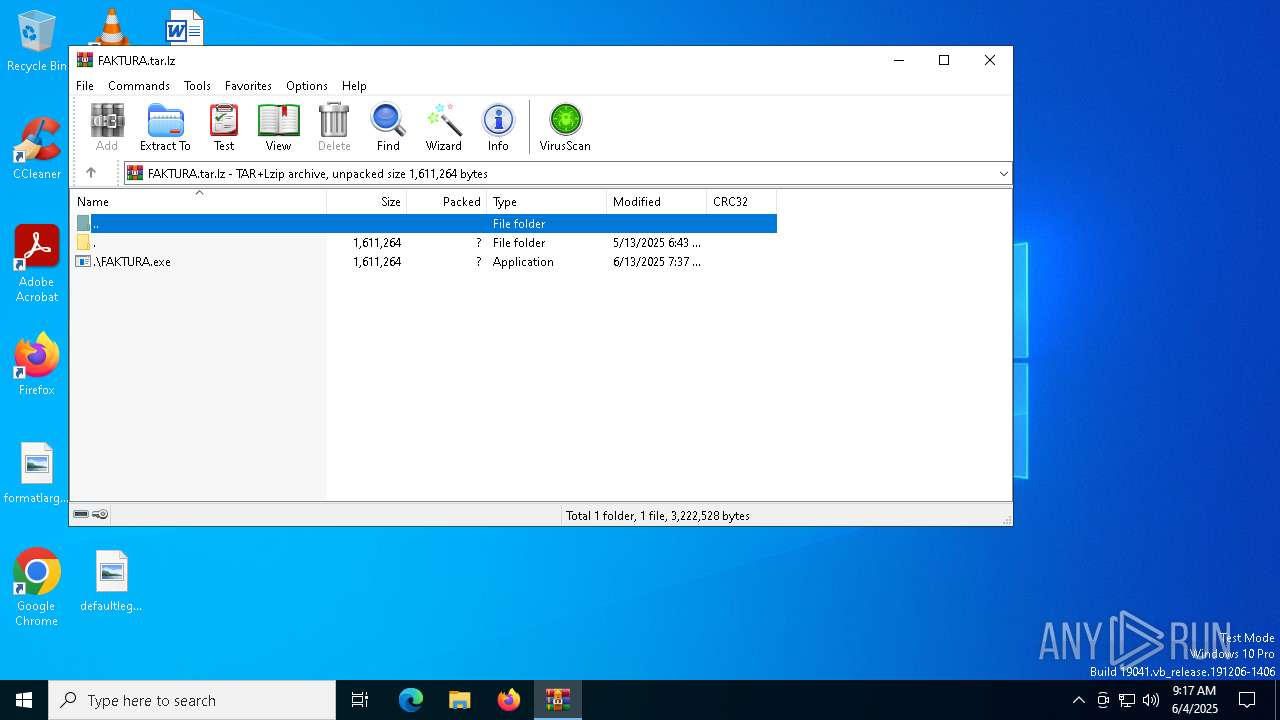
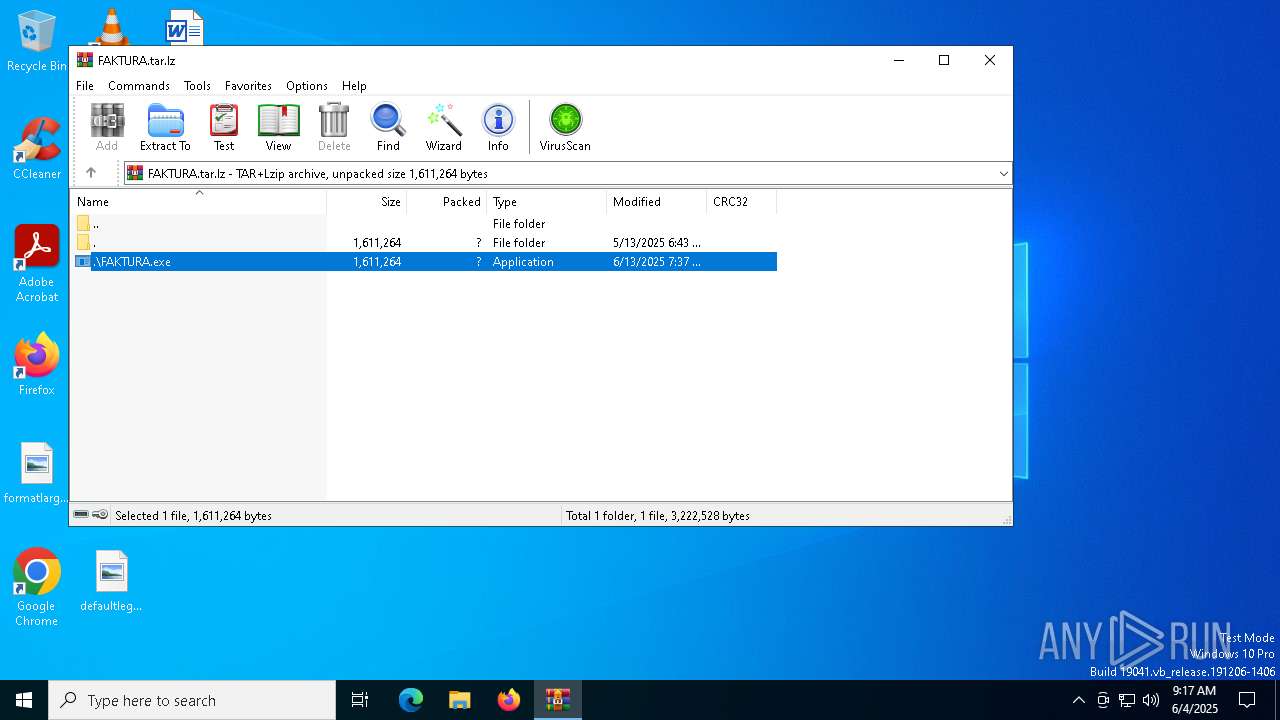
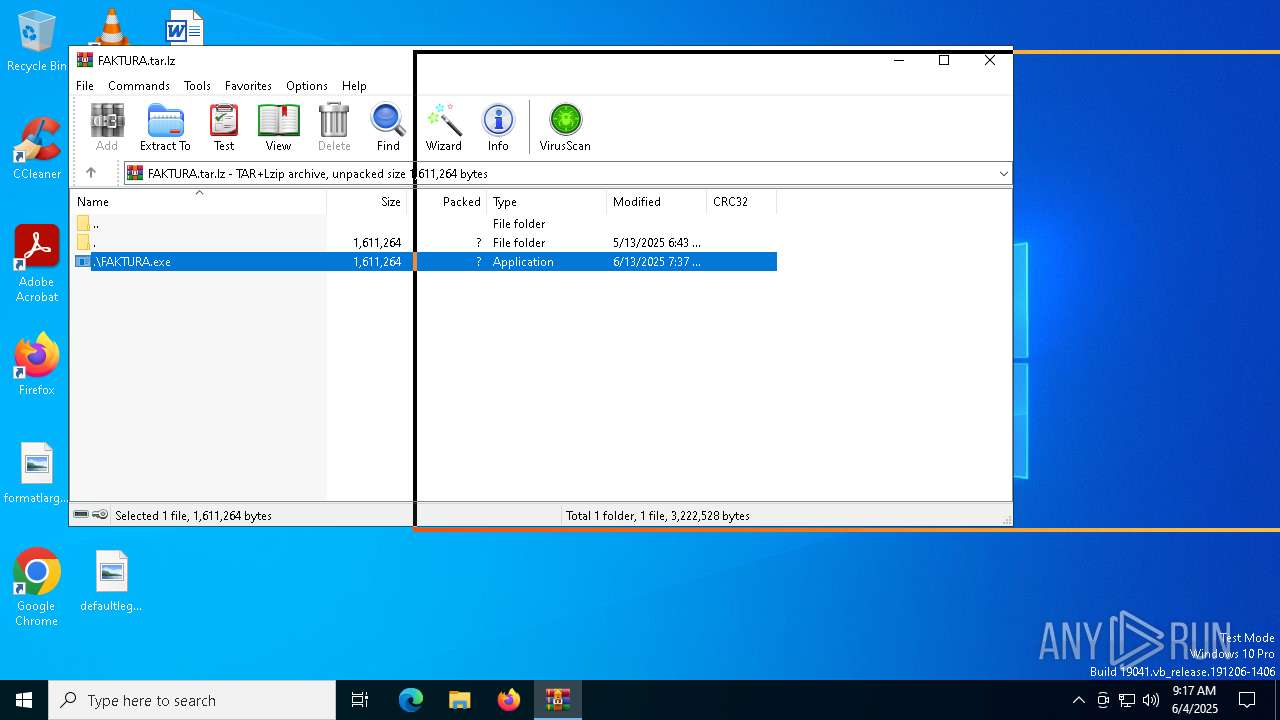
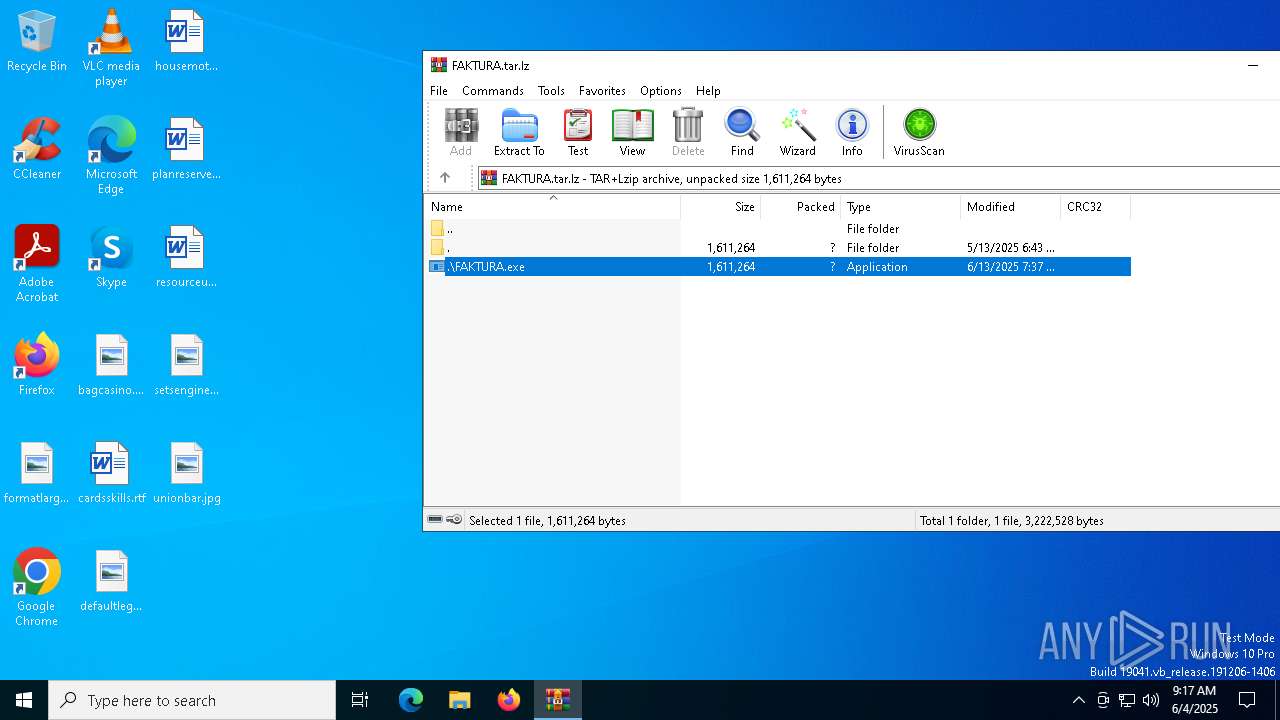
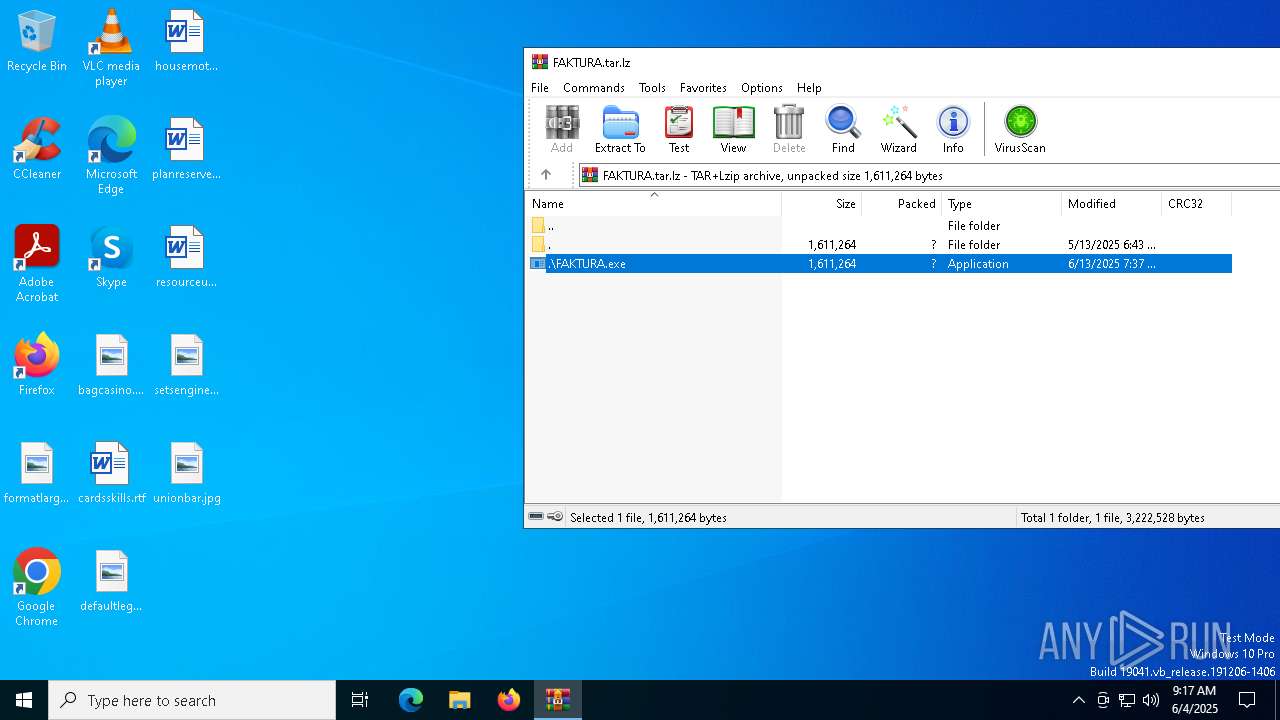
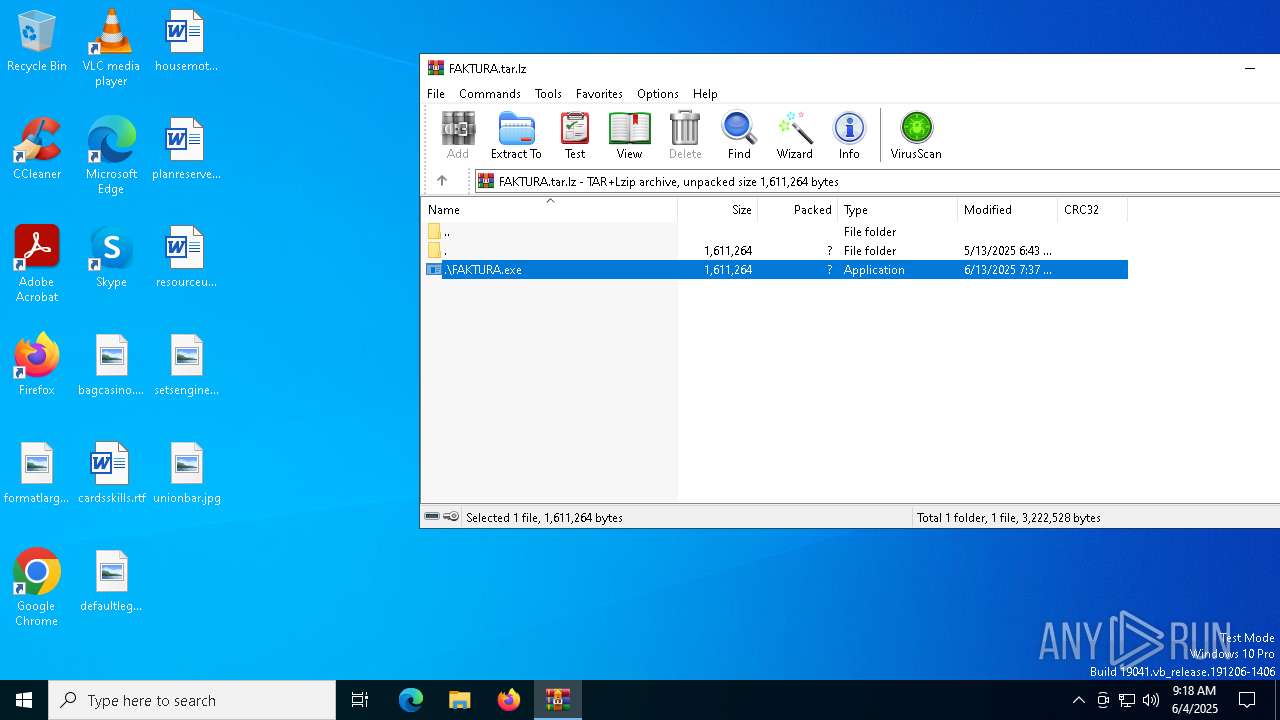
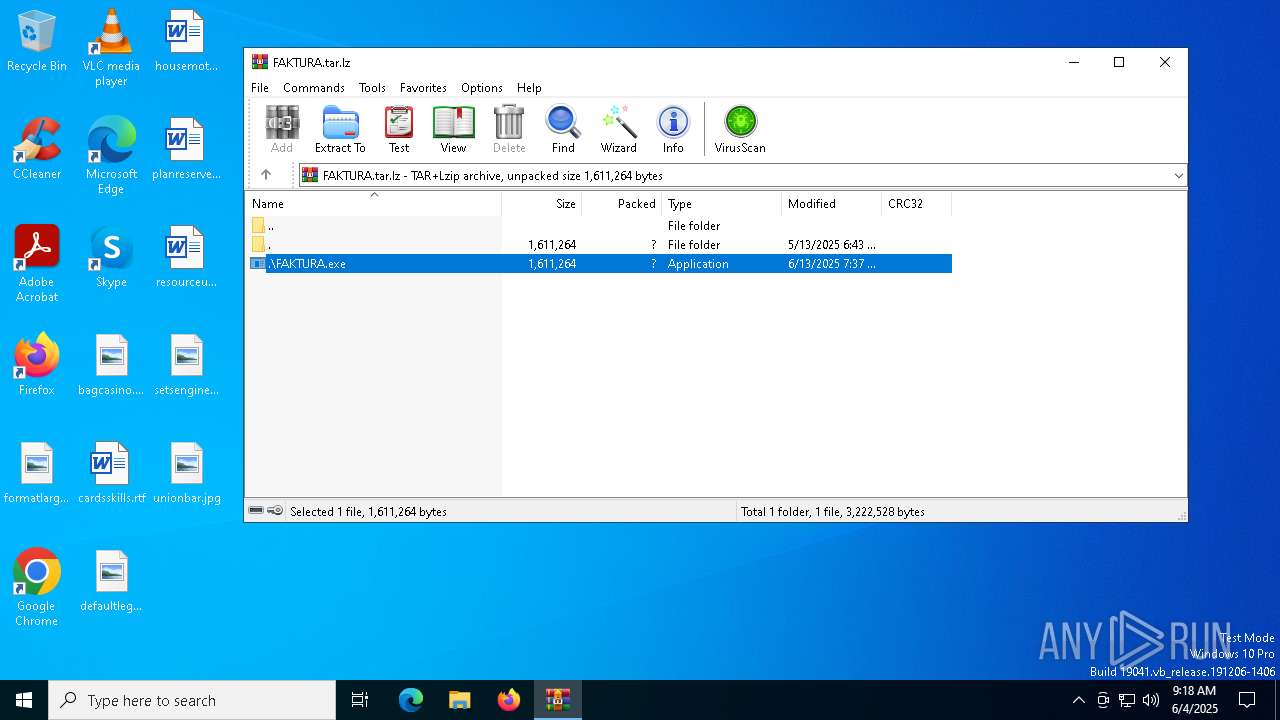
| File name: | FAKTURA.tar.lz |
| Full analysis: | https://app.any.run/tasks/0a0f81d9-6d48-4fcc-8af3-17730621588f |
| Verdict: | Malicious activity |
| Threats: | DBatLoader is a loader malware used for distributing payloads of different types, including WarzoneRAT and Formbook. It is employed in multi-stage attacks that usually start with a phishing email carrying a malicious attachment. |
| Analysis date: | June 04, 2025, 09:17:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-lzip |
| File info: | lzip compressed data, version: 1 |
| MD5: | B7AAF85E1B3EC2C1AF0098AE92D3E46E |
| SHA1: | D0F68506C77F84E098432EC2DF282DD7E0F18018 |
| SHA256: | 09C244D2E7895FA18ACD16451B0BB2CE92A5A5D1BB5E2A4C1E41AFBCA7E8EDB6 |
| SSDEEP: | 49152:KoR2m11VfcNhpSCUxDTFCMyZ0kUqm3xk+F7RUawInAHcFTxn7cFH1VjlMSDp5ez5:KoR2SVfcNvSlDQSkvm5tVQkd7cF1vMZl |
MALICIOUS
GENERIC has been found (auto)
- FAKTURA.exe (PID: 3828)
DBATLOADER has been detected (YARA)
- FAKTURA.exe (PID: 3828)
REMCOS has been detected
- colorcpl.exe (PID: 8036)
- colorcpl.exe (PID: 8036)
REMCOS mutex has been found
- colorcpl.exe (PID: 8036)
- colorcpl.exe (PID: 5608)
- SndVol.exe (PID: 7568)
- SndVol.exe (PID: 1452)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7928)
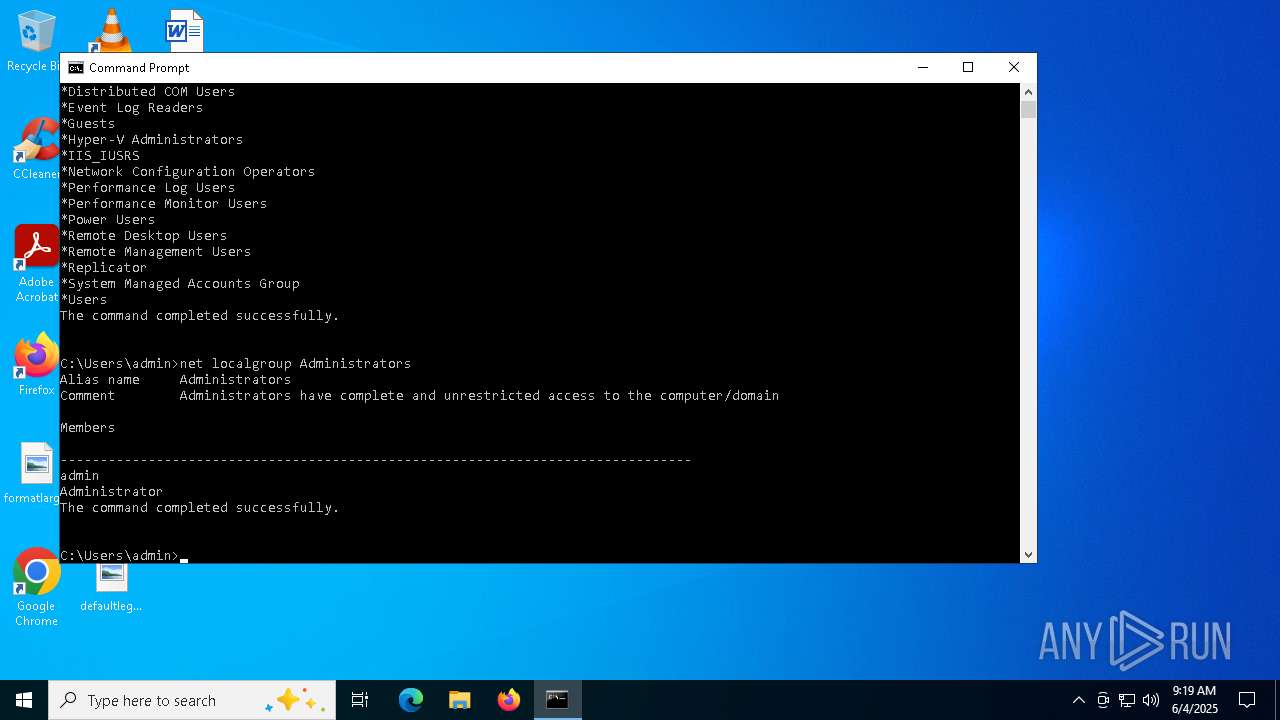
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 8084)
- net.exe (PID: 7616)
- net.exe (PID: 1228)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4400)
- FAKTURA.exe (PID: 3828)
- Cmwdnsyn.PIF (PID: 6584)
- Cmwdnsyn.PIF (PID: 1312)
- Cmwdnsyn.PIF (PID: 1120)
There is functionality for taking screenshot (YARA)
- FAKTURA.exe (PID: 3828)
- Cmwdnsyn.PIF (PID: 6584)
- Cmwdnsyn.PIF (PID: 1312)
Executing commands from ".cmd" file
- FAKTURA.exe (PID: 3828)
Starts CMD.EXE for commands execution
- FAKTURA.exe (PID: 3828)
Likely accesses (executes) a file from the Public directory
- esentutl.exe (PID: 6620)
- alpha.pif (PID: 5344)
- alpha.pif (PID: 5248)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7036)
Drops a file with a rarely used extension (PIF)
- esentutl.exe (PID: 6620)
- FAKTURA.exe (PID: 3828)
Starts itself from another location
- cmd.exe (PID: 1188)
Starts a Microsoft application from unusual location
- alpha.pif (PID: 5344)
- alpha.pif (PID: 5248)
Executable content was dropped or overwritten
- esentutl.exe (PID: 6620)
- FAKTURA.exe (PID: 3828)
Starts application with an unusual extension
- cmd.exe (PID: 1188)
- rundll32.exe (PID: 7388)
- rundll32.exe (PID: 6744)
- rundll32.exe (PID: 5744)
Created directory related to system
- alpha.pif (PID: 5344)
Connects to unusual port
- colorcpl.exe (PID: 8036)
The process executes via Task Scheduler
- rundll32.exe (PID: 7388)
- rundll32.exe (PID: 6744)
- rundll32.exe (PID: 5744)
INFO
Checks supported languages
- FAKTURA.exe (PID: 3828)
- alpha.pif (PID: 5344)
- alpha.pif (PID: 5248)
- Cmwdnsyn.PIF (PID: 1312)
- Cmwdnsyn.PIF (PID: 6584)
- Cmwdnsyn.PIF (PID: 1120)
Checks proxy server information
