgowgbywk.exe (PID: 2288)
- rzktpvrurt.exe (PID: 5368)
- phwhwtwvnk.exe (PID: 3948)
- mbrumwdich.exe (PID: 7400)
- zhlhxurvrq.exe (PID: 4696)
- kkkczucsvr.exe (PID: 6064)
- koysbtwmln.exe (PID: 6328)
- enlbmmdmah.exe (PID: 6340)
- eyclecnxvt.exe (PID: 4620)
- pnacwfqleo.exe (PID: 8020)
- eoxfwdqrpq.exe (PID: 4608)
- wjmntlijzv.exe (PID: 7808)
- esswfjgpfd.exe (PID: 6124)
- bpolhvgvcx.exe (PID: 4956)
Reads the machine GUID from the registry
- csxocllnng.exe (PID: 6780)
- fylqscmjht.exe (PID: 532)
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 7548)
- hicokyuhob.exe (PID: 4696)
- pnohnjcpvo.exe (PID: 5484)
- kprrzqdlin.exe (PID: 4260)
- csxocllnng.exe (PID: 8084)
- xrymecfmql.exe (PID: 2288)
- fylqscmjht.exe (PID: 2176)
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 1600)
- hicokyuhob.exe (PID: 5708)
- kprrzqdlin.exe (PID: 7244)
- zjqpiyscsr.exe (PID: 3516)
- pnohnjcpvo.exe (PID: 8180)
- zxewuuoikf.exe (PID: 2188)
- pcwpdtslad.exe (PID: 4208)
- zjqpiyscsr.exe (PID: 3432)
- xrymecfmql.exe (PID: 4452)
- zxewuuoikf.exe (PID: 8164)
- hyzgvzdacw.exe (PID: 1924)
- pcwpdtslad.exe (PID: 7416)
- kmaqgdjokj.exe (PID: 6176)
- kmaqgdjokj.exe (PID: 7548)
- eoqeutxqer.exe (PID: 332)
- utaxmabstw.exe (PID: 7440)
- zgtfxcobnx.exe (PID: 2852)
- hyzgvzdacw.exe (PID: 4608)
- utaxmabstw.exe (PID: 560)
- eoqeutxqer.exe (PID: 7956)
- hvhsjmlubt.exe (PID: 5424)
- fqxxbmgqhi.exe (PID: 3000)
- zhnjnixtcx.exe (PID: 1212)
- zgtfxcobnx.exe (PID: 2600)
- kdskgeqqwp.exe (PID: 7068)
- ejghdhqhnb.exe (PID: 708)
- mnsayayodo.exe (PID: 2008)
- zhnjnixtcx.exe (PID: 7728)
- urunplbepl.exe (PID: 3268)
- hvhsjmlubt.exe (PID: 8032)
- ejghdhqhnb.exe (PID: 2720)
- zpzvdmaqku.exe (PID: 7776)
- fqxxbmgqhi.exe (PID: 2504)
- urunplbepl.exe (PID: 8116)
- uvrqvrsyin.exe (PID: 3196)
- zpzvdmaqku.exe (PID: 6752)
- mnsayayodo.exe (PID: 5340)
- kdskgeqqwp.exe (PID: 2572)
- rlynrnfiyh.exe (PID: 2080)
- rlynrnfiyh.exe (PID: 1320)
- rixbzgglxu.exe (PID: 3160)
- mwoskcmmxo.exe (PID: 7556)
- uvrqvrsyin.exe (PID: 7360)
- jmwpasdivy.exe (PID: 6660)
- mpyqypuugx.exe (PID: 7608)
- jmwpasdivy.exe (PID: 1924)
- rixbzgglxu.exe (PID: 4488)
- zncysfxtbi.exe (PID: 7012)
- whxlizdfqf.exe (PID: 3552)
- mwoskcmmxo.exe (PID: 2400)
- mpyqypuugx.exe (PID: 6156)
- zncysfxtbi.exe (PID: 7220)
- mtwefhvfel.exe (PID: 6416)
- whxlizdfqf.exe (PID: 2756)
- wlkexlizxr.exe (PID: 1020)
- odxzjlbvoj.exe (PID: 4956)
- wlkexlizxr.exe (PID: 2360)
- odxzjlbvoj.exe (PID: 8144)
- dbsissextr.exe (PID: 764)
- mtwefhvfel.exe (PID: 2328)
- gompxdqcvc.exe (PID: 7788)
- tcqrexcuys.exe (PID: 1604)
- gompxdqcvc.exe (PID: 6196)
- eqsyppkujn.exe (PID: 2392)
- dbsissextr.exe (PID: 2876)
- oqhhyifunb.exe (PID: 5508)
- eqsyppkujn.exe (PID: 2188)
- trpchfdaup.exe (PID: 7736)
- raxxxljoul.exe (PID: 5196)
- tcqrexcuys.exe (PID: 6340)
- blwmewuzju.exe (PID: 8000)
- oqhhyifunb.exe (PID: 2172)
- raxxxljoul.exe (PID: 3056)
- blwmewuzju.exe (PID: 5292)
- bslsveywdt.exe (PID: 2164)
- trpchfdaup.exe (PID: 2080)
- bslsveywdt.exe (PID: 2856)
- orzydgqdhv.exe (PID: 4676)
- egbiwvejae.exe (PID: 6868)
- oojxctwojr.exe (PID: 5868)
- egbiwvejae.exe (PID: 1432)
- qforbihvgw.exe (PID: 7596)
- tadkhcgoyy.exe (PID: 7012)
- jfcszigikn.exe (PID: 6836)
- qforbihvgw.exe (PID: 2268)
- orzydgqdhv.exe (PID: 5368)
- whjvwuijsk.exe (PID: 7276)
- jfcszigikn.exe (PID: 7608)
- amdvpeusmt.exe (PID: 4364)
- tadkhcgoyy.exe (PID: 3260)
- oojxctwojr.exe (PID: 2812)
- amdvpeusmt.exe (PID: 5580)
- jnngvndnql.exe (PID: 2352)
- whjvwuijsk.exe (PID: 4584)
- gvudjjypof.exe (PID: 1560)
- aunbspwkau.exe (PID: 2792)
- jnngvndnql.exe (PID: 1212)
- gvudjjypof.exe (PID: 7956)
- nppfuqatua.exe (PID: 2528)
- gtduxkivrl.exe (PID: 7220)
- dbvqryktjx.exe (PID: 2328)
- aunbspwkau.exe (PID: 2532)
- gaddnnykva.exe (PID: 4708)
- gtduxkivrl.exe (PID: 7068)
- nppfuqatua.exe (PID: 7792)
- dqmbuotzxu.exe (PID: 4432)
- gaddnnykva.exe (PID: 5440)
- izsyxzrwwg.exe (PID: 7808)
- dbvqryktjx.exe (PID: 2868)
- vjbgnlyphc.exe (PID: 796)
- izsyxzrwwg.exe (PID: 6956)
- vjbgnlyphc.exe (PID: 2108)
- gmkzlqpjrc.exe (PID: 7552)
- dqmbuotzxu.exe (PID: 8144)
- ilqbkfaqoz.exe (PID: 572)
- lrgfkmjzuu.exe (PID: 2172)
- gmkzlqpjrc.exe (PID: 6868)
- ilqbkfaqoz.exe (PID: 7656)
- aiaoihjpzf.exe (PID: 6184)
- vrvounwzxb.exe (PID: 600)
- lpowynuywa.exe (PID: 8056)
- lrgfkmjzuu.exe (PID: 1740)
- ngewcpuoup.exe (PID: 7728)
- fgqzncdaxw.exe (PID: 7276)
- aiaoihjpzf.exe (PID: 3056)
- vrvounwzxb.exe (PID: 2080)
- lpowynuywa.exe (PID: 2672)
- ngewcpuoup.exe (PID: 7416)
- ycisjlittj.exe (PID: 5256)
- fgqzncdaxw.exe (PID: 7084)
- ycisjlittj.exe (PID: 8016)
- icfsteusxx.exe (PID: 8168)
- lexngykmbg.exe (PID: 7088)
- yofqtukkgt.exe (PID: 7744)
- icfsteusxx.exe (PID: 8088)
- snfjcegjph.exe (PID: 1560)
- lexngykmbg.exe (PID: 5372)
- skfhycmpgc.exe (PID: 2864)
- anfpcsiwsp.exe (PID: 3708)
- nivcbzbogz.exe (PID: 8100)
- snfjcegjph.exe (PID: 2268)
- yofqtukkgt.exe (PID: 1516)
- anfpcsiwsp.exe (PID: 7788)
- qokscracdj.exe (PID: 6972)
- viucigxcoi.exe (PID: 5684)
- nivcbzbogz.exe (PID: 4584)
- skfhycmpgc.exe (PID: 7472)
- viucigxcoi.exe (PID: 5232)
- cfevrgjeeg.exe (PID: 7992)
- soztejubgy.exe (PID: 4016)
- qokscracdj.exe (PID: 2884)
- czaoqpodwr.exe (PID: 5500)
- njbxuzdgbg.exe (PID: 2572)
- soztejubgy.exe (PID: 2492)
- cfevrgjeeg.exe (PID: 6416)
- pmeigbzvzh.exe (PID: 2176)
- pirxplllek.exe (PID: 5552)
- czaoqpodwr.exe (PID: 3000)
- keylvyjyad.exe (PID: 6396)
- njbxuzdgbg.exe (PID: 708)
- pmeigbzvzh.exe (PID: 1380)
- caywraojoq.exe (PID: 7744)
- pirxplllek.exe (PID: 2028)
- vlmbkfmhqy.exe (PID: 3552)
- keylvyjyad.exe (PID: 4108)
- hqfbkvudsj.exe (PID: 8016)
- fzzhlgjvvl.exe (PID: 2328)
- hqfbkvudsj.exe (PID: 8100)
- caywraojoq.exe (PID: 7404)
- vlmbkfmhqy.exe (PID: 576)
- psxgpipqhl.exe (PID: 4016)
- fzzhlgjvvl.exe (PID: 2816)
- zypigsazyh.exe (PID: 2284)
- zgawcoxedg.exe (PID: 7988)
- cuebmurspj.exe (PID: 2164)
- pljbiomhzn.exe (PID: 2652)
- sgmzncgjgn.exe (PID: 5208)
- psxgpipqhl.exe (PID: 7024)
- zypigsazyh.exe (PID: 4960)
- cuebmurspj.exe (PID: 1476)
- zgawcoxedg.exe (PID: 6292)
- cuocxrzfaj.exe (PID: 1764)
- pljbiomhzn.exe (PID: 1604)
- sgmzncgjgn.exe (PID: 2176)
- rzxpvjgivq.exe (PID: 2492)
- rzxpvjgivq.exe (PID: 7372)
- cuocxrzfaj.exe (PID: 1924)
- xipvivhfsi.exe (PID: 7440)
- euzlwjcrpo.exe (PID: 5580)
- eukowlprtw.exe (PID: 7068)
- xipvivhfsi.exe (PID: 7220)
- eczuuiwbve.exe (PID: 2832)
- euzlwjcrpo.exe (PID: 3000)
- bdsmjtncda.exe (PID: 560)
- eukowlprtw.exe (PID: 708)
- mosqbwxfmq.exe (PID: 2652)
- uzsxfusvrv.exe (PID: 6924)
- uzsxfusvrv.exe (PID: 5404)
- mosqbwxfmq.exe (PID: 4016)
- eczuuiwbve.exe (PID: 6720)
- hbagoozgbr.exe (PID: 7744)
- bdsmjtncda.exe (PID: 532)
- hbagoozgbr.exe (PID: 6772)
- ueryyvrpsh.exe (PID: 2492)
- jlavgkhmiz.exe (PID: 7548)
- onvzbwiaun.exe (PID: 1764)
- elocfqwuye.exe (PID: 1476)
- jlavgkhmiz.exe (PID: 2996)
- ueryyvrpsh.exe (PID: 7084)
- hrdsgichmx.exe (PID: 5296)
- onvzbwiaun.exe (PID: 7032)
- rfgabxtnjs.exe (PID: 3116)
- elocfqwuye.exe (PID: 7440)
- jruldodcef.exe (PID: 1924)
- rfgabxtnjs.exe (PID: 6480)
- bjgouiikhv.exe (PID: 2116)
- hrdsgichmx.exe (PID: 6292)
- jvgegzdsla.exe (PID: 1688)
- tjjutotxid.exe (PID: 5232)
- bjgouiikhv.exe (PID: 2896)
- jruldodcef.exe (PID: 2832)
- jvgegzdsla.exe (PID: 560)
- efgtzeuccn.exe (PID: 7780)
- tjjutotxid.exe (PID: 2400)
- zwmnkfbpri.exe (PID: 6124)
- zwmnkfbpri.exe (PID: 8164)
- bkdevtipzu.exe (PID: 4284)
- efgtzeuccn.exe (PID: 7196)
- yeisetohqr.exe (PID: 6156)
- gxipnxzywl.exe (PID: 4748)
- bkdevtipzu.exe (PID: 2652)
- wgoyrdxvcl.exe (PID: 7280)
- gxipnxzywl.exe (PID: 2480)
- jezcurobuo.exe (PID: 4644)
- yeisetohqr.exe (PID: 4960)
- lkmdvekdws.exe (PID: 6752)
- jezcurobuo.exe (PID: 2900)
- wgoyrdxvcl.exe (PID: 7068)
- itvlxjniyf.exe (PID: 5500)
- lkmdvekdws.exe (PID: 5580)
- bftbkadpgy.exe (PID: 1924)
- dayxkinzxp.exe (PID: 4208)
- itvlxjniyf.exe (PID: 2156)
- bftbkadpgy.exe (PID: 7736)
- dayxkinzxp.exe (PID: 2868)
- qreckkxgbk.exe (PID: 2116)
- letiqyvmxl.exe (PID: 7032)
- vadylndrtg.exe (PID: 6724)
- letiqyvmxl.exe (PID: 2876)
- jnotcqhwce.exe (PID: 7956)
- vadylndrtg.exe (PID: 8164)
- qreckkxgbk.exe (PID: 7788)
- omuukeryey.exe (PID: 4868)
- jnotcqhwce.exe (PID: 7672)
- omuukeryey.exe (PID: 5696)
- ypuhwbkstr.exe (PID: 4488)
- neerqyggmi.exe (PID: 688)
- neerqyggmi.exe (PID: 1020)
- gibvdepsxj.exe (PID: 5192)
- ypuhwbkstr.exe (PID: 3000)
- gibvdepsxj.exe (PID: 7360)
- dyktkxkhge.exe (PID: 6184)
- nrcocittiu.exe (PID: 6388)
- xucchfmvyn.exe (PID: 1320)
- nrcocittiu.exe (PID: 2400)
- pxaauxccoh.exe (PID: 4432)
- dyktkxkhge.exe (PID: 5040)
- nvifhdnajp.exe (PID: 2492)
- xucchfmvyn.exe (PID: 2288)
- ffwlailrtx.exe (PID: 2268)
- fjjojzzbou.exe (PID: 7416)
- pxaauxccoh.exe (PID: 7908)
- nvifhdnajp.exe (PID: 1924)
- fjjojzzbou.exe (PID: 7068)
- ffwlailrtx.exe (PID: 2480)
- dadbqfedcd.exe (PID: 5580)
- dadbqfedcd.exe (PID: 5196)
- pdtxevsxel.exe (PID: 7420)
- lxqsykutai.exe (PID: 8180)
- cxkqobjgua.exe (PID: 7736)
- utyyljbzff.exe (PID: 2436)
- cmibrrkujx.exe (PID: 4804)
- pdtxevsxel.exe (PID: 2156)
- lxqsykutai.exe (PID: 6724)
- cmhwfkmvoz.exe (PID: 7596)
- sogbmnsdrj.exe (PID: 7812)
- utyyljbzff.exe (PID: 6480)
- cxkqobjgua.exe (PID: 3124)
- cmhwfkmvoz.exe (PID: 7740)
- cmibrrkujx.exe (PID: 8044)
- xtchtjmuuc.exe (PID: 7548)
- sdsqzunocw.exe (PID: 4016)
- sdfaosdxwi.exe (PID: 7028)
- sogbmnsdrj.exe (PID: 4744)
- xtchtjmuuc.exe (PID: 708)
- sdfaosdxwi.exe (PID: 7160)
- xxtbpyltyn.exe (PID: 5404)
- atychuwqkn.exe (PID: 1604)
- sdsqzunocw.exe (PID: 2316)
- pywfoaybce.exe (PID: 4956)
- enpqsmmnyu.exe (PID: 6320)
- pywfoaybce.exe (PID: 4732)
- prrgtpskoe.exe (PID: 144)
- xxtbpyltyn.exe (PID: 4488)
- atychuwqkn.exe (PID: 7244)
- enpqsmmnyu.exe (PID: 8116)
- pneqbfgmjb.exe (PID: 2896)
- pnoopaovkl.exe (PID: 6704)
- prrgtpskoe.exe (PID: 1020)
- pneqbfgmjb.exe (PID: 7084)
- pnoopaovkl.exe (PID: 6416)
- sfixedzcop.exe (PID: 2108)
- sfixedzcop.exe (PID: 3084)
- cmgowgbywk.exe (PID: 2288)
- hkyfzgqkle.exe (PID: 5580)
- phwhwtwvnk.exe (PID: 3948)
- hkyfzgqkle.exe (PID: 5040)
- rzktpvrurt.exe (PID: 5368)
- mbrumwdich.exe (PID: 7400)
- kkkczucsvr.exe (PID: 6064)
- cmgowgbywk.exe (PID: 2400)
- phwhwtwvnk.exe (PID: 7908)
- zhlhxurvrq.exe (PID: 4696)
- mbrumwdich.exe (PID: 2436)
- rzktpvrurt.exe (PID: 8180)
- koysbtwmln.exe (PID: 6328)
- zhlhxurvrq.exe (PID: 7580)
- kkkczucsvr.exe (PID: 2980)
- enlbmmdmah.exe (PID: 6340)
- eyclecnxvt.exe (PID: 4620)
- koysbtwmln.exe (PID: 7460)
- enlbmmdmah.exe (PID: 4228)
- eyclecnxvt.exe (PID: 1692)
- pnacwfqleo.exe (PID: 8020)
- wjmntlijzv.exe (PID: 7808)
- eoxfwdqrpq.exe (PID: 4608)
- pnacwfqleo.exe (PID: 7396)
- bpolhvgvcx.exe (PID: 4956)
- wjmntlijzv.exe (PID: 7248)
- eoxfwdqrpq.exe (PID: 7172)
- esswfjgpfd.exe (PID: 6124)
- bpolhvgvcx.exe (PID: 8164)
Reads the computer name
- csxocllnng.exe (PID: 6780)
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 7548)
- fylqscmjht.exe (PID: 532)
- kprrzqdlin.exe (PID: 4260)
- 09e4b890cfb48bd51937754512d22b96976a965965505b822e156697e5768aaf.exe (PID: 1600)
- pnohnjcpvo.exe (PID: 5484)
- hicokyuhob.exe (PID: 4696)
- fylqscmjht.exe (PID: 2176)
- csxocllnng.exe (PID: 8084)
- xrymecfmql.exe (PID: 2288)
- hicokyuhob.exe (PID: 5708)
- pnohnjcpvo.exe (PID: 8180)
- zxewuuoikf.exe (PID: 2188)
- kprrzqdlin.exe (PID: 7244)
- zjqpiyscsr.exe (PID: 3516)
- zxewuuoikf.exe (PID: 8164)
- zjqpiyscsr.exe (PID: 3432)
- pcwpdtslad.exe (PID: 4208)
- xrymecfmql.exe (PID: 4452)
- pcwpdtslad.exe (PID: 7416)
- kmaqgdjokj.exe (PID: 6176)
- hyzgvzdacw.exe (PID: 1924)
- eoqeutxqer.exe (PID: 332)
- kmaqgdjokj.exe (PID: 7548)
- utaxmabstw.exe (PID: 7440)
- hyzgvzdacw.exe (PID: 4608)
- utaxmabstw.exe (PID: 560)
- zgtfxcobnx.exe (PID: 2852)
- hvhsjmlubt.exe (PID: 5424)
- zhnjnixtcx.exe (PID: 1212)
- eoqeutxqer.exe (PID: 7956)
- zgtfxcobnx.exe (PID: 2600)
- fqxxbmgqhi.exe (PID: 3000)
- kdskgeqqwp.exe (PID: 7068)
- ejghdhqhnb.exe (PID: 708)
- zhnjnixtcx.exe (PID: 7728)
- urunplbepl.exe (PID: 3268)
- hvhsjmlubt.exe (PID: 8032)
- mnsayayodo.exe (PID: 2008)
- fqxxbmgqhi.exe (PID: 2504)
- ejghdhqhnb.exe (PID: 2720)
- zpzvdmaqku.exe (PID: 7776)
- zpzvdmaqku.exe (PID: 6752)
- kdskgeqqwp.exe (PID: 2572)
- mnsayayodo.exe (PID: 5340)
- rlynrnfiyh.exe (PID: 2080)
- urunplbepl.exe (PID: 8116)
- rlynrnfiyh.exe (PID: 1320)
- rixbzgglxu.exe (PID: 3160)
- uvrqvrsyin.exe (PID: 3196)
- uvrqvrsyin.exe (PID: 7360)
- mwoskcmmxo.exe (PID: 7556)
- jmwpasdivy.exe (PID: 6660)
- mpyqypuugx.exe (PID: 7608)
- zncysfxtbi.exe (PID: 7012)
- jmwpasdivy.exe (PID: 1924)
- rixbzgglxu.exe (PID: 4488)
- whxlizdfqf.exe (PID: 3552)
- mwoskcmmxo.exe (PID: 2400)
- mpyqypuugx.exe (PID: 6156)
- zncysfxtbi.exe (PID: 7220)
- mtwefhvfel.exe (PID: 6416)
- wlkexlizxr.exe (PID: 1020)
- whxlizdfqf.exe (PID: 2756)
- odxzjlbvoj.exe (PID: 4956)
- wlkexlizxr.exe (PID: 2360)
- mtwefhvfel.exe (PID: 2328)
- odxzjlbvoj.exe (PID: 8144)
- dbsissextr.exe (PID: 764)
- gompxdqcvc.exe (PID: 7788)
- eqsyppkujn.exe (PID: 2392)
- tcqrexcuys.exe (PID: 1604)
- gompxdqcvc.exe (PID: 6196)
- oqhhyifunb.exe (PID: 5508)
- dbsissextr.exe (PID: 2876)
- raxxxljoul.exe (PID: 5196)
- trpchfdaup.exe (PID: 7736)
- eqsyppkujn.exe (PID: 2188)
- oqhhyifunb.exe (PID: 2172)
- blwmewuzju.exe (PID: 8000)
- tcqrexcuys.exe (PID: 6340)
- bslsveywdt.exe (PID: 2164)
- trpchfdaup.exe (PID: 2080)
- orzydgqdhv.exe (PID: 4676)
- blwmewuzju.exe (PID: 5292)
- egbiwvejae.exe (PID: 6868)
- raxxxljoul.exe (PID: 3056)
- bslsveywdt.exe (PID: 2856)
- qforbihvgw.exe (PID: 7596)
- egbiwvejae.exe (PID: 1432)
- oojxctwojr.exe (PID: 5868)
- jfcszigikn.exe (PID: 6836)
- orzydgqdhv.exe (PID: 5368)
- whjvwuijsk.exe (PID: 7276)
- tadkhcgoyy.exe (PID: 7012)
- qforbihvgw.exe (PID: 2268)
- tadkhcgoyy.exe (PID: 3260)
- whjvwuijsk.exe (PID: 4584)
- oojxctwojr.exe (PID: 2812)
- jfcszigikn.exe (PID: 7608)
- amdvpeusmt.exe (PID: 4364)
- jnngvndnql.exe (PID: 2352)
- gvudjjypof.exe (PID: 1560)
- amdvpeusmt.exe (PID: 5580)
- aunbspwkau.exe (PID: 2792)
- jnngvndnql.exe (PID: 1212)
- gvudjjypof.exe (PID: 7956)
- nppfuqatua.exe (PID: 2528)
- gtduxkivrl.exe (PID: 7220)
- dbvqryktjx.exe (PID: 2328)
- izsyxzrwwg.exe (PID: 7808)
- aunbspwkau.exe (PID: 2532)
- gaddnnykva.exe (PID: 4708)
- gtduxkivrl.exe (PID: 7068)
- nppfuqatua.exe (PID: 7792)
- gaddnnykva.exe (PID: 5440)
- dqmbuotzxu.exe (PID: 4432)
- izsyxzrwwg.exe (PID: 6956)
- vjbgnlyphc.exe (PID: 796)
- dbvqryktjx.exe (PID: 2868)
- ilqbkfaqoz.exe (PID: 572)
- vjbgnlyphc.exe (PID: 2108)
- gmkzlqpjrc.exe (PID: 7552)
- dqmbuotzxu.exe (PID: 8144)
- lrgfkmjzuu.exe (PID: 2172)
- gmkzlqpjrc.exe (PID: 6868)
- ilqbkfaqoz.exe (PID: 7656)
- aiaoihjpzf.exe (PID: 6184)
- vrvounwzxb.exe (PID: 600)
- lpowynuywa.exe (PID: 8056)
- lrgfkmjzuu.exe (PID: 1740)
- ngewcpuoup.exe (PID: 7728)
- aiaoihjpzf.exe (PID: 3056)
- vrvounwzxb.exe (PID: 2080)
- fgqzncdaxw.exe (PID: 7276)
- lpowynuywa.exe (PID: 2672)
- fgqzncdaxw.exe (PID: 7084)
- ycisjlittj.exe (PID: 5256)
- ngewcpuoup.exe (PID: 7416)
- ycisjlittj.exe (PID: 8016)
- icfsteusxx.exe (PID: 8168)
- lexngykmbg.exe (PID: 7088)
- yofqtukkgt.exe (PID: 7744)
- snfjcegjph.exe (PID: 1560)
- lexngykmbg.exe (PID: 5372)
- icfsteusxx.exe (PID: 8088)
- anfpcsiwsp.exe (PID: 3708)
- skfhycmpgc.exe (PID: 2864)
- nivcbzbogz.exe (PID: 8100)
- yofqtukkgt.exe (PID: 1516)
- snfjcegjph.exe (PID: 2268)
- viucigxcoi.exe (PID: 5684)
- anfpcsiwsp.exe (PID: 7788)
- nivcbzbogz.exe (PID: 4584)
- viucigxcoi.exe (PID: 5232)
- qokscracdj.exe (PID: 6972)
- skfhycmpgc.exe (PID: 7472)
- qokscracdj.exe (PID: 2884)
- cfevrgjeeg.exe (PID: 7992)
- czaoqpodwr.exe (PID: 5500)
- soztejubgy.exe (PID: 2492)
- njbxuzdgbg.exe (PID: 2572)
- soztejubgy.exe (PID: 4016)
- cfevrgjeeg.exe (PID: 6416)
- pmeigbzvzh.exe (PID: 2176)
- pirxplllek.exe (PID: 5552)
- czaoqpodwr.exe (PID: 3000)
- keylvyjyad.exe (PID: 6396)
- njbxuzdgbg.exe (PID: 708)
- pmeigbzvzh.exe (PID: 1380)
- pirxplllek.exe (PID: 2028)
- caywraojoq.exe (PID: 7744)
- vlmbkfmhqy.exe (PID: 3552)
- keylvyjyad.exe (PID: 4108)
- vlmbkfmhqy.exe (PID: 576)
- fzzhlgjvvl.exe (PID: 2328)
- zypigsazyh.exe (PID: 2284)
- hqfbkvudsj.exe (PID: 8016)
- caywraojoq.exe (PID: 7404)
- hqfbkvudsj.exe (PID: 8100)
- psxgpipqhl.exe (PID: 4016)
- fzzhlgjvvl.exe (PID: 2816)
- zgawcoxedg.exe (PID: 7988)
- zypigsazyh.exe (PID: 4960)
- cuebmurspj.exe (PID: 2164)
- sgmzncgjgn.exe (PID: 5208)
- pljbiomhzn.exe (PID: 2652)
- psxgpipqhl.exe (PID: 7024)
- cuebmurspj.exe (PID: 1476)
- zgawcoxedg.exe (PID: 6292)
- cuocxrzfaj.exe (PID: 1764)
- cuocxrzfaj.exe (PID: 1924)
- pljbiomhzn.exe (PID: 1604)
- sgmzncgjgn.exe (PID: 2176)
- rzxpvjgivq.exe (PID: 2492)
- euzlwjcrpo.exe (PID: 5580)
- xipvivhfsi.exe (PID: 7440)
- rzxpvjgivq.exe (PID: 7372)
- eukowlprtw.exe (PID: 7068)
- xipvivhfsi.exe (PID: 7220)
- eczuuiwbve.exe (PID: 2832)
- eukowlprtw.exe (PID: 708)
- euzlwjcrpo.exe (PID: 3000)
- bdsmjtncda.exe (PID: 560)
- mosqbwxfmq.exe (PID: 2652)
- eczuuiwbve.exe (PID: 6720)
- uzsxfusvrv.exe (PID: 6924)
- hbagoozgbr.exe (PID: 7744)
- bdsmjtncda.exe (PID: 532)
- uzsxfusvrv.exe (PID: 5404)
- mosqbwxfmq.exe (PID: 4016)
- hbagoozgbr.exe (PID: 6772)
- ueryyvrpsh.exe (PID: 2492)
- jlavgkhmiz.exe (PID: 7548)
- onvzbwiaun.exe (PID: 1764)
- ueryyvrpsh.exe (PID: 7084)
- jlavgkhmiz.exe (PID: 2996)
- elocfqwuye.exe (PID: 1476)
- onvzbwiaun.exe (PID: 7032)
- hrdsgichmx.exe (PID: 5296)
- elocfqwuye.exe (PID: 7440)
- jruldodcef.exe (PID: 1924)
- rfgabxtnjs.exe (PID: 3116)
- rfgabxtnjs.exe (PID: 6480)
- bjgouiikhv.exe (PID: 2116)
- hrdsgichmx.exe (PID: 6292)
- jvgegzdsla.exe (PID: 1688)
- jvgegzdsla.exe (PID: 560)
- tjjutotxid.exe (PID: 5232)
- bjgouiikhv.exe (PID: 2896)
- jruldodcef.exe (PID: 2832)
- tjjutotxid.exe (PID: 2400)
- efgtzeuccn.exe (PID: 7780)
- zwmnkfbpri.exe (PID: 6124)
- zwmnkfbpri.exe (PID: 8164)
- bkdevtipzu.exe (PID: 4284)
- efgtzeuccn.exe (PID: 7196)
- yeisetohqr.exe (PID: 6156)
- gxipnxzywl.exe (PID: 4748)
- jezcurobuo.exe (PID: 4644)
- wgoyrdxvcl.exe (PID: 7280)
- bkdevtipzu.exe (PID: 2652)
- gxipnxzywl.exe (PID: 2480)
- yeisetohqr.exe (PID: 4960)
- lkmdvekdws.exe (PID: 6752)
- jezcurobuo.exe (PID: 2900)
- itvlxjniyf.exe (PID: 5500)
- lkmdvekdws.exe (PID: 5580)
- wgoyrdxvcl.exe (PID: 7068)
- bftbkadpgy.exe (PID: 1924)
- dayxkinzxp.exe (PID: 4208)
- itvlxjniyf.exe (PID: 2156)
- qreckkxgbk.exe (PID: 2116)
- bftbkadpgy.exe (PID: 7736)
- dayxkinzxp.exe (PID: 2868)
- letiqyvmxl.exe (PID: 7032)
- vadylndrtg.exe (PID: 6724)
- jnotcqhwce.exe (PID: 7956)
- letiqyvmxl.exe (PID: 2876)
- omuukeryey.exe (PID: 4868)
- vadylndrtg.exe (PID: 8164)
- qreckkxgbk.exe (PID: 7788)
- jnotcqhwce.exe (PID: 7672)
- omuukeryey.exe (PID: 5696)
- ypuhwbkstr.exe (PID: 4488)
- neerqyggmi.exe (PID: 688)
- gibvdepsxj.exe (PID: 5192)
- ypuhwbkstr.exe (PID: 3000)
- neerqyggmi.exe (PID: 1020)
- gibvdepsxj.exe (PID: 7360)
- nrcocittiu.exe (PID: 6388)
- dyktkxkhge.exe (PID: 6184)
- xucchfmvyn.exe (PID: 1320)
- dyktkxkhge.exe (PID: 5040)
- nrcocittiu.exe (PID: 2400)
- pxaauxccoh.exe (PID: 4432)
- nvifhdnajp.exe (PID: 2492)
- xucchfmvyn.exe (PID: 2288)
- ffwlailrtx.exe (PID: 2268)
- nvifhdnajp.exe (PID: 1924)
- fjjojzzbou.exe (PID: 7416)
- pxaauxccoh.exe (PID: 7908)
- dadbqfedcd.exe (PID: 5580)
- fjjojzzbou.exe (PID: 7068)
- ffwlailrtx.exe (PID: 2480)
- dadbqfedcd.exe (PID: 5196)
- pdtxevsxel.exe (PID: 7420)
- lxqsykutai.exe (PID: 8180)
- cxkqobjgua.exe (PID: 7736)
- utyyljbzff.exe (PID: 2436)
- cmhwfkmvoz.exe (PID: 7596)
- lxqsykutai.exe (PID: 6724)
- cxkqobjgua.exe (PID: 3124)
- cmhwfkmvoz.exe (PID: 7740)
- pdtxevsxel.exe (PID: 2156)
- cmibrrkujx.exe (PID: 4804)
- utyyljbzff.exe (PID: 6480)
- xtchtjmuuc.exe (PID: 7548)
- sogbmnsdrj.exe (PID: 7812)
- cmibrrkujx.exe (PID: 8044)
- sdsqzunocw.exe (PID: 4016)
- sogbmnsdrj.exe (PID: 4744)
- xtchtjmuuc.exe (PID: 708)
- sdfaosdxwi.exe (PID: 7028)
- xxtbpyltyn.exe (PID: 5404)
- sdfaosdxwi.exe (PID: 7160)
- atychuwqkn.exe (PID: 1604)
- sdsqzunocw.exe (PID: 2316)
- pywfoaybce.exe (PID: 4956)
- pywfoaybce.exe (PID: 4732)
- prrgtpskoe.exe (PID: 144)
- xxtbpyltyn.exe (PID: 4488)
- enpqsmmnyu.exe (PID: 6320)
- pneqbfgmjb.exe (PID: 2896)
- atychuwqkn.exe (PID: 7244)
- enpqsmmnyu.exe (PID: 8116)
- pnoopaovkl.exe (PID: 6704)
- prrgtpskoe.exe (PID: 1020)
- pneqbfgmjb.exe (PID: 7084)
- hkyfzgqkle.exe (PID: 5580)
- sfixedzcop.exe (PID: 2108)
- pnoopaovkl.exe (PID: 6416)
- cmgowgbywk.exe (PID: 2288)
- sfixedzcop.exe (PID: 3084)
- phwhwtwvnk.exe (PID: 3948)
- hkyfzgqkle.exe (PID: 5040)
- rzktpvrurt.exe (PID: 5368)
- kkkczucsvr.exe (PID: 6064)
- cmgowgbywk.exe (PID: 2400)
- mbrumwdich.exe (PID: 7400)
- zhlhxurvrq.exe (PID: 4696)
- mbrumwdich.exe (PID: 2436)
- rzktpvrurt.exe (PID: 8180)
- phwhwtwvnk.exe (PID: 7908)
- koysbtwmln.exe (PID: 6328)
- zhlhxurvrq.exe (PID: 7580)
- eyclecnxvt.exe (PID: 4620)
- kkkczucsvr.exe (PID: 2980)
- enlbmmdmah.exe (PID: 6340)
- koysbtwmln.exe (PID: 7460)
- pnacwfqleo.exe (PID: 8020)
- wjmntlijzv.exe (PID: 7808)
- eyclecnxvt.exe (PID: 1692)
- enlbmmdmah.exe (PID: 4228)
- pnacwfqleo.exe (PID: 7396)
- bpolhvgvcx.exe (PID: 4956)
- eoxfwdqrpq.exe (PID: 4608)
- wjmntlijzv.exe (PID: 7248)
- eoxfwdqrpq.exe (PID: 7172)
- esswfjgpfd.exe (PID: 6124)
- bpolhvgvcx.exe (PID: 8164)
Checks proxy server information
- slui.exe (PID: 2536)
Reads the software policy settings
- slui.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.5) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Win16/32 Executable Delphi generic (4.2) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:07:15 17:54:42+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1421312 |
| InitializedDataSize: | 536576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x87f838 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | 固定打怪,新手村任务,门派任务 |
| ProductName: | 千年3_新手任务 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | QQ:6365272 |
| LegalCopyright: | QQ:6365272 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
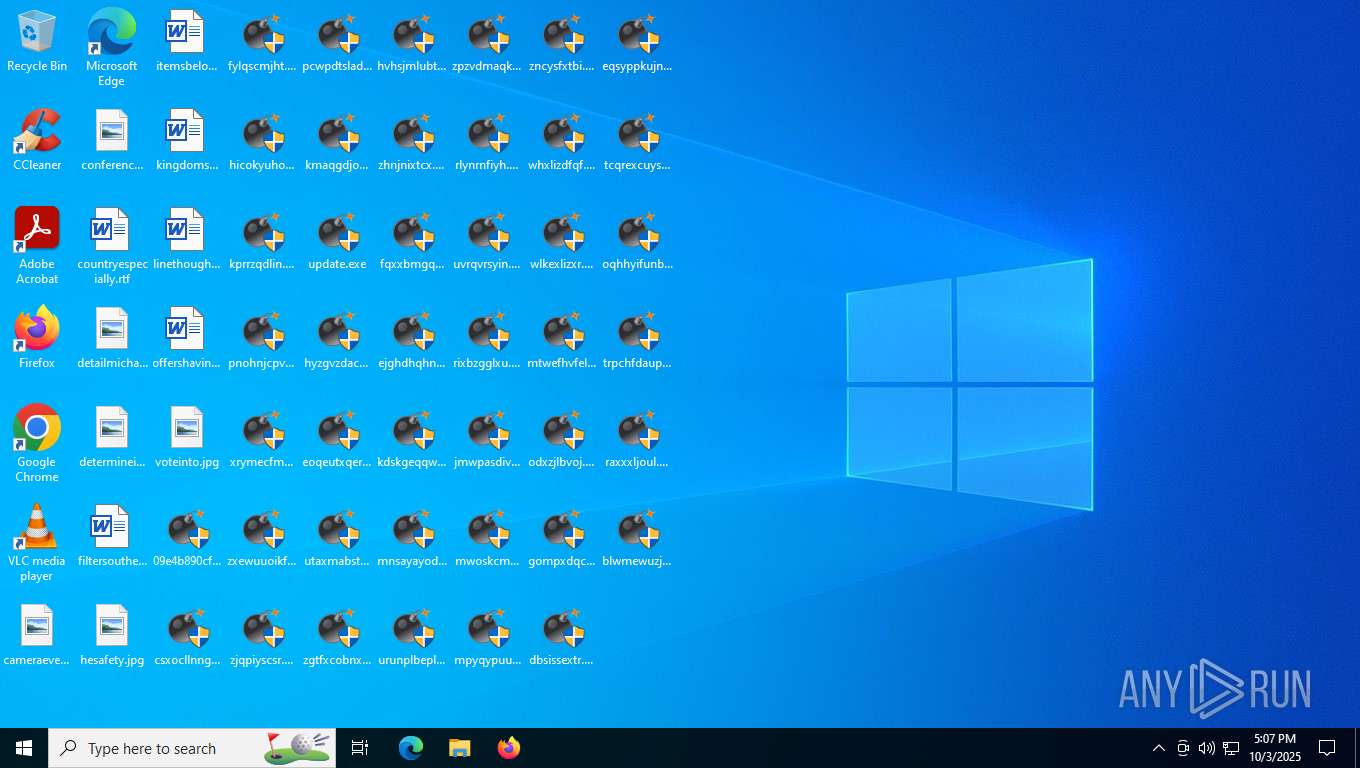
Total processes
524
Monitored processes
355
Malicious processes
62
Suspicious processes
60
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | C:\Users\admin\Desktop\prrgtpskoe.exe update pneqbfgmjb.exe | C:\Users\admin\Desktop\prrgtpskoe.exe | prrgtpskoe.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 332 | C:\Users\admin\Desktop\eoqeutxqer.exe update utaxmabstw.exe | C:\Users\admin\Desktop\eoqeutxqer.exe | eoqeutxqer.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 532 | C:\Users\admin\Desktop\fylqscmjht.exe update hicokyuhob.exe | C:\Users\admin\Desktop\fylqscmjht.exe | fylqscmjht.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 532 | C:\Users\admin\Desktop\bdsmjtncda.exe | C:\Users\admin\Desktop\bdsmjtncda.exe | — | eczuuiwbve.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 560 | C:\Users\admin\Desktop\utaxmabstw.exe | C:\Users\admin\Desktop\utaxmabstw.exe | — | eoqeutxqer.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 560 | C:\Users\admin\Desktop\bdsmjtncda.exe update uzsxfusvrv.exe | C:\Users\admin\Desktop\bdsmjtncda.exe | bdsmjtncda.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 560 | C:\Users\admin\Desktop\jvgegzdsla.exe | C:\Users\admin\Desktop\jvgegzdsla.exe | — | jruldodcef.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 572 | C:\Users\admin\Desktop\ilqbkfaqoz.exe update gmkzlqpjrc.exe | C:\Users\admin\Desktop\ilqbkfaqoz.exe | ilqbkfaqoz.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 576 | C:\Users\admin\Desktop\vlmbkfmhqy.exe | C:\Users\admin\Desktop\vlmbkfmhqy.exe | — | caywraojoq.exe | |||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 600 | C:\Users\admin\Desktop\vrvounwzxb.exe update aiaoihjpzf.exe | C:\Users\admin\Desktop\vrvounwzxb.exe | vrvounwzxb.exe | ||||||||||||
User: admin Company: QQ:6365272 Integrity Level: HIGH Description: 固定打怪,新手村任务,门派任务 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
65 002
Read events
65 002
Write events
0
Delete events
0
Modification events
Executable files
177
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4208 | pcwpdtslad.exe | C:\Users\admin\Desktop\kmaqgdjokj.exe | executable | |
MD5:9B51A26BFF167B171649F8388468BD24 | SHA256:9357D8C55B71D3CF094DC2358A683AF0E5322E85761EBD6DA1F316793DD39FDD | |||
| 3516 | zjqpiyscsr.exe | C:\Users\admin\Desktop\pcwpdtslad.exe | executable | |
MD5:CF1A1D09A686153F4653D13BA09EDD7C | SHA256:AD412A2F278CE14A40F02E5DB14A6F35EC084223C8EE2A69F1CBDE71A5514496 | |||
| 8084 | csxocllnng.exe | C:\Users\admin\Desktop\update.exe | executable | |
MD5:E0E91564D4D03B0B01421A469DEAD414 | SHA256:F343B3D7DD03B60E05494E5F4B5D1E5C240E528F0A9AEFA9A19DBBA203698CFD | |||
| 4260 | kprrzqdlin.exe | C:\Users\admin\Desktop\pnohnjcpvo.exe | executable | |
MD5:3C9966FCCE4DBF1A45C2A23A0E41E3B7 | SHA256:1CC4858710F8C4E592B72FCDF7FE6FA28360D99391ED6DCE6E5B2B1E4EC8F4C1 | |||
| 2288 | xrymecfmql.exe | C:\Users\admin\Desktop\zxewuuoikf.exe | executable | |
MD5:4B0C28DDA400833AE429E969B65C183E | SHA256:C5017134E9C608839B592F3119A657D91495CE7E513B1B8C2507734F3A610F26 | |||
| 2852 | zgtfxcobnx.exe | C:\Users\admin\Desktop\hvhsjmlubt.exe | executable | |
MD5:AEA463926CC4C54EE571E8C21FC9A232 | SHA256:6C8C03EAB57D4DB9EC3DC1FA7EBD1A171F9C5E93F4A403105FE87F7A998BE613 | |||
| 6176 | kmaqgdjokj.exe | C:\Users\admin\Desktop\hyzgvzdacw.exe | executable | |
MD5:CB93BCF90D6DF00DC5D2BEF600CFD064 | SHA256:B7E368AA498DB9703E9D8C18D760582BC458164B5842D2B2CD8C4DDA3BCC5F26 | |||
| 1924 | hyzgvzdacw.exe | C:\Users\admin\Desktop\eoqeutxqer.exe | executable | |
MD5:83CDB64AF6CF1181AE9C73FE93546BE0 | SHA256:EF1C08321808405A6DD15B1E069CE89FB4D883B6C1B97A43985EFFB6D3C9349C | |||
| 2188 | zxewuuoikf.exe | C:\Users\admin\Desktop\zjqpiyscsr.exe | executable | |
MD5:3368820B48C8C483BA39262873636109 | SHA256:1A28EED71CFCC01733C532AB6D913585727764964B52E8A0BF38BB4804EB57E8 | |||
| 4696 | hicokyuhob.exe | C:\Users\admin\Desktop\kprrzqdlin.exe | executable | |
MD5:6118C1FFD8FBB50821B4EE408FE91560 | SHA256:597D015FFDA15580A5A2B0507E0706D6E545E622D95ABC66C331B87FF0819AA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
44
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 204 | 92.123.104.4:443 | https://www.bing.com/web/xlsc.aspx?t=5&dl=1&wsbc=1 | unknown | — | — | unknown |
— | — | GET | 200 | 92.123.104.4:443 | https://www.bing.com/DSB/search?dsbmr=1&format=dsbjson&client=windowsminiserp&dsbschemaversion=1.1&dsbminiserp=1&q=q&cc=US&setlang=en-us&clientDateTime=10%2F3%2F2025%2C%205%3A07%3A59%20PM | unknown | binary | 59.8 Kb | unknown |
— | — | POST | 200 | 40.126.32.140:443 | https://login.live.com/RST2.srf | US | xml | 11.0 Kb | unknown |
— | — | POST | 200 | 20.190.160.3:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | unknown |
— | — | POST | 200 | 20.190.160.130:443 | https://login.live.com/RST2.srf | US | xml | 11.2 Kb | unknown |
— | — | GET | 200 | 92.123.104.63:443 | https://www.bing.com/th?id=ODSWG.8229b0e5-fa8c-4e4a-af74-69717698b903&pid=dsb | unknown | image | 4.62 Kb | unknown |
— | — | POST | 200 | 20.190.160.64:443 | https://login.live.com/RST2.srf | US | xml | 11.2 Kb | unknown |
— | — | POST | 200 | 40.126.32.68:443 | https://login.live.com/RST2.srf | US | xml | 11.2 Kb | unknown |
— | — | POST | 200 | 40.126.32.74:443 | https://login.live.com/RST2.srf | US | xml | 11.3 Kb | unknown |
— | — | GET | 200 | 20.223.35.26:443 | https://arc.msn.com/v3/Delivery/Placement?pubid=da63df93-3dbc-42ae-a505-b34988683ac7&pid=88000045&adm=2&w=1&h=1&wpx=1&hpx=1&fmt=json&cltp=app&dim=le&rafb=0&nct=1&pm=1&cfmt=text,image,poly&sft=jpeg,png,gif&topt=1&poptin=0&localid=w:AC7699B0-48EA-FD22-C8DC-06A02098A0F0&ctry=US&time=20251003T170806Z&lc=en-US&pl=en-US&idtp=mid&uid=9115d6d1-9f4e-4053-9297-2a8c833b3912&aid=00000000-0000-0000-0000-000000000000&ua=WindowsShellClient%2F9.0.40929.0%20%28Windows%29&asid=49fbed84f91f41a586b3d8c0279dac73&ctmode=MultiSession&arch=x64&betaedgever=0.0.0.0&canedgever=0.0.0.0&cdm=1&cdmver=10.0.19041.3636&currsel=137271744000000000&devedgever=0.0.0.0&devfam=Windows.Desktop&devform=Unknown&devosver=10.0.19045.4046&disphorzres=1360&dispsize=16.3&dispvertres=768&fosver=16299&isu=0&lo=4245667&metered=false&nettype=ethernet&npid=sc-88000045&oemName=DELL&oemid=DELL&ossku=Professional&prevosver=15063&smBiosDm=DELL&stabedgever=133.0.3065.92&tl=2&tsu=1636197&waasBldFlt=1&waasCfgExp=1&waasCfgSet=1&waasRetail=1&waasRing=&svoffered=2 | US | binary | 3.21 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6016 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4644 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.58:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6016 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5948 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4804 | slui.exe | 4.154.185.43:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5224 | SearchApp.exe | 92.123.104.62:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4740 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |