| File name: | Attachment.eml |
| Full analysis: | https://app.any.run/tasks/197ac55c-ac37-4966-b9bf-d8a79f70b1d7 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | March 31, 2020, 12:05:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
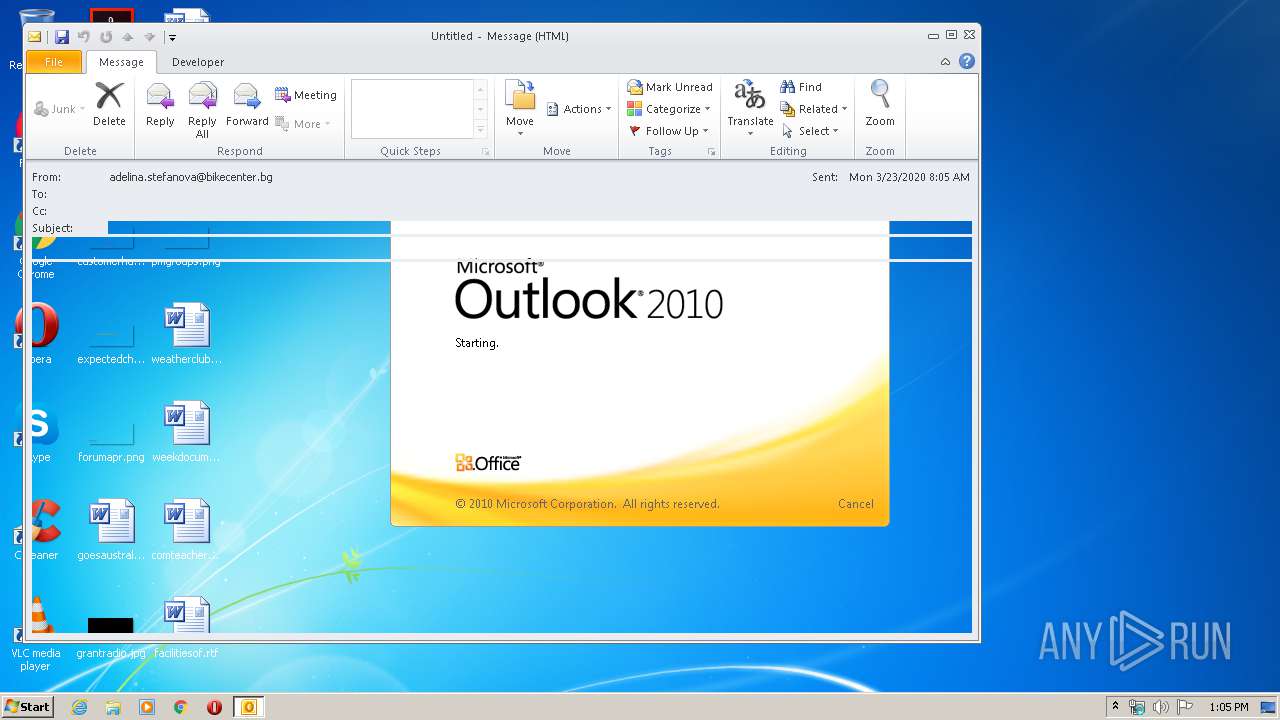
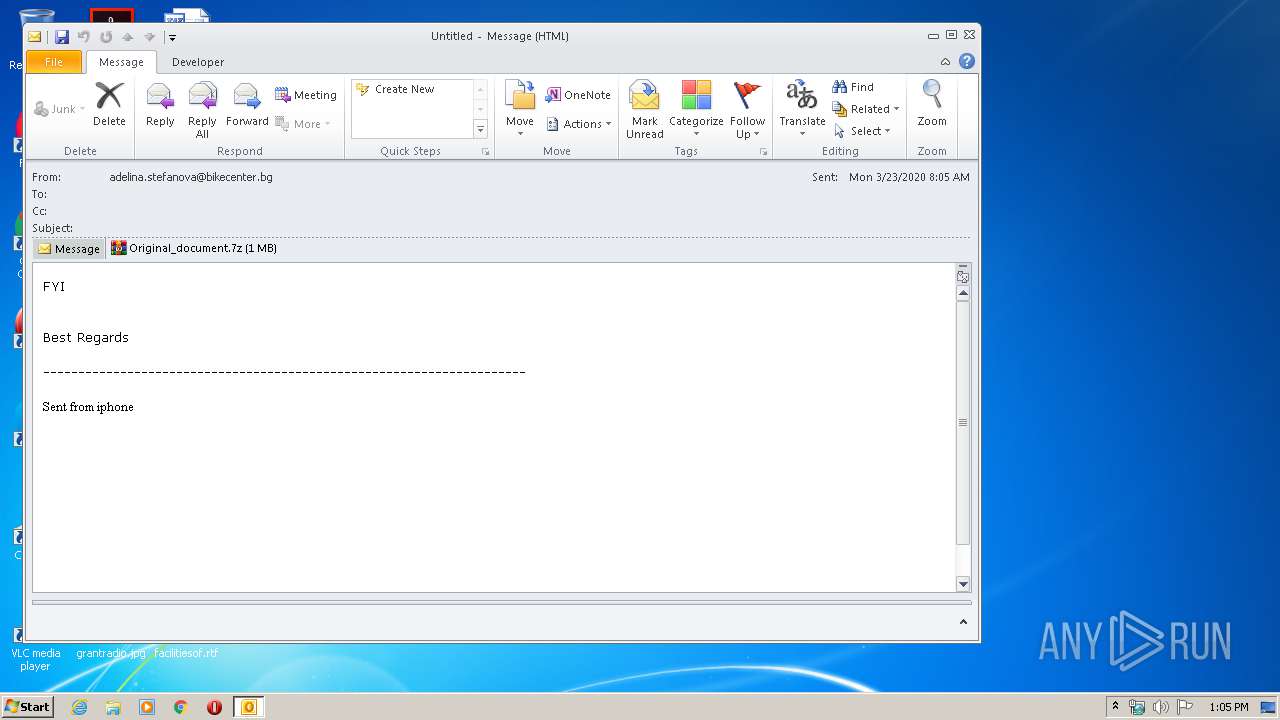
| MIME: | text/html |
| File info: | HTML document, ASCII text, with CRLF line terminators |
| MD5: | 64C4A81E9FF51D2C86BF7C05D2D75582 |
| SHA1: | 47B85C324308AAD13FBA19E6DB411CDC0BD1C535 |
| SHA256: | 085F0ADBDF4A0D292D415839D280F2AA0E6C727CE29EA2D45642EA5840B57316 |
| SSDEEP: | 24576:5k2DIYYkVE4FKFEGyEd5e290ylXLgEgiUlkrCeGFz7teDA5PNxDG4V2bs5SxIL7J:Tq7yL2zmbeLExV52s6yqwoCJYuthAs |
MALICIOUS
Uses NirSoft utilities to collect credentials
- vbc.exe (PID: 3912)
- vbc.exe (PID: 680)
Application was dropped or rewritten from another process
- Original_document.exe (PID: 4084)
Detected Hawkeye Keylogger
- RegAsm.exe (PID: 3560)
Actions looks like stealing of personal data
- vbc.exe (PID: 680)
- vbc.exe (PID: 3912)
Stealing of credential data
- vbc.exe (PID: 680)
- vbc.exe (PID: 3912)
SUSPICIOUS
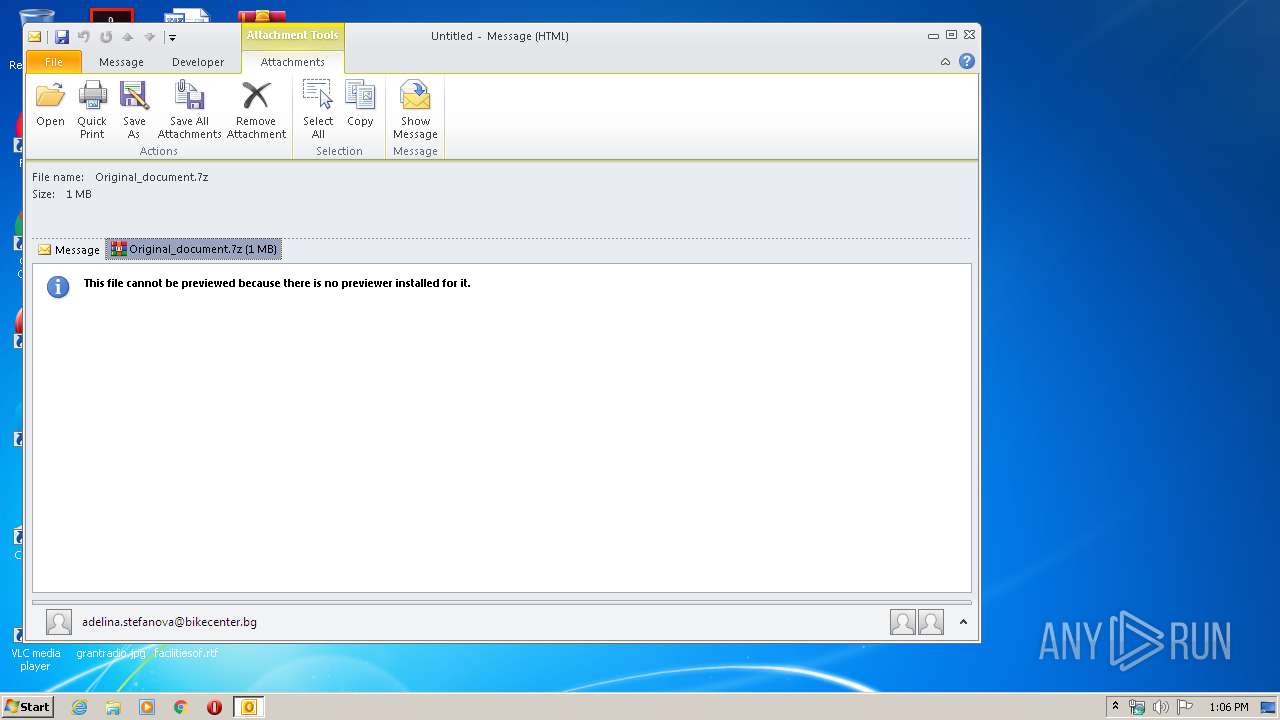
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 916)
Executable content was dropped or overwritten
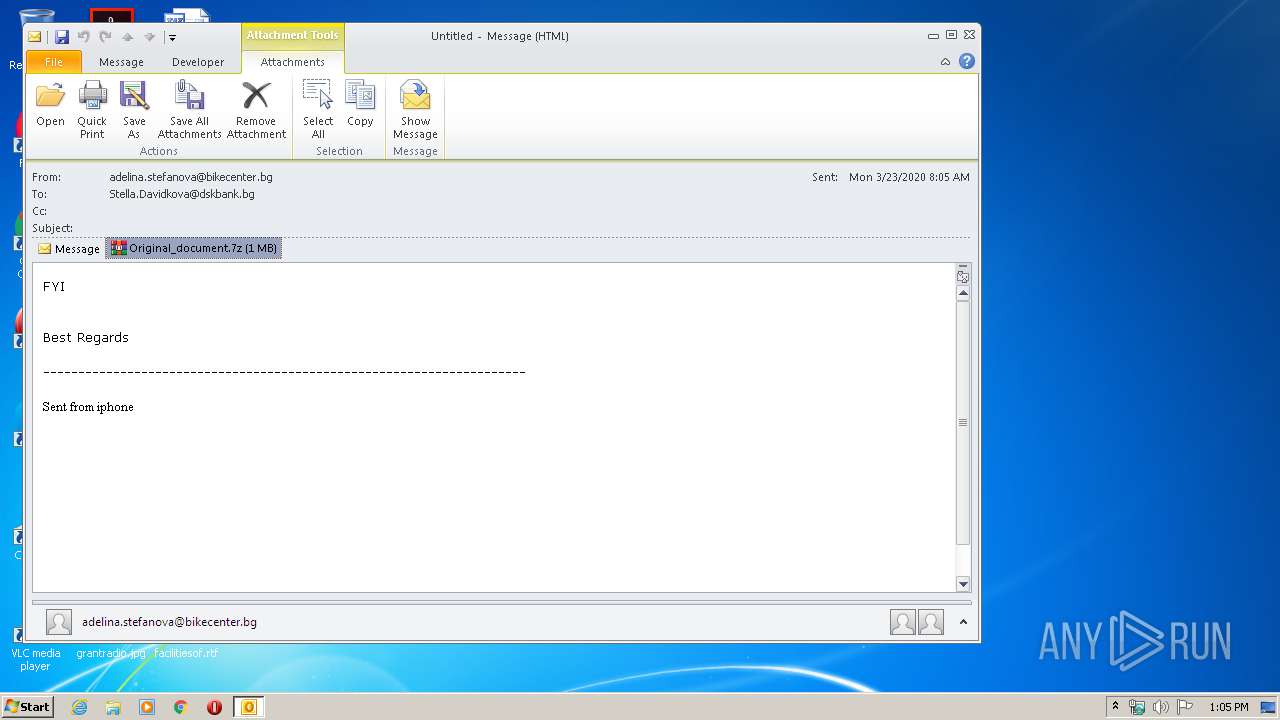
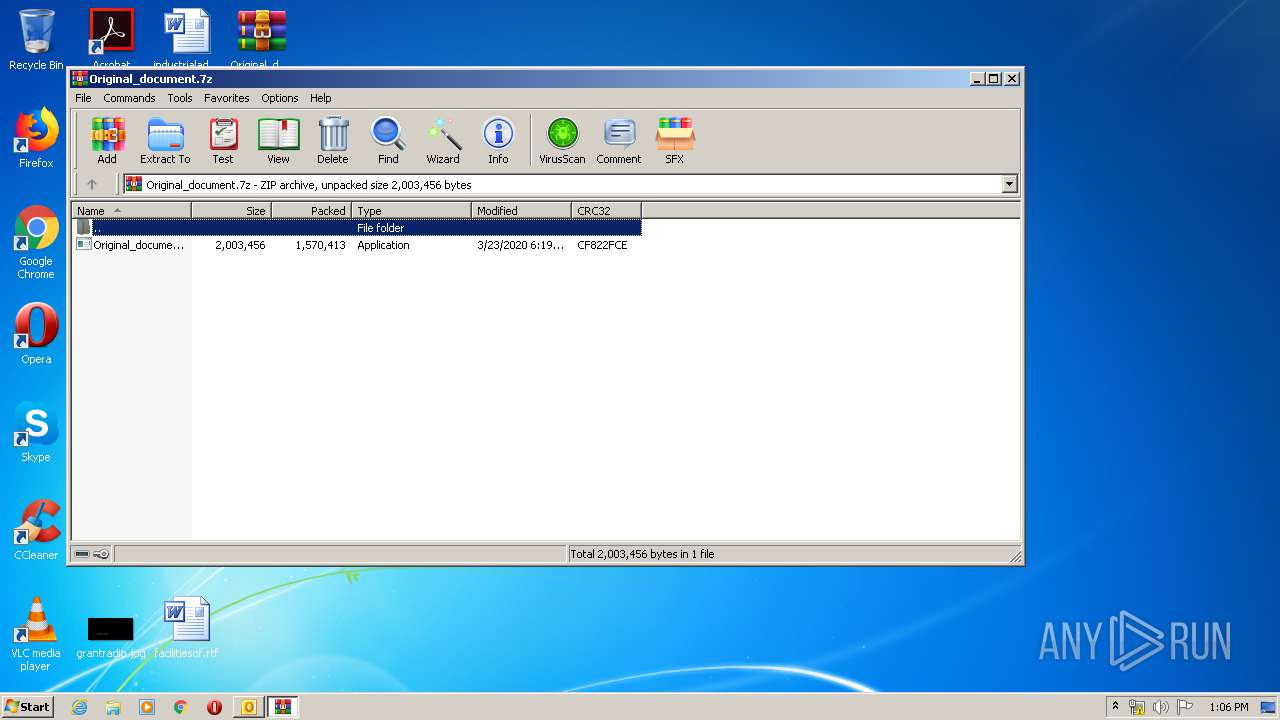
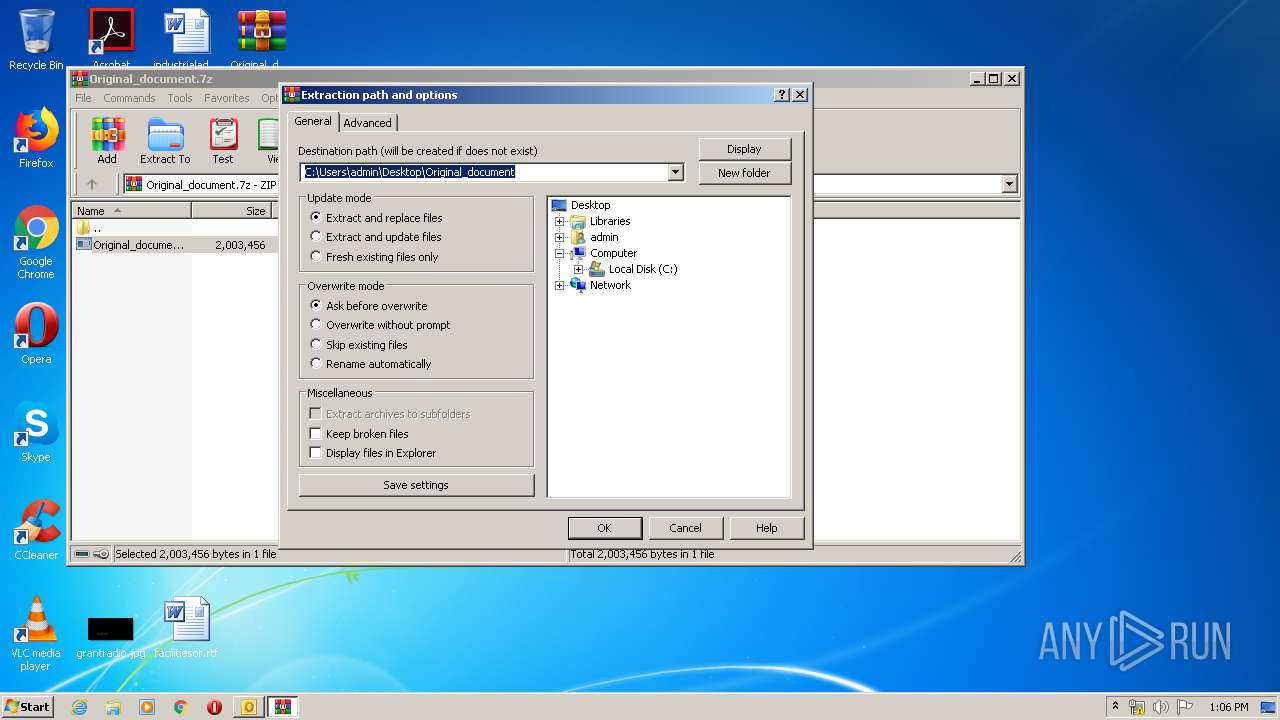
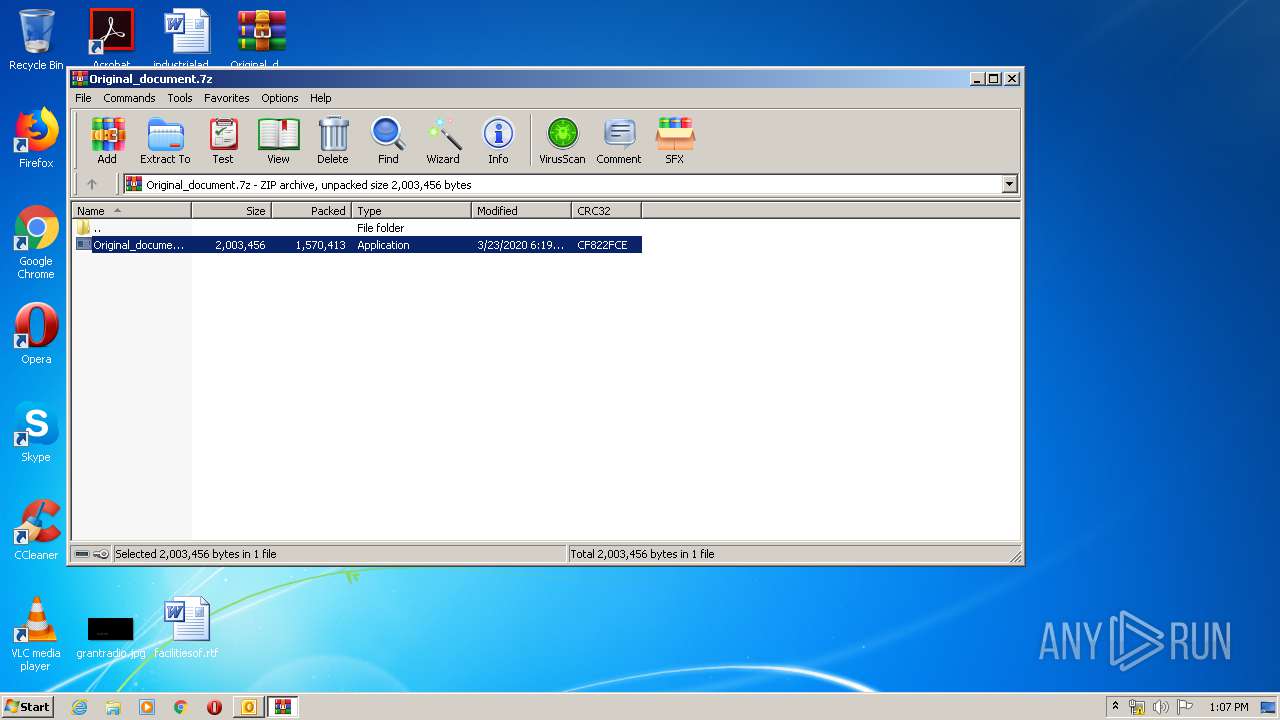
- WinRAR.exe (PID: 604)
Creates files in the user directory
- OUTLOOK.EXE (PID: 916)
Executes scripts
- RegAsm.exe (PID: 3560)
INFO
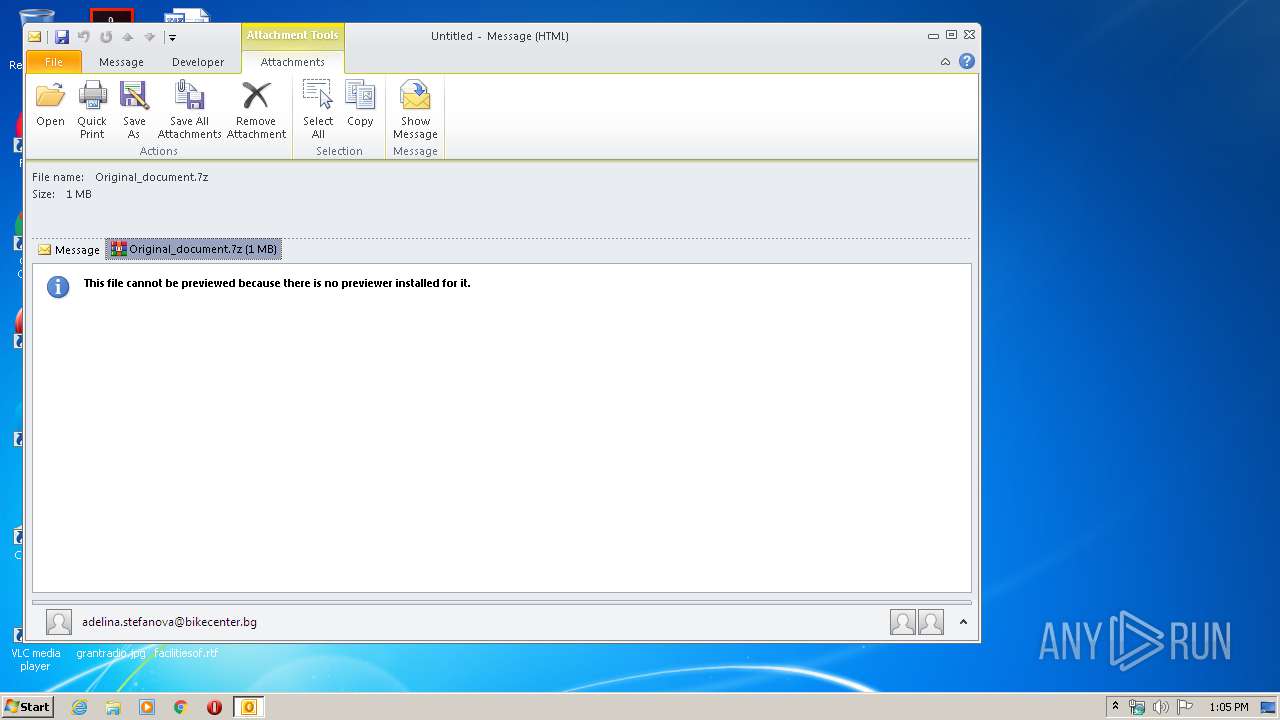
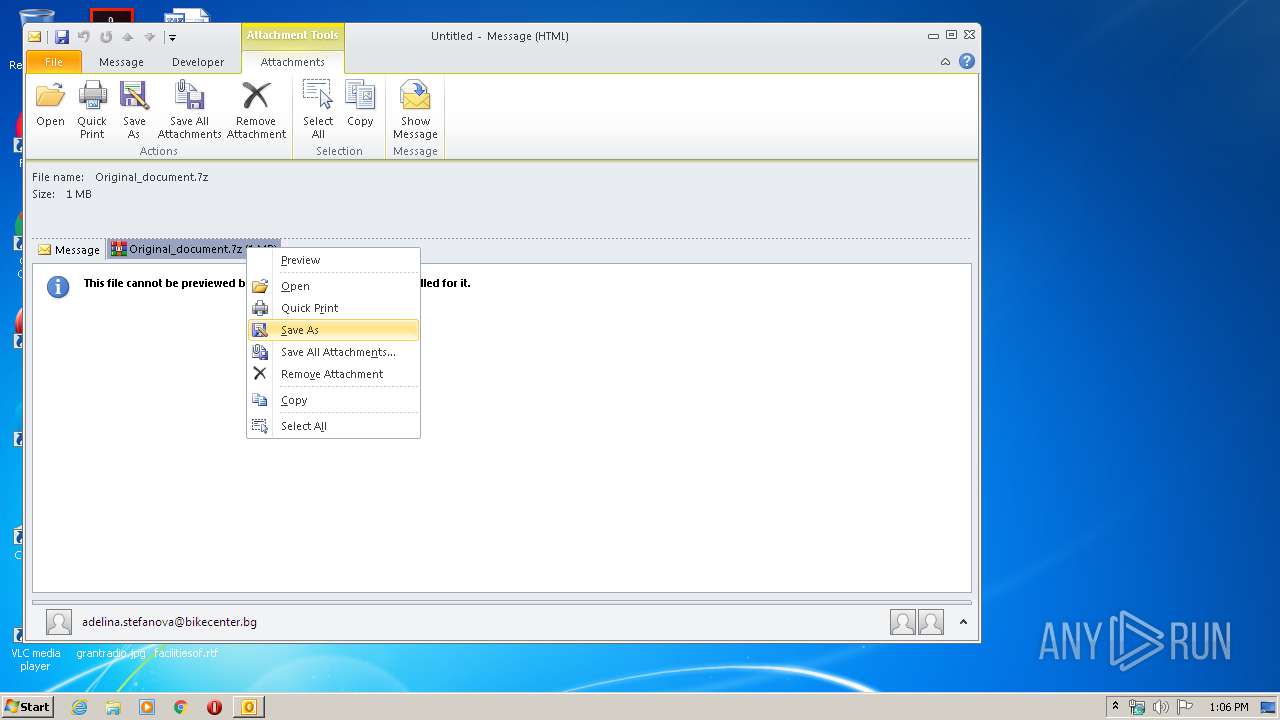
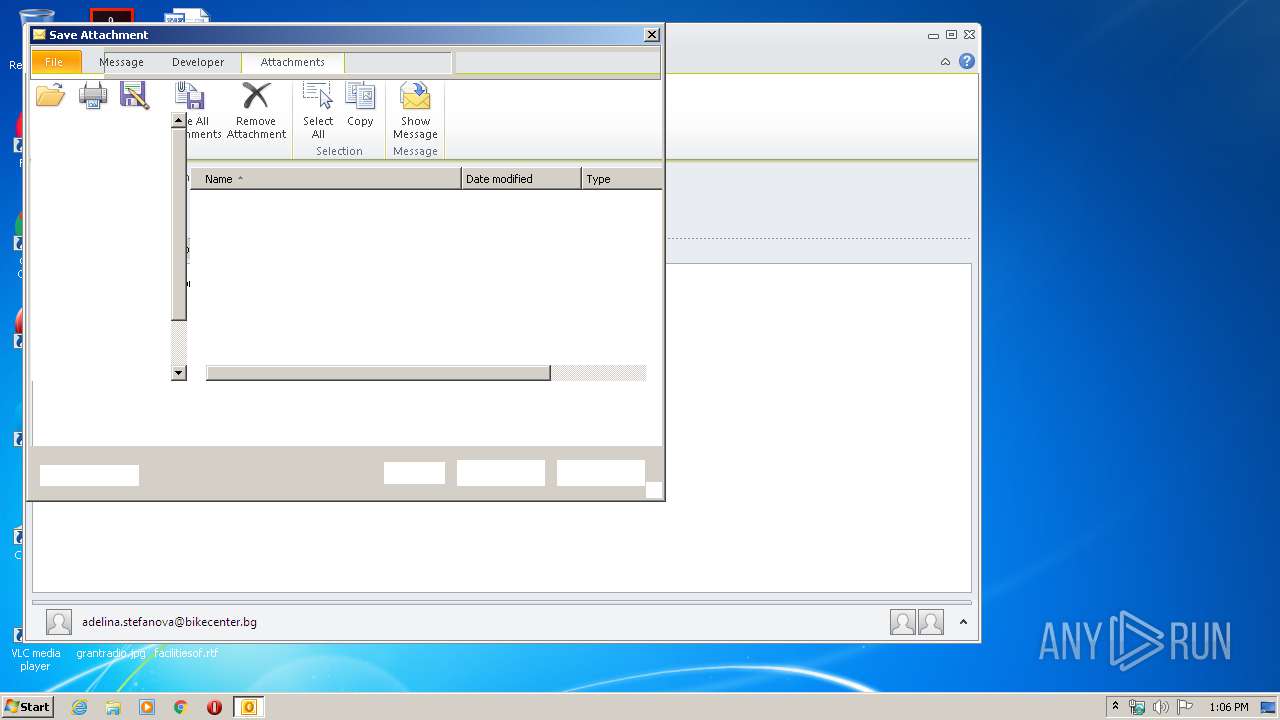
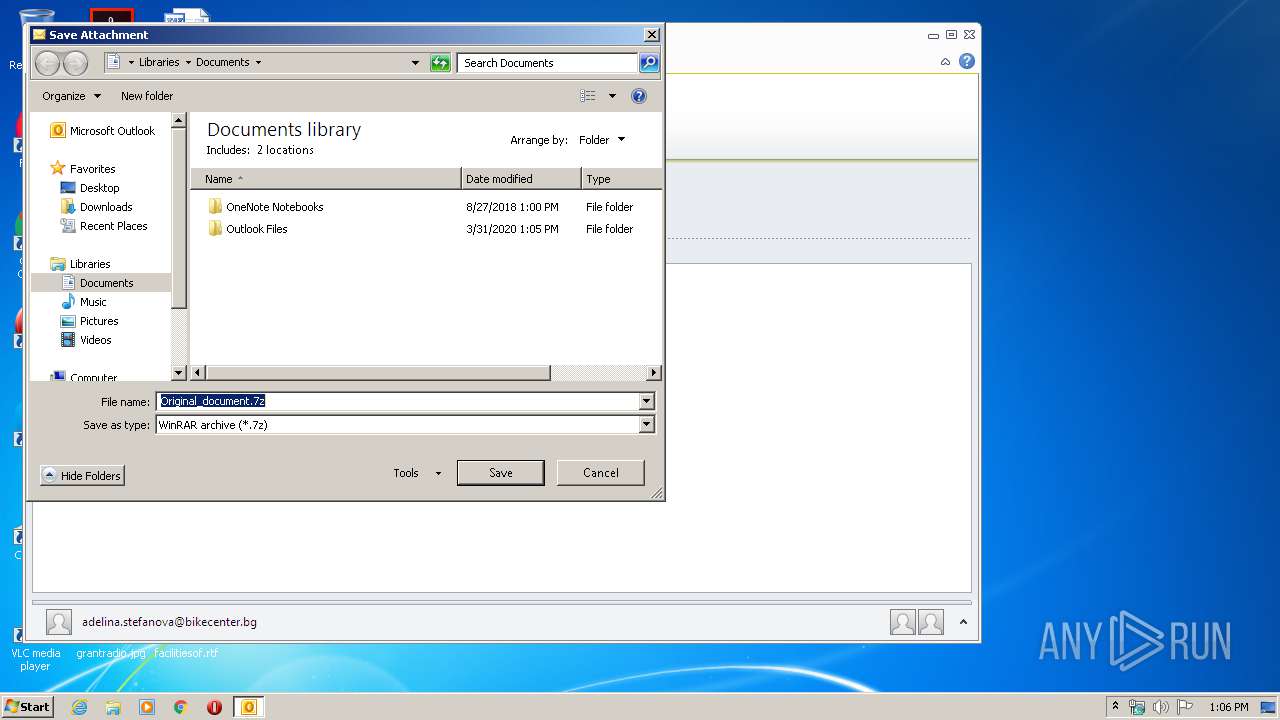
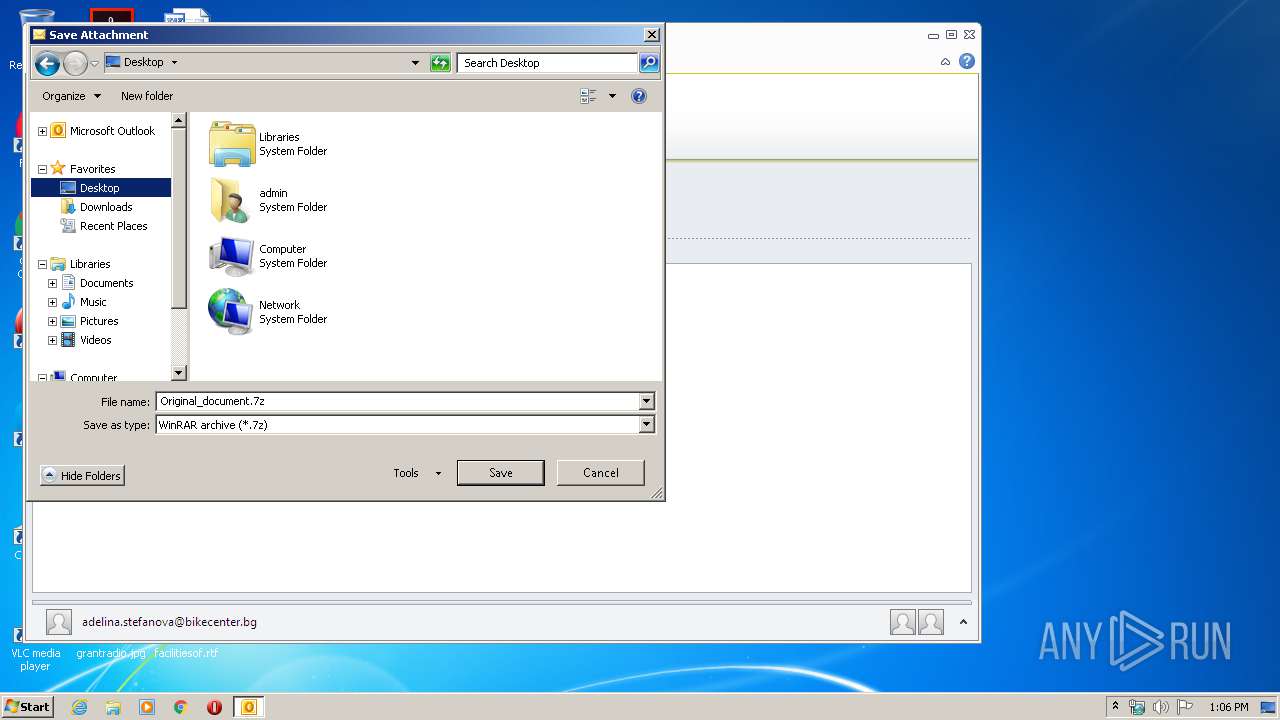
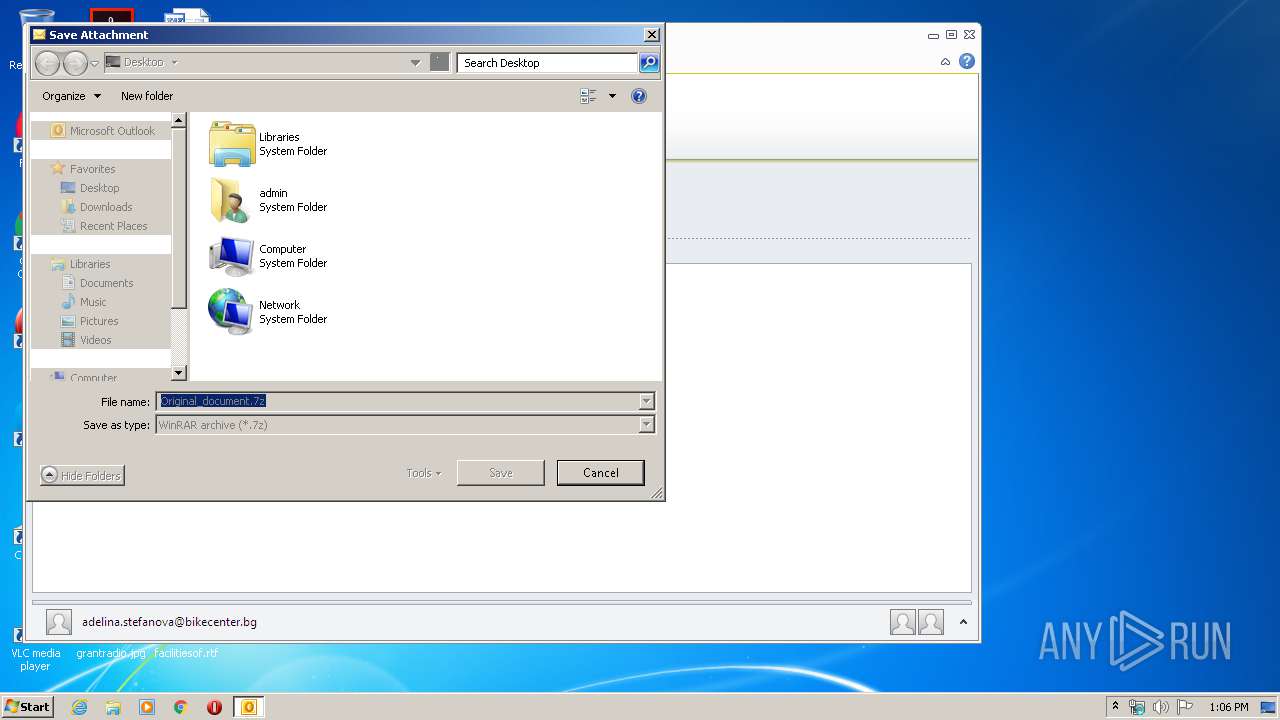
Manual execution by user
- WinRAR.exe (PID: 604)
- Original_document.exe (PID: 4084)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 3) (100) |
|---|
Total processes
46
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Original_document.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 680 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp1943.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 916 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Attachment.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3560 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v2.0.50727\\\\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | Original_document.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3912 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp1D4B.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 4084 | "C:\Users\admin\Desktop\Original_document.exe" | C:\Users\admin\Desktop\Original_document.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 385
Read events
1 731
Write events
632
Delete events
22
Modification events
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (916) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
1
Suspicious files
3
Text files
30
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6D78.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 916 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp6FCA.tmp | — | |
MD5:— | SHA256:— | |||
| 916 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\MC0Z6933\Original_document (2).7z\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 916 | OUTLOOK.EXE | C:\Users\admin\Desktop\Original_document.7z\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 680 | vbc.exe | C:\Users\admin\AppData\Local\Temp\bhv1991.tmp | — | |
MD5:— | SHA256:— | |||
| 916 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\MC0Z6933\Original_document.7z | compressed | |
MD5:— | SHA256:— | |||
| 916 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\MC0Z6933\Original_document (2).7z | compressed | |
MD5:— | SHA256:— | |||
| 916 | OUTLOOK.EXE | C:\Users\admin\Desktop\Original_document.7z | compressed | |
MD5:— | SHA256:— | |||
| 916 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 916 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3560 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 13 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | RegAsm.exe | 176.223.208.23:21 | ftp.firesupport.ro | Easyhost Srl | — | suspicious |
3560 | RegAsm.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
916 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
bot.whatismyipaddress.com |
| shared |
ftp.firesupport.ro |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3560 | RegAsm.exe | A Network Trojan was detected | SPYWARE [PTsecurity] HawkEye IP Check |
3560 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report