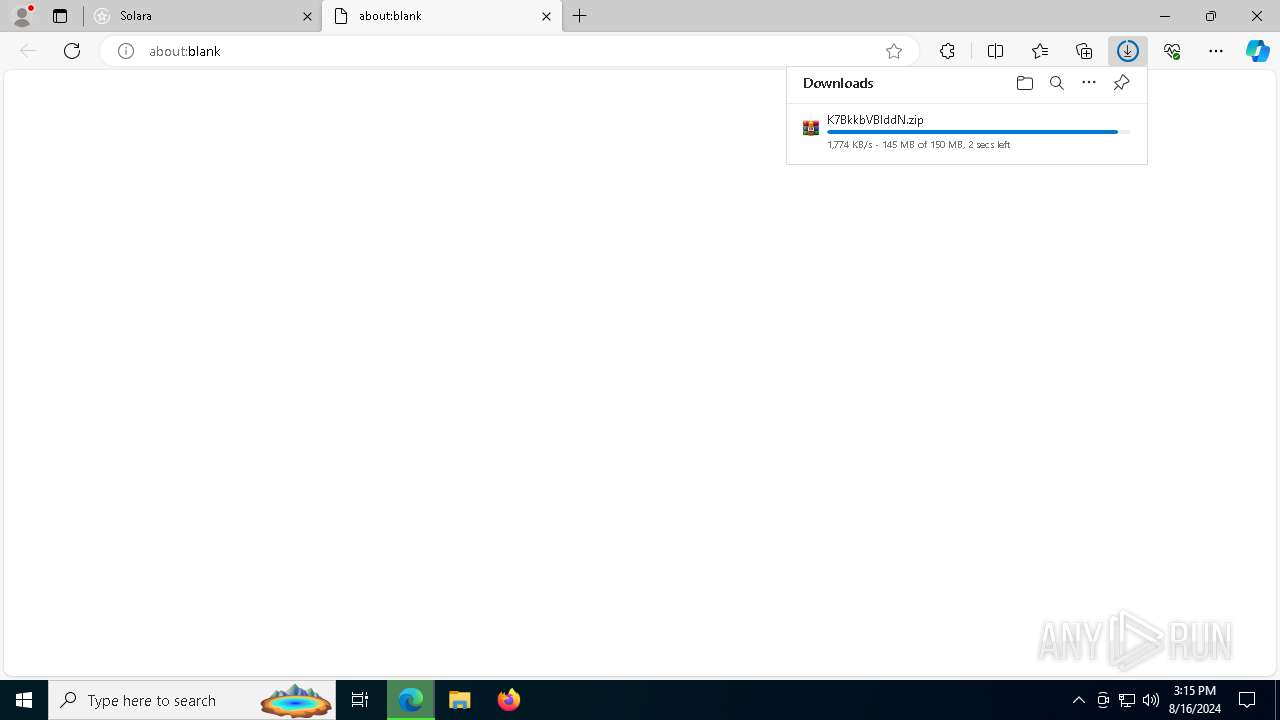
| URL: | https://byfron.cc/solara/ |
| Full analysis: | https://app.any.run/tasks/3cd5a47a-b2df-4ebc-b7c9-b755a3b837c1 |
| Verdict: | Malicious activity |
| Threats: | MetaStealer is an info-stealing malware primarily targeting sensitive data like login credentials, payment details, and browser history. It typically infects systems via phishing emails or malicious downloads and can exfiltrate data to a command and control (C2) server. MetaStealer is known for its stealthy techniques, including evasion and persistence mechanisms, which make it difficult to detect. This malware has been actively used in various cyberattacks, particularly for financial theft and credential harvesting from individuals and organizations. |
| Analysis date: | August 16, 2024, 15:13:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9EE0784A555D35EBF7649CEE0D6EAAB7 |
| SHA1: | 284EC66669439498DF83AD88CC435FCE2C701C07 |
| SHA256: | 09B15244DDAC559DB122BC47215F157162BE1373BFA7A24645EA79E0F1261016 |
| SSDEEP: | 3:N8Ca:2Ca |
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 7328)
- findstr.exe (PID: 7432)
- findstr.exe (PID: 1664)
- findstr.exe (PID: 2796)
Stealers network behavior
- RegAsm.exe (PID: 6572)
METASTEALER has been detected (SURICATA)
- RegAsm.exe (PID: 6572)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 6572)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 6572)
Connects to the CnC server
- RegAsm.exe (PID: 6572)
SUSPICIOUS
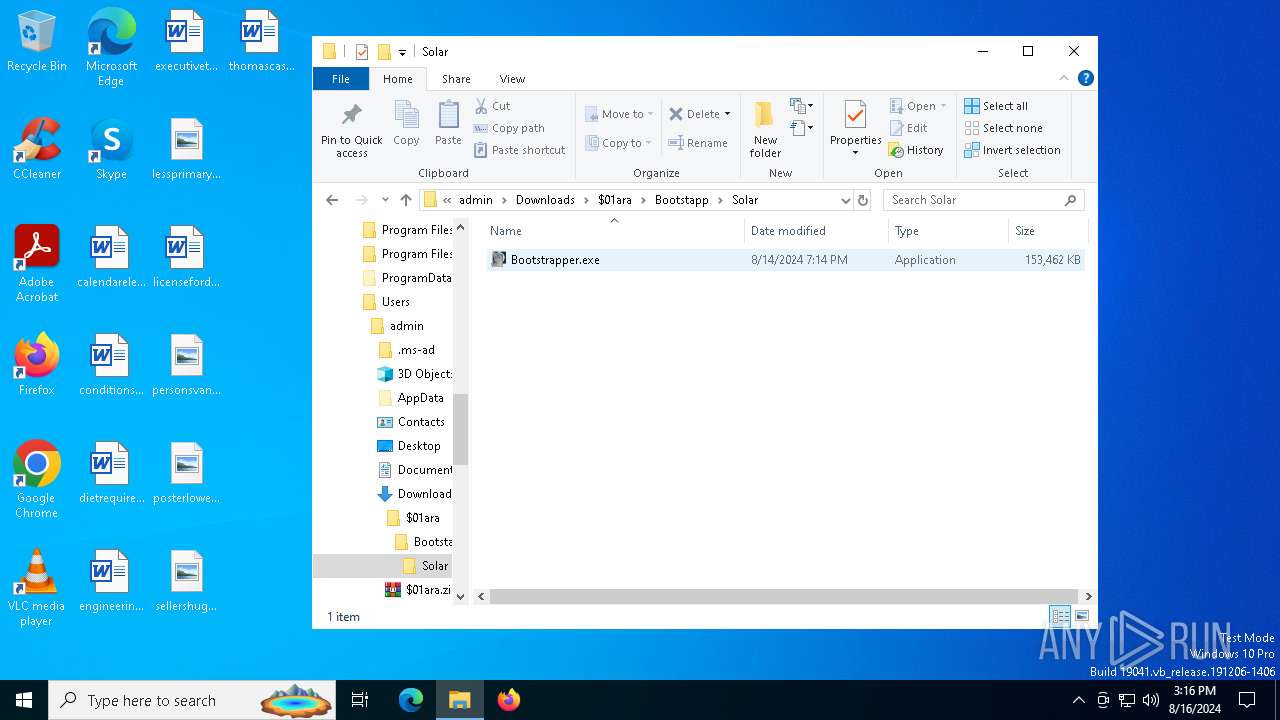
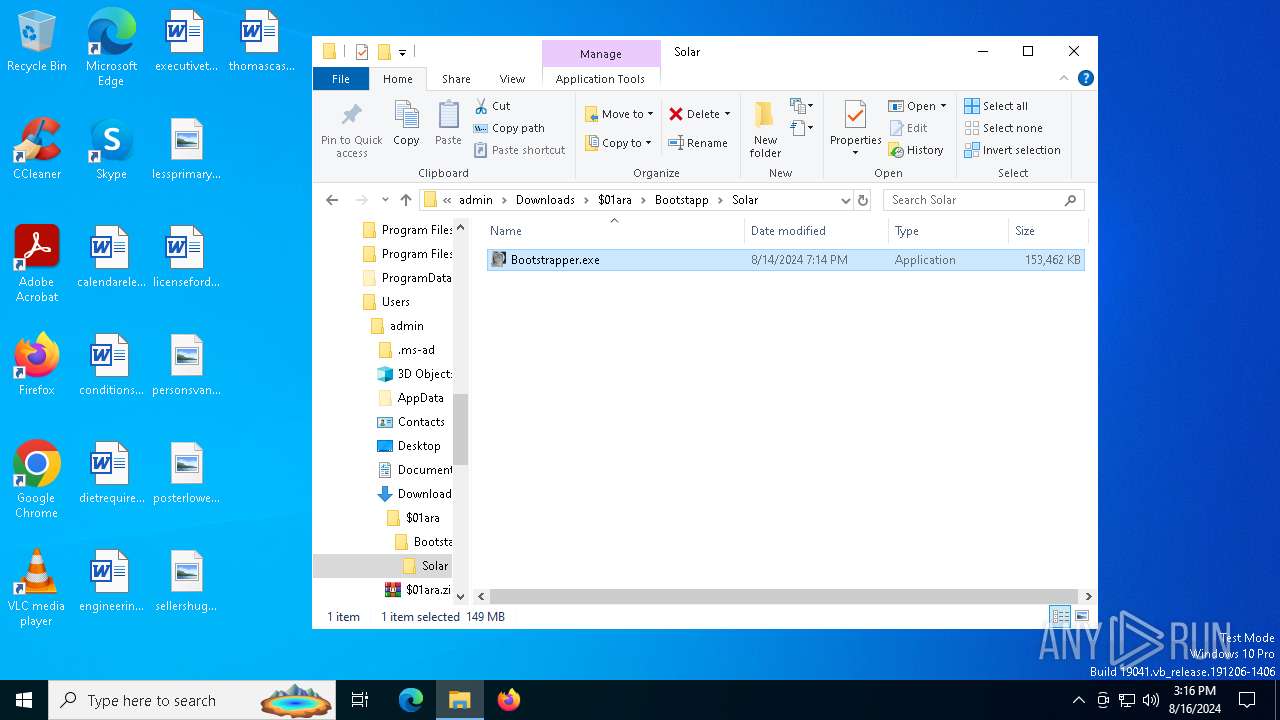
Reads the date of Windows installation
- Bootstrapper.exe (PID: 7524)
- Bootstrapper.exe (PID: 6476)
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 7524)
- Bootstrapper.exe (PID: 6476)
Executing commands from ".cmd" file
- Bootstrapper.exe (PID: 7524)
- Bootstrapper.exe (PID: 6476)
Starts CMD.EXE for commands execution
- Bootstrapper.exe (PID: 7524)
- cmd.exe (PID: 7532)
- Bootstrapper.exe (PID: 6476)
- cmd.exe (PID: 6424)
Get information on the list of running processes
- cmd.exe (PID: 7532)
- cmd.exe (PID: 6424)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 7532)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7532)
- cmd.exe (PID: 6424)
Application launched itself
- cmd.exe (PID: 7532)
- cmd.exe (PID: 6424)
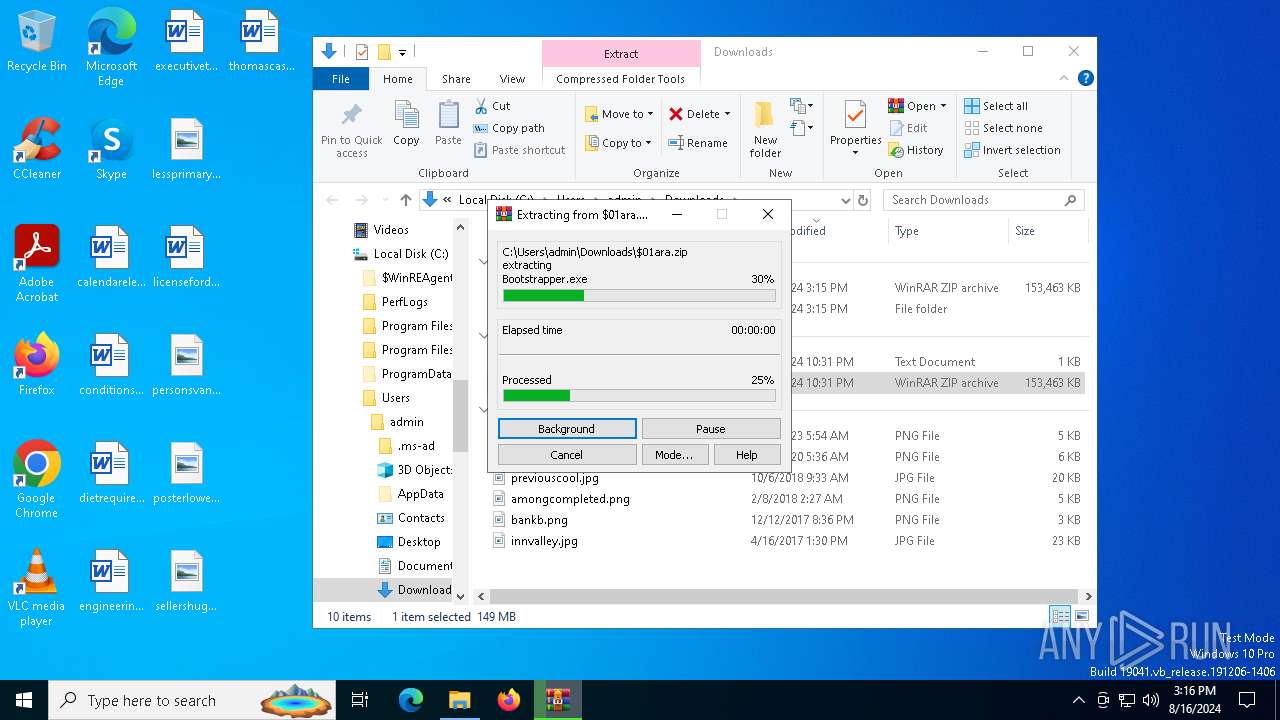
Executable content was dropped or overwritten
- cmd.exe (PID: 7532)
- Sampling.pif (PID: 7608)
- Sampling.pif (PID: 640)
Drops the executable file immediately after the start
- cmd.exe (PID: 7532)
- Sampling.pif (PID: 7608)
- Sampling.pif (PID: 640)
The process creates files with name similar to system file names
- Sampling.pif (PID: 7608)
- Sampling.pif (PID: 640)
Process drops legitimate windows executable
- Sampling.pif (PID: 7608)
- Sampling.pif (PID: 640)
Starts a Microsoft application from unusual location
- RegAsm.exe (PID: 6676)
- RegAsm.exe (PID: 6572)
- RegAsm.exe (PID: 3660)
The executable file from the user directory is run by the CMD process
- Sampling.pif (PID: 7608)
- Sampling.pif (PID: 640)
Starts application with an unusual extension
- cmd.exe (PID: 7532)
- cmd.exe (PID: 6424)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 6572)
Searches for installed software
- RegAsm.exe (PID: 6572)
Connects to unusual port
- RegAsm.exe (PID: 6572)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6264)
- msedge.exe (PID: 7780)
Reads Environment values
- identity_helper.exe (PID: 7000)
- identity_helper.exe (PID: 7140)
- RegAsm.exe (PID: 6572)
Application launched itself
- msedge.exe (PID: 6264)
- msedge.exe (PID: 7780)
Checks supported languages
- identity_helper.exe (PID: 7000)
- identity_helper.exe (PID: 7140)
- Bootstrapper.exe (PID: 7524)
- Sampling.pif (PID: 7608)
- RegAsm.exe (PID: 6572)
- Bootstrapper.exe (PID: 6476)
- Sampling.pif (PID: 640)
Reads the computer name
- identity_helper.exe (PID: 7000)
- identity_helper.exe (PID: 7140)
- Bootstrapper.exe (PID: 7524)
- Sampling.pif (PID: 7608)
- RegAsm.exe (PID: 6572)
- Bootstrapper.exe (PID: 6476)
- Sampling.pif (PID: 640)
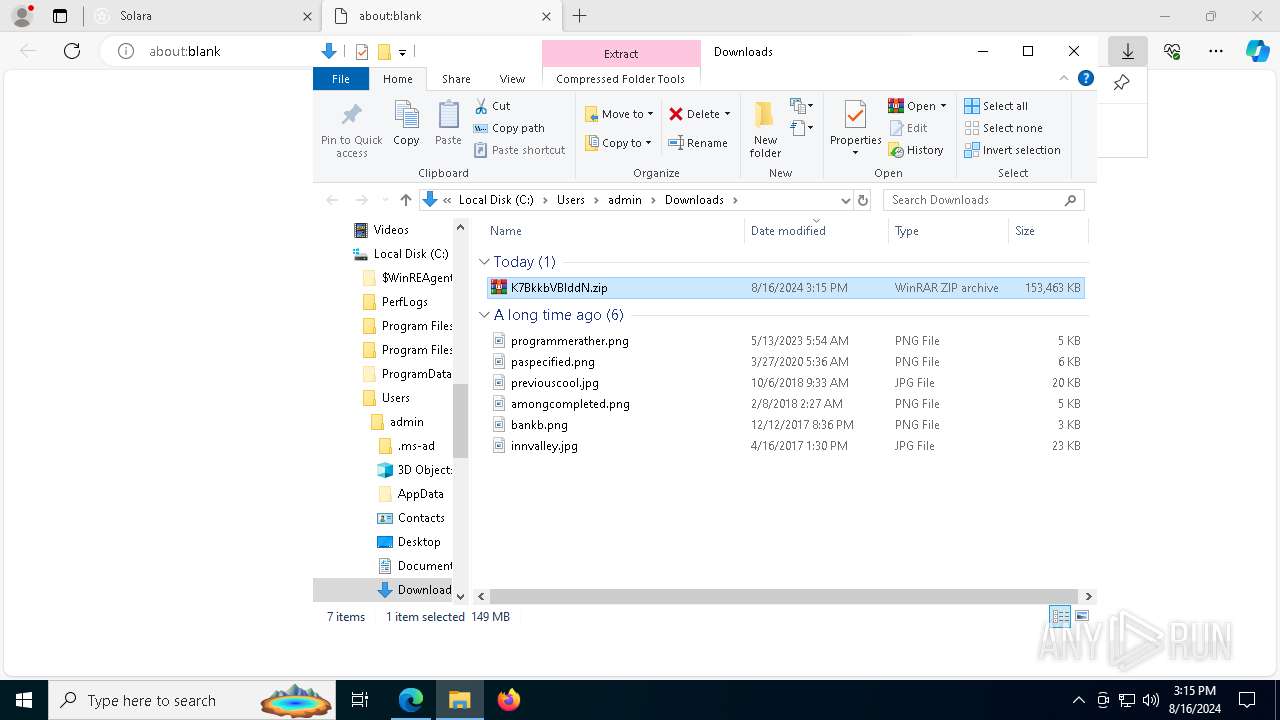
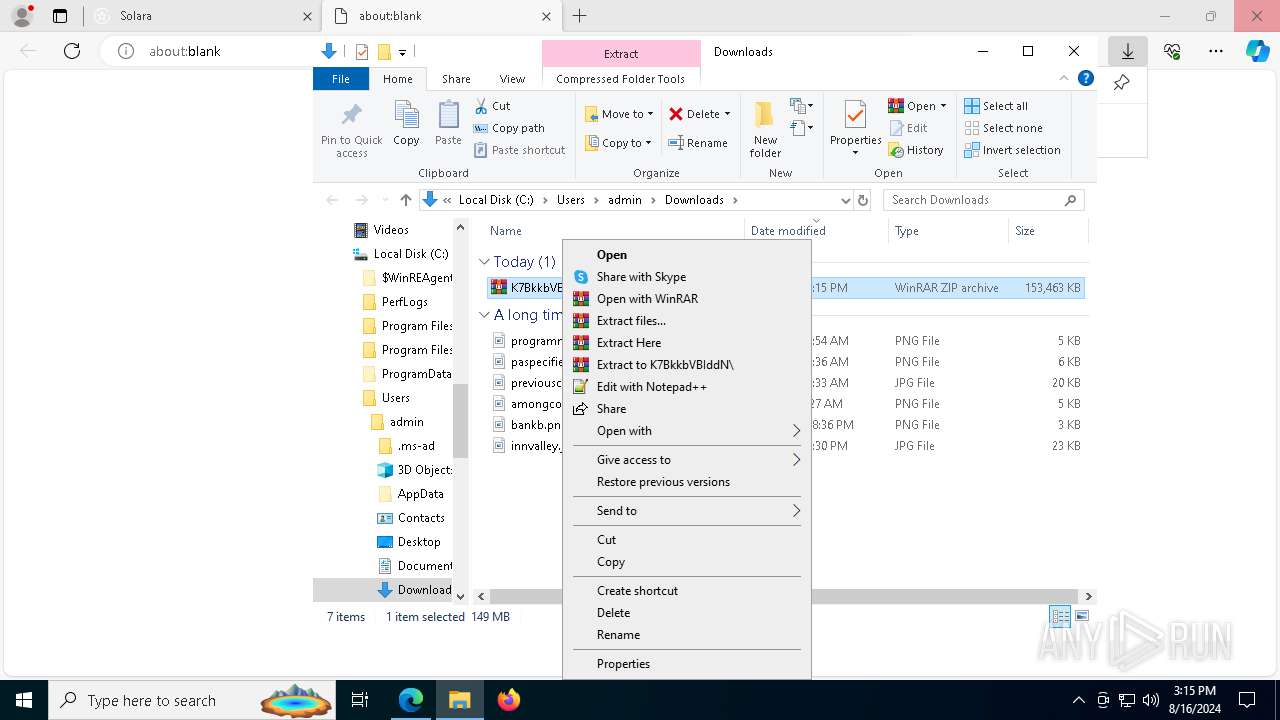
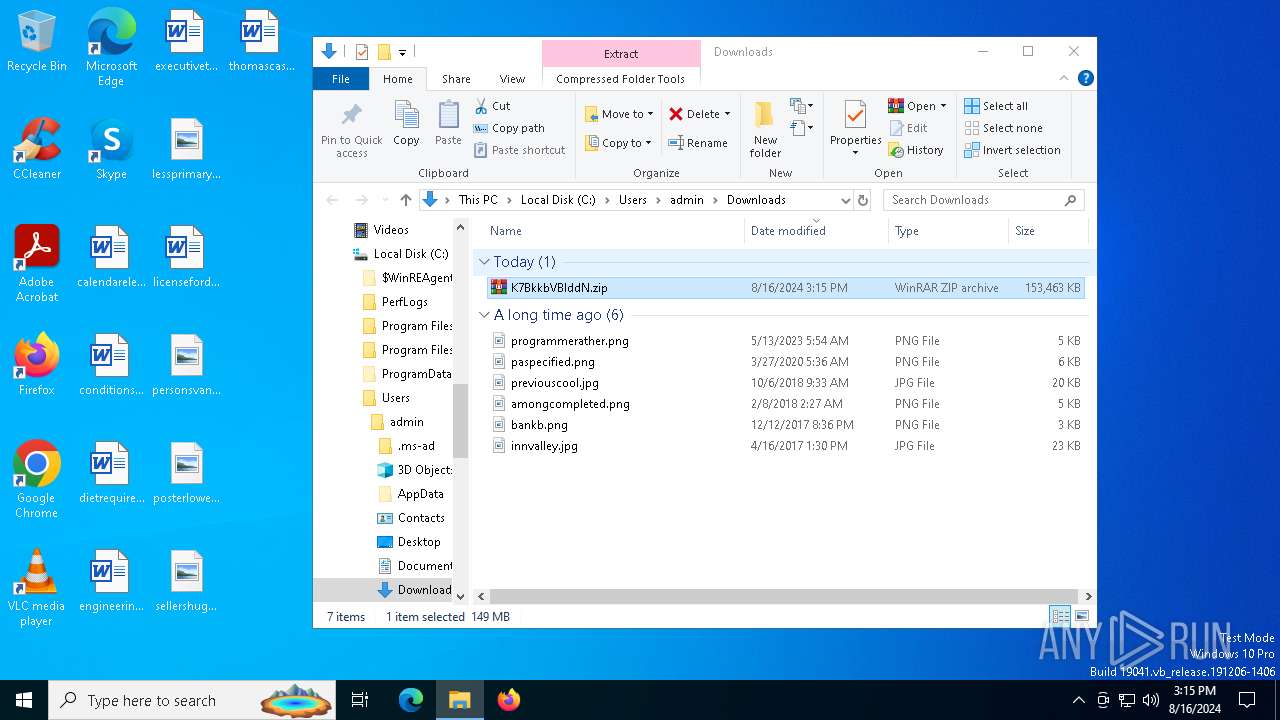
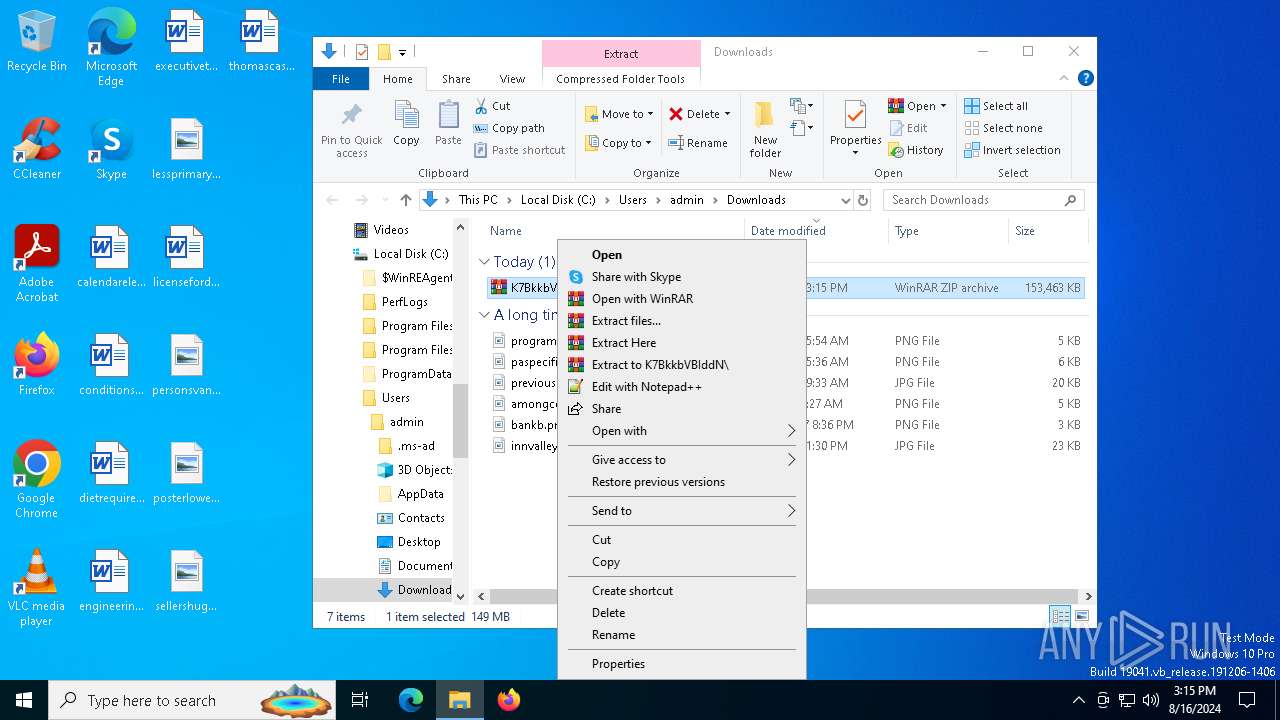
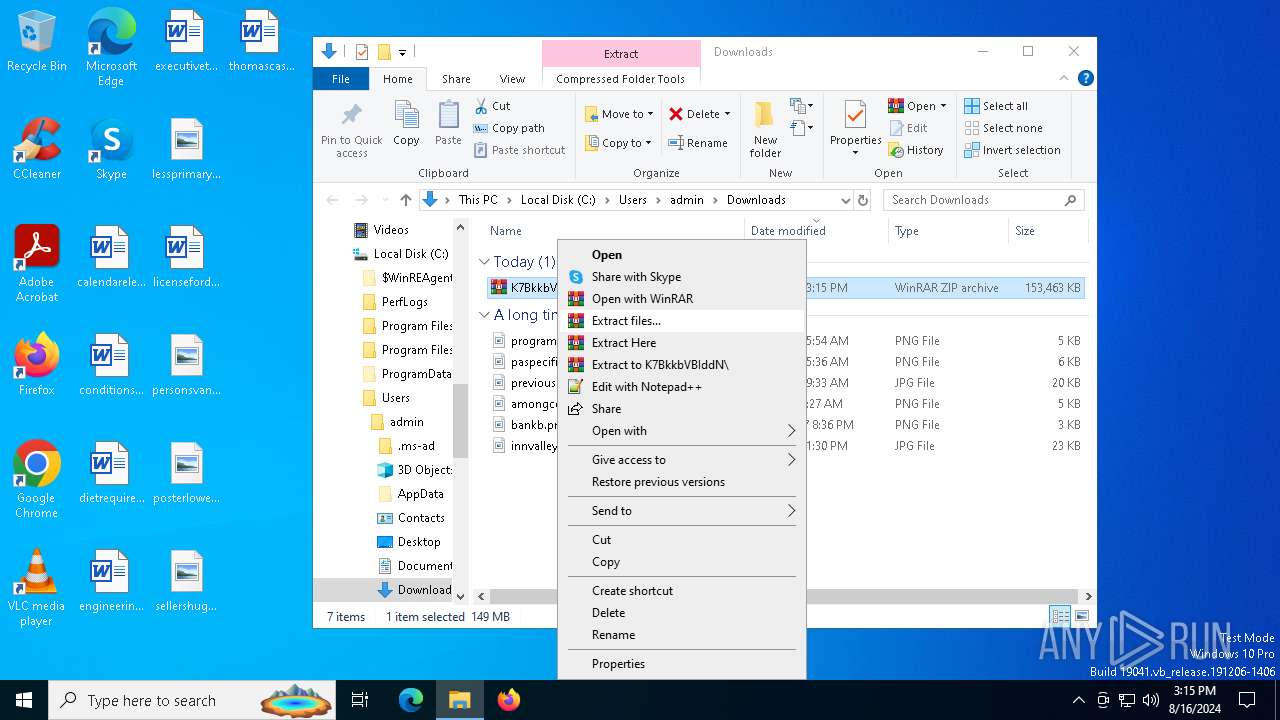
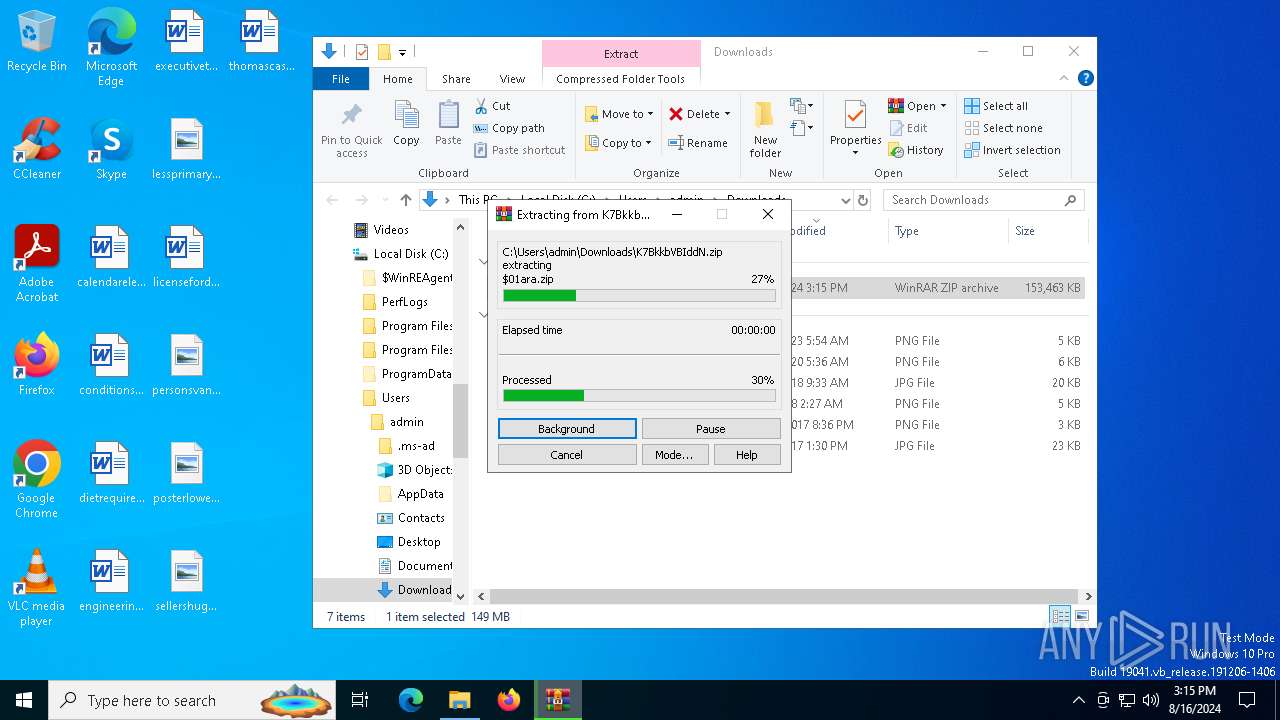
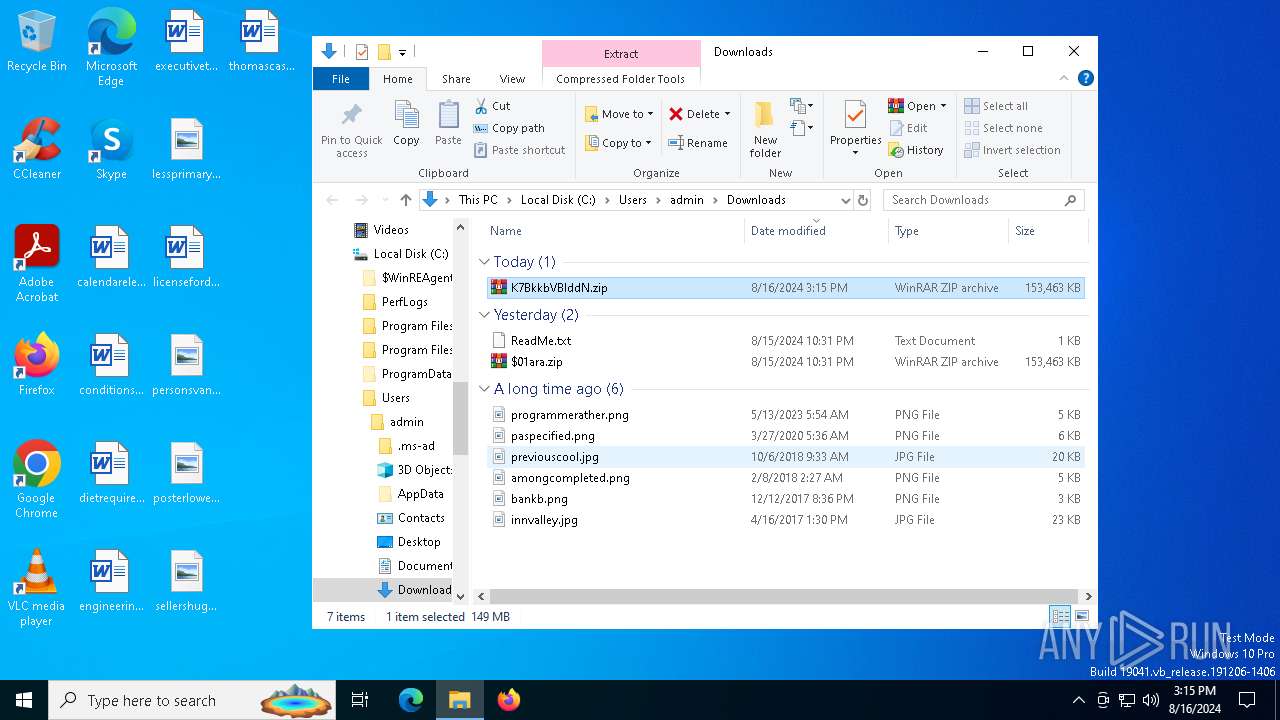
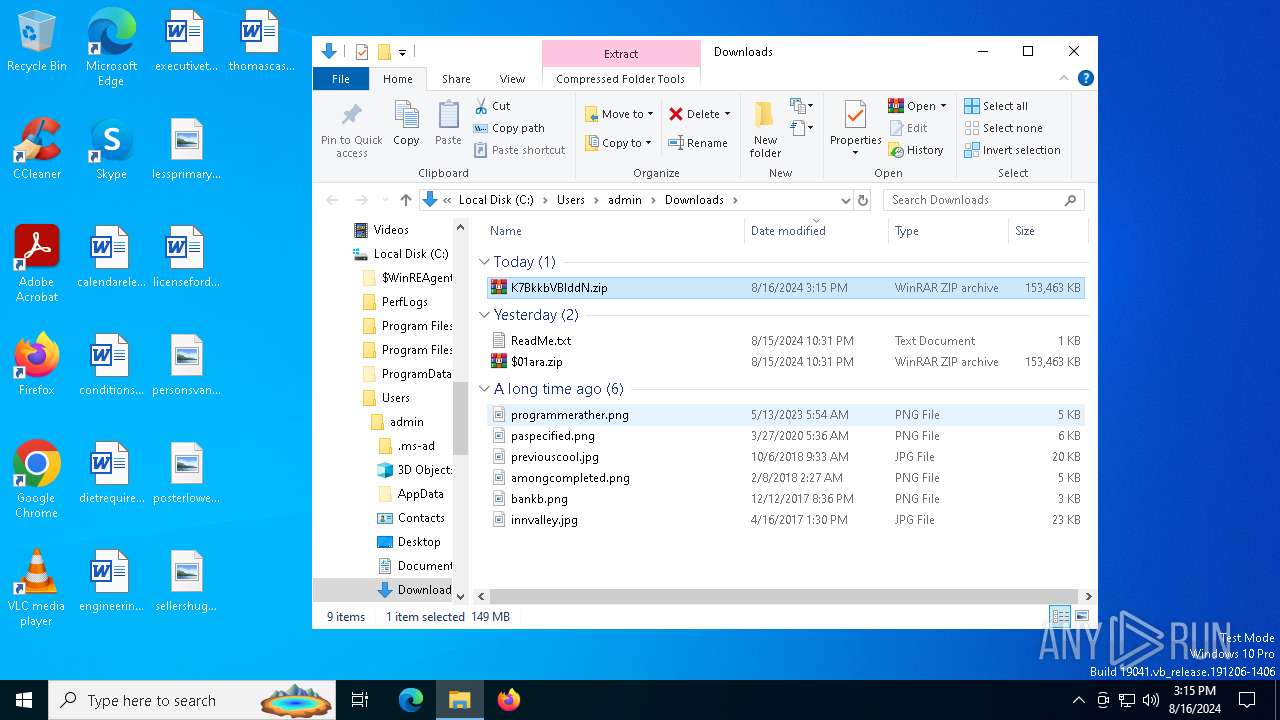
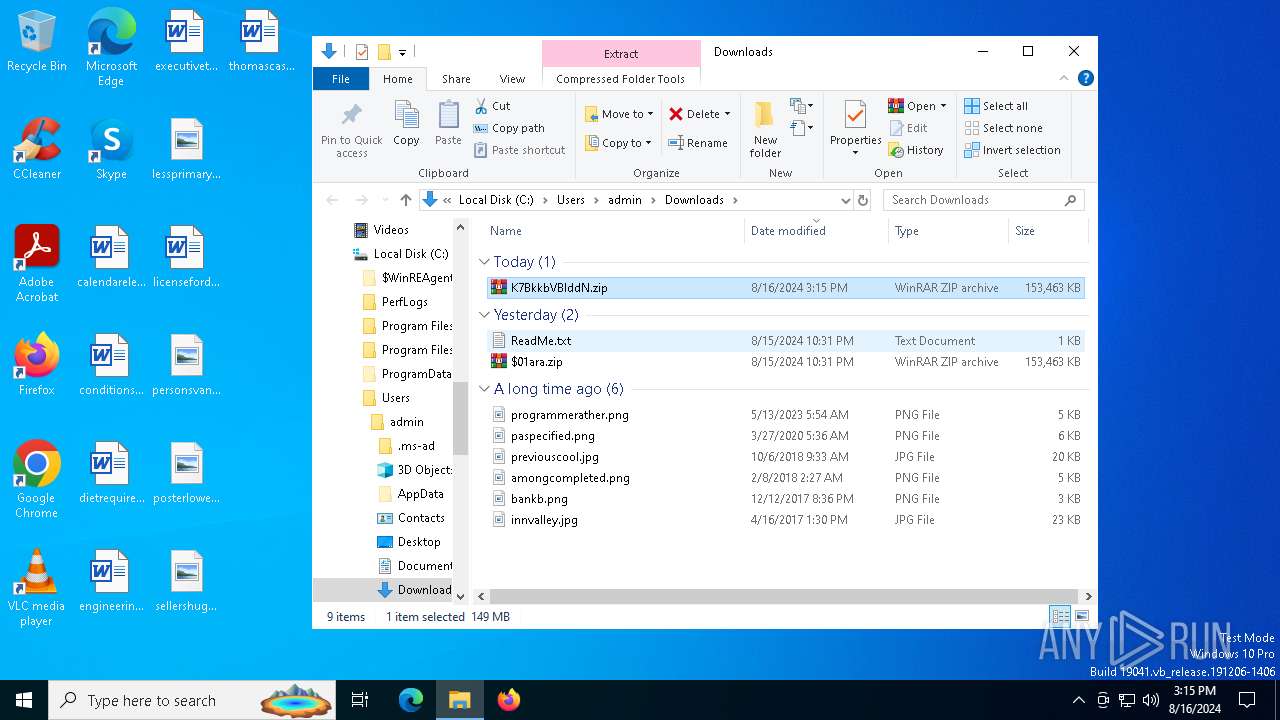
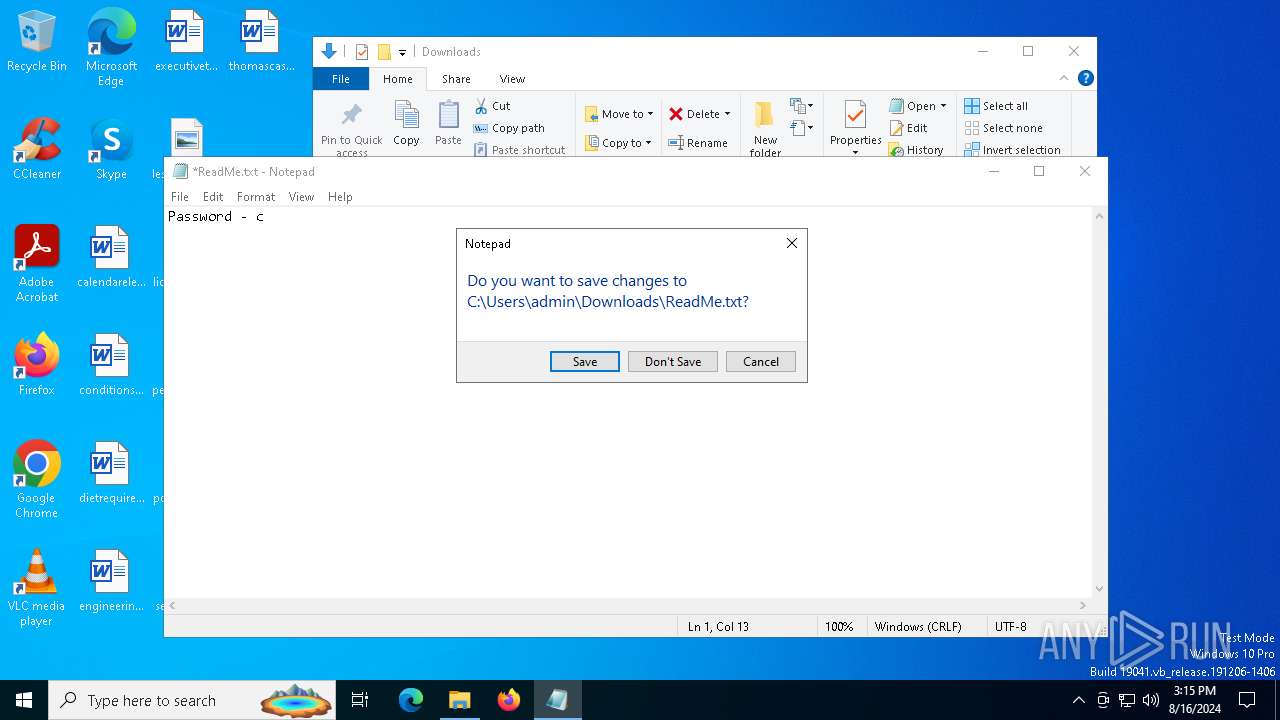
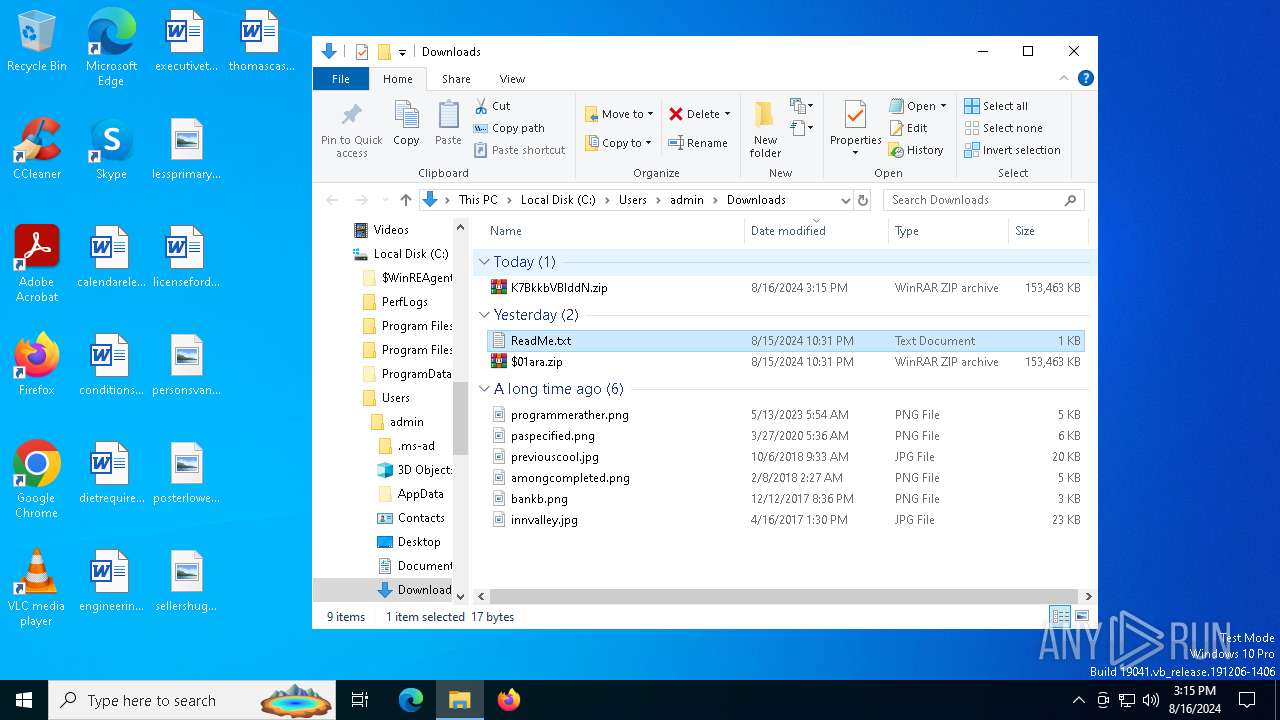
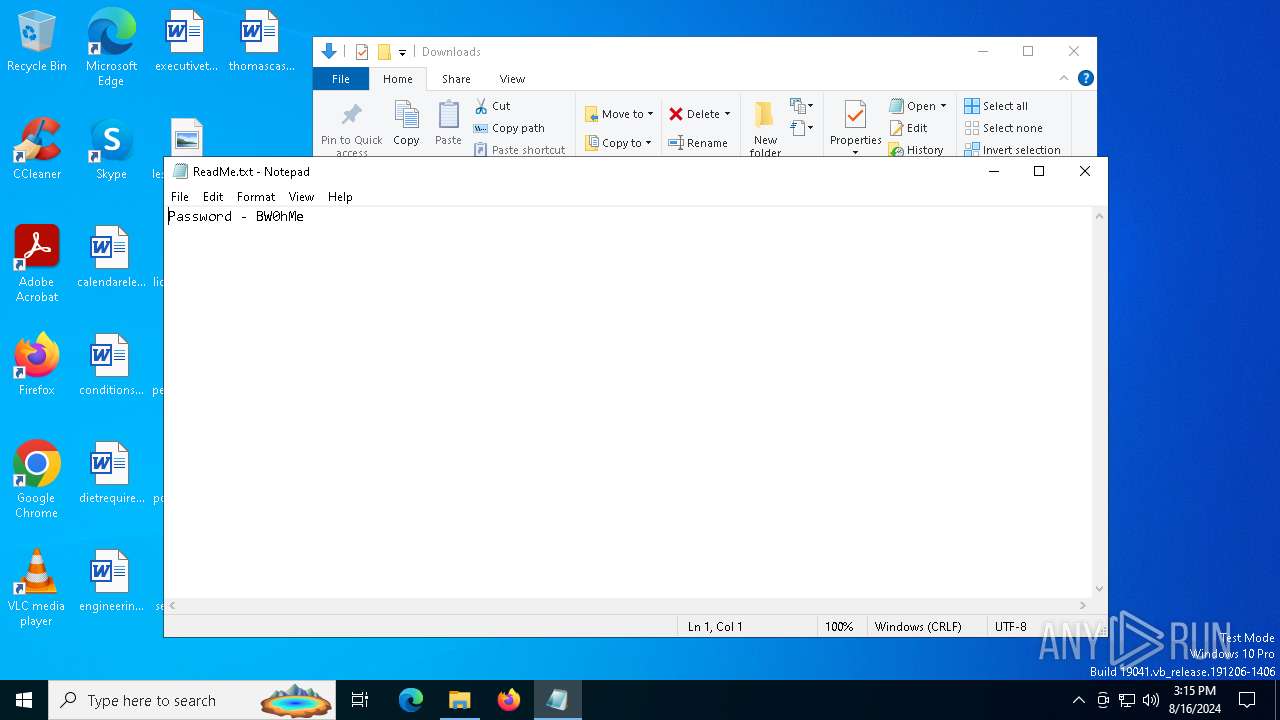
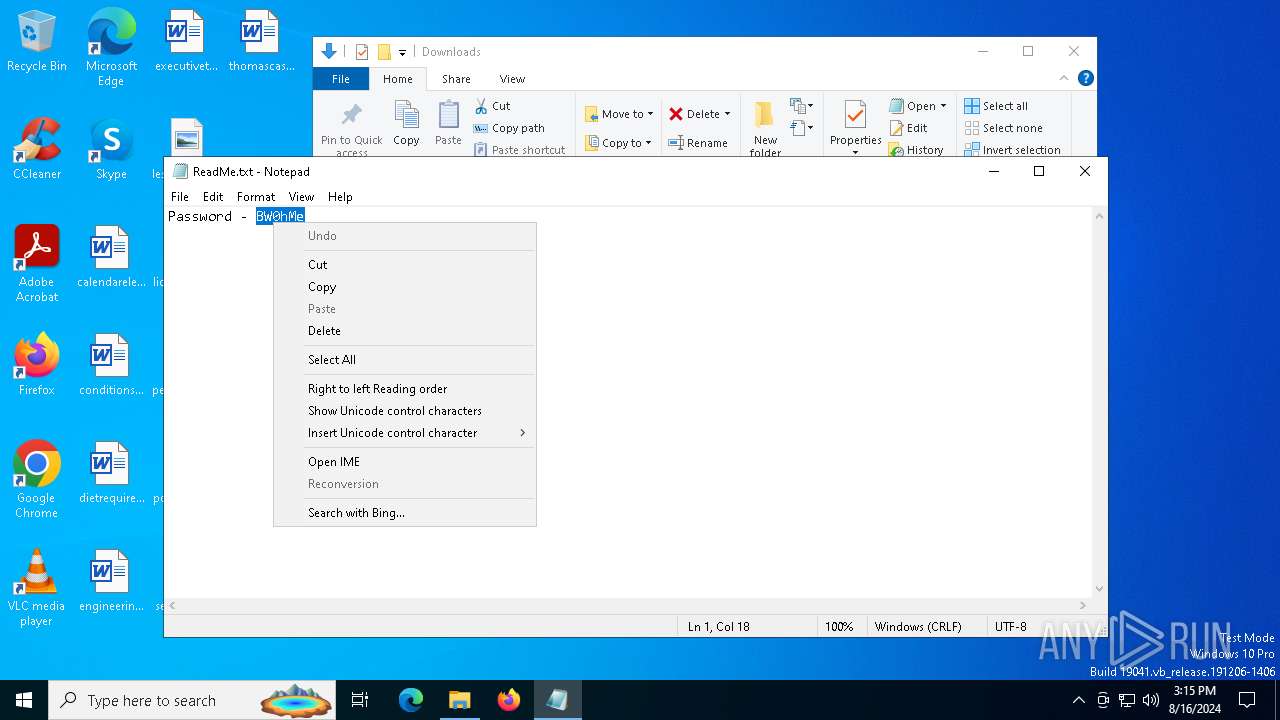
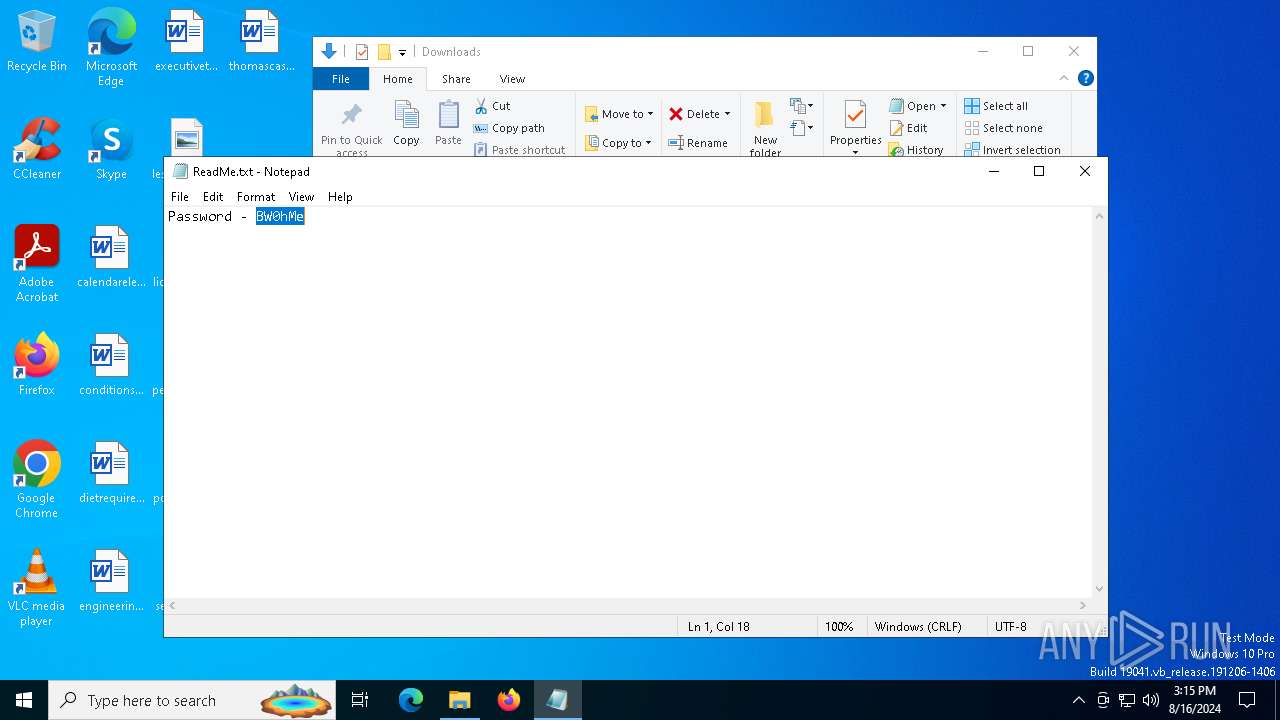
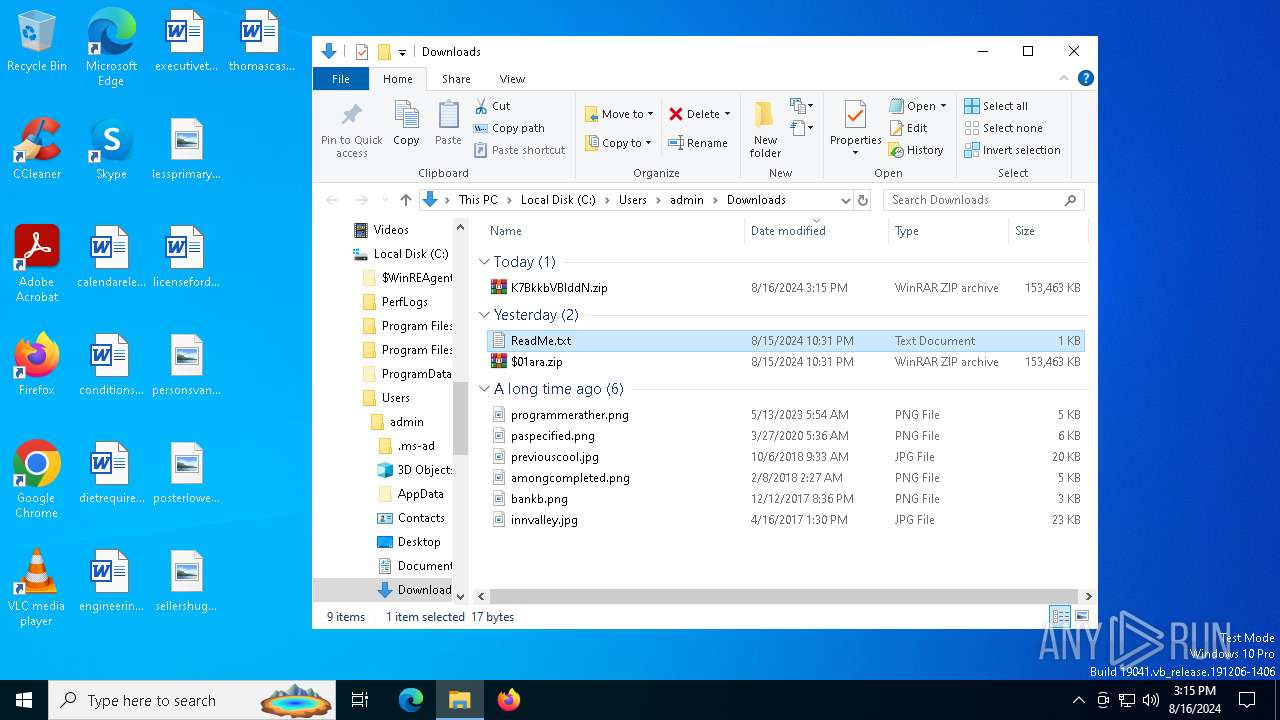
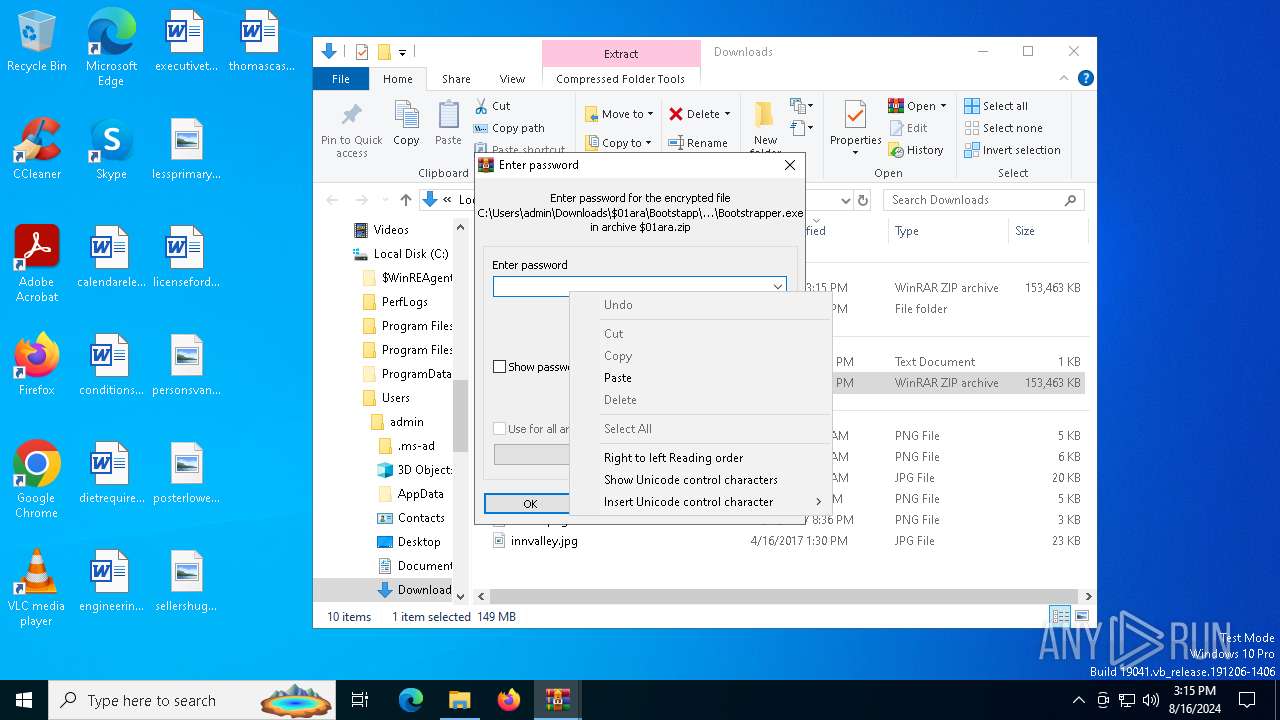
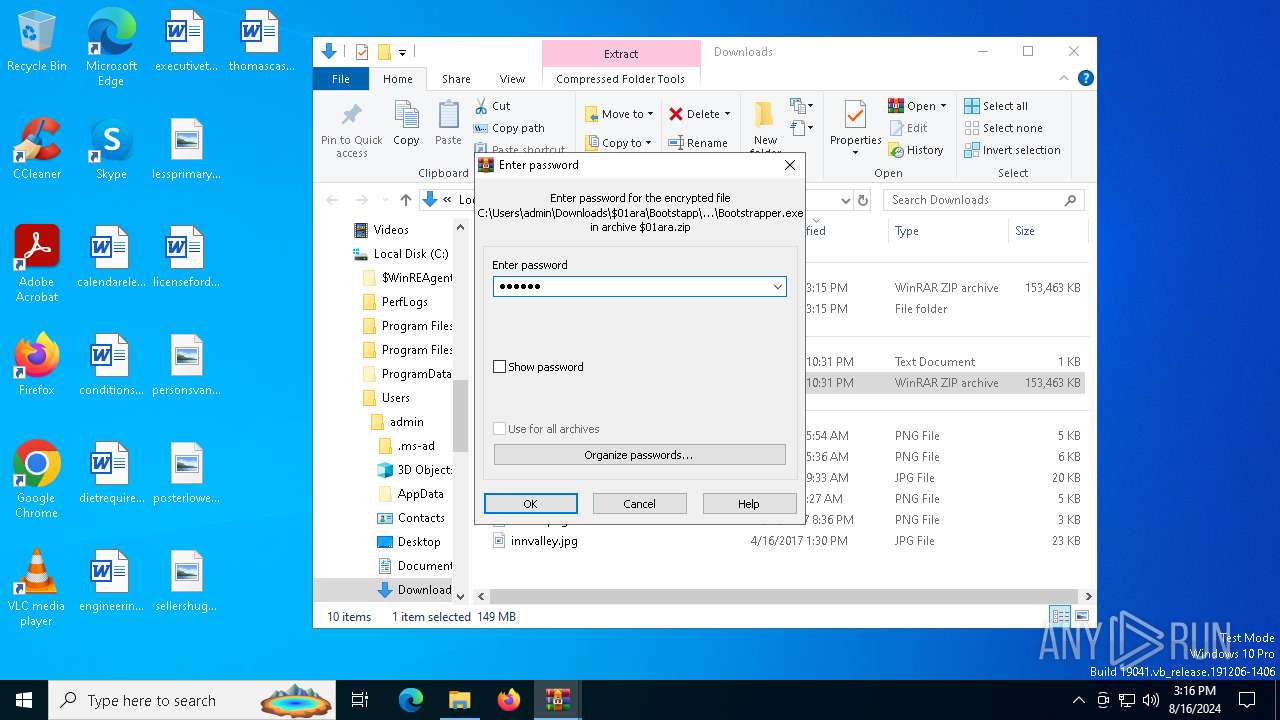
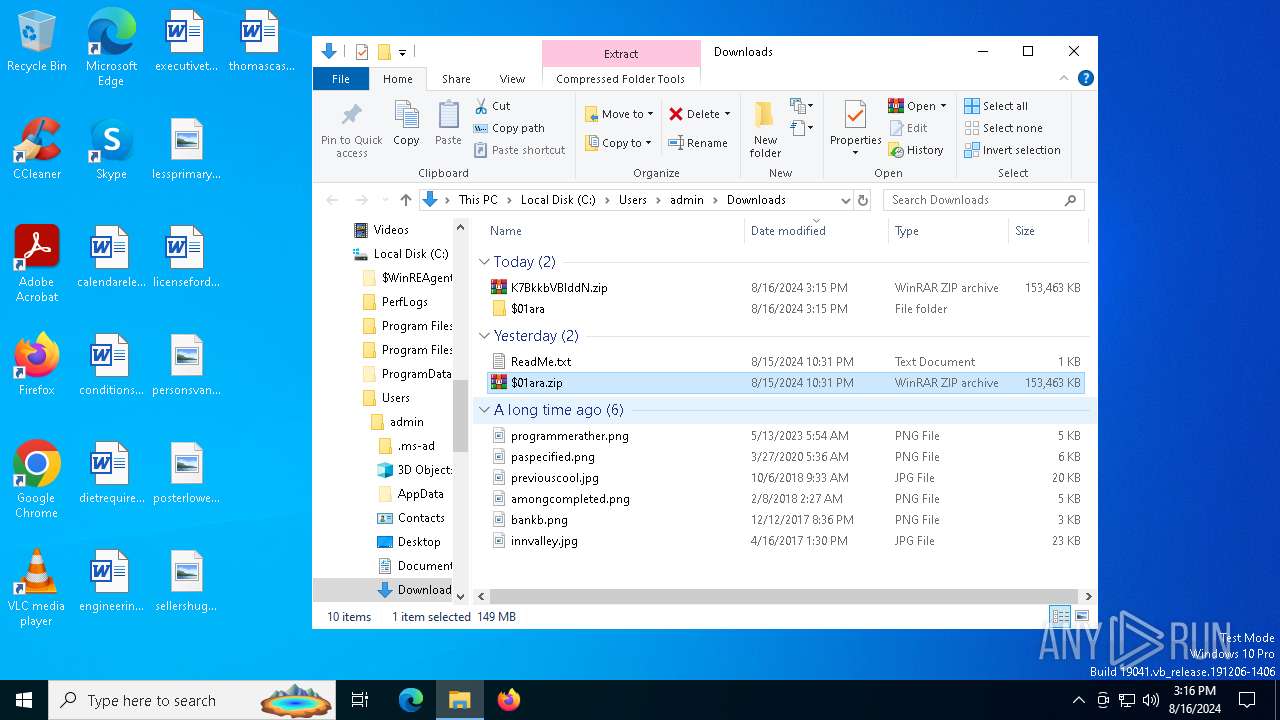
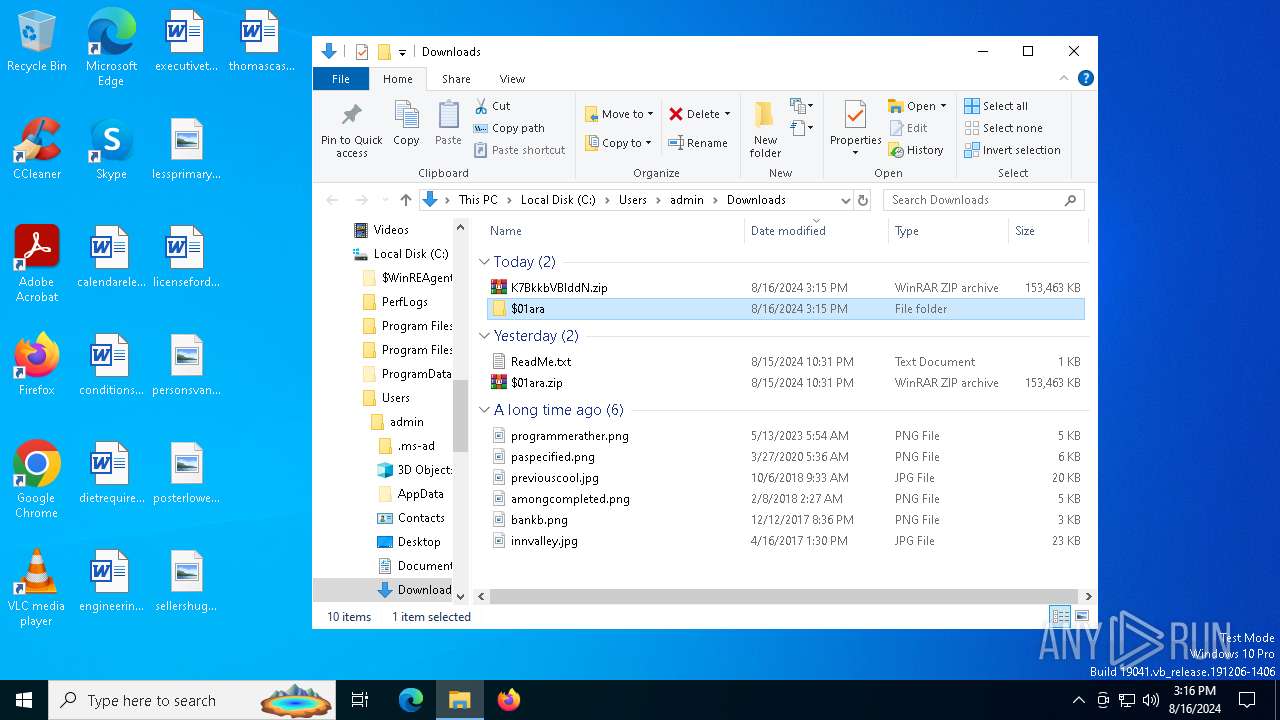
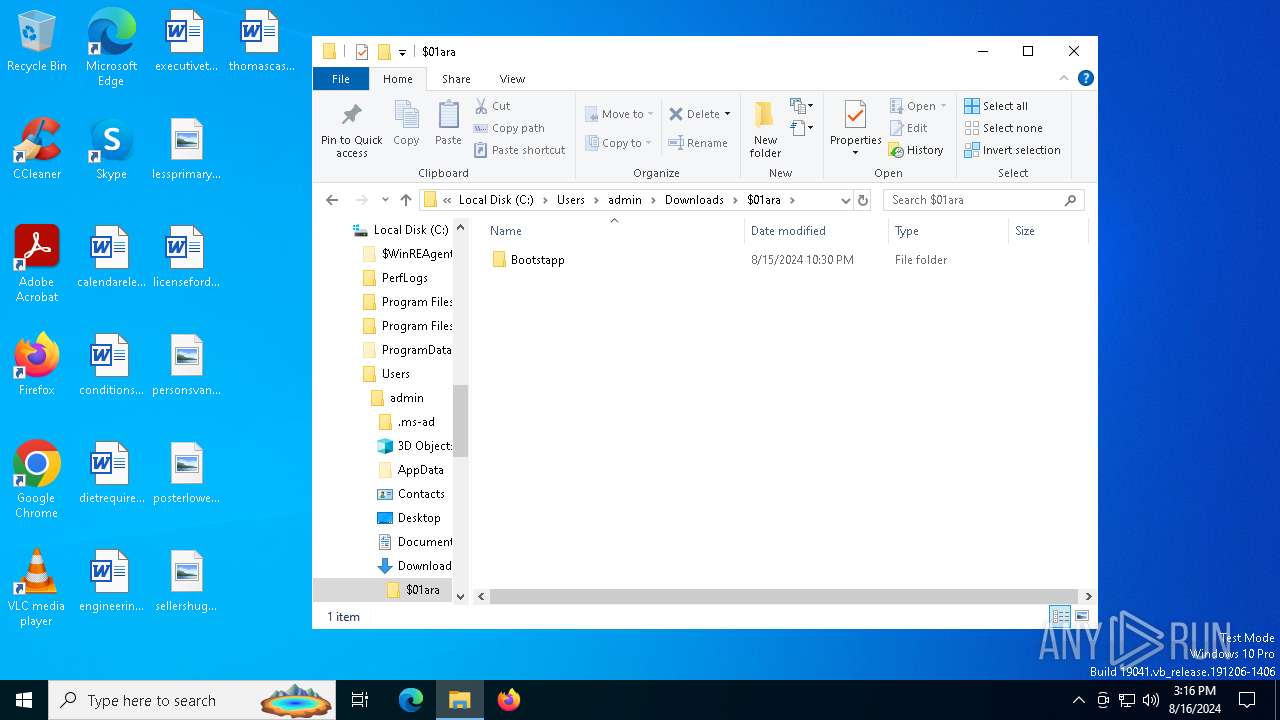
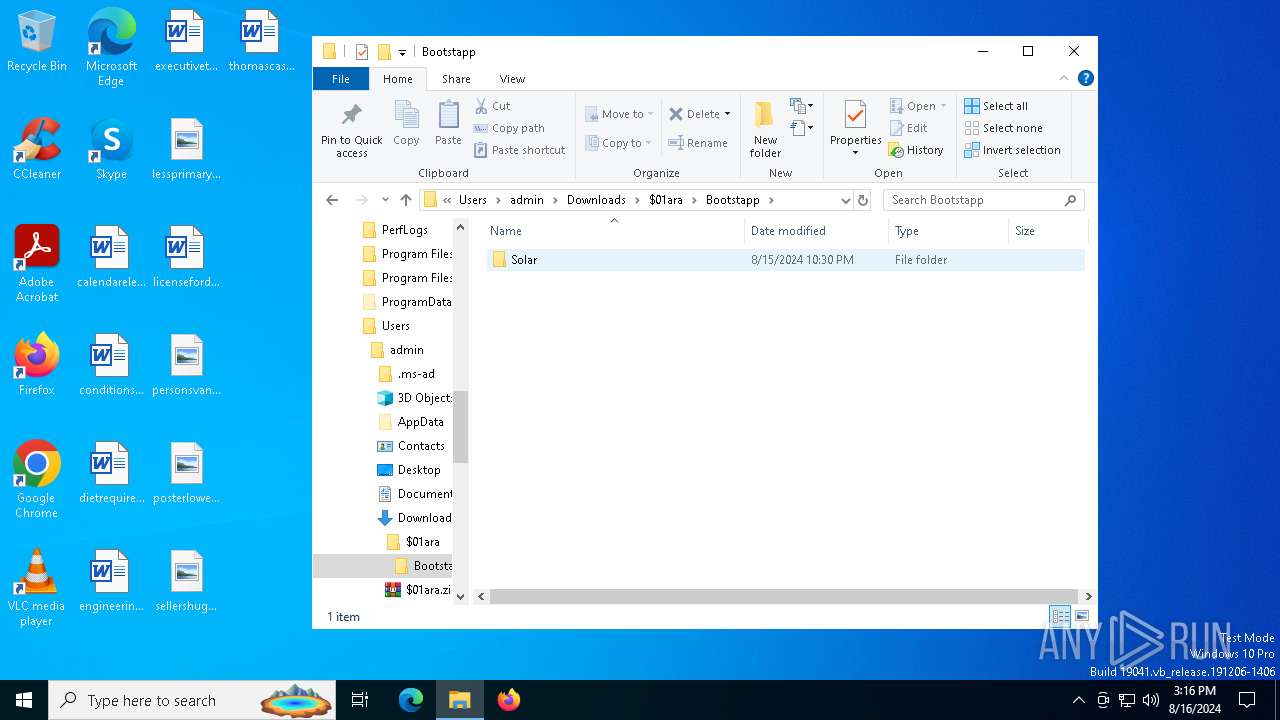
The process uses the downloaded file
- msedge.exe (PID: 2336)
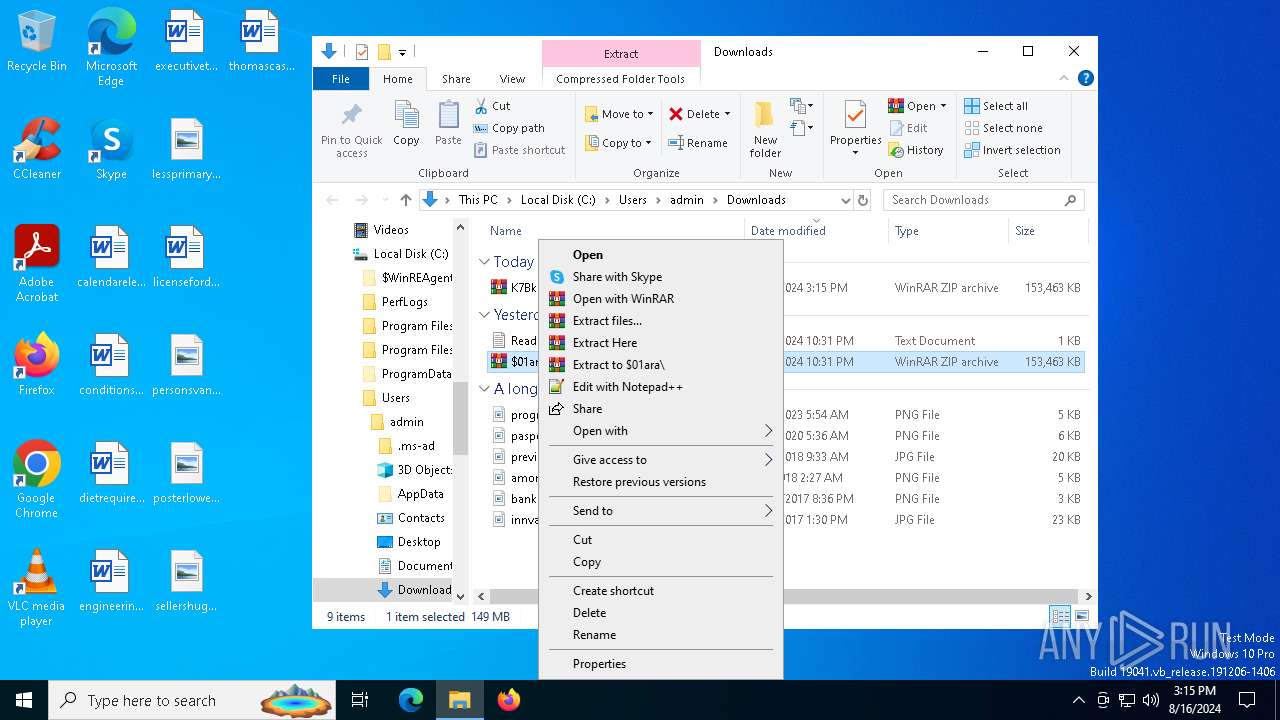
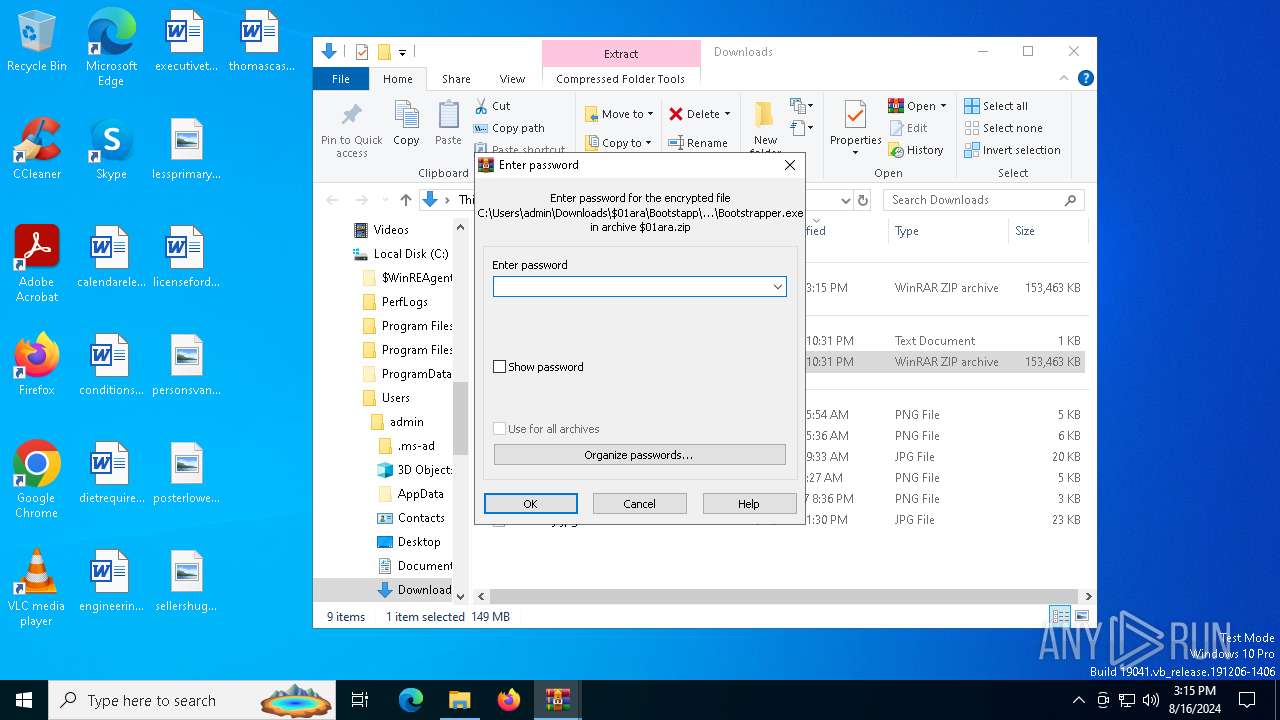
- WinRAR.exe (PID: 7888)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5056)
- notepad.exe (PID: 644)
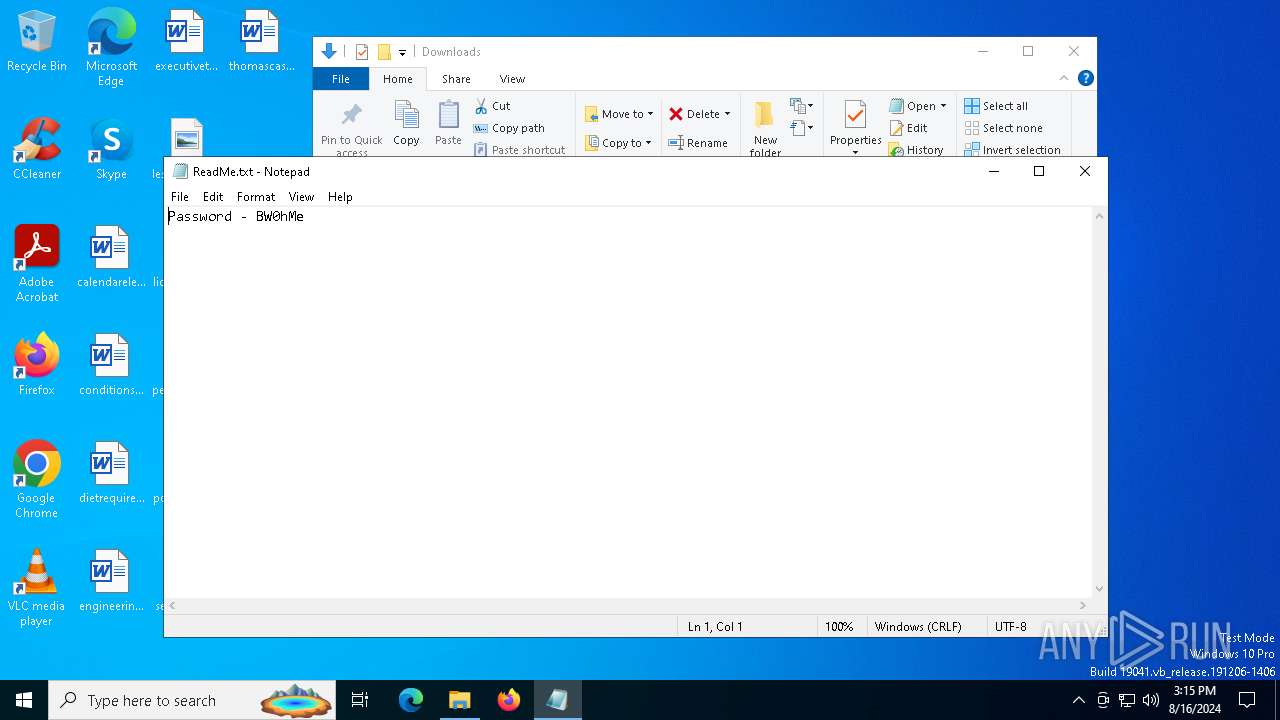
Manual execution by a user
- WinRAR.exe (PID: 7888)
- notepad.exe (PID: 5056)
- notepad.exe (PID: 644)
- WinRAR.exe (PID: 6496)
- RegAsm.exe (PID: 6676)
- RegAsm.exe (PID: 6572)
- Bootstrapper.exe (PID: 6476)
- RegAsm.exe (PID: 3660)
- Bootstrapper.exe (PID: 7524)
Create files in a temporary directory
- Bootstrapper.exe (PID: 7524)
- Sampling.pif (PID: 7608)
- Bootstrapper.exe (PID: 6476)
- Sampling.pif (PID: 640)
Process checks computer location settings
- Bootstrapper.exe (PID: 7524)
- Bootstrapper.exe (PID: 6476)
Reads mouse settings
- Sampling.pif (PID: 7608)
- Sampling.pif (PID: 640)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 6572)
.NET Reactor protector has been detected
- RegAsm.exe (PID: 6572)
Reads the software policy settings
- RegAsm.exe (PID: 6572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
224
Monitored processes
88
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | Sampling.pif Q | C:\Users\admin\AppData\Local\Temp\26485\Sampling.pif | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 644 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\ReadMe.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1608 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2308 --field-trial-handle=2320,i,7000510489932658285,3796325898587523234,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1664 | findstr /I "wrsa.exe opssvc.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4448 --field-trial-handle=2292,i,14602844663846098034,9521218233802596291,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2796 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3256 --field-trial-handle=2320,i,7000510489932658285,3796325898587523234,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2796 | findstr /I "avastui.exe avgui.exe bdservicehost.exe ekrn.exe nswscsvc.exe sophoshealth.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2804 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5216 --field-trial-handle=2320,i,7000510489932658285,3796325898587523234,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
29 364
Read events
29 209
Write events
151
Delete events
4
Modification events
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
4
Suspicious files
157
Text files
115
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe504e.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe504e.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe504e.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe504e.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe505e.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
86
DNS requests
80
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
300 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