- FAKTURA.exe (PID: 3828)
- Cmwdnsyn.PIF (PID: 6584)
- slui.exe (PID: 7436)
- Cmwdnsyn.PIF (PID: 1120)
- Cmwdnsyn.PIF (PID: 1312)
Reads the computer name
- FAKTURA.exe (PID: 3828)
- Cmwdnsyn.PIF (PID: 6584)
- Cmwdnsyn.PIF (PID: 1120)
- Cmwdnsyn.PIF (PID: 1312)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4400)
Creates files in the program directory
- FAKTURA.exe (PID: 3828)
- colorcpl.exe (PID: 8036)
Compiled with Borland Delphi (YARA)
- FAKTURA.exe (PID: 3828)
- Cmwdnsyn.PIF (PID: 6584)
- Cmwdnsyn.PIF (PID: 1312)
The sample compiled with english language support
- esentutl.exe (PID: 6620)
Reads the machine GUID from the registry
- FAKTURA.exe (PID: 3828)
- Cmwdnsyn.PIF (PID: 6584)
- Cmwdnsyn.PIF (PID: 1312)
- Cmwdnsyn.PIF (PID: 1120)
Reads the software policy settings
- slui.exe (PID: 3884)
- slui.exe (PID: 7436)
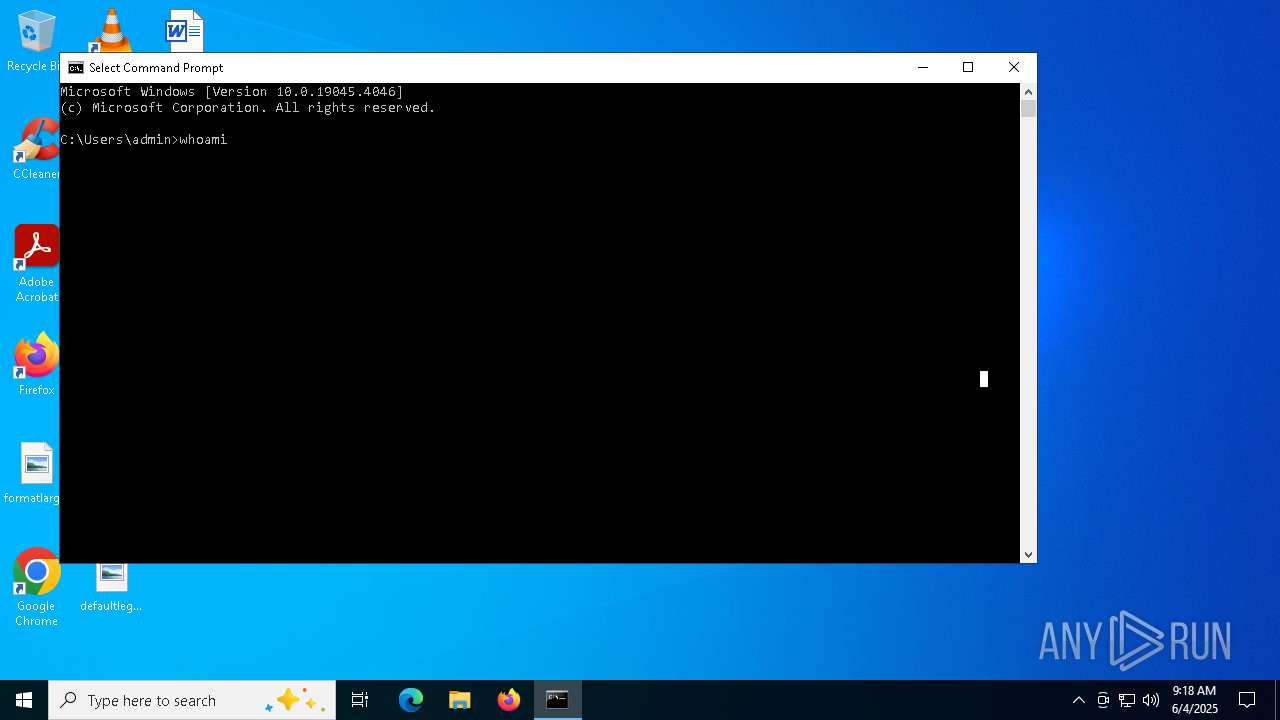
Manual execution by a user
- cmd.exe (PID: 8084)
- cmd.exe (PID: 8048)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 7388)
- rundll32.exe (PID: 6744)
- rundll32.exe (PID: 5744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lz | | | LZIP compressed archive (100) |
|---|
Total processes
166
Monitored processes
37
Malicious processes
8
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1120 | "C:\Users\admin\Links\Cmwdnsyn.PIF" | C:\Users\admin\Links\Cmwdnsyn.PIF | — | rundll32.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1188 | C:\WINDOWS\system32\cmd.exe /c C:\\ProgramData\\1023.cmd | C:\Windows\SysWOW64\cmd.exe | — | FAKTURA.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | net localgroup Administrators | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | "C:\Users\admin\Links\Cmwdnsyn.PIF" | C:\Users\admin\Links\Cmwdnsyn.PIF | — | rundll32.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1452 | C:\Windows\System32\SndVol.exe | C:\Windows\SysWOW64\SndVol.exe | Cmwdnsyn.PIF | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Volume Mixer Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | C:\WINDOWS\system32\net1 localgroup Administrators | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3828 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.46995\FAKTURA.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.46995\FAKTURA.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
8 283
Read events
8 260
Write events
23
Delete events
0
Modification events
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\FAKTURA.tar.lz | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8036) colorcpl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-BL8XAF |
| Operation: | write | Name: | exepath |
Value: 0BE6702401F3D9040CB28EB741DDB617698BE2967206DEAF71B30558060F49079C4A77FB5077066367CCD5E5FBE379C5279C4CEEE2F86B2225E1DDF6E7E3001D8474 | |||
| (PID) Process: | (8036) colorcpl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-BL8XAF |
| Operation: | write | Name: | licence |
Value: 6545D47F92D8F1615EF33B2648024E63 | |||
Executable files
3
Suspicious files
1
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8036 | colorcpl.exe | C:\ProgramData\remcos\logs.dat | binary | |
MD5:F32924D1E00F5061766BF4550368E208 | SHA256:01A6CC3482557745A95AB1B73C0BEC011AA7EBAB2C6BA2C94389CED9E546E2CD | |||
| 3828 | FAKTURA.exe | C:\ProgramData\neo.cmd | text | |
MD5:5BAF253744AD26F35BA17DB6B80763E9 | SHA256:9CBB41E6C4F8565A6D121B770FCF3F15A6891C8DF8BFBA6D0414B3AD3298BDBA | |||
| 6620 | esentutl.exe | C:\Users\Public\alpha.pif | executable | |
MD5:D3348AC2130C7E754754A6E9CB053B09 | SHA256:E9EF013238495BFFCE7459E059BFFE340A0F08B439EC94E7D4436F4E13714ECD | |||
| 3828 | FAKTURA.exe | C:\ProgramData\8095.cmd | text | |
MD5:9A020804EBA1FFAC2928D7C795144BBF | SHA256:A86C6C7A2BF9E12C45275A5E7EBEBD5E6D2BA302FE0A12600B7C9FDF283D9E63 | |||
| 3828 | FAKTURA.exe | C:\ProgramData\Cmwdnsyn.url | url | |
MD5:744AB3389AD665AEFCF10DB4CBE984F1 | SHA256:48B32C5F56A08B5B731190FF057CB3E46D5288B76FBB07794E76A13EB43FB4F2 | |||
| 3828 | FAKTURA.exe | C:\Users\admin\Links\Cmwdnsyn.PIF | executable | |
MD5:F6EE27081BF89AAD60F3996386EB0231 | SHA256:799EB6BFDCB552FE2CB6548E6953EC13B97B776C761478C92C3F425E9CAA3108 | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.46995\FAKTURA.exe | executable | |
MD5:F6EE27081BF89AAD60F3996386EB0231 | SHA256:799EB6BFDCB552FE2CB6548E6953EC13B97B776C761478C92C3F425E9CAA3108 | |||
| 3828 | FAKTURA.exe | C:\ProgramData\1023.cmd | text | |
MD5:1DF650CCA01129127D30063634AB5C03 | SHA256:EDD4094E7A82A6FF8BE65D6B075E9513BD15A6B74F8032B5C10CE18F7191FA60 | |||
| 3828 | FAKTURA.exe | C:\ProgramData\36.cmd | text | |
MD5:36BCB50025875F43932C6C7D76C538EC | SHA256:EF31C01D32537A66832F802FBA6ABA25048A028C7847BE8F70D01E504190DDCD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
59
DNS requests
38
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.25.50.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5408 | svchost.exe | GET | 200 | 184.25.50.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5408 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7344 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 184.25.50.10:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5408 | svchost.exe | 184.25.50.10:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5408 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5408 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
craekuro.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |