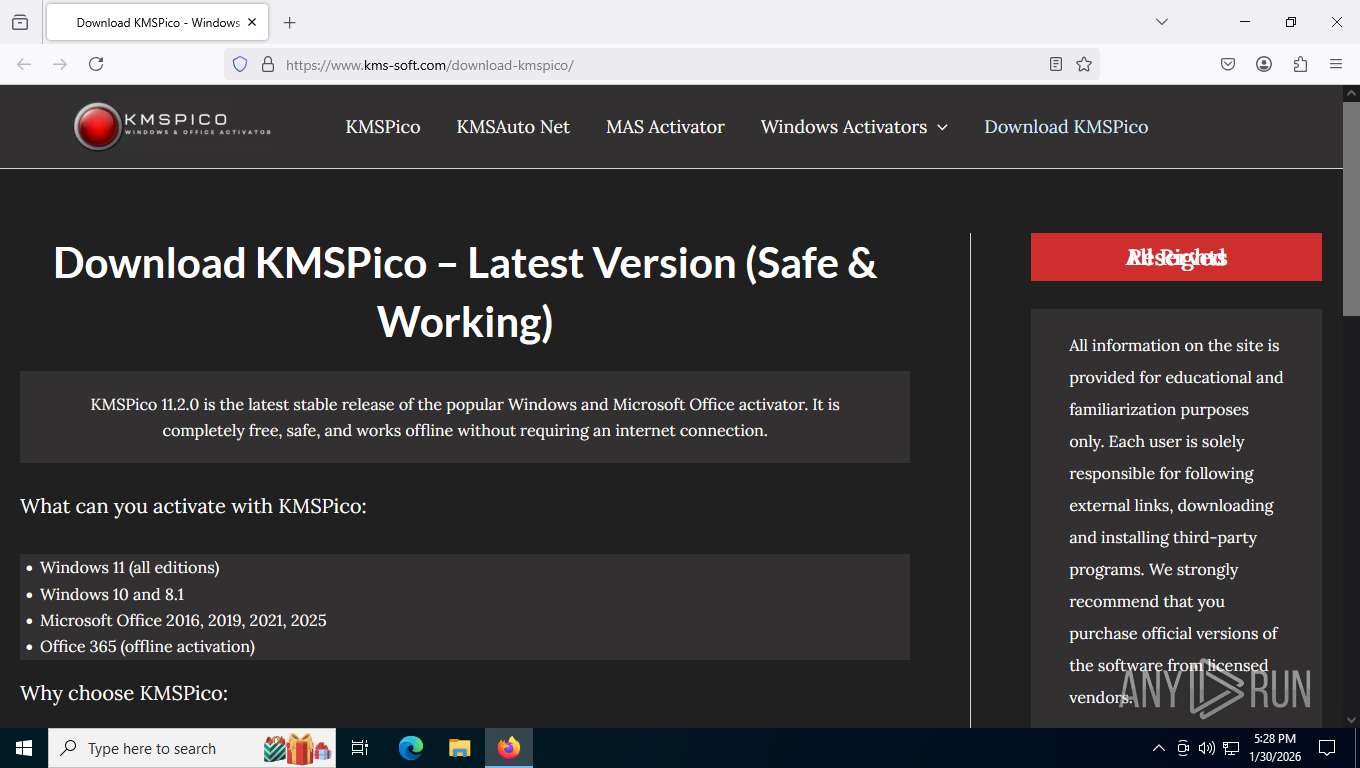
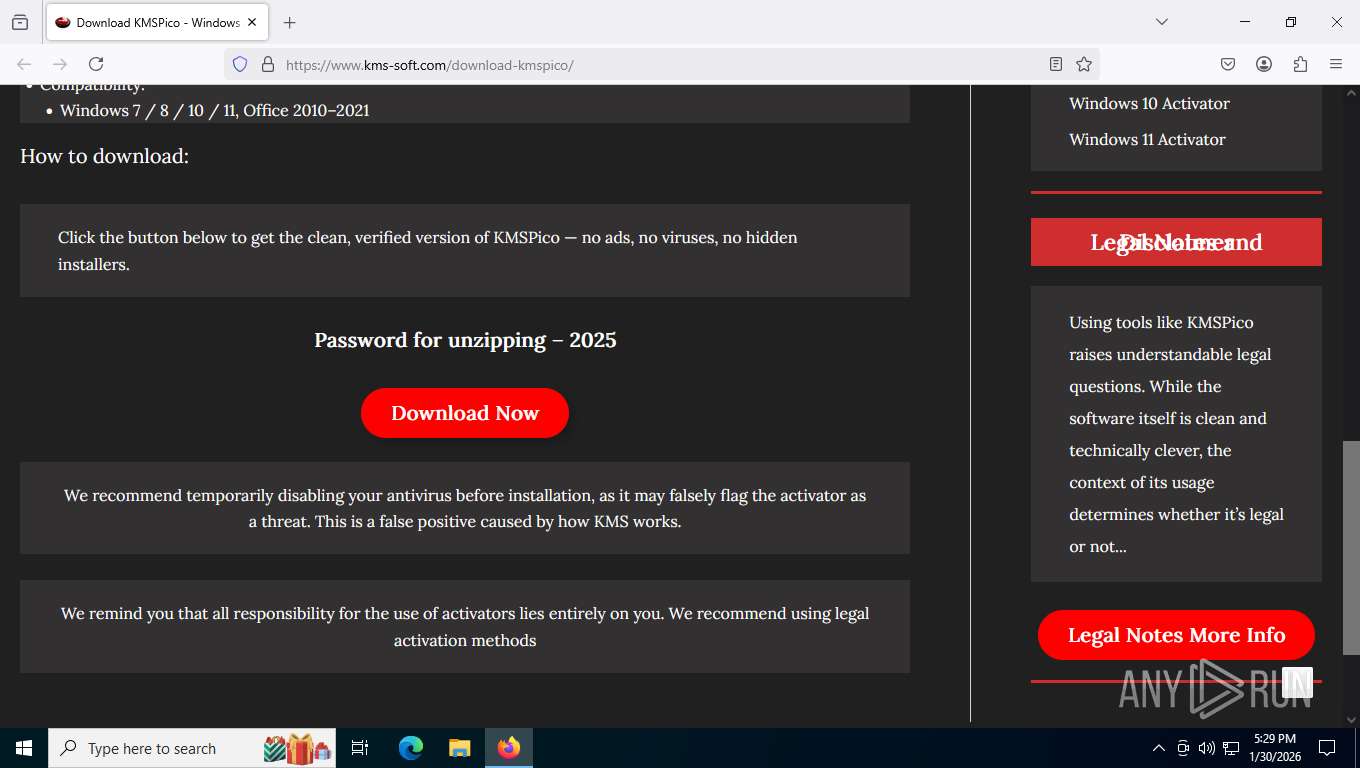
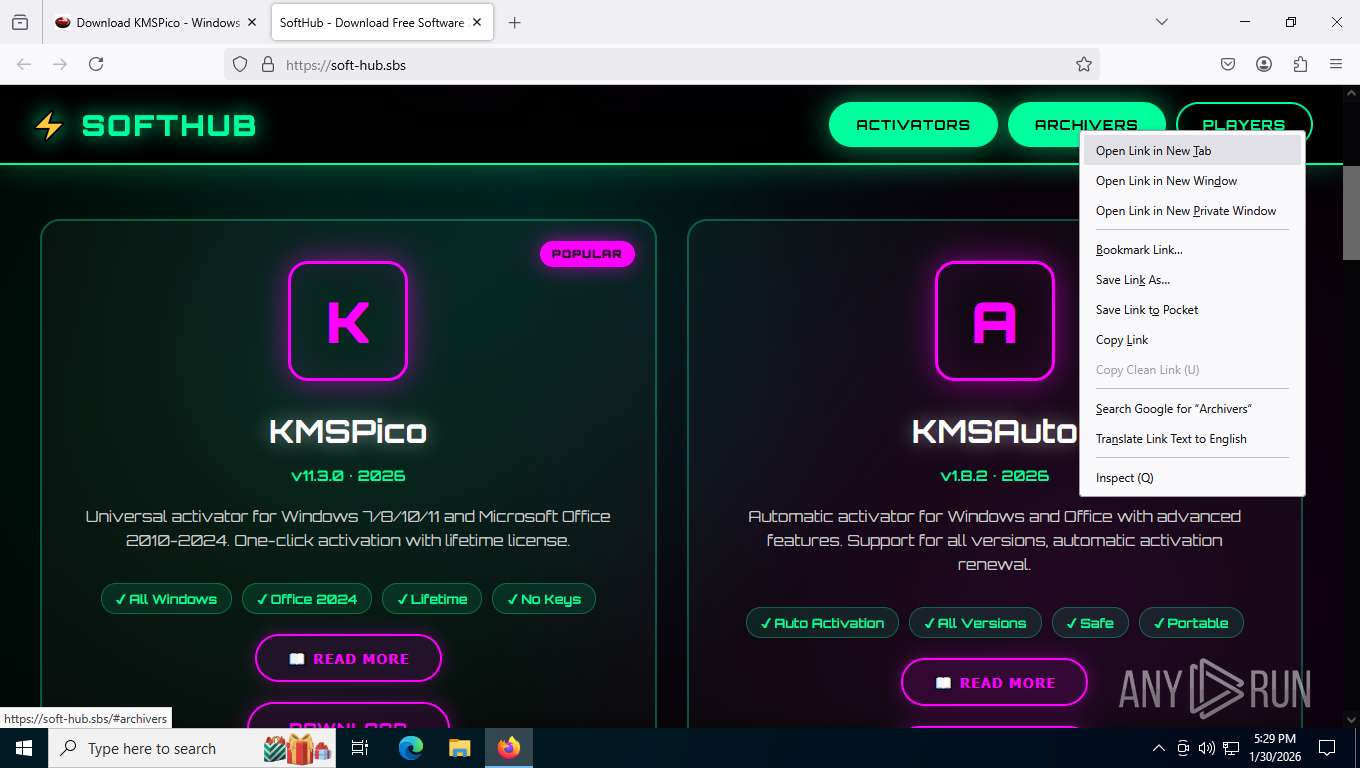
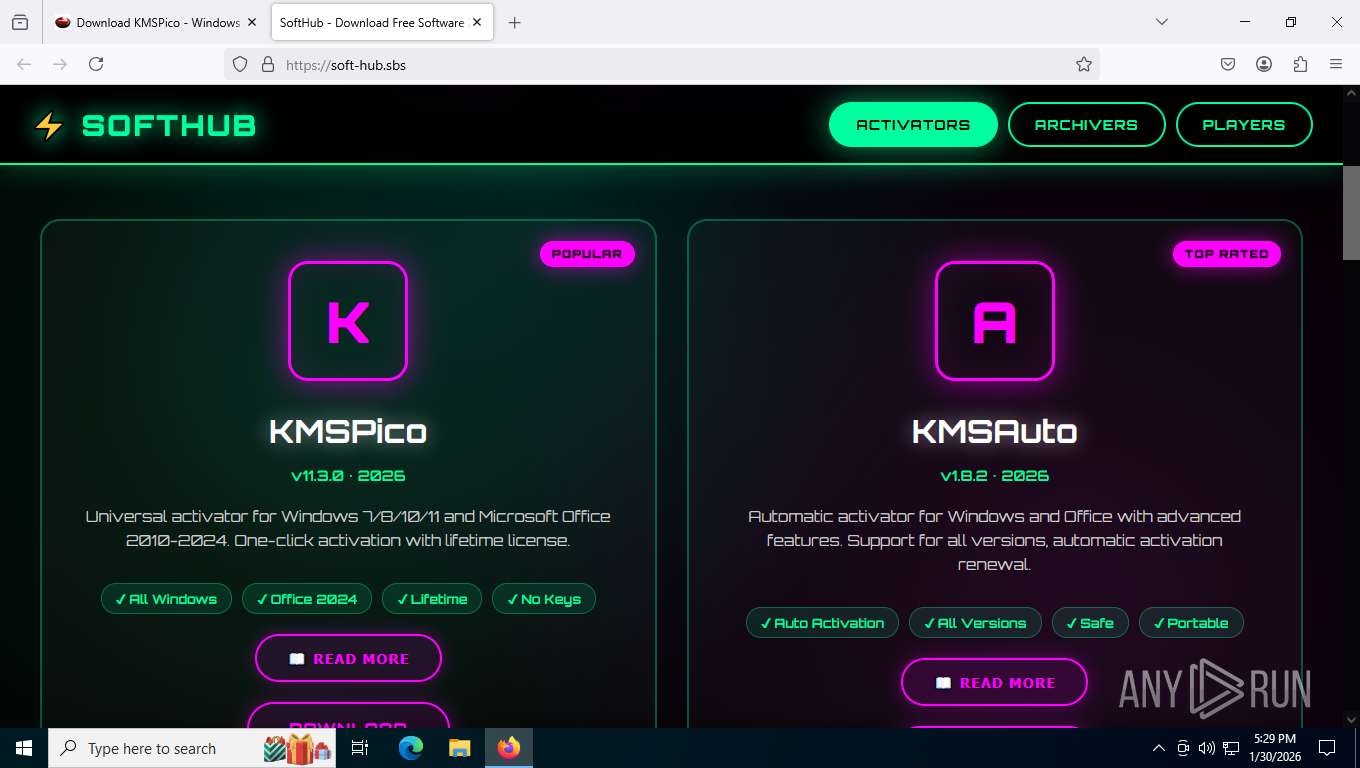
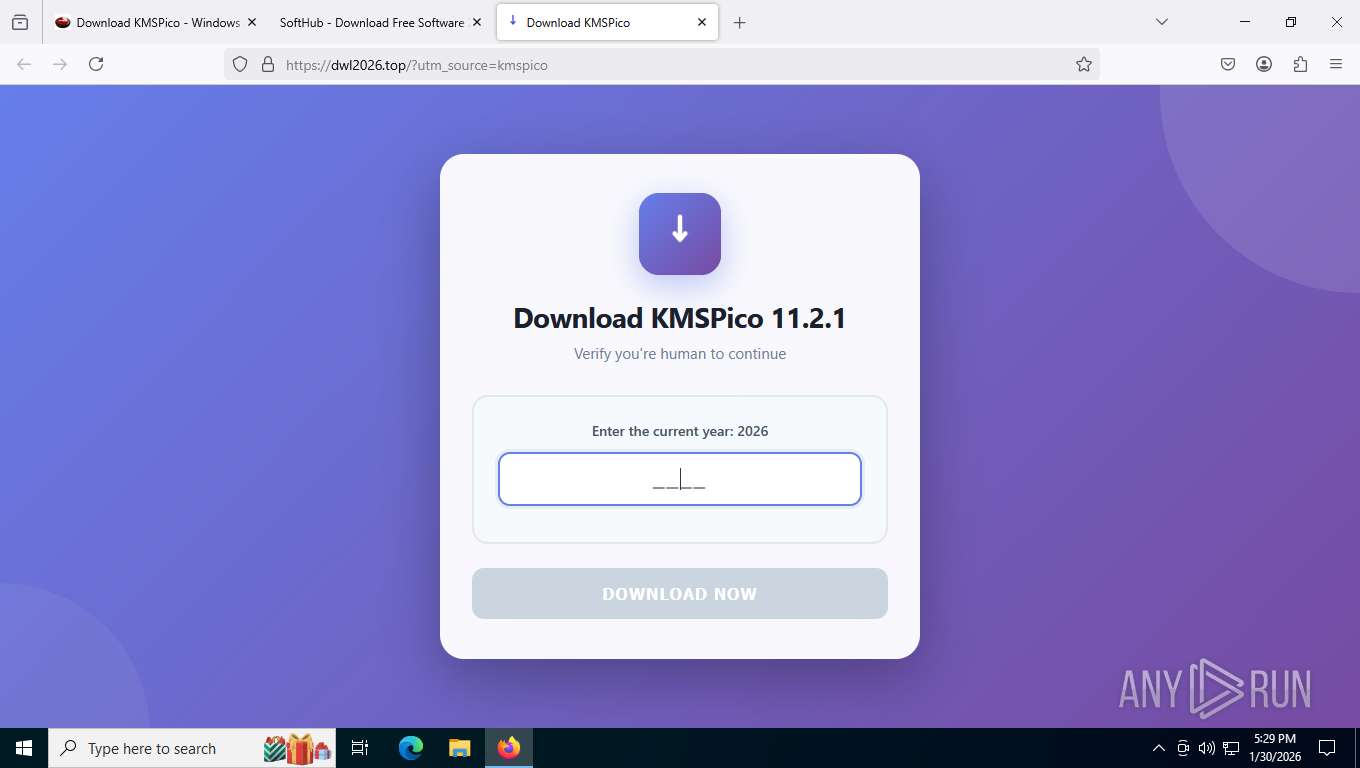
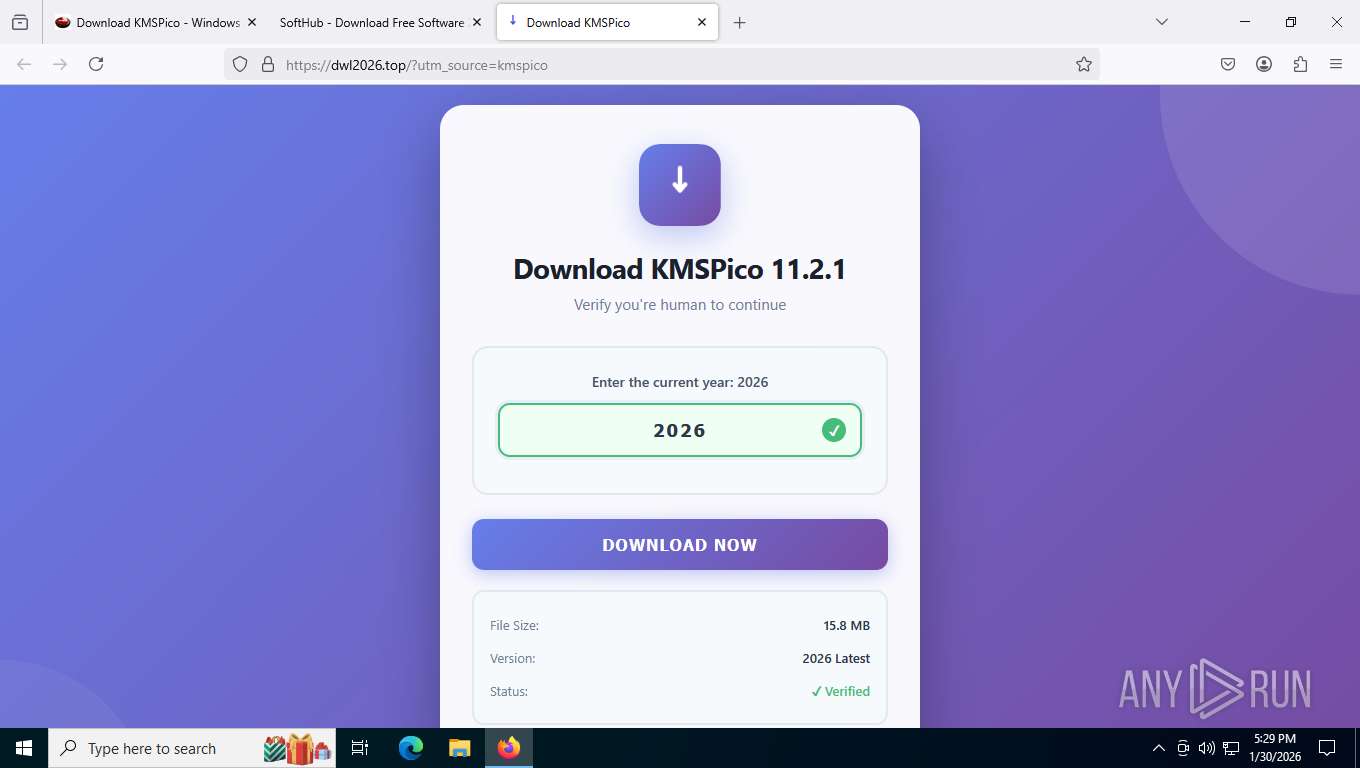
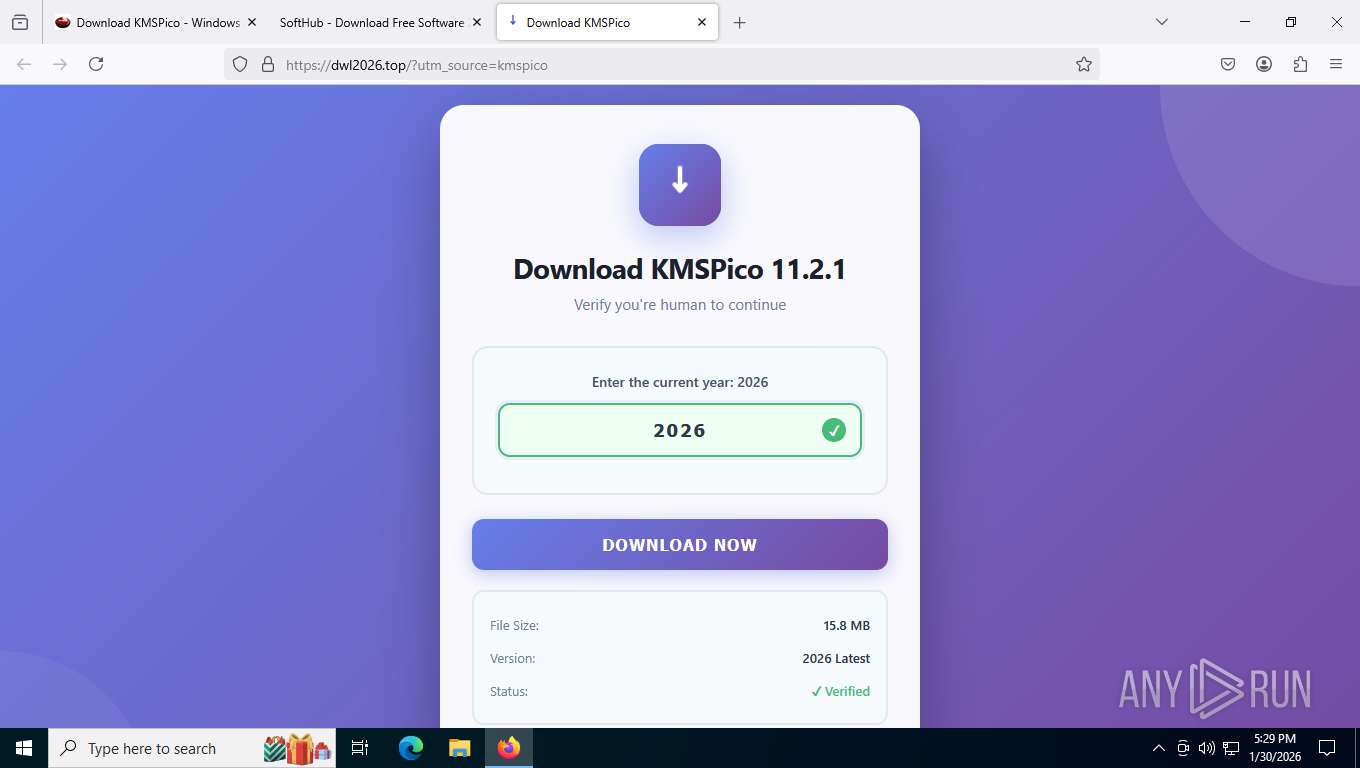
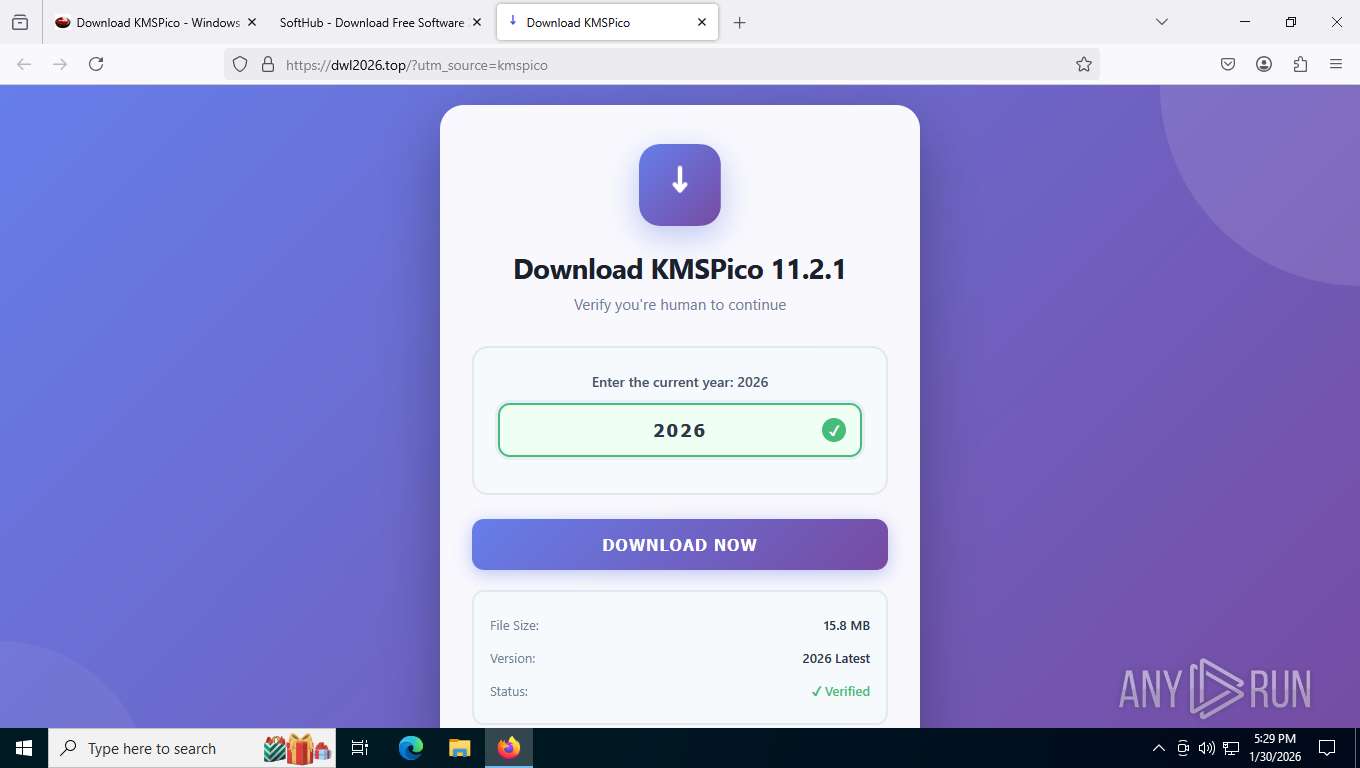
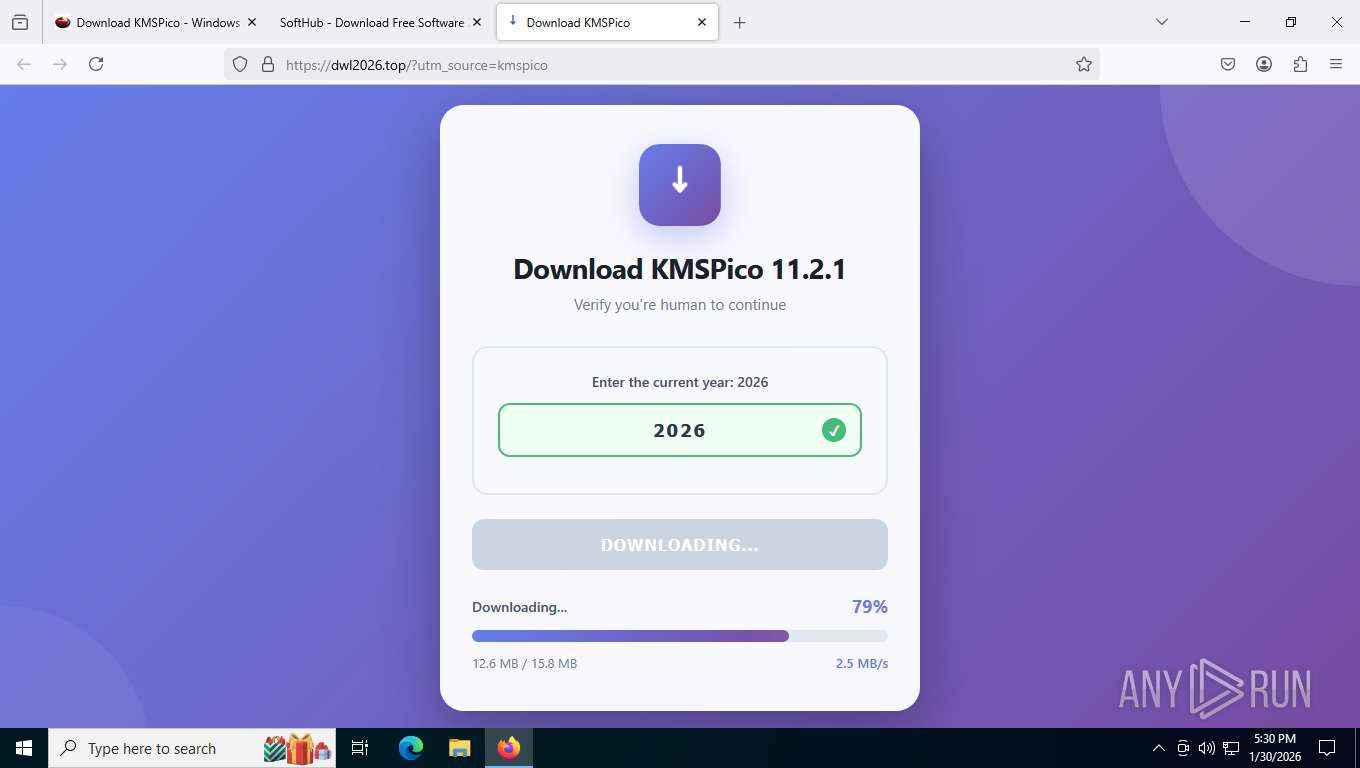
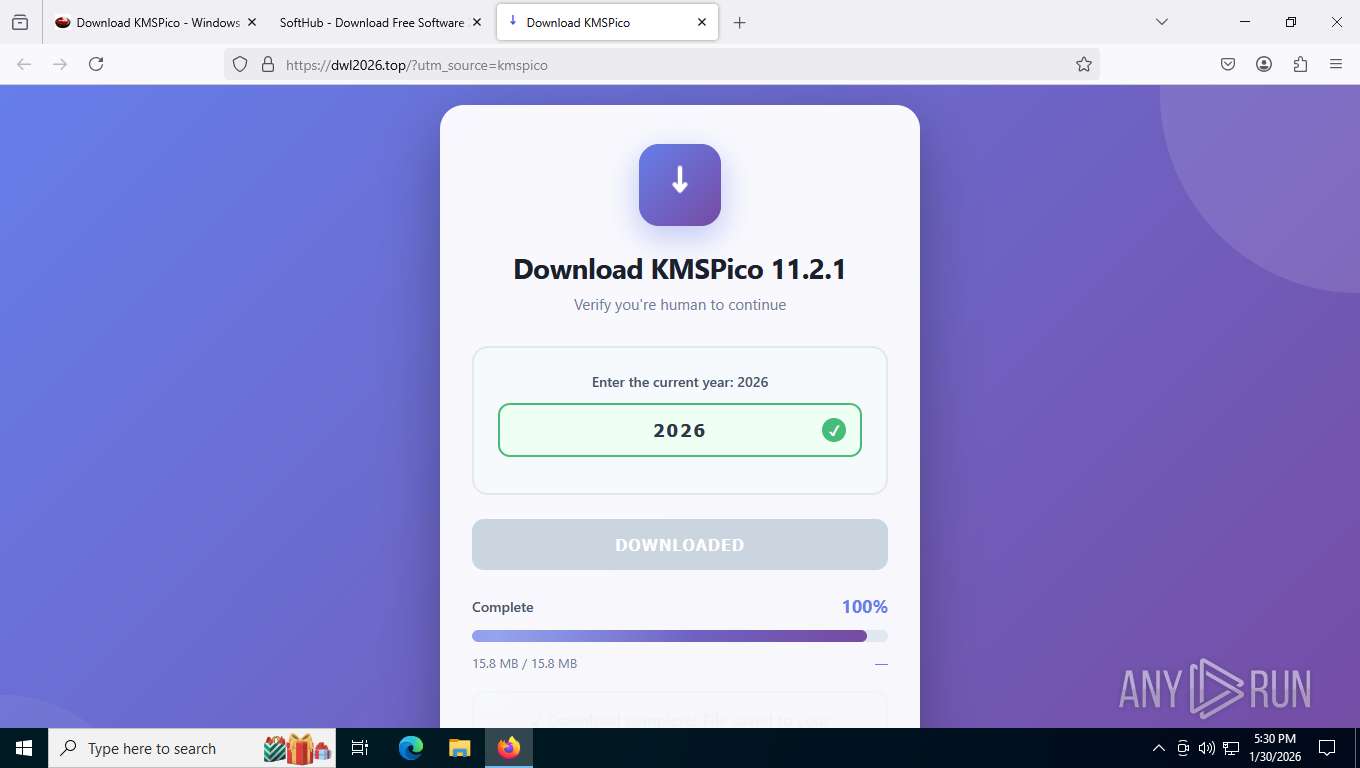
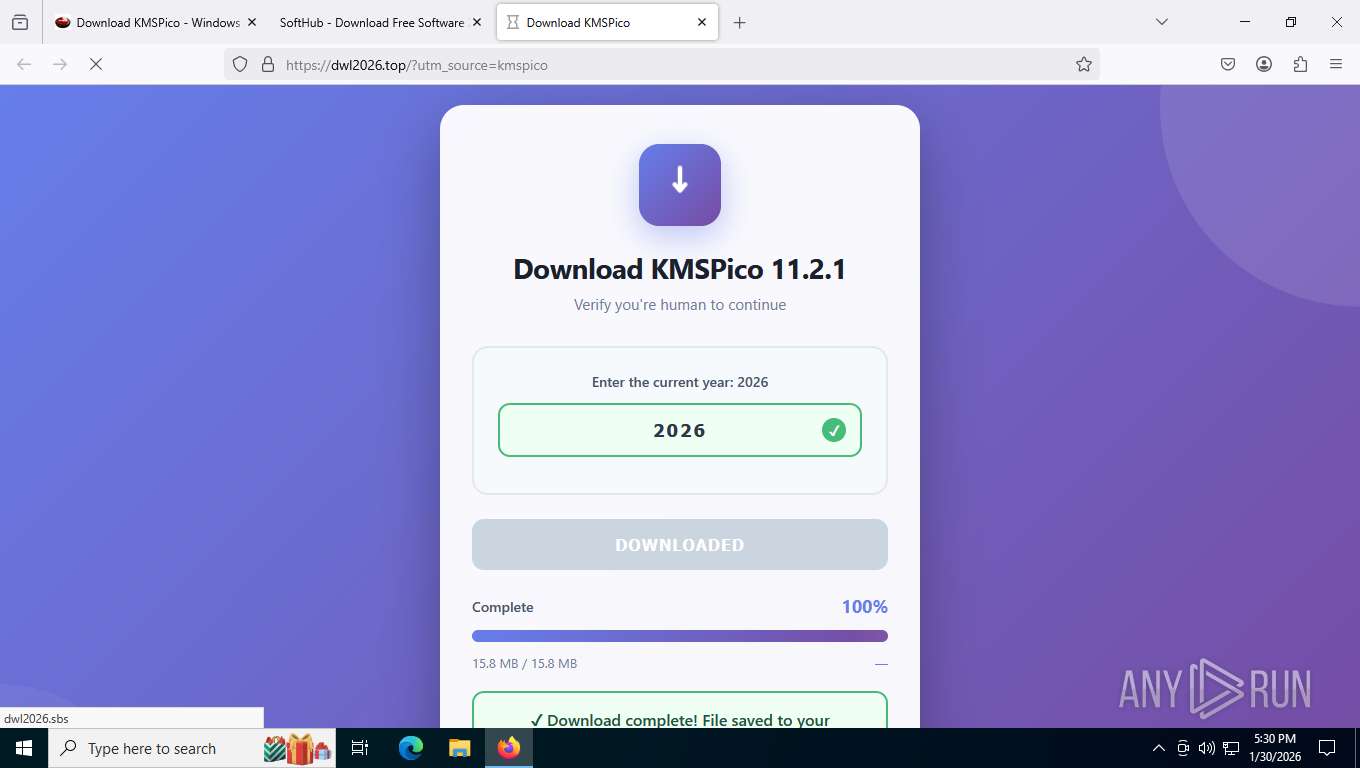
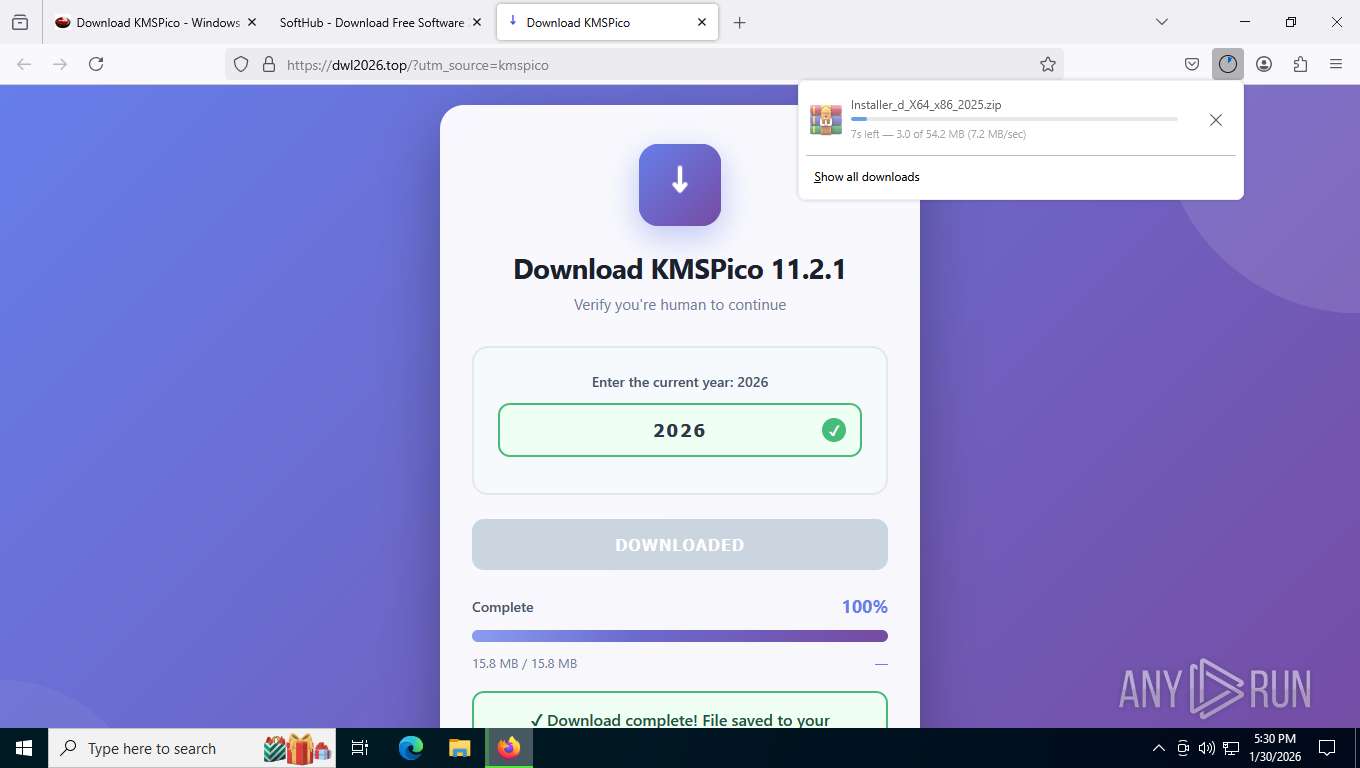
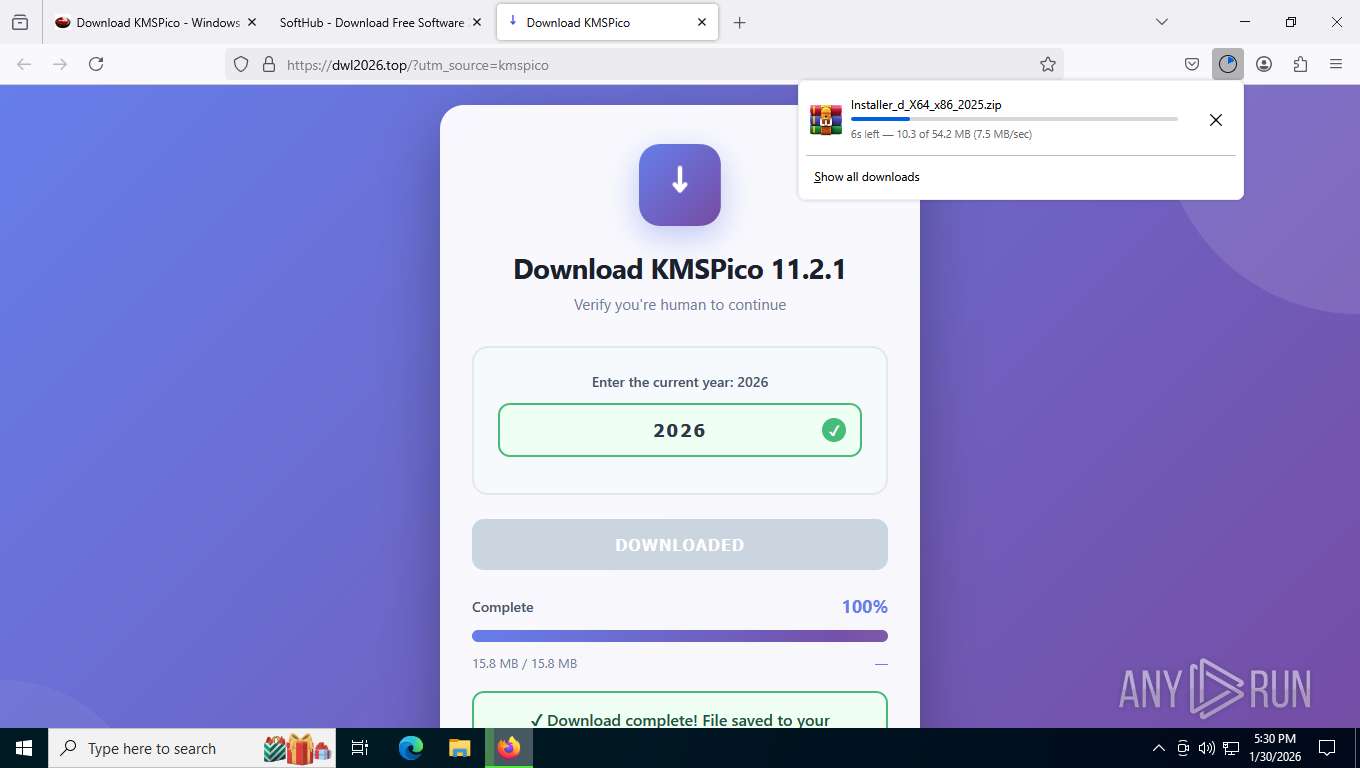
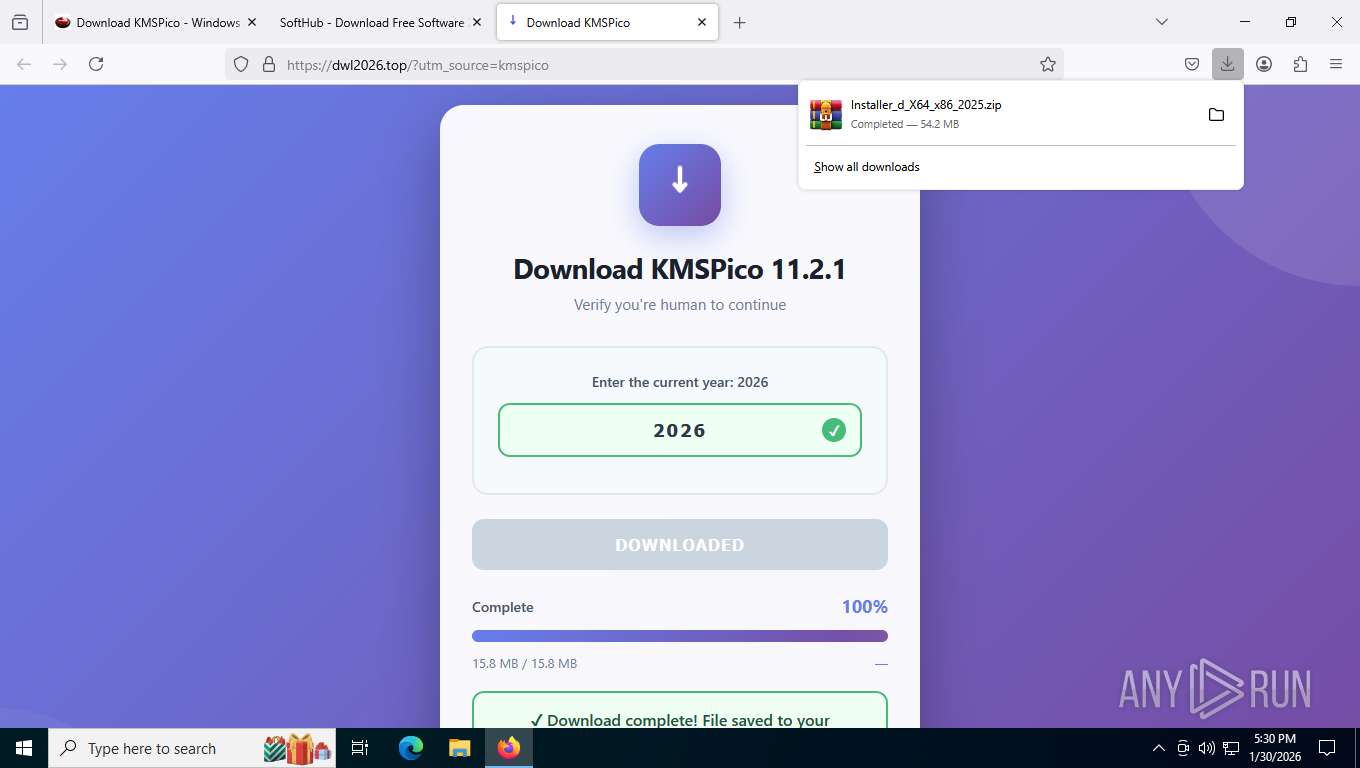
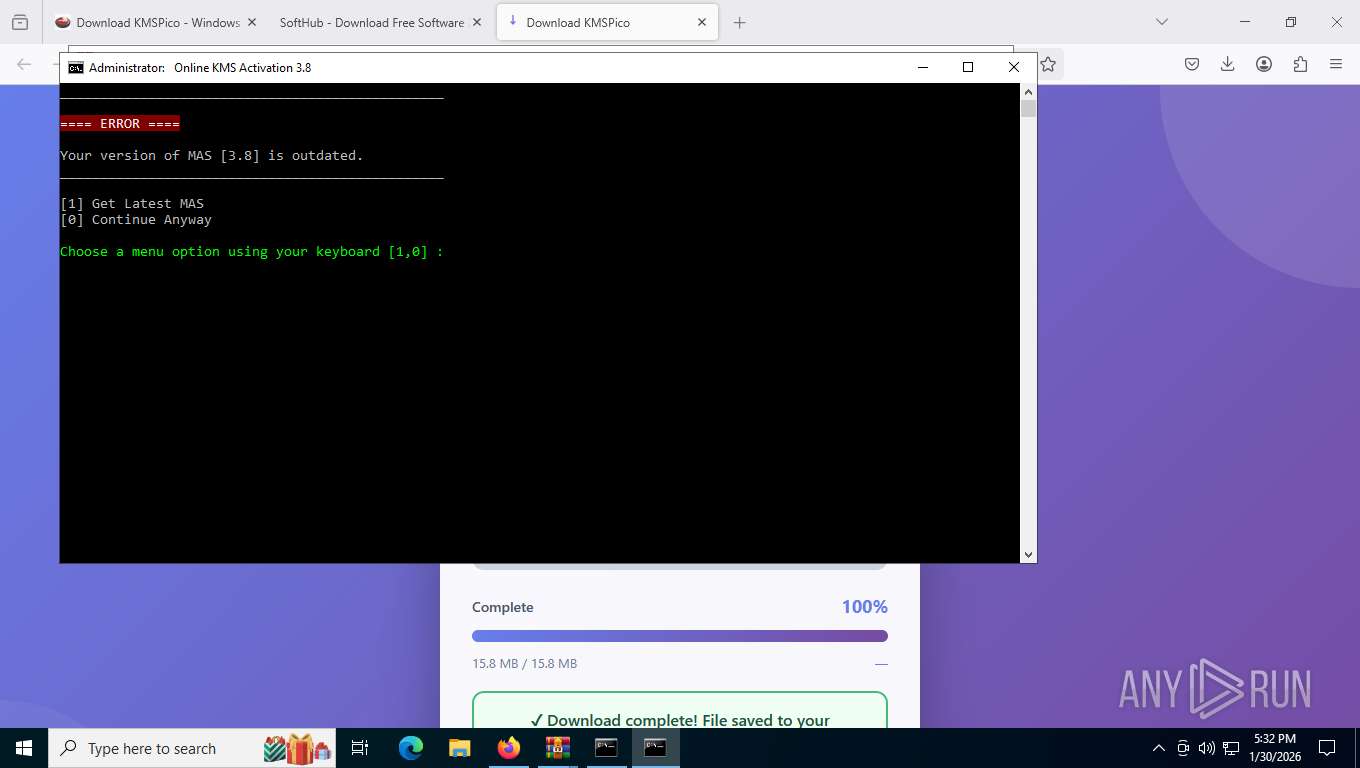
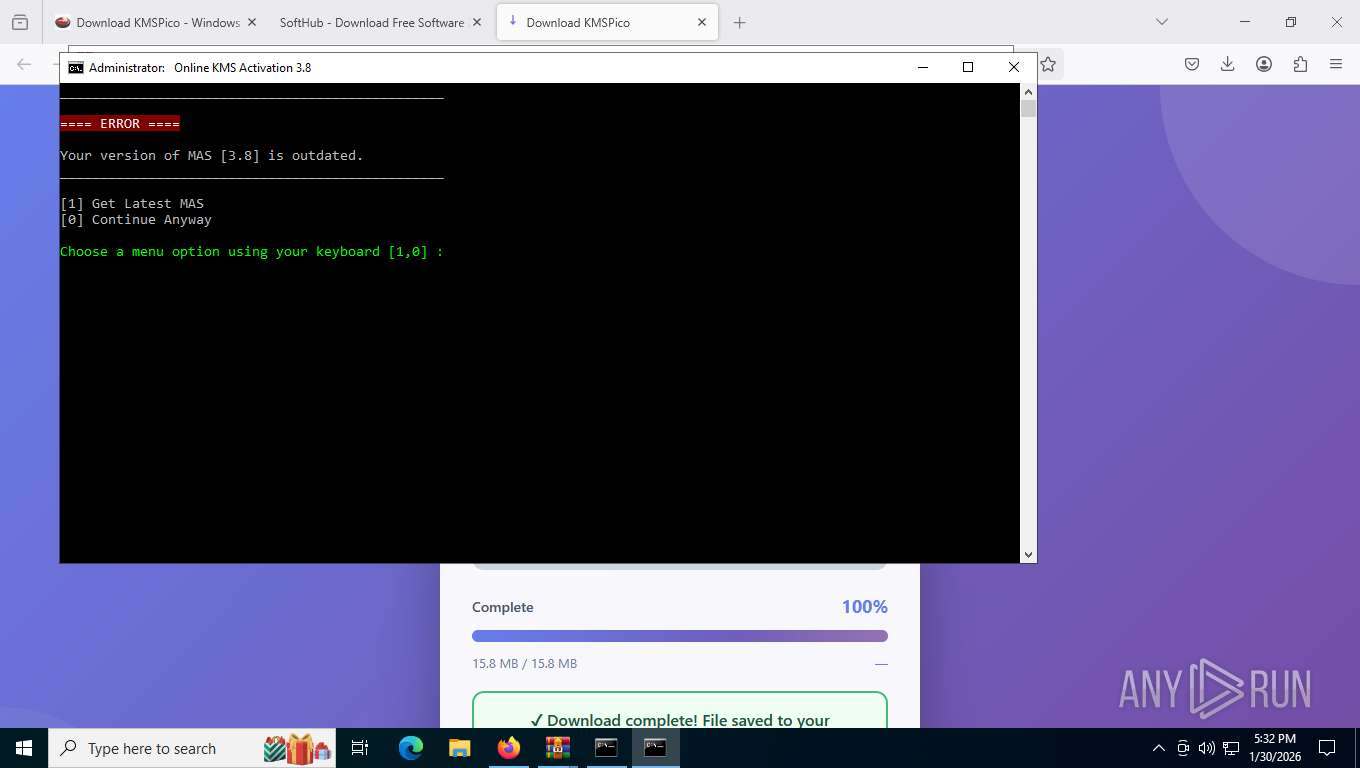
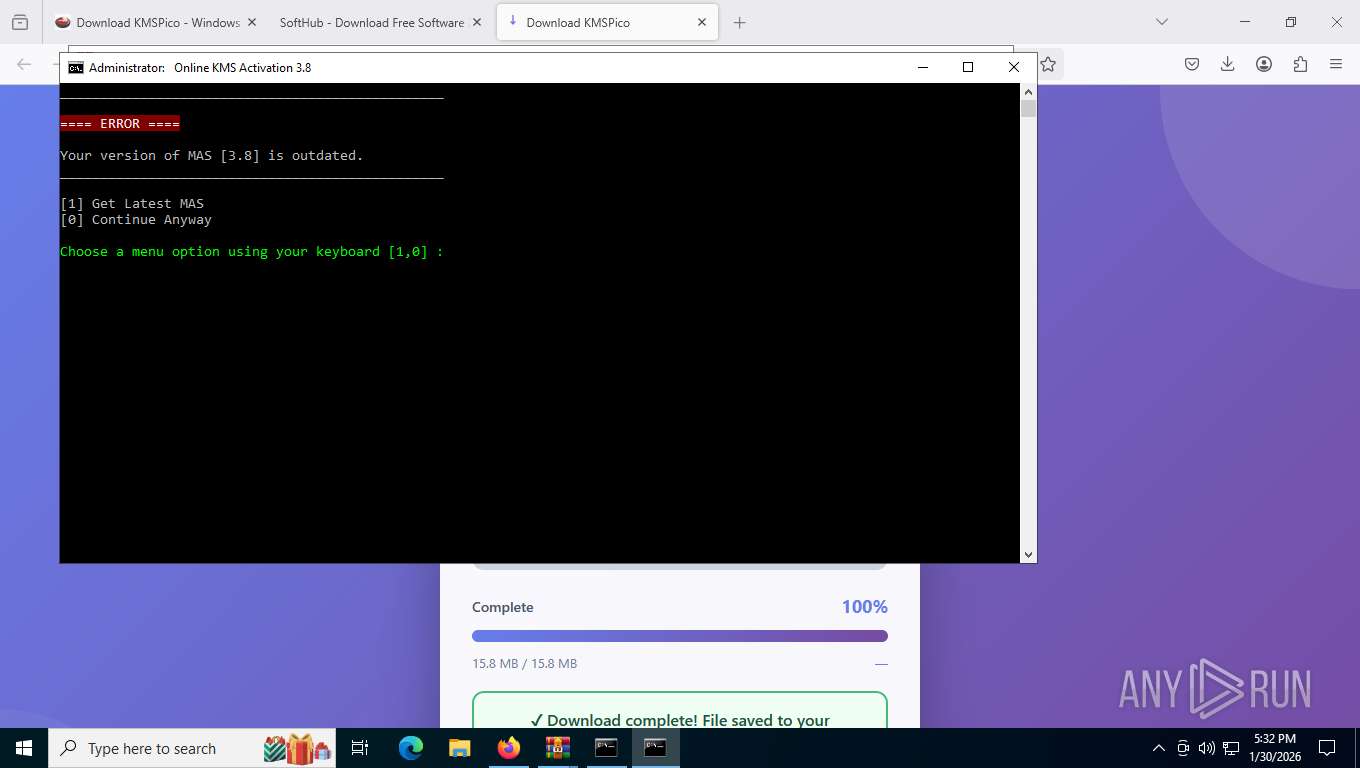
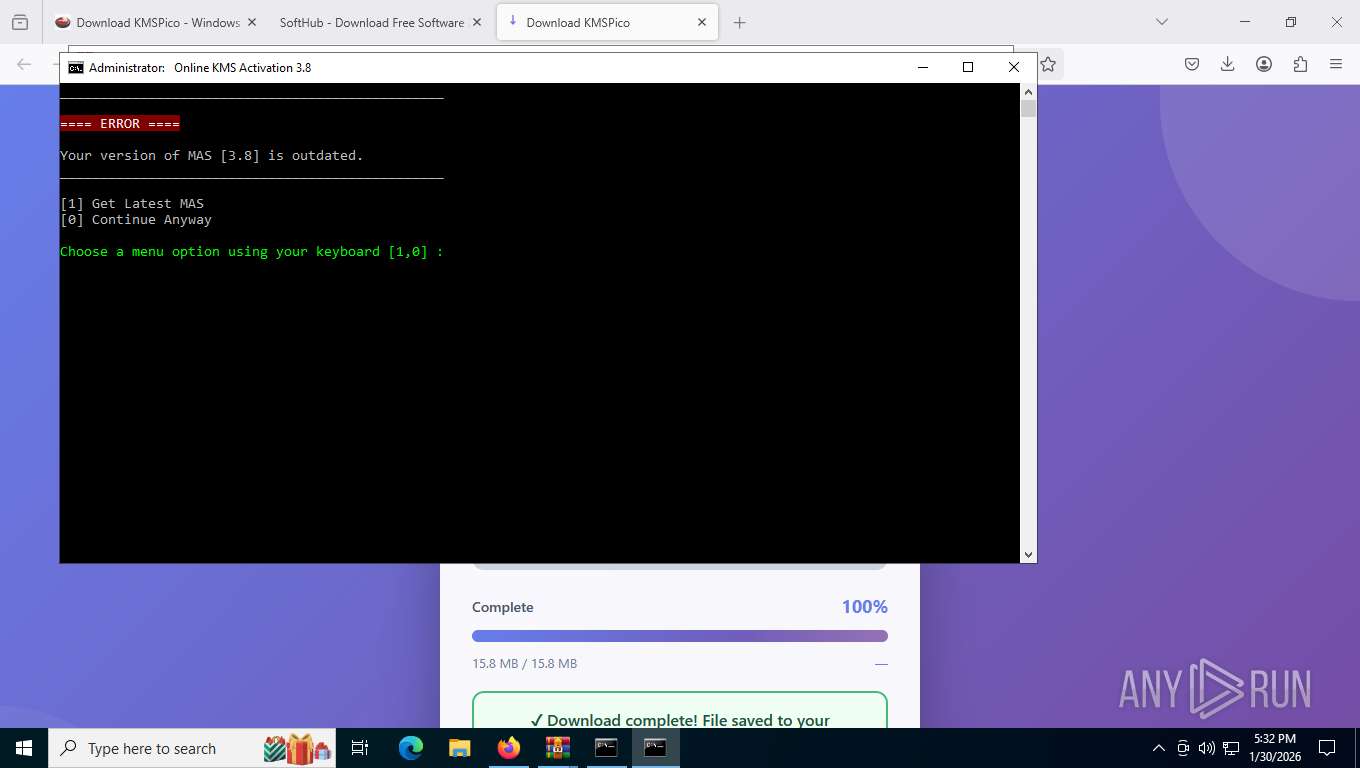
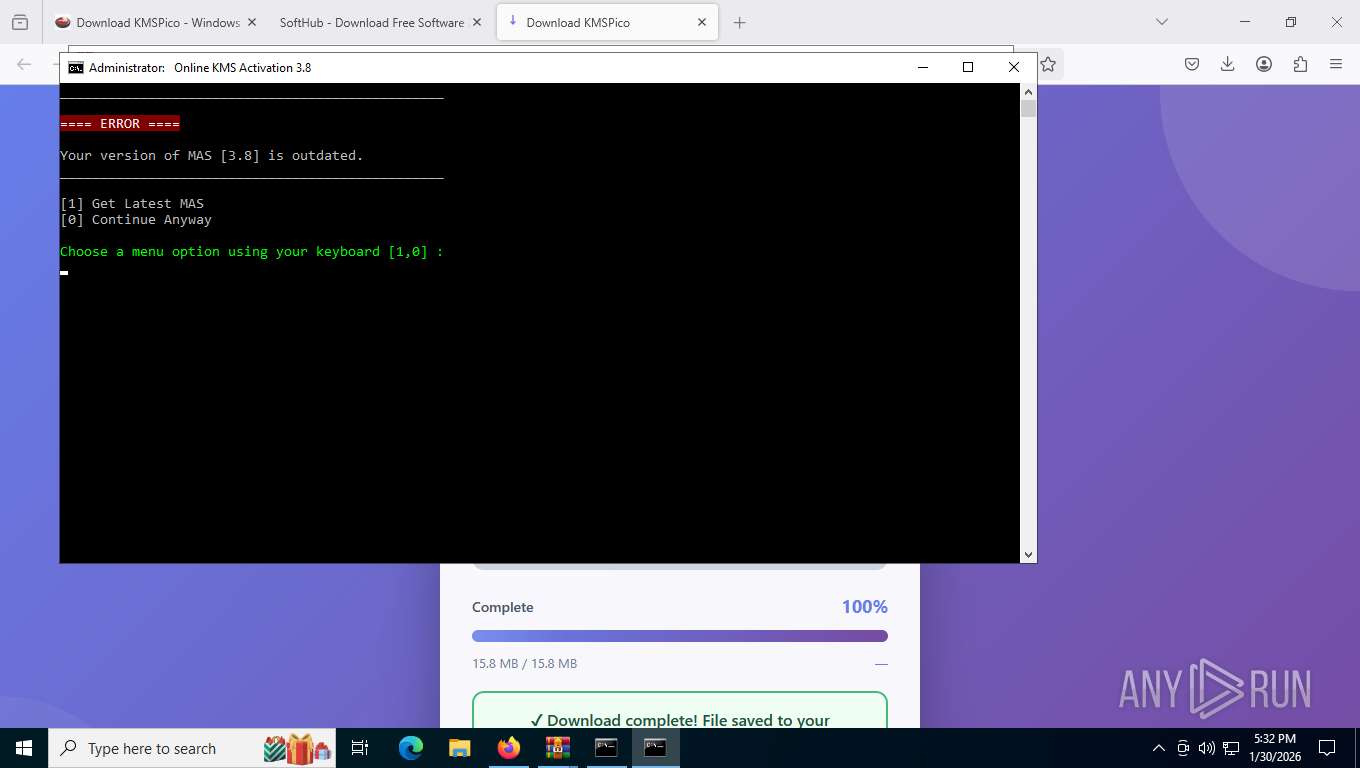
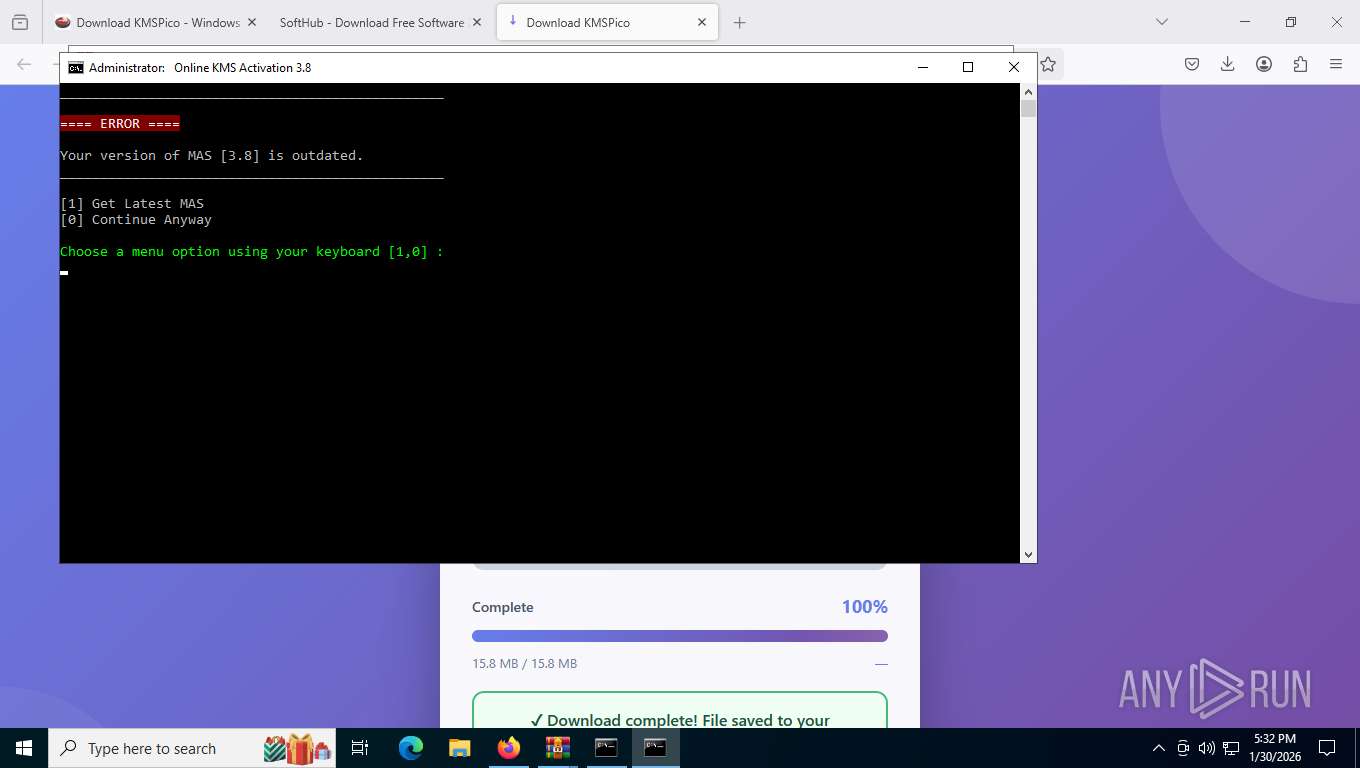
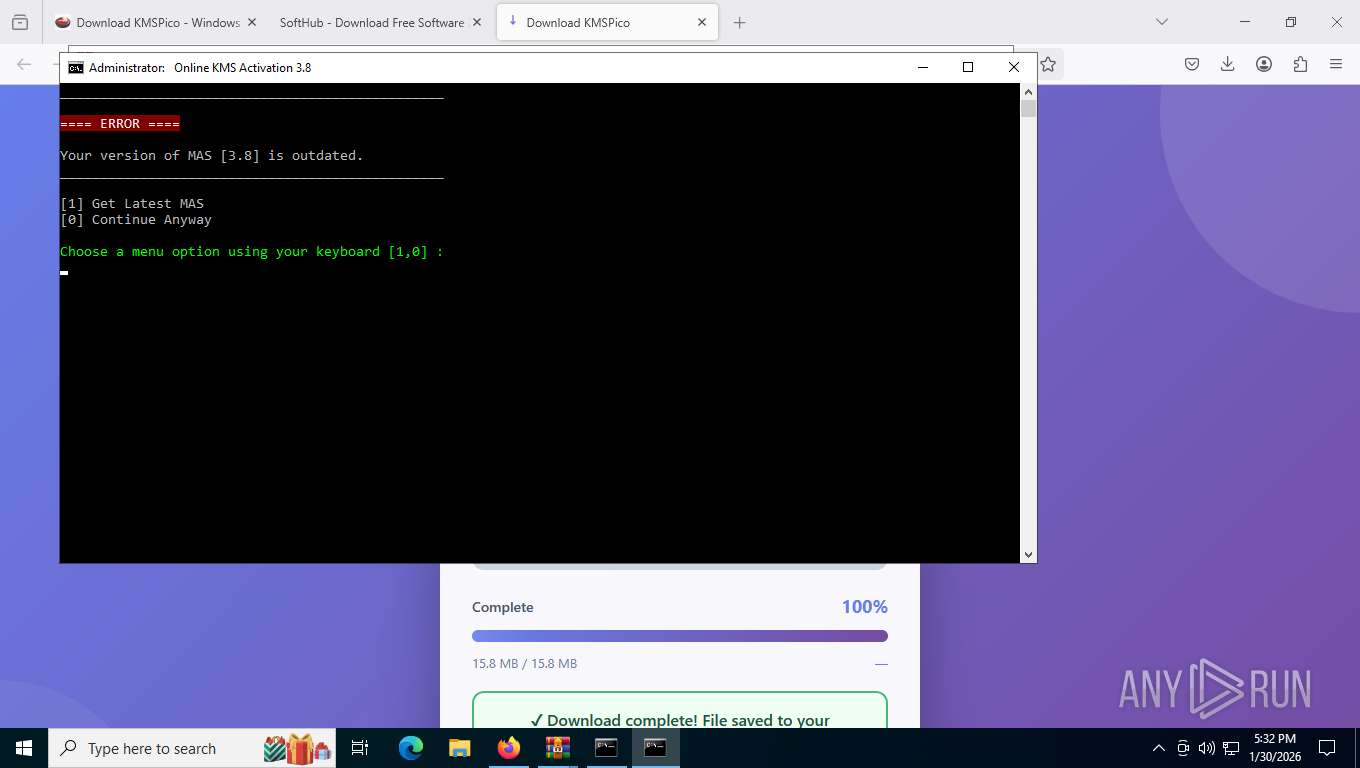
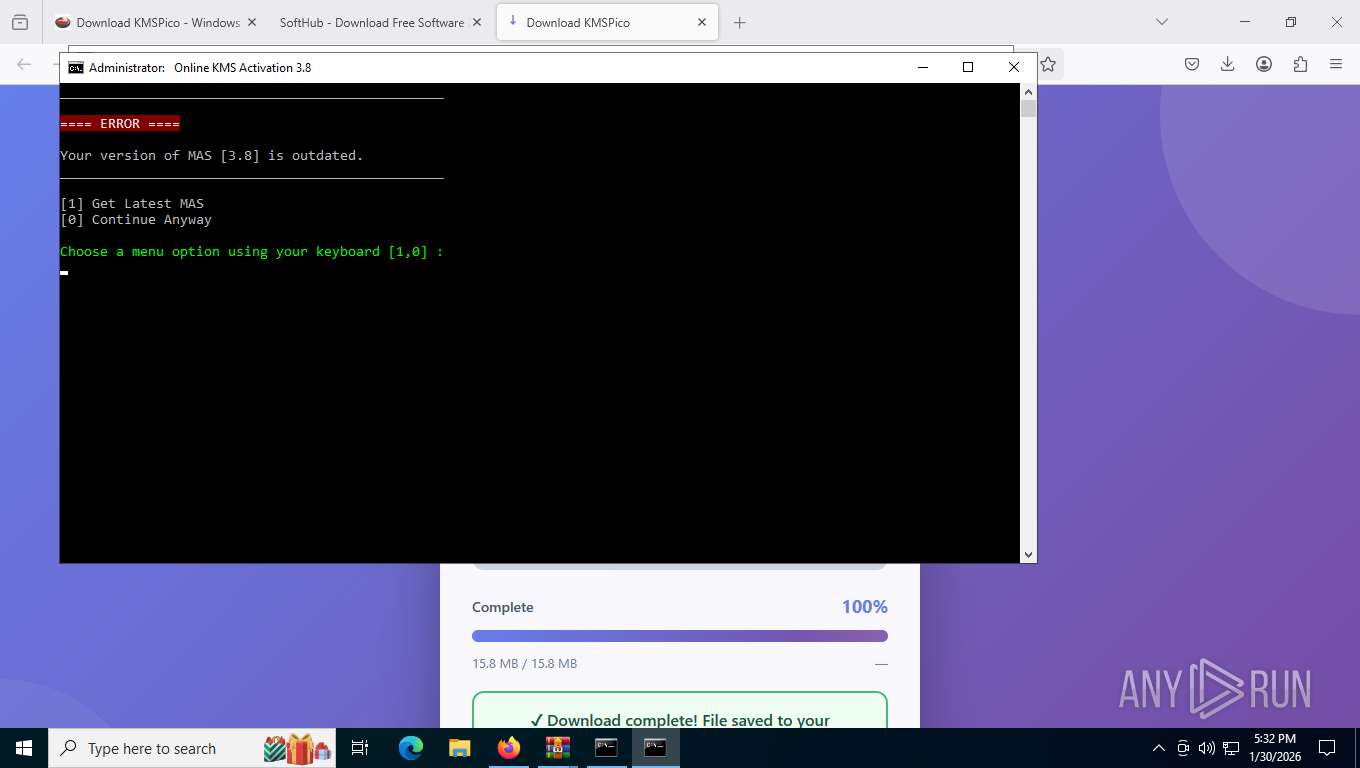
| URL: | https://www.kms-soft.com/download-kmspico/ |
| Full analysis: | https://app.any.run/tasks/b3841203-0eb9-45e2-b8f7-4d6304ec179e |
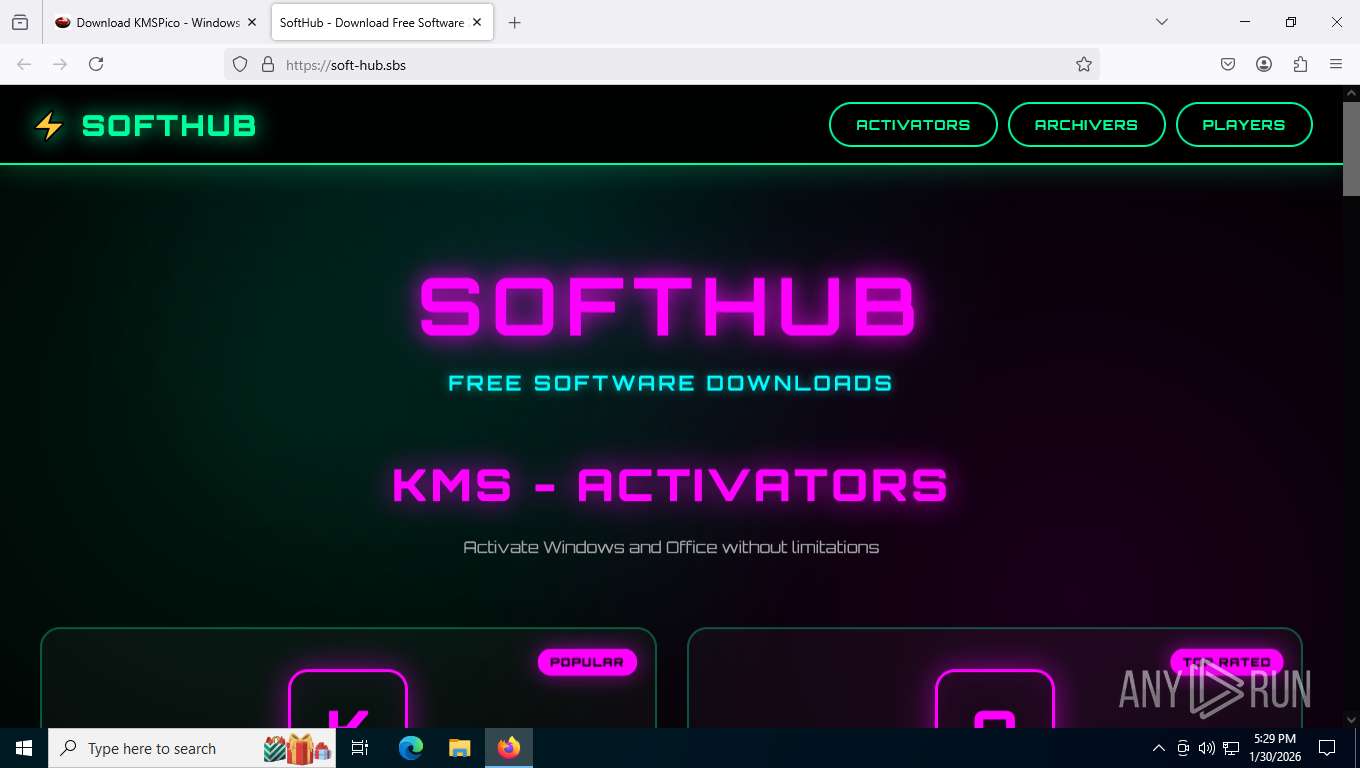
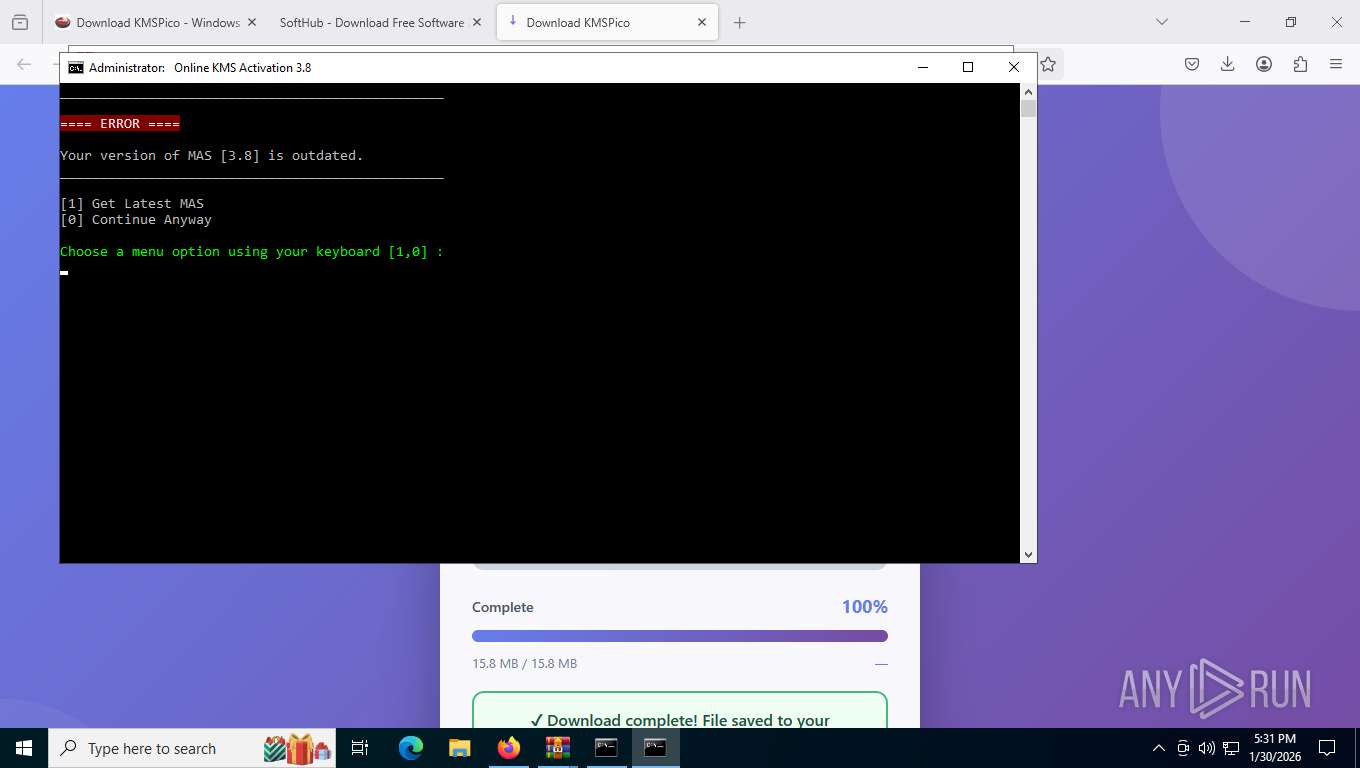
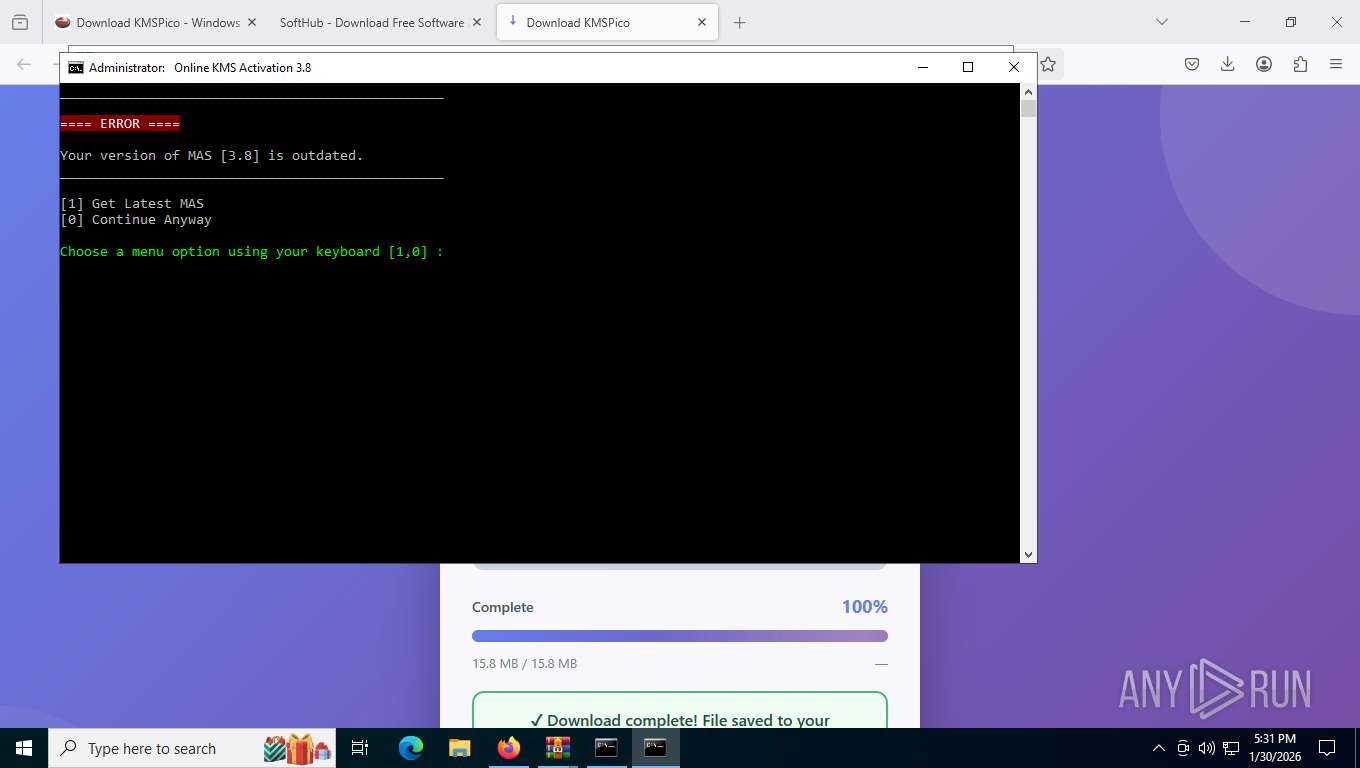
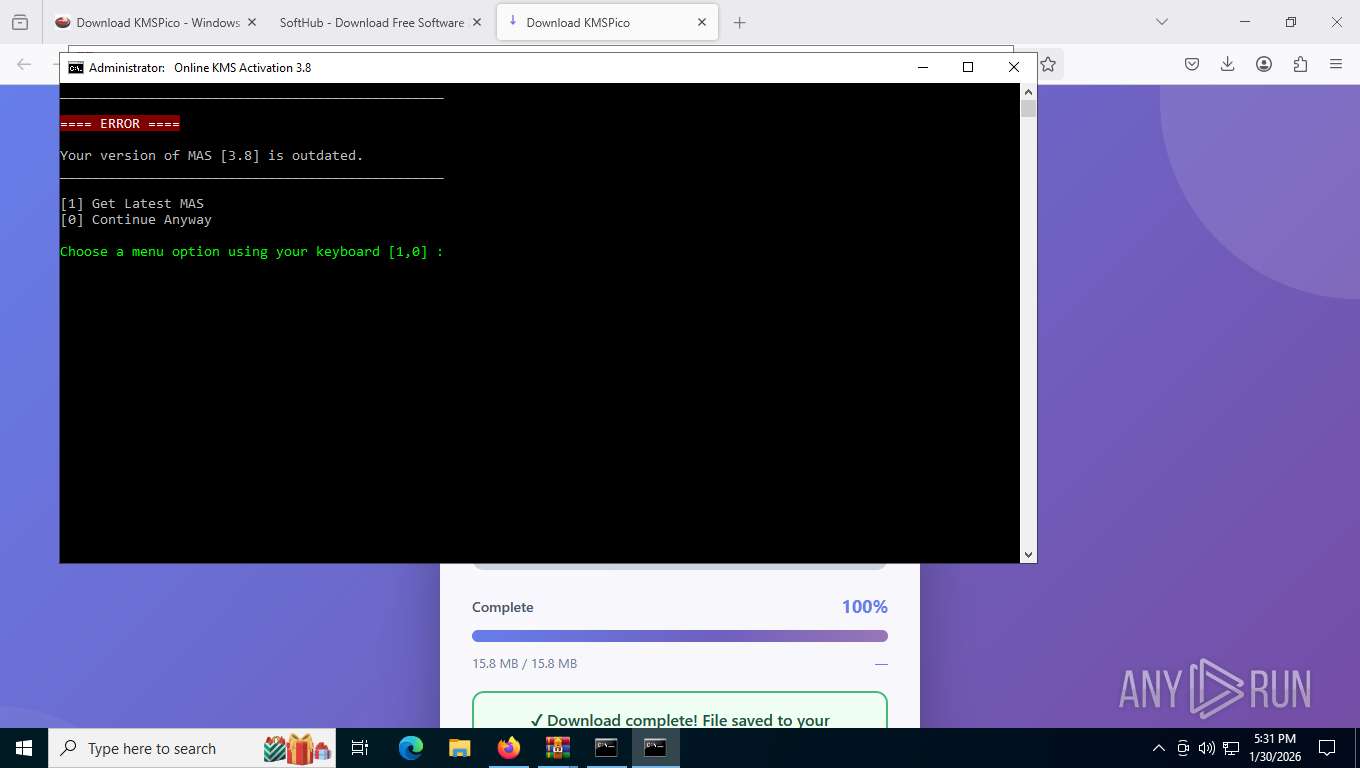
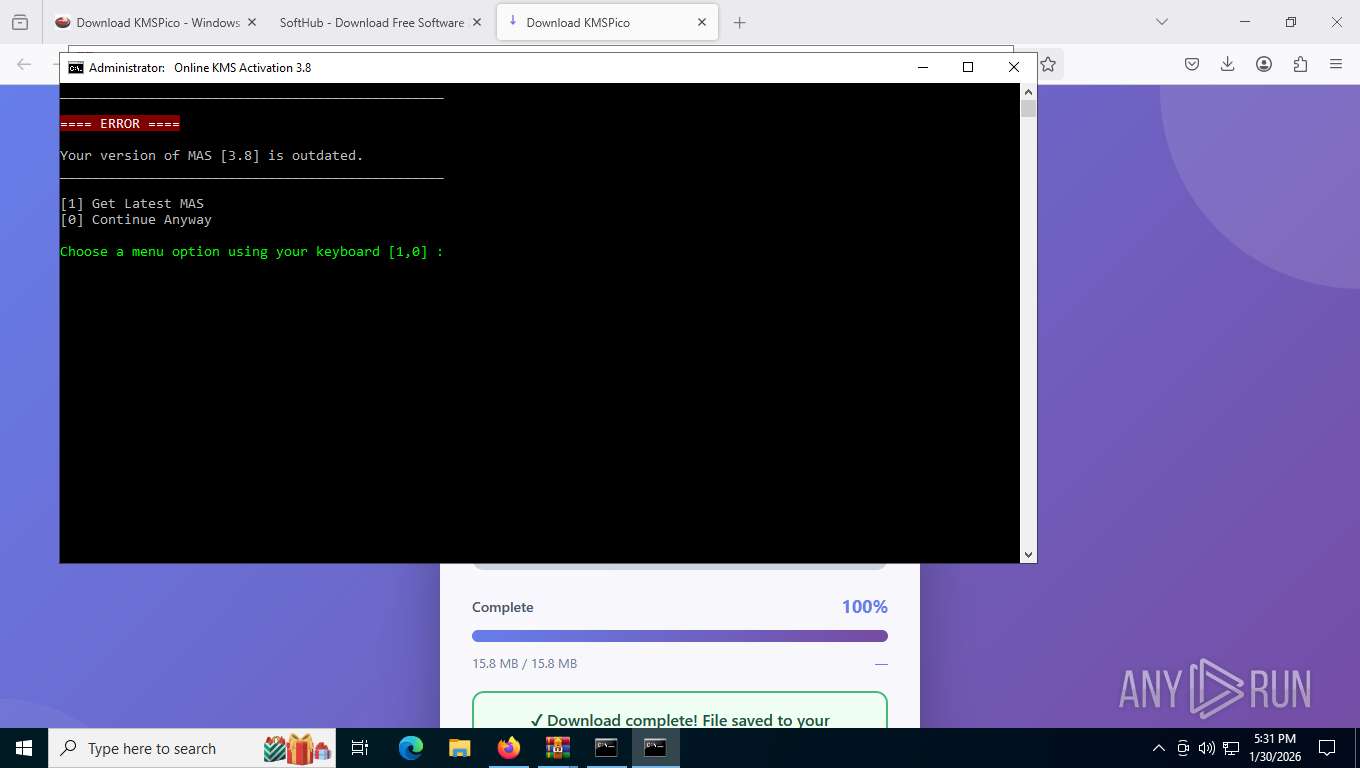
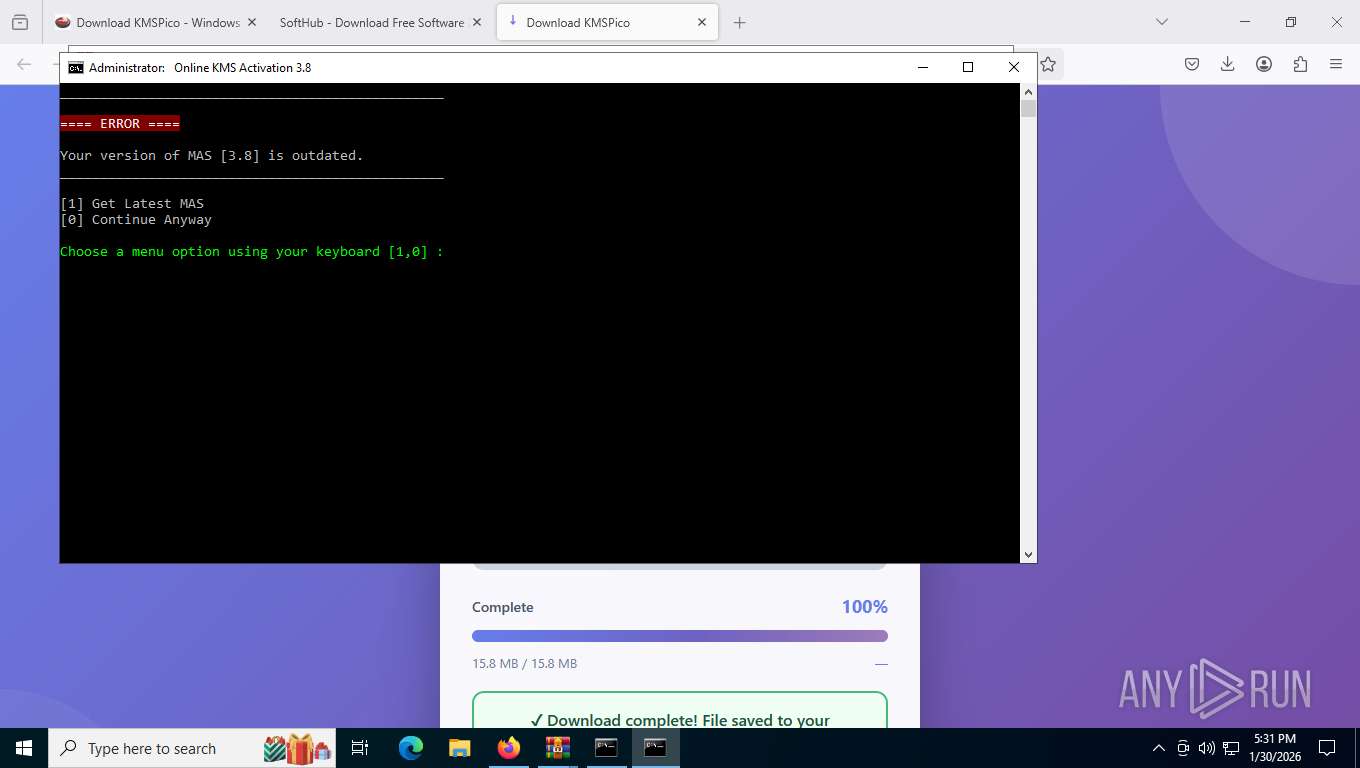
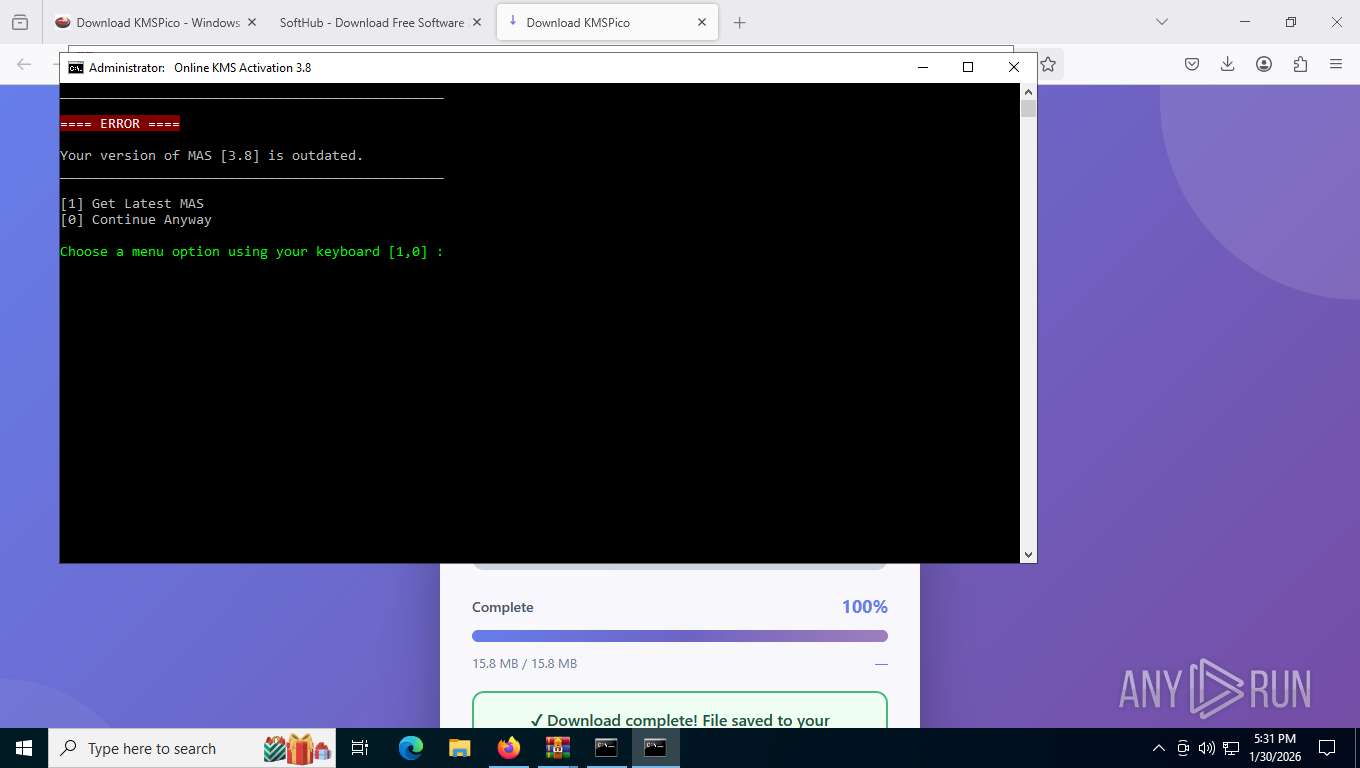
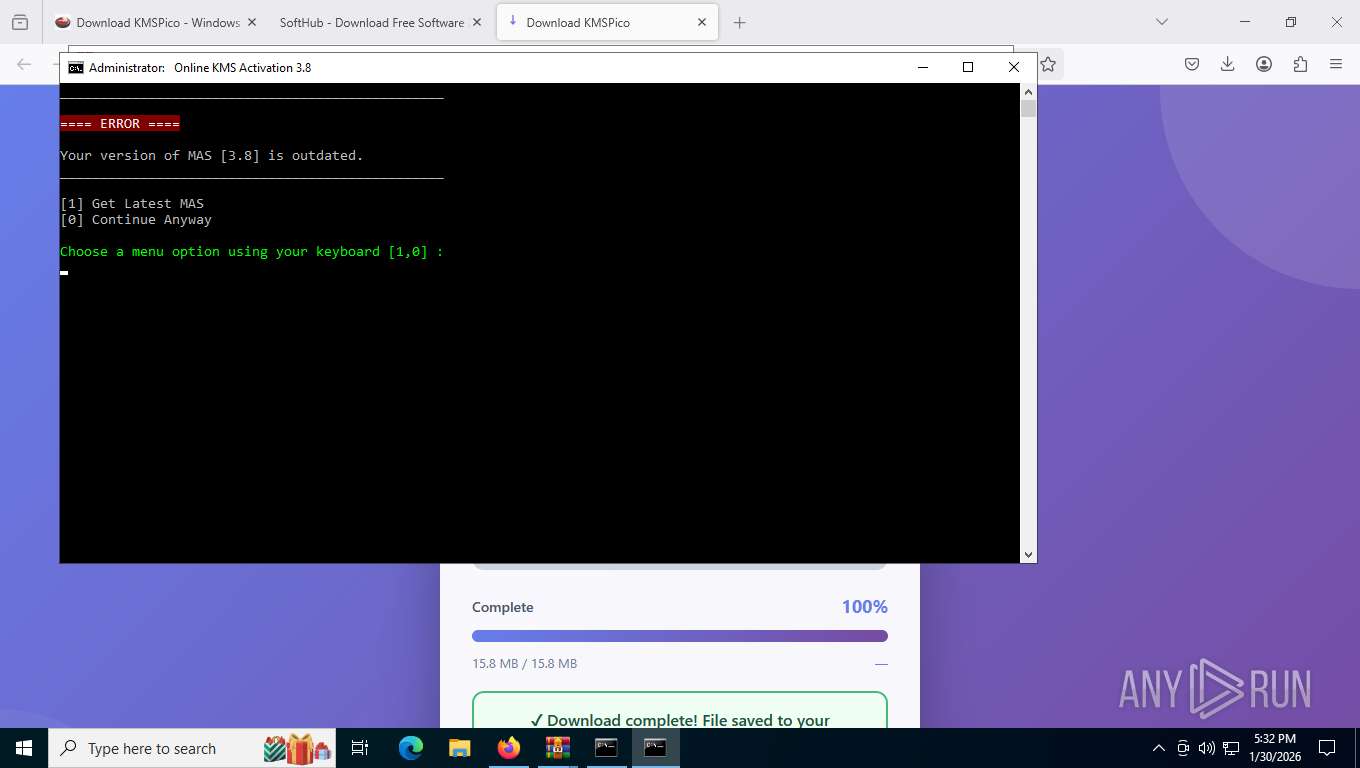
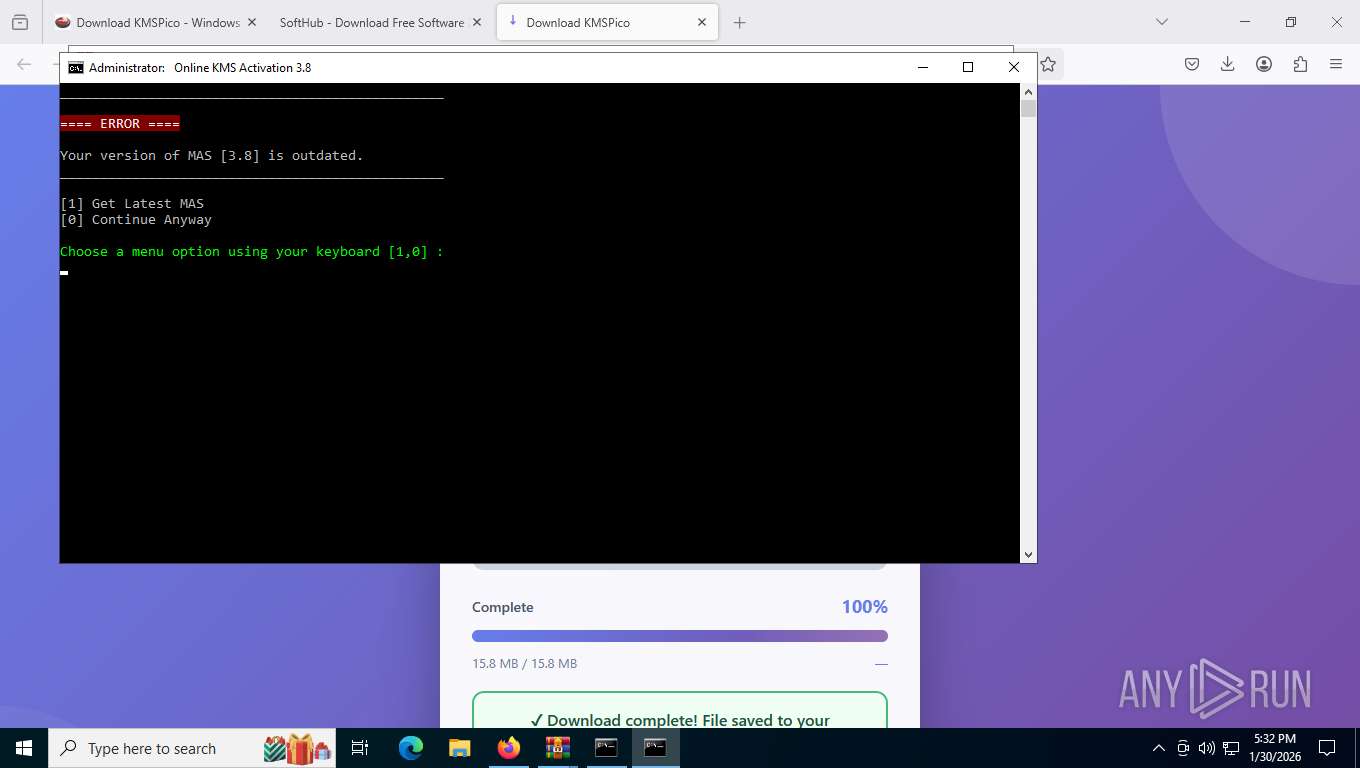
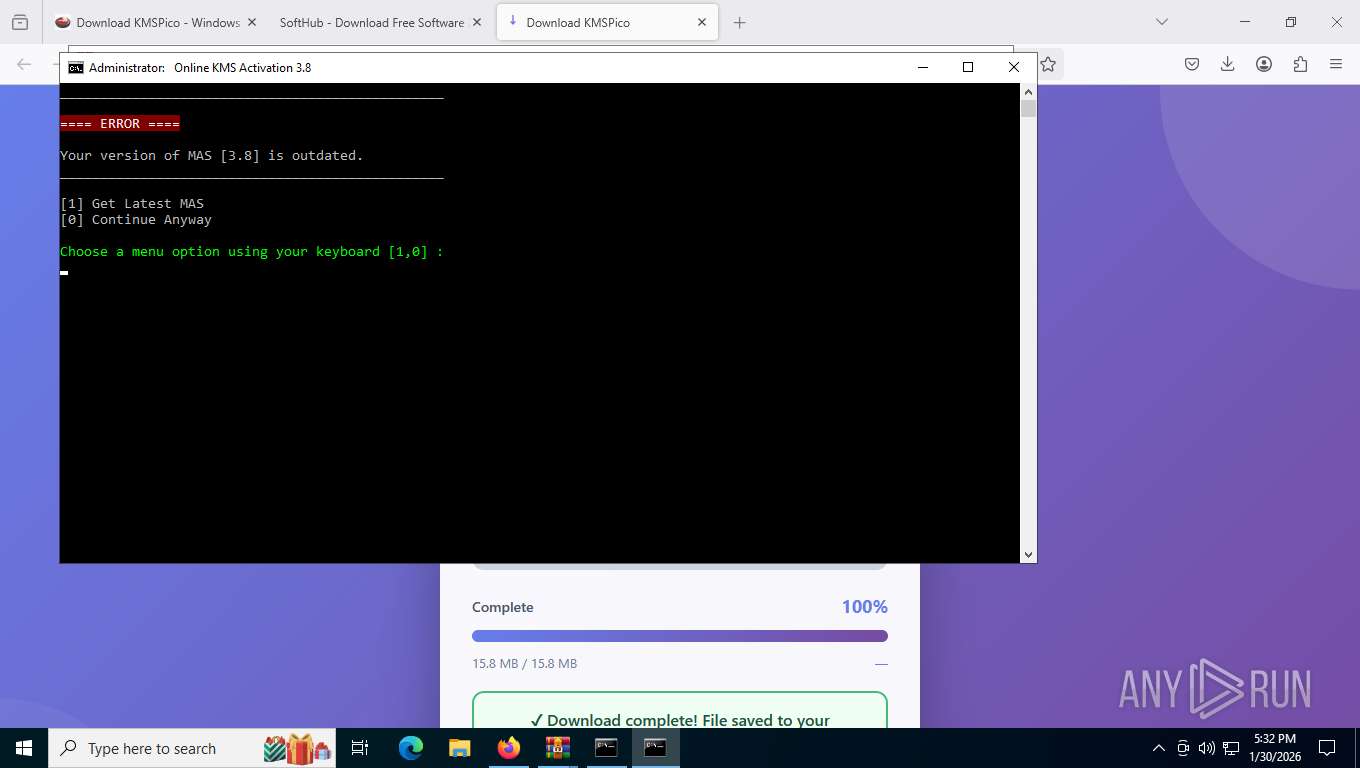
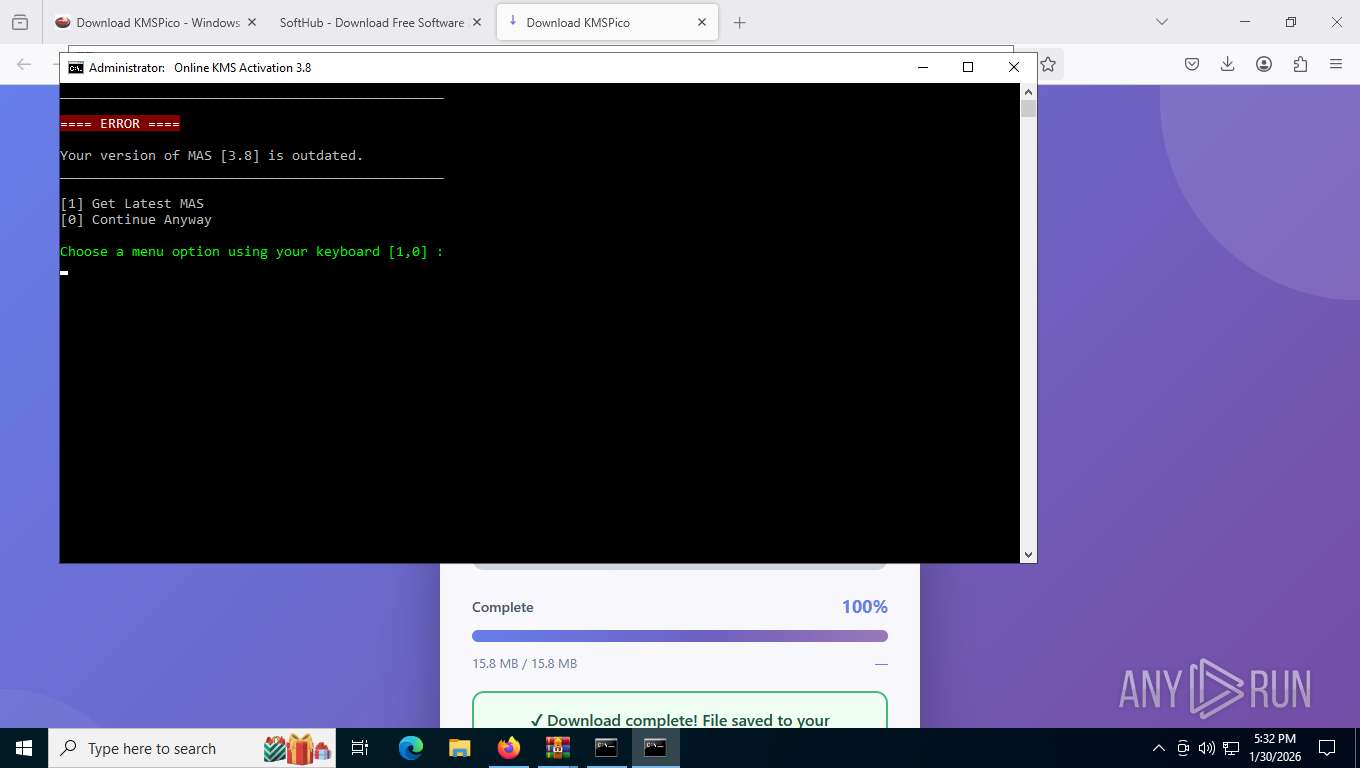
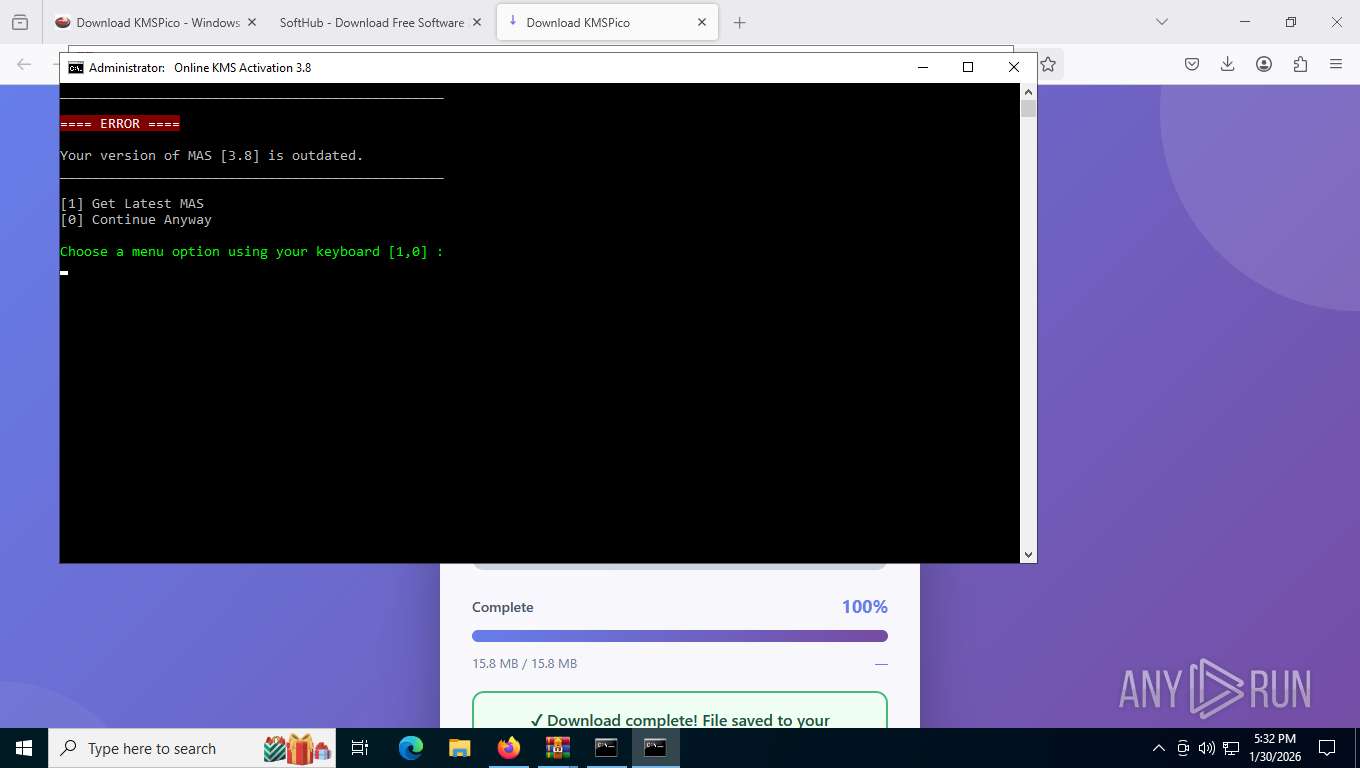
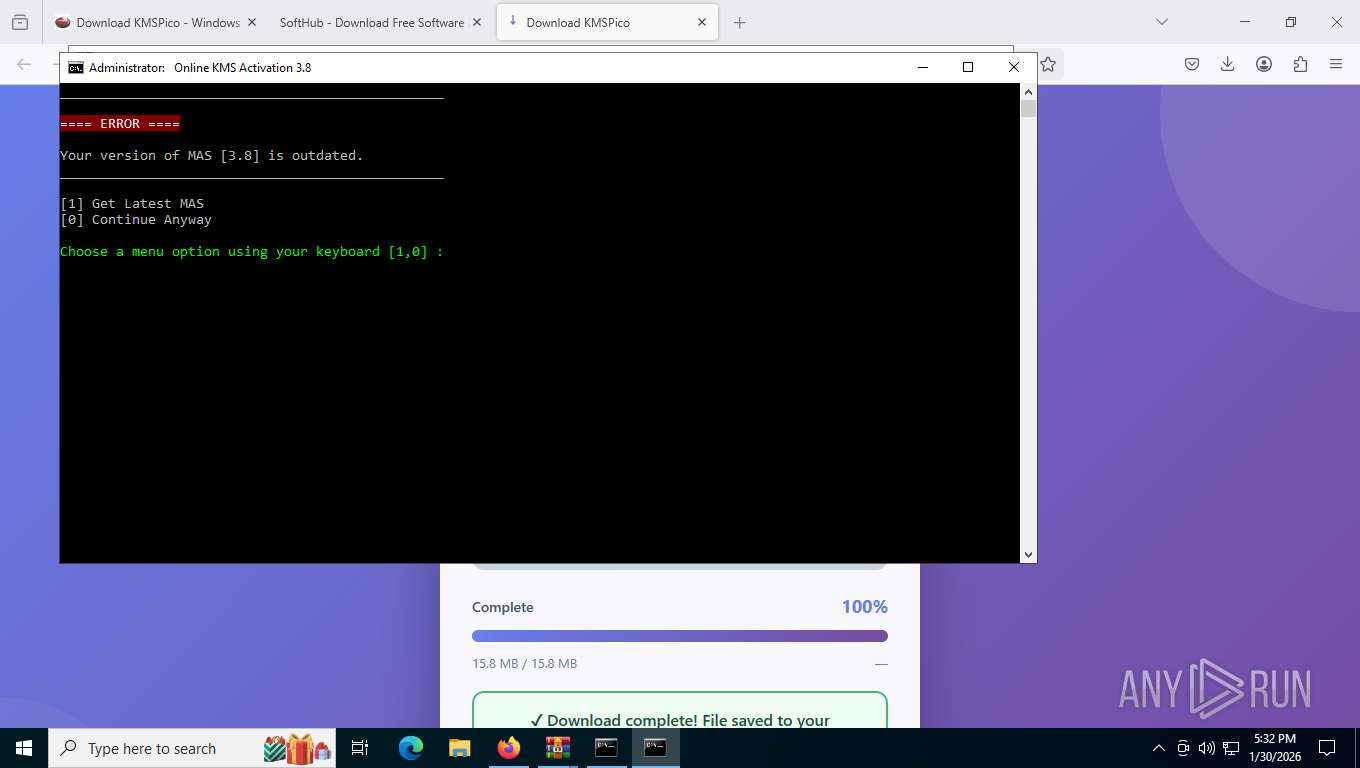
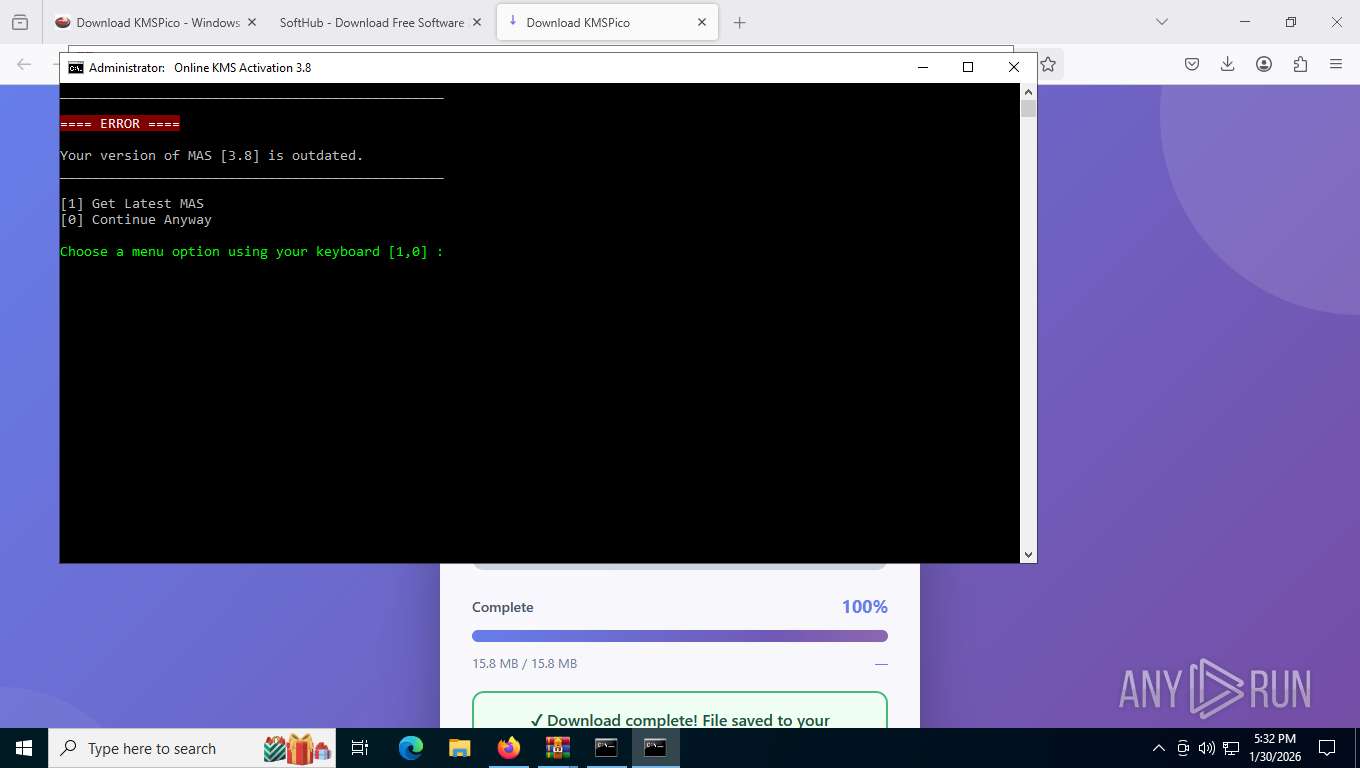
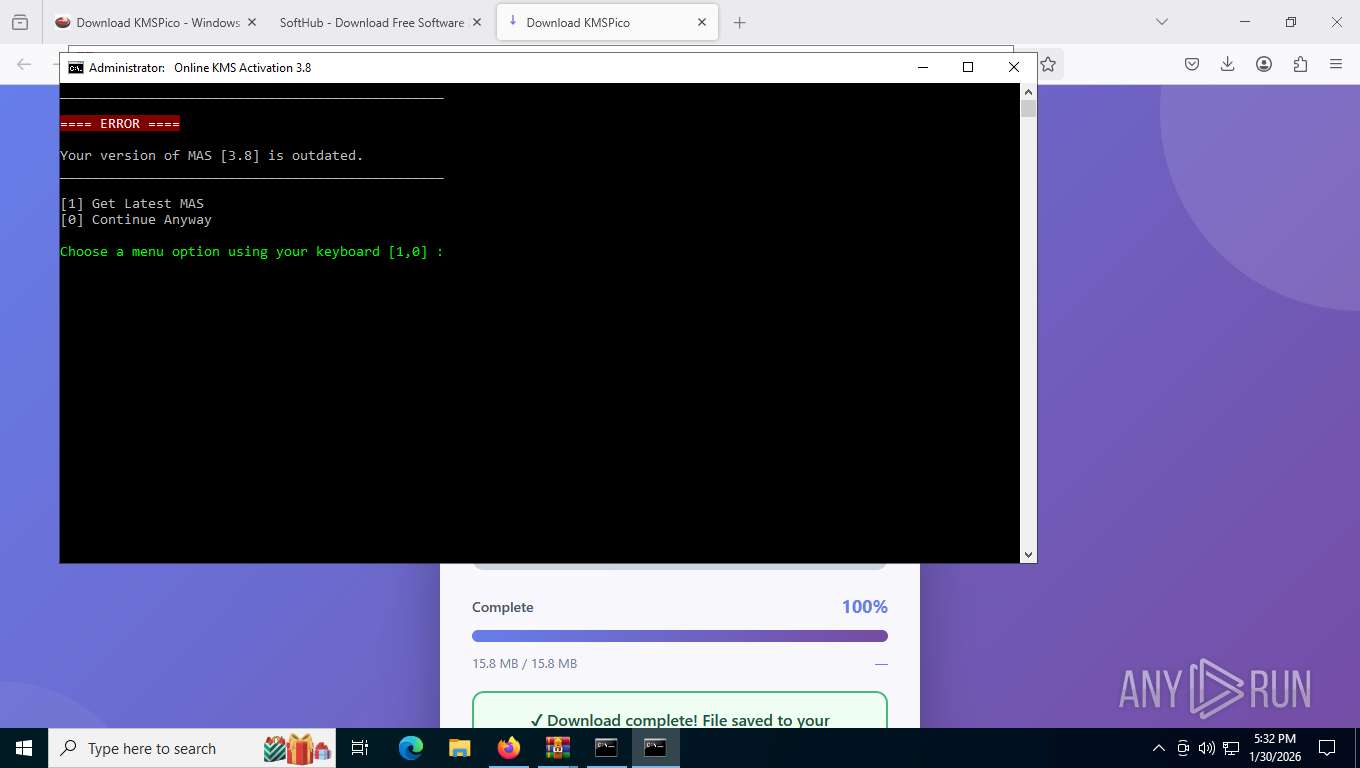
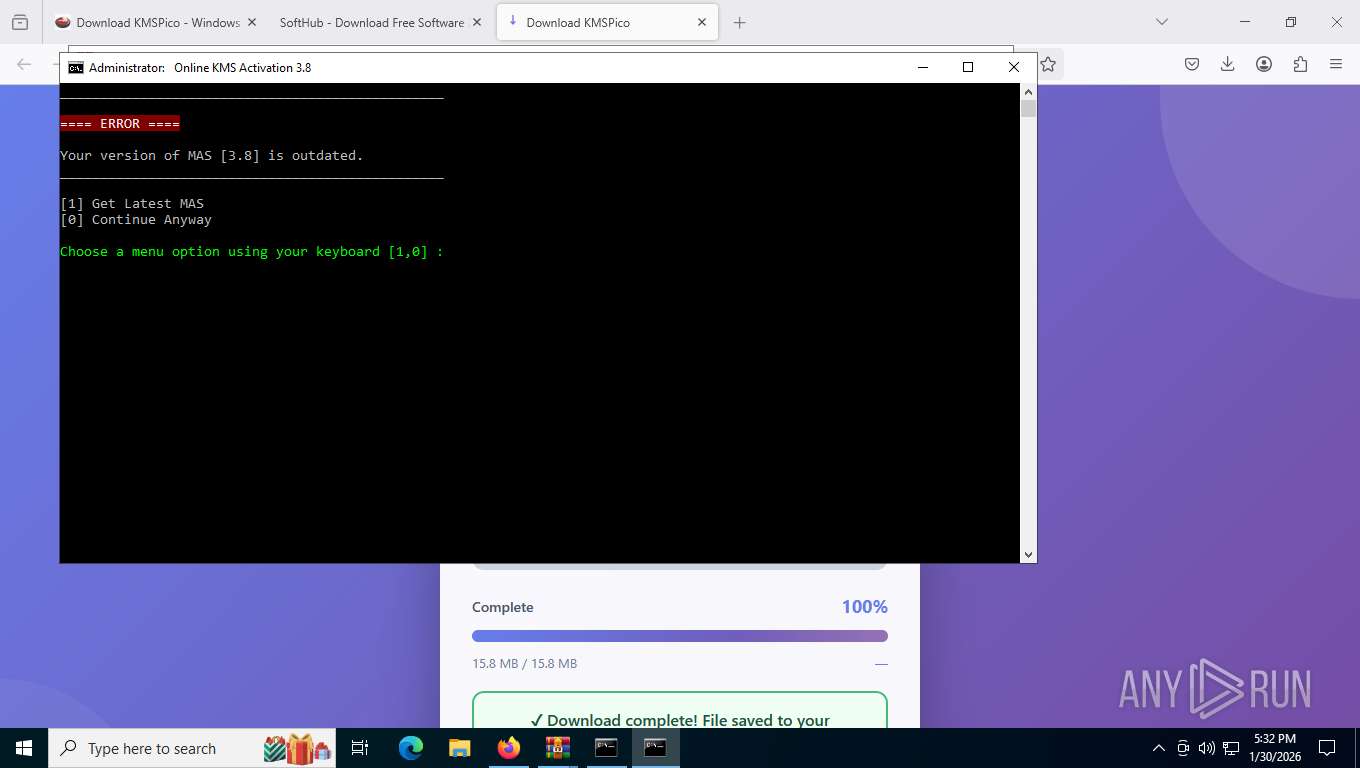
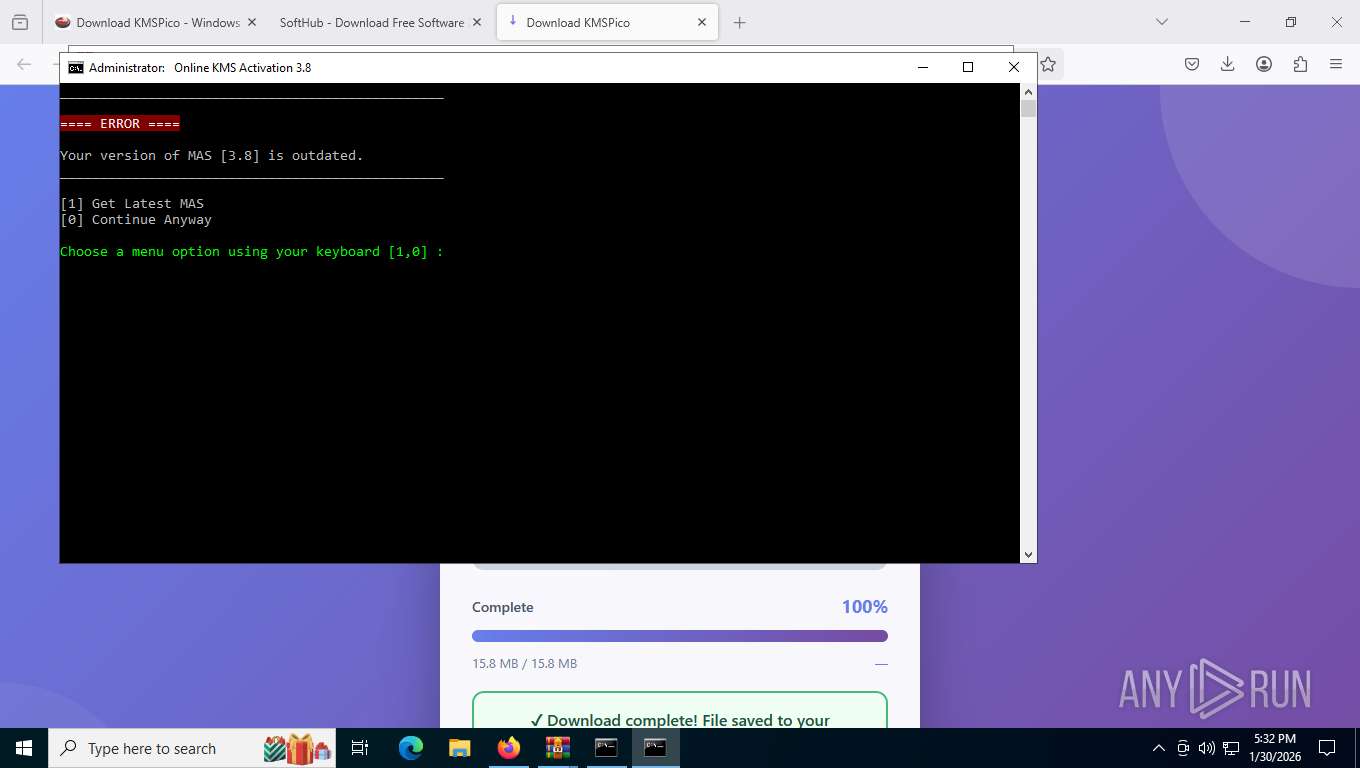
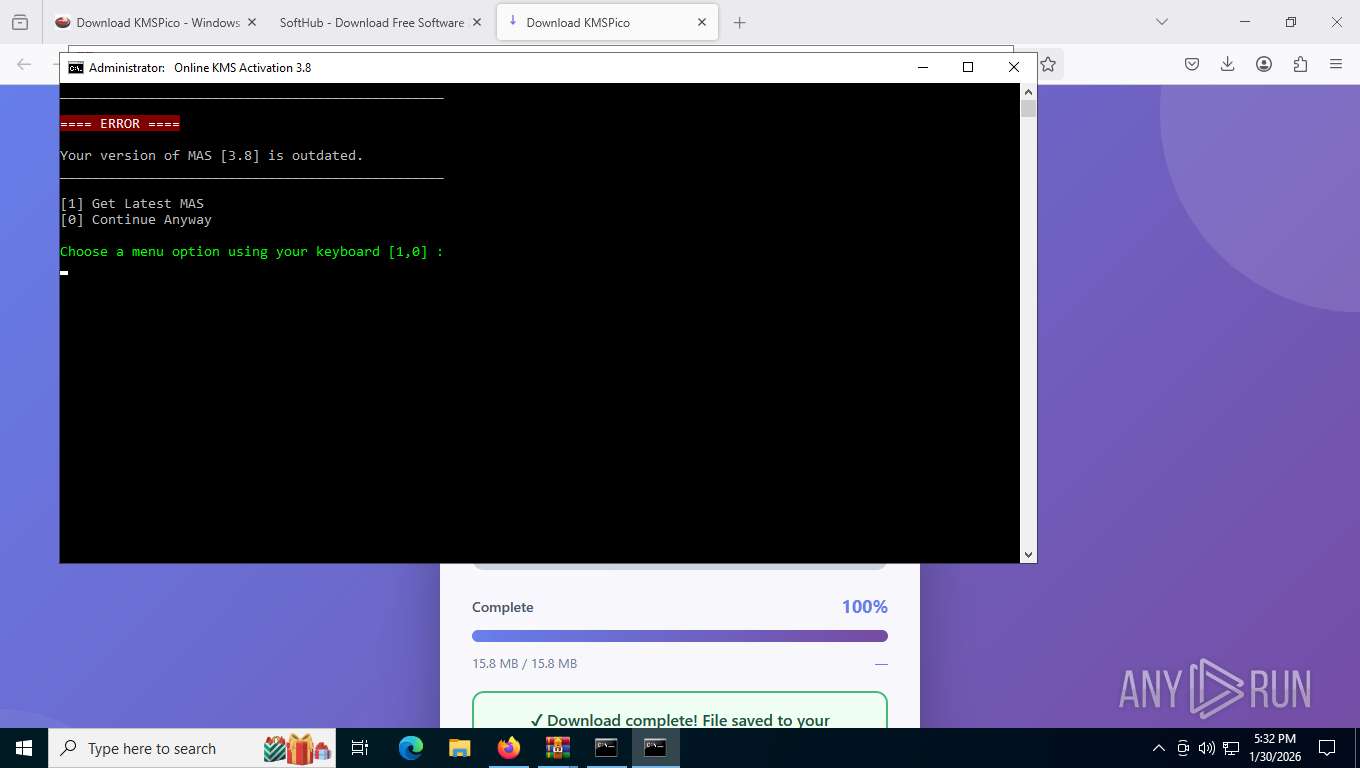
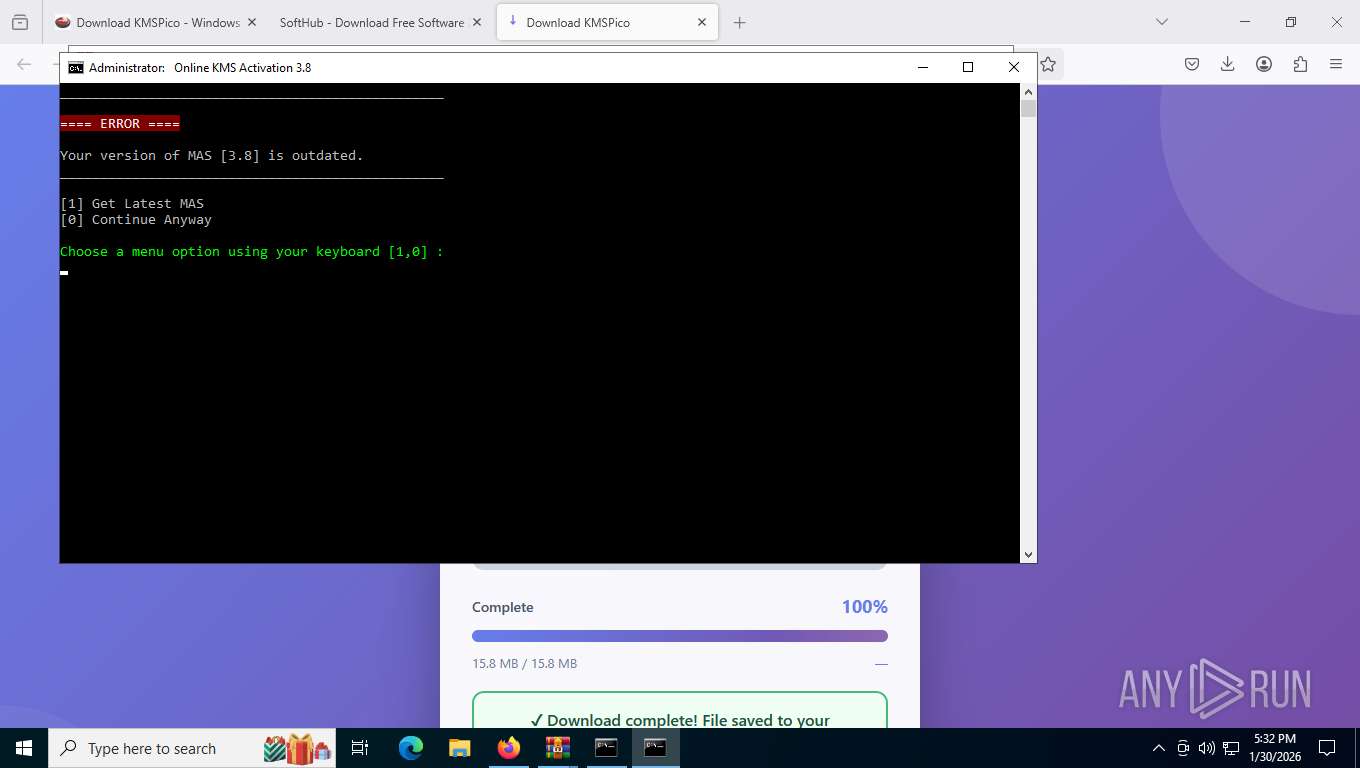
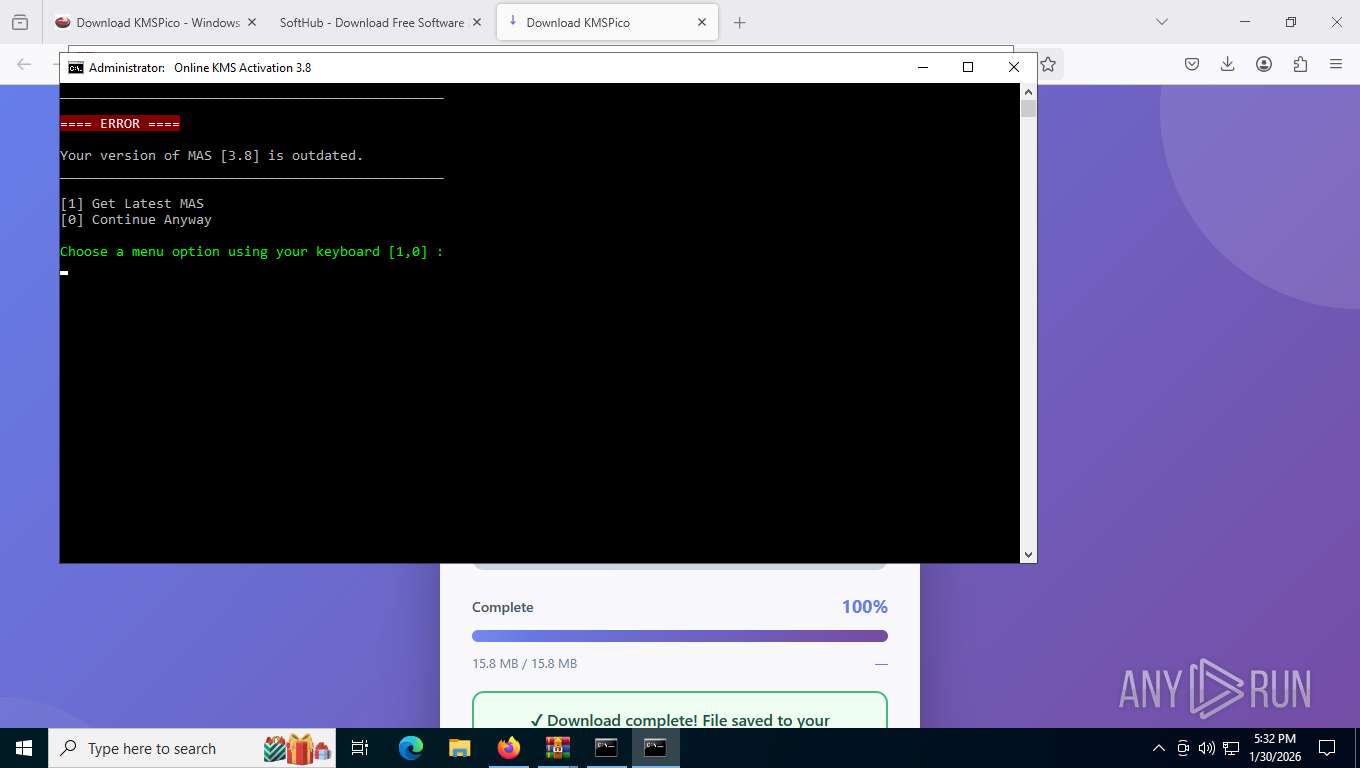
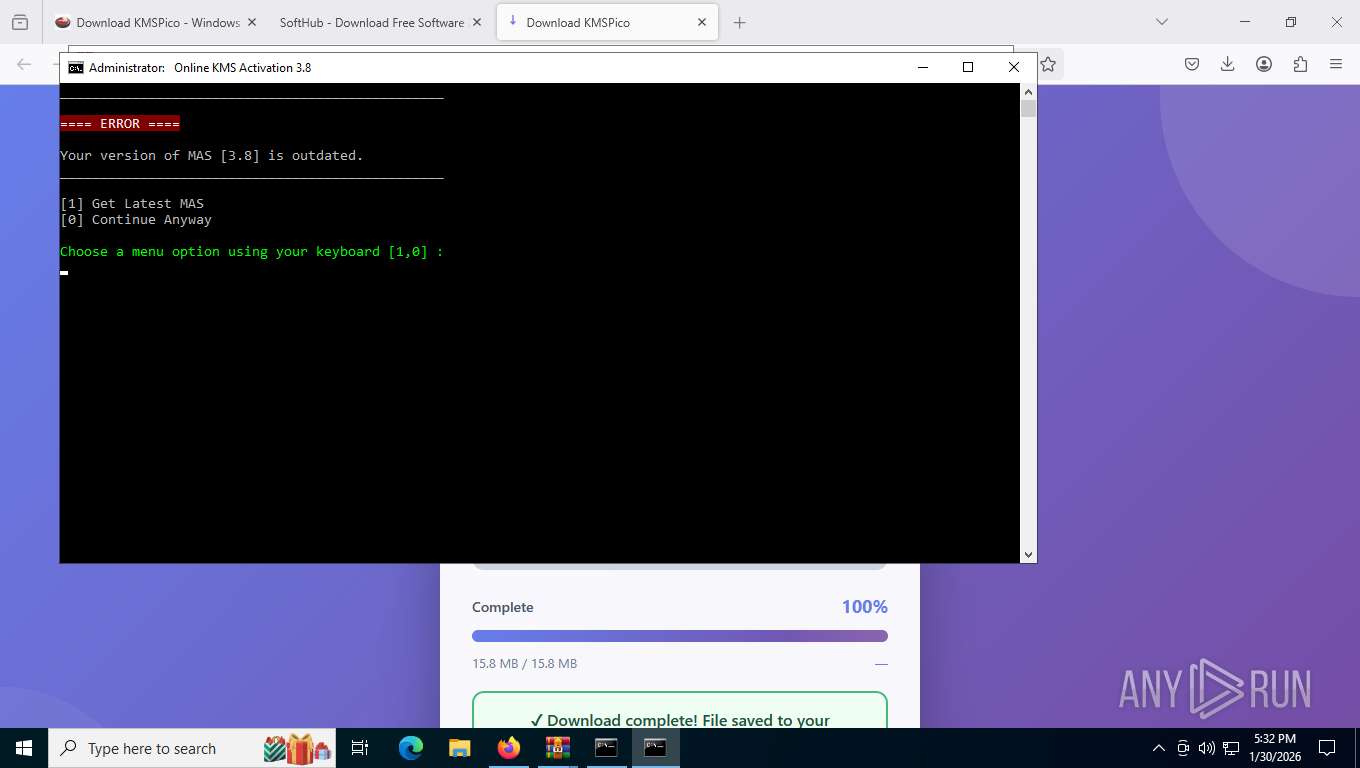
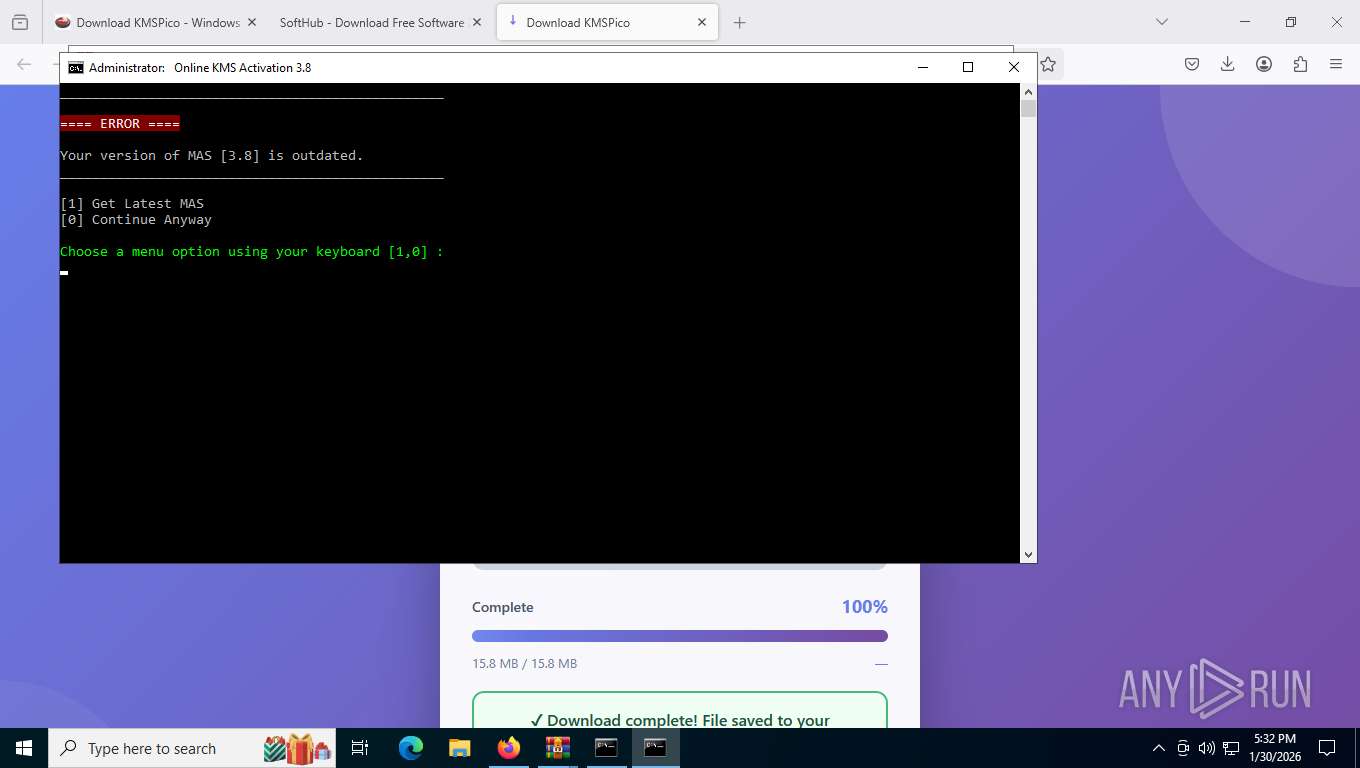
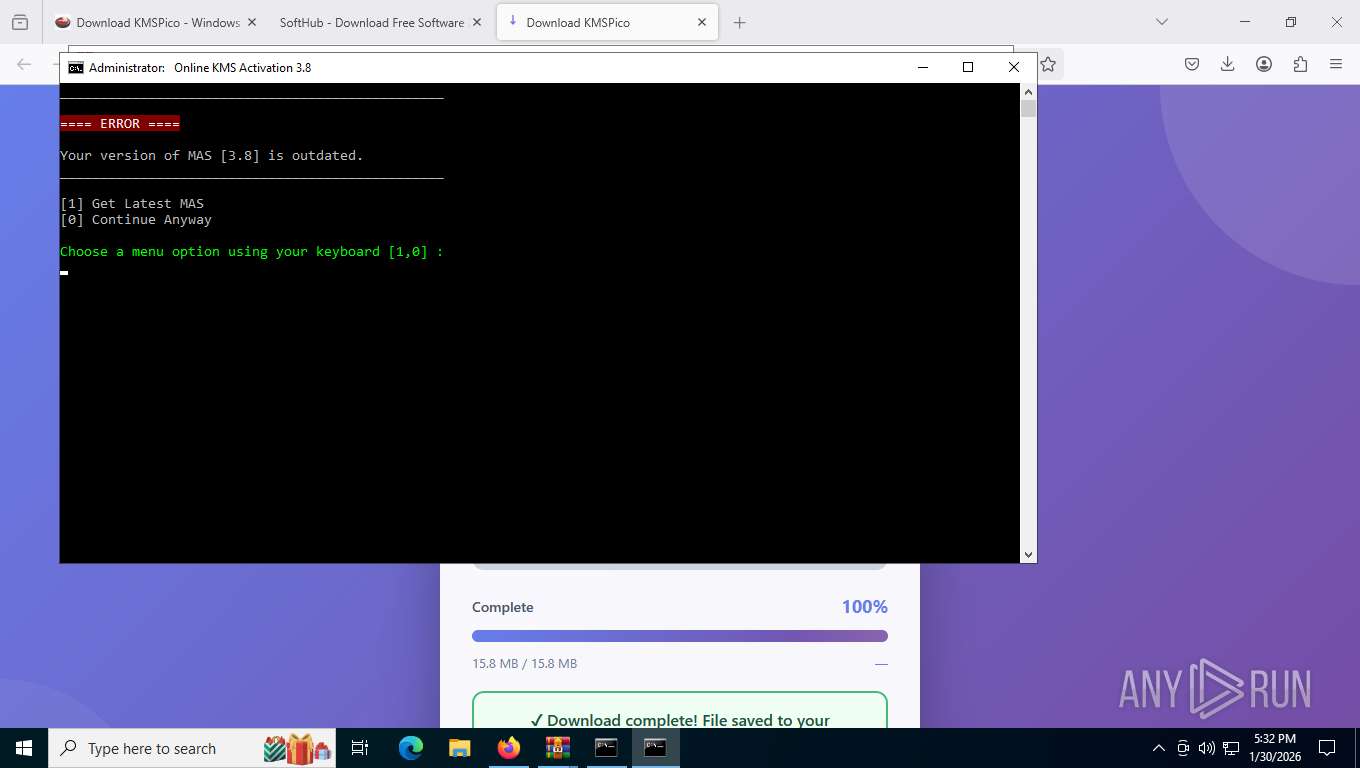
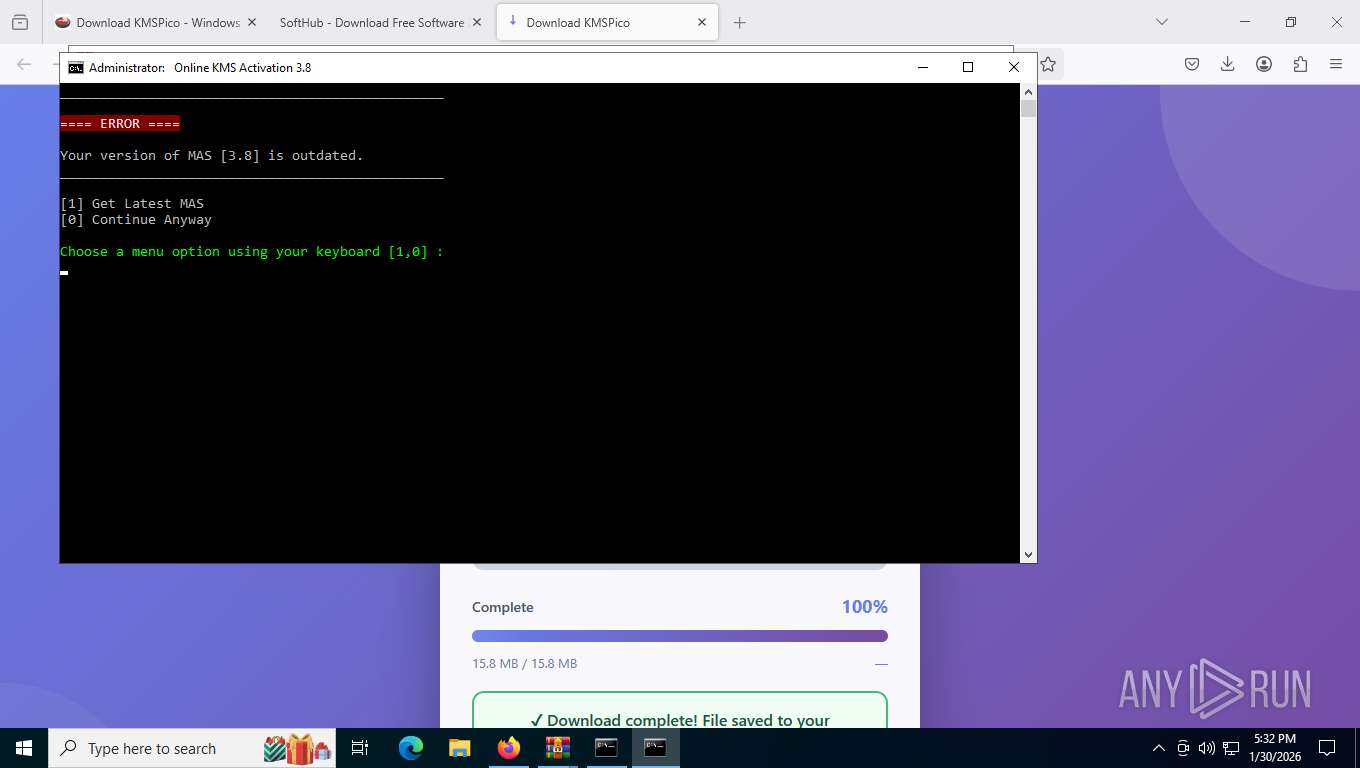
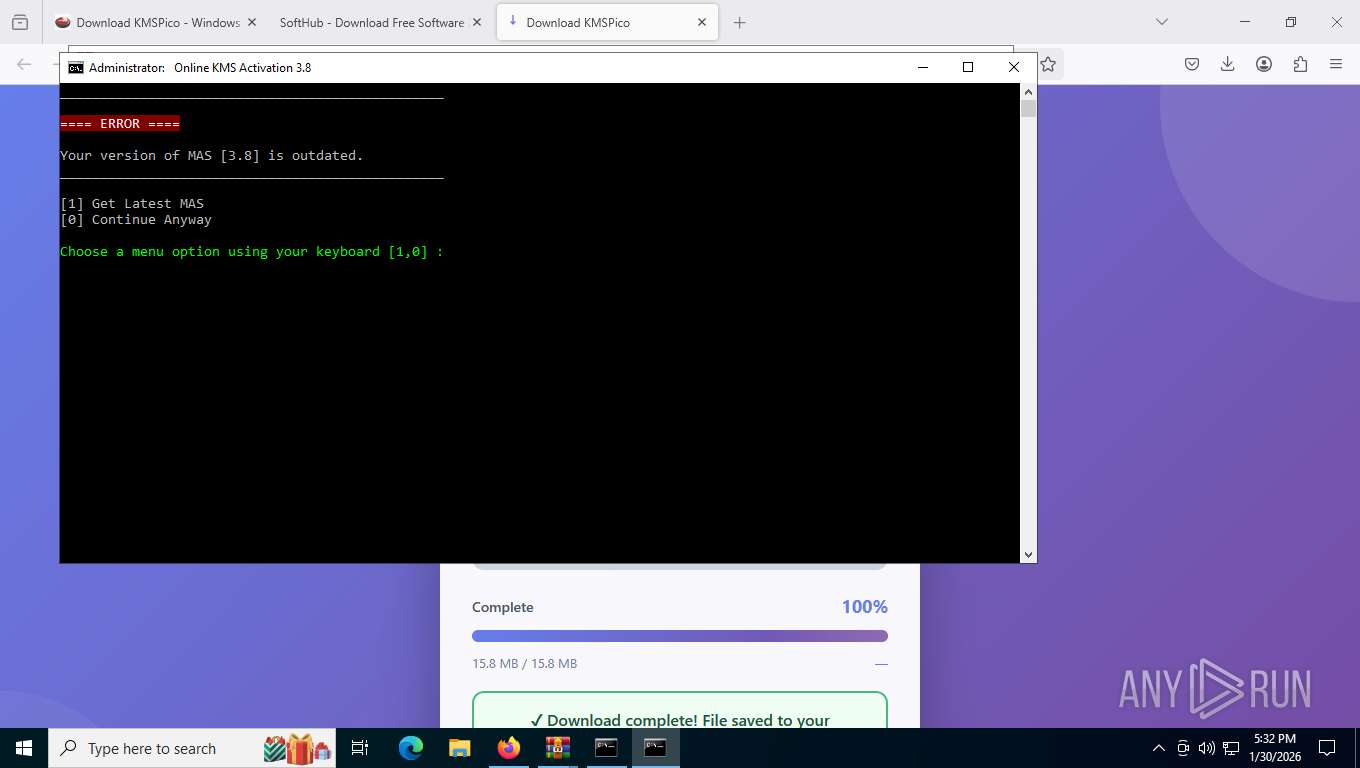
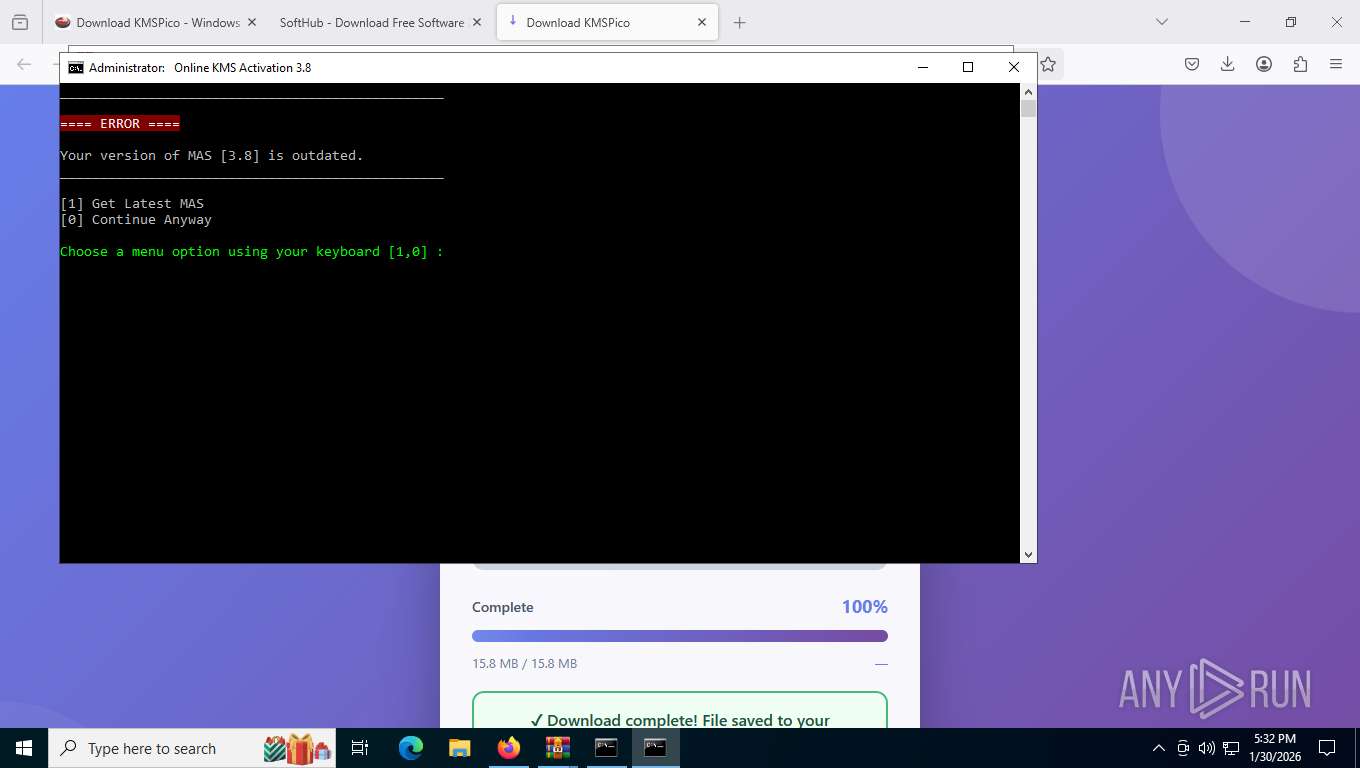
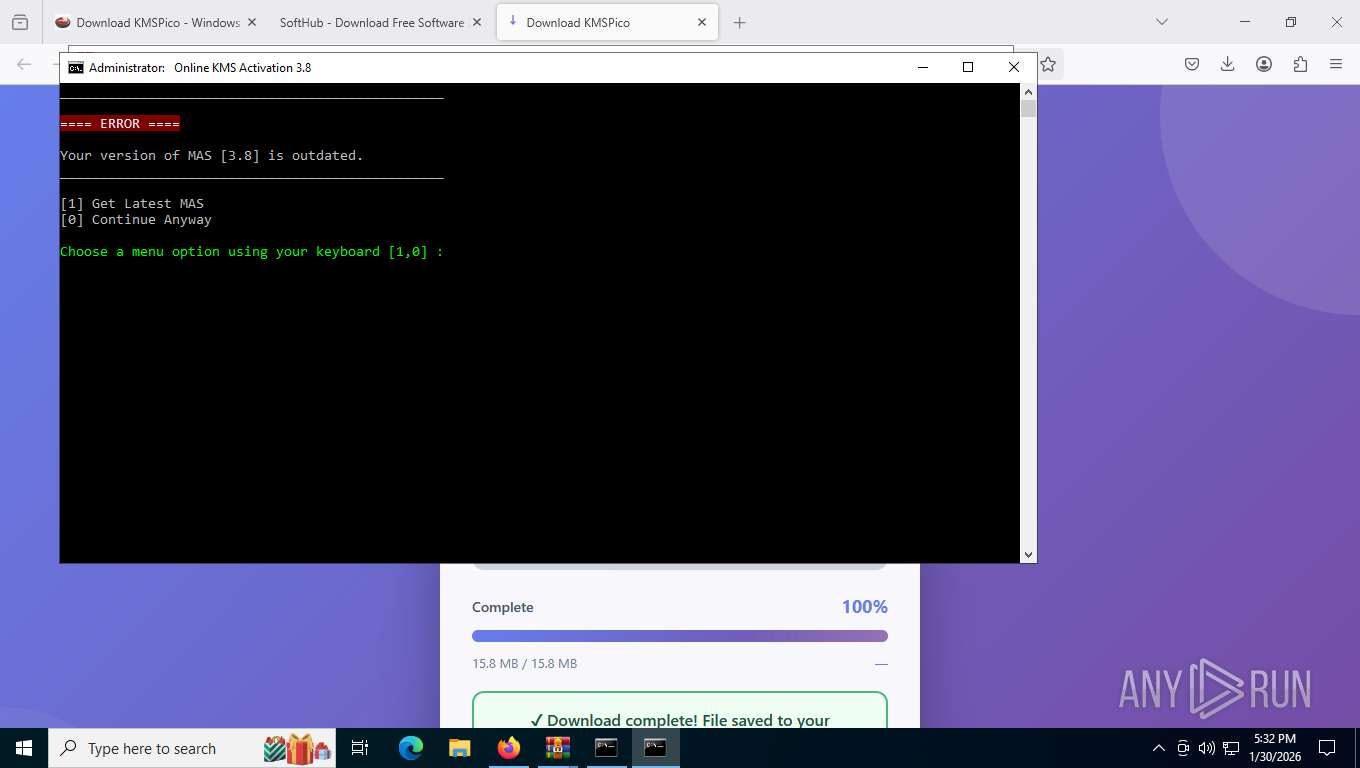
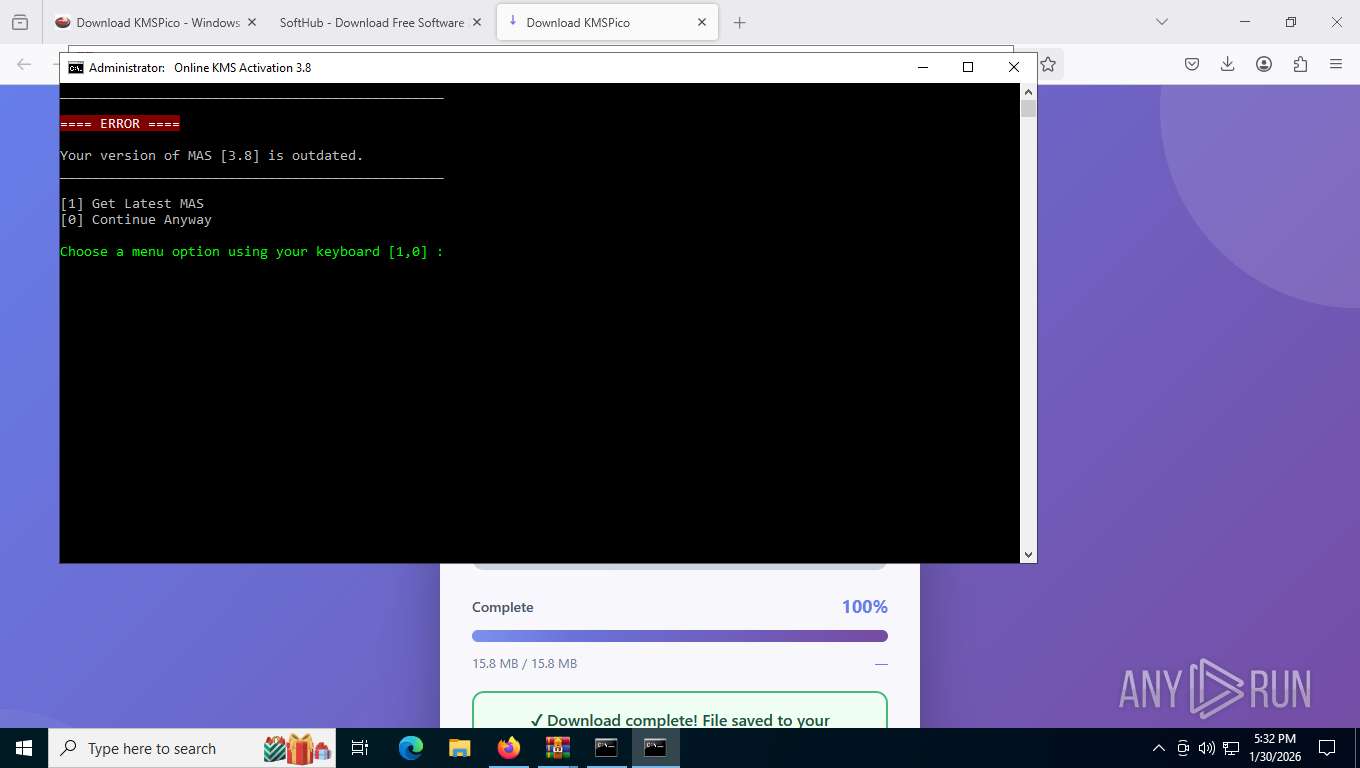
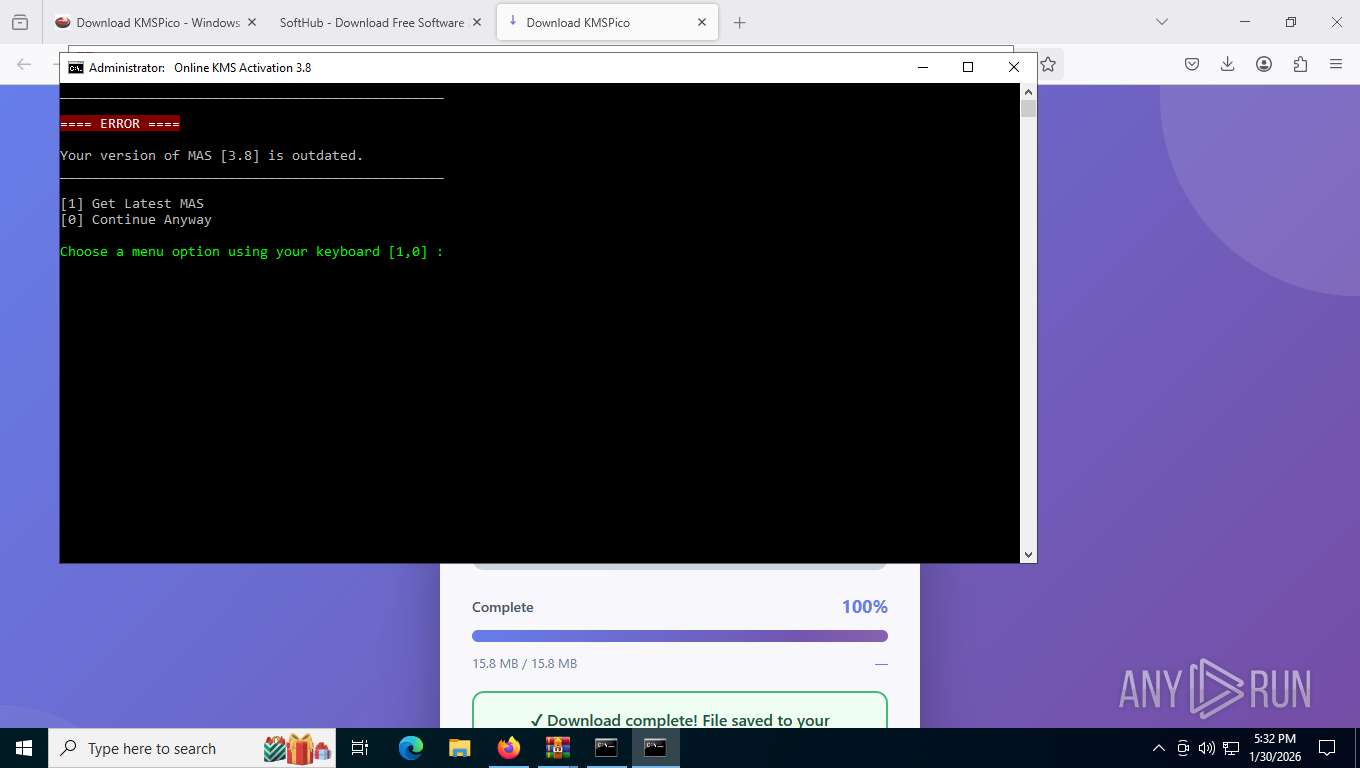
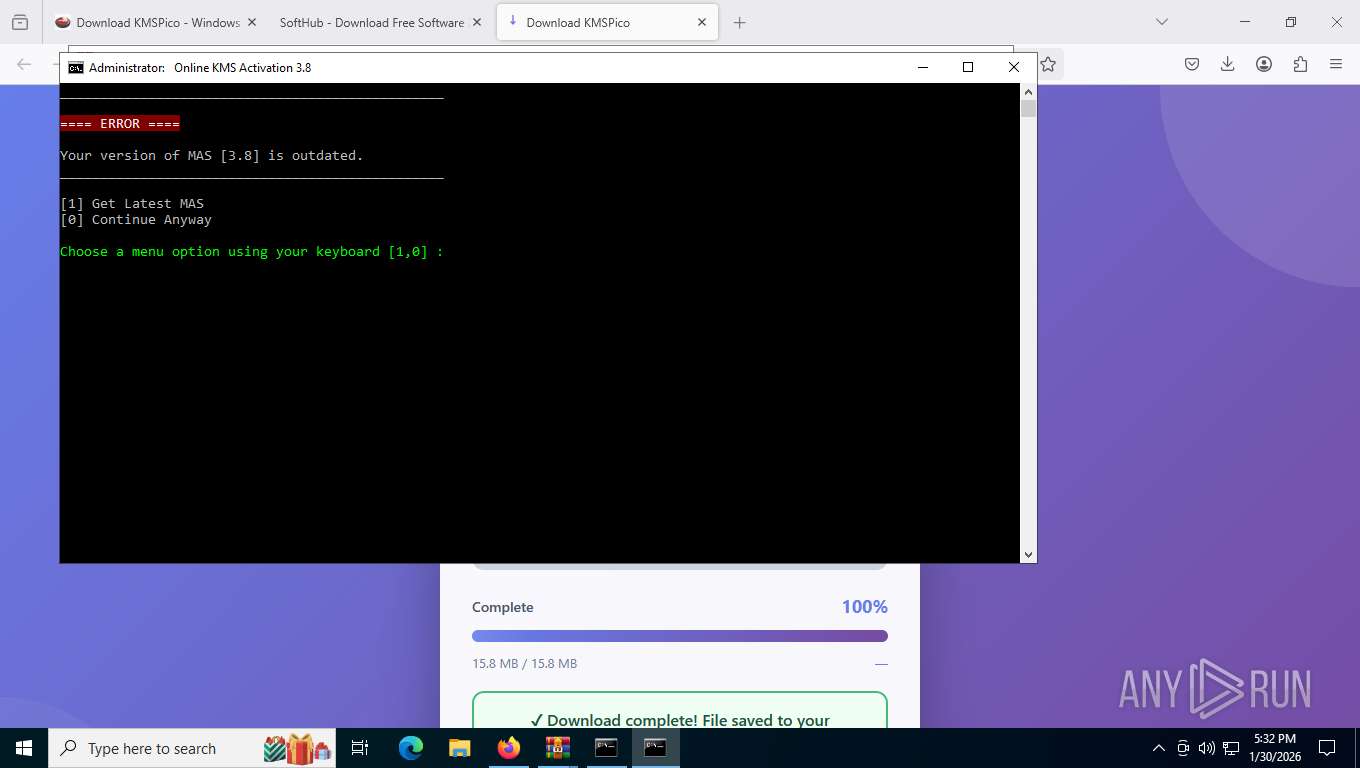
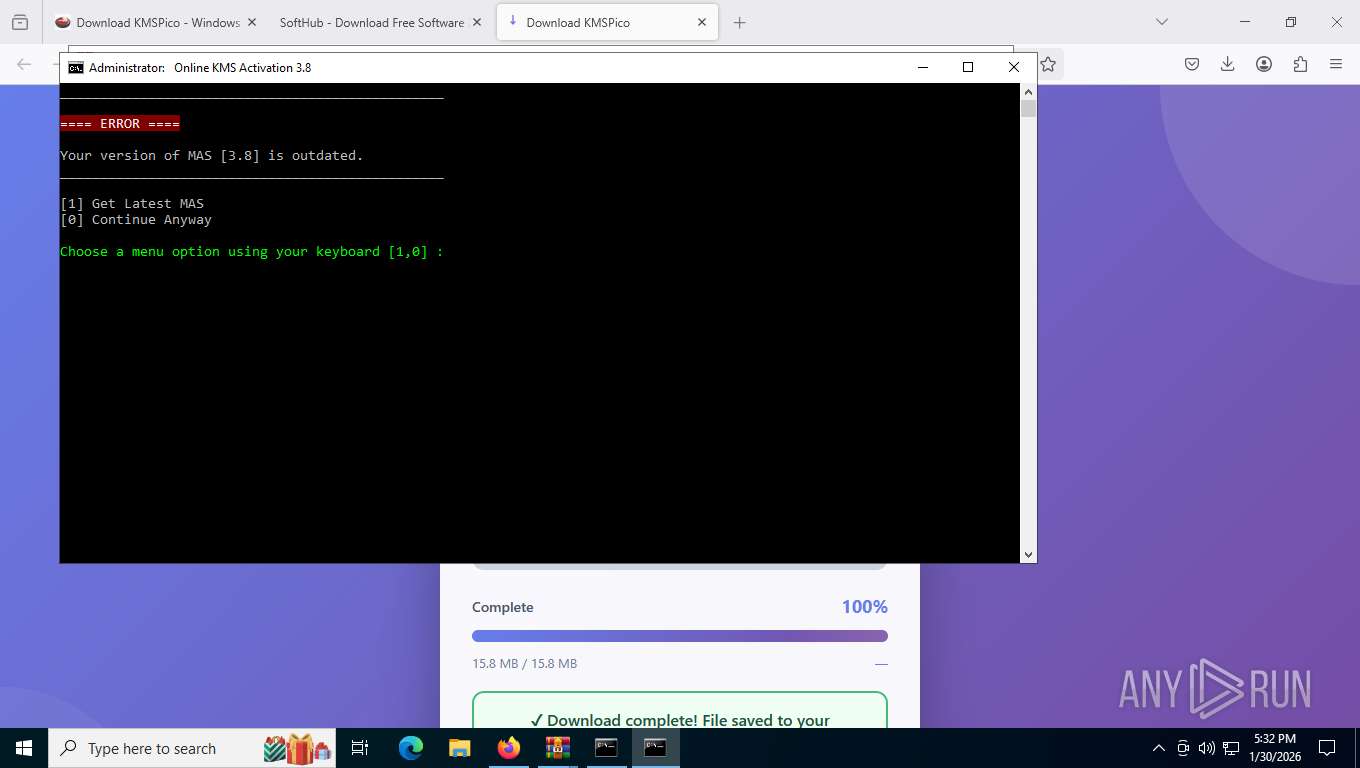
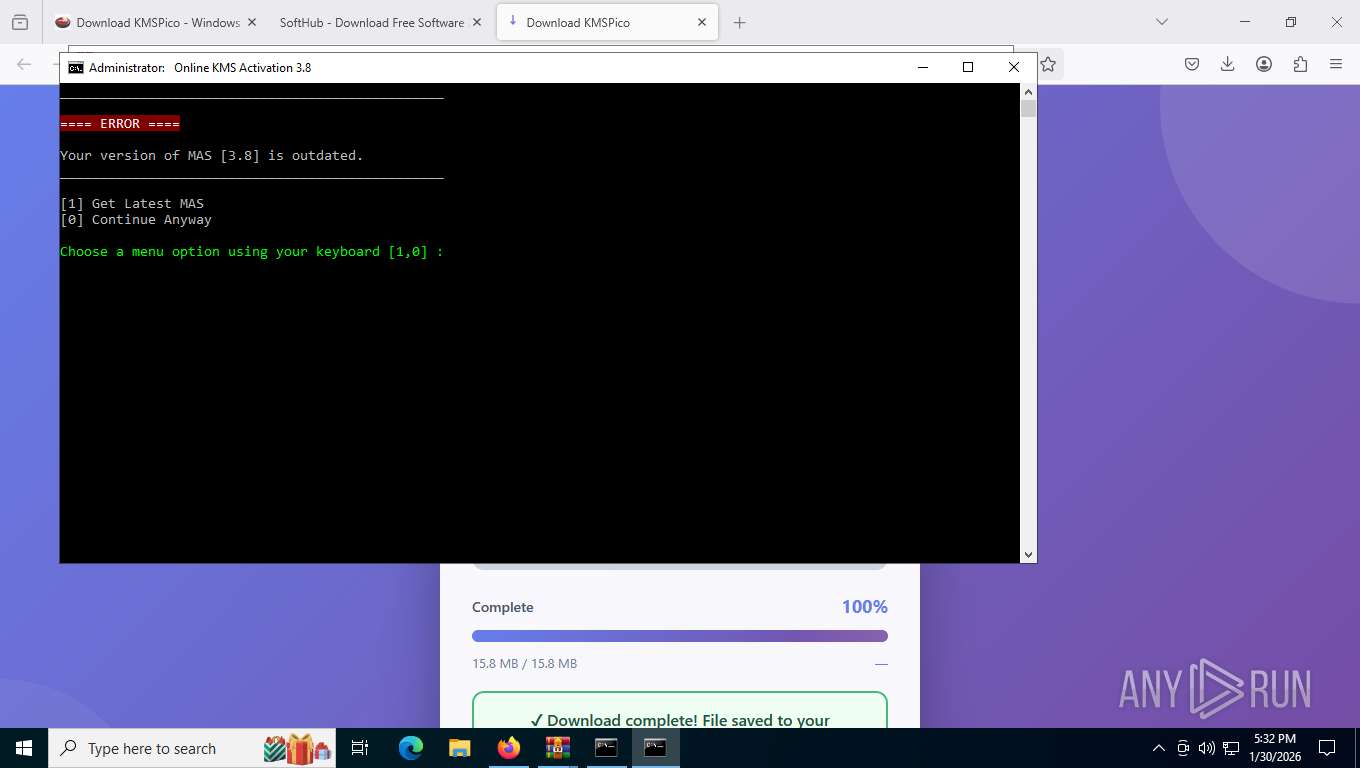
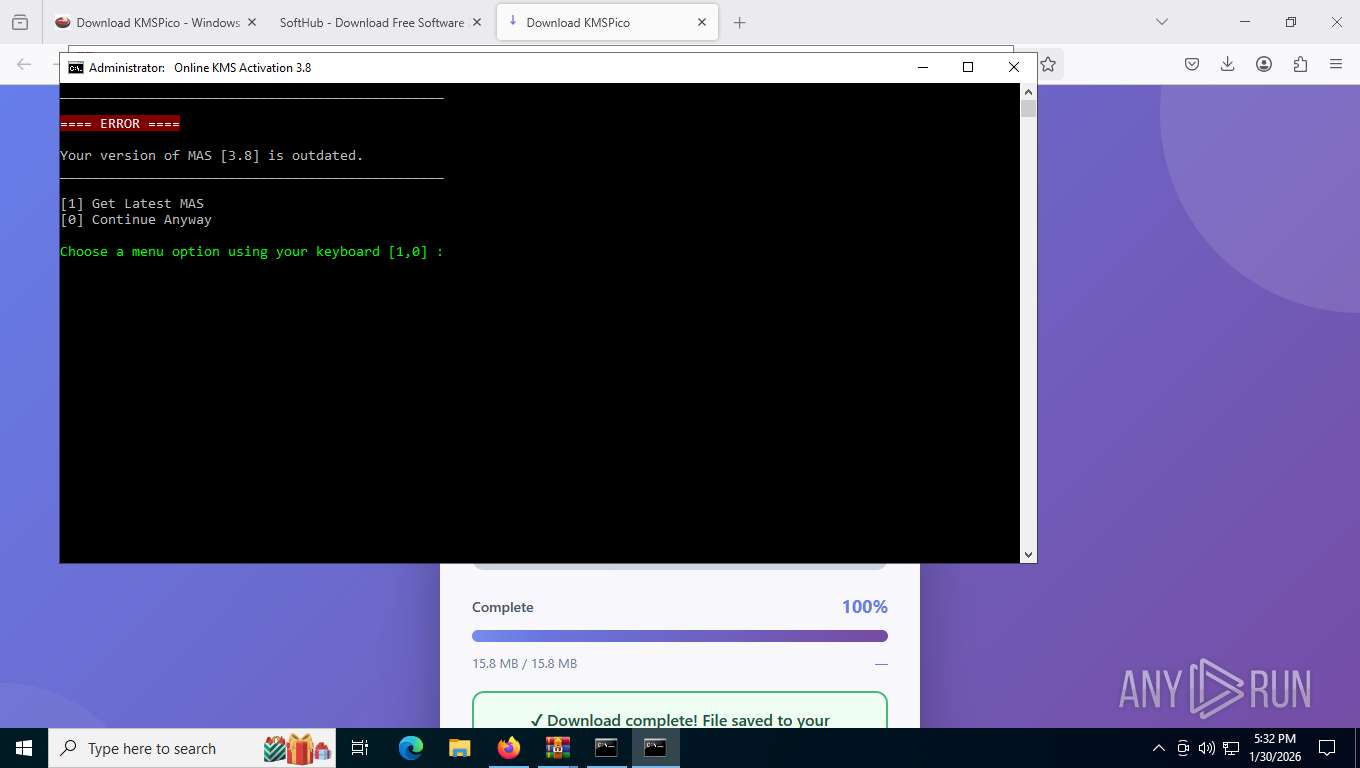
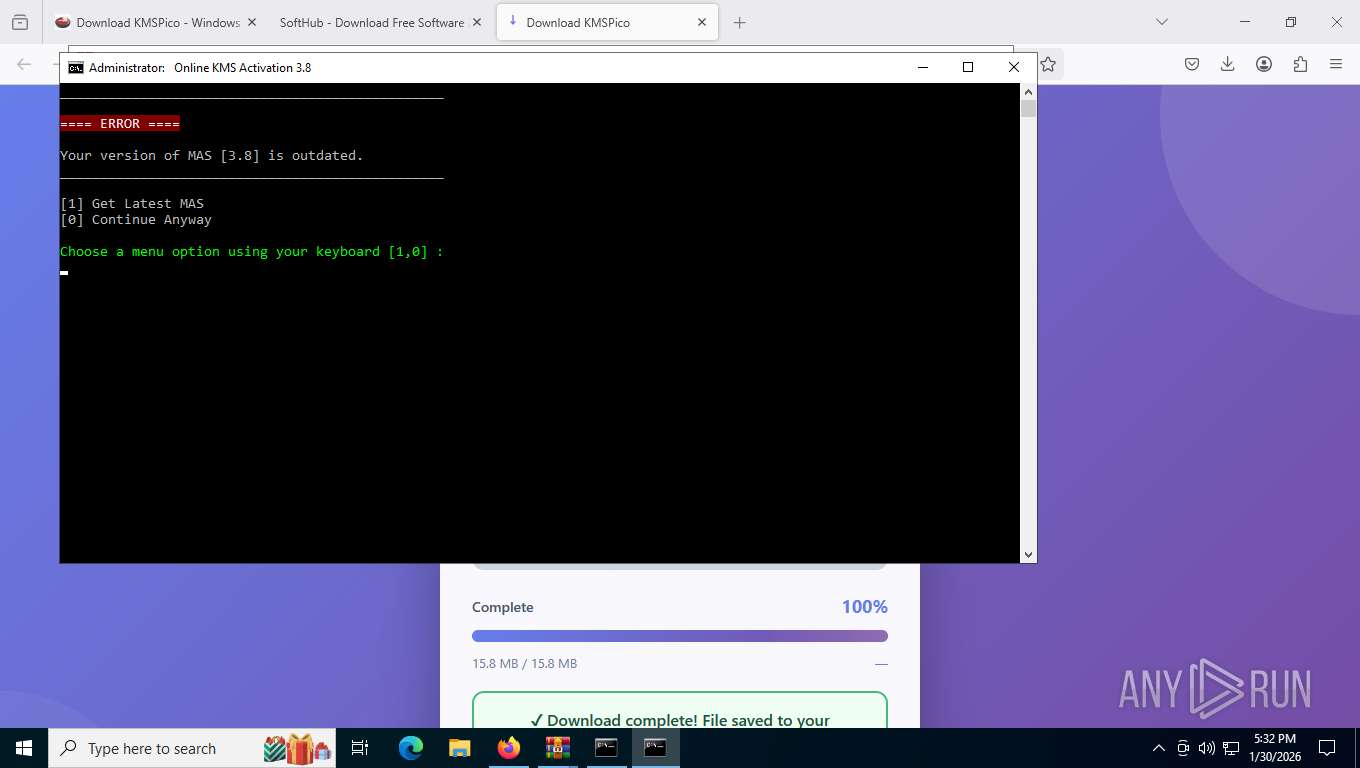
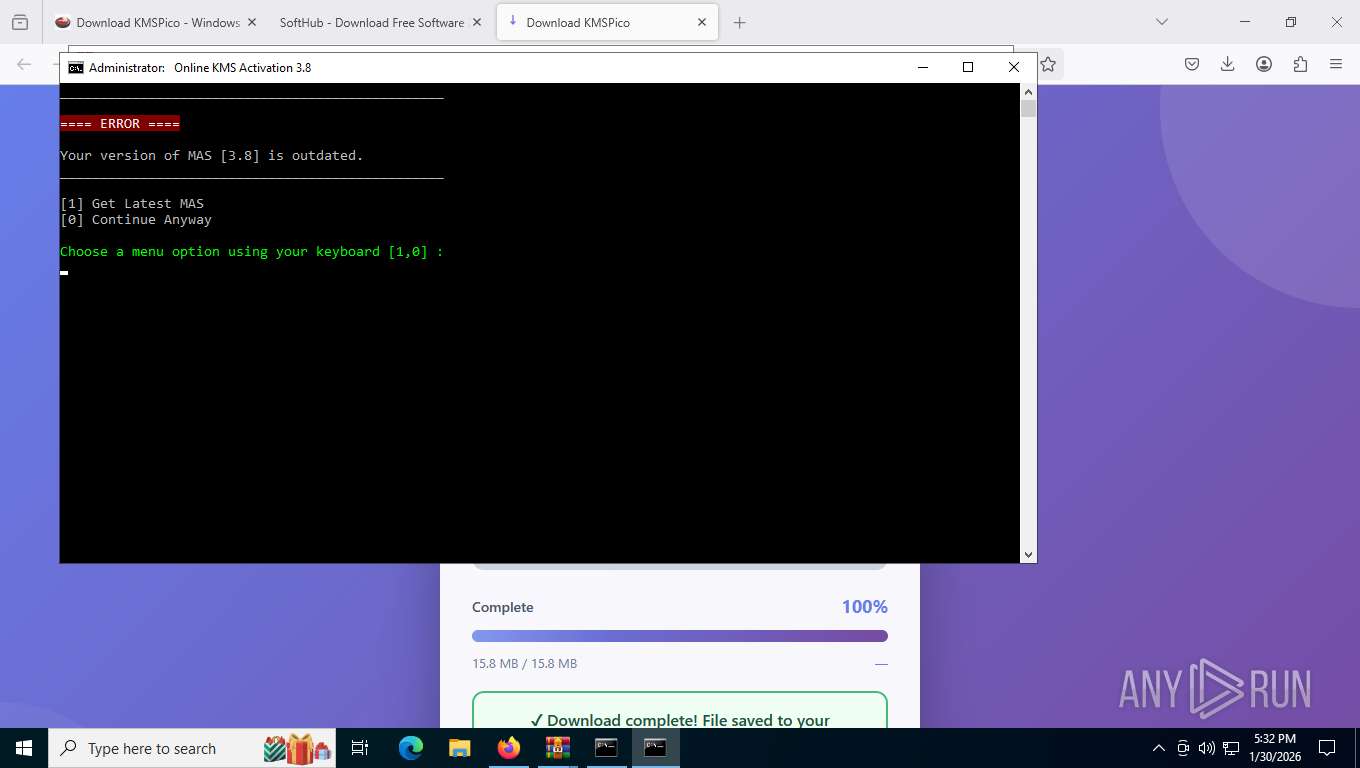
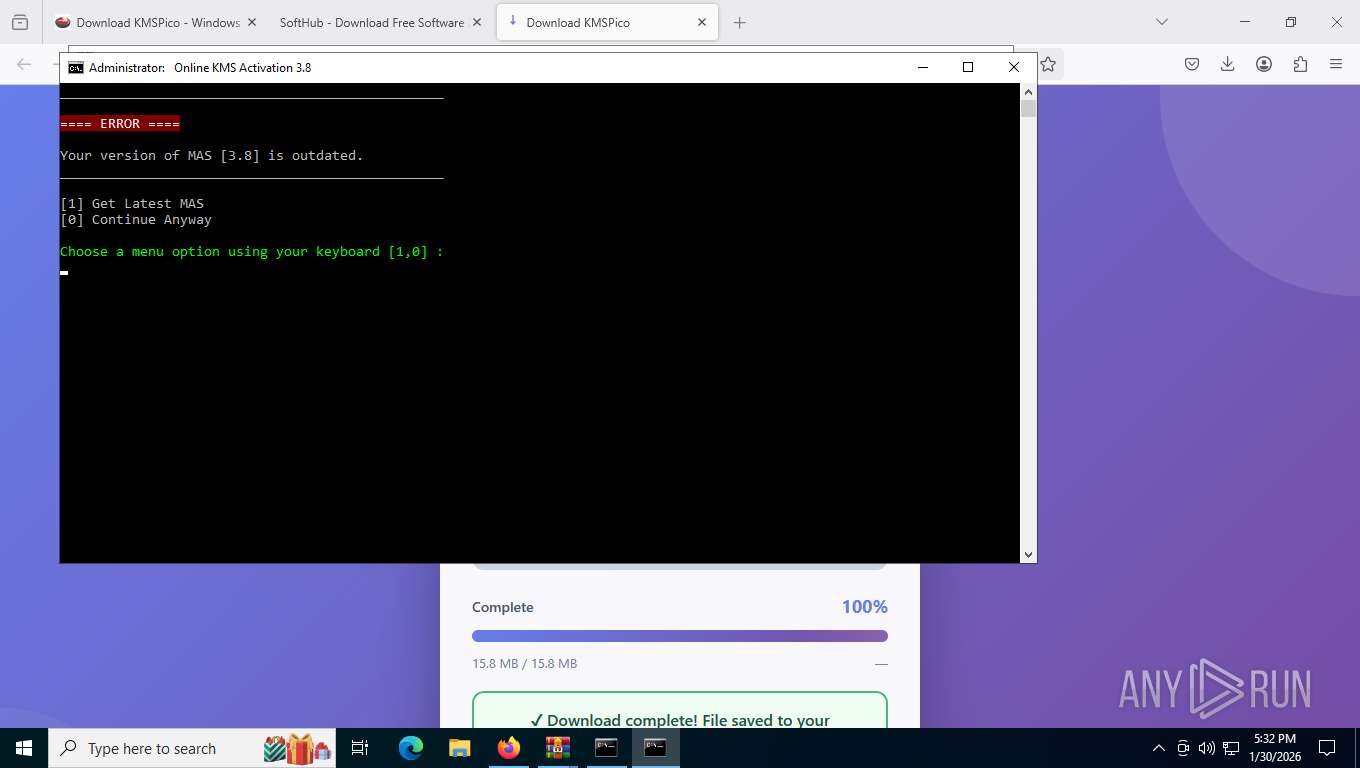
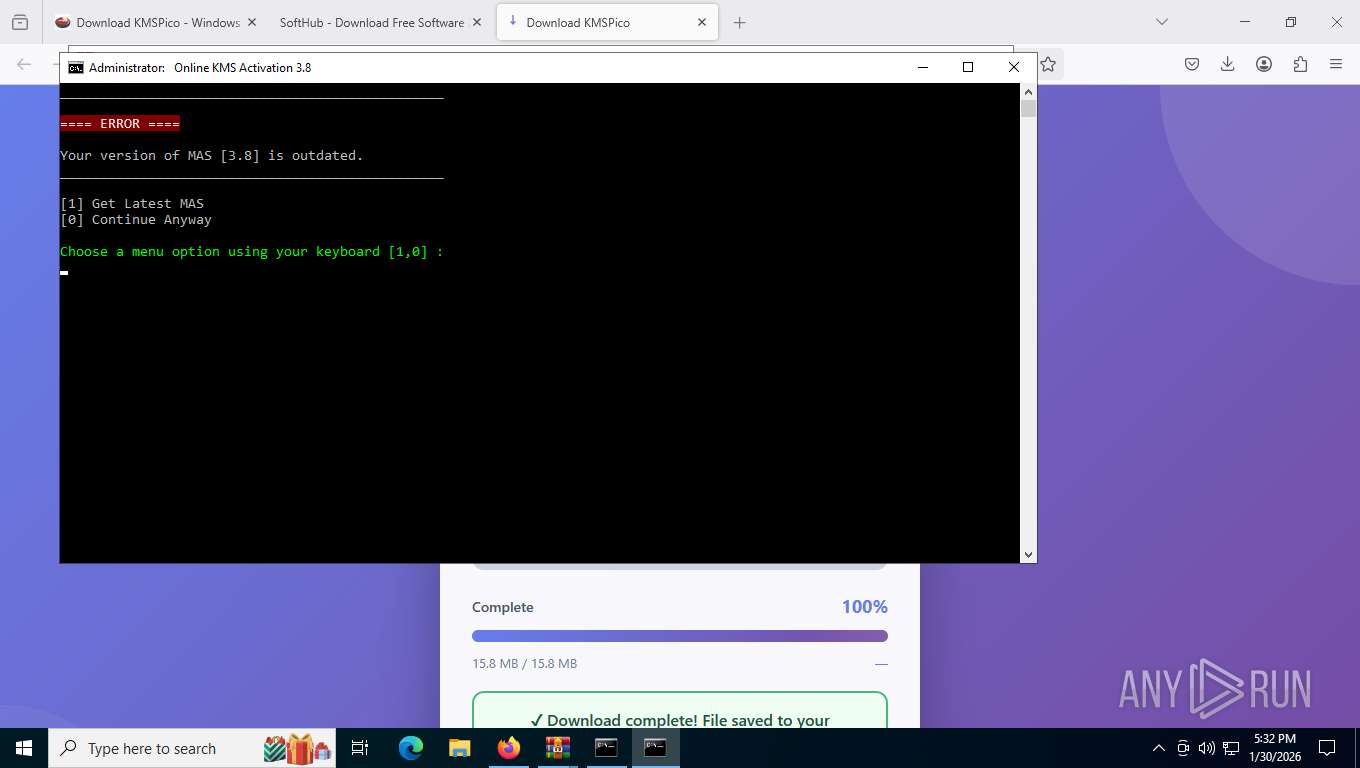
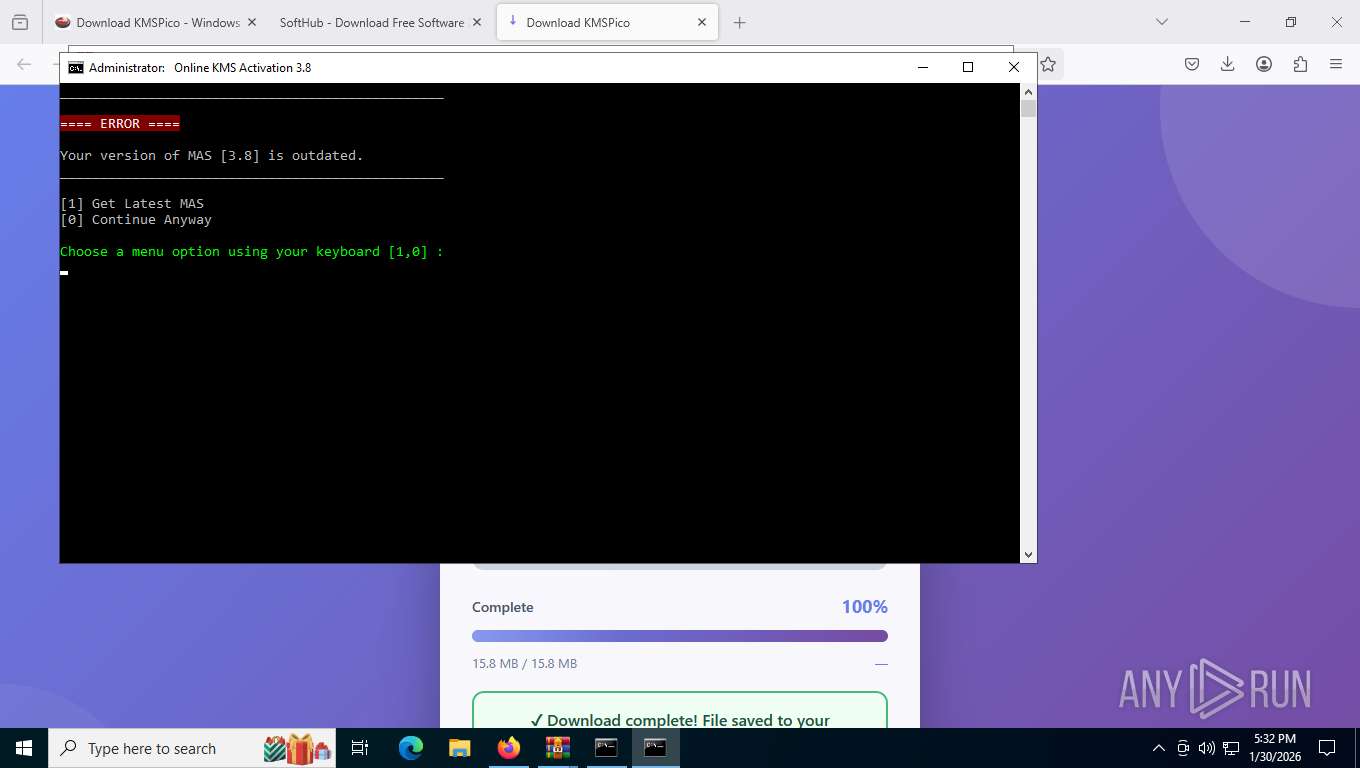
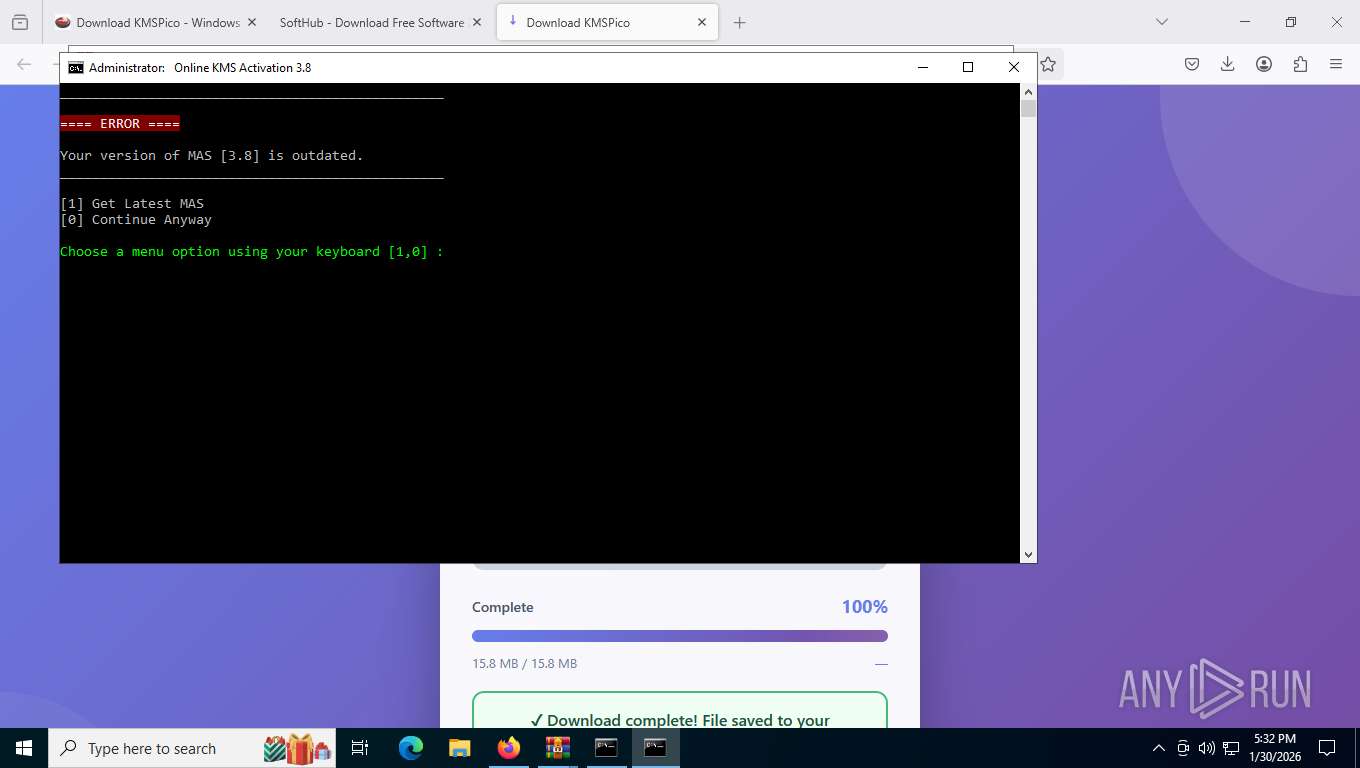
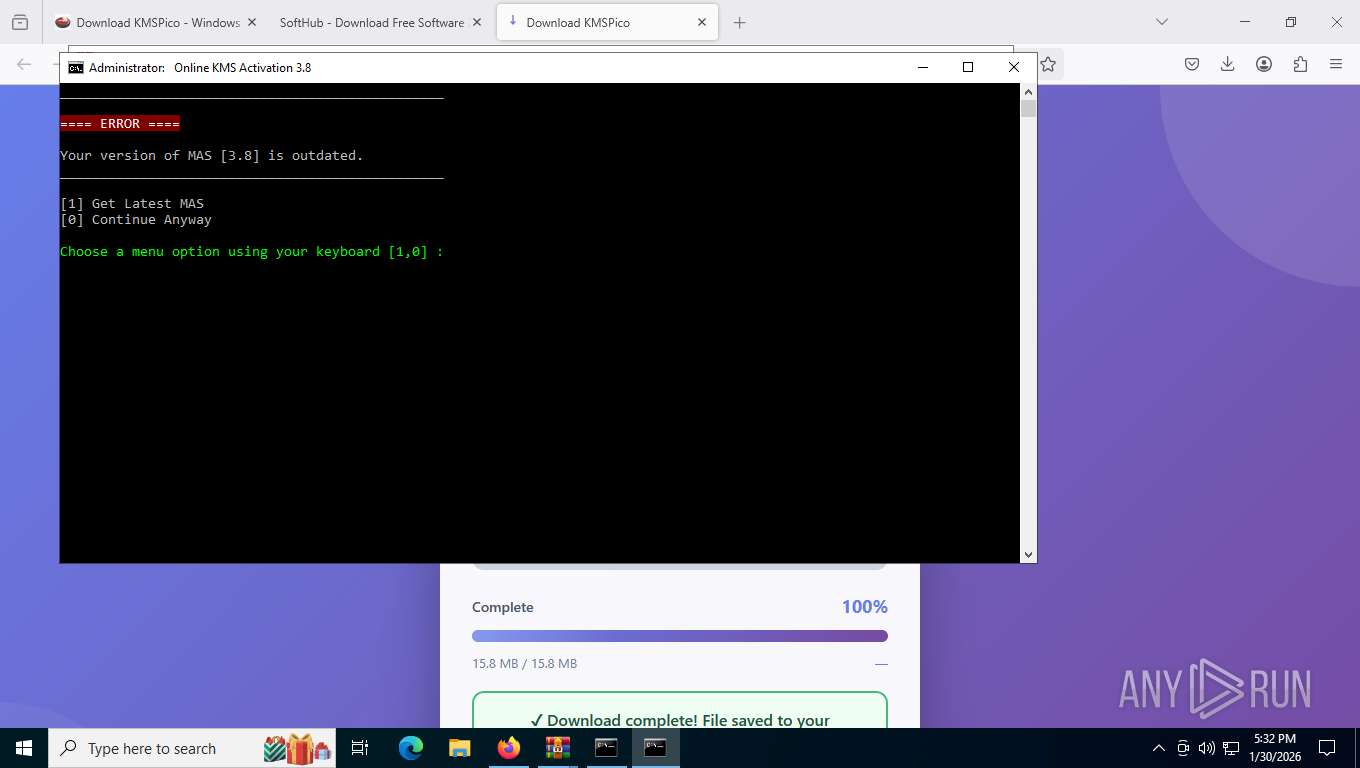
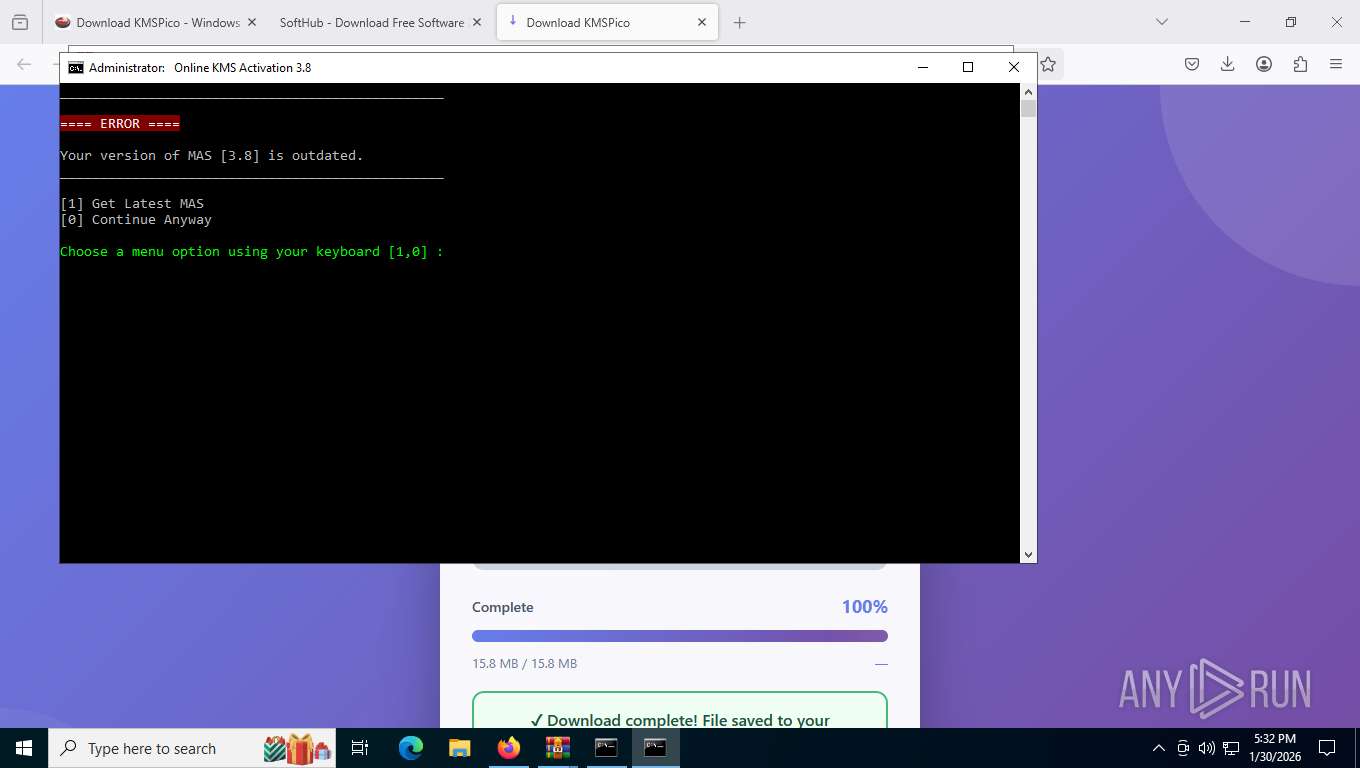
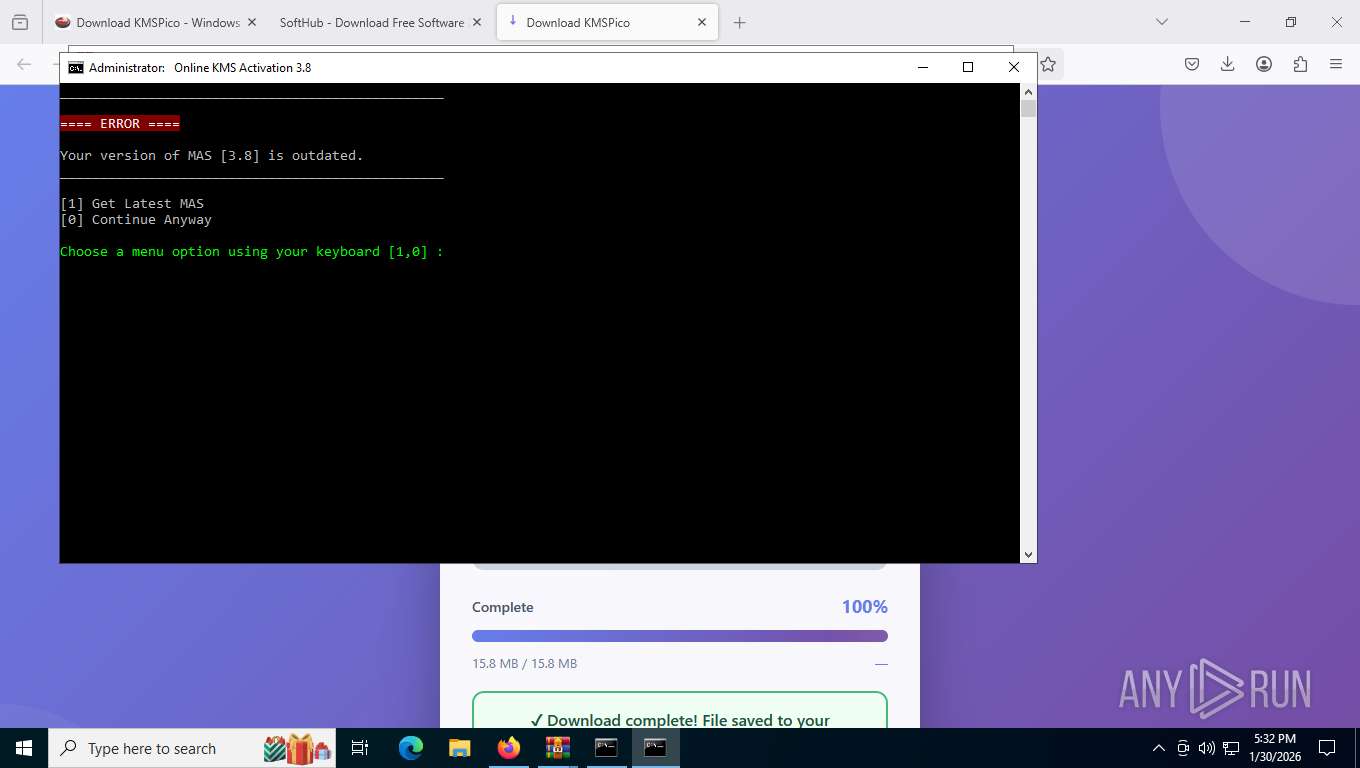
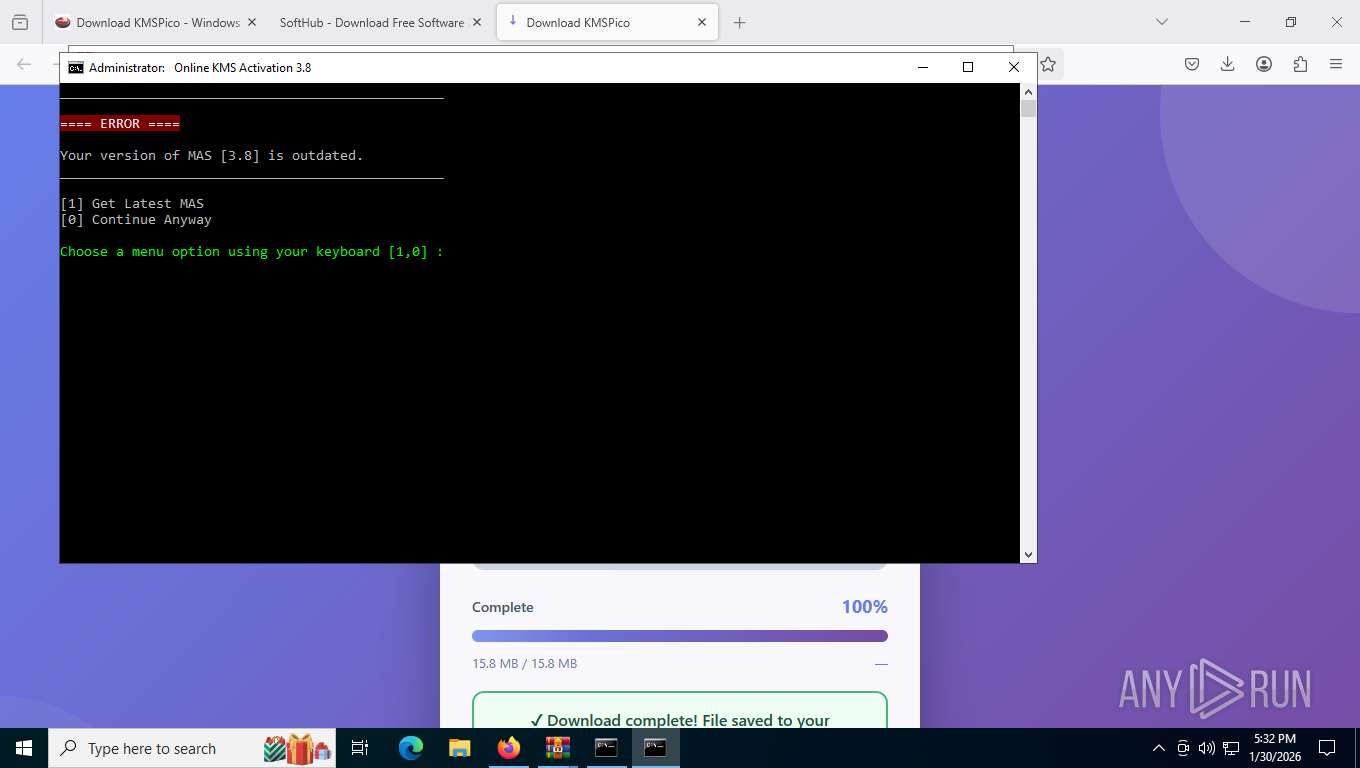
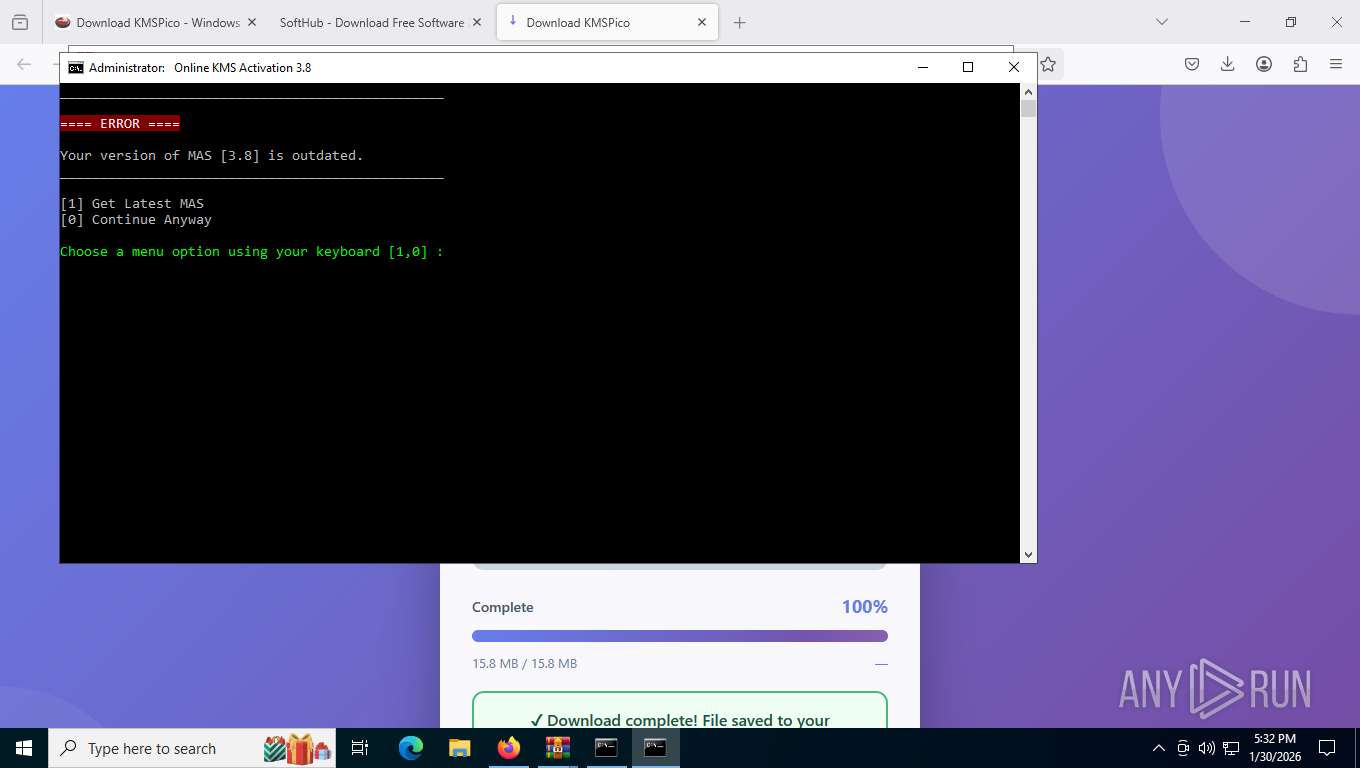
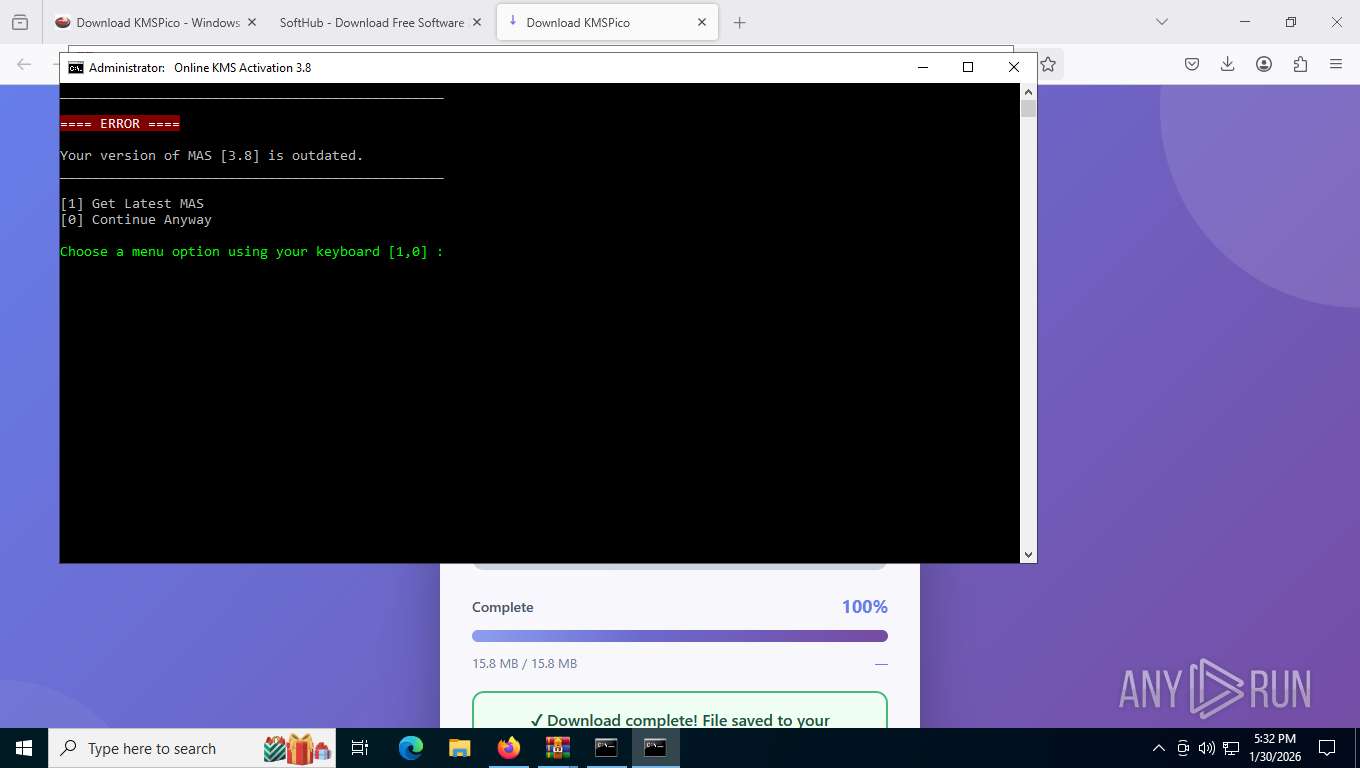
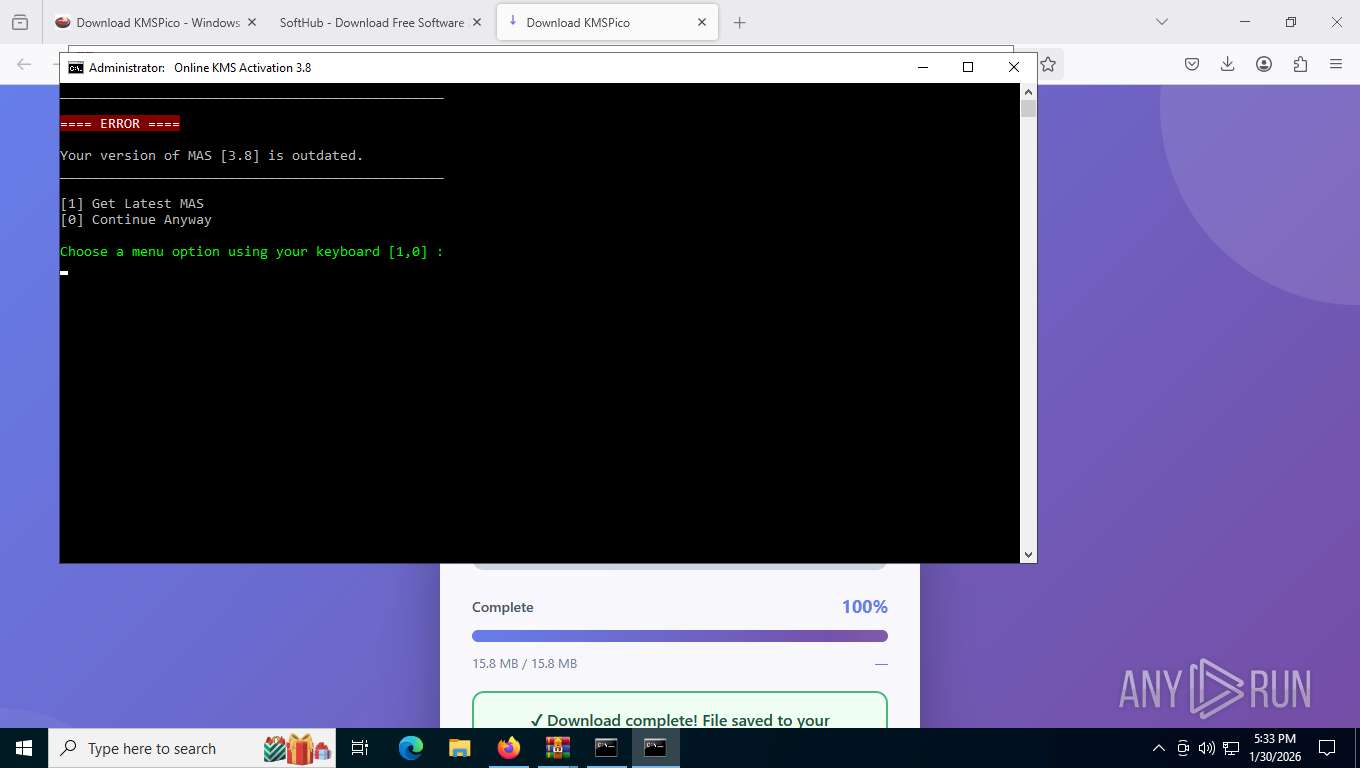
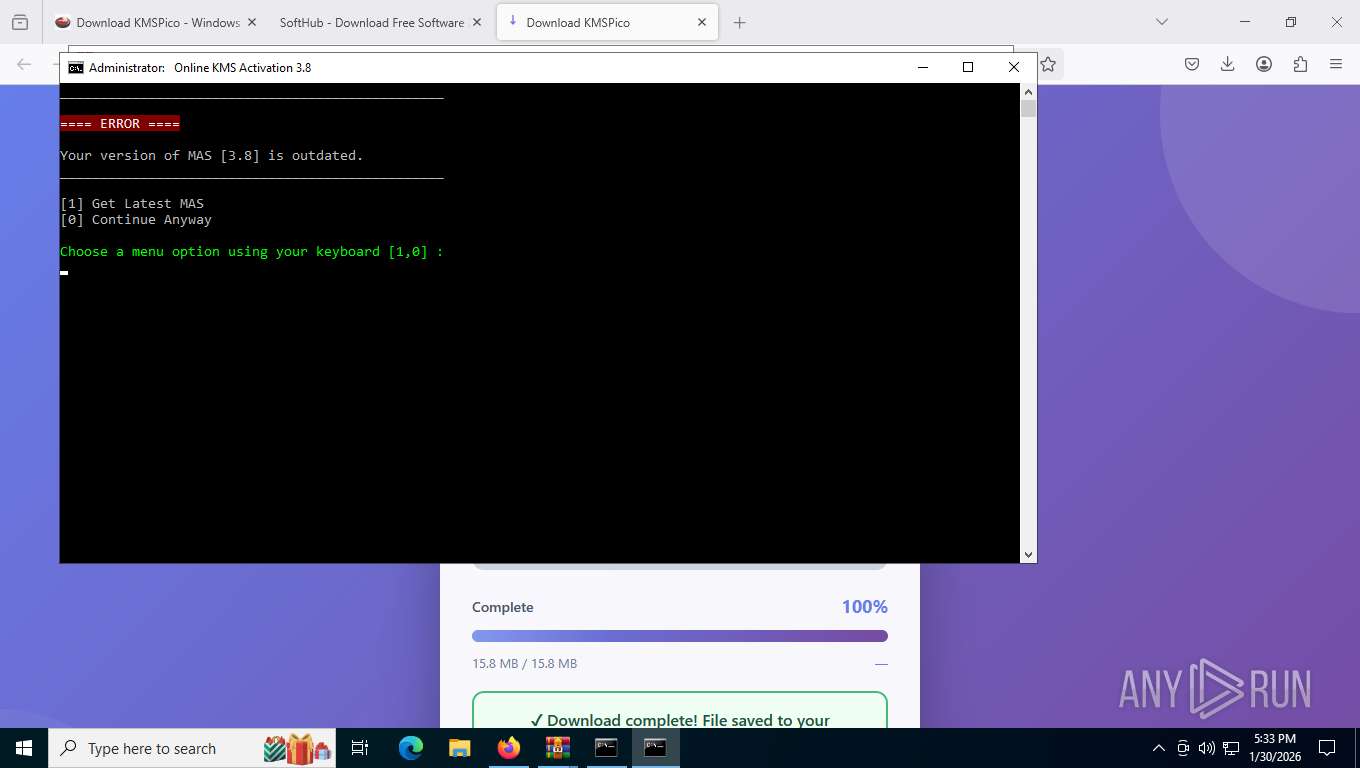
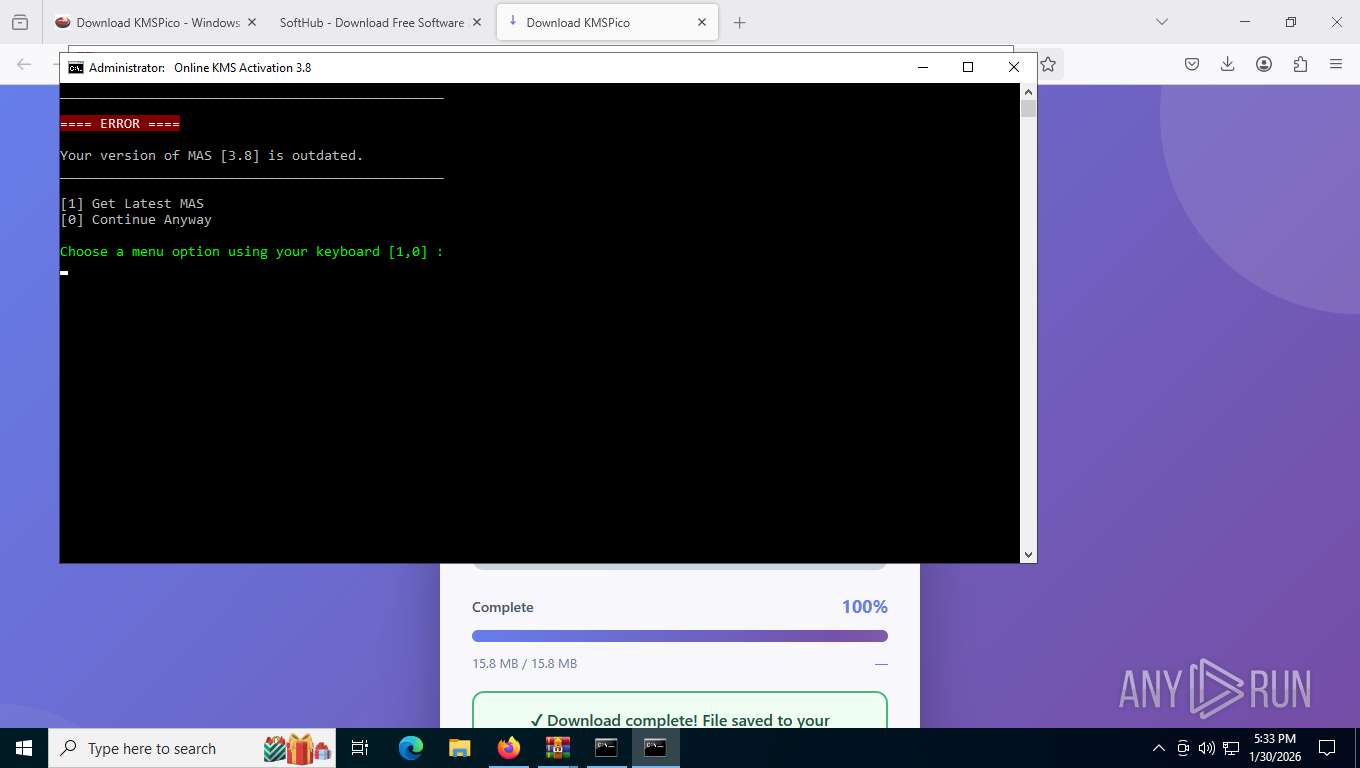
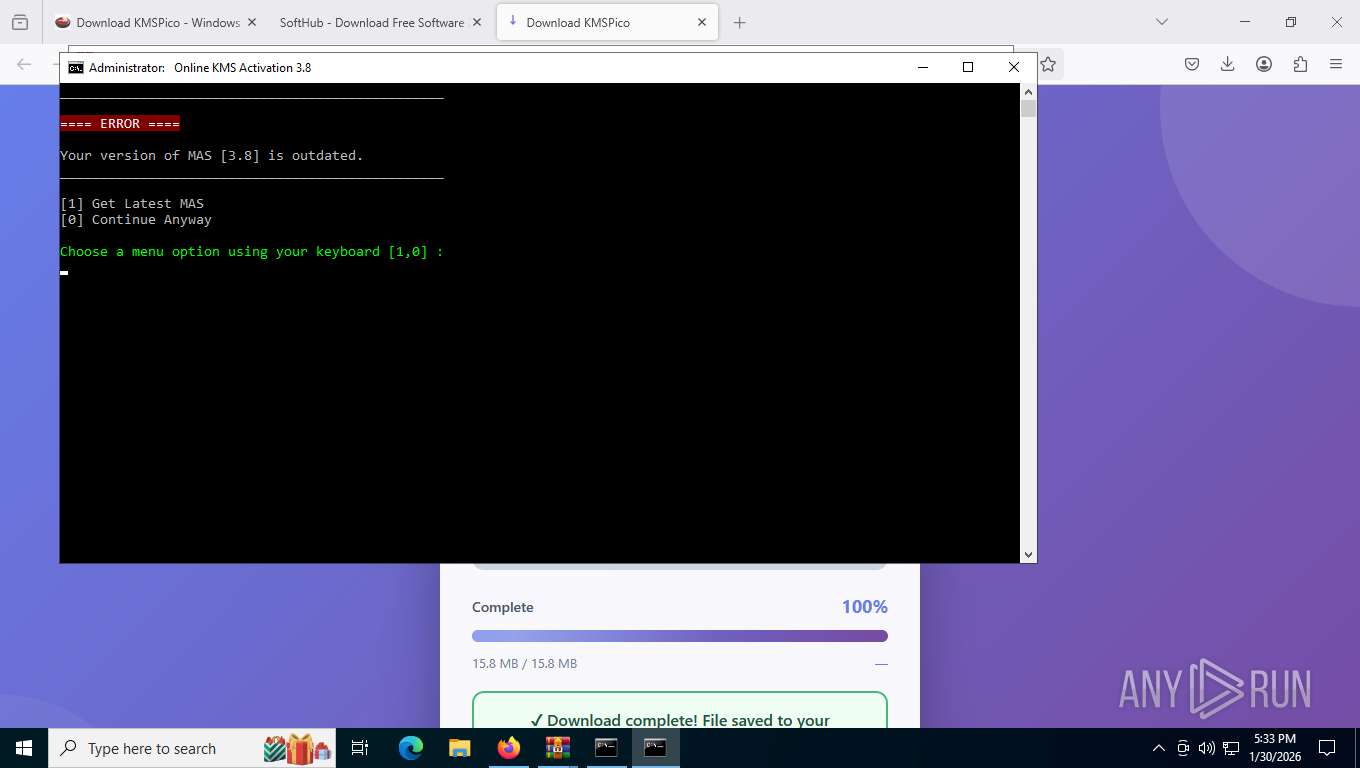
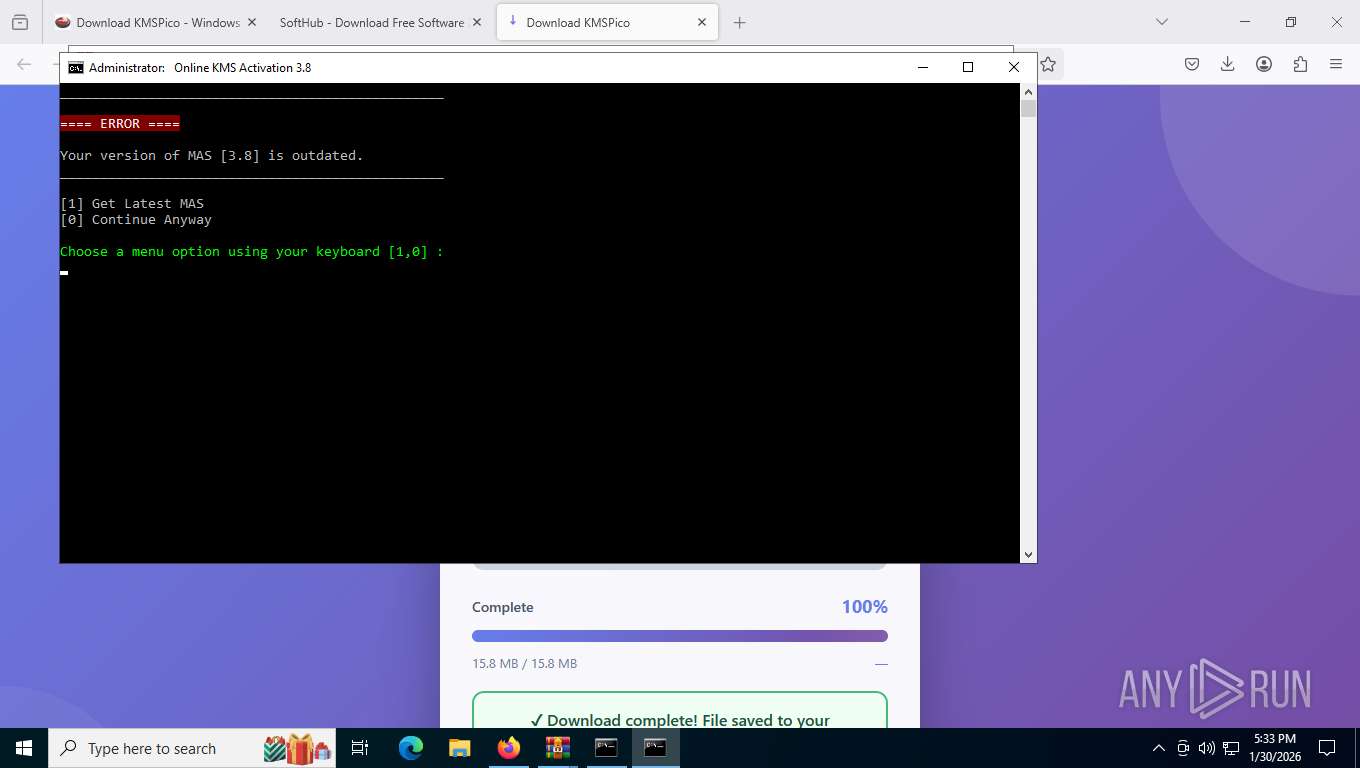
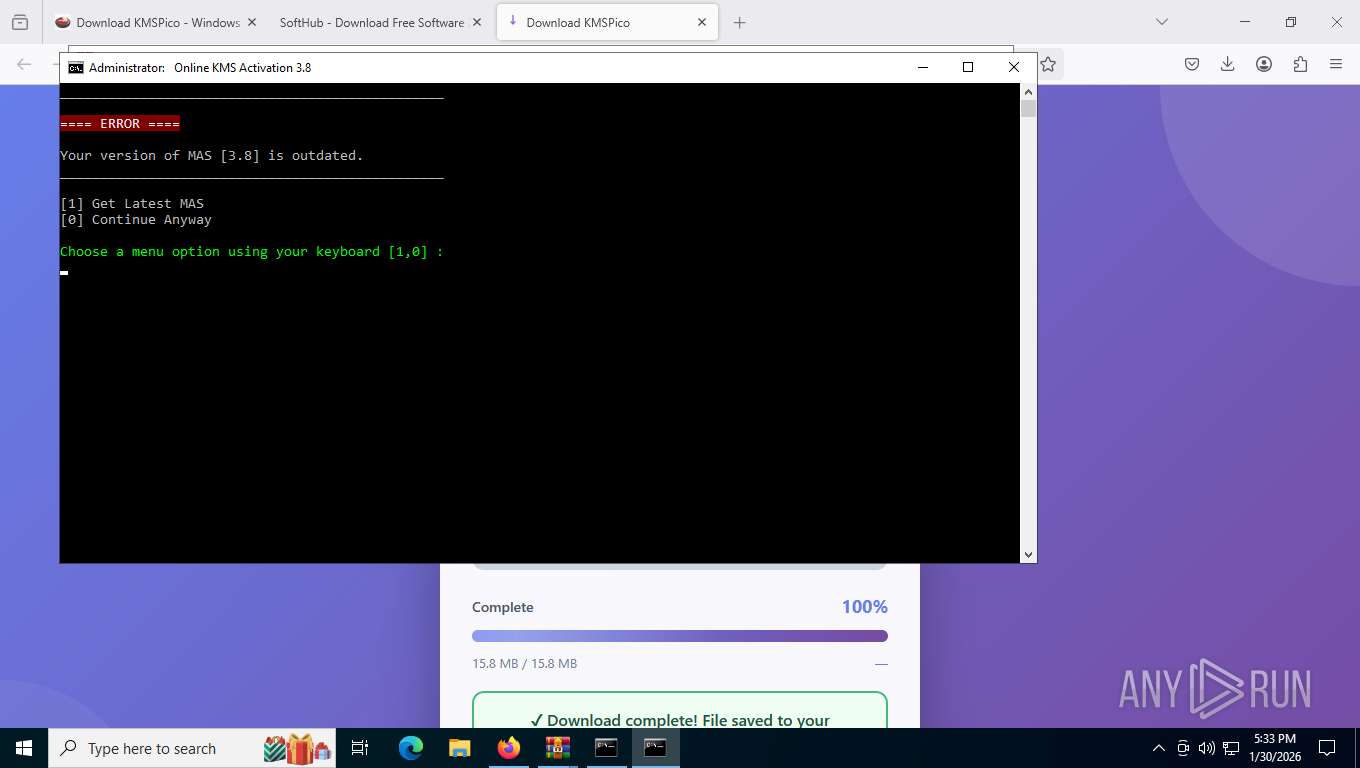
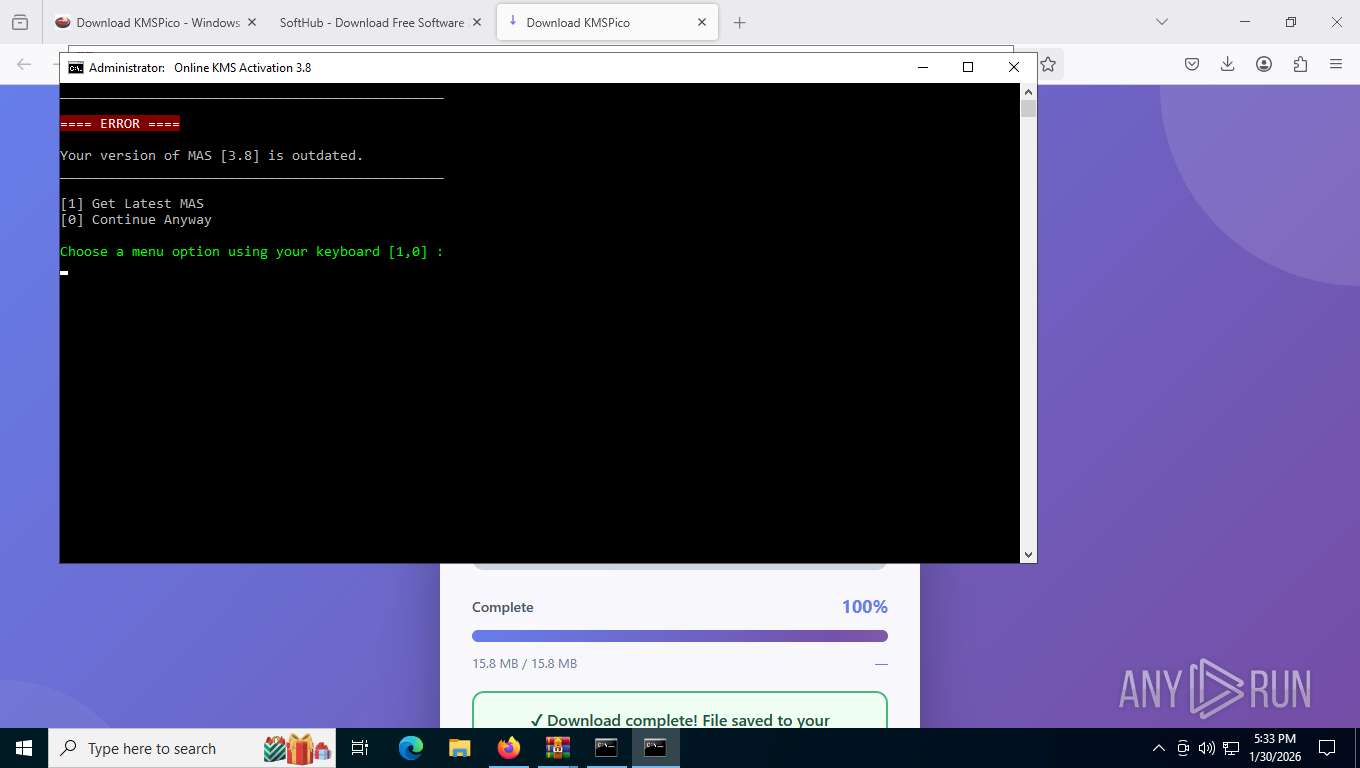
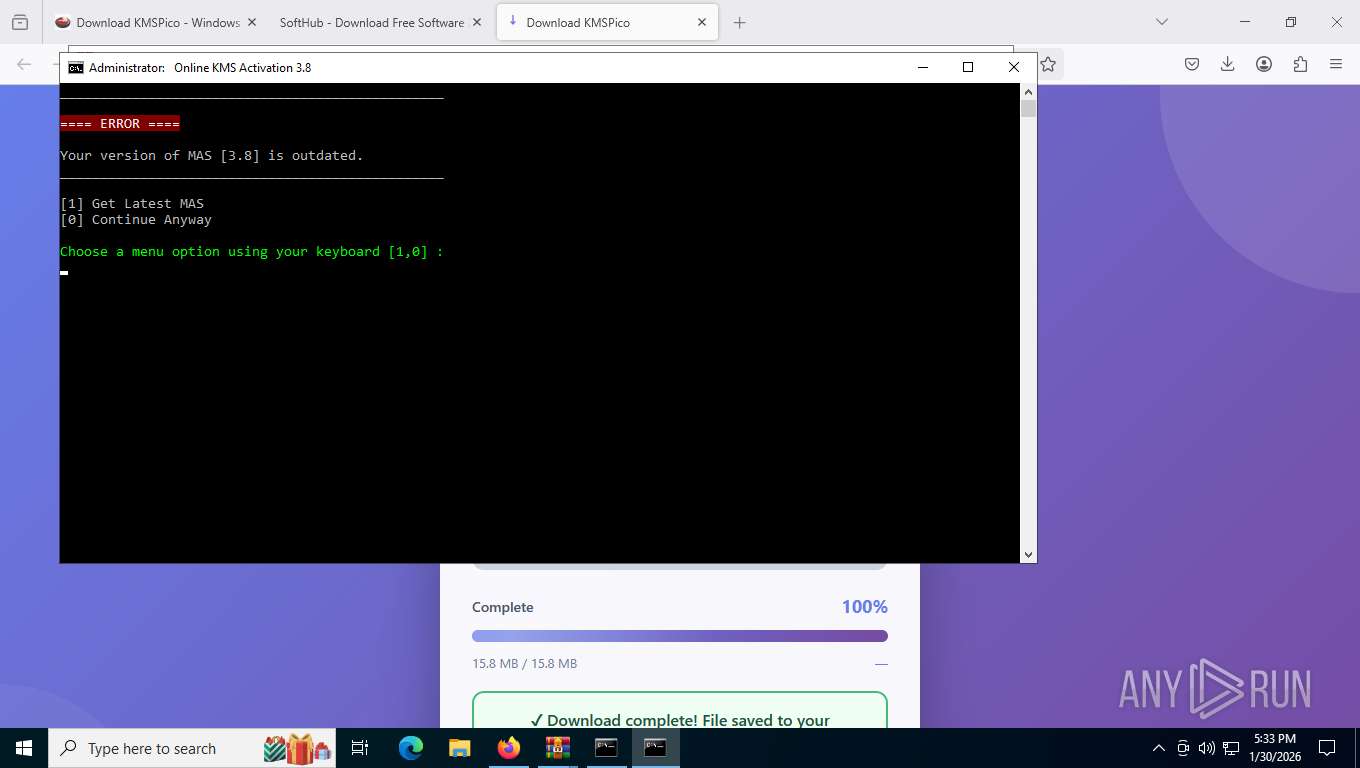
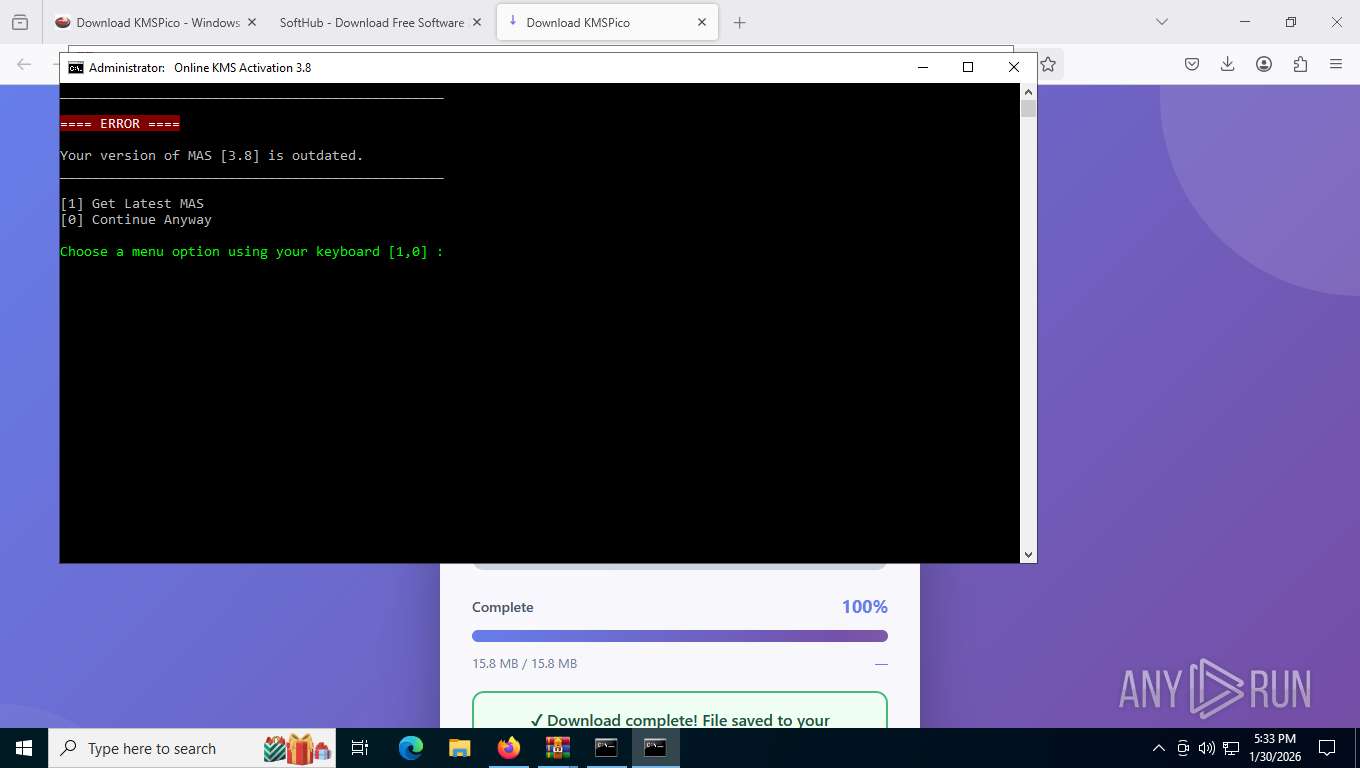
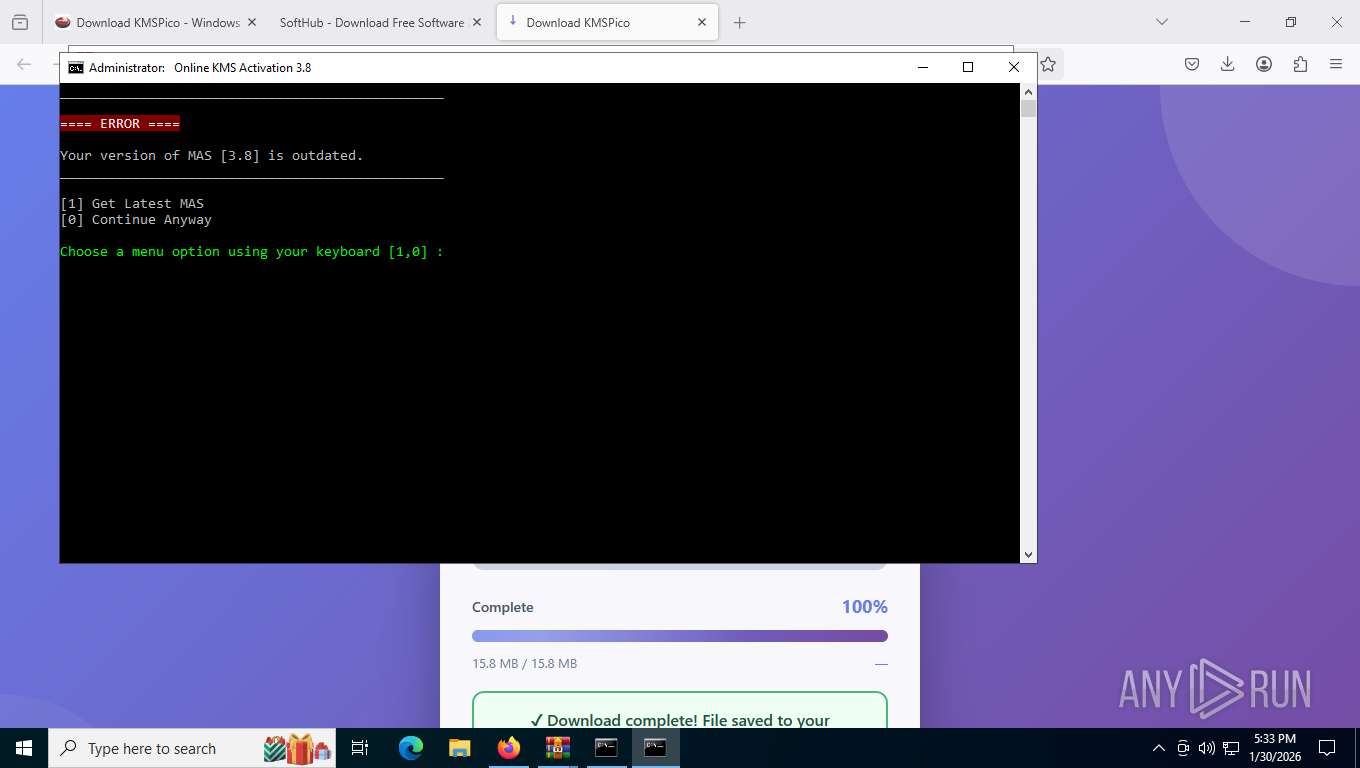
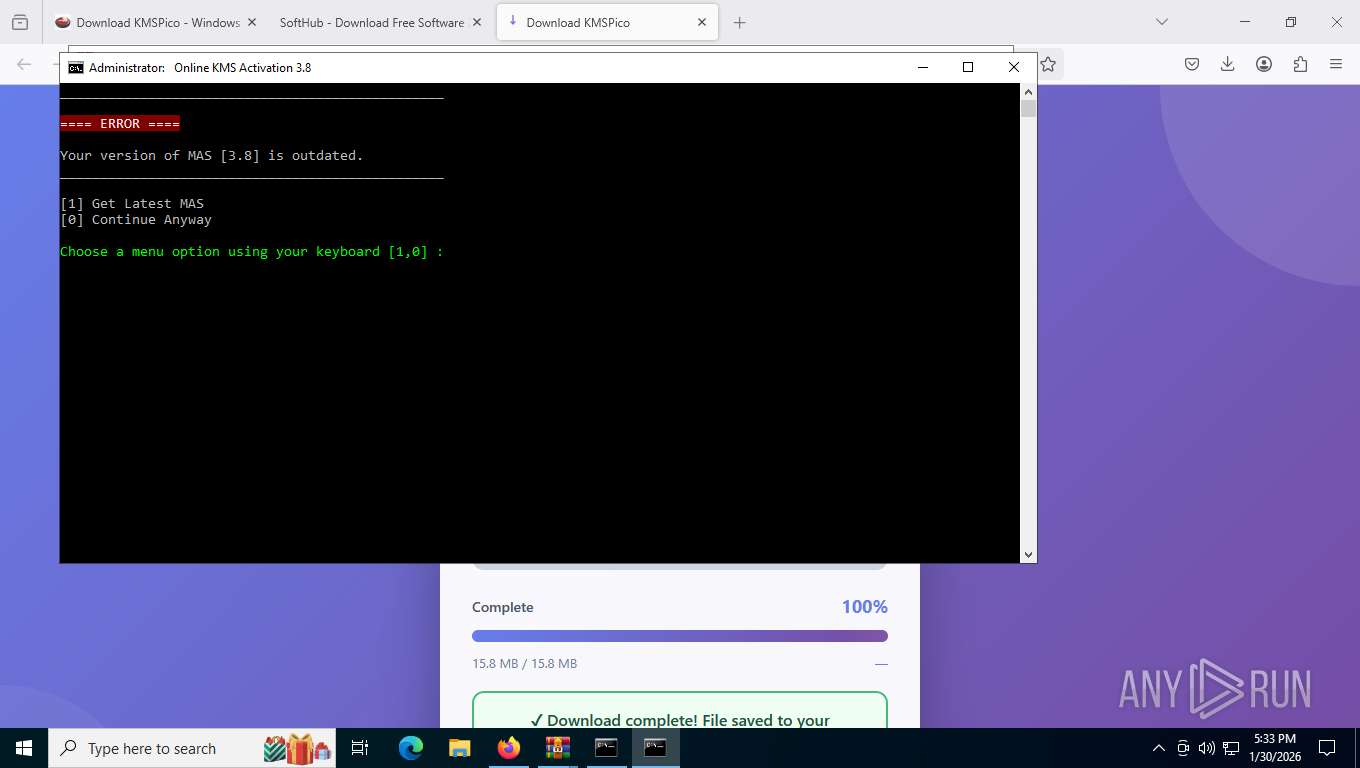
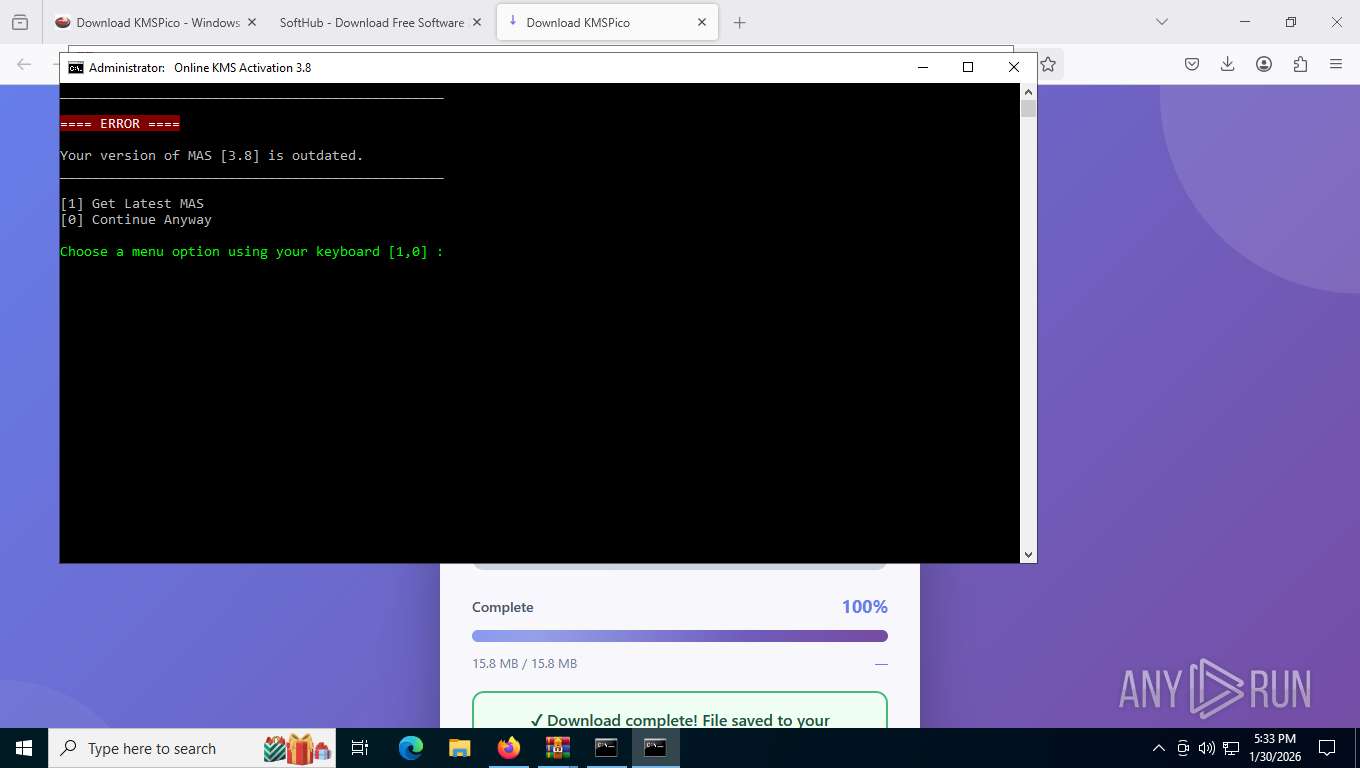
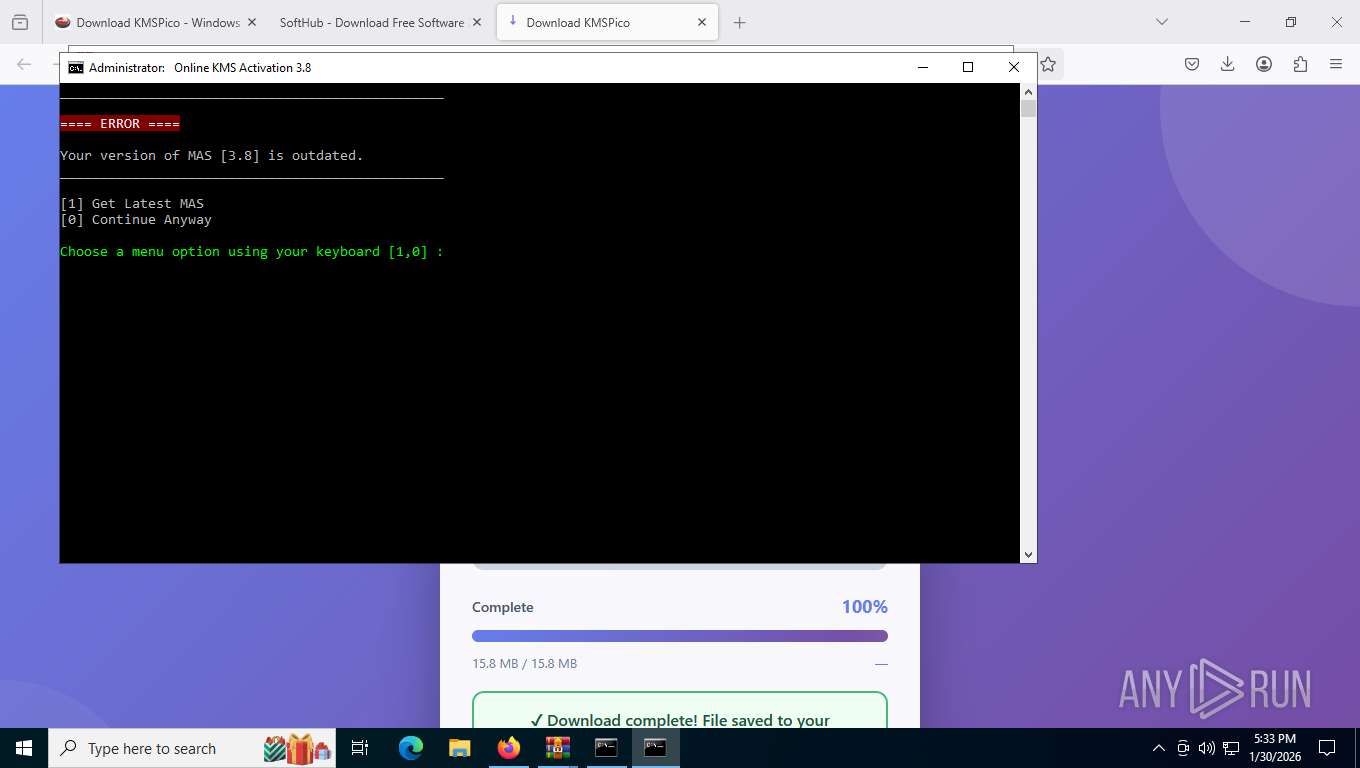
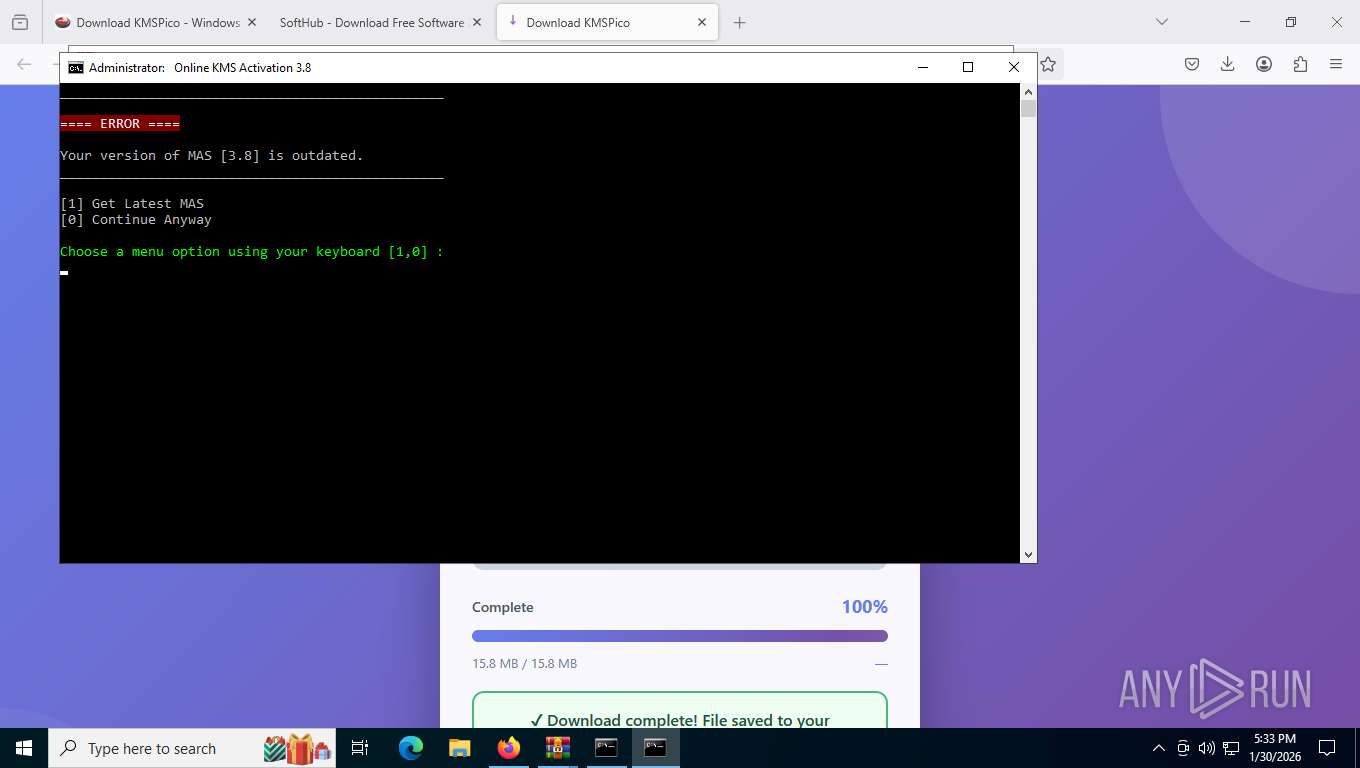
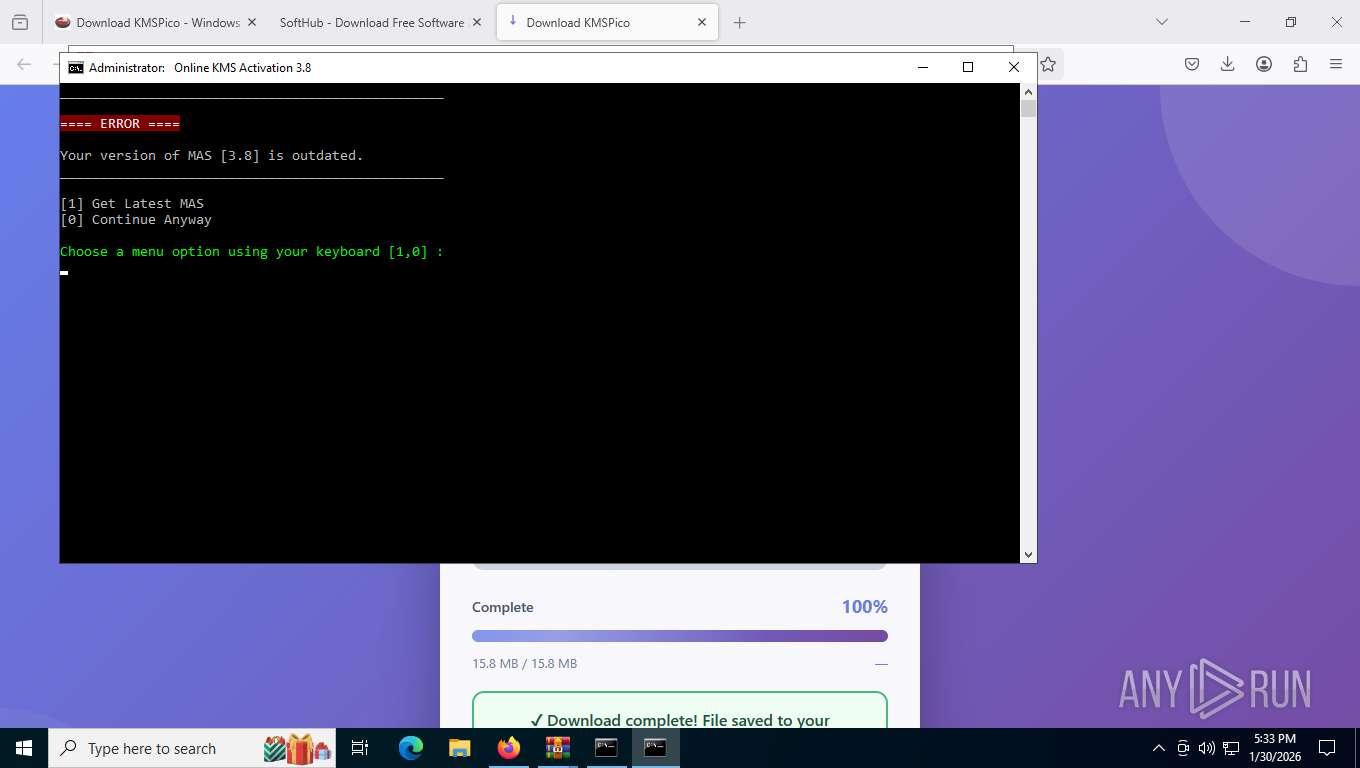
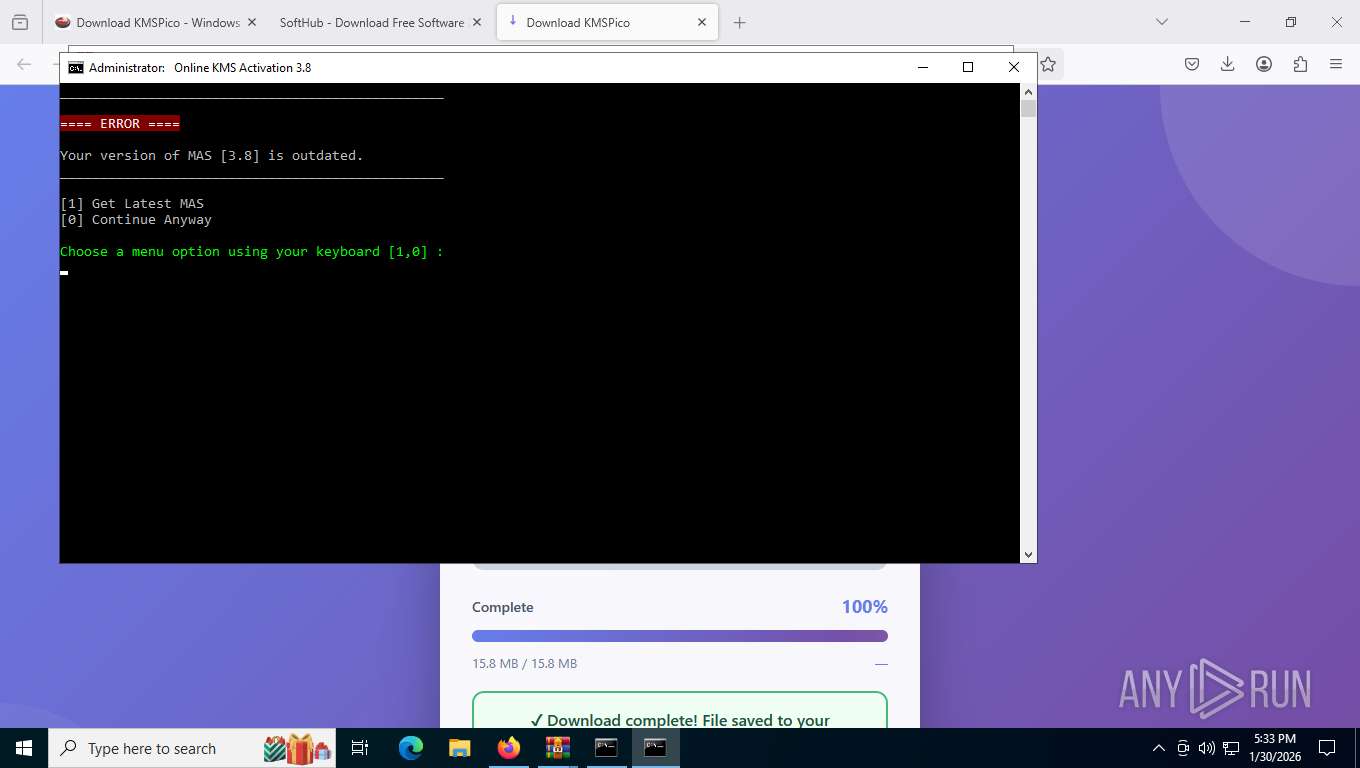
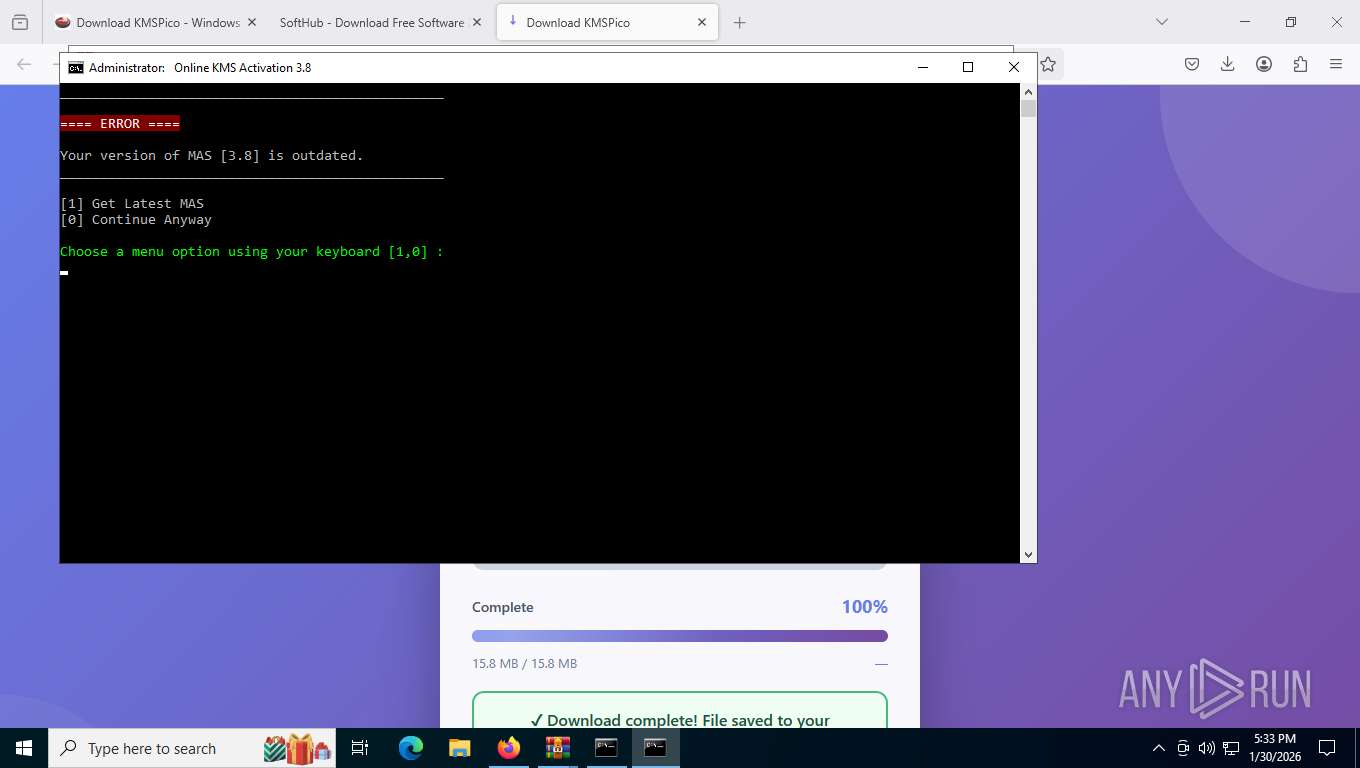
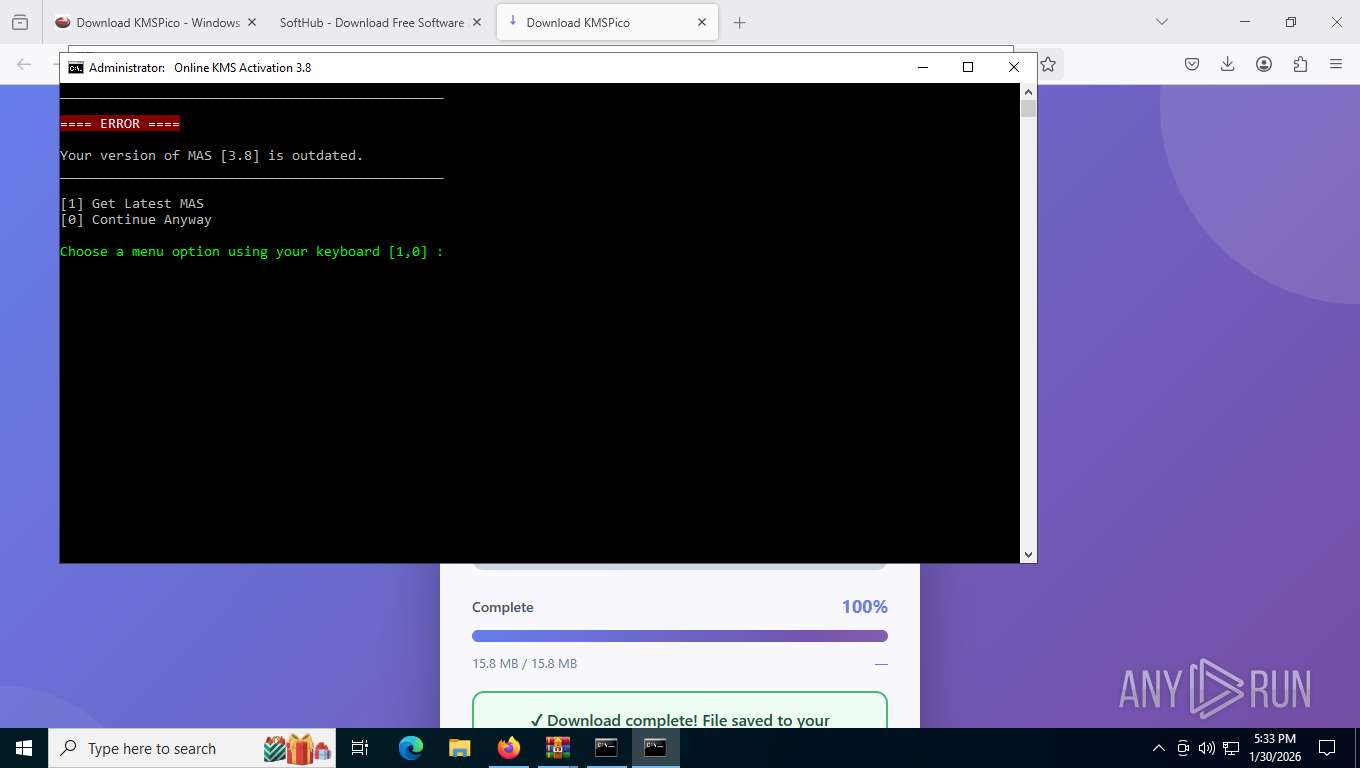
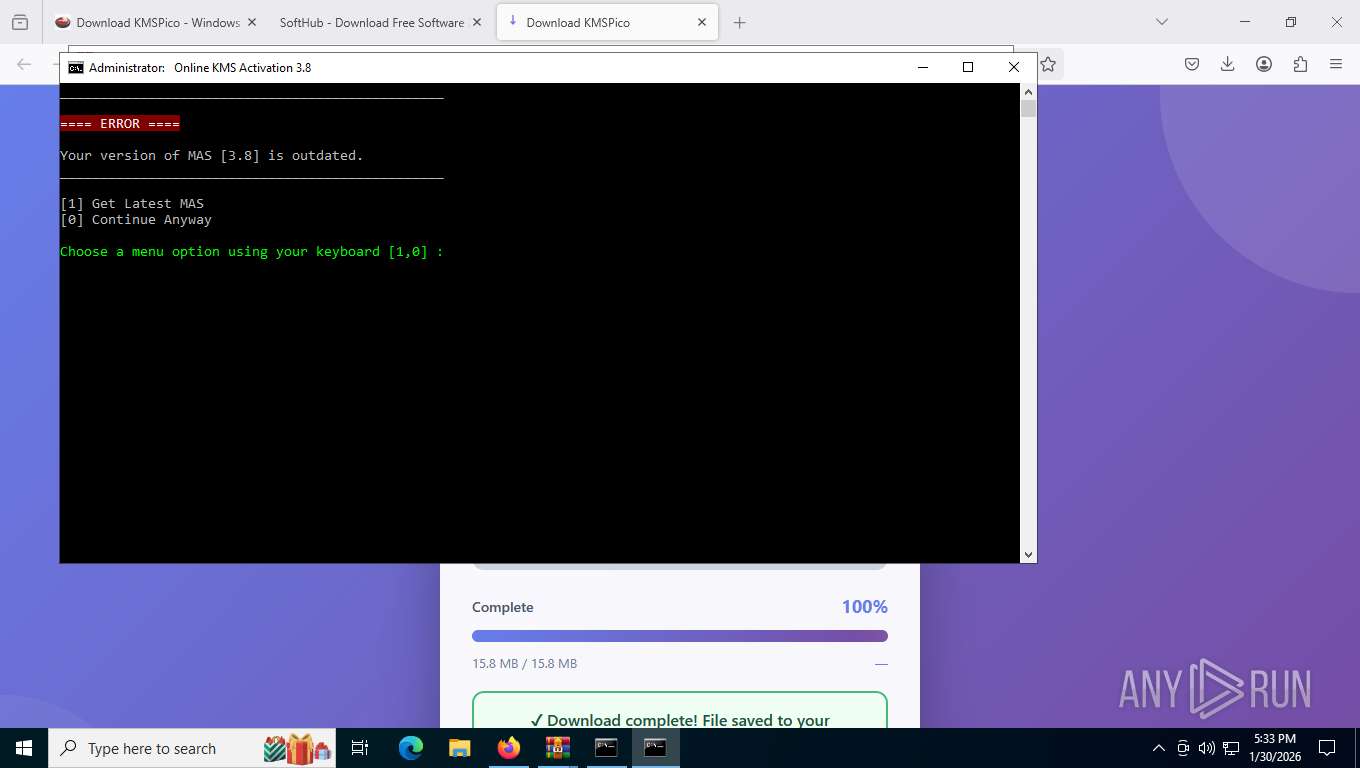
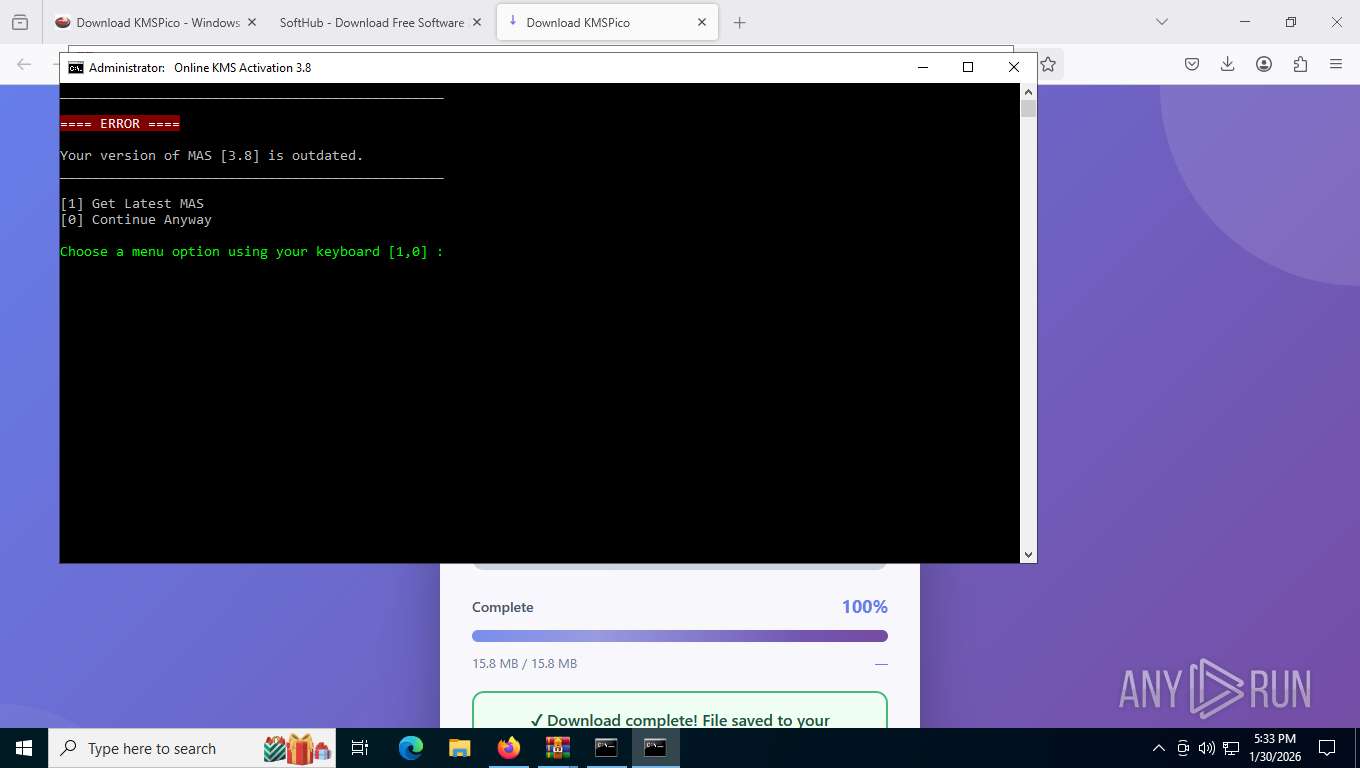
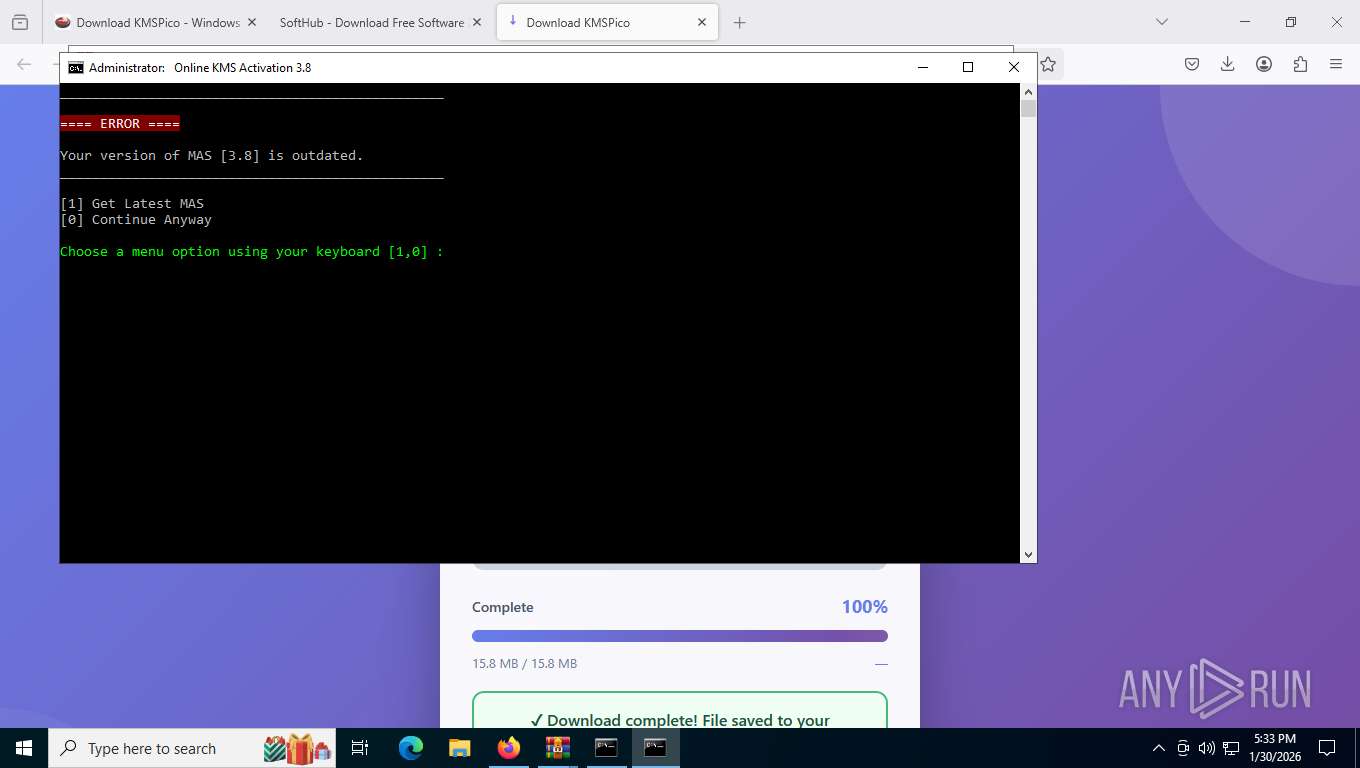
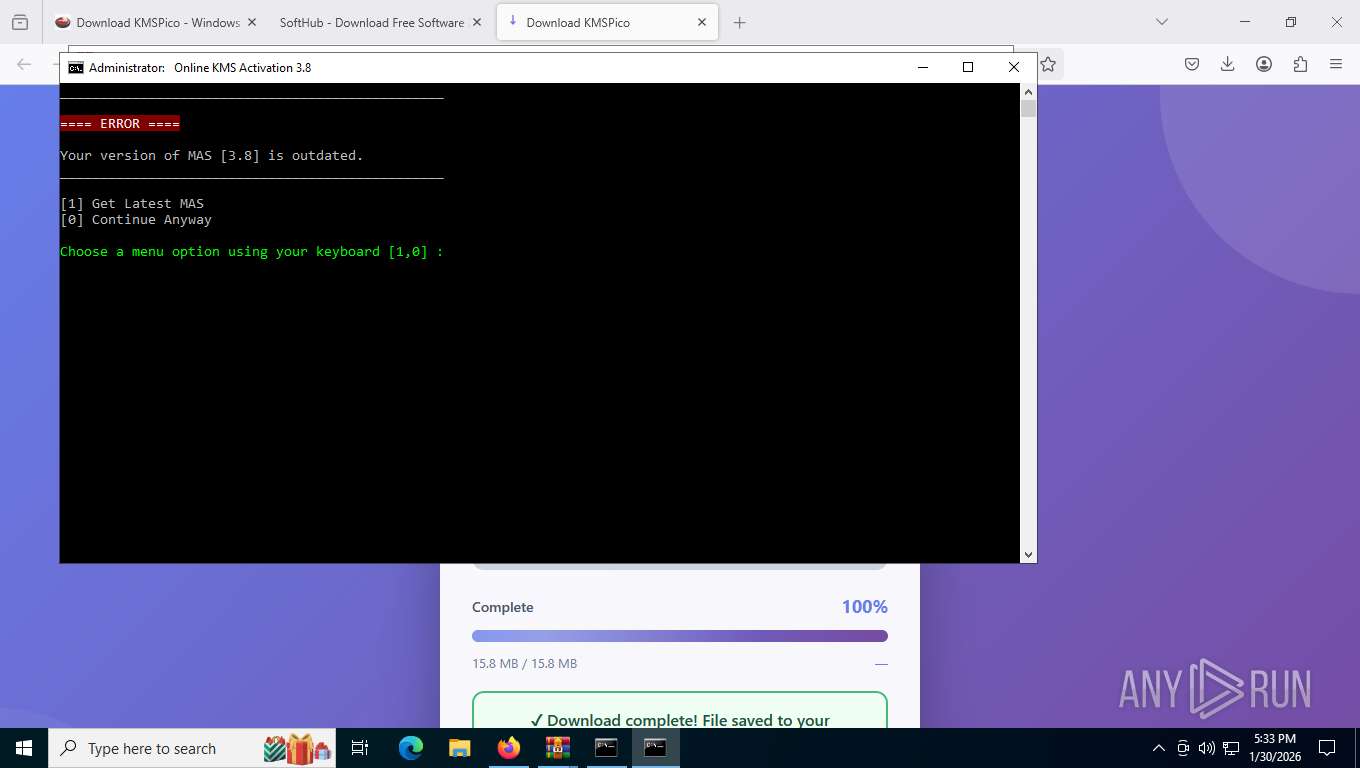
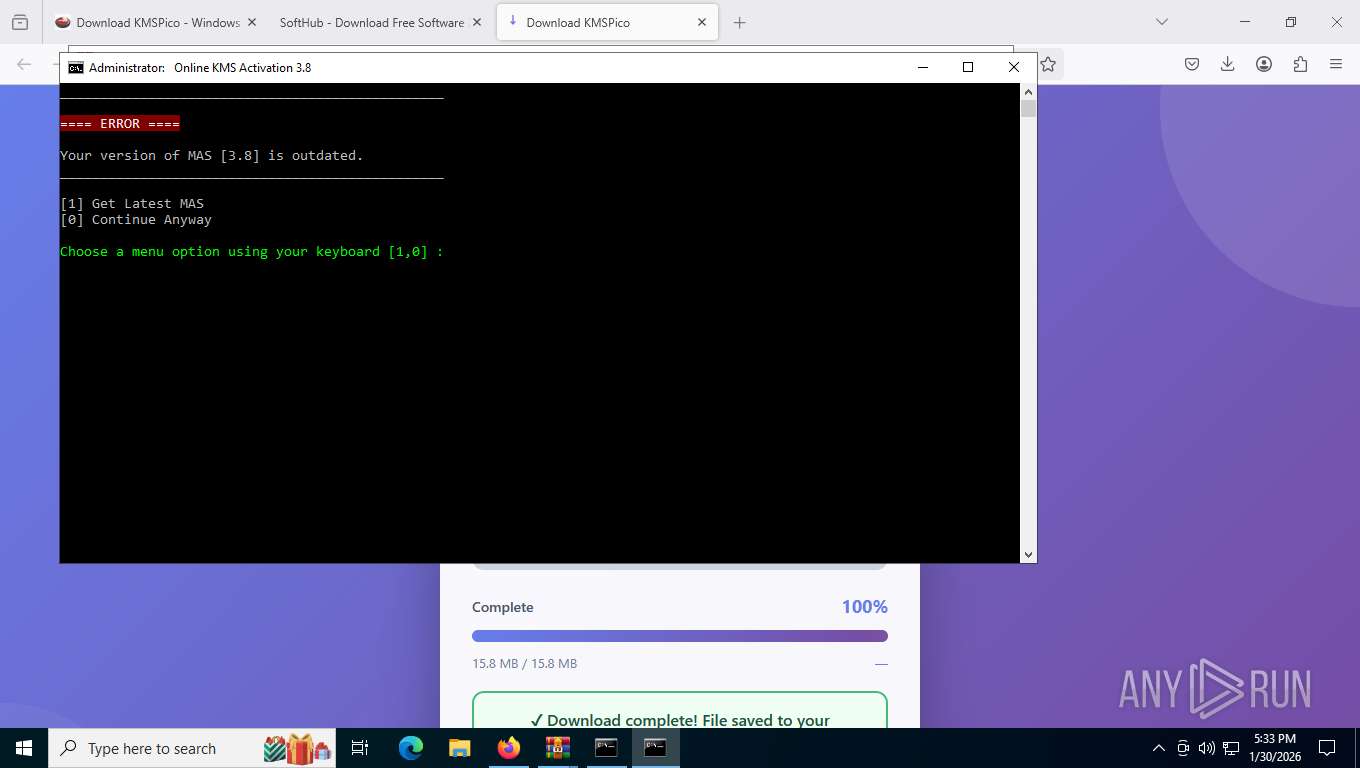
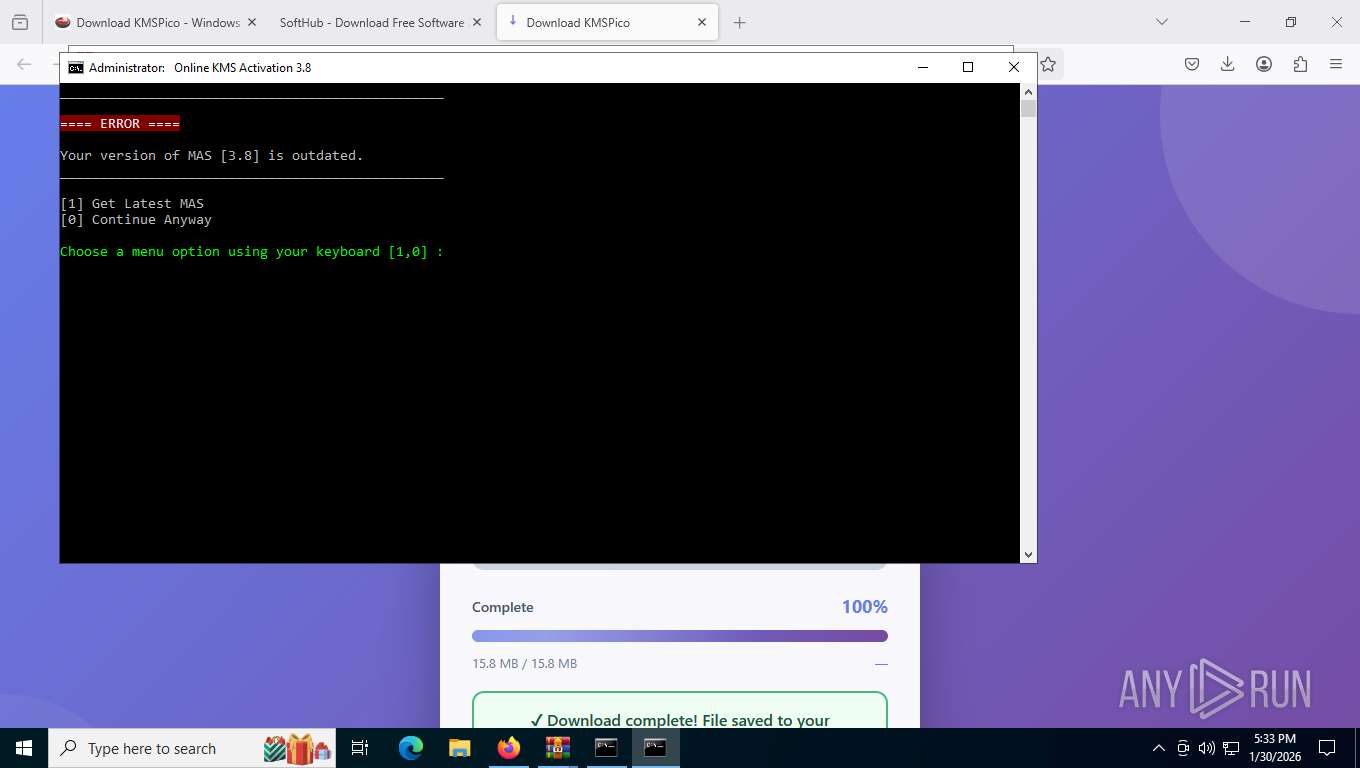
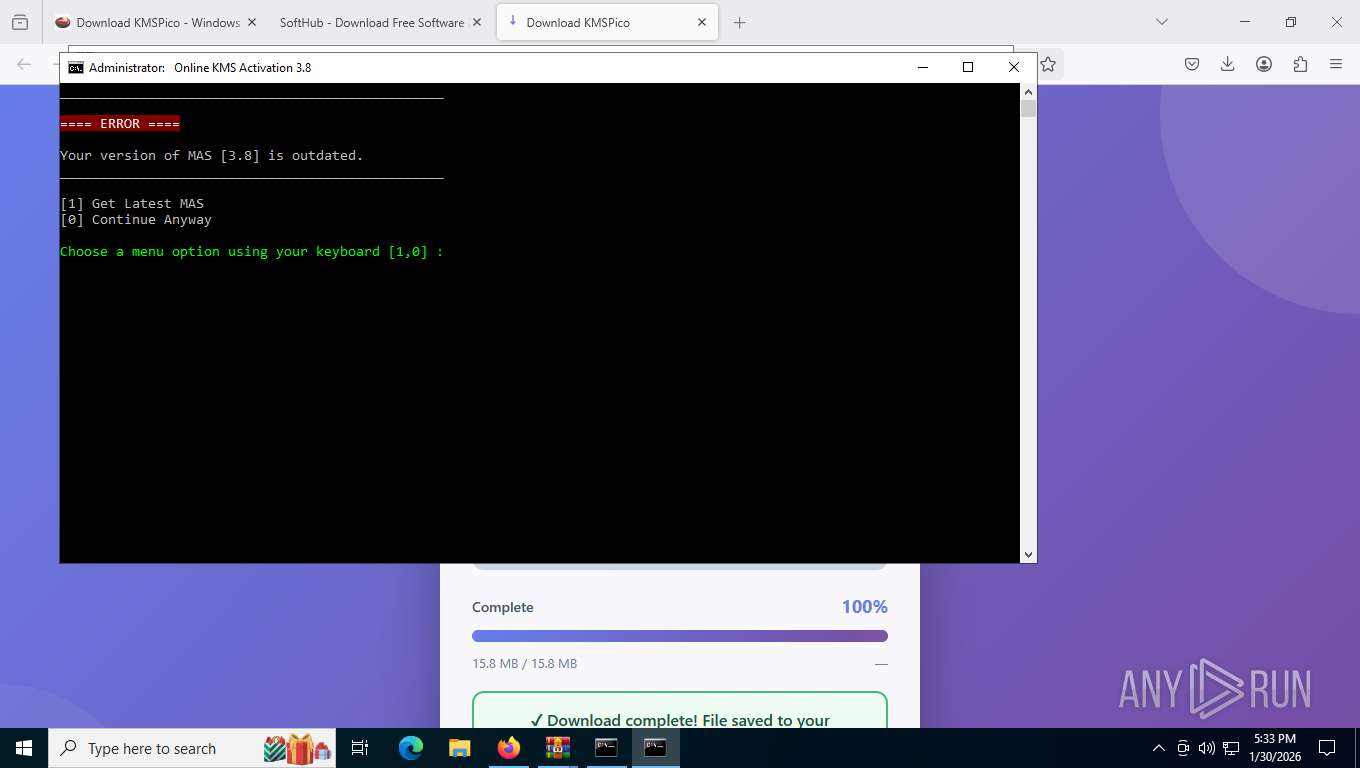
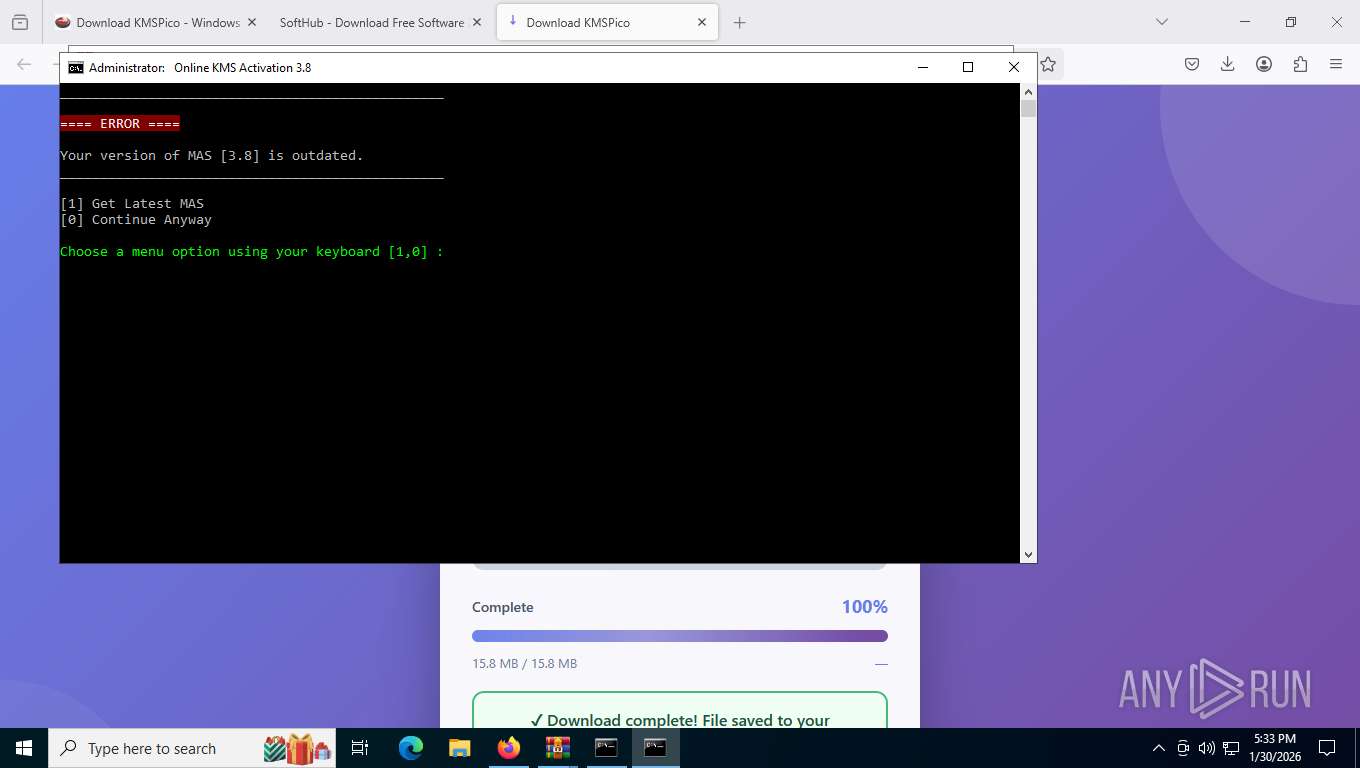
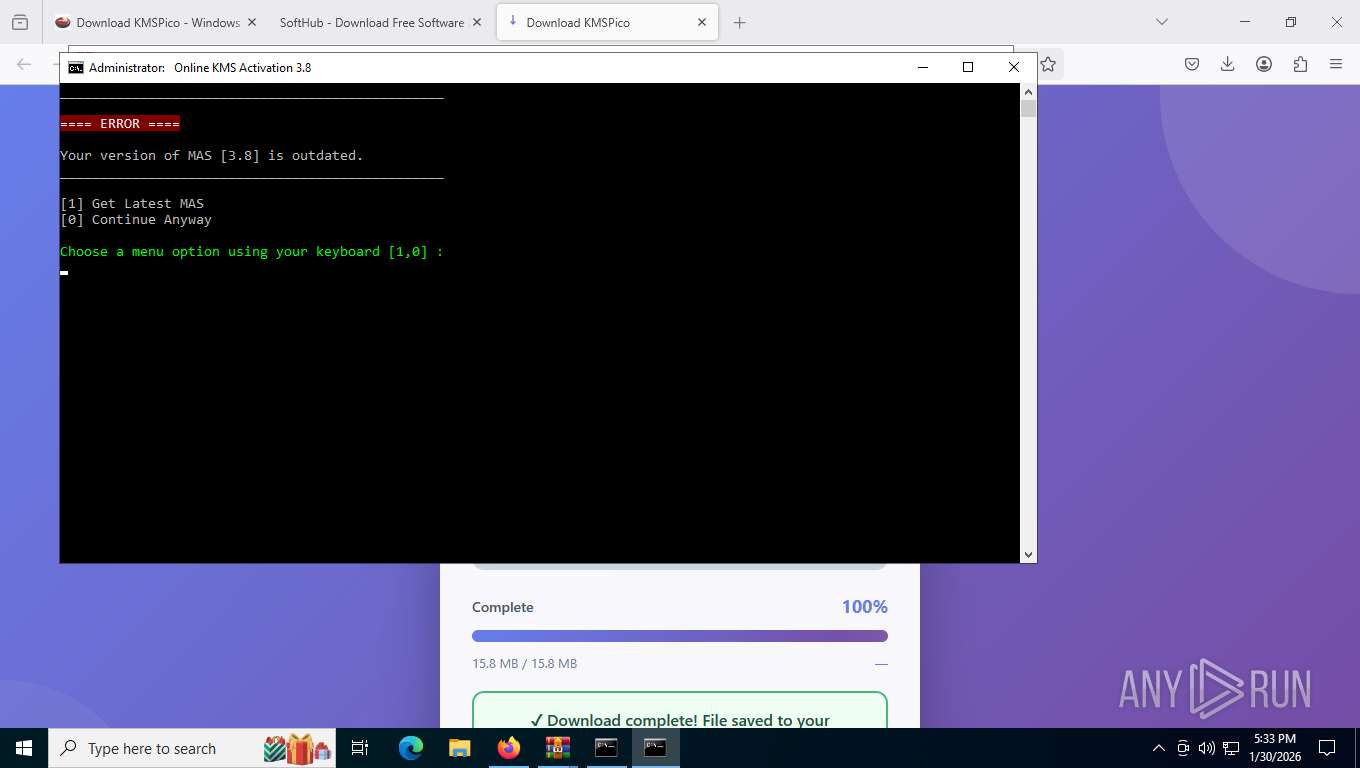
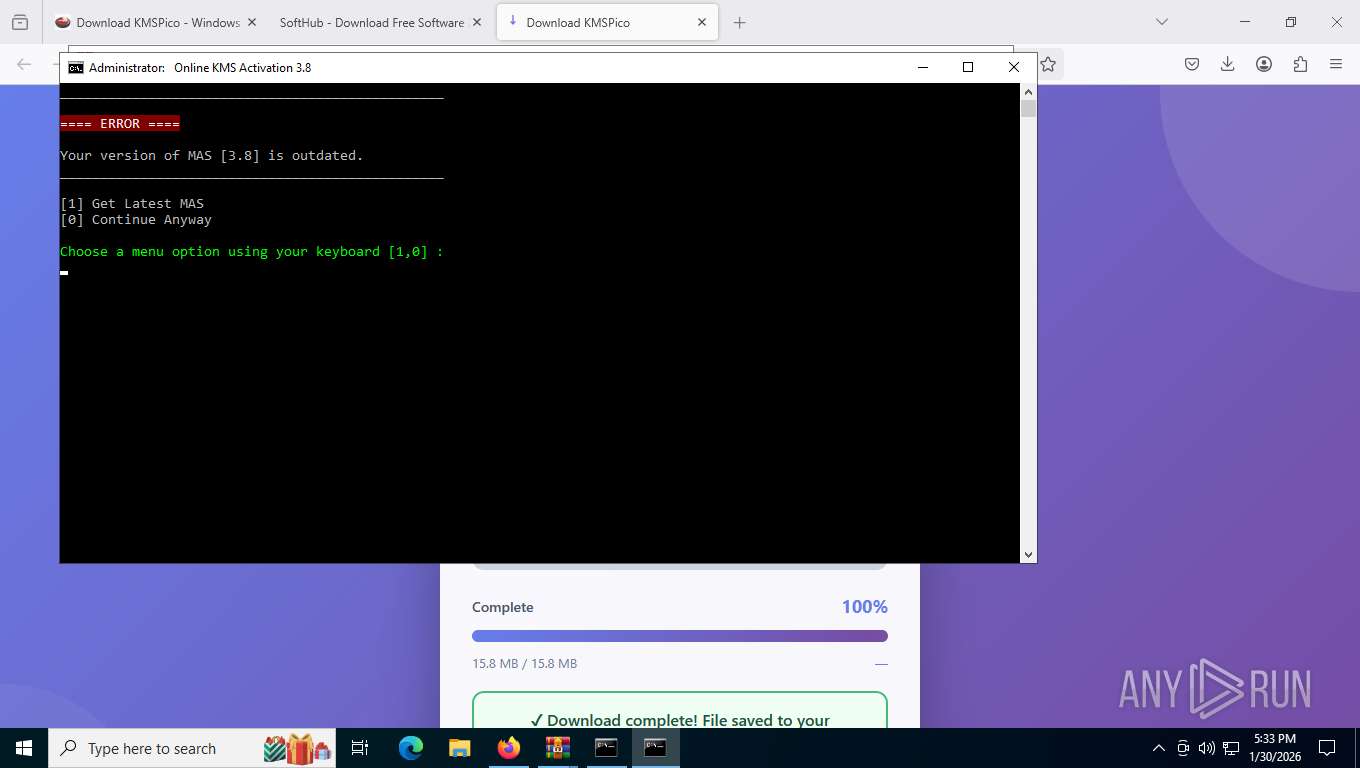
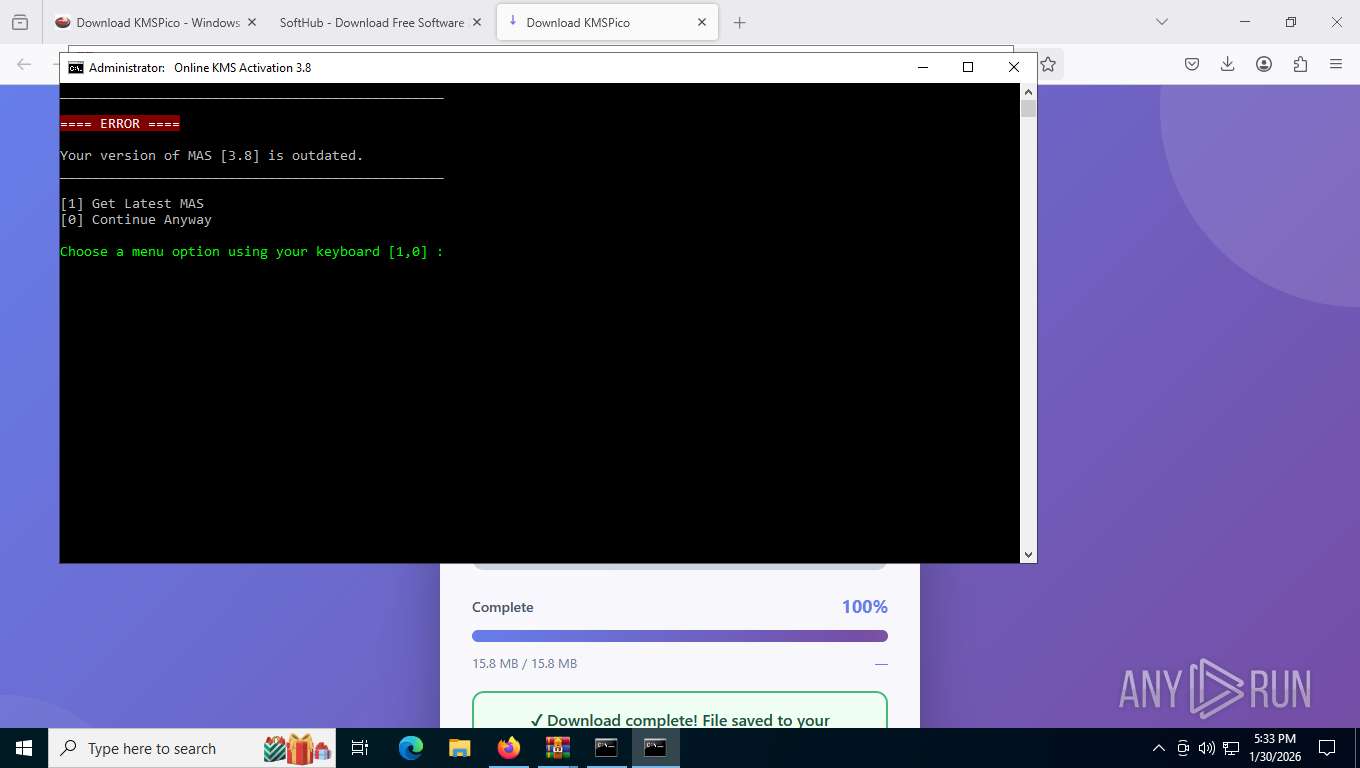
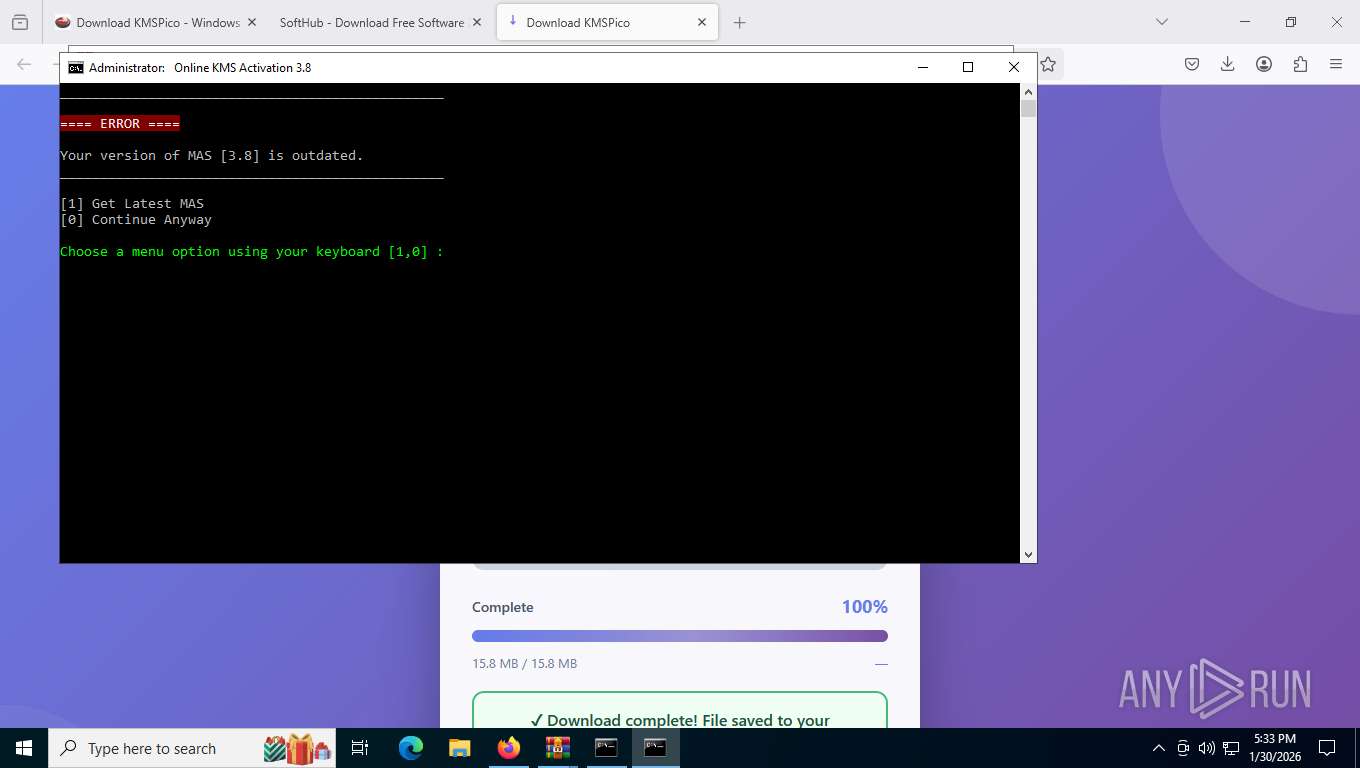
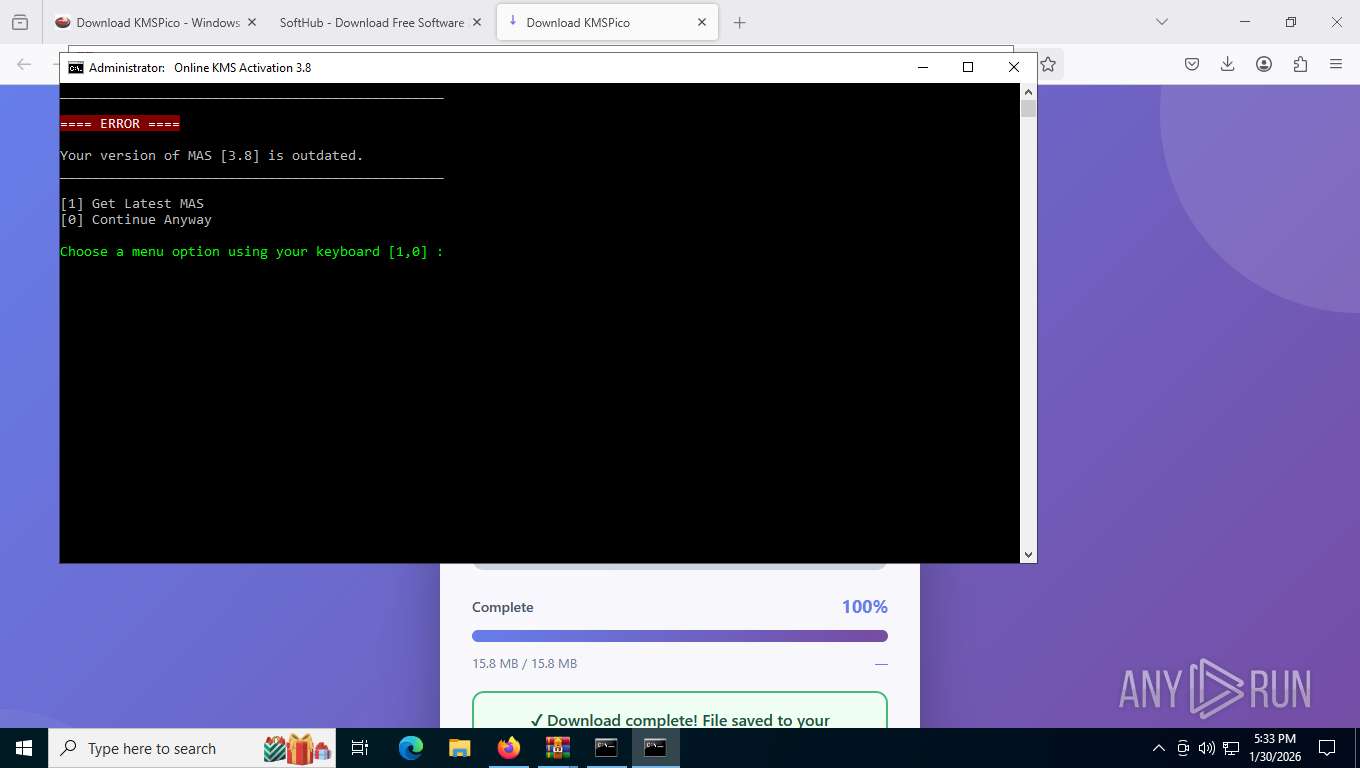
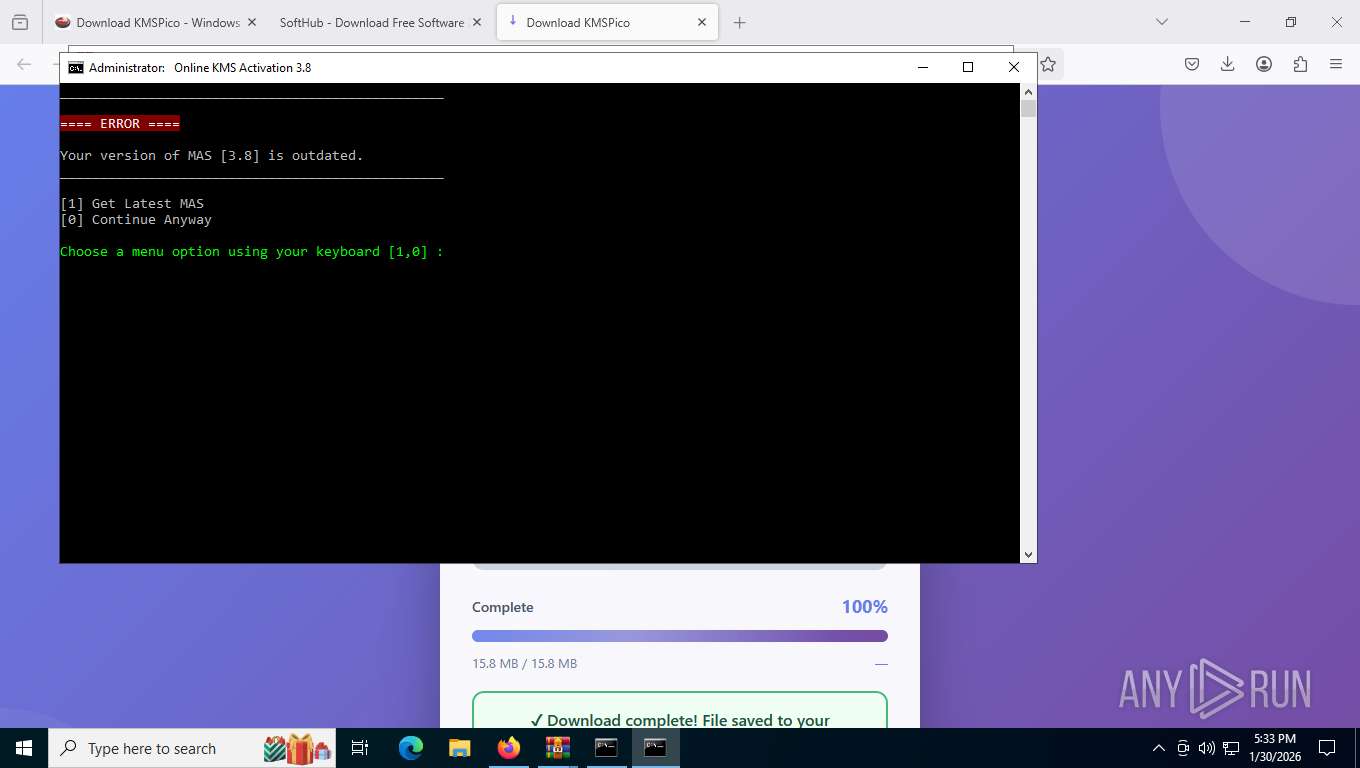
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
| Analysis date: | January 30, 2026, 22:28:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 592EDD5B5F8463EC9E33AC46F02F829B |
| SHA1: | 9DAFD7F3613BA64098050D84B871B123B3560D95 |
| SHA256: | 08A95B57D72B3EAAC6F1806CA260FCF71FAD6CBFCF9B3635C74BBA3380533C68 |
| SSDEEP: | 3:N8DSLPNDRyG8JOISx:2OL5D8AIQ |
MALICIOUS
PHISHING has been detected (SURICATA)
- firefox.exe (PID: 7704)
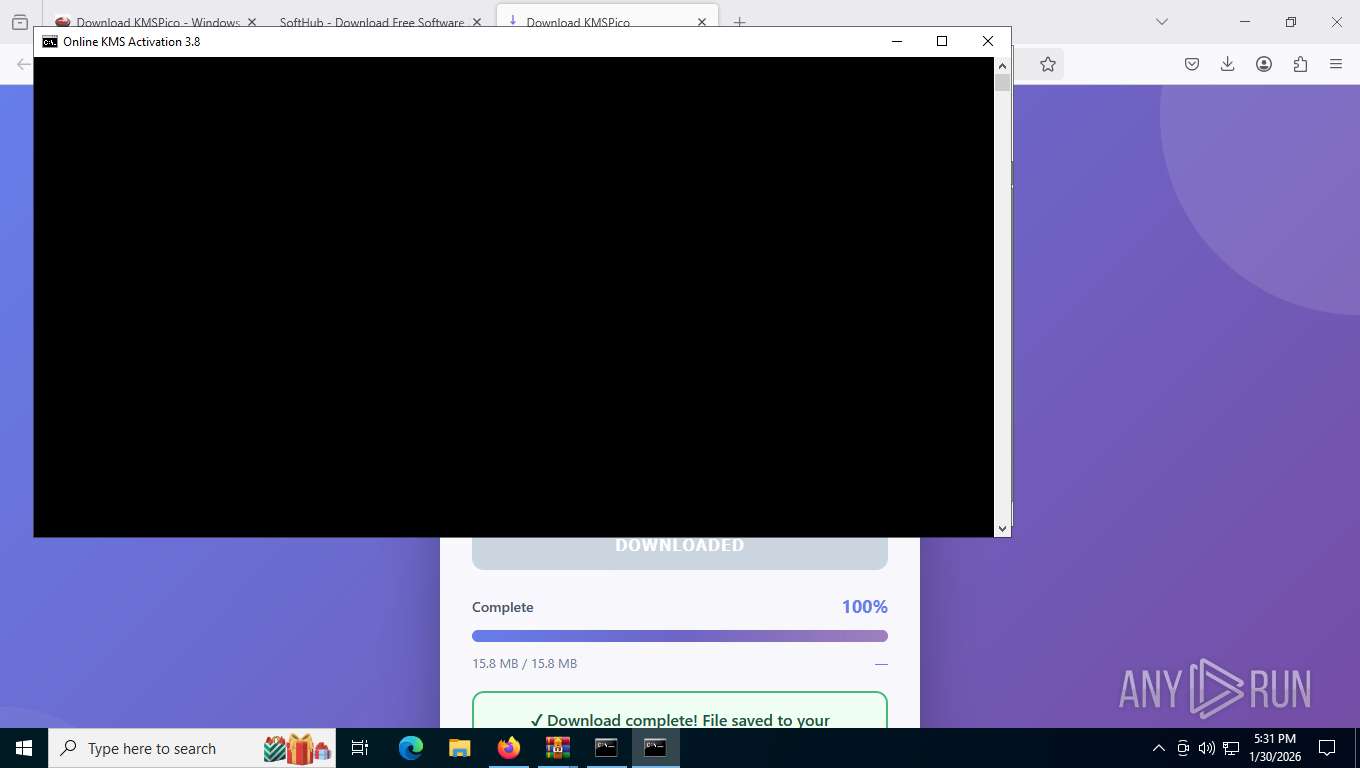
HIJACKLOADER has been detected (YARA)
- Turbo-Nav.exe (PID: 4136)
- PhotonGen.exe (PID: 3384)
- MatrixBridg.exe (PID: 4404)
- Crisp.exe (PID: 8760)
XORed URL has been found (YARA)
- PhotonGen.exe (PID: 3384)
Actions looks like stealing of personal data
- PhotonGen.exe (PID: 3384)
- MatrixBridg.exe (PID: 4404)
HIJACKLOADER has been detected (SURICATA)
- MatrixBridg.exe (PID: 4404)
Connects to the CnC server
- MatrixBridg.exe (PID: 4404)
- PhotonGen.exe (PID: 3384)
Steals credentials from Web Browsers