300 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7904 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6208 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/629cd657-4aea-4775-ae11-4d4f0e202193?P1=1724416344&P2=404&P3=2&P4=lufrwO%2bjTOaip14QUsk0LJe5nxhZUBPMcTl8N2Evr%2fVTsnpENHds7oYhtn12ZNF5bCCrd%2fedG4TQfHc16KTuDg%3d%3d | unknown | — | — | whitelisted |
7932 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/629cd657-4aea-4775-ae11-4d4f0e202193?P1=1724416344&P2=404&P3=2&P4=lufrwO%2bjTOaip14QUsk0LJe5nxhZUBPMcTl8N2Evr%2fVTsnpENHds7oYhtn12ZNF5bCCrd%2fedG4TQfHc16KTuDg%3d%3d | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/629cd657-4aea-4775-ae11-4d4f0e202193?P1=1724416344&P2=404&P3=2&P4=lufrwO%2bjTOaip14QUsk0LJe5nxhZUBPMcTl8N2Evr%2fVTsnpENHds7oYhtn12ZNF5bCCrd%2fedG4TQfHc16KTuDg%3d%3d | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/629cd657-4aea-4775-ae11-4d4f0e202193?P1=1724416344&P2=404&P3=2&P4=lufrwO%2bjTOaip14QUsk0LJe5nxhZUBPMcTl8N2Evr%2fVTsnpENHds7oYhtn12ZNF5bCCrd%2fedG4TQfHc16KTuDg%3d%3d | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/629cd657-4aea-4775-ae11-4d4f0e202193?P1=1724416344&P2=404&P3=2&P4=lufrwO%2bjTOaip14QUsk0LJe5nxhZUBPMcTl8N2Evr%2fVTsnpENHds7oYhtn12ZNF5bCCrd%2fedG4TQfHc16KTuDg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3028 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2472 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6572 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6572 | msedge.exe | 188.114.96.3:443 | byfron.cc | — | — | unknown |
6264 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6572 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6572 | msedge.exe | 89.187.188.226:443 | syol.lol | Datacamp Limited | CZ | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
byfron.cc |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
syol.lol |
| unknown |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6572 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6572 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6572 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6572 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6572 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6572 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6572 | RegAsm.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
6572 | RegAsm.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] MetaStealer v.5 (MC-NMF TLS Server Certificate) |
6572 | RegAsm.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] MetaStealer v.5 TLS Certificate |
6572 | RegAsm.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] MetaStealer v.5 TLS Connection |