| File name: | d3d9446802a44259755d38e6d163e820.zip |
| Full analysis: | https://app.any.run/tasks/9865077f-5c55-4c50-8ca0-1b57d2a3b56b |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | August 31, 2024, 00:48:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 8209B1FDEF48ED2F8AB18E9D13F6F76B |
| SHA1: | BBF66640D065D0C1F0F41AF28BE4A5FEA2F88B82 |
| SHA256: | 0896D16A38C3910CCABABDA1E0AD9A9817ED1E88587225D6FFA3ED91B904DF75 |
| SSDEEP: | 98304:JbqGnXh+er0ux8MJ9RzUqDjaTnfunfMw4qpN3xVy1ZxB1xjnVx29wypJFg6D33iW:J/Vjv4Ccol |
MALICIOUS
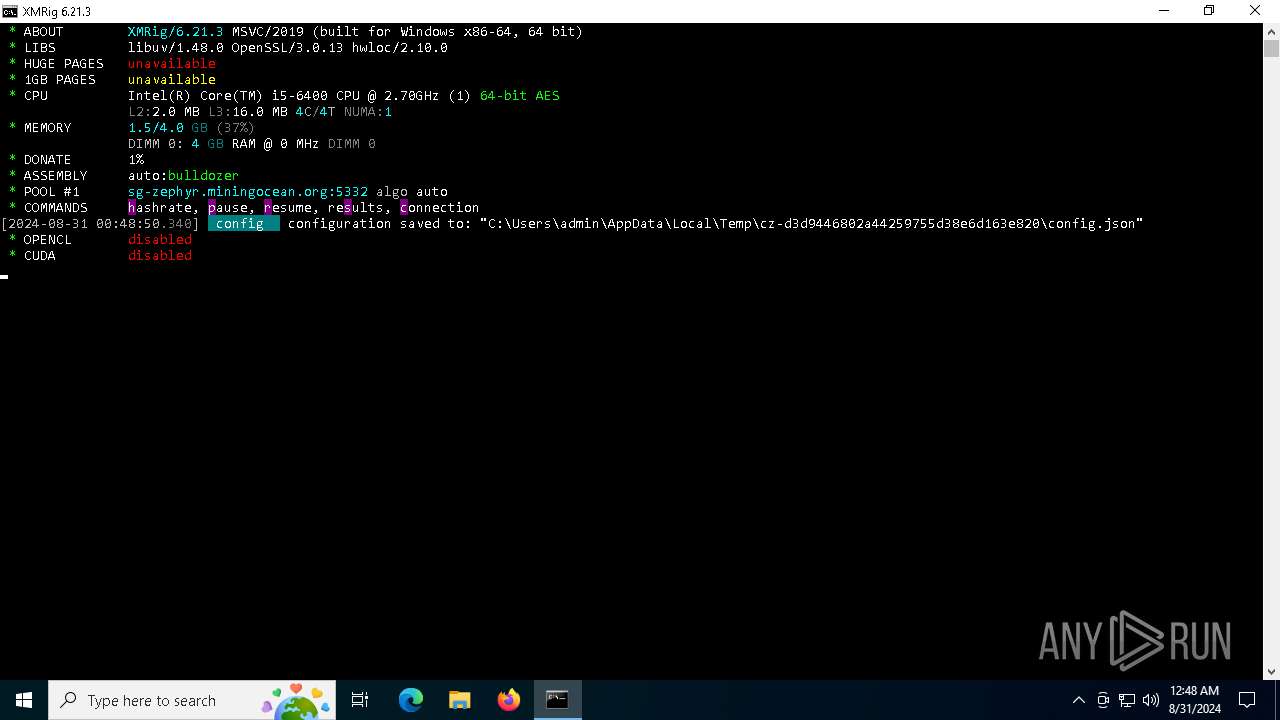
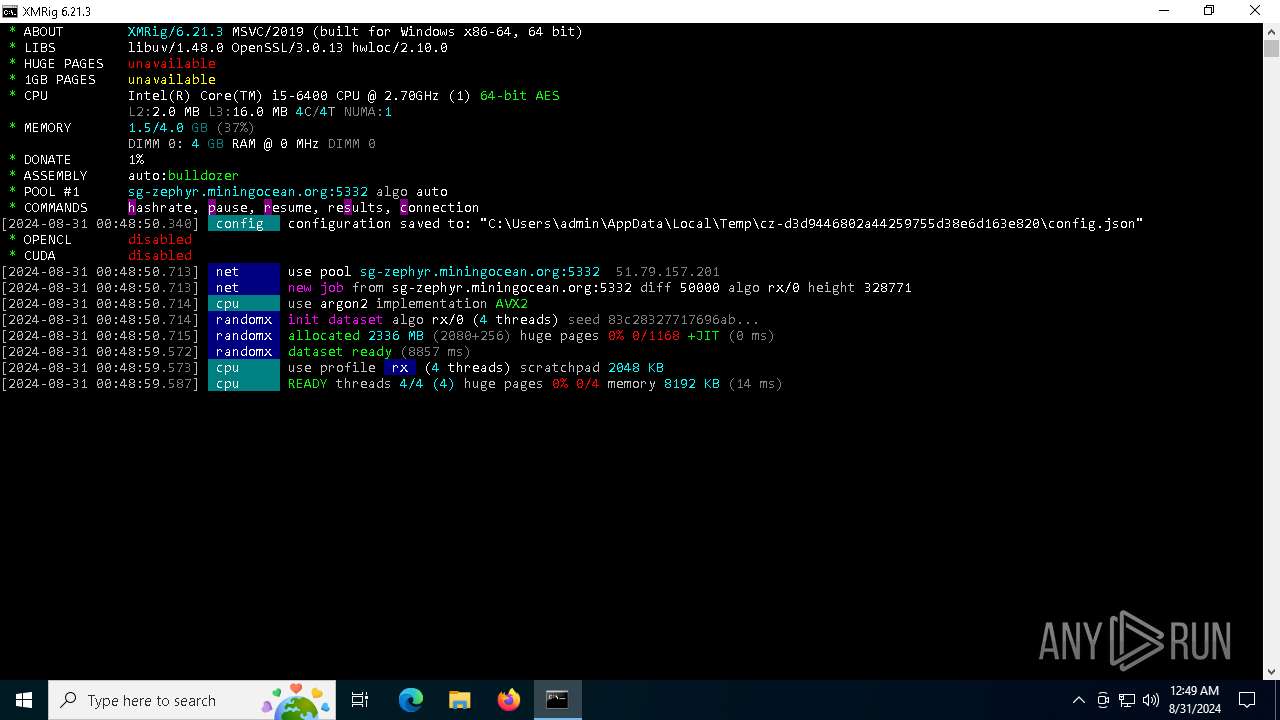
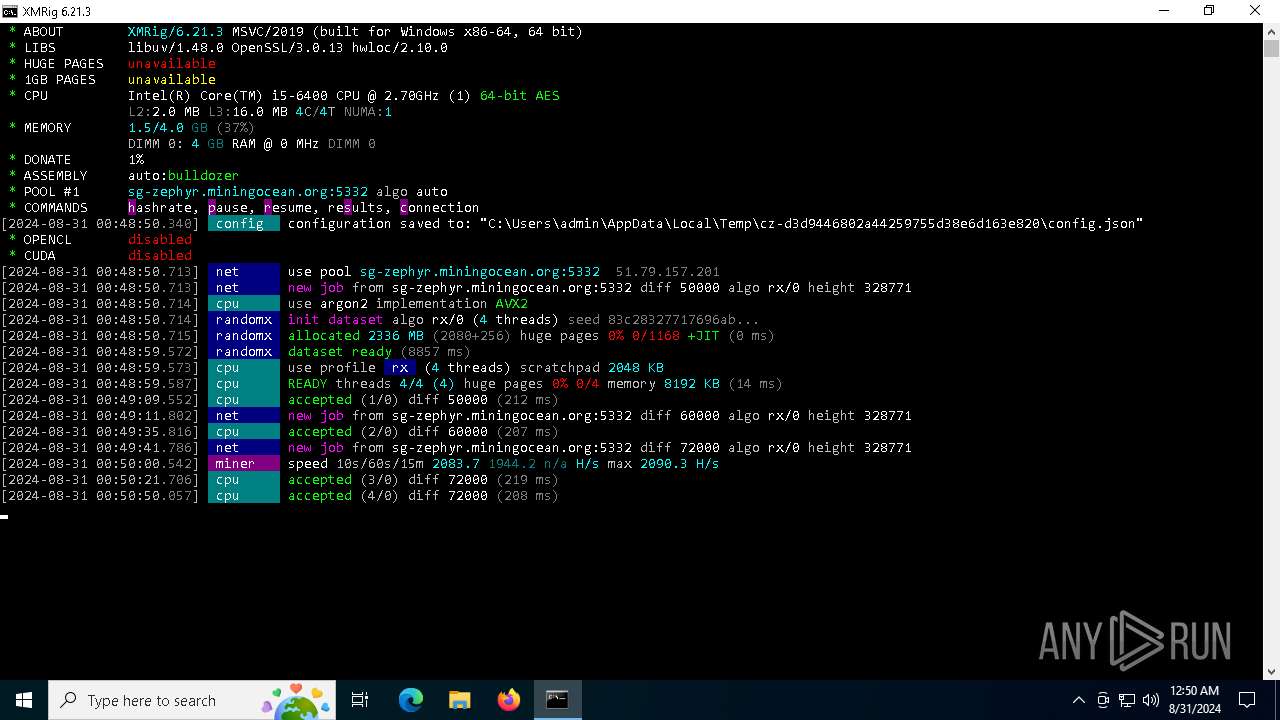
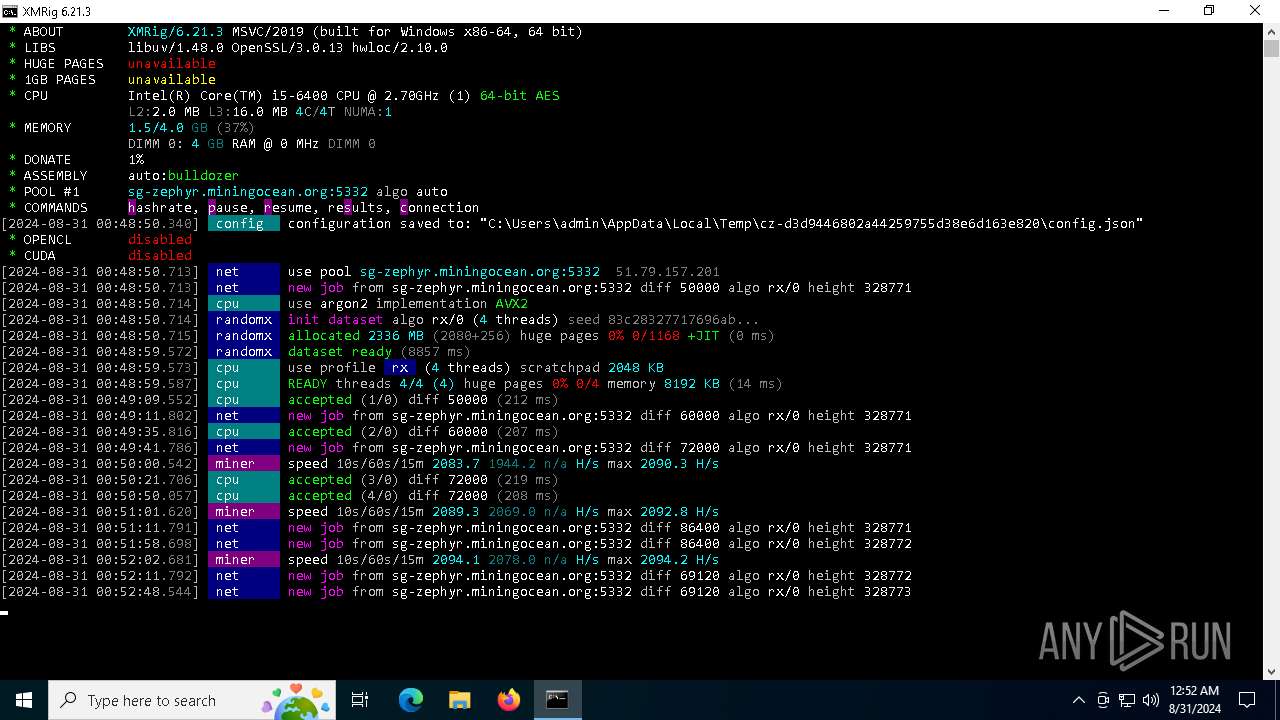
XMRig has been detected
- xmrig.exe (PID: 5264)
Connects to the CnC server
- xmrig.exe (PID: 5264)
MINER has been detected (SURICATA)
- xmrig.exe (PID: 5264)
XMRIG has been detected (YARA)
- xmrig.exe (PID: 5264)
SUSPICIOUS
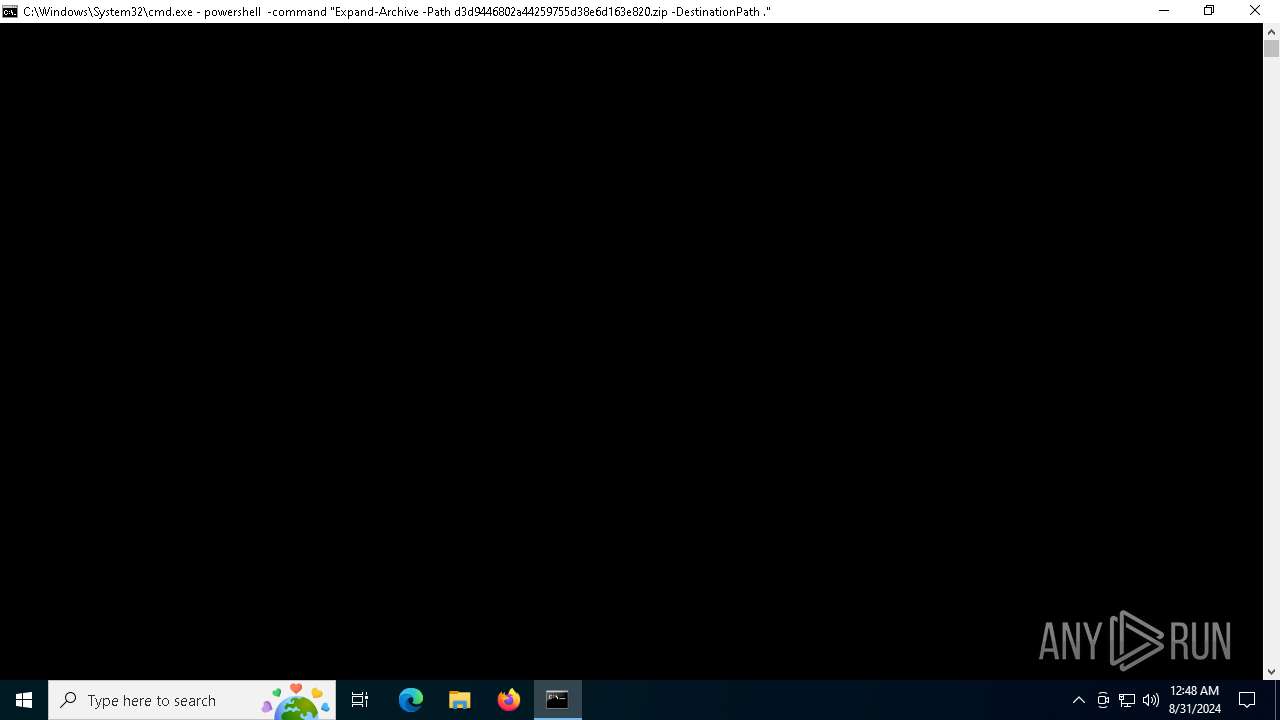
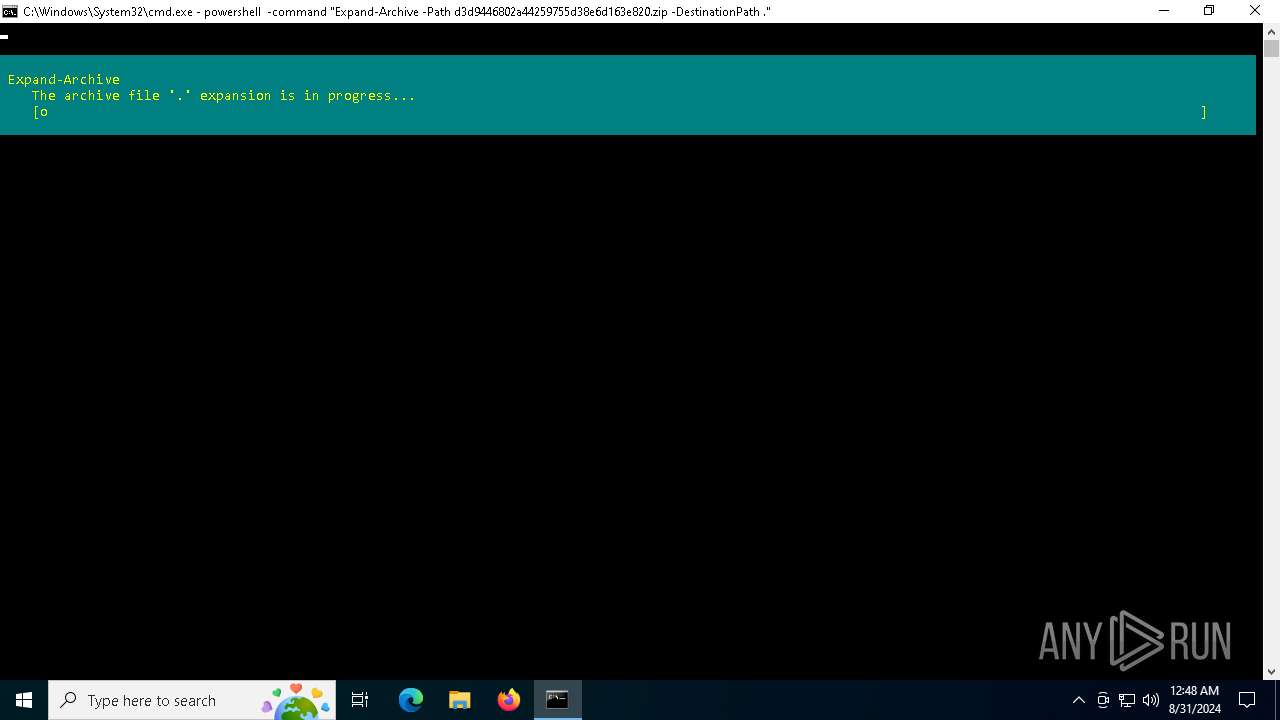
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7164)
The executable file from the user directory is run by the CMD process
- xmrig.exe (PID: 5264)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6152)
Drops the executable file immediately after the start
- powershell.exe (PID: 6152)
Drops a system driver (possible attempt to evade defenses)
- powershell.exe (PID: 6152)
Executable content was dropped or overwritten
- powershell.exe (PID: 6152)
Potential Corporate Privacy Violation
- xmrig.exe (PID: 5264)
Connects to unusual port
- xmrig.exe (PID: 5264)
Crypto Currency Mining Activity Detected
- xmrig.exe (PID: 5264)
INFO
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6152)
Create files in a temporary directory
- xmrig.exe (PID: 5264)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6152)
Checks supported languages
- xmrig.exe (PID: 5264)
Reads the computer name
- xmrig.exe (PID: 5264)
Reads the software policy settings
- slui.exe (PID: 6992)
- slui.exe (PID: 5700)
Checks proxy server information
- slui.exe (PID: 5700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:08:06 00:46:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | cz-d3d9446802a44259755d38e6d163e820/ |
Total processes
136
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5264 | xmrig.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\xmrig.exe | cmd.exe | ||||||||||||
User: admin Company: www.xmrig.com Integrity Level: MEDIUM Description: XMRig miner Version: 6.21.3 Modules
| |||||||||||||||
| 5700 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6152 | powershell -command "Expand-Archive -Path d3d9446802a44259755d38e6d163e820.zip -DestinationPath ." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6980 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6992 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7164 | "C:\Windows\System32\cmd.exe" /k powershell -command "Expand-Archive -Path d3d9446802a44259755d38e6d163e820.zip -DestinationPath ." && cd cz-d3d9446802a44259755d38e6d163e820 && xmrig.exe | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 740
Read events
6 740
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
2
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\benchmark_1M.cmd | text | |
MD5:CBA1927CF6959DC99ECBD0C553E4DB6F | SHA256:D7747E7A3C782009F4CEB6E9C106115876386853929563B509DA5258E3968D15 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2b553l3b.mg3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\solo_mine_example.cmd | text | |
MD5:090703E56F46330ED625AC4363C9D25C | SHA256:33497C69C21FA96BBC96F1D7F09608E462F8AB22555364977C0BD35FEF27BC29 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\WinRing0x64.sys | executable | |
MD5:0C0195C48B6B8582FA6F6373032118DA | SHA256:11BD2C9F9E2397C9A16E0990E4ED2CF0679498FE0FD418A3DFDAC60B5C160EE5 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\start.cmd | text | |
MD5:EAF3A00CC0465F8AF471B849ADA29843 | SHA256:8E70EF38FE14A2EE2848DF3D6F7E260D1CAF8CFC15DE694D678B8AF151D62333 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\pool_mine_example.cmd | text | |
MD5:2E737F5C3AF9C8AA5216DFDC5BE02CC6 | SHA256:E73491065D86B1AD69229BB5D2019E08B947E11A2A57ADF5C2D9A2B5D8F4ACAD | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\benchmark_10M.cmd | text | |
MD5:5BE1C4CACB5AE37C43527E99A097DC7A | SHA256:235A64E3520B1C2C27763122B303F78AEE8D7C083DFD9F1EB936CD5174383609 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\SHA256SUMS | text | |
MD5:DE6CDB6BB50EF79E724CE9B7CEAD44A6 | SHA256:3E7BE216E75D6038F67E5CE9B87FD5A1BD4968548628B53F42D11C8963DD7CF1 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fzk5zusg.50w.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cz-d3d9446802a44259755d38e6d163e820\config.json | binary | |
MD5:ED5B4B29E9E1C159AED86EA8C4C7CBBD | SHA256:28308116E7A89D2B6D26F85C9A19B96942C7853B9C940FD190025A09E826A403 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
34
DNS requests
13
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4060 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2036 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4060 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6232 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5264 | xmrig.exe | 51.79.157.201:5332 | sg-zephyr.miningocean.org | OVH SAS | SG | unknown |
2036 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2036 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6232 | svchost.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
sg-zephyr.miningocean.org |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5264 | xmrig.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
5264 | xmrig.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
1 ETPRO signatures available at the full report