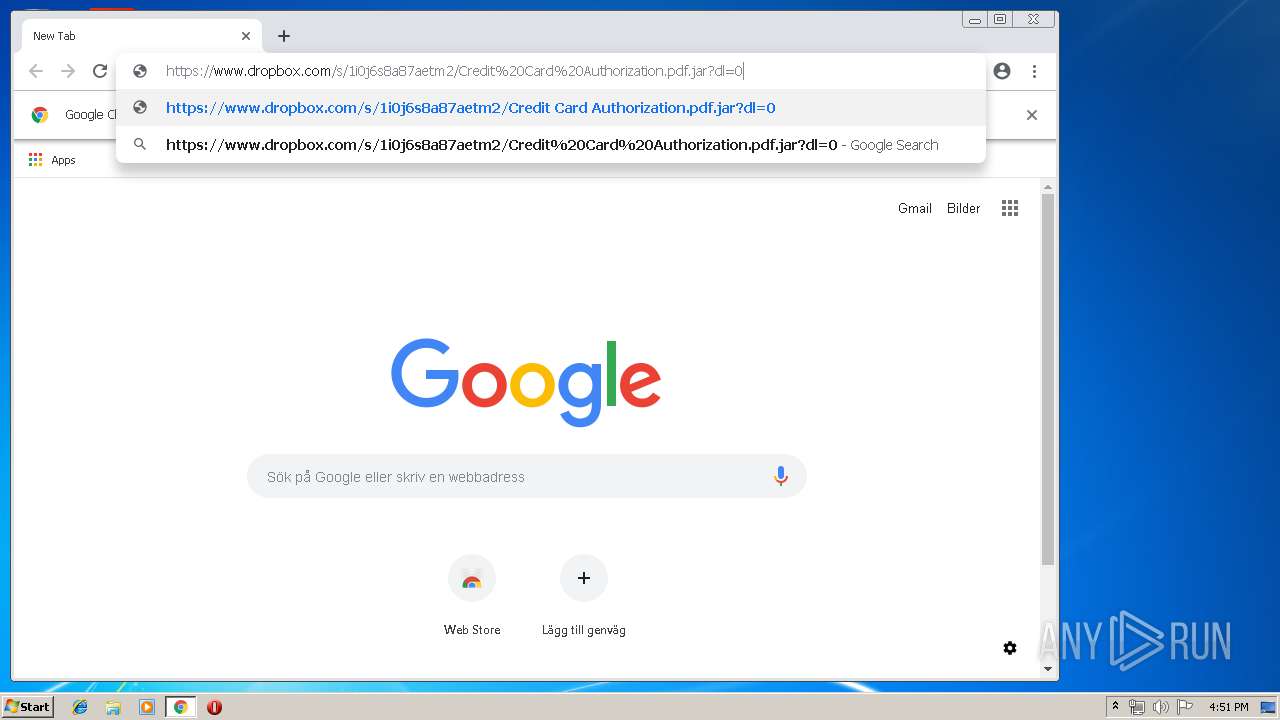
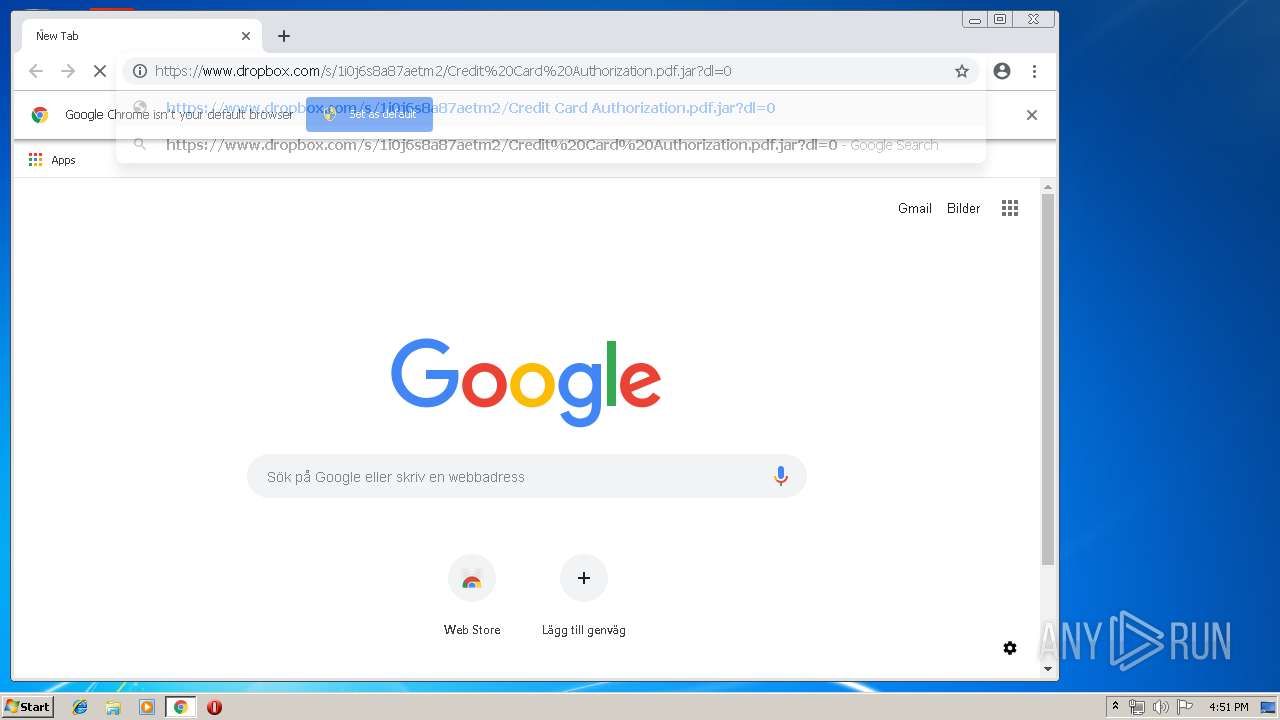
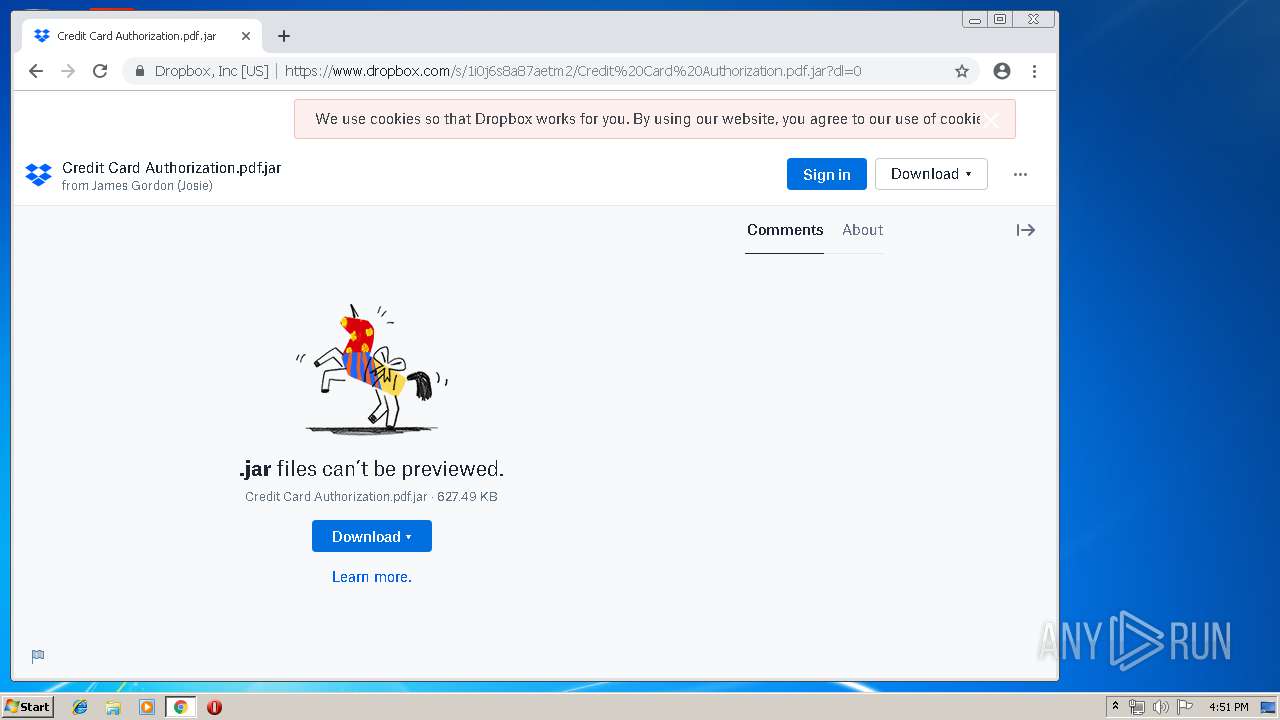
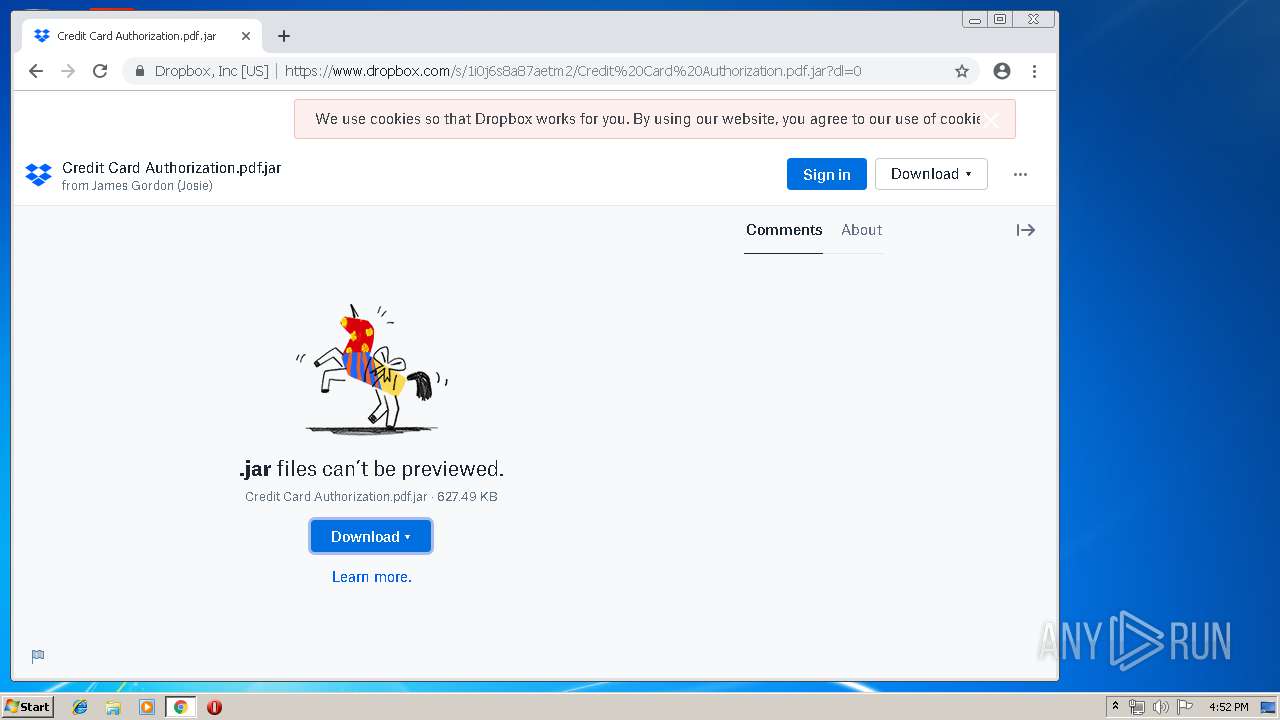
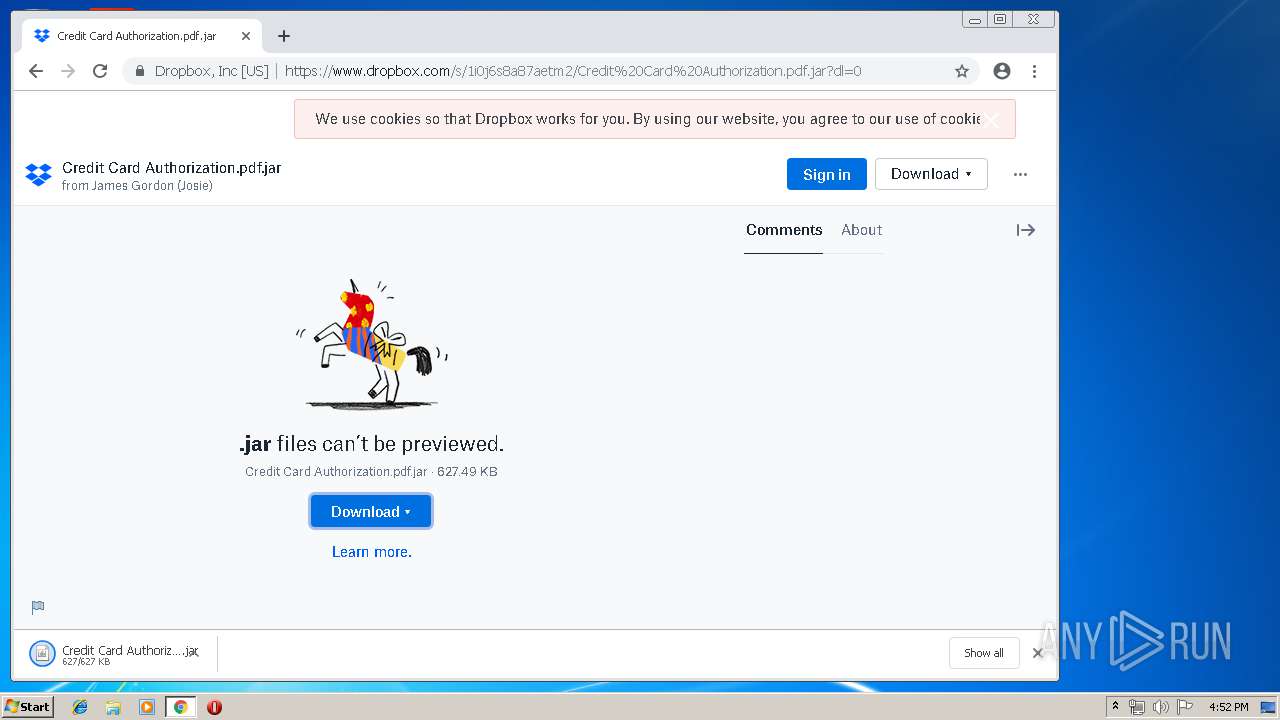
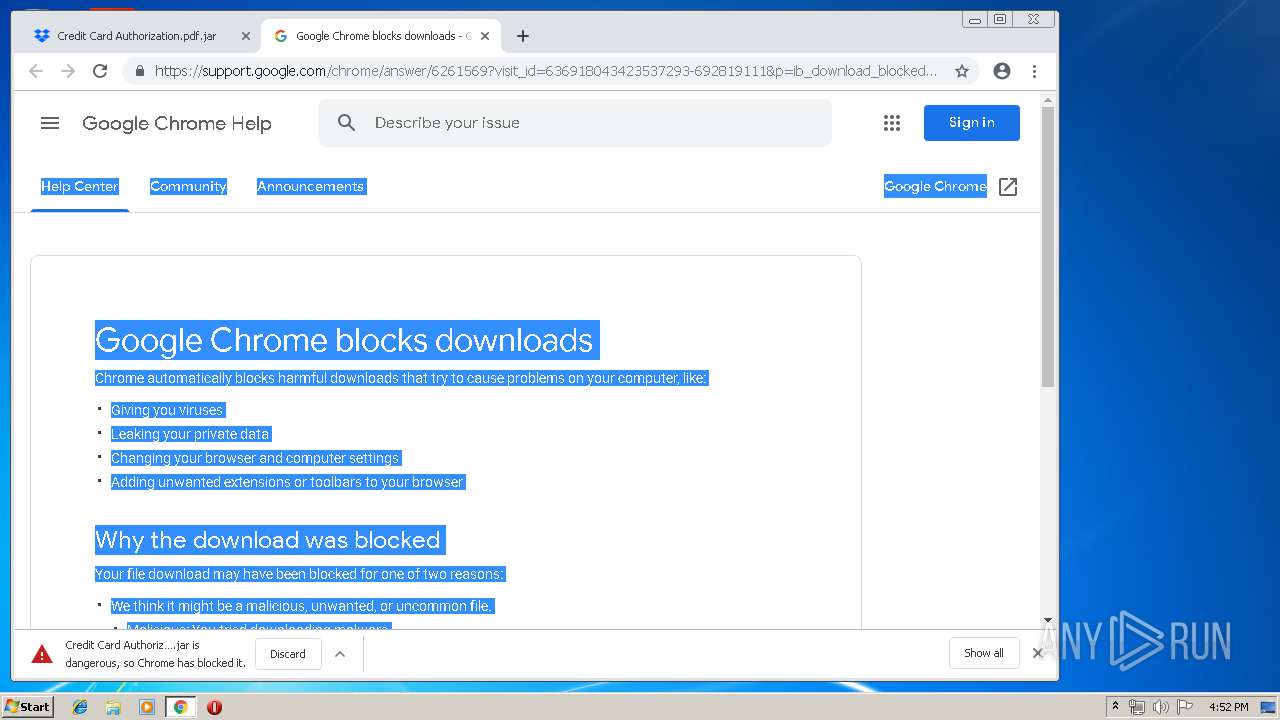
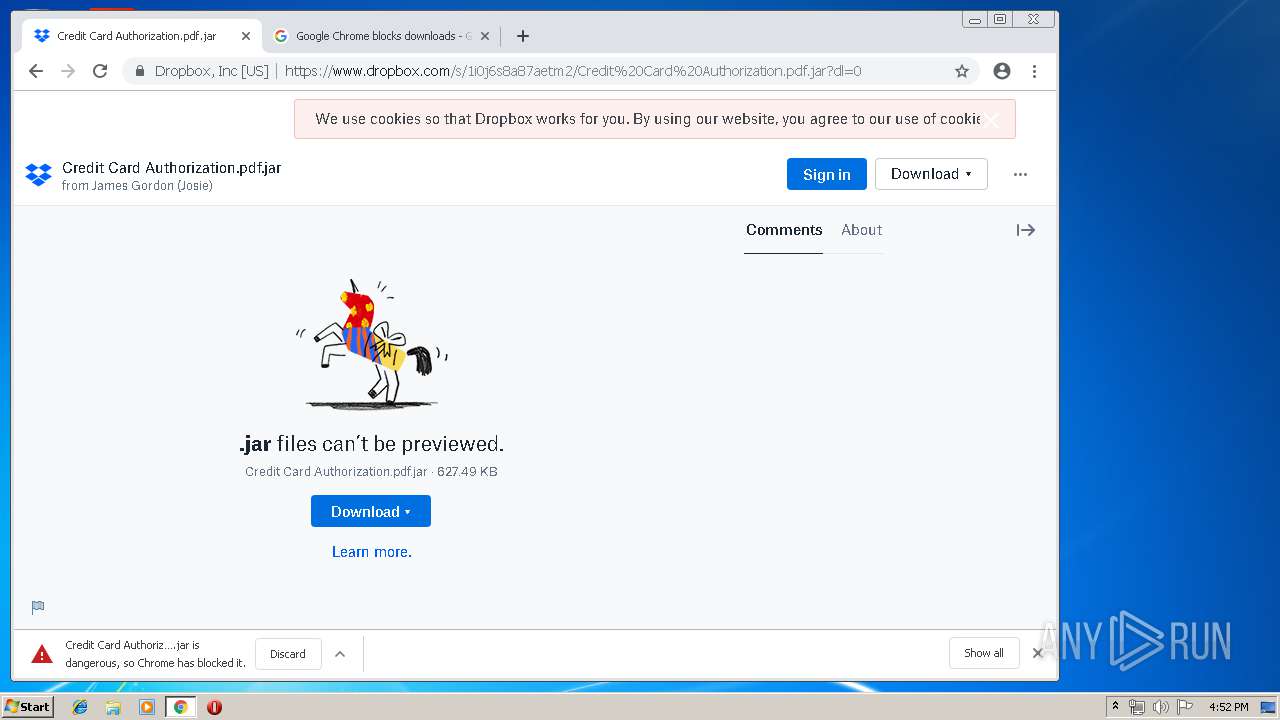
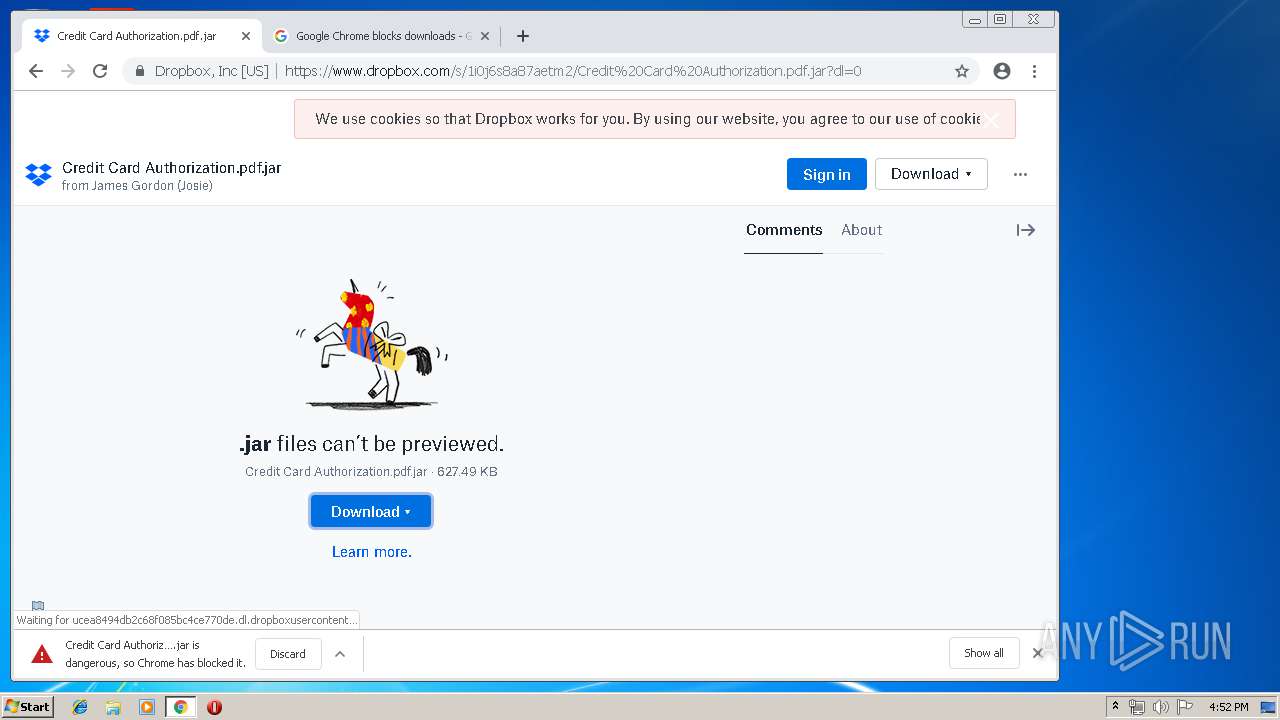
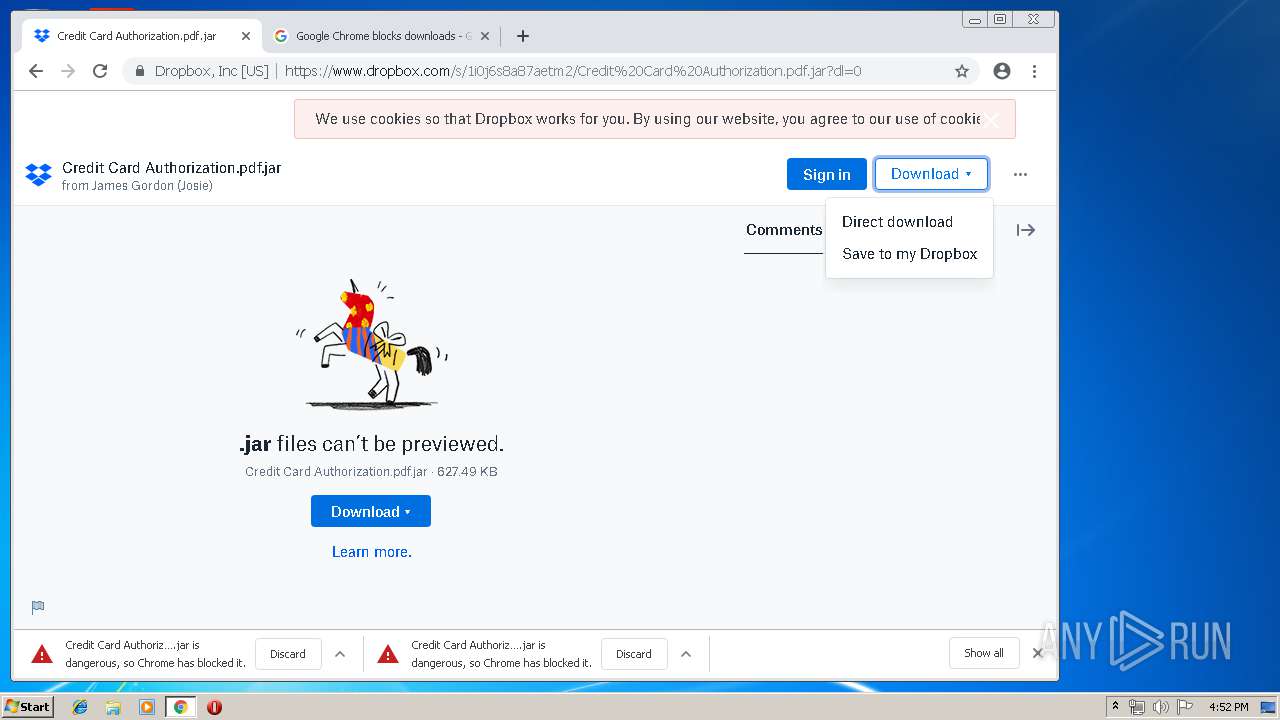
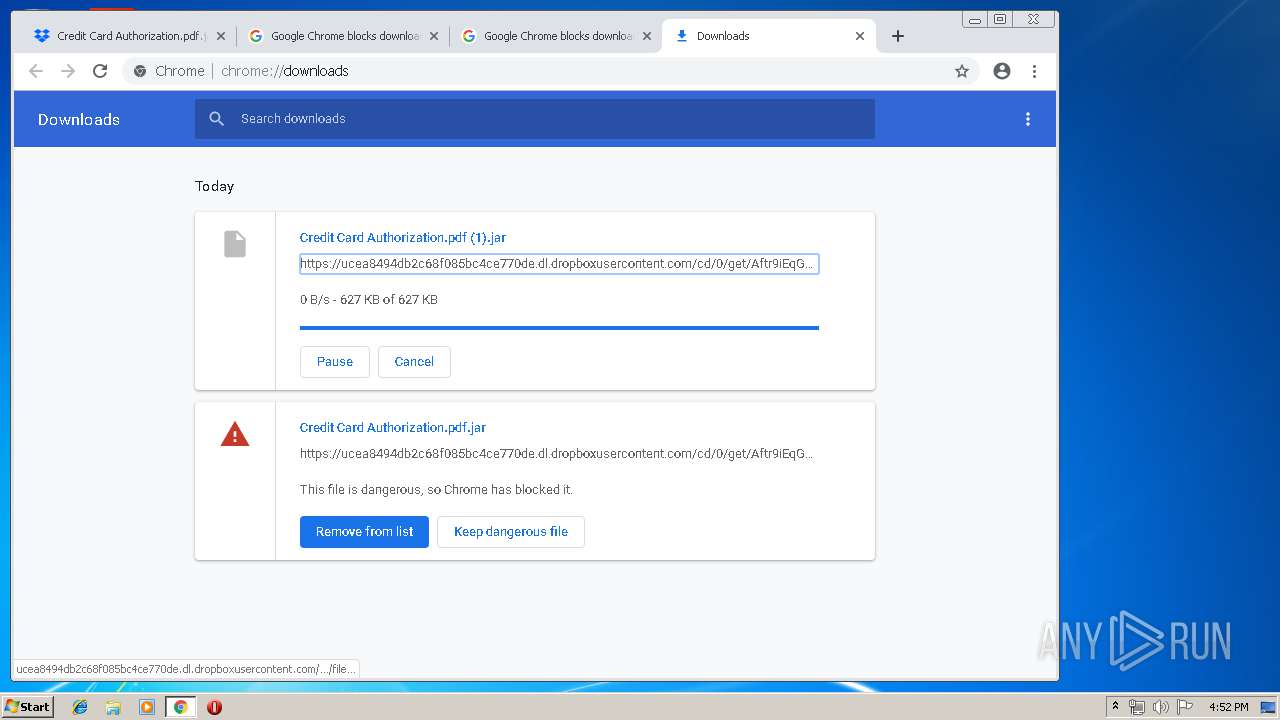
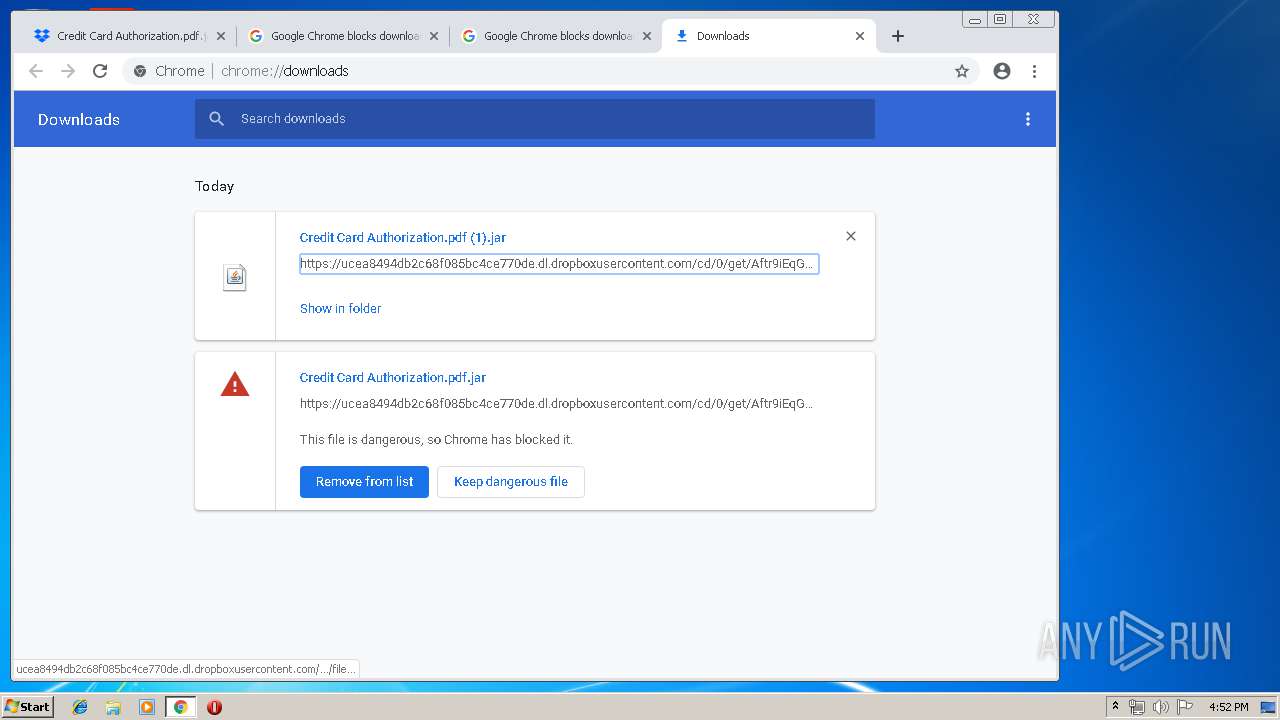
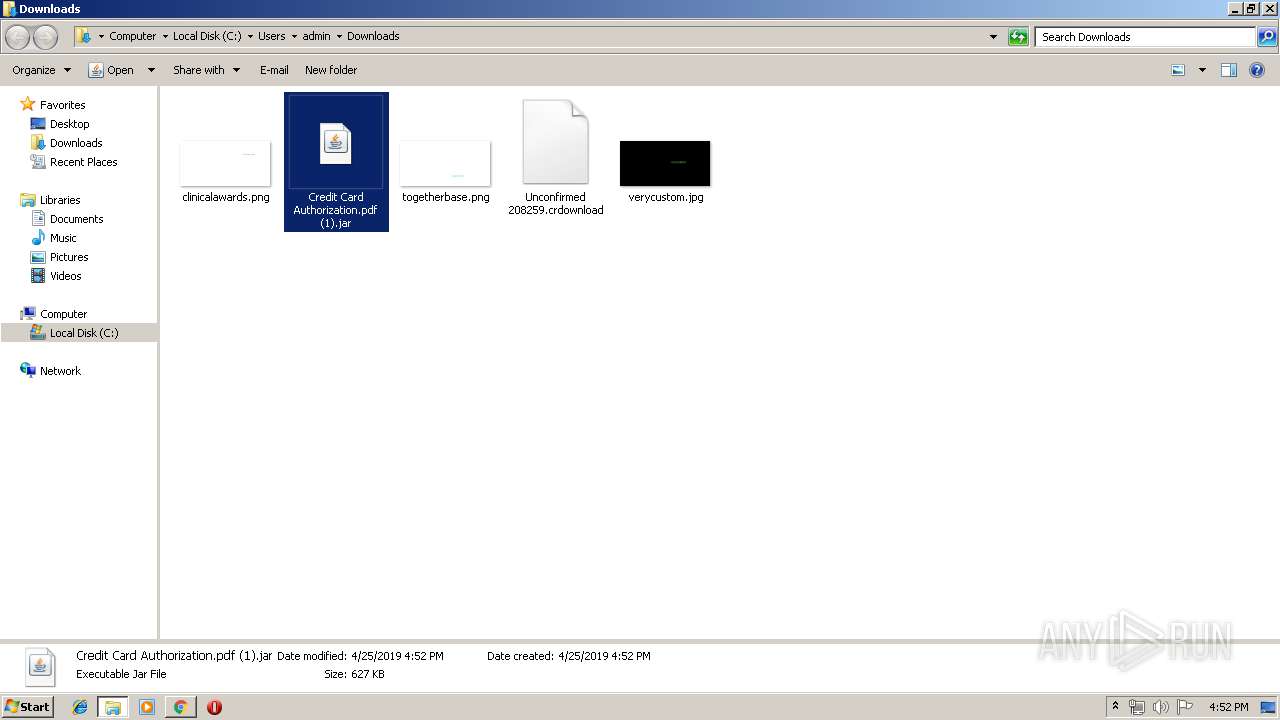
| URL: | https://www.dropbox.com/s/1i0j6s8a87aetm2/Credit%20Card%20Authorization.pdf.jar?dl=0 |
| Full analysis: | https://app.any.run/tasks/ea879bb3-4fe0-4e20-9d70-4651677b94ec |
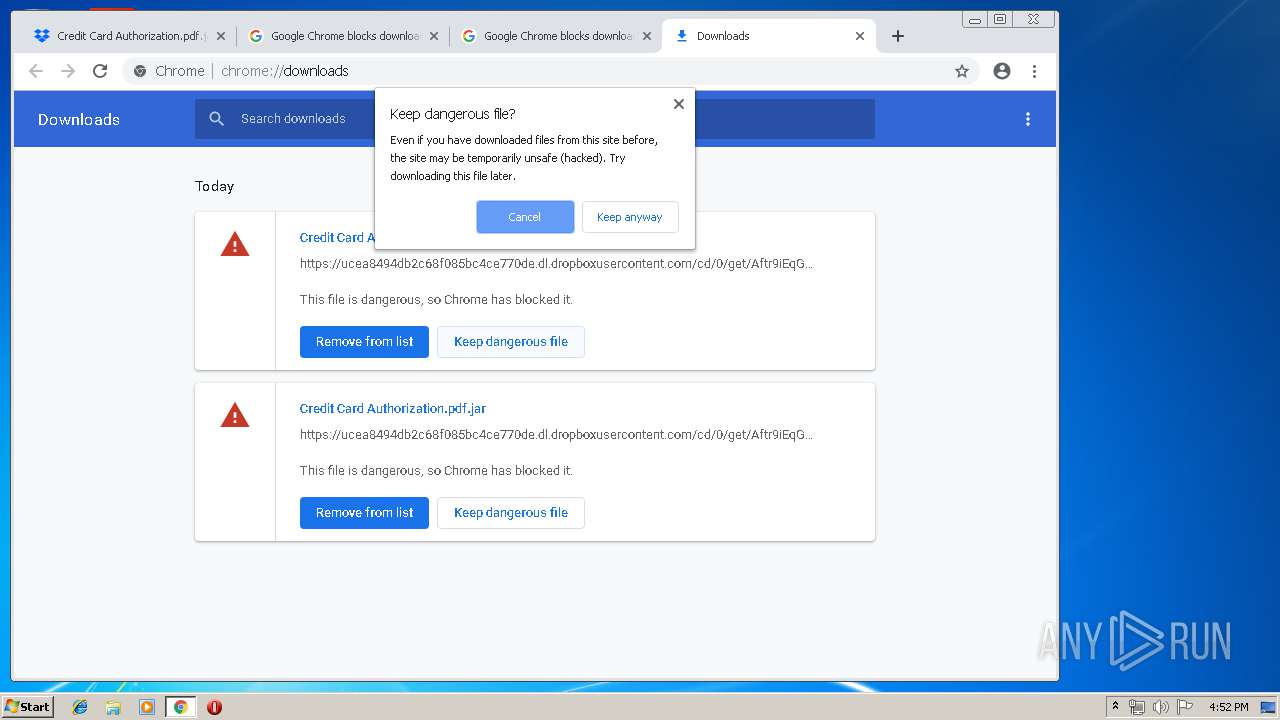
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
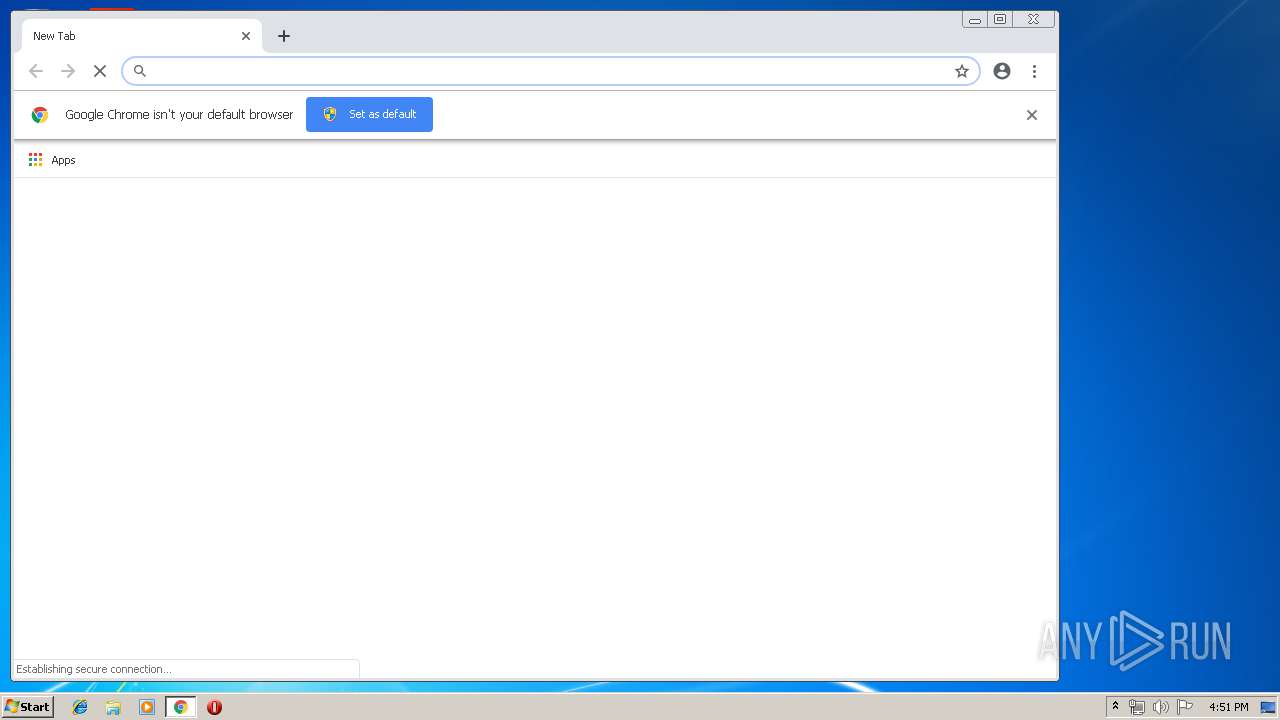
| Analysis date: | April 25, 2019, 15:51:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 155D12DC85D69E5C08305731DFDF7E73 |
| SHA1: | 3B69B802416B7F85EA0D777AD2A2A5CEC703D969 |
| SHA256: | 085F0D4EB426EAAC2BF2FB4AA9E5CFFC25841B72EF5697E19191D1092C6CC18C |
| SSDEEP: | 3:N8DSLcVHGkuTa030q9Q6RCQSeERPsXrV:2OLHk1qK6PURPsXrV |
MALICIOUS
Changes the autorun value in the registry
- WScript.exe (PID: 4036)
- reg.exe (PID: 3824)
Uses Task Scheduler to run other applications
- WScript.exe (PID: 4036)
Writes to a start menu file
- WScript.exe (PID: 4036)
AdWind was detected
- java.exe (PID: 2876)
- java.exe (PID: 3504)
Loads dropped or rewritten executable
- iexplore.exe (PID: 1388)
- java.exe (PID: 2876)
- wscript.exe (PID: 3384)
- explorer.exe (PID: 2036)
- javaw.exe (PID: 3640)
- javaw.exe (PID: 3716)
- java.exe (PID: 3504)
- javaw.exe (PID: 3452)
- svchost.exe (PID: 812)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3604)
Application was dropped or rewritten from another process
- javaw.exe (PID: 3716)
- java.exe (PID: 2876)
- javaw.exe (PID: 3640)
- javaw.exe (PID: 3452)
- java.exe (PID: 3504)
SUSPICIOUS
Starts Internet Explorer
- explorer.exe (PID: 2036)
Executes JAVA applets
- explorer.exe (PID: 2036)
- wscript.exe (PID: 3384)
- javaw.exe (PID: 3716)
Creates files in the user directory
- wscript.exe (PID: 3384)
- WScript.exe (PID: 4036)
- javaw.exe (PID: 3716)
- xcopy.exe (PID: 2948)
Application launched itself
- wscript.exe (PID: 3384)
Executes scripts
- javaw.exe (PID: 3640)
- wscript.exe (PID: 3384)
- cmd.exe (PID: 2664)
- cmd.exe (PID: 2900)
- cmd.exe (PID: 1100)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 3144)
- cmd.exe (PID: 3296)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2228)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3716)
- java.exe (PID: 2876)
- javaw.exe (PID: 3452)
- java.exe (PID: 3504)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2948)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 3716)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 3716)
Starts itself from another location
- javaw.exe (PID: 3716)
INFO
Creates files in the user directory
- iexplore.exe (PID: 1388)
Reads Internet Cache Settings
- iexplore.exe (PID: 1388)
Application launched itself
- iexplore.exe (PID: 3152)
- chrome.exe (PID: 2228)
Changes internet zones settings
- iexplore.exe (PID: 3152)
Reads internet explorer settings
- iexplore.exe (PID: 1388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
102
Monitored processes
57
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15029044412879511854,9697648263475175853,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10798295615402327050 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10798295615402327050 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 812 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive7279801481728296456.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1100 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive7886102626472775478.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15029044412879511854,9697648263475175853,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3209857402243983943 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3209857402243983943 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15029044412879511854,9697648263475175853,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14068561748969214442 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14068561748969214442 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3152 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15029044412879511854,9697648263475175853,131072 --enable-features=PasswordImport --service-pipe-token=1699695938151817537 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1699695938151817537 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15029044412879511854,9697648263475175853,131072 --enable-features=PasswordImport --service-pipe-token=2537467805371948377 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2537467805371948377 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2036 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 981
Read events
2 733
Write events
242
Delete events
6
Modification events
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {FC29BD33-6771-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070400040019000F0033001C00DC02 | |||
Executable files
110
Suspicious files
394
Text files
252
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1388 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@dropbox[1].txt | — | |
MD5:— | SHA256:— | |||
| 1388 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.dropbox[2].txt | — | |
MD5:— | SHA256:— | |||
| 1388 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\41I7MH4N\Credit%20Card%20Authorization.pdf[1].jar | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6A3A1C6B023B7B36.TMP | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF95BF940B4264BE96.TMP | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2763ADE36E7304BE.TMP | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{FC29BD34-6771-11E9-B63D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFE3C3AB745C31050D.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
85
DNS requests
34
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2228 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2228 | chrome.exe | GET | 200 | 172.217.130.73:80 | http://r4---sn-2gb7sn7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.76.9.72&mm=28&mn=sn-2gb7sn7r&ms=nvh&mt=1556207426&mv=m&pl=25&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2228 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAU5fm3dSuY9dJCdoTinHgw%3D | US | der | 471 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1388 | iexplore.exe | 162.125.66.1:443 | www.dropbox.com | Dropbox, Inc. | DE | shared |
2228 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.16.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.23.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.23.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1388 | iexplore.exe | 104.16.100.29:443 | cfl.dropboxstatic.com | Cloudflare Inc | US | shared |
2228 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 162.125.66.1:443 | www.dropbox.com | Dropbox, Inc. | DE | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.dropbox.com |
| shared |
cfl.dropboxstatic.com |
| shared |
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2228 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
2228 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2228 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |