| File name: | 44.bin |
| Full analysis: | https://app.any.run/tasks/3db632bb-86ab-4914-8228-6ca7ec028ea3 |
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | March 31, 2020, 12:16:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D701F8D41BA8085F9513EFB7D2DE139C |
| SHA1: | 1E10128D4B3AC48858999F70499AF8E38AACB7B7 |
| SHA256: | 0962C9378E8488C4C959808B63DBF2FCD08C23044CD95352ED2007A4CC43A5E9 |
| SSDEEP: | 6144:I/JeE4Pgrjea7bifBRPOVDGwCoa7T7SrnB:I/QYr6KGBRP2GwCZ74 |
MALICIOUS
QBOT was detected
- 44.bin.exe (PID: 3680)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3832)
Changes the autorun value in the registry
- explorer.exe (PID: 1900)
SUSPICIOUS
Creates files in the user directory
- 44.bin.exe (PID: 3680)
Application launched itself
- 44.bin.exe (PID: 3680)
- ytfovlym.exe (PID: 2552)
Executable content was dropped or overwritten
- 44.bin.exe (PID: 3680)
- cmd.exe (PID: 3832)
Starts itself from another location
- 44.bin.exe (PID: 3680)
Starts CMD.EXE for commands execution
- 44.bin.exe (PID: 3680)
INFO
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 3832)
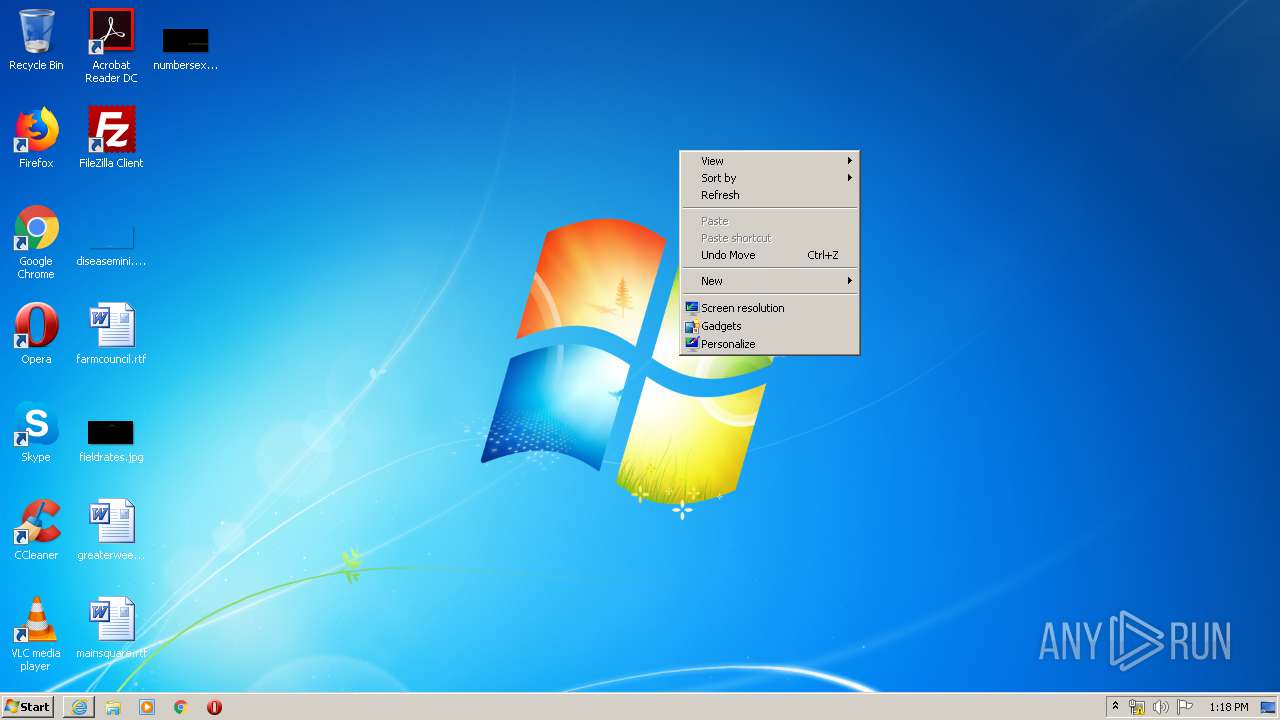
Manual execution by user
- iexplore.exe (PID: 2012)
- explorer.exe (PID: 1832)
Reads Internet Cache Settings
- iexplore.exe (PID: 2012)
- iexplore.exe (PID: 3244)
Application launched itself
- iexplore.exe (PID: 2012)
Changes internet zones settings
- iexplore.exe (PID: 2012)
Reads internet explorer settings
- iexplore.exe (PID: 3244)
Creates files in the user directory
- iexplore.exe (PID: 2012)
Reads settings of System Certificates
- iexplore.exe (PID: 2012)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2012)
Changes settings of System certificates
- iexplore.exe (PID: 2012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
| .vxd | | | VXD Driver (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:30 19:03:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1918464 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b80 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Mar-2020 17:03:01 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 30-Mar-2020 17:03:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001D44B2 | 0x001D4600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 1.49502 |
.data | 0x001D6000 | 0x00000698 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.24613 |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
44
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1832 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | ytfovlym.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2012 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2132 | ping.exe -n 6 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2552 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | 44.bin.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3176 | C:\Users\admin\AppData\Local\Temp\44.bin.exe /C | C:\Users\admin\AppData\Local\Temp\44.bin.exe | — | 44.bin.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3220 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe /C | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | ytfovlym.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3244 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2012 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3680 | "C:\Users\admin\AppData\Local\Temp\44.bin.exe" | C:\Users\admin\AppData\Local\Temp\44.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3832 | "C:\Windows\System32\cmd.exe" /c ping.exe -n 6 127.0.0.1 & type "C:\Windows\System32\calc.exe" > "C:\Users\admin\AppData\Local\Temp\44.bin.exe" | C:\Windows\System32\cmd.exe | 44.bin.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
8 207
Read events
511
Write events
5 137
Delete events
2 559
Modification events
| (PID) Process: | (3680) 44.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3680) 44.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1934841042 | |||
| (PID) Process: | (2012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803798 | |||
| (PID) Process: | (2012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
12
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_D9817BD5013875AD517DA73475345203 | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2CAC.tmp | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar2CAD.tmp | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver2D89.tmp | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\7A35XN3V.txt | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\R5H90VP4.txt | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCF8478753618D99B.TMP | — | |
MD5:— | SHA256:— | |||
| 3680 | 44.bin.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.dat | binary | |
MD5:— | SHA256:— | |||
| 3680 | 44.bin.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2012 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2012 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2012 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2012 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2012 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dns.msftncsi.com |
| shared |