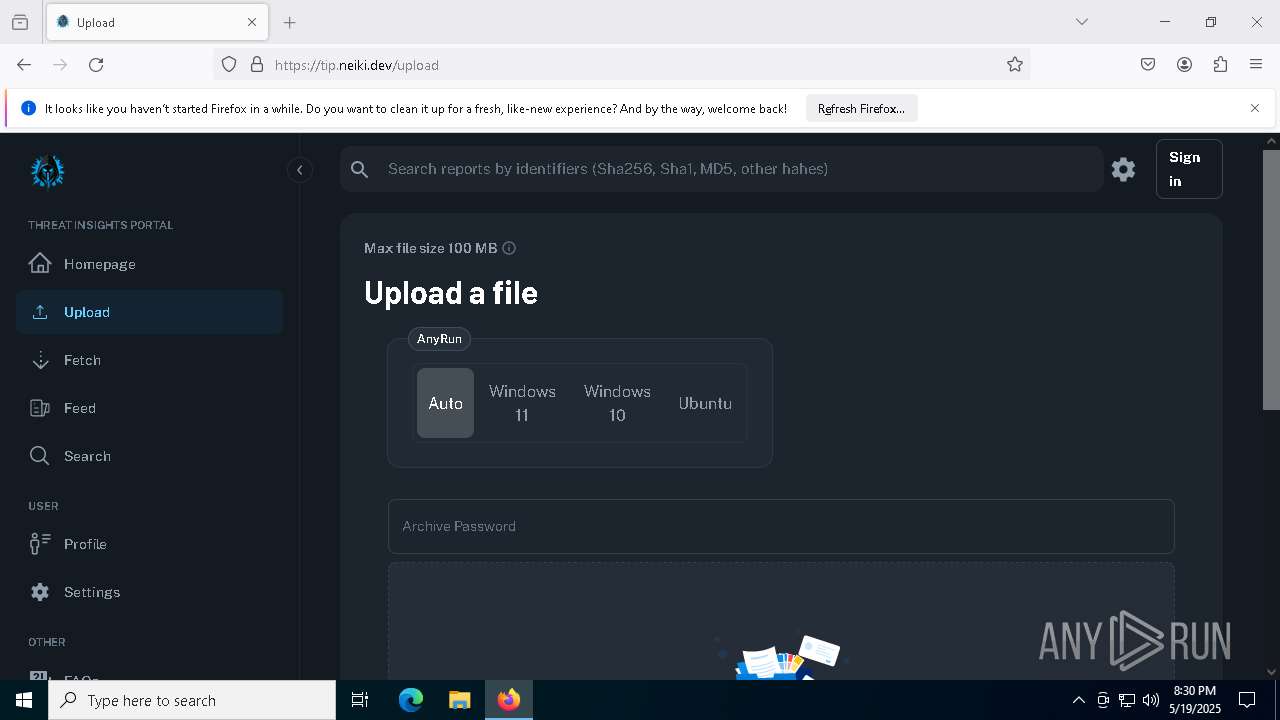
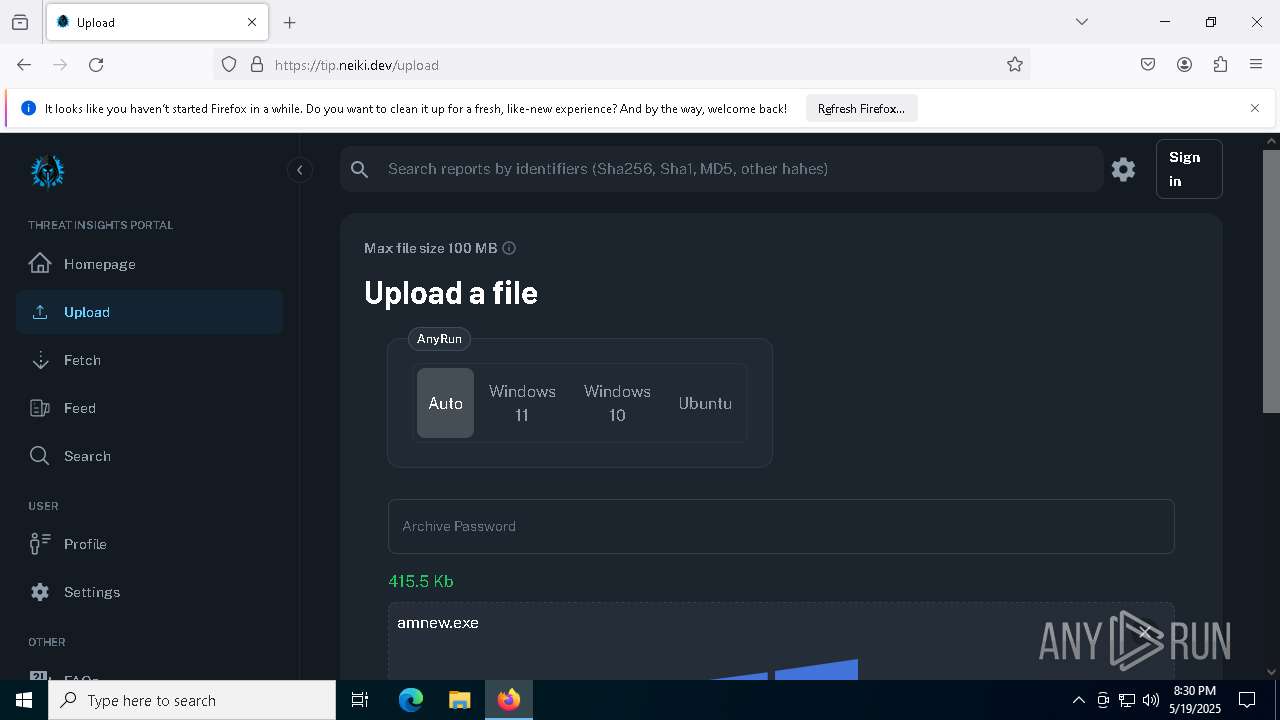
| File name: | amnew.exe |
| Full analysis: | https://app.any.run/tasks/0dfce99f-1ba7-4624-80c0-ec8d390ccf2b |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 19, 2025, 20:29:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 14BCF4728388BDCD9C6AFDE0C9792B85 |
| SHA1: | D6D47A5EA667A84098C2500FB35C6B28845AA94D |
| SHA256: | 07CF56CD893705BC40A0F27C7575E4E78798098A681A1C88A7F67576101A6821 |
| SSDEEP: | 6144:XS1FBY5lPBd20rxuTwKEA2lLlB1HM6bSXikT7Gtht:H5RBLQkKEAQxB1s6GXiMet |
MALICIOUS
AMADEY mutex has been found
- amnew.exe (PID: 5404)
- saren.exe (PID: 6620)
- saren.exe (PID: 7020)
AMADEY has been detected (SURICATA)
- saren.exe (PID: 6620)
Connects to the CnC server
- saren.exe (PID: 6620)
AMADEY has been detected (YARA)
- saren.exe (PID: 6620)
SUSPICIOUS
Reads security settings of Internet Explorer
- amnew.exe (PID: 5404)
- saren.exe (PID: 6620)
Executable content was dropped or overwritten
- amnew.exe (PID: 5404)
Starts itself from another location
- amnew.exe (PID: 5404)
Contacting a server suspected of hosting an CnC
- saren.exe (PID: 6620)
Connects to the server without a host name
- saren.exe (PID: 6620)
The process executes via Task Scheduler
- saren.exe (PID: 7020)
There is functionality for enable RDP (YARA)
- saren.exe (PID: 6620)
There is functionality for taking screenshot (YARA)
- saren.exe (PID: 6620)
INFO
Process checks computer location settings
- amnew.exe (PID: 5404)
Create files in a temporary directory
- amnew.exe (PID: 5404)
Reads the computer name
- amnew.exe (PID: 5404)
- saren.exe (PID: 6620)
Checks supported languages
- amnew.exe (PID: 5404)
- saren.exe (PID: 6620)
- saren.exe (PID: 7020)
Checks proxy server information
- saren.exe (PID: 6620)
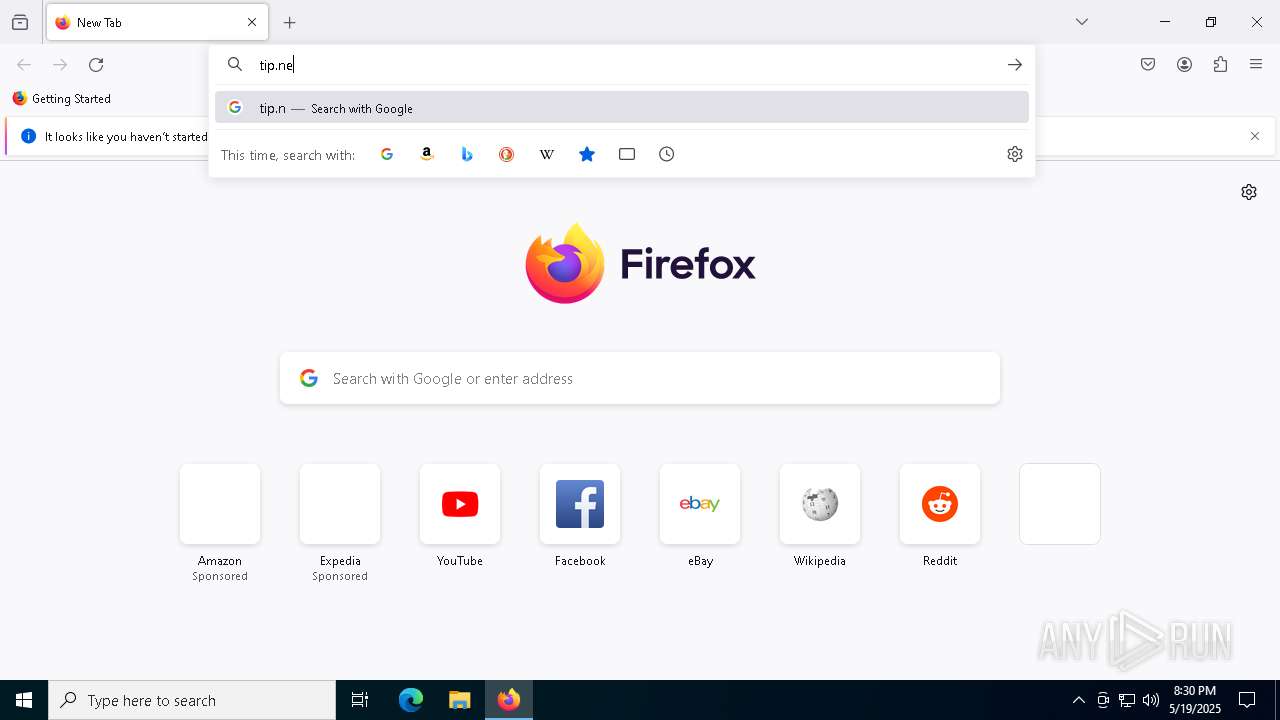
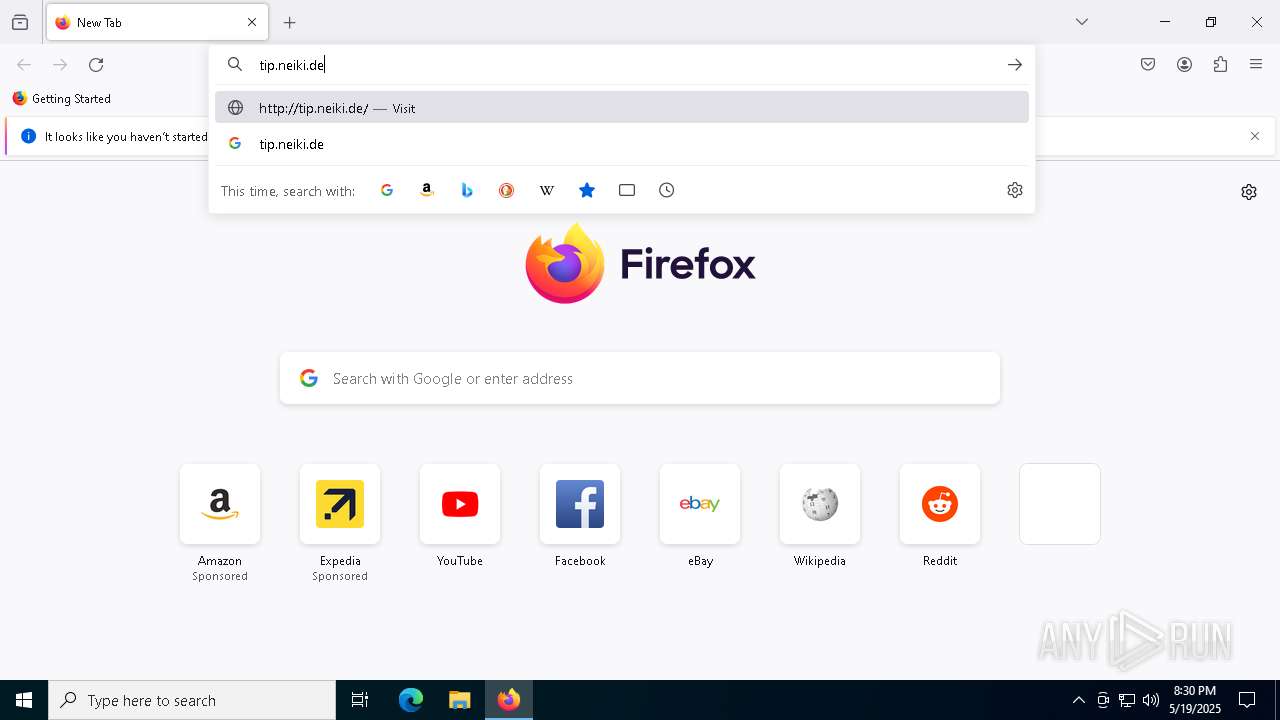
Application launched itself
- firefox.exe (PID: 5392)
- firefox.exe (PID: 1616)
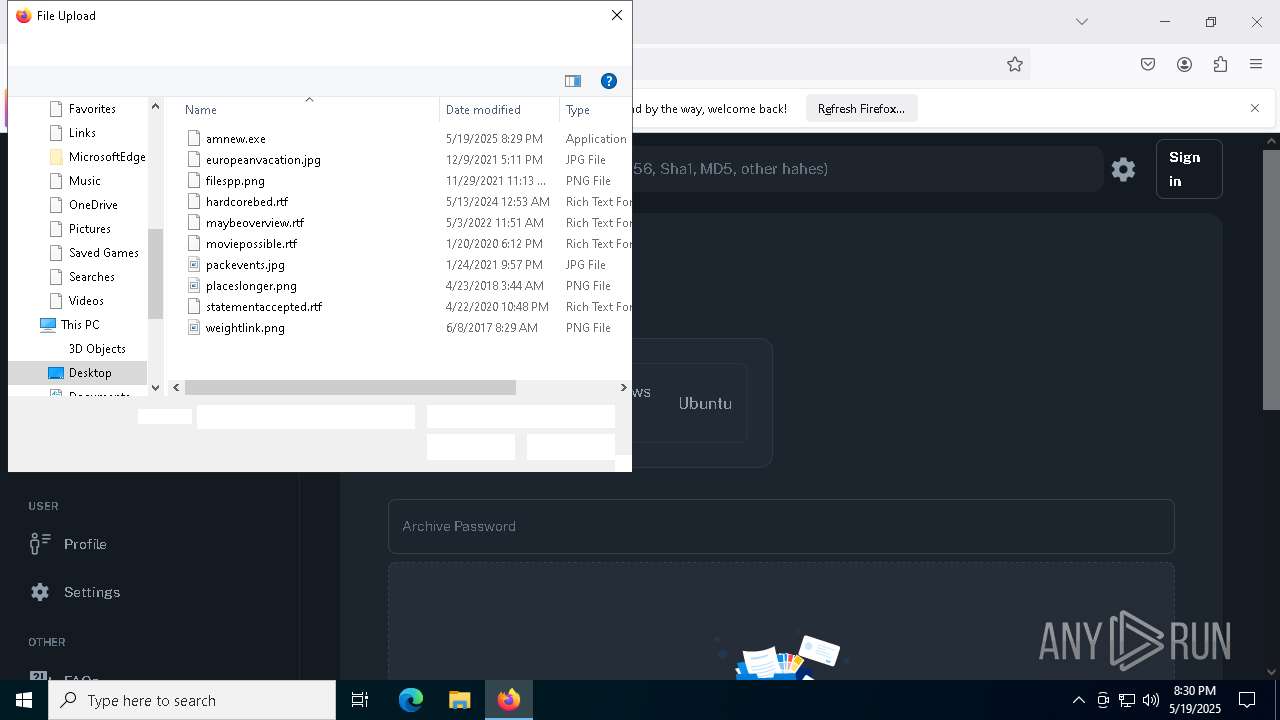
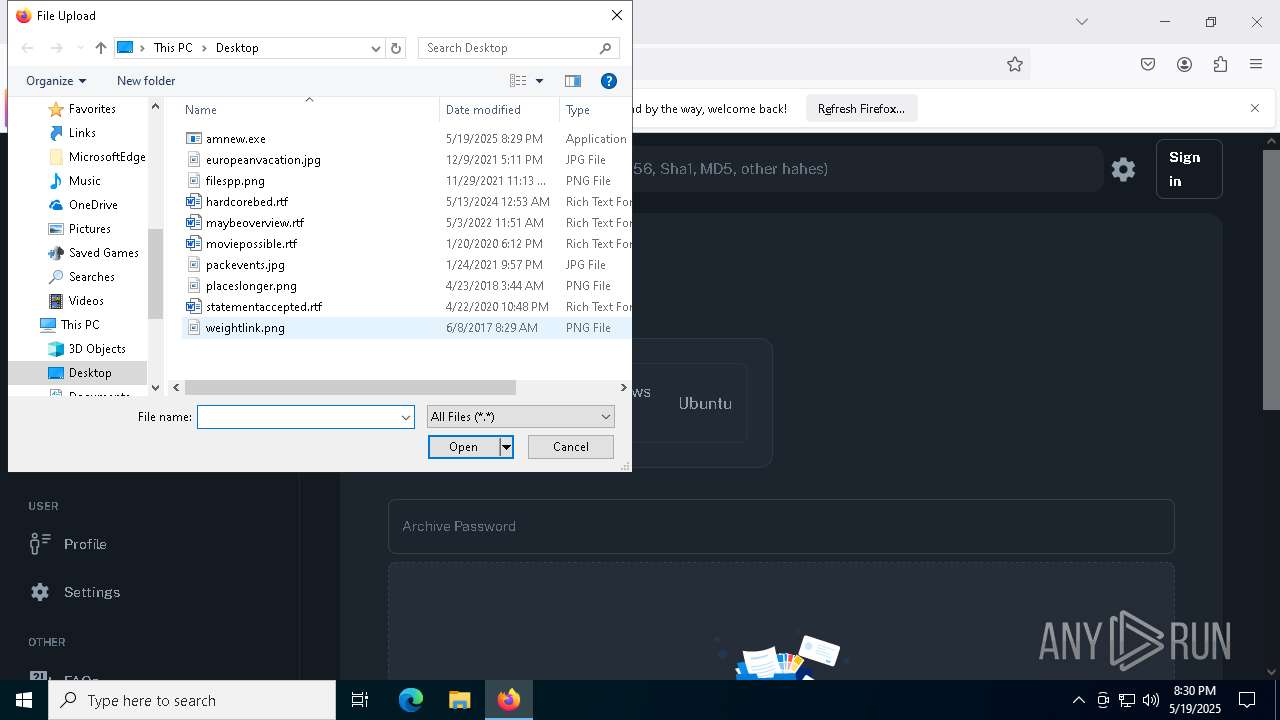
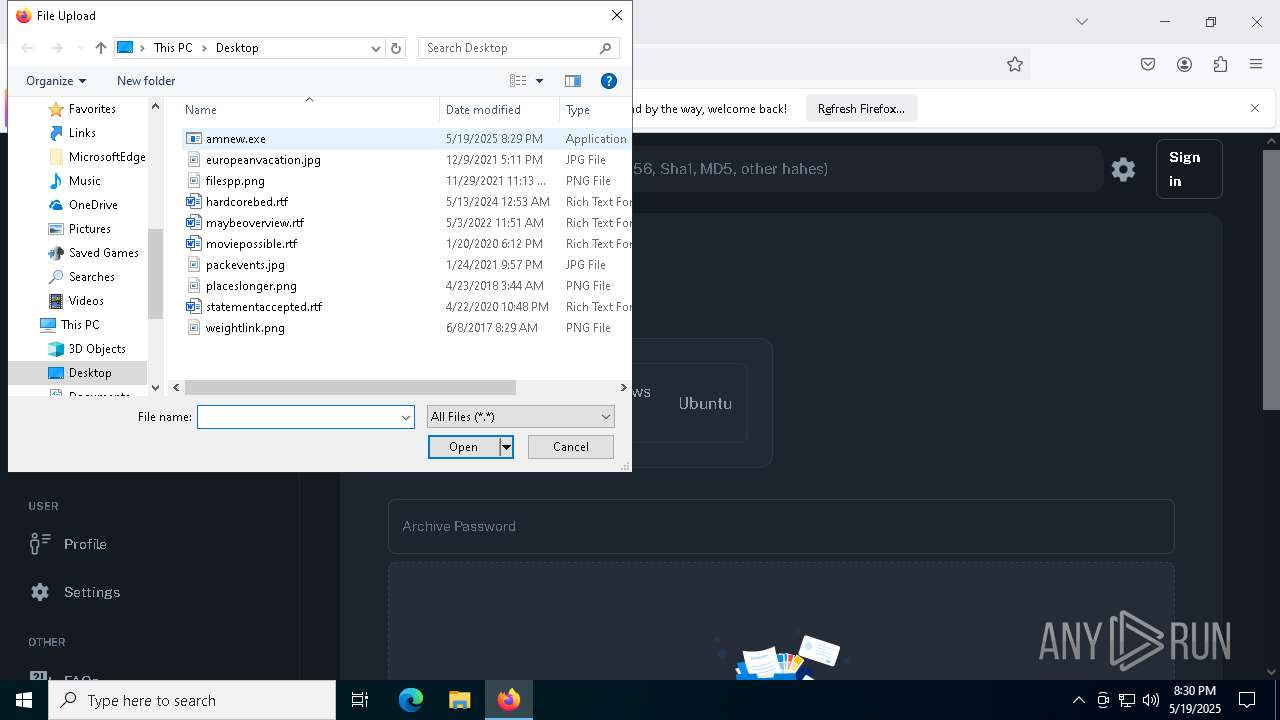
Manual execution by a user
- firefox.exe (PID: 5392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(6620) saren.exe
C277.83.207.69
URLhttp://77.83.207.69/rob75u9v/index.php
Version5.34
Options
Drop directory02106dbc20
Drop namesaren.exe
Strings (125)lv:
msi
Kaspersky Lab
av:
|
#
"
\App
00000422
dm:
Powershell.exe
ProgramData\
ps1
rundll32
http://
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
dll
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
id:
VideoID
cred.dll|clip.dll|
0000043f
cmd
00000423
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
-executionpolicy remotesigned -File "
2022
------
2016
og:
\0000
02106dbc20
CurrentBuild
2019
:::
S-%lu-
" && timeout 1 && del
ProductName
Panda Security
ESET
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/k
+++
?scr=1
Doctor Web
GET
SYSTEM\ControlSet001\Services\BasicDisplay\Video
/quiet
.jpg
saren.exe
vs:
sd:
rundll32.exe
"taskkill /f /im "
pc:
random
=
360TotalSecurity
<d>
wb
Content-Type: multipart/form-data; boundary=----
Startup
Norton
&& Exit"
os:
https://
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
/rob75u9v/index.php
2025
Avira
%-lu
zip
POST
"
Content-Type: application/octet-stream
Rem
77.83.207.69
------
5.34
<c>
clip.dll
AVAST Software
\
shell32.dll
" && ren
e3
kernel32.dll
DefaultSettings.XResolution
d1
DefaultSettings.YResolution
r=
cred.dll
--
GetNativeSystemInfo
-%lu
ComputerName
&unit=
Keyboard Layout\Preload
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
ar:
Sophos
%USERPROFILE%
exe
e1
e2
st=s
Programs
0123456789
un:
rb
bi:
abcdefghijklmnopqrstuvwxyz0123456789-_
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
cmd /C RMDIR /s/q
Bitdefender
-unicode-
AVG
WinDefender
&&
shutdown -s -t 0
Comodo
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
Main
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:17 14:01:41+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 317952 |
| InitializedDataSize: | 123392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x28c3a |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
146
Monitored processes
19
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1616 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2100 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4220 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2800 -childID 1 -isForBrowser -prefsHandle 2820 -prefMapHandle 2292 -prefsLen 31447 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {66fe7e80-4eba-434c-821c-f191ee6d99c9} 1616 "\\.\pipe\gecko-crash-server-pipe.1616" 132a51a2f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4448 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1920 -parentBuildID 20240213221259 -prefsHandle 1856 -prefMapHandle 1848 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {d06c28ab-7d7c-401b-93c1-24b37a435983} 1616 "\\.\pipe\gecko-crash-server-pipe.1616" 132a04eae10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 4776 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2120 -prefMapHandle 2076 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e4a00481-46f5-4acd-8340-f69905c89276} 1616 "\\.\pipe\gecko-crash-server-pipe.1616" 13293680b10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5392 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5404 | "C:\Users\admin\Desktop\amnew.exe" | C:\Users\admin\Desktop\amnew.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6480 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | "C:\Users\admin\AppData\Local\Temp\02106dbc20\saren.exe" | C:\Users\admin\AppData\Local\Temp\02106dbc20\saren.exe | amnew.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
Amadey(PID) Process(6620) saren.exe C277.83.207.69 URLhttp://77.83.207.69/rob75u9v/index.php Version5.34 Options Drop directory02106dbc20 Drop namesaren.exe Strings (125)lv: msi Kaspersky Lab av: | # " \App 00000422 dm: Powershell.exe ProgramData\ ps1 rundll32 http:// Content-Disposition: form-data; name="data"; filename=" SOFTWARE\Microsoft\Windows NT\CurrentVersion dll SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders id: VideoID cred.dll|clip.dll| 0000043f cmd 00000423 SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName -executionpolicy remotesigned -File " 2022 ------ 2016 og: \0000 02106dbc20 CurrentBuild 2019 ::: S-%lu- " && timeout 1 && del ProductName Panda Security ESET SOFTWARE\Microsoft\Windows\CurrentVersion\Run /k +++ ?scr=1 Doctor Web GET SYSTEM\ControlSet001\Services\BasicDisplay\Video /quiet .jpg saren.exe vs: sd: rundll32.exe "taskkill /f /im " pc: random = 360TotalSecurity <d> wb Content-Type: multipart/form-data; boundary=---- Startup Norton && Exit" os: https:// SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce /rob75u9v/index.php 2025 Avira %-lu zip POST "
Content-Type: application/octet-stream Rem 77.83.207.69 ------ 5.34 <c> clip.dll AVAST Software \ shell32.dll " && ren e3 kernel32.dll DefaultSettings.XResolution d1 DefaultSettings.YResolution r= cred.dll -- GetNativeSystemInfo -%lu ComputerName &unit= Keyboard Layout\Preload SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders ar: Sophos %USERPROFILE% exe e1 e2 st=s Programs 0123456789 un: rb bi: abcdefghijklmnopqrstuvwxyz0123456789-_ SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\ cmd /C RMDIR /s/q Bitdefender -unicode- AVG WinDefender && shutdown -s -t 0 Comodo 00000419 Content-Type: application/x-www-form-urlencoded /Plugins/ Main | |||||||||||||||
| 7020 | "C:\Users\admin\AppData\Local\Temp\02106dbc20\saren.exe" | C:\Users\admin\AppData\Local\Temp\02106dbc20\saren.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
20 089
Read events
20 047
Write events
41
Delete events
1
Modification events
| (PID) Process: | (6620) saren.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6620) saren.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6620) saren.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1616) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1616) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1616) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (1616) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 010000000000000004000000050000000200000003000000FFFFFFFF | |||
| (PID) Process: | (1616) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\34\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (1616) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
| (PID) Process: | (1616) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\exe |
| Operation: | write | Name: | 2 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D14002E803ACCBFB42CDB4C42B0297FE99A87C6415C003200007E0600B35ABBA32000616D6E65772E65786500440009000400EFBEB35ABBA3B35ABBA32E000000A30D0000000010000000000000000000000000000000DCD2C40061006D006E00650077002E00650078006500000018000000 | |||
Executable files
1
Suspicious files
173
Text files
18
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1616 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1616 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
90
DNS requests
119
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.185:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6620 | saren.exe | POST | 200 | 77.83.207.69:80 | http://77.83.207.69/rob75u9v/index.php | unknown | — | — | malicious |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1616 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6620 | saren.exe | POST | 200 | 77.83.207.69:80 | http://77.83.207.69/rob75u9v/index.php | unknown | — | — | malicious |
1616 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1616 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
1616 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1616 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.185:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6620 | saren.exe | 77.83.207.69:80 | — | Internet Technologies LLC | UA | malicious |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6620 | saren.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
6620 | saren.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
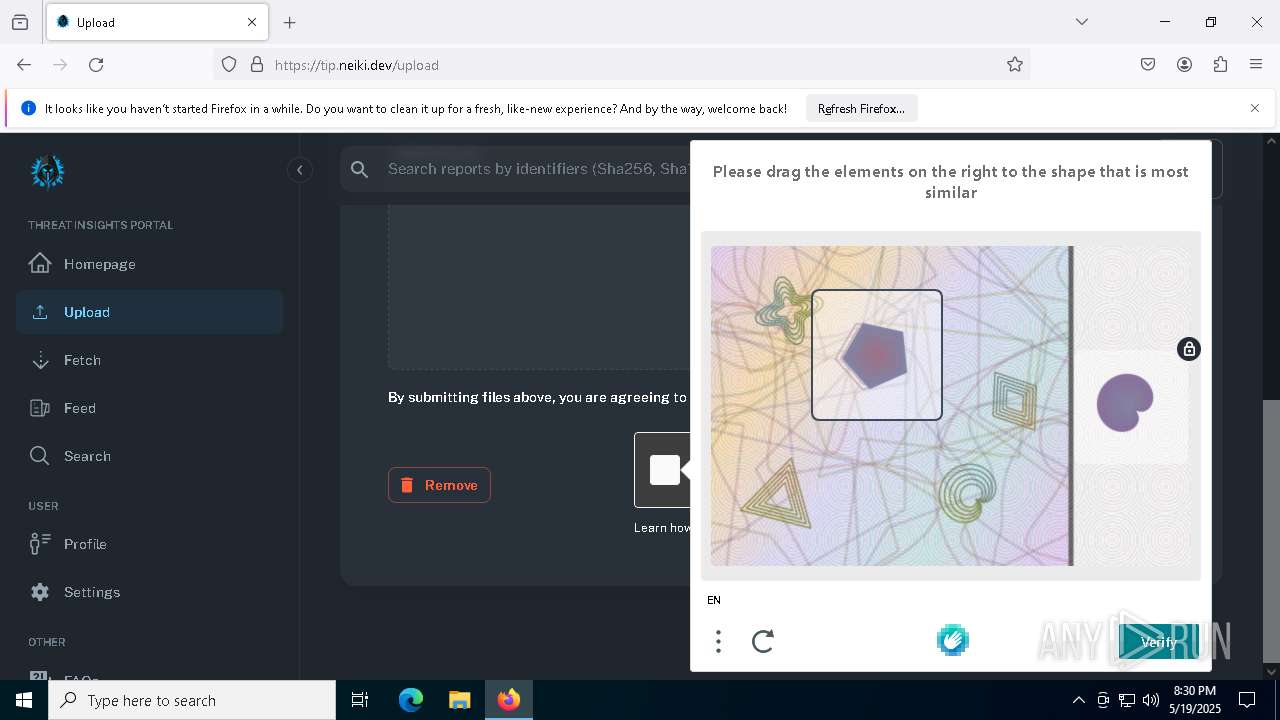
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
6620 | saren.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |