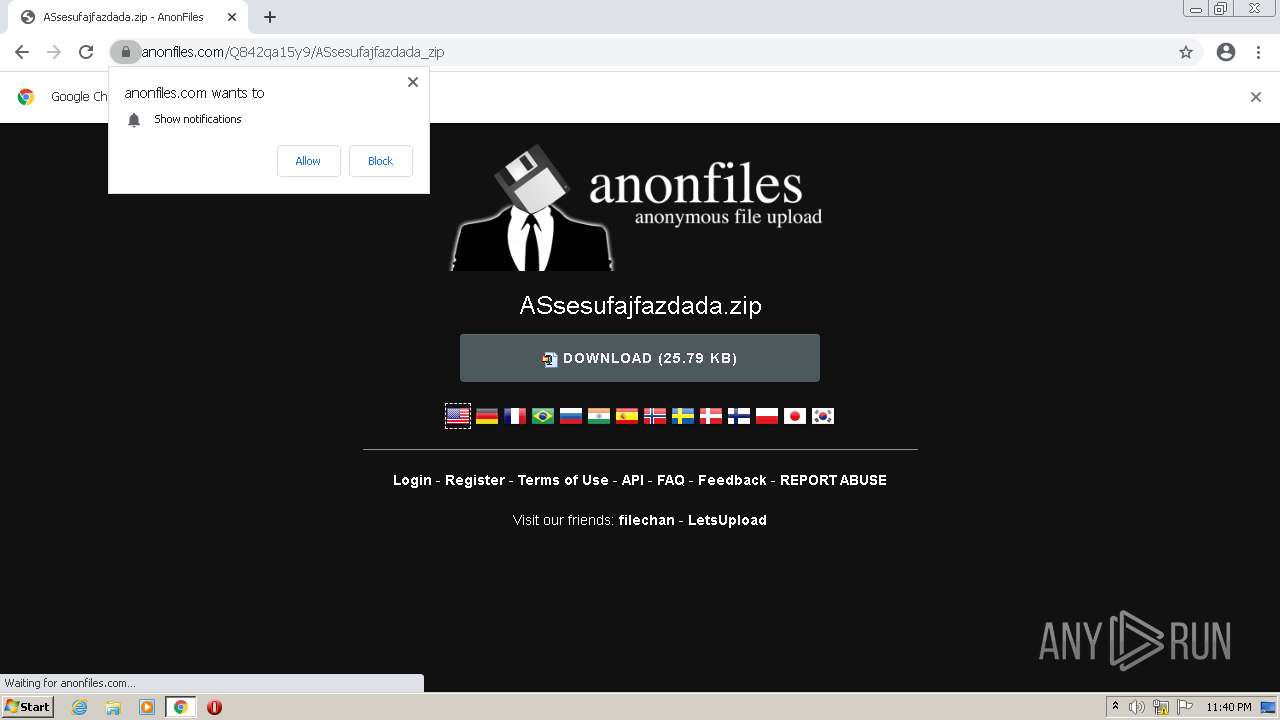
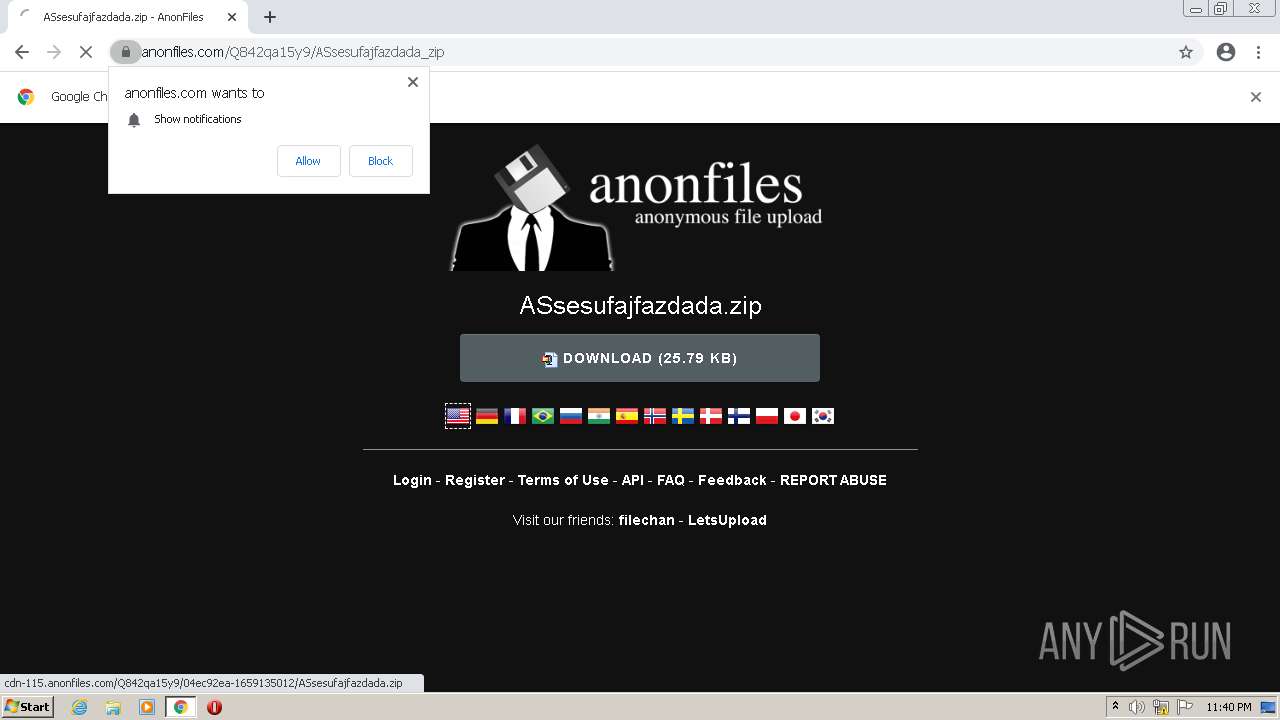
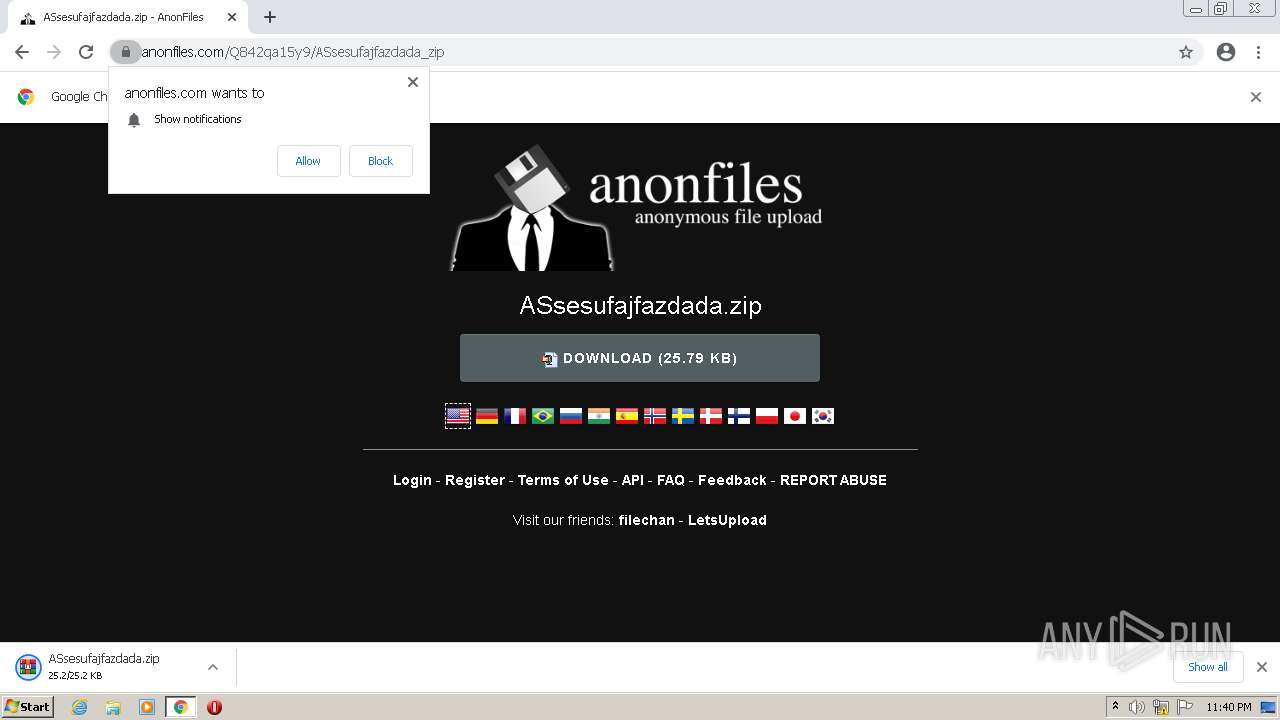
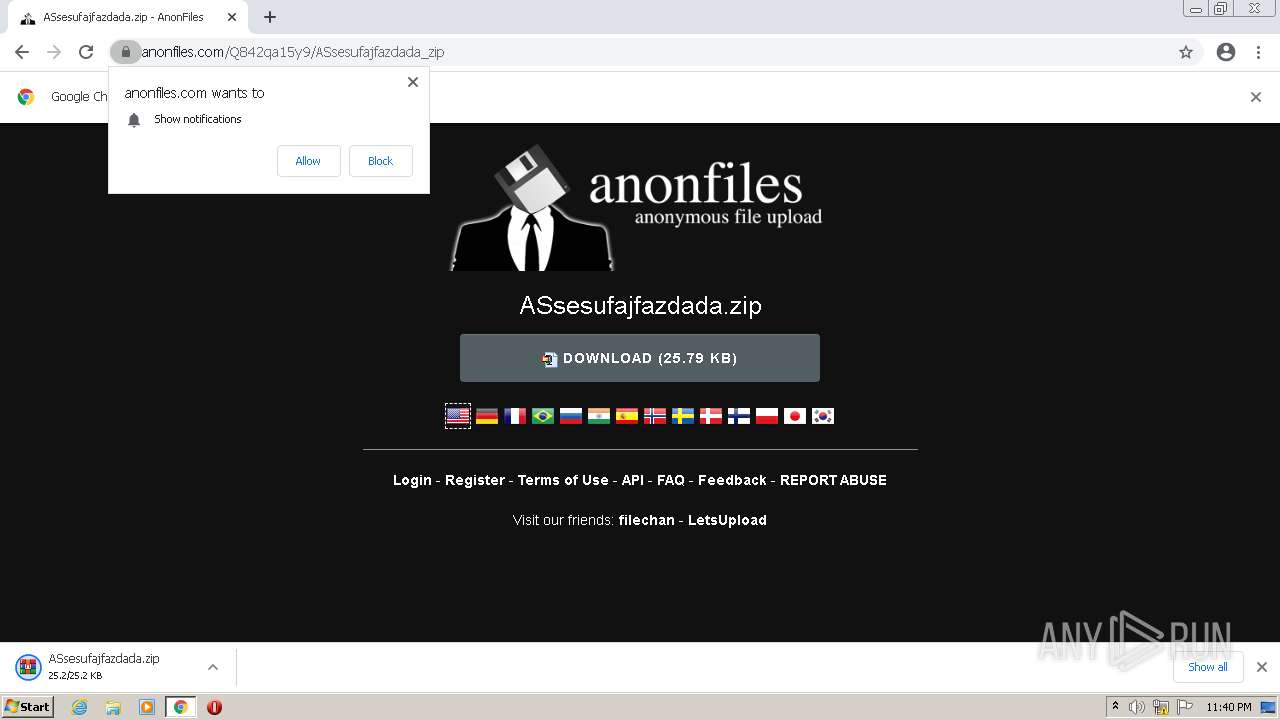
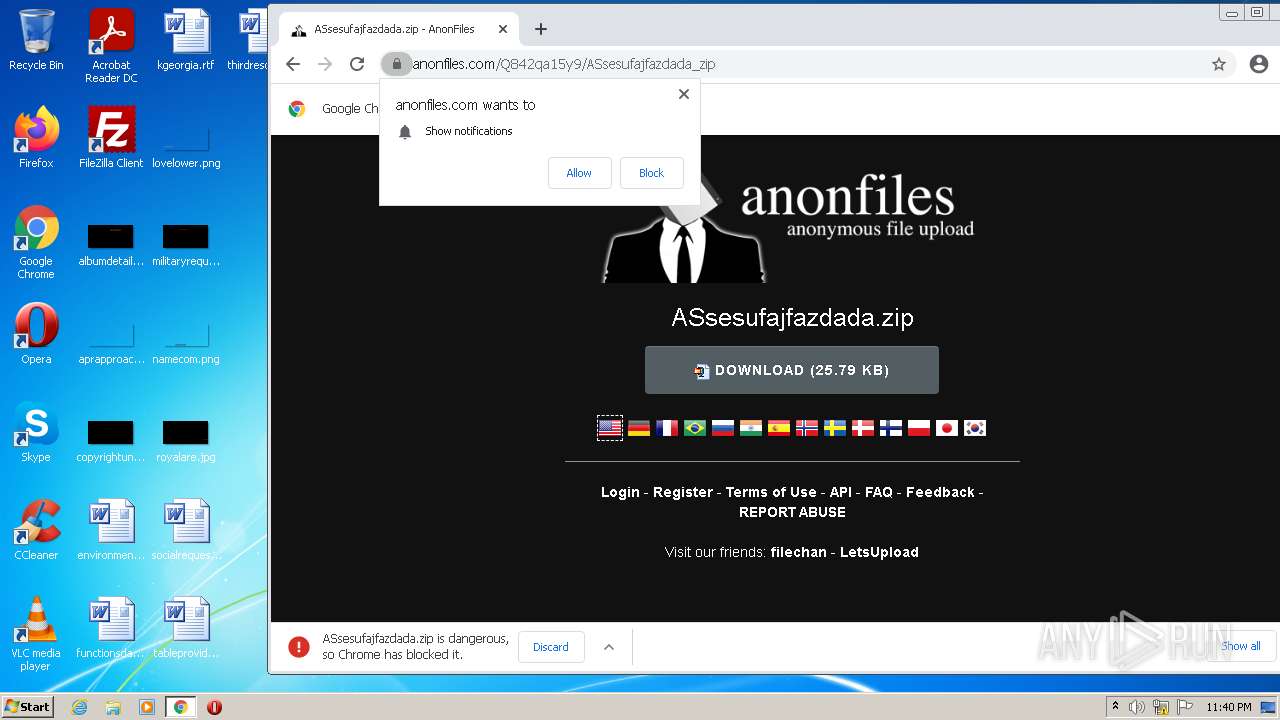
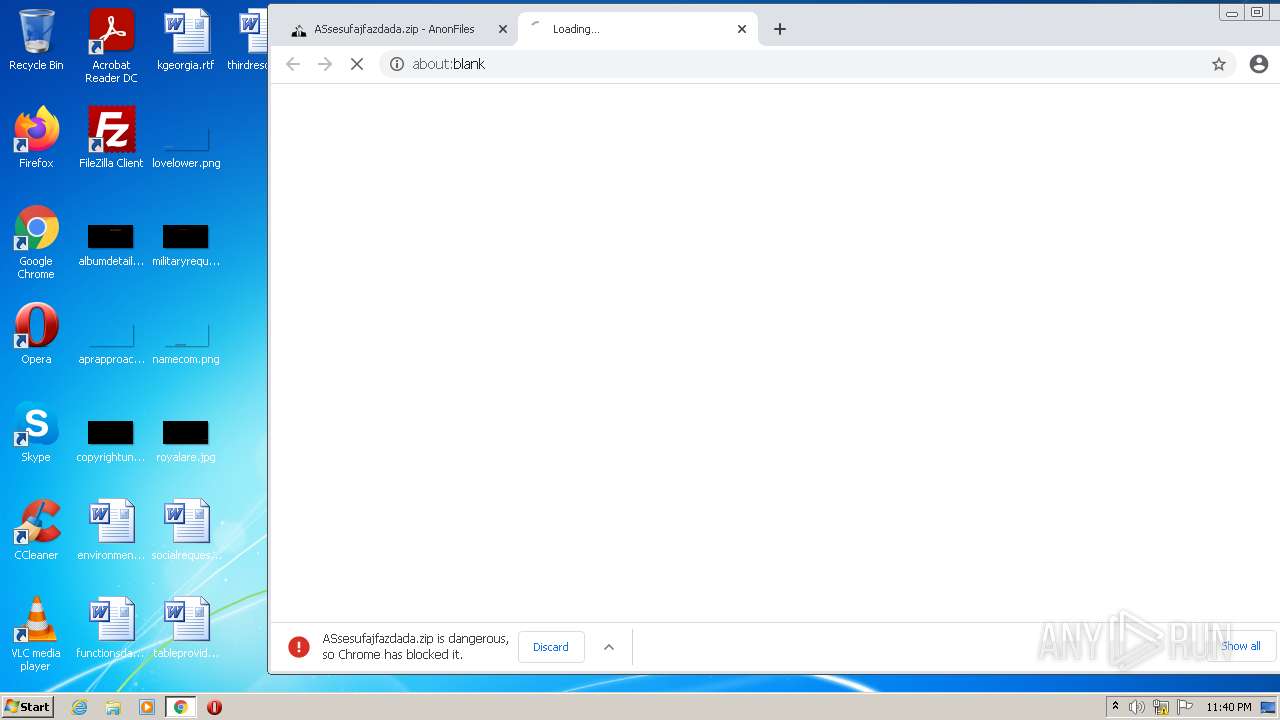
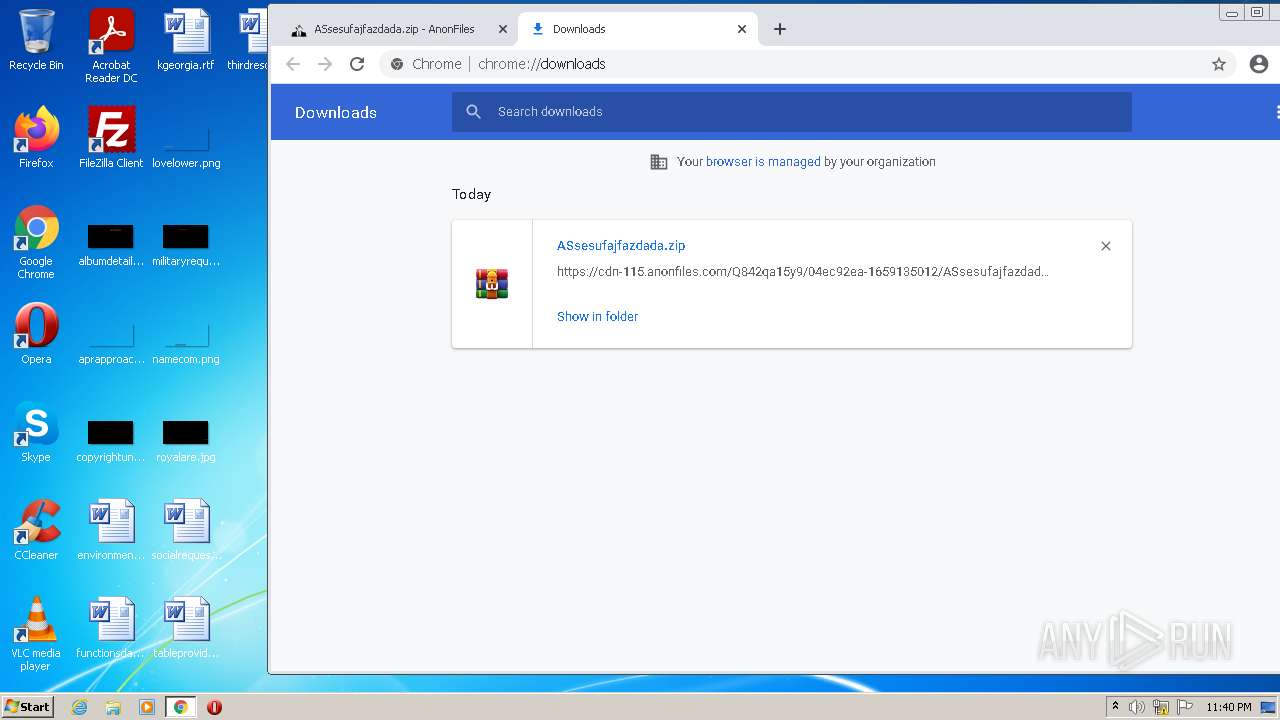
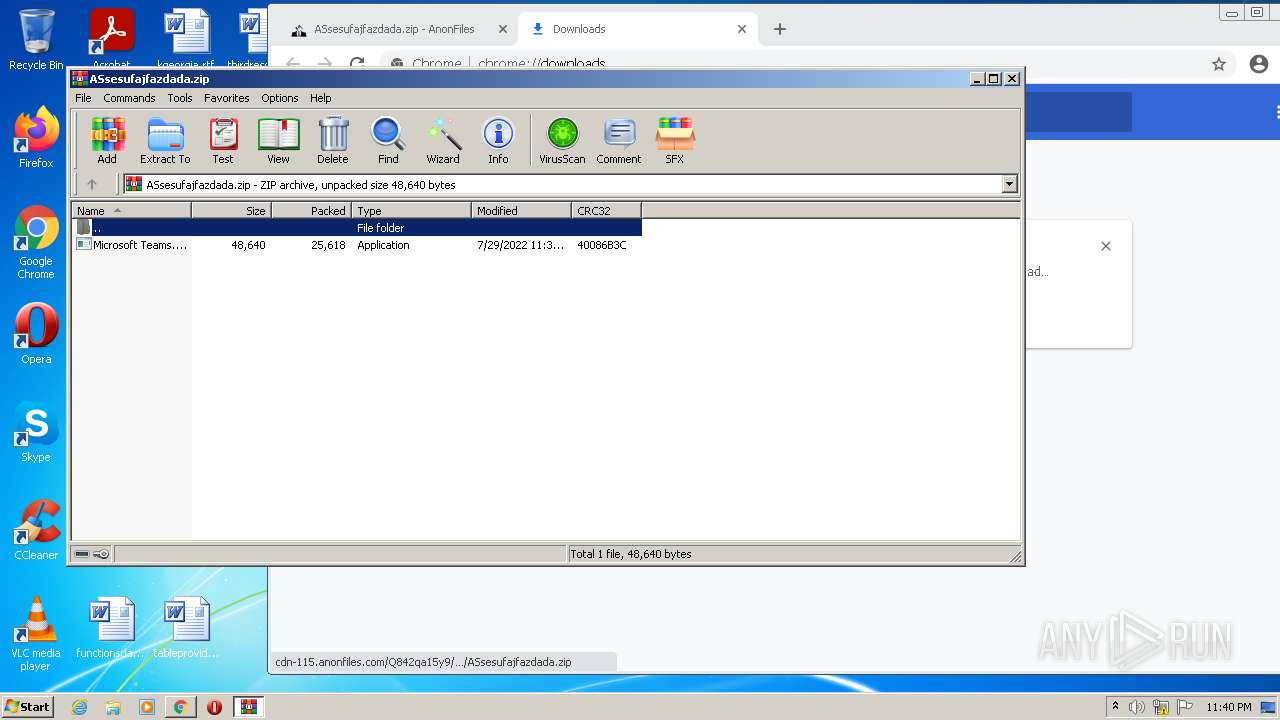
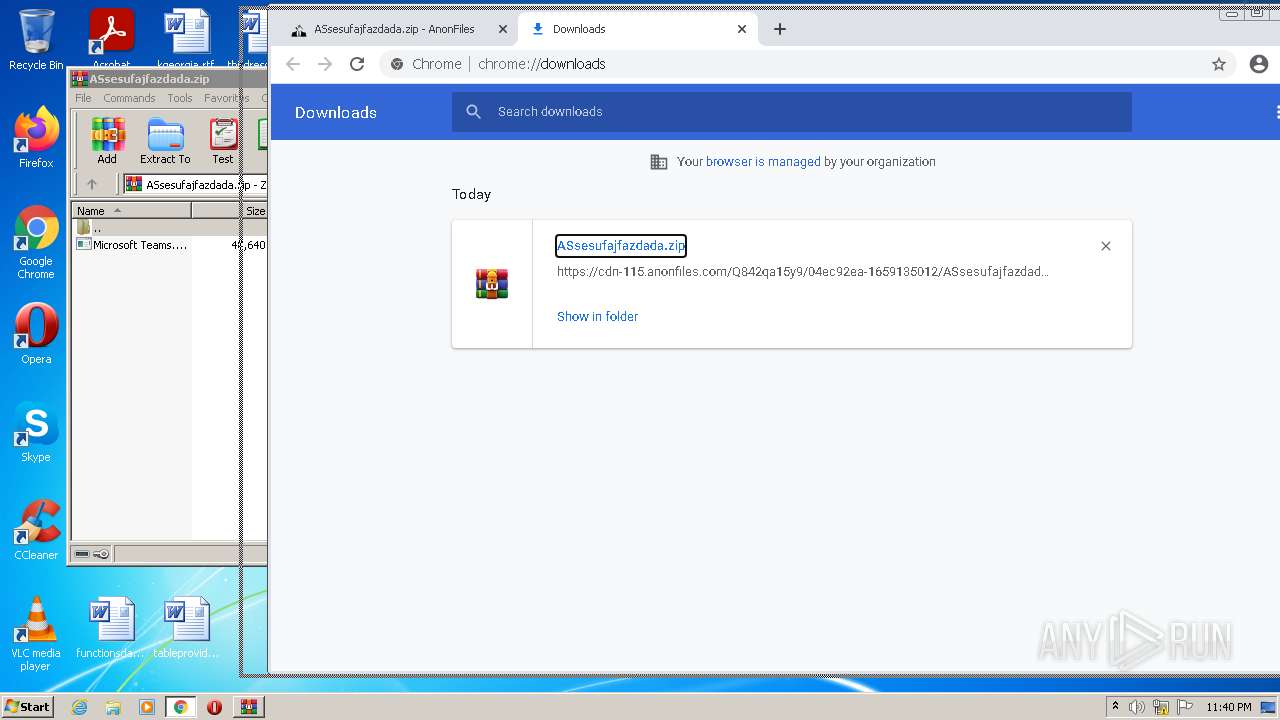
| URL: | https://anonfiles.com/Q842qa15y9/ASsesufajfazdada_zip |
| Full analysis: | https://app.any.run/tasks/a0f00095-74c3-4fbc-b2cf-86371706655a |
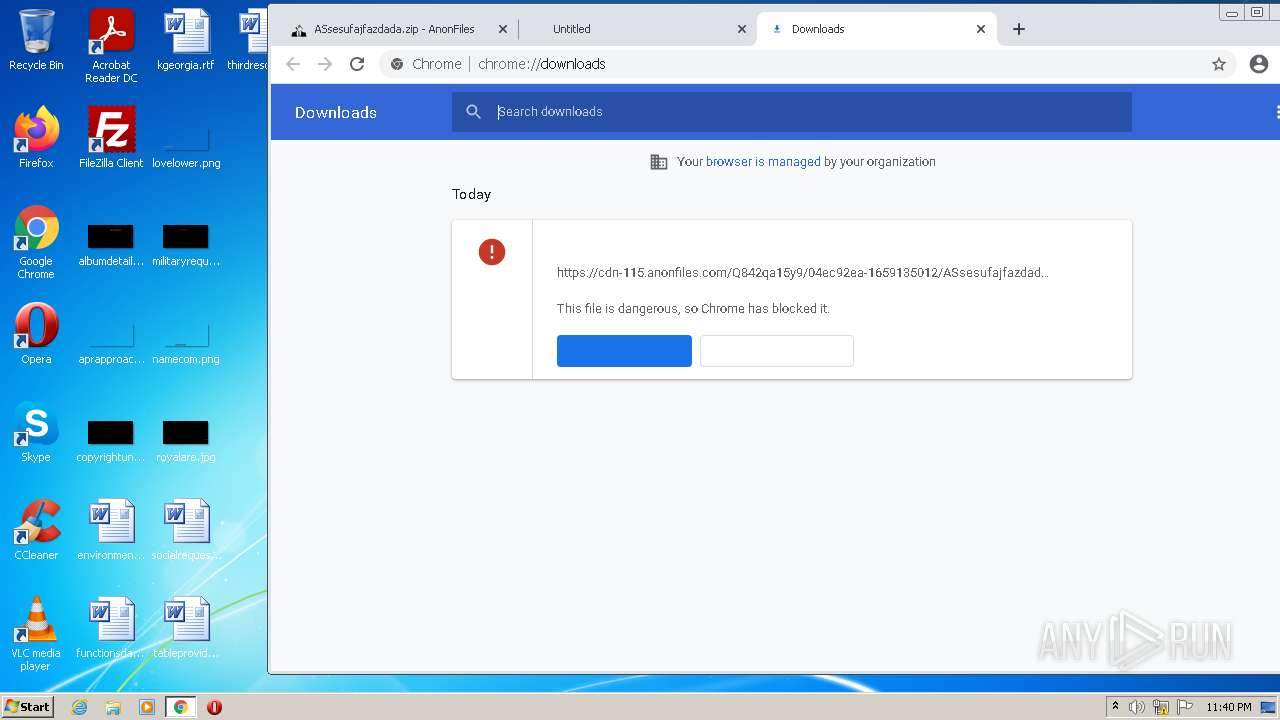
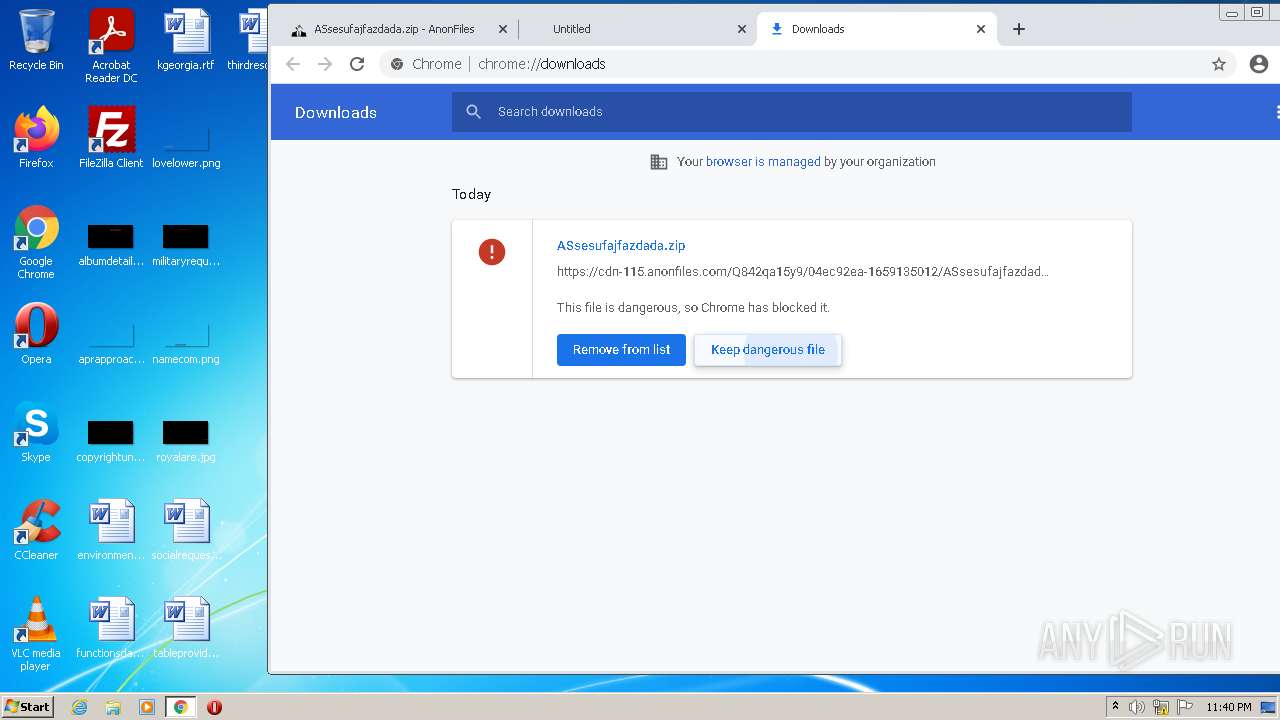
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | July 29, 2022, 22:40:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 70967CECDA1109EF943E98AA4250B756 |
| SHA1: | FD00B7553E457F0A3D9844DA68F17184336349C0 |
| SHA256: | 07D6191632F3CC38D385BE91E9A21BBC4D20B64EC82621F949C8F7A6CBCE0EC6 |
| SSDEEP: | 3:N8M2DUyLKf:2M2LLW |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 584)
- WinRAR.exe (PID: 2816)
ASYNCRAT detected by memory dumps
- WinRAR.exe (PID: 2816)
- Microsoft Teams.exe (PID: 564)
Application was dropped or rewritten from another process
- Microsoft Teams.exe (PID: 564)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2856)
Executable content was dropped or overwritten
- chrome.exe (PID: 584)
- WinRAR.exe (PID: 2816)
Drops a file with a compile date too recent
- chrome.exe (PID: 584)
- WinRAR.exe (PID: 2816)
Checks supported languages
- Microsoft Teams.exe (PID: 564)
- WinRAR.exe (PID: 2816)
Reads the computer name
- Microsoft Teams.exe (PID: 564)
- WinRAR.exe (PID: 2816)
Reads Environment values
- Microsoft Teams.exe (PID: 564)
INFO
Checks supported languages
- chrome.exe (PID: 2856)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 584)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 1924)
- chrome.exe (PID: 988)
Application launched itself
- chrome.exe (PID: 2856)
Reads the computer name
- chrome.exe (PID: 2856)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 988)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3348)
Reads settings of System Certificates
- chrome.exe (PID: 3560)
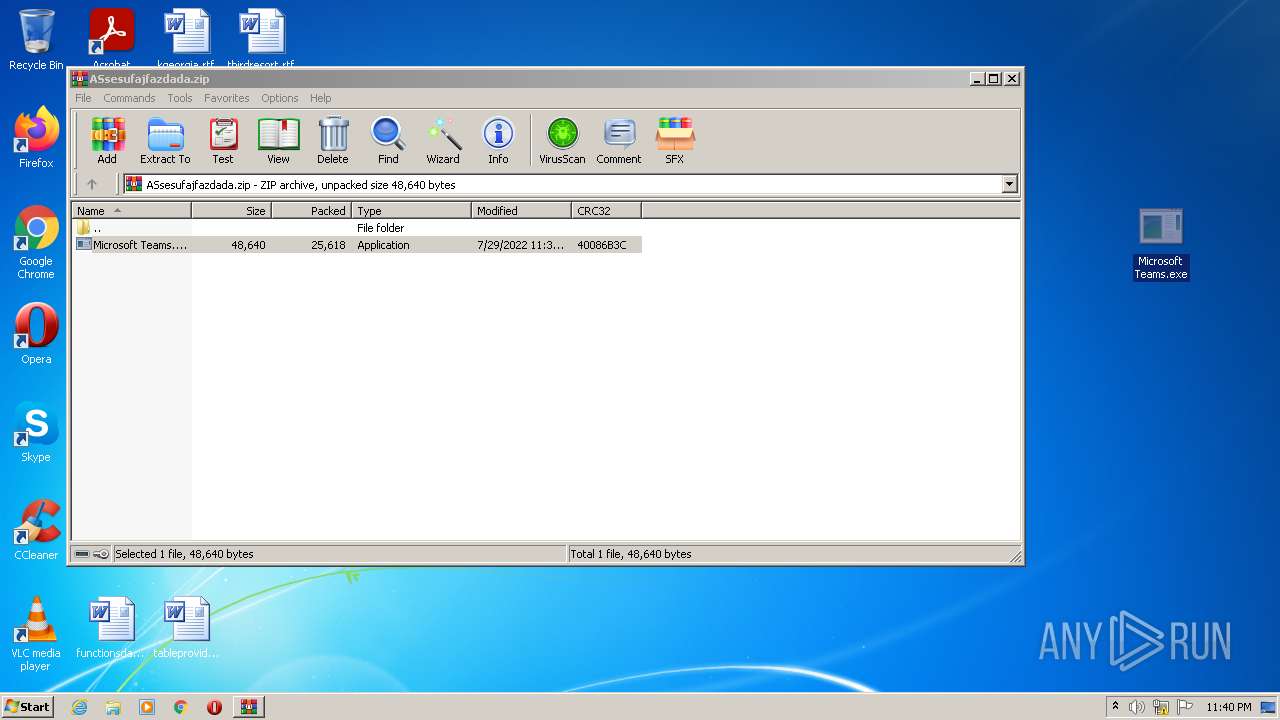
Manual execution by user
- Microsoft Teams.exe (PID: 564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(564) Microsoft Teams.exe
C2 (1)0.tcp.eu.ngrok.io
Ports (2)80
19572
Version0.5.7B
Autorunfalse
MutexAsyncMutex_6SI8OkPnk
CertificateMIIE8jCCAtqgAwIBAgIQANZPihCMyS7wBjOzeNIbaTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwNzI3MjIyNzM2WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBALJdOSflNzsOqMpL1gripPIeqILmWBL+tUWRTpp73wDRWcNJPcF3p52yMYUeFtPOJ2g+kYdNG6fn...
Server_SignatureBJBqnAcbgECSfkkm9qptY+FN8mD3nzWJnUBqSuaaZr2UEbN7WGZWeXtoF2UAqTxNSCOiQ6zOvRTWzykerYdUoG5AZCZQZrqi++NtAty2ZbK/2yrkPFZsVg9CWkKmKR+97dM8UmZOzHN3JW1J1TbyHD71ZugF29UQij8icPA0SB2LgLls3jPzVBXE56Bo0xGB9uzPQXfnKMkRniDjERsH09r0GxWUQq9rZelHEOL8HqLIn5OJi9SdXcvWpyBIWwb2qp0A150eXEMEutJ9ccDvp8V2C0HycAKz6wx8KUbRWGqp...
AntiVMfalse
PasteBinnull
bdosfalse
BotnetDefault
Aes_Key895109b456a837fb1f5154587192ab9f19f92a730734682a6c34e1ccbba2fa3c
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Install_Folder%AppData%
Total processes
52
Monitored processes
18
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Users\admin\Desktop\Microsoft Teams.exe" | C:\Users\admin\Desktop\Microsoft Teams.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
AsyncRat(PID) Process(564) Microsoft Teams.exe C2 (1)0.tcp.eu.ngrok.io Ports (2)80 19572 Version0.5.7B Autorunfalse MutexAsyncMutex_6SI8OkPnk CertificateMIIE8jCCAtqgAwIBAgIQANZPihCMyS7wBjOzeNIbaTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwNzI3MjIyNzM2WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBALJdOSflNzsOqMpL1gripPIeqILmWBL+tUWRTpp73wDRWcNJPcF3p52yMYUeFtPOJ2g+kYdNG6fn... Server_SignatureBJBqnAcbgECSfkkm9qptY+FN8mD3nzWJnUBqSuaaZr2UEbN7WGZWeXtoF2UAqTxNSCOiQ6zOvRTWzykerYdUoG5AZCZQZrqi++NtAty2ZbK/2yrkPFZsVg9CWkKmKR+97dM8UmZOzHN3JW1J1TbyHD71ZugF29UQij8icPA0SB2LgLls3jPzVBXE56Bo0xGB9uzPQXfnKMkRniDjERsH09r0GxWUQq9rZelHEOL8HqLIn5OJi9SdXcvWpyBIWwb2qp0A150eXEMEutJ9ccDvp8V2C0HycAKz6wx8KUbRWGqp... AntiVMfalse PasteBinnull bdosfalse BotnetDefault Aes_Key895109b456a837fb1f5154587192ab9f19f92a730734682a6c34e1ccbba2fa3c Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 Install_Folder%AppData% | |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1048,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3760 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1048,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
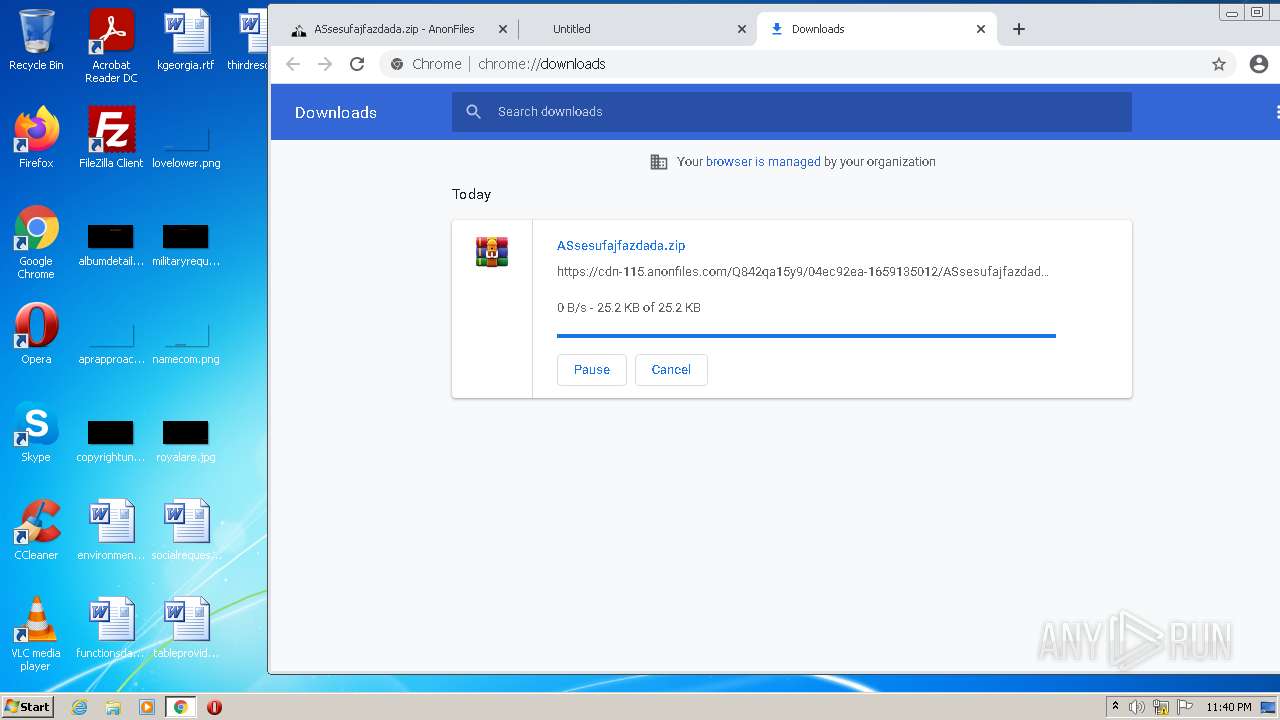
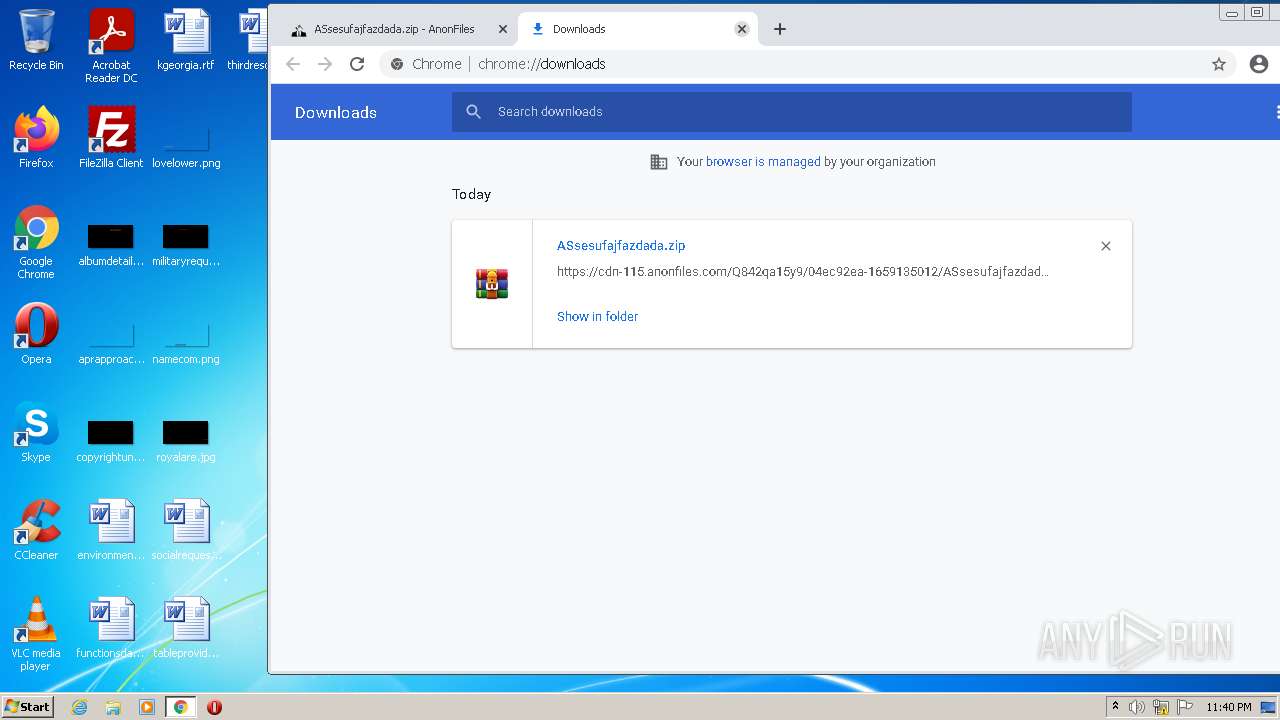
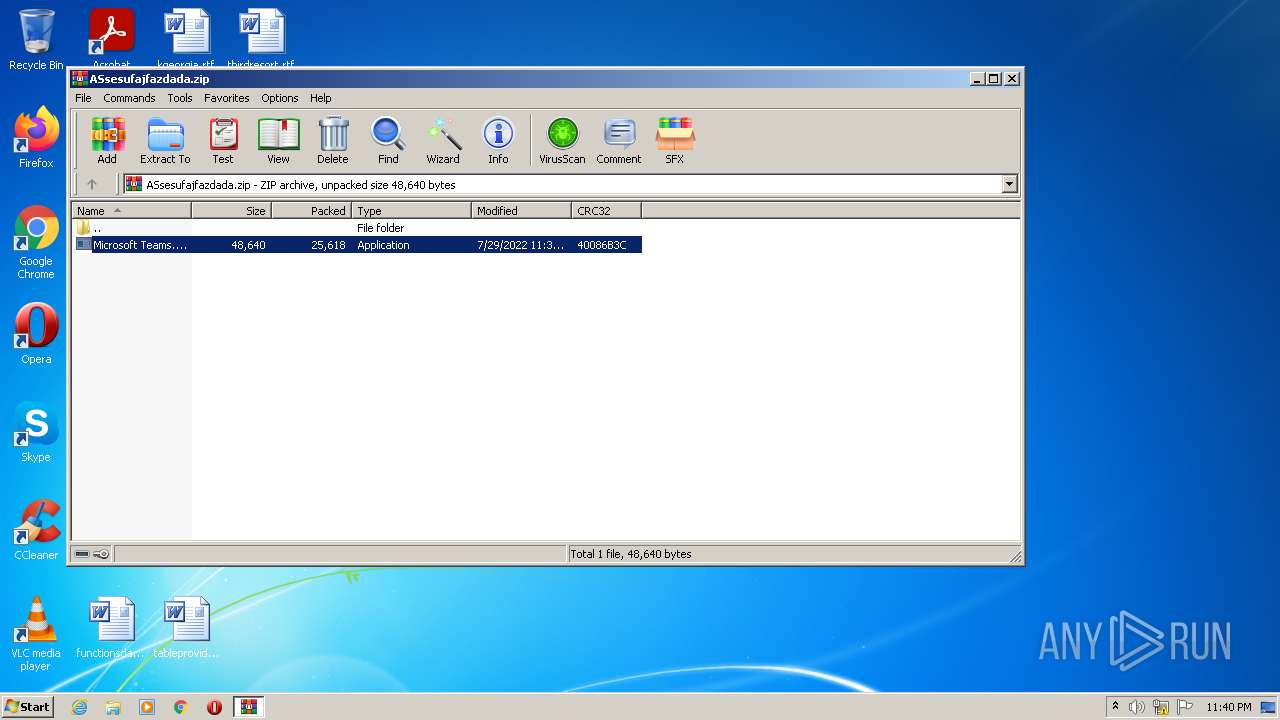
| 2816 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ASsesufajfazdada.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://anonfiles.com/Q842qa15y9/ASsesufajfazdada_zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ed7d988,0x6ed7d998,0x6ed7d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
14 306
Read events
14 197
Write events
109
Delete events
0
Modification events
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
2
Suspicious files
55
Text files
94
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62E461DD-B28.pma | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1050a2.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1050c2.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e2f28c4d-8a79-4b3a-9a47-1684a0e47683.tmp | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b5792e72-9fb7-457b-92d0-acc2e5e2cdaa.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
78
DNS requests
24
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3560 | chrome.exe | GET | 200 | 8.248.119.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d74d706bfcd34022 | US | compressed | 60.2 Kb | whitelisted |
3560 | chrome.exe | GET | 200 | 8.248.119.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3b90222206b30d27 | US | compressed | 60.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | chrome.exe | 142.250.186.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3560 | chrome.exe | 142.250.185.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3560 | chrome.exe | 18.66.192.29:443 | onianstarvar.xyz | Massachusetts Institute of Technology | US | unknown |
3560 | chrome.exe | 8.248.119.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3560 | chrome.exe | 44.195.137.121:443 | baconaces.pro | University of California, San Diego | US | shared |
3560 | chrome.exe | 172.67.218.221:443 | freychang.fun | — | US | suspicious |
3560 | chrome.exe | 143.204.89.36:443 | naleapprength.xyz | — | US | unknown |
3560 | chrome.exe | 188.114.97.3:443 | chedstimaarr.pics | Cloudflare Inc | US | malicious |
3560 | chrome.exe | 195.96.151.67:443 | cdn-115.anonfiles.com | Archway S.r.l | IQ | unknown |
3560 | chrome.exe | 31.13.92.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
onianstarvar.xyz |
| suspicious |
smetotrea.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3560 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3560 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3560 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3560 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
564 | Microsoft Teams.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
564 | Microsoft Teams.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
564 | Microsoft Teams.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |