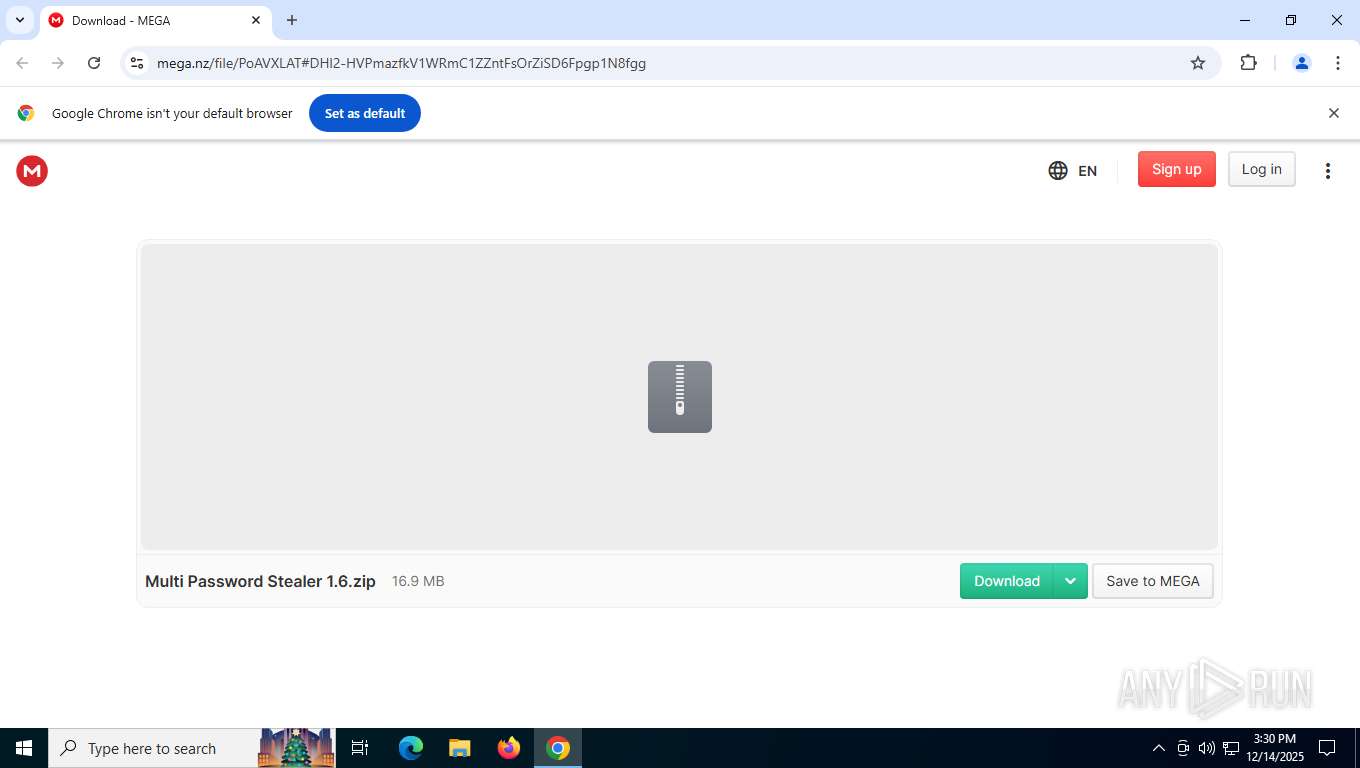
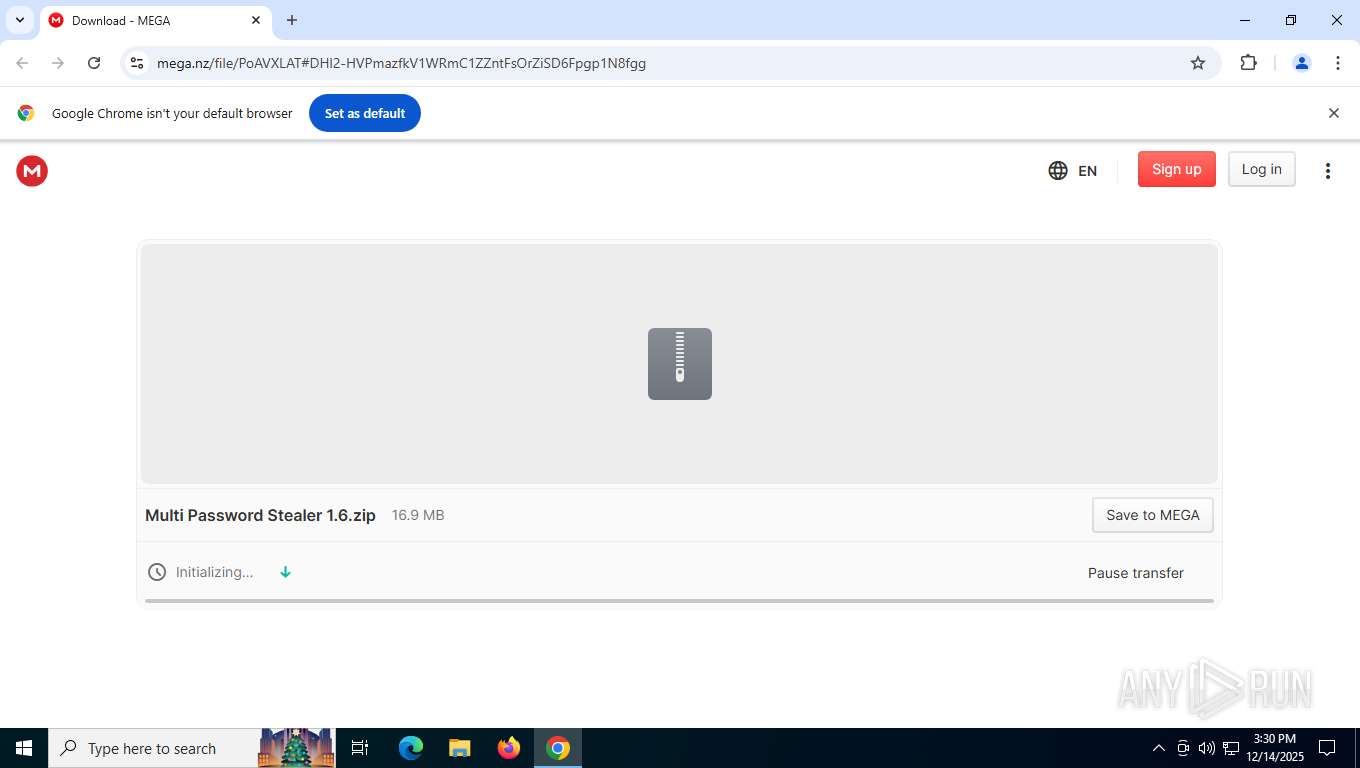
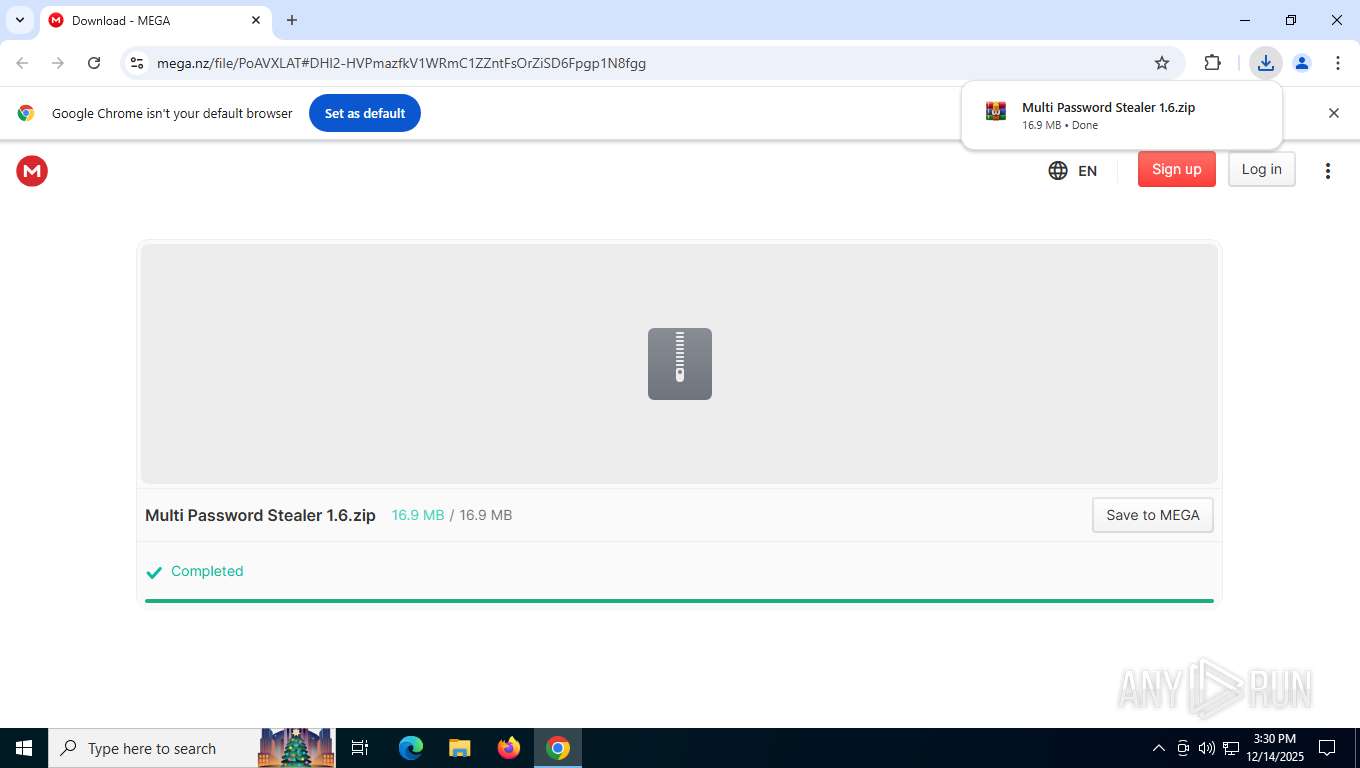
| URL: | https://mega.nz/file/PoAVXLAT#DHl2-HVPmazfkV1WRmC1ZZntFsOrZiSD6Fpgp1N8fgg |
| Full analysis: | https://app.any.run/tasks/4beef2d2-b42f-4ea6-986f-016617fceca9 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
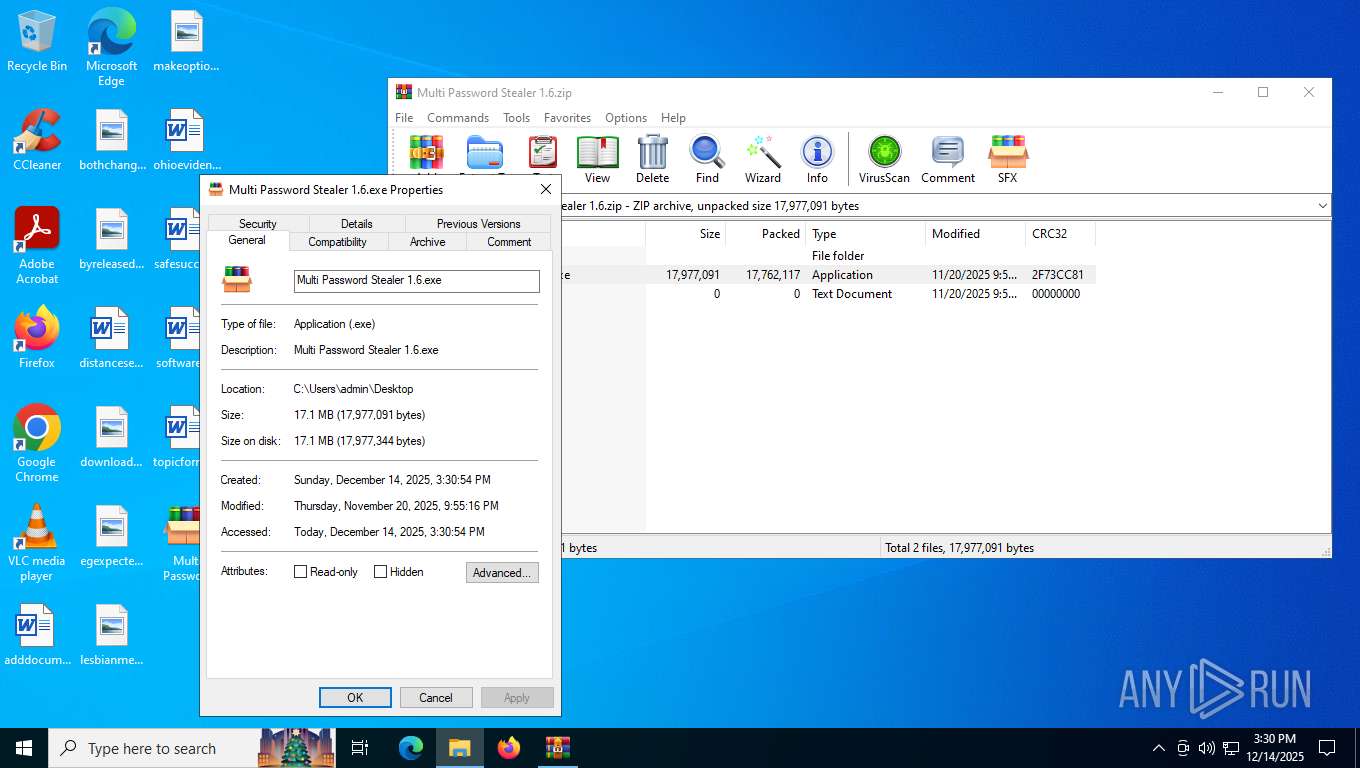
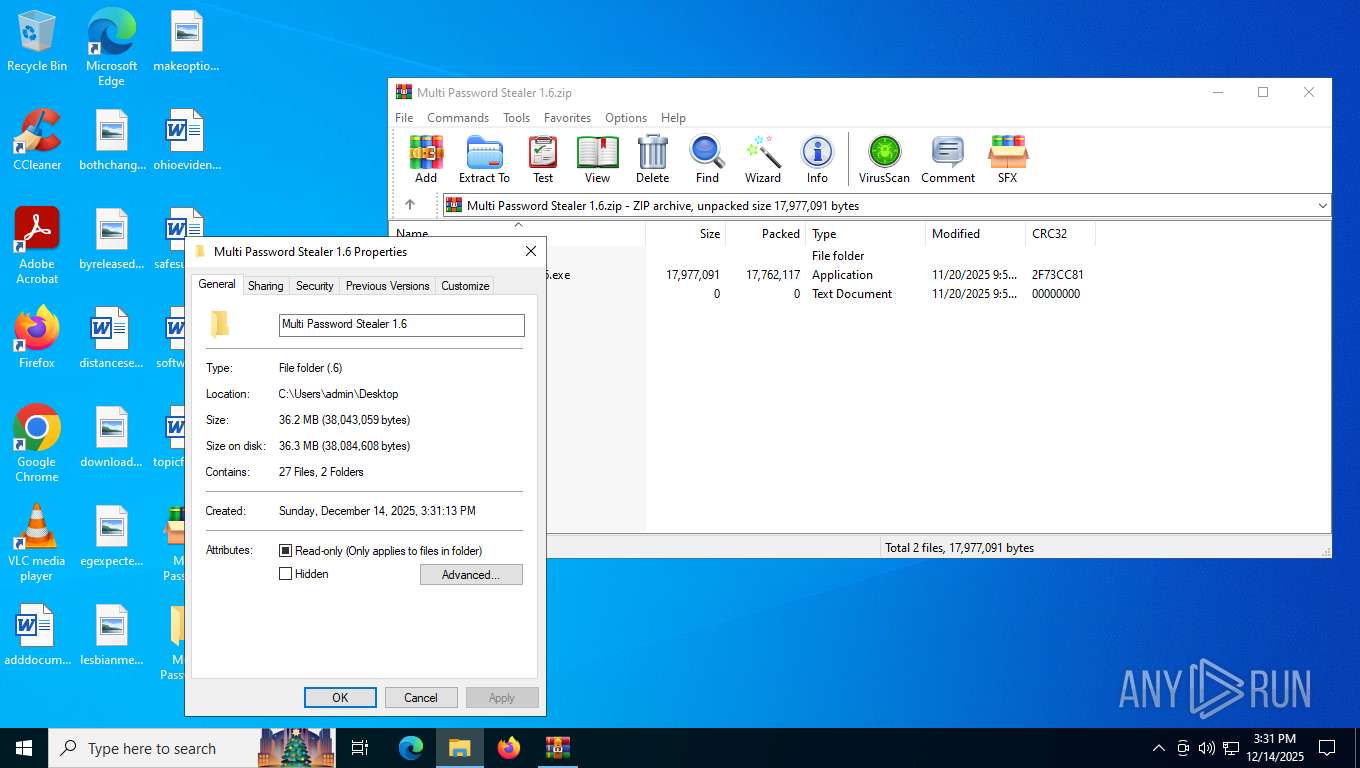
| Analysis date: | December 14, 2025, 15:30:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
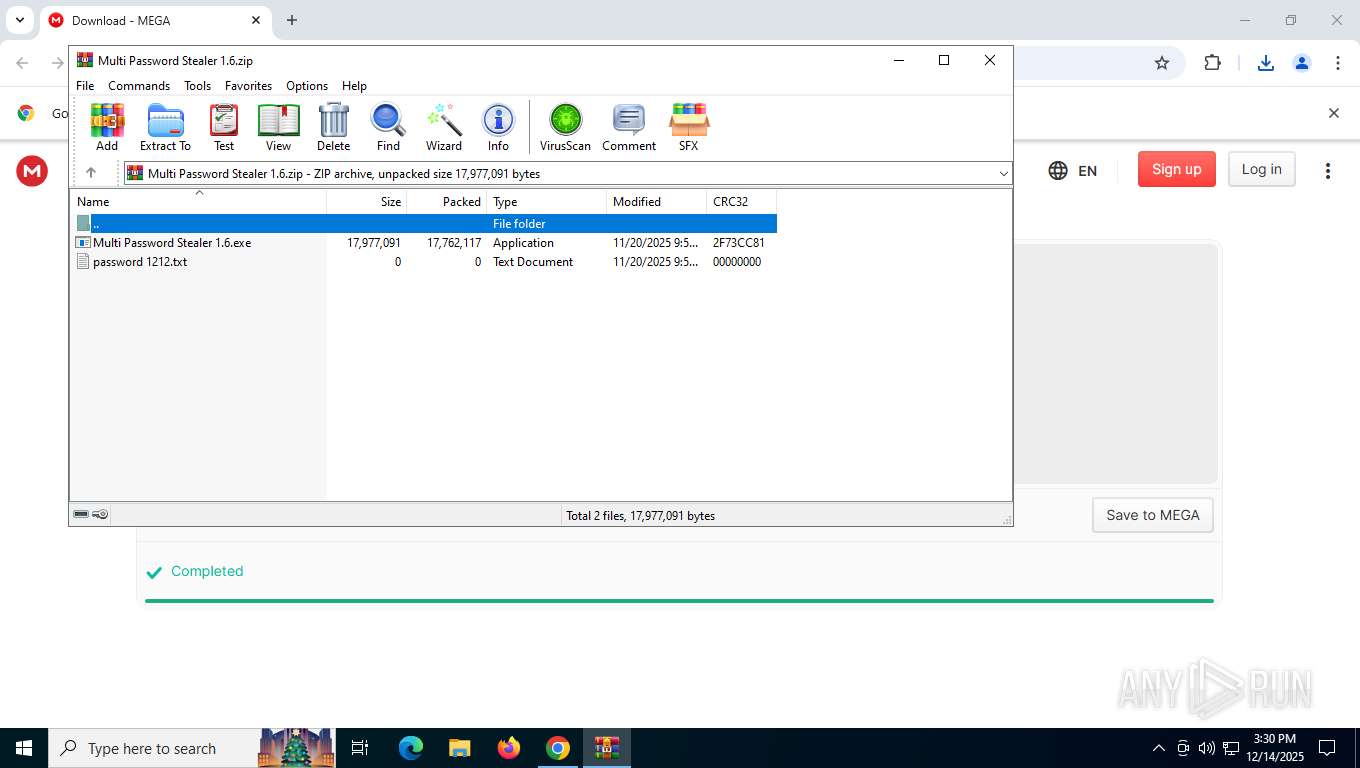
| MD5: | AE0CFF6B4614504390DA95E8CBCDD4ED |
| SHA1: | D3F7A32B18C06685667AAD4A6579821555FF4269 |
| SHA256: | 06F65B320EC9EFA76A4AED7C7C3E07DD277566A255B61552942D9065D3BE83BF |
| SSDEEP: | 3:N8X/izlSyIHz0D/v3Zo+r7n:2wzIgDX3ZpXn |
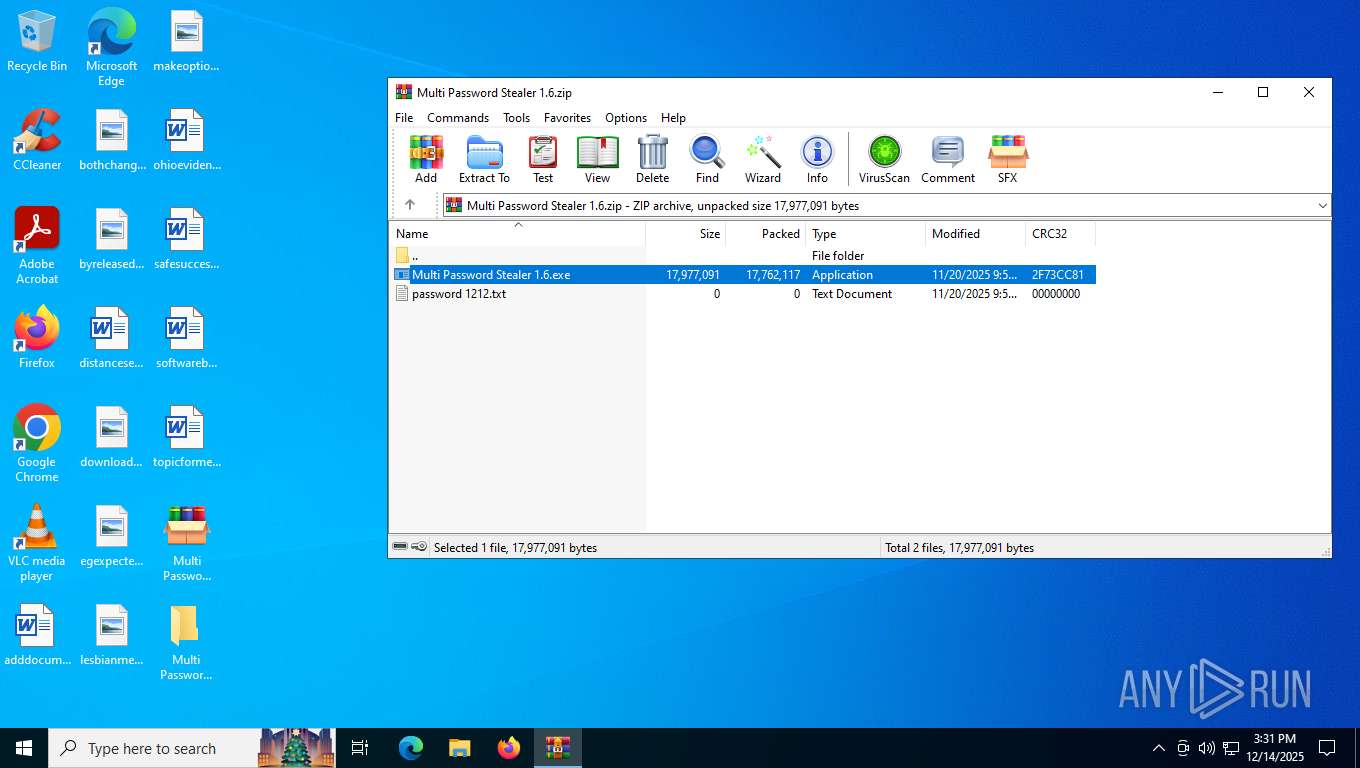
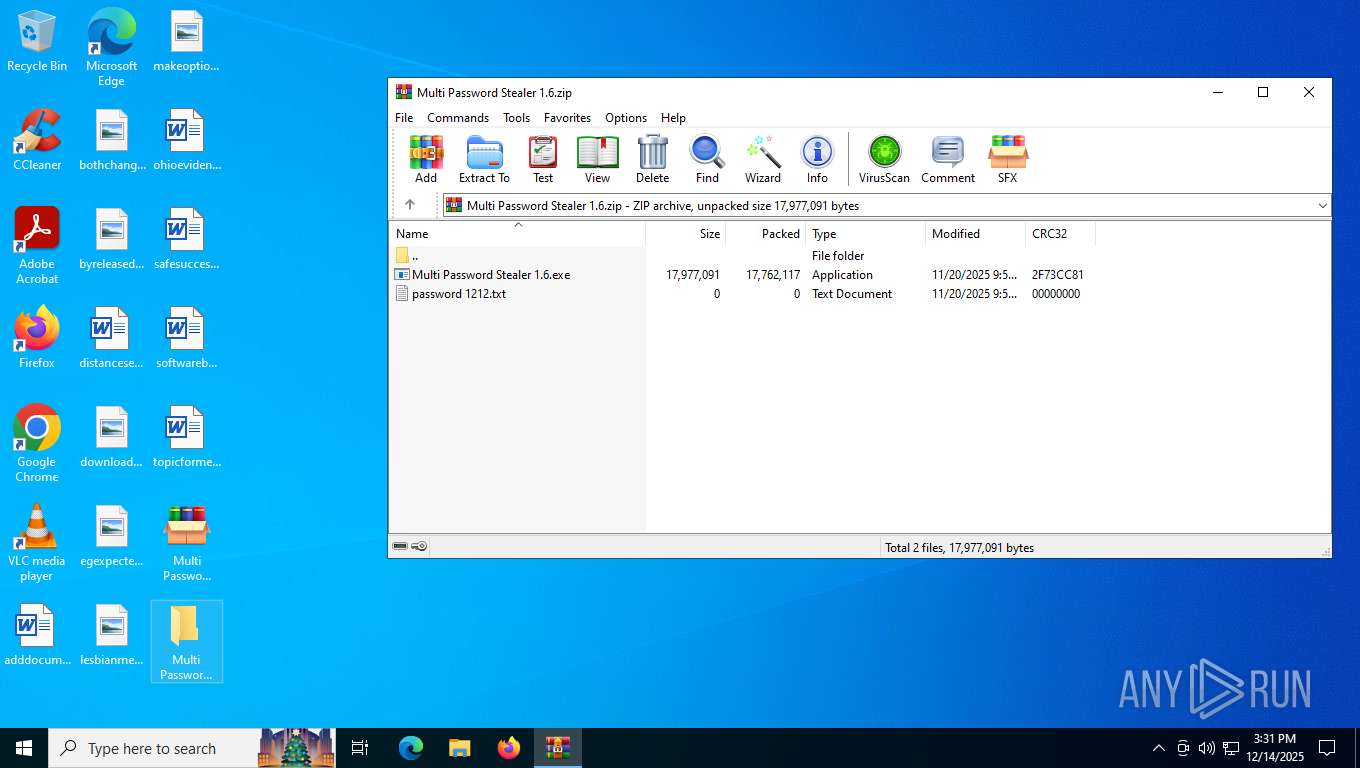
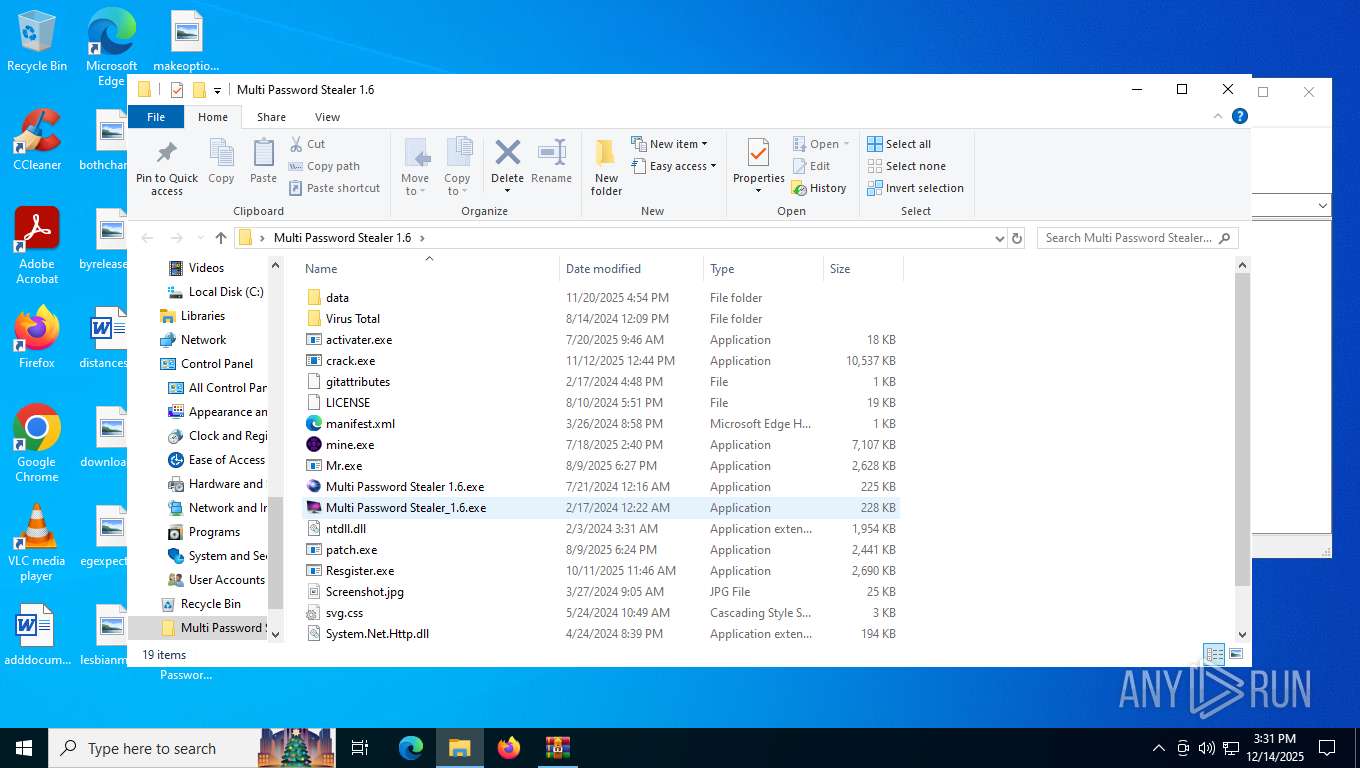
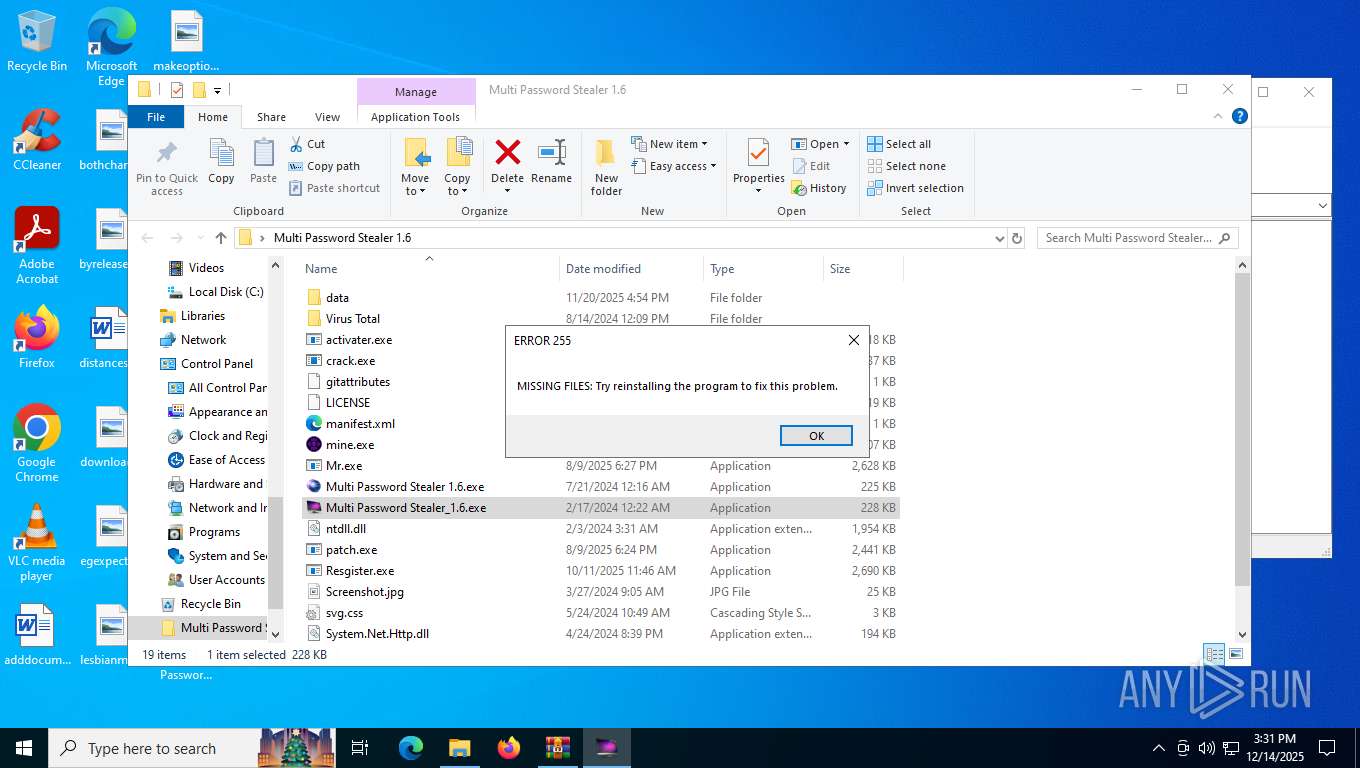
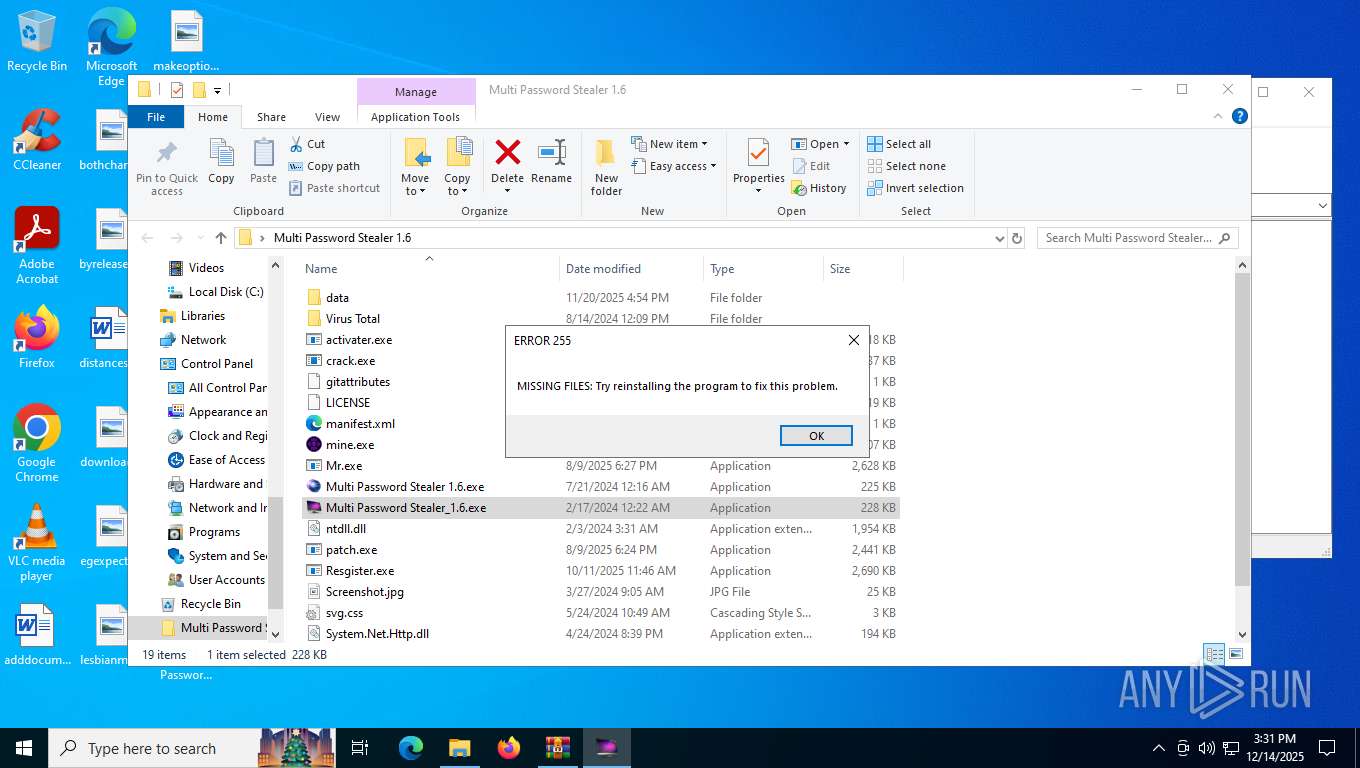
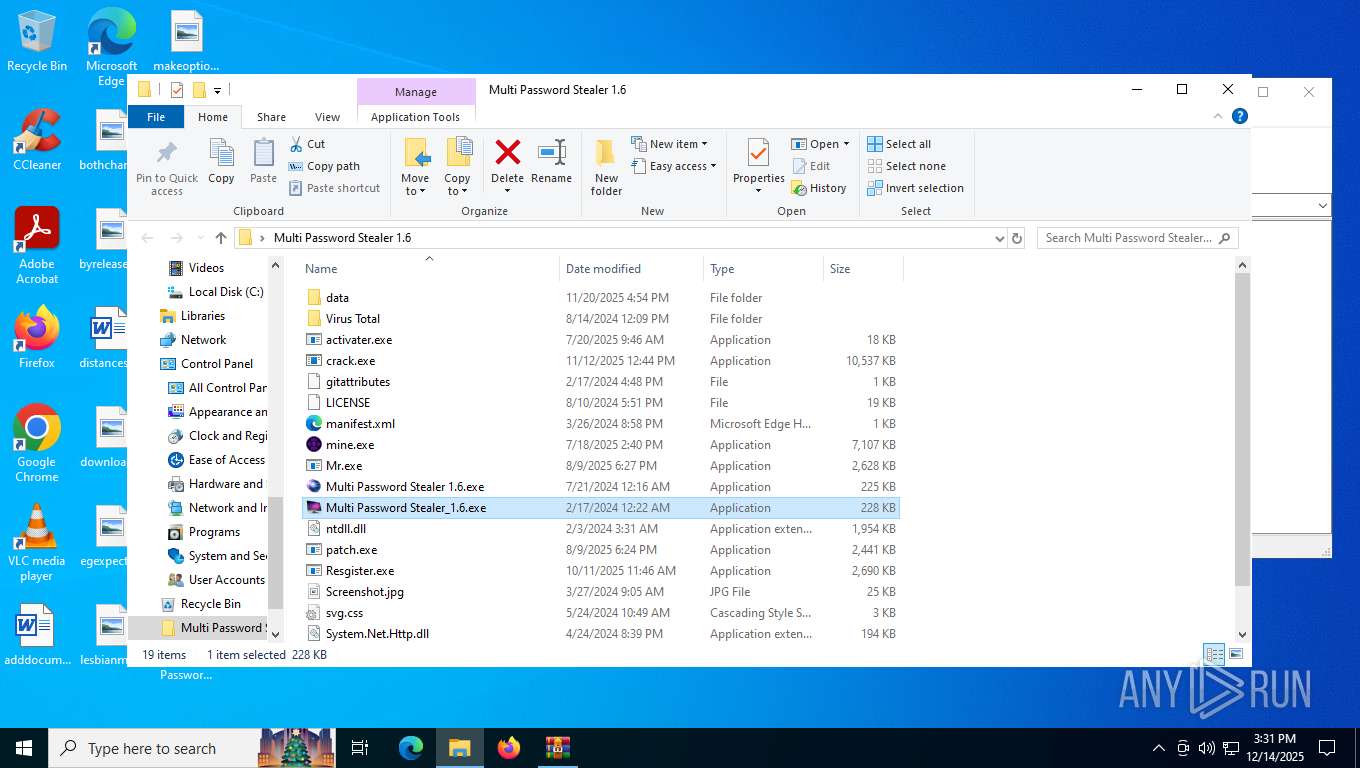
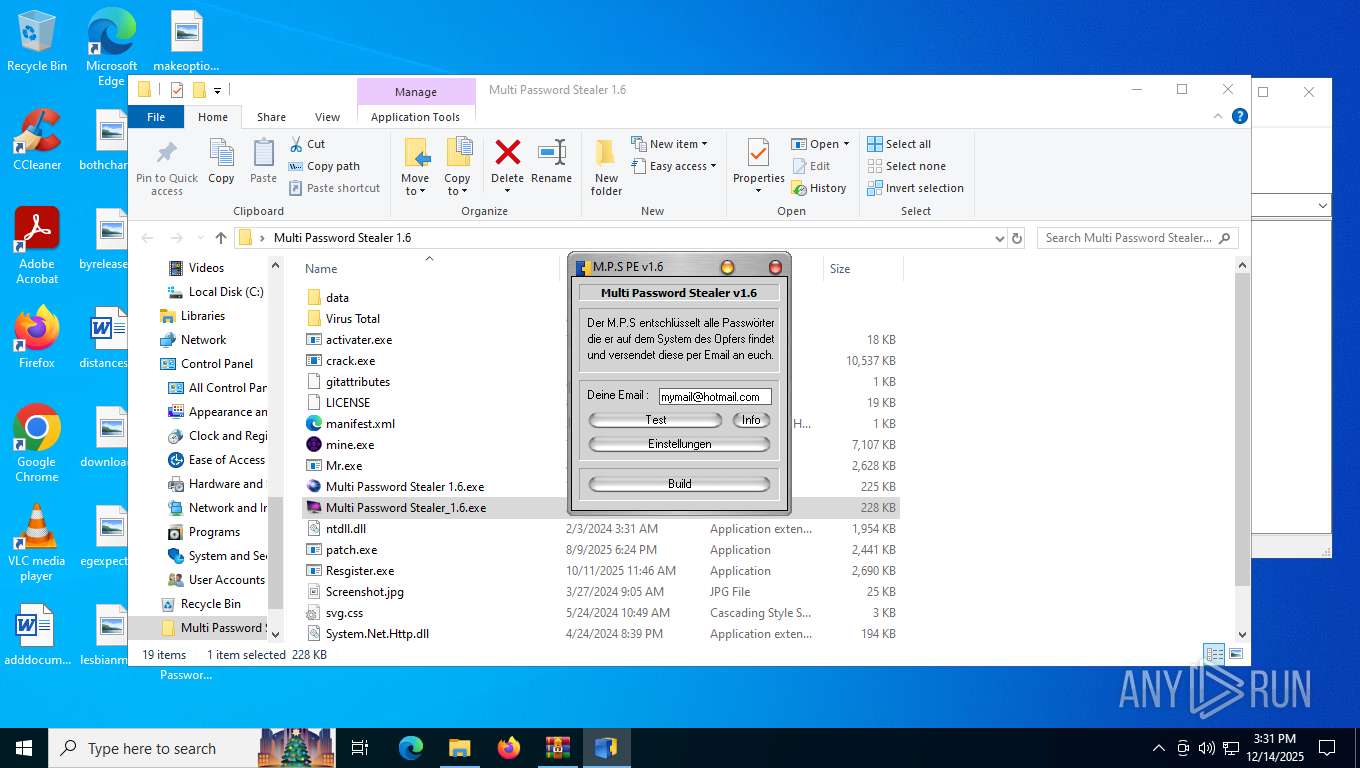
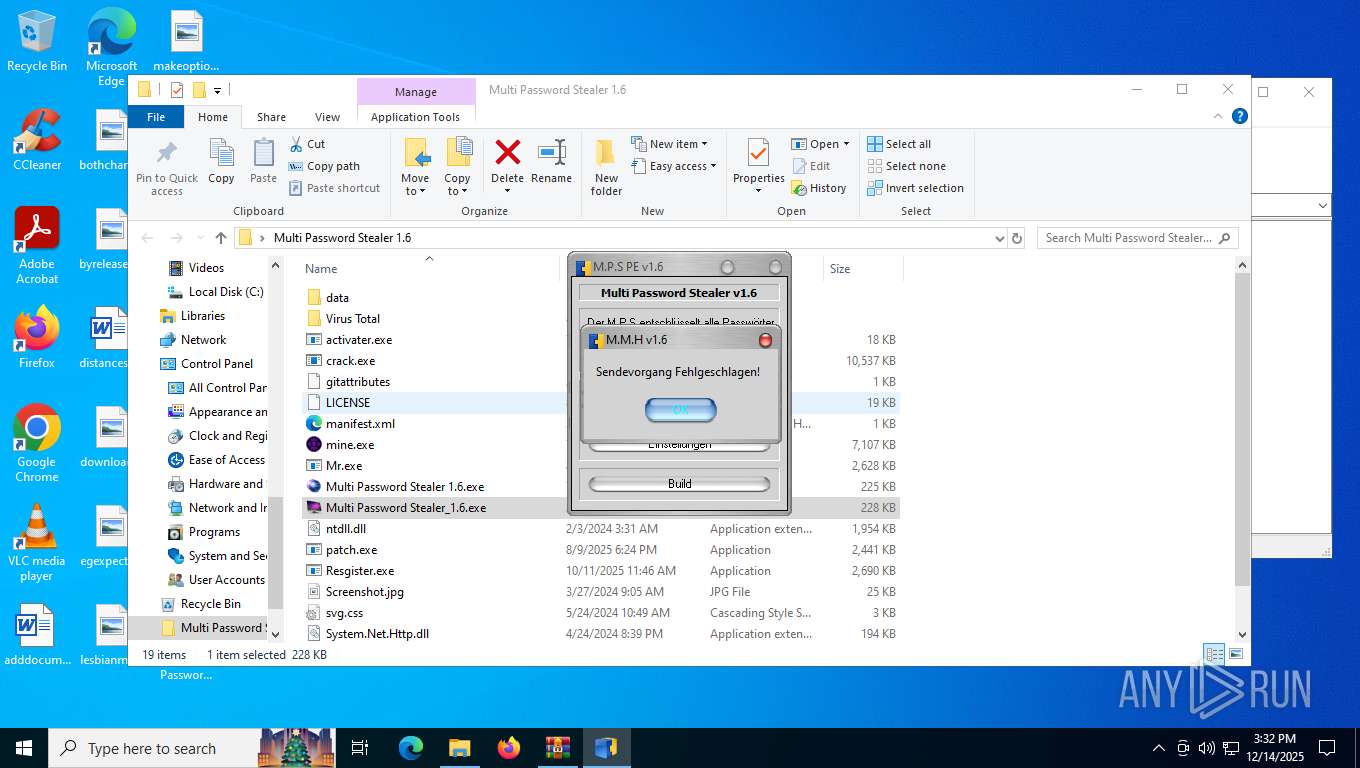
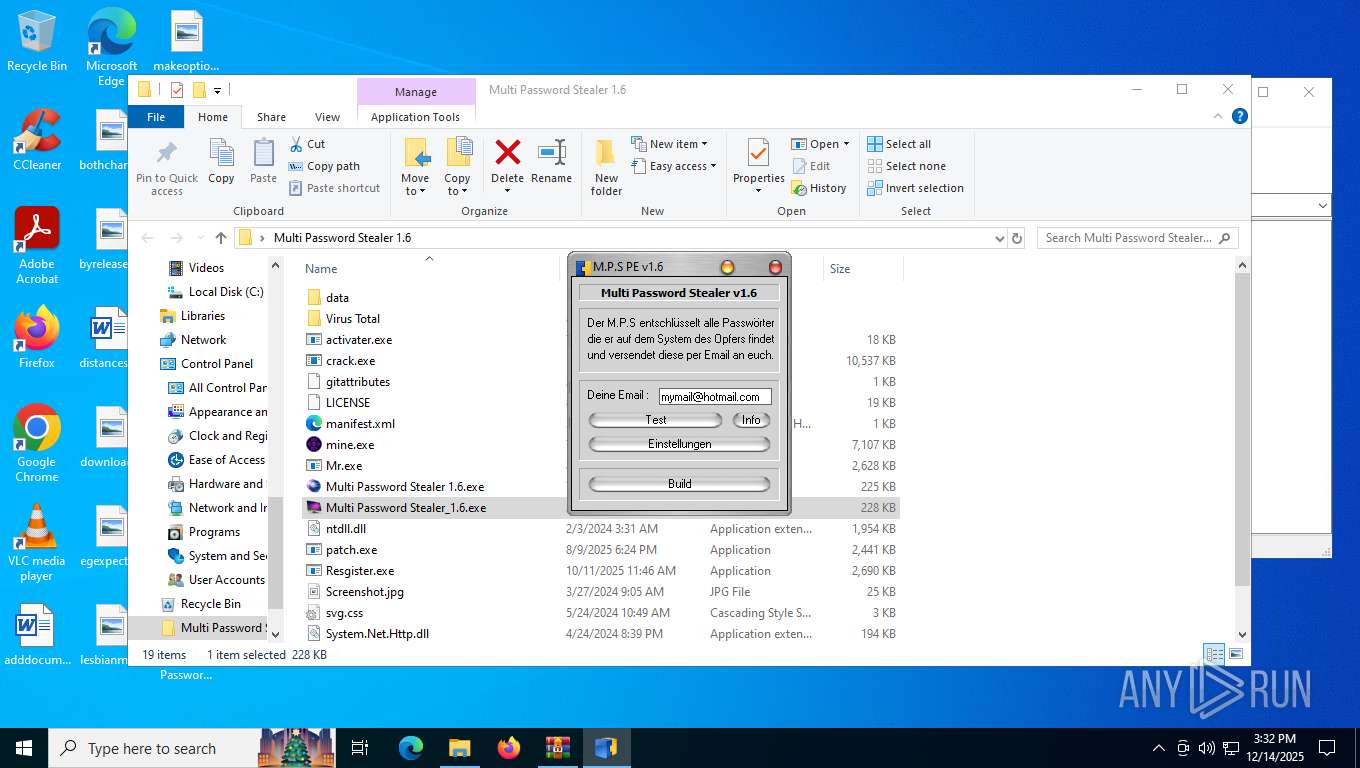
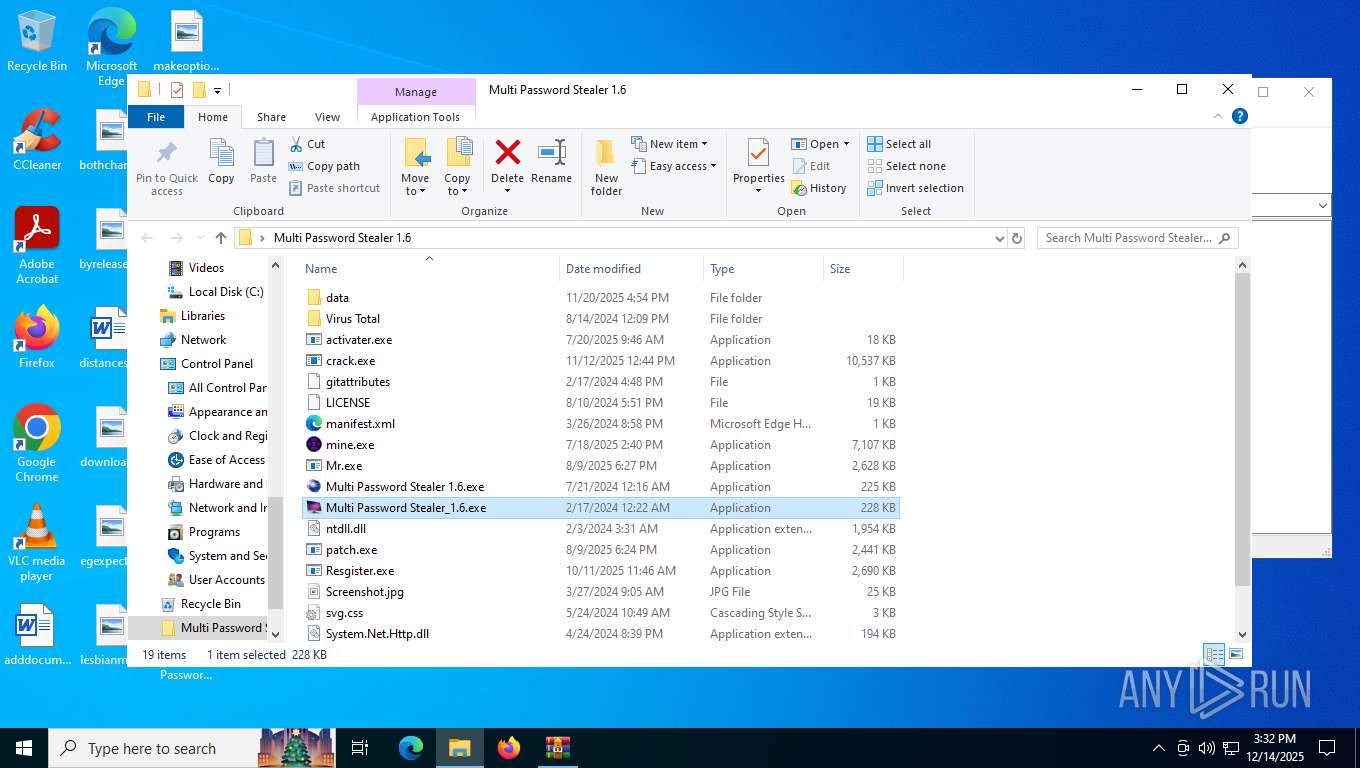
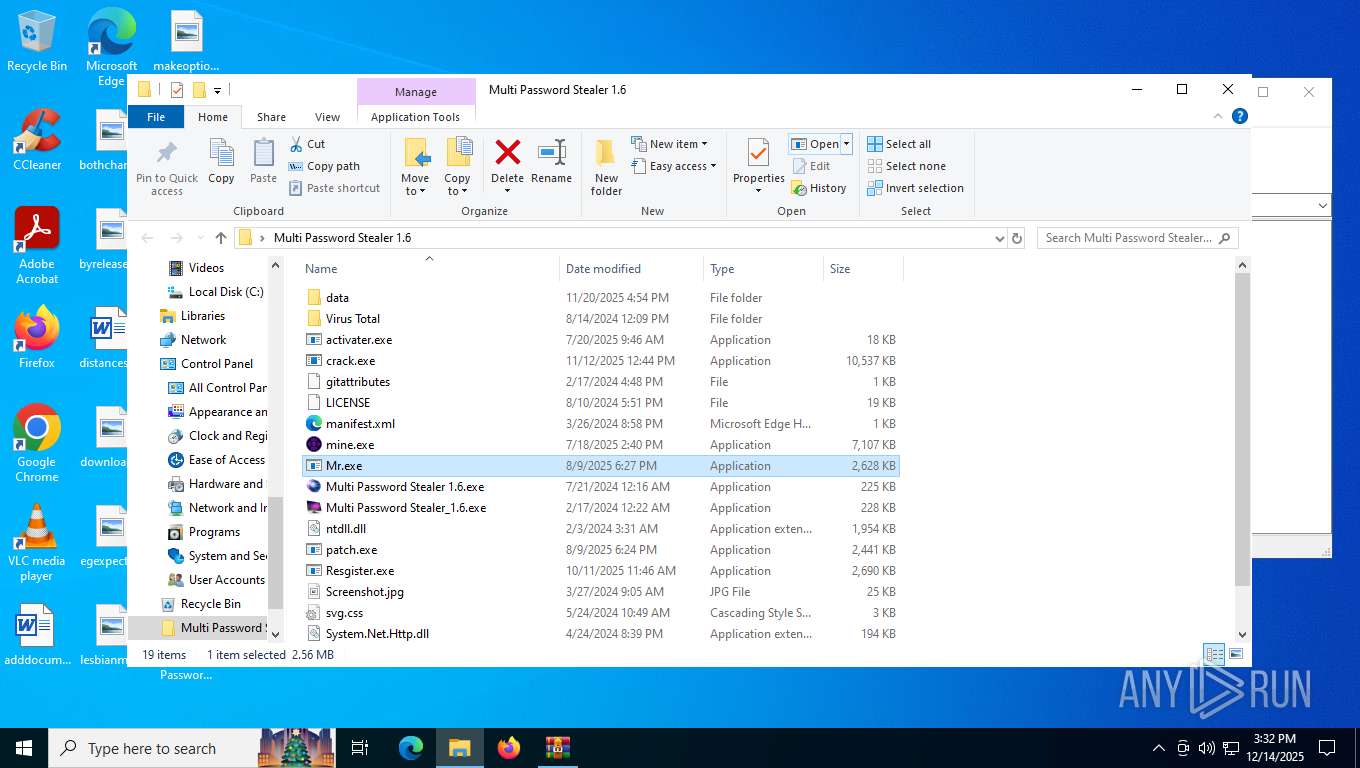
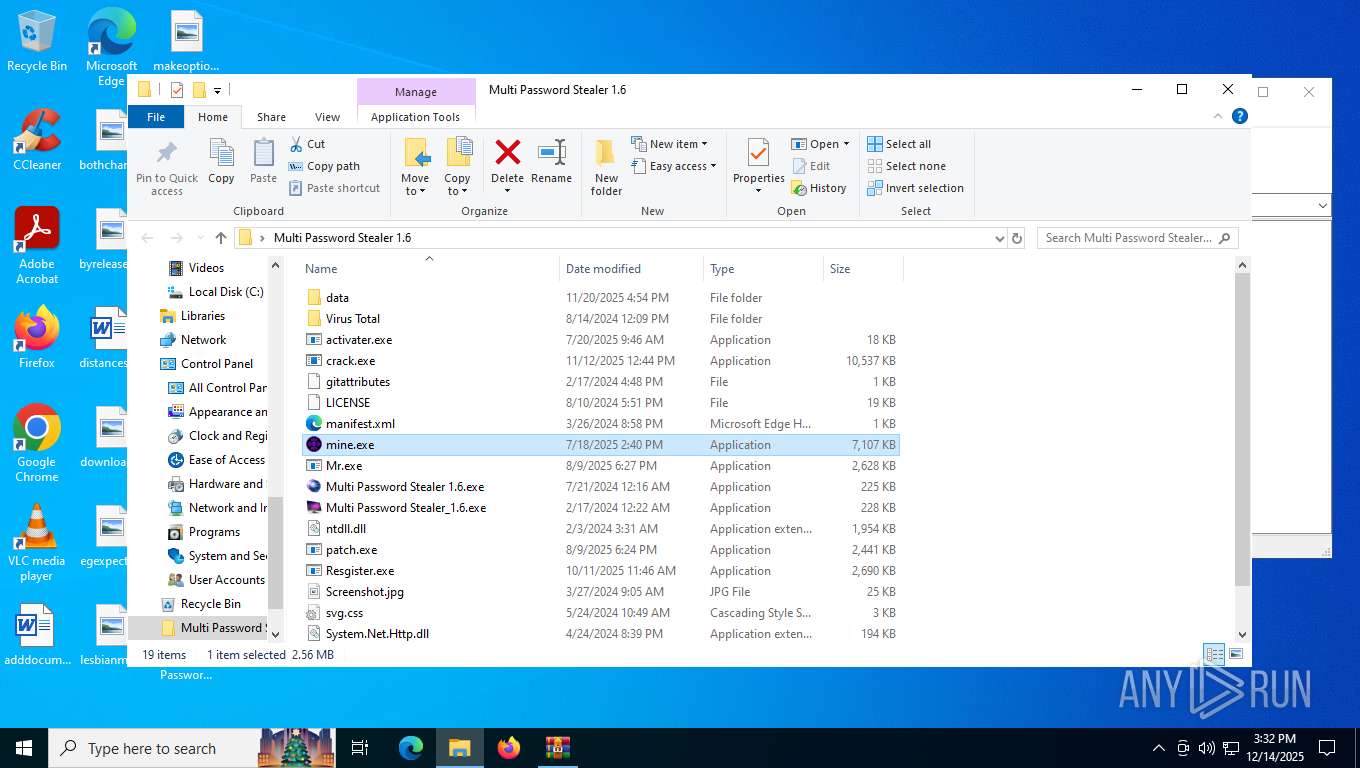
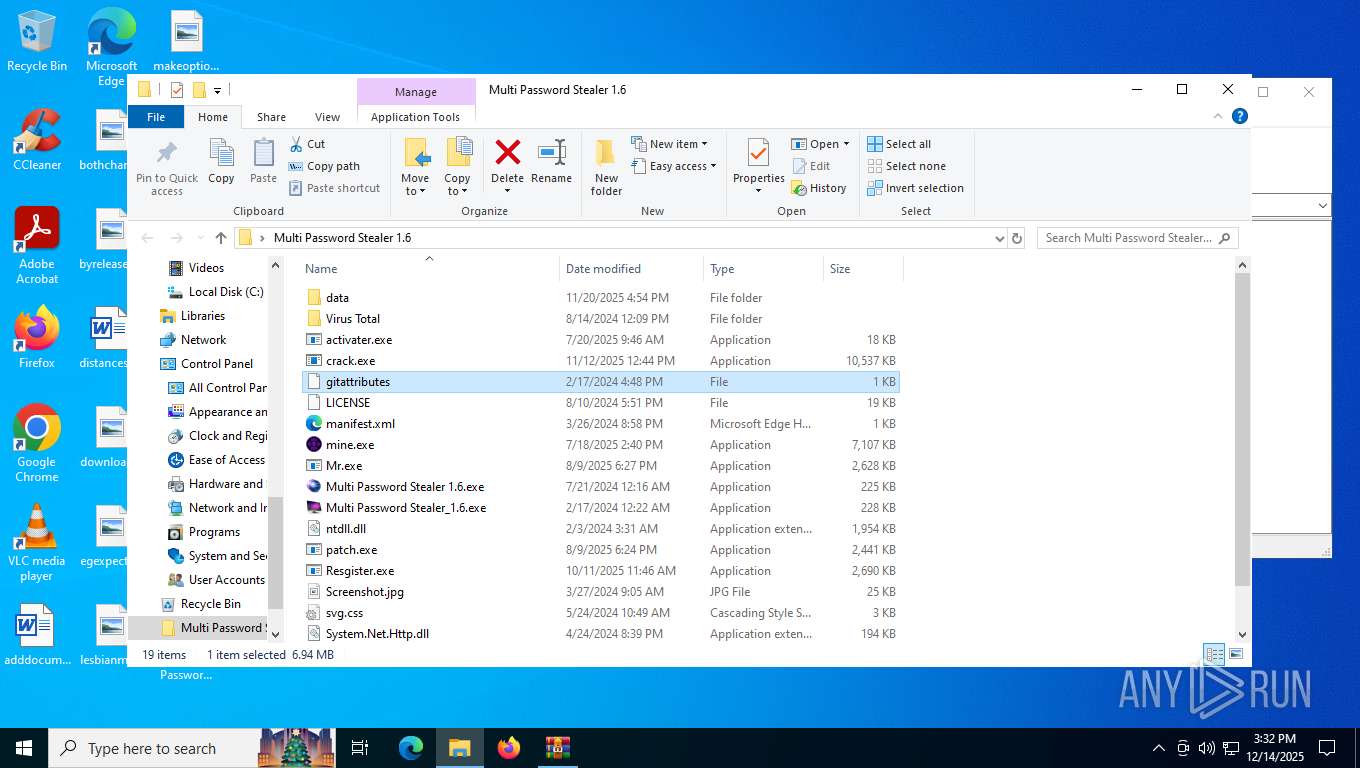
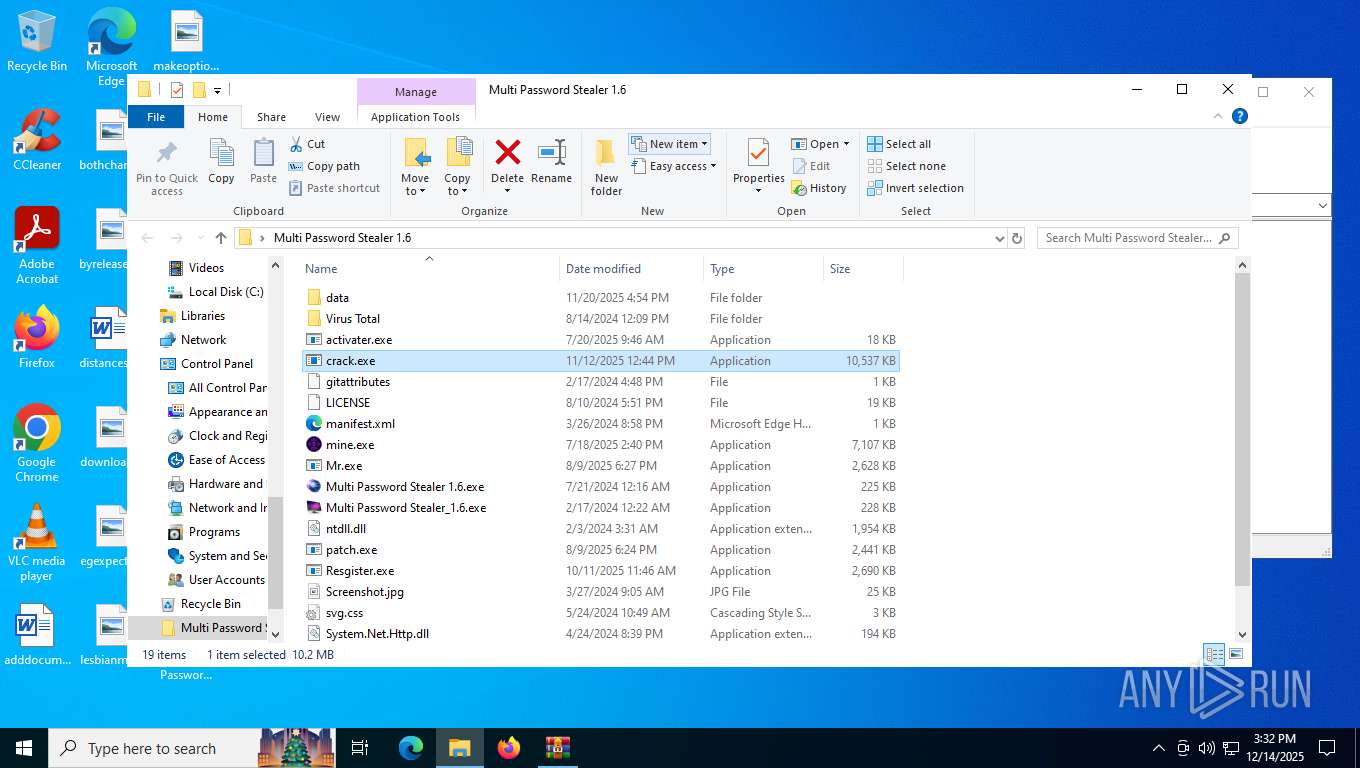
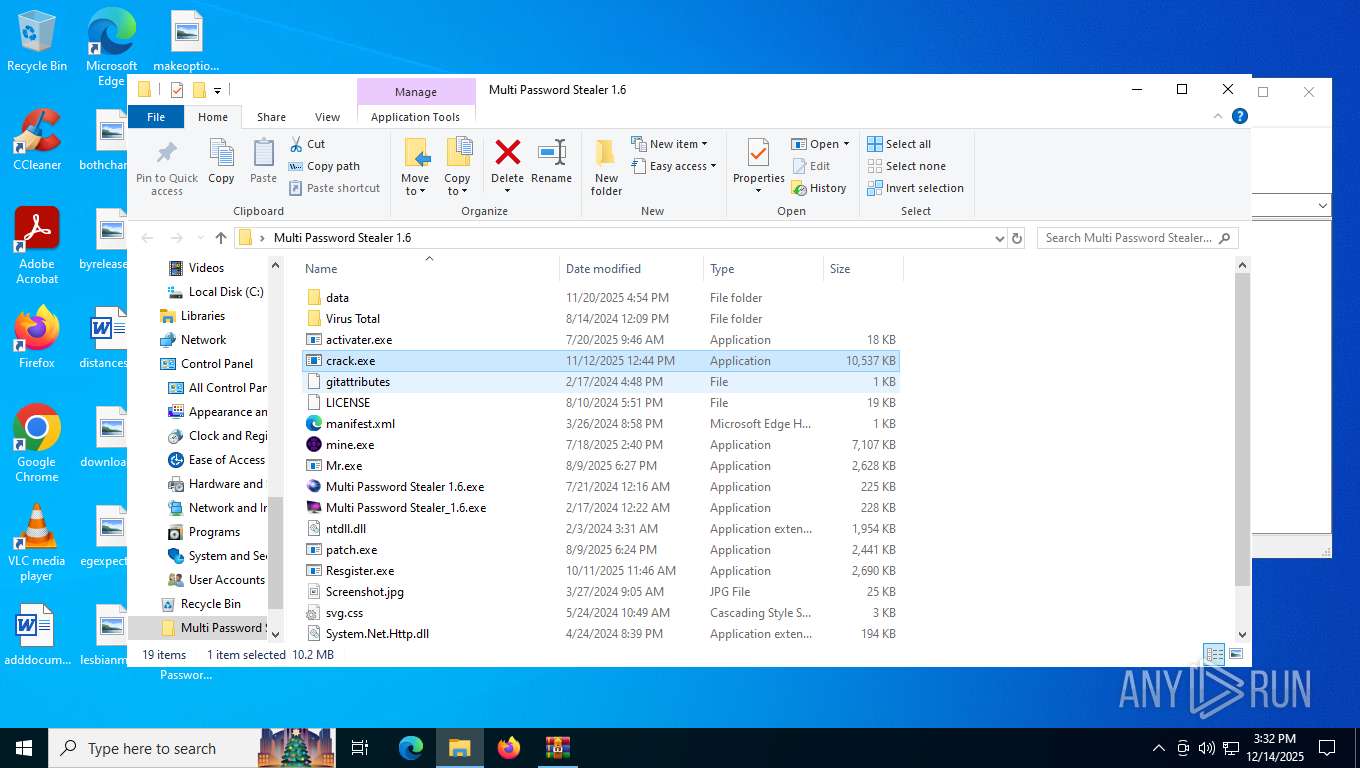
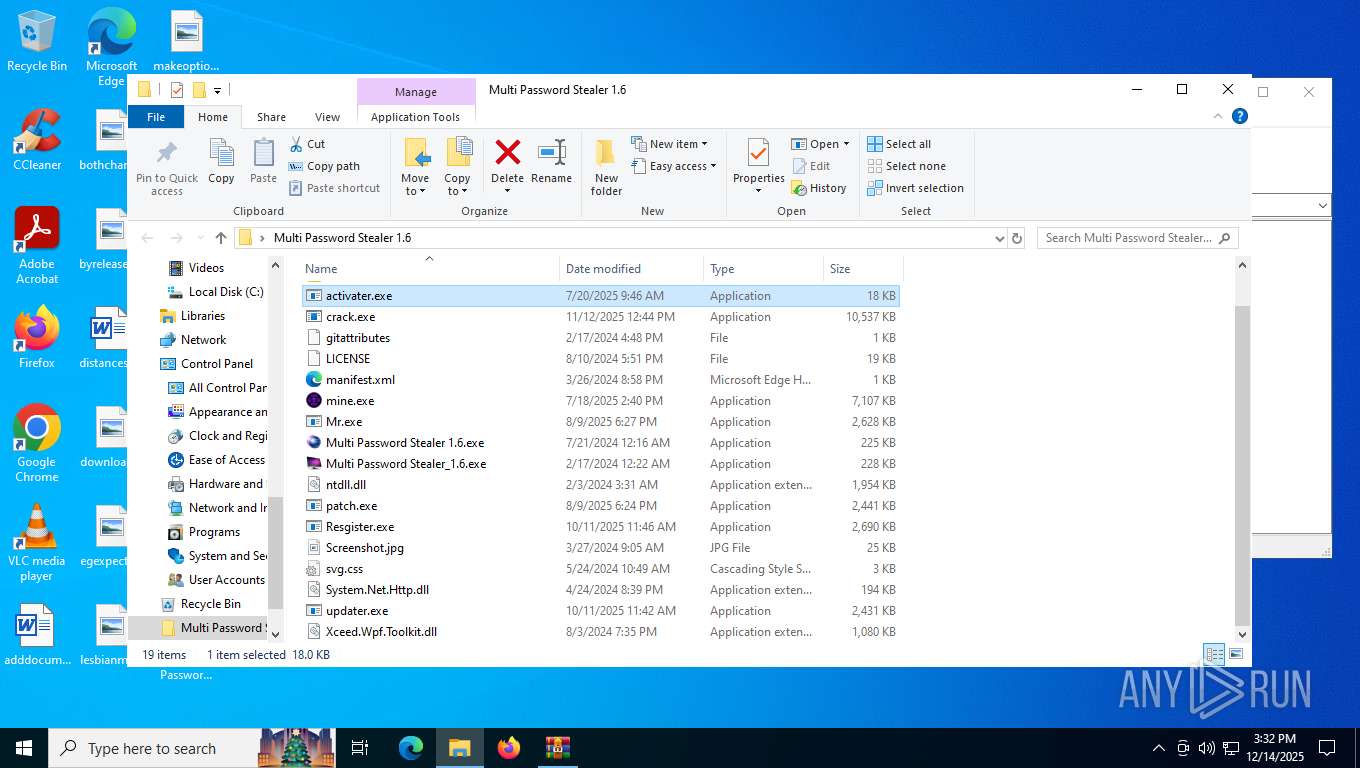
MALICIOUS
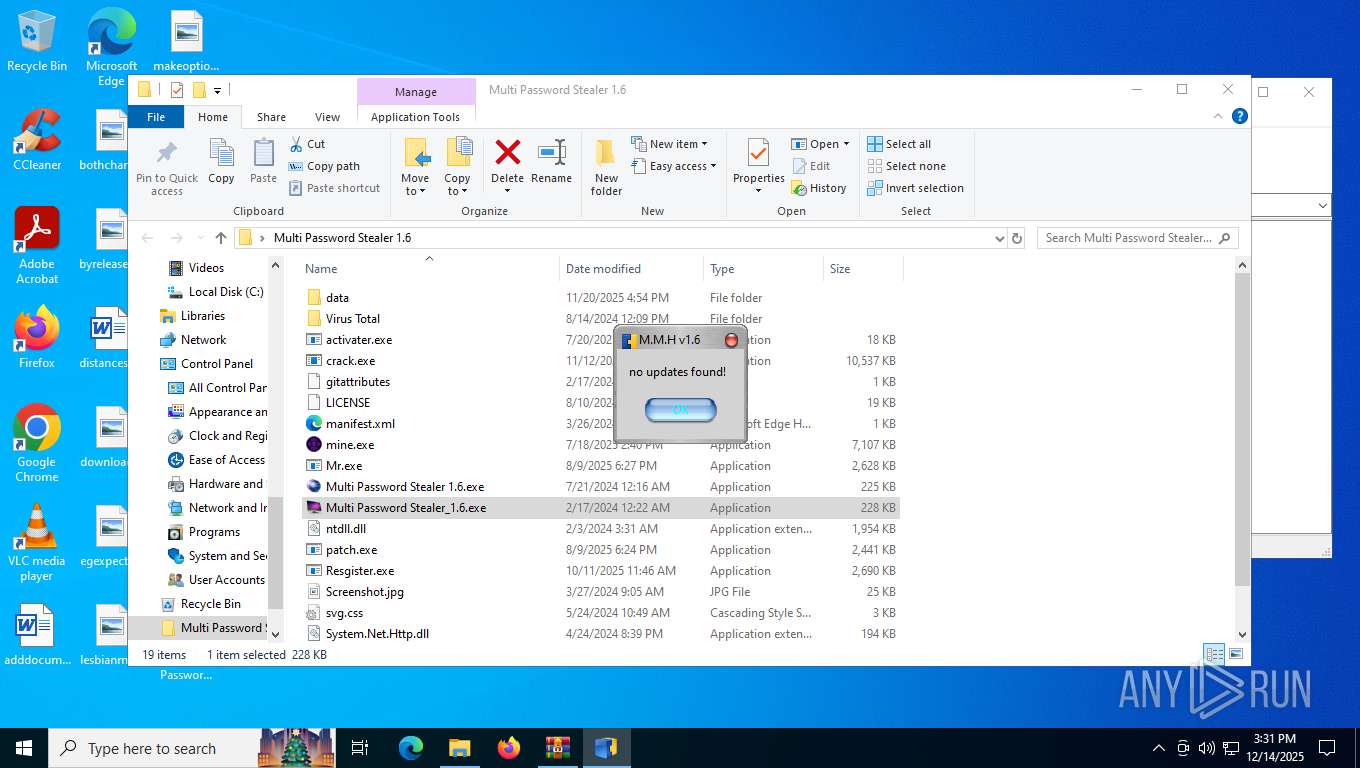
MILLENIUM has been found (auto)
- Multi Password Stealer 1.6.exe (PID: 940)
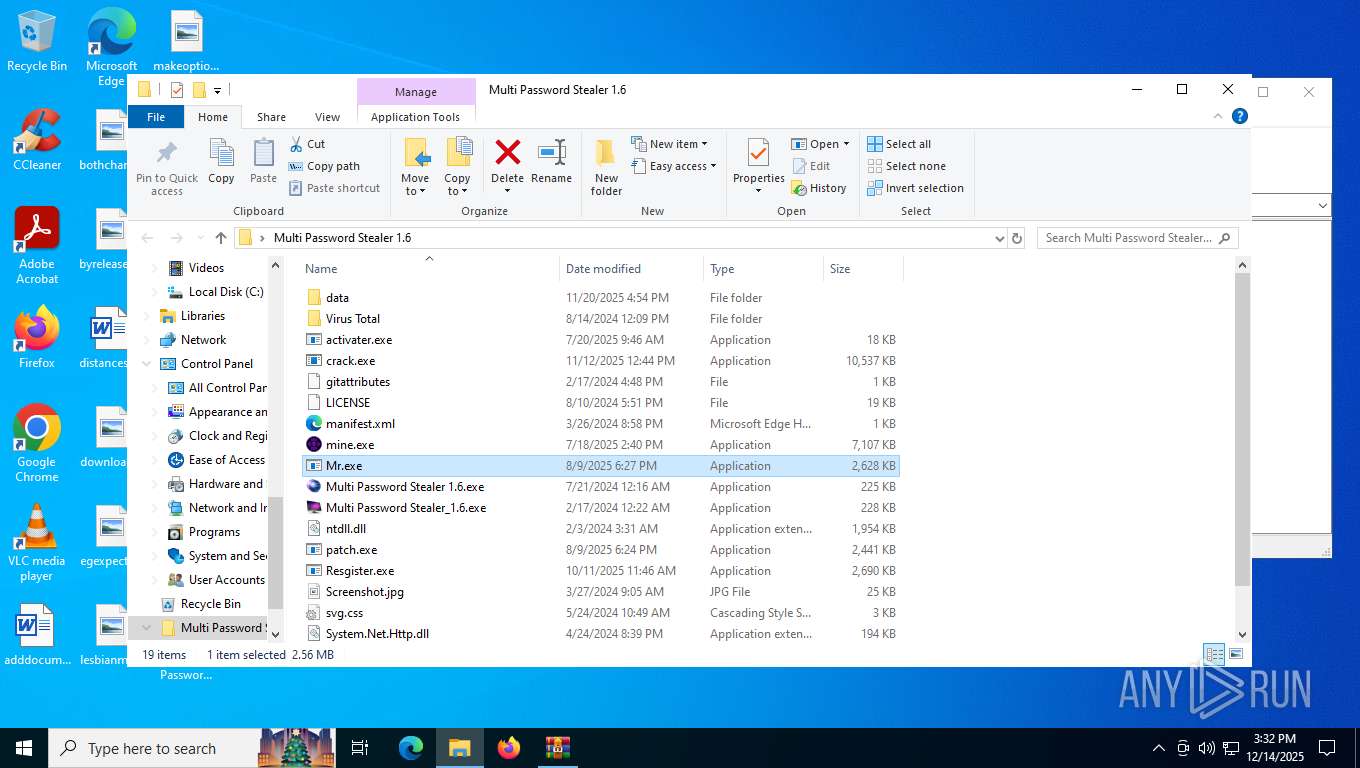
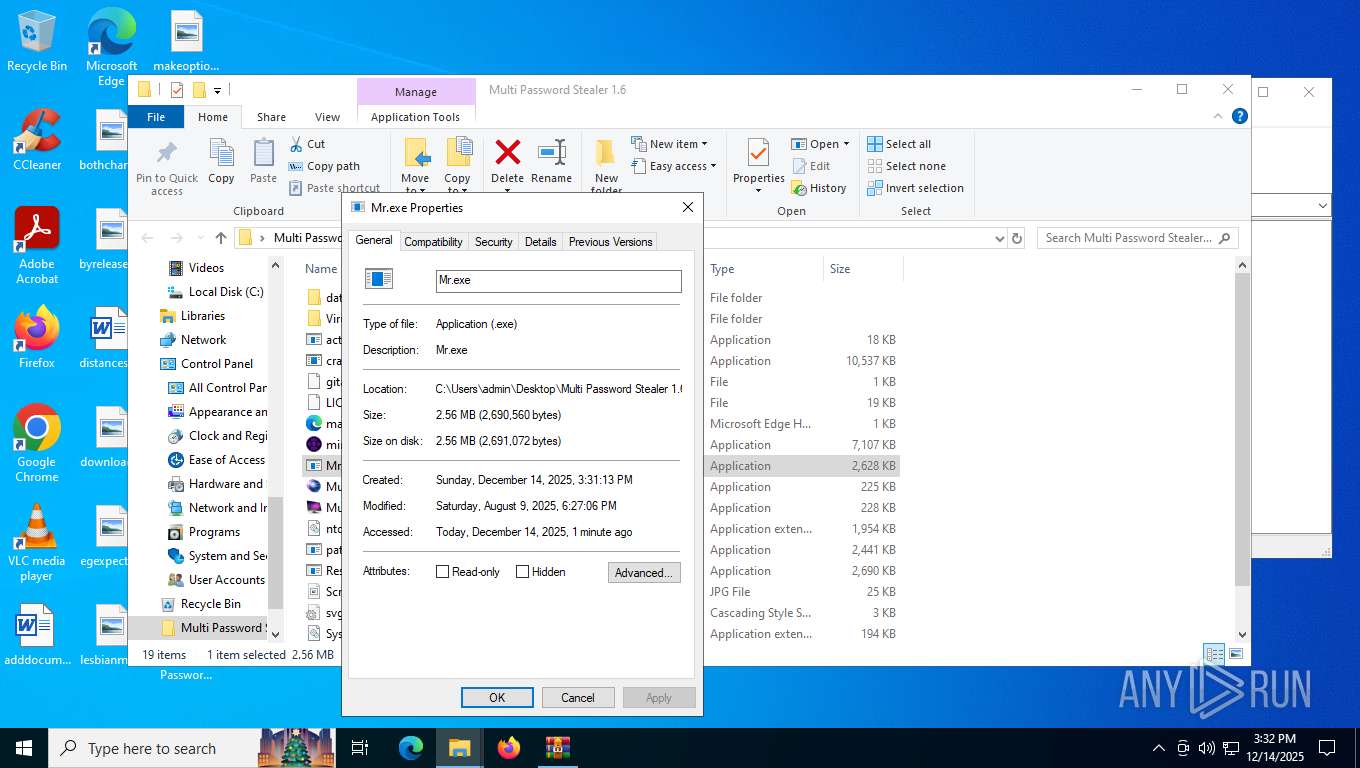
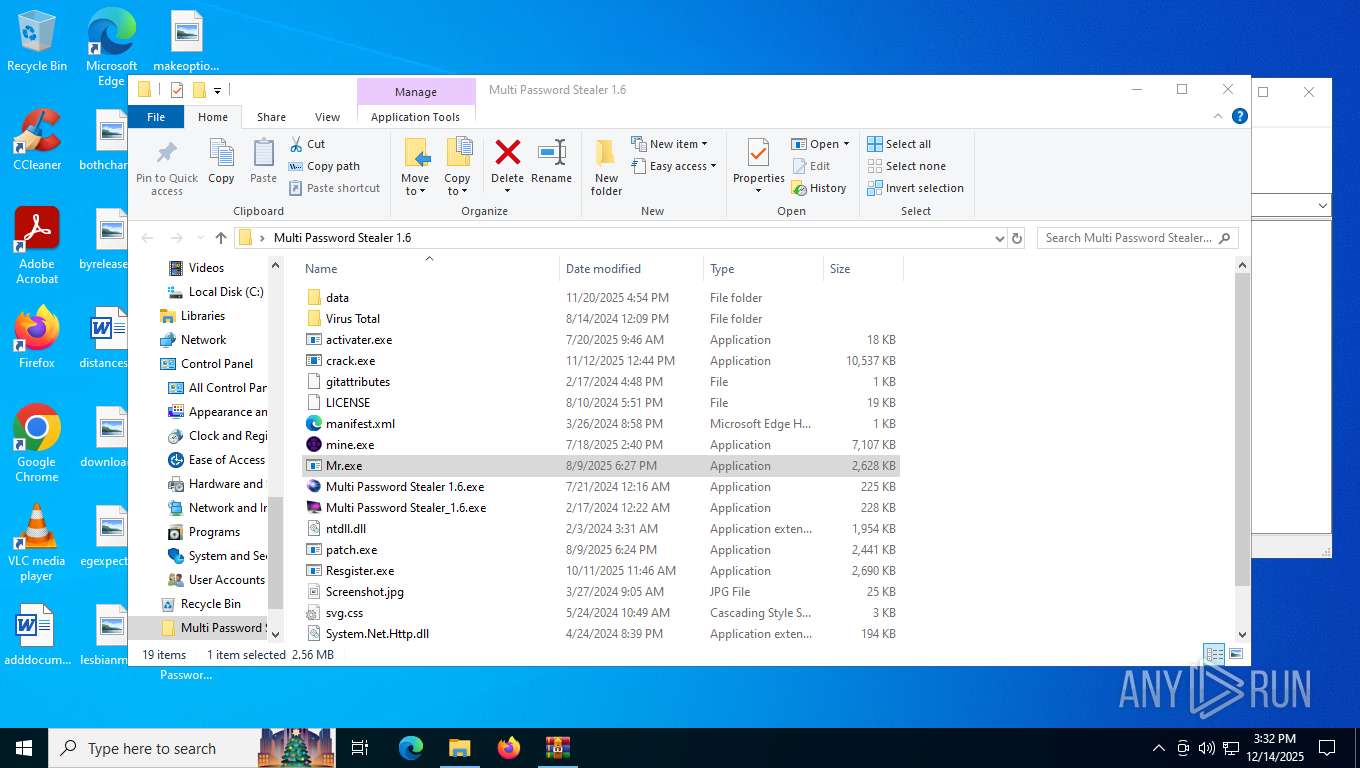
- Mr.exe (PID: 7756)
Vulnerable driver has been detected
- mine.exe (PID: 8096)
Miner pattern has been detected
- OmegaEngine.exe (PID: 3152)
XMRig has been detected
- OmegaEngine.exe (PID: 3152)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2292)
- OmegaEngine.exe (PID: 3152)
Connects to the CnC server
- OmegaEngine.exe (PID: 3152)
Actions looks like stealing of personal data
- svchost.exe (PID: 8004)
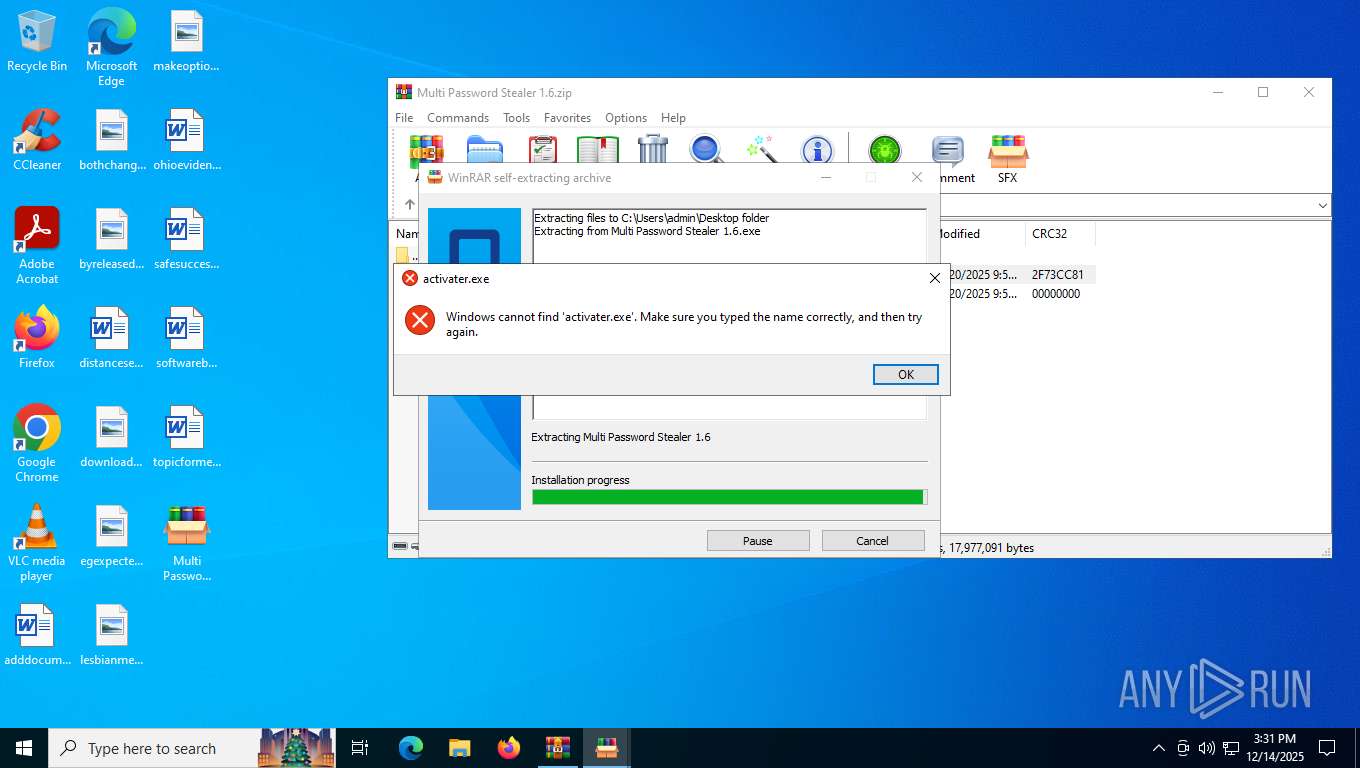
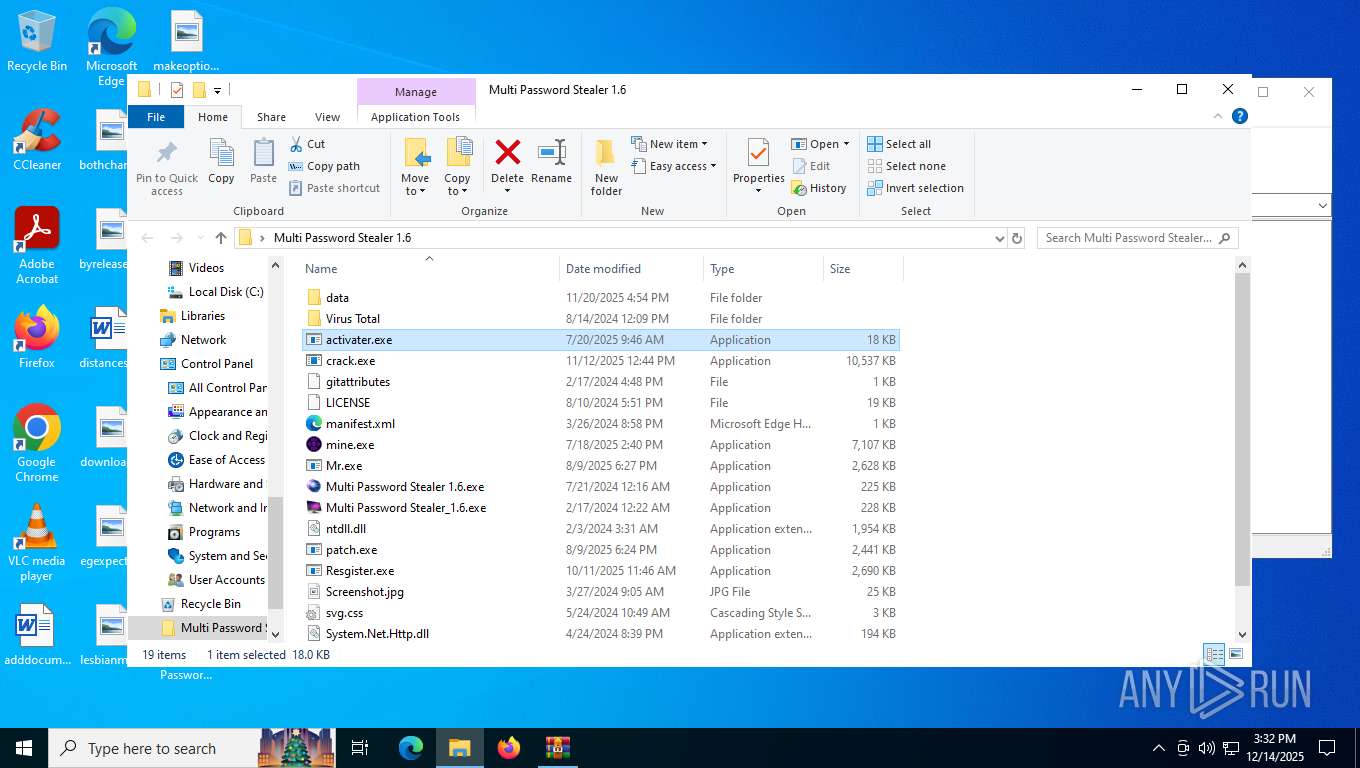
Create files in the Startup directory
- activater.exe (PID: 7384)
Steals credentials from Web Browsers
- svchost.exe (PID: 8004)
XMRIG has been detected (YARA)
- mine.exe (PID: 8096)
- OmegaEngine.exe (PID: 3152)
MILLENIUMRAT has been detected (YARA)
- svchost.exe (PID: 8004)
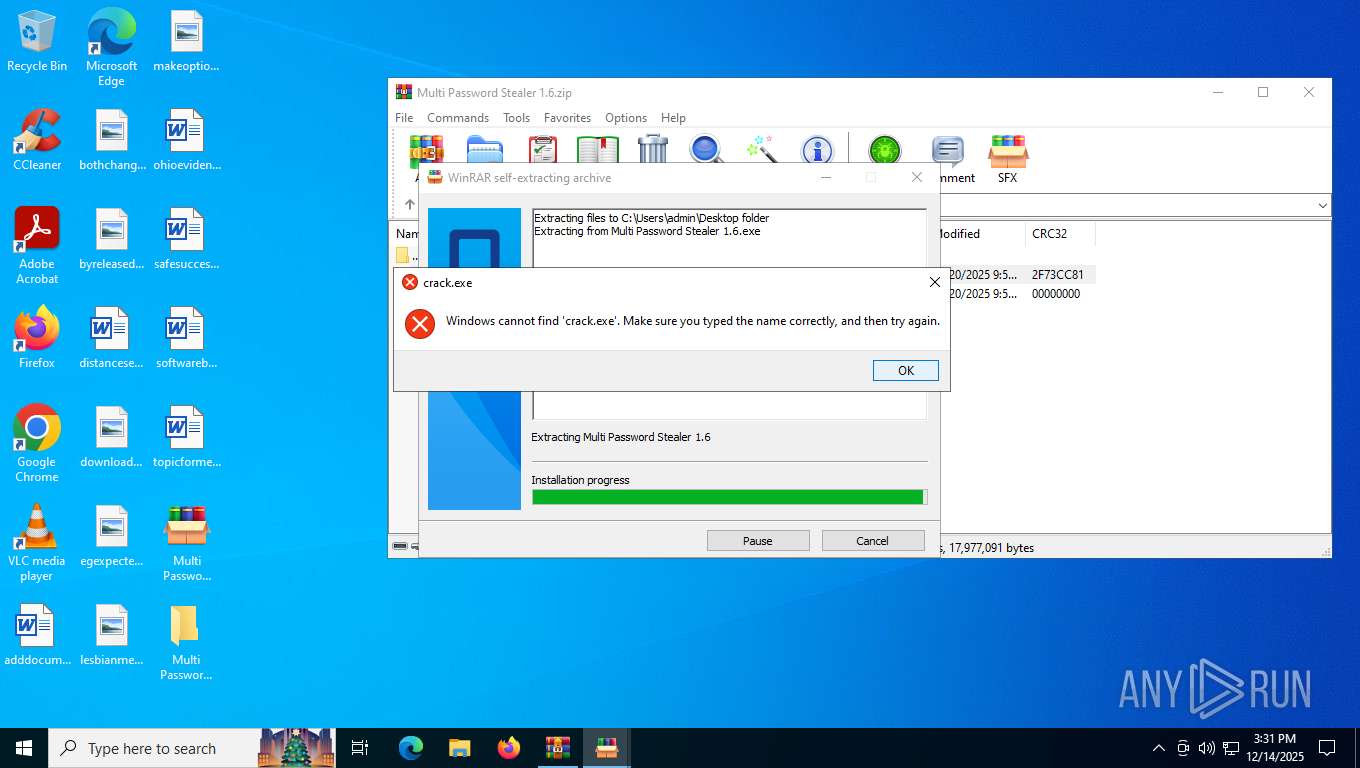
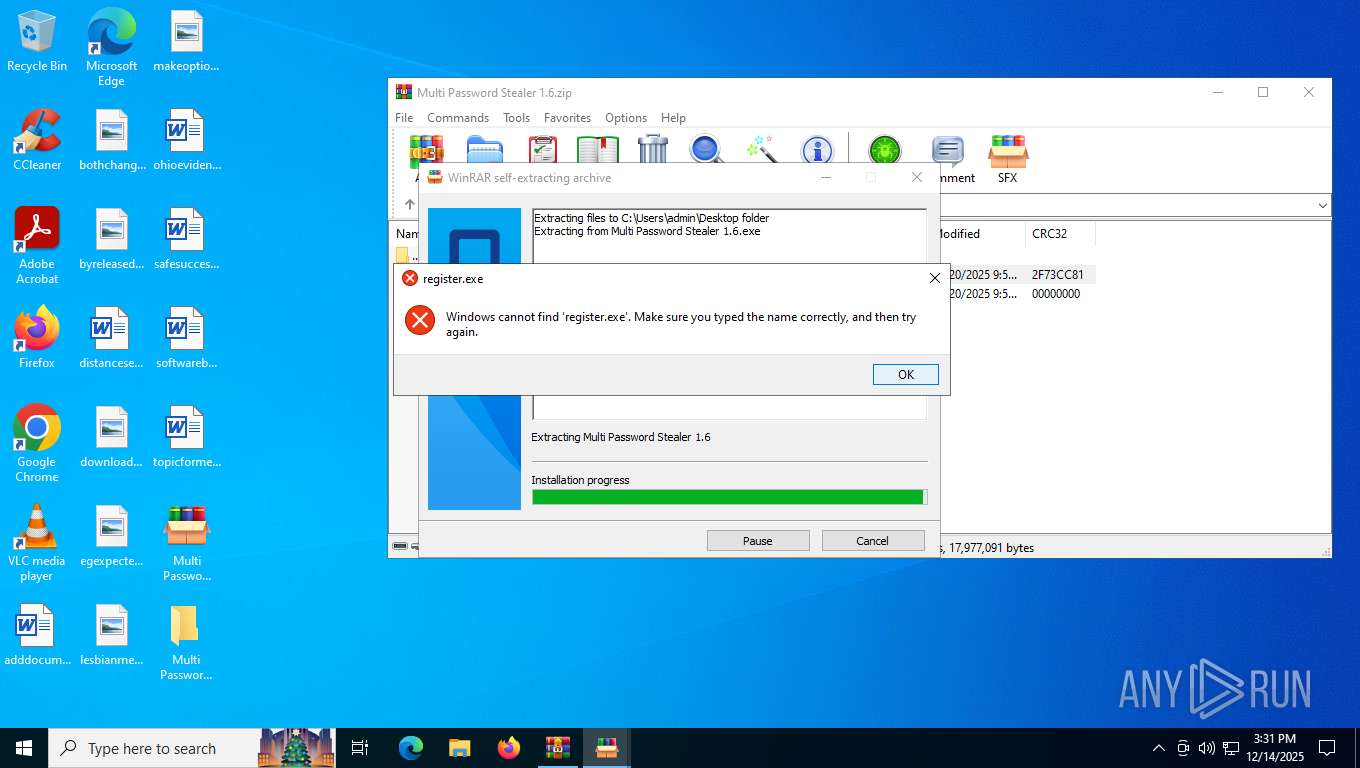
Changes the autorun value in the registry
- crack.exe (PID: 7328)
SUSPICIOUS
Reads security settings of Internet Explorer
- Multi Password Stealer 1.6.exe (PID: 940)
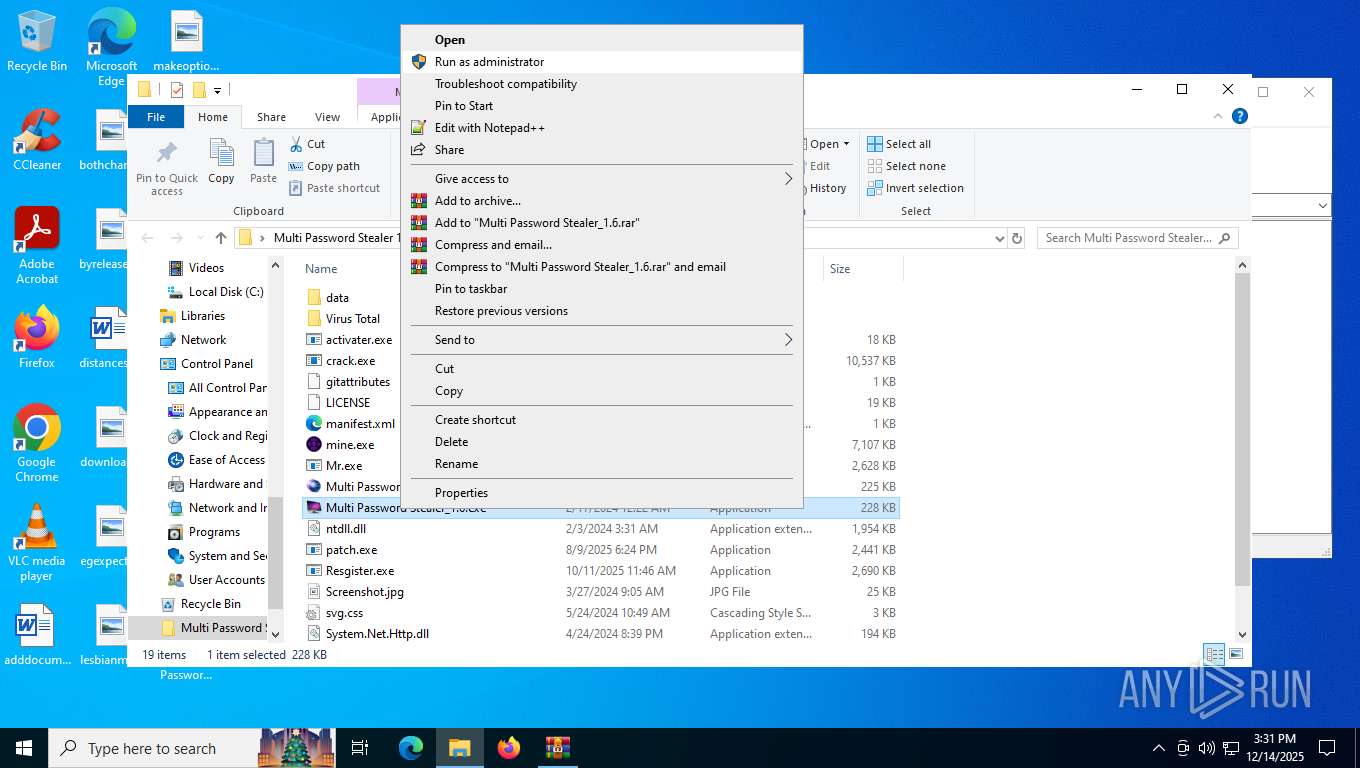
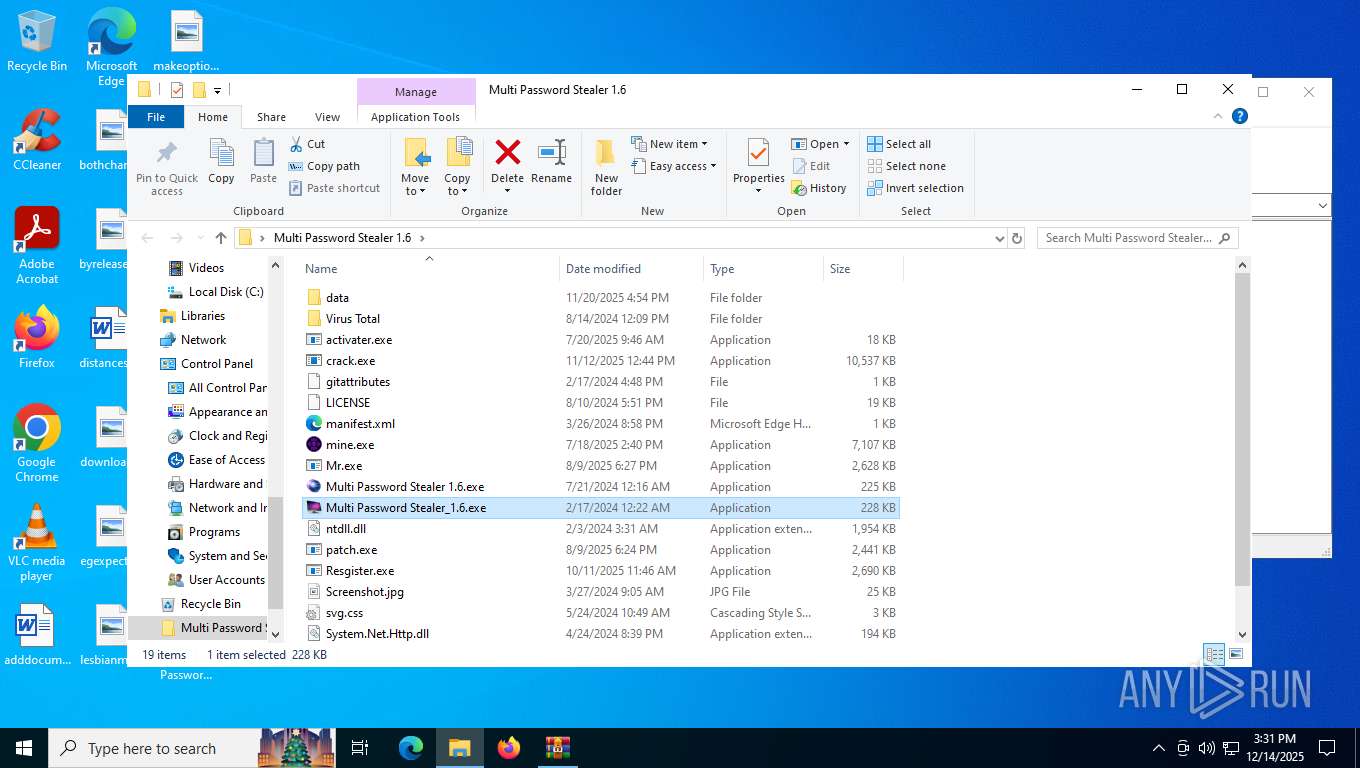
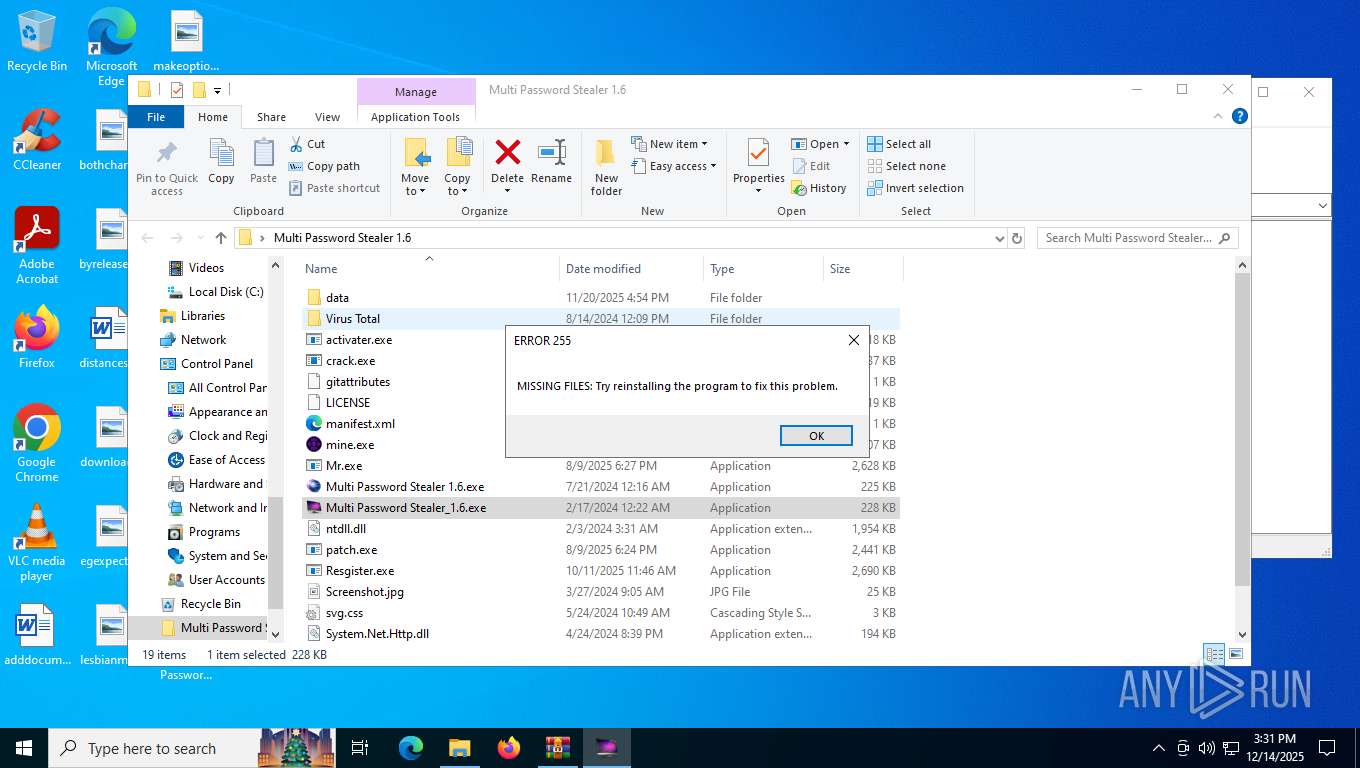
- Multi Password Stealer_1.6.exe (PID: 1340)
- mps.exe (PID: 7956)
- Mr.exe (PID: 8160)
- mine.exe (PID: 8096)
Reads Microsoft Outlook installation path
- Multi Password Stealer 1.6.exe (PID: 940)
- mps.exe (PID: 7956)
Reads Internet Explorer settings
- Multi Password Stealer 1.6.exe (PID: 940)
- mps.exe (PID: 7956)
Write to the desktop.ini file (may be used to cloak folders)
- Multi Password Stealer 1.6.exe (PID: 940)
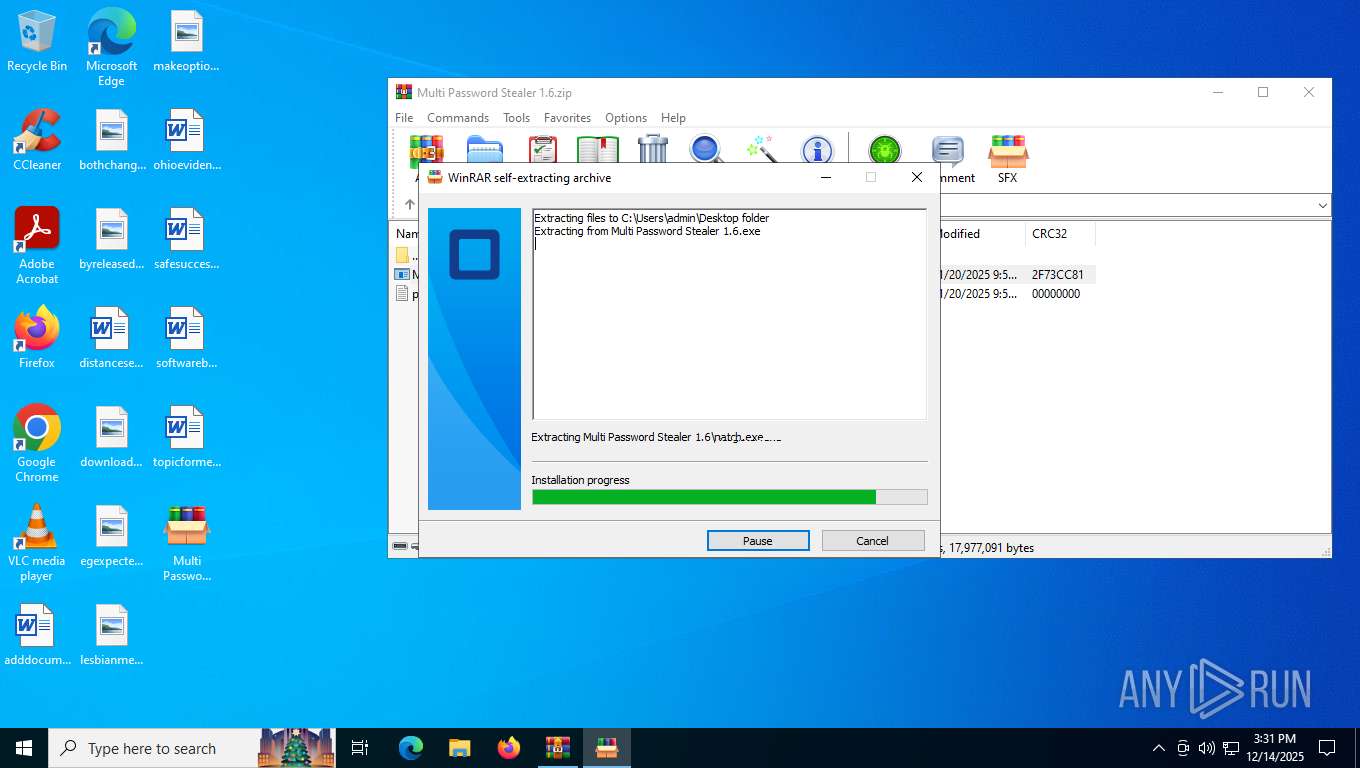
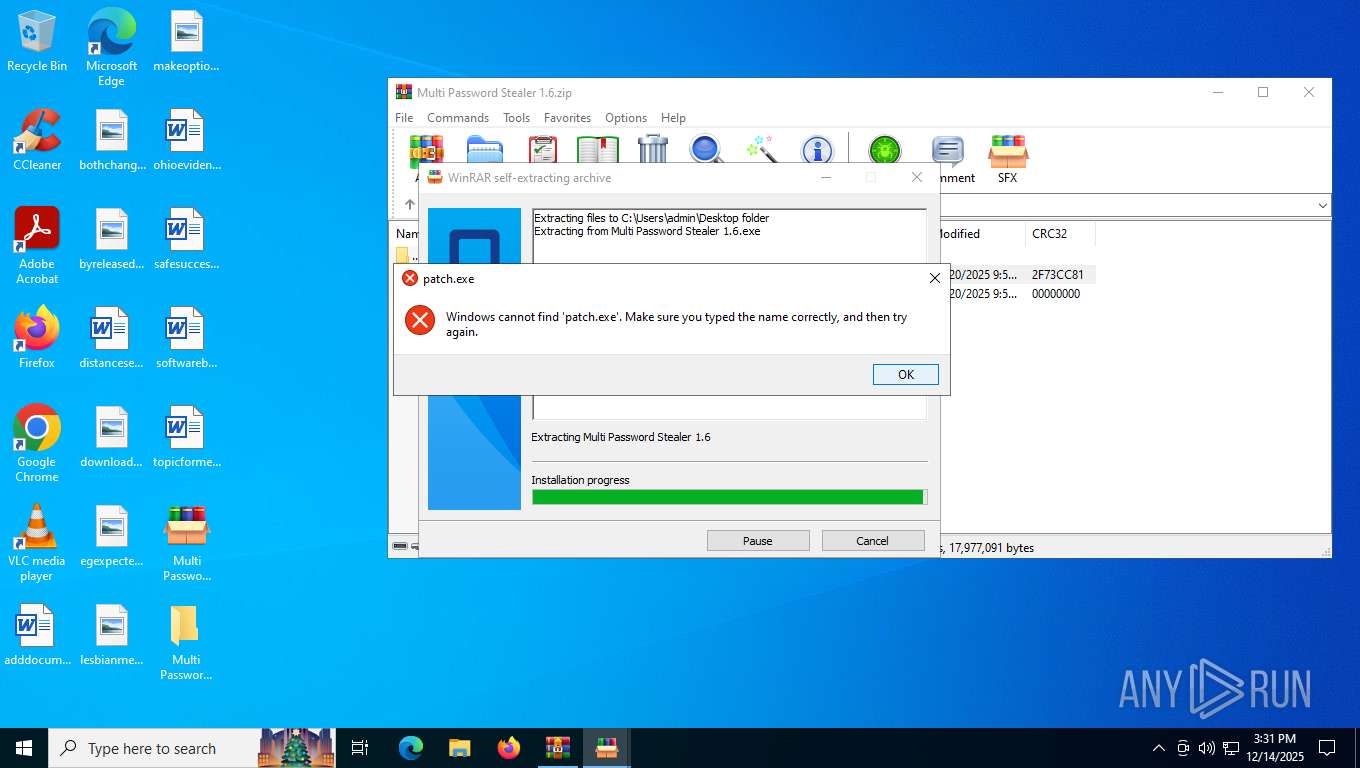
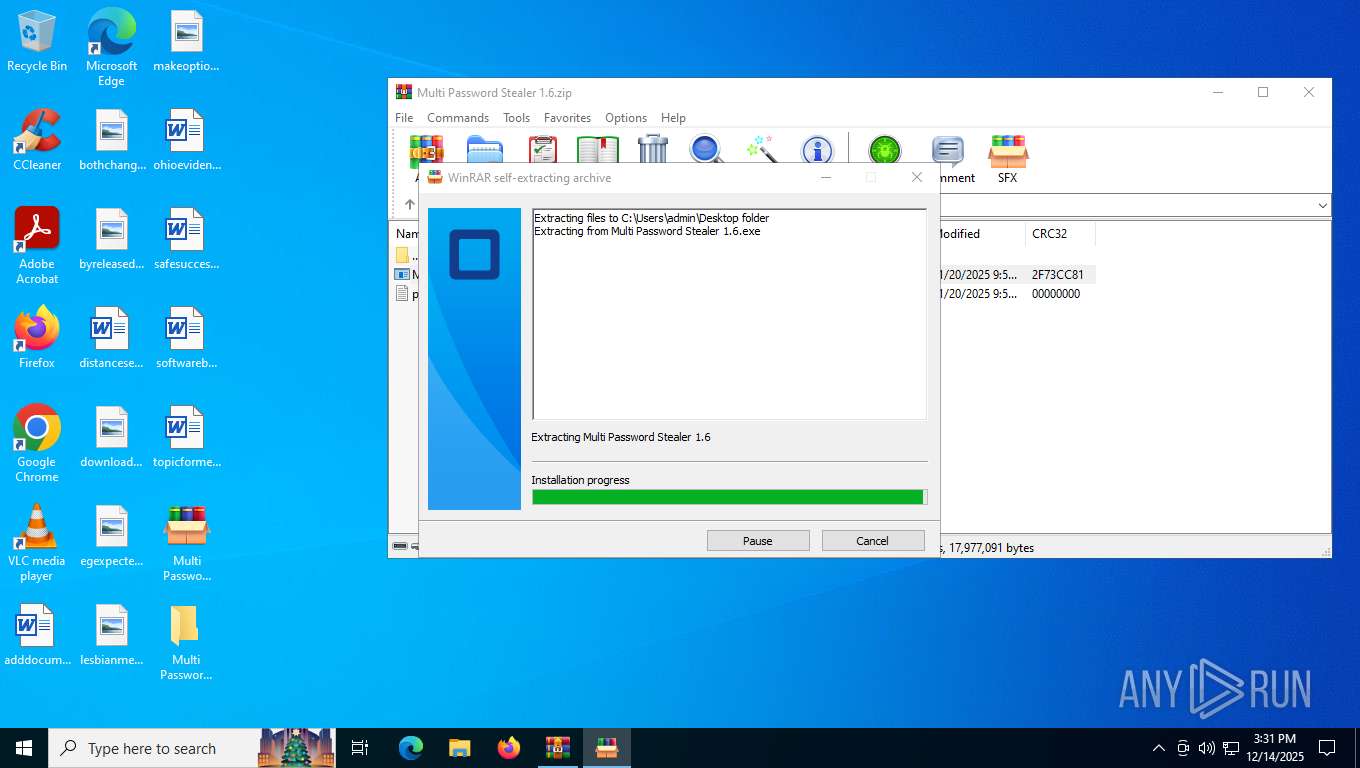
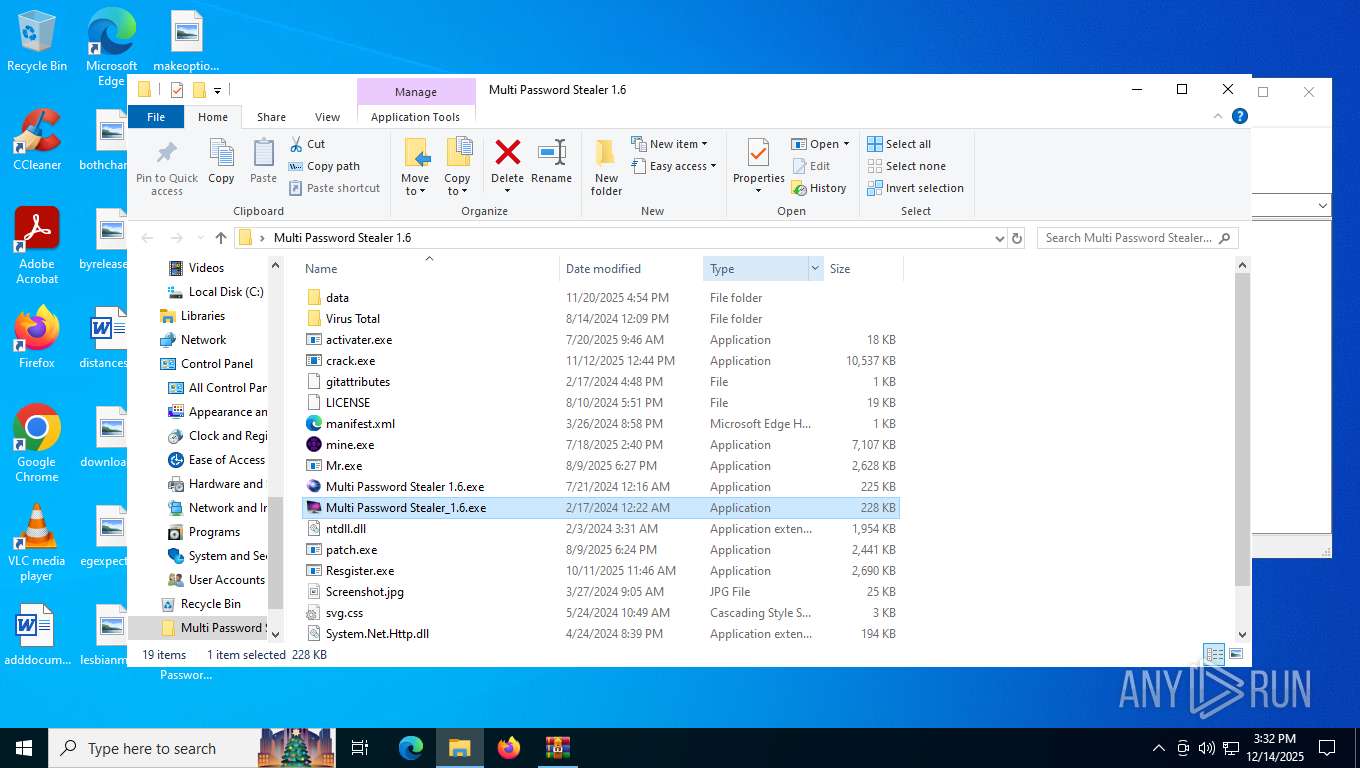
Executable content was dropped or overwritten
- Multi Password Stealer 1.6.exe (PID: 940)
- mine.exe (PID: 8096)
- Mr.exe (PID: 7756)
- crack.exe (PID: 5424)
- activater.exe (PID: 7384)
- crack.exe (PID: 7328)
Process drops legitimate windows executable
- Multi Password Stealer 1.6.exe (PID: 940)
- crack.exe (PID: 5424)
There is functionality for taking screenshot (YARA)
- Multi Password Stealer 1.6.exe (PID: 940)
- mps.exe (PID: 7956)
- crack.exe (PID: 5424)
Connects to SMTP port
- mps.exe (PID: 7956)
Starts CMD.EXE for commands execution
- Mr.exe (PID: 8160)
Drops a system driver (possible attempt to evade defenses)
- mine.exe (PID: 8096)
Starts itself from another location
- Mr.exe (PID: 7756)
Reads the date of Windows installation
- mine.exe (PID: 8096)
The process creates files with name similar to system file names
- Mr.exe (PID: 7756)
Checks for external IP
- svchost.exe (PID: 2292)
- crack.exe (PID: 7328)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2292)
Browser headless start
- chrome.exe (PID: 7724)
- chrome.exe (PID: 6952)
- msedge.exe (PID: 3656)
- msedge.exe (PID: 1600)
- msedge.exe (PID: 4816)
- msedge.exe (PID: 7348)
- msedge.exe (PID: 6908)
Potential Corporate Privacy Violation
- OmegaEngine.exe (PID: 3152)
The process drops C-runtime libraries
- crack.exe (PID: 5424)
Process drops python dynamic module
- crack.exe (PID: 5424)
Multiple wallet extension IDs have been found
- svchost.exe (PID: 8004)
Found regular expressions for crypto-addresses (YARA)
- activater.exe (PID: 7384)
Loads Python modules
- crack.exe (PID: 7328)
Possible usage of Discord/Telegram API has been detected (YARA)
- svchost.exe (PID: 8004)
Reads browser cookies
- svchost.exe (PID: 8004)
Application launched itself
- crack.exe (PID: 5424)
INFO
Application launched itself
- chrome.exe (PID: 7504)
- chrome.exe (PID: 7724)
- msedge.exe (PID: 3656)
- msedge.exe (PID: 1600)
- msedge.exe (PID: 4816)
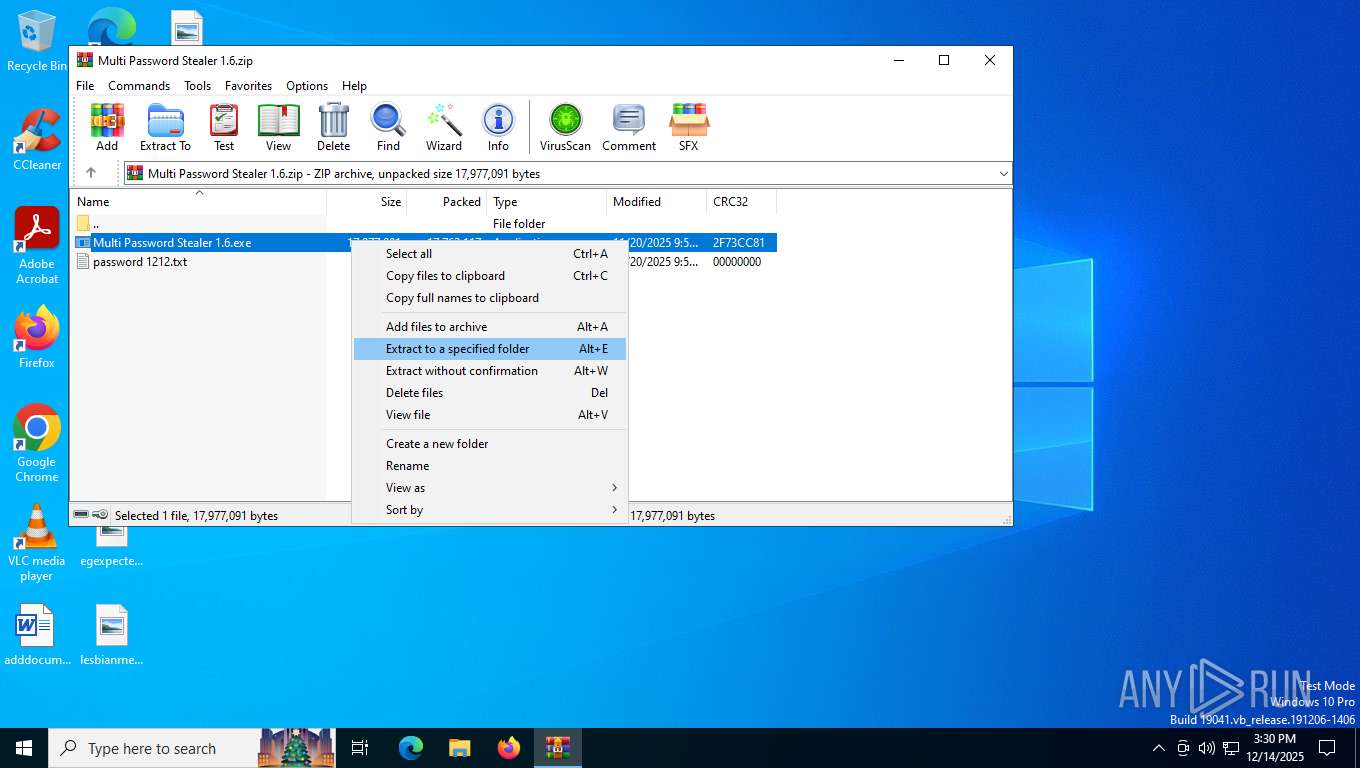
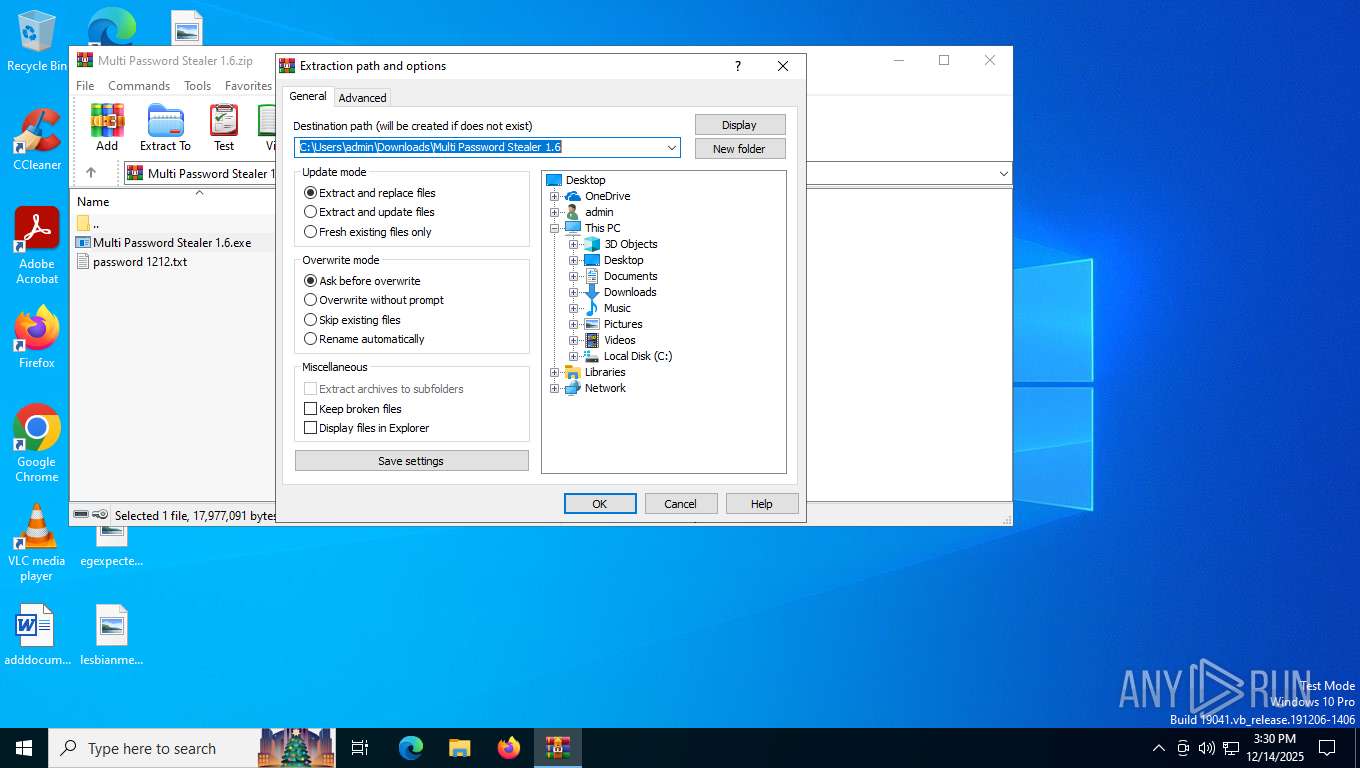
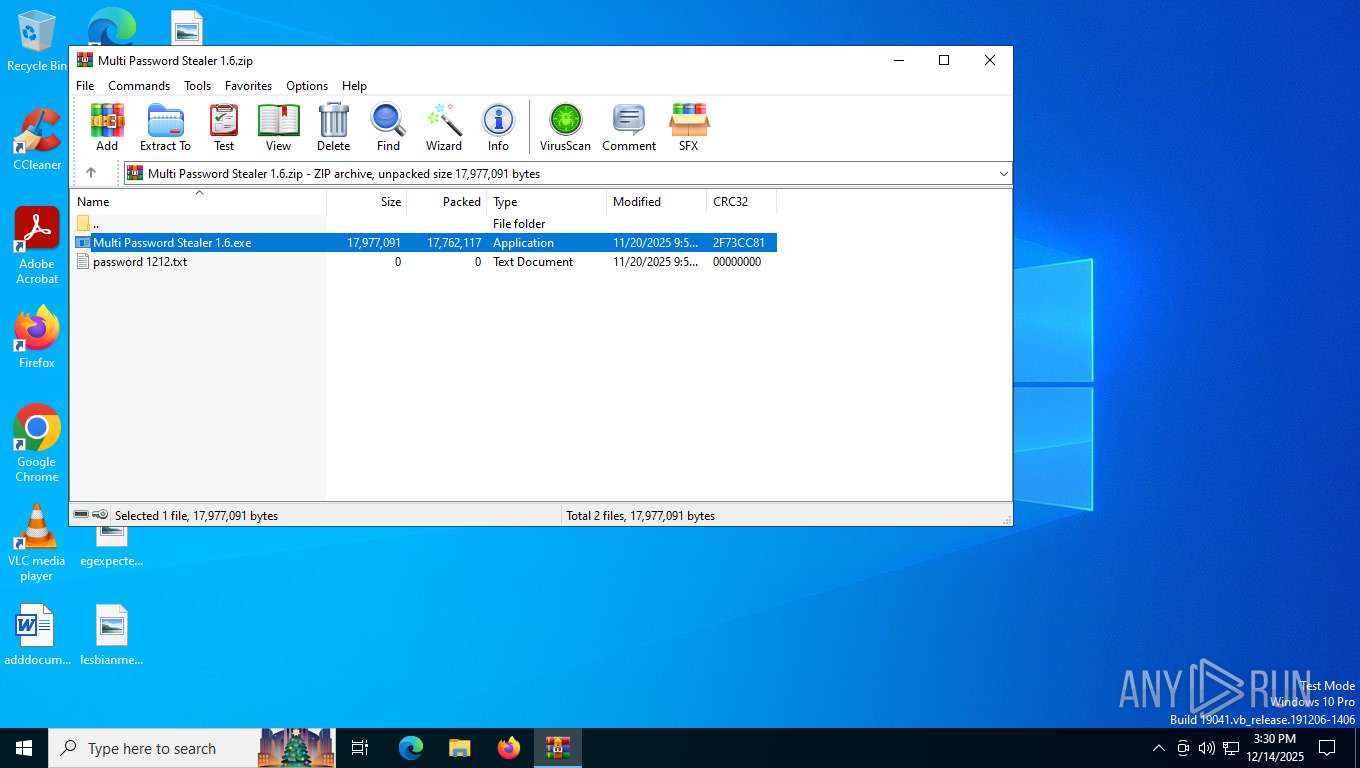
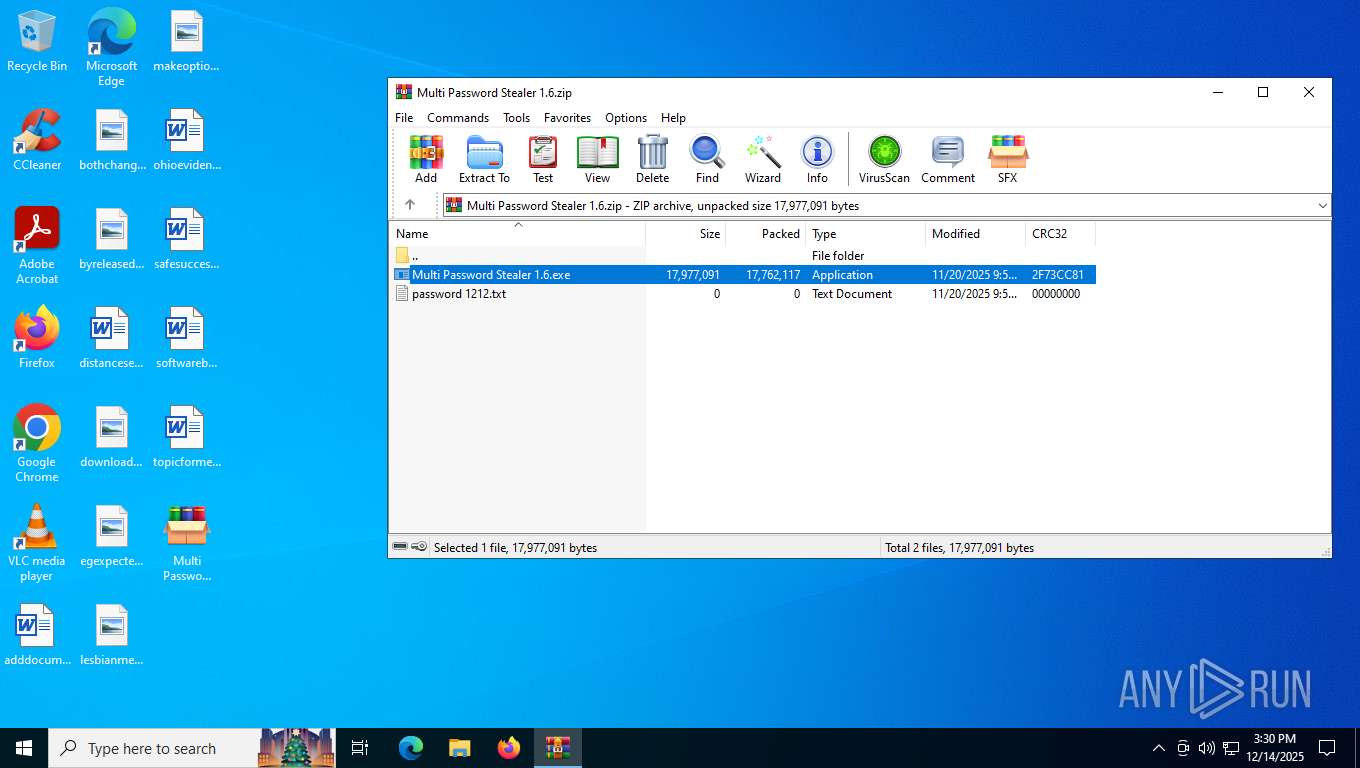
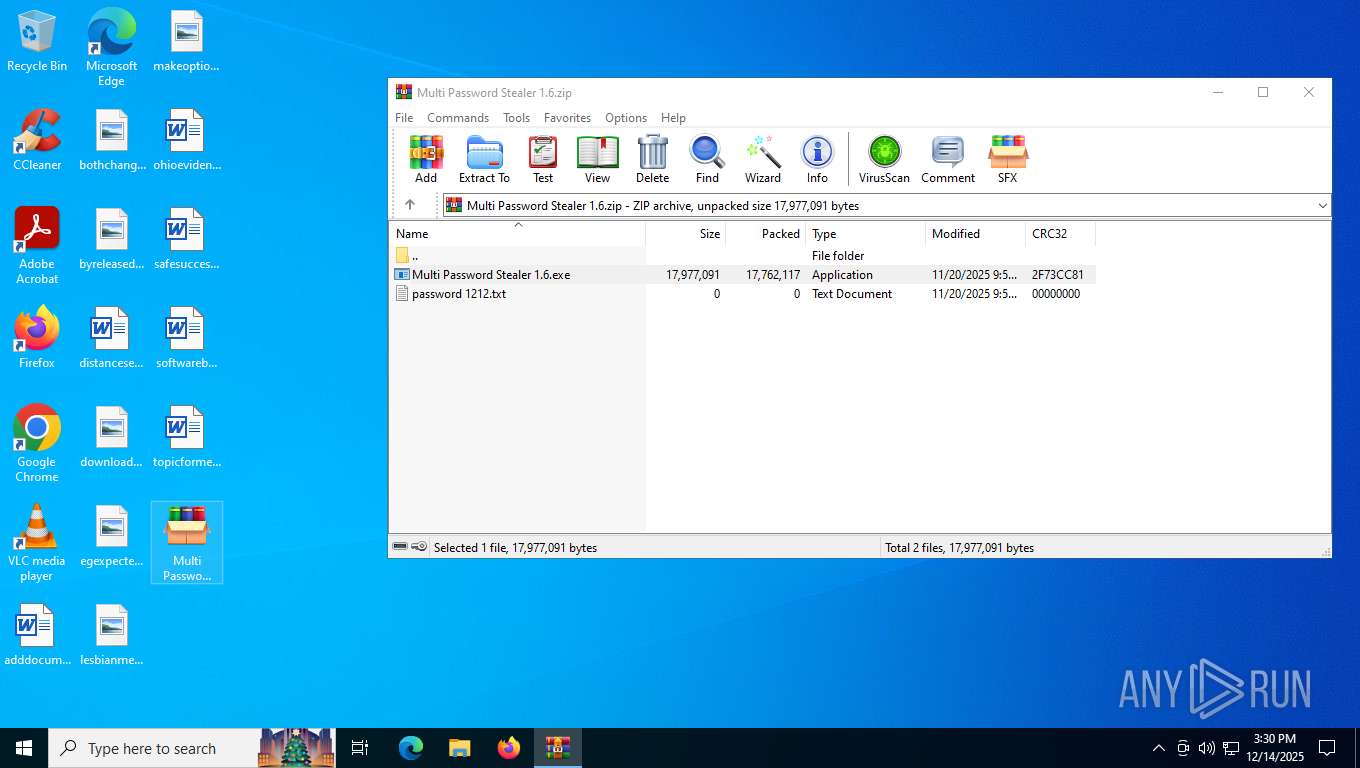
Launching a file from the Downloads directory
- chrome.exe (PID: 7504)
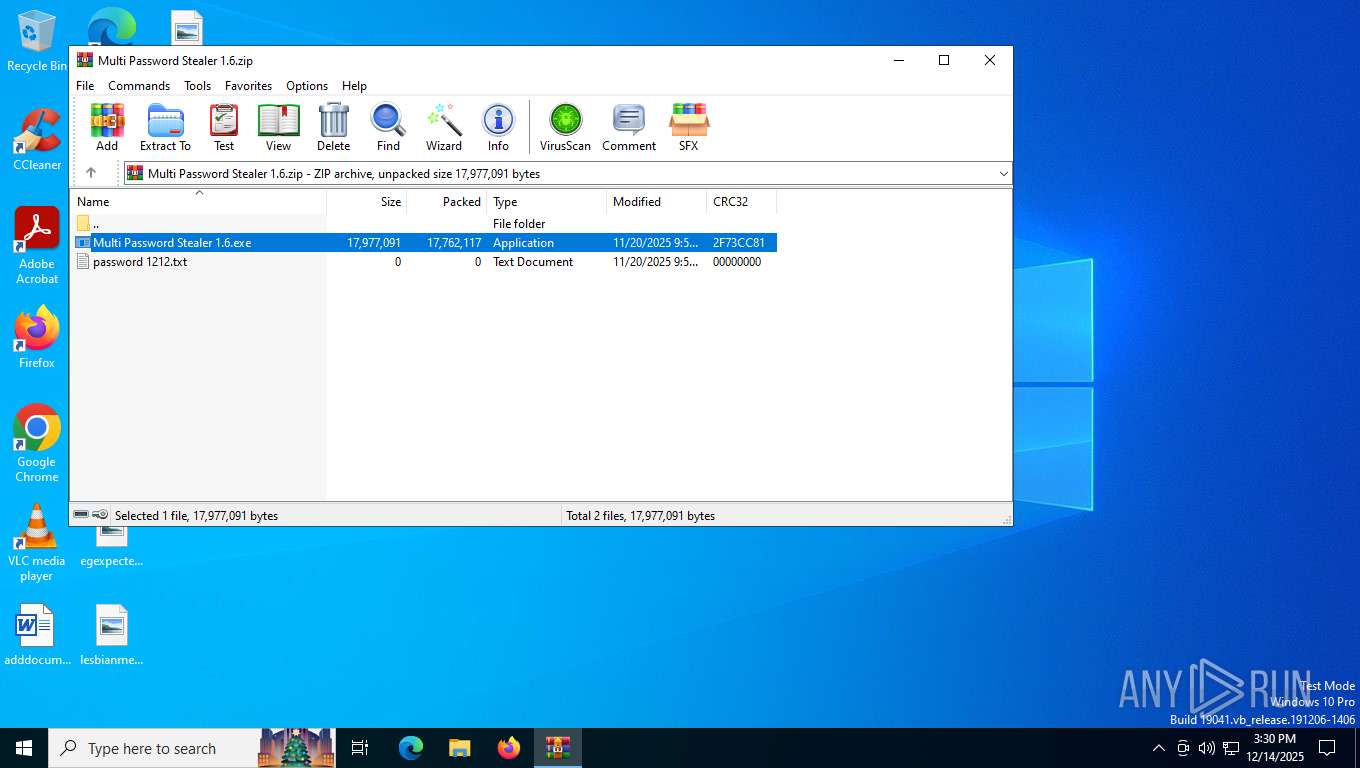
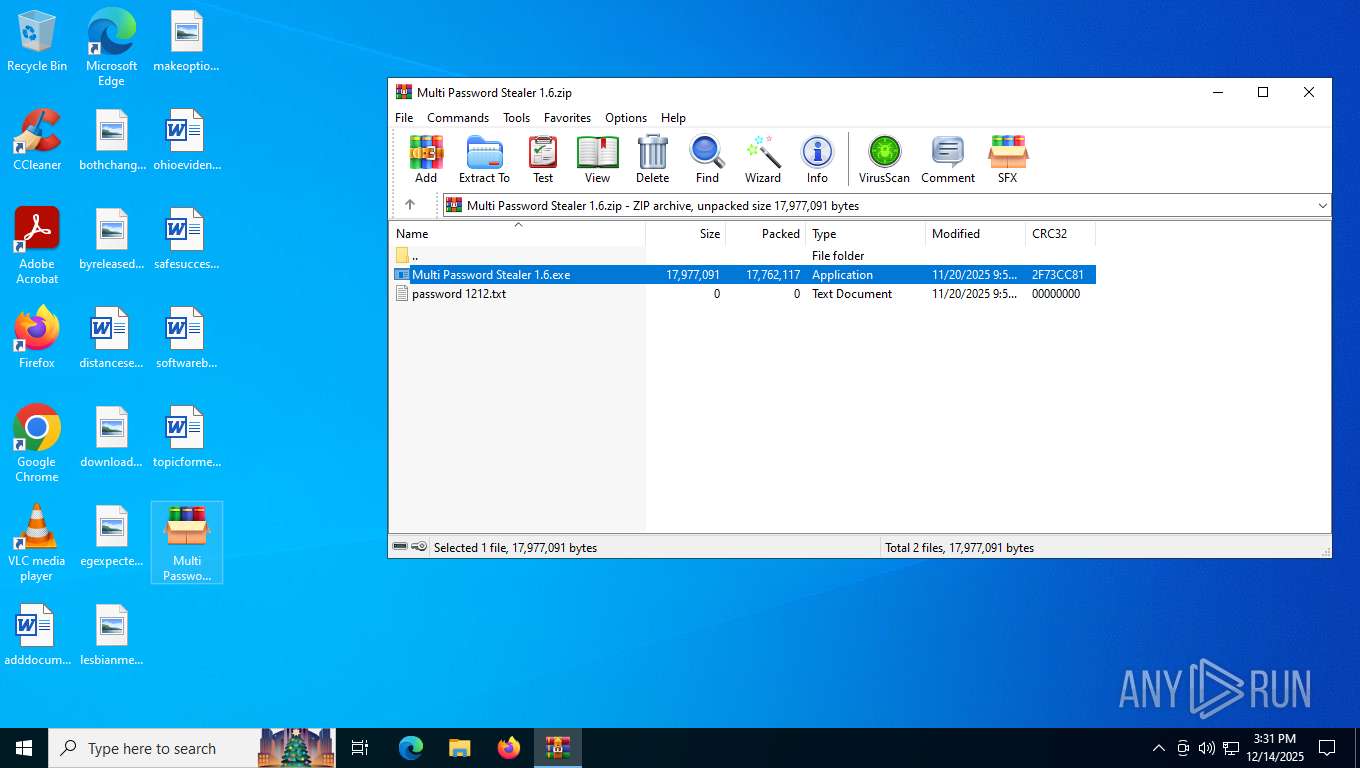
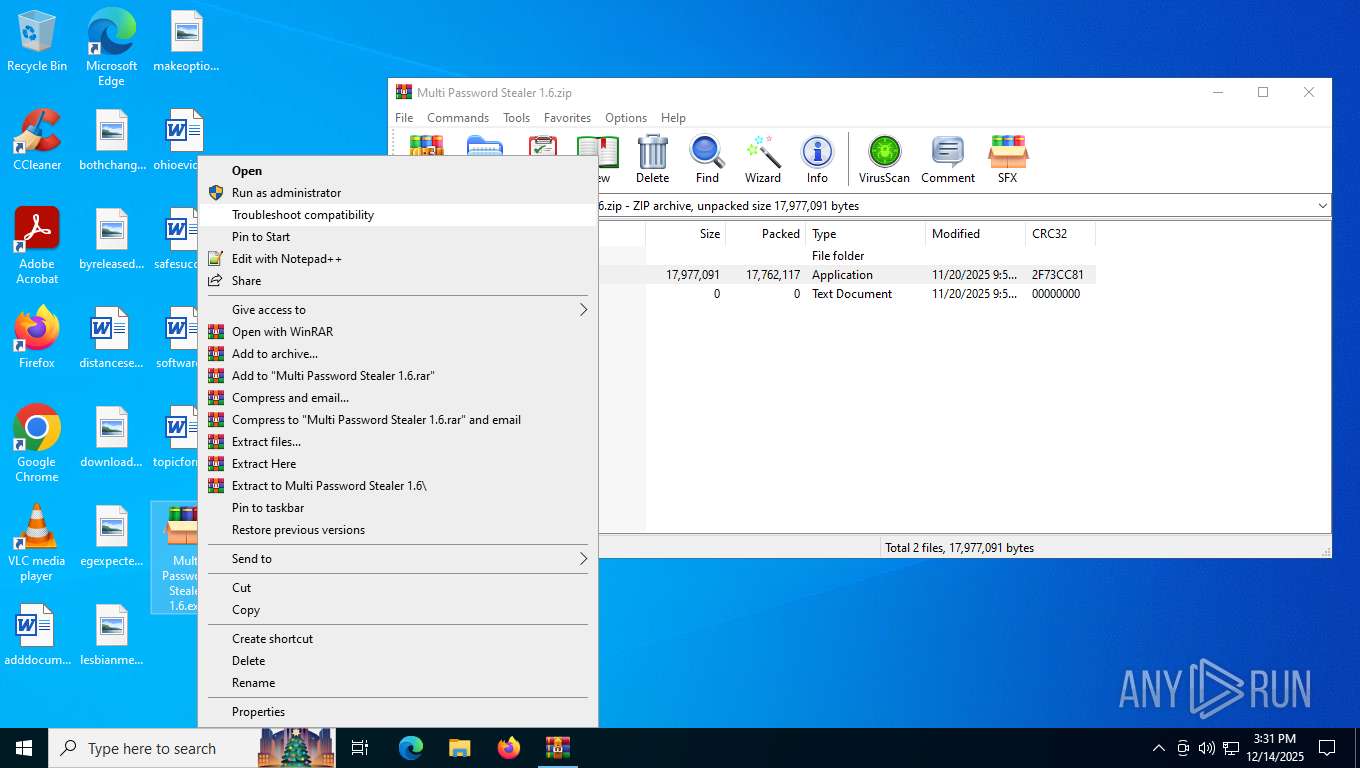
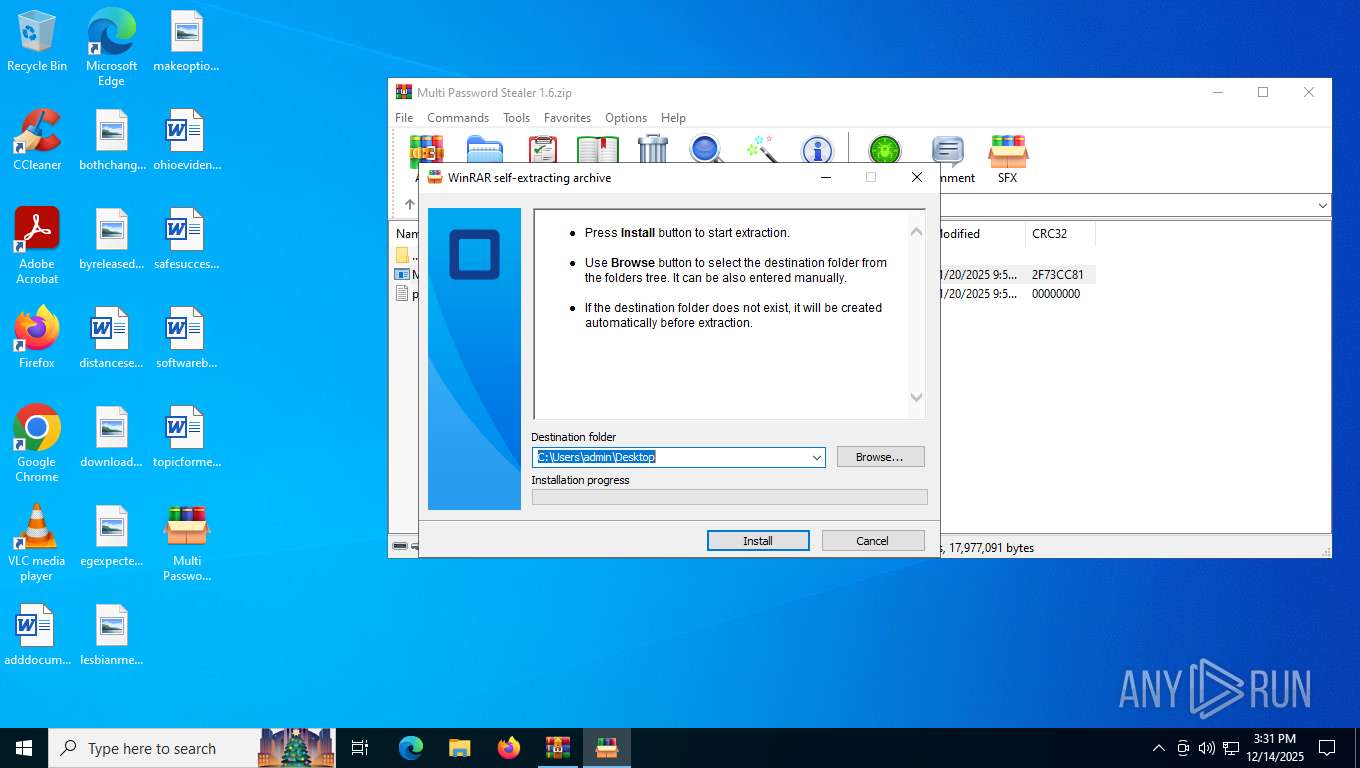
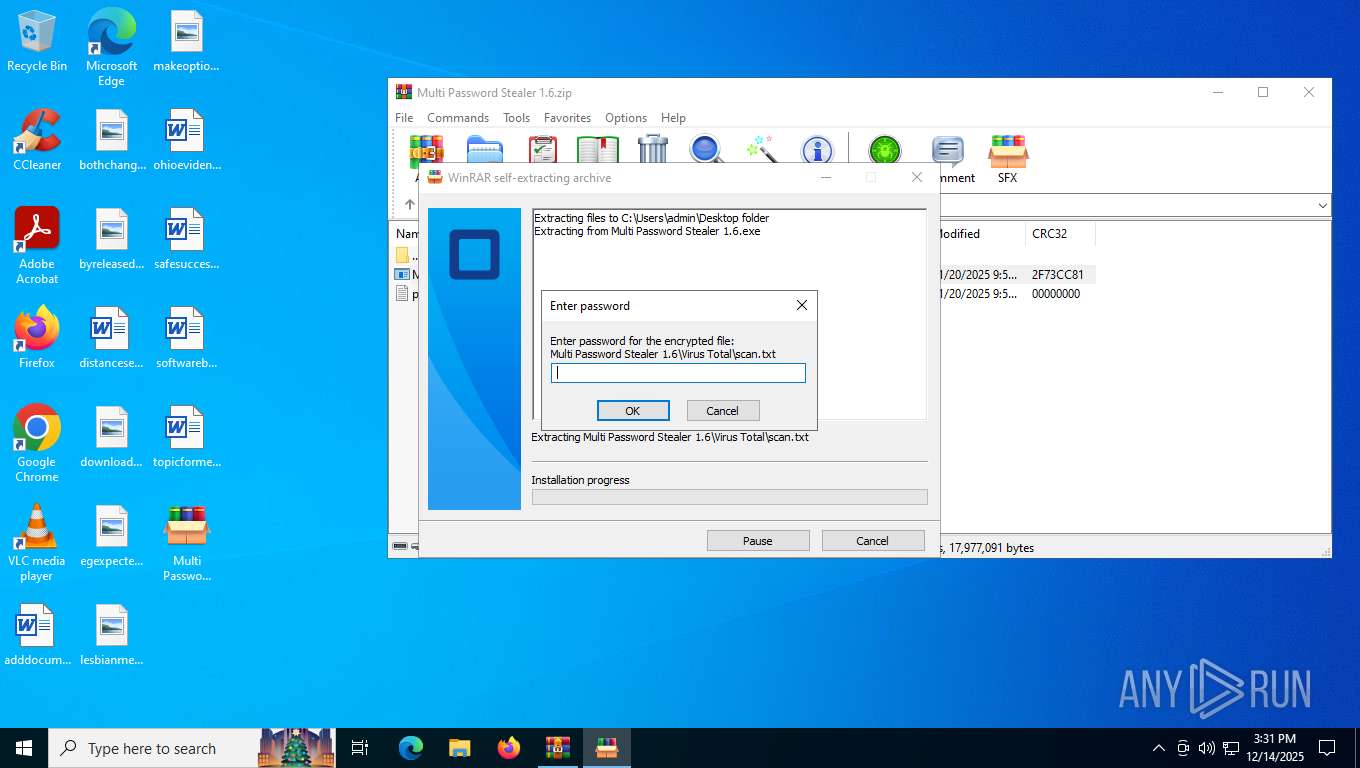
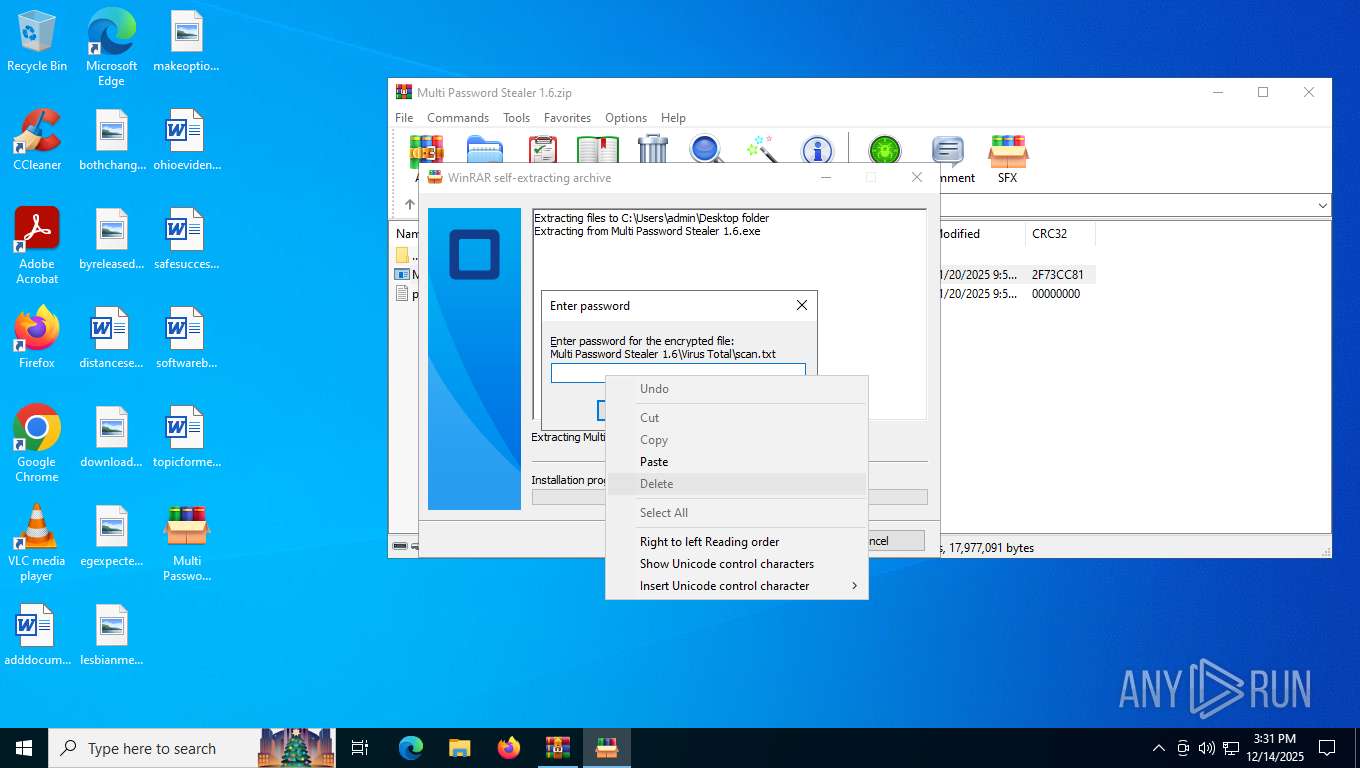
Manual execution by a user
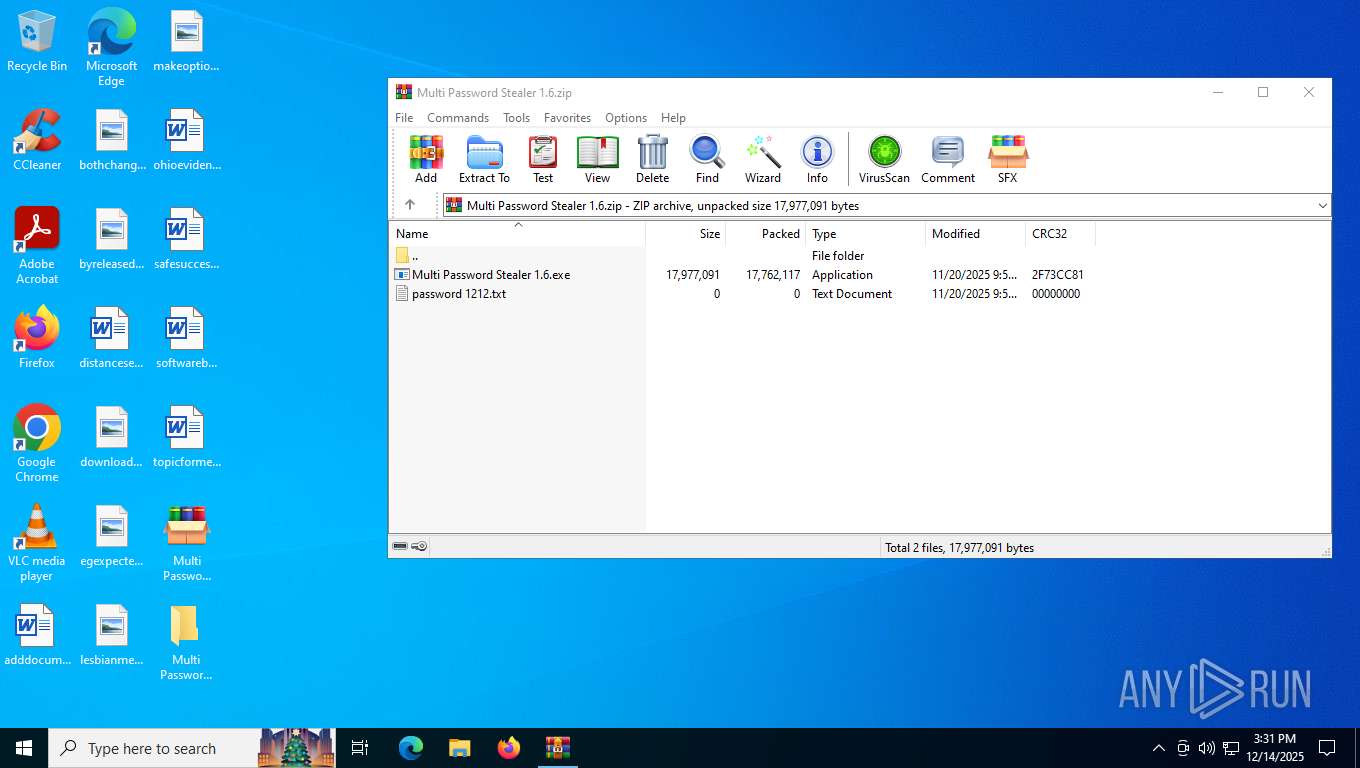
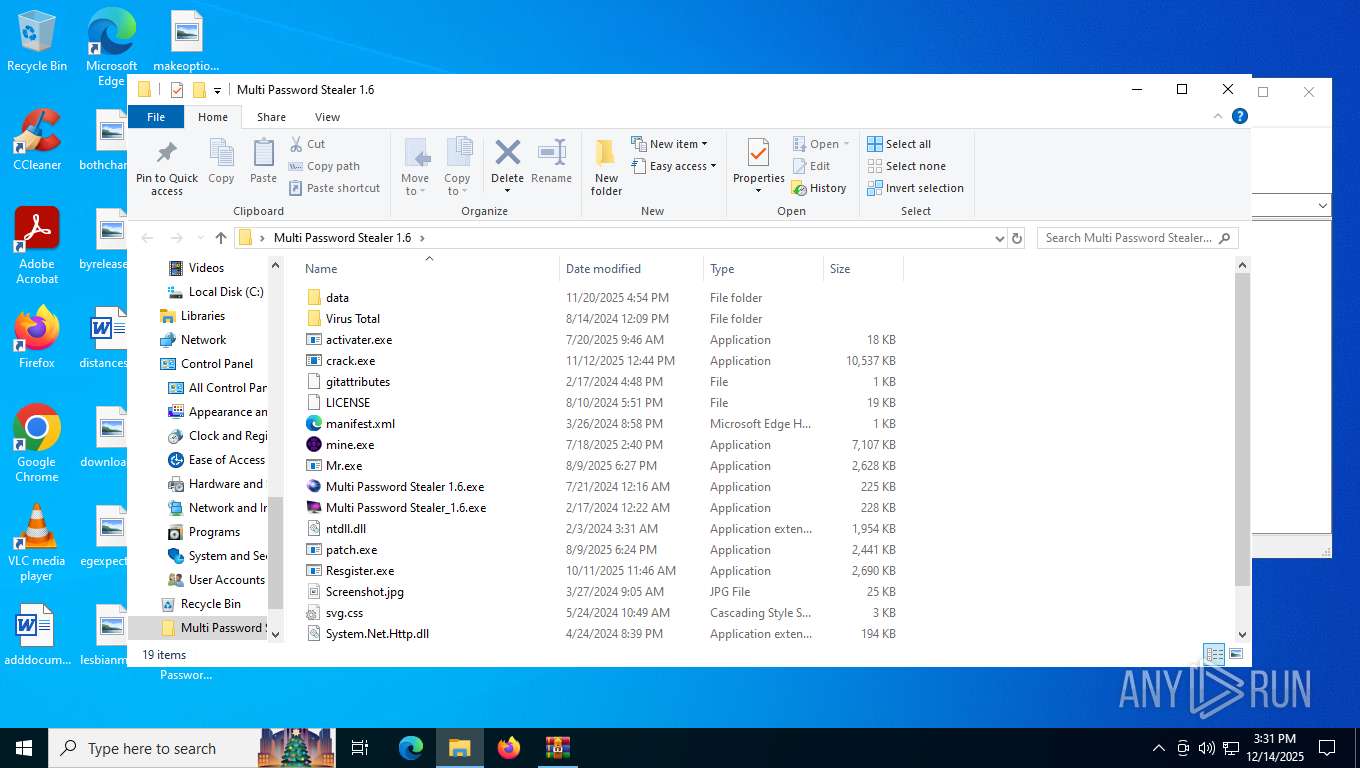
- Multi Password Stealer 1.6.exe (PID: 940)
- Multi Password Stealer_1.6.exe (PID: 1340)
- Mr.exe (PID: 8160)
- mine.exe (PID: 8096)
- crack.exe (PID: 5424)
- activater.exe (PID: 7384)
- msedge.exe (PID: 4816)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6624)
Checks supported languages
- Multi Password Stealer 1.6.exe (PID: 940)
- Multi Password Stealer_1.6.exe (PID: 1340)
- mps.exe (PID: 7956)
- Mr.exe (PID: 8160)
- Mr.exe (PID: 7756)
- mine.exe (PID: 8096)
- svchost.exe (PID: 8004)
- crack.exe (PID: 5424)
- OmegaEngine.exe (PID: 3152)
- activater.exe (PID: 7384)
- crack.exe (PID: 7328)
Reads the computer name
- Multi Password Stealer 1.6.exe (PID: 940)
- Multi Password Stealer_1.6.exe (PID: 1340)
- mps.exe (PID: 7956)
- Mr.exe (PID: 8160)
- mine.exe (PID: 8096)
- OmegaEngine.exe (PID: 3152)
- svchost.exe (PID: 8004)
- crack.exe (PID: 5424)
- activater.exe (PID: 7384)
- crack.exe (PID: 7328)
Checks proxy server information
- Multi Password Stealer 1.6.exe (PID: 940)
- mps.exe (PID: 7956)
- slui.exe (PID: 7200)
The sample compiled with english language support
- Multi Password Stealer 1.6.exe (PID: 940)
- crack.exe (PID: 5424)
Reads the machine GUID from the registry
- Multi Password Stealer_1.6.exe (PID: 1340)
- activater.exe (PID: 7384)
Process checks computer location settings
- Multi Password Stealer_1.6.exe (PID: 1340)
- Mr.exe (PID: 8160)
- mine.exe (PID: 8096)
Creates files or folders in the user directory
- mps.exe (PID: 7956)
- Mr.exe (PID: 7756)
- activater.exe (PID: 7384)
- svchost.exe (PID: 8004)
- crack.exe (PID: 7328)
Create files in a temporary directory
- mps.exe (PID: 7956)
- crack.exe (PID: 5424)
UPX packer has been detected
- mps.exe (PID: 7956)
Compiled with Borland Delphi (YARA)
- mps.exe (PID: 7956)
The sample compiled with japanese language support
- mine.exe (PID: 8096)
Launching a file from the Startup directory
- activater.exe (PID: 7384)
Launching a file from a Registry key
- crack.exe (PID: 7328)
Attempting to use instant messaging service
- svchost.exe (PID: 8004)
PyInstaller has been detected (YARA)
- crack.exe (PID: 5424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(8004) svchost.exe
Telegram-Tokens (1)7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U
Telegram-Info-Links
7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U
Get info about bothttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/getMe
Get incoming updateshttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/getUpdates
Get webhookhttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U
End-PointsendMessage
Args
chat_id (1)7540145121
text (1)🖥Computer info:
System: Microsoft Windows 10 Pro (x64)
Computer name: DESKTOP-JGLLJLD
User name: admin
System time: 2025-12-14 03:32:21 PM
CPU: AMD Ryzen 5 3500 6-Core Processor
GPU: Microsoft Basic Display Adapter
RAM: 6138 MB
HWID: 078BFBFF00800F12
🛡Security:
Installed antivirus: Windows%2
Telegram-Tokens (1)7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U
Telegram-Info-Links
7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U
Get info about bothttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/getMe
Get incoming updateshttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/getUpdates
Get webhookhttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7929677763:AAEuKsIo2xD5TBD1mTEbqBGPdabbARKmm-U/deleteWebhook?drop_pending_updates=true
Total processes
203
Monitored processes
52
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\User Data" --enable-dinosaur-easter-egg-alt-images --remote-debugging-port=9222 --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4640,i,7951841033920837134,16788470572039743942,262144 --disable-features=PaintHolding --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4636 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 940 | "C:\Users\admin\Desktop\Multi Password Stealer 1.6.exe" | C:\Users\admin\Desktop\Multi Password Stealer 1.6.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5552,i,9604266255644050628,865480333996128242,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1340 | "C:\Users\admin\Desktop\Multi Password Stealer 1.6\Multi Password Stealer_1.6.exe" | C:\Users\admin\Desktop\Multi Password Stealer 1.6\Multi Password Stealer_1.6.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\User Data" --field-trial-handle=2288,i,7951841033920837134,16788470572039743942,262144 --disable-features=PaintHolding --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2280 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --remote-debugging-port=9222 --user-data-dir="C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --profile-directory=Default --headless --disable-gpu --edge-skip-compat-layer-relaunch | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\User Data" --extension-process --enable-dinosaur-easter-egg-alt-images --remote-debugging-port=9222 --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3636,i,7951841033920837134,16788470572039743942,262144 --disable-features=PaintHolding --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3632 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\User Data" --field-trial-handle=2064,i,7951841033920837134,16788470572039743942,262144 --disable-features=PaintHolding --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2060 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\User Data" --field-trial-handle=4880,i,7951841033920837134,16788470572039743942,262144 --disable-features=PaintHolding --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4876 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
12 949
Read events
12 909
Write events
22
Delete events
18
Modification events
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Multi Password Stealer 1.6.zip | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
68
Suspicious files
183
Text files
1 038
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFf6bef.TMP | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFf6bff.TMP | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFf6bff.TMP | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFf6bff.TMP | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFf6bff.TMP | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RFf6bff.TMP | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
437
TCP/UDP connections
209
DNS requests
114
Threats
213
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7764 | chrome.exe | GET | 200 | 172.217.23.110:80 | http://clients2.google.com/time/1/current?cup2key=8:Zij0iRIA3sXleT11l5VraWzHo_KycHmlev_0k_zgjik&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
7764 | chrome.exe | GET | 200 | 142.250.186.138:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
7764 | chrome.exe | GET | 200 | 31.216.145.5:443 | https://mega.nz/file/PoAVXLAT | LU | html | 2.05 Kb | whitelisted |
7764 | chrome.exe | GET | 200 | 31.216.145.5:443 | https://mega.nz/loading-sprite_light.png | LU | image | 8.41 Kb | whitelisted |
7764 | chrome.exe | GET | 200 | 31.216.145.5:443 | https://mega.nz/secureboot.js?r=1765430884 | LU | binary | 128 Kb | whitelisted |
7764 | chrome.exe | GET | 200 | 31.216.145.5:443 | https://mega.nz/manifest.json | LU | binary | 806 b | whitelisted |
7764 | chrome.exe | GET | 200 | 31.216.145.5:443 | https://mega.nz/favicon.ico?v=3 | LU | image | 6.37 Kb | whitelisted |
7764 | chrome.exe | GET | 200 | 31.216.145.5:443 | https://mega.nz/secureboot.js?r=1765430884 | LU | binary | 128 Kb | whitelisted |
7764 | chrome.exe | GET | 200 | 66.203.127.11:443 | https://eu.static.mega.co.nz/4/lang/en_883bd0f1c7bfad2363db4ef1e81053b0c6a6a6a7e5fda07620afc25ca0e6d89f.json | NZ | text | 128 Kb | whitelisted |
7764 | chrome.exe | GET | 200 | 66.203.127.11:443 | https://eu.static.mega.co.nz/4/js/BDL-1_6ed957bbbf0a5edc78715b929223c283d7aafd3ee8d241fba2ea50b95f925dc4.js | NZ | binary | 128 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3060 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4828 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.241.201:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7764 | chrome.exe | 172.217.23.110:80 | clients2.google.com | GOOGLE | US | whitelisted |
7764 | chrome.exe | 142.250.186.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7764 | chrome.exe | 31.216.145.5:443 | mega.nz | MEGA-LIMITED-AS Mega Limited | LU | whitelisted |
7764 | chrome.exe | 66.203.127.11:443 | eu.static.mega.co.nz | MEGA | NZ | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| whitelisted |
g.api.mega.co.nz |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7764 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7764 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Google\Chrome\User Data directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Microsoft\Edge\User Data directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Microsoft\Edge\User Data directory exists )
|