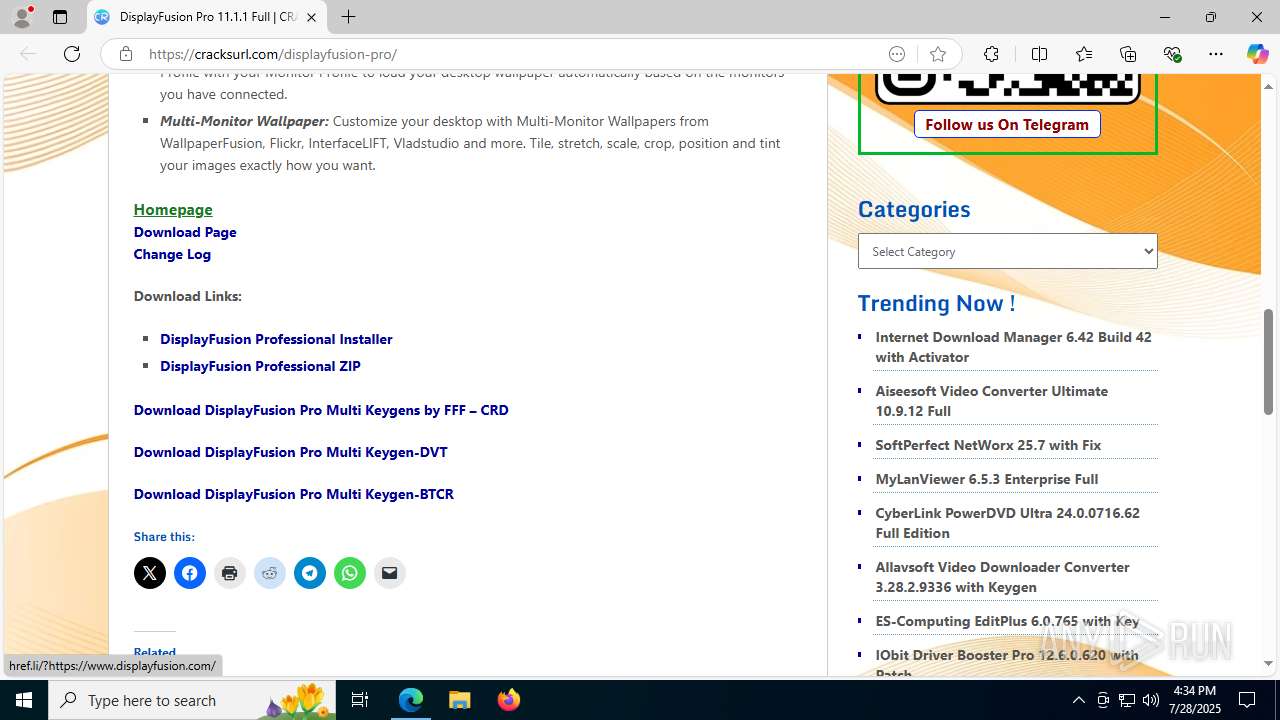
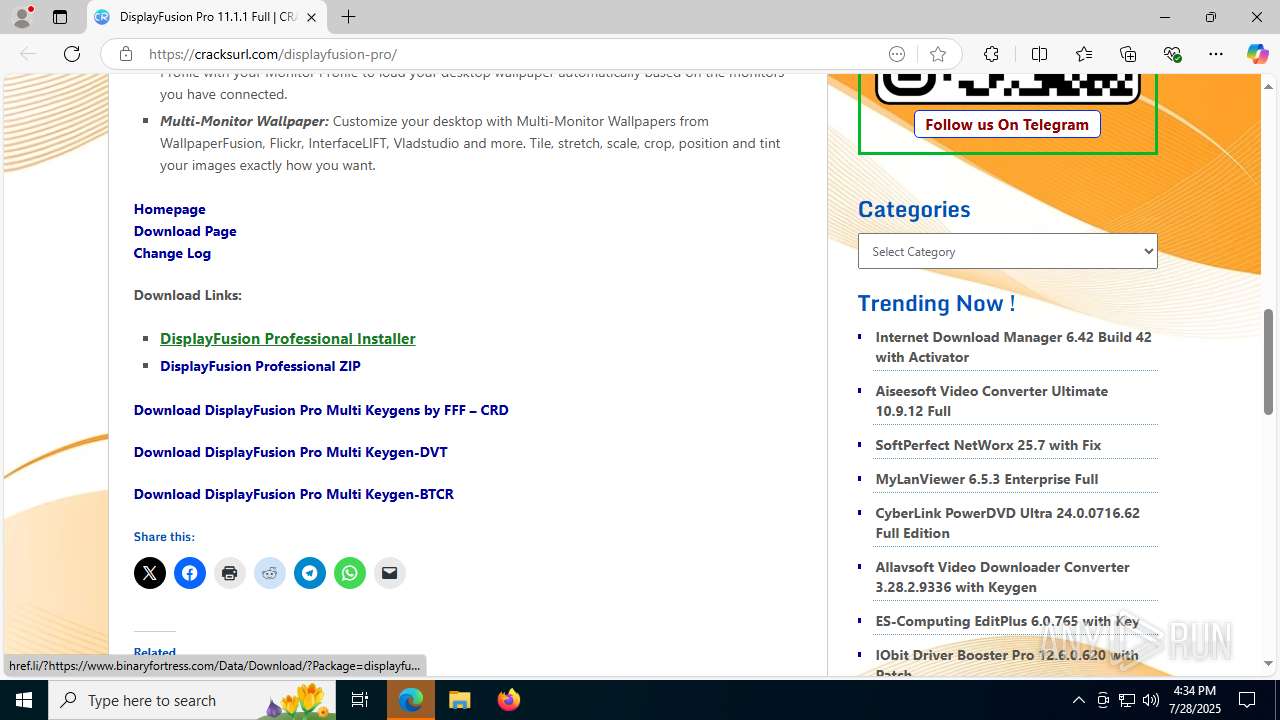
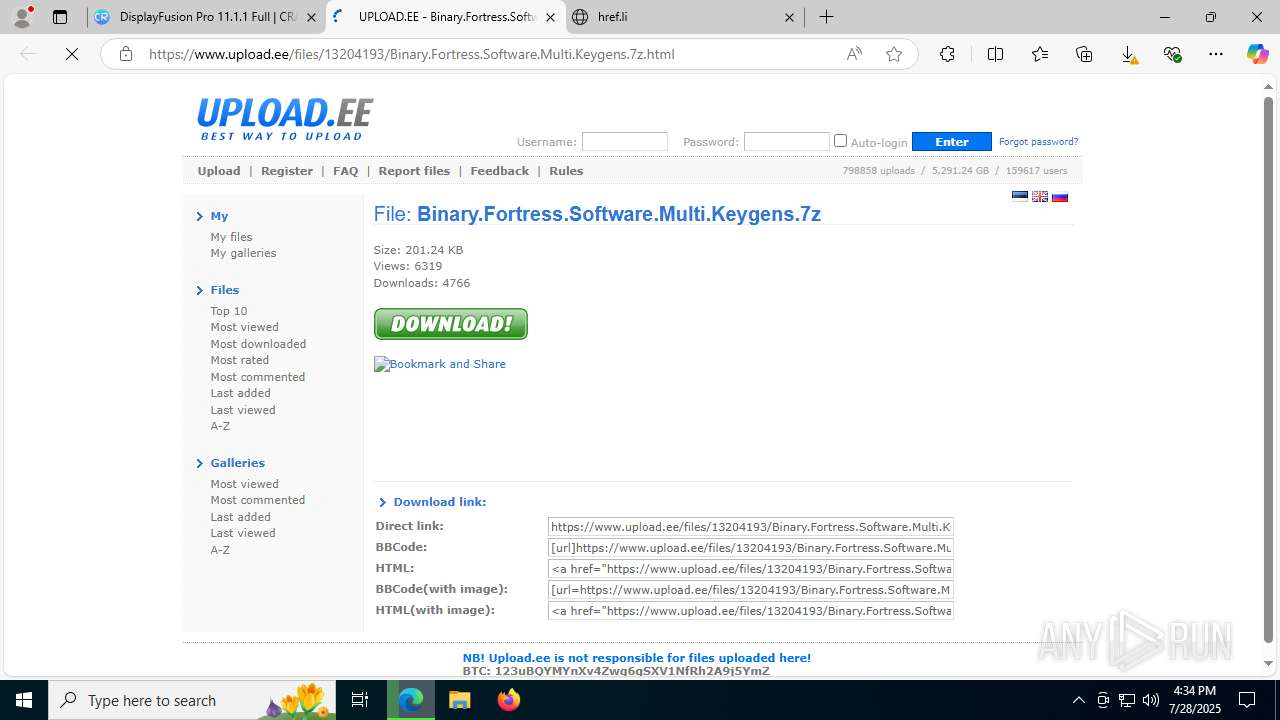
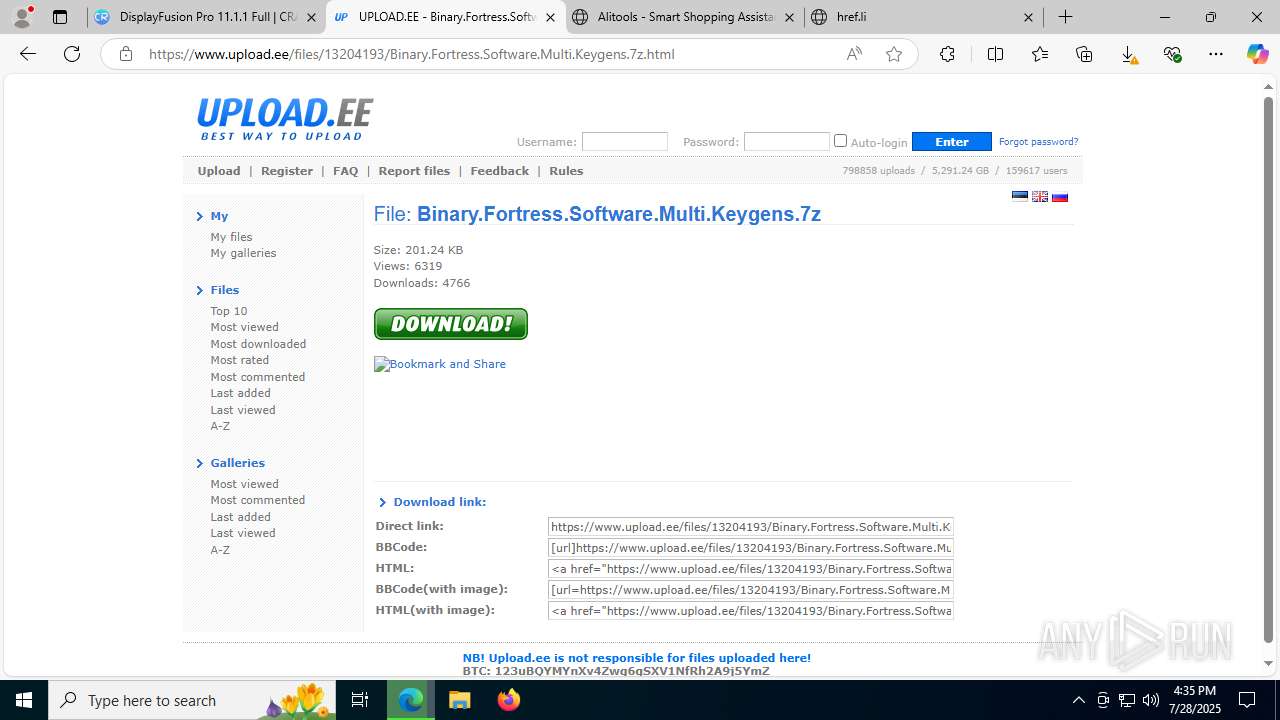
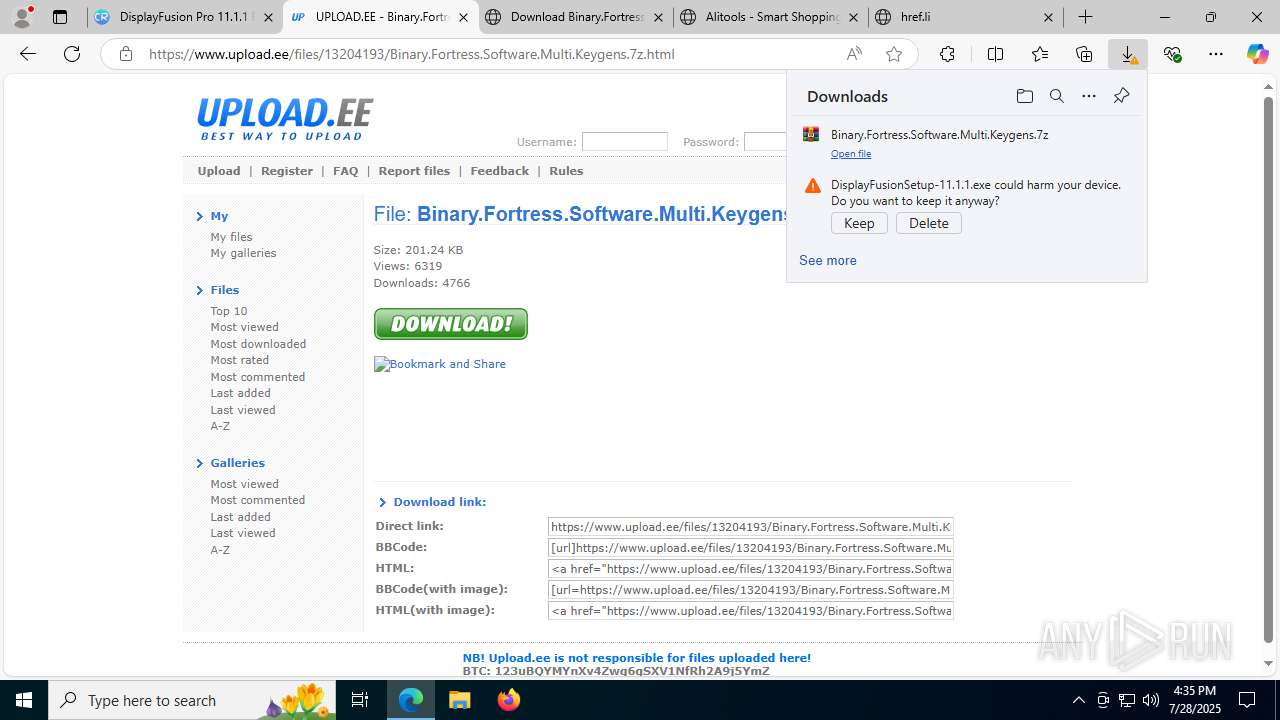
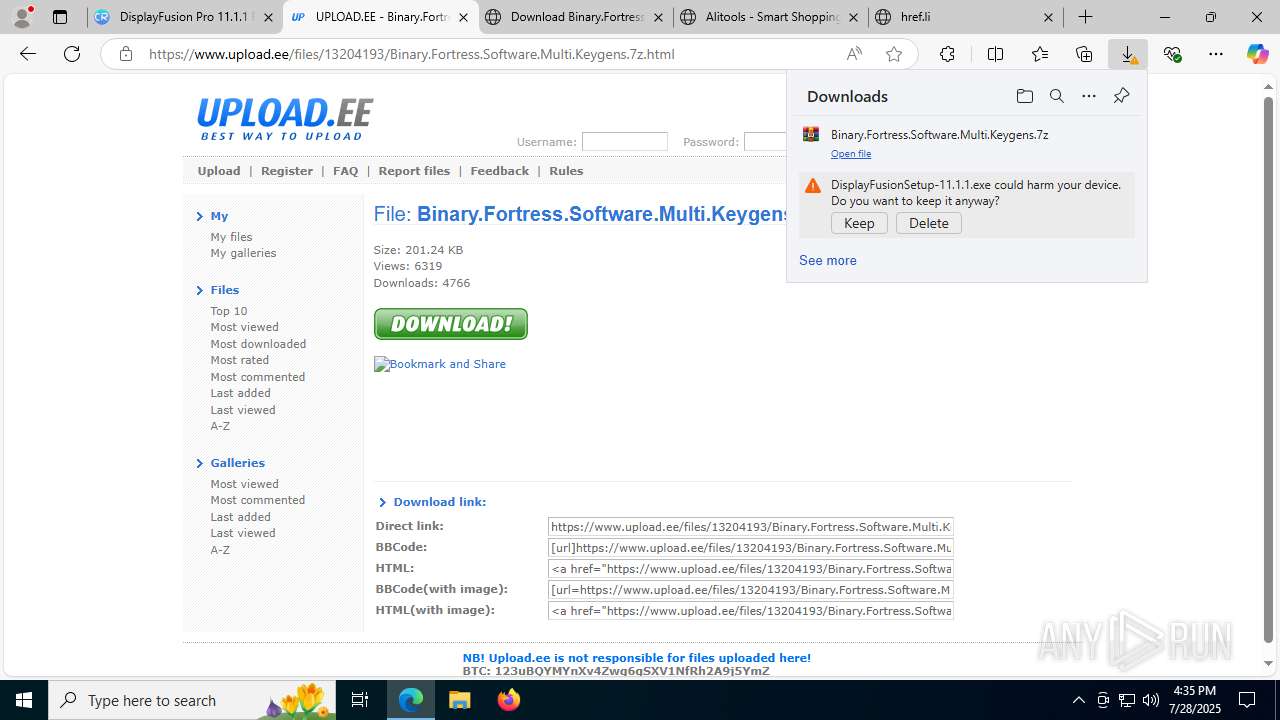
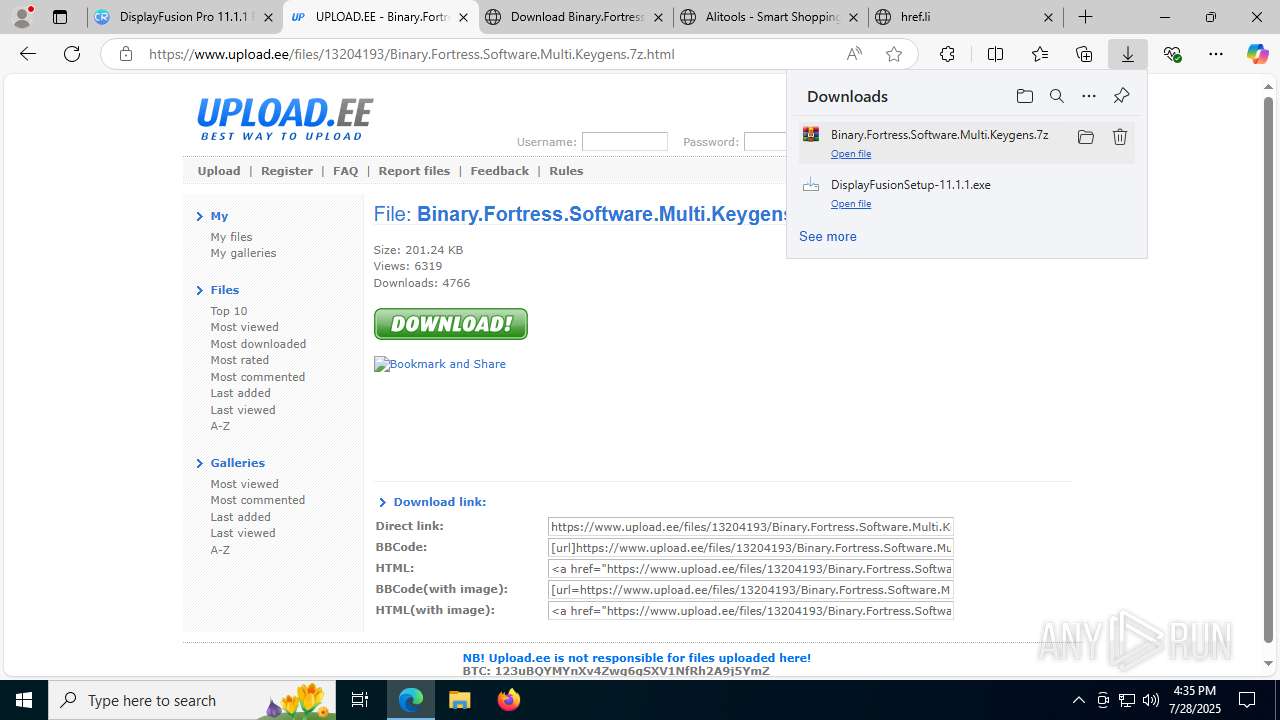
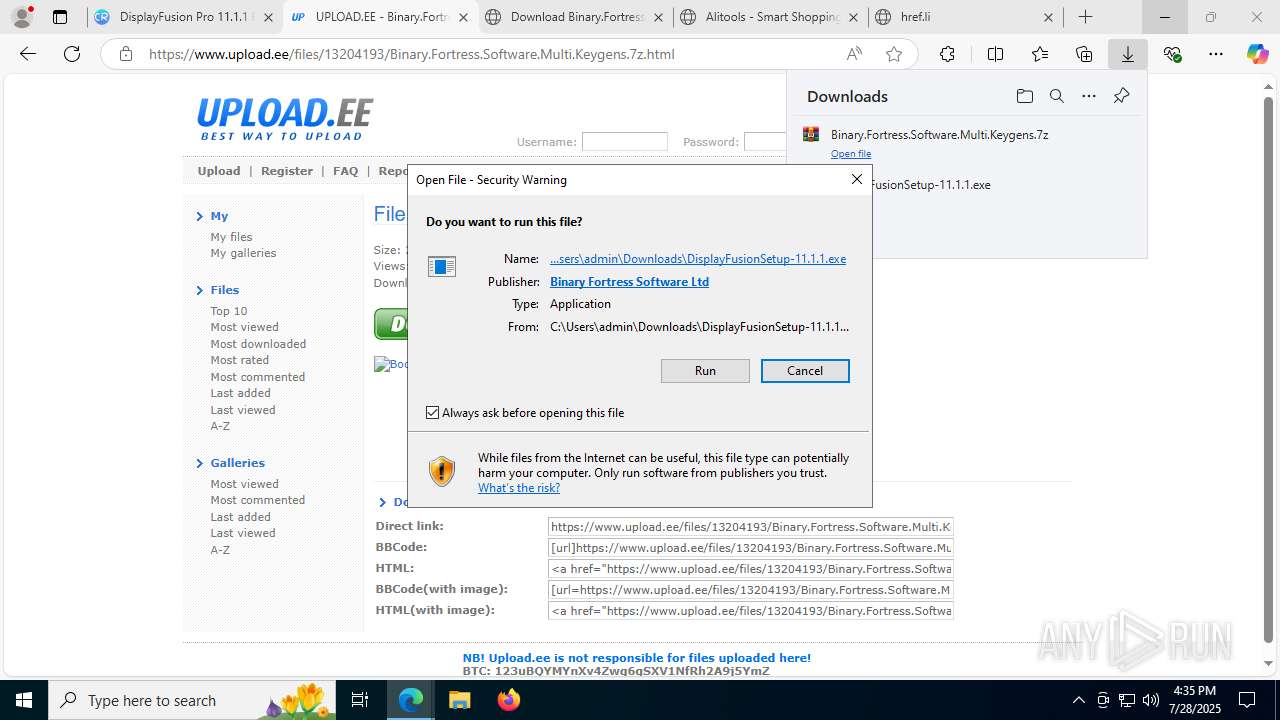
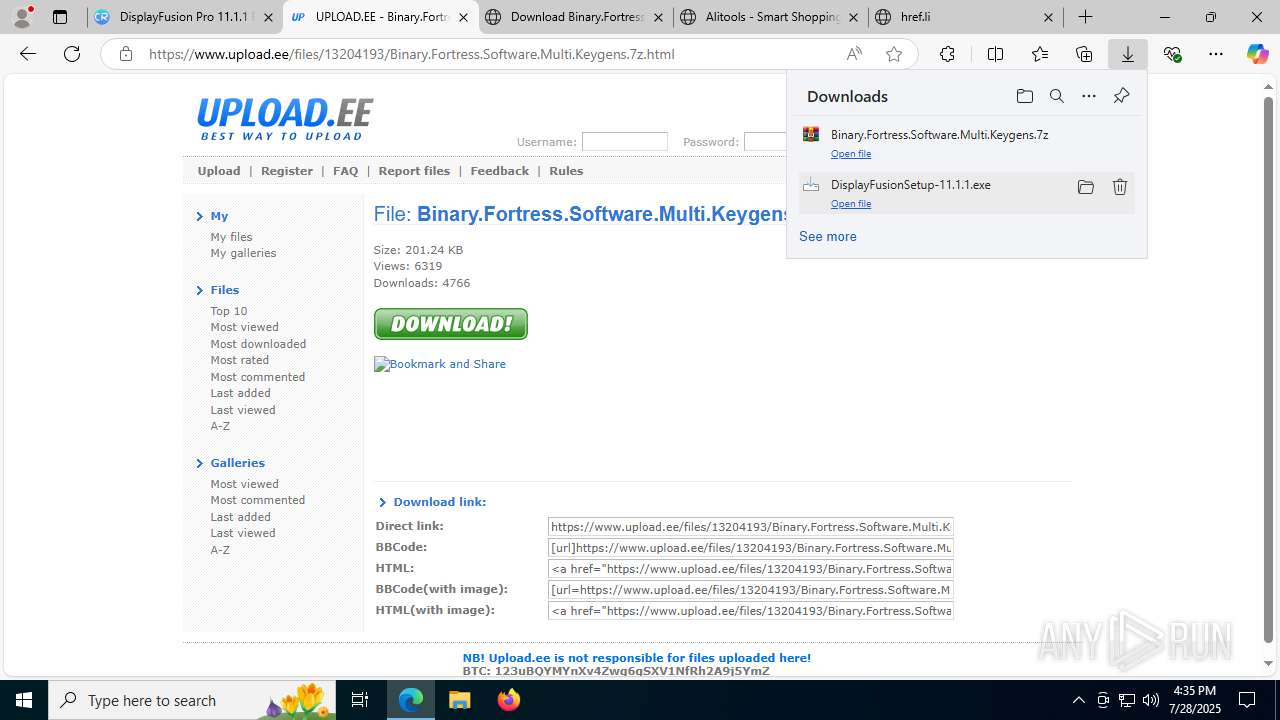
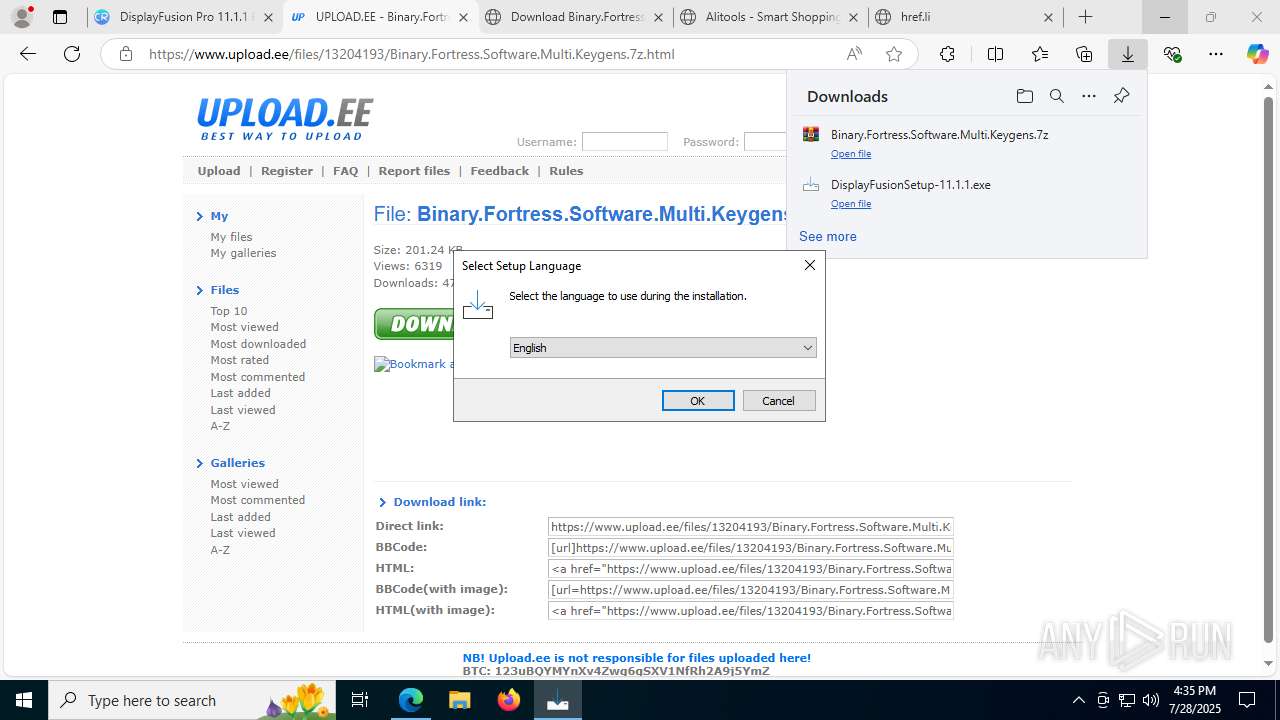
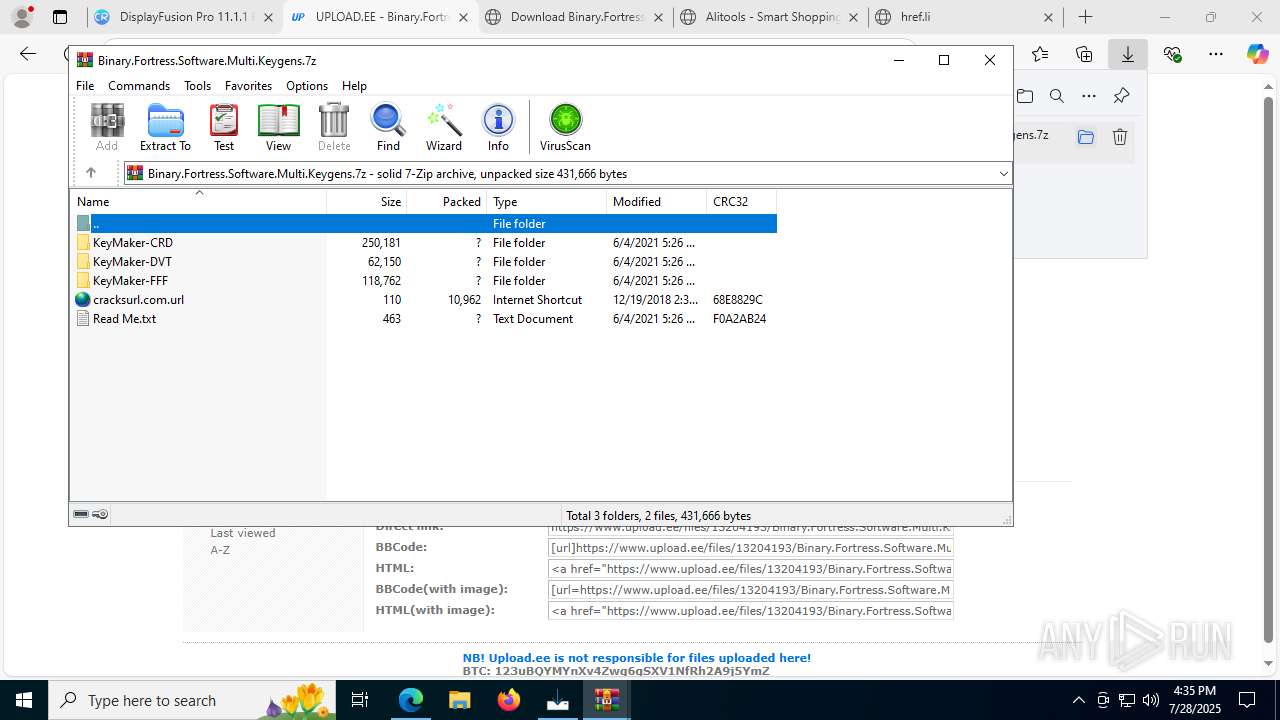
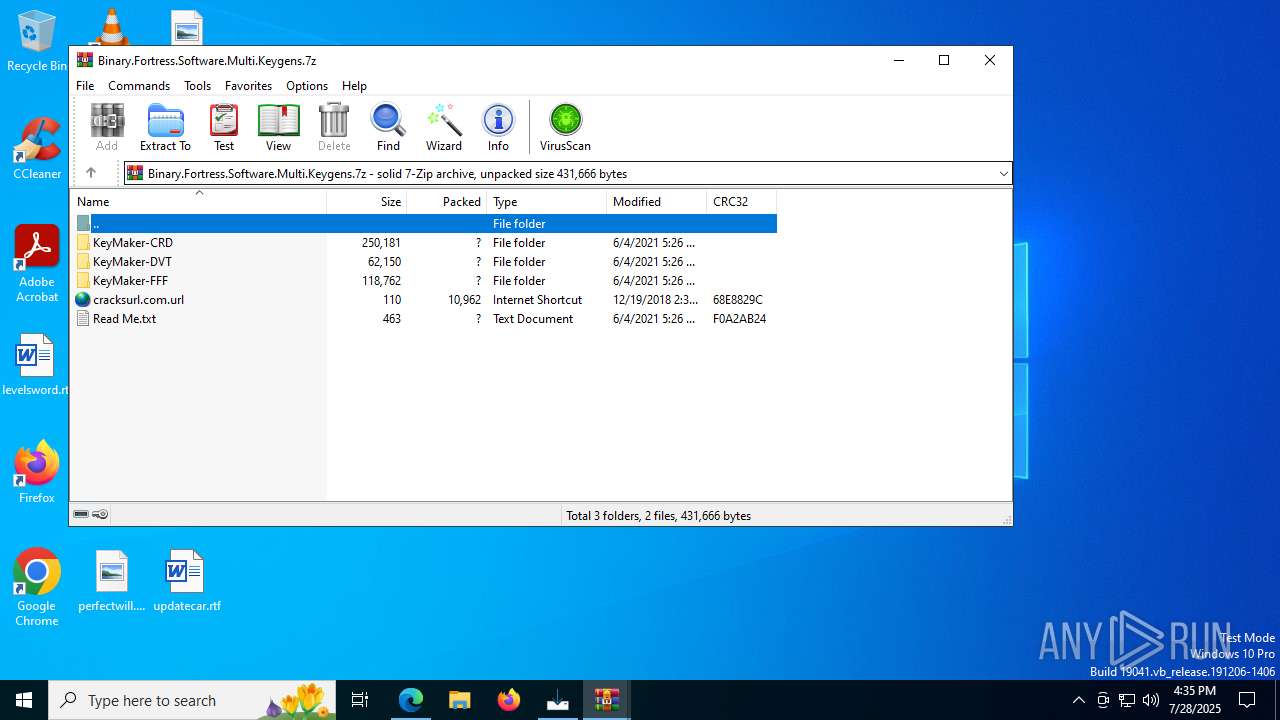
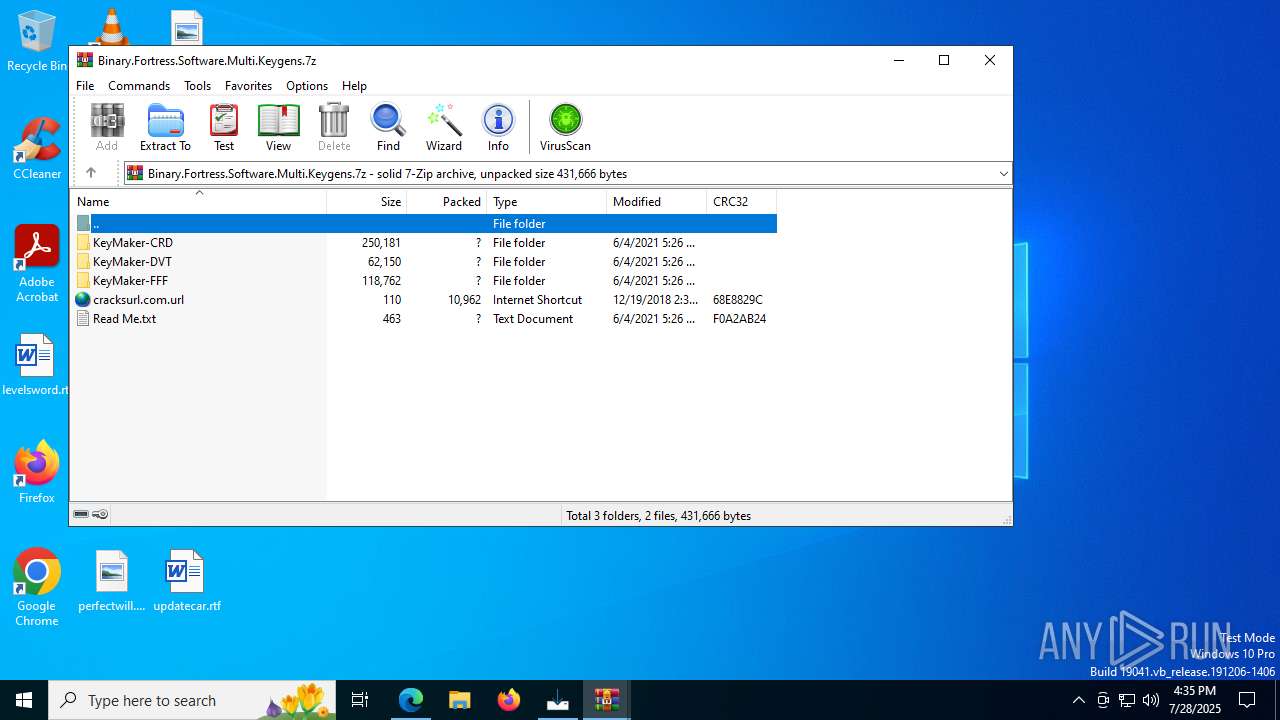
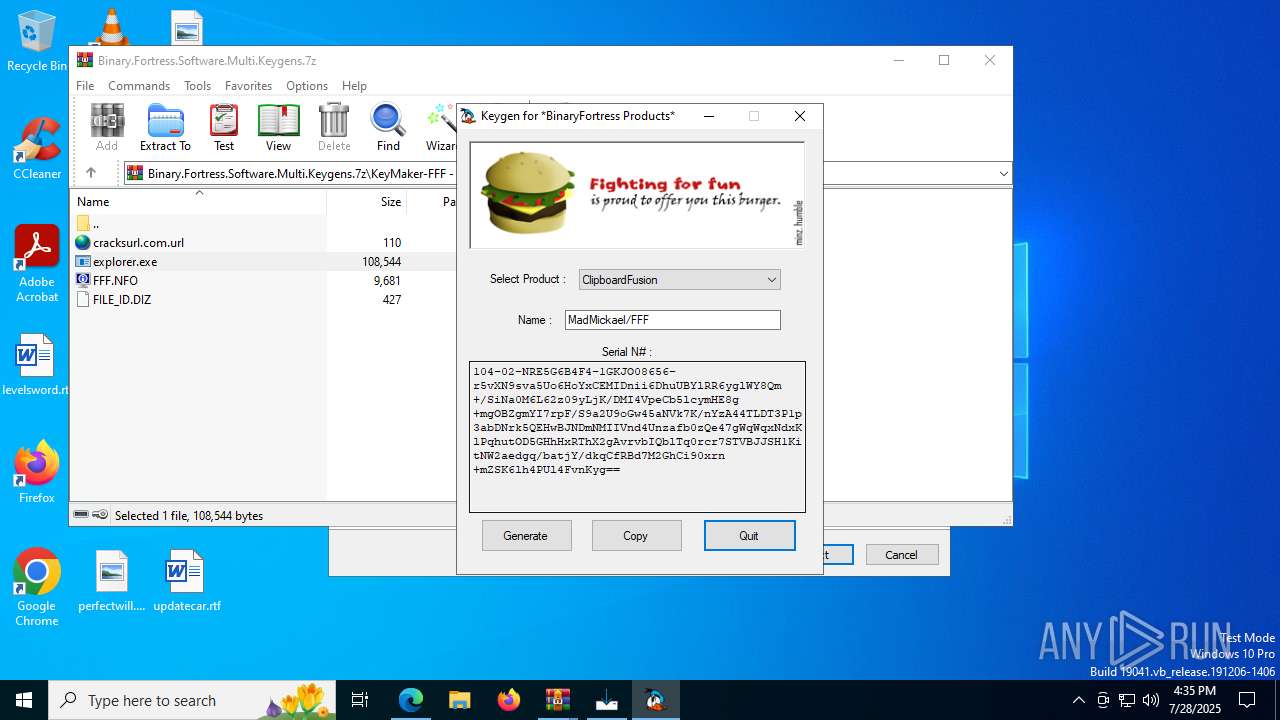
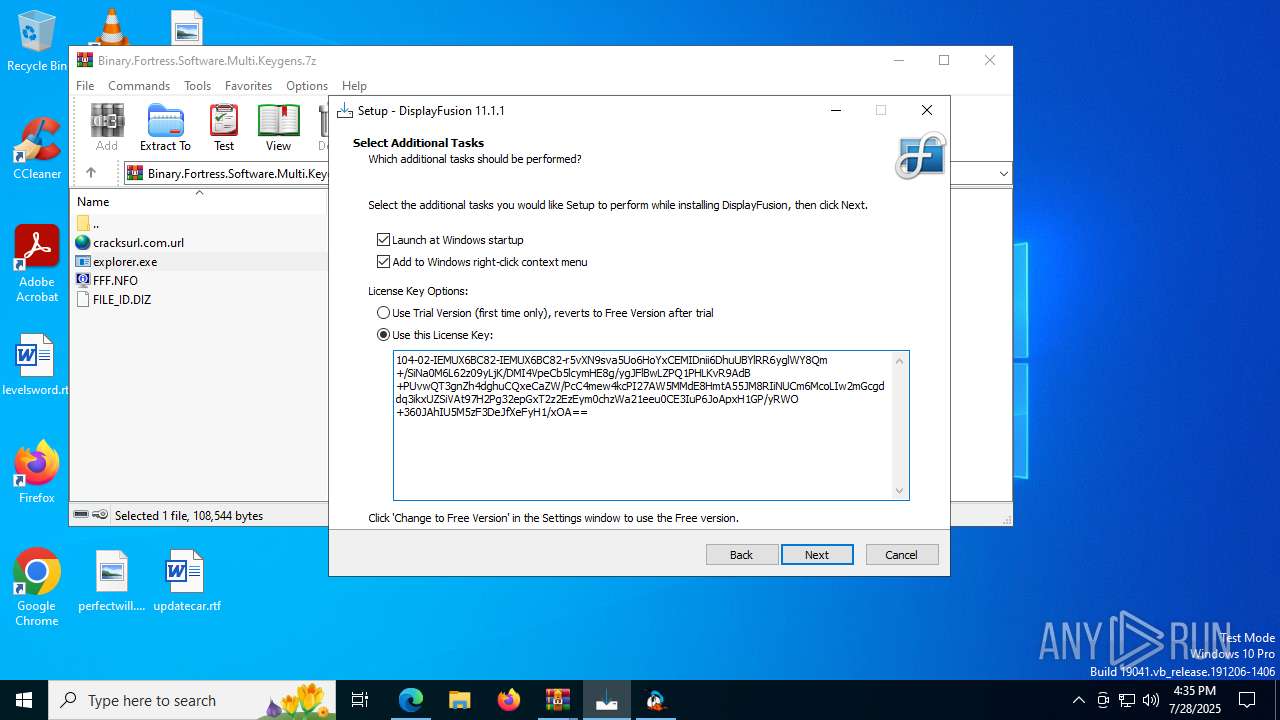
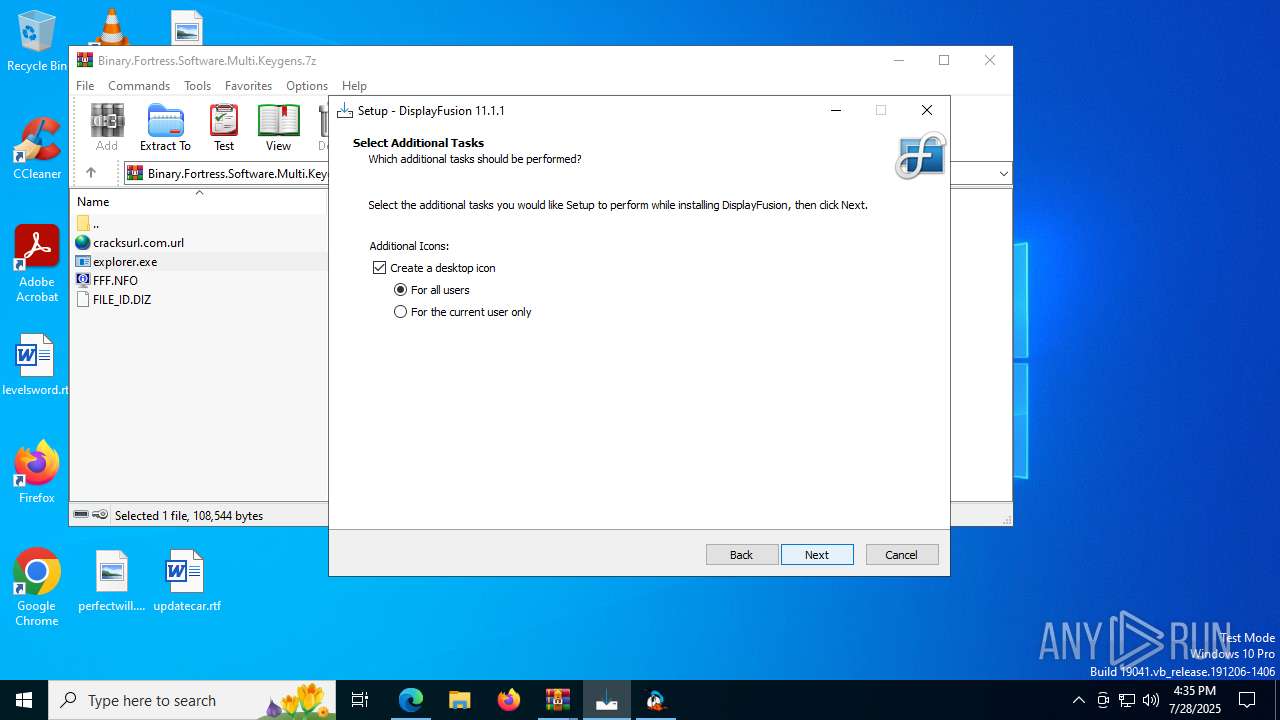
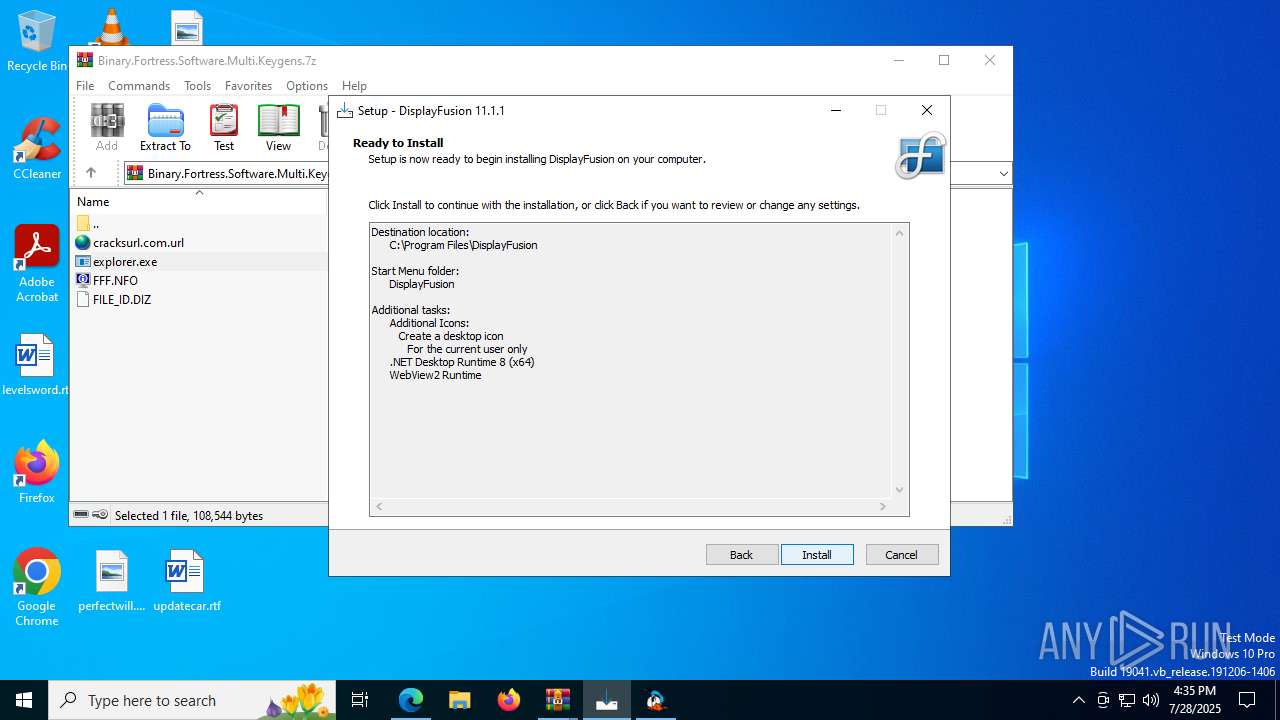
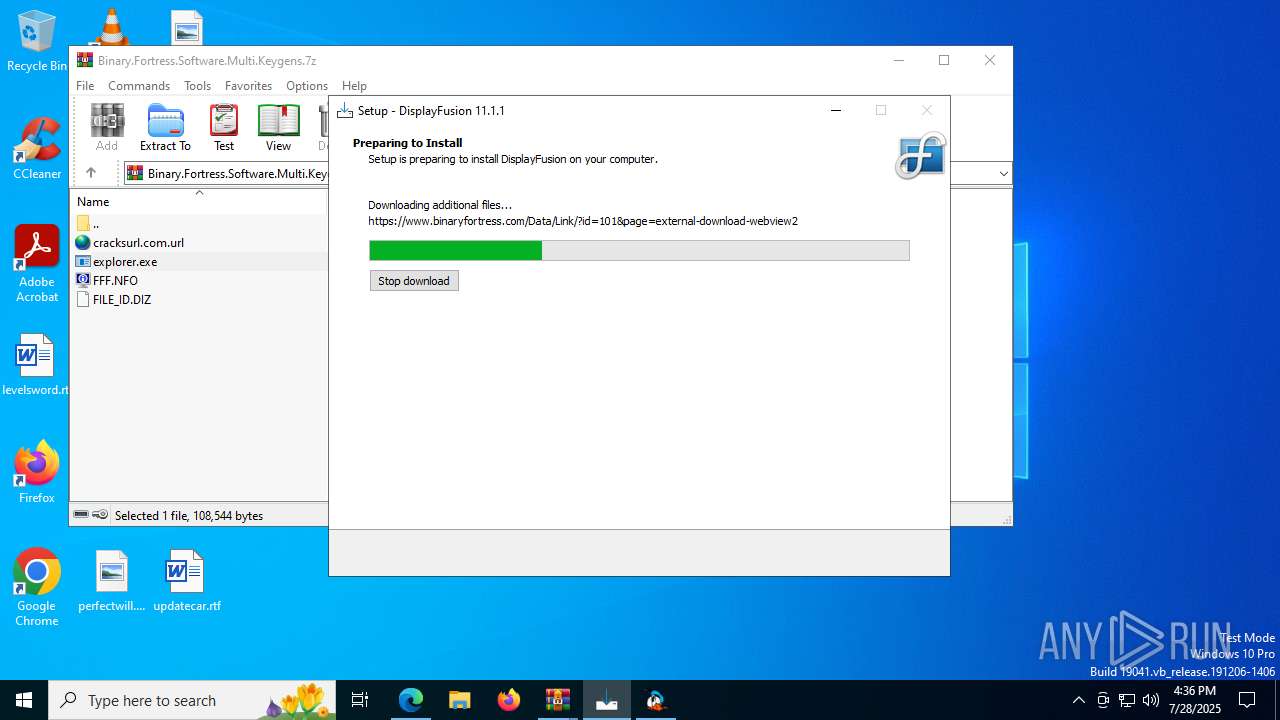
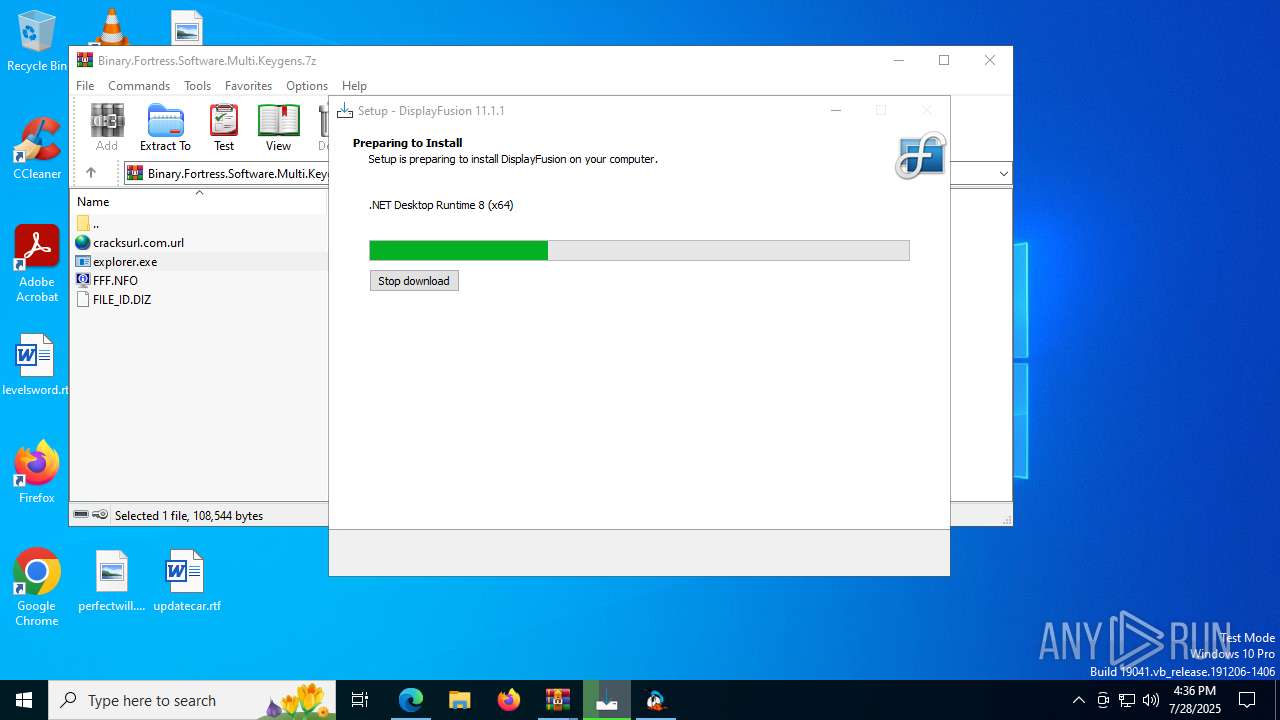
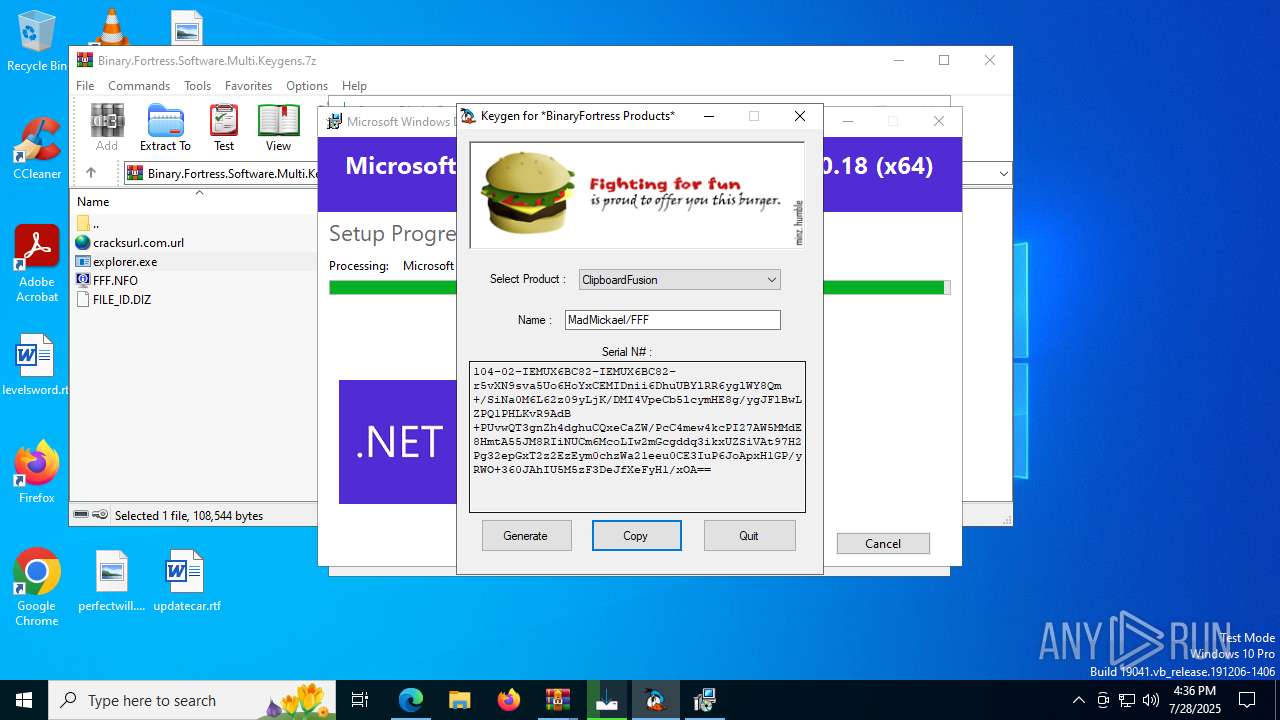
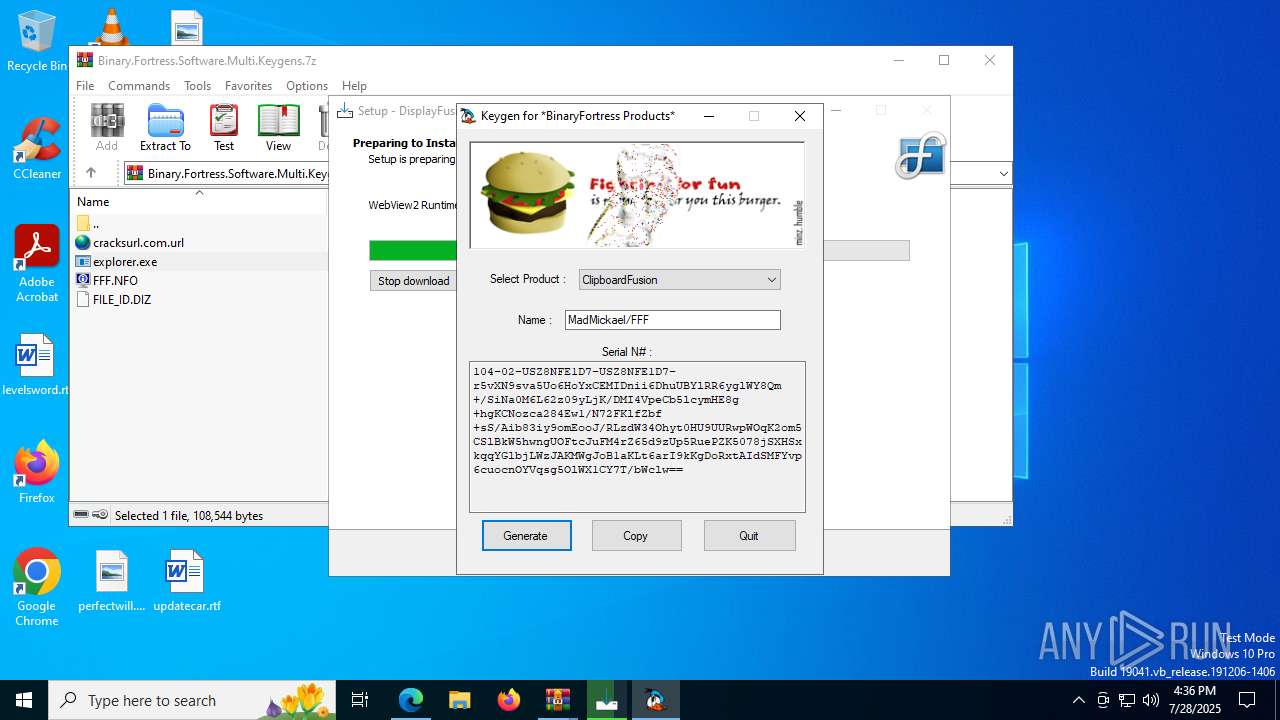
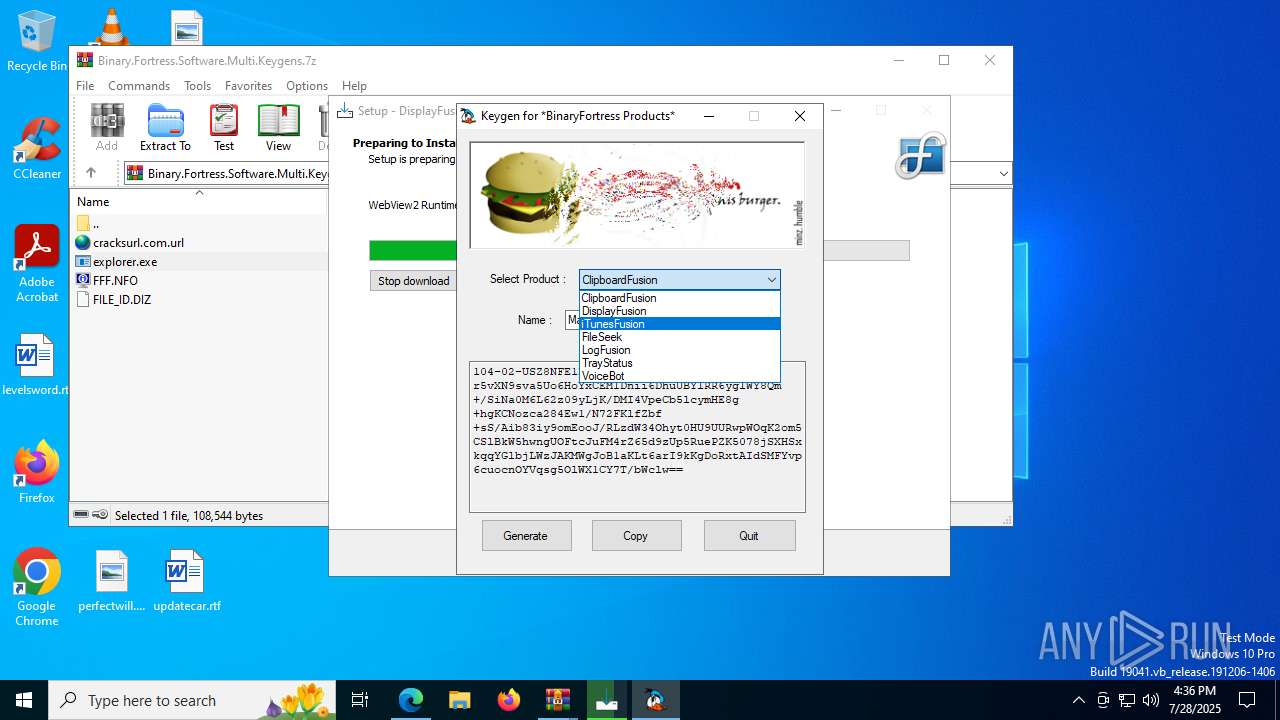
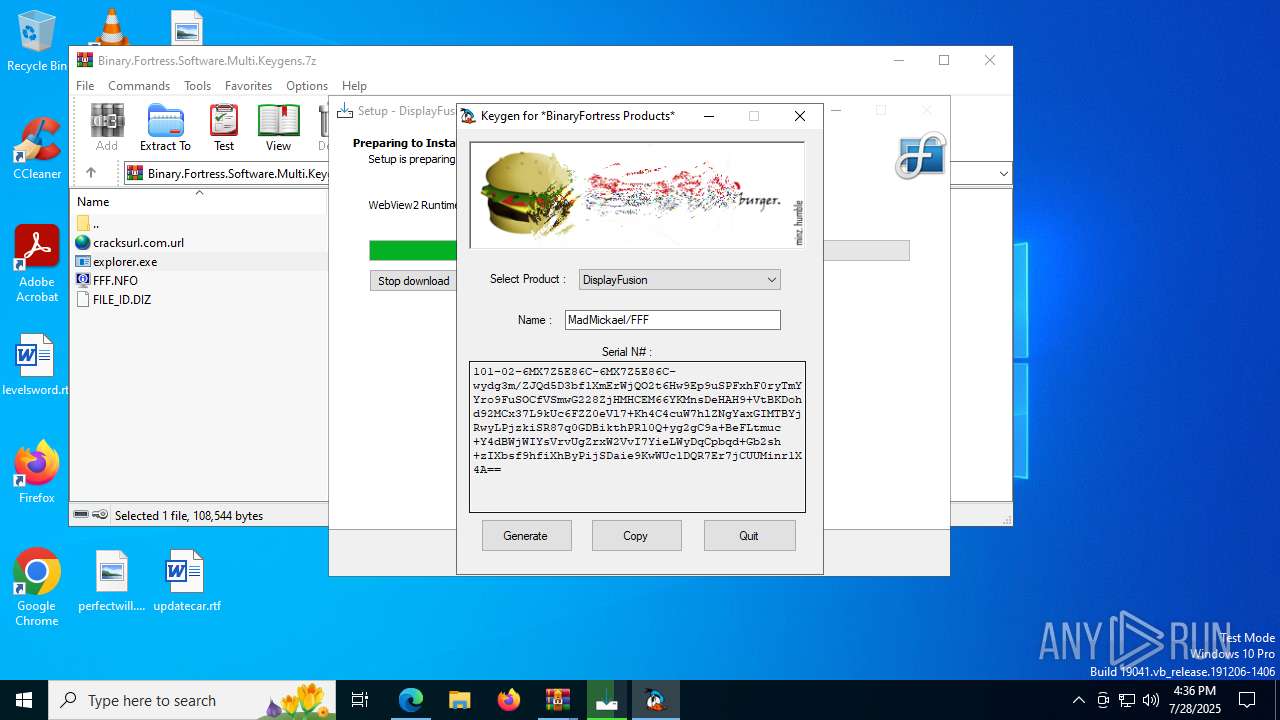
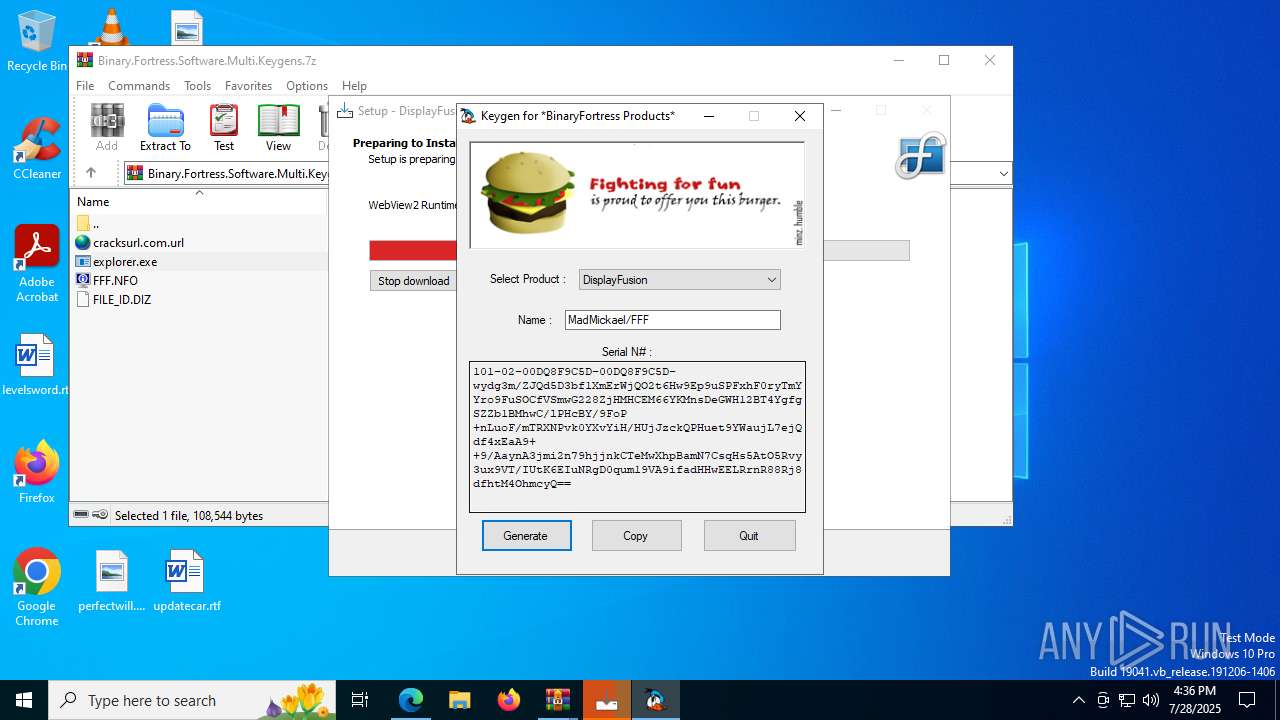
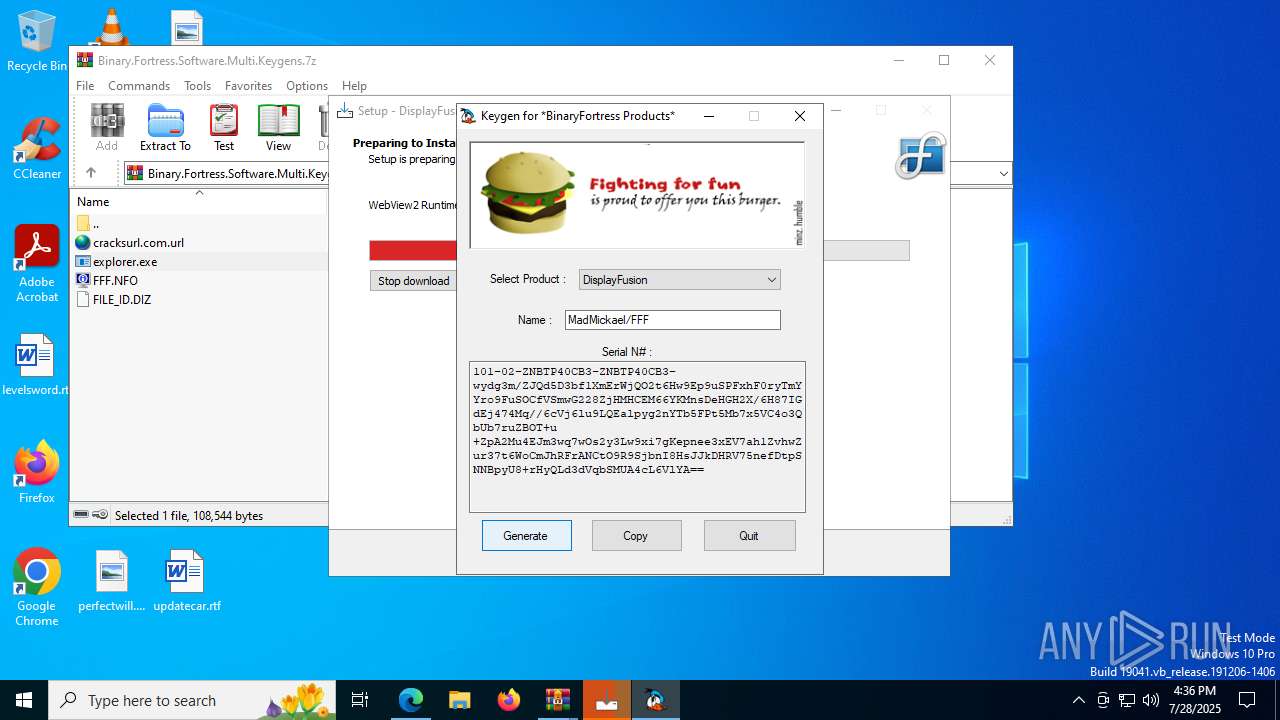
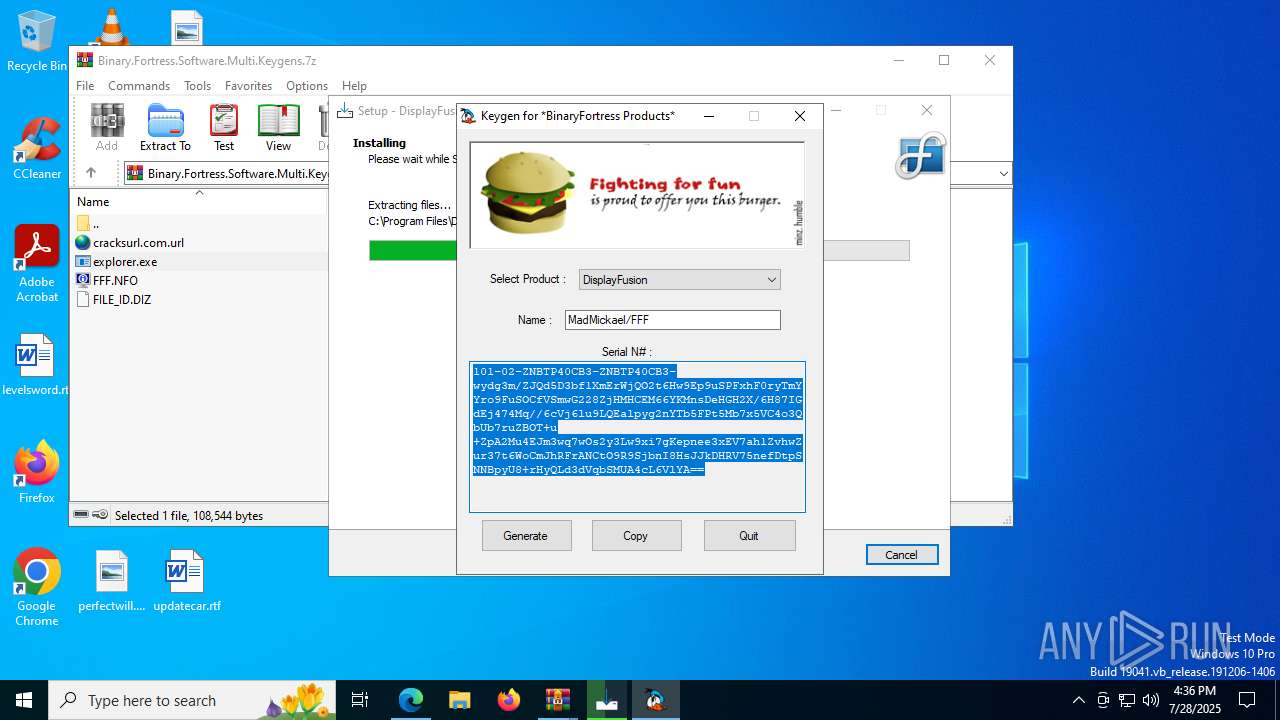
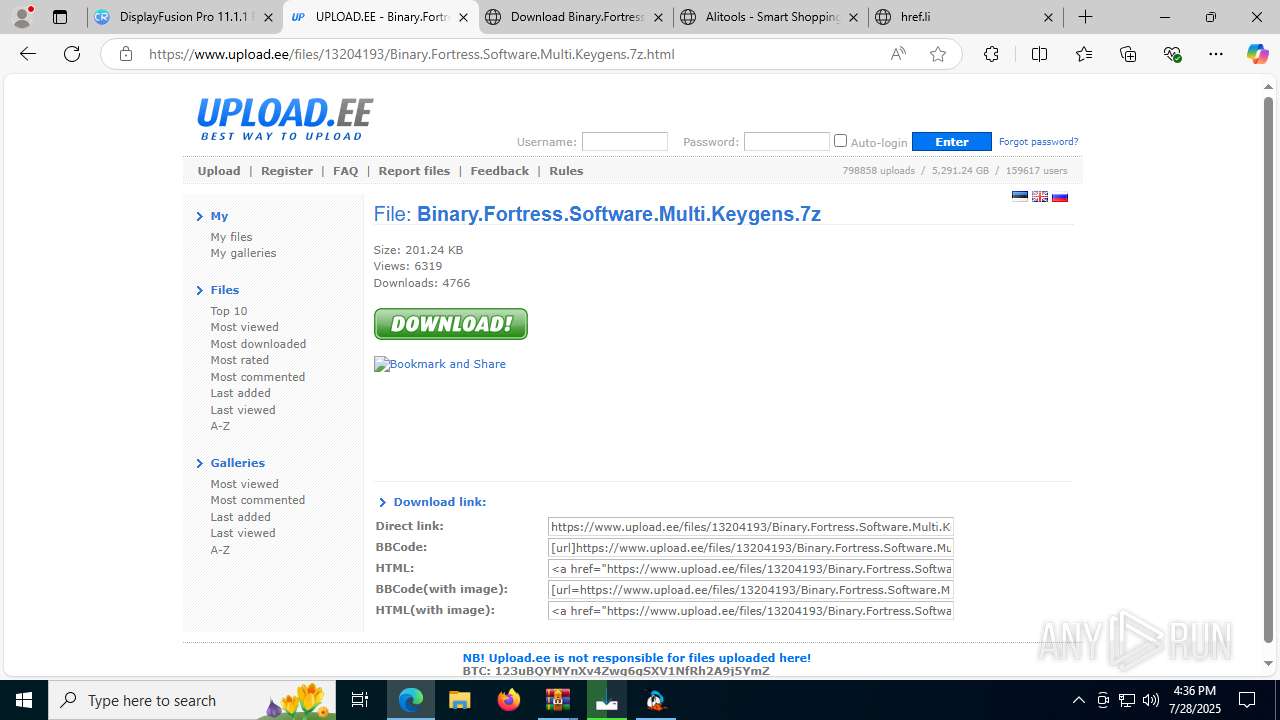
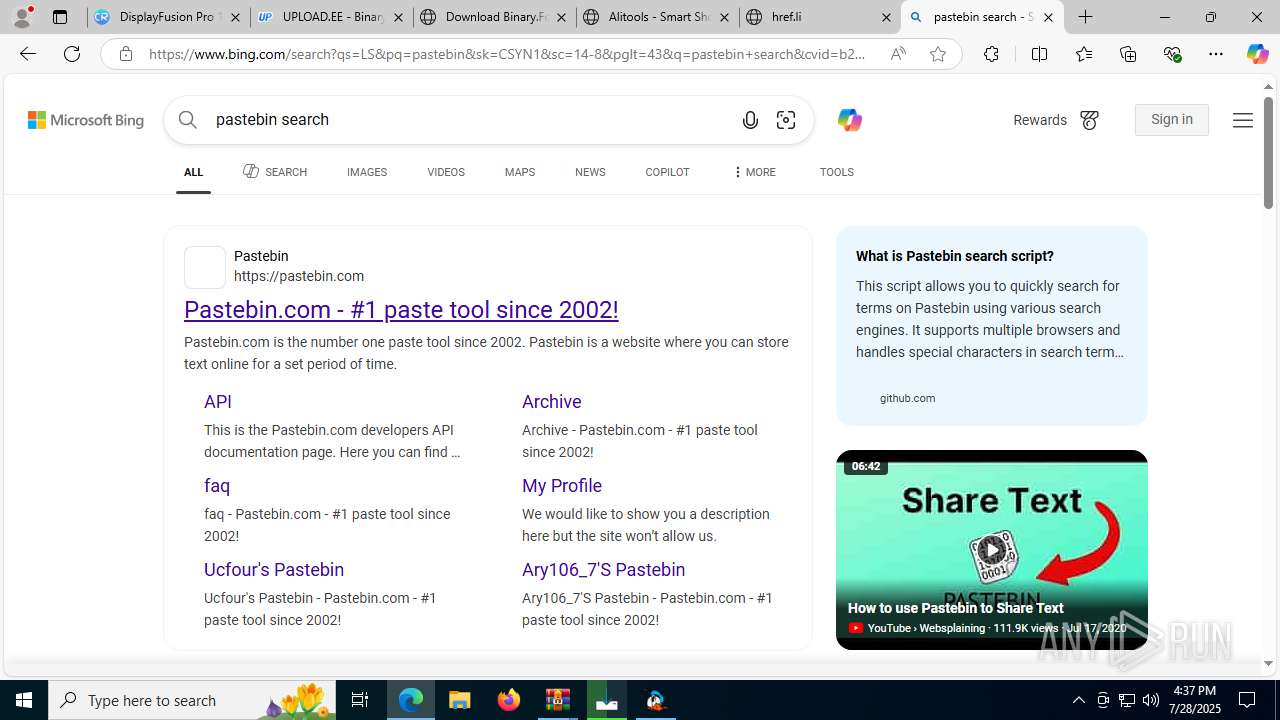
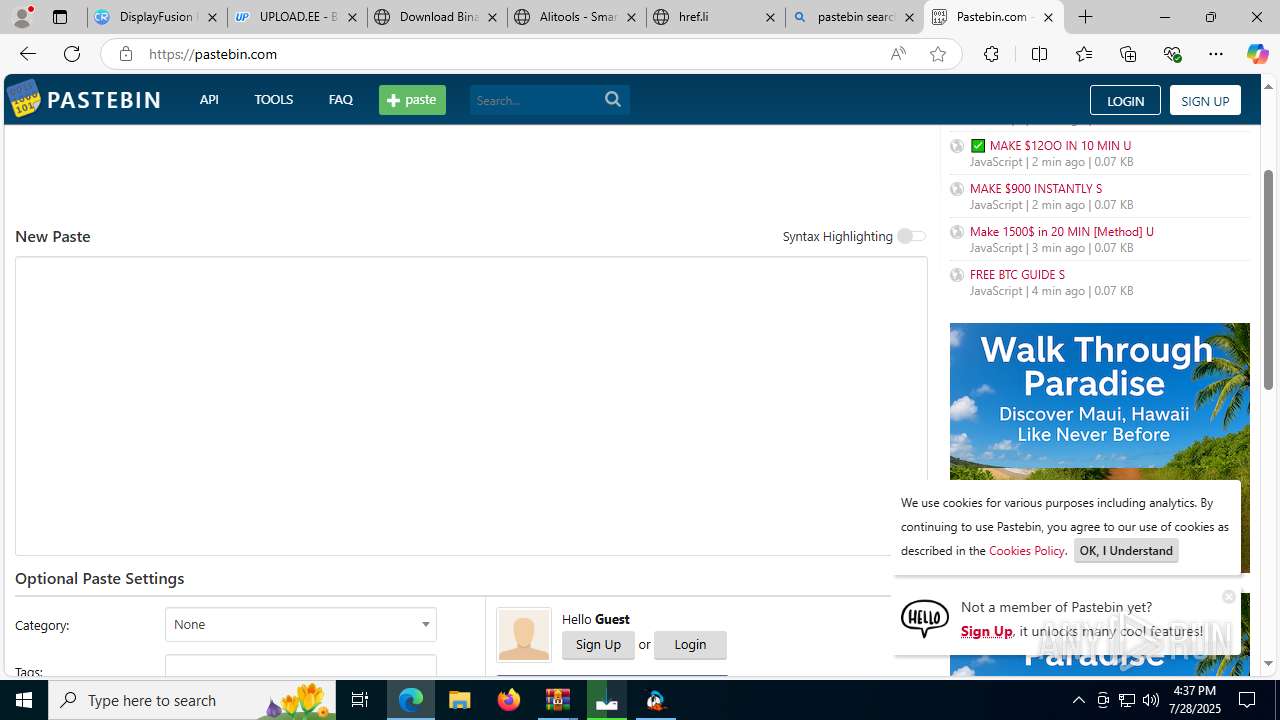
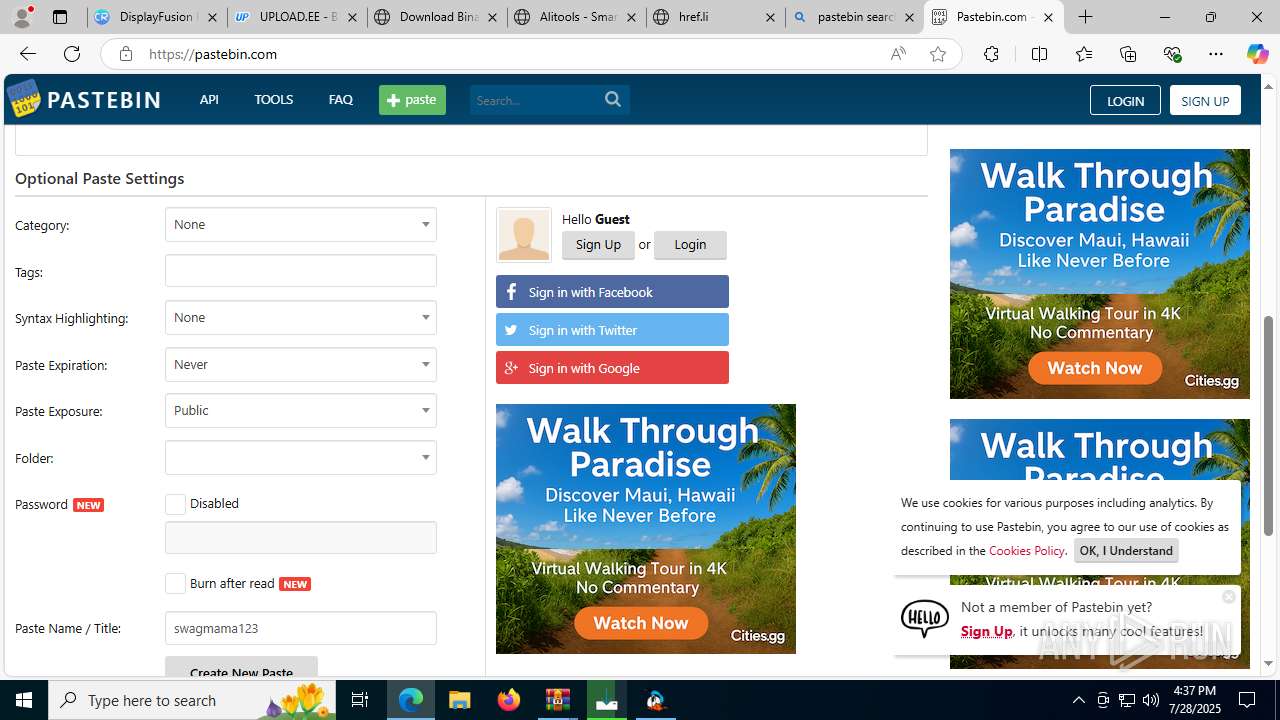
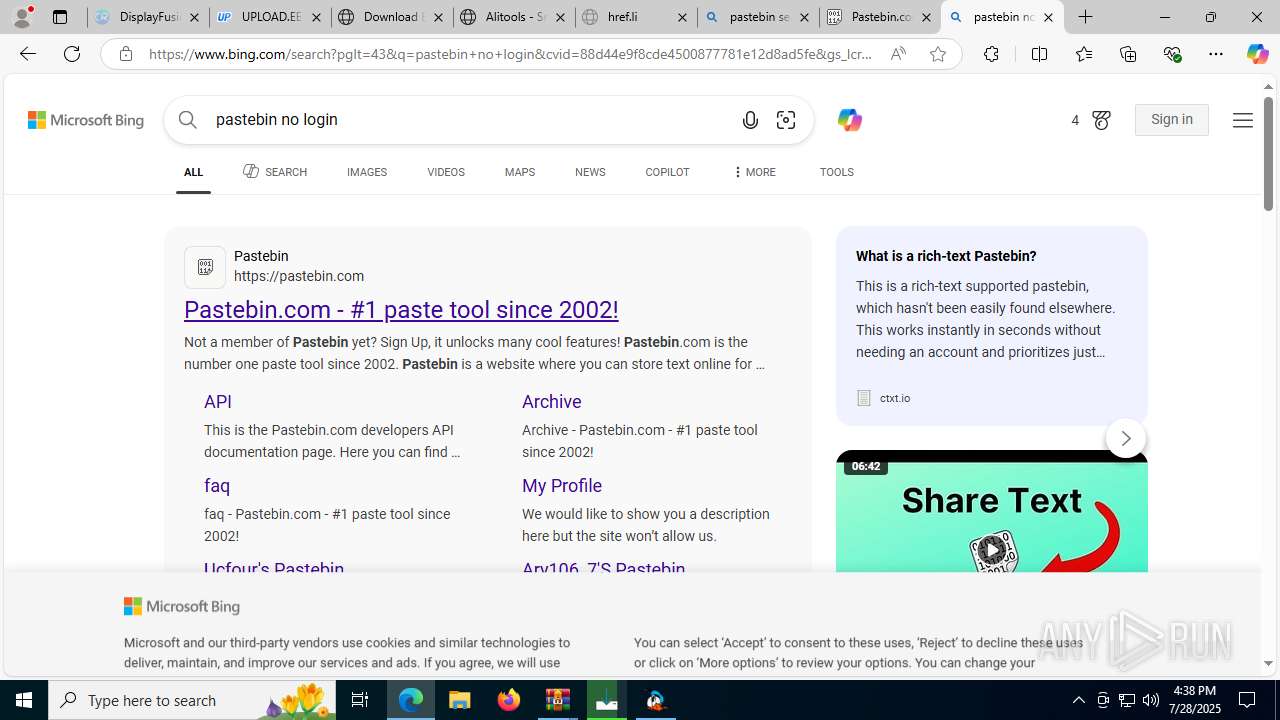
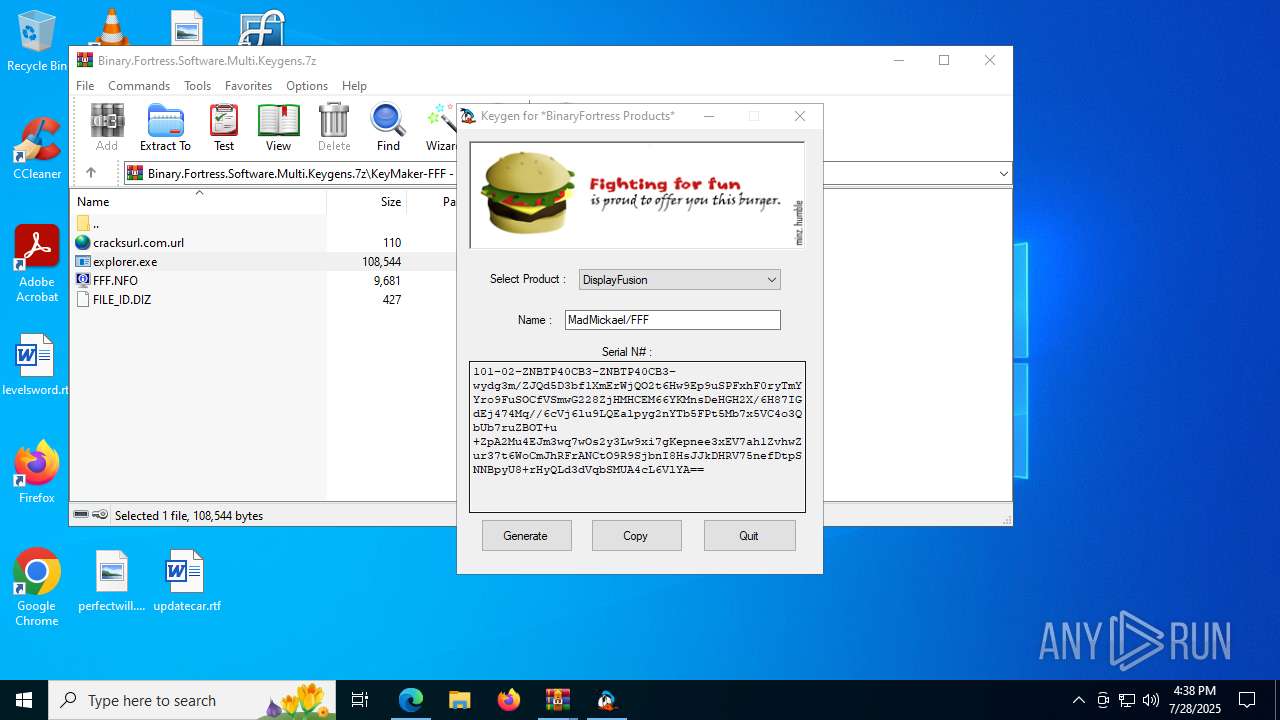
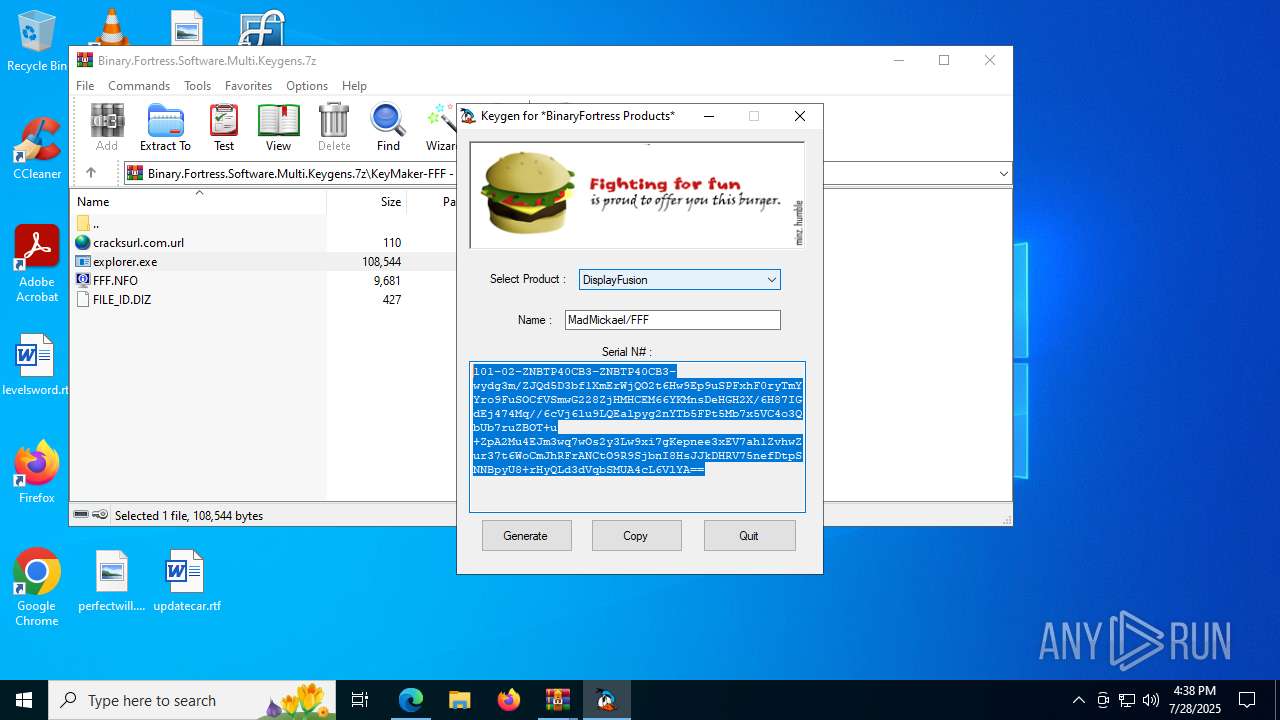
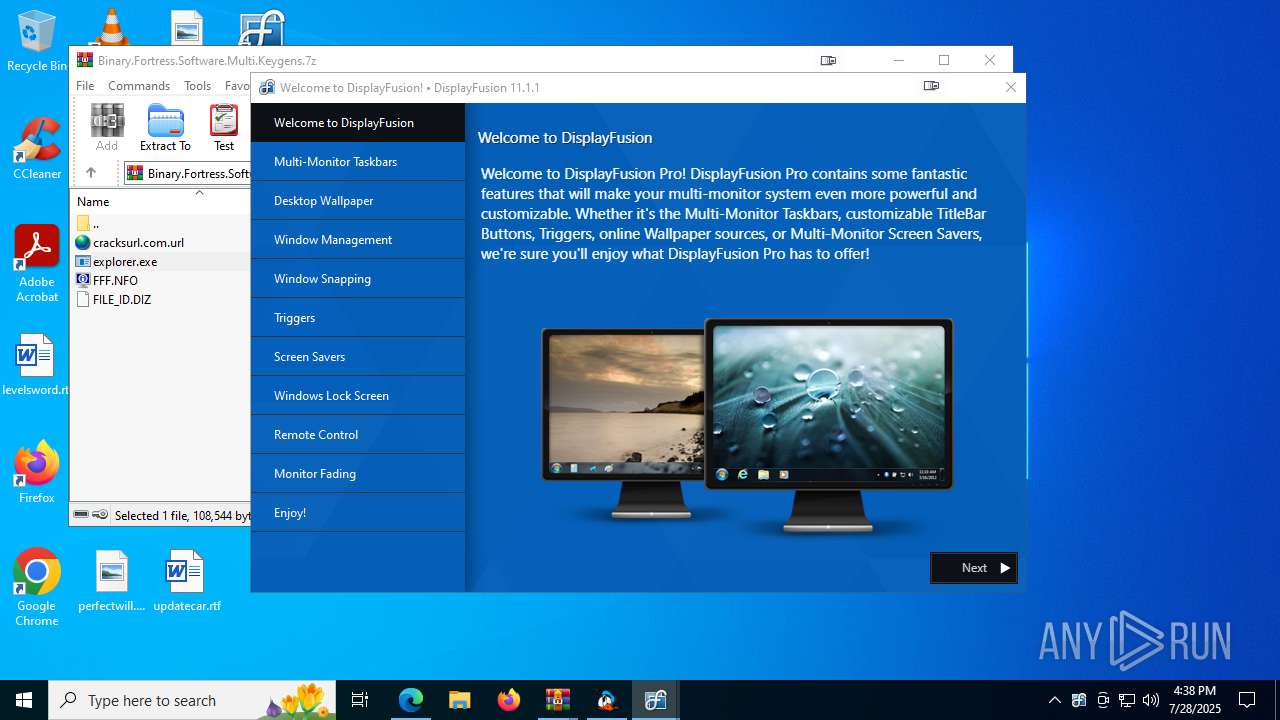
| URL: | https://cracksurl.com/displayfusion-pro/ |
| Full analysis: | https://app.any.run/tasks/6202c114-f887-40ae-a688-bc15af1ec537 |
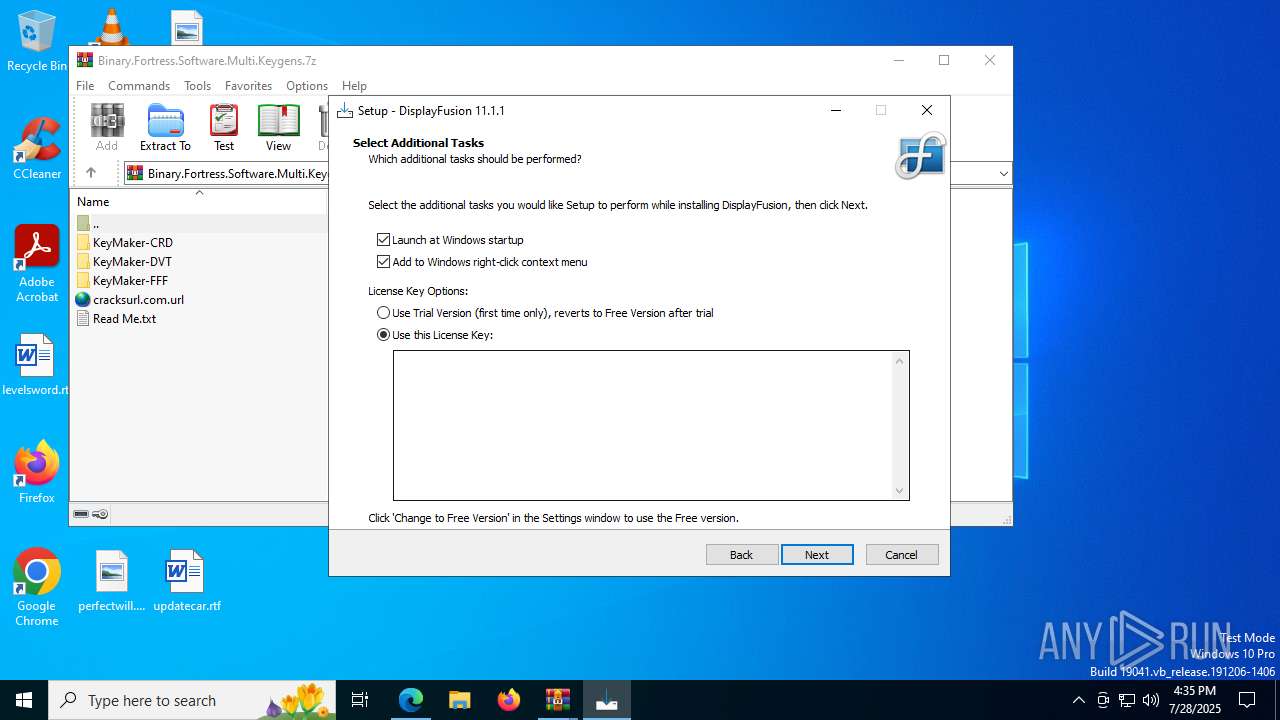
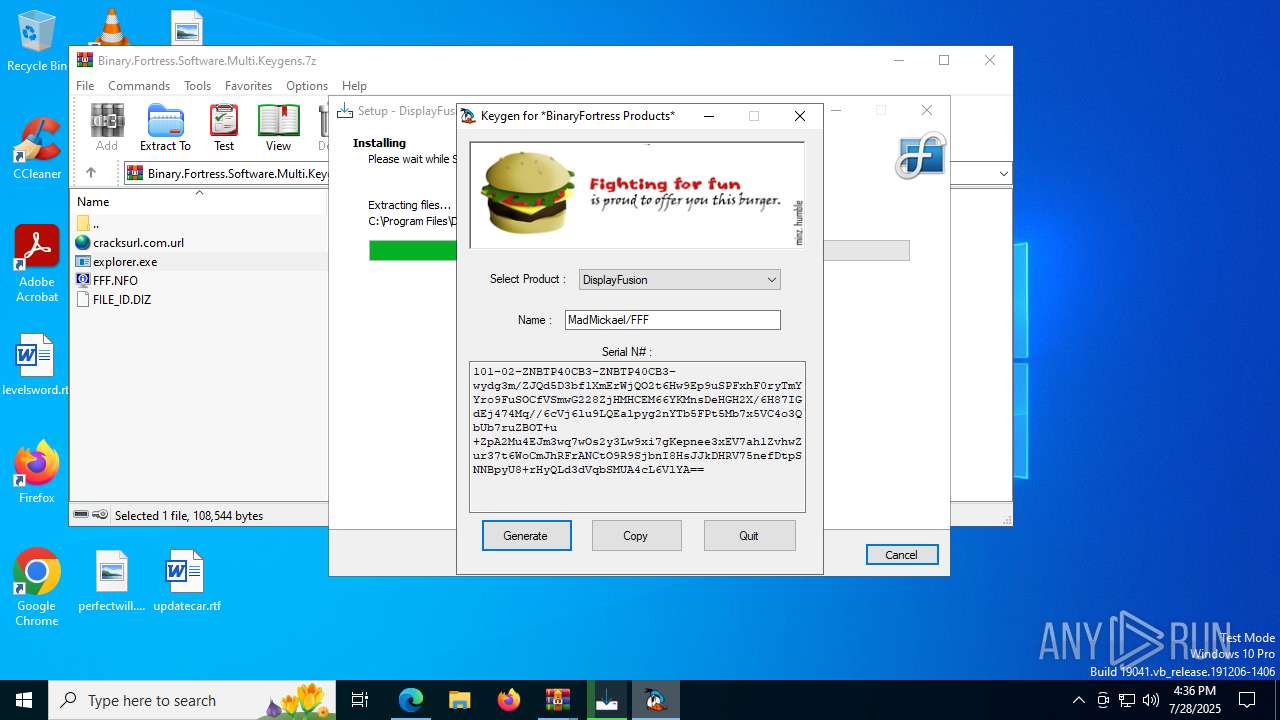
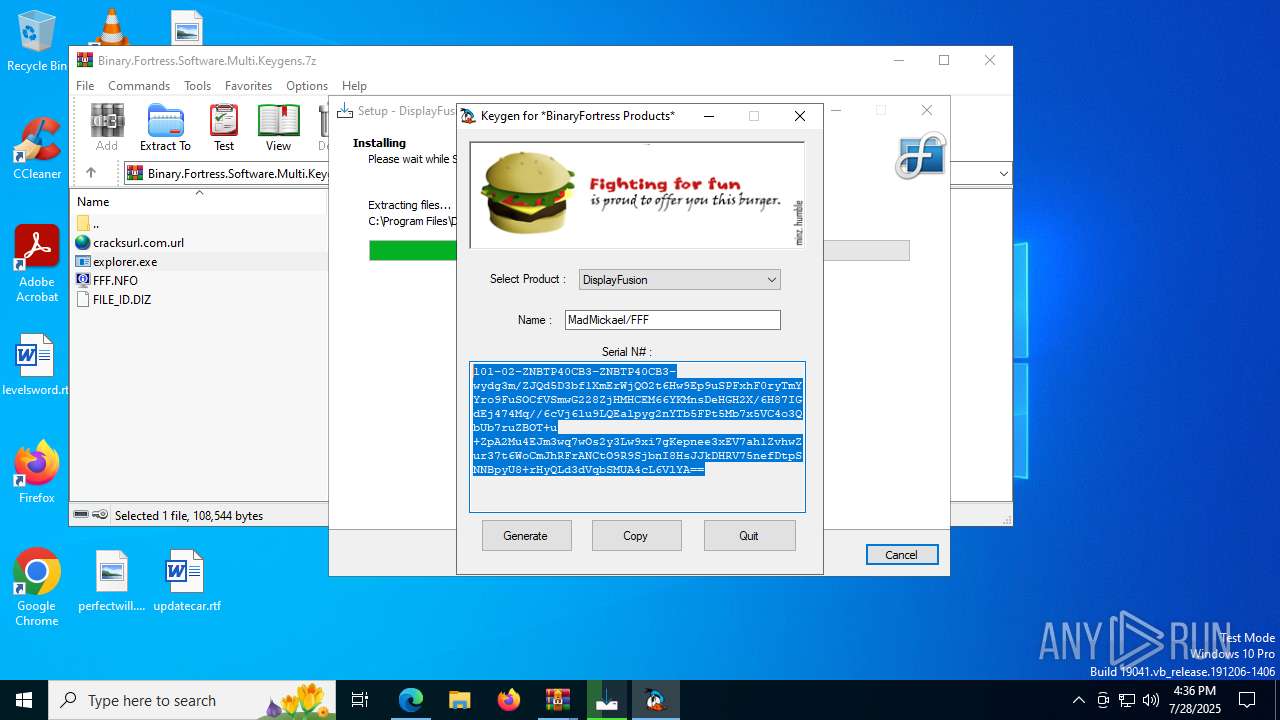
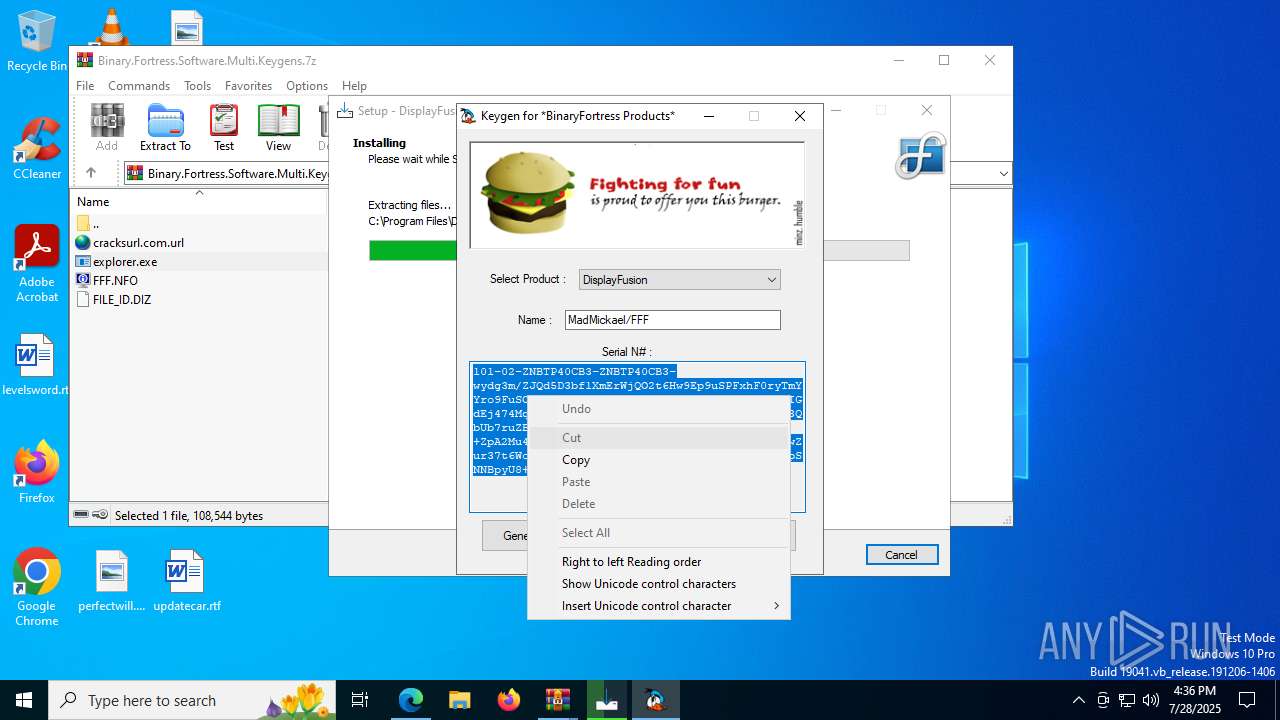
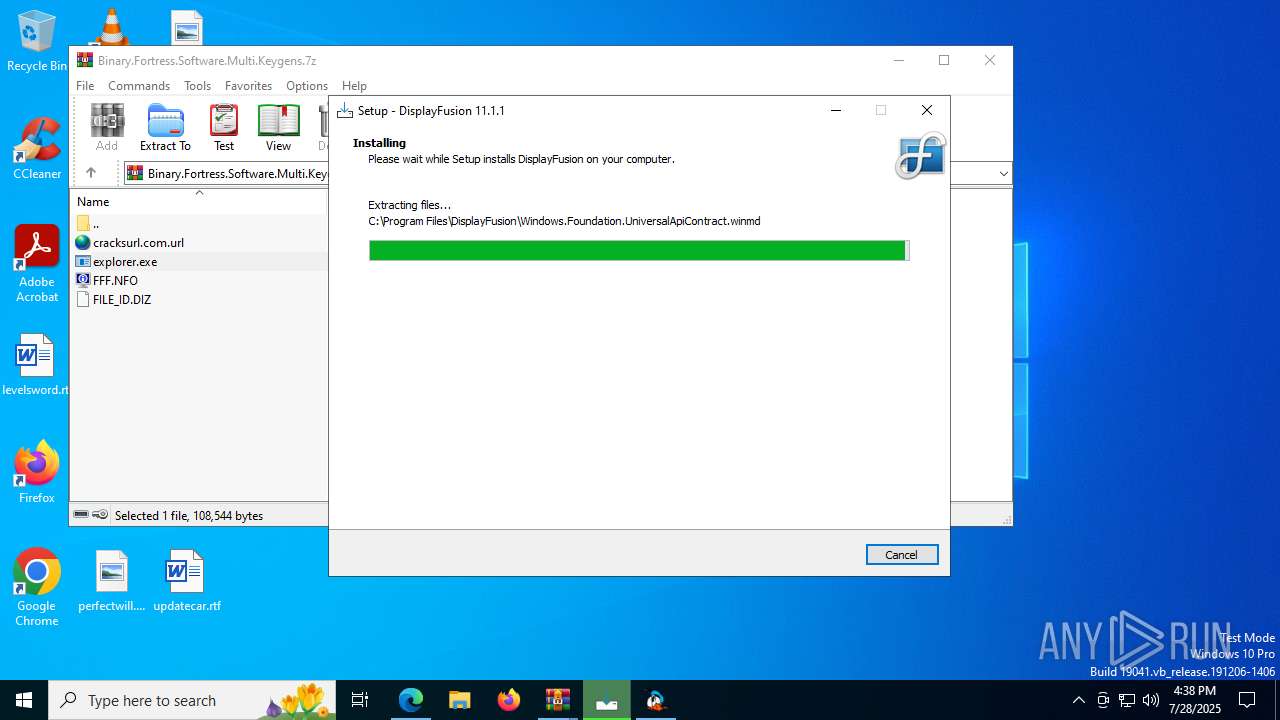
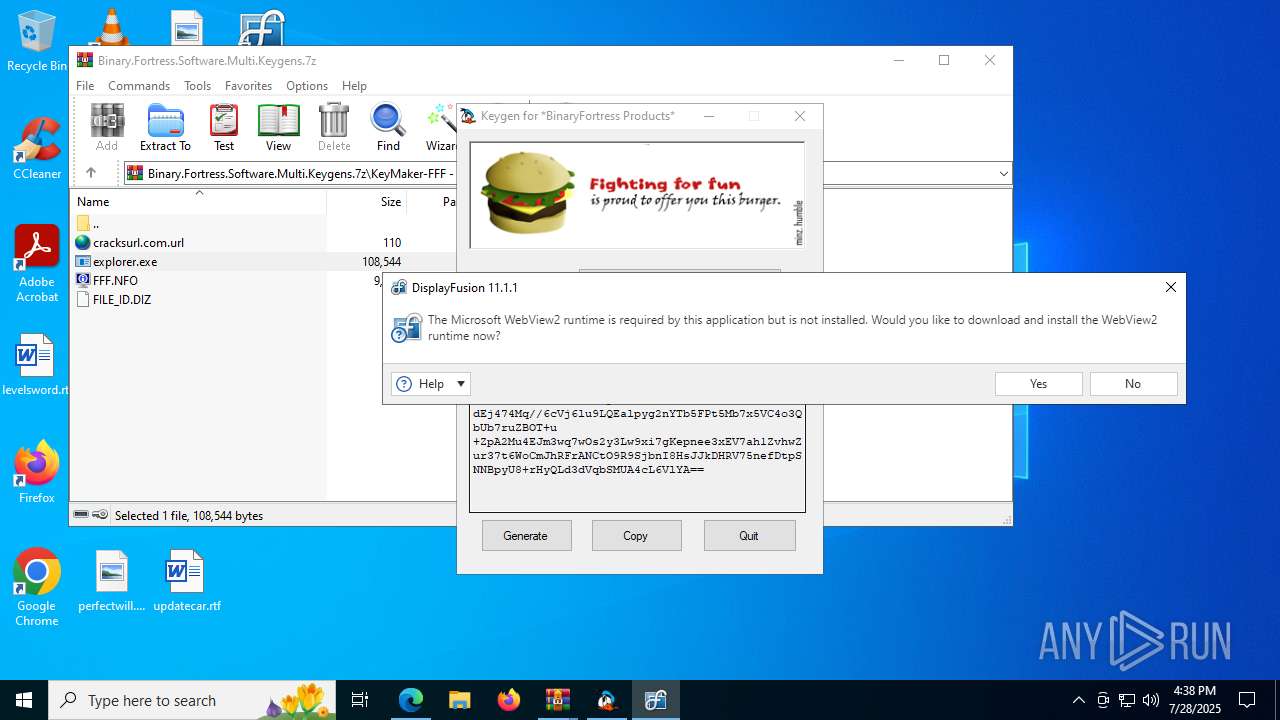
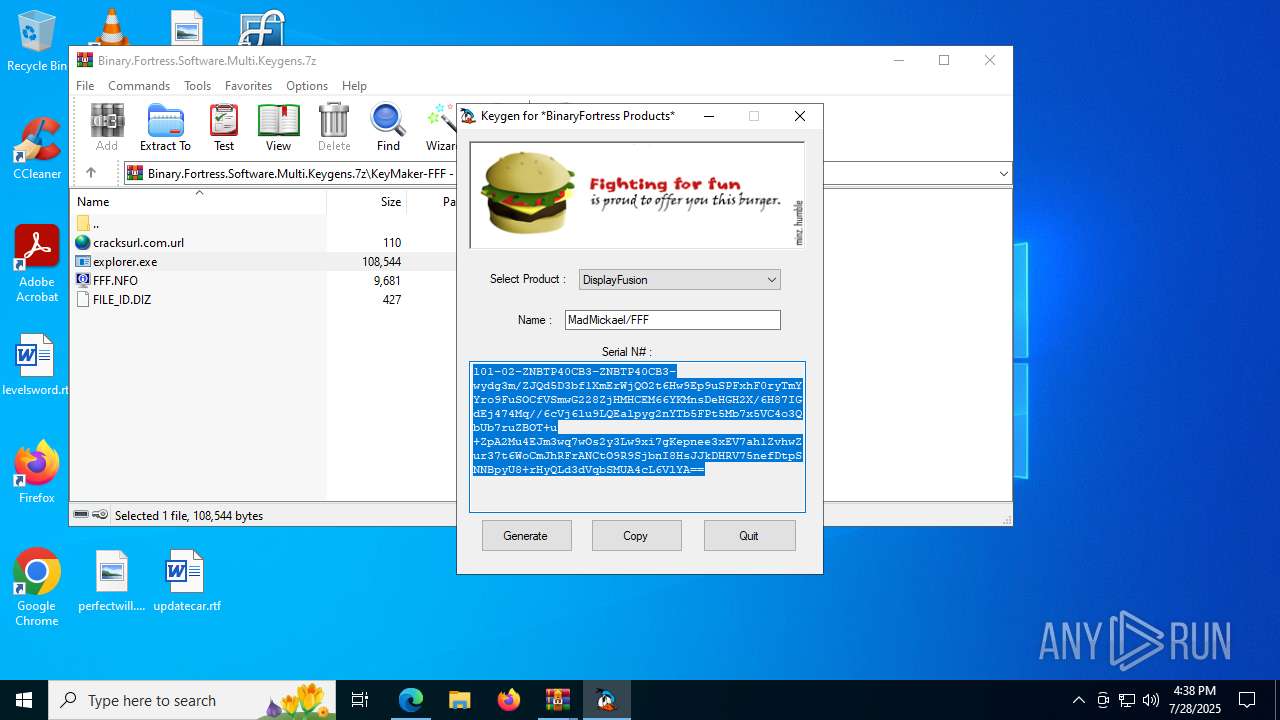
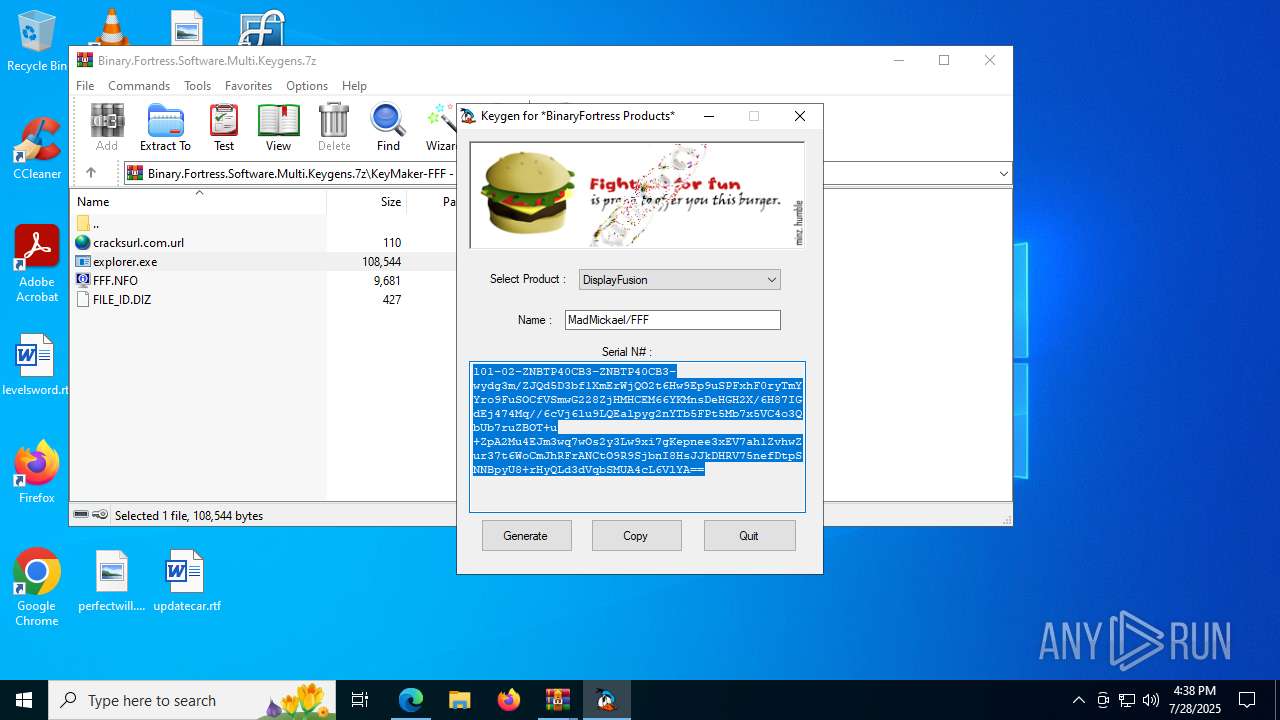
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | July 28, 2025, 16:34:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
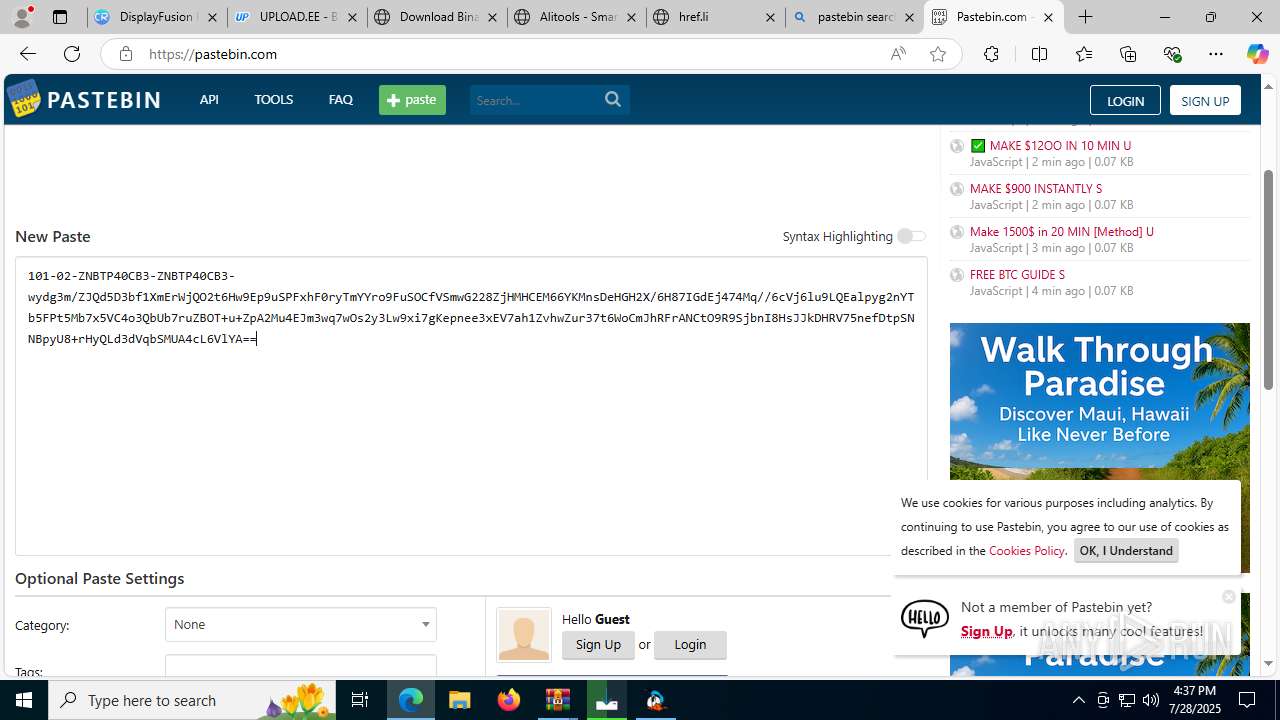
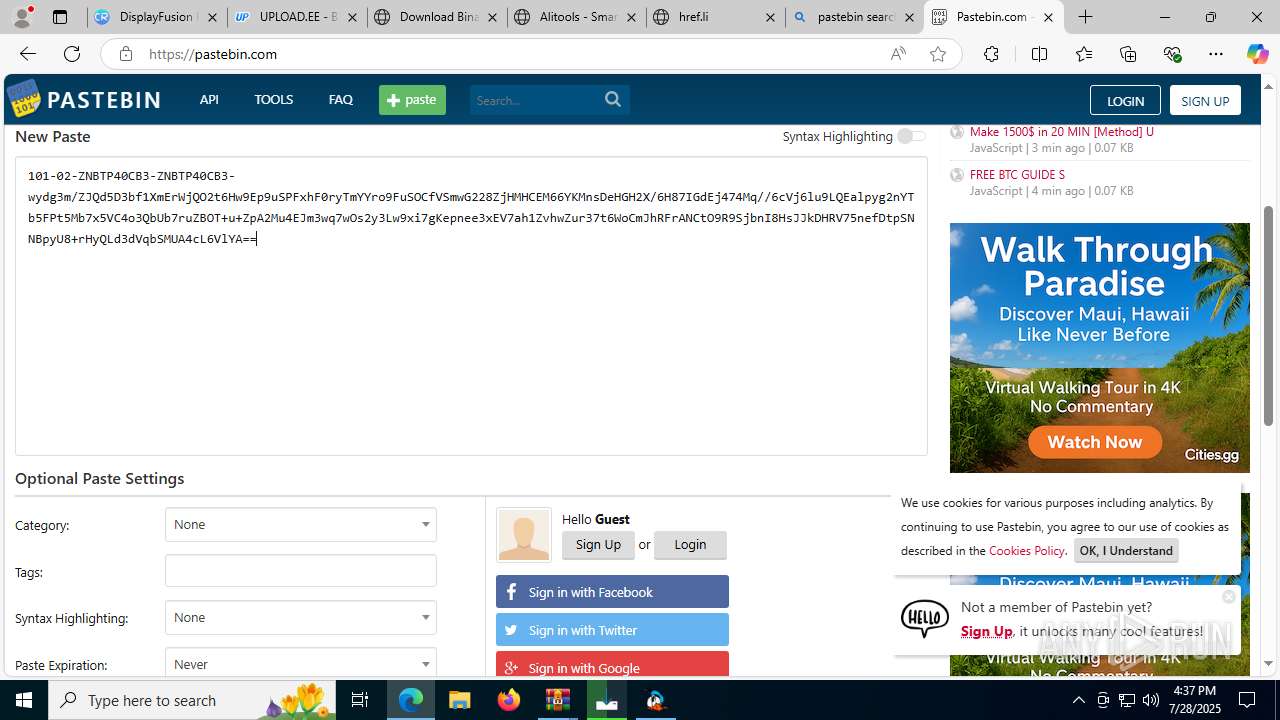
| MD5: | 659D8AD86BCAE6112D8D2E37D60A0034 |
| SHA1: | 329A0B2128CC8F78BFB992B6960B44FF62D06329 |
| SHA256: | 08C10FAFBE4CC46A86C5D50CF764B575D7FE258232A32BA0B3597A84AC442E00 |
| SSDEEP: | 3:N8K82aMWhs:2KV5 |
MALICIOUS
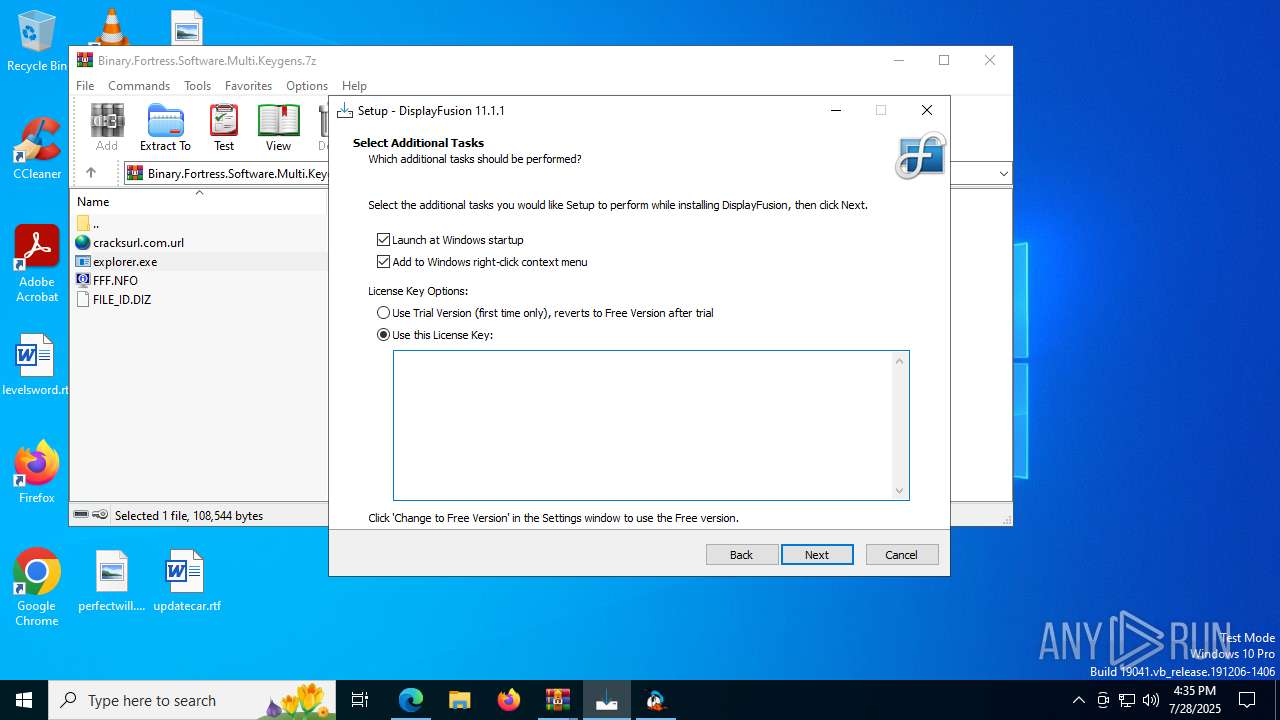
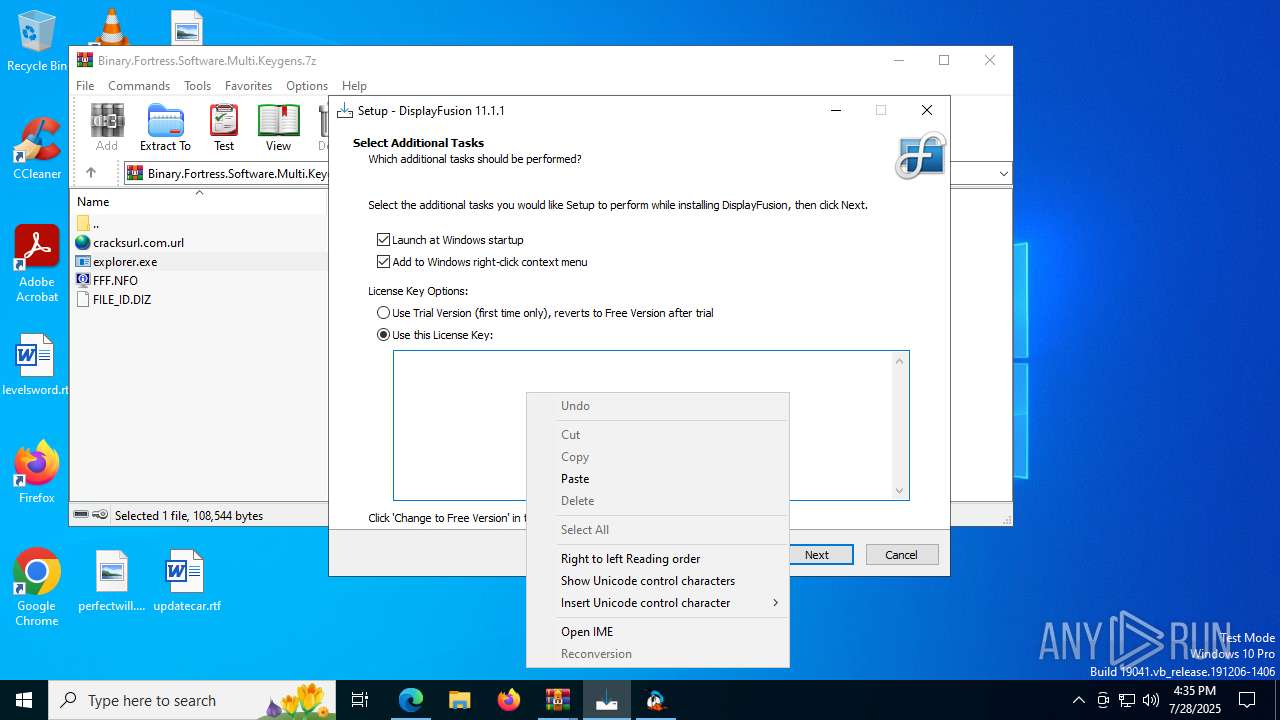
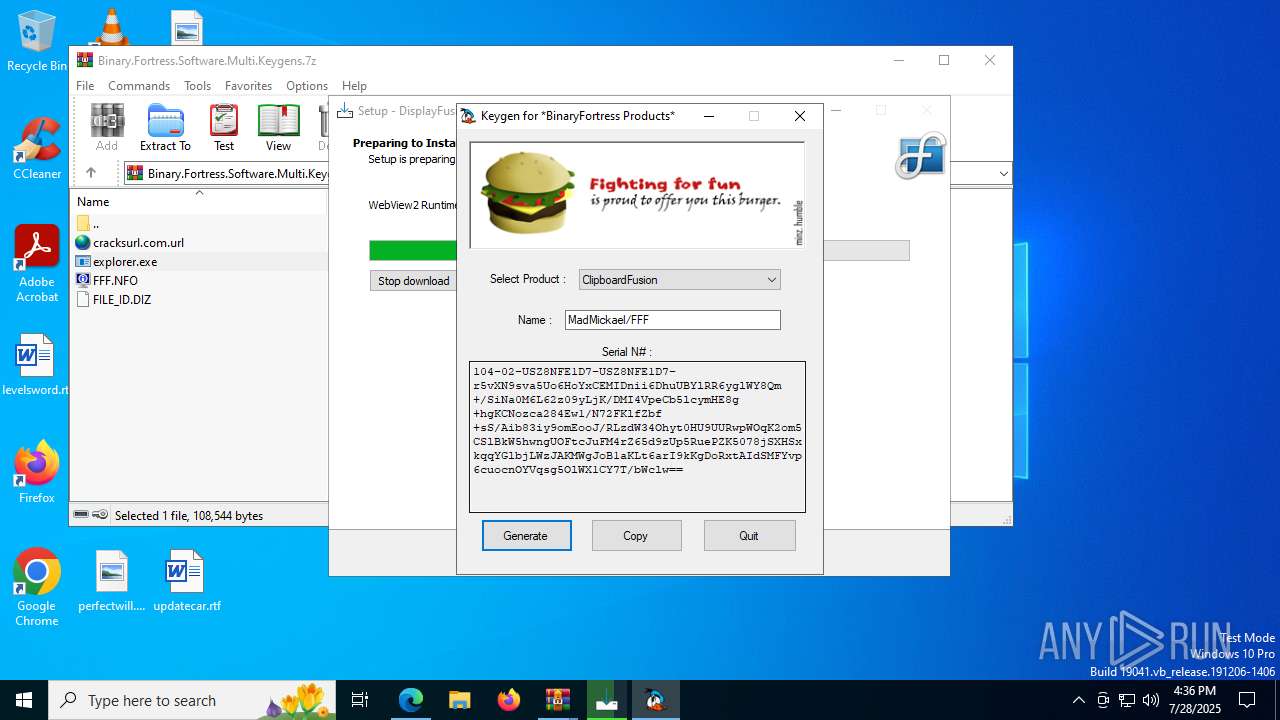
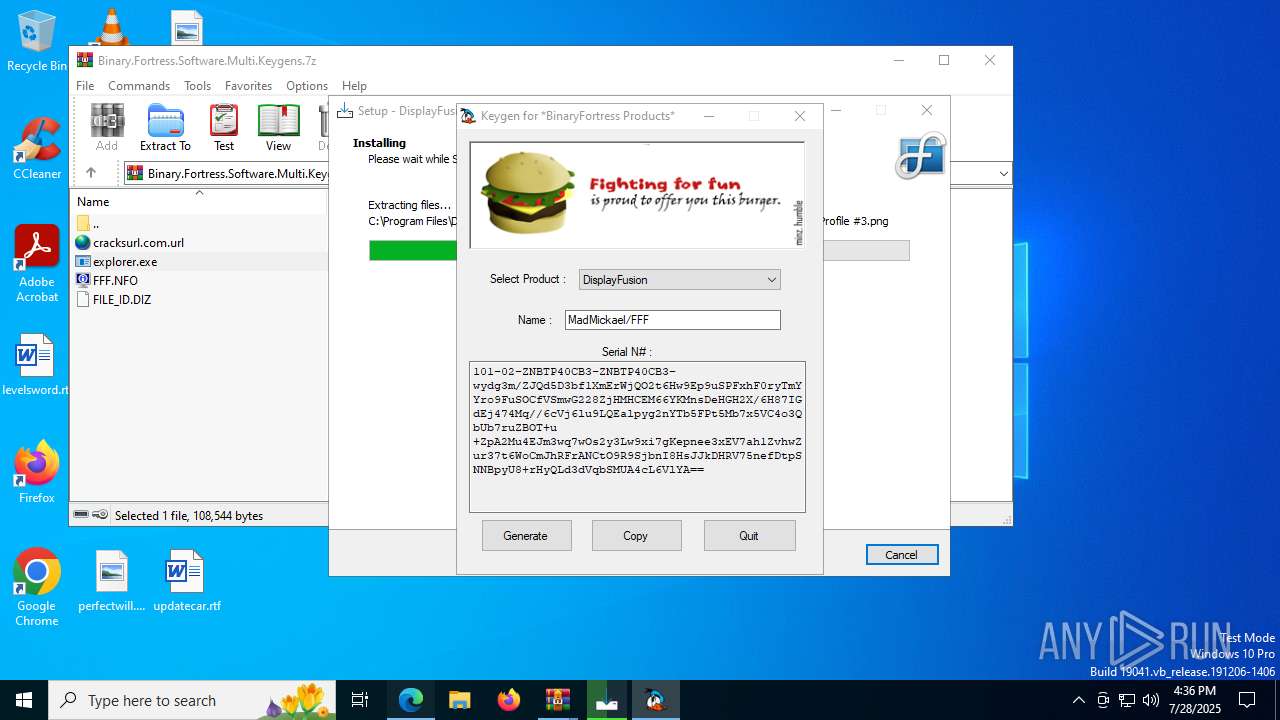
Changes the autorun value in the registry
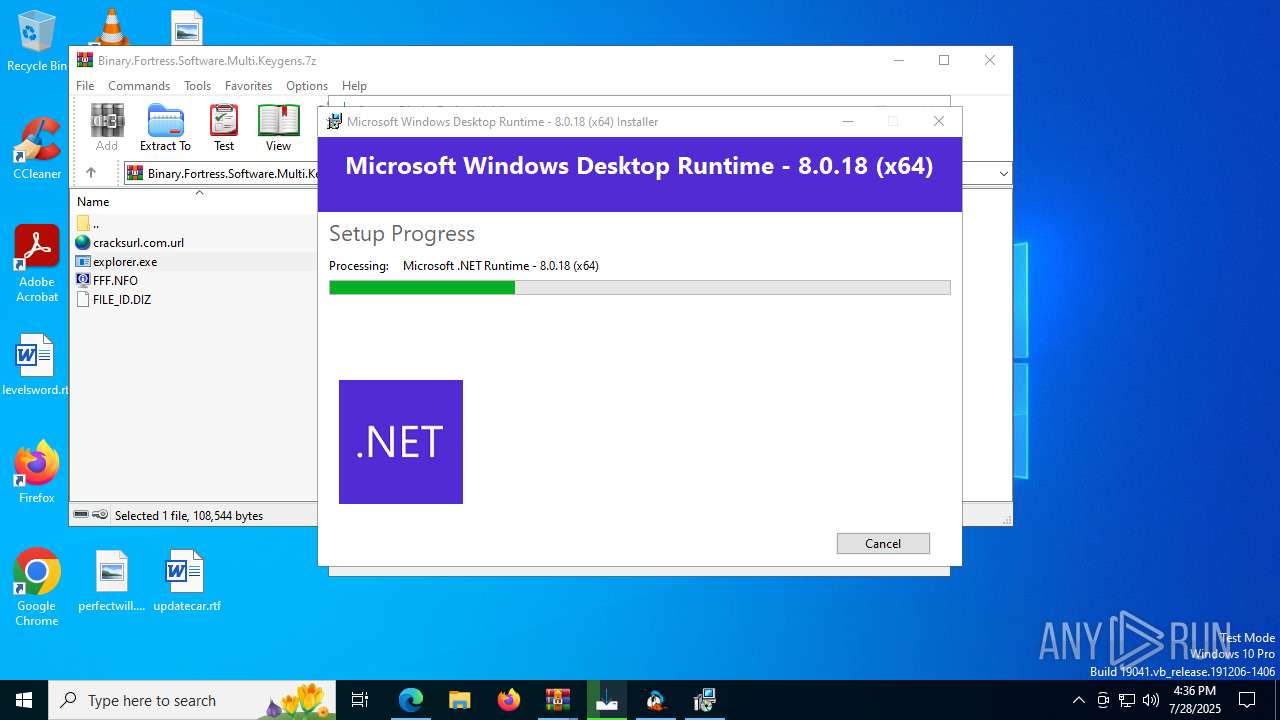
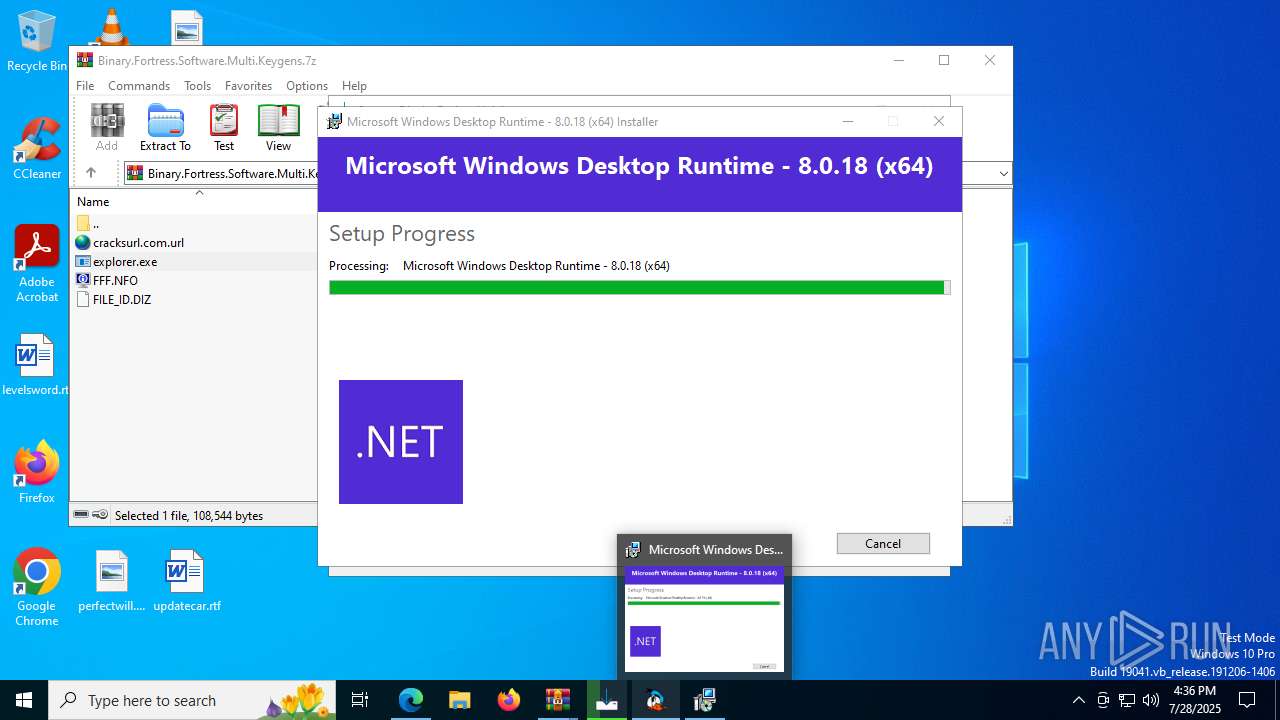
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
SUSPICIOUS
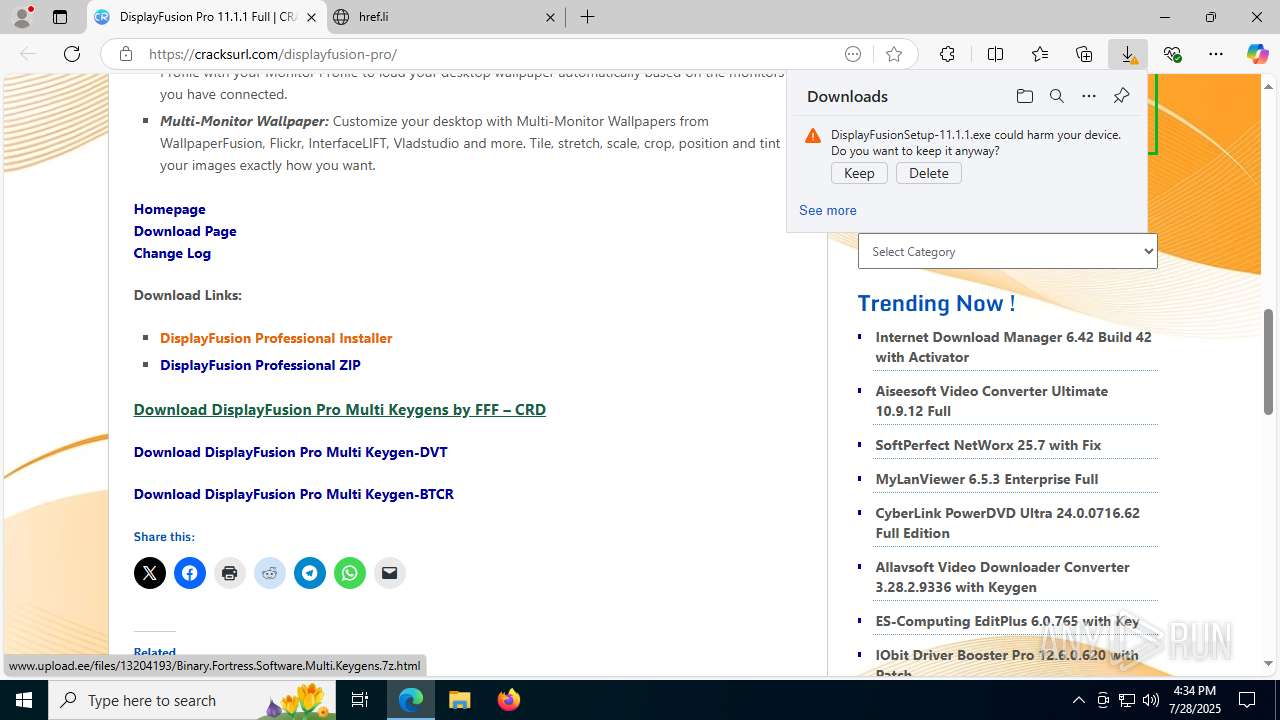
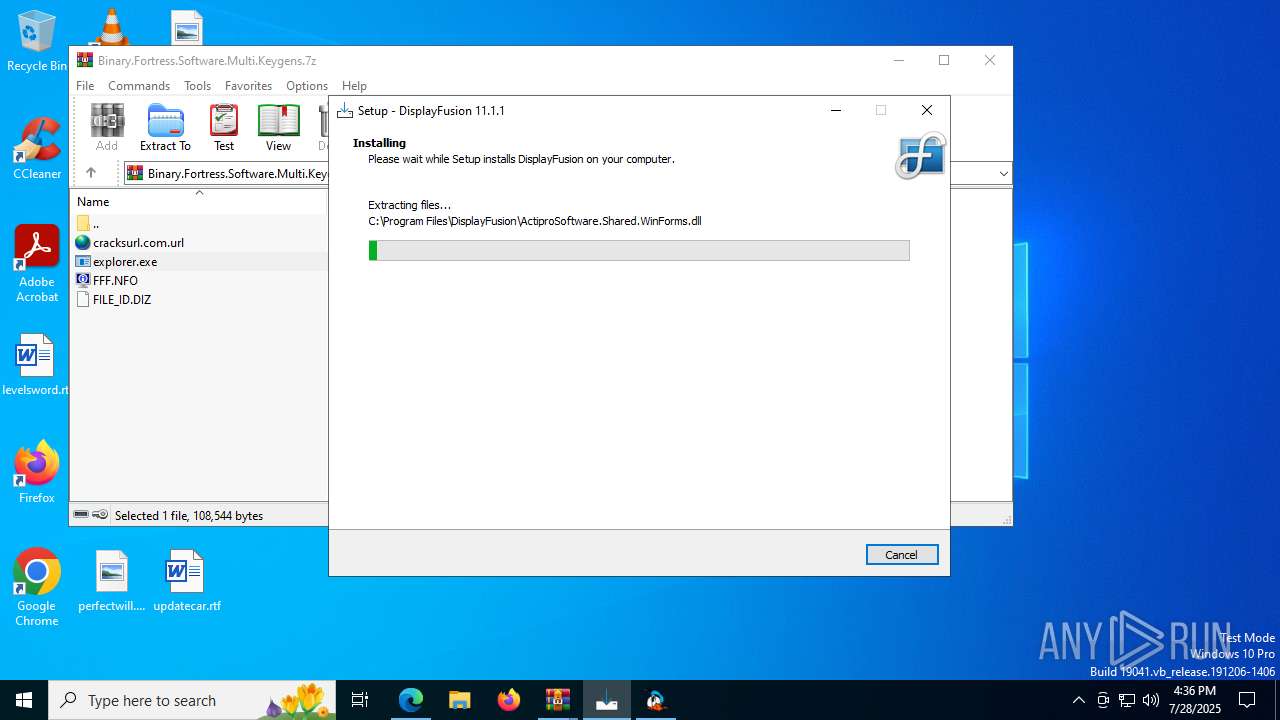
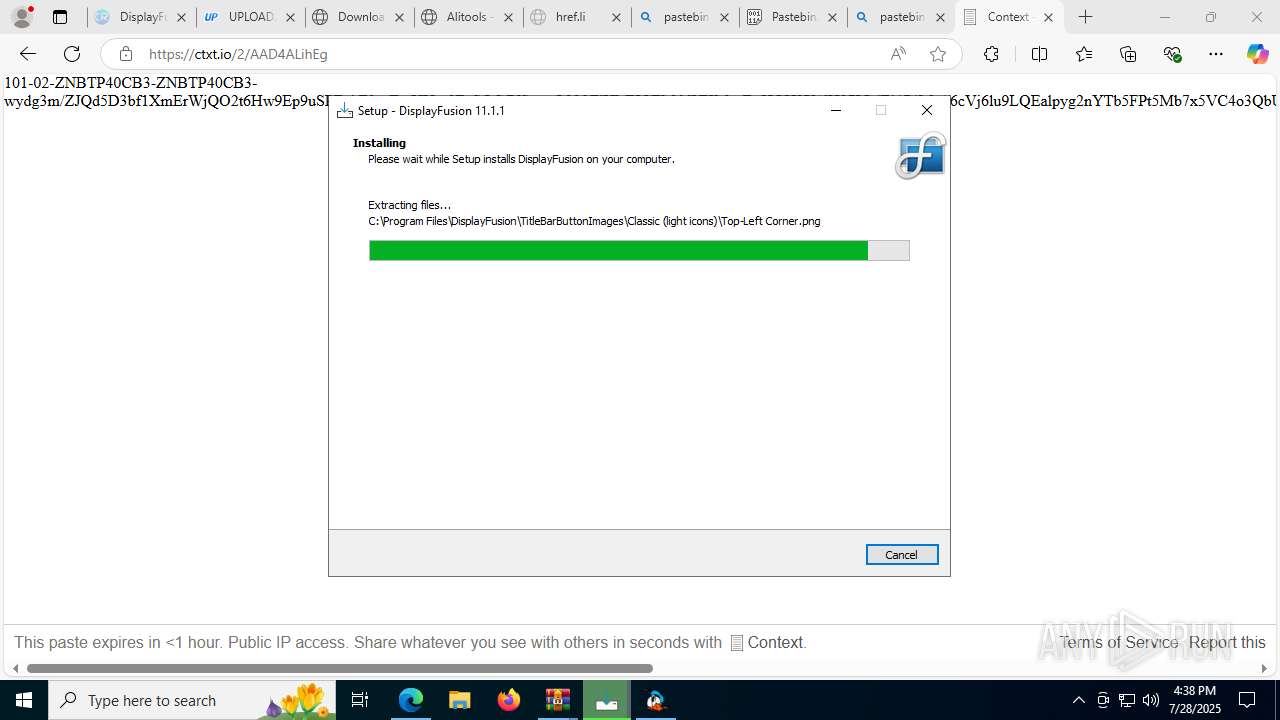
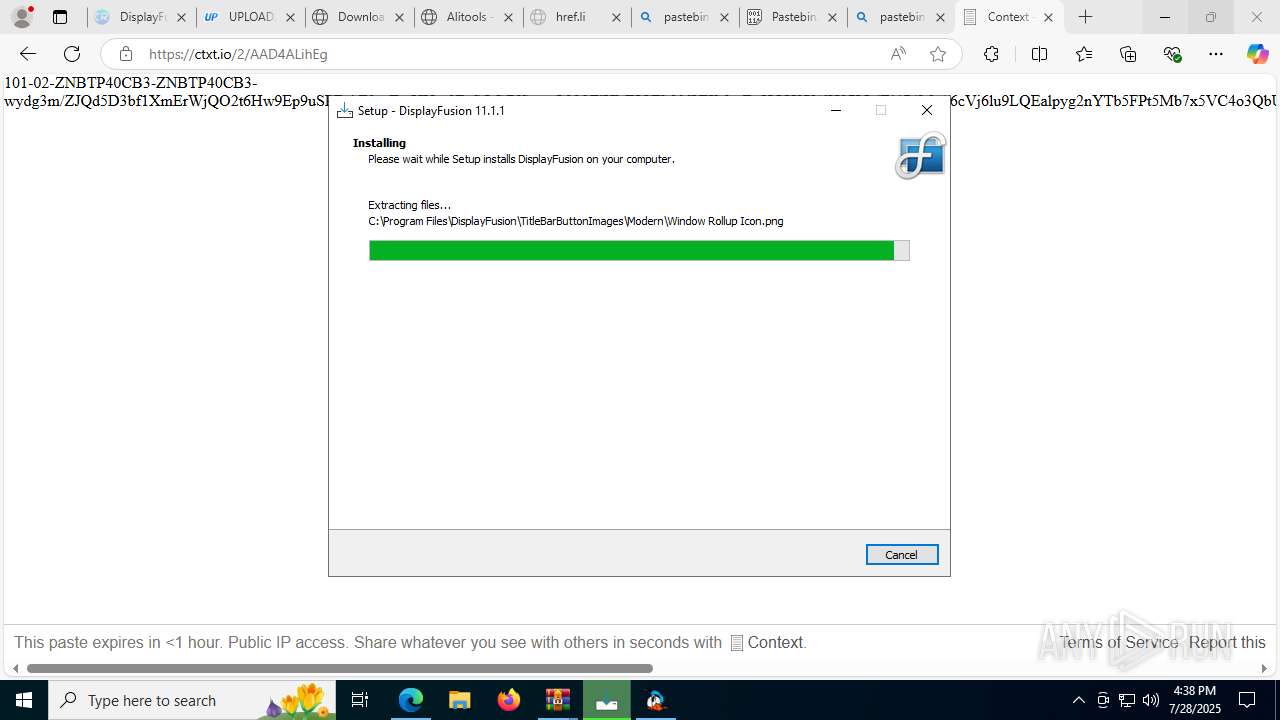
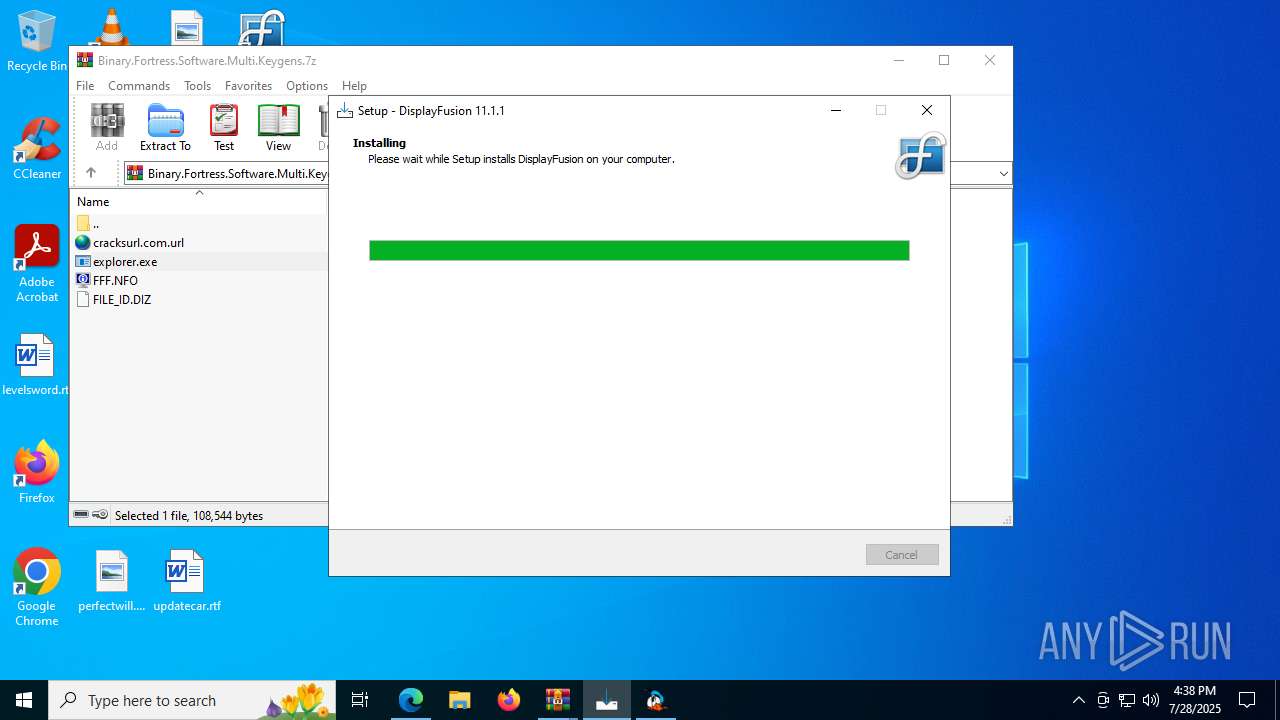
Executable content was dropped or overwritten
- DisplayFusionSetup-11.1.1.exe (PID: 1840)
- DisplayFusionSetup-11.1.1.exe (PID: 8164)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- dotnet80desktop64.exe (PID: 3960)
- dotnet80desktop64.exe (PID: 6584)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- MicrosoftEdgeWebview2Setup.exe (PID: 7668)
- DisplayFusion.exe (PID: 8748)
Reads security settings of Internet Explorer
- DisplayFusionSetup-11.1.1.tmp (PID: 7132)
- WinRAR.exe (PID: 6268)
- WinRAR.exe (PID: 6096)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- dotnet80desktop64.exe (PID: 6584)
- MicrosoftEdgeUpdate.exe (PID: 8168)
- DisplayFusion.exe (PID: 8748)
Reads the Windows owner or organization settings
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- msiexec.exe (PID: 7916)
Process drops legitimate windows executable
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- dotnet80desktop64.exe (PID: 3960)
- dotnet80desktop64.exe (PID: 6584)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- msiexec.exe (PID: 7916)
- MicrosoftEdgeWebview2Setup.exe (PID: 7668)
- MicrosoftEdgeUpdate.exe (PID: 8168)
Starts a Microsoft application from unusual location
- netcorecheck64.exe (PID: 8156)
- dotnet80desktop64.exe (PID: 3960)
- dotnet80desktop64.exe (PID: 6584)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- MicrosoftEdgeWebview2Setup.exe (PID: 7668)
- MicrosoftEdgeUpdate.exe (PID: 8168)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 6096)
- msiexec.exe (PID: 7916)
Searches for installed software
- dotnet80desktop64.exe (PID: 6584)
Starts itself from another location
- dotnet80desktop64.exe (PID: 6584)
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
The process drops C-runtime libraries
- msiexec.exe (PID: 7916)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 8168)
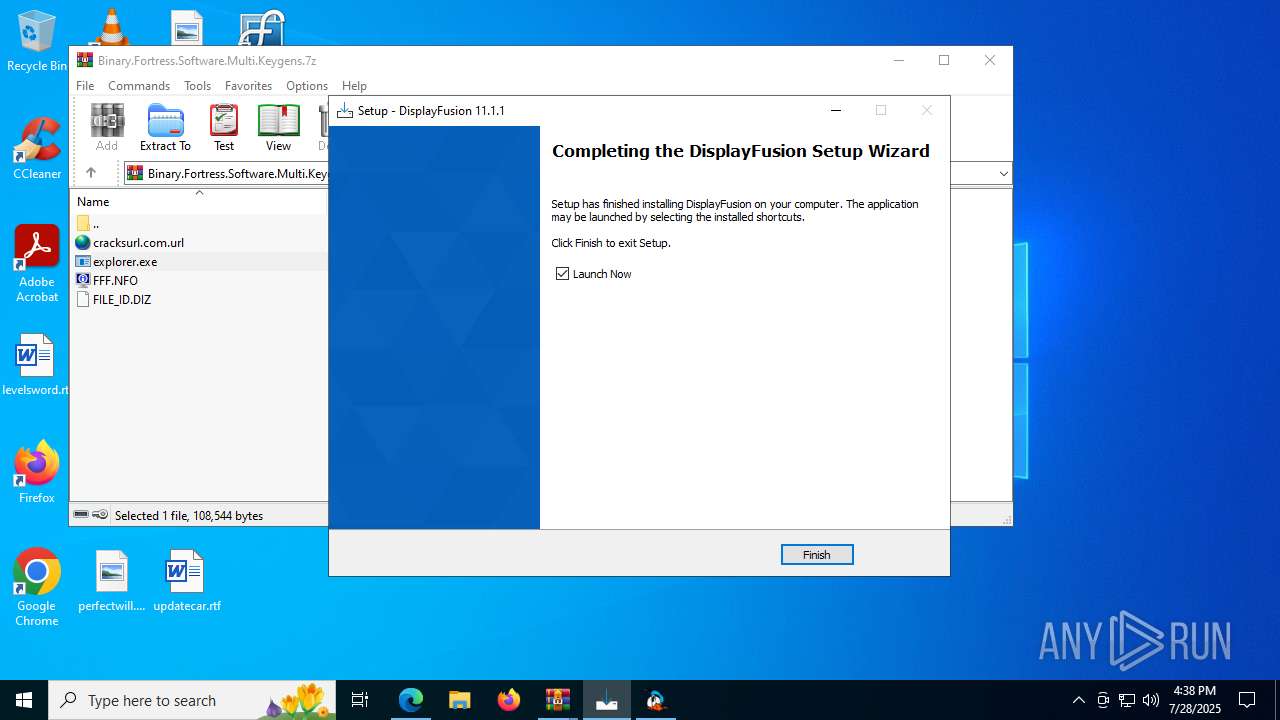
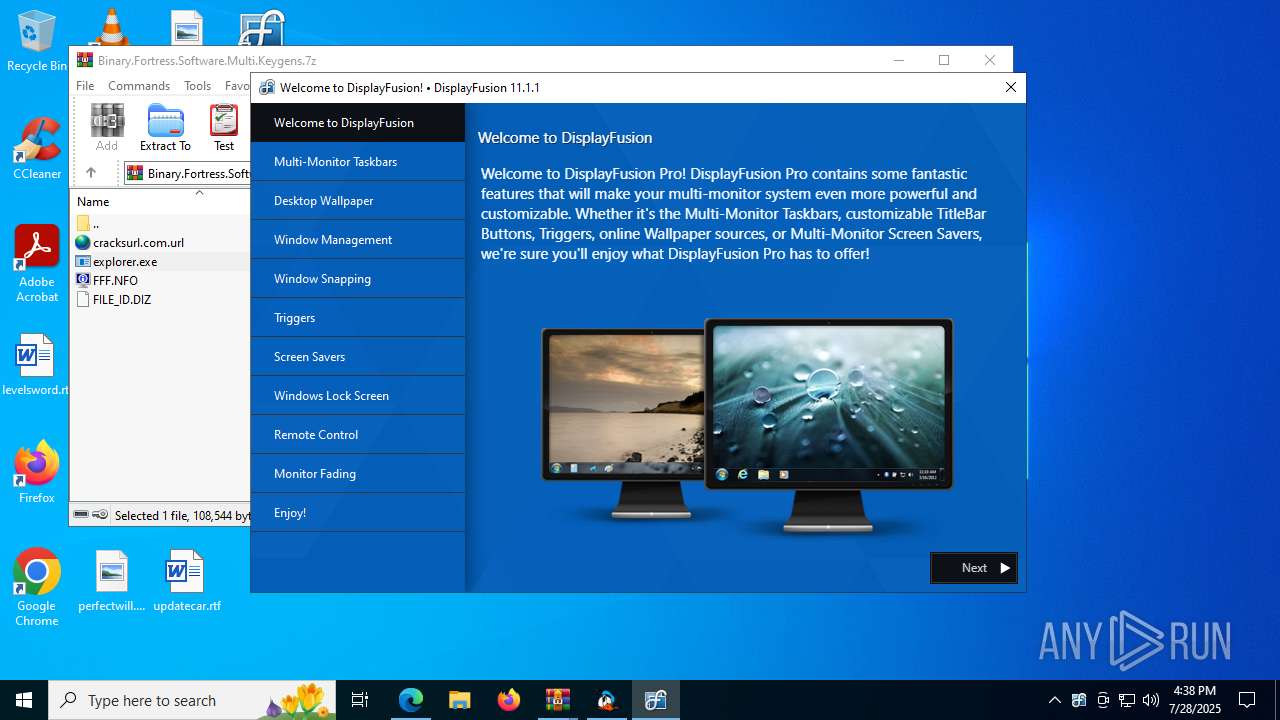
Creates or modifies Windows services
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
Executes as Windows Service
- DisplayFusionService.exe (PID: 432)
Reads the date of Windows installation
- DisplayFusionService.exe (PID: 432)
- DisplayFusion.exe (PID: 8748)
INFO
Application launched itself
- msedge.exe (PID: 2384)
Checks supported languages
- identity_helper.exe (PID: 7796)
- DisplayFusionSetup-11.1.1.exe (PID: 1840)
- DisplayFusionSetup-11.1.1.tmp (PID: 7132)
- DisplayFusionSetup-11.1.1.exe (PID: 8164)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- netcorecheck64.exe (PID: 8156)
- explorer.exe (PID: 7356)
- dotnet80desktop64.exe (PID: 3960)
- dotnet80desktop64.exe (PID: 6584)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- msiexec.exe (PID: 7916)
- msiexec.exe (PID: 1352)
- msiexec.exe (PID: 6192)
- msiexec.exe (PID: 6736)
- msiexec.exe (PID: 2592)
- MicrosoftEdgeWebview2Setup.exe (PID: 7668)
- MicrosoftEdgeUpdate.exe (PID: 8168)
- DisplayFusionService.exe (PID: 432)
- DisplayFusionHookApp32.exe (PID: 8652)
- DisplayFusionHookApp64.exe (PID: 8888)
- DisplayFusion.exe (PID: 8748)
Reads the computer name
- identity_helper.exe (PID: 7796)
- DisplayFusionSetup-11.1.1.tmp (PID: 7132)
- DisplayFusionSetup-11.1.1.exe (PID: 8164)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- explorer.exe (PID: 7356)
- dotnet80desktop64.exe (PID: 3960)
- dotnet80desktop64.exe (PID: 6584)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- msiexec.exe (PID: 7916)
- msiexec.exe (PID: 1352)
- msiexec.exe (PID: 2592)
- msiexec.exe (PID: 6736)
- msiexec.exe (PID: 6192)
- MicrosoftEdgeUpdate.exe (PID: 8168)
- DisplayFusionService.exe (PID: 432)
- DisplayFusion.exe (PID: 8748)
Reads Environment values
- identity_helper.exe (PID: 7796)
- MicrosoftEdgeUpdate.exe (PID: 8168)
- DisplayFusionService.exe (PID: 432)
- DisplayFusion.exe (PID: 8748)
Connects to unusual port
- msedge.exe (PID: 2348)
Create files in a temporary directory
- DisplayFusionSetup-11.1.1.exe (PID: 1840)
- DisplayFusionSetup-11.1.1.exe (PID: 8164)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- netcorecheck64.exe (PID: 8156)
- dotnet80desktop64.exe (PID: 6584)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
Executable content was dropped or overwritten
- msedge.exe (PID: 2384)
- WinRAR.exe (PID: 6096)
- msiexec.exe (PID: 7916)
Process checks computer location settings
- DisplayFusionSetup-11.1.1.tmp (PID: 7132)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- dotnet80desktop64.exe (PID: 6584)
- MicrosoftEdgeUpdate.exe (PID: 8168)
- DisplayFusion.exe (PID: 8748)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2384)
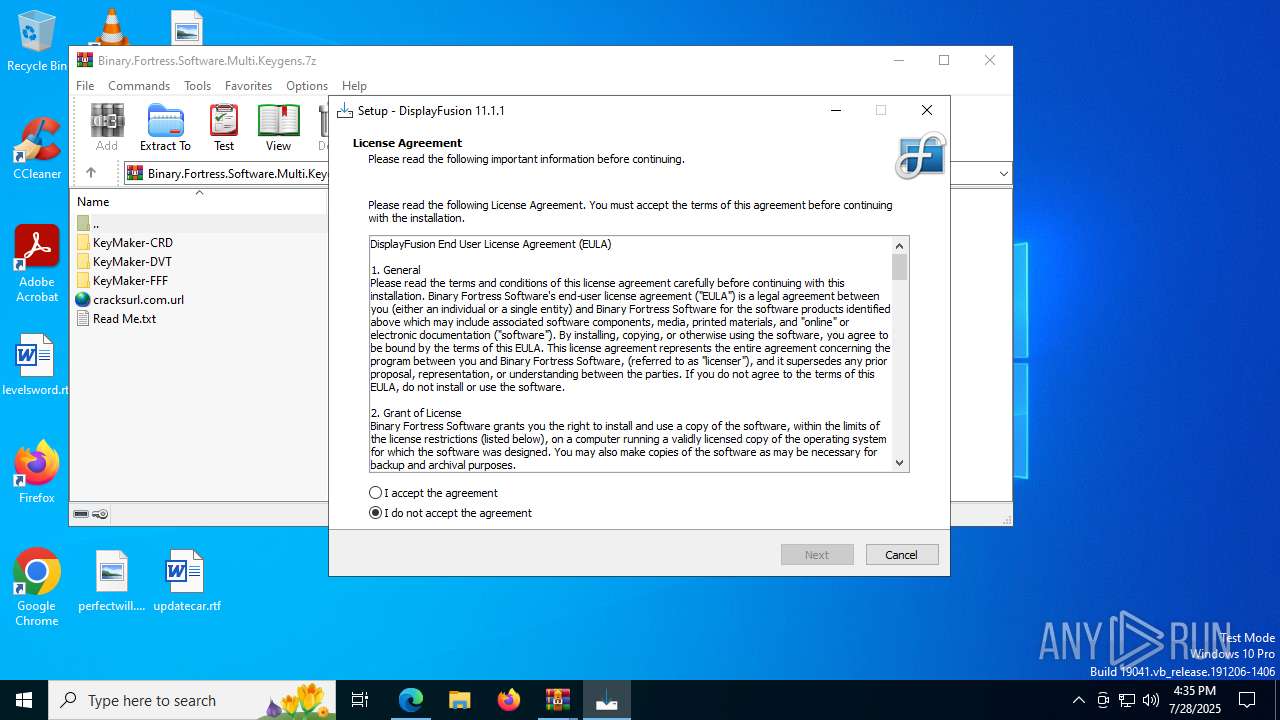
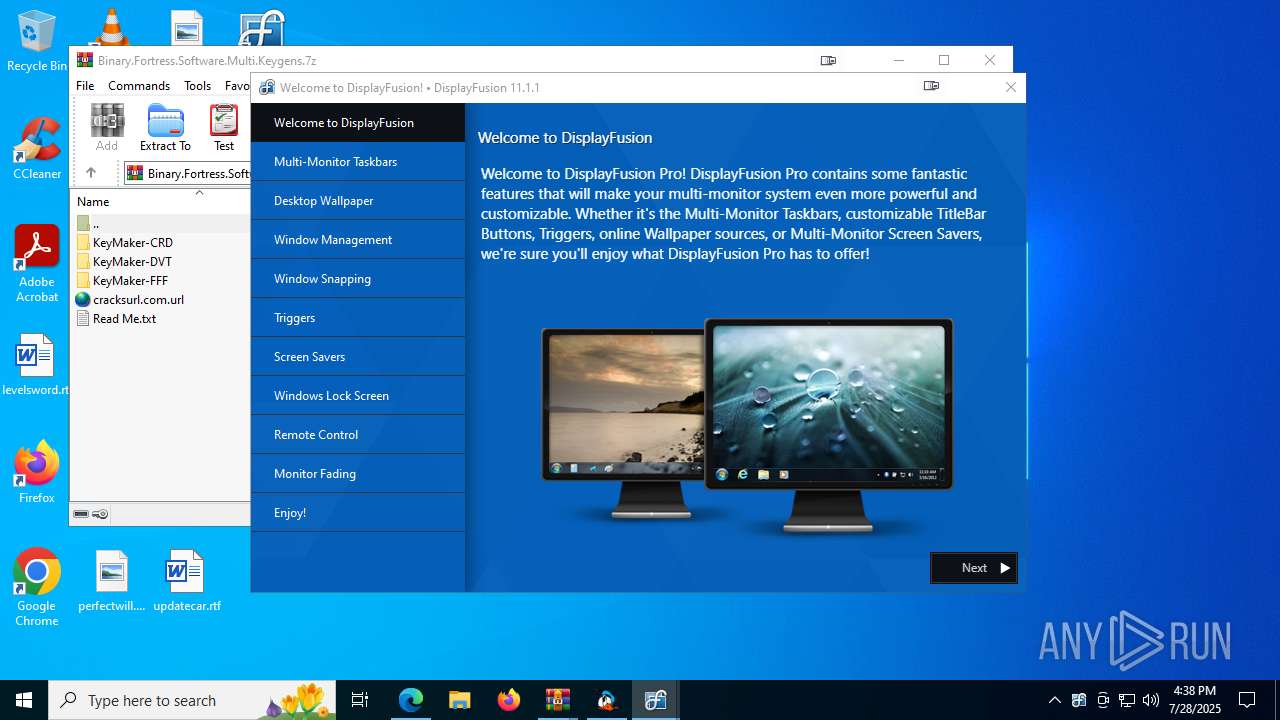
Compiled with Borland Delphi (YARA)
- DisplayFusionSetup-11.1.1.exe (PID: 1840)
- DisplayFusionSetup-11.1.1.tmp (PID: 7132)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- DisplayFusionSetup-11.1.1.exe (PID: 8164)
Detects InnoSetup installer (YARA)
- DisplayFusionSetup-11.1.1.exe (PID: 1840)
- DisplayFusionSetup-11.1.1.tmp (PID: 7132)
- DisplayFusionSetup-11.1.1.exe (PID: 8164)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
The sample compiled with english language support
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- dotnet80desktop64.exe (PID: 3960)
- dotnet80desktop64.exe (PID: 6584)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- msiexec.exe (PID: 7916)
- MicrosoftEdgeWebview2Setup.exe (PID: 7668)
- MicrosoftEdgeUpdate.exe (PID: 8168)
- DisplayFusion.exe (PID: 8748)
Reads the machine GUID from the registry
- explorer.exe (PID: 7356)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- msiexec.exe (PID: 7916)
- DisplayFusionService.exe (PID: 432)
- DisplayFusion.exe (PID: 8748)
Checks proxy server information
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- MicrosoftEdgeUpdate.exe (PID: 8168)
- slui.exe (PID: 2632)
- wermgr.exe (PID: 8172)
- DisplayFusion.exe (PID: 8748)
Reads the software policy settings
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- msiexec.exe (PID: 7916)
- MicrosoftEdgeUpdate.exe (PID: 8168)
- slui.exe (PID: 2632)
- wermgr.exe (PID: 8172)
- DisplayFusion.exe (PID: 8748)
Creates files in the program directory
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- MicrosoftEdgeWebview2Setup.exe (PID: 7668)
- DisplayFusionService.exe (PID: 432)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
- DisplayFusion.exe (PID: 8748)
Launching a file from a Registry key
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 1336)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
Creates a software uninstall entry
- msiexec.exe (PID: 7916)
- DisplayFusionSetup-11.1.1.tmp (PID: 1644)
Reads product name
- DisplayFusionService.exe (PID: 432)
- DisplayFusion.exe (PID: 8748)
Creates files or folders in the user directory
- wermgr.exe (PID: 8172)
- DisplayFusion.exe (PID: 8748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
264
Monitored processes
106
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Program Files\DisplayFusion\DisplayFusionService.exe" | C:\Program Files\DisplayFusion\DisplayFusionService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Binary Fortress Software Integrity Level: SYSTEM Description: DisplayFusion Service Version: 11.1.1.0 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6372,i,3720832337585821106,10554270236951888956,262144 --variations-seed-version --mojo-platform-channel-handle=6080 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\DisplayFusion\DisplayFusionHookApp32.exe" "8748" "852798" "67040" "0" "65668" "65760" "019851e6-958a-7572-860e-c6f2d474bb01" "C:\Program Files\DisplayFusion\Hooks\AppHook32_3FD48854-88B1-437D-BBF2-A0459A571B9C.dll" "DisplayFusion" "Software\Binary Fortress Software\DisplayFusion" "Software\Binary Fortress Software\DisplayFusion\Session\1" "0" "100" "1" "1" | C:\Program Files\DisplayFusion\DisplayFusionHookApp32.exe | — | DisplayFusion.exe | |||||||||||
User: admin Company: Binary Fortress Software Integrity Level: MEDIUM Description: DisplayFusion Hook App Exit code: 3221226540 Version: 11.1.0.1 Modules
| |||||||||||||||
| 1336 | "C:\WINDOWS\Temp\{7E5EA425-9826-44A7-9DAB-19A03CD1CBAF}\.be\windowsdesktop-runtime-8.0.18-win-x64.exe" -q -burn.elevated BurnPipe.{45F6F930-81A5-44D7-A093-41A19D6C3571} {2C949369-FB17-4E78-9D68-2DF33CA5E949} 6584 | C:\Windows\Temp\{7E5EA425-9826-44A7-9DAB-19A03CD1CBAF}\.be\windowsdesktop-runtime-8.0.18-win-x64.exe | dotnet80desktop64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Desktop Runtime - 8.0.18 (x64) Exit code: 0 Version: 8.0.18.35017 Modules
| |||||||||||||||
| 1352 | C:\Windows\syswow64\MsiExec.exe -Embedding DDD66A28F8BD7157D5156D806A648727 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4232,i,3720832337585821106,10554270236951888956,262144 --variations-seed-version --mojo-platform-channel-handle=4272 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1588 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3640,i,3720832337585821106,10554270236951888956,262144 --variations-seed-version --mojo-platform-channel-handle=3636 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\AppData\Local\Temp\is-BAJSG.tmp\DisplayFusionSetup-11.1.1.tmp" /SL5="$80316,110947990,844800,C:\Users\admin\Downloads\DisplayFusionSetup-11.1.1.exe" /SPAWNWND=$802DE /NOTIFYWND=$B033E | C:\Users\admin\AppData\Local\Temp\is-BAJSG.tmp\DisplayFusionSetup-11.1.1.tmp | DisplayFusionSetup-11.1.1.exe | ||||||||||||
User: admin Company: Binary Fortress Software Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\DisplayFusion\DisplayFusionHookApp64.exe" "8748" "852798" "67040" "0" "65668" "65760" "019851e6-958a-7572-860e-c6f2d474bb01" "C:\Program Files\DisplayFusion\Hooks\AppHook64_712F0719-0FF2-47CC-9AE4-AE38FF5D5E63.dll" "DisplayFusion" "Software\Binary Fortress Software\DisplayFusion" "Software\Binary Fortress Software\DisplayFusion\Session\1" "1" "100" "1" "1" | C:\Program Files\DisplayFusion\DisplayFusionHookApp64.exe | — | DisplayFusion.exe | |||||||||||
User: admin Company: Binary Fortress Software Integrity Level: MEDIUM Description: DisplayFusion Hook App Exit code: 3221226540 Version: 11.1.0.1 Modules
| |||||||||||||||
| 1816 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=8608,i,3720832337585821106,10554270236951888956,262144 --variations-seed-version --mojo-platform-channel-handle=8664 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
44 106
Read events
40 095
Write events
3 084
Delete events
927
Modification events
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A494F72696992F00 | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393914 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AC4FBD4A-AF86-4B21-AE89-BA5F6302AB7D} | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393914 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4E56CFD4-05E9-4E5E-B3B6-FF22839B71F3} | |||
| (PID) Process: | (2384) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393914 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C7FE550C-F47C-4C04-A9F2-60B394080EEA} | |||
Executable files
952
Suspicious files
1 010
Text files
1 655
Unknown types
120
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d56c.TMP | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d56c.TMP | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d57b.TMP | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d59a.TMP | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d5aa.TMP | — | |
MD5:— | SHA256:— | |||
| 2384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
521
DNS requests
570
Threats
52
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2348 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:BjyxjdgdTdidQOyrDMeuAm3UEWARe9sUAgUoRVW4ipc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5628 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5628 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2384 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
2384 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
2384 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAyqQ4oZzefEuJPFO7WN6Z8%3D | unknown | — | — | whitelisted |
1068 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753751243&P2=404&P3=2&P4=JPM%2bm9OS0NDZA6ASOnGdK2LX69nrppI%2bzvfVFZWMLubcdz3GuKFZBezlHY2okN0%2b1xKjiGd6JjjM2iXb4GnRsQ%3d%3d | unknown | — | — | whitelisted |
6176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5476 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2348 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2348 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2348 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2348 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
2348 | msedge.exe | 88.223.84.178:443 | cracksurl.com | UAB INIT | LT | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
cracksurl.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |
stats.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
2348 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2348 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2348 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ghabovethec .info) |
2348 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Malicious CrossDomain (nriceukwater .org) |
2348 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ukankingwithea .com) |
2348 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
netcorecheck64.exe | A fatal error occurred. The required library hostfxr.dll could not be found.
If this is a self-contained application, that library should exist in [].
If this is a framework-dependent application, install the runtime in the global location [C:\Program Files\dotnet] or use the DOTNET_ROOT environment variable to specify the runtime location or register the runtime location in [HKLM\SOFTWARE\dotnet\Setup\InstalledVersions\x64\InstallLocation]. |
netcorecheck64.exe | - https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win10-x64&apphost_version=5.0.0-preview.6.20264.1 |
netcorecheck64.exe | The .NET runtime can be found at: |
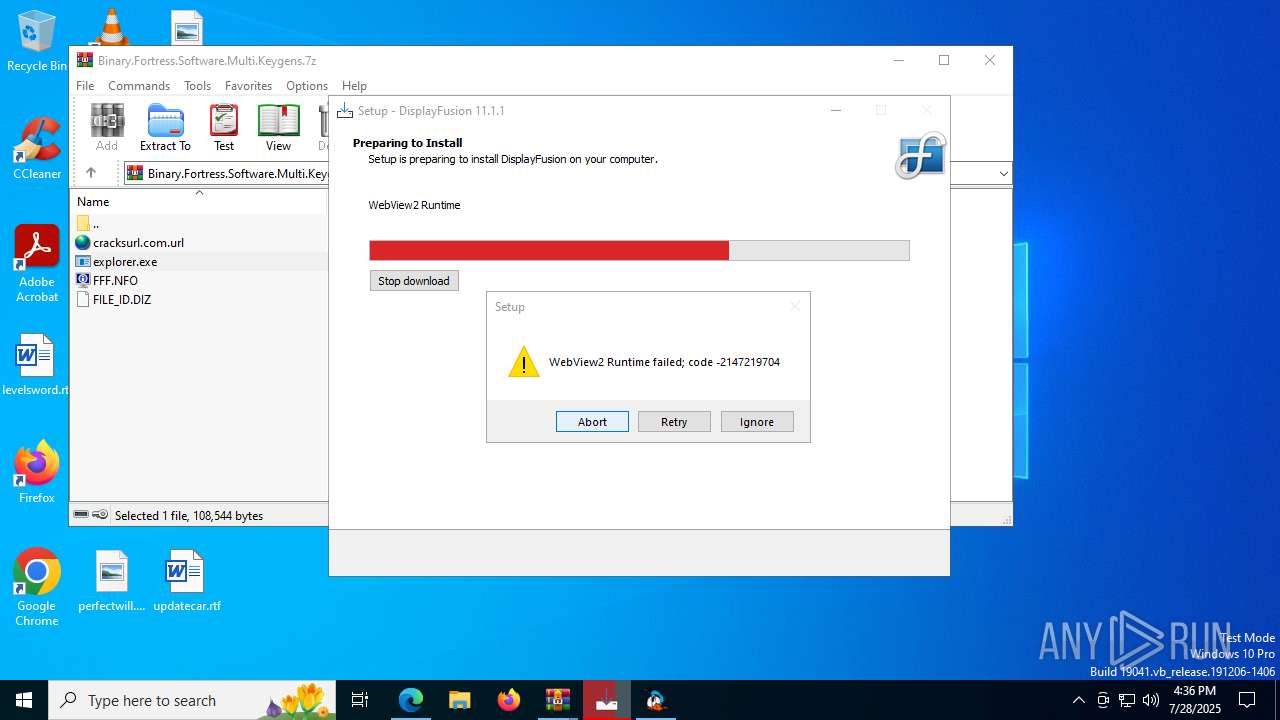
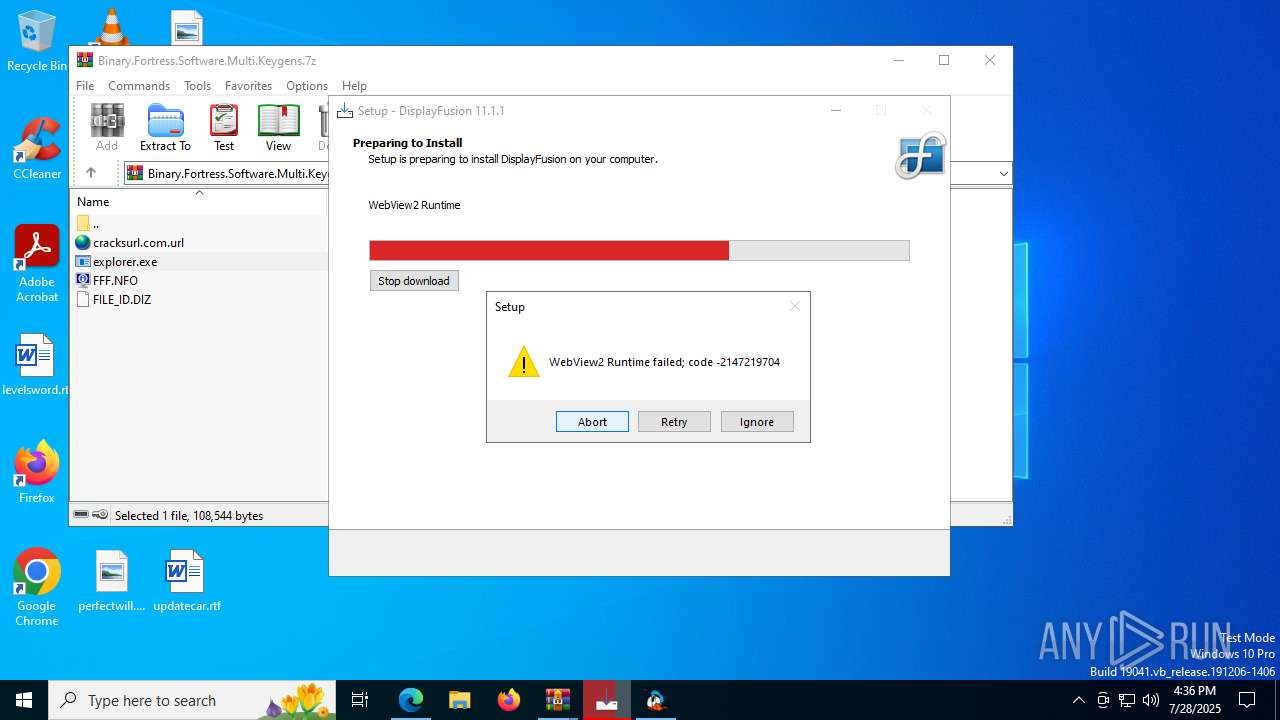
DisplayFusion.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
DisplayFusion.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
DisplayFusionHookApp64.exe | LogFile: |
DisplayFusionHookApp32.exe | LogFile: |
DisplayFusionHookApp64.exe | LogLevel: 0 |
DisplayFusionHookApp32.exe | LogLevel: 0 |
DisplayFusionHookApp64.exe | LogLevel: 0 |