- PhotonGen.exe (PID: 3384)
- MatrixBridg.exe (PID: 4404)
STEALC has been detected (SURICATA)
- PhotonGen.exe (PID: 3384)
SUSPICIOUS
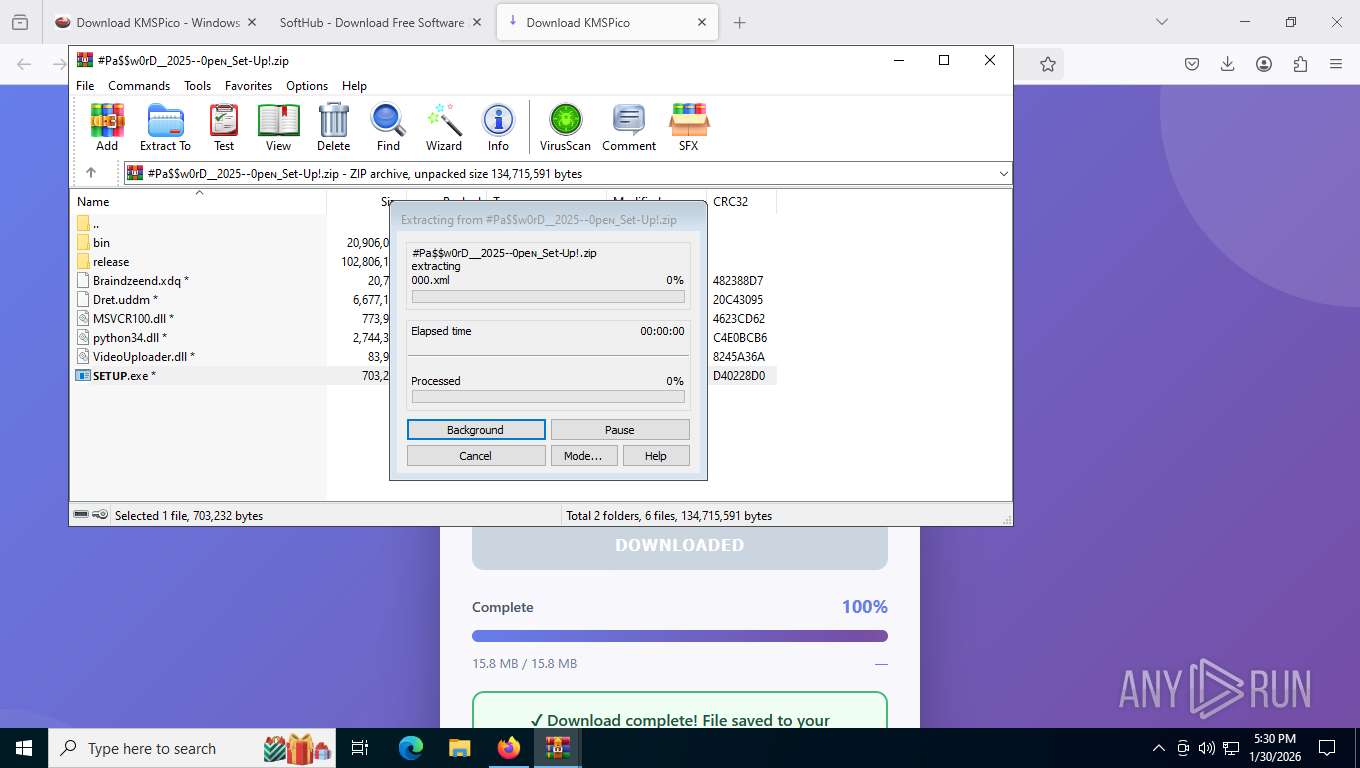
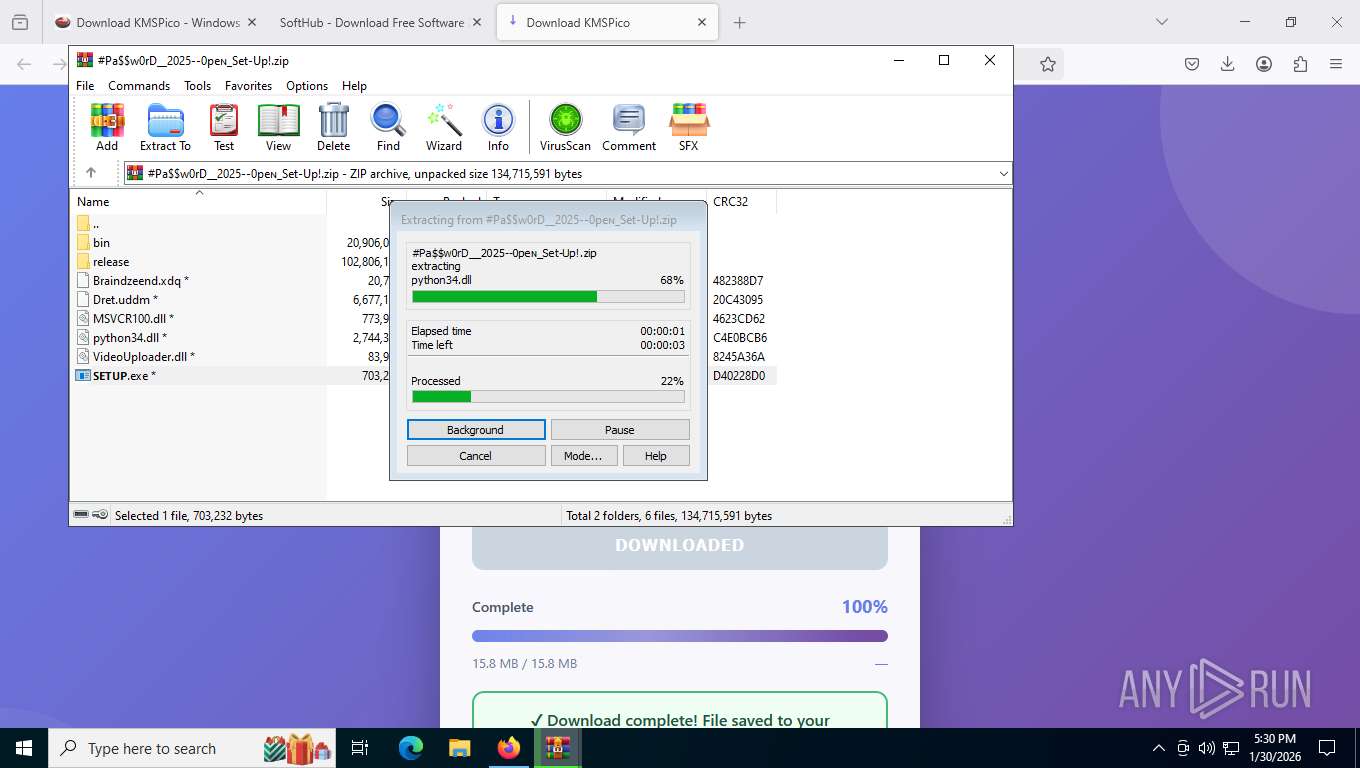
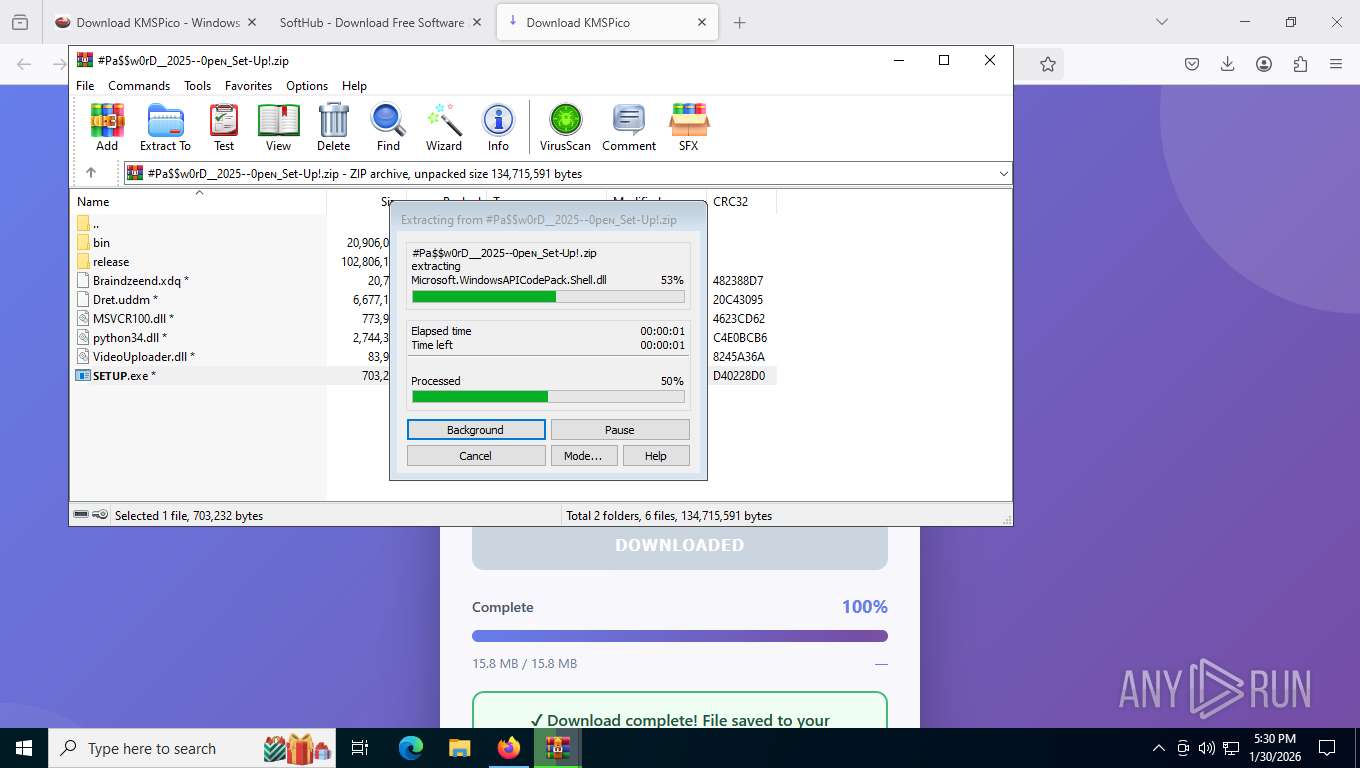
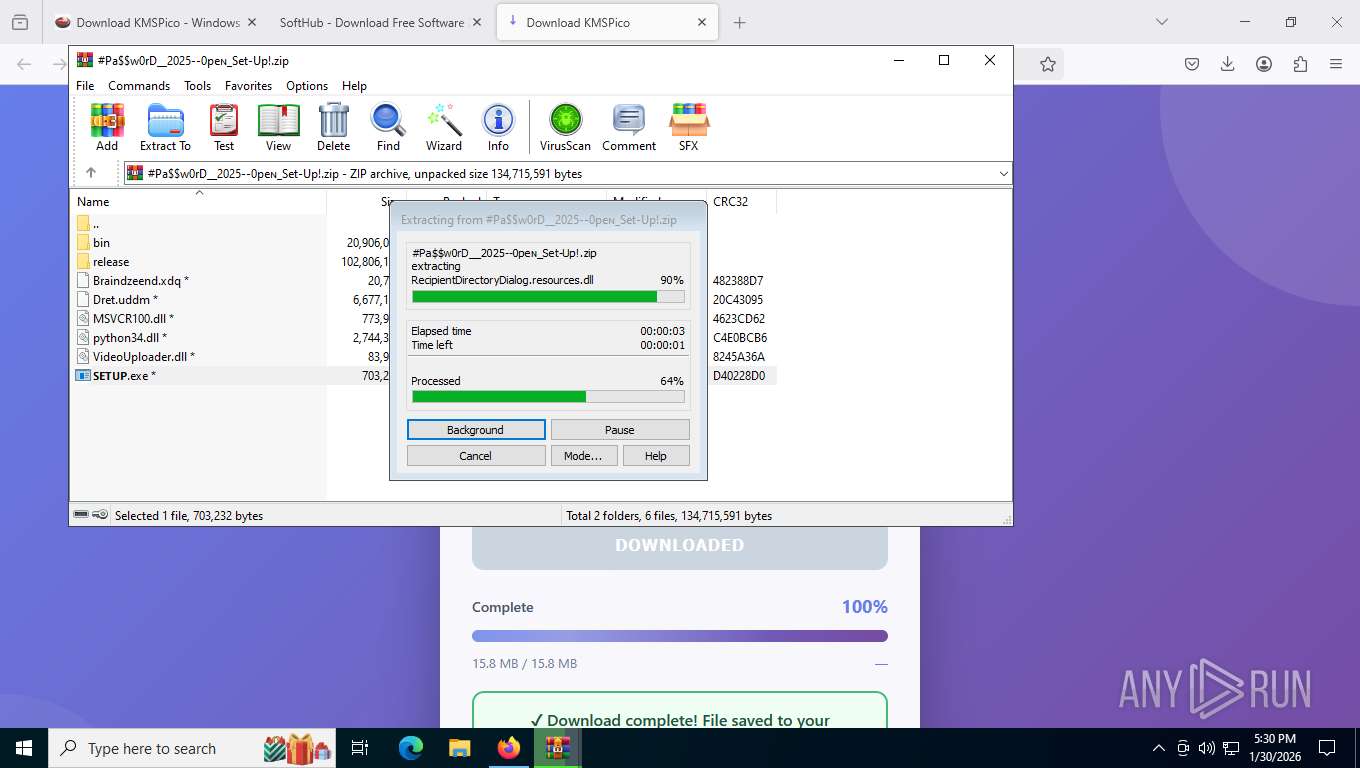
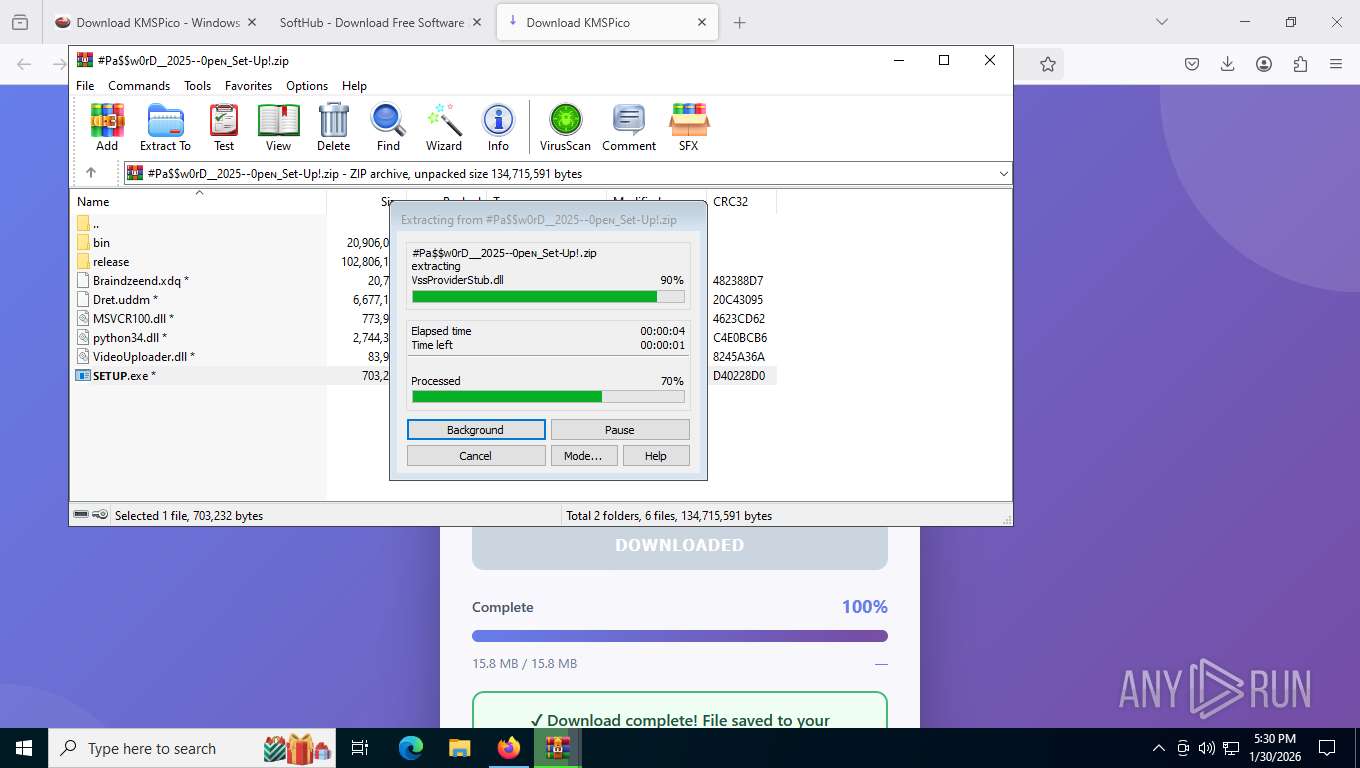
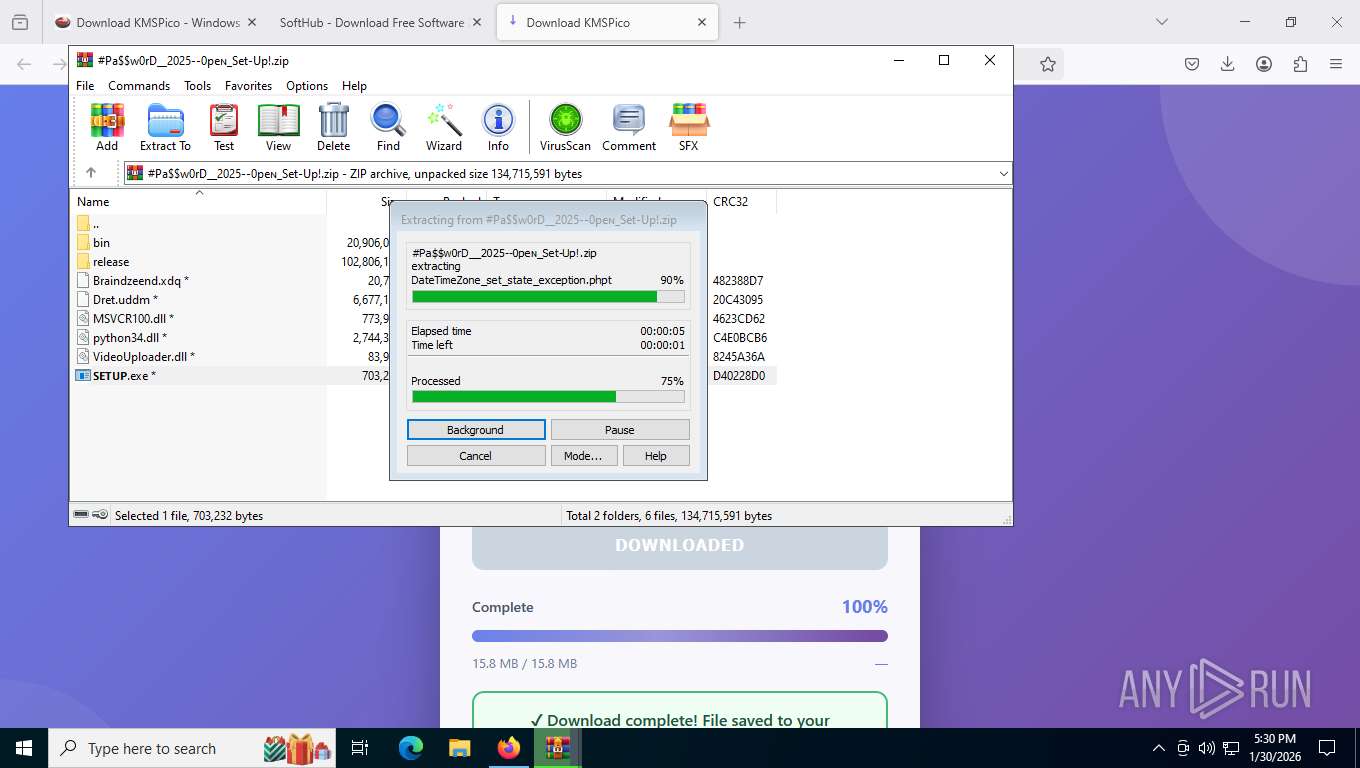
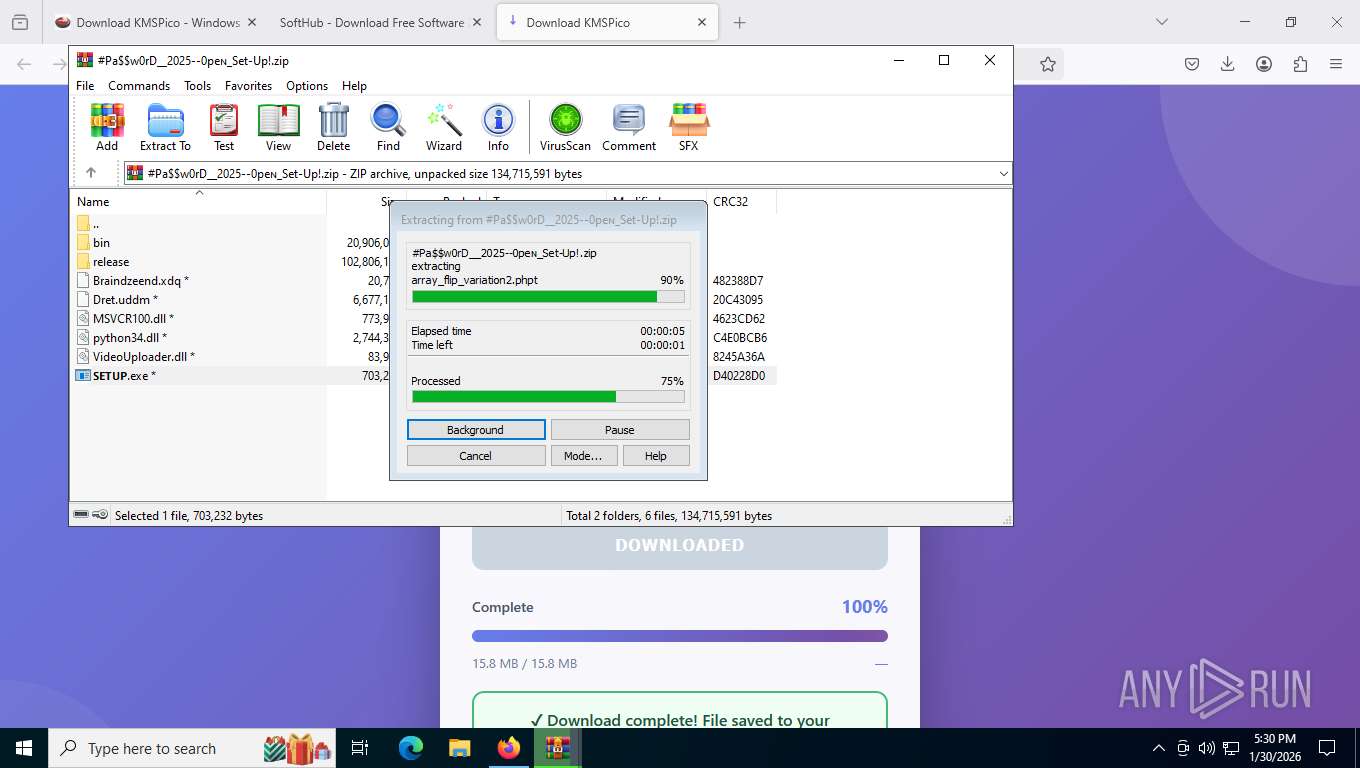
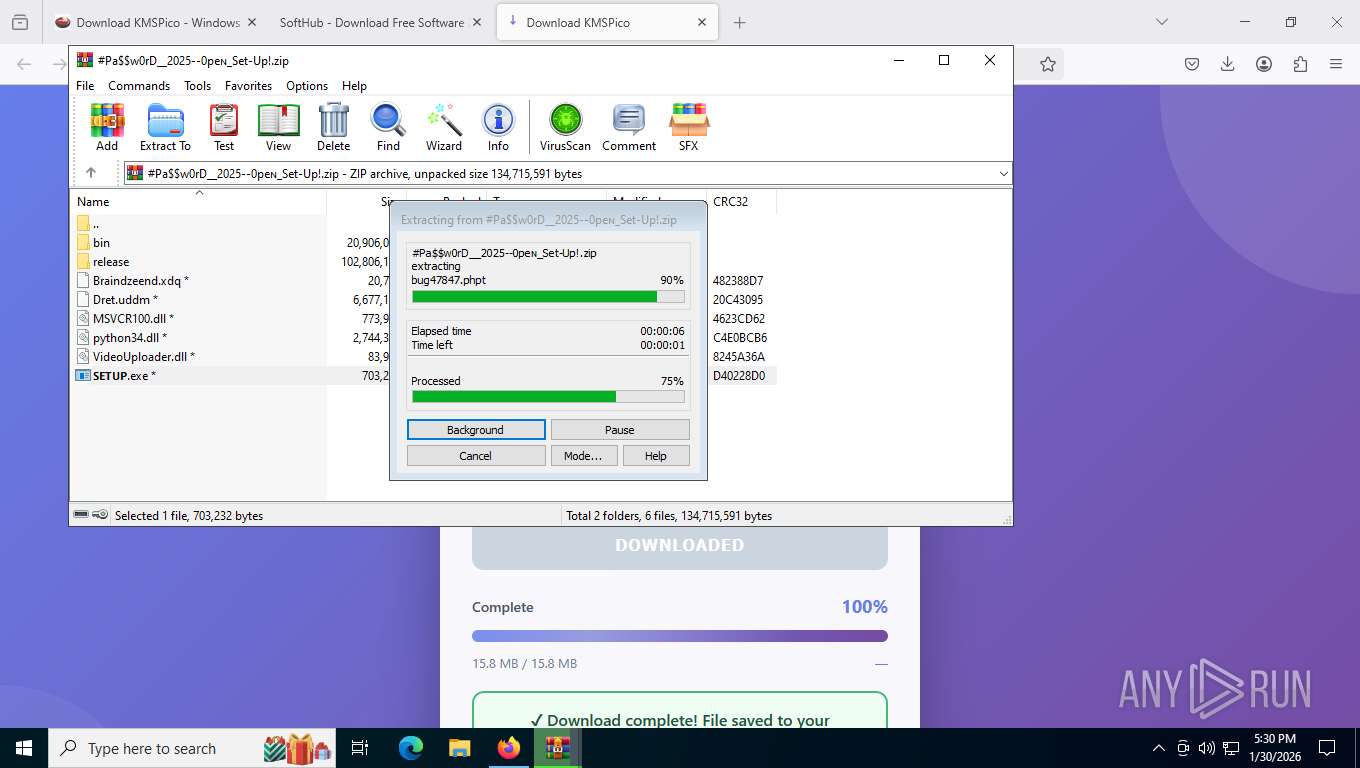
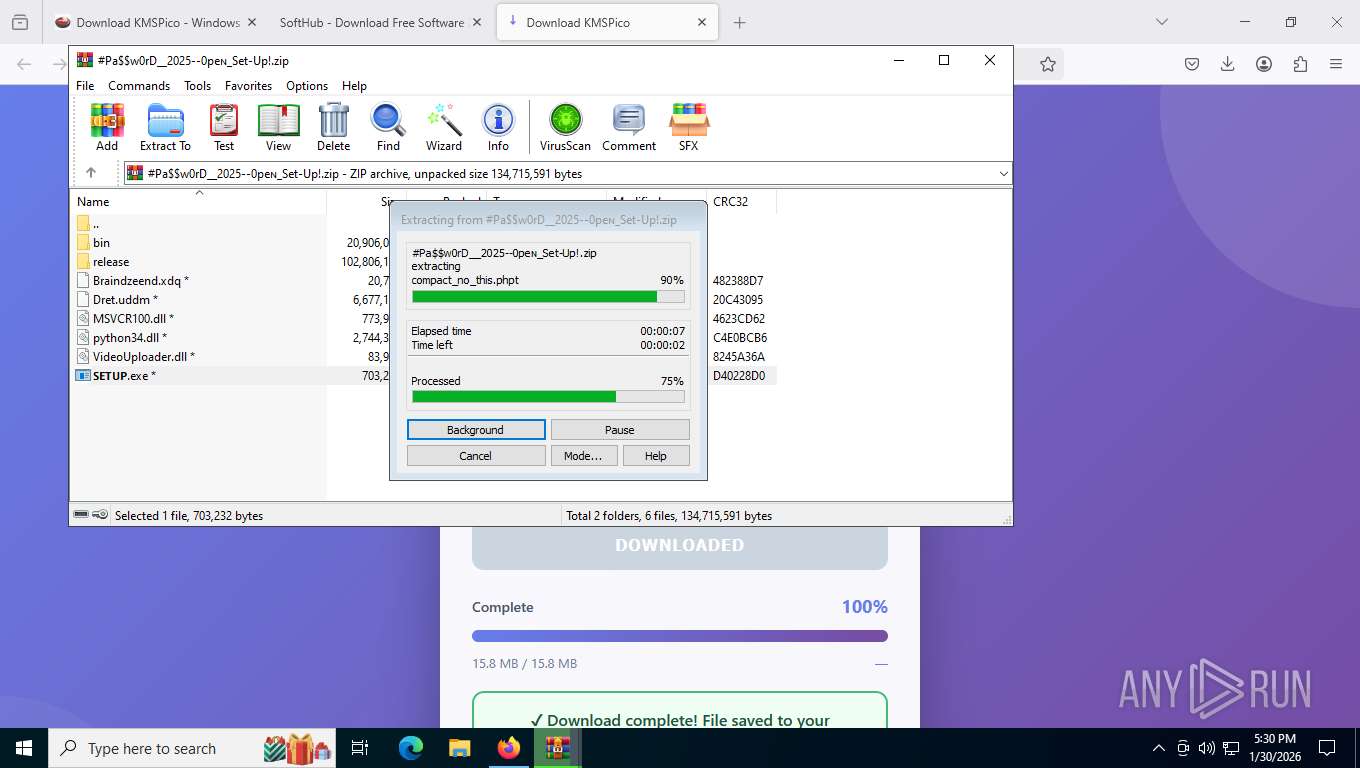
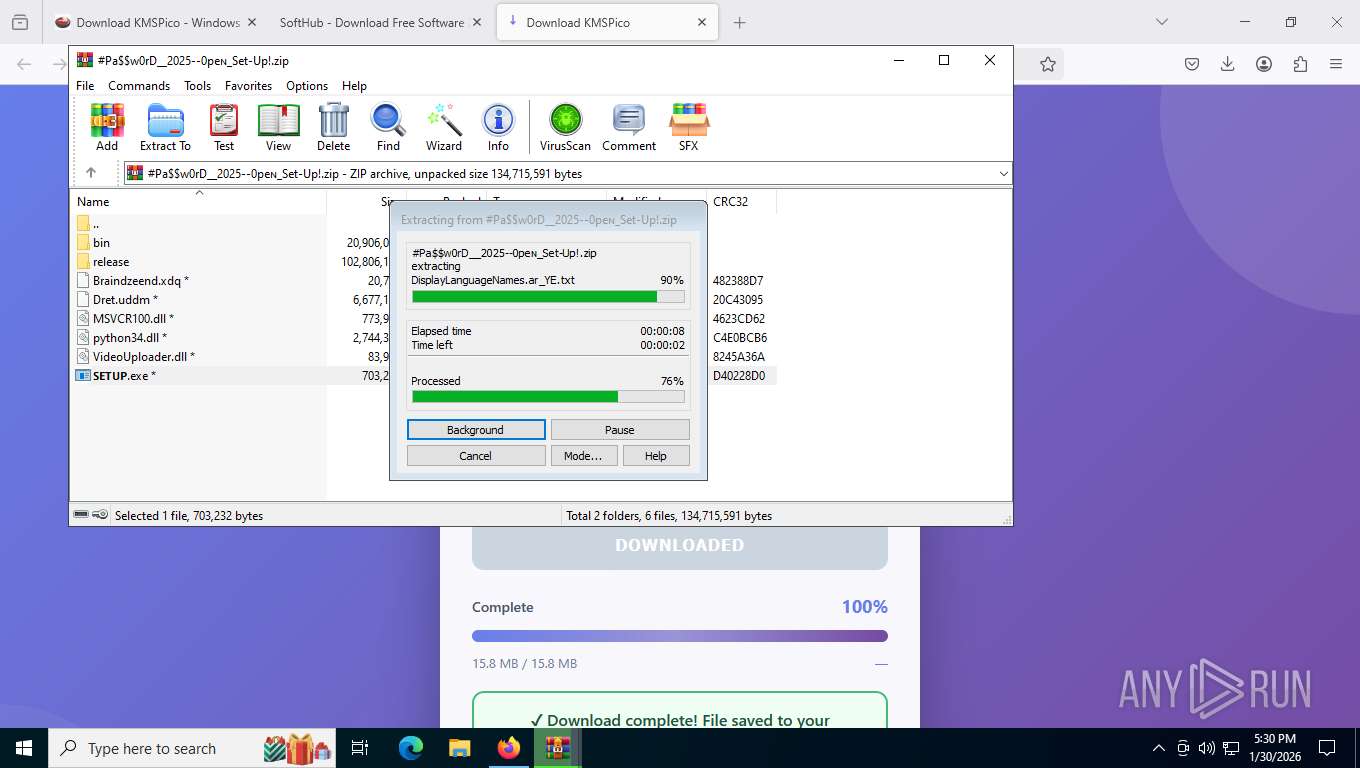
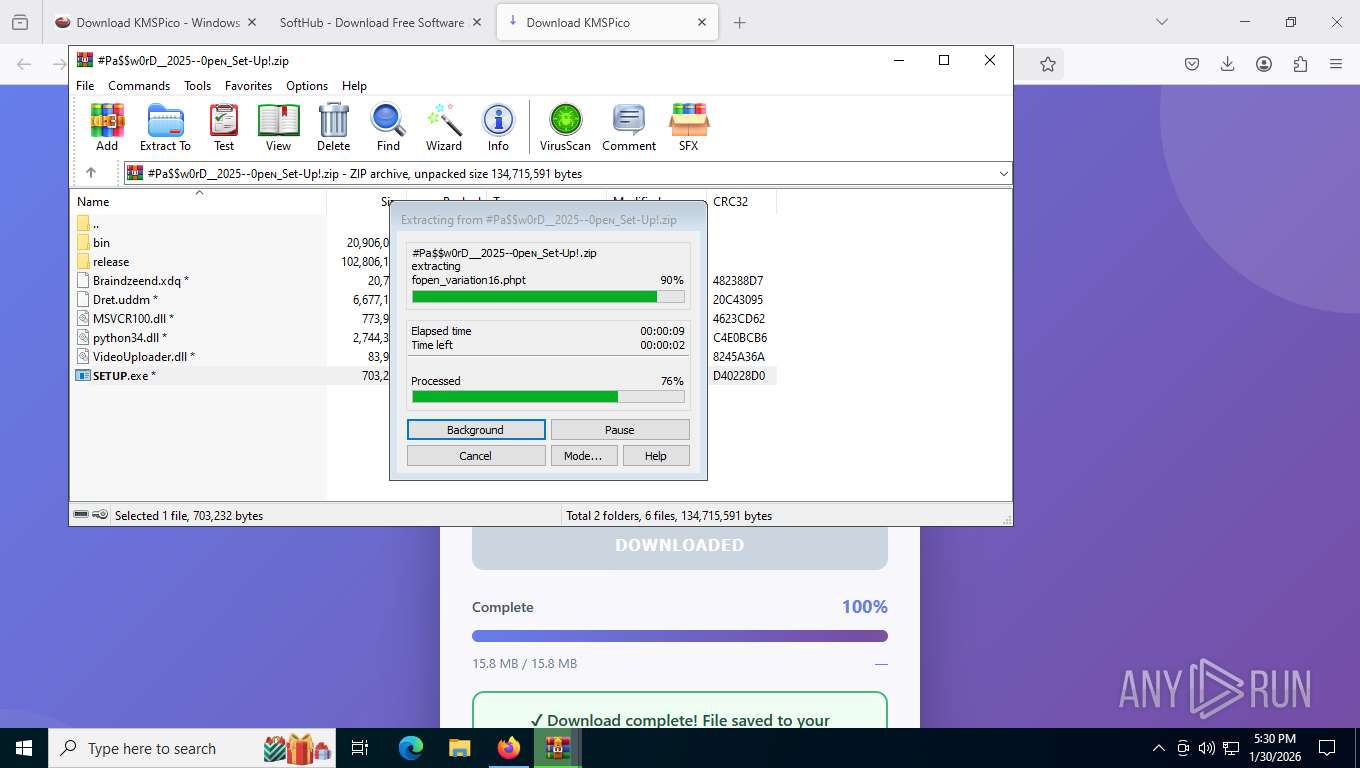
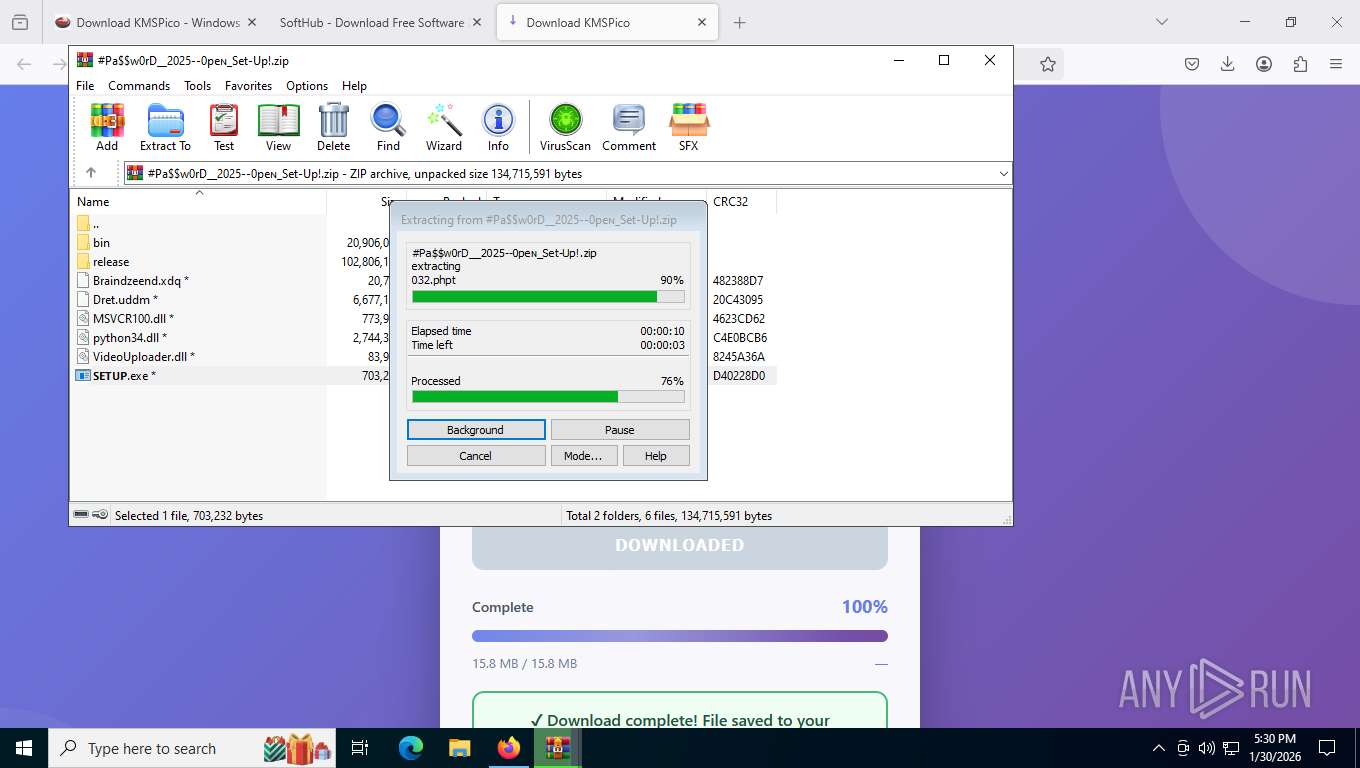
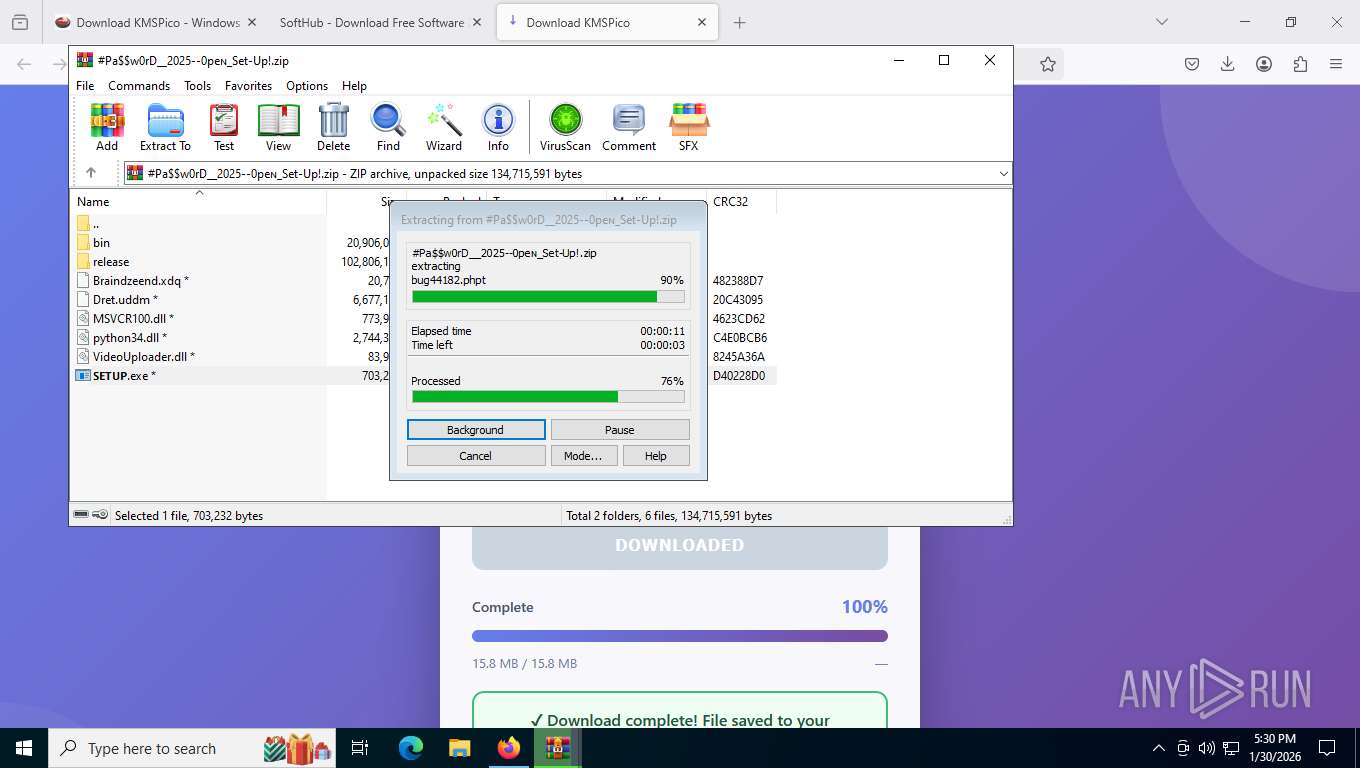
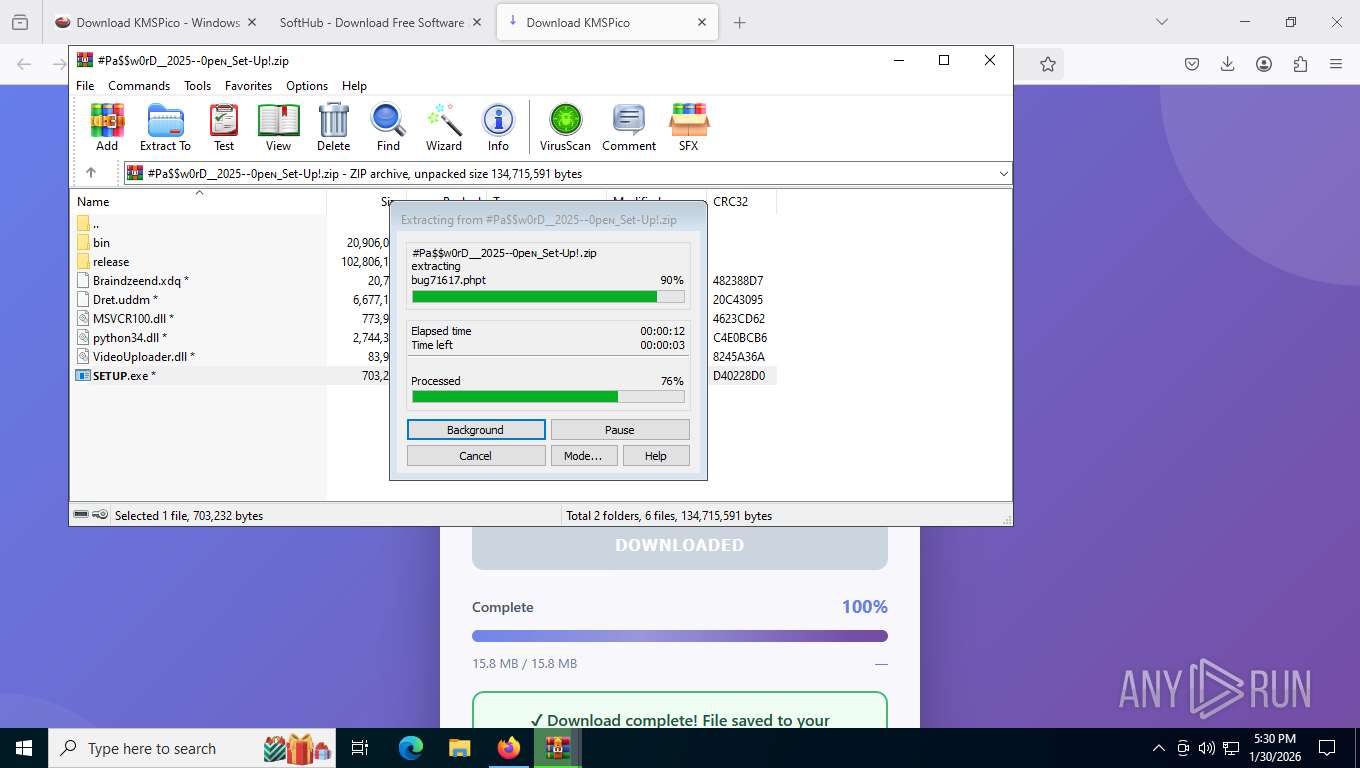
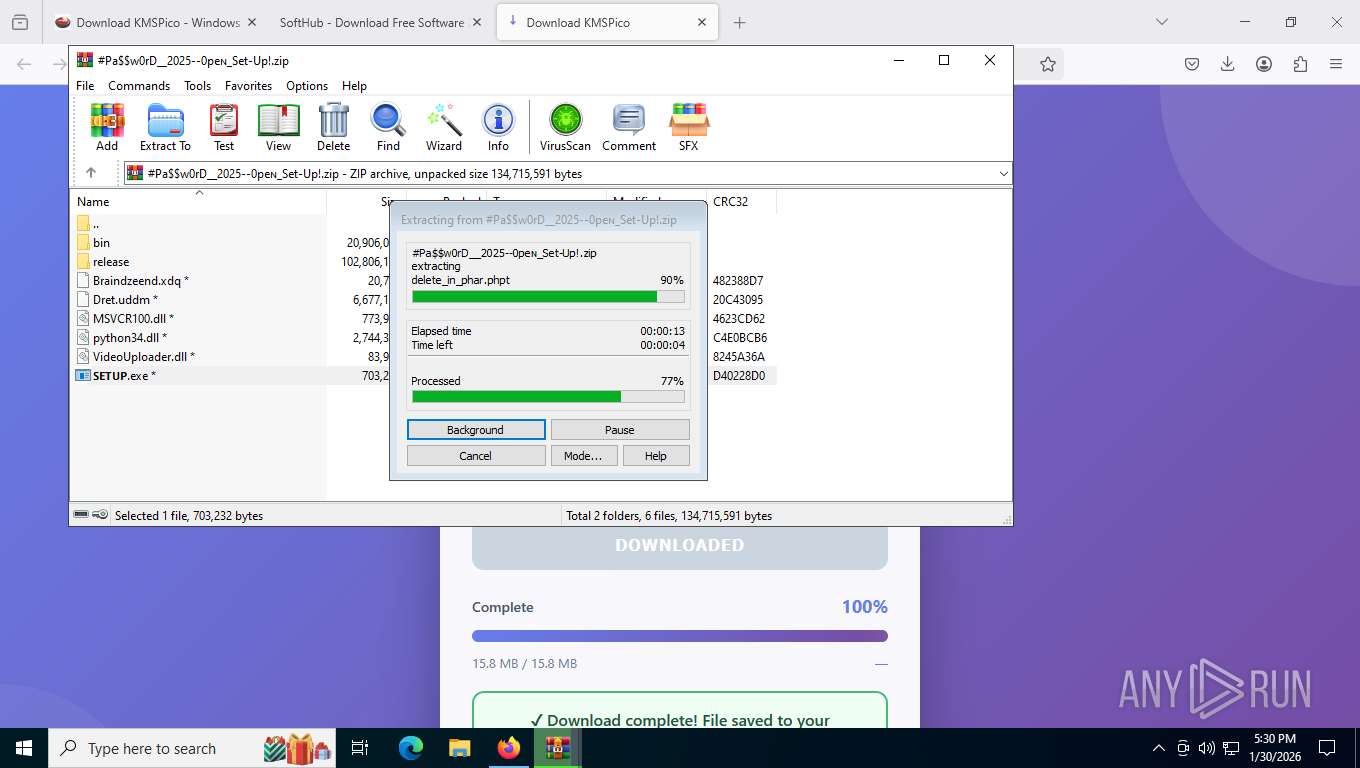
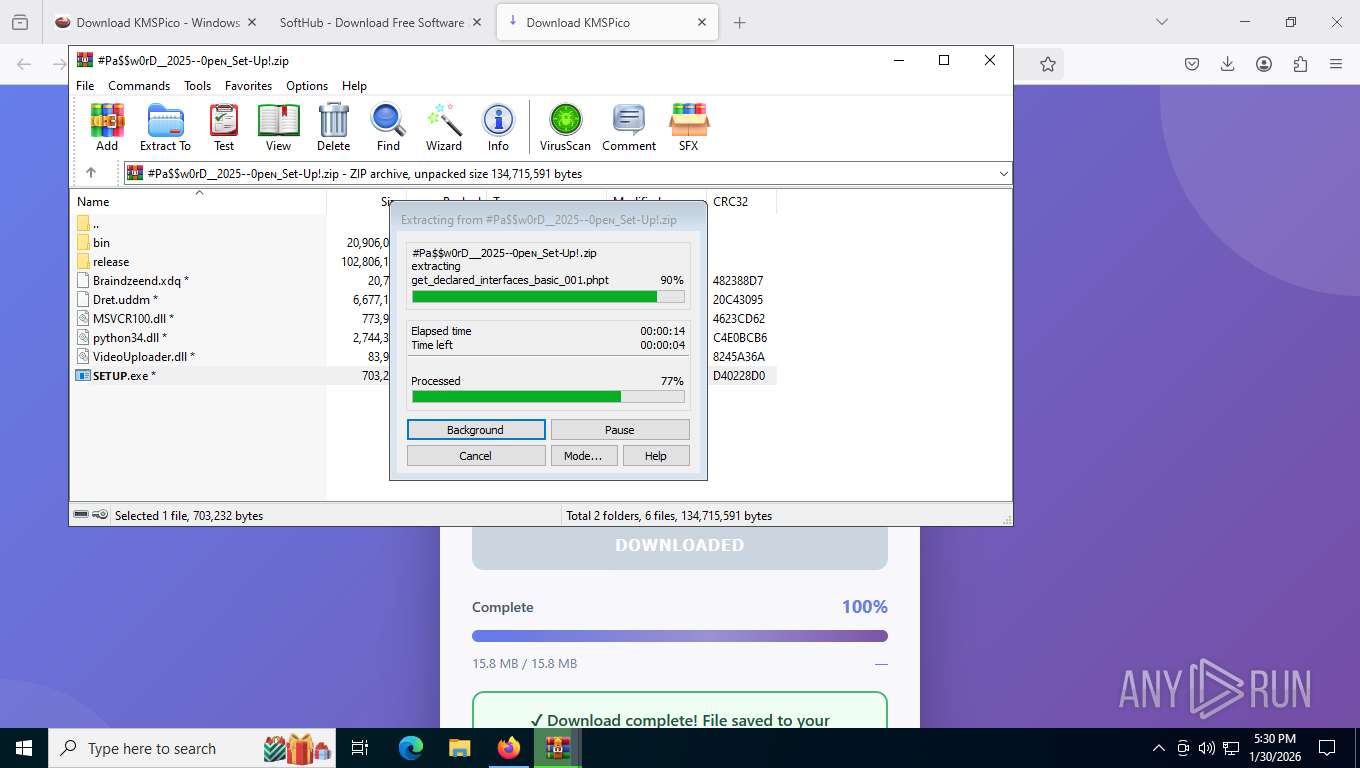
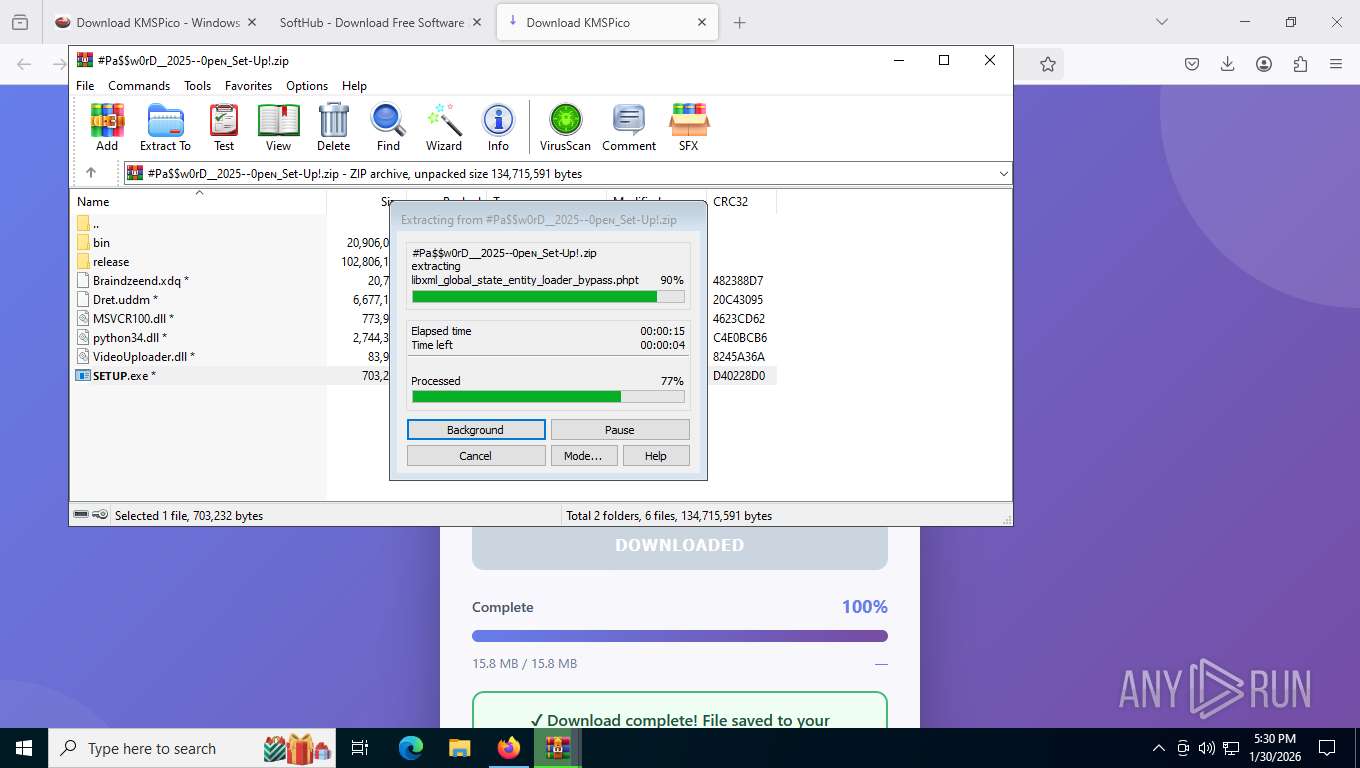
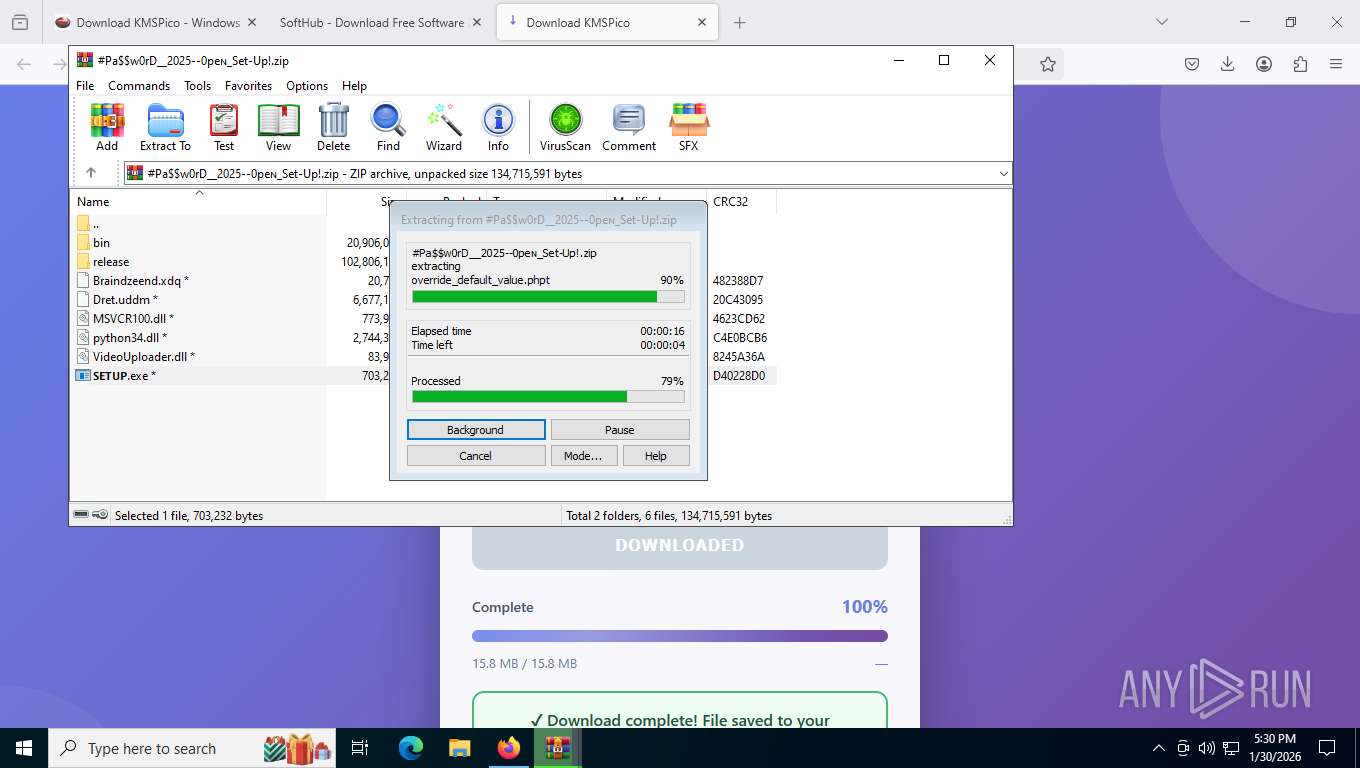
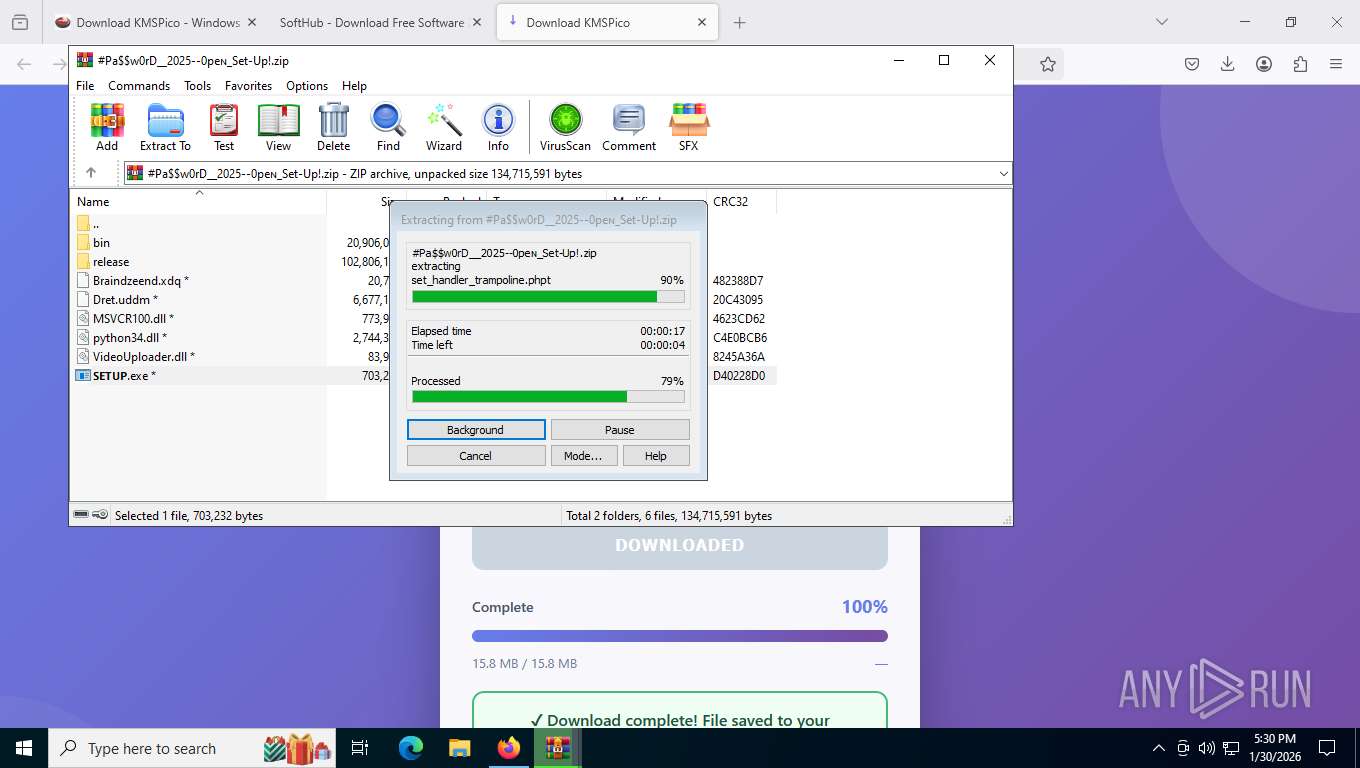
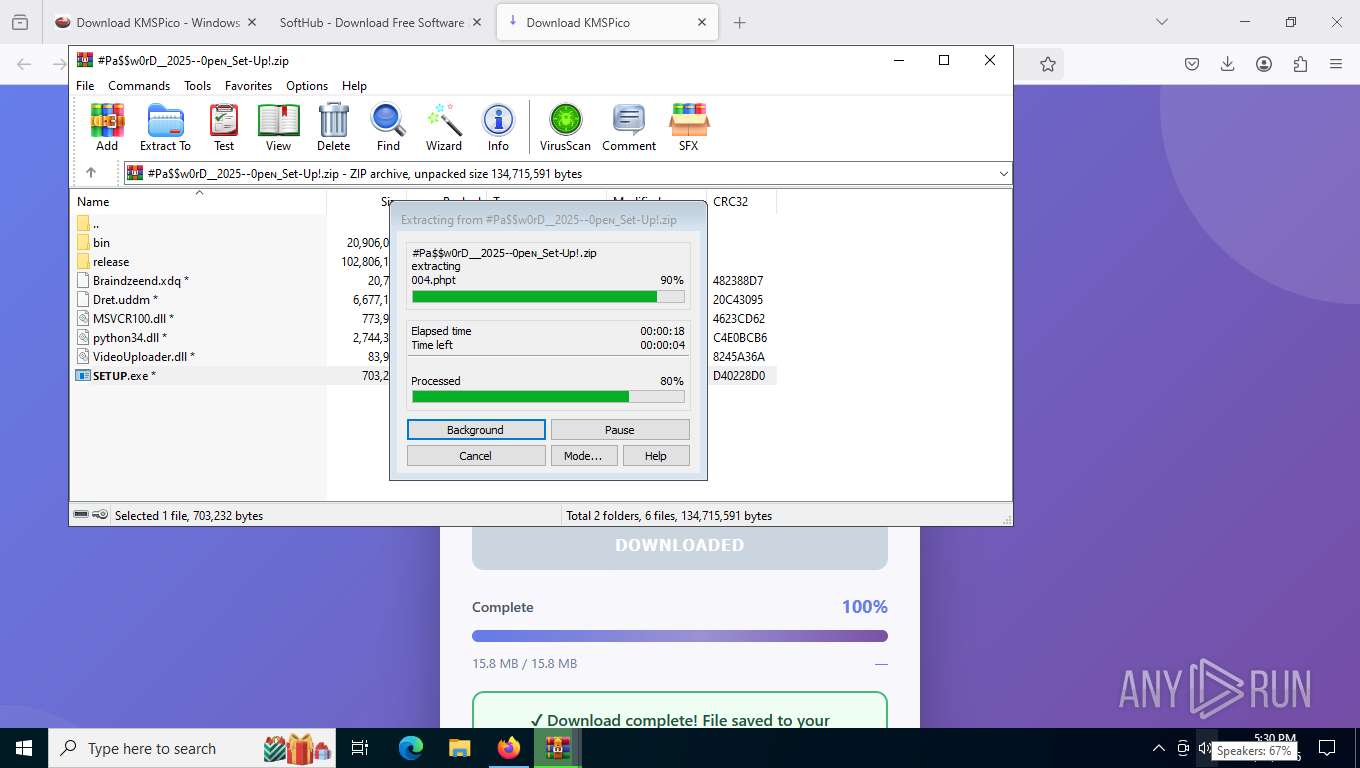
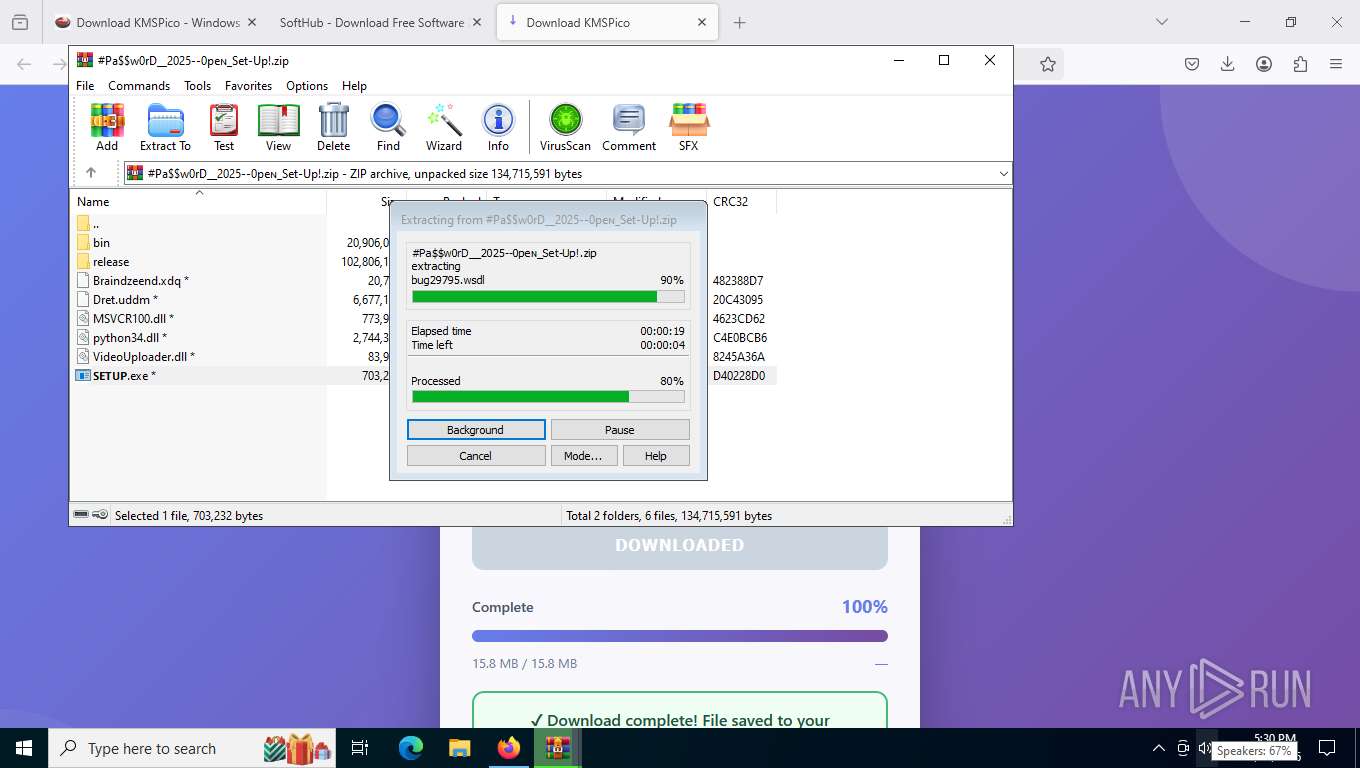
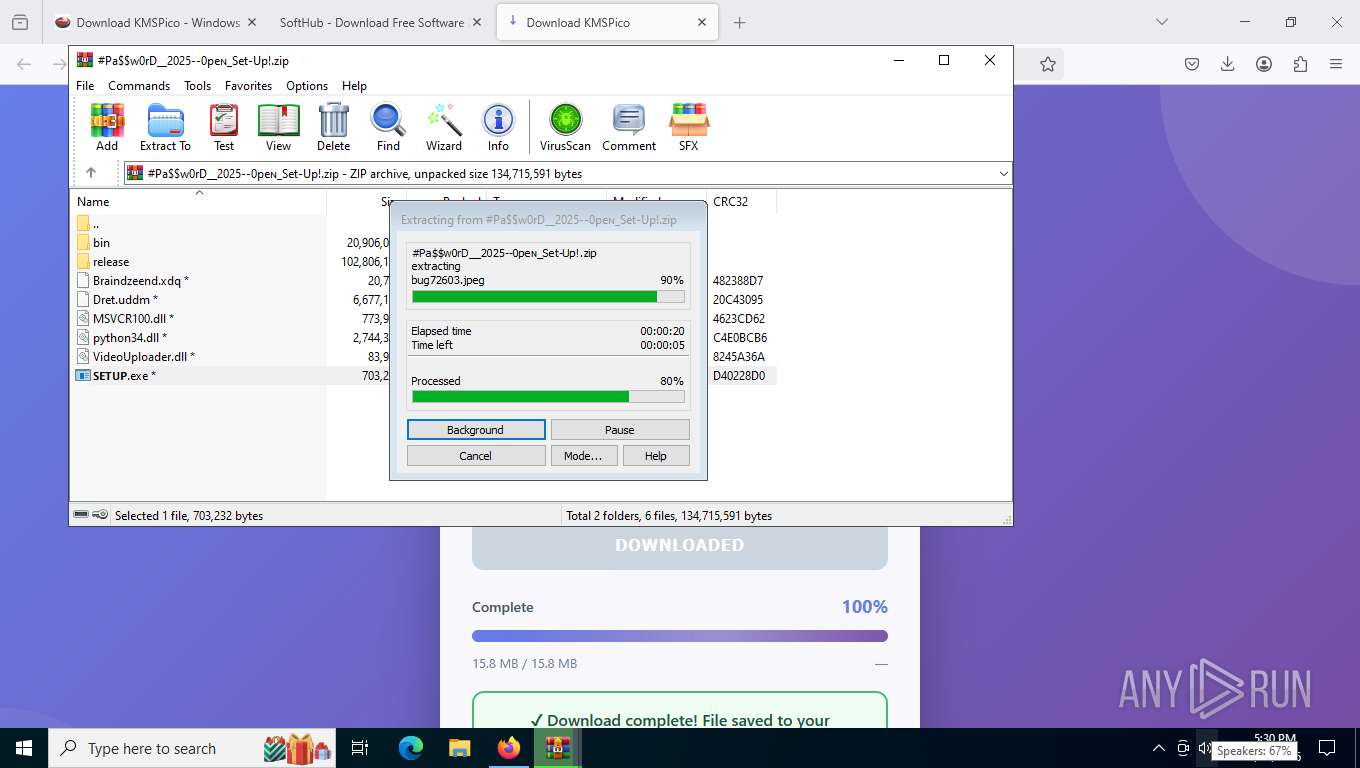
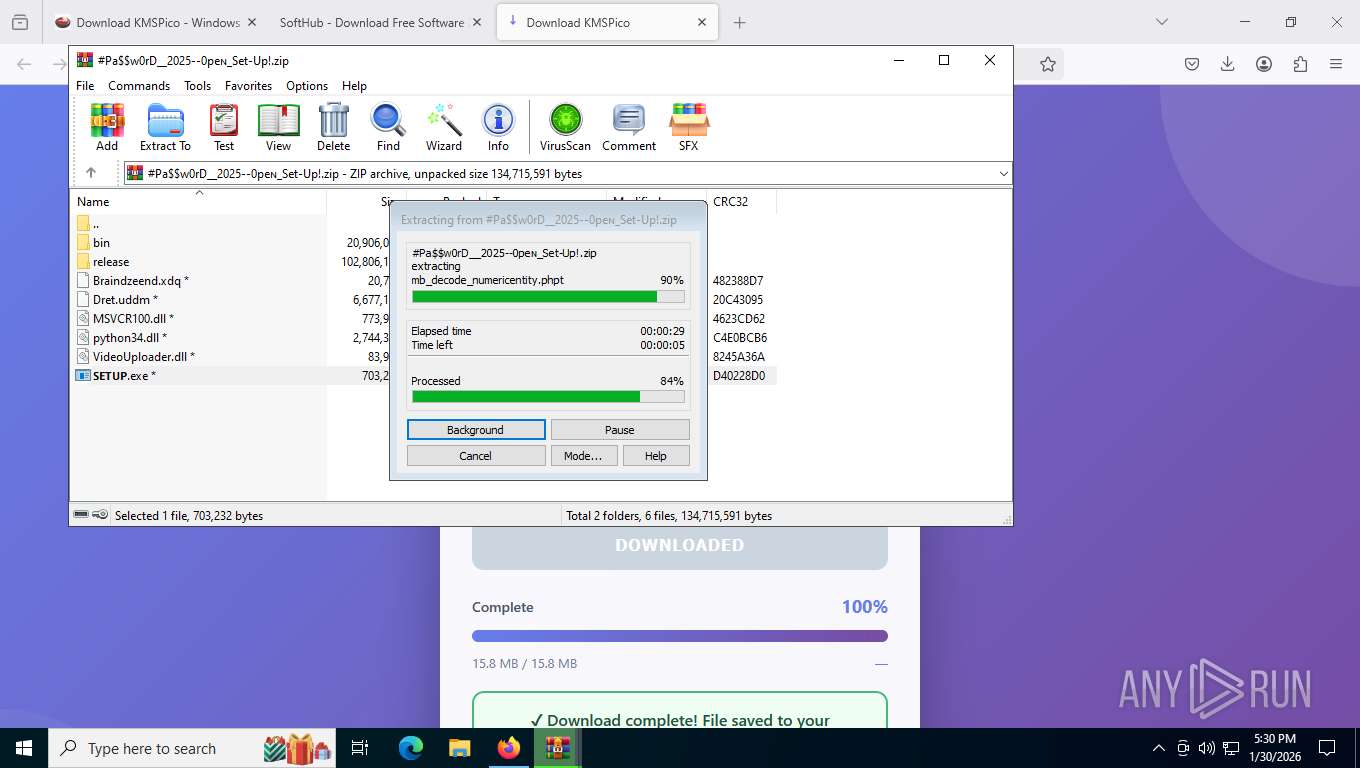
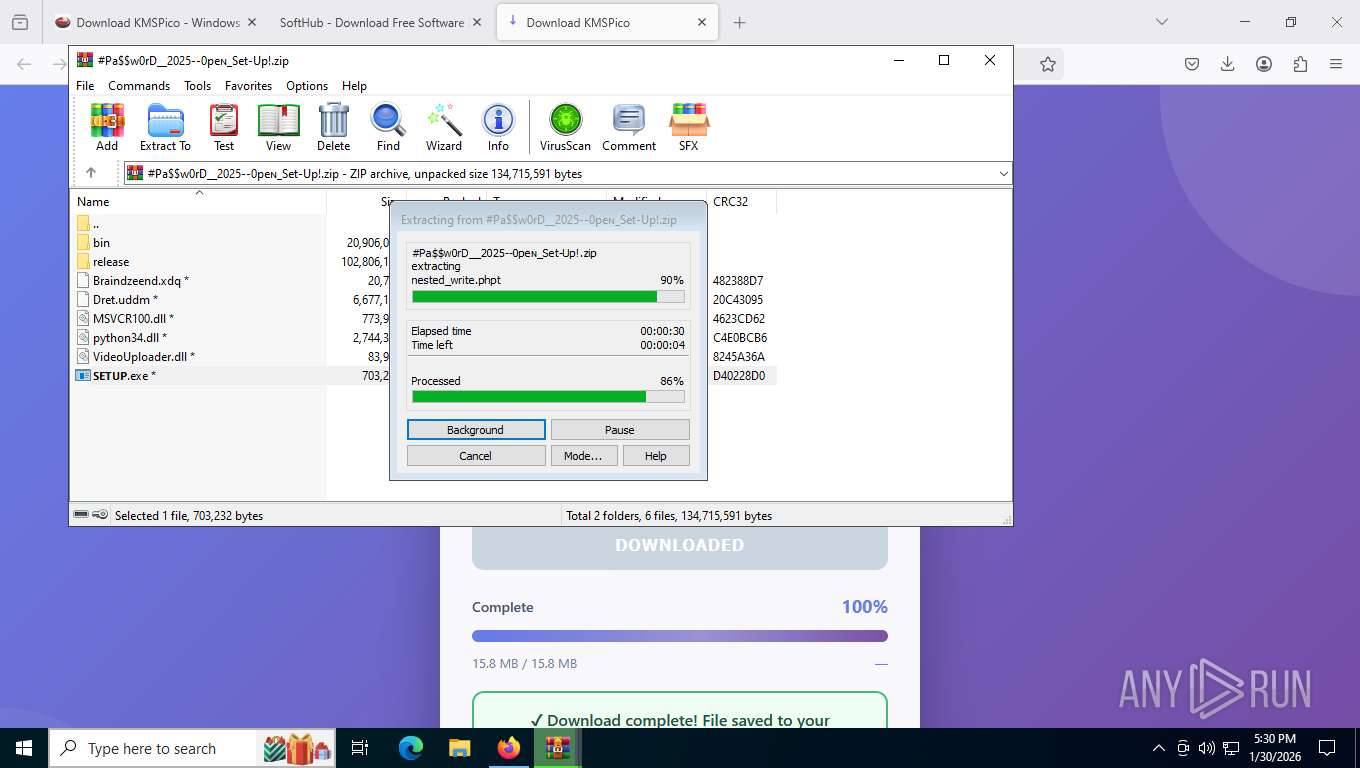
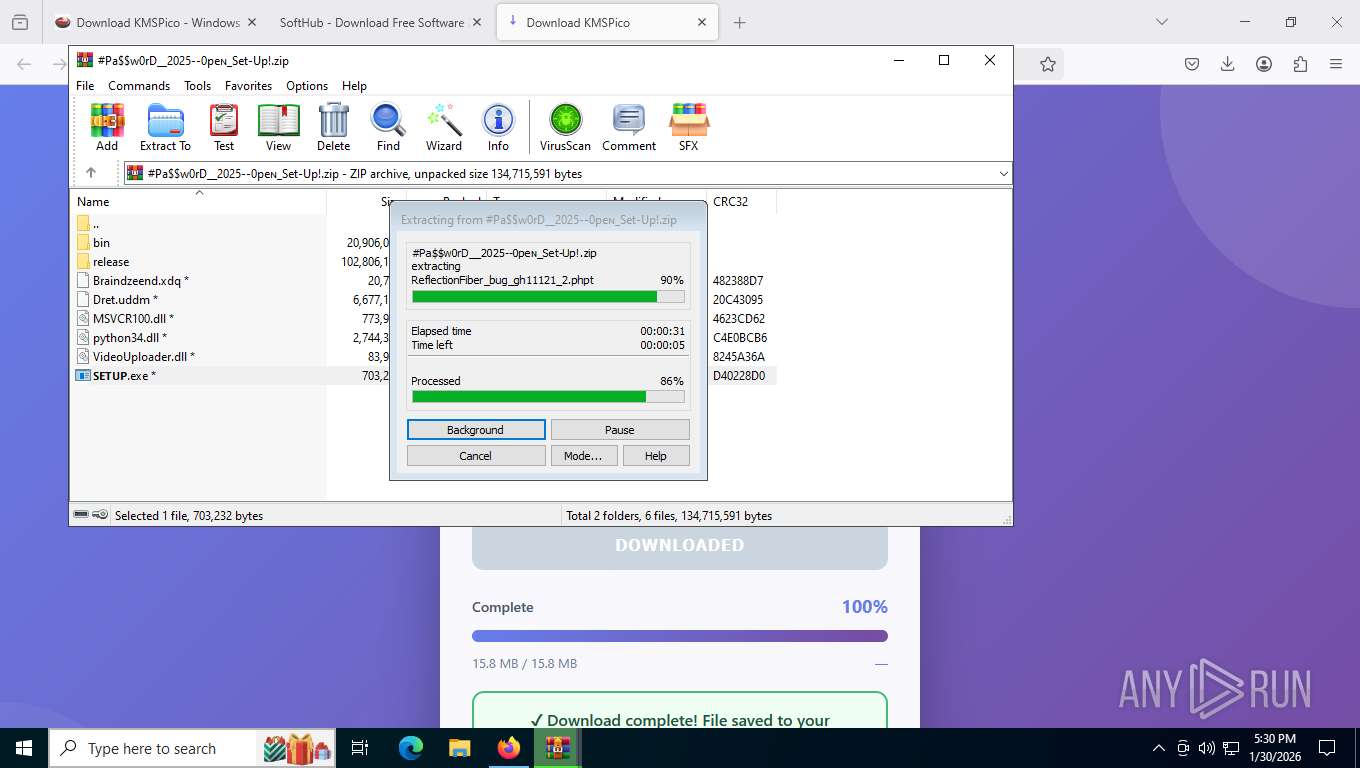
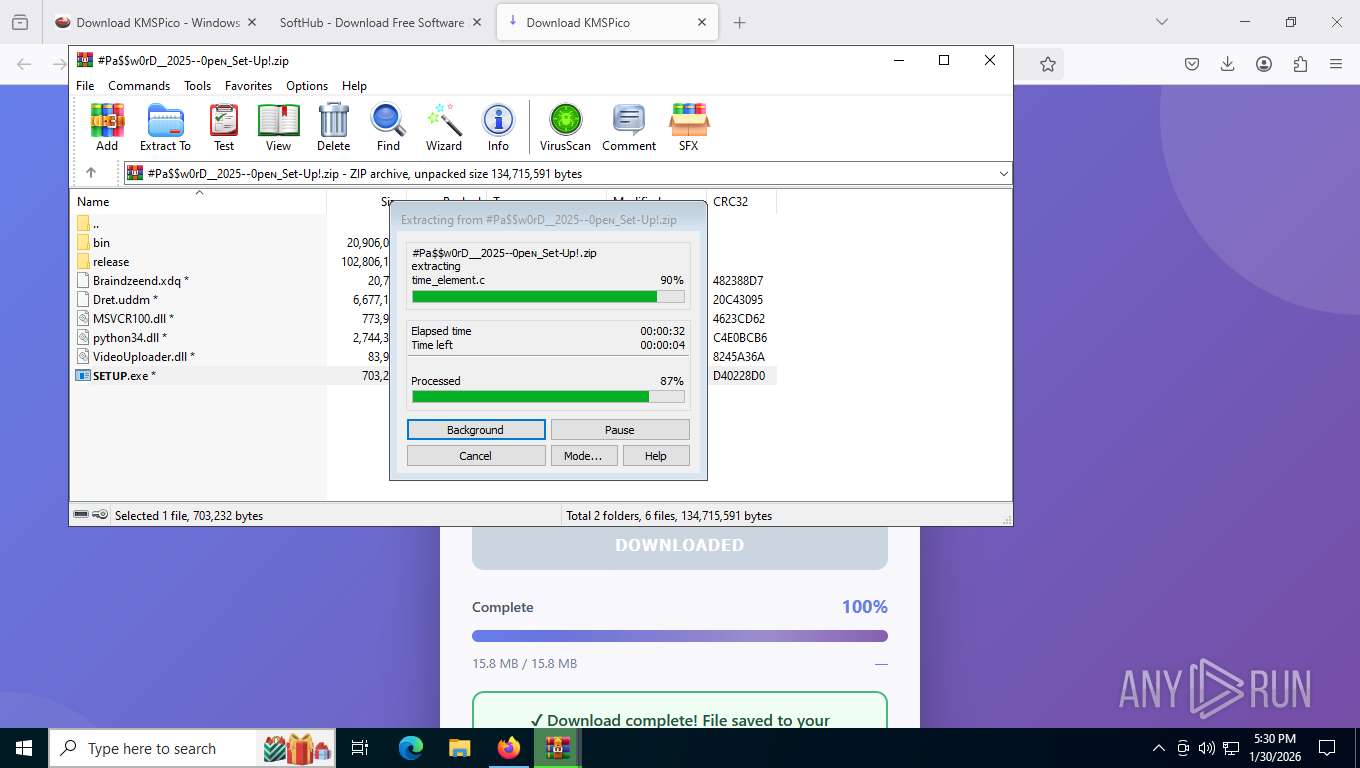
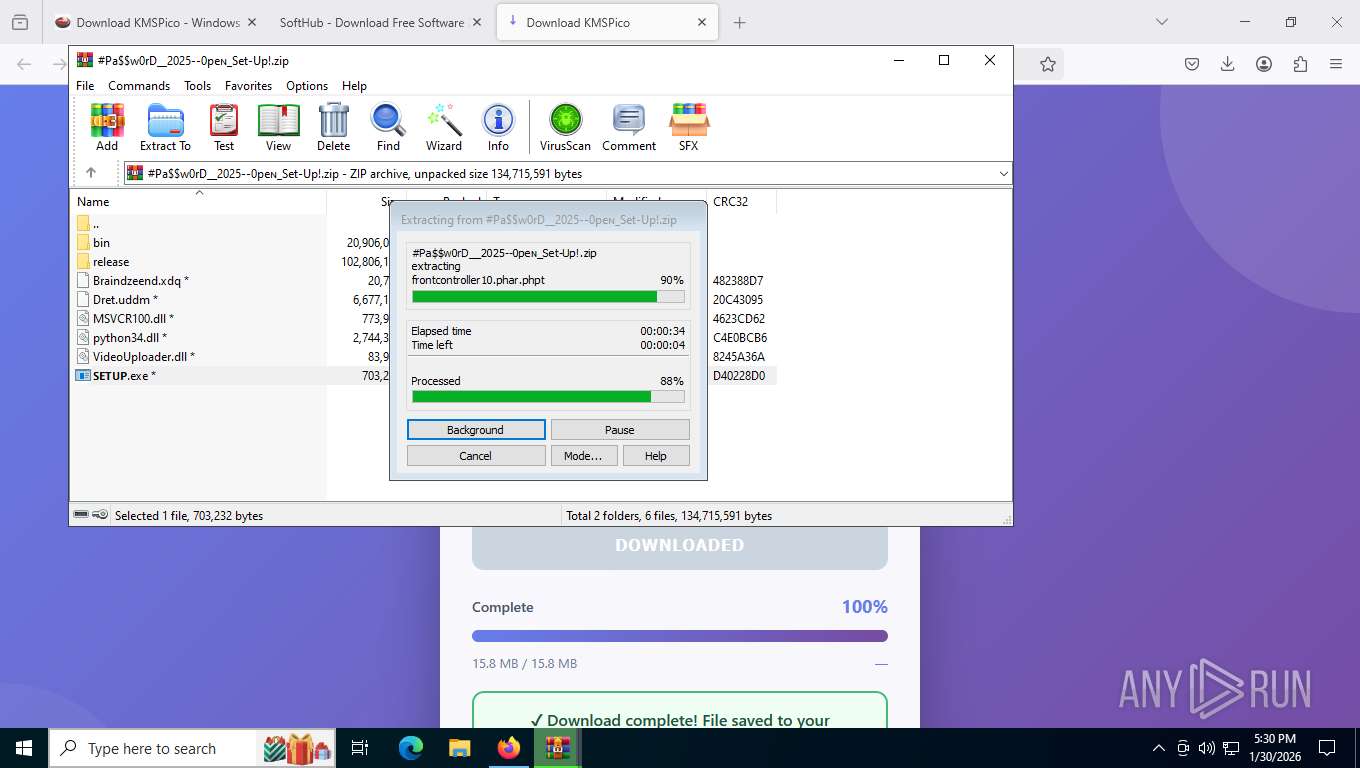
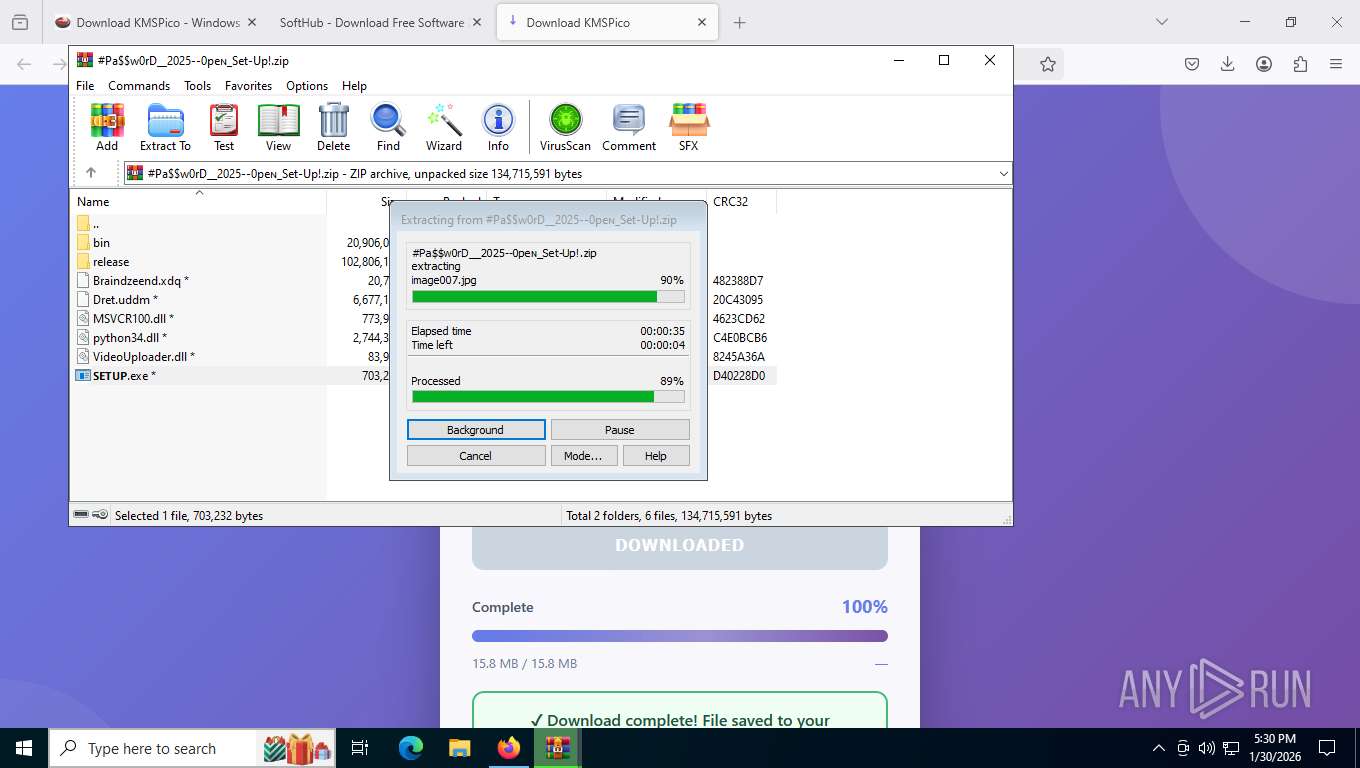
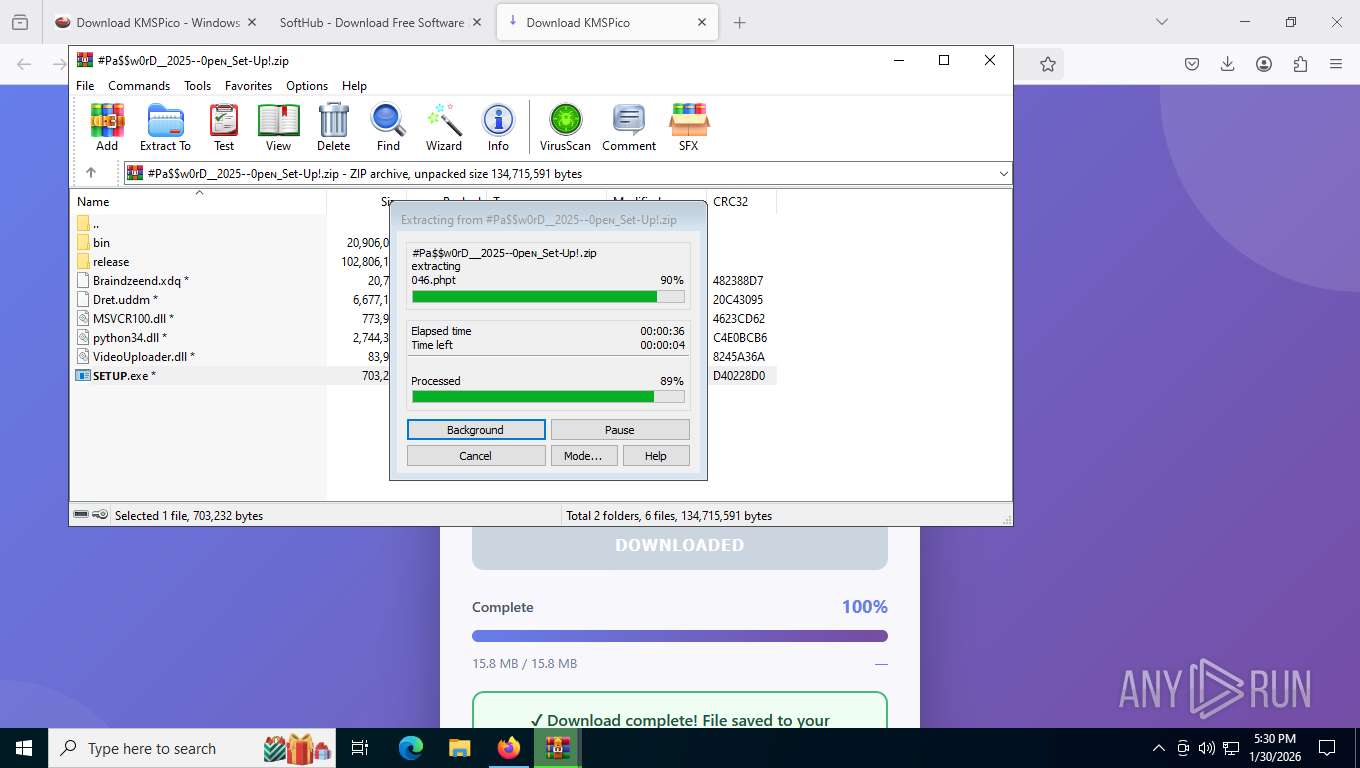
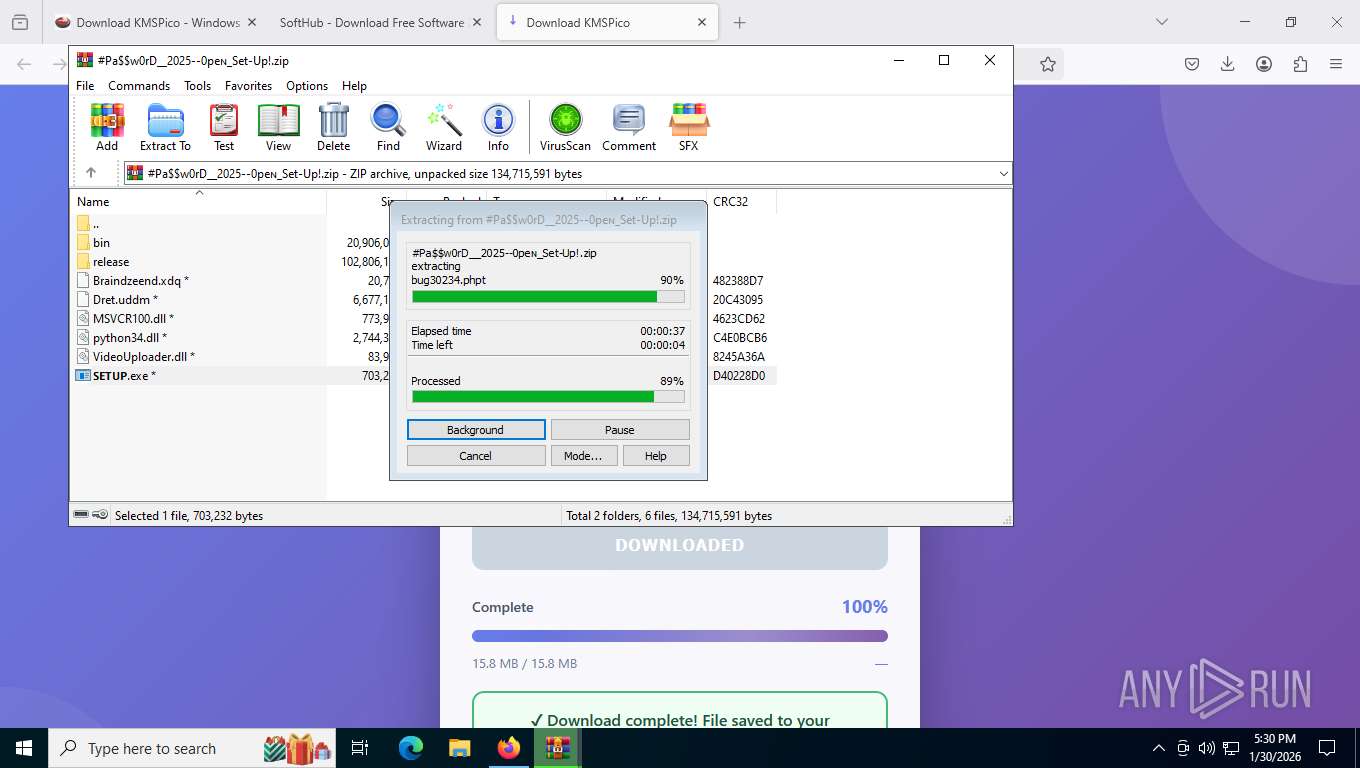
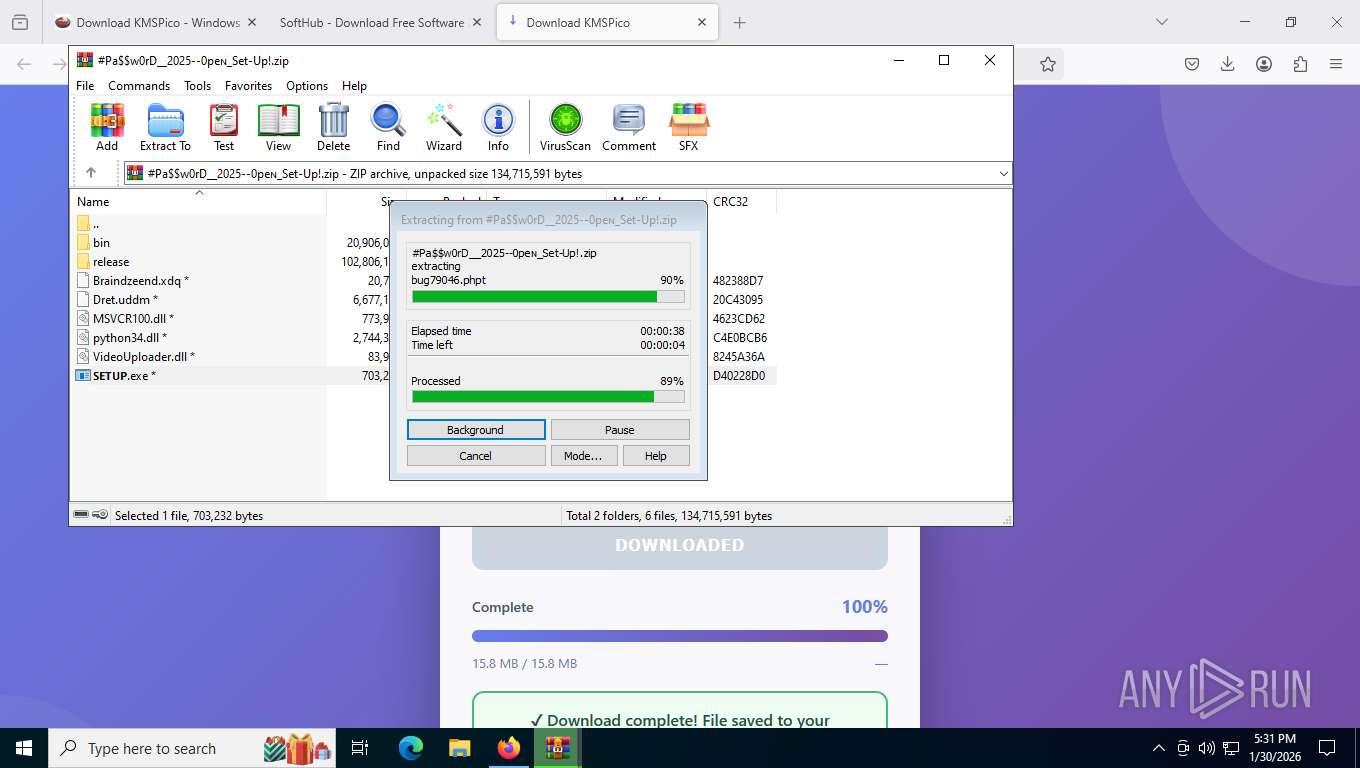
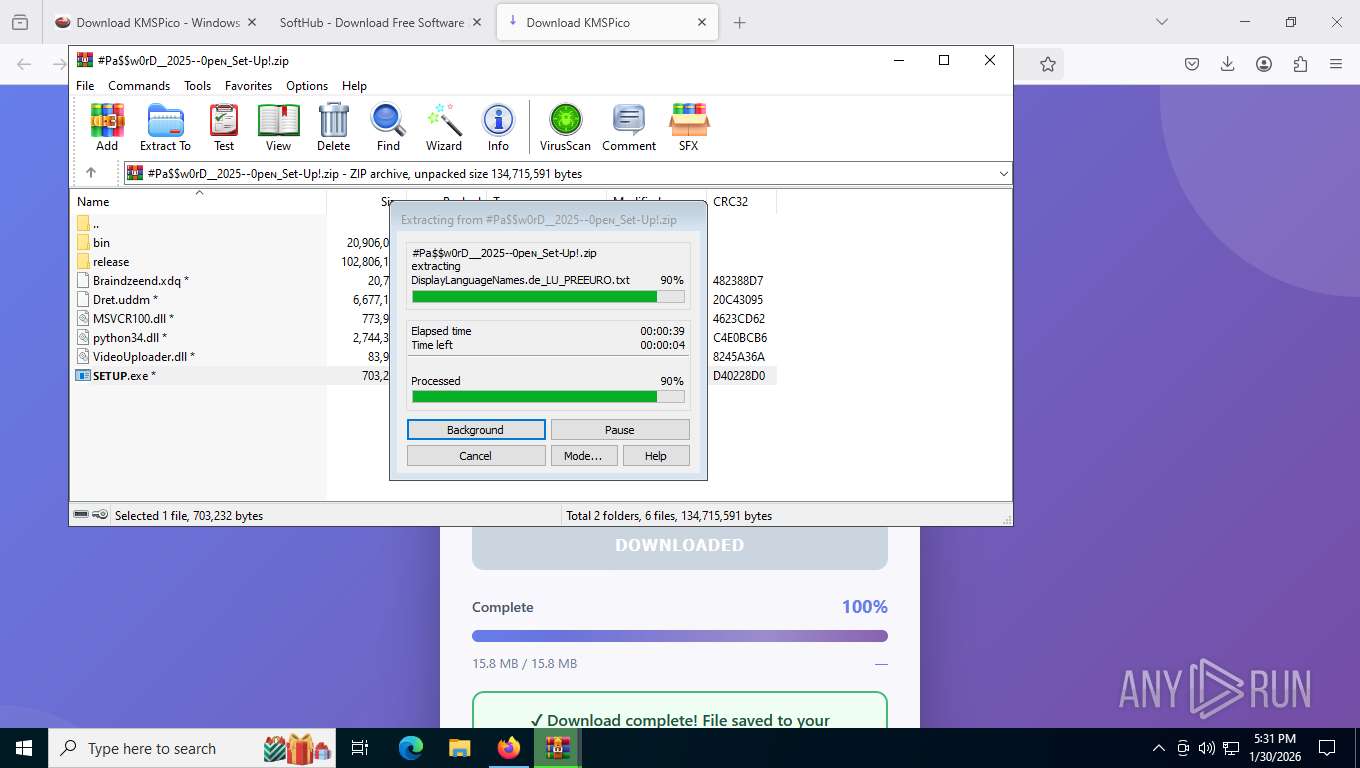
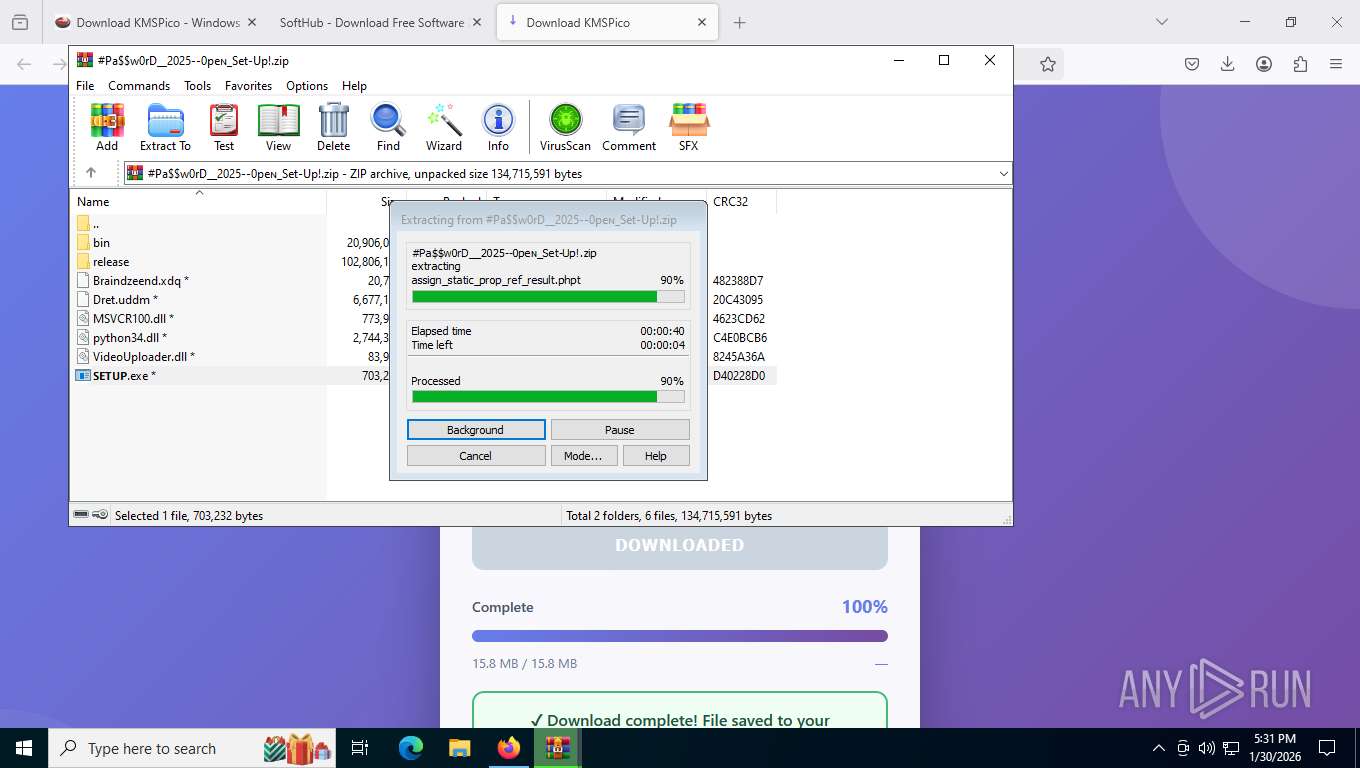
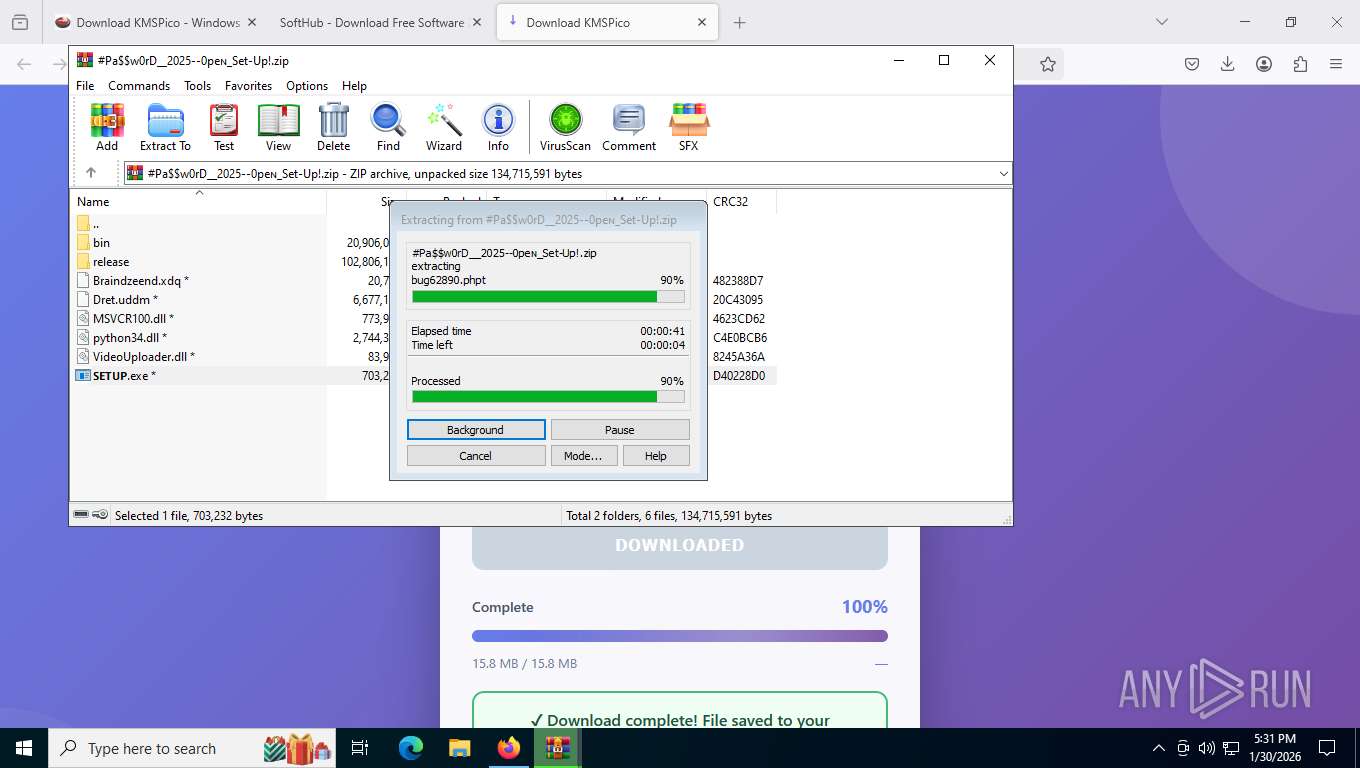
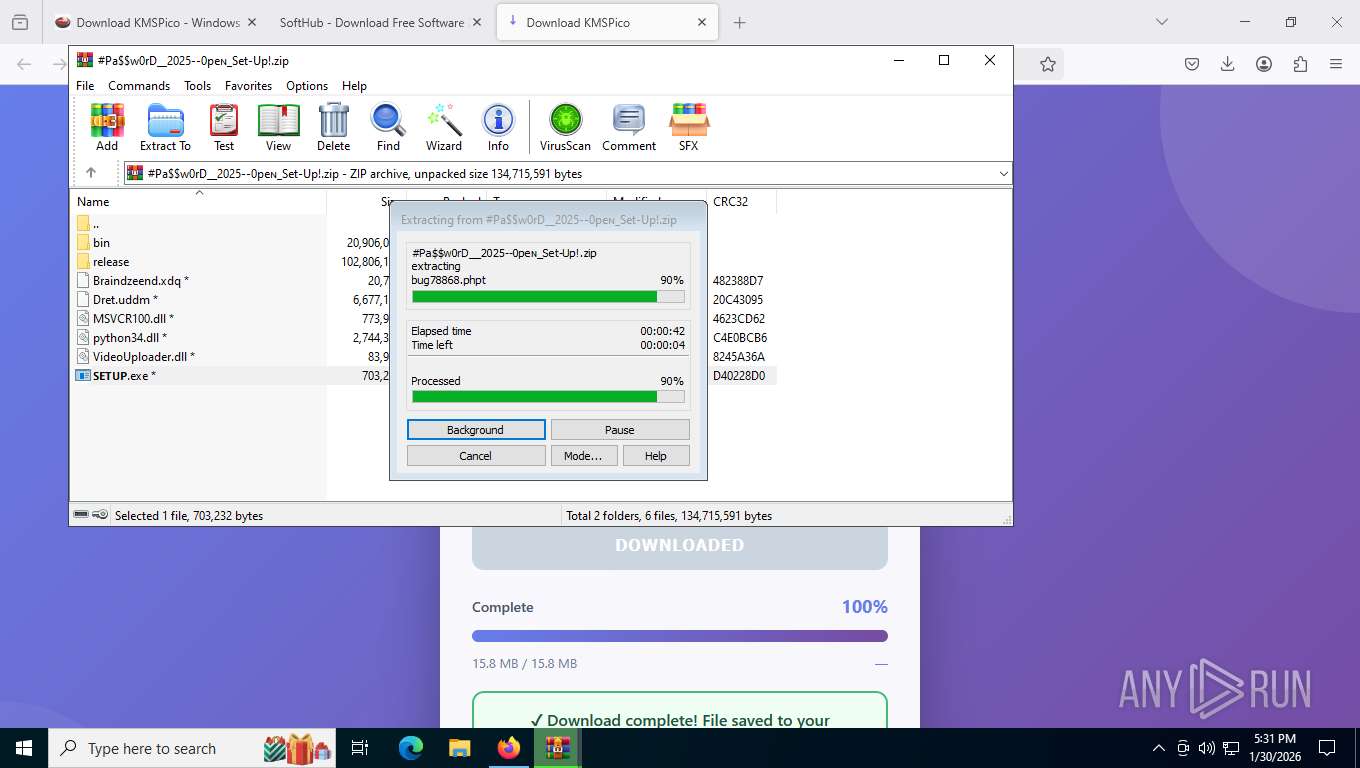
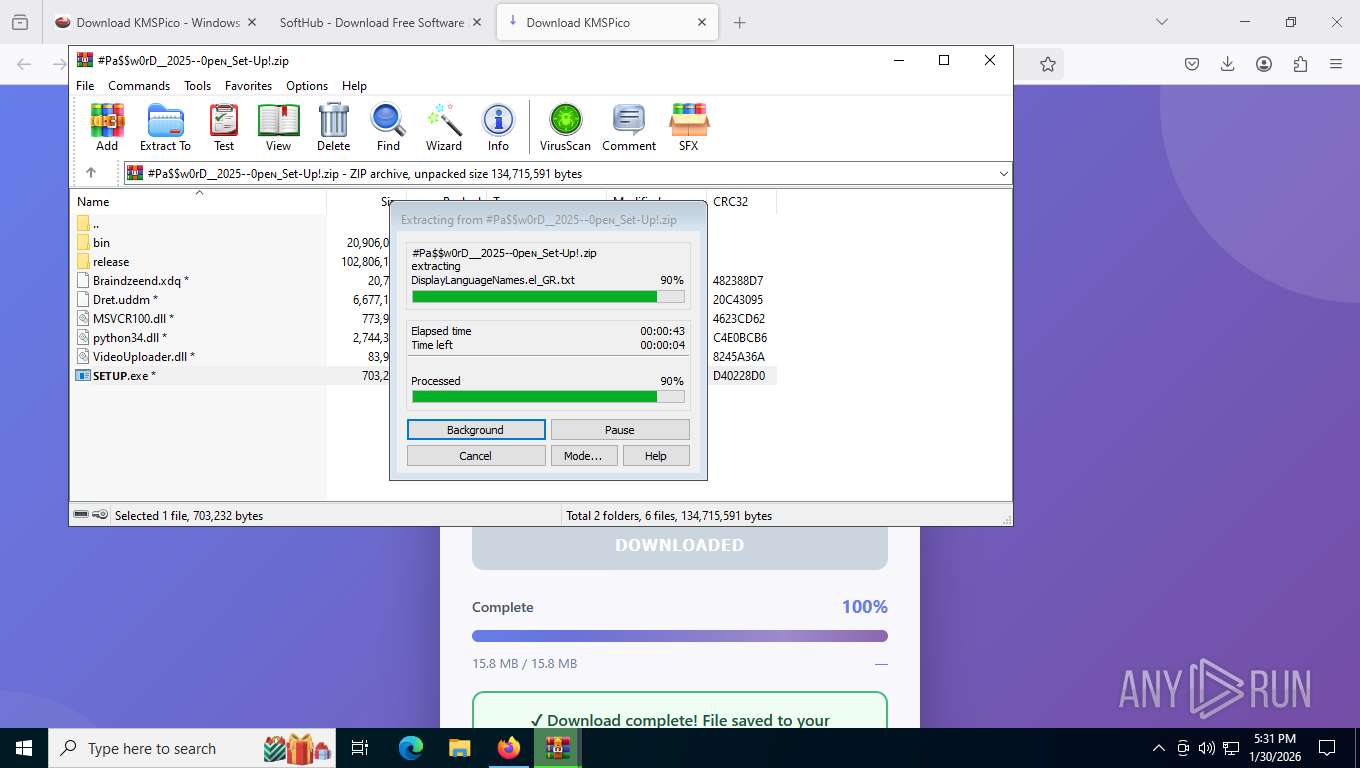
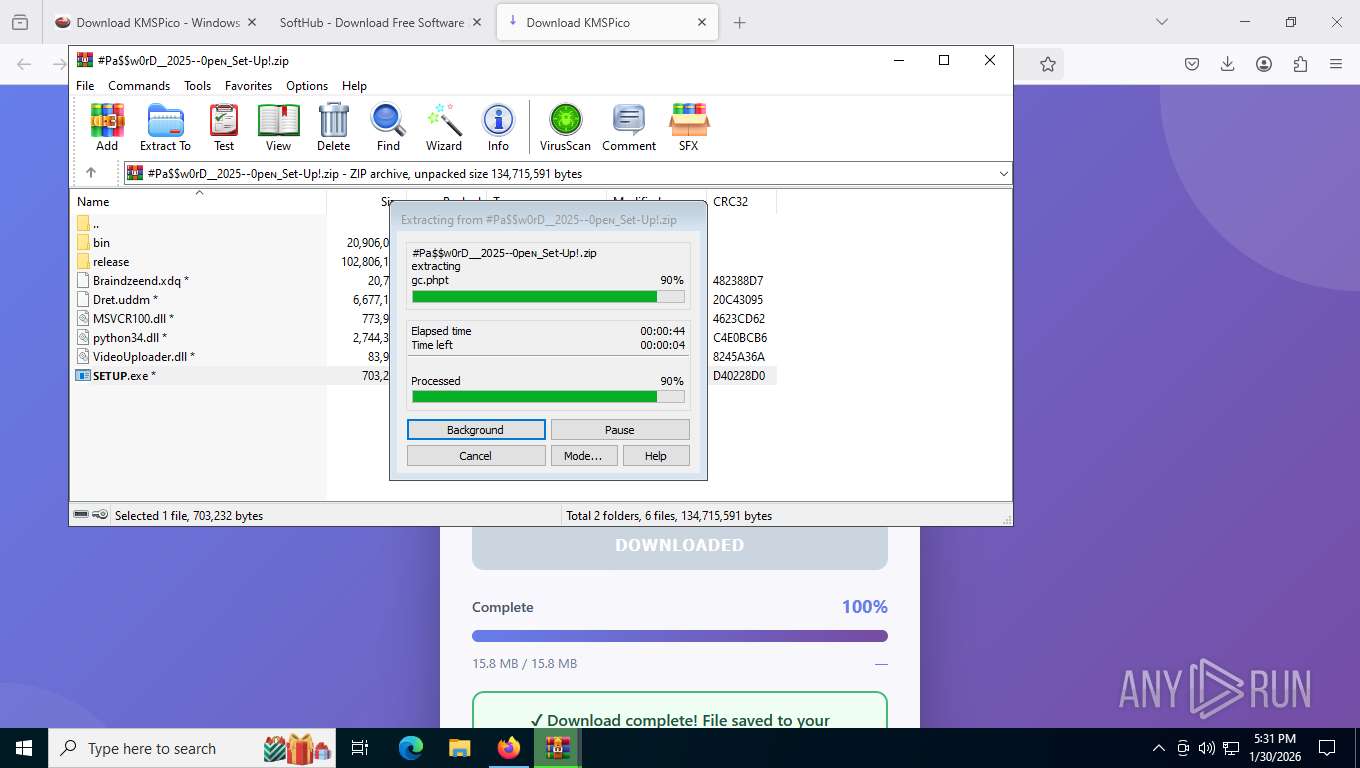
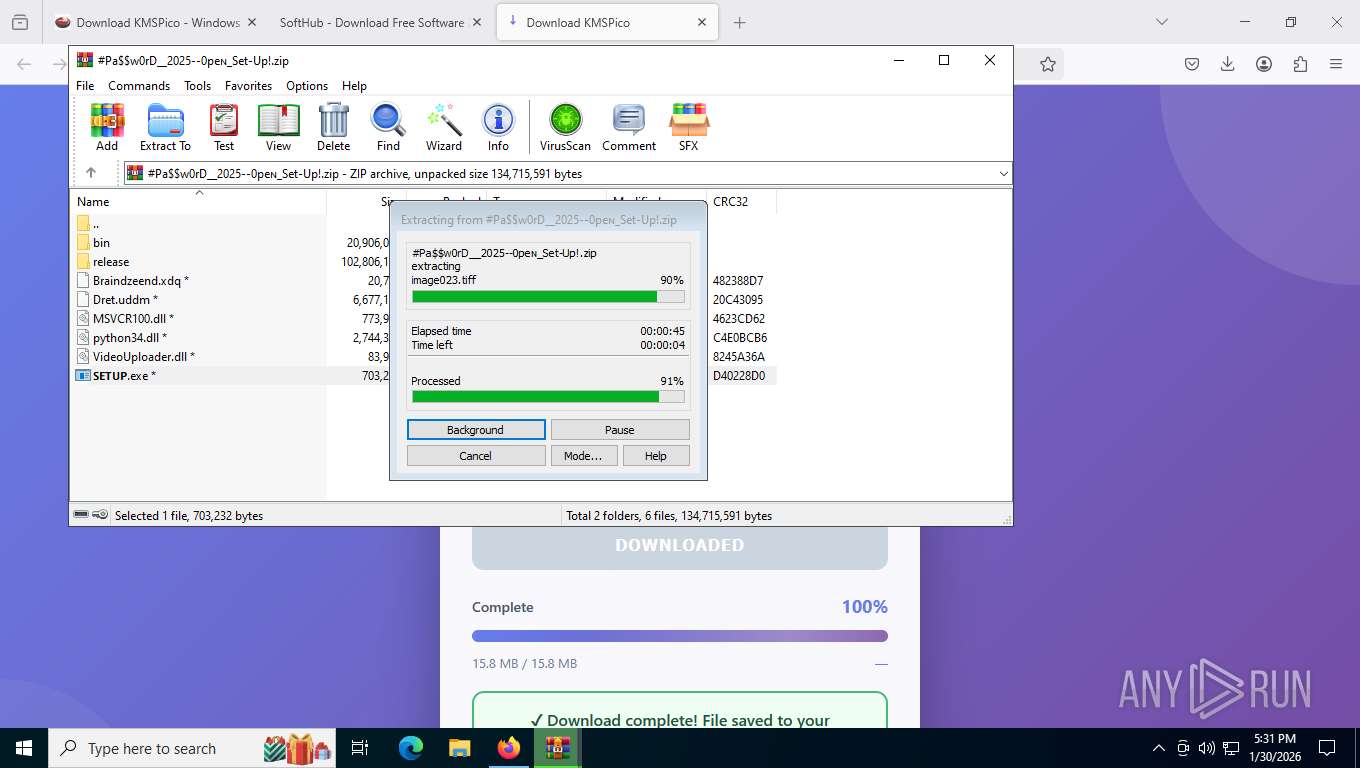
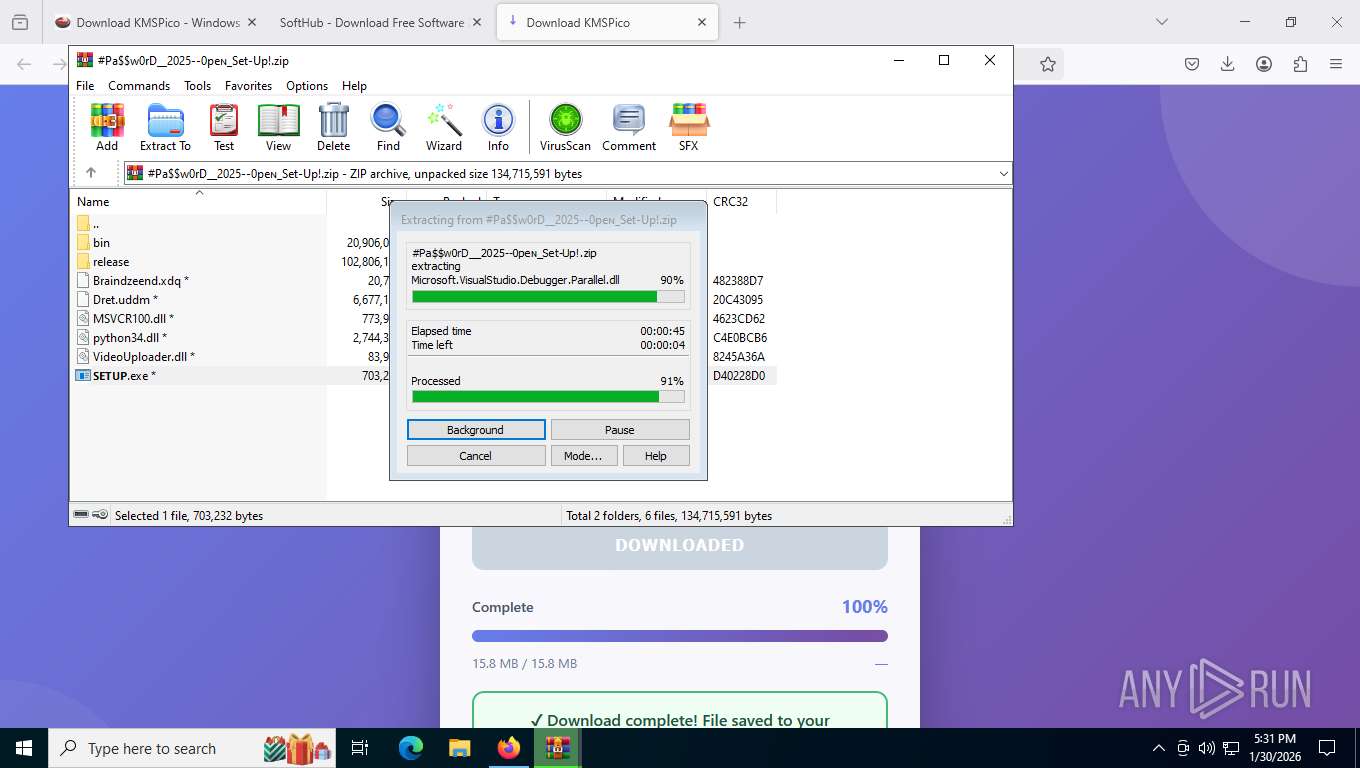
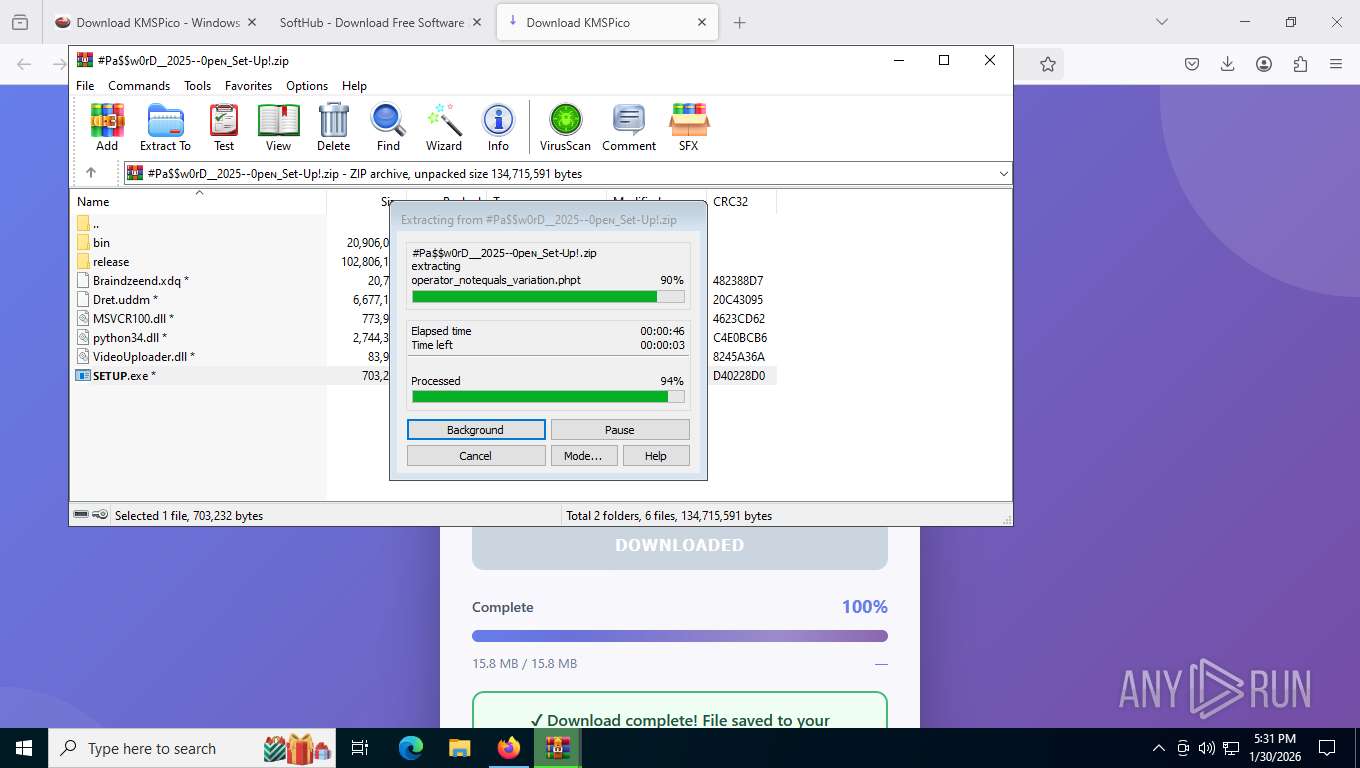
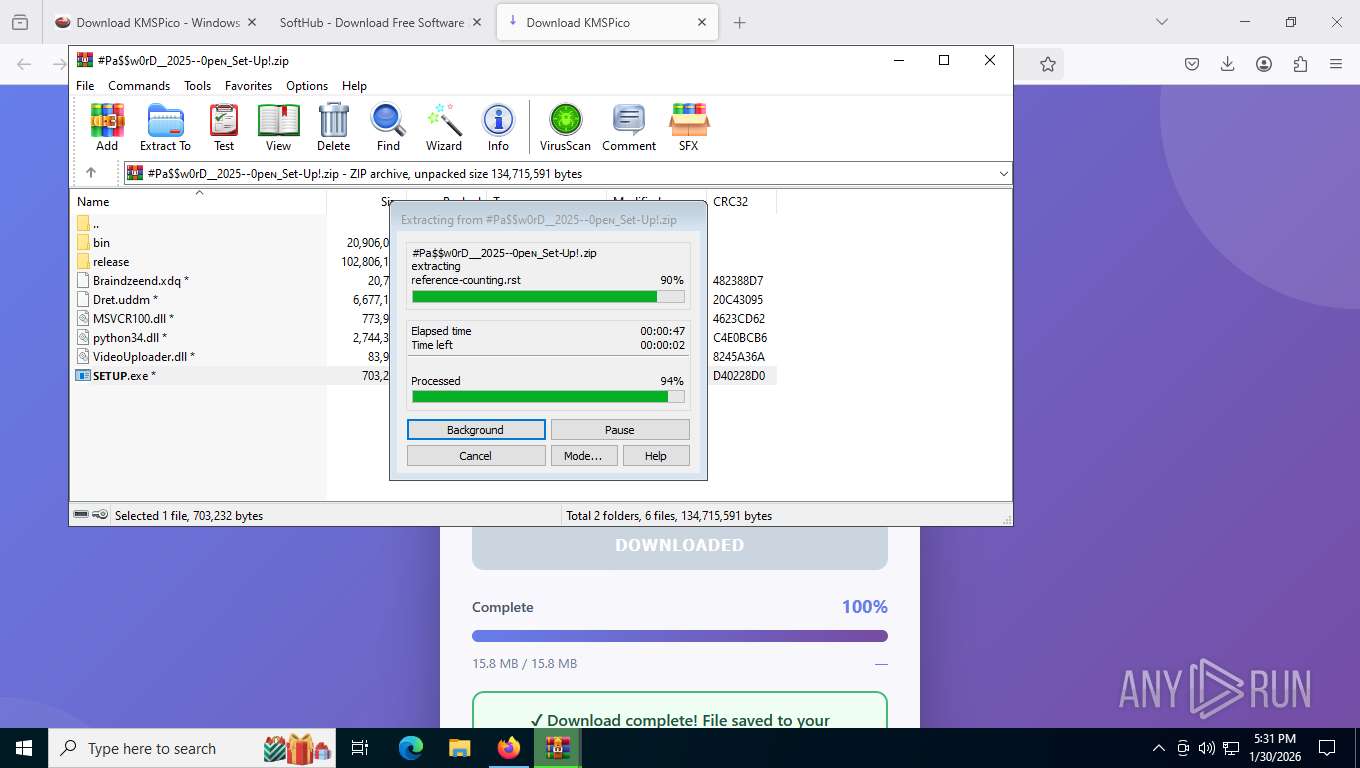
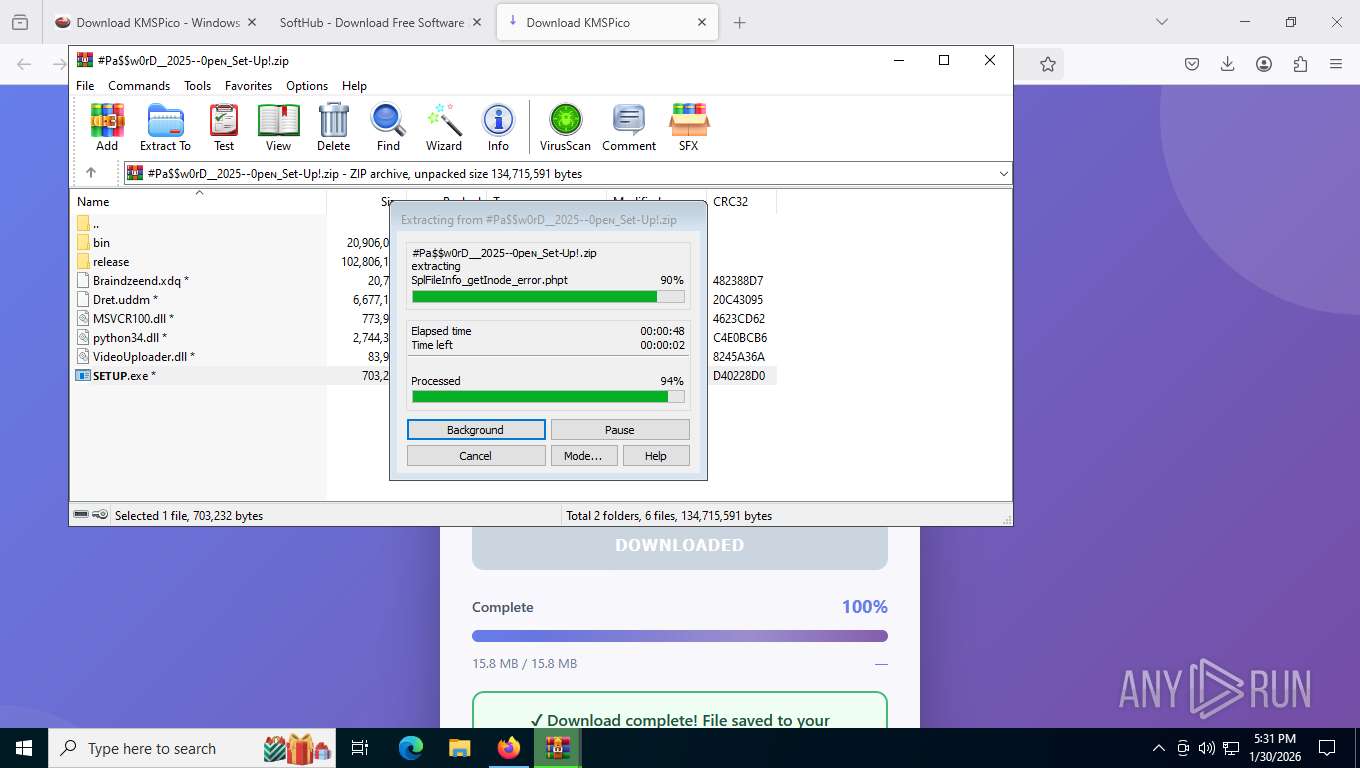
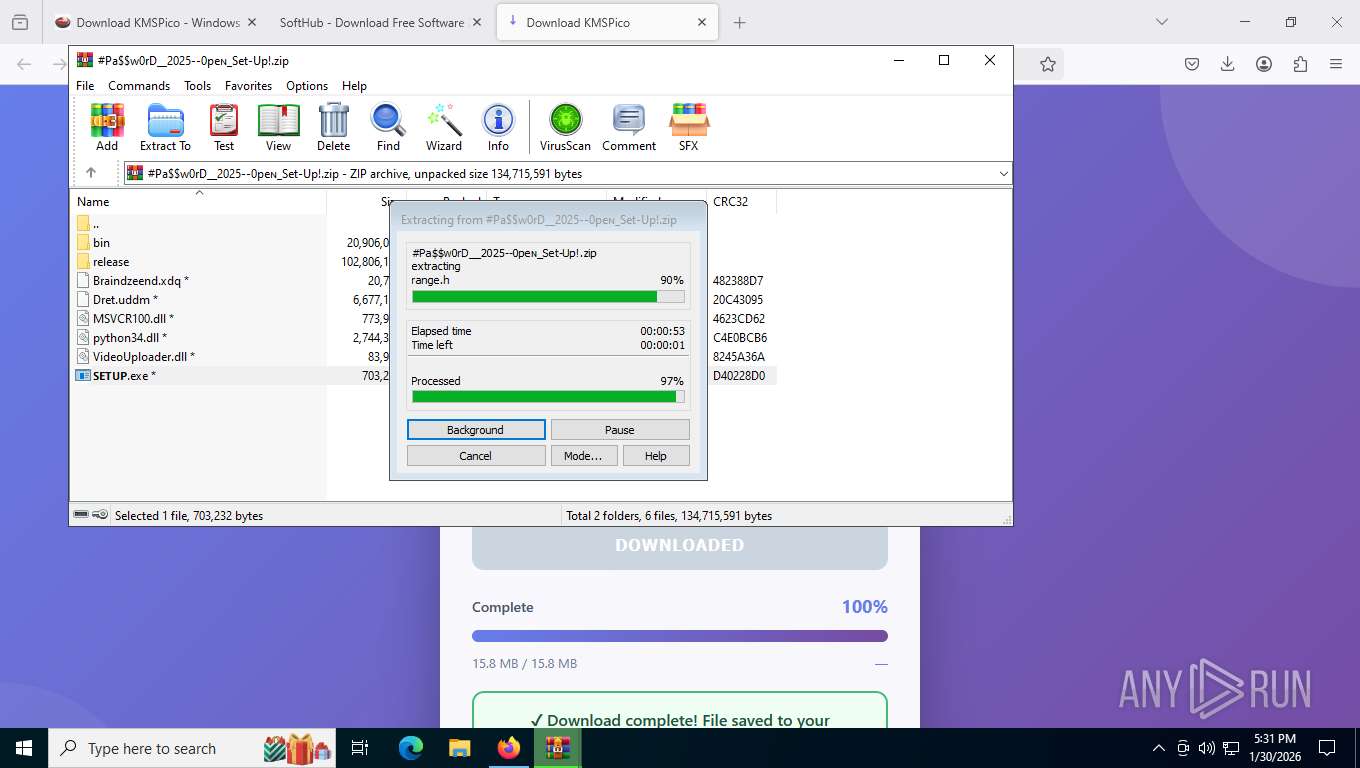
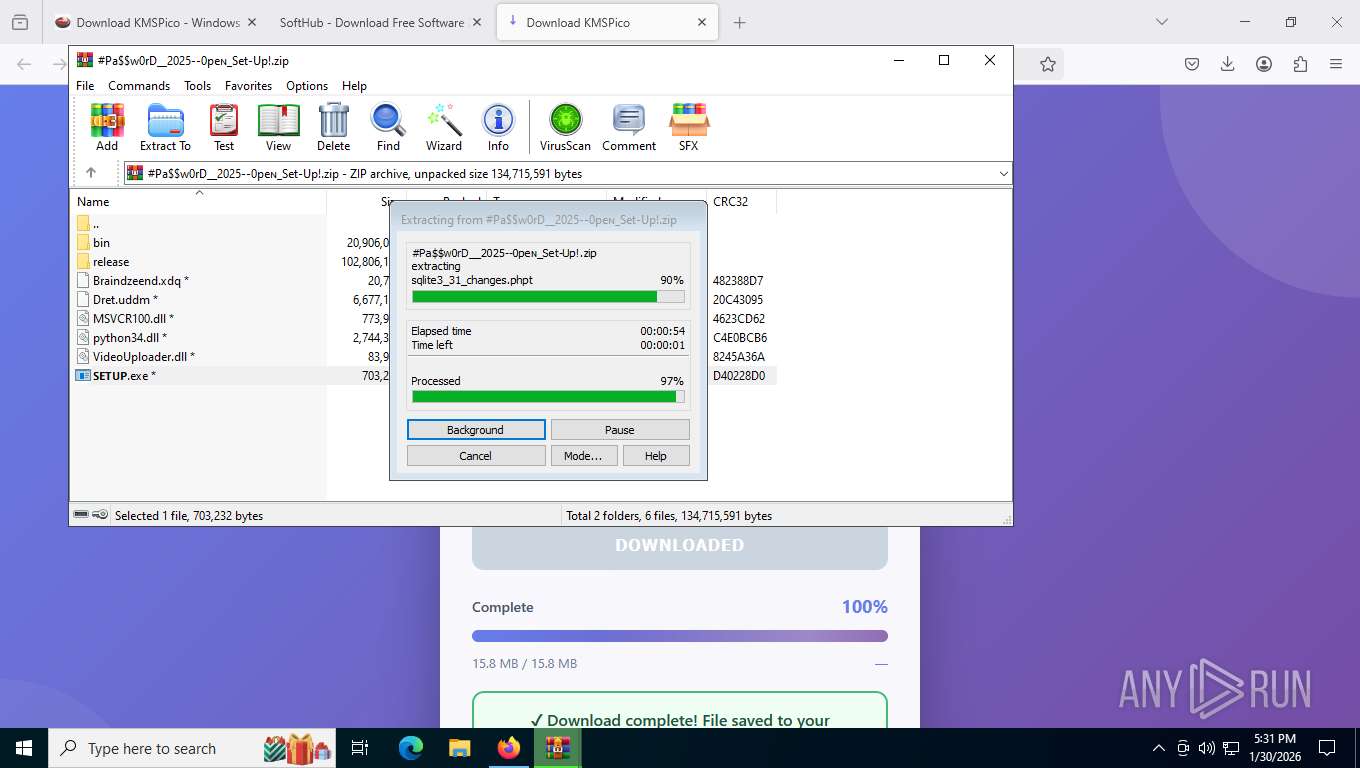
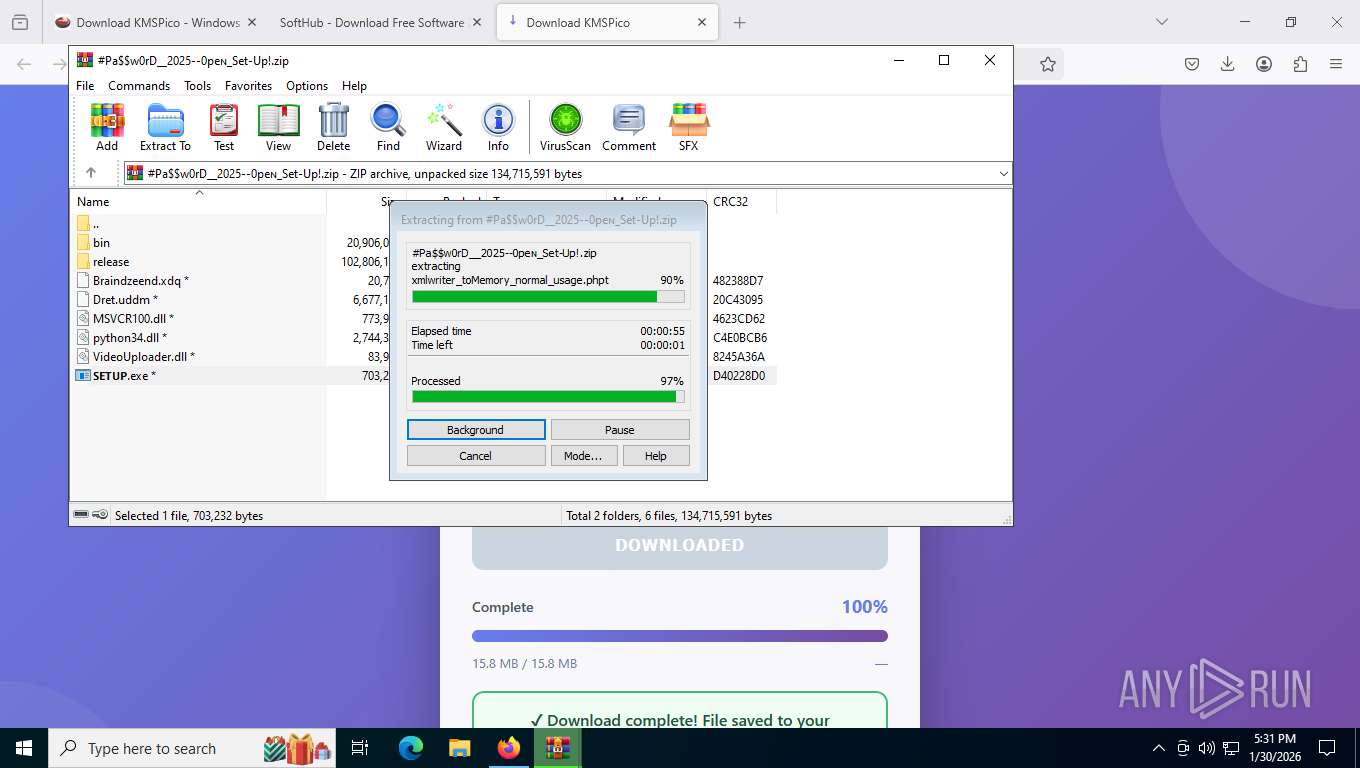
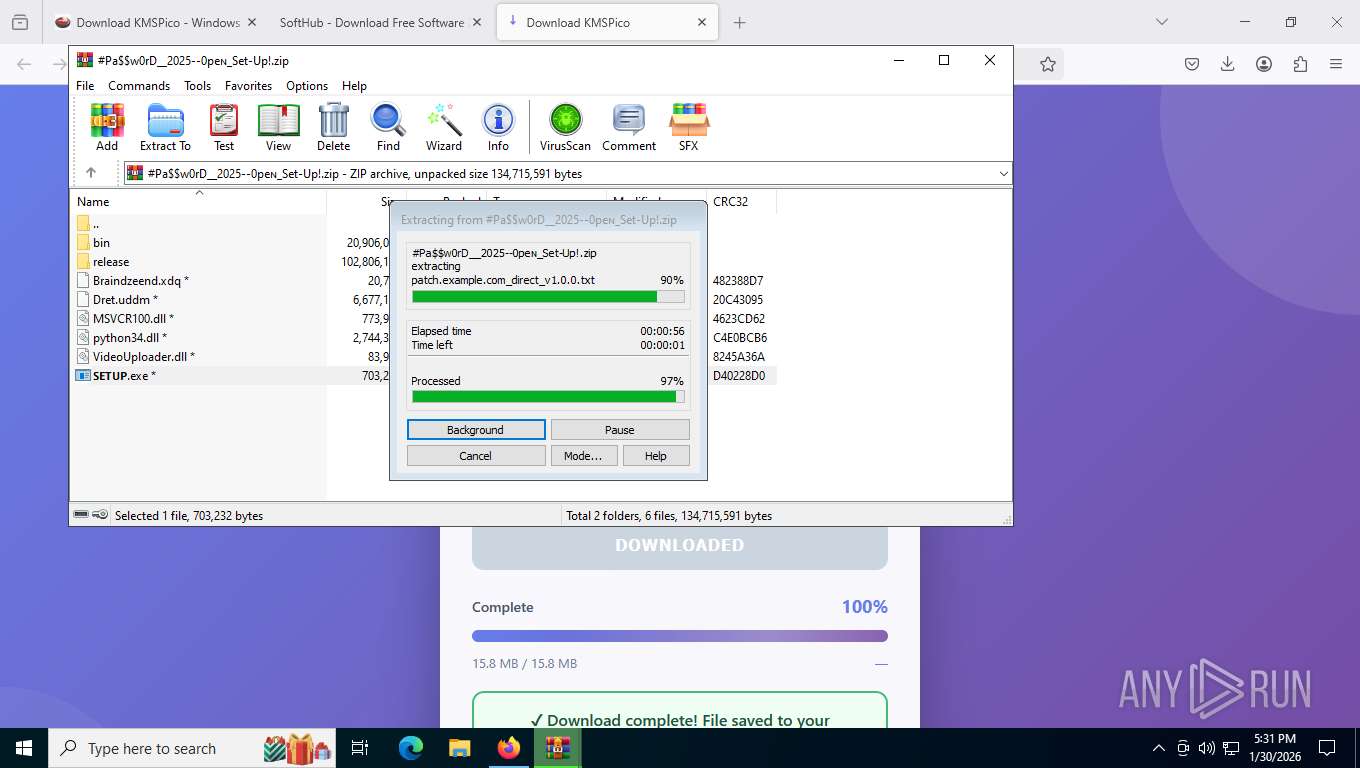
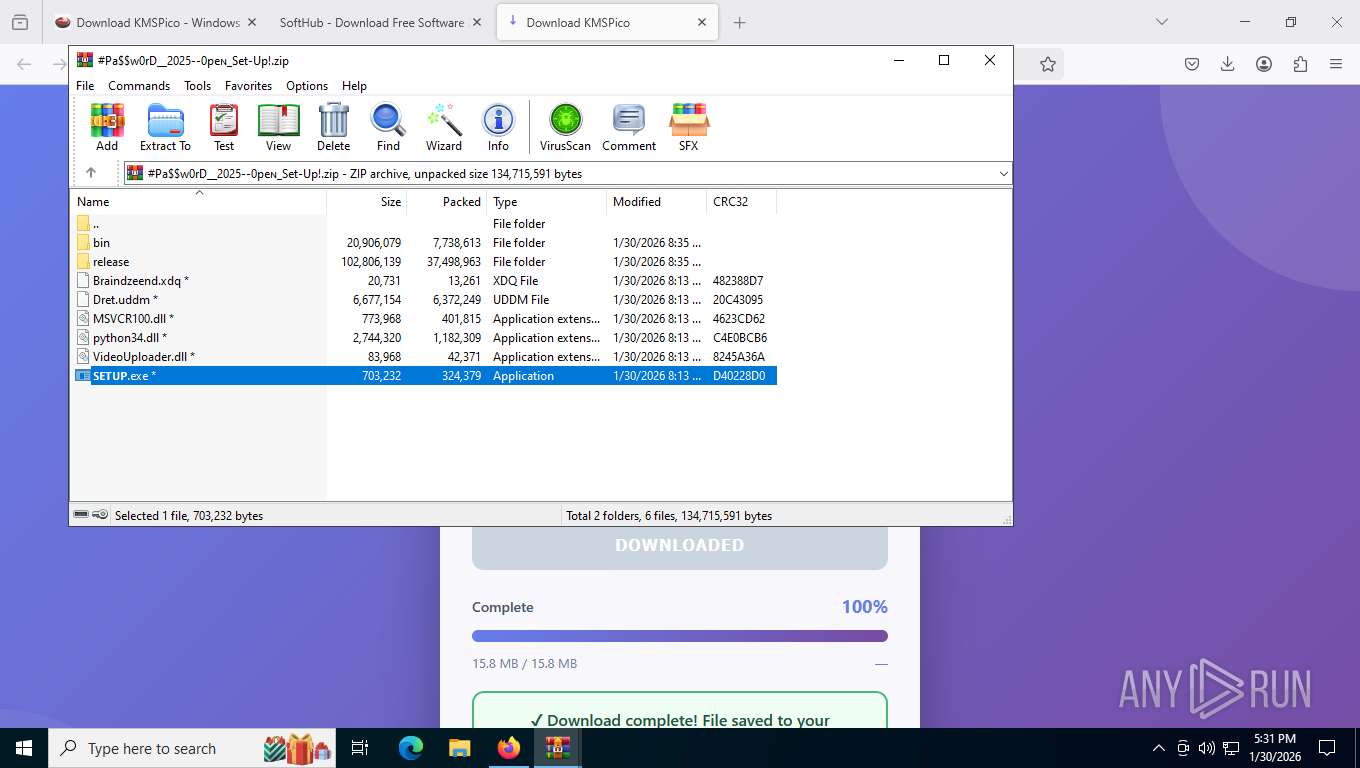
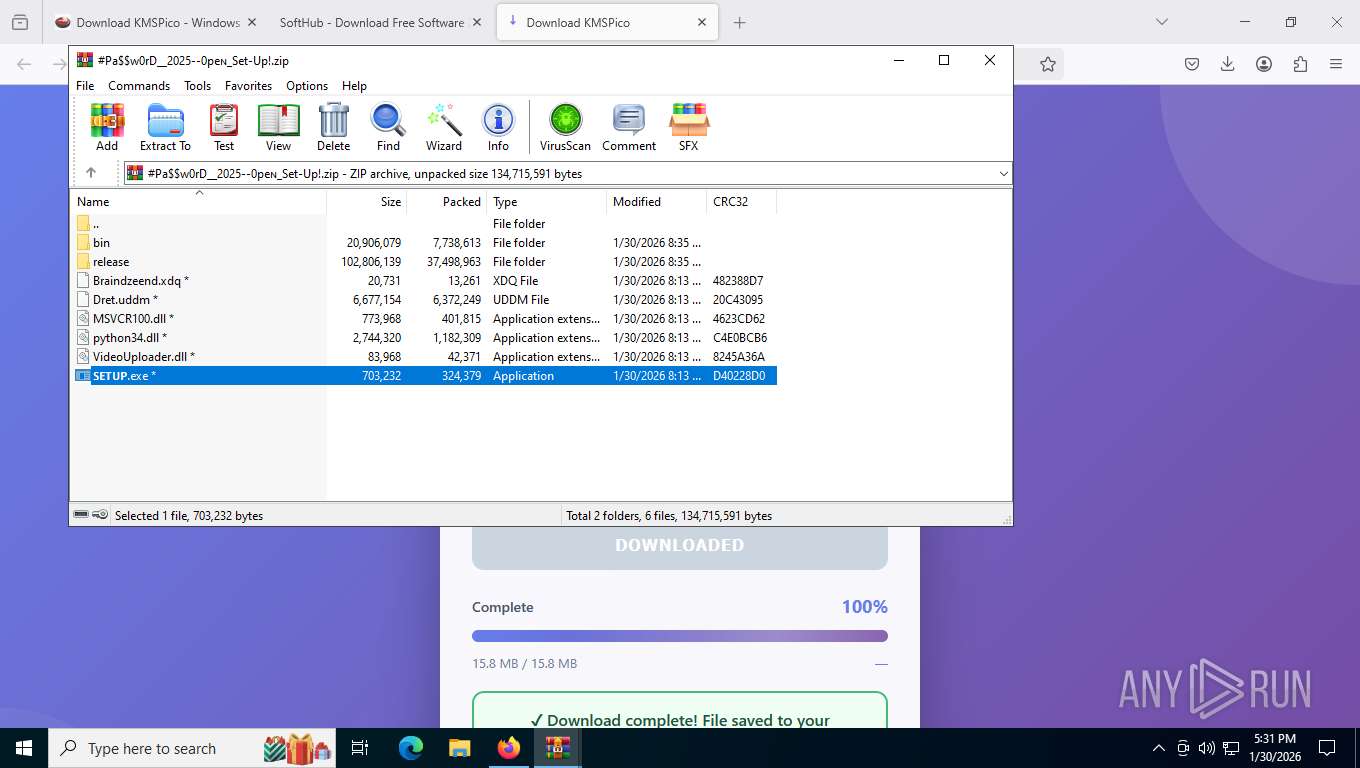
Process drops legitimate windows executable
- firefox.exe (PID: 7704)
- WinRAR.exe (PID: 676)
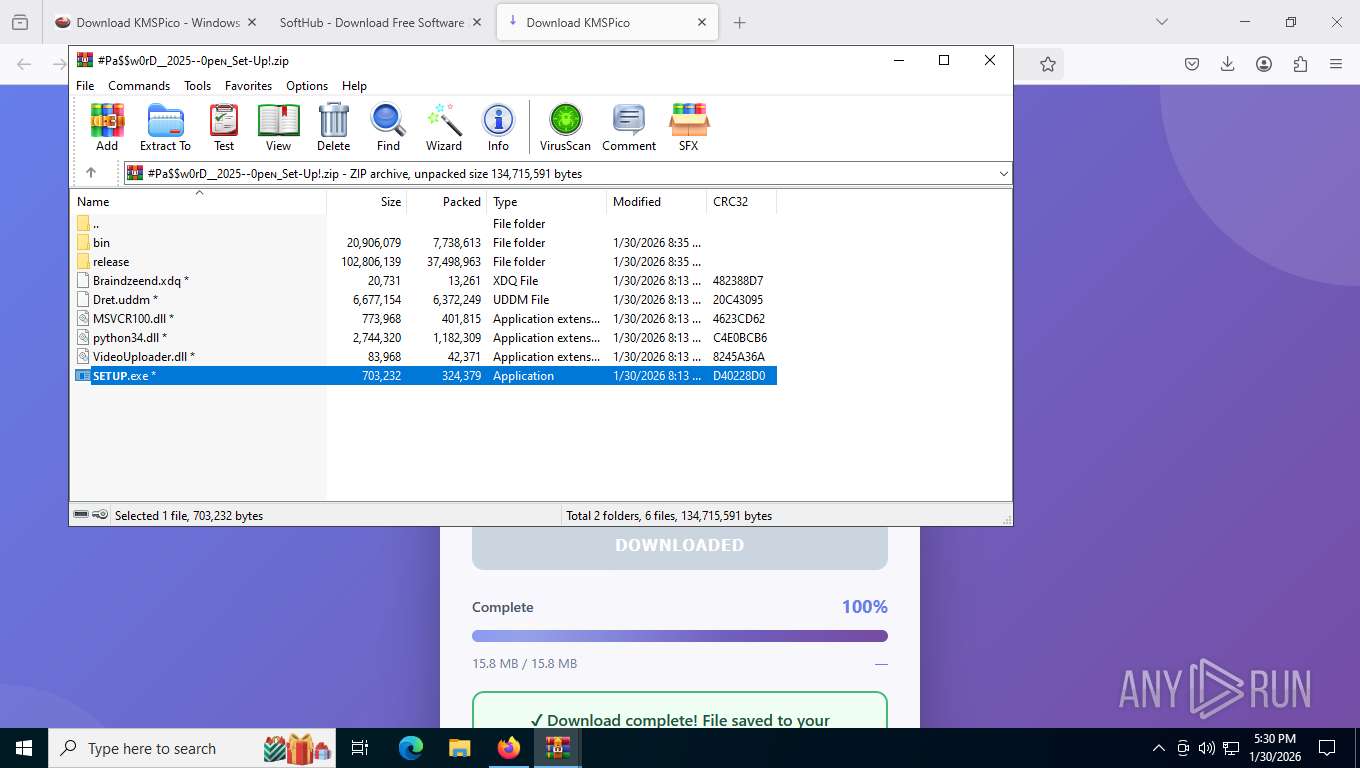
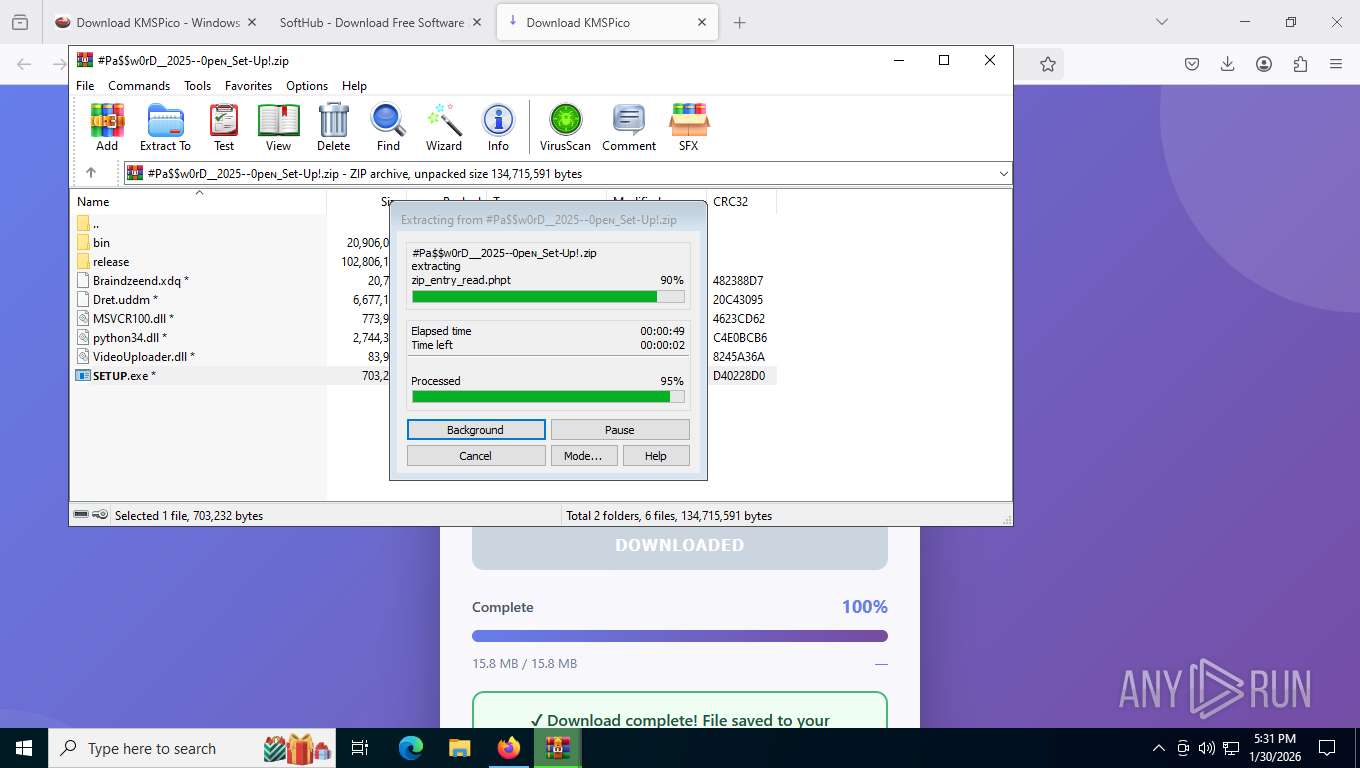
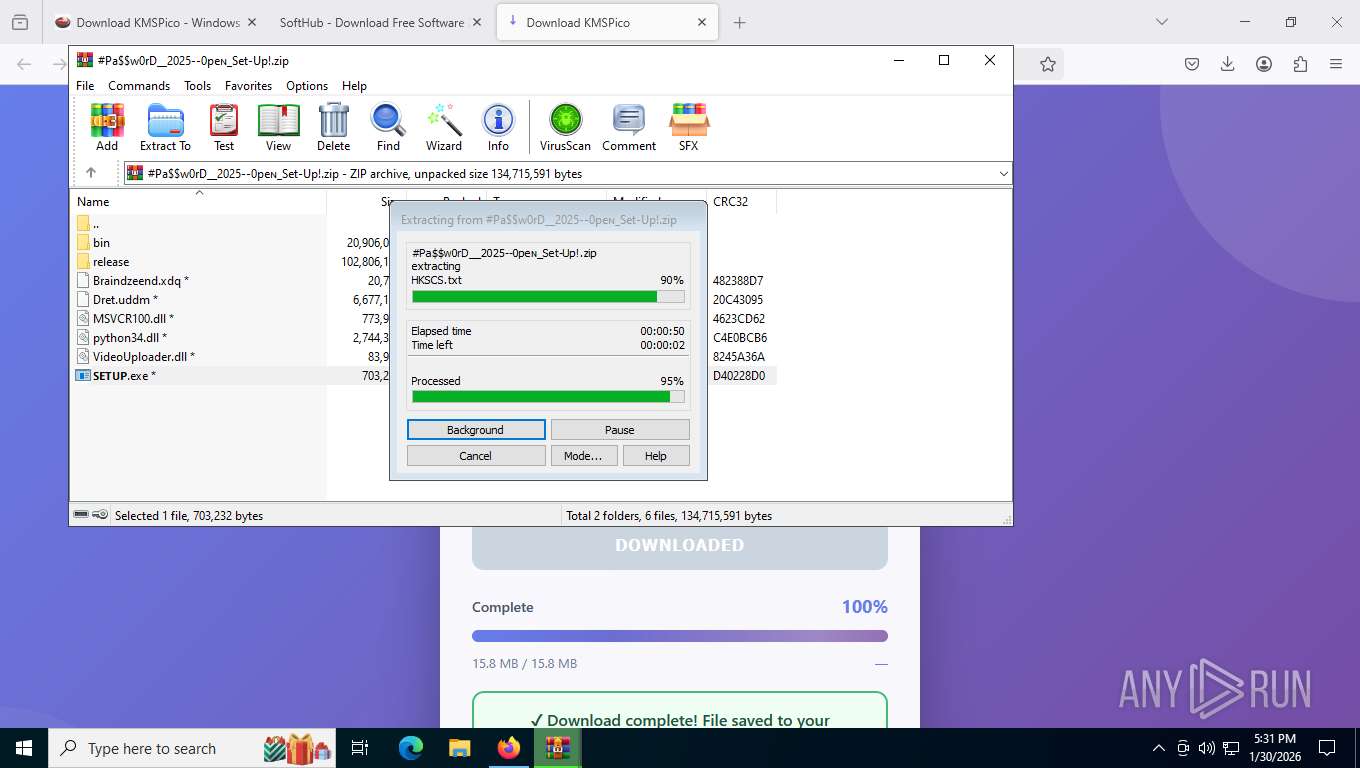
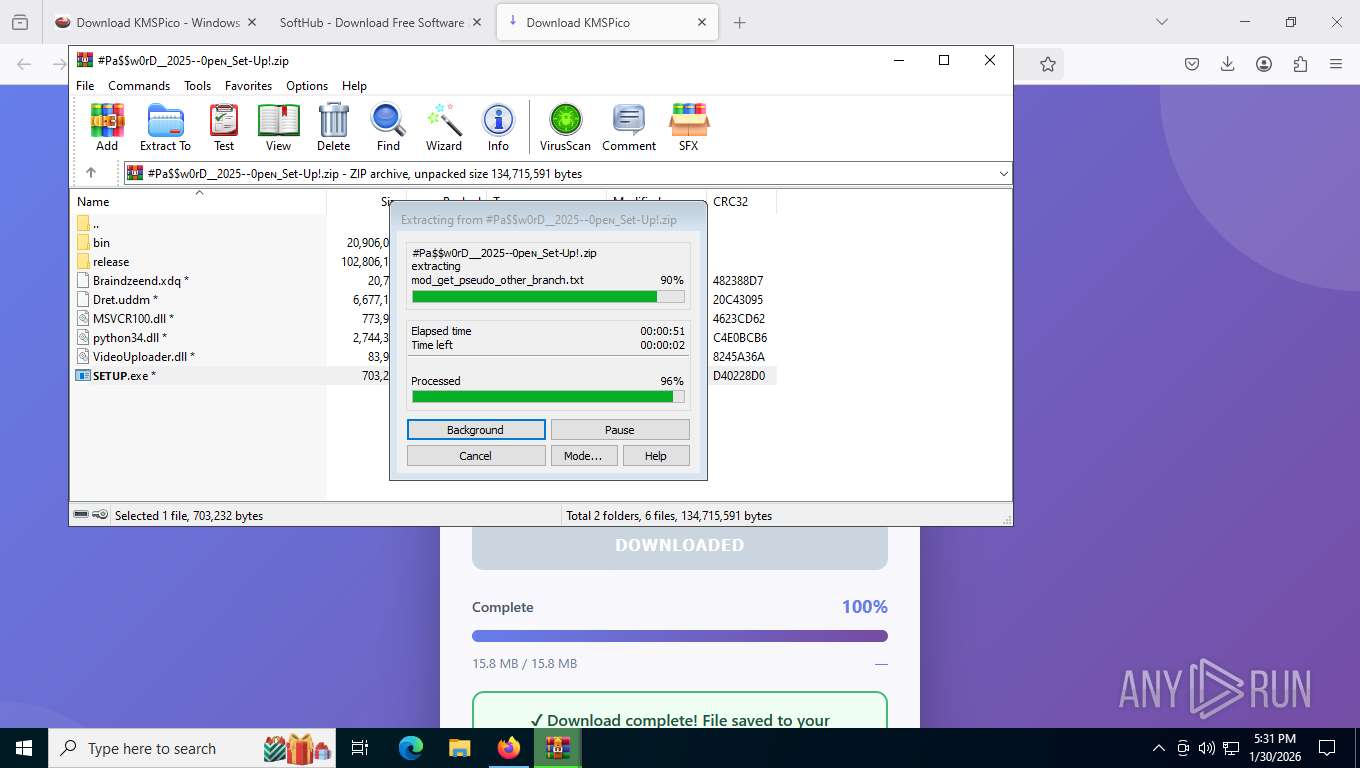
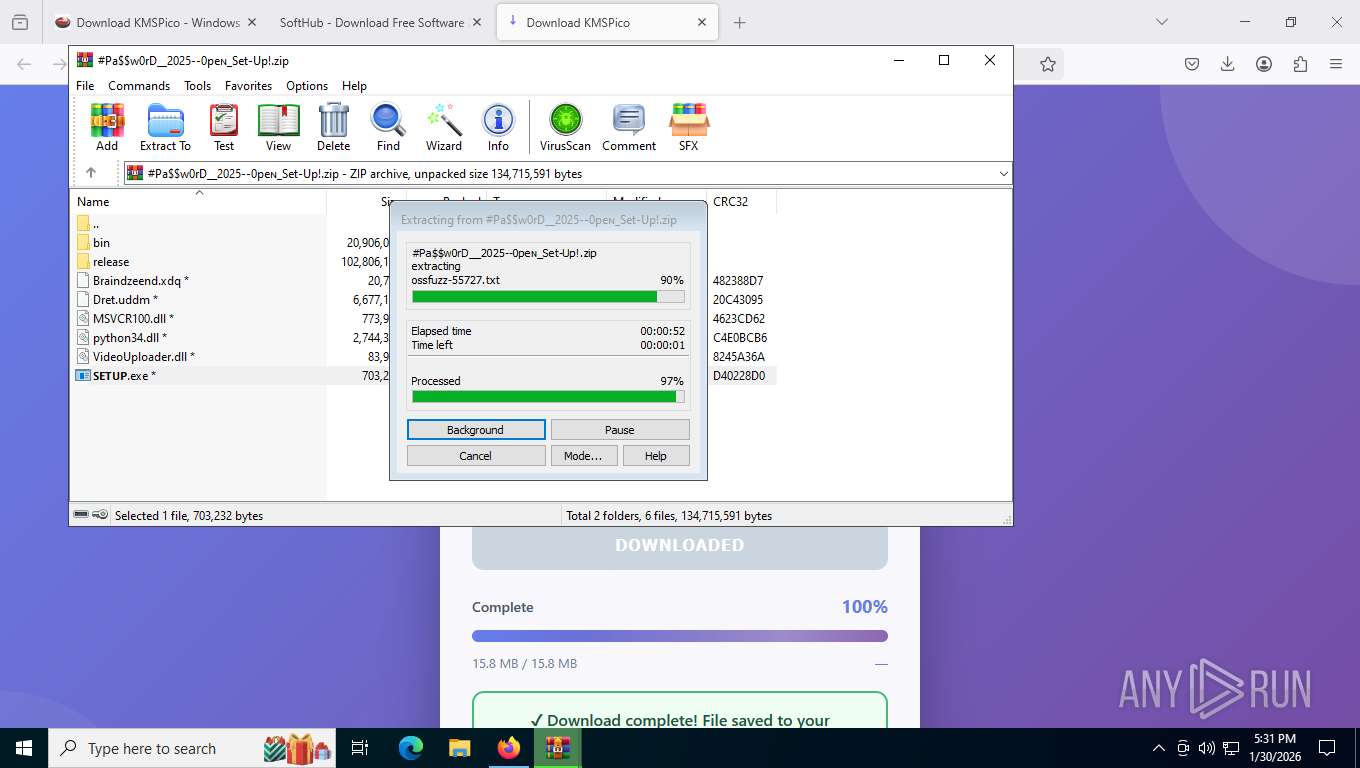
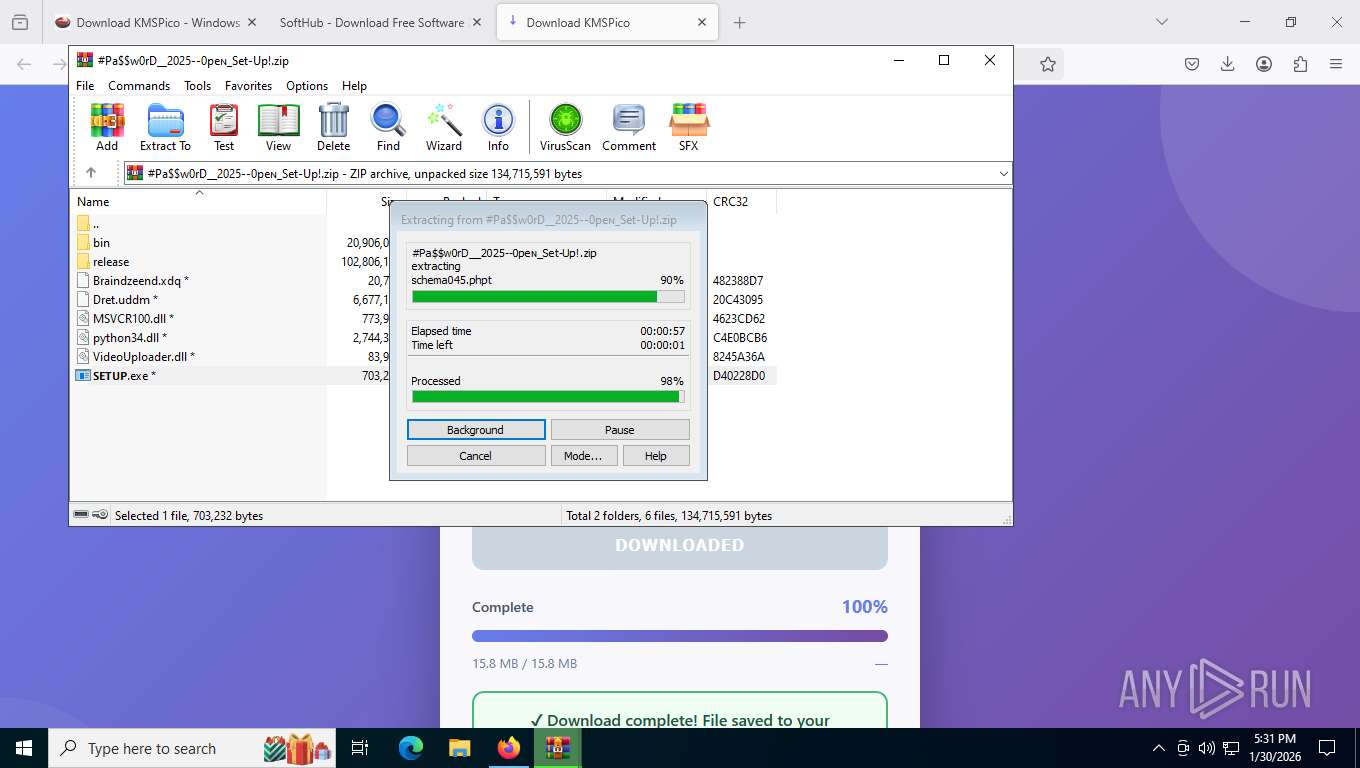
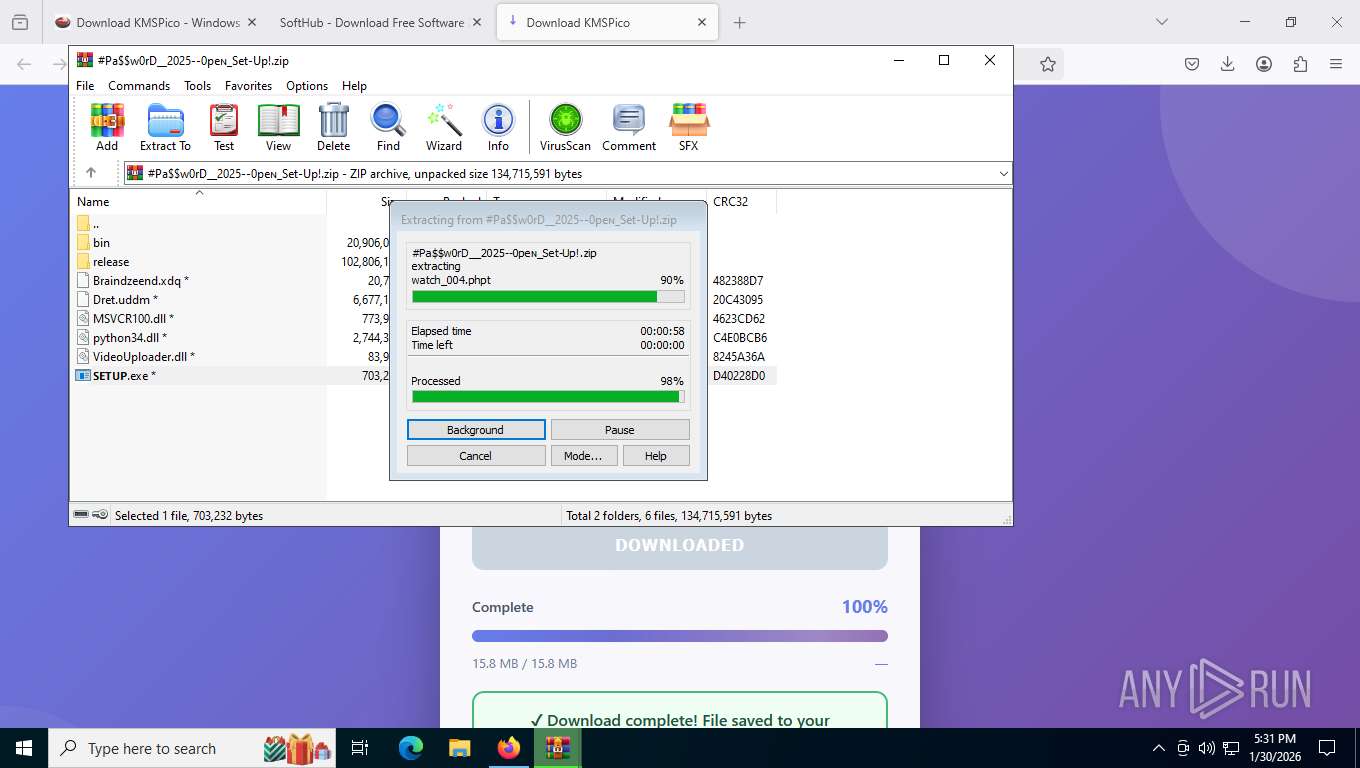
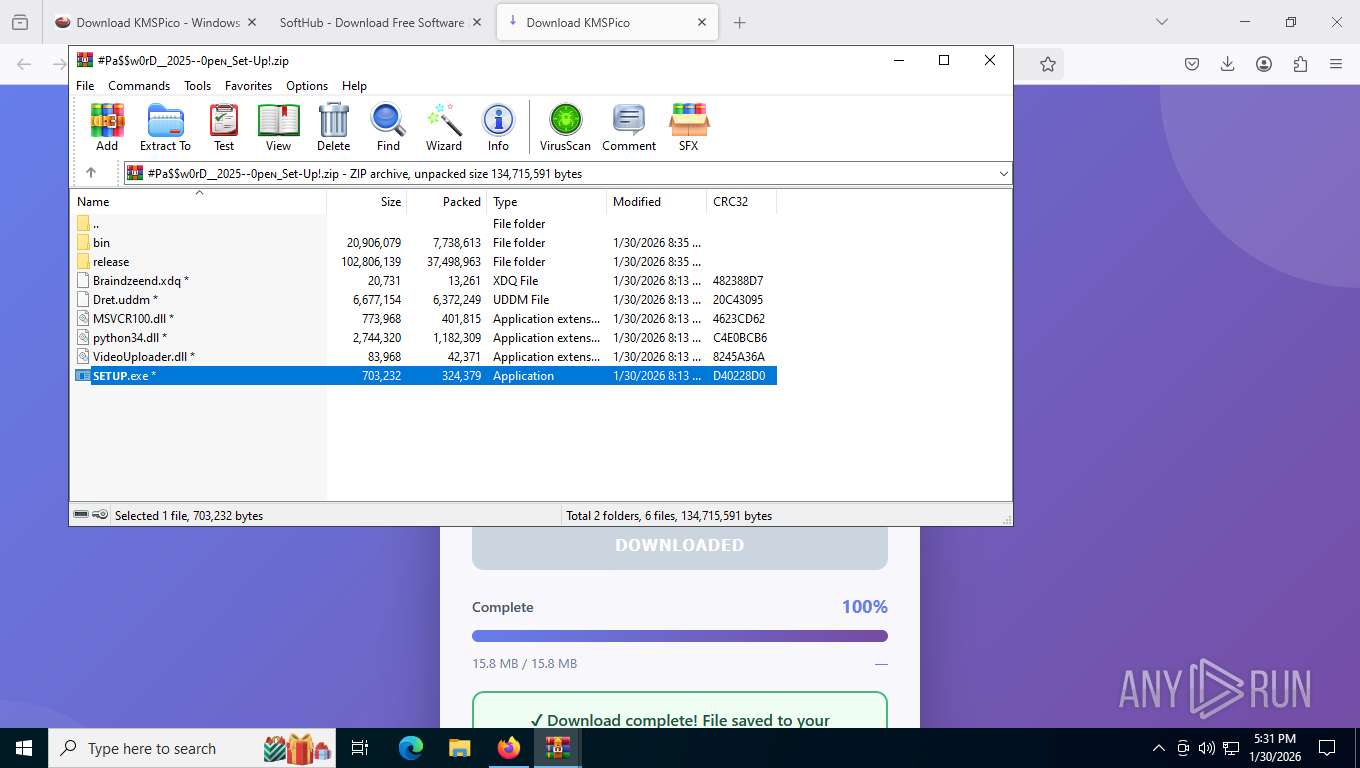
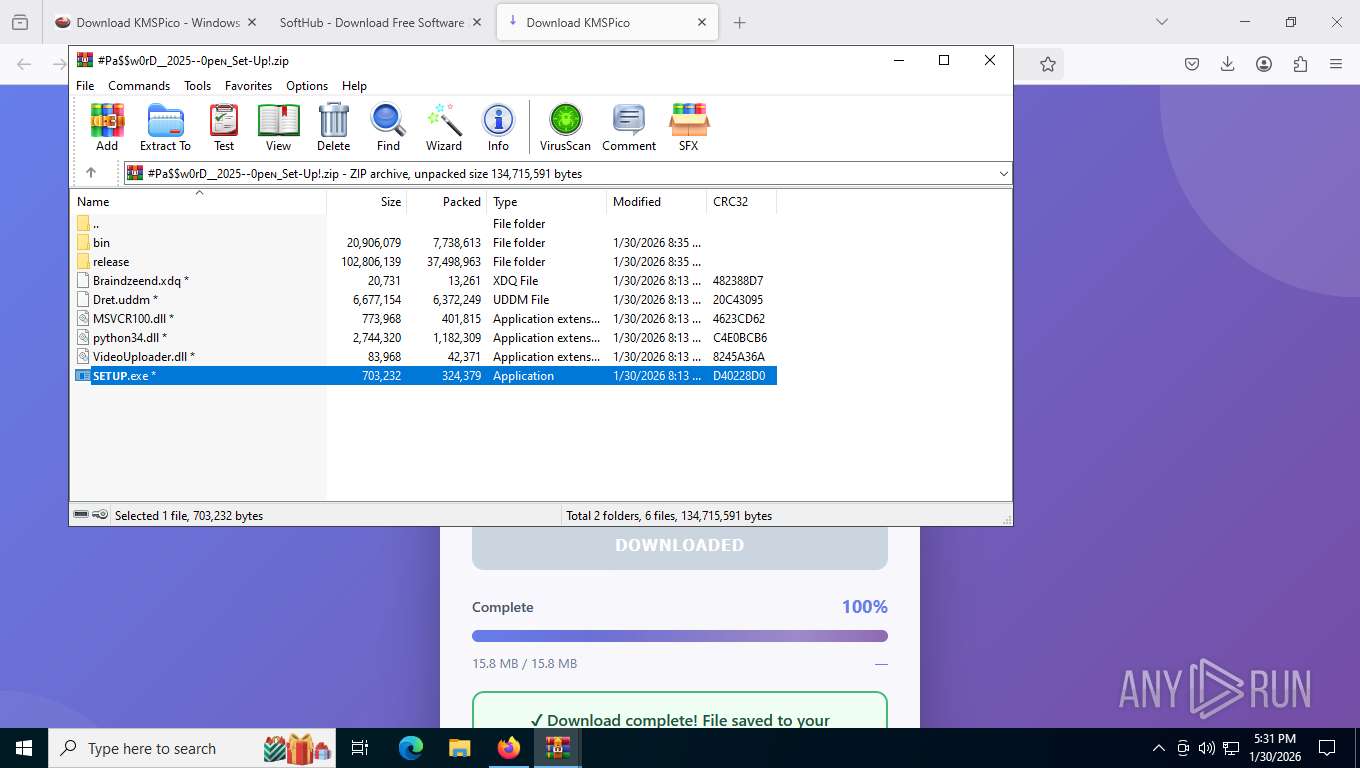
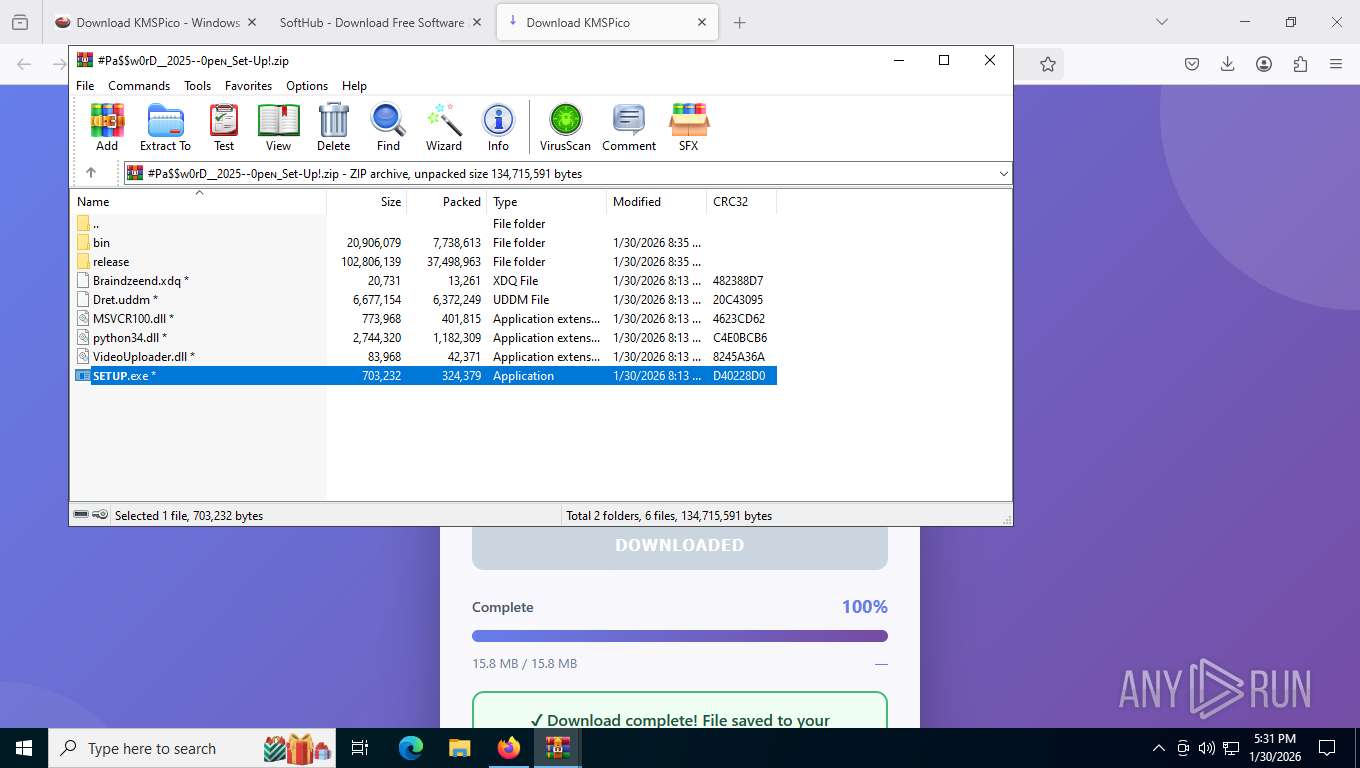
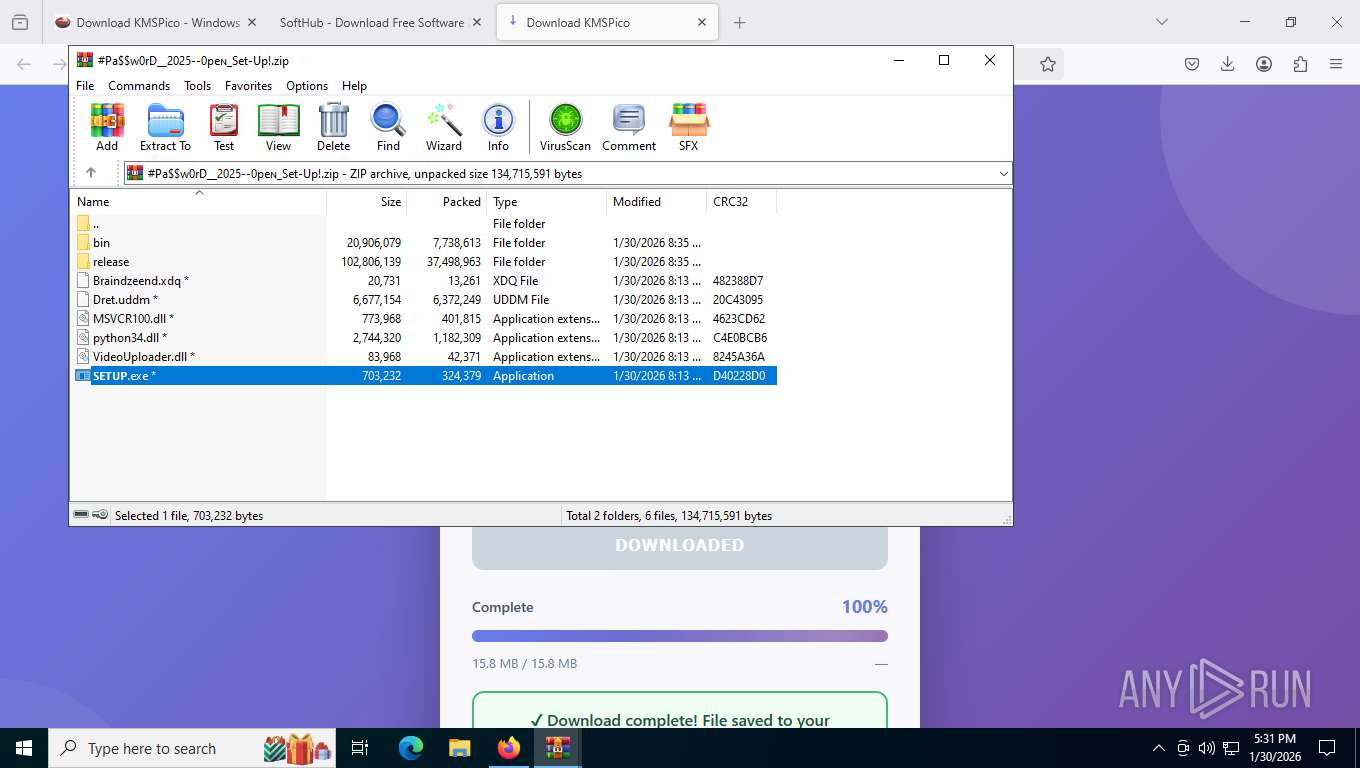
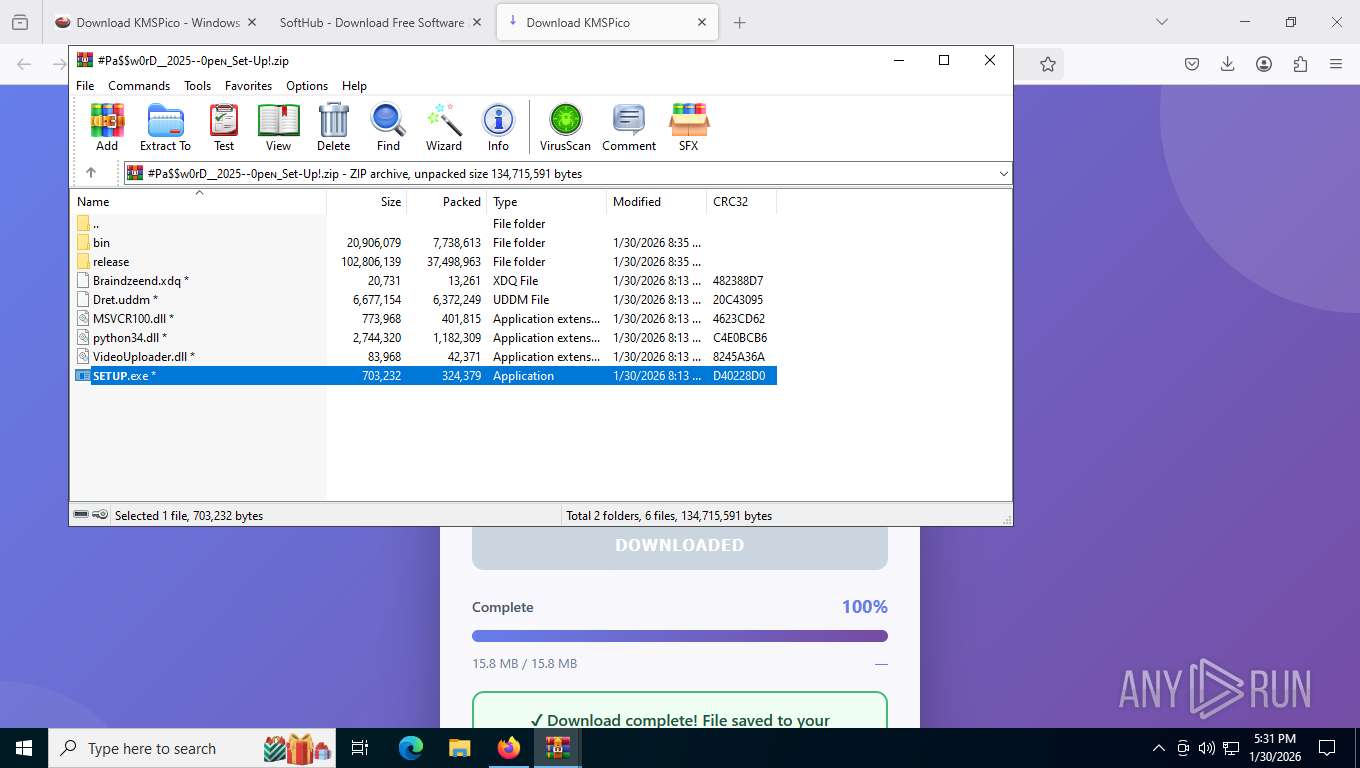
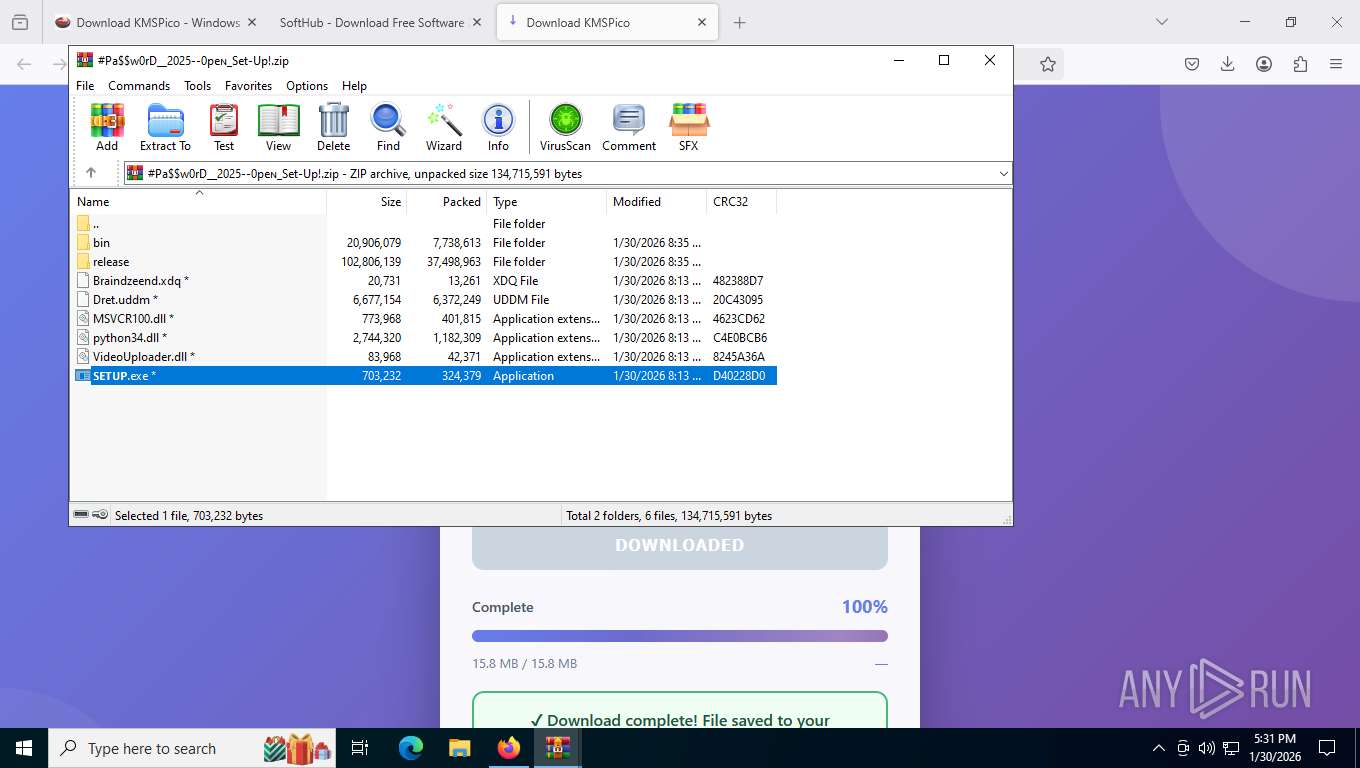
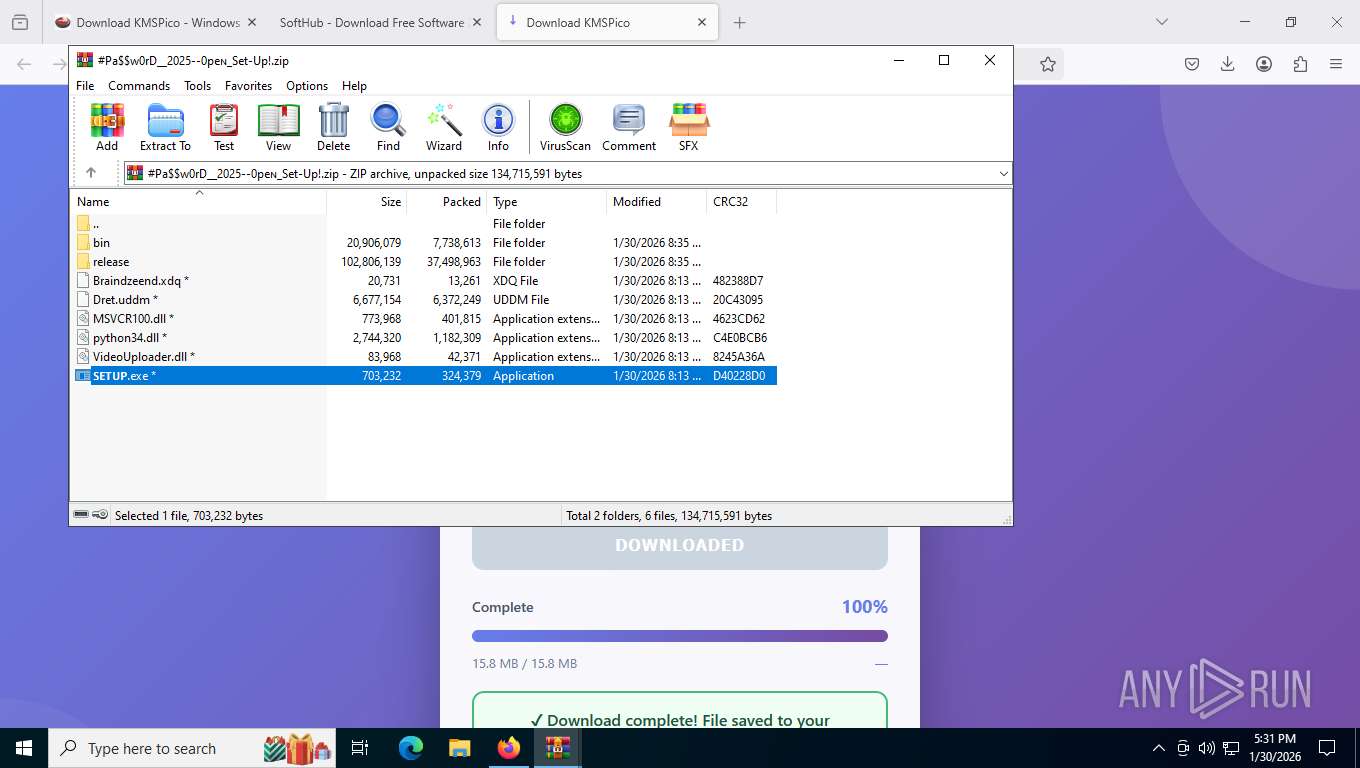
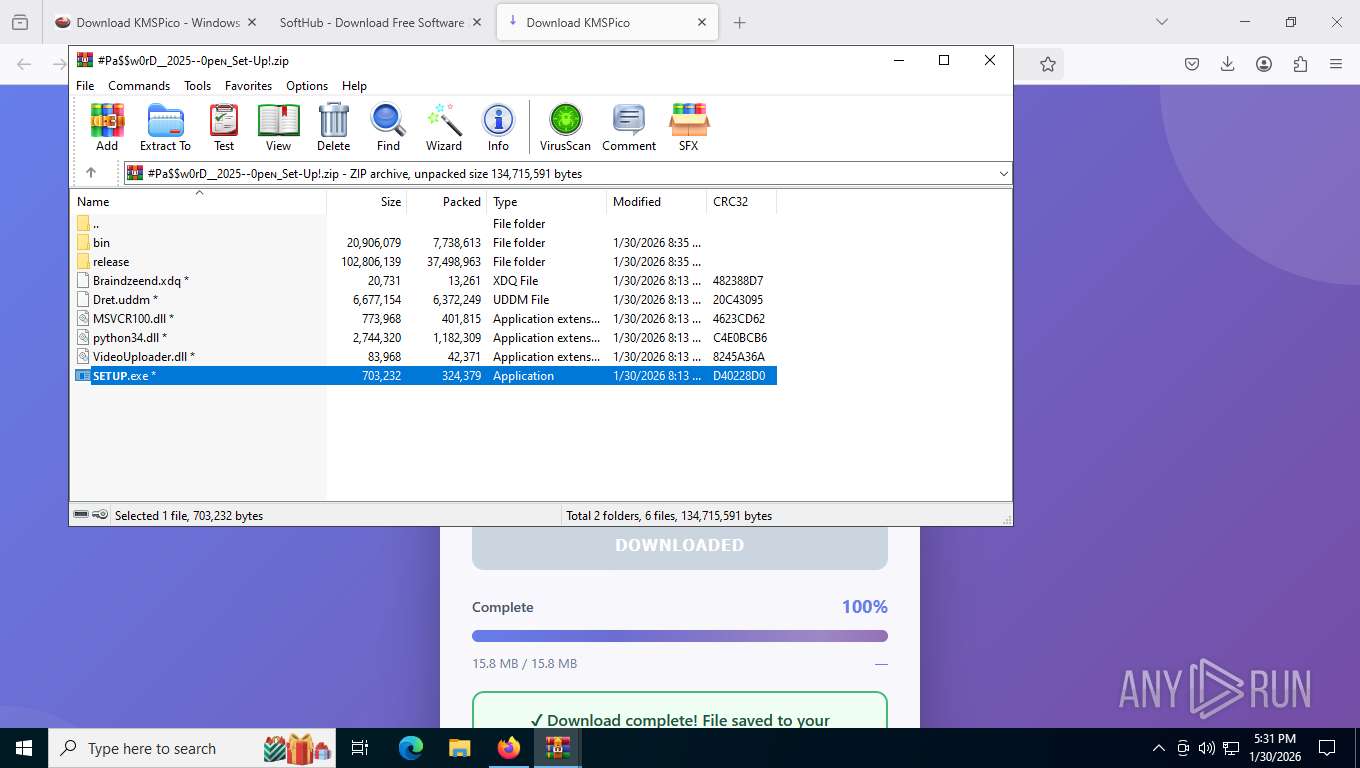
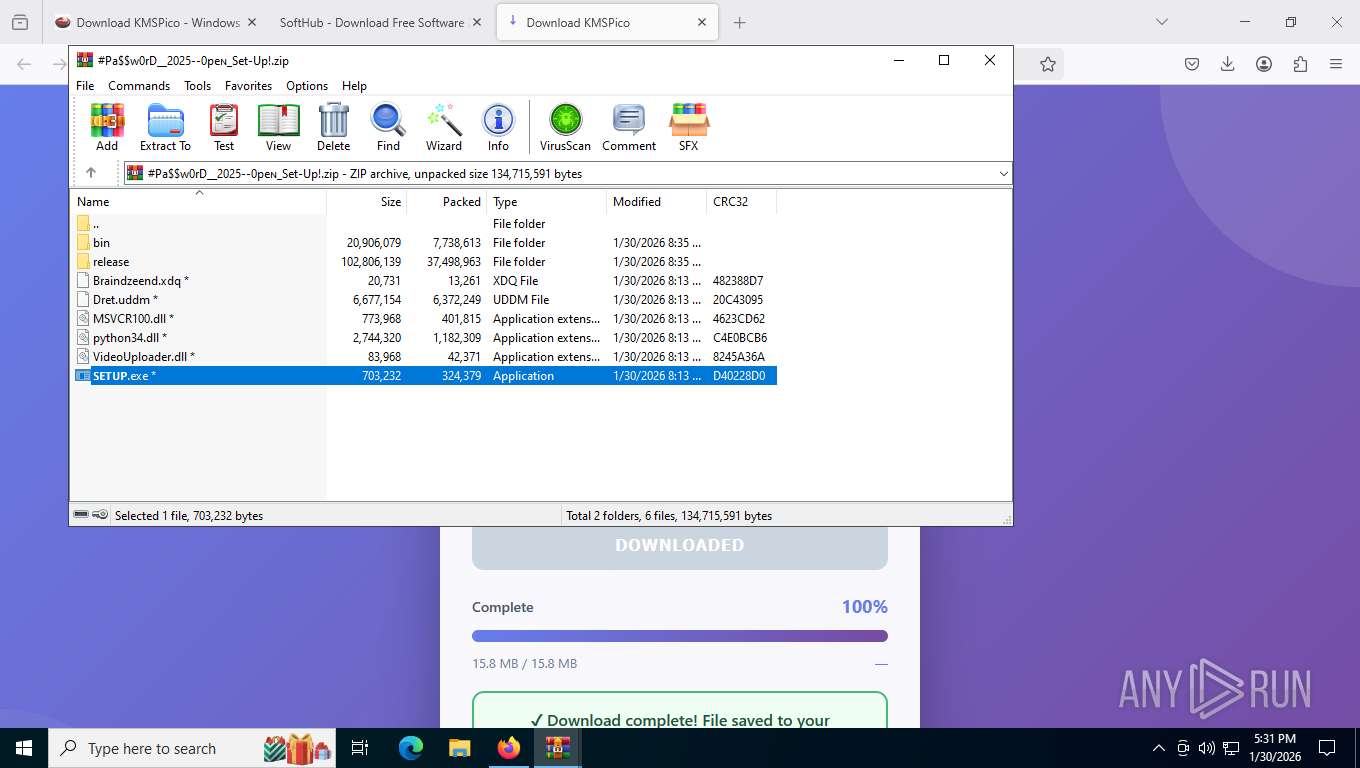
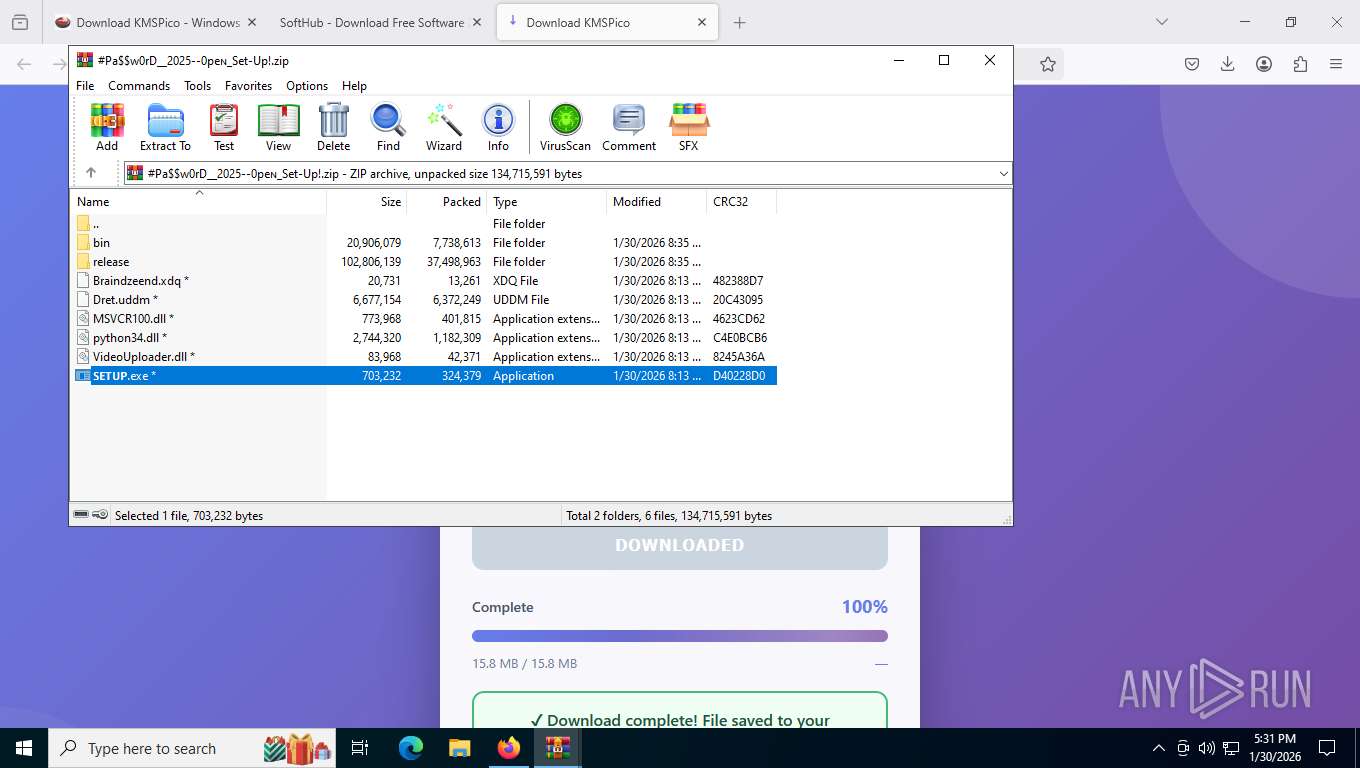
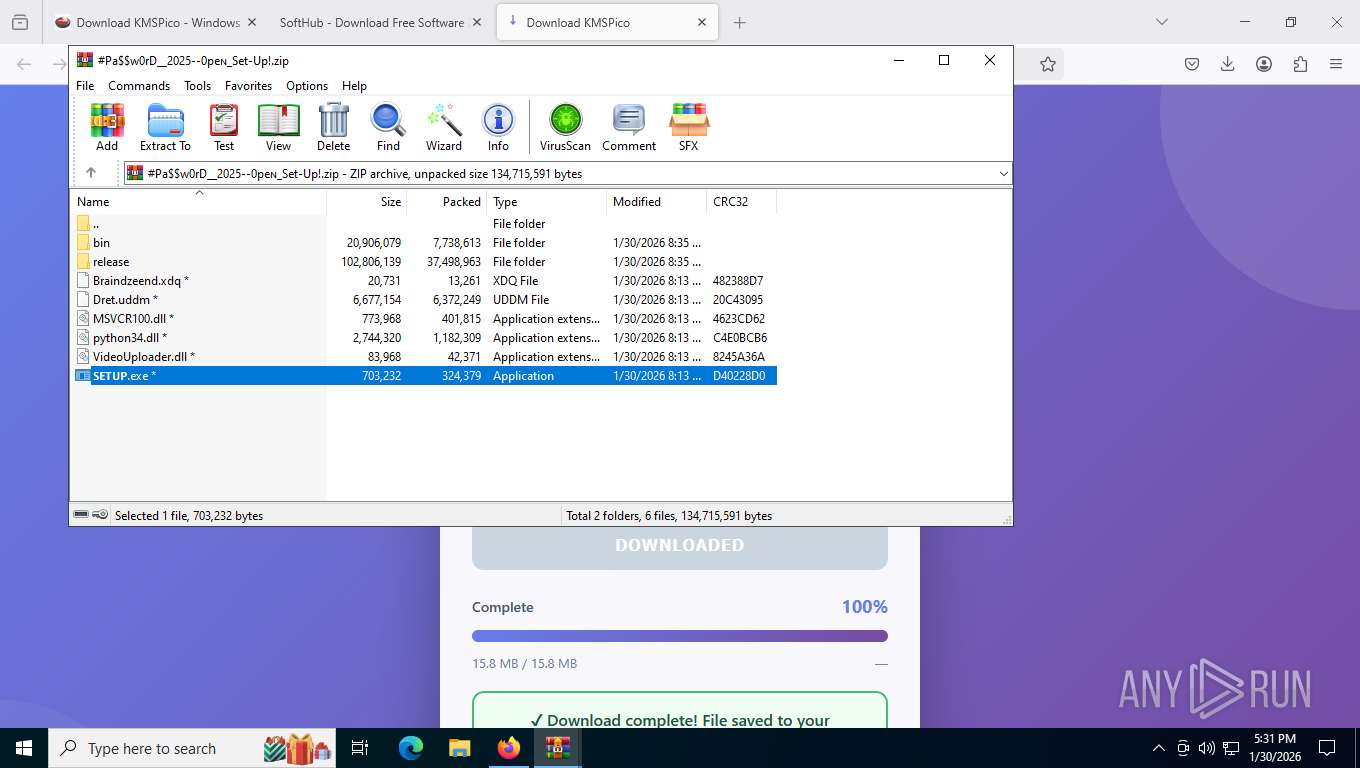
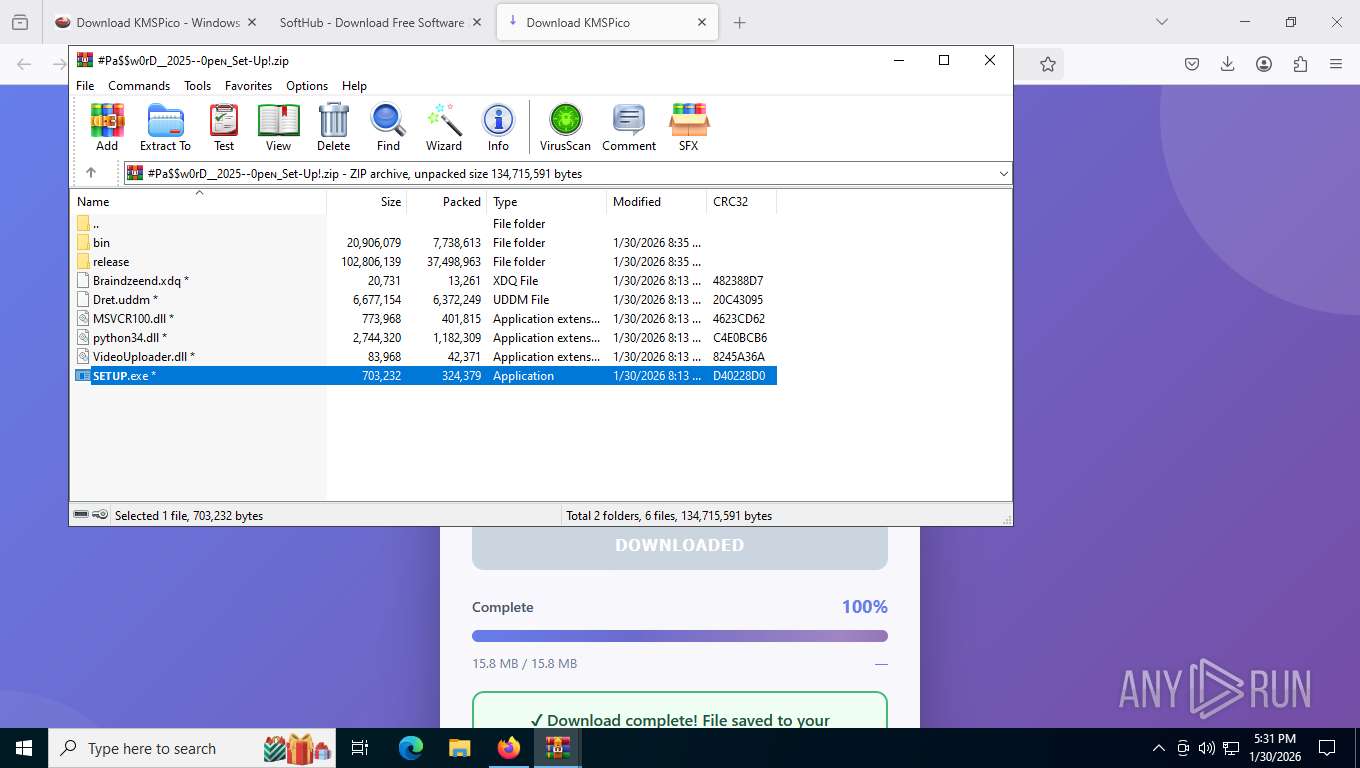
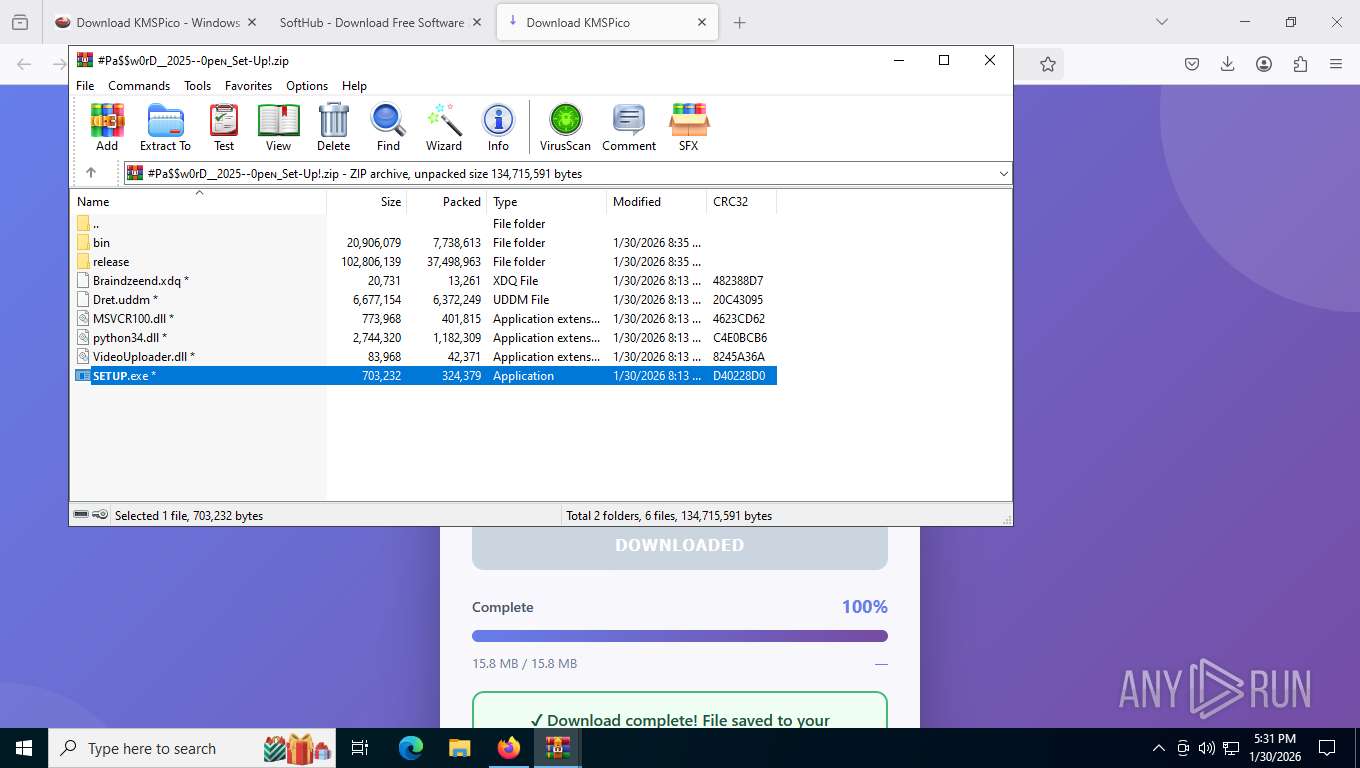
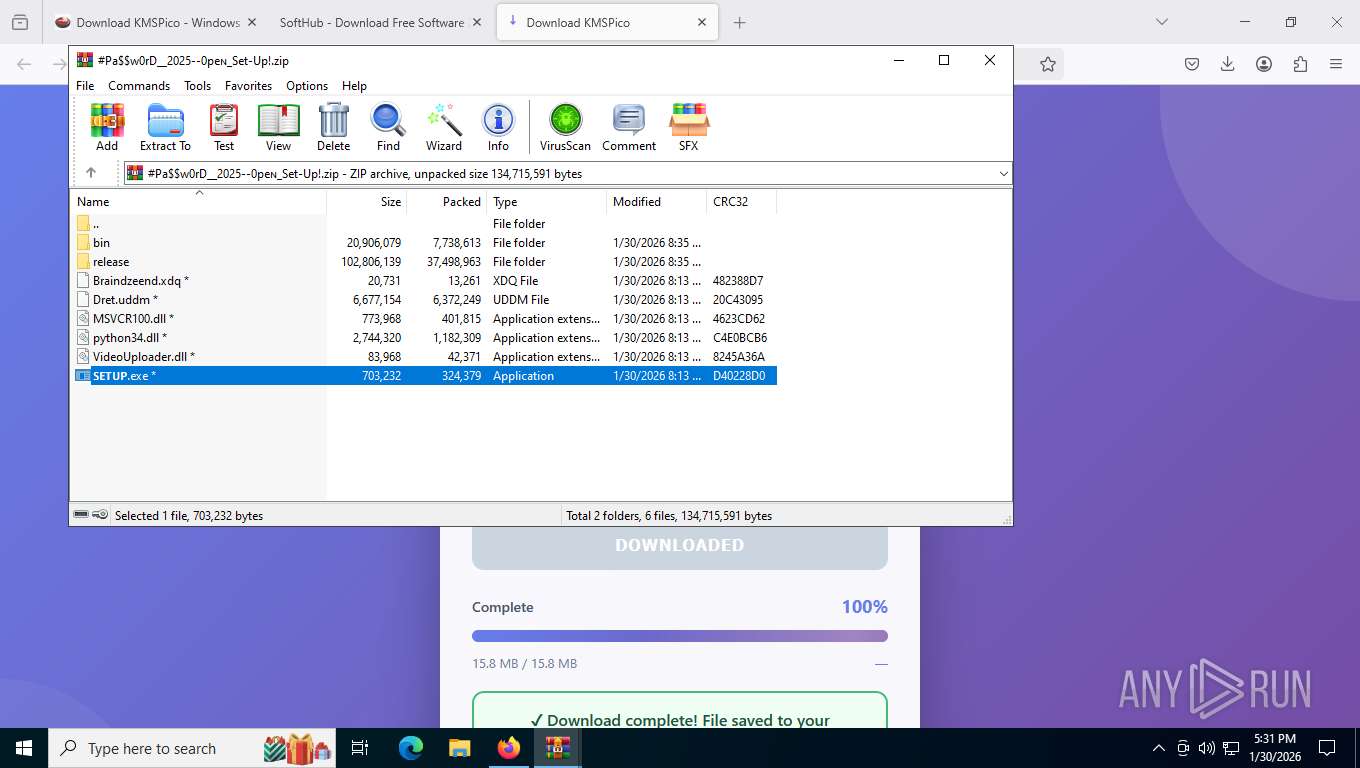
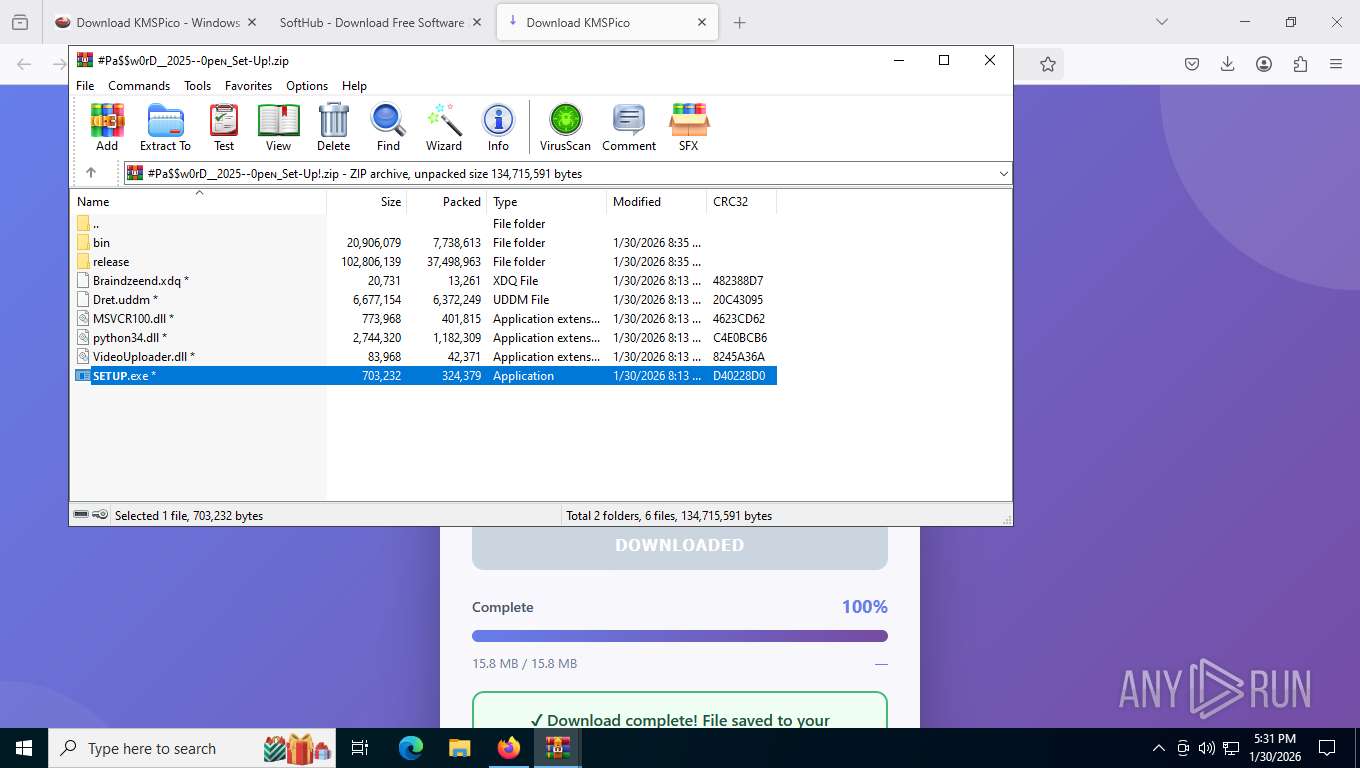
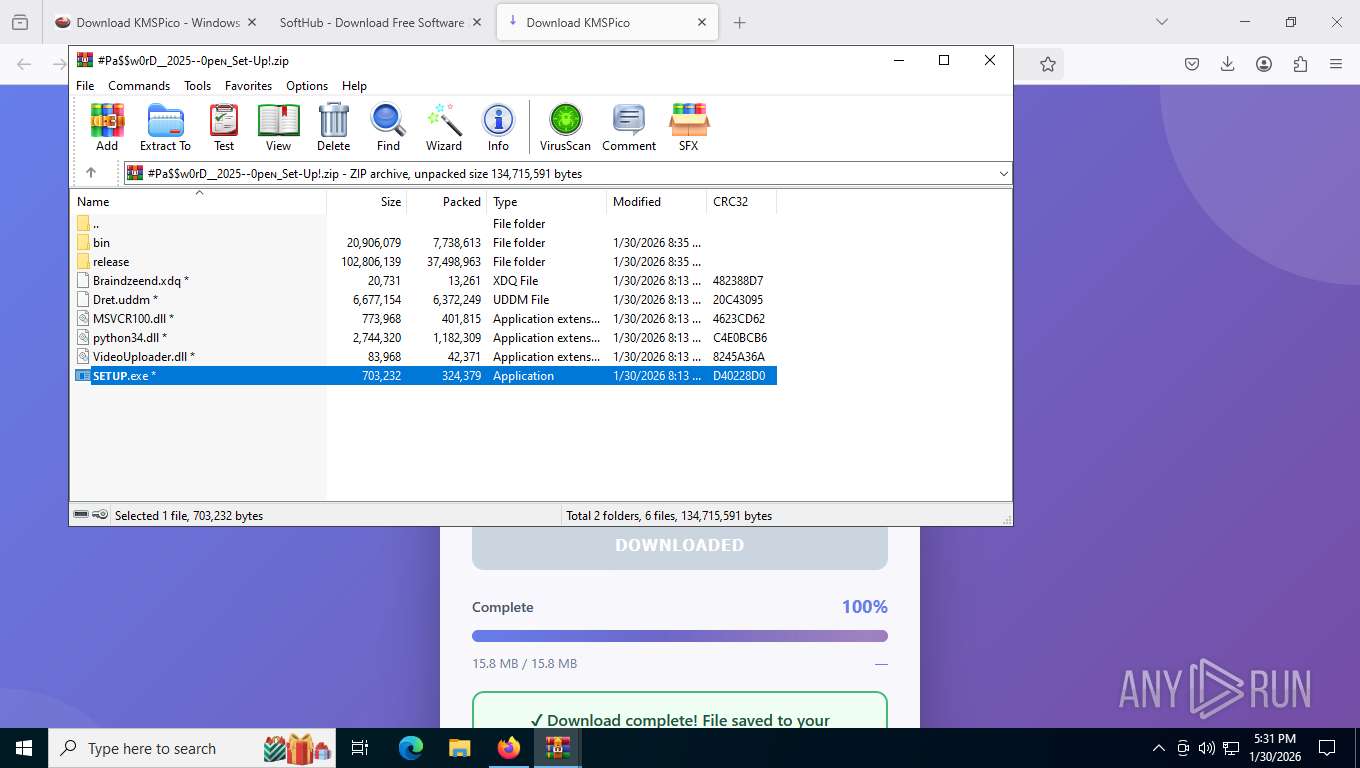
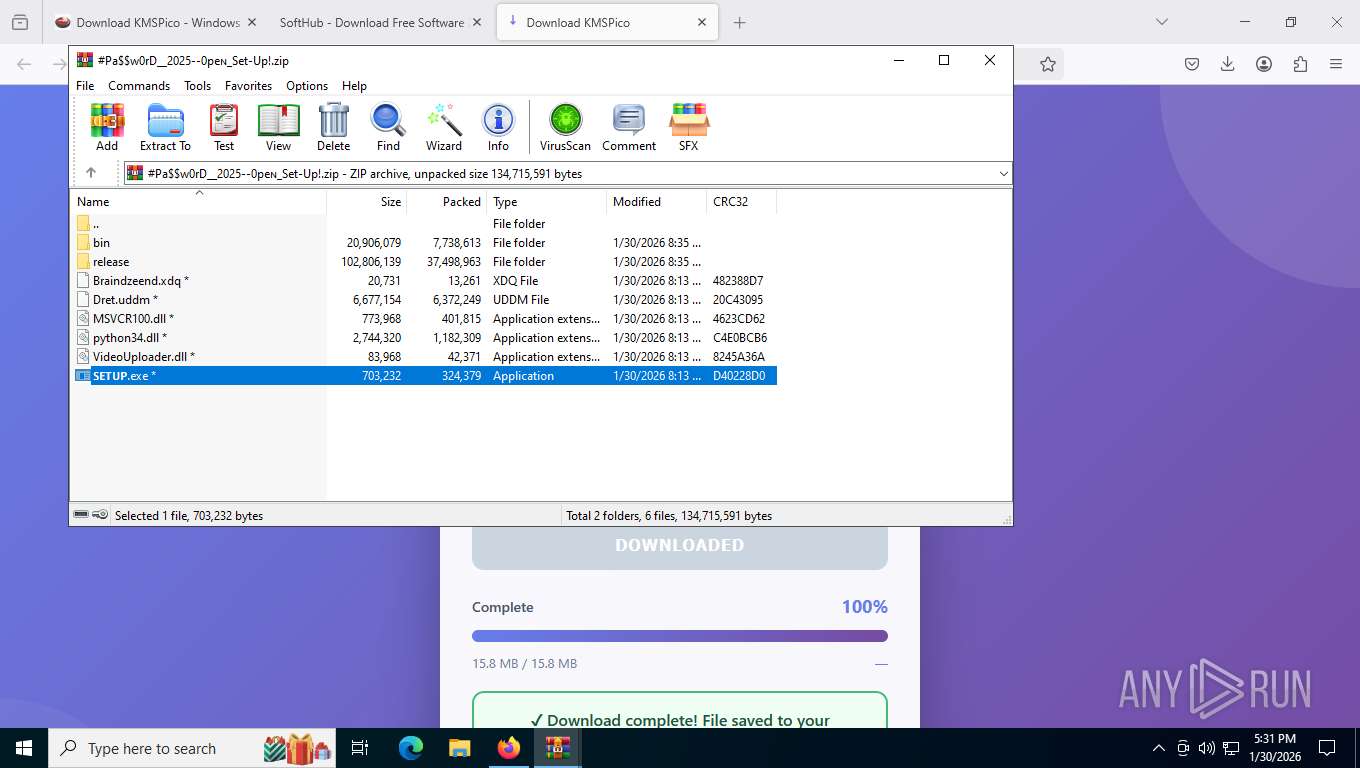
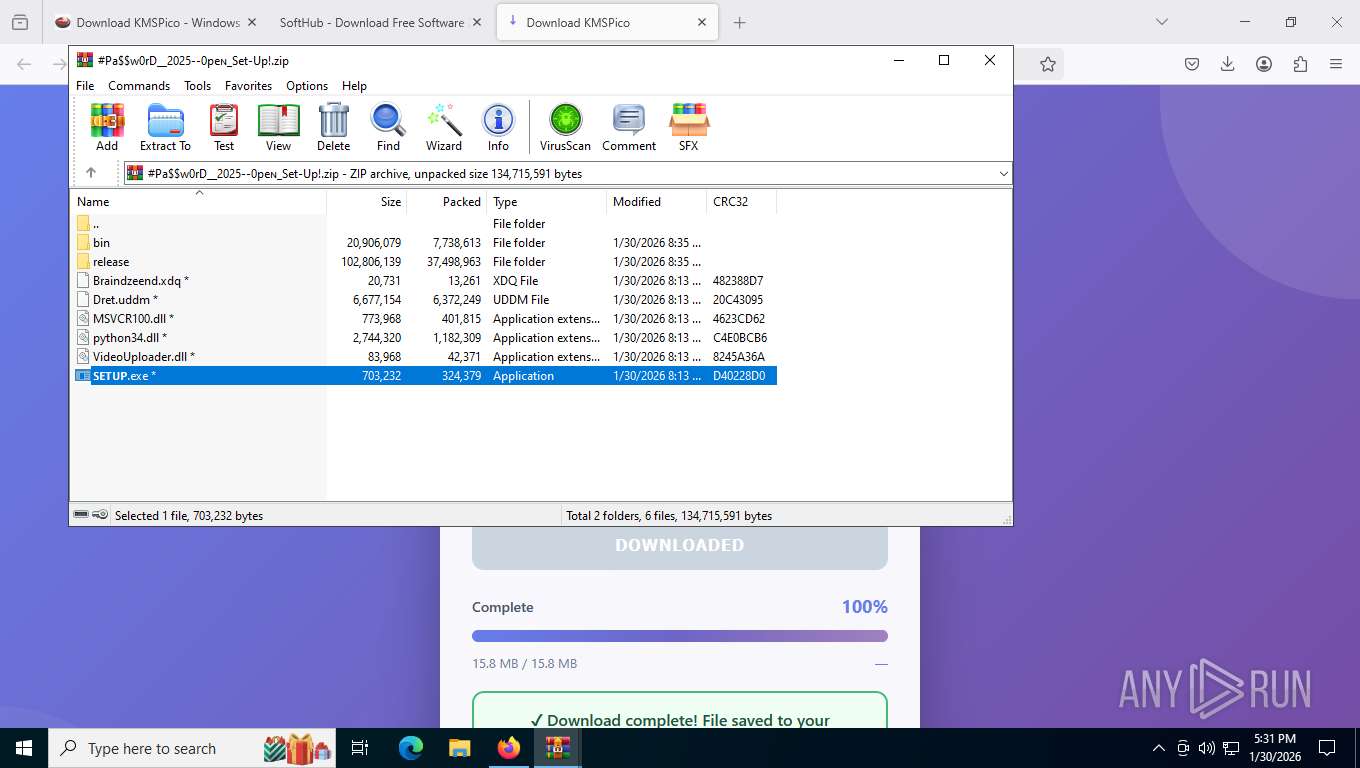
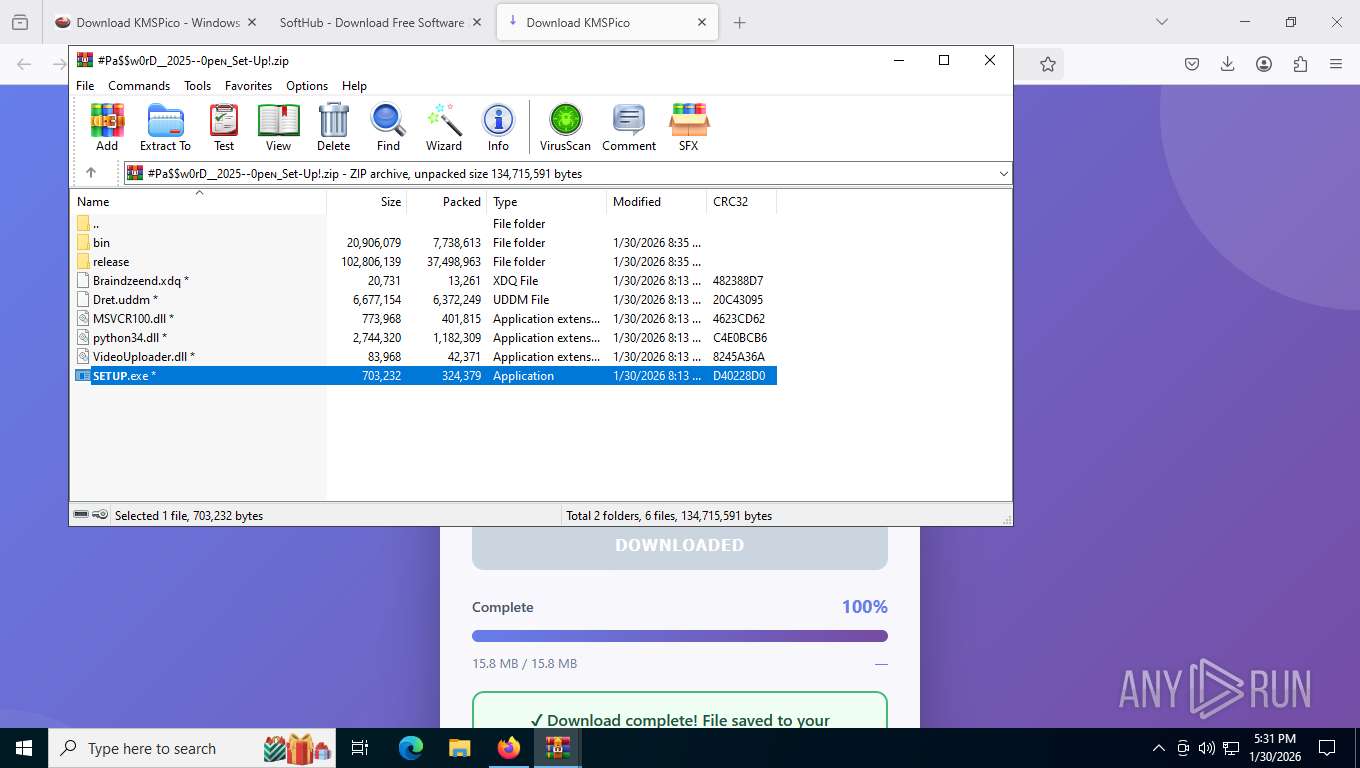
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
Application launched itself
- WinRAR.exe (PID: 9084)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 8348)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 5900)
- cmd.exe (PID: 1172)
- cmd.exe (PID: 8600)
Executable content was dropped or overwritten
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- Turbo-Nav.exe (PID: 4136)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 676)
Starts CMD.EXE for commands execution
- Turbo-Nav.exe (PID: 4136)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 2688)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 8348)
- powershell.exe (PID: 5464)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 5900)
- cmd.exe (PID: 1172)
- cmd.exe (PID: 8600)
Executing commands from a ".bat" file
- Turbo-Nav.exe (PID: 4136)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 2688)
- cmd.exe (PID: 7756)
- powershell.exe (PID: 5464)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 1172)
The process drops C-runtime libraries
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
Starts itself from another location
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
Starts SC.EXE for service management
- cmd.exe (PID: 7756)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 1172)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7756)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 1172)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7756)
- cmd.exe (PID: 8304)
- cmd.exe (PID: 4500)
Executes script without checking the security policy
- powershell.exe (PID: 5464)
- powershell.exe (PID: 4516)
- powershell.exe (PID: 3344)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7756)
- cmd.exe (PID: 8304)
- cmd.exe (PID: 4500)
Windows service management via SC.EXE
- sc.exe (PID: 3500)
- sc.exe (PID: 8756)
- sc.exe (PID: 2332)
Converts TXT file into a string
- powershell.exe (PID: 4516)
- powershell.exe (PID: 3344)
Hides command output
- cmd.exe (PID: 8304)
- cmd.exe (PID: 4500)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8304)
- cmd.exe (PID: 4500)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- powershell.exe (PID: 4516)
- powershell.exe (PID: 3344)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5680)
Searches for installed software
- PhotonGen.exe (PID: 3384)
Possible stealing from crypto wallets
- PhotonGen.exe (PID: 3384)
- MatrixBridg.exe (PID: 4404)
Possible stealing from password managers
- PhotonGen.exe (PID: 3384)
Contacting a server suspected of hosting an CnC
- MatrixBridg.exe (PID: 4404)
- PhotonGen.exe (PID: 3384)
Reads the date of Windows installation
- PhotonGen.exe (PID: 3384)
Browser headless start
- chrome.exe (PID: 2640)
- chrome.exe (PID: 7460)
- msedge.exe (PID: 3644)
- msedge.exe (PID: 4044)
Browser launch with unusual user-data-dir
- chrome.exe (PID: 2640)
- msedge.exe (PID: 3644)
Possible stealing from browsers
- PhotonGen.exe (PID: 3384)
INFO
Drops script file
- firefox.exe (PID: 7704)
- WinRAR.exe (PID: 676)
- Turbo-Nav.exe (PID: 4136)
- cmd.exe (PID: 2688)
- cmd.exe (PID: 7756)
- findstr.exe (PID: 5592)
- powershell.exe (PID: 5464)
- cmd.exe (PID: 5680)
- findstr.exe (PID: 5780)
- cmd.exe (PID: 1172)
- findstr.exe (PID: 1932)
- powershell.exe (PID: 4516)
- powershell.exe (PID: 3344)
- PhotonGen.exe (PID: 3384)
- msedge.exe (PID: 10380)
- msedge.exe (PID: 10420)
Application launched itself
- firefox.exe (PID: 8392)
- firefox.exe (PID: 7704)
- chrome.exe (PID: 2640)
- chrome.exe (PID: 8852)
- chrome.exe (PID: 7820)
- msedge.exe (PID: 3644)
- chrome.exe (PID: 9856)
- chrome.exe (PID: 10728)
- chrome.exe (PID: 8628)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 9084)
- WinRAR.exe (PID: 676)
- PhotonGen.exe (PID: 3384)
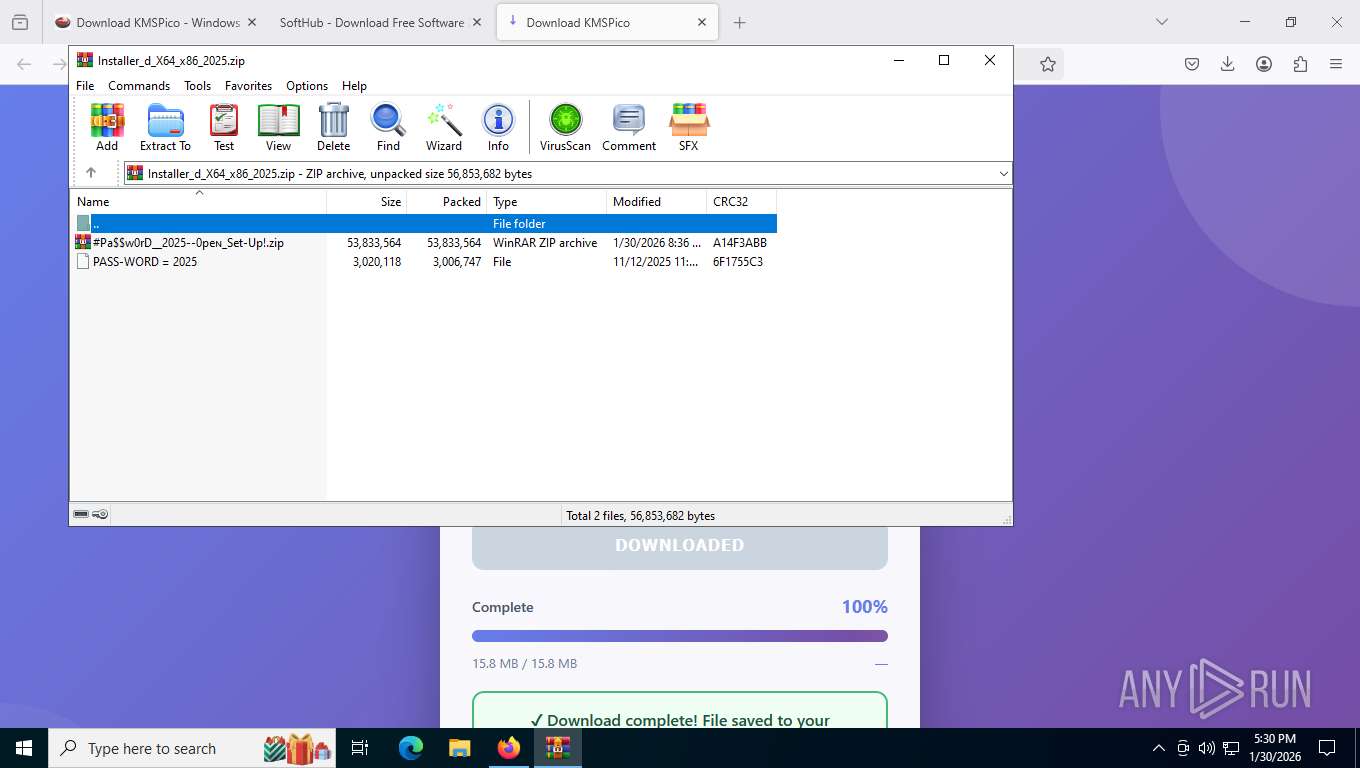
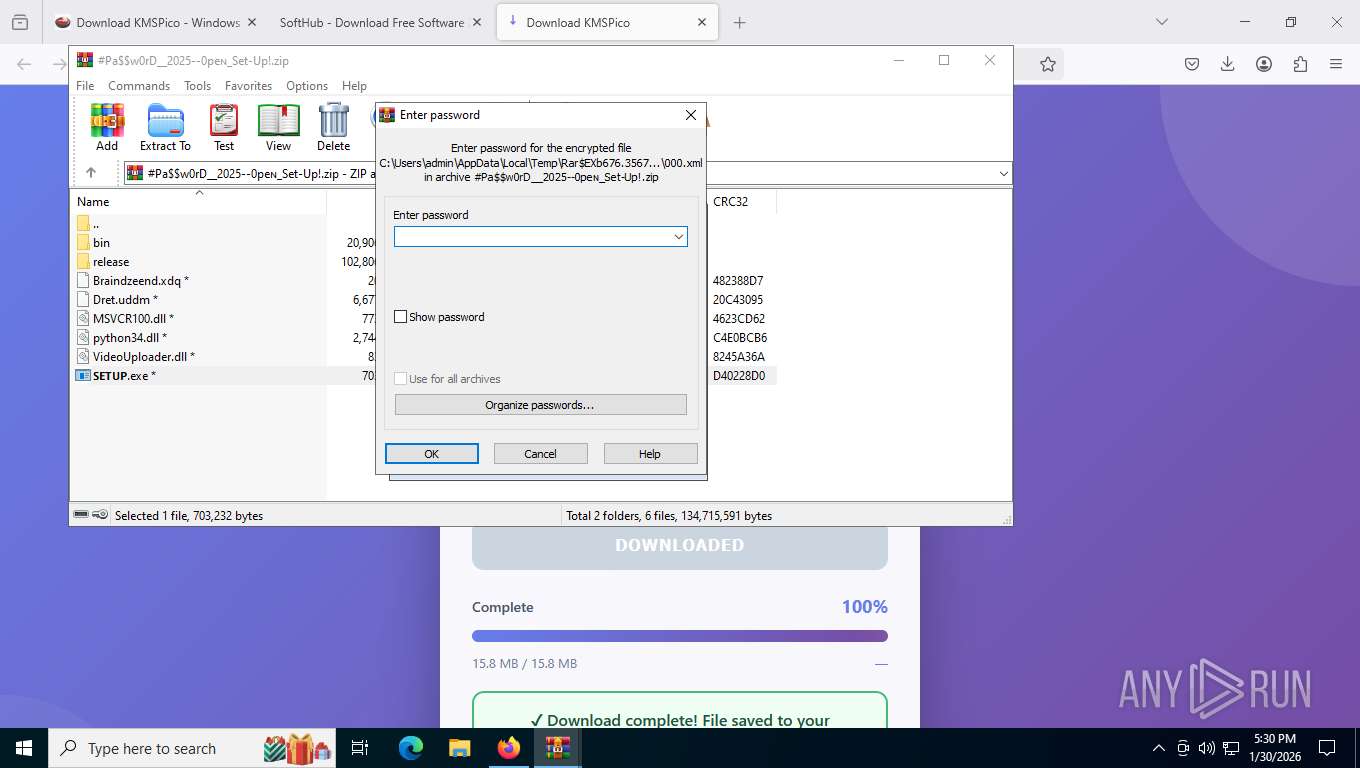
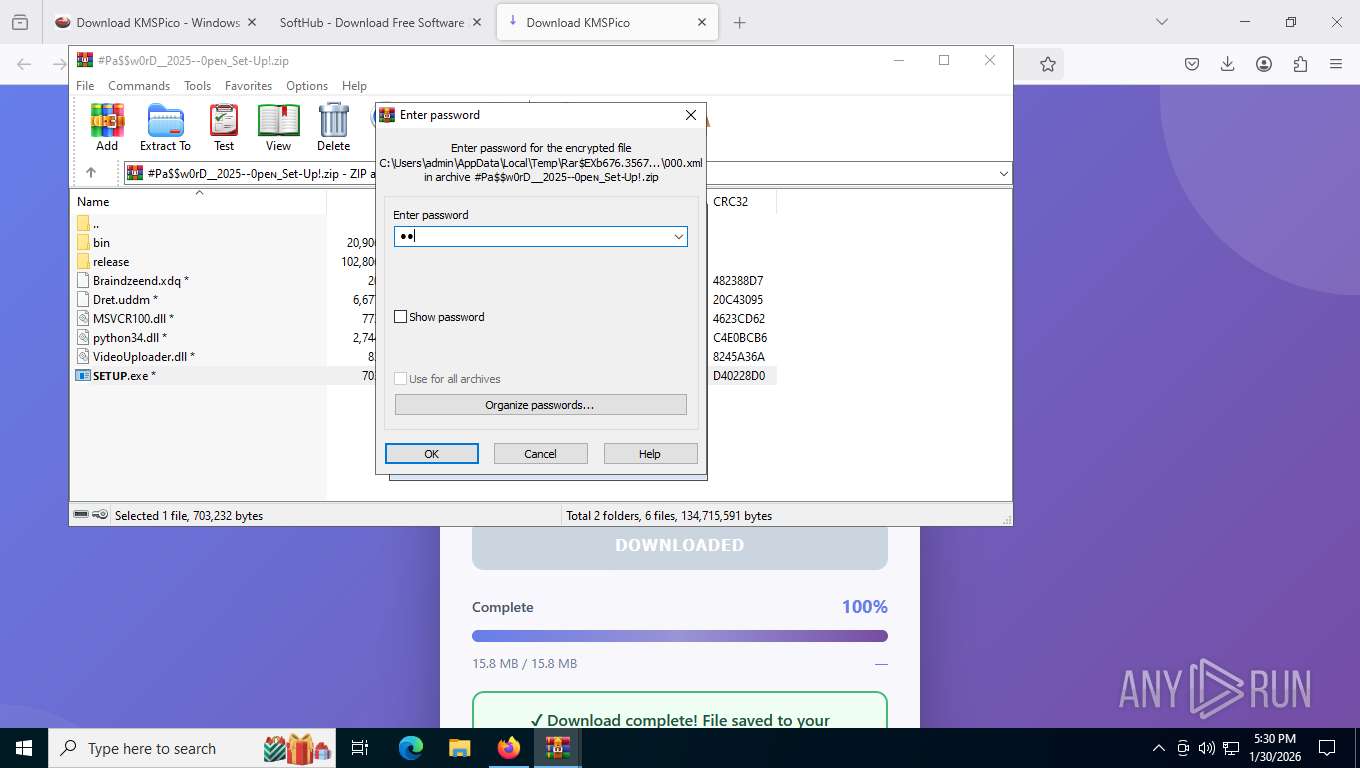
Manual execution by a user
- WinRAR.exe (PID: 9084)
Creates files in the program directory
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- PhotonGen.exe (PID: 3384)
- MatrixBridg.exe (PID: 4404)
Reads the computer name
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- Turbo-Nav.exe (PID: 4136)
- PhotonGen.exe (PID: 3384)
- MatrixBridg.exe (PID: 4404)
- Crisp.exe (PID: 1688)
- Crisp.exe (PID: 8760)
- identity_helper.exe (PID: 10220)
Creates files or folders in the user directory
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- Turbo-Nav.exe (PID: 4136)
The sample compiled with english language support
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- WinRAR.exe (PID: 676)
- Turbo-Nav.exe (PID: 4136)
- firefox.exe (PID: 7704)
The sample compiled with french language support
- WinRAR.exe (PID: 676)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 676)
- firefox.exe (PID: 7704)
Checks proxy server information
- slui.exe (PID: 4516)
- PhotonGen.exe (PID: 3384)
Compiled with Borland Delphi (YARA)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- PhotonGen.exe (PID: 3384)
- Turbo-Nav.exe (PID: 4136)
The sample compiled with chinese language support
- WinRAR.exe (PID: 676)
There is functionality for taking screenshot (YARA)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- Turbo-Nav.exe (PID: 4136)
Checks supported languages
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- Turbo-Nav.exe (PID: 4136)
- mode.com (PID: 9112)
- mode.com (PID: 7644)
- Crisp.exe (PID: 1688)
- MatrixBridg.exe (PID: 4404)
- PhotonGen.exe (PID: 3384)
- Crisp.exe (PID: 8760)
- identity_helper.exe (PID: 10220)
Create files in a temporary directory
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 9188)
- Turbo-Nav.exe (PID: 4136)
- Crisp.exe (PID: 8760)
- MatrixBridg.exe (PID: 4404)
Checks operating system version
- cmd.exe (PID: 7756)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 1172)
Search a value from a registry key
- reg.exe (PID: 1428)
- reg.exe (PID: 6580)
- reg.exe (PID: 5632)
- reg.exe (PID: 1960)
Python executable
- PhotonGen.exe (PID: 3384)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4516)
- powershell.exe (PID: 3344)
Starts MODE.COM to configure console settings
- mode.com (PID: 9112)
- mode.com (PID: 7644)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4516)
- powershell.exe (PID: 3344)
Reads the machine GUID from the registry
- PhotonGen.exe (PID: 3384)
- MatrixBridg.exe (PID: 4404)
Reads CPU info
- PhotonGen.exe (PID: 3384)
Reads product name
- PhotonGen.exe (PID: 3384)
Reads Environment values
- PhotonGen.exe (PID: 3384)
- identity_helper.exe (PID: 10220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
386
Monitored processes
232
Malicious processes
14
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | ping -n 1 updatecheck38.activated.win | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
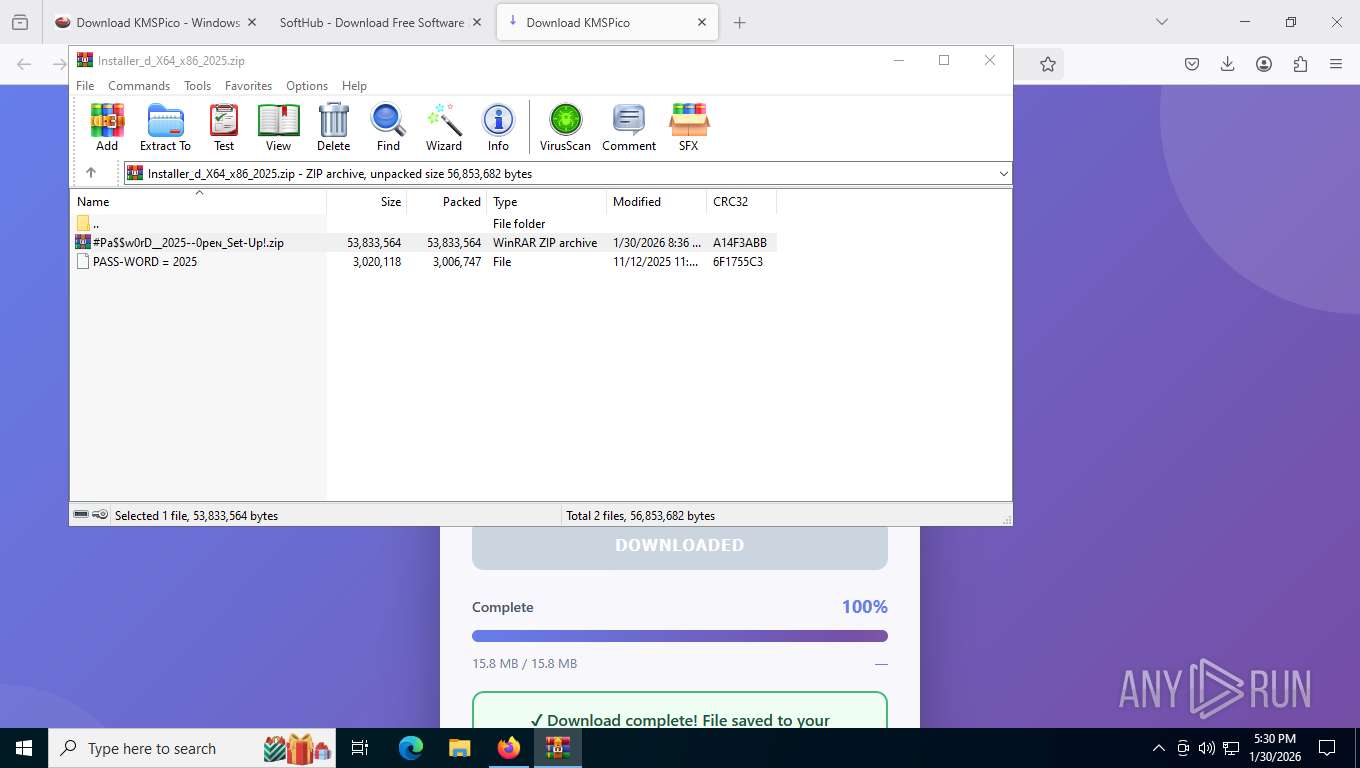
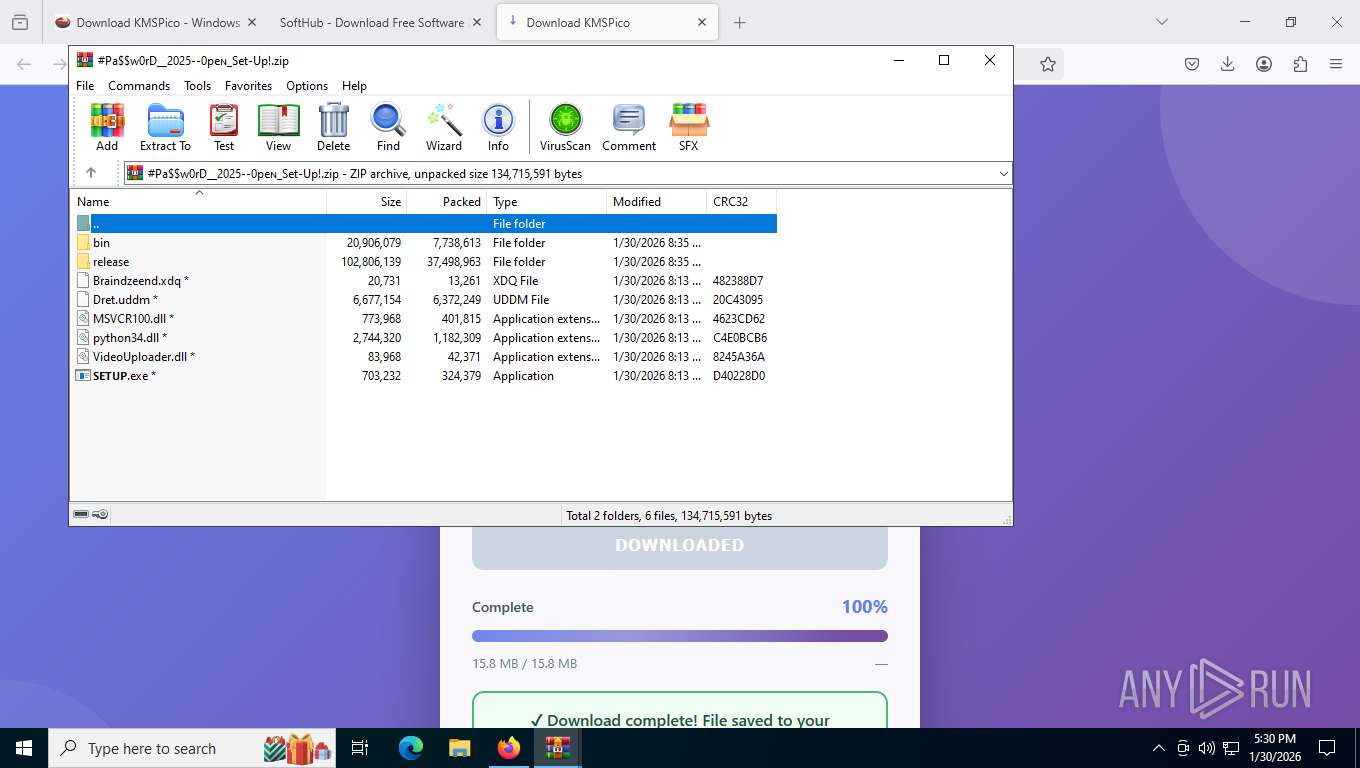
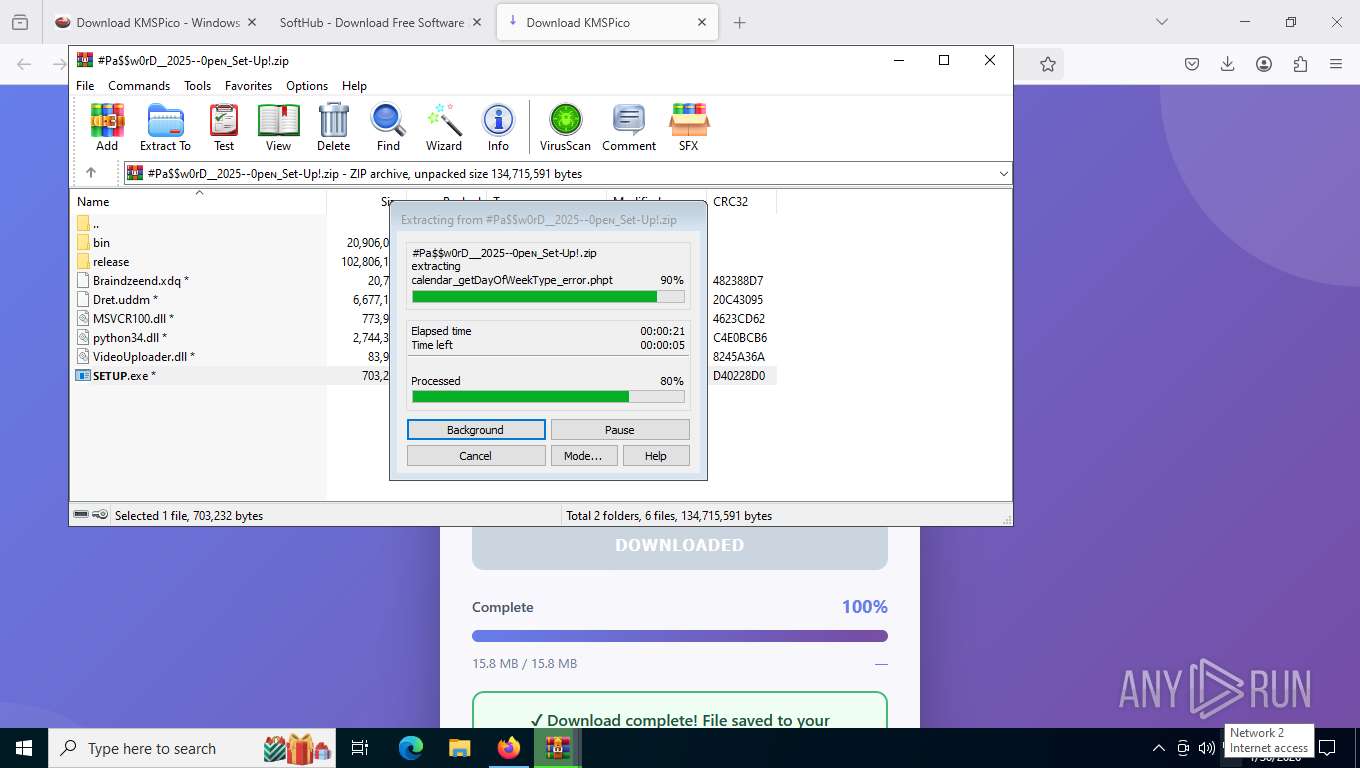
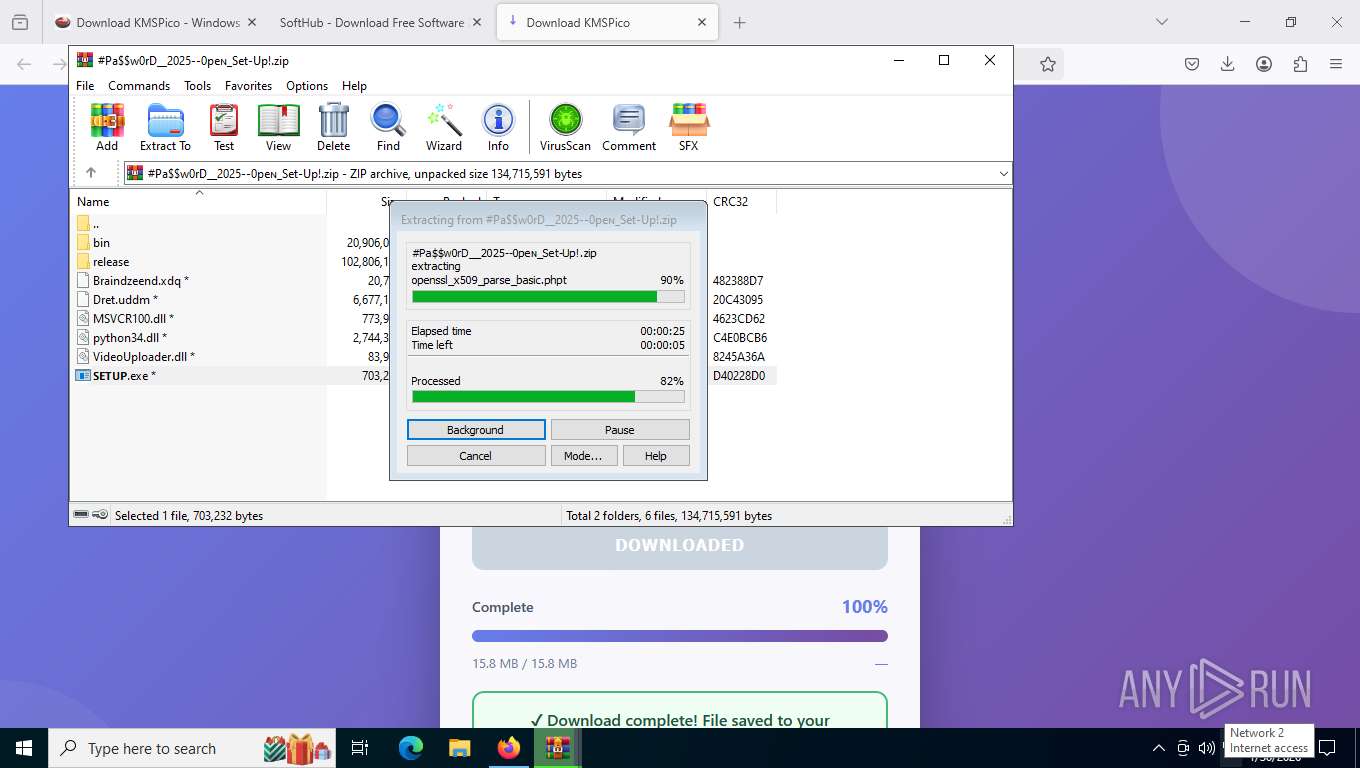
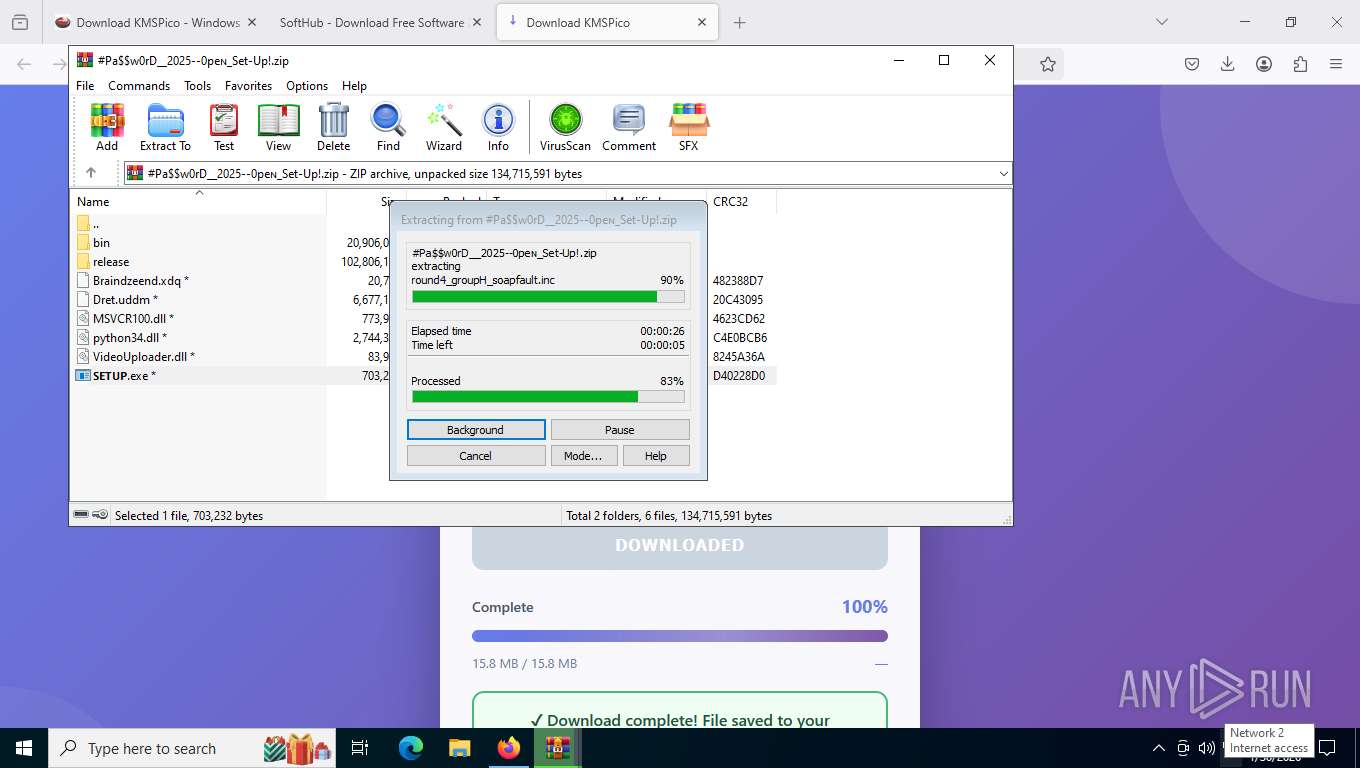
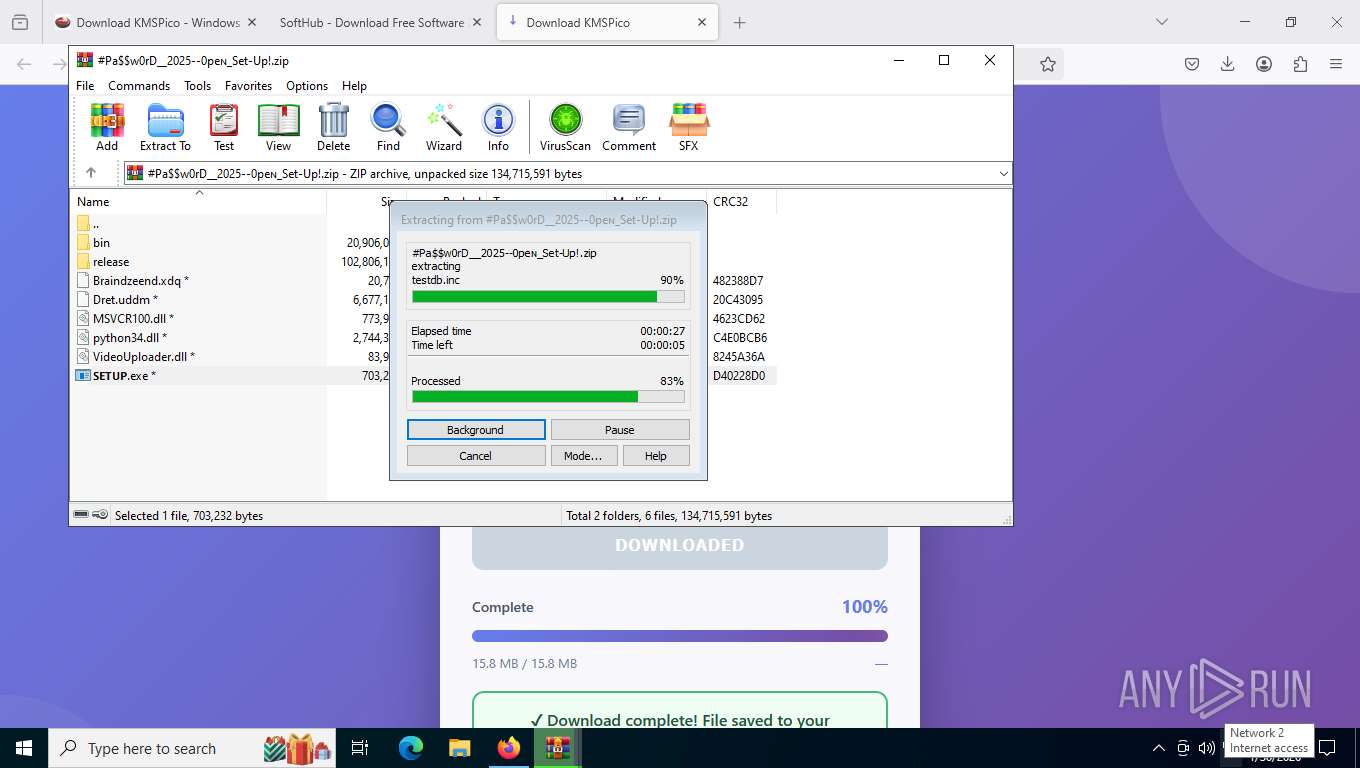
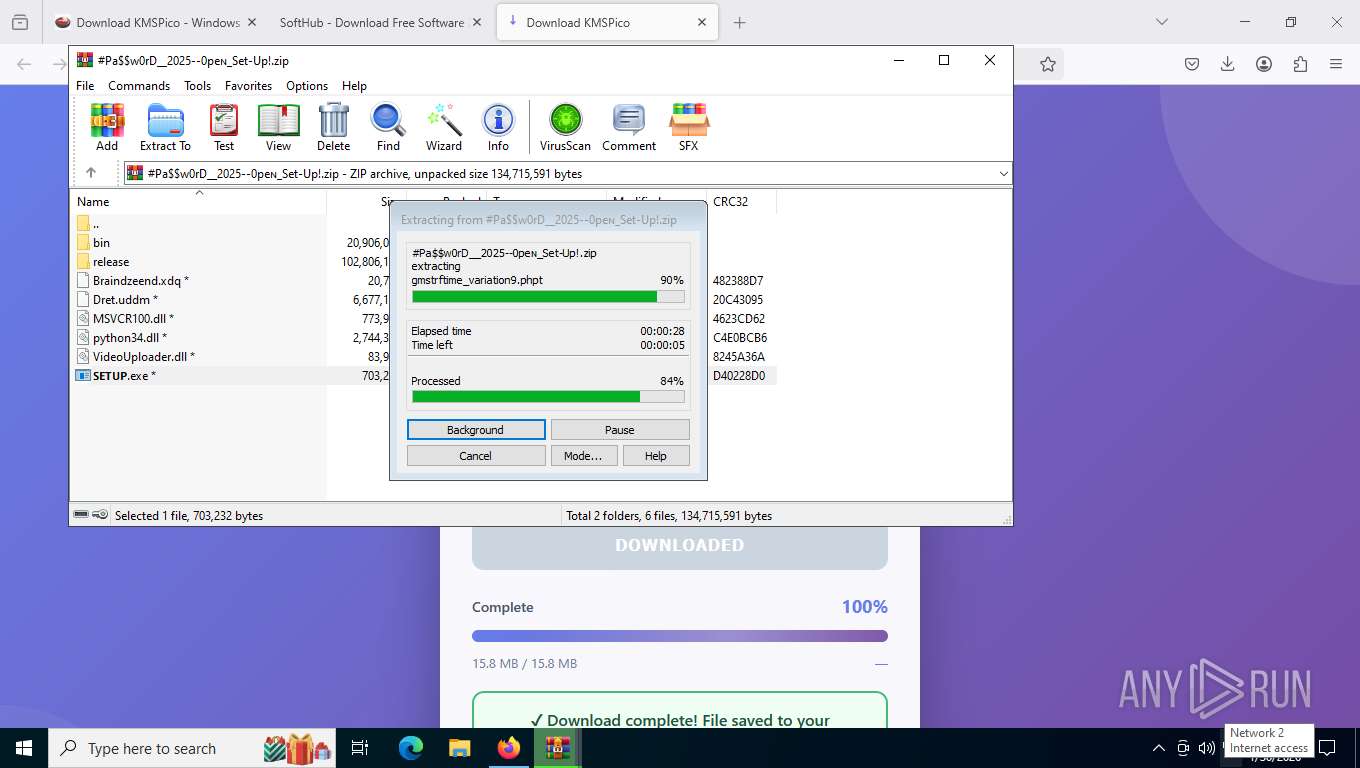
| 676 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa9084.35337\#Pa$w0rD__2025--0peɴ_Set-Up!.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 824 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "-qedit" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | cmd.exe /c ""C:\Users\admin\AppData\Roaming\QeDebug_rtm\YYBPPXUFMRDRJMCYOFR\123.bat" -el -qedit" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffd70b9fff8,0x7ffd70ba0004,0x7ffd70ba0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --string-annotations --field-trial-handle=2352,i,3285203499687882072,15008492562917656299,262144 --variations-seed-version --mojo-platform-channel-handle=2436 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5976,i,990331907914310391,10278246173148316685,262144 --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5016 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2188,i,12210809522246603996,2065240847718082769,262144 --variations-seed-version --mojo-platform-channel-handle=2200 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1400 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 042
Read events
28 022
Write events
20
Delete events
0
Modification events
| (PID) Process: | (9084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (9084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (9084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (9084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Installer_d_X64_x86_2025.zip | |||
| (PID) Process: | (9084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (9084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (9084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (9084) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
Executable files
209
Suspicious files
748
Text files
1 701
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:5152D8F49F1AD4219D935611EFE18437 | SHA256:9A6E50715E3C49A43E3D622EDE7E37ECF0767342B3039B8B0AE25BBE4FF6F66E | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:6FD8120B2BD61D3F745963D57CD6266B | SHA256:4849830FF5E987CBDACEC5ED8708F3D4766BDA227865C63779BD22E7A39D04A2 | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:3134ED3F12E4F4F8643DB90043B0FD7B | SHA256:26E4F122034D7A03F6DA0E707799B09CBEEBDAF8D7A3133A1F7BD894AC72EEA1 | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:926E42E625D1B51D9E715A7624338569 | SHA256:E35E9194BAA27498E0A0F5CFF119689336D9587D1E784C35DD464069303A84A3 | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
269
TCP/UDP connections
191
DNS requests
236
Threats
60
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7704 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | unknown |
7704 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | unknown |
7704 | firefox.exe | POST | 200 | 142.251.208.163:80 | http://o.pki.goog/s/wr3/peI | unknown | — | — | whitelisted |
7704 | firefox.exe | POST | 200 | 142.251.208.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7704 | firefox.exe | POST | 200 | 142.251.208.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7704 | firefox.exe | POST | 200 | 142.251.208.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7704 | firefox.exe | POST | 200 | 142.251.208.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7704 | firefox.exe | GET | 200 | 151.101.193.91:443 | https://firefox.settings.services.mozilla.com/v1/buckets/monitor/collections/changes/changeset?collection=url-parser-default-unknown-schemes-interventions&bucket=main&_expected=0 | unknown | text | 274 b | unknown |
7704 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5780 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8400 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.201:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7704 | firefox.exe | 151.101.193.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7704 | firefox.exe | 188.114.97.3:443 | www.kms-soft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
mozilla.map.fastly.net |
| whitelisted |
www.kms-soft.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7704 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
7704 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP request field missing colon |
7704 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP request header invalid |
7704 | firefox.exe | Possible Social Engineering Attempted | ET PHISHING Common Credential Theft Redirect Page |
2292 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
7704 | firefox.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
7704 | firefox.exe | Possible Social Engineering Attempted | ET PHISHING Common Credential Theft Redirect Page |
4404 | MatrixBridg.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Win32/HijackLoader CnC connection established M1 |
4404 | MatrixBridg.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Win32/HijackLoader CnC frame outbound |
4404 | MatrixBridg.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Win32/HijackLoader CnC frame inbound |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome26402191359 directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessEdge36442224343 directory exists )
|