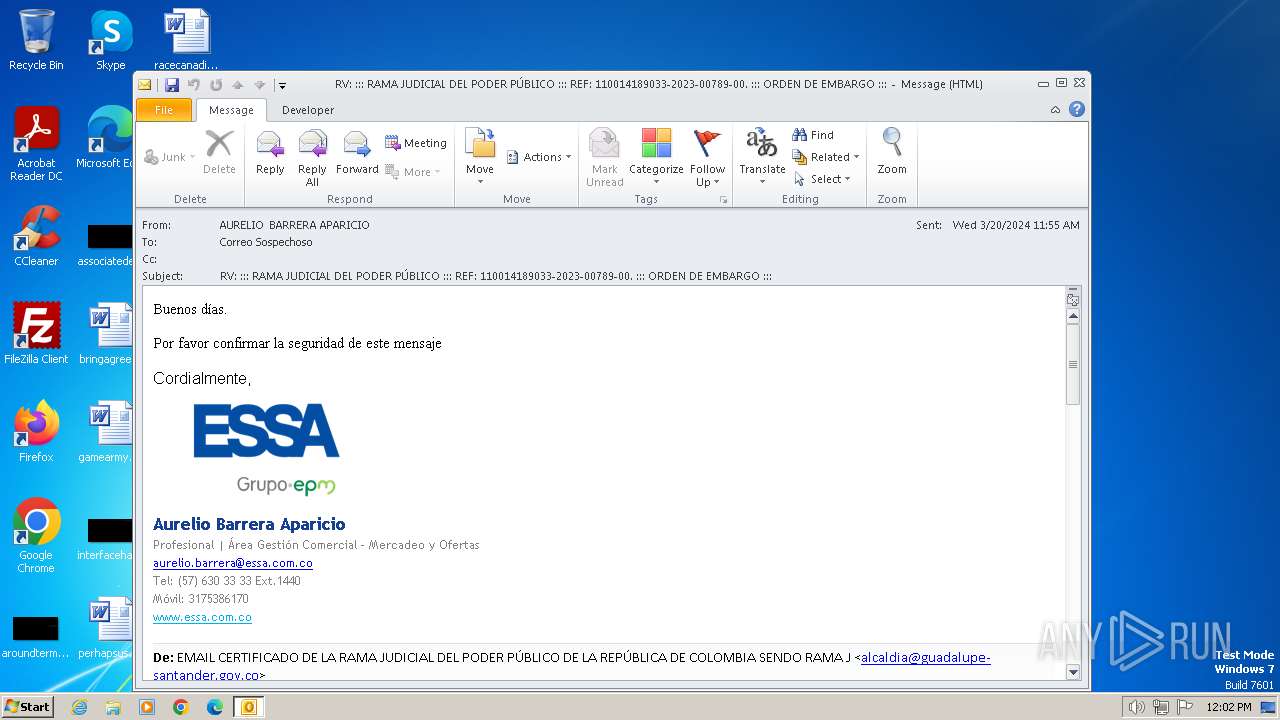
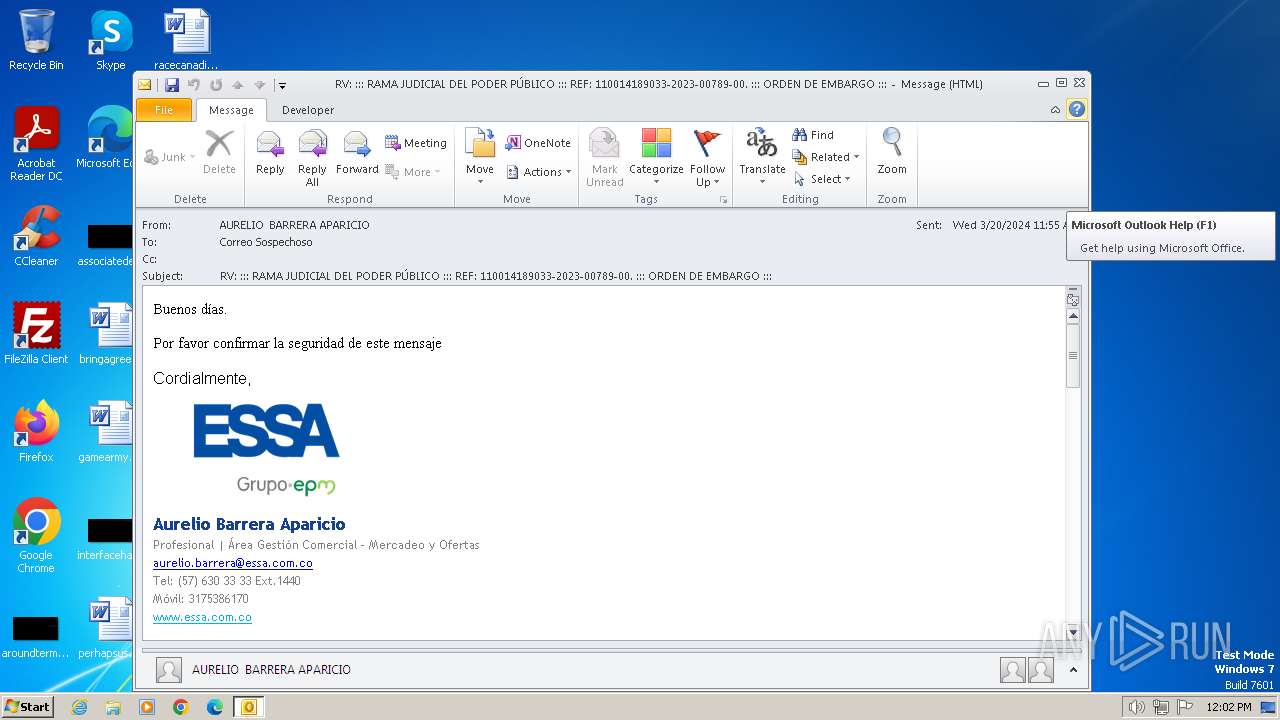
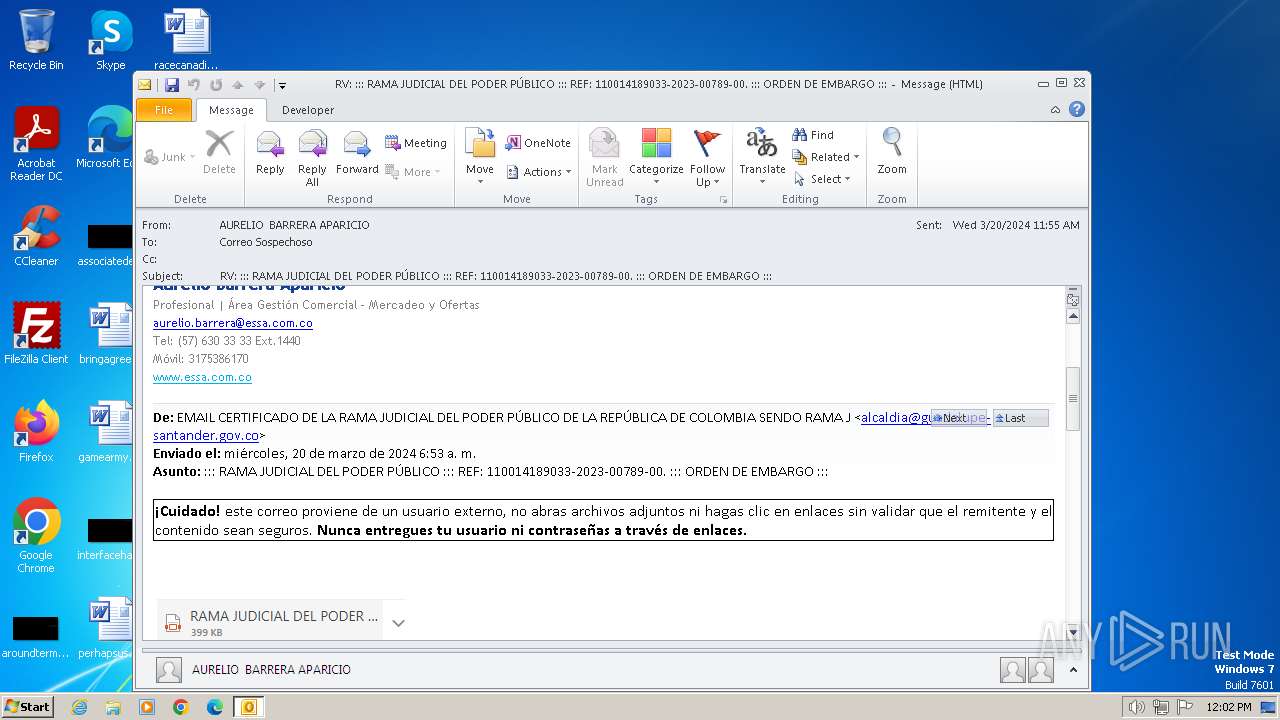
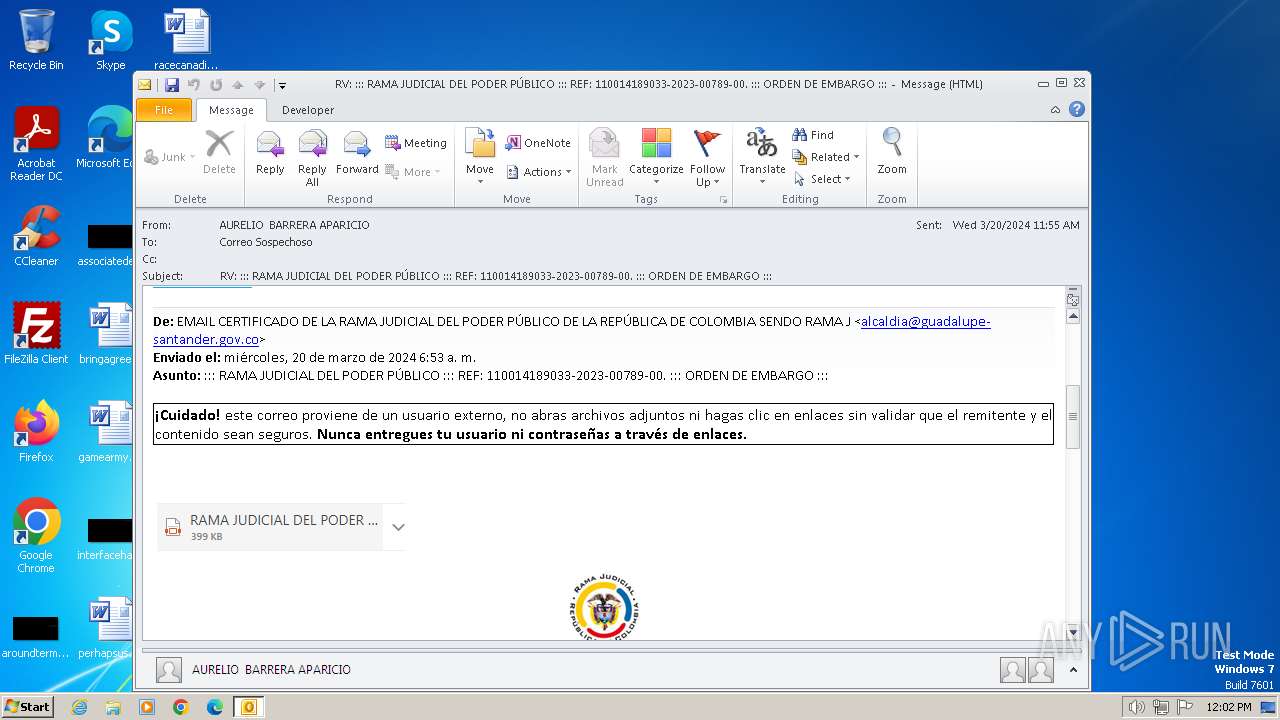
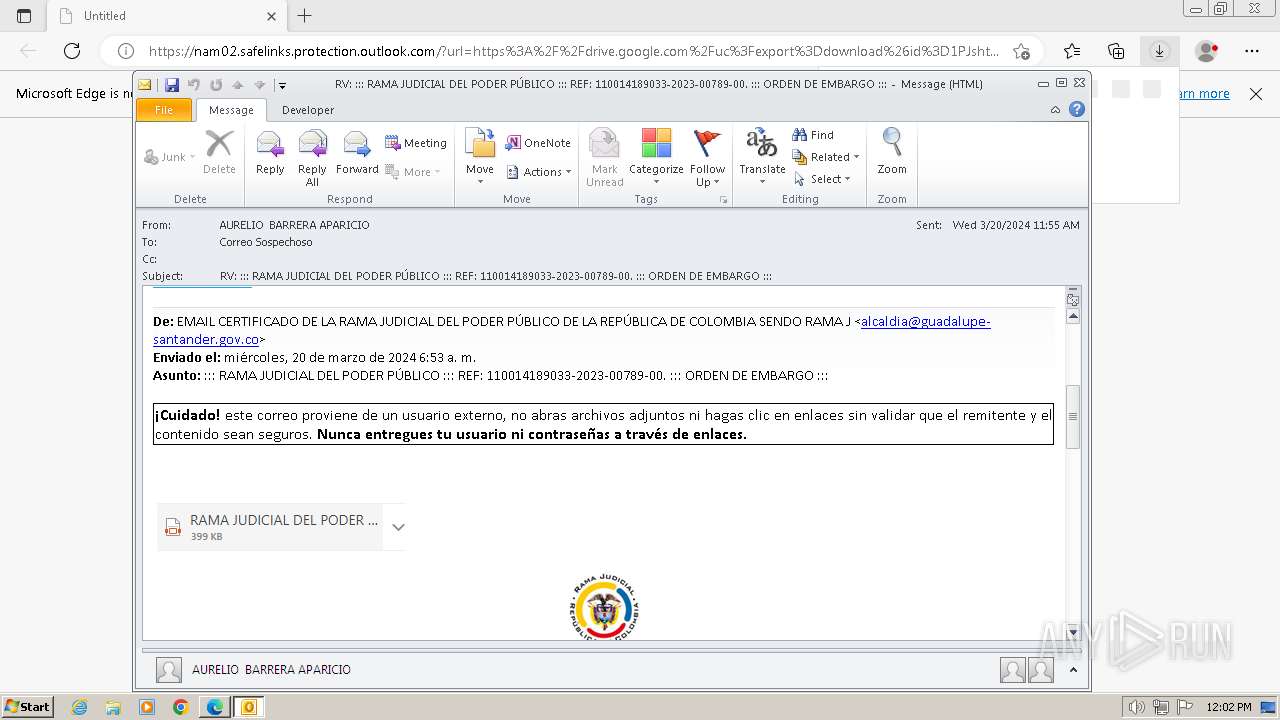
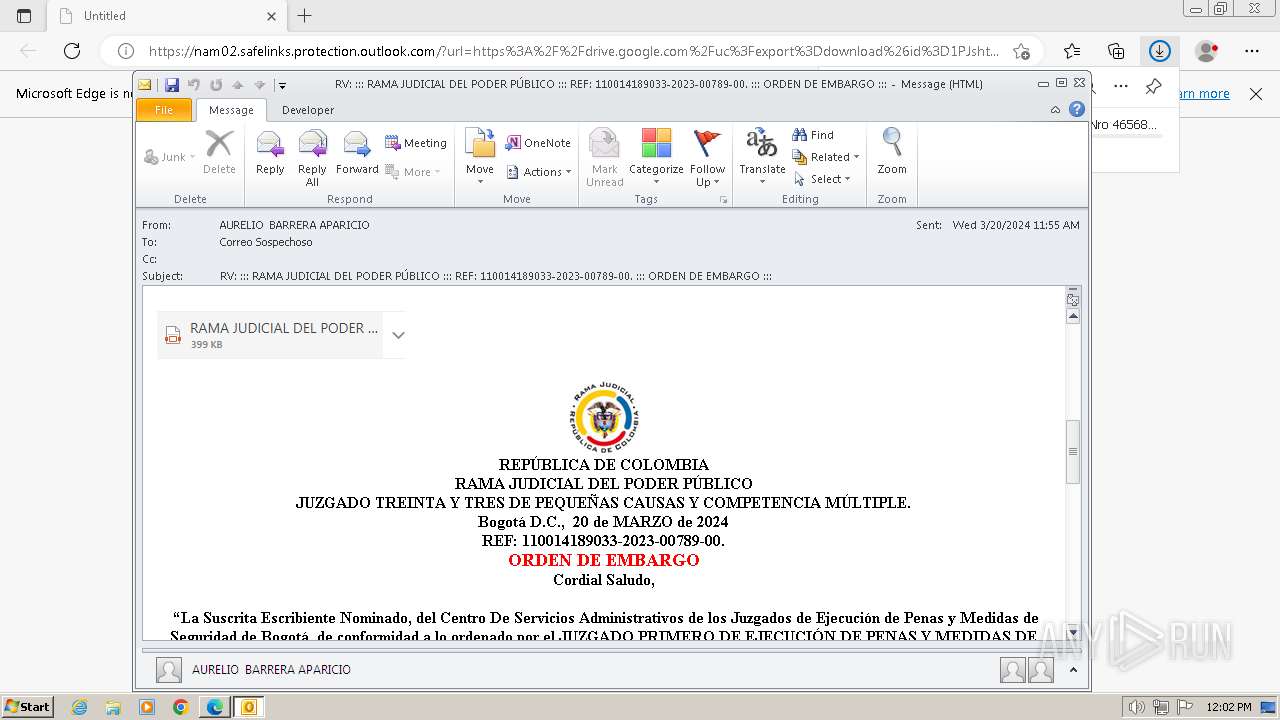
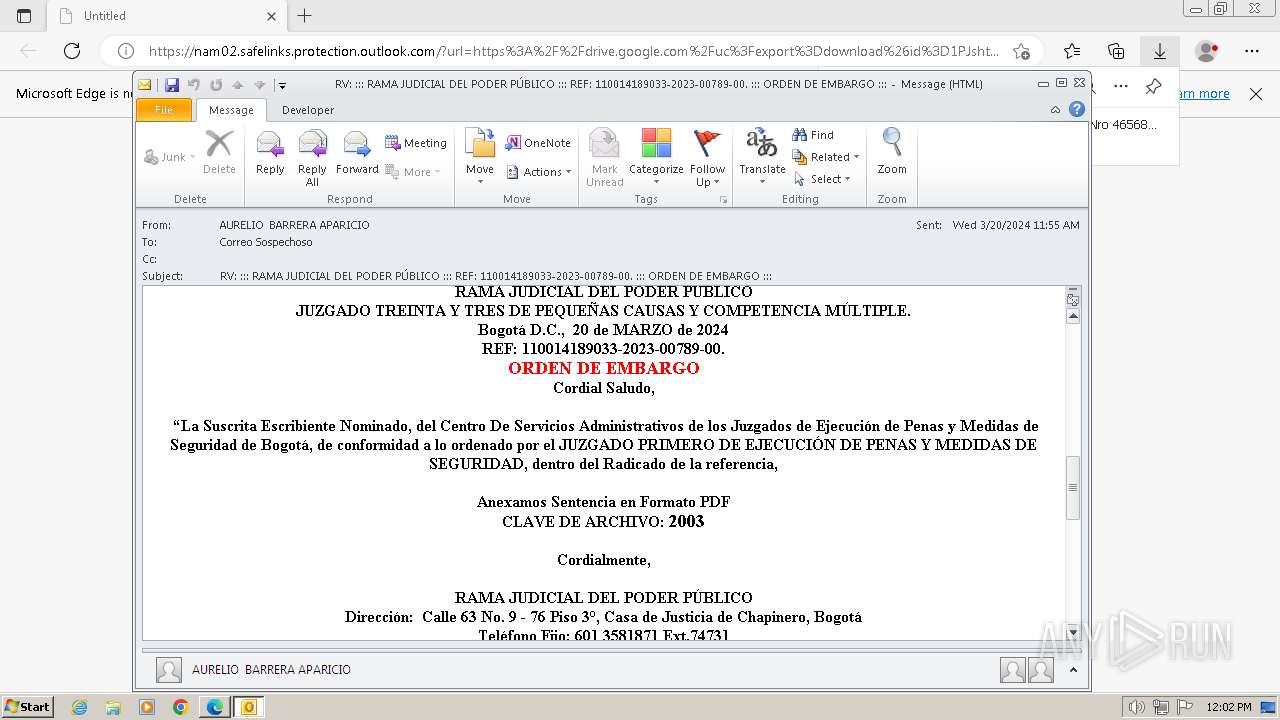
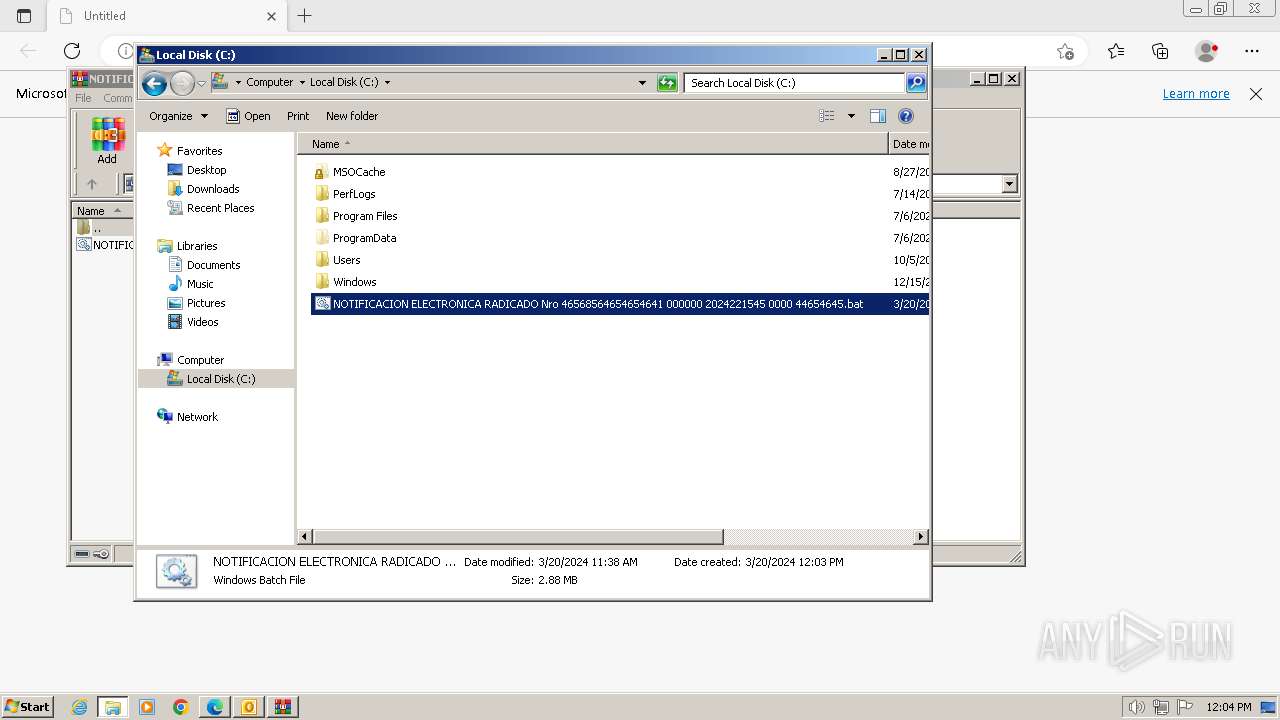
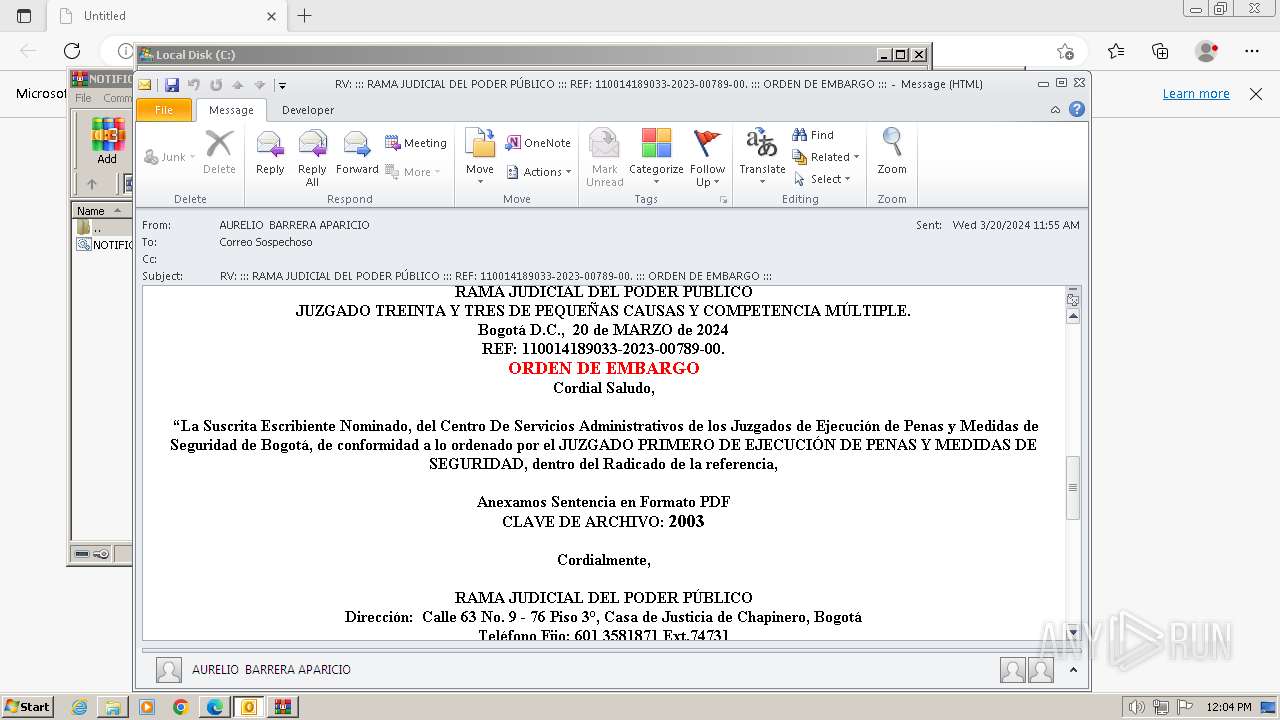
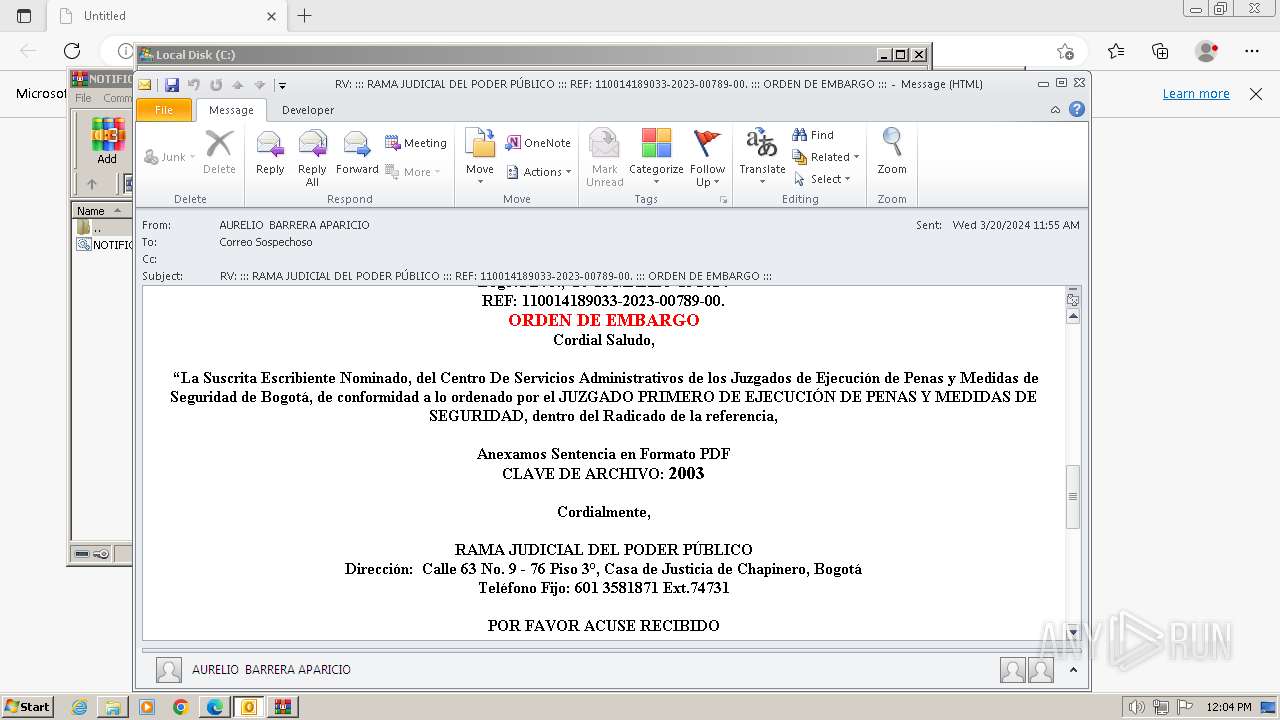
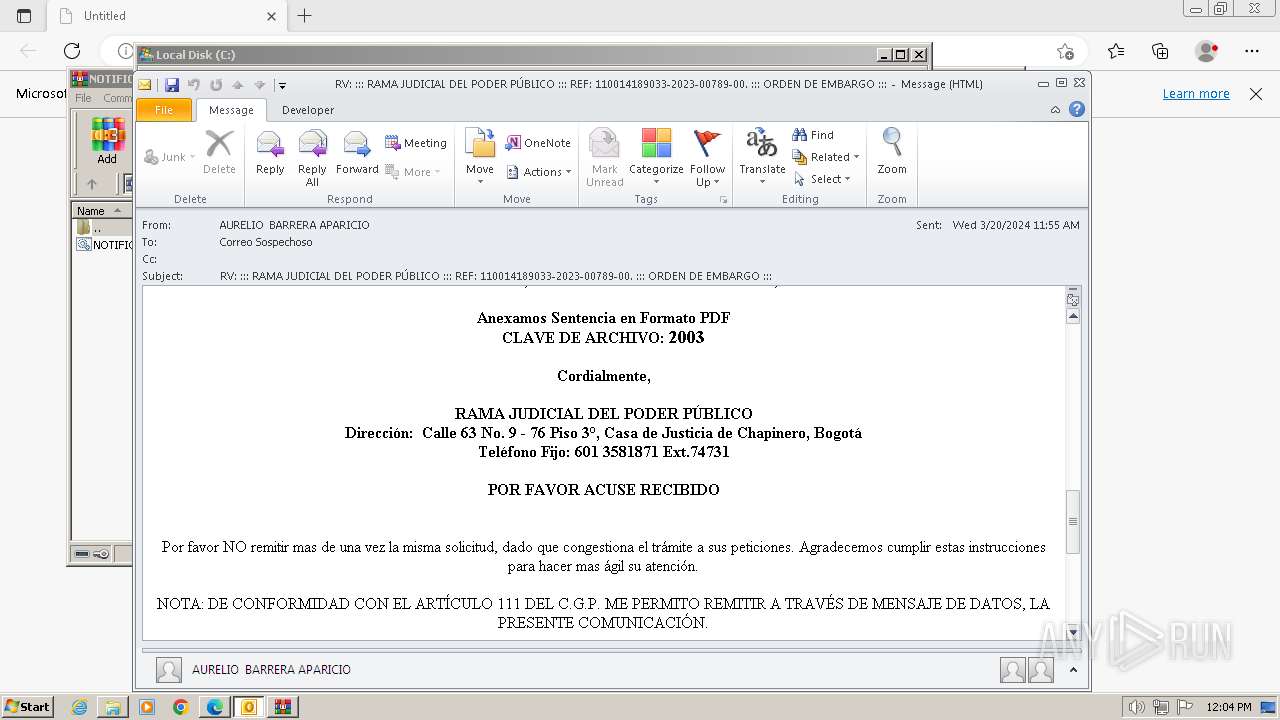
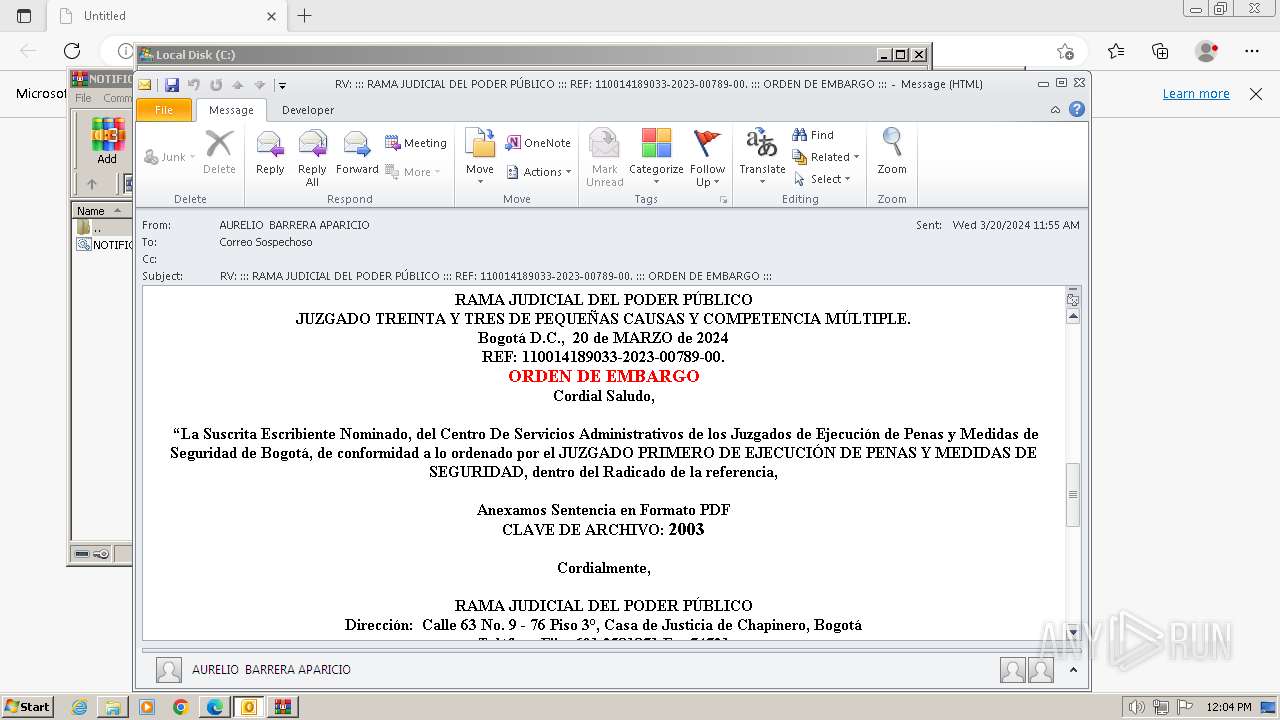
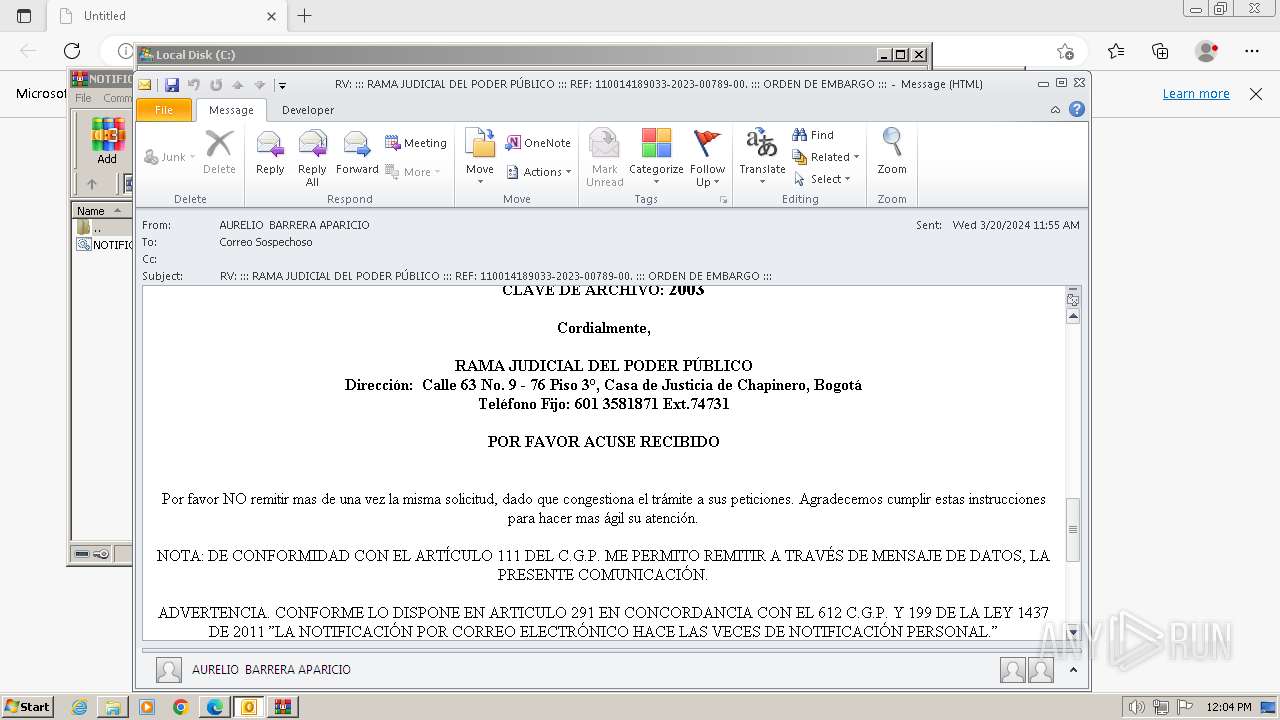
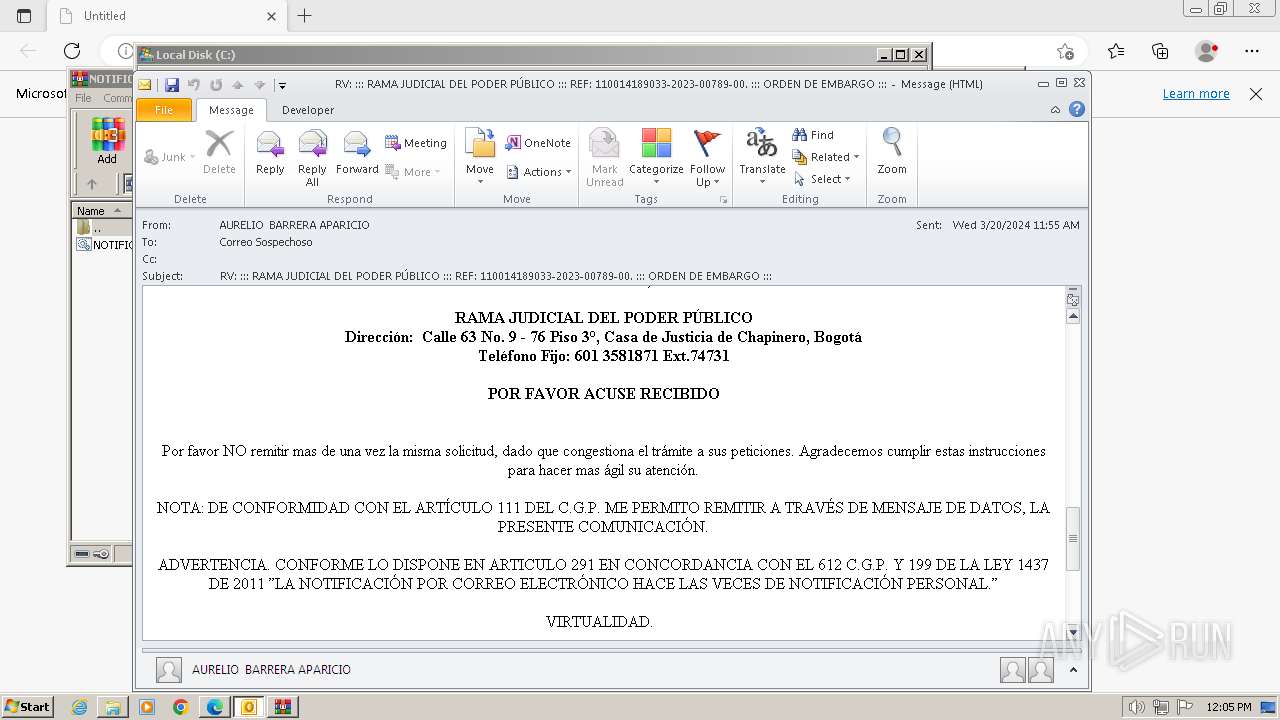
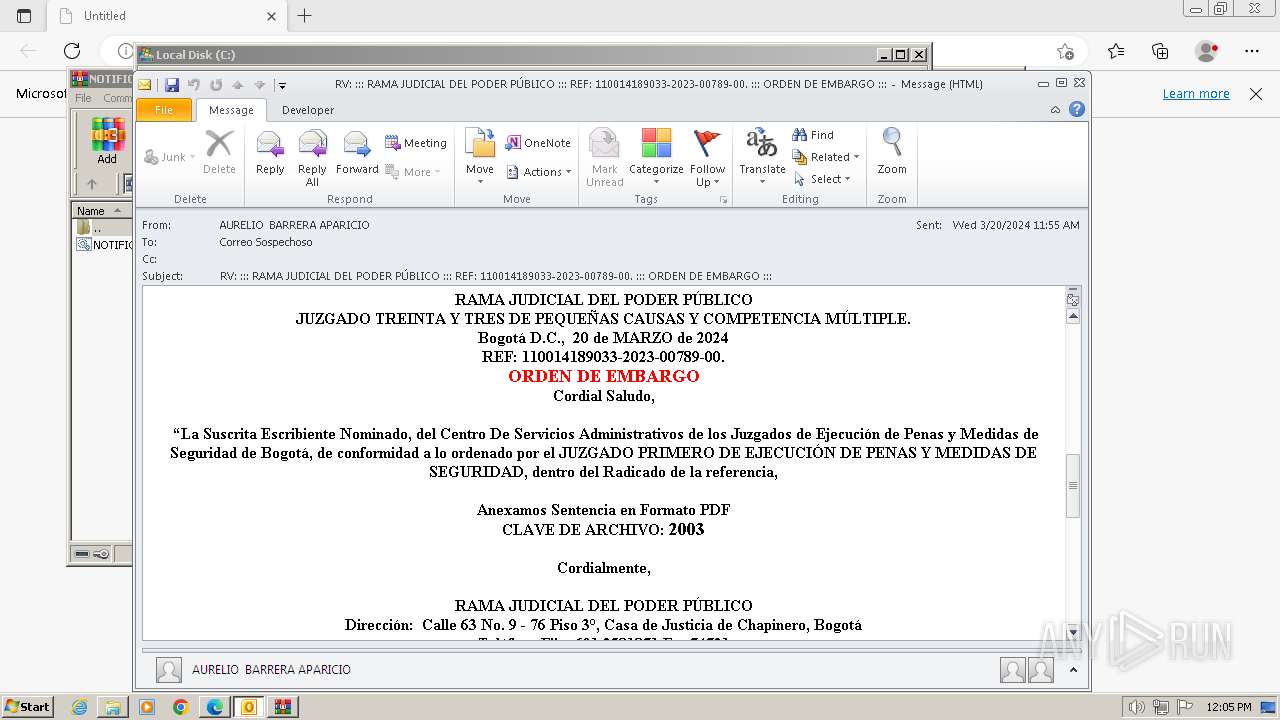
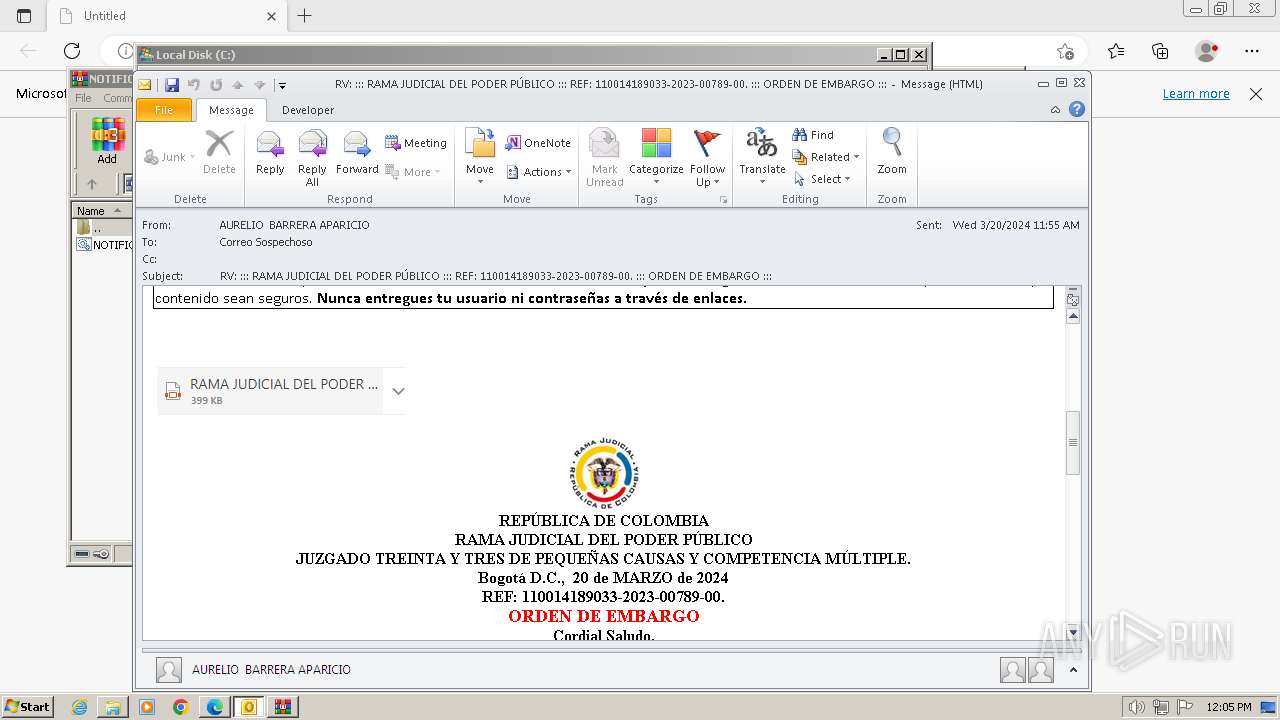
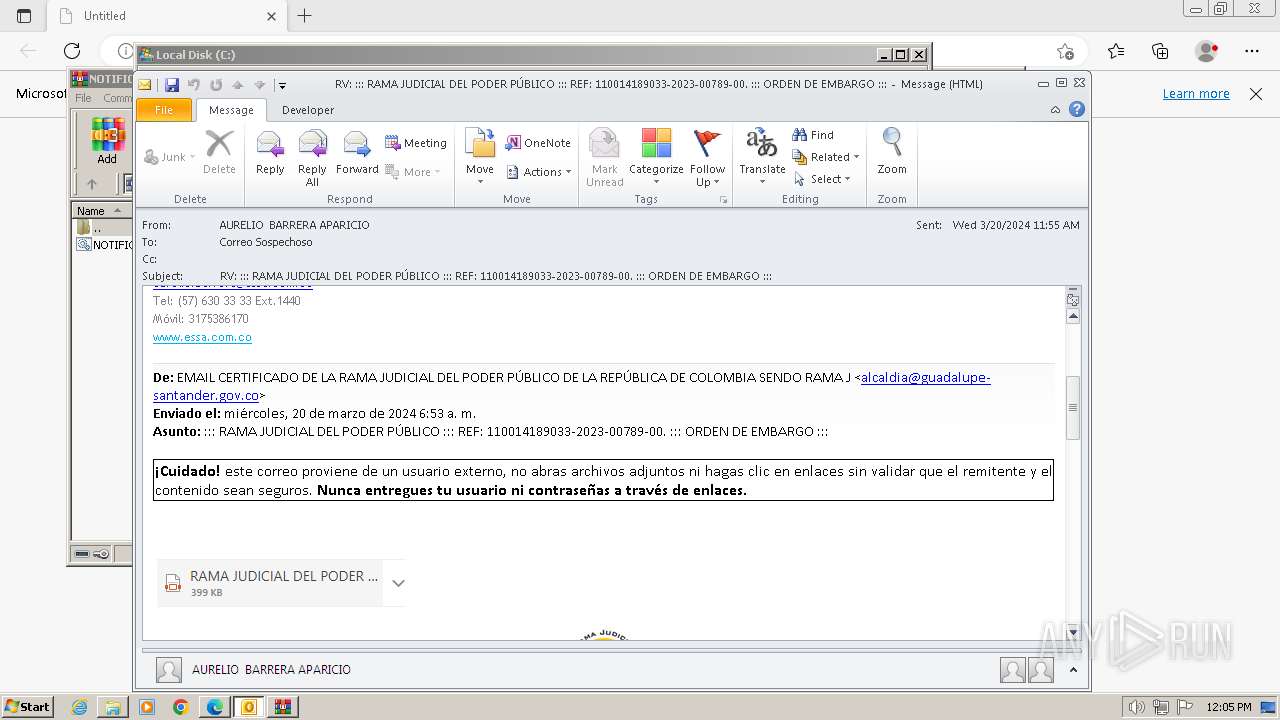
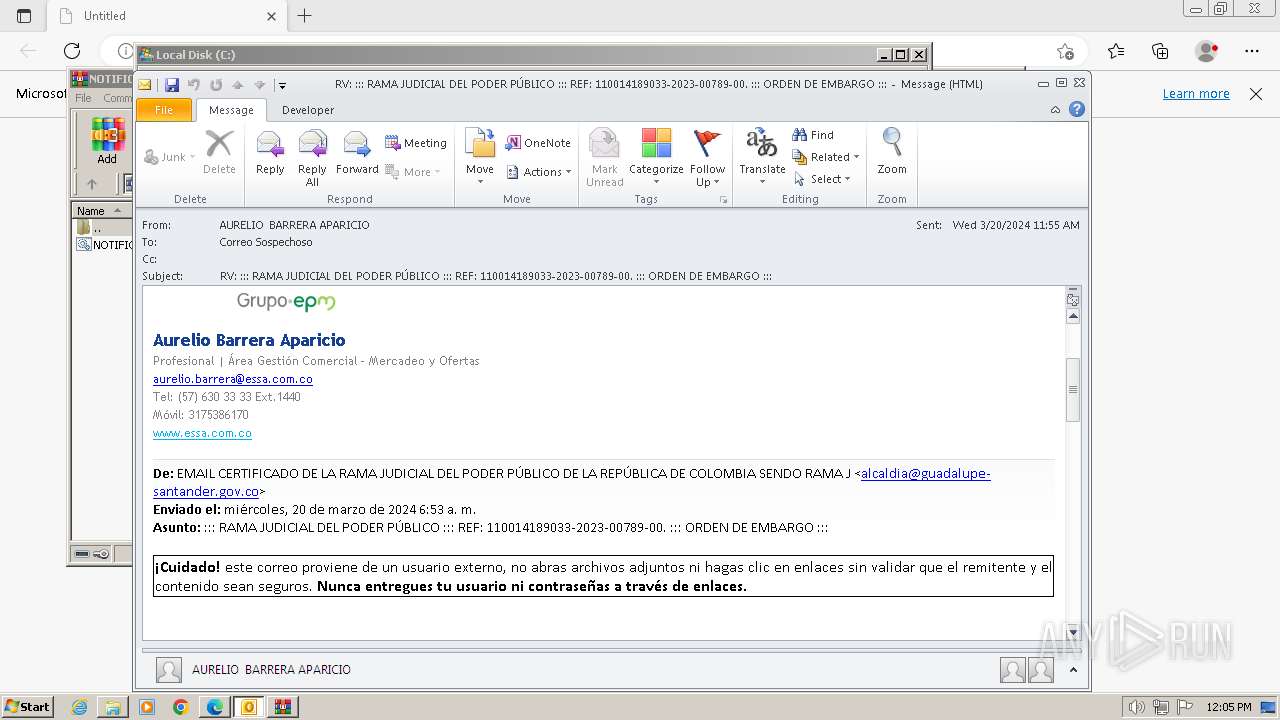
| File name: | RV RAMA JUDICIAL DEL PODER PÚBLICO REF 110014189033-2023-00789-00. ORDEN DE EMBARGO .msg |
| Full analysis: | https://app.any.run/tasks/ef720404-442c-48aa-abcd-4cf33fdbe071 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 20, 2024, 12:01:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 7778506D5FAD4339B72306CE528E2C27 |
| SHA1: | A90393072BA60FB89AACB302D32A8A14139D8C87 |
| SHA256: | 084C5FE44D99C786AEBCB6B9466FA385FA39B6762C67BFBE8B947775A191A771 |
| SSDEEP: | 1536:NcwckLj7++vrEs3lTJvQdccW2WHWwWgYvedcqWlWWZK829NlS7PdsELl1K:Ncu7++vrEMTJ4dJGdAw59ypLl1 |
MALICIOUS
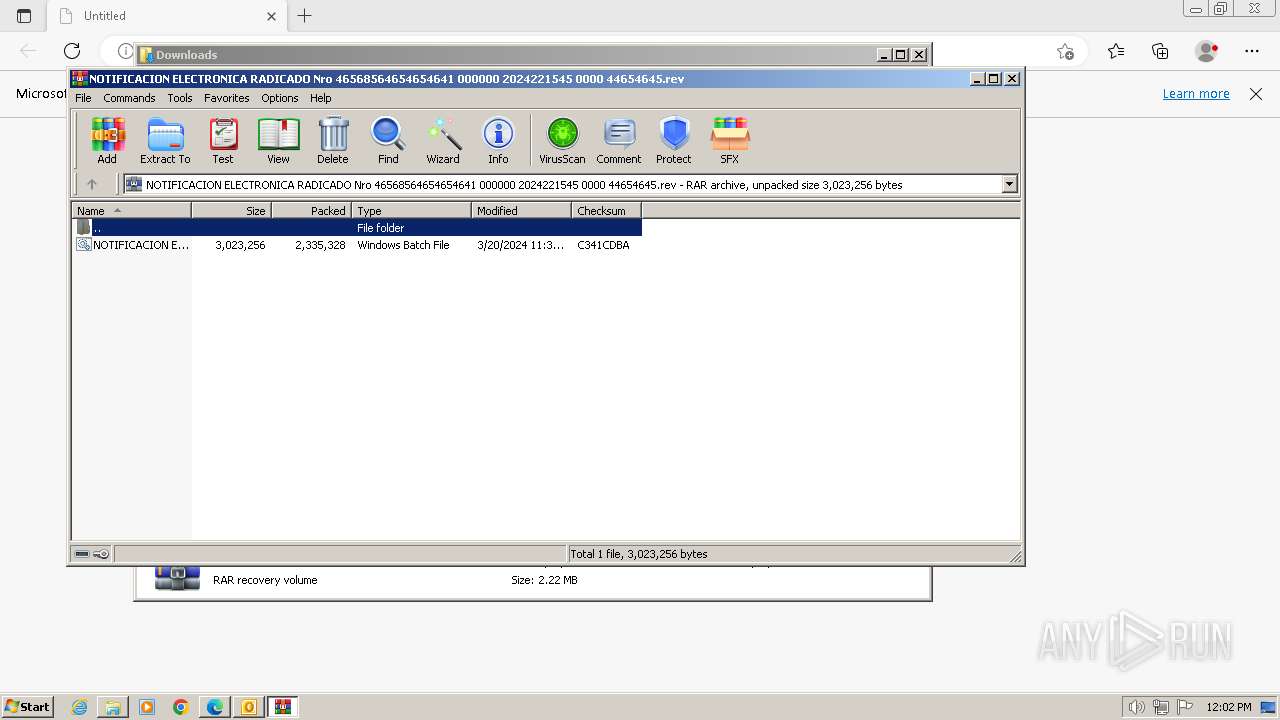
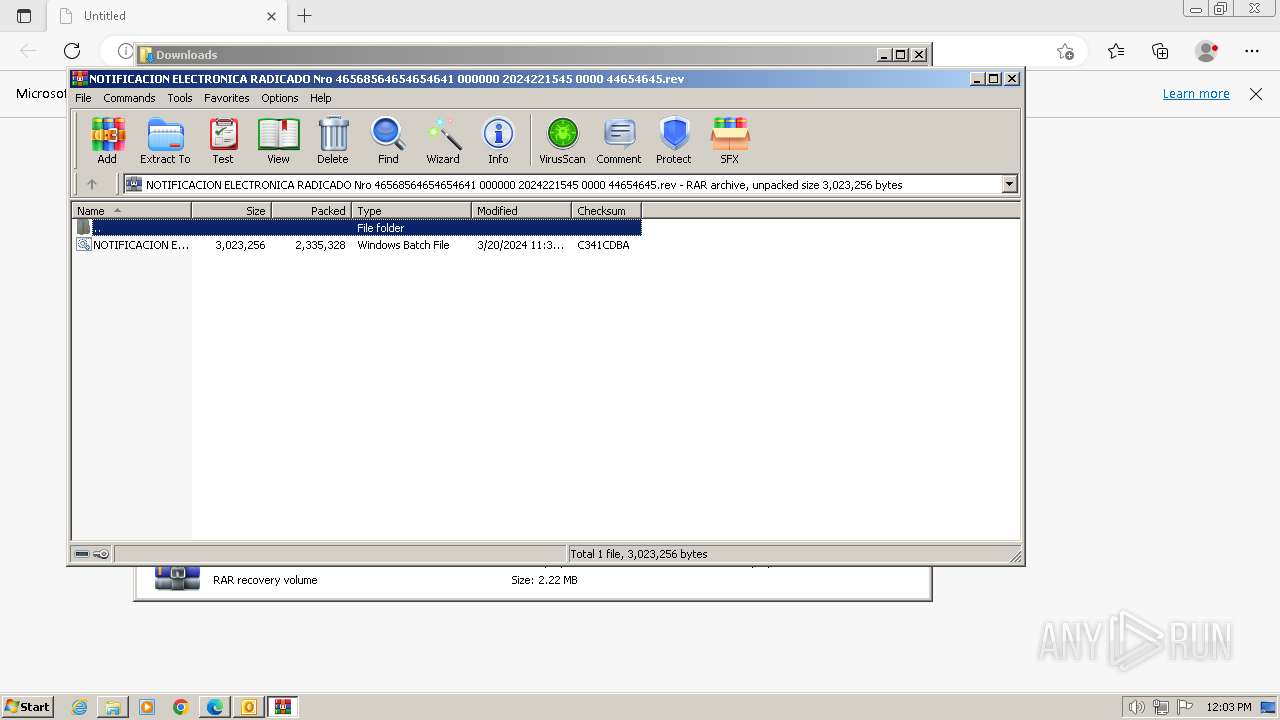
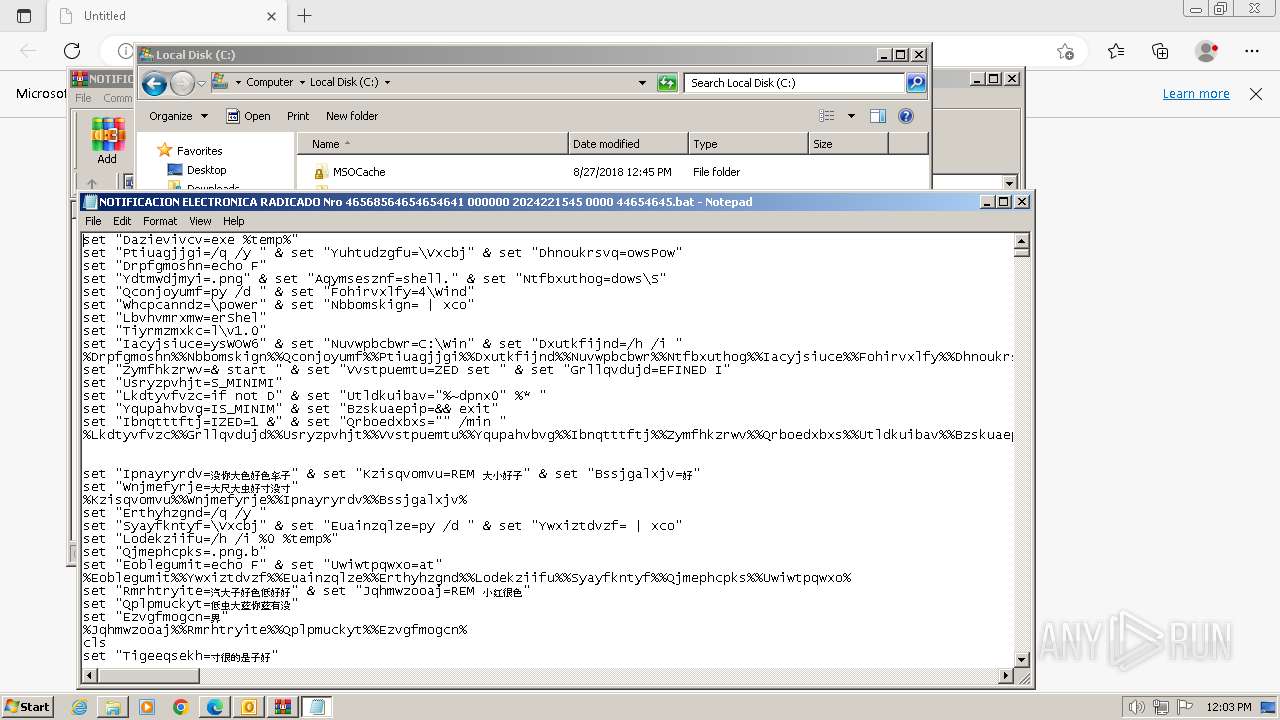
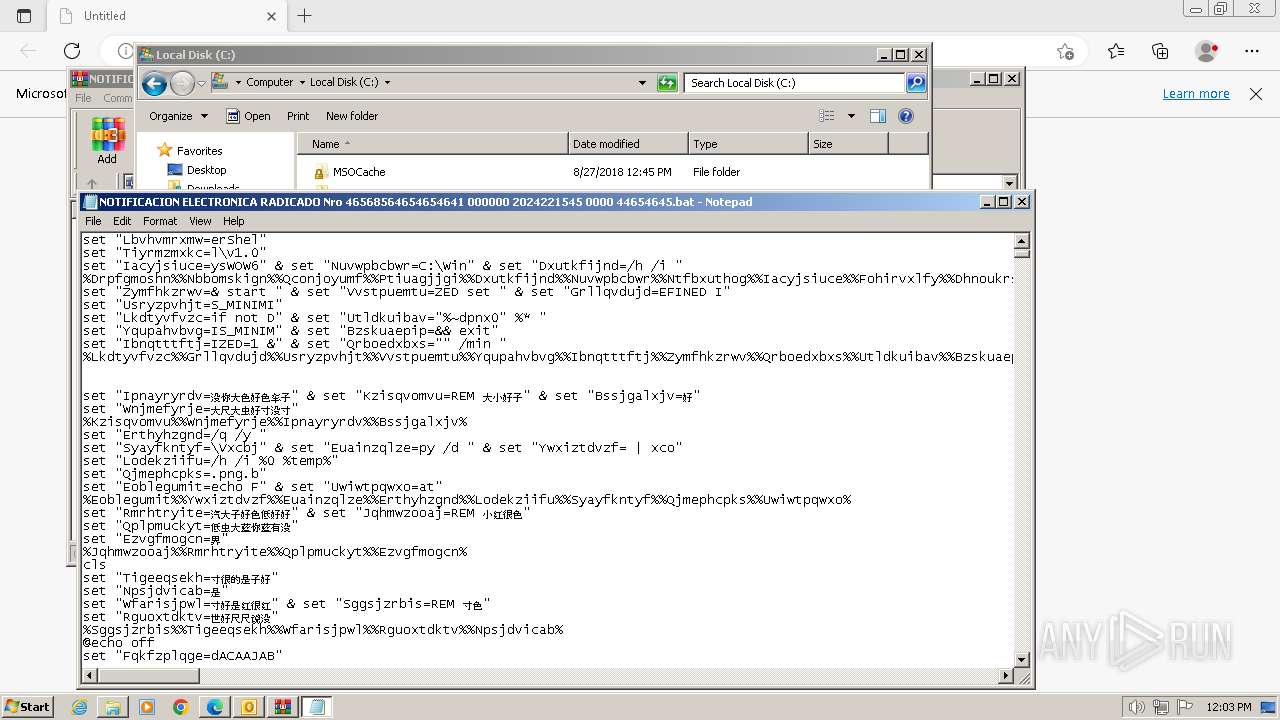
Xcopy is used to copy an executable file into an image
- xcopy.exe (PID: 3244)
- xcopy.exe (PID: 1172)
- xcopy.exe (PID: 1220)
- xcopy.exe (PID: 1432)
Starts PowerShell from an unusual location
- cmd.exe (PID: 2556)
- cmd.exe (PID: 2228)
Changes the autorun value in the registry
- Vxcbj.png (PID: 2652)
ASYNCRAT has been detected (MUTEX)
- RegAsm.exe (PID: 1592)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 1592)
ASYNCRAT has been detected (YARA)
- RegAsm.exe (PID: 1592)
SUSPICIOUS
Non-standard symbols in registry
- OUTLOOK.EXE (PID: 1692)
Blank space has been found in the path
- OUTLOOK.EXE (PID: 1692)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3832)
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
Application launched itself
- WinRAR.exe (PID: 3832)
- cmd.exe (PID: 2548)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 3644)
- cmd.exe (PID: 2228)
Process copies executable file
- cmd.exe (PID: 2548)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 3644)
- cmd.exe (PID: 2228)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2548)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 3644)
- cmd.exe (PID: 2228)
- Vxcbj.png (PID: 3136)
- cmd.exe (PID: 3568)
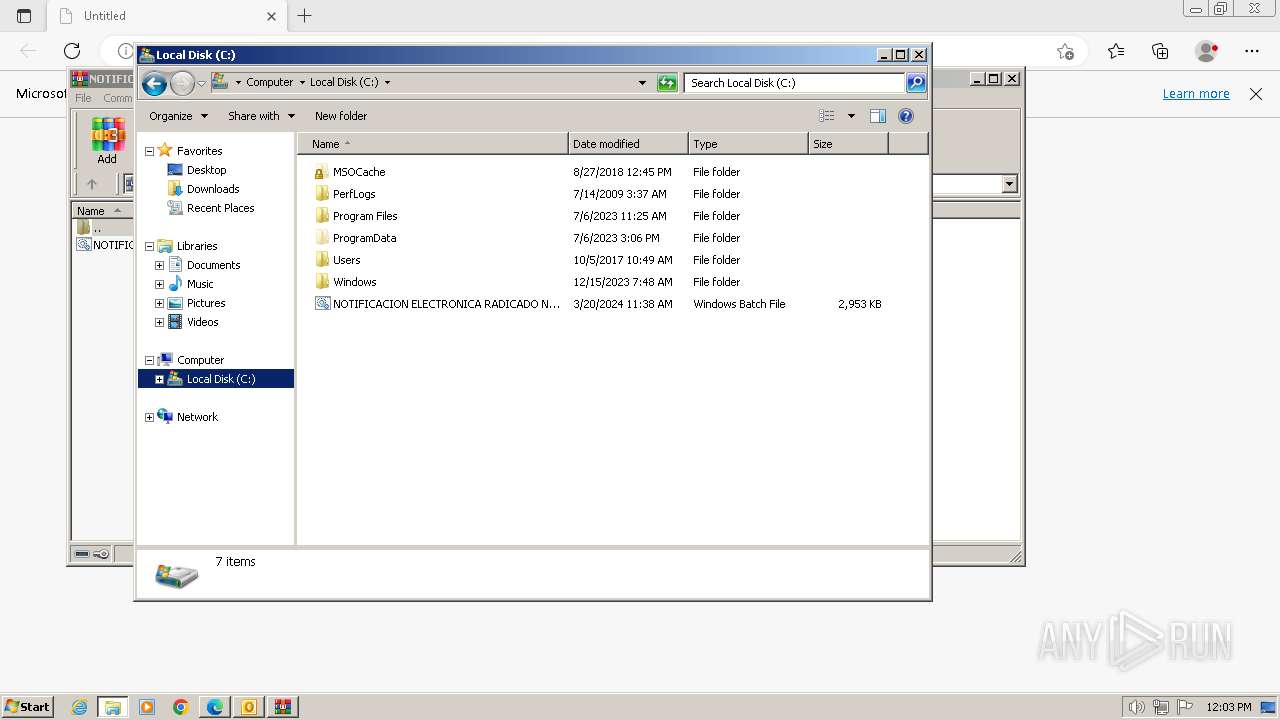
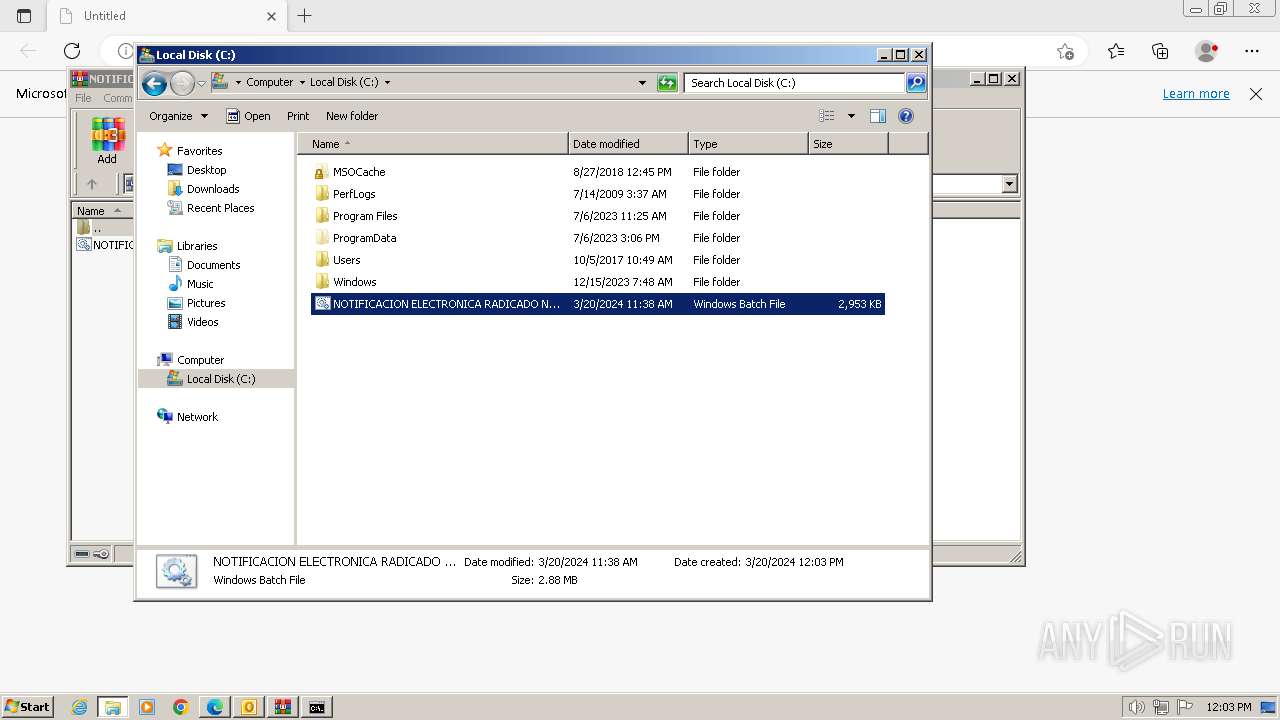
Process drops legitimate windows executable
- xcopy.exe (PID: 3244)
Executable content was dropped or overwritten
- xcopy.exe (PID: 3244)
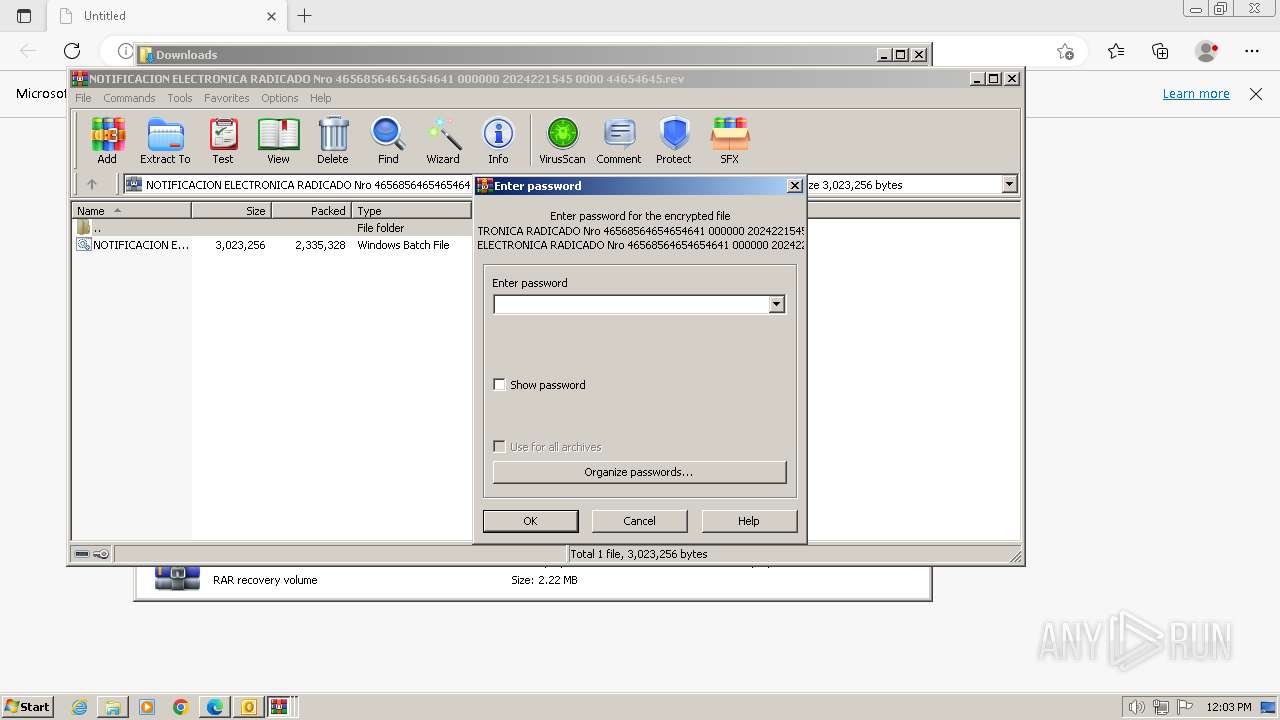
Executing commands from a ".bat" file
- cmd.exe (PID: 2548)
- cmd.exe (PID: 3644)
- Vxcbj.png (PID: 3136)
- cmd.exe (PID: 3568)
Starts a Microsoft application from unusual location
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
Starts application with an unusual extension
- cmd.exe (PID: 2556)
- cmd.exe (PID: 2228)
The executable file from the user directory is run by the CMD process
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
Checks Windows Trust Settings
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
Reads the Internet Settings
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
- RegAsm.exe (PID: 1592)
- powershell.exe (PID: 2984)
Starts POWERSHELL.EXE for commands execution
- Vxcbj.png (PID: 2652)
Base64-obfuscated command line is found
- Vxcbj.png (PID: 2652)
Starts itself from another location
- Vxcbj.png (PID: 2652)
BASE64 encoded PowerShell command has been detected
- Vxcbj.png (PID: 2652)
Connects to unusual port
- RegAsm.exe (PID: 1592)
Reads settings of System Certificates
- RegAsm.exe (PID: 1592)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2984)
INFO
Application launched itself
- msedge.exe (PID: 2832)
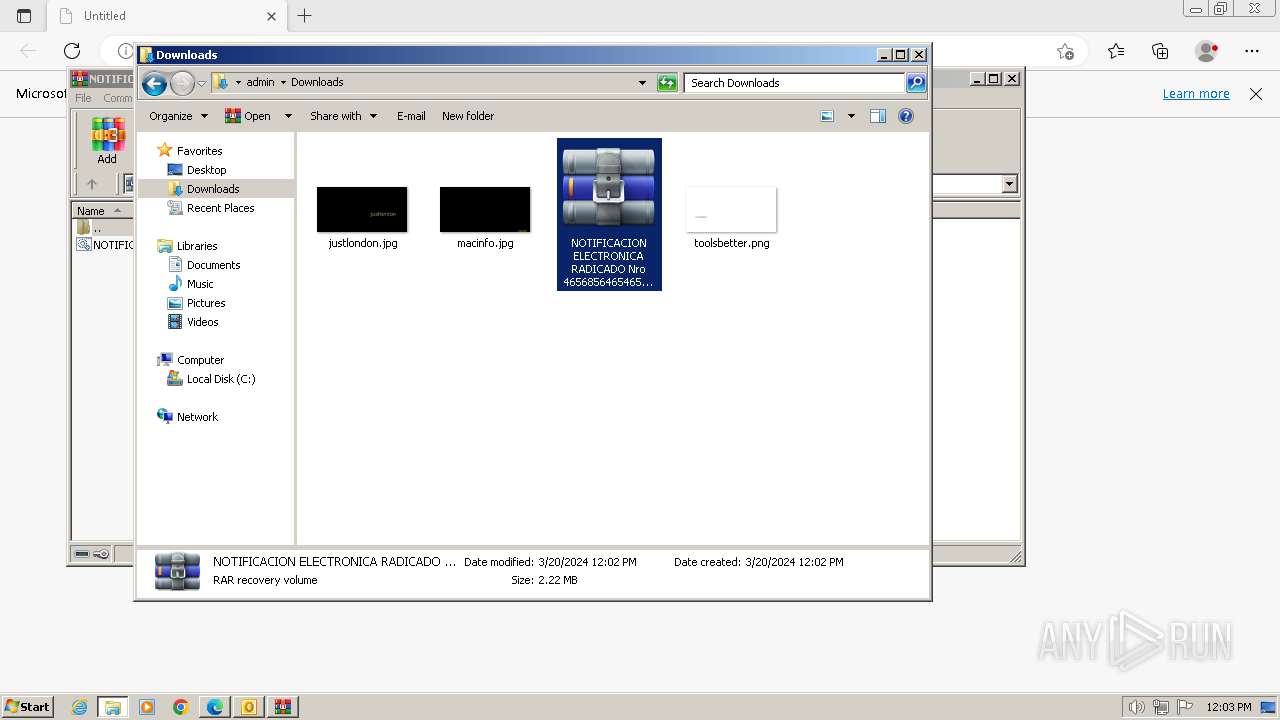
The process uses the downloaded file
- msedge.exe (PID: 532)
- WinRAR.exe (PID: 3824)
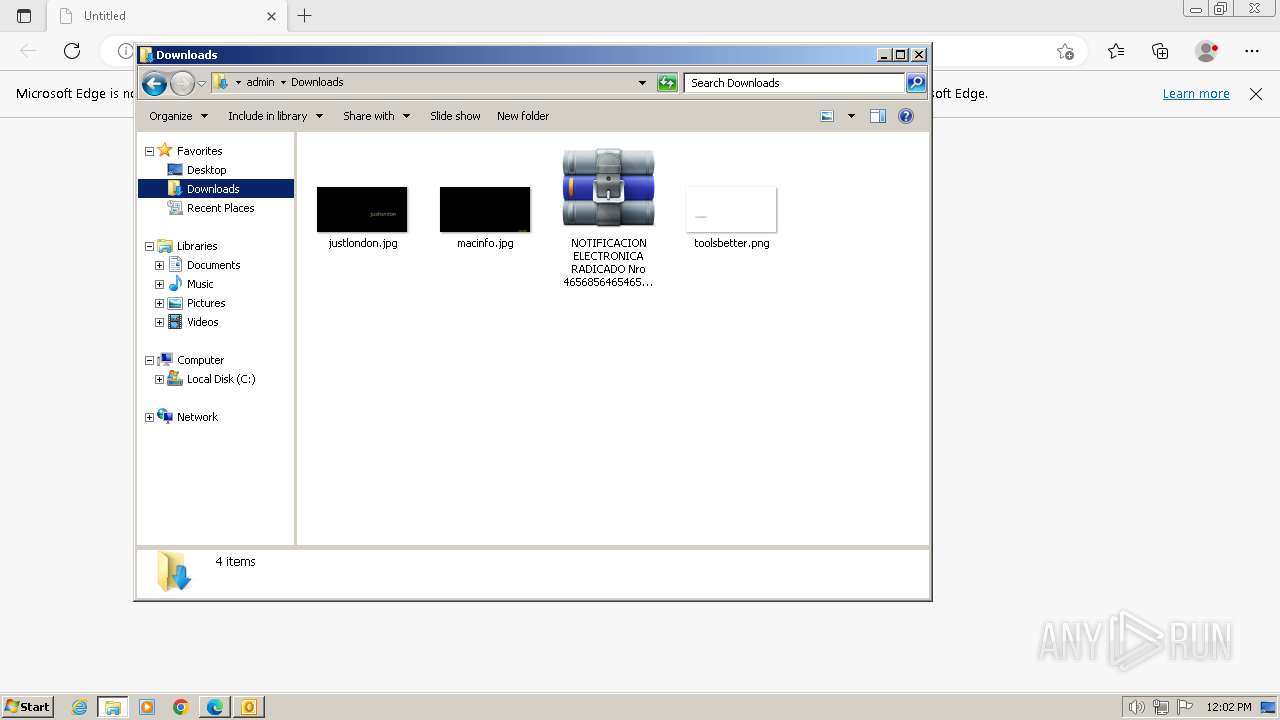
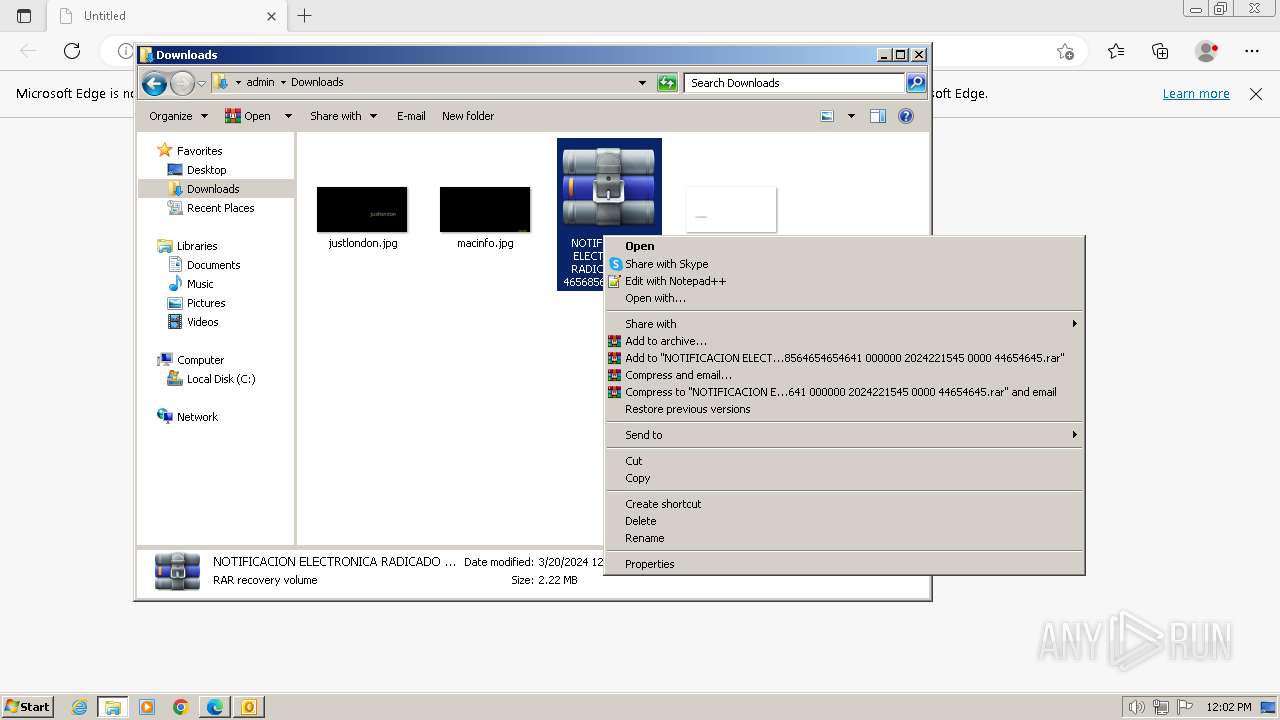
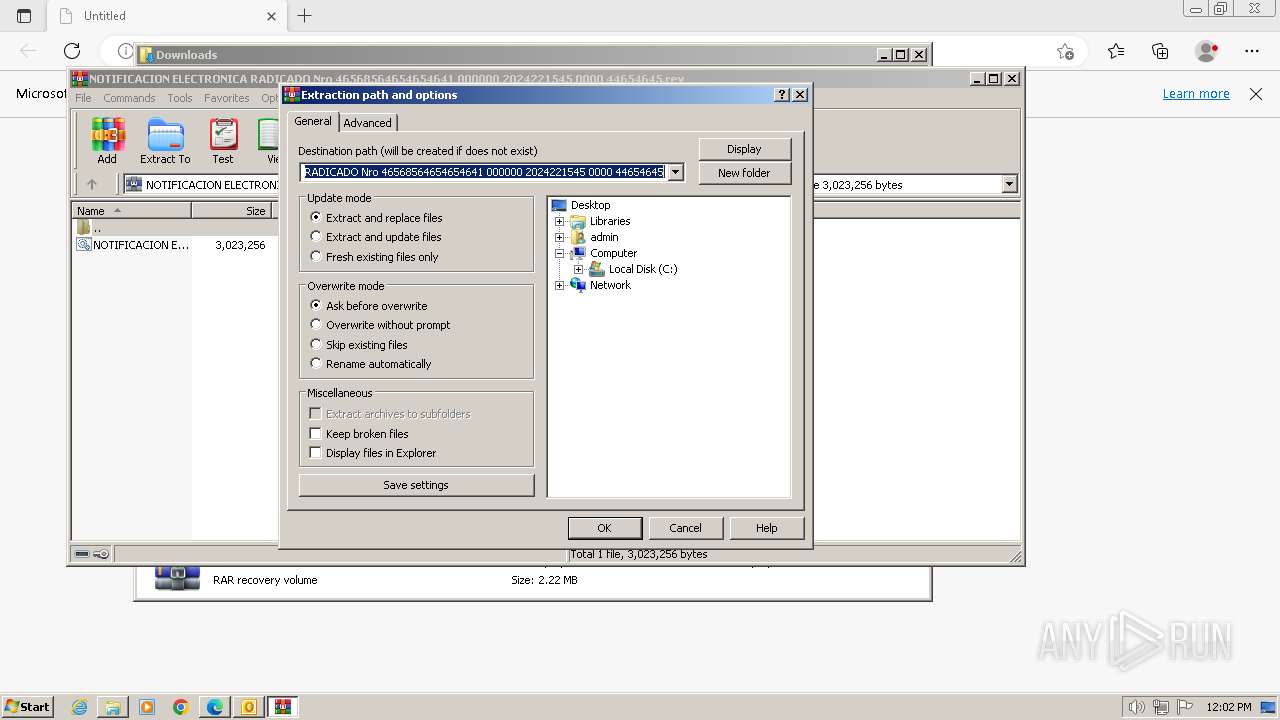
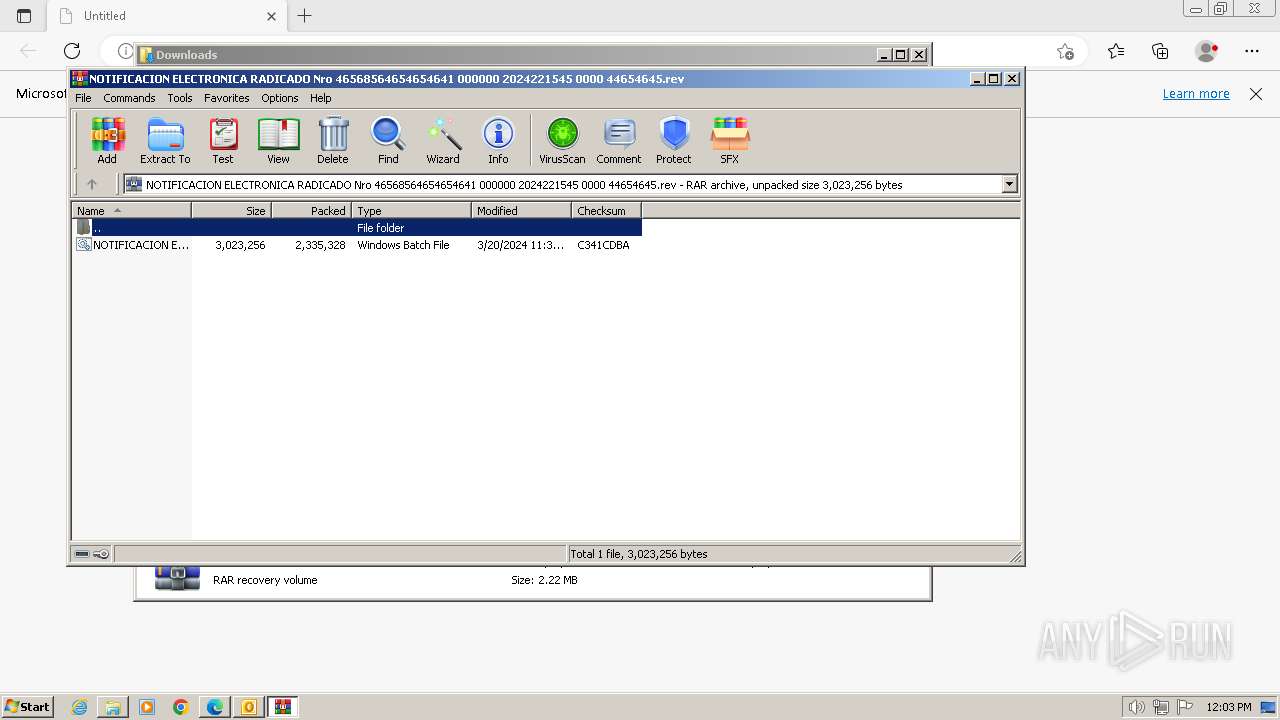
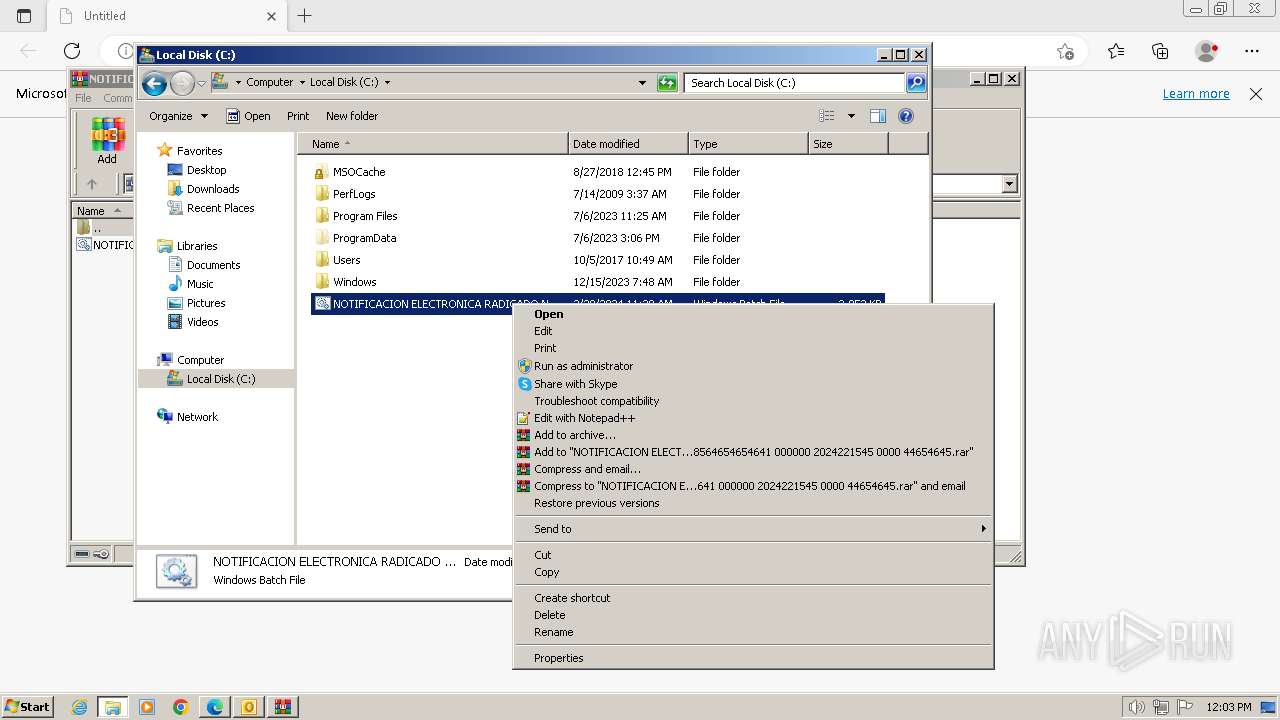
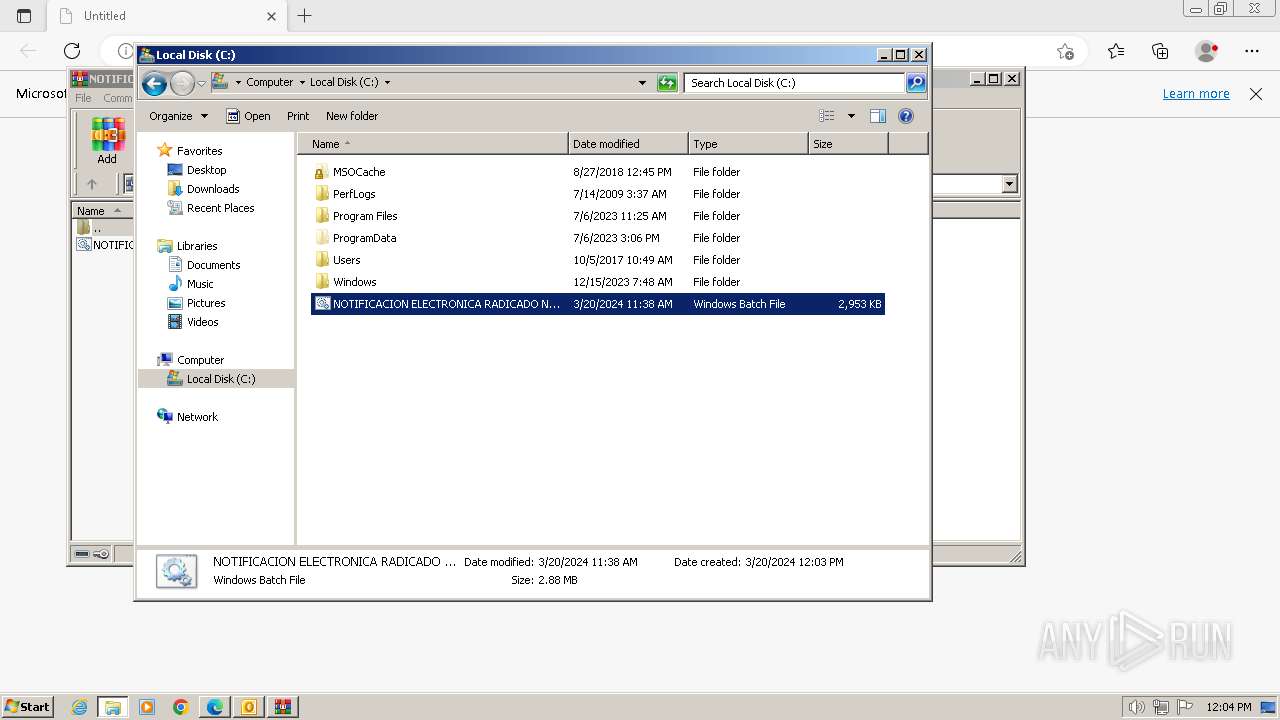
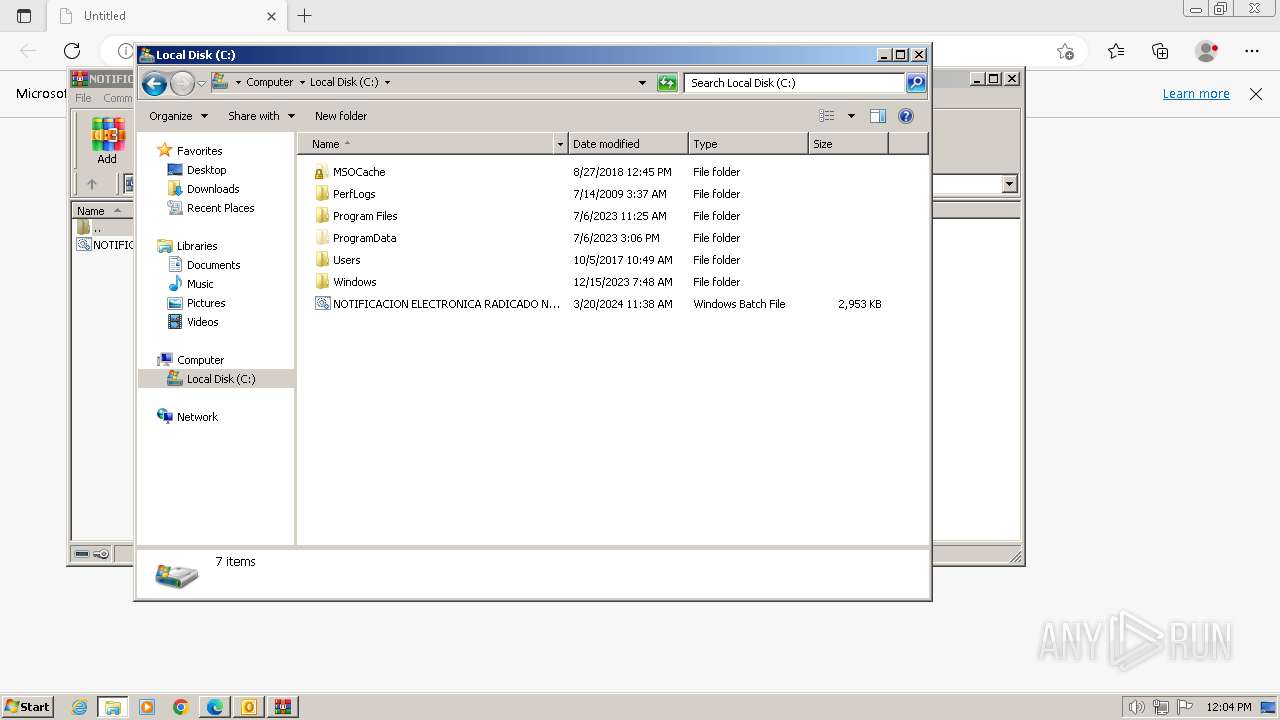
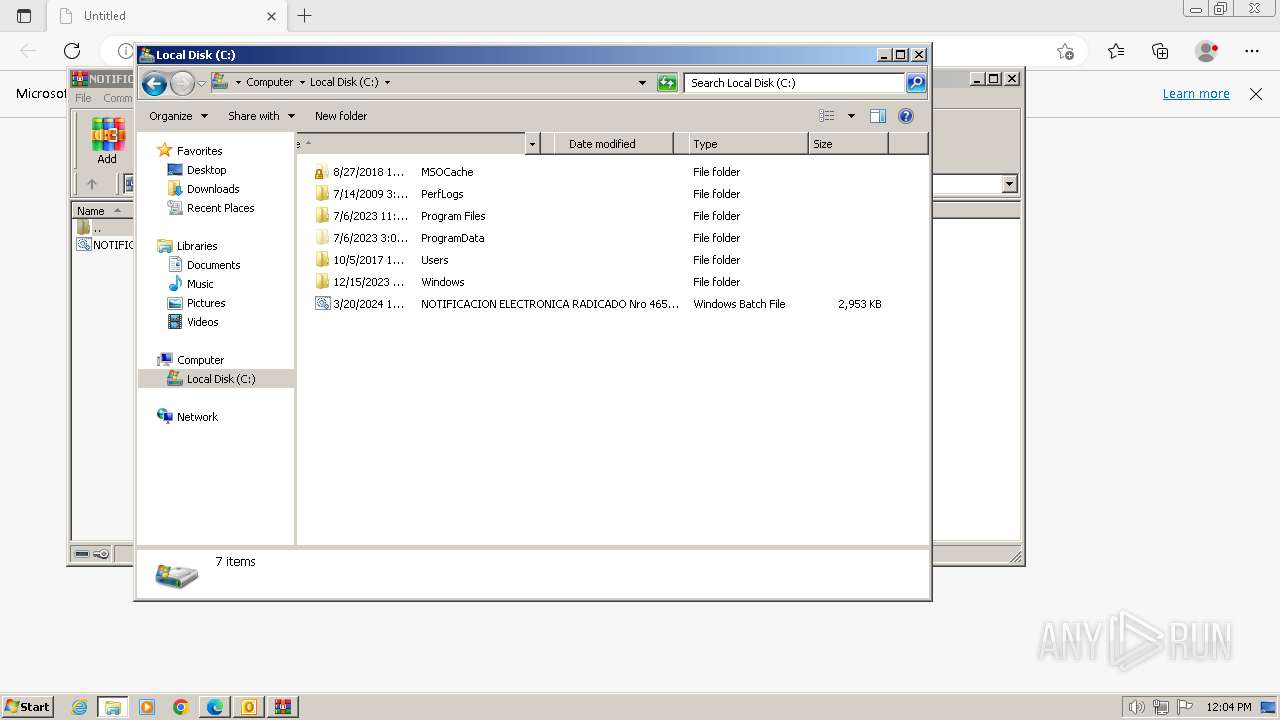
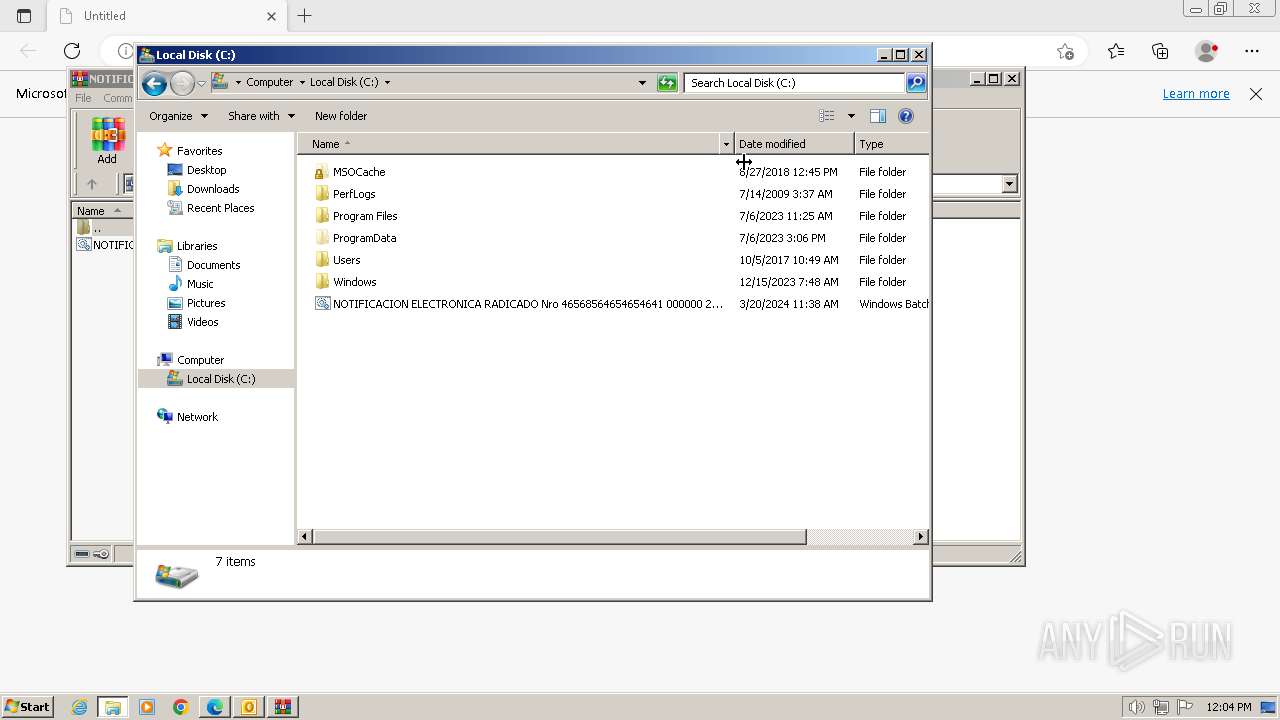
Manual execution by a user
- explorer.exe (PID: 3416)
- WinRAR.exe (PID: 3832)
- cmd.exe (PID: 2548)
- notepad.exe (PID: 668)
Create files in a temporary directory
- xcopy.exe (PID: 3244)
- xcopy.exe (PID: 1316)
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
- RegAsm.exe (PID: 1592)
Drops the executable file immediately after the start
- xcopy.exe (PID: 3244)
Reads the machine GUID from the registry
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
- RegAsm.exe (PID: 1592)
Checks supported languages
- Vxcbj.png (PID: 3136)
- RegAsm.exe (PID: 1592)
- Vxcbj.png (PID: 2652)
Process checks Powershell version
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
Reads the computer name
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
- RegAsm.exe (PID: 1592)
Reads the bytes from the current stream and writes them to another stream(SCRIPT)
- Vxcbj.png (PID: 3136)
- Vxcbj.png (PID: 2652)
Creates files or folders in the user directory
- Vxcbj.png (PID: 2652)
Reads the software policy settings
- RegAsm.exe (PID: 1592)
Reads Environment values
- RegAsm.exe (PID: 1592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1592) RegAsm.exe
C2 (1)winscapmarzo.duckdns.org
Ports (1)9003
BotnetDefault
Version| CRACKED BY https://t.me/xworm_v2
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAPeWQ4YJ3MvReCGwLzn7rTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwNDI1MDA0MTA5WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKT9nYYTjYTZhY+g1tekZ8/F29gsEIDgf/8odvCbCmYKGGZZi2yND9NjtBXEMANM9PAXCyMapGva...
Server_Signatureou9O1WSXv7F3RsyWMUBaYdtHkcoVEvonQIDDr8YDa9LcBI7DH5q8GWBKt+389C7EbU1HkUlRr66vlfzwnGhZABsDBGJQbBUkt3p1hXec4ZBh9566orWlfMr5IzQvGQ7sZz+Fv+FrGiuM+XpZyBDHzkwSqDdcZya/iqEmflgi9/UdTZv4XXOa3iS8EECpFXAu+wUzME8KaUx/b8d+4CjHcZxPCUZZzq8hBW5E7fs2xTT9BTEwMLaQyHlCeXB1Ur9K992NacmpmqYoUiN+yx9J/McjbLPAR09C0iuQnOZdD540...
Keys
AES2b210725104d9f6abe8cf2f28b3496c2e98970e33c6d8ec2d47b015dd7a75a5b
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
100
Monitored processes
45
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3312 --field-trial-handle=1384,i,6323513536780411366,17183763405947562397,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 668 | "C:\Windows\System32\NOTEPAD.EXE" C:\NOTIFICACION ELECTRONICA RADICADO Nro 46568564654654641 000000 2024221545 0000 44654645.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3644 --field-trial-handle=1384,i,6323513536780411366,17183763405947562397,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1616 --field-trial-handle=1384,i,6323513536780411366,17183763405947562397,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1172 | xcopy /d /q /y /h /i C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe C:\Users\admin\AppData\Local\Temp\Vxcbj.png | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1196 | C:\Windows\system32\cmd.exe /S /D /c" echo F " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1220 | xcopy /d /q /y /h /i C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe C:\Users\admin\AppData\Local\Temp\Vxcbj.png | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1316 | xcopy /d /q /y /h /i "C:\NOTIFICACION ELECTRONICA RADICADO Nro 46568564654654641 000000 2024221545 0000 44654645.bat" C:\Users\admin\AppData\Local\Temp\Vxcbj.png.bat | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | xcopy /d /q /y /h /i C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe C:\Users\admin\AppData\Local\Temp\Vxcbj.png | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=1408 --field-trial-handle=1384,i,6323513536780411366,17183763405947562397,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
36 294
Read events
35 218
Write events
1 030
Delete events
46
Modification events
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
2
Suspicious files
33
Text files
65
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR35A1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1692 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF186e26.TMP | — | |
MD5:— | SHA256:— | |||
| 2832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF186e84.TMP | — | |
MD5:— | SHA256:— | |||
| 2832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A90D7AF.dat | image | |
MD5:B14AEECD20DA949F18053876570BB136 | SHA256:96E4C9222E7EE9BE743D18128D10B5C166A821C5400D2700C79FF510DE6A317D | |||
| 2832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF186ee2.TMP | — | |
MD5:— | SHA256:— | |||
| 2832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4F61ADE4.dat | image | |
MD5:5E8AE14485F4DE256676A45C7C03DEE8 | SHA256:1773A049E0148C6C6AED518164163CB39C4DC64948D00E56F836E0B59F73AEA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
23
DNS requests
30
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1692 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | unknown | — | — | unknown |
1592 | RegAsm.exe | GET | 200 | 173.222.108.147:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9cf722093823c04d | unknown | compressed | 67.5 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
1692 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1772 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2832 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
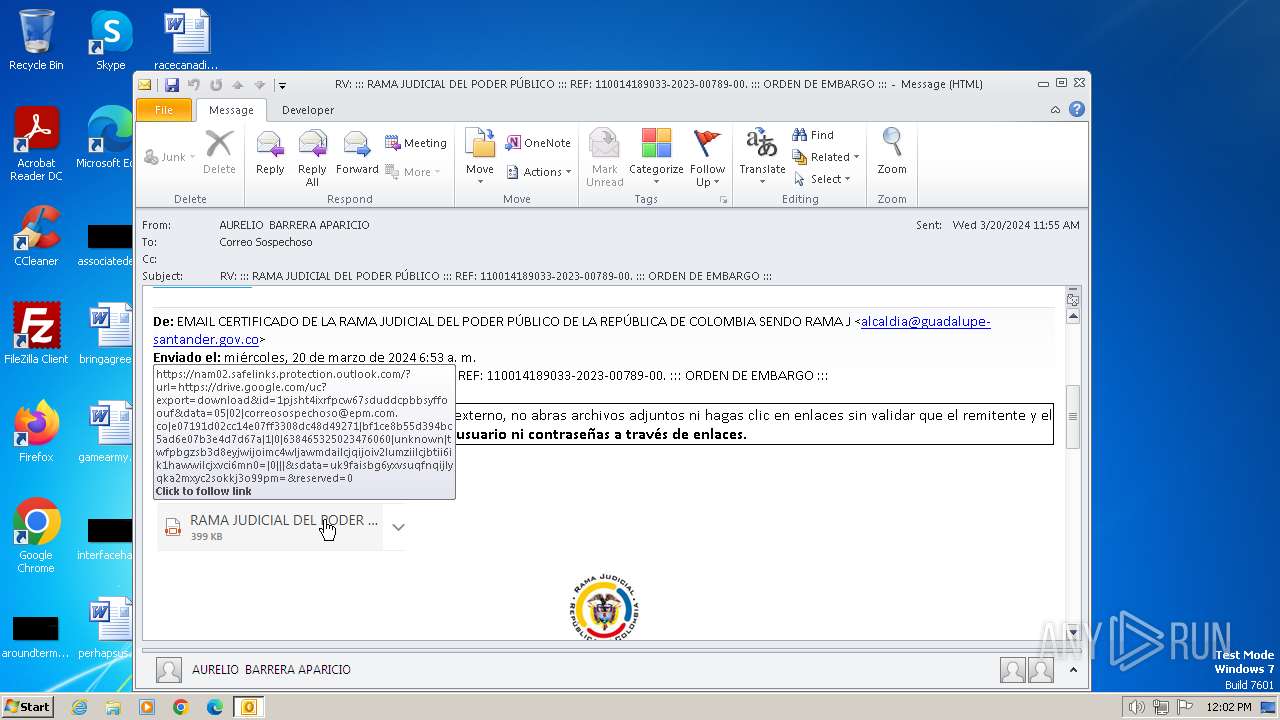
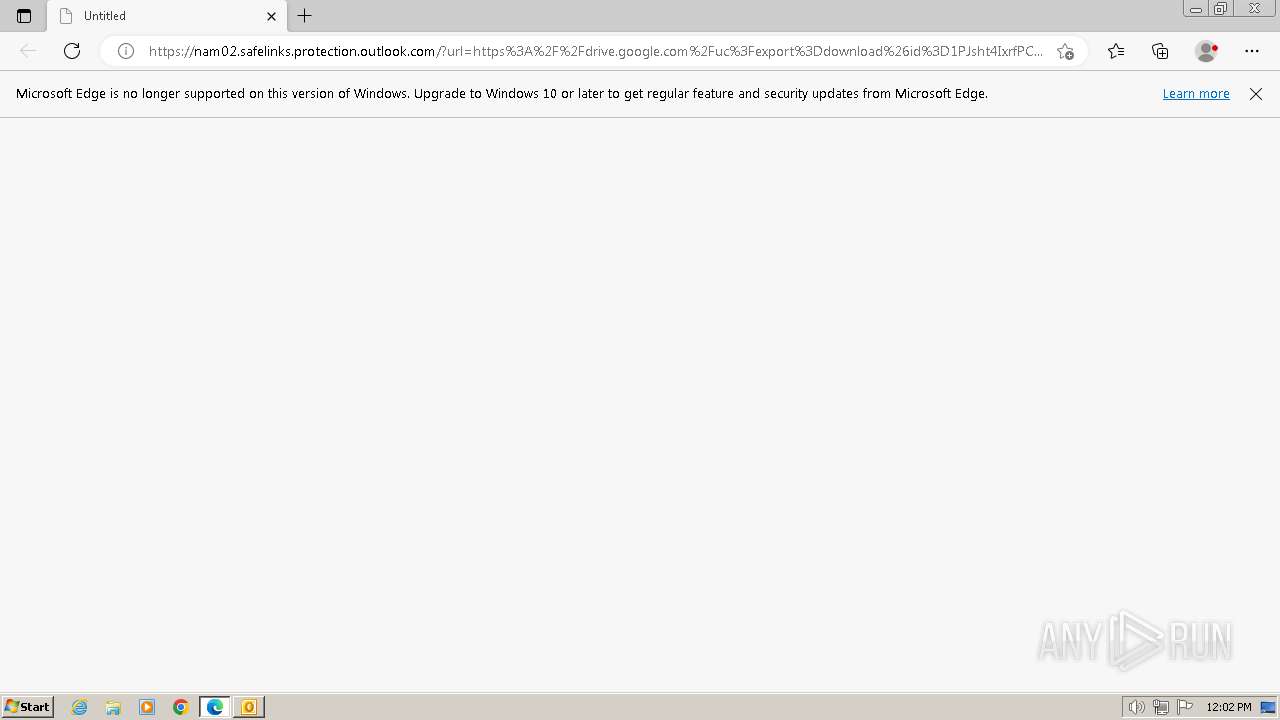
1772 | msedge.exe | 104.47.57.28:443 | nam02.safelinks.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1772 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1772 | msedge.exe | 142.250.185.174:443 | drive.google.com | GOOGLE | US | whitelisted |
1772 | msedge.exe | 216.58.212.129:443 | drive.usercontent.google.com | GOOGLE | US | whitelisted |
1772 | msedge.exe | 104.110.240.114:443 | www.bing.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
nam02.safelinks.protection.outlook.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
drive.google.com |
| shared |
drive.usercontent.google.com |
| unknown |
www.bing.com |
| whitelisted |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
winscapmarzo.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
— | — | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
— | — | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
— | — | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |