| URL: | https://protect.checkpoint.com/v2/r01/___https://lsems.gravityzone.bitdefender.com/xhfsdfMW5hMR*~*QDcqg1KugH/rhrqqgrWni2pyg1KugH/og75AgMRA37Cu37x!i2GzU2ZBRIJzR2iCW8uXhEGt12GDVsqzW1SPS135WYiLZE0SSK4AhpWv0LOL41CEW5iqYn5DVrOzSZCQ3si0hrm0f8070pxyRp37h0qff2WoZMq3WpK4Yruo0KGLT0qxiriR4H5DWpiAi5yoZEOfSMqzfE01YJuRgLt9g7yRgK4fYqOQfD5DWohEZqSTW1OYYEm6RZcHTIOTRZ/1ir0f1oSXS5bEY7Z5R7cBj0Wp414P0pOXV04LW2q9XIi5TJSNh0GmV64TRZquR2lCV5qwgsGMhqiMTJuYjYOwW508V1i0RKqU0JiP48K7W6KLZs4wfMWZZJCJ01KtS6GrX7Cr0pu91IWJ014Zi0OPhpuYiKWRYLyI0Z6B0oi900SHSsWViEO8g8WvXEKKTKW5XLuH37y84KSYhK4IWIRDiJ0NXs0H0puK4qWH0pi8ZLcQjZ4I1p6yhJmTQYOH4IKmR6OJS84VQYOLQYOH1IGXgZyoh8qBX8G3XLpDi2SmhpuVSr95iIm0TMKBYJSHj20L0IN74pyNTIWBjry*~*g6qIXriCjpu4SLRB4Mh5ipx6XJ4DXH5DWpioV1OfjJpChsVD32GWW2S8jrJ50JqC0r/vQYOL41iIXE0Qh6iQXK0pV2S0gL4D4ZxyRp3EipKLfZu8fYOzjrSO1JqMTIirXYq*~*VrcogIG8gsOIf5C8grywfJcO3pq13p0xWsuq3qK3fJuSREqAT1cHfMZyRpOVjquJ1ZB9gIWM01/JV8K9Z2SpSJSqY7OyZKl8hEiYZ00RS7yC1YSmirKA3ESN016LXsZDW0iLTJi6WoZyRp4rX2SRjL4Hg6KnX8KKg1i/1sqAZoG3gJq31L09h7/Ogrux07/mQYOL1JiZQYOLZq0rhJyL1Ly/0qqmh7mLV5BCh8h9X80NXp/qQYOHhs37ZqOu11JEV2hyR5VyR5VEY2mA2EWBf1mNj1iTZ5NBhoqX4qhB4IV5Y5mG1ZmGg7K0W1iHiMGOQYOLgrh5hq0N4Li3goiZXrh542JEXq4Pf0Grh6u4YYS/36V6Z6uoZJ/fRKOqTJWqS50yfs4tZISpYIKHg2KCf7OSgJcIXK3DZ7/uQYOLS1qO42uXZ8JD1qWwXIKpjYV7XYSPR7m1W5i2iMKuWqR/W1y4ZJKz0pZ61LCq0MK8h2qsQYOLWIh9hqGAiLiS11iJYrc3jr6PfYlyRp4GR7RBXpy9QYOLYL5=dbFKaGcIbG/GKHK*~*9*/2*H7aJaaIbI6K7ccF/bFHKI*~*J9c/65Ja6F8F886JHIHa/8K9?h=6&fru;n=6&fru;ithx=6___.YzJ1OnNlcXVhbGNvcnA6YzpvOjI2Mzg4MTdmNDQzNWRjNDY2Nzg5NzMyOWZmYzFkMWMyOjc6ODVjNToxOTQ2YTEzYTcxMDBkNDE0MzFjMmI1Mjk2MmEwYjRmNjU0OTBlNWJiYmEwYjM1MzUxNGJjOWFmODZmNzlkZjQ3Omg6VDpU |
| Full analysis: | https://app.any.run/tasks/07aed8bb-c2e4-40c2-88e0-2033d21c537d |
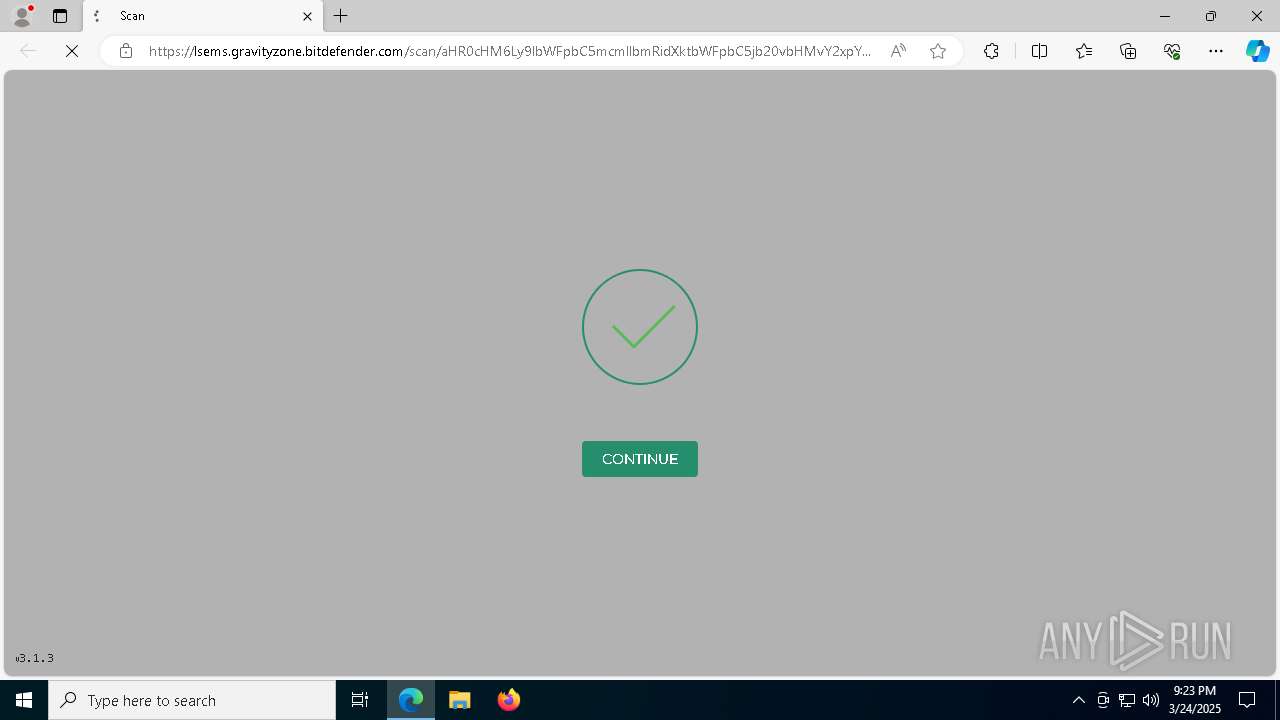
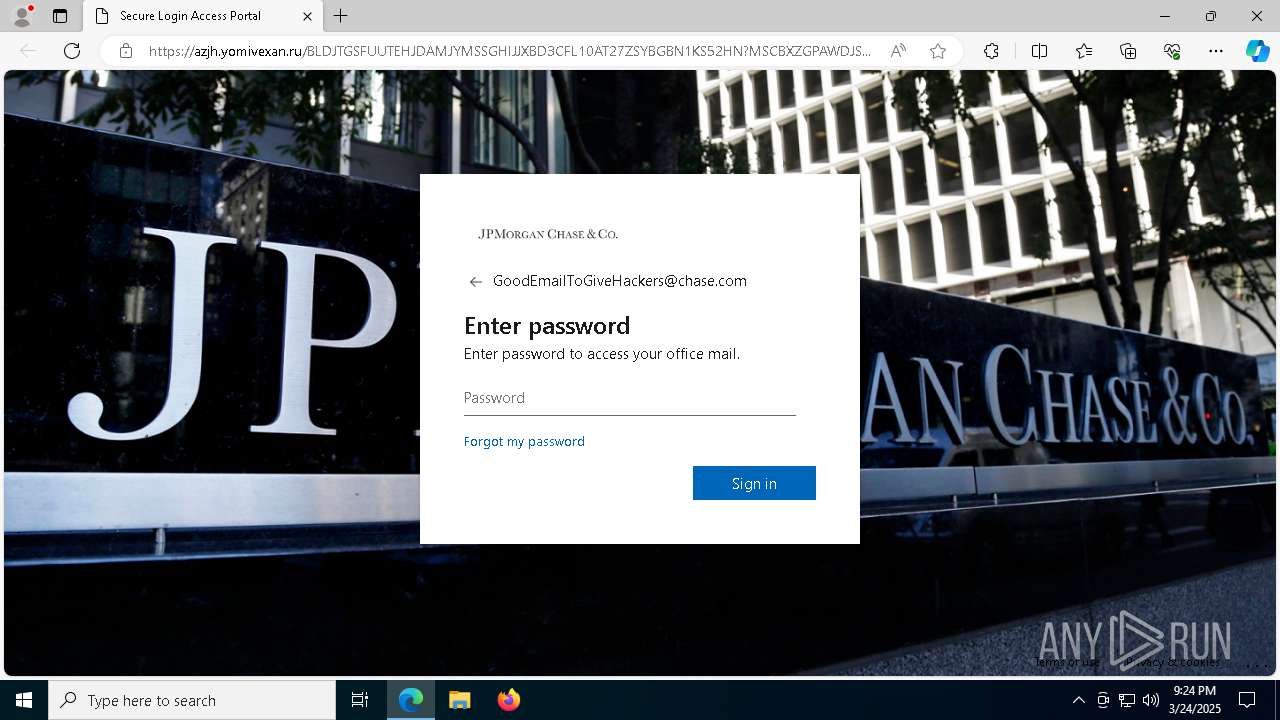
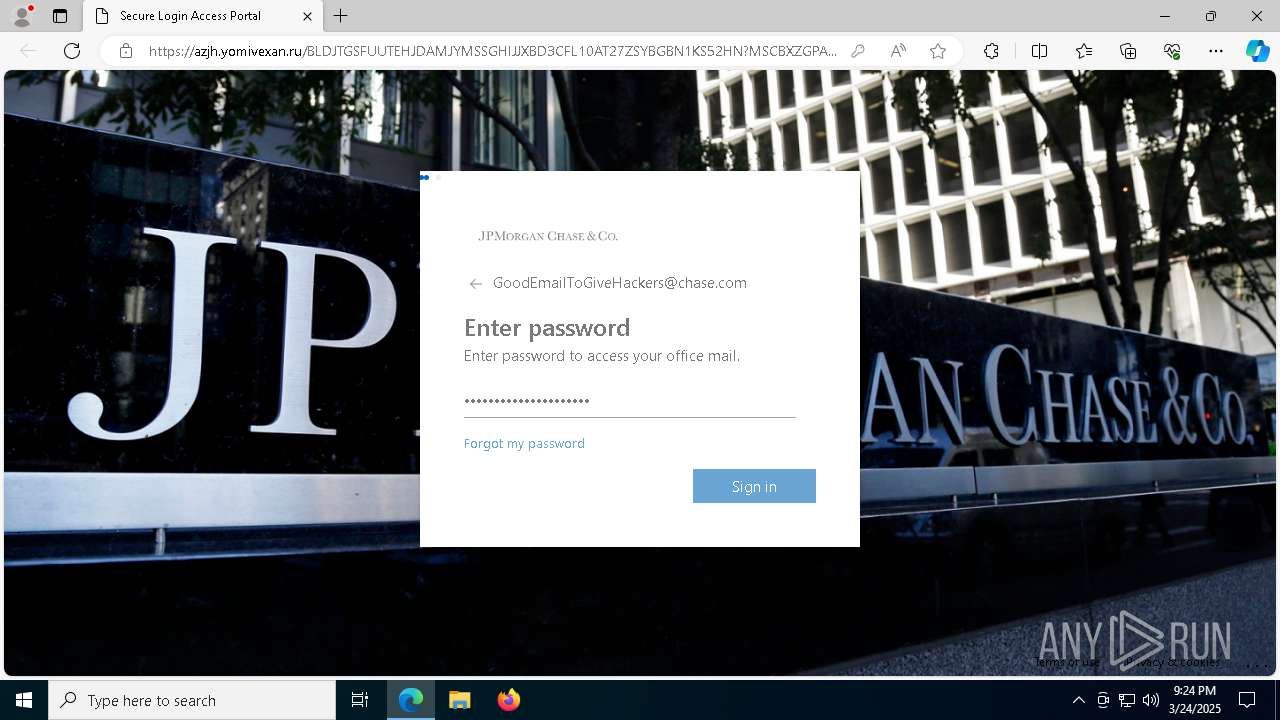
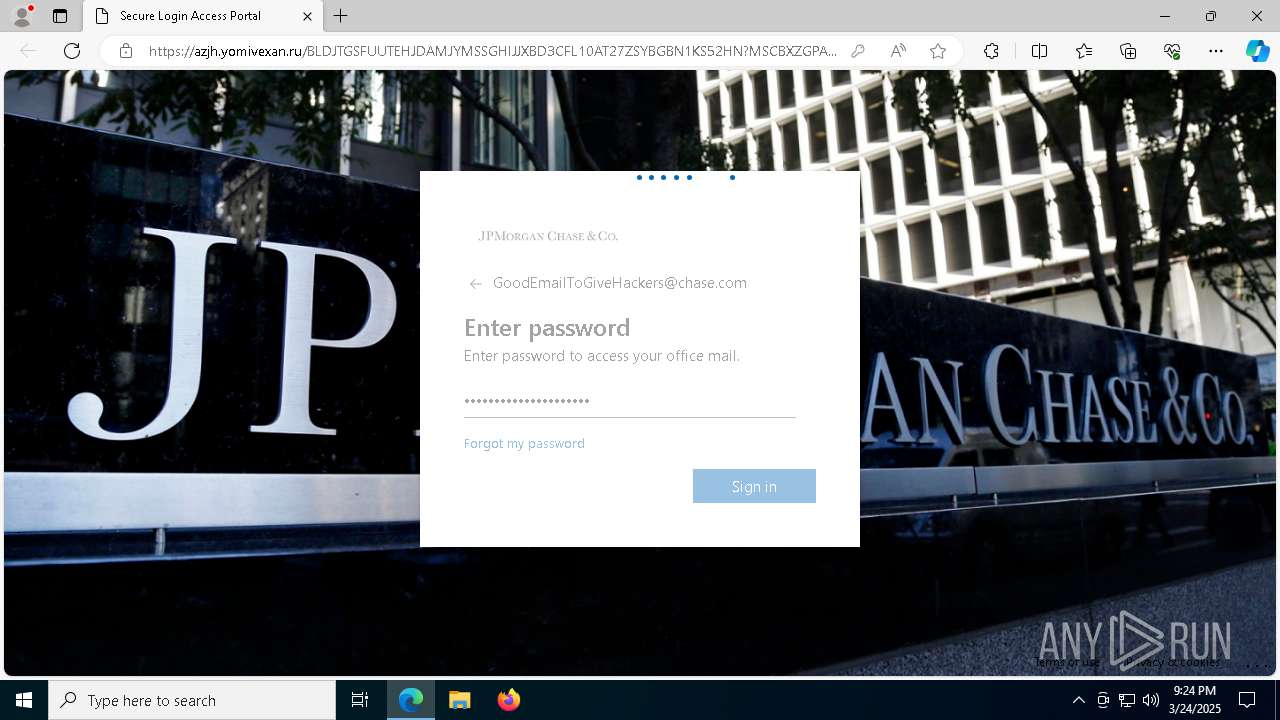
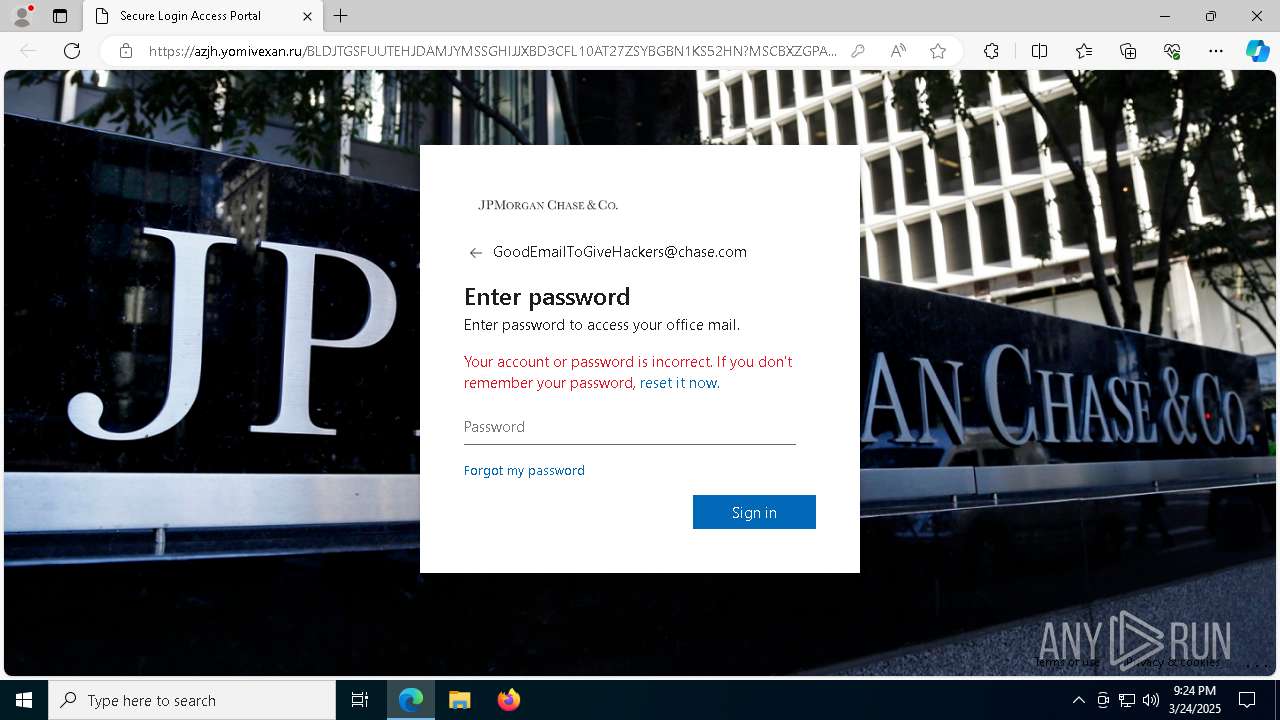
| Verdict: | Malicious activity |
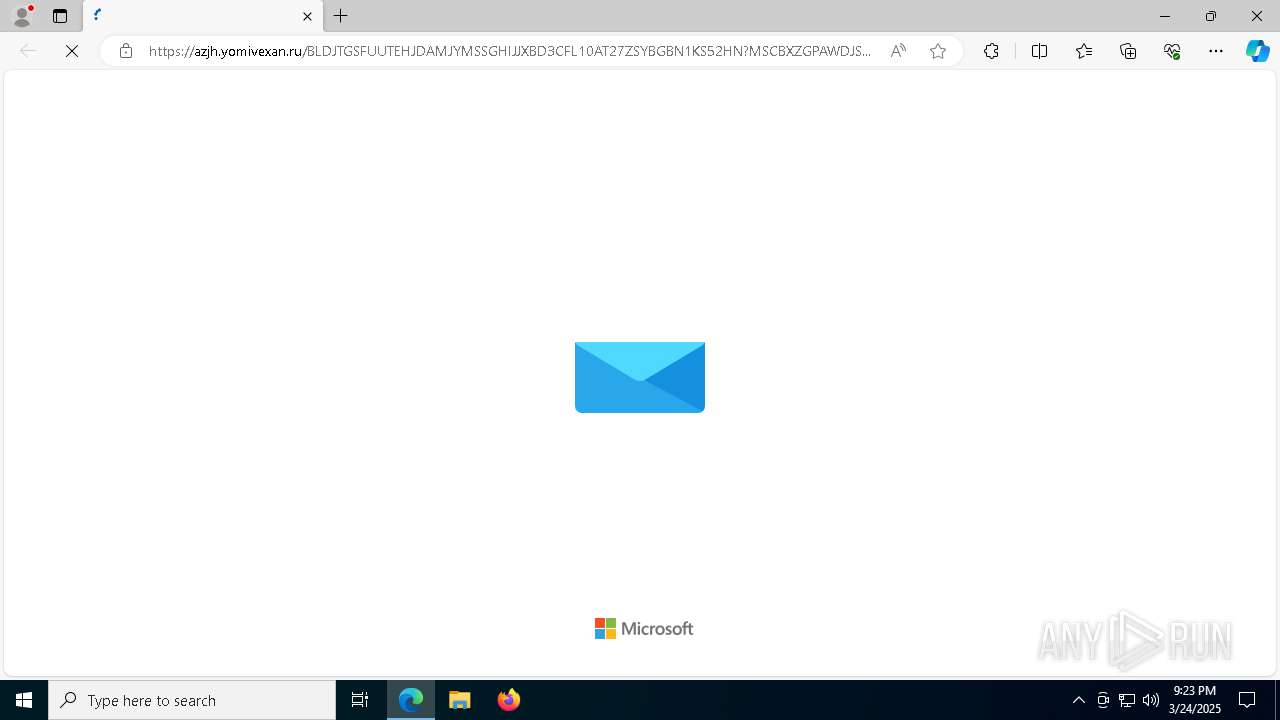
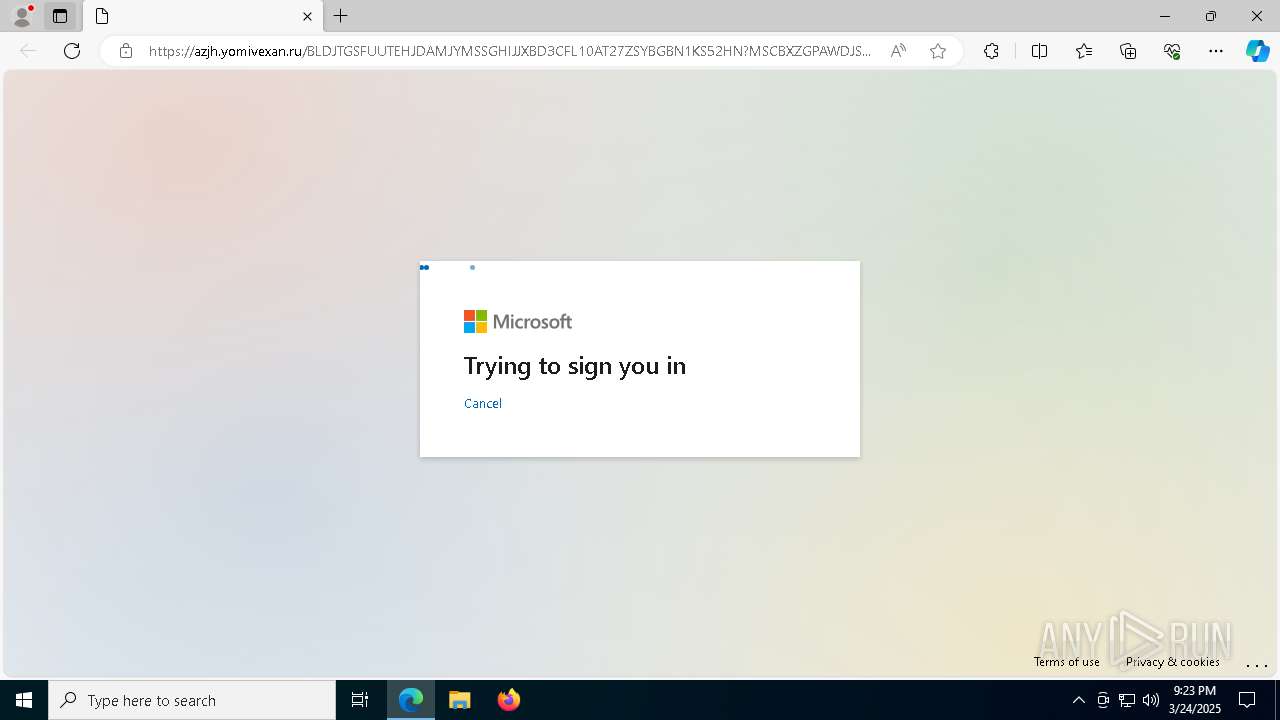
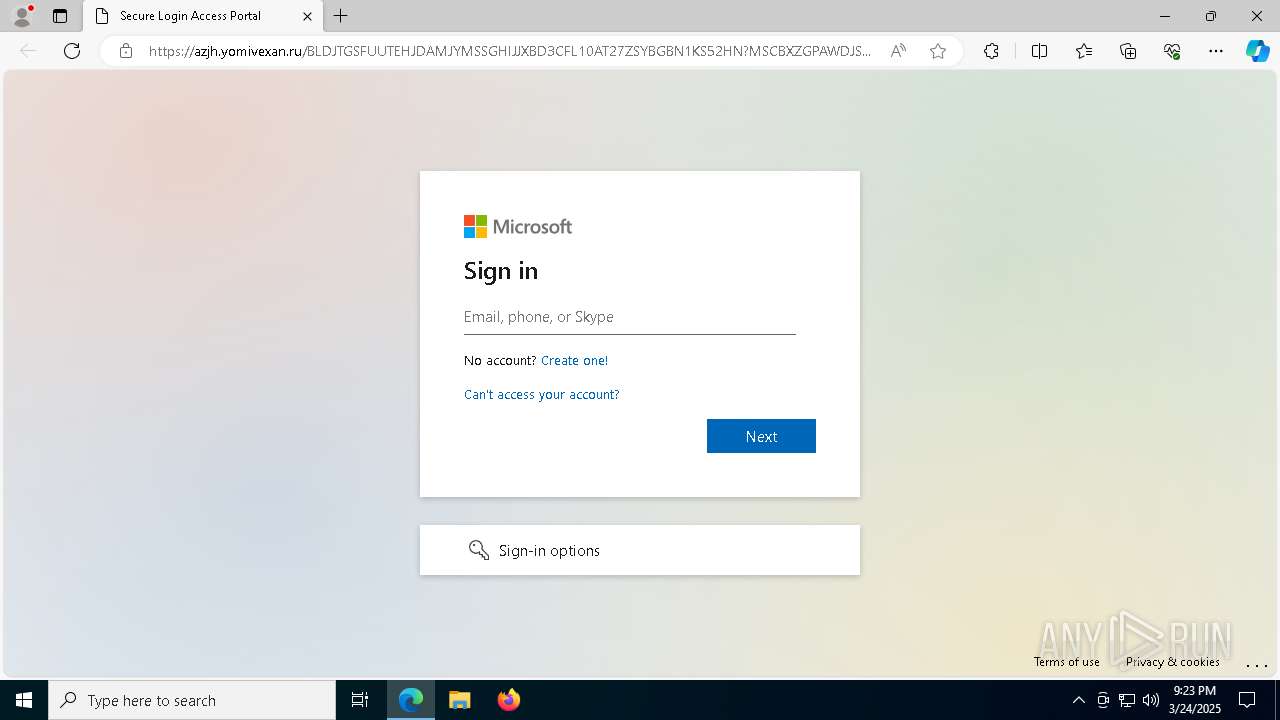
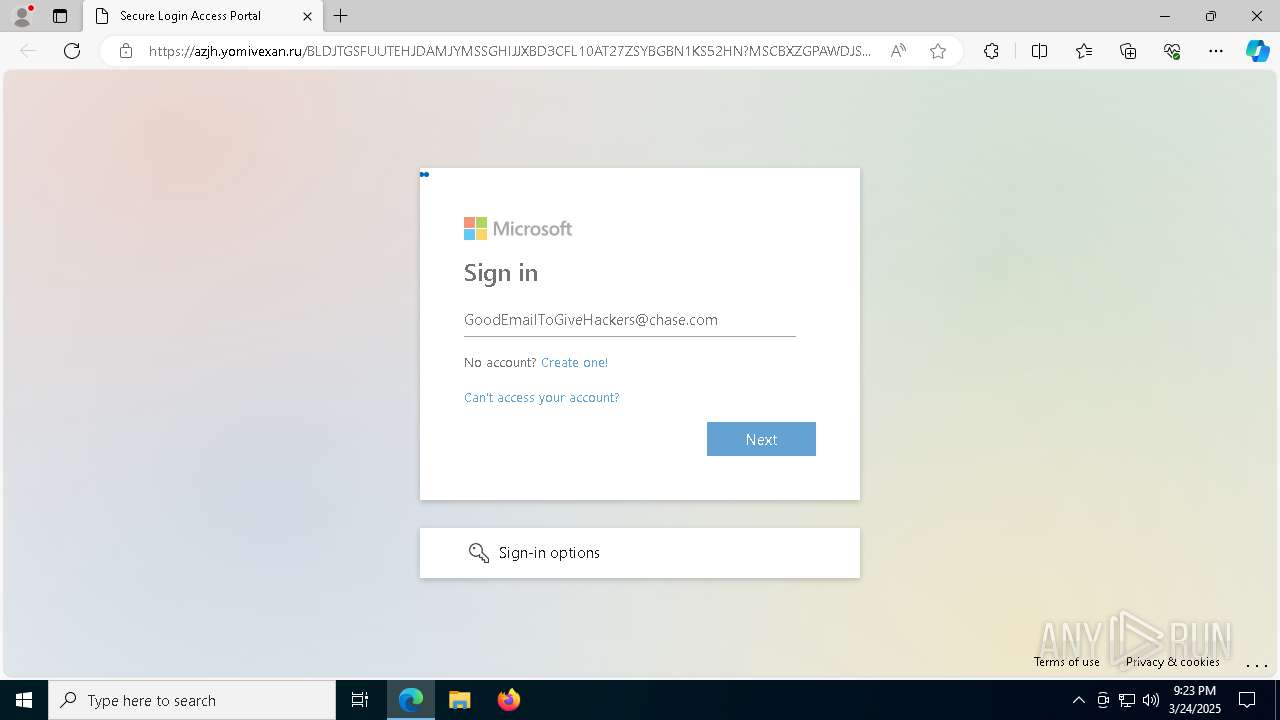
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | March 24, 2025, 21:23:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9976E5CD16D630CB6F910A6977796933 |
| SHA1: | CA19190452F5ED79CDE2E82927712F93787DA741 |
| SHA256: | 07D3D9DD22FC86CEFFF237B40C4FB3B91CB878ED6DF18E840B8BF38CAA03207A |
| SSDEEP: | 48:Fk22XC5Dny4MobyYEwzZ8nVteHW5NY0WALwpr80w:m25MdpSZ8nVtt5NY0xd0w |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7336)
SUSPICIOUS
No suspicious indicators.INFO
Reads Environment values
- identity_helper.exe (PID: 6512)
Checks supported languages
- identity_helper.exe (PID: 6512)
Reads the computer name
- identity_helper.exe (PID: 6512)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8952)
- BackgroundTransferHost.exe (PID: 8372)
- BackgroundTransferHost.exe (PID: 9176)
- BackgroundTransferHost.exe (PID: 8564)
- BackgroundTransferHost.exe (PID: 8776)
Reads the software policy settings
- slui.exe (PID: 496)
- BackgroundTransferHost.exe (PID: 8776)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8776)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8776)
Application launched itself
- msedge.exe (PID: 1184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
167
Monitored processes
36
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 496 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://protect.checkpoint.com/v2/r01/___https://lsems.gravityzone.bitdefender.com/xhfsdfMW5hMR*~*QDcqg1KugH/rhrqqgrWni2pyg1KugH/og75AgMRA37Cu37x!i2GzU2ZBRIJzR2iCW8uXhEGt12GDVsqzW1SPS135WYiLZE0SSK4AhpWv0LOL41CEW5iqYn5DVrOzSZCQ3si0hrm0f8070pxyRp37h0qff2WoZMq3WpK4Yruo0KGLT0qxiriR4H5DWpiAi5yoZEOfSMqzfE01YJuRgLt9g7yRgK4fYqOQfD5DWohEZqSTW1OYYEm6RZcHTIOTRZ/1ir0f1oSXS5bEY7Z5R7cBj0Wp414P0pOXV04LW2q9XIi5TJSNh0GmV64TRZquR2lCV5qwgsGMhqiMTJuYjYOwW508V1i0RKqU0JiP48K7W6KLZs4wfMWZZJCJ01KtS6GrX7Cr0pu91IWJ014Zi0OPhpuYiKWRYLyI0Z6B0oi900SHSsWViEO8g8WvXEKKTKW5XLuH37y84KSYhK4IWIRDiJ0NXs0H0puK4qWH0pi8ZLcQjZ4I1p6yhJmTQYOH4IKmR6OJS84VQYOLQYOH1IGXgZyoh8qBX8G3XLpDi2SmhpuVSr95iIm0TMKBYJSHj20L0IN74pyNTIWBjry*~*g6qIXriCjpu4SLRB4Mh5ipx6XJ4DXH5DWpioV1OfjJpChsVD32GWW2S8jrJ50JqC0r/vQYOL41iIXE0Qh6iQXK0pV2S0gL4D4ZxyRp3EipKLfZu8fYOzjrSO1JqMTIirXYq*~*VrcogIG8gsOIf5C8grywfJcO3pq13p0xWsuq3qK3fJuSREqAT1cHfMZyRpOVjquJ1ZB9gIWM01/JV8K9Z2SpSJSqY7OyZKl8hEiYZ00RS7yC1YSmirKA3ESN016LXsZDW0iLTJi6WoZyRp4rX2SRjL4Hg6KnX8KKg1i/1sqAZoG3gJq31L09h7/Ogrux07/mQYOL1JiZQYOLZq0rhJyL1Ly/0qqmh7mLV5BCh8h9X80NXp/qQYOHhs37ZqOu11JEV2hyR5VyR5VEY2mA2EWBf1mNj1iTZ5NBhoqX4qhB4IV5Y5mG1ZmGg7K0W1iHiMGOQYOLgrh5hq0N4Li3goiZXrh542JEXq4Pf0Grh6u4YYS/36V6Z6uoZJ/fRKOqTJWqS50yfs4tZISpYIKHg2KCf7OSgJcIXK3DZ7/uQYOLS1qO42uXZ8JD1qWwXIKpjYV7XYSPR7m1W5i2iMKuWqR/W1y4ZJKz0pZ61LCq0MK8h2qsQYOLWIh9hqGAiLiS11iJYrc3jr6PfYlyRp4GR7RBXpy9QYOLYL5=dbFKaGcIbG/GKHK*~*9*/2*H7aJaaIbI6K7ccF/bFHKI*~*J9c/65Ja6F8F886JHIHa/8K9?h=6&fru;n=6&fru;ithx=6___.YzJ1OnNlcXVhbGNvcnA6YzpvOjI2Mzg4MTdmNDQzNWRjNDY2Nzg5NzMyOWZmYzFkMWMyOjc6ODVjNToxOTQ2YTEzYTcxMDBkNDE0MzFjMmI1Mjk2MmEwYjRmNjU0OTBlNWJiYmEwYjM1MzUxNGJjOWFmODZmNzlkZjQ3Omg6VDpU" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7216 --field-trial-handle=2376,i,11509955955452783072,16299115676599597318,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --mojo-platform-channel-handle=5852 --field-trial-handle=2376,i,11509955955452783072,16299115676599597318,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2600 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4268 --field-trial-handle=2376,i,11509955955452783072,16299115676599597318,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=6708 --field-trial-handle=2376,i,11509955955452783072,16299115676599597318,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 5592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=6244 --field-trial-handle=2376,i,11509955955452783072,16299115676599597318,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
Total events
5 850
Read events
5 796
Write events
36
Delete events
18
Modification events
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4CFB667EB38F2F00 | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E93F757EB38F2F00 | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C84D2B27-5BDA-4146-BA05-FA38DF201261} | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FADE2E52-F63D-48B8-B6C8-628F4E4CAAD4} | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {919632B7-C0F2-452C-91B2-F72D46547648} | |||
| (PID) Process: | (1184) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EE73F146-451D-47F9-8FB1-C5B1E9EAAF9E} | |||
Executable files
6
Suspicious files
123
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10f500.TMP | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10f500.TMP | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10f500.TMP | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10f510.TMP | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10f57d.TMP | — | |
MD5:— | SHA256:— | |||
| 1184 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
120
DNS requests
129
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.157:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 302 | 34.102.239.211:80 | http://email.double.serviceautopilot.com/c/eJwEwD1SxCAUAODThA4GHv8FhU3GykYvALzHBCdZIpvdcT29Xx3HmW-vjimX5ottkhdSlpvoGg8gC9fOymAwFgqeYWouQnCMkvIGrJPOWUZH7nvHVLMH0tVxZVFyU2vjkRpyjRhbLdW1YtiWoscYoFmbDUoIHjVoaqWZFnQtaFhPIMFKDUqB9saKYkB51xRVicrLuBiJ41F2Eneaz14pP65x9n1coo6D7Wm7rvO-6LcF1gXW_Pe9idc4-pN-803MxwLrz_z4_HpfYGUz1W32-zXOjabI-55vi5HznENcVDf2TPAfAAD__1MYWZU | unknown | — | — | whitelisted |
— | — | GET | 304 | 184.30.131.245:80 | http://cacerts.digicert.com/DigiCertGlobalG2TLSRSASHA2562020CA1-1.crt | unknown | — | — | whitelisted |
1600 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8776 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8412 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743001785&P2=404&P3=2&P4=B78BZUIBo5CjTh87LnCniEd%2fTRKD4c%2fYxqWTxPnaDBK33KV20%2bJCwTAA7DasZ%2fhAXvsSXKxxX2zwk4yUIKDT5g%3d%3d | unknown | — | — | whitelisted |
5204 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8412 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743001785&P2=404&P3=2&P4=B78BZUIBo5CjTh87LnCniEd%2fTRKD4c%2fYxqWTxPnaDBK33KV20%2bJCwTAA7DasZ%2fhAXvsSXKxxX2zwk4yUIKDT5g%3d%3d | unknown | — | — | whitelisted |
8412 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743001785&P2=404&P3=2&P4=B78BZUIBo5CjTh87LnCniEd%2fTRKD4c%2fYxqWTxPnaDBK33KV20%2bJCwTAA7DasZ%2fhAXvsSXKxxX2zwk4yUIKDT5g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.157:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 40.126.31.69:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 40.126.31.69:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1184 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
protect.checkpoint.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
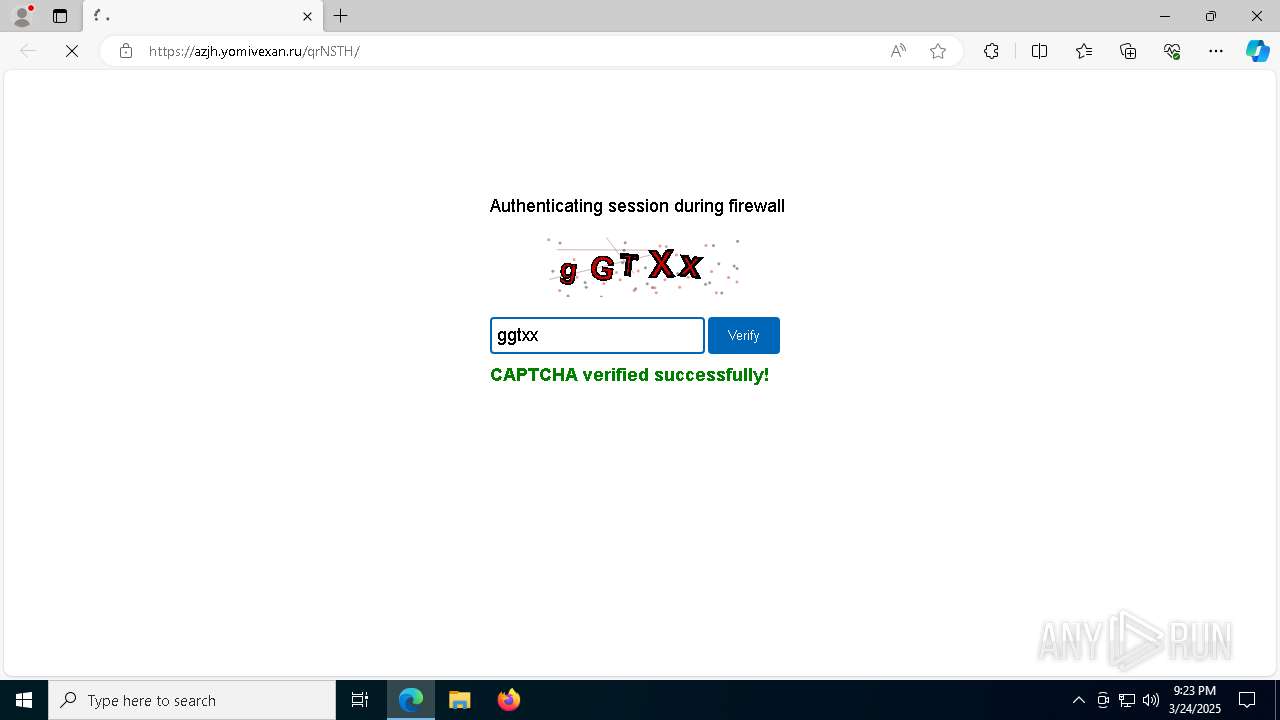
7336 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Tycoon2FA`s Phishing-Kit domain by CrossDomain ( .yomivexan .ru) |
7336 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Tycoon2FA`s Phishing-Kit domain by CrossDomain ( .yomivexan .ru) |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4 ETPRO signatures available at the full report