| File name: | Built.exe |
| Full analysis: | https://app.any.run/tasks/8dc276ce-a2b6-4d24-a9d0-fdb58b4381d7 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
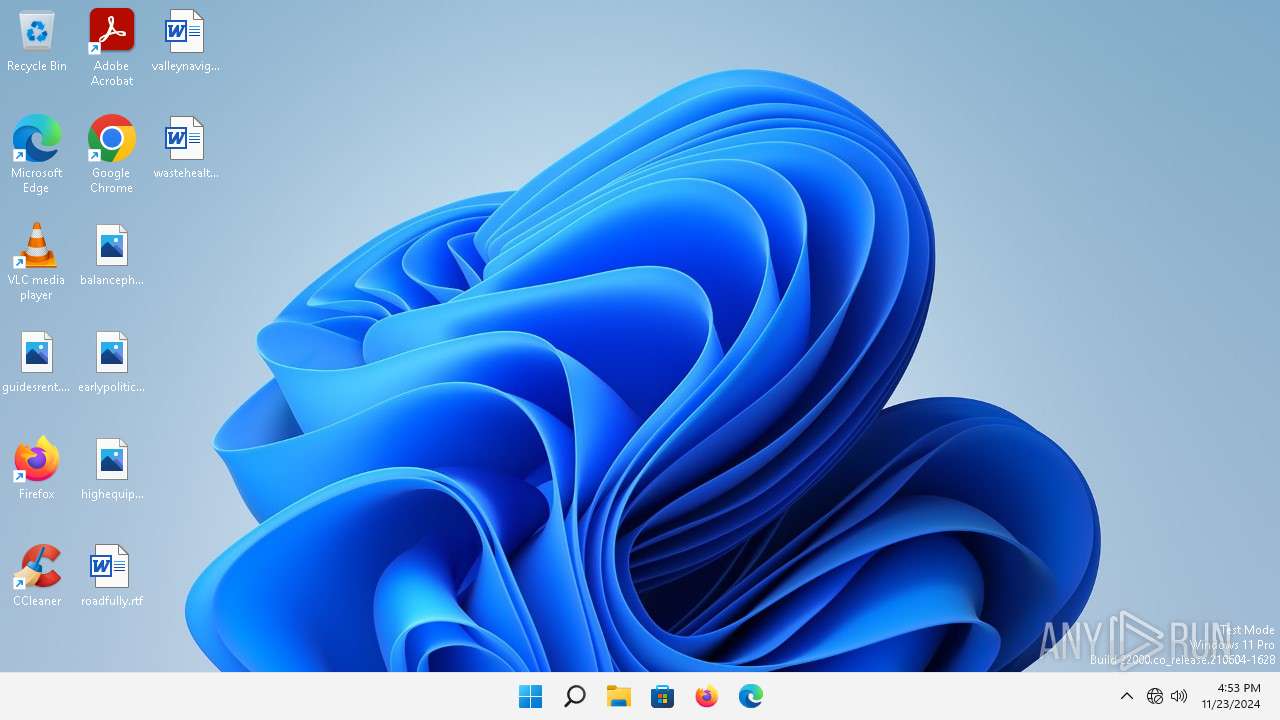
| Analysis date: | November 23, 2024, 16:53:38 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 5E69CE68A987A33EF4881CB9066F7FD4 |
| SHA1: | D9D109226241D26A13459F544AA020306A955353 |
| SHA256: | 082F4601E02C2518396DC3B1F7BF30739ABC221EB268F3F4FEB449303F720024 |
| SSDEEP: | 98304:fJ3NSBZYrYH4ES4/NCz0kKaKMDBttHfktEzafhOsE+XZ0m6GHgBuHh7FgfAfqqQI:WhrJ44a+yuvVcHa |
MALICIOUS
Executing a file with an untrusted certificate
- Built.exe (PID: 3368)
- Built.exe (PID: 3324)
BlankGrabber has been detected
- Built.exe (PID: 3368)
SUSPICIOUS
Process drops legitimate windows executable
- Built.exe (PID: 3368)
Executable content was dropped or overwritten
- Built.exe (PID: 3368)
Process drops python dynamic module
- Built.exe (PID: 3368)
Starts a Microsoft application from unusual location
- Built.exe (PID: 3368)
- Built.exe (PID: 3324)
- Built.exe (PID: 6200)
Application launched itself
- Built.exe (PID: 3368)
- Built.exe (PID: 3324)
The process drops C-runtime libraries
- Built.exe (PID: 3368)
Reads security settings of Internet Explorer
- Built.exe (PID: 3324)
Reads the Internet Settings
- Built.exe (PID: 3324)
Reads the date of Windows installation
- Built.exe (PID: 3324)
INFO
Checks supported languages
- Built.exe (PID: 3368)
- Built.exe (PID: 3324)
Reads the computer name
- Built.exe (PID: 3368)
- Built.exe (PID: 3324)
Create files in a temporary directory
- Built.exe (PID: 3324)
- Built.exe (PID: 3368)
The process uses the downloaded file
- Built.exe (PID: 3324)
PyInstaller has been detected (YARA)
- Built.exe (PID: 6200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:23 16:37:54+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 172032 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.0.19041.1 |
| ProductVersionNumber: | 10.0.19041.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Add Hardware Wizard |
| FileVersion: | 10.0.19041.1 (WinBuild.160101.0800) |
| InternalName: | HdwWiz.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | HdwWiz.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.19041.1 |
Total processes
206
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3324 | "C:\Users\admin\Desktop\Built.exe" | C:\Users\admin\Desktop\Built.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Add Hardware Wizard Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3368 | "C:\Users\admin\Desktop\Built.exe" | C:\Users\admin\Desktop\Built.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Add Hardware Wizard Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6200 | "C:\Users\admin\Desktop\Built.exe" C:\Users\admin\Desktop\Built.exe | C:\Users\admin\Desktop\Built.exe | Built.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Add Hardware Wizard Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8084 | C:\Windows\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.22000.795_none_047def894cac2b60\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.22000.795_none_047def894cac2b60\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.22000.795 (WinBuild.160101.0800) | |||||||||||||||
Total events
405
Read events
397
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3324) Built.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3324) Built.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3324) Built.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3324) Built.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
57
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\_queue.pyd | executable | |
MD5:97CC5797405F90B20927E29867BC3C4F | SHA256:FB304CA68B41E573713ABB012196EF1AE2D5B5E659D846BBF46B1F13946C2A39 | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\_lzma.pyd | executable | |
MD5:17082C94B383BCA187EB13487425EC2C | SHA256:DDBFEF8DA4A0D8C1C8C24D171DE65B9F4069E2EDB8F33EF5DFECF93CB2643BD4 | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\_sqlite3.pyd | executable | |
MD5:37A88A19BB1DE9CF33141872C2C534CB | SHA256:CCA0FBE5268AB181BF8AFBDC4AF258D0FBD819317A78DDD1F58BEF7D2F197350 | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:E8B9D74BFD1F6D1CC1D99B24F44DA796 | SHA256:B1B3FD40AB437A43C8DB4994CCFFC7F88000CC8BB6E34A2BCBFF8E2464930C59 | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:ACCC640D1B06FB8552FE02F823126FF5 | SHA256:332BA469AE84AA72EC8CCE2B33781DB1AB81A42ECE5863F7A3CB5A990059594F | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:EFAD0EE0136532E8E8402770A64C71F9 | SHA256:3D2C55902385381869DB850B526261DDEB4628B83E690A32B67D2E0936B2C6ED | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\_ssl.pyd | executable | |
MD5:34402EFC9A34B91768CF1280CC846C77 | SHA256:FE52C34028C5D62430EA7A9BE034557CCFECDDDDA9C57874F2832F584FEDB031 | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:CFE0C1DFDE224EA5FED9BD5FF778A6E0 | SHA256:0D0F80CBF476AF5B1C9FD3775E086ED0DFDB510CD0CC208EC1CCB04572396E3E | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\_socket.pyd | executable | |
MD5:F52C1C015FB147729A7CAAB03B2F64F4 | SHA256:06D91AC02B00A29180F4520521DE2F7DE2593DD9C52E1C2B294E717C826A1B7D | |||
| 3368 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI33682\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:1C58526D681EFE507DEB8F1935C75487 | SHA256:EF13DCE8F71173315DFC64AB839B033AB19A968EE15230E9D4D2C9D558EFEEE2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
44
DNS requests
38
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.55.161.191:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
6368 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6368 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 172.217.18.99:443 | https://gstatic.com/generate_204 | unknown | — | — | unknown |
— | — | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
— | — | HEAD | 200 | 2.17.18.8:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
6368 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6368 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
— | — | GET | 304 | 23.50.131.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?10fa3c5e1542861e | unknown | — | — | whitelisted |
6368 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5272 | OfficeC2RClient.exe | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
6368 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
6368 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3420 | rundll32.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.55.161.191:80 | — | Akamai International B.V. | DE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.50.131.203:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
— | — | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
— | — | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
1656 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
— | — | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
— | — | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
— | — | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |