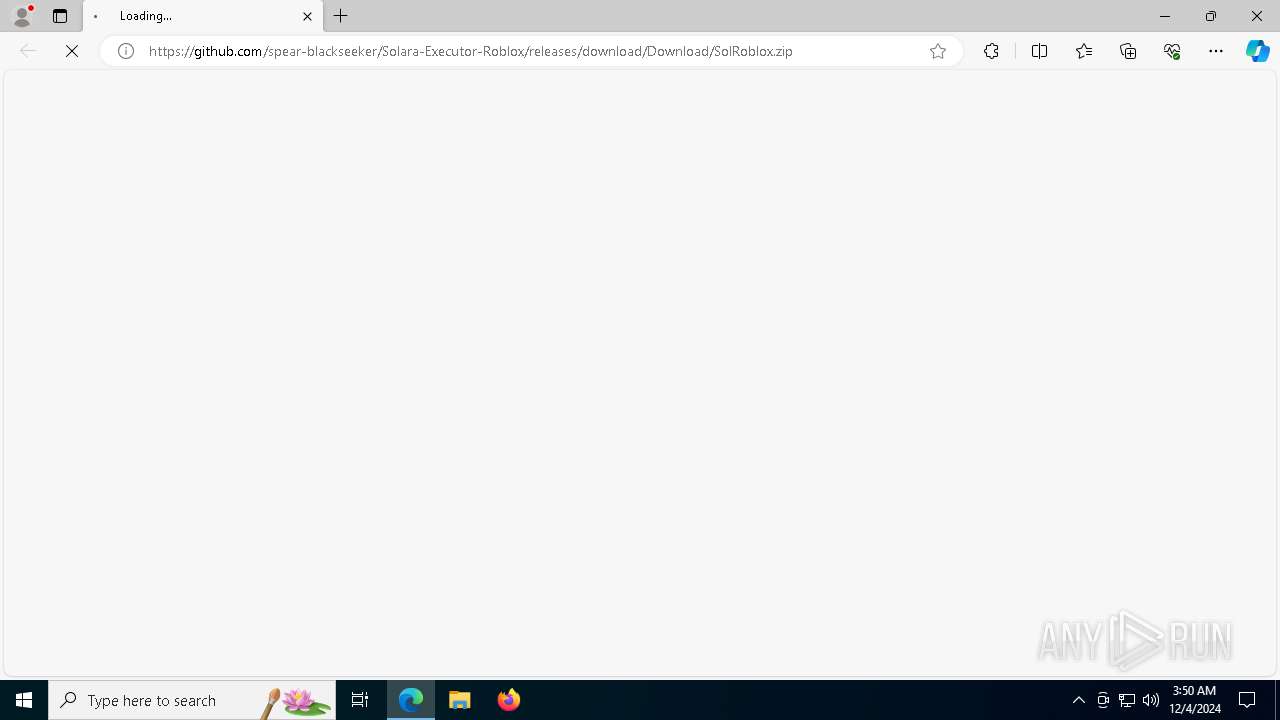
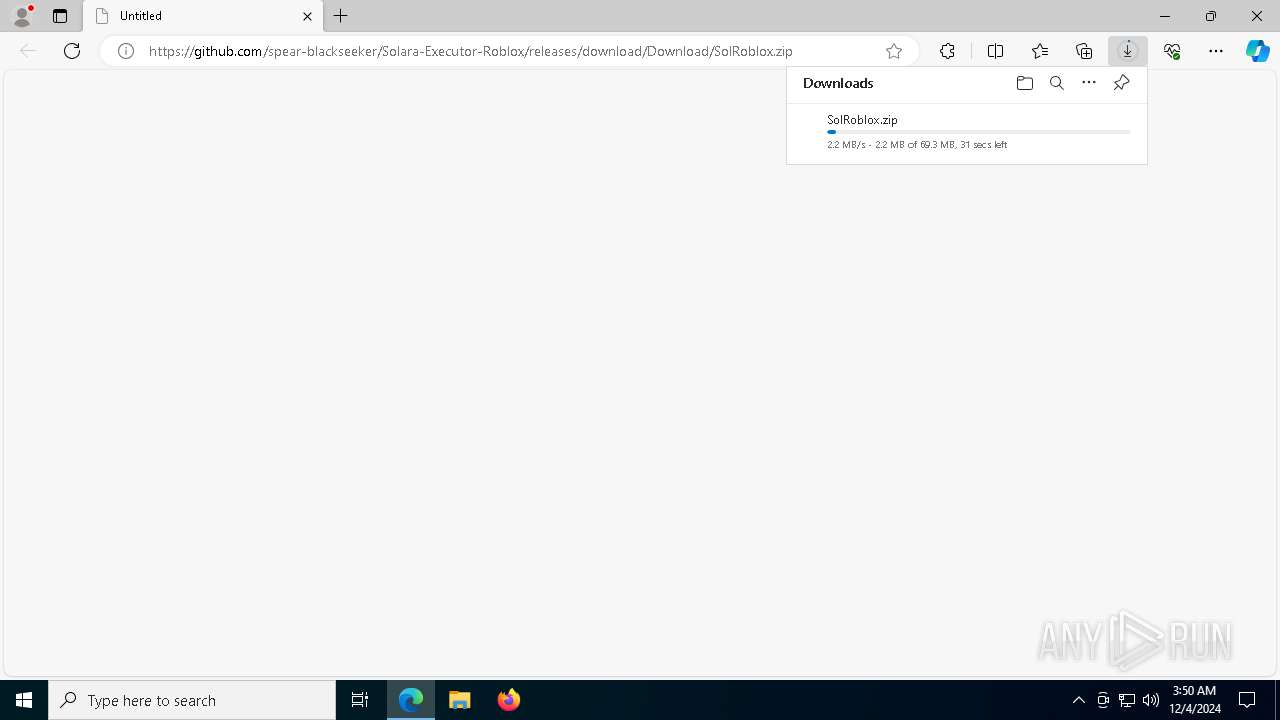
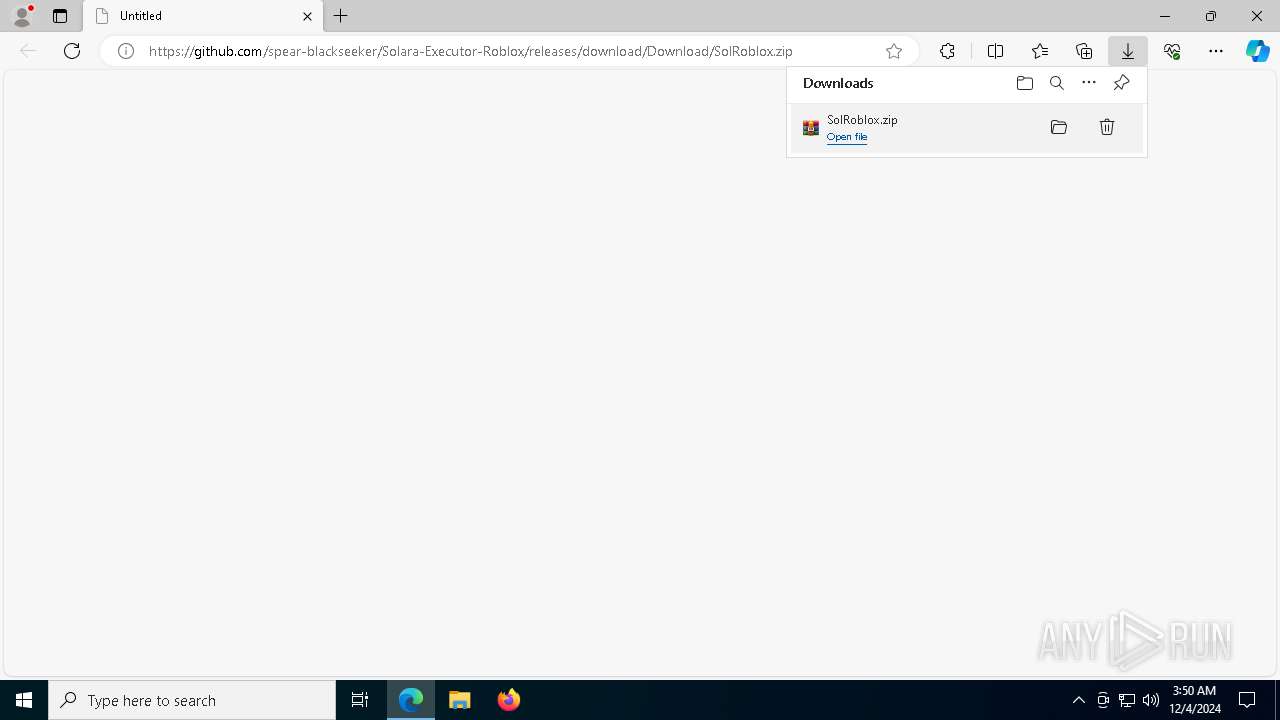
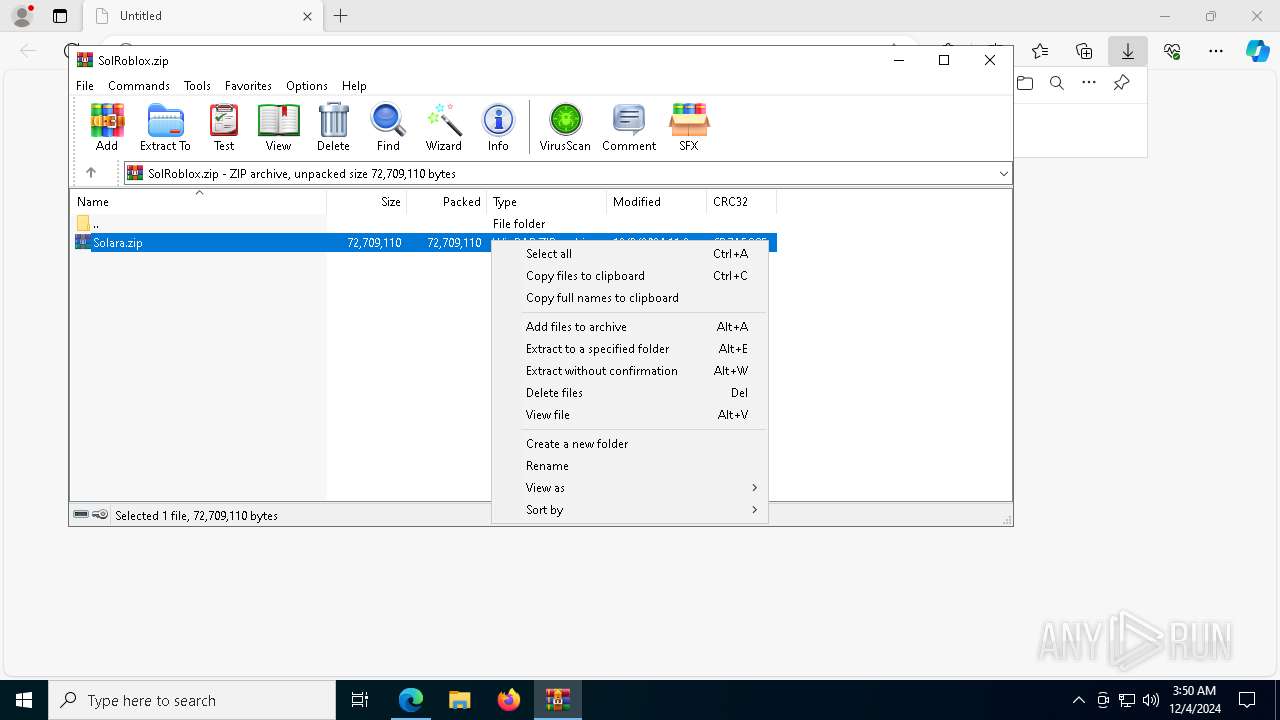
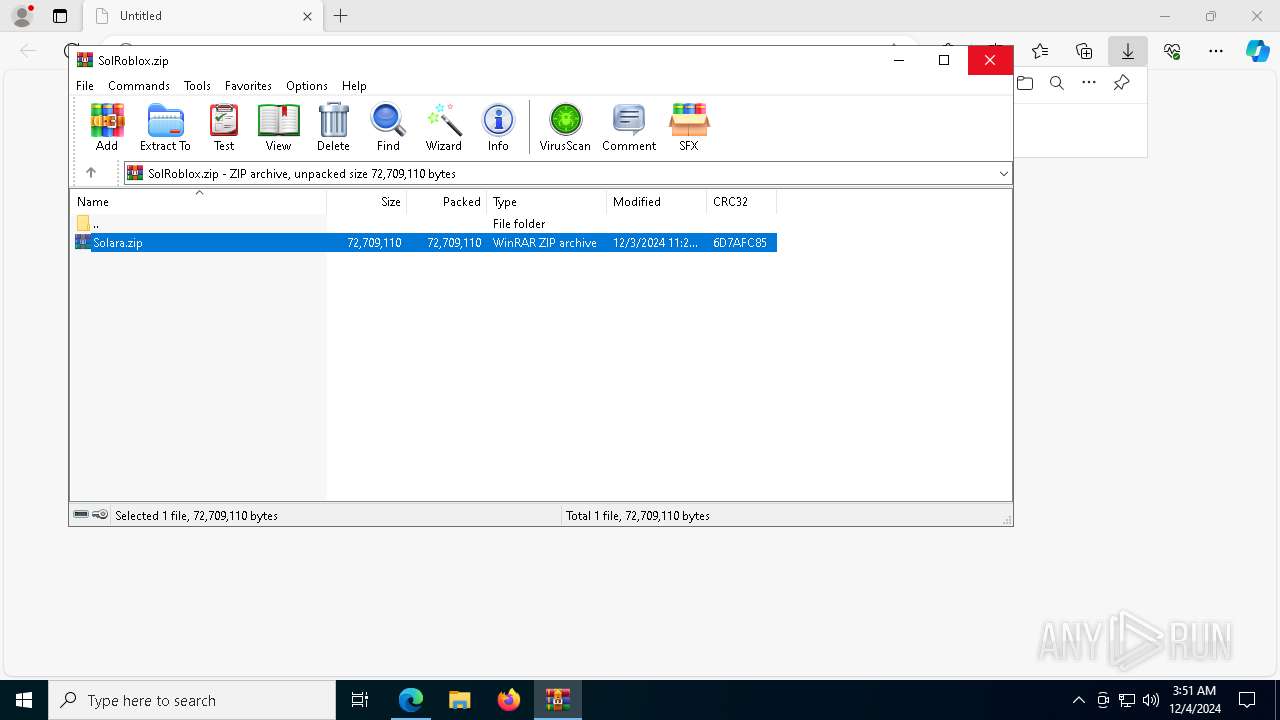
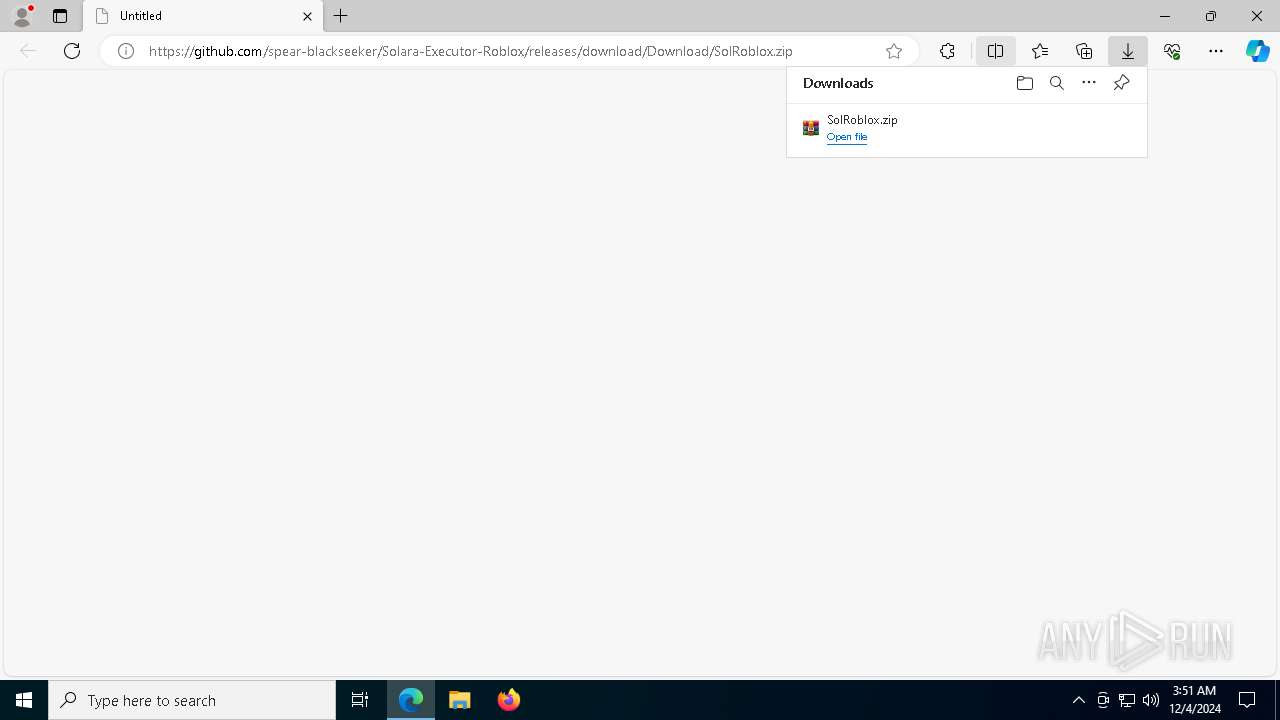
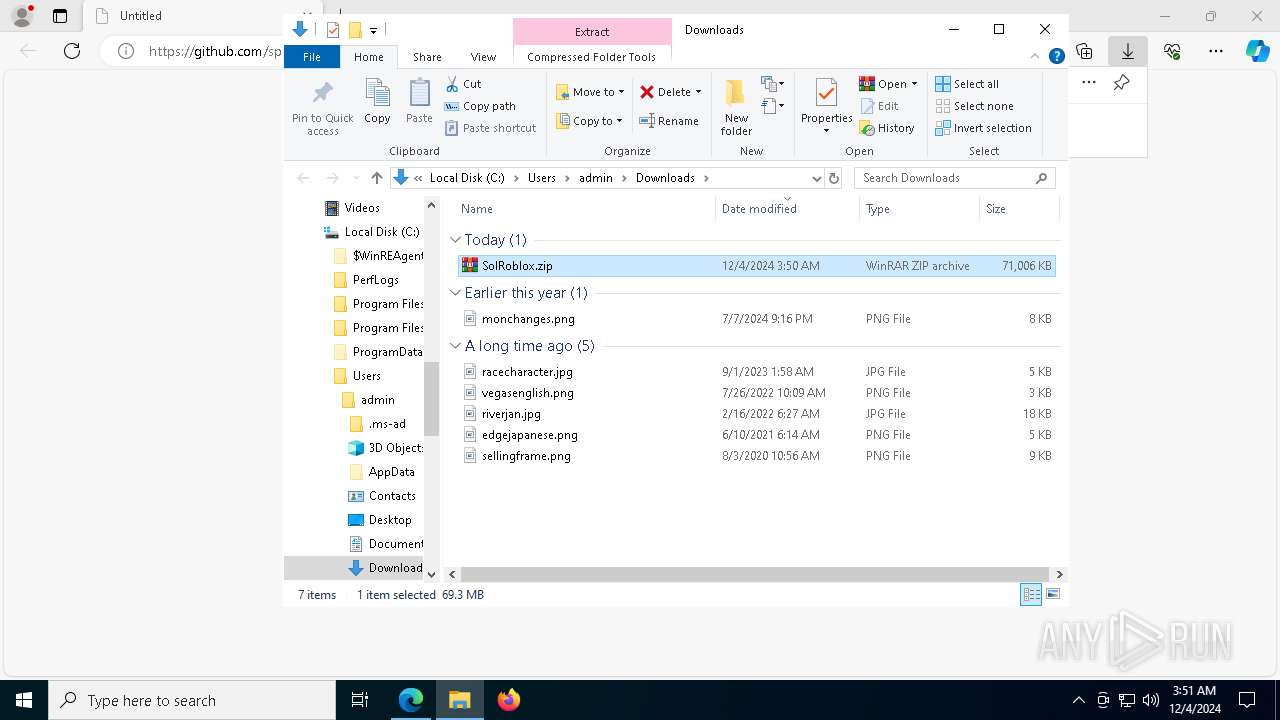
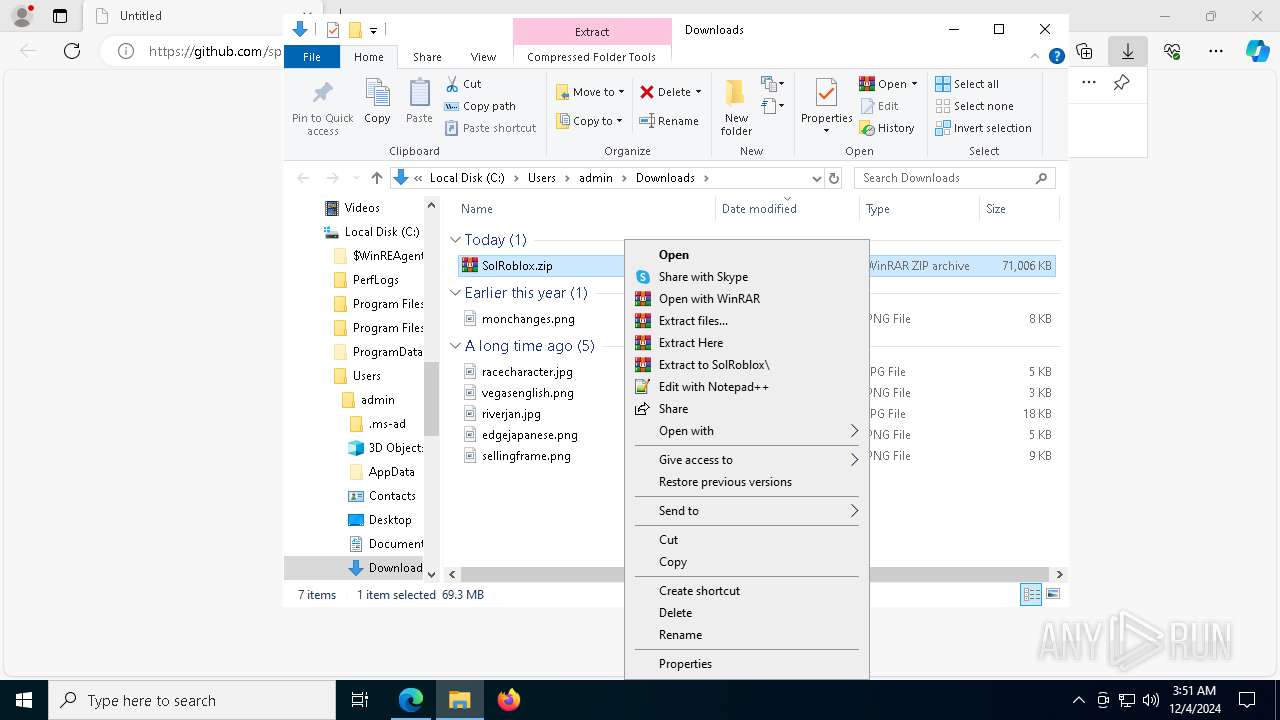
| URL: | https://github.com/spear-blackseeker/Solara-Executor-Roblox/releases/download/Download/SolRoblox.zip |
| Full analysis: | https://app.any.run/tasks/07a6e83c-31db-43f7-bb05-b95117809ff8 |
| Verdict: | Malicious activity |
| Threats: | Meduza Stealer is an information-stealing malware primarily targeting Windows systems, designed to harvest sensitive data such as login credentials, browsing histories, cookies, cryptocurrency wallets, and password manager data. It has advanced anti-detection mechanisms, allowing it to evade many antivirus programs. The malware is distributed through various means, including phishing emails and malicious links. It’s marketed on underground forums and Telegram channels. |
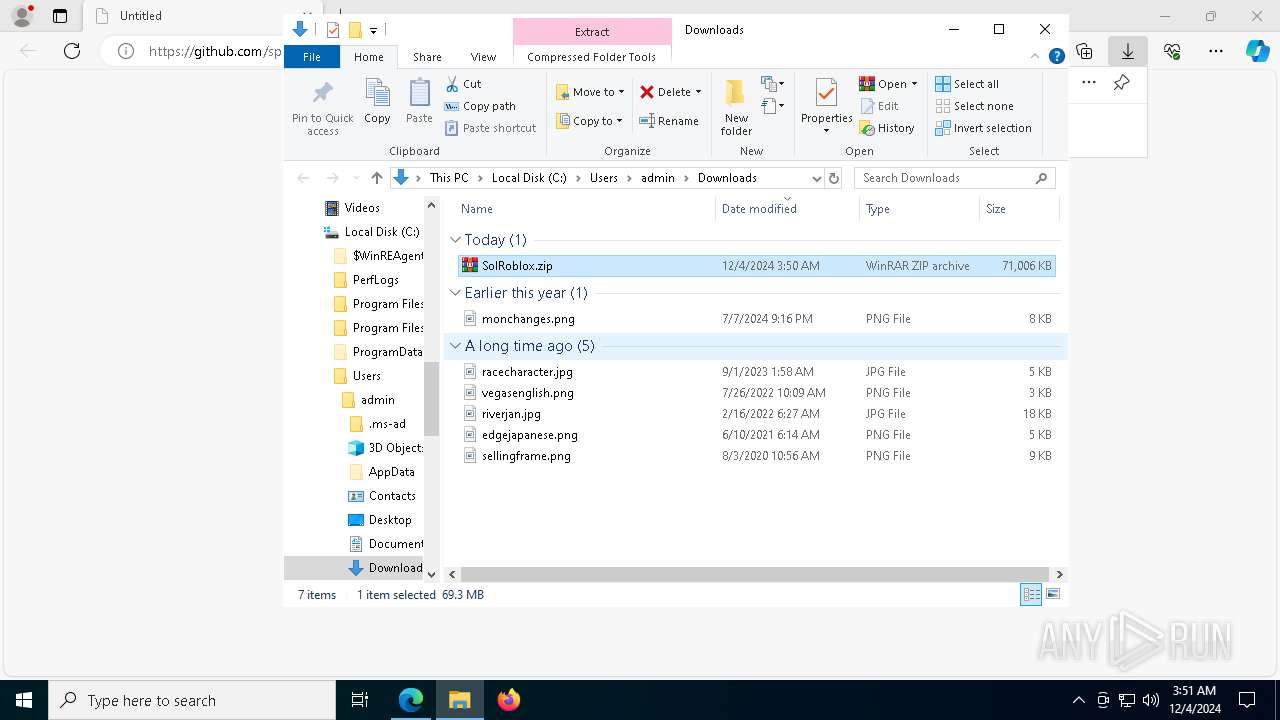
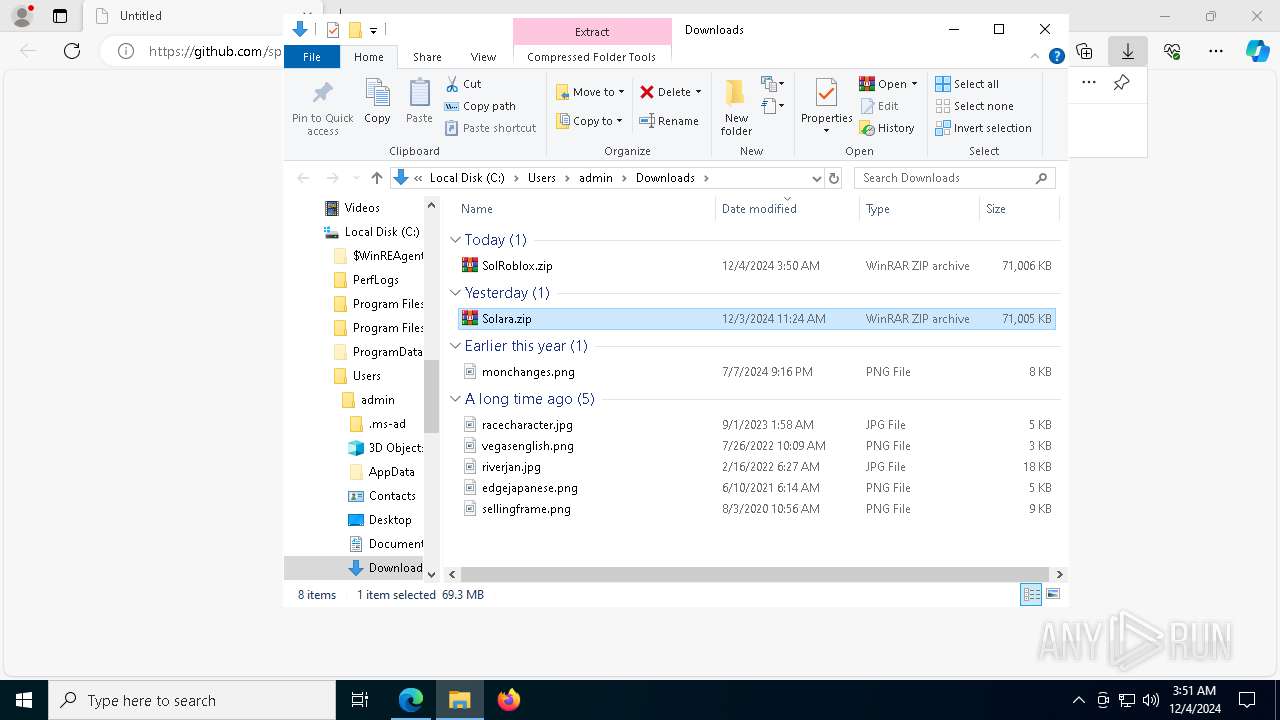
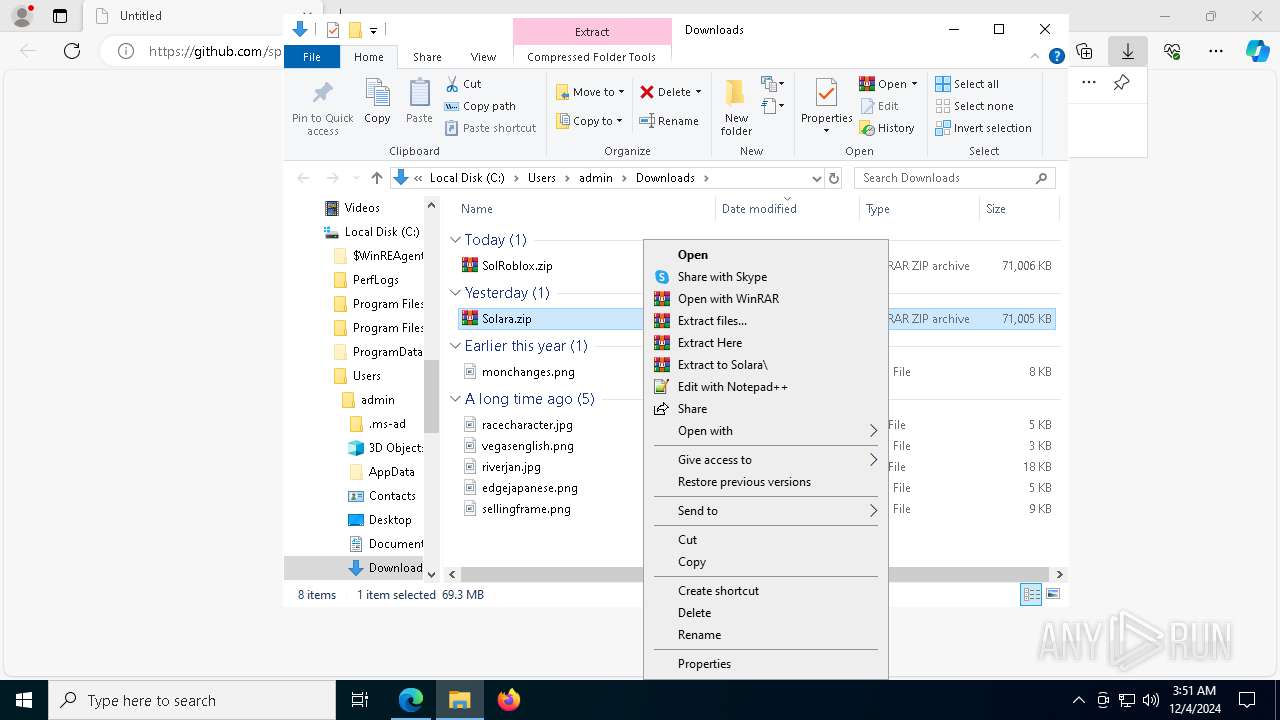
| Analysis date: | December 04, 2024, 03:50:28 |
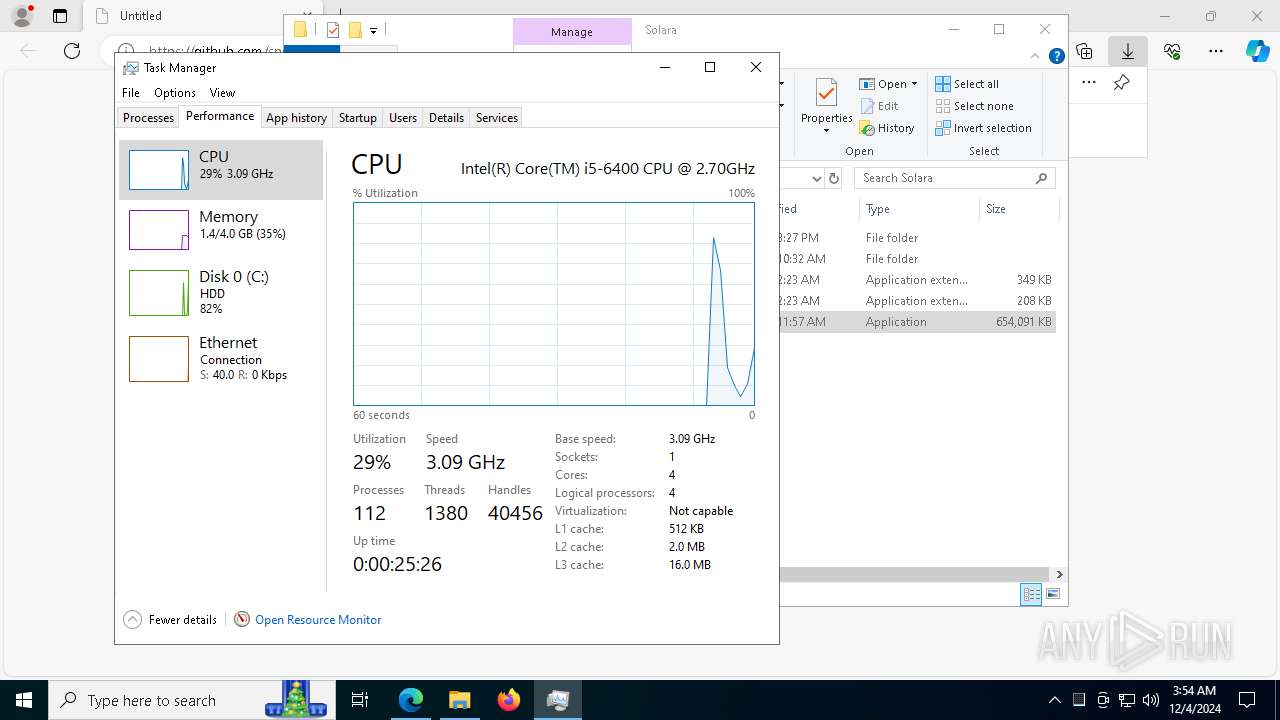
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0E52CC44B91B1FB349116C16493CB084 |
| SHA1: | 152101DF01B1352901BDB351D7804EE310D1991B |
| SHA256: | 09E0EC02B9C7C8A4A85BC0C55DE87B194C8325D47CF792D04543D7E3E2909F16 |
| SSDEEP: | 3:N8tEdmV+HkaRYssNAOrkCcSLJf8tJ3Hun:2uwV+CszOr9tKJ3O |
MALICIOUS
MEDUZASTEALER has been detected (SURICATA)
- venomderek.exe (PID: 7536)
Adds extension to the Windows Defender exclusion list
- lokigod.exe (PID: 7128)
- vzppfnnlsyit.exe (PID: 5460)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 2940)
- cmd.exe (PID: 1760)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2192)
SUSPICIOUS
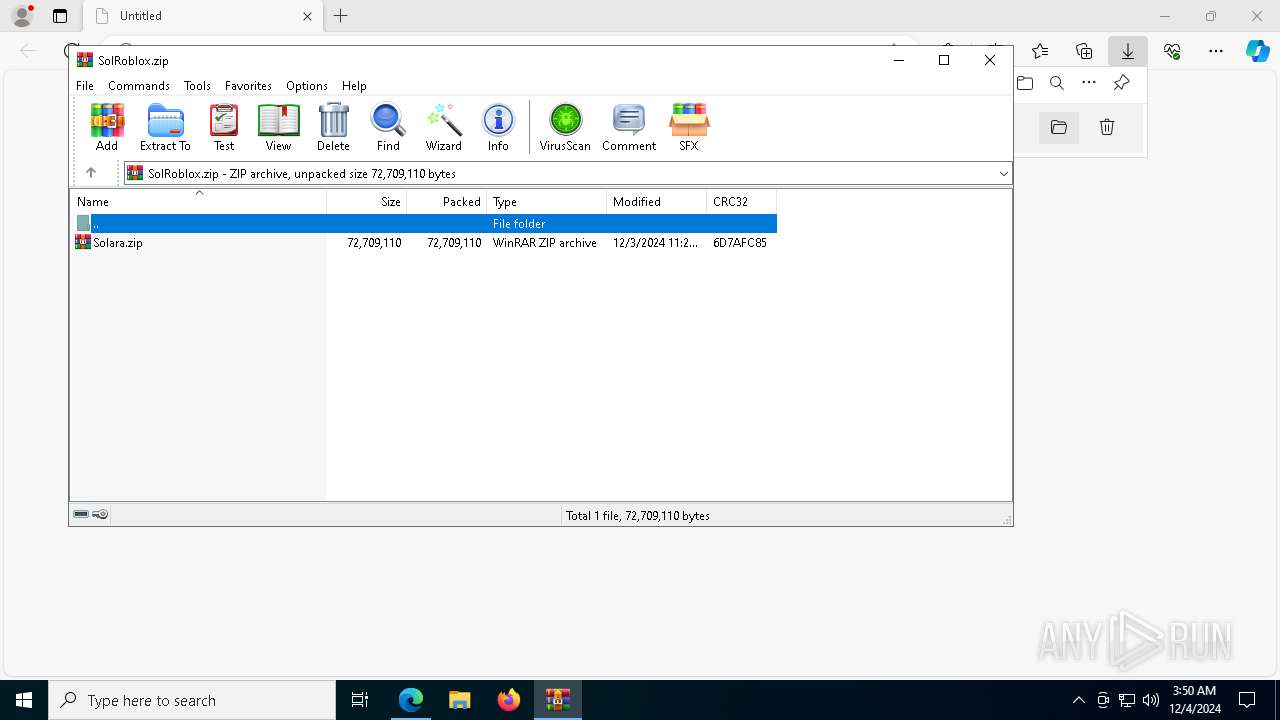
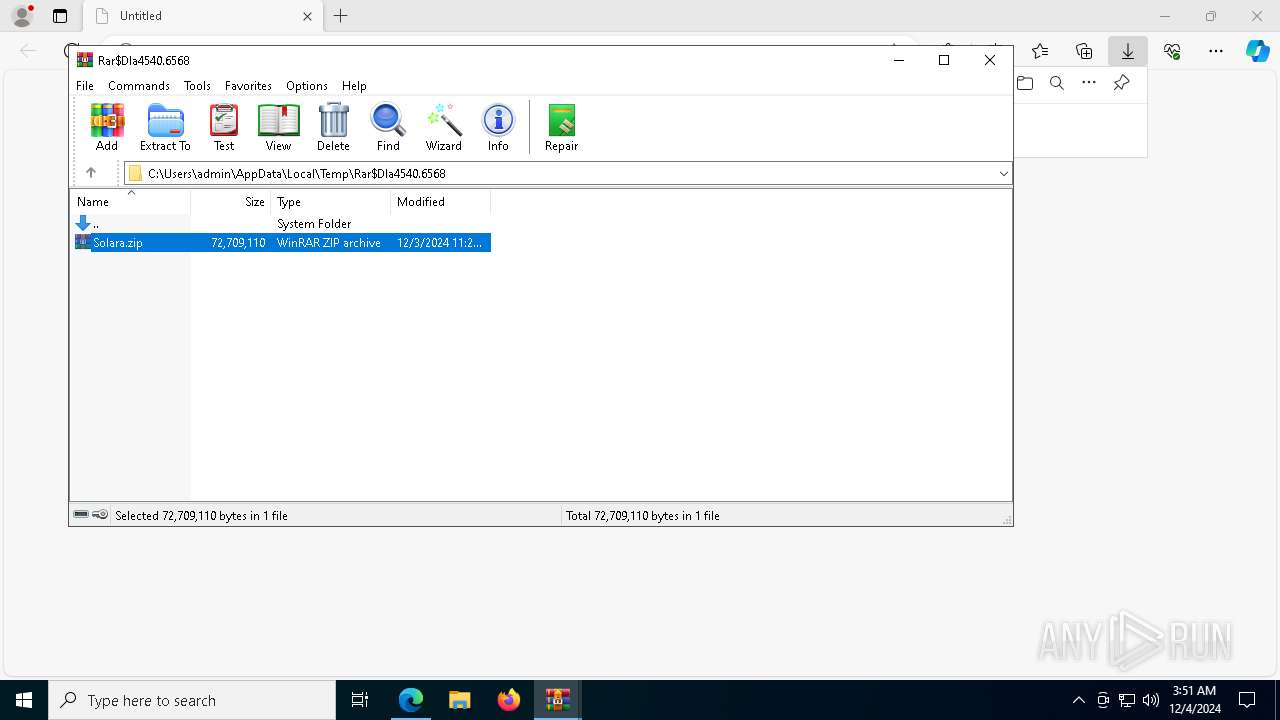
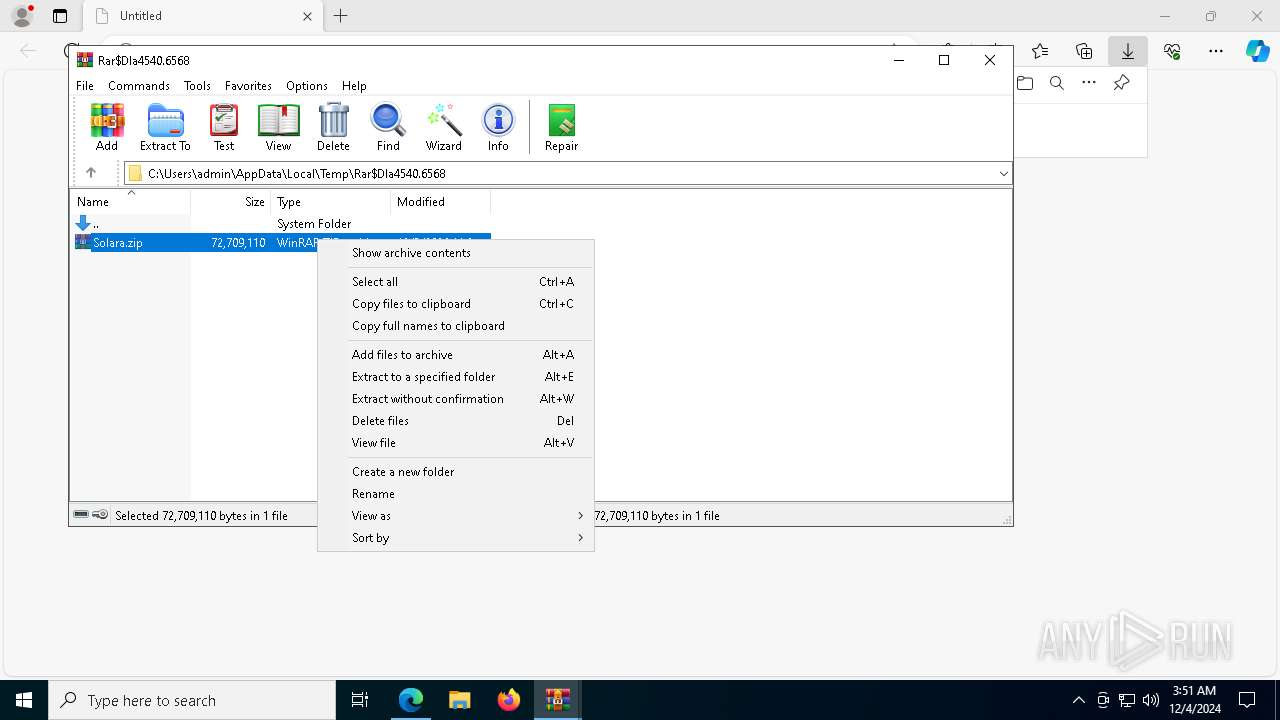
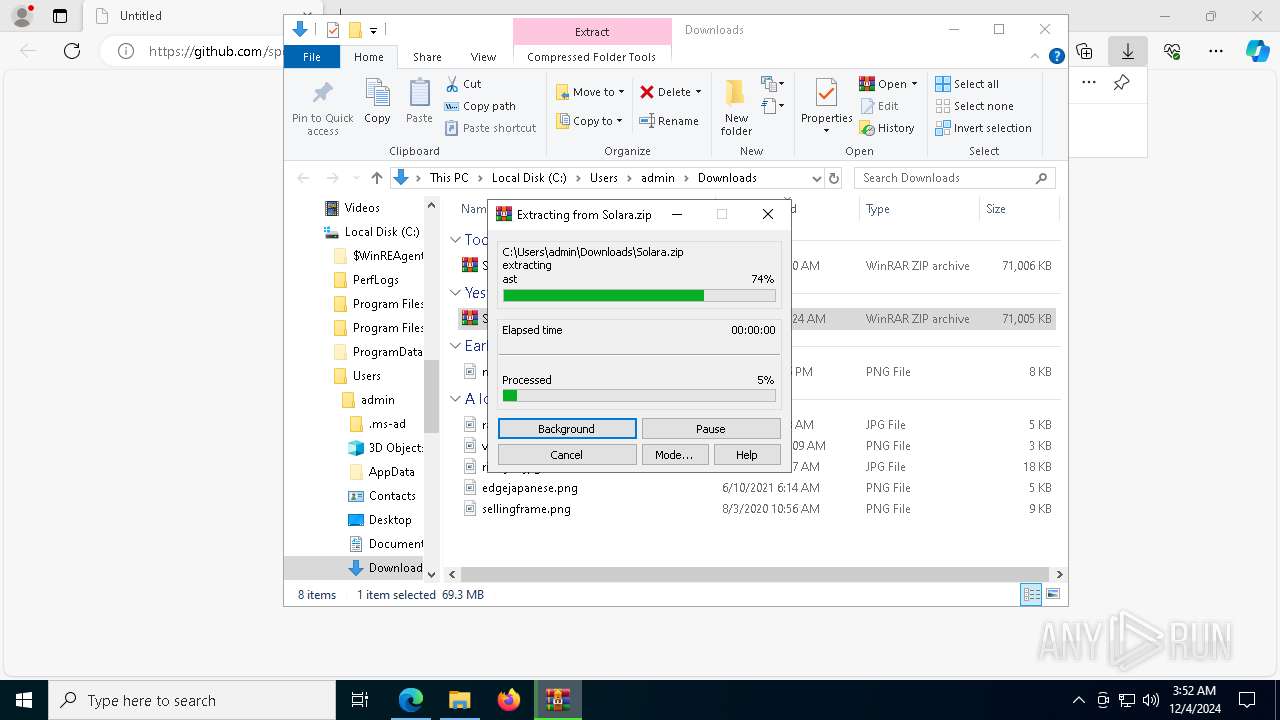
Reads security settings of Internet Explorer
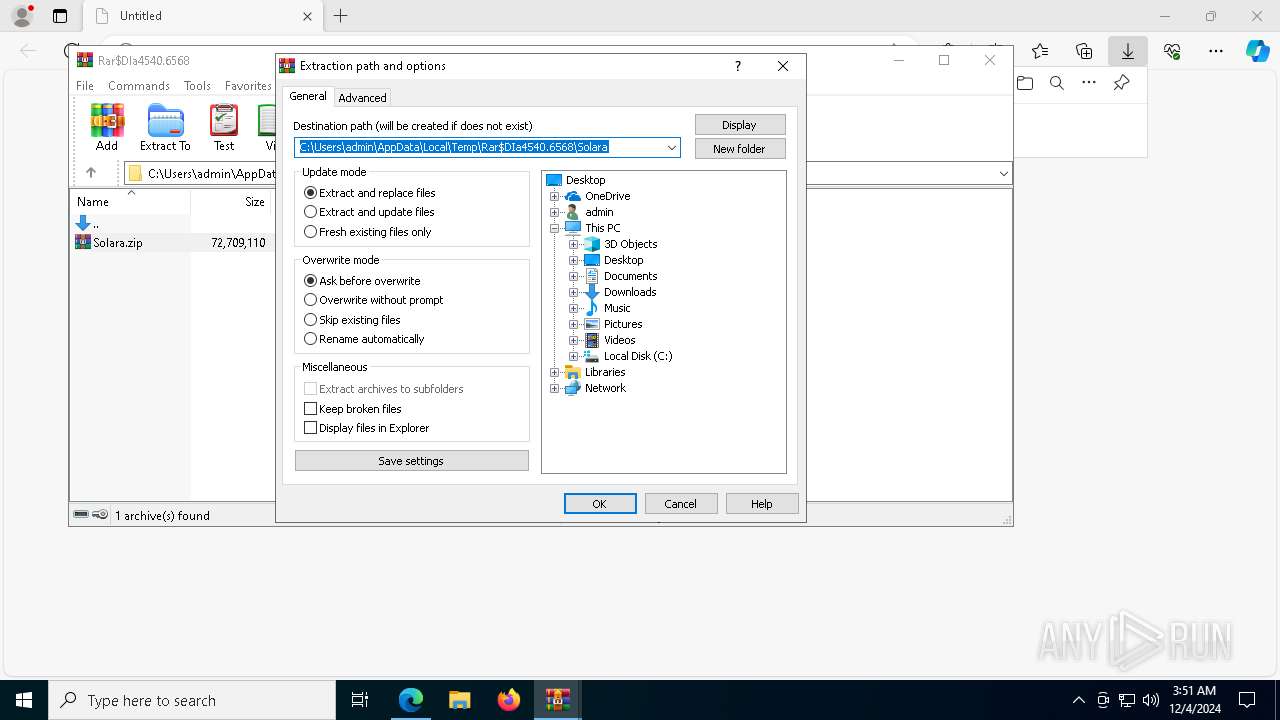
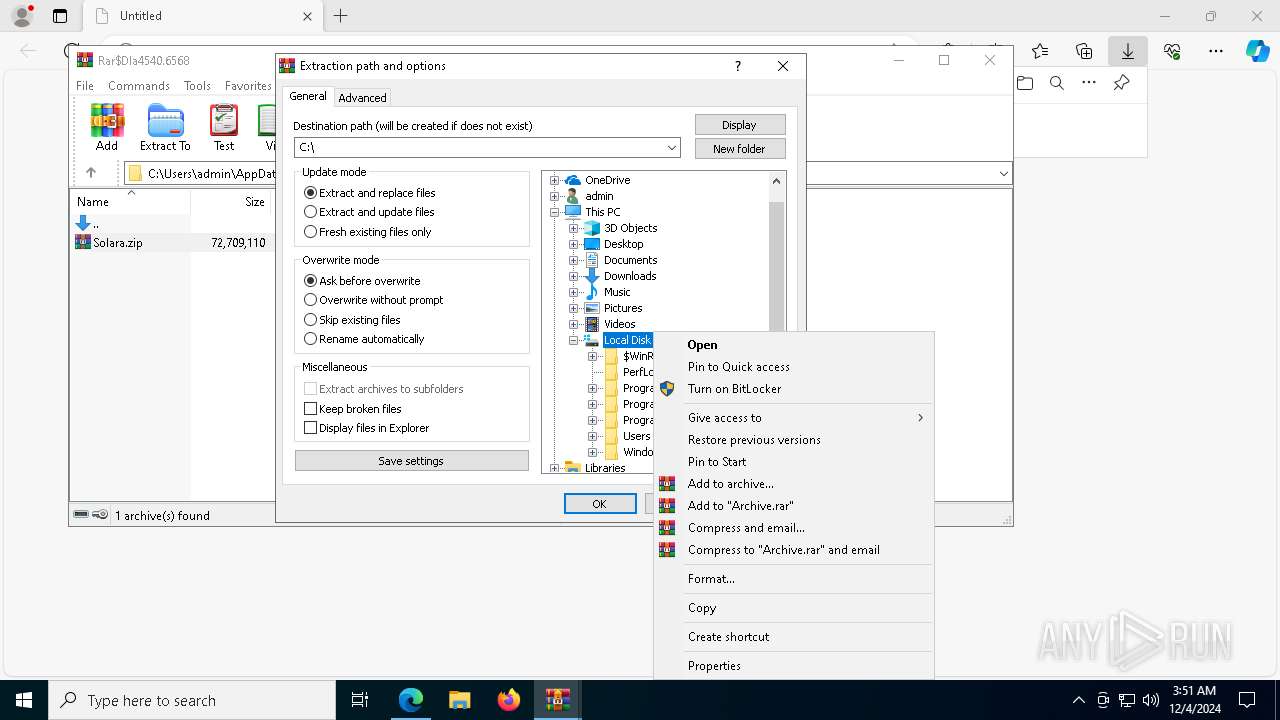
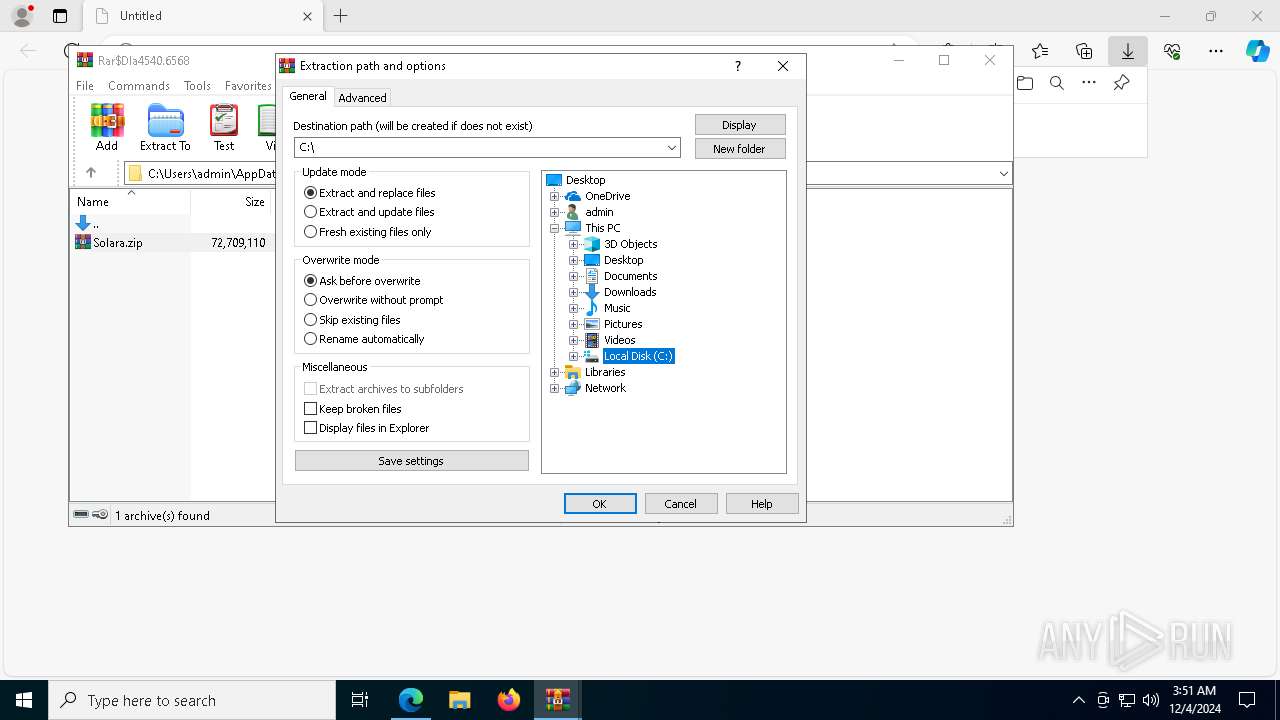
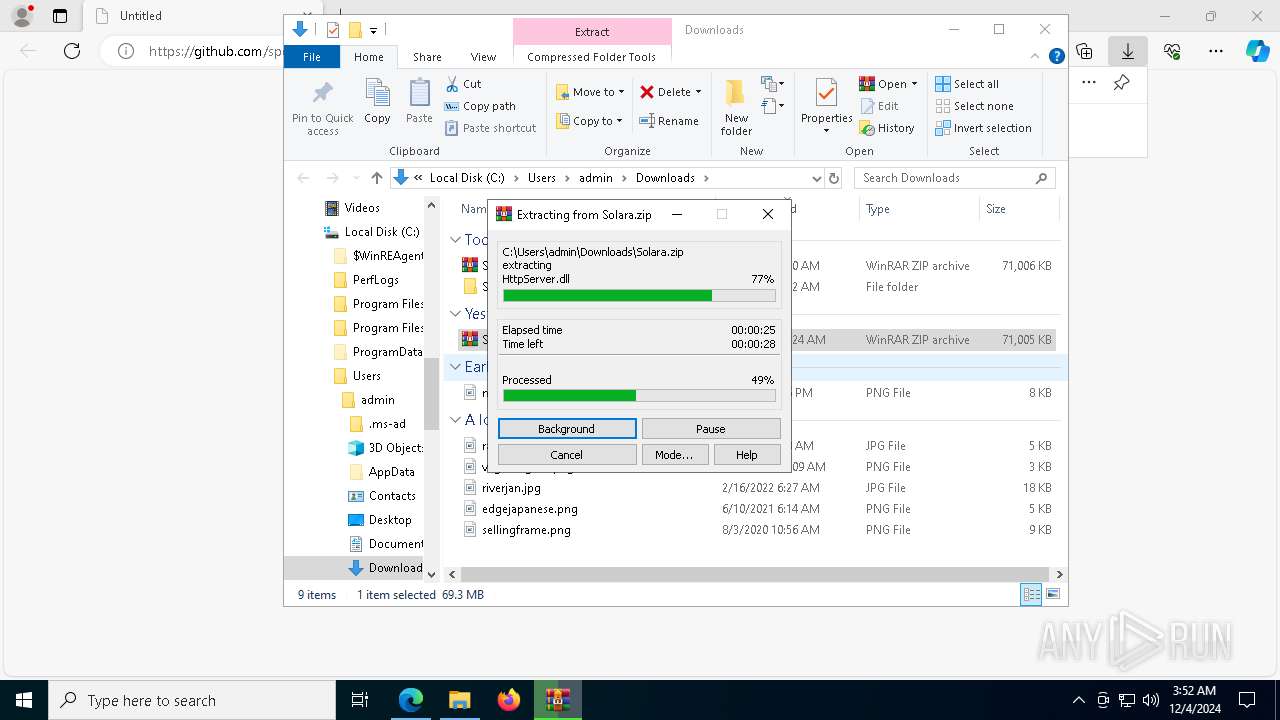
- WinRAR.exe (PID: 4540)
- WinRAR.exe (PID: 4384)
Application launched itself
- WinRAR.exe (PID: 4540)
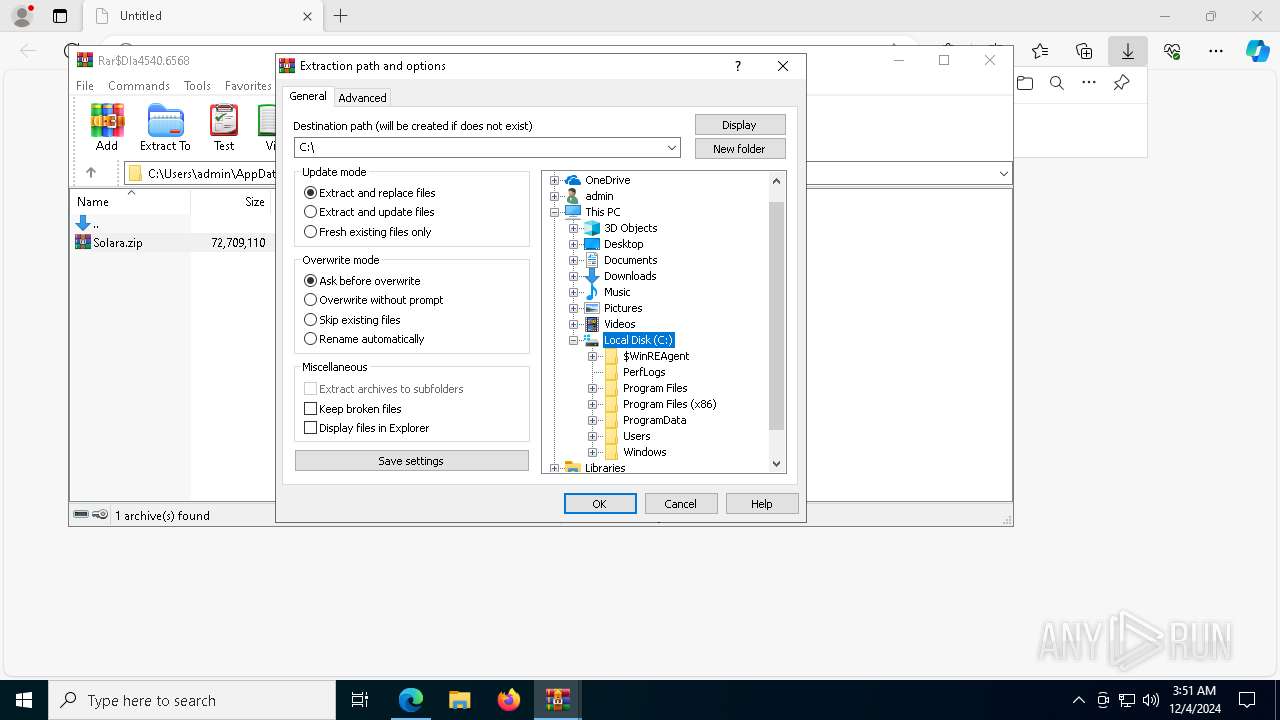
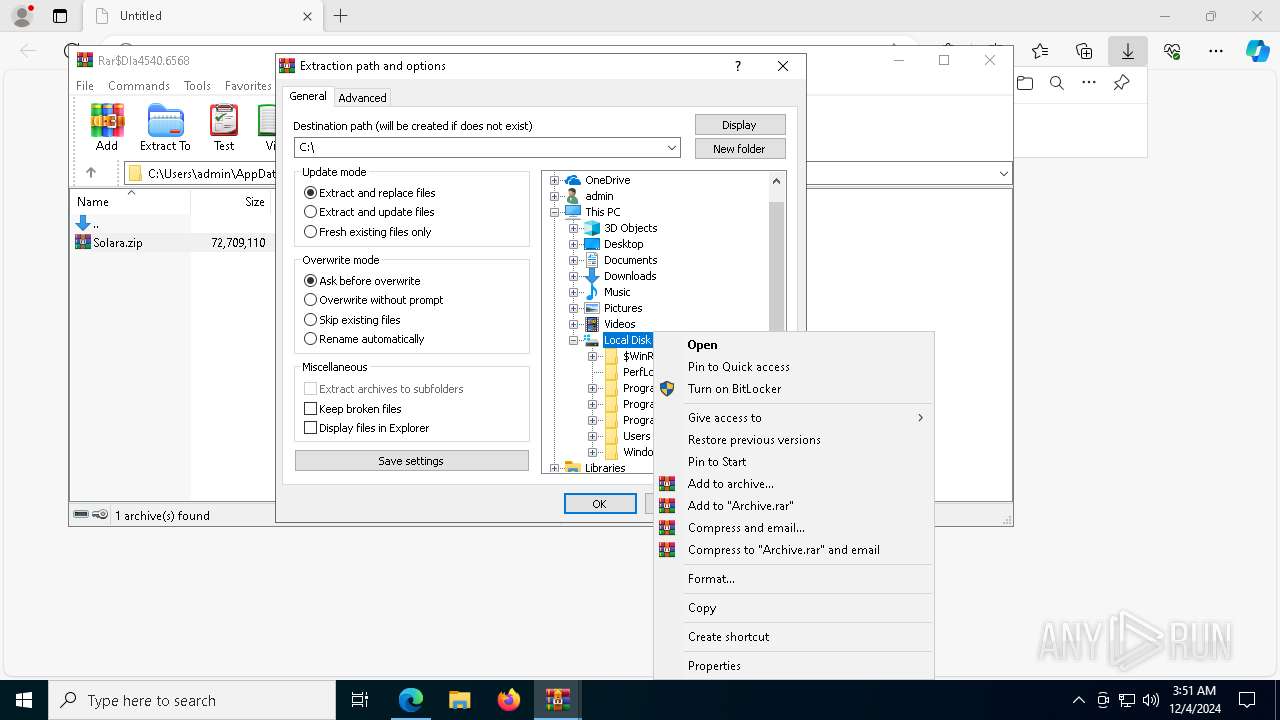
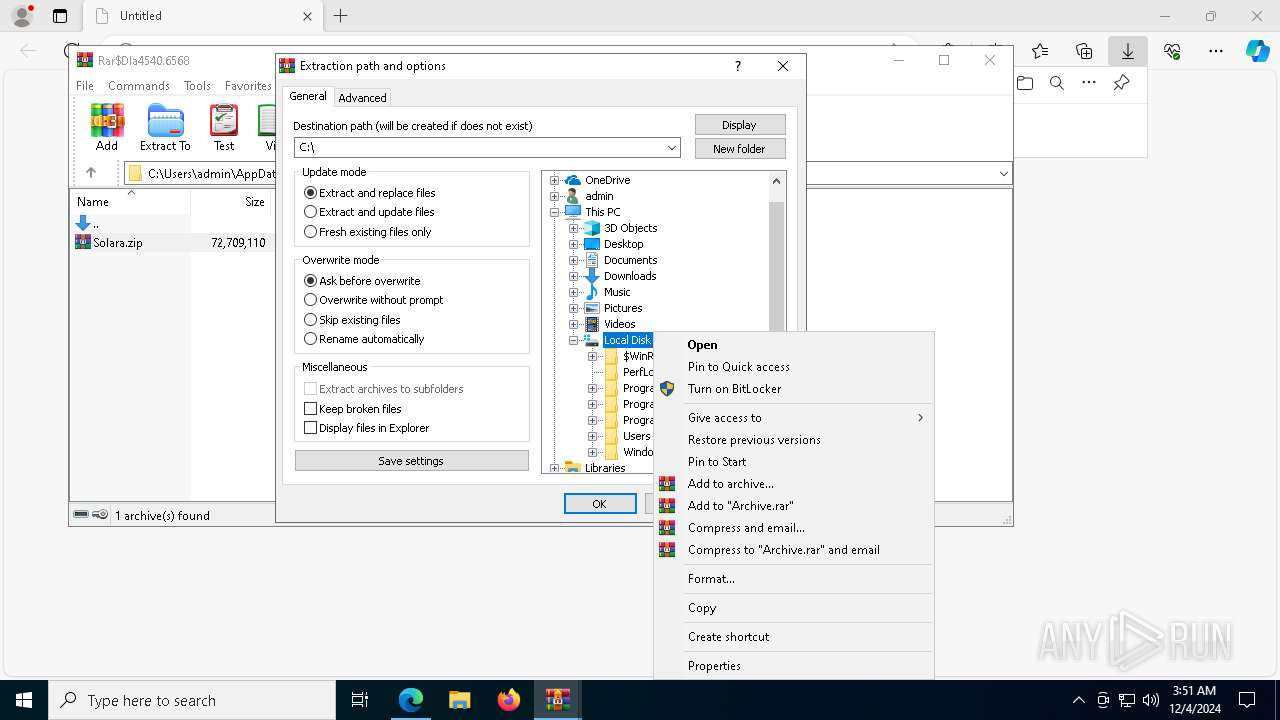
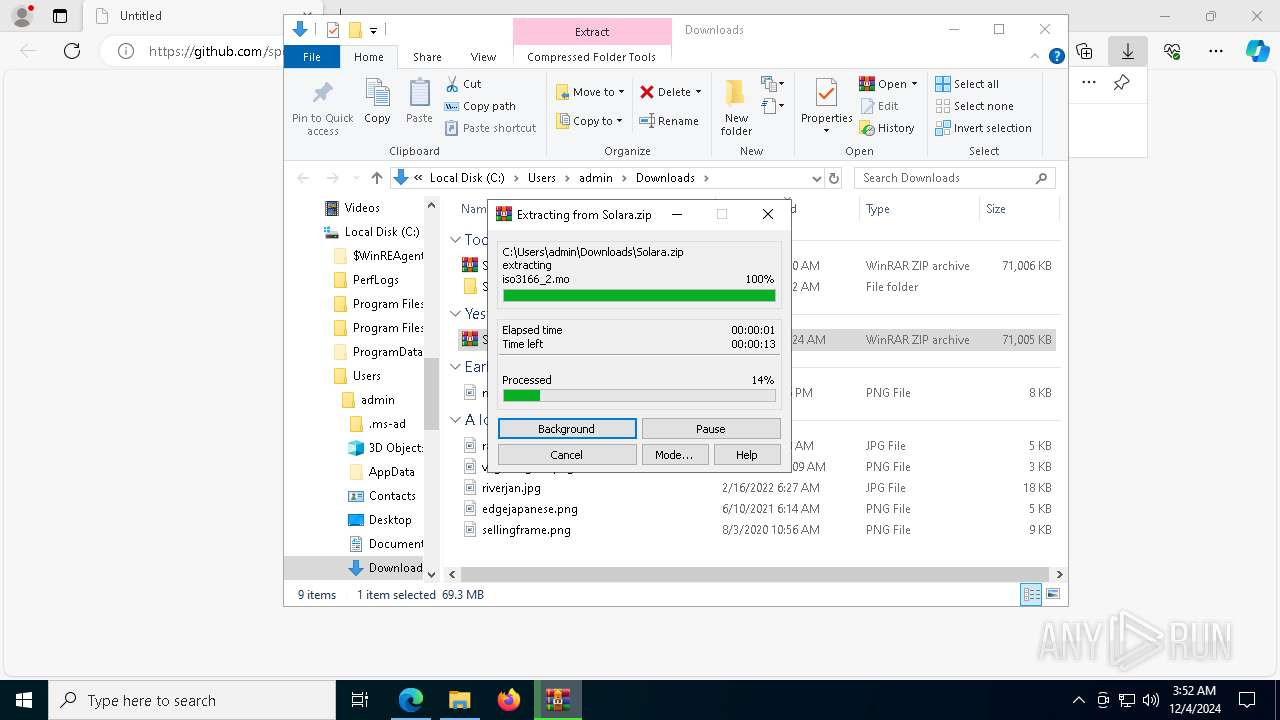
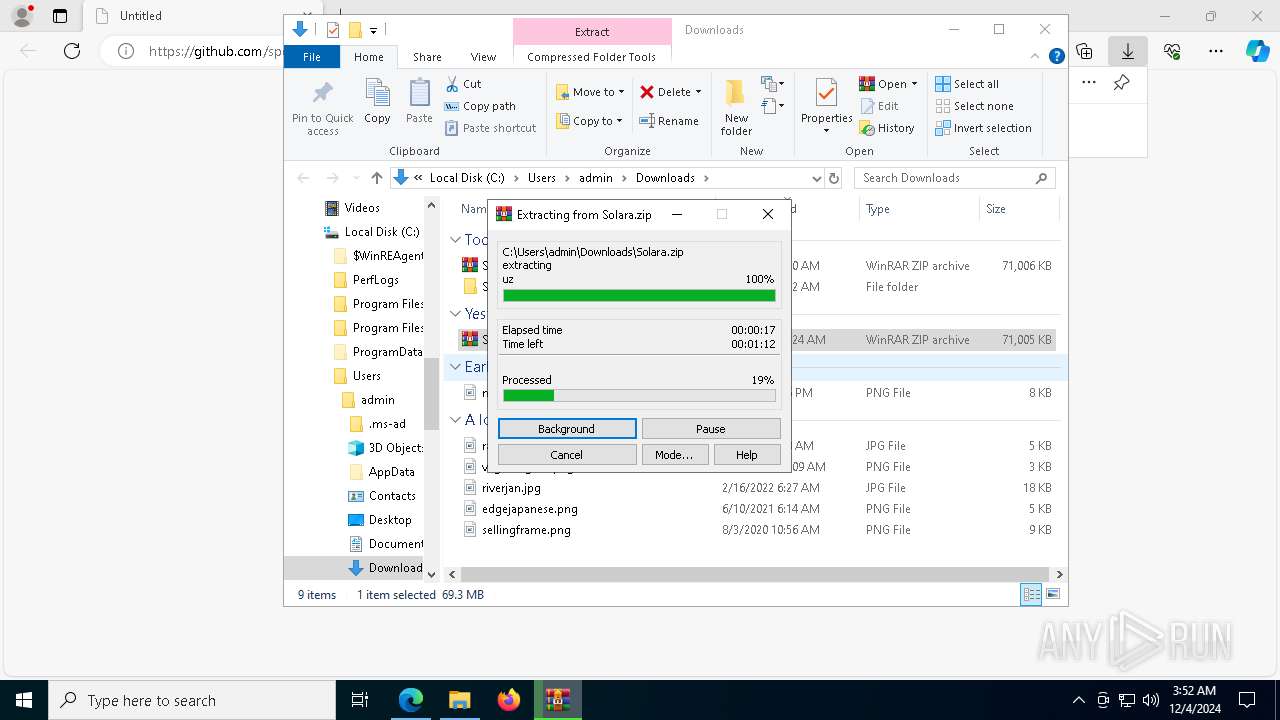
Creates file in the systems drive root
- WinRAR.exe (PID: 4384)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5308)
Checks for external IP
- svchost.exe (PID: 2192)
- venomderek.exe (PID: 7536)
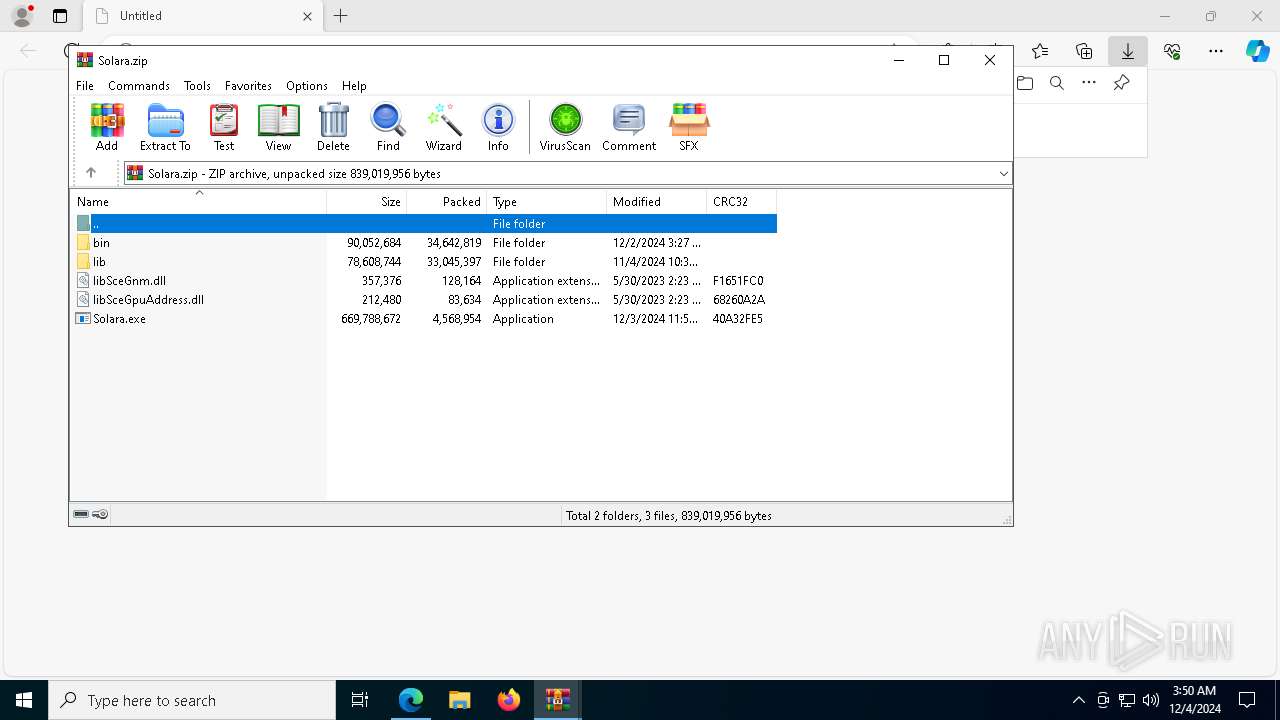
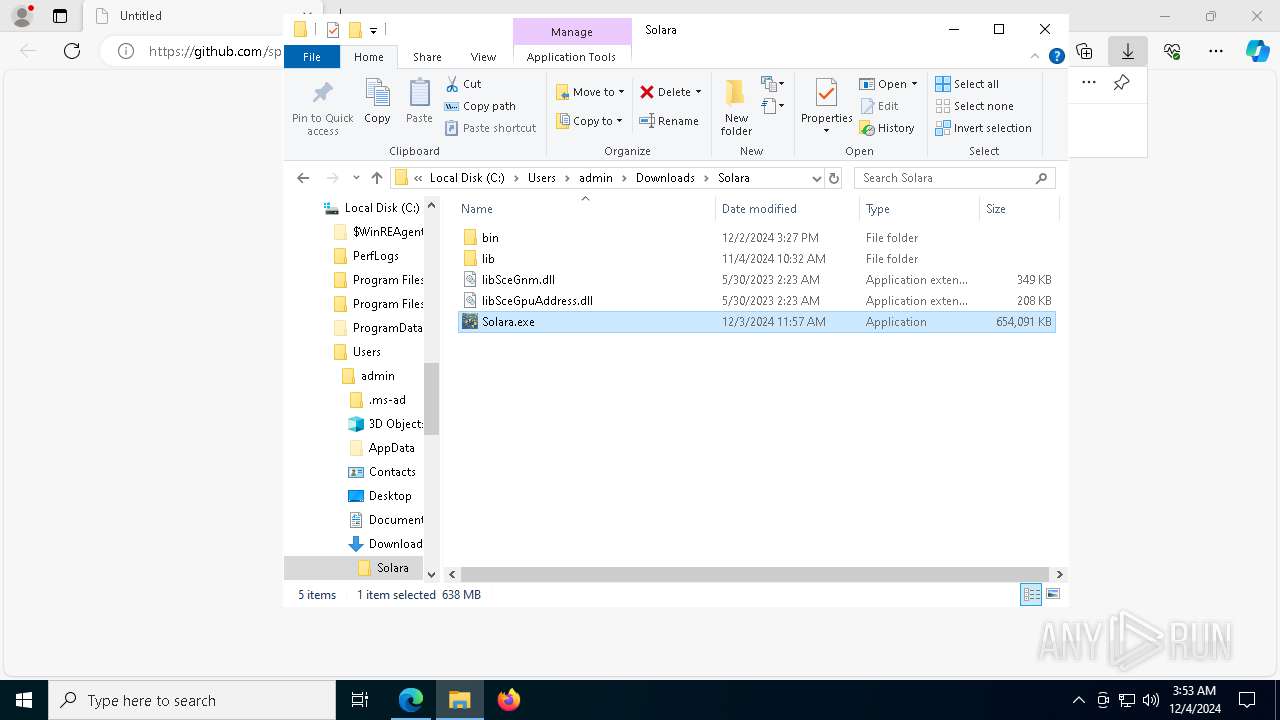
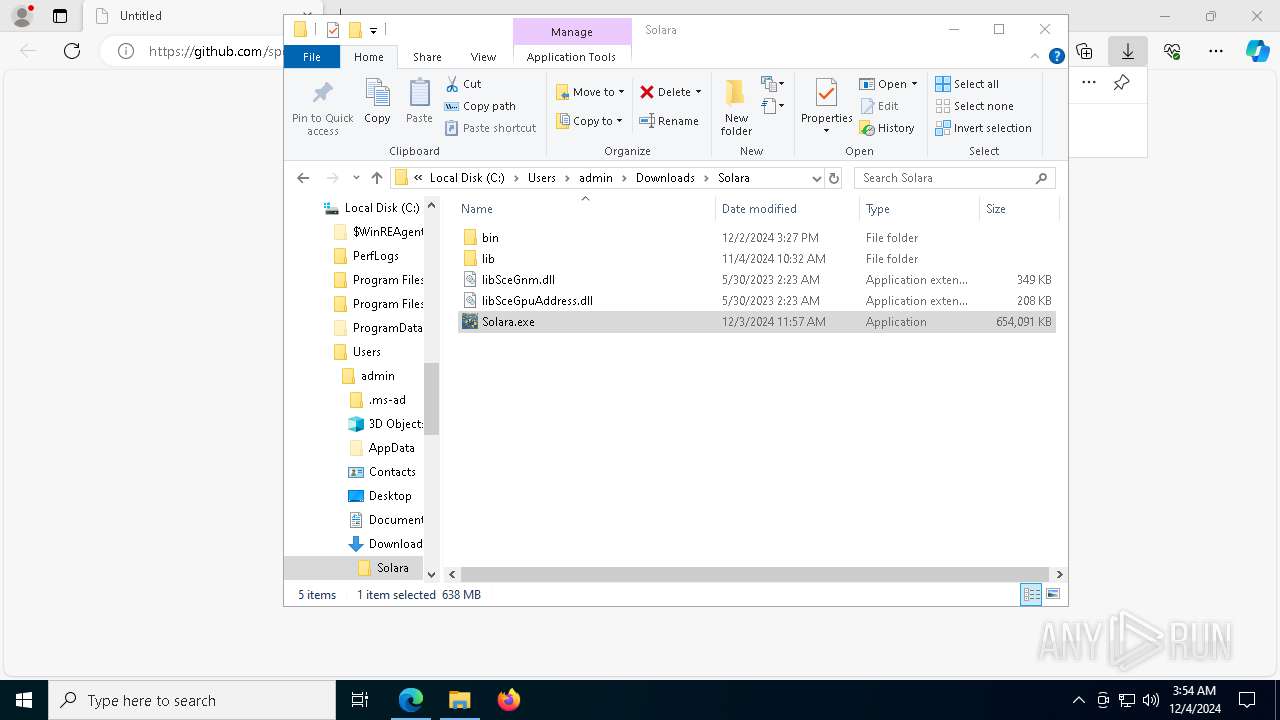
Executable content was dropped or overwritten
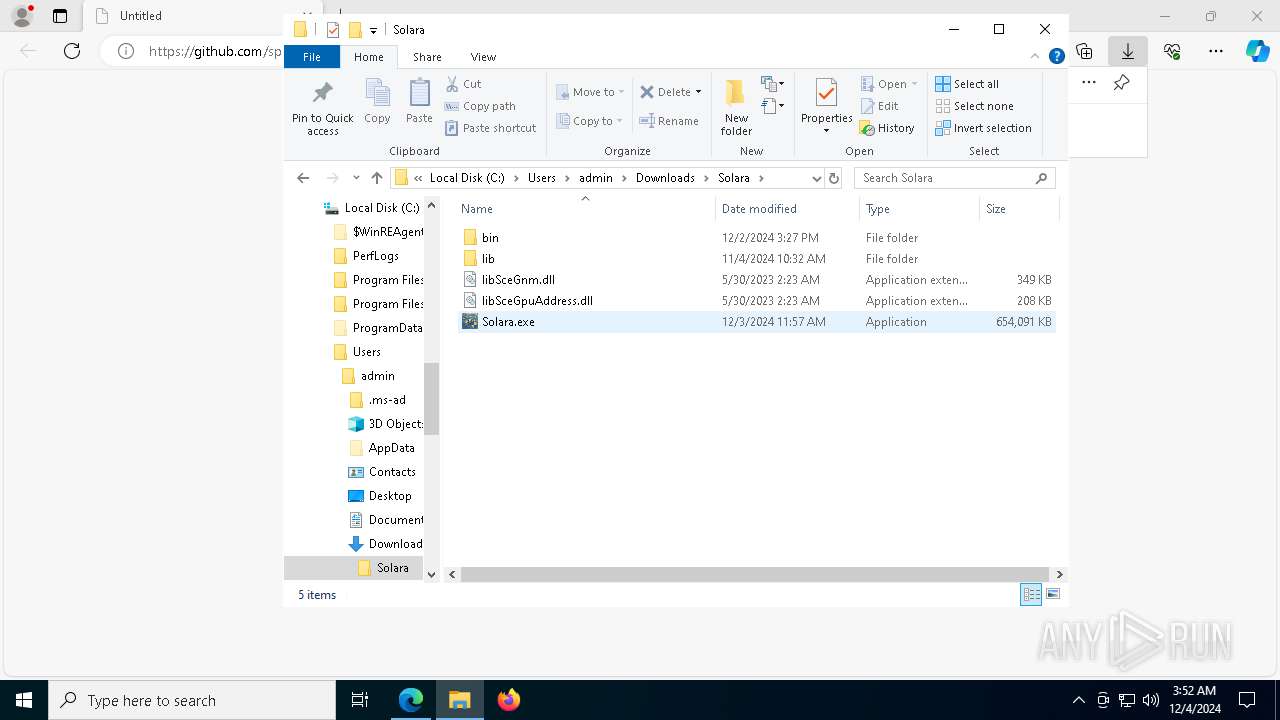
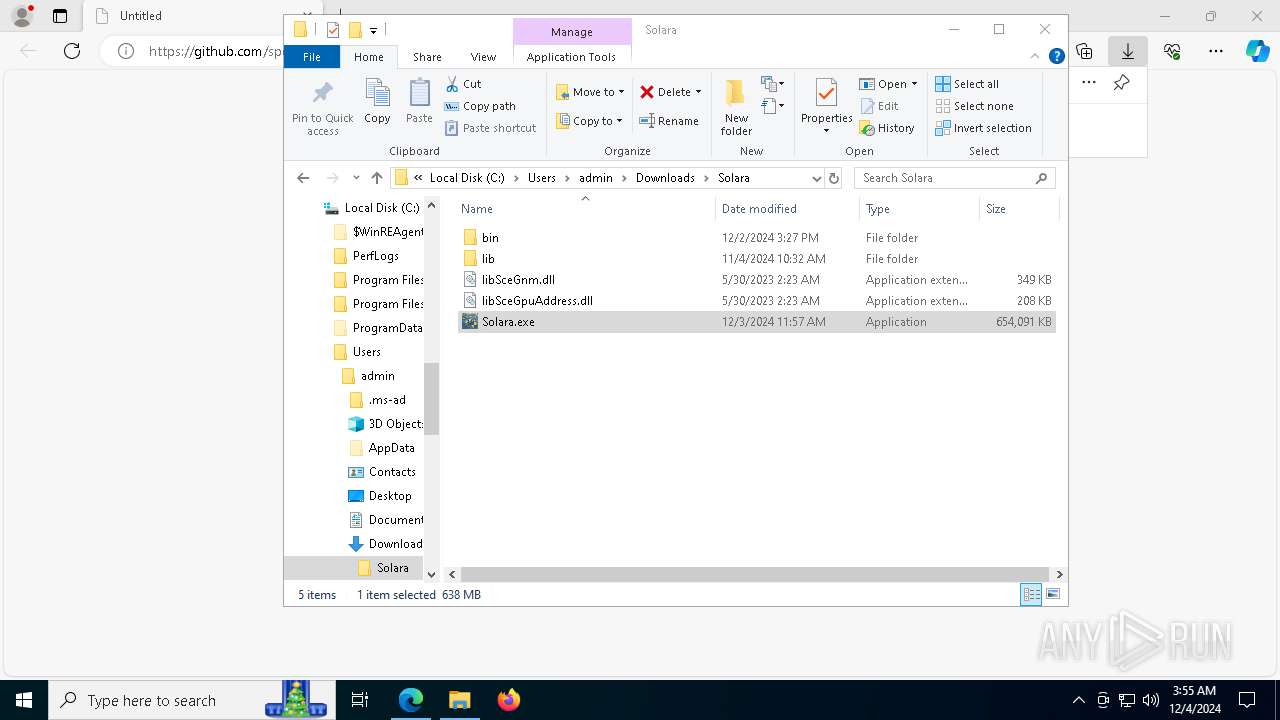
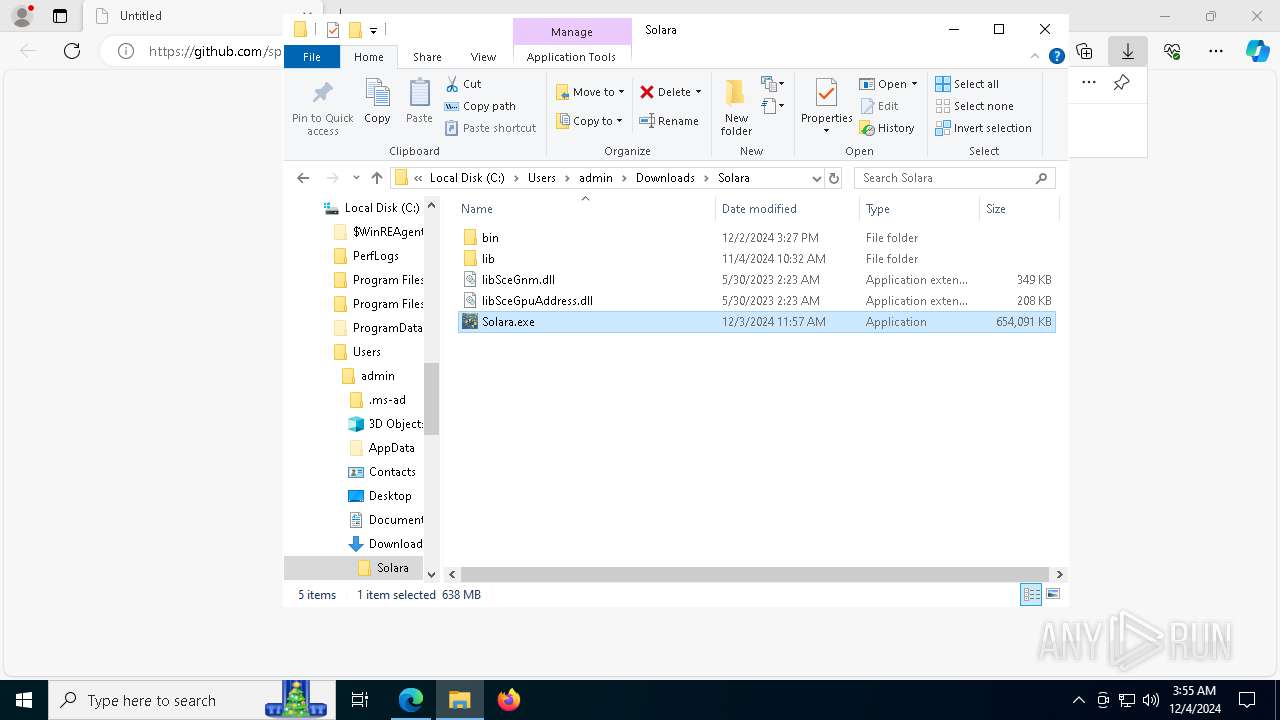
- Solara.exe (PID: 8160)
- lokigod.exe (PID: 7128)
- vzppfnnlsyit.exe (PID: 5460)
The process connected to a server suspected of theft
- venomderek.exe (PID: 7536)
Connects to unusual port
- venomderek.exe (PID: 7536)
Manipulates environment variables
- powershell.exe (PID: 1612)
- powershell.exe (PID: 4596)
Script adds exclusion extension to Windows Defender
- lokigod.exe (PID: 7128)
- vzppfnnlsyit.exe (PID: 5460)
Script adds exclusion path to Windows Defender
- lokigod.exe (PID: 7128)
- vzppfnnlsyit.exe (PID: 5460)
Process uninstalls Windows update
- wusa.exe (PID: 2224)
- wusa.exe (PID: 6820)
Starts POWERSHELL.EXE for commands execution
- lokigod.exe (PID: 7128)
- vzppfnnlsyit.exe (PID: 5460)
Starts SC.EXE for service management
- lokigod.exe (PID: 7128)
- vzppfnnlsyit.exe (PID: 5460)
Uses powercfg.exe to modify the power settings
- lokigod.exe (PID: 7128)
- vzppfnnlsyit.exe (PID: 5460)
Starts CMD.EXE for commands execution
- lokigod.exe (PID: 7128)
- vzppfnnlsyit.exe (PID: 5460)
Executes as Windows Service
- vzppfnnlsyit.exe (PID: 5460)
Drops a system driver (possible attempt to evade defenses)
- vzppfnnlsyit.exe (PID: 5460)
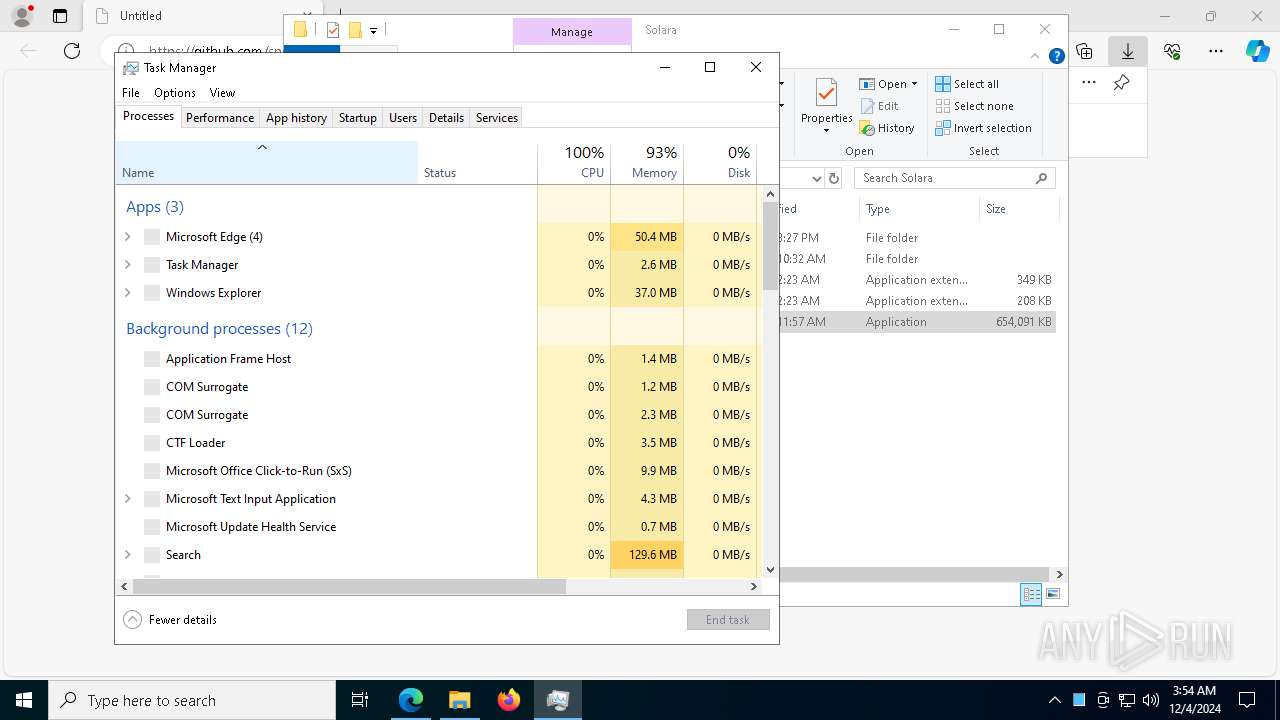
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2192)
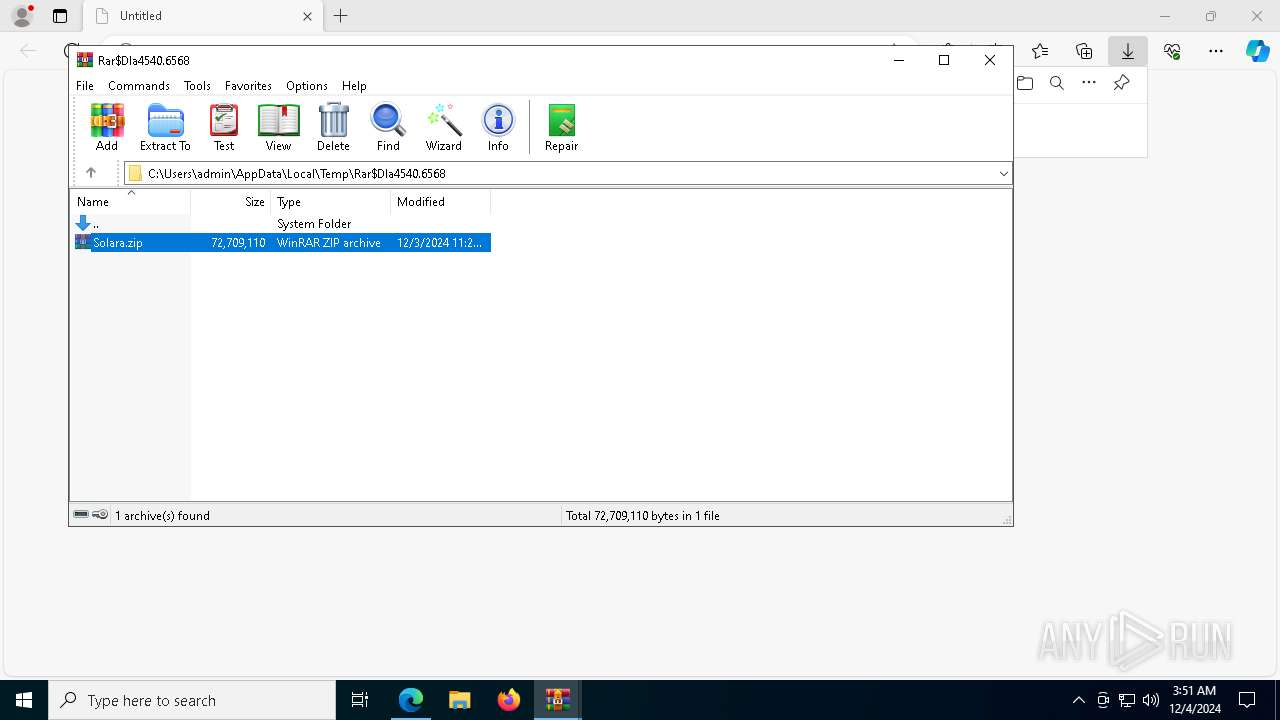
Process drops python dynamic module
- WinRAR.exe (PID: 5308)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 4540)
- msedge.exe (PID: 520)
- msedge.exe (PID: 5560)
Reads Microsoft Office registry keys
- msedge.exe (PID: 520)
Checks supported languages
- identity_helper.exe (PID: 7588)
Reads the computer name
- identity_helper.exe (PID: 7588)
Reads Environment values
- identity_helper.exe (PID: 7588)
Application launched itself
- msedge.exe (PID: 520)
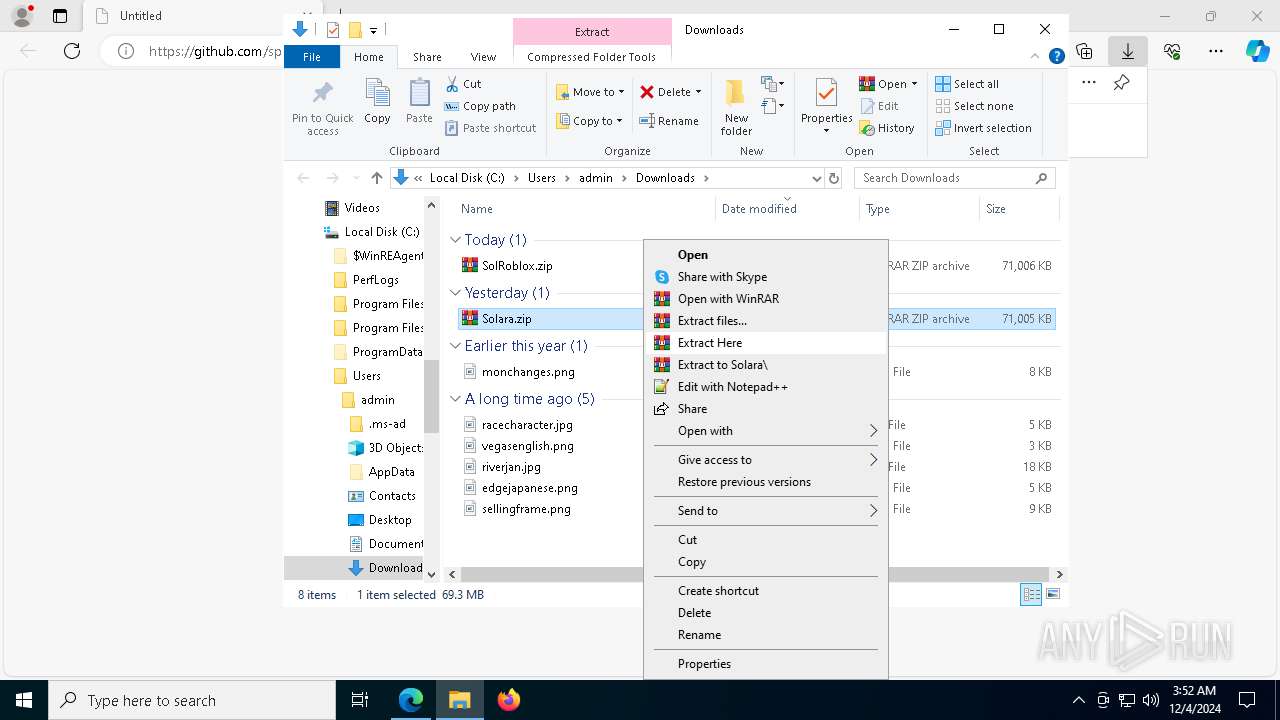
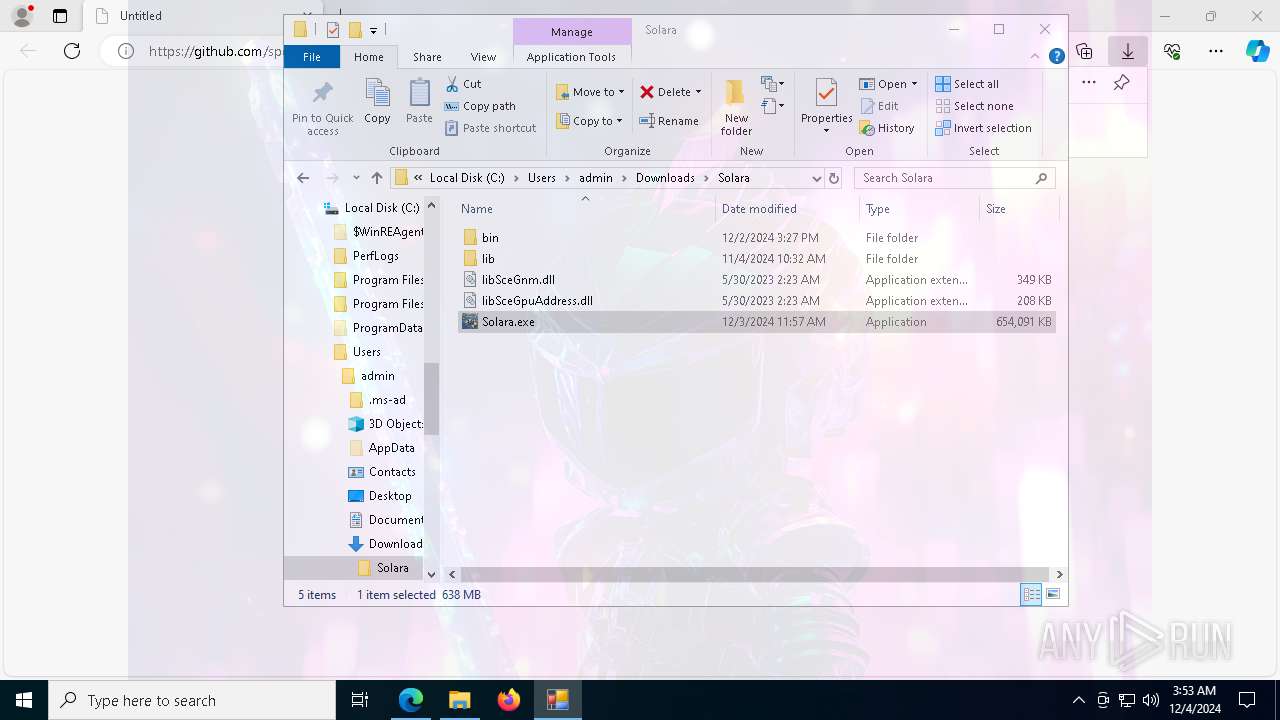
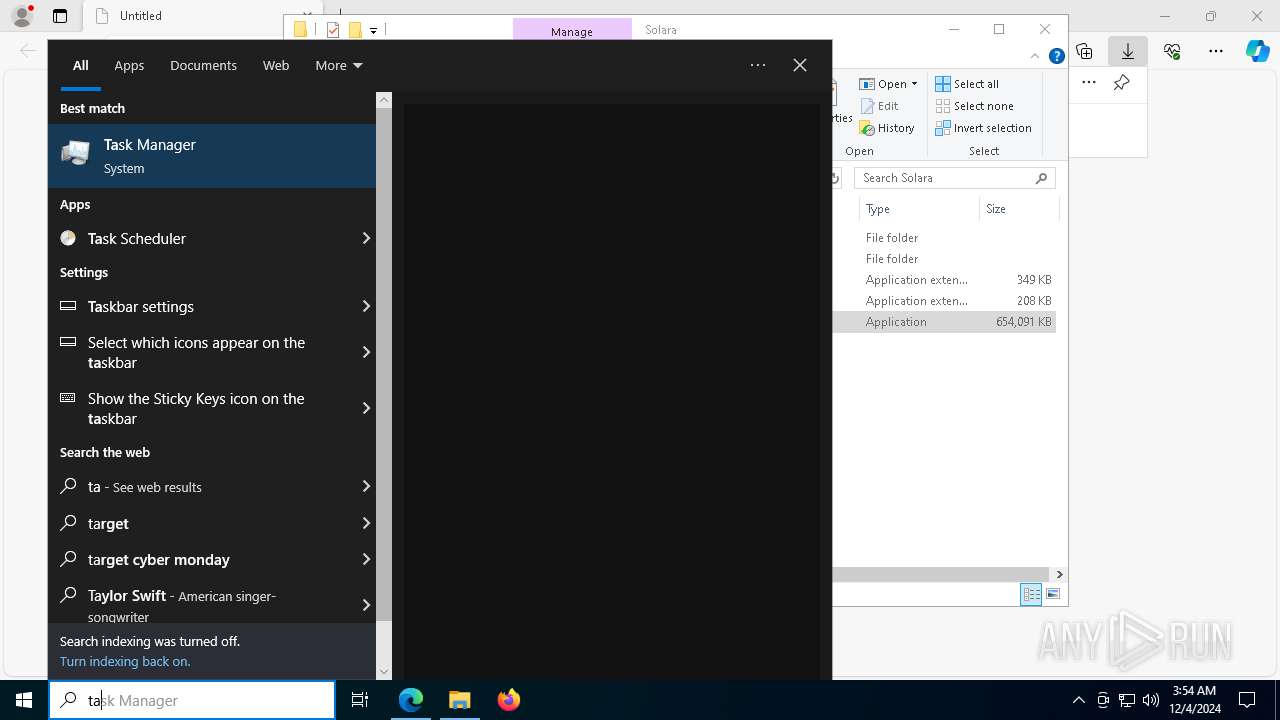
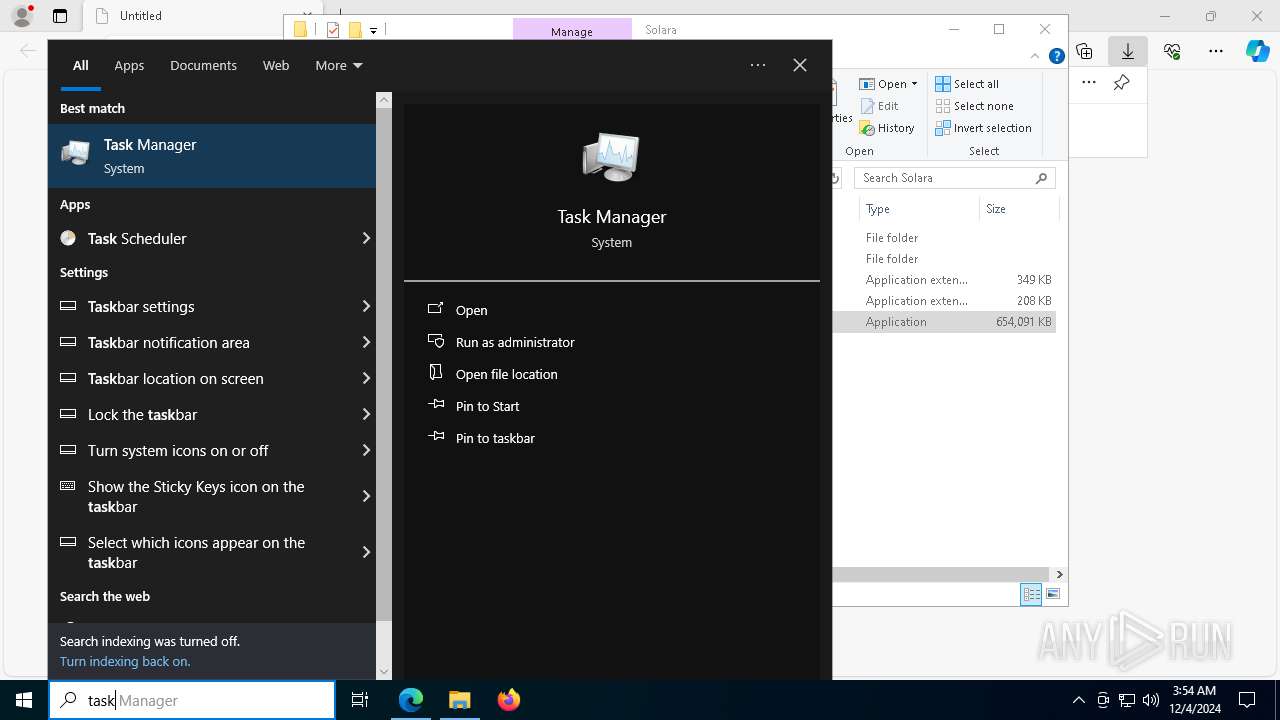
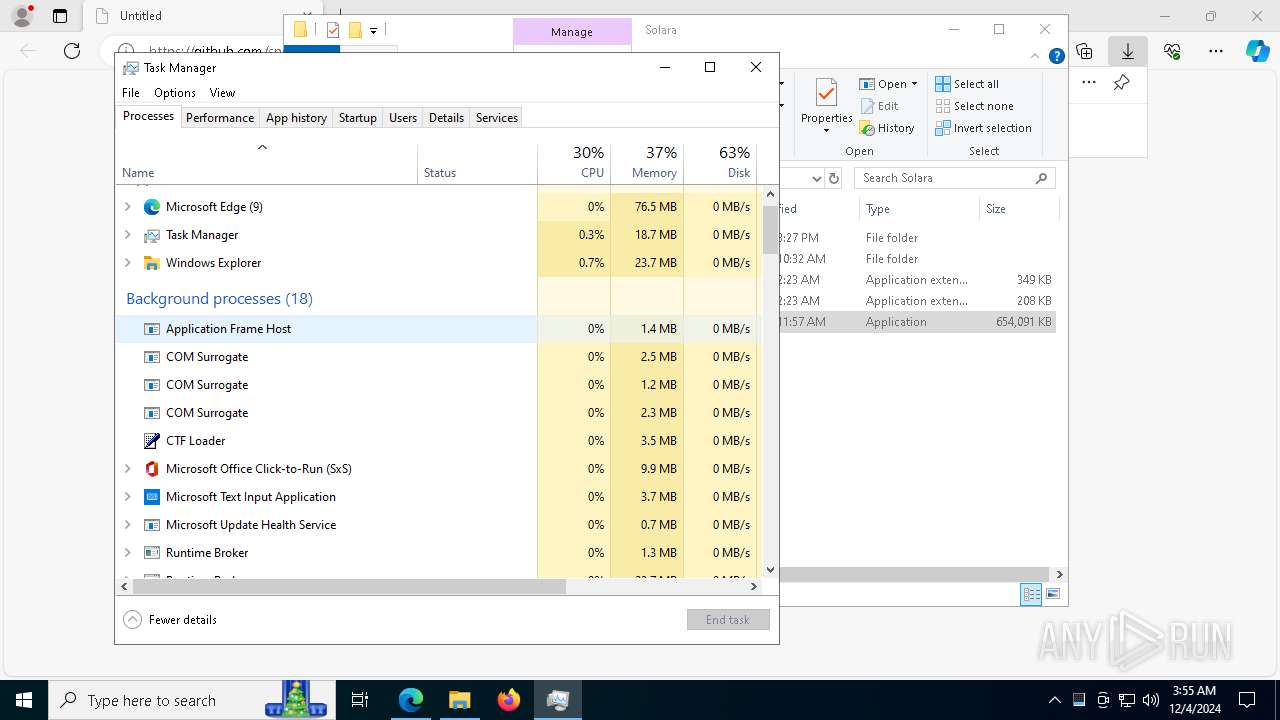
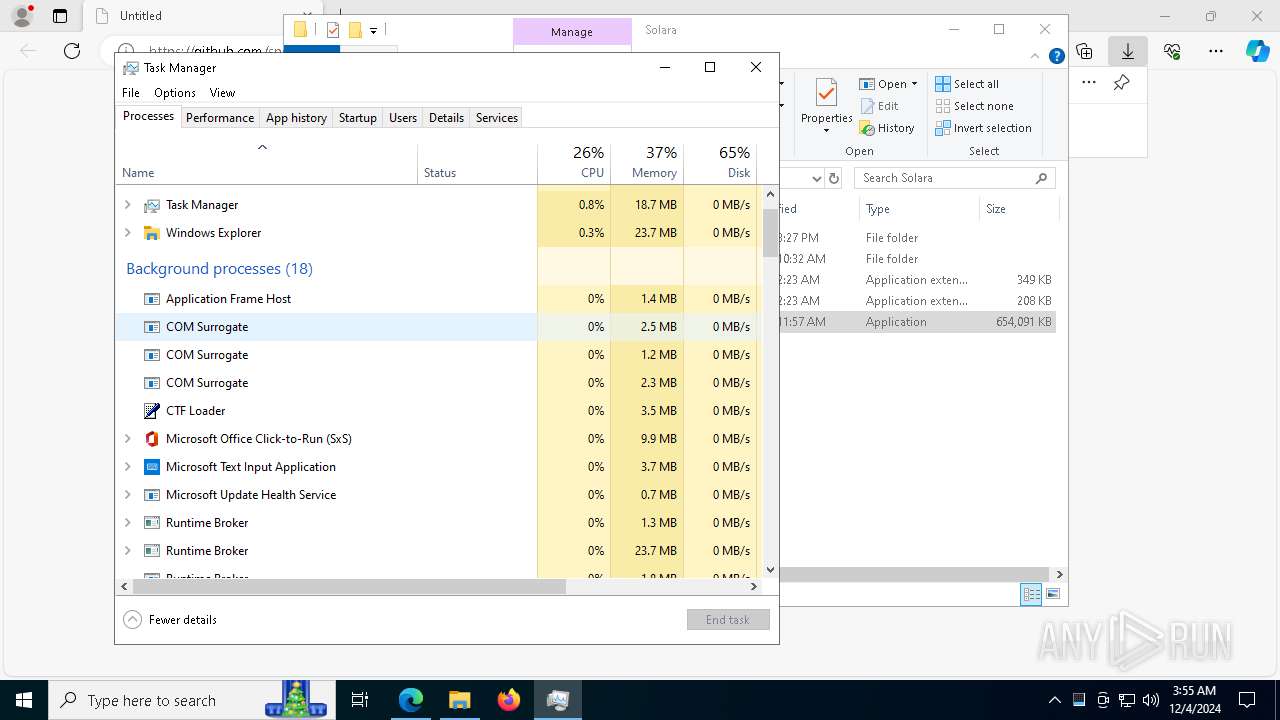
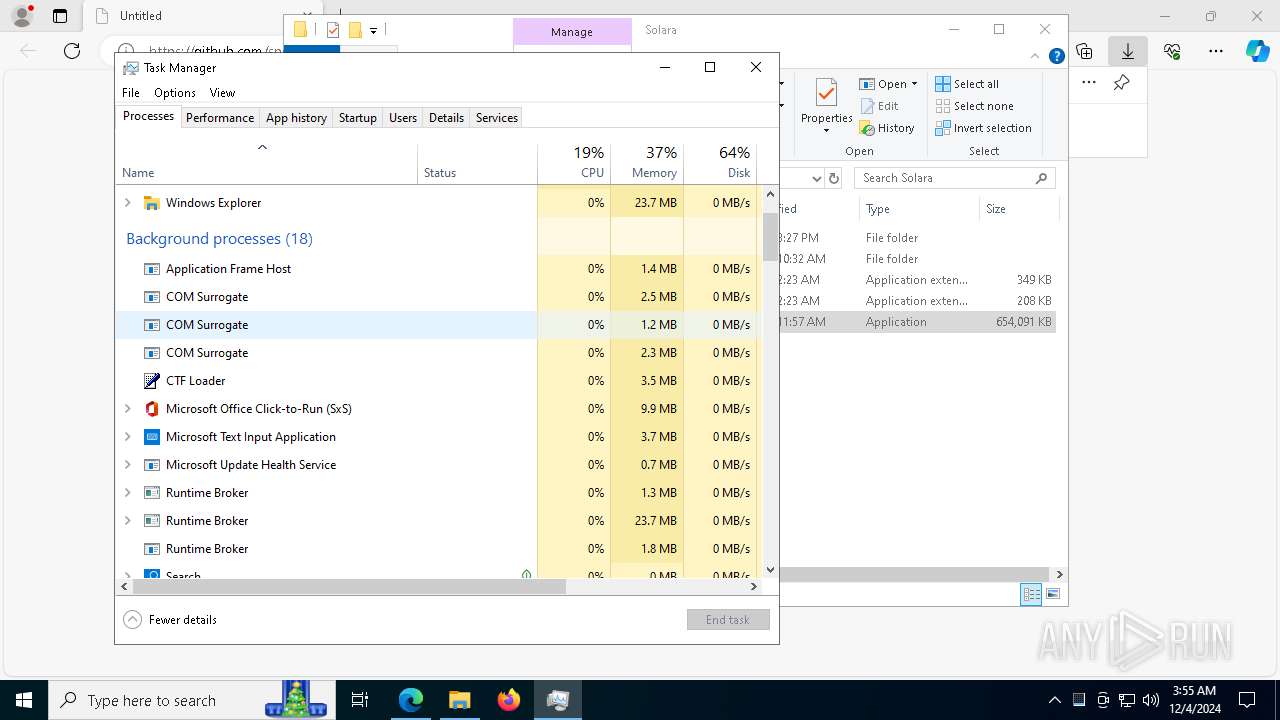
Manual execution by a user
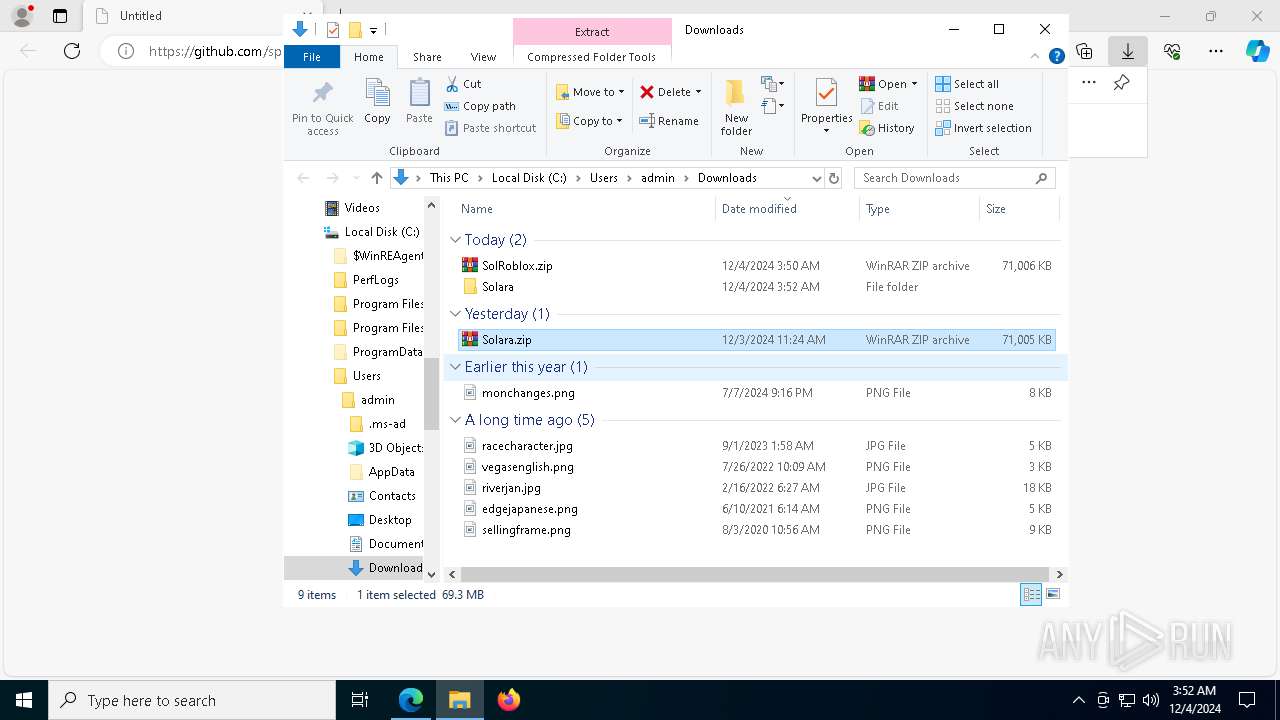
- WinRAR.exe (PID: 5472)
- Solara.exe (PID: 8160)
- WinRAR.exe (PID: 5308)
- Solara.exe (PID: 2956)
- Taskmgr.exe (PID: 1412)
- Taskmgr.exe (PID: 3700)
Executable content was dropped or overwritten
- msedge.exe (PID: 5888)
- WinRAR.exe (PID: 5308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
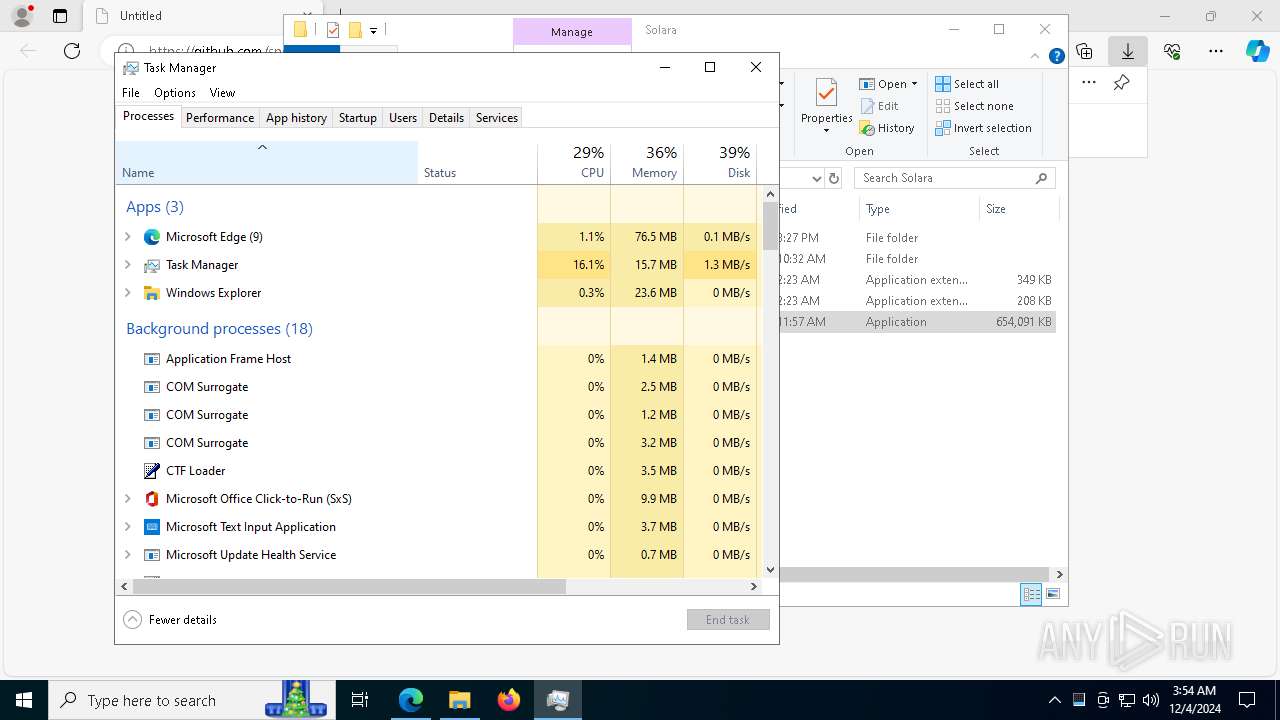
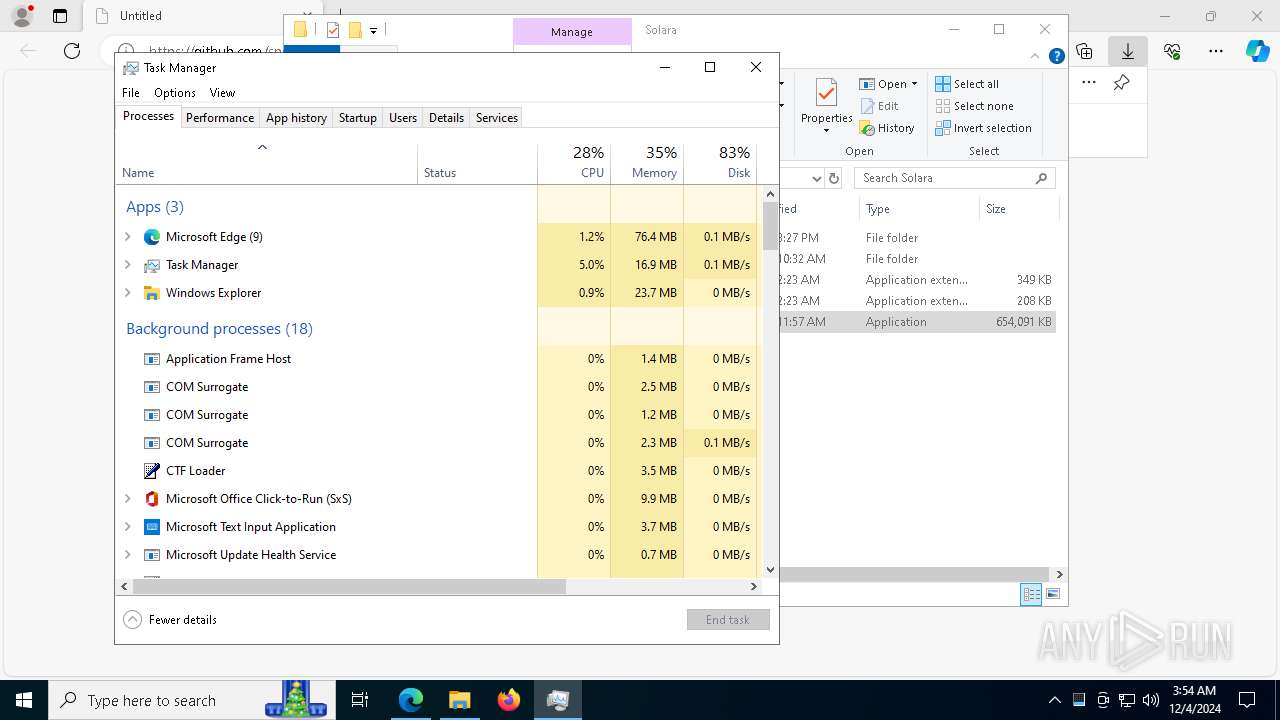
Total processes
256
Monitored processes
119
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7464 --field-trial-handle=2476,i,11976463045010025640,13774258420301205499,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/spear-blackseeker/Solara-Executor-Roblox/releases/download/Download/SolRoblox.zip" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | C:\WINDOWS\system32\powercfg.exe /x -standby-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | lokigod.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6644 --field-trial-handle=2476,i,11976463045010025640,13774258420301205499,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1144 | C:\WINDOWS\system32\powercfg.exe /x -standby-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | lokigod.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1224 | C:\WINDOWS\system32\sc.exe stop bits | C:\Windows\System32\sc.exe | — | vzppfnnlsyit.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7024 --field-trial-handle=2476,i,11976463045010025640,13774258420301205499,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1296 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | lokigod.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1380 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6716 --field-trial-handle=2476,i,11976463045010025640,13774258420301205499,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
36 777
Read events
36 694
Write events
82
Delete events
1
Modification events
| (PID) Process: | (520) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 960479F7FF862F00 | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 52E380F7FF862F00 | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262924 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C8DAC14C-156C-4139-8744-5B7064B9A736} | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262924 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {985CD8DE-15AF-4ADA-ABD2-84114F359A34} | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3F38A5F7FF862F00 | |||
| (PID) Process: | (520) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
85
Suspicious files
1 313
Text files
121
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1352b7.TMP | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1352b7.TMP | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1352b7.TMP | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1352b7.TMP | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1352d6.TMP | — | |
MD5:— | SHA256:— | |||
| 520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
88
DNS requests
72
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
6060 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5008 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6888 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
5732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/be1098f2-af7c-46fa-9fb6-e1f0043ecb69?P1=1733818743&P2=404&P3=2&P4=afey4fvdAUYFZwErHbaYss5ihSLNuDh7oCr5%2fYAJSf5ozMNQbKyaGupecINrhQY3L3NxDYdLJxzRd5QB%2fdrPlA%3d%3d | US | binary | 2.26 Kb | whitelisted |
5732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/be1098f2-af7c-46fa-9fb6-e1f0043ecb69?P1=1733818743&P2=404&P3=2&P4=afey4fvdAUYFZwErHbaYss5ihSLNuDh7oCr5%2fYAJSf5ozMNQbKyaGupecINrhQY3L3NxDYdLJxzRd5QB%2fdrPlA%3d%3d | US | binary | 4.80 Kb | whitelisted |
5732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/be1098f2-af7c-46fa-9fb6-e1f0043ecb69?P1=1733818743&P2=404&P3=2&P4=afey4fvdAUYFZwErHbaYss5ihSLNuDh7oCr5%2fYAJSf5ozMNQbKyaGupecINrhQY3L3NxDYdLJxzRd5QB%2fdrPlA%3d%3d | US | binary | 2.93 Kb | whitelisted |
5732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/be1098f2-af7c-46fa-9fb6-e1f0043ecb69?P1=1733818743&P2=404&P3=2&P4=afey4fvdAUYFZwErHbaYss5ihSLNuDh7oCr5%2fYAJSf5ozMNQbKyaGupecINrhQY3L3NxDYdLJxzRd5QB%2fdrPlA%3d%3d | US | compressed | 43.4 Kb | whitelisted |
5732 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1733662755&P2=404&P3=2&P4=OURxMENHlURPkcIMzPipCA%2fvYC4xILvxP07k7yoCczdJPfY8euydpjf9dWG7uc0xF5Tu6JlRpH9IBaz69VNRkA%3d%3d | US | binary | 141 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6060 | svchost.exe | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6060 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6300 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
520 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6300 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
6300 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7536 | venomderek.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
7536 | venomderek.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Meduza Stealer Exfiltration M1 |
7536 | venomderek.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
7536 | venomderek.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Meduza Stealer |
7536 | venomderek.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
7536 | venomderek.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Meduza Stealer Exfiltration M1 |
7536 | venomderek.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
7536 | venomderek.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Meduza Stealer |
7536 | venomderek.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |