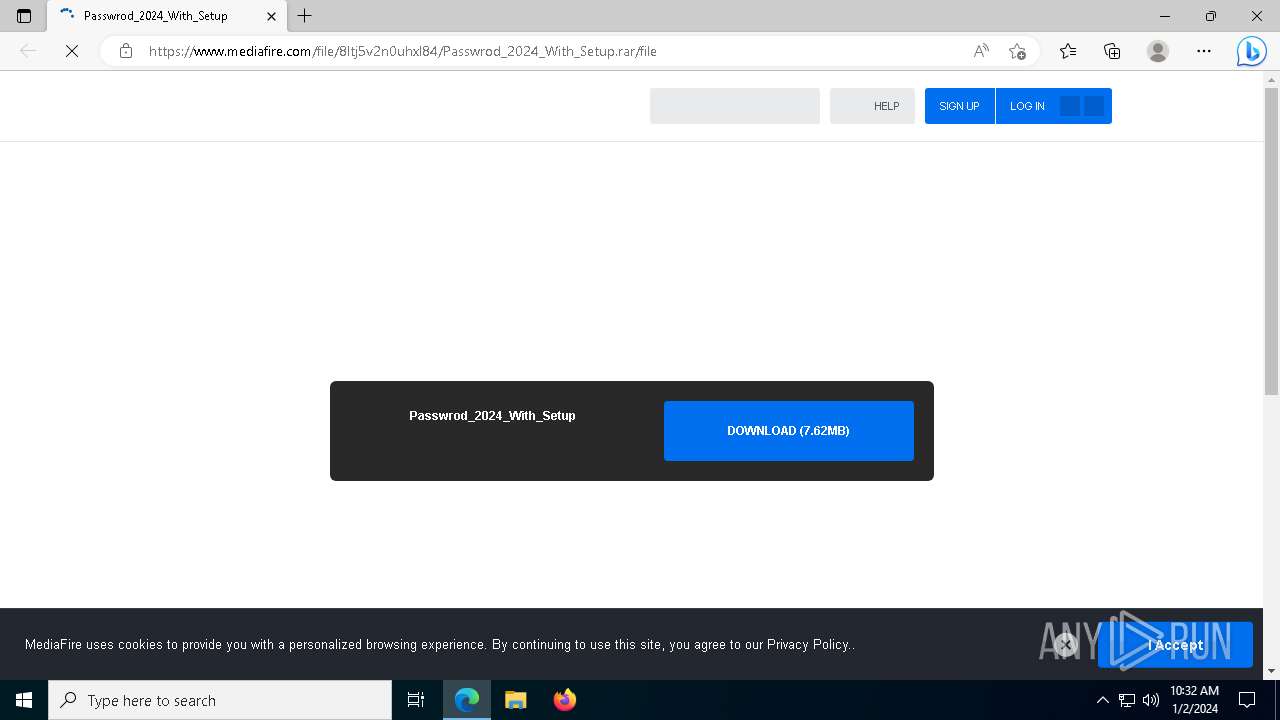
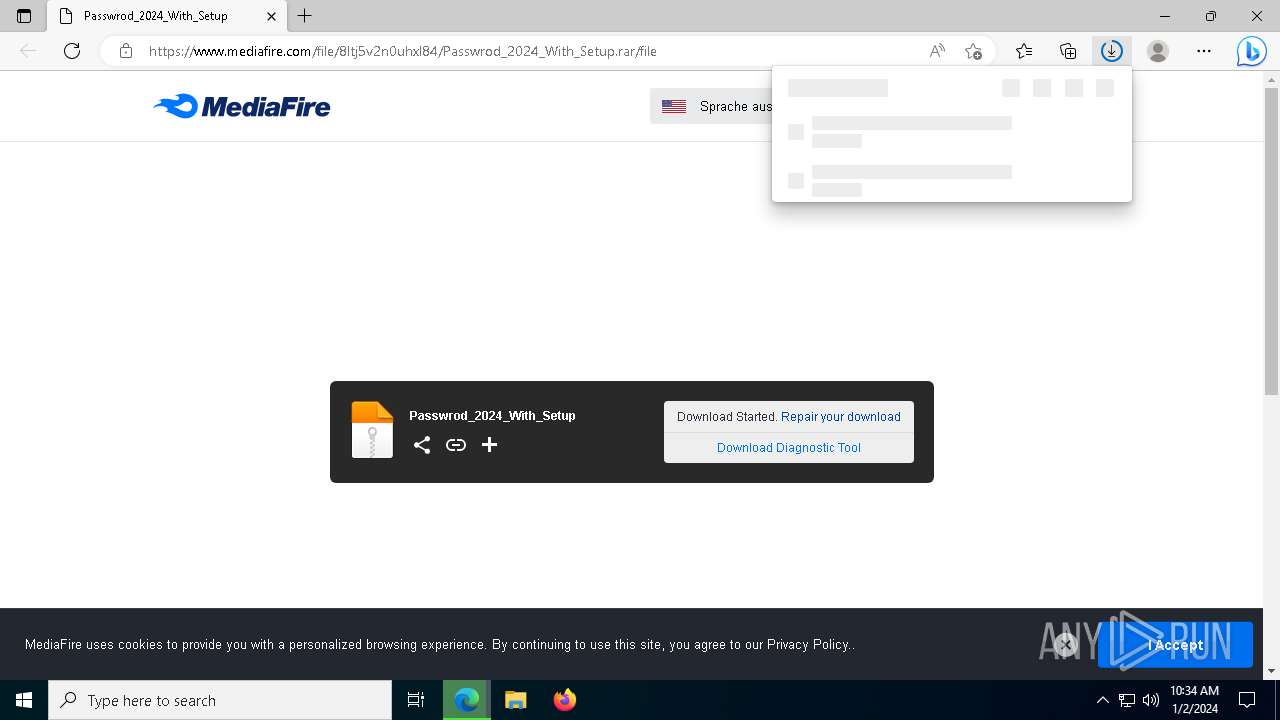
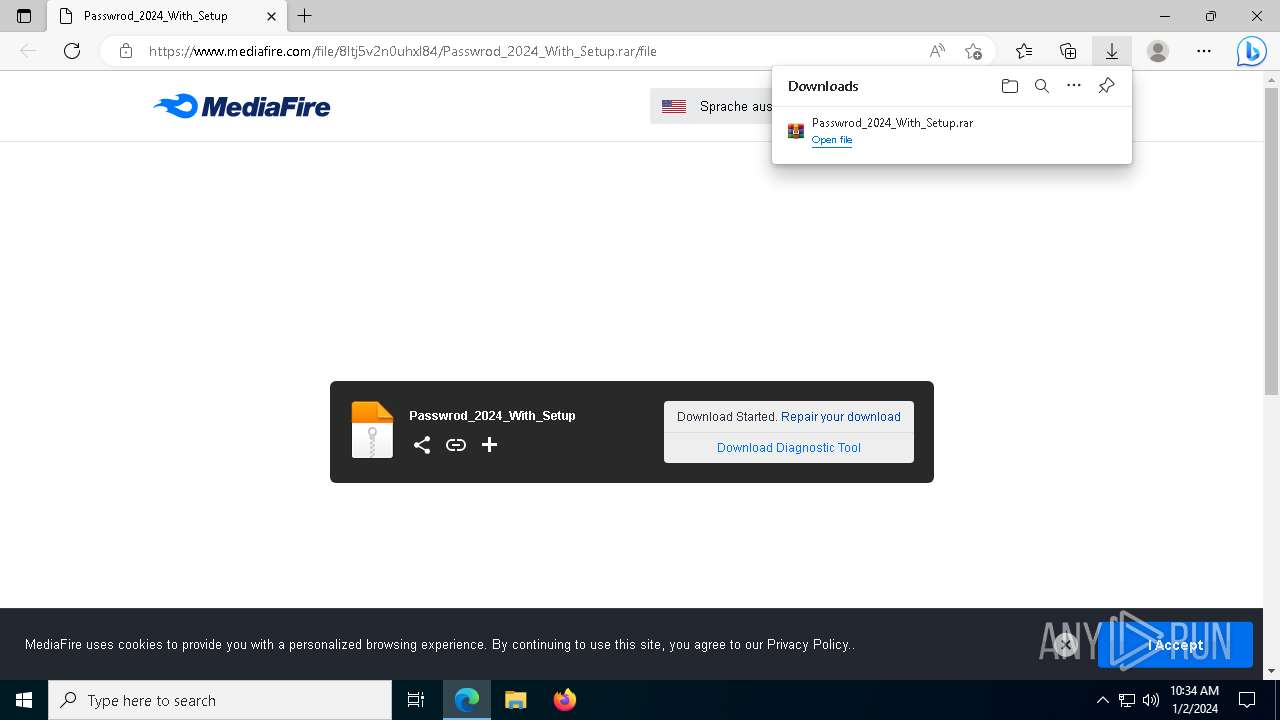
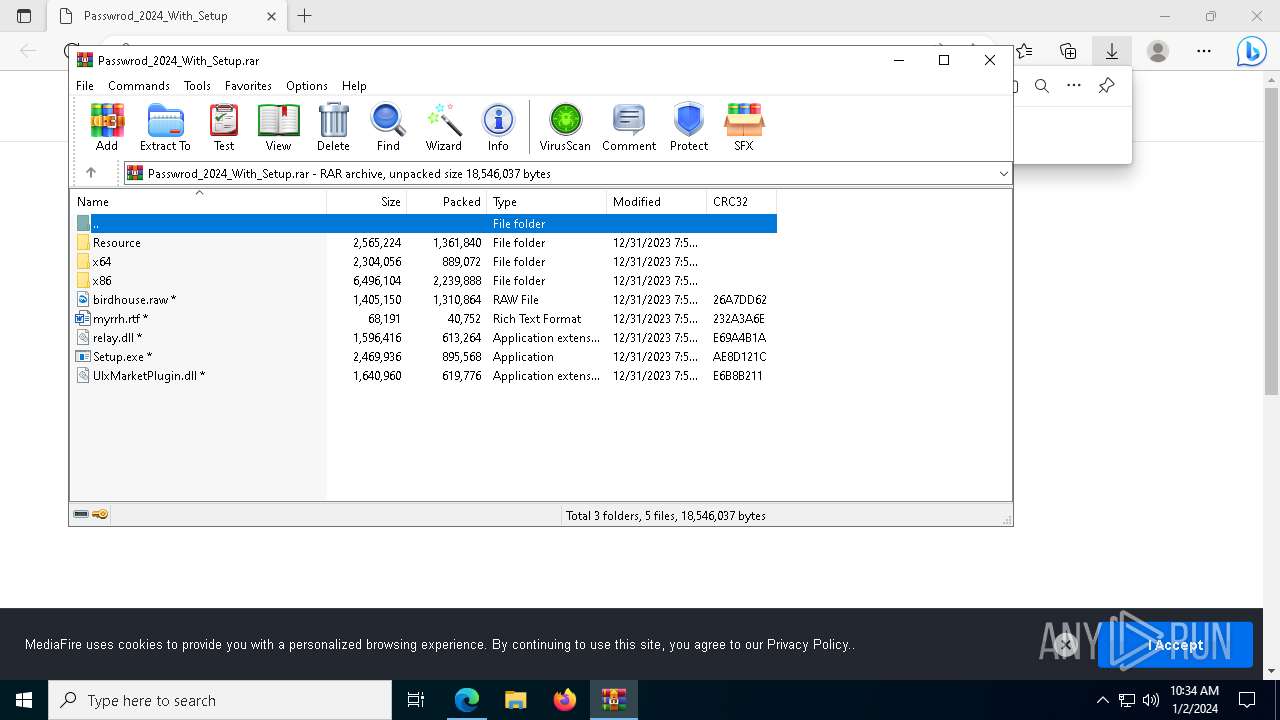
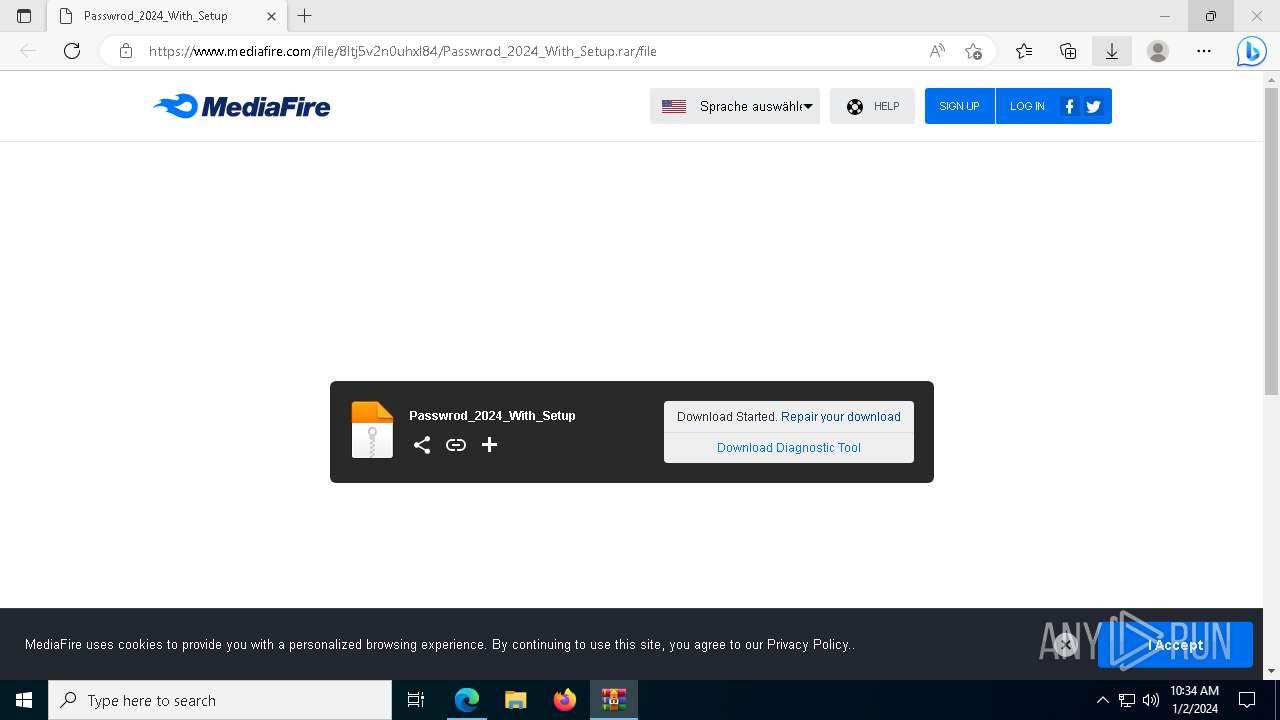
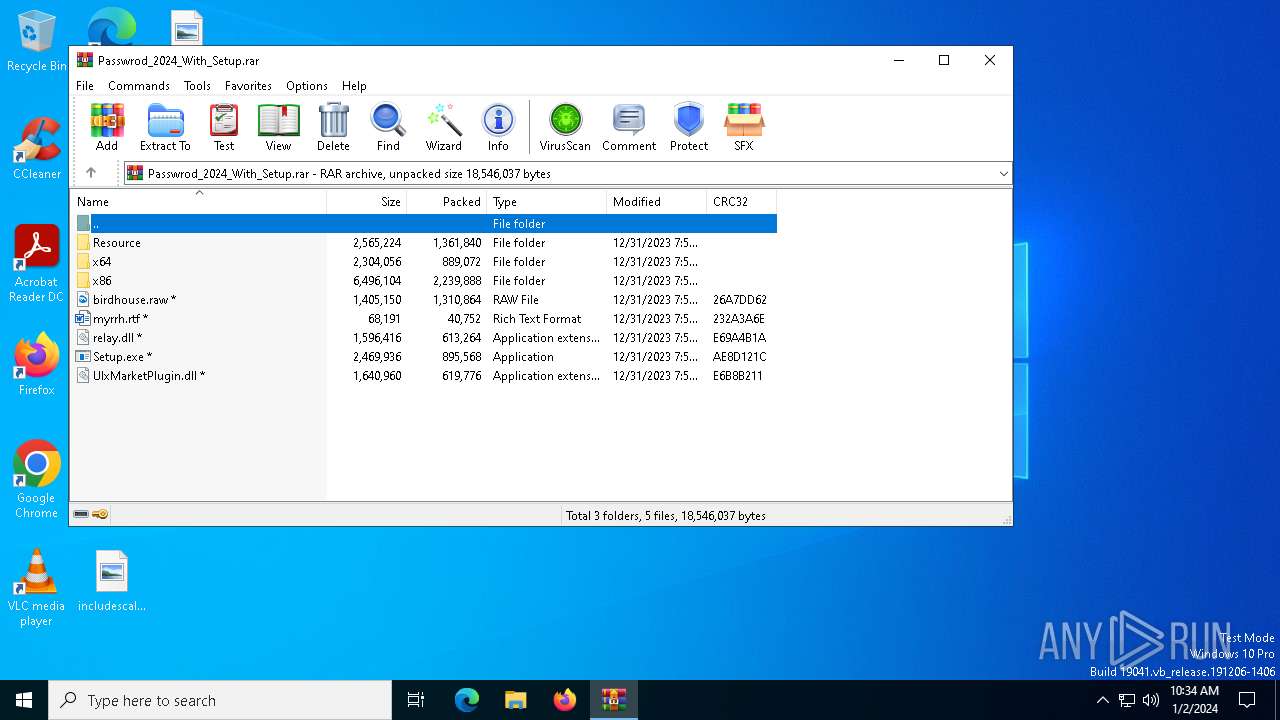
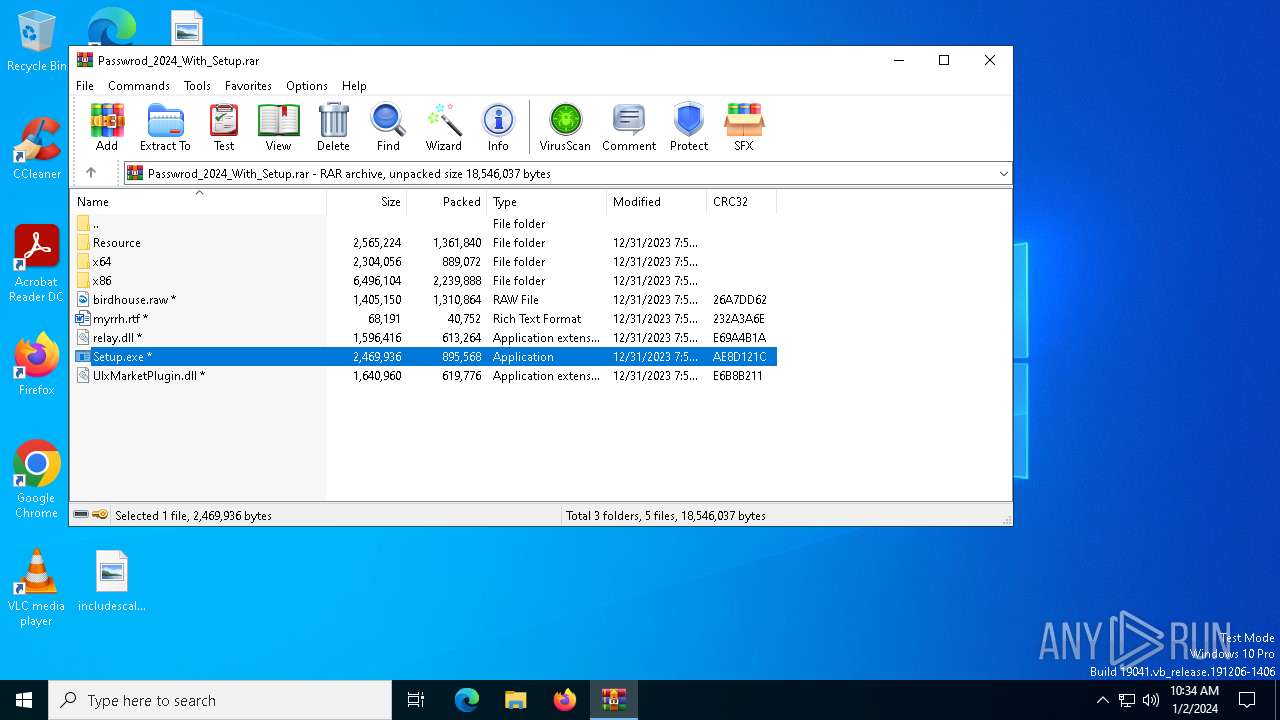
| URL: | https://www.mediafire.com/file/8ltj5v2n0uhxl84/Passwrod_2024_With_Setup.rar/file |
| Full analysis: | https://app.any.run/tasks/808e44ff-0081-41d2-9634-d46bc49efa13 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | January 02, 2024, 10:32:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DA50724B9D8B95A68799F5F62B9CE8E3 |
| SHA1: | 95333E32F2BA24F0DF495EB3B3C8743E6FD3D82D |
| SHA256: | 0648C135C15A2C5EC1EA5457BD5A7B834454D98155BAA293F7A05233CFFB88C5 |
| SSDEEP: | 3:N8DSLw3eGUodGWPI1wWW5oR5KcA:2OLw3eG5G51wWxycA |
MALICIOUS
LUMMA has been detected (YARA)
- cmd.exe (PID: 6712)
- RarExt32.exe (PID: 5128)
HIJACKLOADER has been detected (YARA)
- RarExt32.exe (PID: 5128)
- cmd.exe (PID: 6712)
Actions looks like stealing of personal data
- RarExt32.exe (PID: 5128)
- rundll32.exe (PID: 4104)
Uses Task Scheduler to run other applications
- XRJNZC.exe (PID: 6896)
- Utsysc.exe (PID: 3876)
- OneDrive.exe (PID: 4476)
- OneDrive.exe (PID: 6744)
Changes the autorun value in the registry
- Utsysc.exe (PID: 3876)
Steals credentials from Web Browsers
- rundll32.exe (PID: 4104)
SUSPICIOUS
Starts CMD.EXE for commands execution
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- T7VEM6FUG5I90S4270BRJWBLJHZ.exe (PID: 1876)
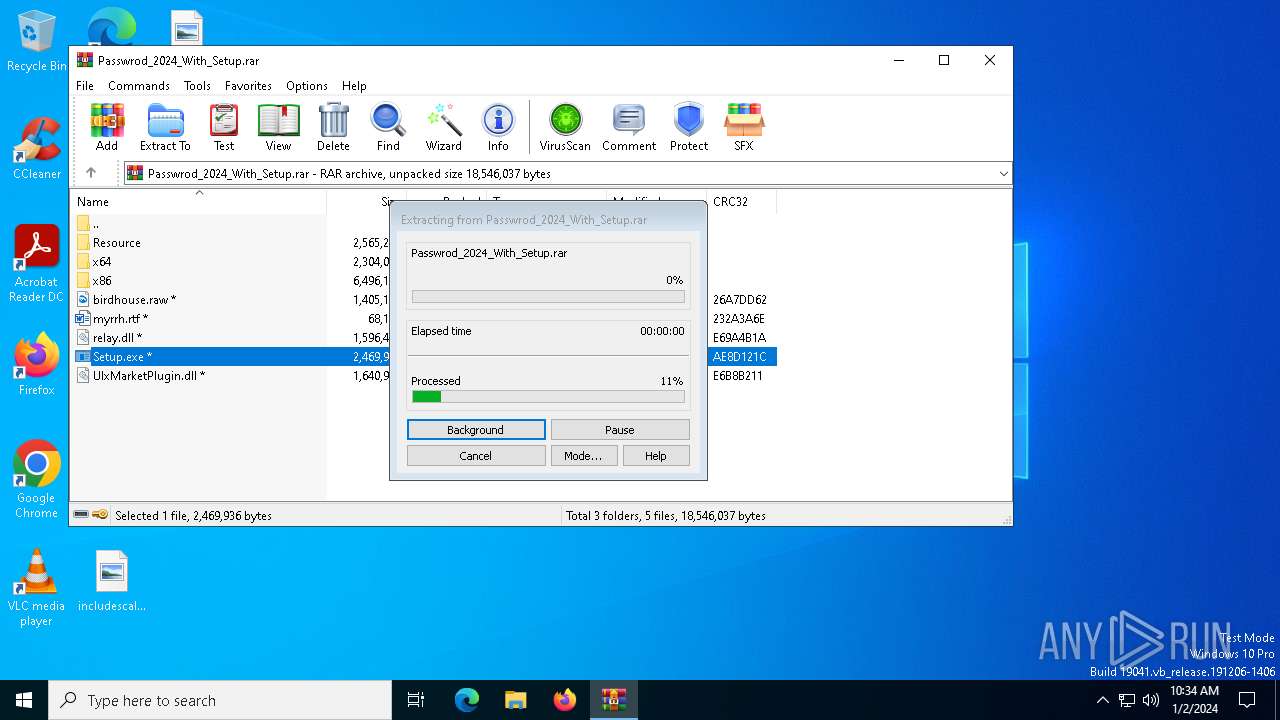
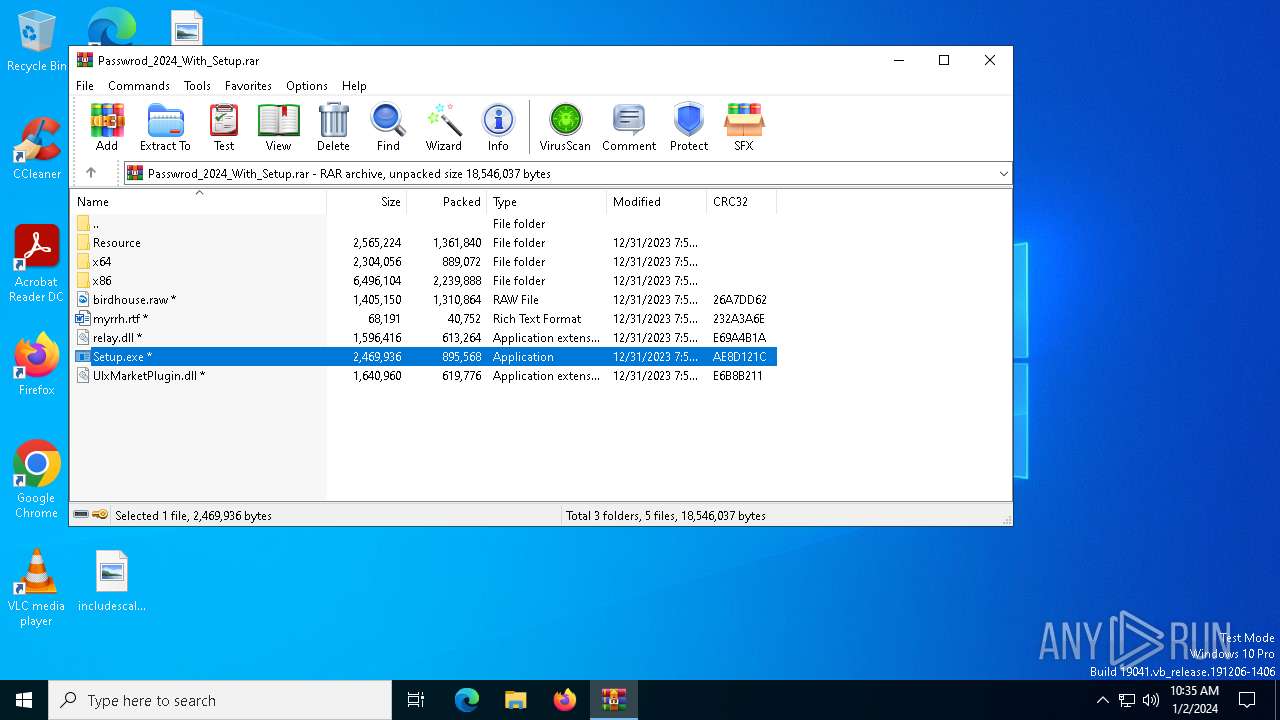
- Setup.exe (PID: 6636)
Reads the date of Windows installation
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- XRJNZC.exe (PID: 6896)
- D3FMOCB6MU7YTLJTQ8.exe (PID: 3024)
- Utsysc.exe (PID: 3876)
Executing commands from a ".bat" file
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- T7VEM6FUG5I90S4270BRJWBLJHZ.exe (PID: 1876)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5420)
- cmd.exe (PID: 6492)
Searches for installed software
- RarExt32.exe (PID: 5128)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 3476)
Loads DLL from Mozilla Firefox
- rundll32.exe (PID: 4104)
Uses NETSH.EXE to obtain data on the network
- rundll32.exe (PID: 4104)
Starts POWERSHELL.EXE for commands execution
- rundll32.exe (PID: 4104)
INFO
The process uses the downloaded file
- msedge.exe (PID: 6468)
- WinRAR.exe (PID: 2580)
- msedge.exe (PID: 6128)
Application launched itself
- msedge.exe (PID: 7064)
- msedge.exe (PID: 6128)
Reads the computer name
- identity_helper.exe (PID: 7044)
- identity_helper.exe (PID: 6792)
- Setup.exe (PID: 6636)
- RarExt32.exe (PID: 5128)
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- XRJNZC.exe (PID: 6896)
- D3FMOCB6MU7YTLJTQ8.exe (PID: 3024)
- Utsysc.exe (PID: 3876)
- T7VEM6FUG5I90S4270BRJWBLJHZ.exe (PID: 1876)
- OneDrive.exe (PID: 4476)
- vbc.exe (PID: 3060)
- OneDrive.exe (PID: 6744)
Checks supported languages
- identity_helper.exe (PID: 7044)
- identity_helper.exe (PID: 6792)
- Setup.exe (PID: 6636)
- RarExt32.exe (PID: 5128)
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- D3FMOCB6MU7YTLJTQ8.exe (PID: 3024)
- XRJNZC.exe (PID: 6896)
- Utsysc.exe (PID: 3876)
- T7VEM6FUG5I90S4270BRJWBLJHZ.exe (PID: 1876)
- OneDrive.exe (PID: 4476)
- vbc.exe (PID: 3060)
- XRJNZC.exe (PID: 6236)
- Utsysc.exe (PID: 6740)
- OneDrive.exe (PID: 6744)
- Utsysc.exe (PID: 1964)
- XRJNZC.exe (PID: 6372)
- Utsysc.exe (PID: 240)
- XRJNZC.exe (PID: 2704)
- XRJNZC.exe (PID: 5448)
- Utsysc.exe (PID: 6340)
- Utsysc.exe (PID: 6948)
- XRJNZC.exe (PID: 5976)
Creates files in the program directory
- Setup.exe (PID: 6636)
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- T7VEM6FUG5I90S4270BRJWBLJHZ.exe (PID: 1876)
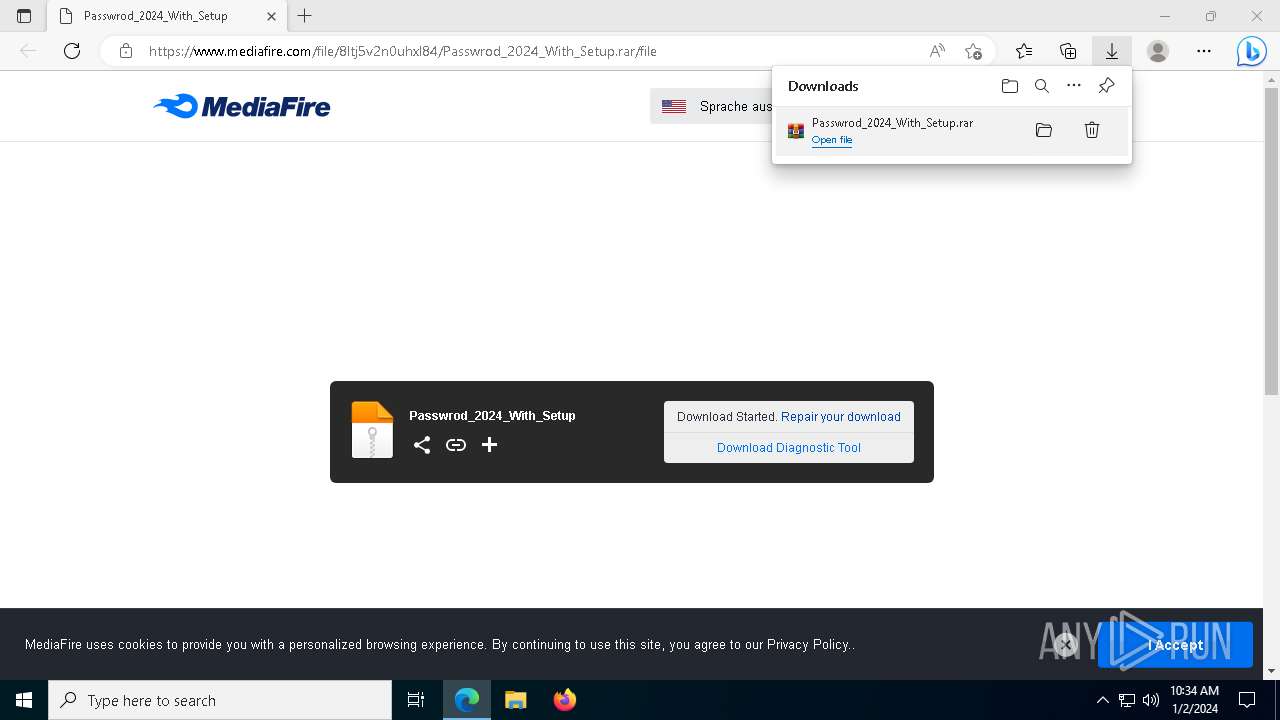
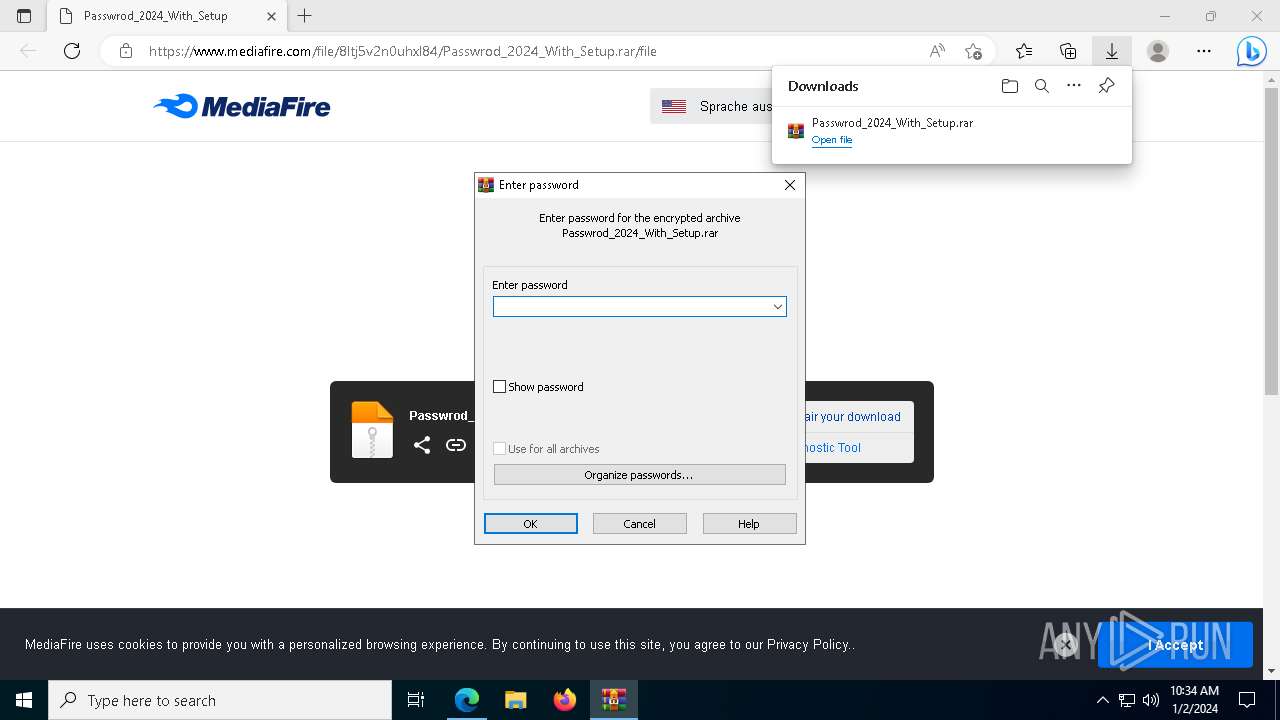
Drops the executable file immediately after the start
- msedge.exe (PID: 896)
- WinRAR.exe (PID: 2580)
- Setup.exe (PID: 6636)
- RarExt32.exe (PID: 5128)
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- D3FMOCB6MU7YTLJTQ8.exe (PID: 3024)
- T7VEM6FUG5I90S4270BRJWBLJHZ.exe (PID: 1876)
- Utsysc.exe (PID: 3876)
- cmd.exe (PID: 6712)
Creates files or folders in the user directory
- Setup.exe (PID: 6636)
- T7VEM6FUG5I90S4270BRJWBLJHZ.exe (PID: 1876)
- OneDrive.exe (PID: 4476)
- Utsysc.exe (PID: 3876)
Reads the software policy settings
- RarExt32.exe (PID: 5128)
Reads the machine GUID from the registry
- RarExt32.exe (PID: 5128)
- OneDrive.exe (PID: 4476)
- OneDrive.exe (PID: 6744)
Create files in a temporary directory
- RarExt32.exe (PID: 5128)
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- D3FMOCB6MU7YTLJTQ8.exe (PID: 3024)
- Utsysc.exe (PID: 3876)
- T7VEM6FUG5I90S4270BRJWBLJHZ.exe (PID: 1876)
- Setup.exe (PID: 6636)
Process requests binary or script from the Internet
- RarExt32.exe (PID: 5128)
- Utsysc.exe (PID: 3876)
Connects to the server without a host name
- RarExt32.exe (PID: 5128)
- Utsysc.exe (PID: 3876)
- OneDrive.exe (PID: 4476)
- rundll32.exe (PID: 3680)
- rundll32.exe (PID: 4104)
Process checks computer location settings
- XRJNZC.exe (PID: 6896)
- ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe (PID: 1532)
- Utsysc.exe (PID: 3876)
- D3FMOCB6MU7YTLJTQ8.exe (PID: 3024)
- OneDrive.exe (PID: 4476)
- OneDrive.exe (PID: 6744)
Reads Environment values
- D3FMOCB6MU7YTLJTQ8.exe (PID: 3024)
- Utsysc.exe (PID: 3876)
- OneDrive.exe (PID: 4476)
- Utsysc.exe (PID: 240)
- Utsysc.exe (PID: 6740)
- Utsysc.exe (PID: 1964)
- Utsysc.exe (PID: 6340)
- Utsysc.exe (PID: 6948)
Starts itself from another location
- D3FMOCB6MU7YTLJTQ8.exe (PID: 3024)
Checks proxy server information
- Utsysc.exe (PID: 3876)
- OneDrive.exe (PID: 4476)
- rundll32.exe (PID: 4104)
- rundll32.exe (PID: 3680)
Connects to the CnC server
- vbc.exe (PID: 3060)
Connects to unusual port
- vbc.exe (PID: 3060)
MINER has been detected (SURICATA)
- vbc.exe (PID: 3060)
Unusual connection from system programs
- vbc.exe (PID: 3060)
- rundll32.exe (PID: 3680)
- rundll32.exe (PID: 4104)
AMADEY has been detected (SURICATA)
- Utsysc.exe (PID: 3876)
The executable file from the user directory is run by the CMD process
- RarExt32.exe (PID: 5128)
The process executes via Task Scheduler
- XRJNZC.exe (PID: 6236)
- Utsysc.exe (PID: 6740)
- XRJNZC.exe (PID: 2704)
- OneDrive.exe (PID: 6744)
- Utsysc.exe (PID: 1964)
- XRJNZC.exe (PID: 6372)
- Utsysc.exe (PID: 240)
- Utsysc.exe (PID: 6340)
- XRJNZC.exe (PID: 5976)
- Utsysc.exe (PID: 6948)
- XRJNZC.exe (PID: 5448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(6712) cmd.exe
C2 (7)insertrichdedicatewa.pw
opposesicknessopw.pw
carstirgapcheatdeposwte.pw
playerweighmailydailew.pw
politefrightenpowoa.pw
recessionconceptjetwe.pw
blastechohackopeower.pw
(PID) Process(5128) RarExt32.exe
C2 (7)insertrichdedicatewa.pw
opposesicknessopw.pw
carstirgapcheatdeposwte.pw
playerweighmailydailew.pw
politefrightenpowoa.pw
recessionconceptjetwe.pw
blastechohackopeower.pw
Total processes
220
Monitored processes
86
Malicious processes
9
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | C:\Users\admin\AppData\Local\Temp\4fdb51ccdc\Utsysc.exe | C:\Users\admin\AppData\Local\Temp\4fdb51ccdc\Utsysc.exe | — | svchost.exe | |||||||||||
User: admin Company: tamirgal.com Integrity Level: MEDIUM Description: SharpSSH Exit code: 0 Version: 1.1.1.13 Modules
| |||||||||||||||
| 892 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --mojo-platform-channel-handle=6684 --field-trial-handle=2088,i,4575296219535514552,12276948766648894601,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=7004 --field-trial-handle=2088,i,4575296219535514552,12276948766648894601,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1408 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4804 --field-trial-handle=1880,i,3192454677792069554,3961176339853448987,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\AppData\Local\Temp\ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe" | C:\Users\admin\AppData\Local\Temp\ZV8FSNXYIZ9XSPCCXI5GKD3Y6XUF6Q.exe | — | RarExt32.exe | |||||||||||
User: admin Company: TomTom Integrity Level: MEDIUM Description: TomTom MyDrive Connect Exit code: 0 Version: 4.3.6.5021 Modules
| |||||||||||||||
| 1540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=7064 --field-trial-handle=2088,i,4575296219535514552,12276948766648894601,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4956 --field-trial-handle=1880,i,3192454677792069554,3961176339853448987,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\T7VEM6FUG5I90S4270BRJWBLJHZ.exe" | C:\Users\admin\AppData\Local\Temp\T7VEM6FUG5I90S4270BRJWBLJHZ.exe | — | RarExt32.exe | |||||||||||
User: admin Company: MobiSystems Integrity Level: MEDIUM Description: OfficeSuite Exit code: 0 Version: 8.0.53263 Modules
| |||||||||||||||
| 1912 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3436 --field-trial-handle=2088,i,4575296219535514552,12276948766648894601,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 1920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=4556 --field-trial-handle=2088,i,4575296219535514552,12276948766648894601,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
Total events
33 042
Read events
32 879
Write events
161
Delete events
2
Modification events
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
| (PID) Process: | (6128) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 74A98451B7602F00 | |||
Executable files
33
Suspicious files
218
Text files
103
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFf24a5.TMP | — | |
MD5:— | SHA256:— | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFf24b5.TMP | — | |
MD5:— | SHA256:— | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFf24e4.TMP | — | |
MD5:— | SHA256:— | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgeCoupons\coupons_data.db\LOG.old~RFf24b5.TMP | text | |
MD5:6ACBB48AEE4E1CADD116DA54B6A2B926 | SHA256:0D80A67E0F54D8098CFDE1B38C450EEE9E0A8AAEDA8B02D450F284BB26E74A0B | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RFf24b5.TMP | text | |
MD5:5DB127C66F688E2B285A0816EC4BDE1C | SHA256:1A490965A2E4688809FF31A5DB1971688F92700DEFA536BEF28D91512B9AA966 | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RFf2486.TMP | binary | |
MD5:DF75AE8CBAE008C19531D12A895A32A9 | SHA256:3D93E0AE1670DC35077C55FEACC46B133A6015AFC74F6AEA072B7DD9D7039531 | |||
| 6128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgeCoupons\coupons_data.db\LOG.old | text | |
MD5:63D47248EB1C3F5B97CAAE6599A6FCD0 | SHA256:4124BD344E193D3DDBE94EF996C5AFBEA6C00C939F405B3CCBEE9058BA5AE257 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
165
TCP/UDP connections
130
DNS requests
100
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3340 | msedge.exe | GET | 200 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/Edge/111.0.1661.62?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfull=0&scpguard=0&scpfre=0&scpver=0&osarch=x86_64&osver=10.0.19044&wu=1&devicefamily=desktop&uma=0&sessionid=12&mngd=0&installdate=1661339457&edu=0&bphint=2&soobedate=1504771245 | unknown | binary | 968 b | unknown |
3340 | msedge.exe | POST | 200 | 20.103.180.120:443 | https://sploit-edge.smartscreen.microsoft.com/api/browser/edge/ssrs/3?MSURS-Client-Key=gWk17R3rsHpq2NOfGTB9CQ==&MSURS-MAC=rmDFlGJXkNY= | unknown | text | 395 b | unknown |
— | — | GET | 200 | 104.16.113.74:443 | https://www.mediafire.com/file/8ltj5v2n0uhxl84/Passwrod_2024_With_Setup.rar/file | unknown | html | 91.9 Kb | unknown |
— | — | POST | 200 | 20.103.180.120:443 | https://nav-edge.smartscreen.microsoft.com/api/browser/edge/navigate/3/sync | unknown | binary | 1.20 Kb | unknown |
— | — | GET | 200 | 172.217.18.104:443 | https://www.googletagmanager.com/gtag/js?id=UA-829541-1 | unknown | text | 173 Kb | unknown |
— | — | GET | 200 | 172.217.18.104:443 | https://www.googletagmanager.com/gtm.js?id=GTM-53LP4T | unknown | text | 259 Kb | unknown |
3340 | msedge.exe | GET | — | 104.16.56.101:443 | https://static.cloudflareinsights.com/beacon.min.js/v84a3a4012de94ce1a686ba8c167c359c1696973893317 | unknown | — | — | unknown |
3340 | msedge.exe | POST | 204 | 216.239.34.36:443 | https://region1.analytics.google.com/g/collect?v=2&tid=G-K68XP6D85D>m=45je3bt0v887485693z86304663&_p=1704191562325&_gaz=1&gcd=11l1l1l1l1&dma_cps=sypham&dma=1&cid=855511322.1704191602&ul=en-us&sr=1280x720&uaa=x86&uab=64&uafvl=Microsoft%2520Edge%3B111.0.1661.62%7CNot(A%253ABrand%3B8.0.0.0%7CChromium%3B111.0.5563.149&uamb=0&uam=&uap=Windows&uapv=10.0.0&uaw=0&_s=1&sid=1704191602&sct=1&seg=0&dl=https%3A%2F%2Fwww.mediafire.com%2Ffile%2F8ltj5v2n0uhxl84%2FPasswrod_2024_With_Setup.rar%2Ffile&dt=Passwrod_2024_With_Setup&en=page_view&_fv=1&_nsi=1&_ss=1&up.page_url=https%3A%2F%2Fwww.mediafire.com%2Ffile%2F8ltj5v2n0uhxl84%2FPasswrod_2024_With_Setup.rar%2Ffile&tfd=42647 | unknown | — | — | unknown |
— | — | GET | 200 | 104.16.113.74:443 | https://www.mediafire.com/images/icons/svg_dark/icons_sprite.svg | unknown | image | 36.1 Kb | unknown |
— | — | POST | 200 | 20.105.95.163:443 | https://data-edge.smartscreen.microsoft.com/api/browser/edge/data/bloomfilter/x/3 | unknown | binary | 57 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5612 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1676 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6128 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3340 | msedge.exe | 104.16.114.74:443 | www.mediafire.com | CLOUDFLARENET | — | unknown |
3340 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3340 | msedge.exe | 20.103.180.120:443 | sploit-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3340 | msedge.exe | 20.31.251.109:443 | nav-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3720 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3340 | msedge.exe | 216.58.212.168:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
3340 | msedge.exe | 2.19.96.90:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
config.edge.skype.com |
| whitelisted |
sploit-edge.smartscreen.microsoft.com |
| whitelisted |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
data-edge.smartscreen.microsoft.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
static.mediafire.com |
| shared |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
translate.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3340 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
3340 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
3340 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
3340 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
3340 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
3340 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2136 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
5128 | RarExt32.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5128 | RarExt32.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
5128 | RarExt32.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1 ETPRO signatures available at the full report