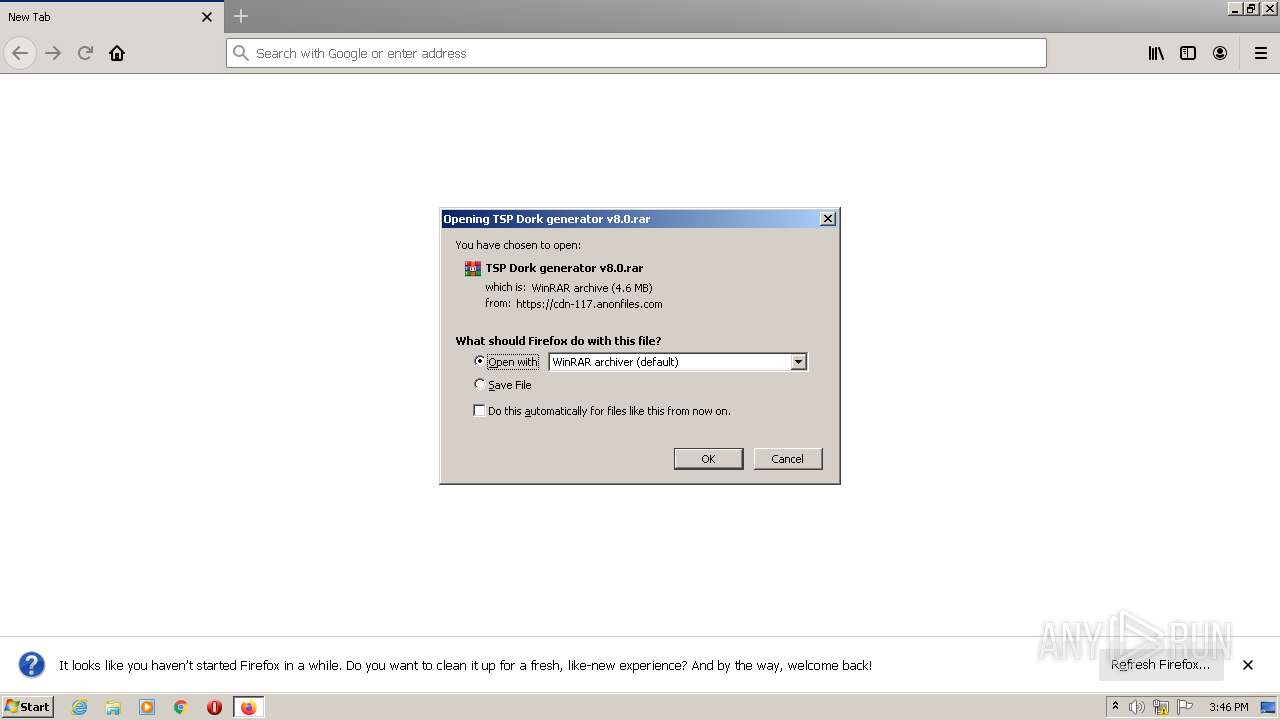
| URL: | https://cdn-117.anonfiles.com/Ra740c3fy5/be5fbad3-1660316187/TSP%20Dork%20generator%20v8.0.rar |
| Full analysis: | https://app.any.run/tasks/507746c7-d6aa-4892-8006-f8ca7f7c8b20 |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | August 12, 2022, 14:46:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 473B1EB53A391A826A20A76CB9379E29 |
| SHA1: | F88FD951931936BFF084A7FCFE88834DA704BED5 |
| SHA256: | 07E7AA9AE0E731CD14C8AB18554E857877369A01A1562EBC3B38A6CB12F7F440 |
| SSDEEP: | 3:N8cFU4EL12lSxcYXAVTwu4MOA4cXDLVLXEX:2cFUJL12lLFN+AZXyX |
MALICIOUS
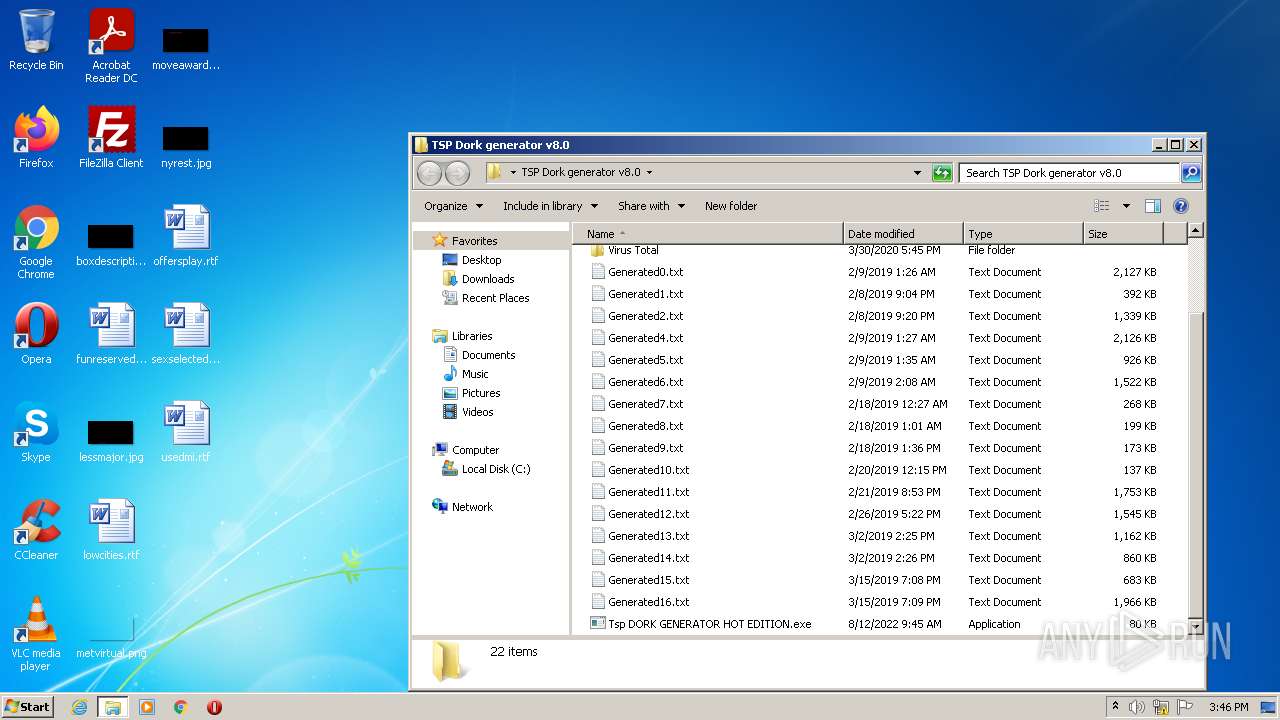
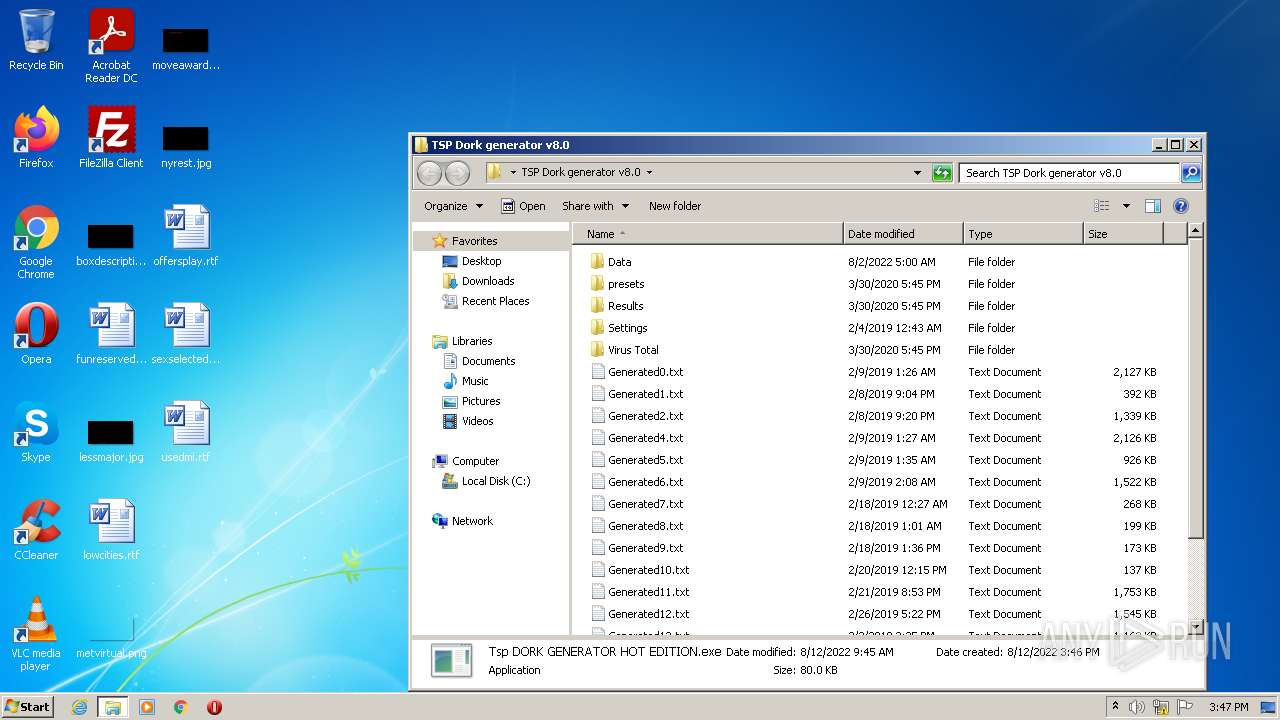
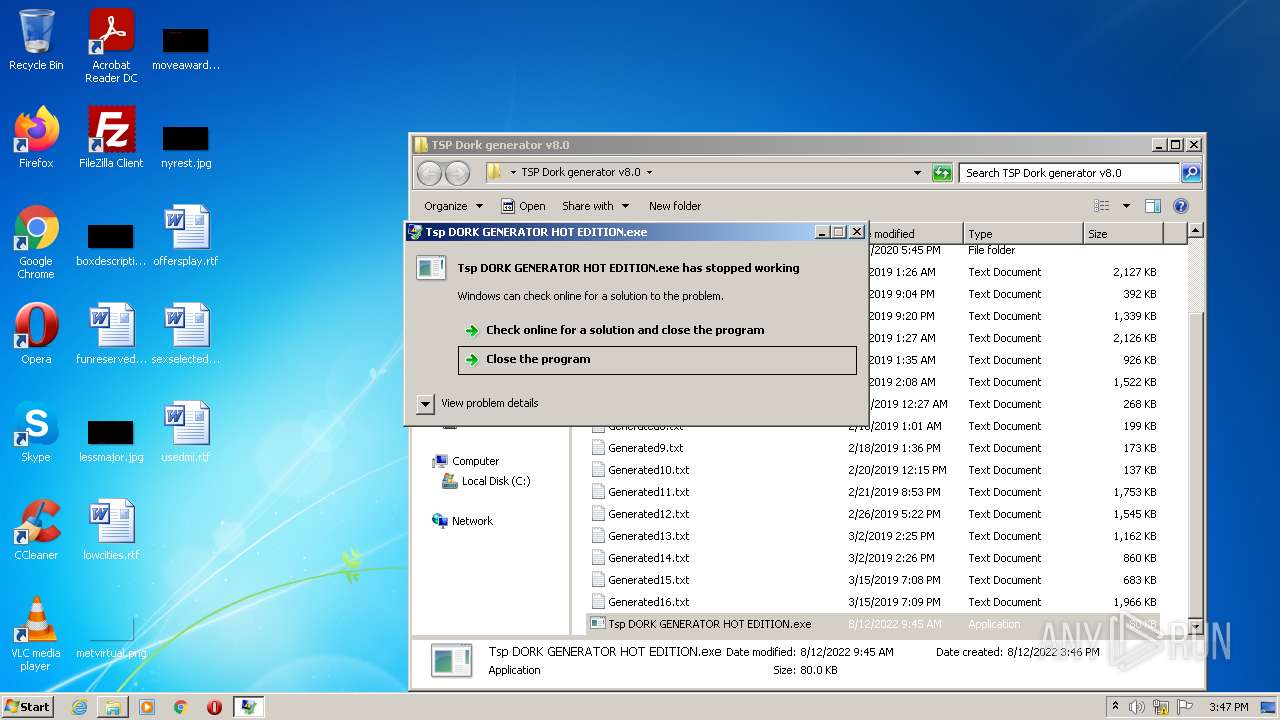
Application was dropped or rewritten from another process
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 3108)
- TSP Dork generator hot edition.exe (PID: 3976)
- server.exe (PID: 2844)
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 1968)
Drops executable file immediately after starts
- WinRAR.exe (PID: 2456)
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 3108)
- server.exe (PID: 2844)
NJRAT was detected
- server.exe (PID: 2844)
Writes to a start menu file
- TSP Dork generator hot edition.exe (PID: 3976)
- server.exe (PID: 2844)
Changes the autorun value in the registry
- server.exe (PID: 2844)
Connects to CnC server
- server.exe (PID: 2844)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2456)
- TSP Dork generator hot edition.exe (PID: 3976)
- server.exe (PID: 2844)
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 3108)
- dw20.exe (PID: 3120)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2456)
- server.exe (PID: 2844)
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 3108)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2456)
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 3108)
- server.exe (PID: 2844)
Writes to a desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 2456)
Checks supported languages
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 3108)
- WinRAR.exe (PID: 2456)
- TSP Dork generator hot edition.exe (PID: 3976)
- server.exe (PID: 2844)
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 1968)
- dw20.exe (PID: 3120)
Reads Environment values
- netsh.exe (PID: 872)
- server.exe (PID: 2844)
Creates files in the program directory
- dw20.exe (PID: 3120)
INFO
Application launched itself
- firefox.exe (PID: 3528)
- firefox.exe (PID: 2648)
Checks supported languages
- firefox.exe (PID: 2648)
- firefox.exe (PID: 2636)
- firefox.exe (PID: 3556)
- firefox.exe (PID: 3528)
- firefox.exe (PID: 556)
- firefox.exe (PID: 4072)
- firefox.exe (PID: 2948)
- netsh.exe (PID: 872)
Reads the computer name
- firefox.exe (PID: 2648)
- firefox.exe (PID: 556)
- firefox.exe (PID: 2636)
- firefox.exe (PID: 4072)
- firefox.exe (PID: 2948)
- firefox.exe (PID: 3556)
- netsh.exe (PID: 872)
Creates files in the program directory
- firefox.exe (PID: 2648)
Reads CPU info
- firefox.exe (PID: 2648)
Checks Windows Trust Settings
- firefox.exe (PID: 2648)
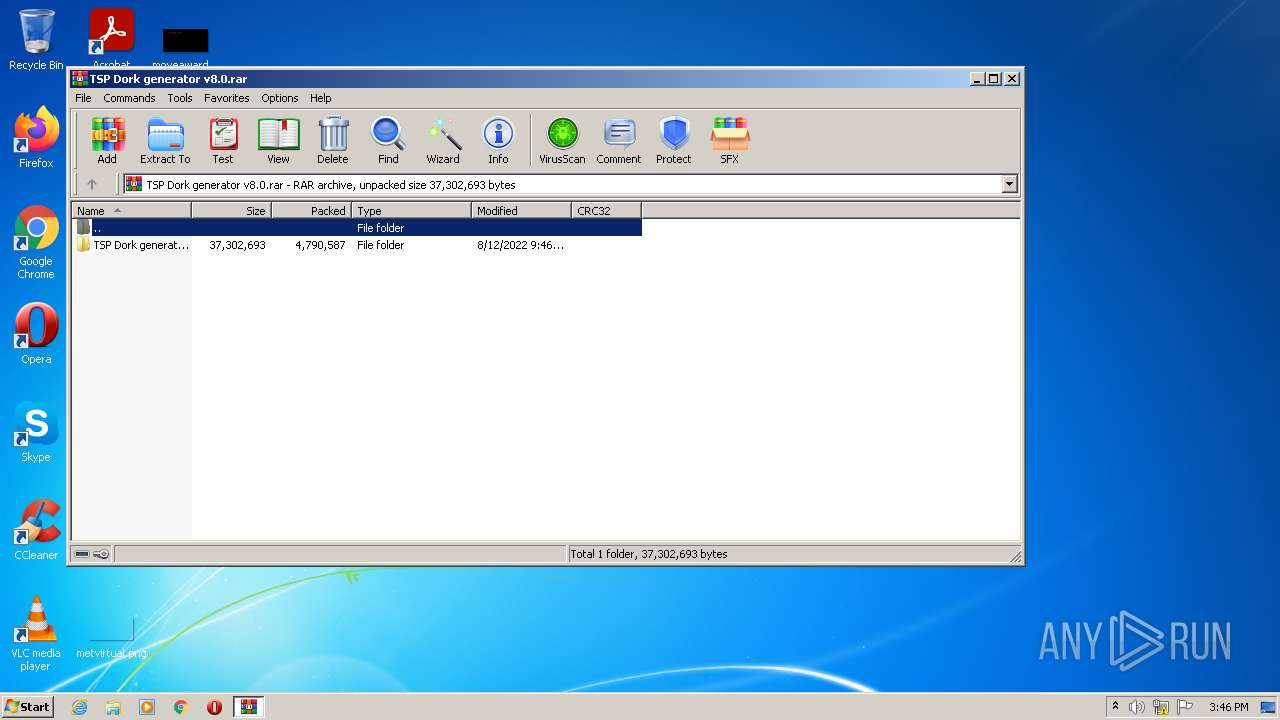
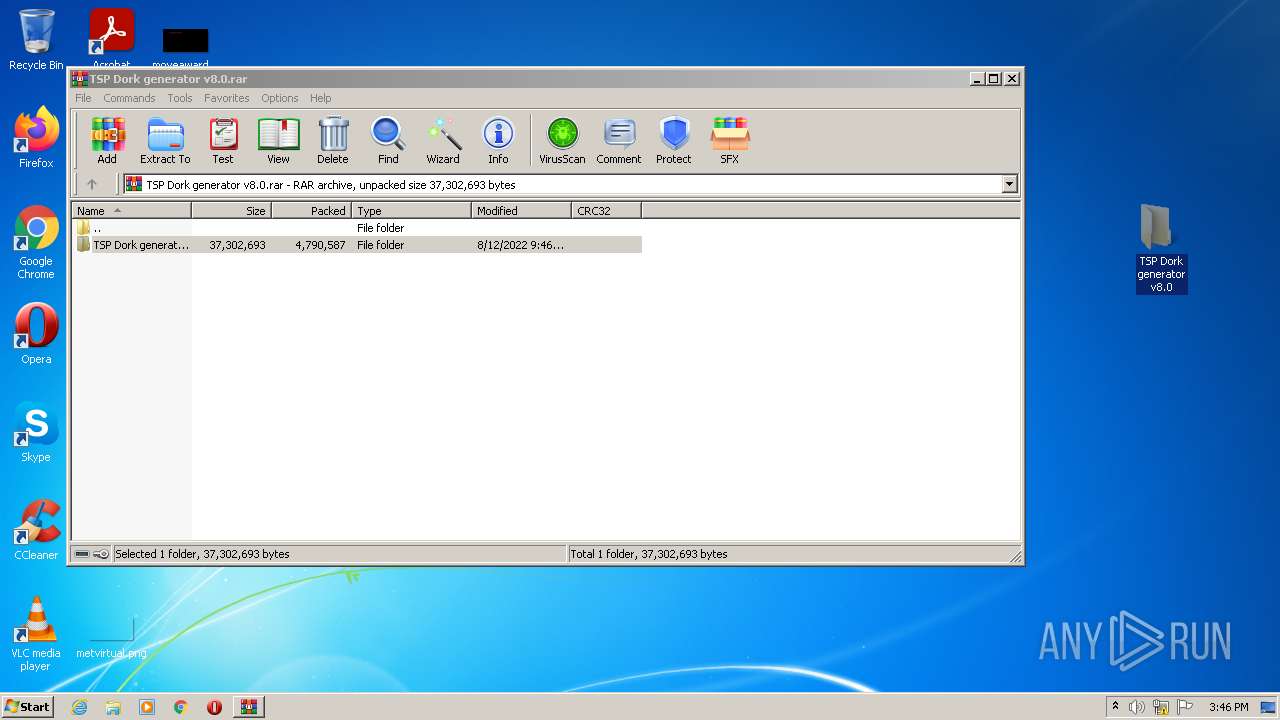
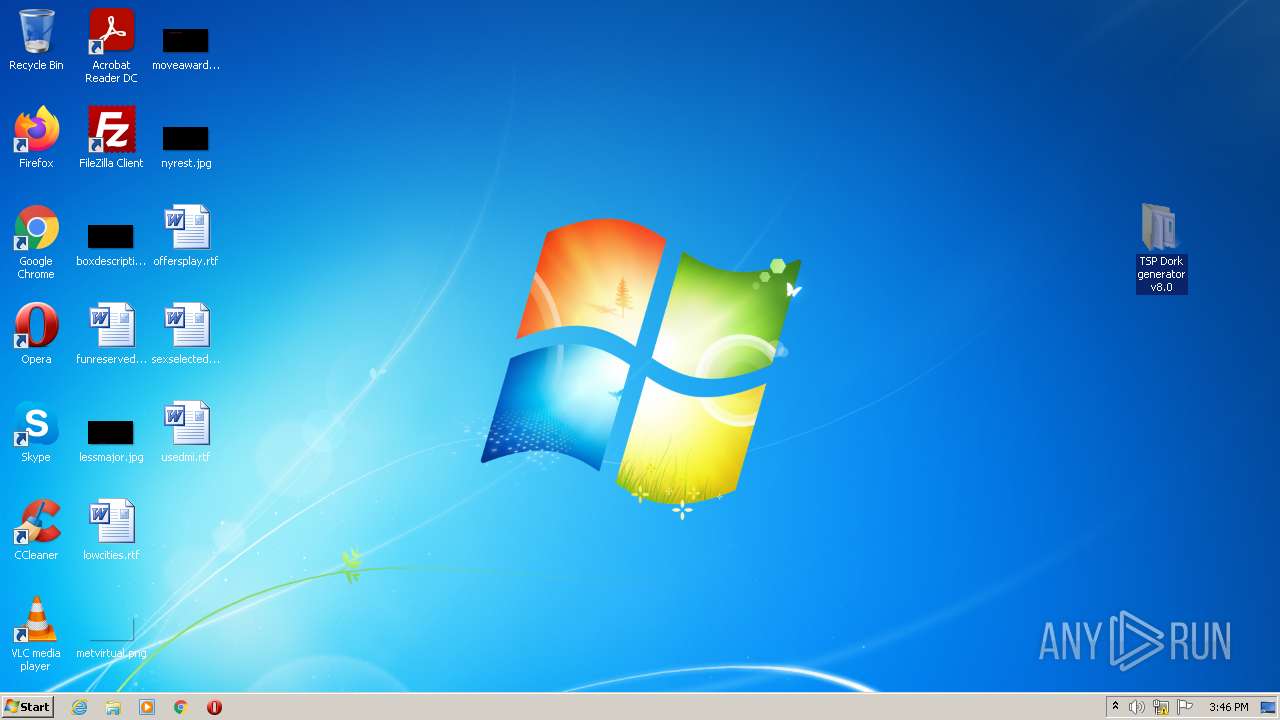
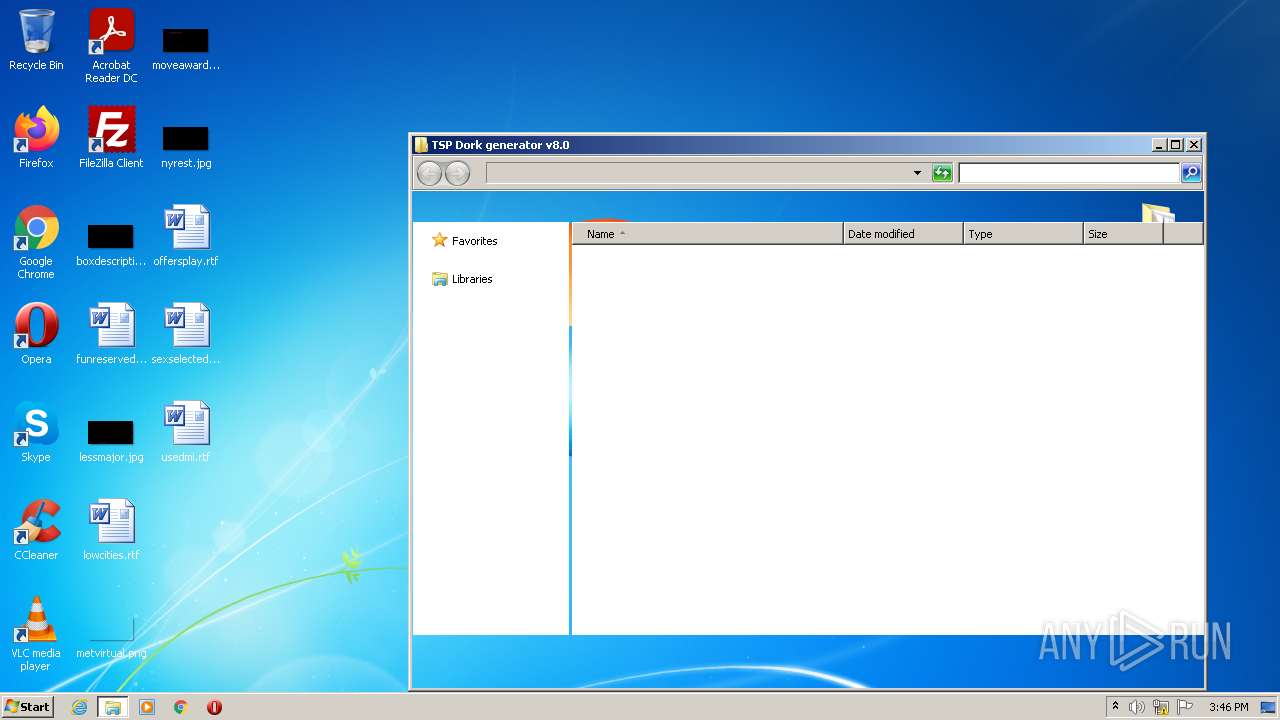
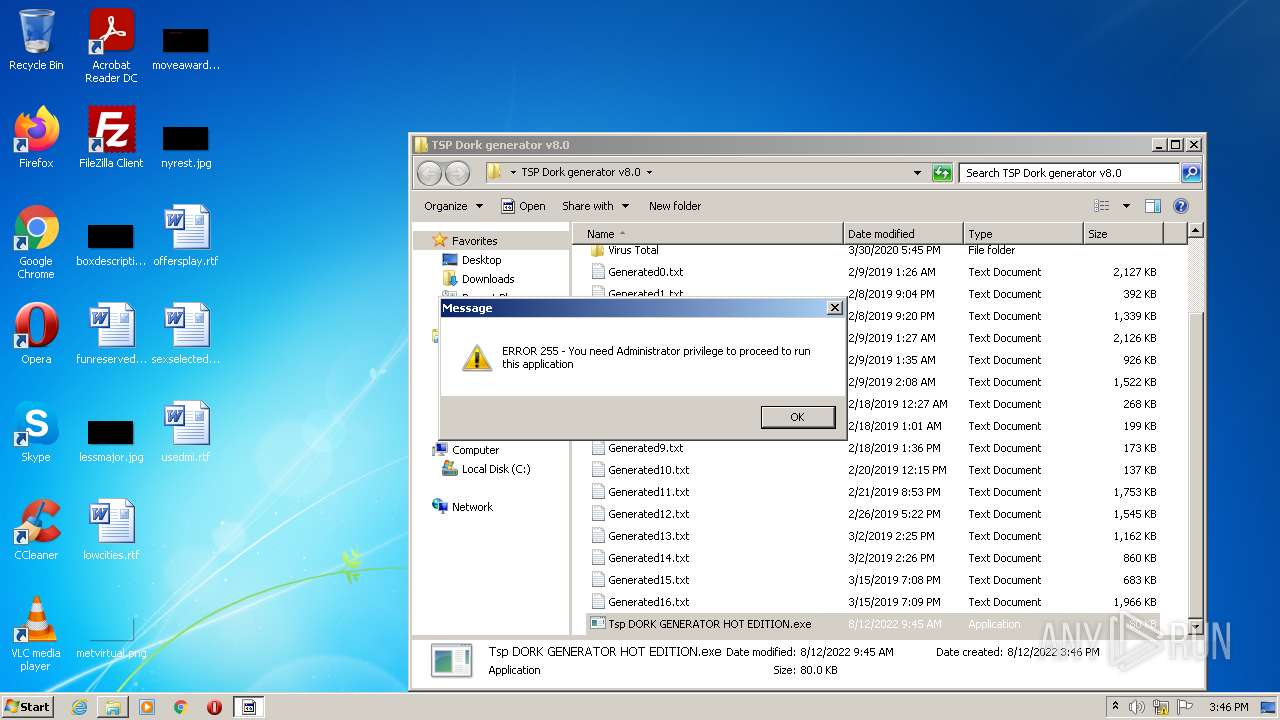
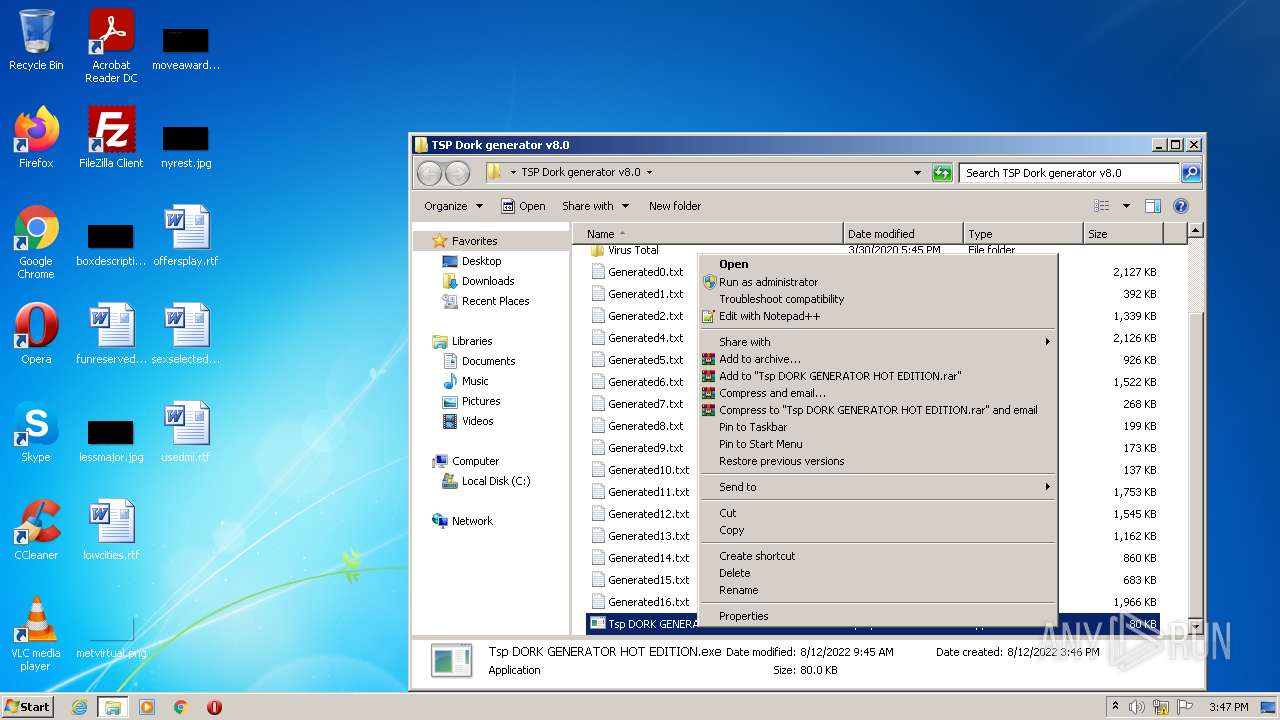
Manual execution by user
- WinRAR.exe (PID: 2456)
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 3108)
- Tsp DORK GENERATOR HOT EDITION.exe (PID: 1968)
Reads the date of Windows installation
- firefox.exe (PID: 2648)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
14
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2648.6.1799607664\1000927610" -childID 1 -isForBrowser -prefsHandle 2816 -prefMapHandle 2812 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2648 "\\.\pipe\gecko-crash-server-pipe.2648" 2828 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 872 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Local\Temp\server.exe" "server.exe" ENABLE | C:\Windows\system32\netsh.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1968 | "C:\Users\admin\Desktop\TSP Dork generator v8.0\Tsp DORK GENERATOR HOT EDITION.exe" | C:\Users\admin\Desktop\TSP Dork generator v8.0\Tsp DORK GENERATOR HOT EDITION.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 3762507597 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\TSP Dork generator v8.0.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2648.0.808473553\1007220552" -parentBuildID 20201112153044 -prefsHandle 1168 -prefMapHandle 1160 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2648 "\\.\pipe\gecko-crash-server-pipe.2648" 1232 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://cdn-117.anonfiles.com/Ra740c3fy5/be5fbad3-1660316187/TSP%20Dork%20generator%20v8.0.rar | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2844 | "C:\Users\admin\AppData\Local\Temp\server.exe" | C:\Users\admin\AppData\Local\Temp\server.exe | Tsp DORK GENERATOR HOT EDITION.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2948 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2648.20.1788956874\374770469" -childID 3 -isForBrowser -prefsHandle 3784 -prefMapHandle 3780 -prefsLen 7470 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2648 "\\.\pipe\gecko-crash-server-pipe.2648" 3800 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\Desktop\TSP Dork generator v8.0\Tsp DORK GENERATOR HOT EDITION.exe" | C:\Users\admin\Desktop\TSP Dork generator v8.0\Tsp DORK GENERATOR HOT EDITION.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3120 | dw20.exe -x -s 376 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | Tsp DORK GENERATOR HOT EDITION.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
Total events
10 539
Read events
10 393
Write events
146
Delete events
0
Modification events
| (PID) Process: | (3528) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: D528183006000000 | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: BC2F183006000000 | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2648) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
7
Suspicious files
44
Text files
99
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2648 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2648 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2648 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_9xsihUGsscnJCFo | binary | |
MD5:— | SHA256:— | |||
| 2648 | firefox.exe | C:\Users\admin\AppData\Local\Temp\lAb4d8Ko.rar.part | — | |
MD5:— | SHA256:— | |||
| 2648 | firefox.exe | C:\Users\admin\Downloads\TSP Dork generator v8.0.rar | — | |
MD5:— | SHA256:— | |||
| 2648 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 2648 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:994A33896BB41A278A315D0D796422B6 | SHA256:54EC50A20FFF8CC016710E49437CF6A11D3FE5EE7B28C185E4A9AAFEE2908B63 | |||
| 2648 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2648 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 2648 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
28
DNS requests
40
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2648 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2648 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2648 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
2648 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
2648 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2648 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
2648 | firefox.exe | 13.224.189.76:443 | firefox.settings.services.mozilla.com | — | US | unknown |
2648 | firefox.exe | 195.96.151.69:443 | cdn-117.anonfiles.com | Archway S.r.l | IQ | unknown |
2648 | firefox.exe | 44.241.228.251:443 | location.services.mozilla.com | University of California, San Diego | US | unknown |
2648 | firefox.exe | 142.250.186.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2648 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2648 | firefox.exe | 142.250.181.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2648 | firefox.exe | 13.225.78.36:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | whitelisted |
2648 | firefox.exe | 13.224.189.85:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
2844 | server.exe | 147.185.221.180:27272 | fund-linda.at.playit.gg | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
cdn-117.anonfiles.com |
| unknown |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2648 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2648 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
8 ETPRO signatures available at the full report