| URL: | http://r20.rs6.net/tn.jsp?f=001g4HbmzerCeQSmSbfKyIs0w4FH5pvzTw3SzAUwnOy-Juz8cebXECVIHg9or-0jqkJV0WxnNshceZfbcgtNEYmQlpsc9L9efRjpaZEbYF0EYv5XtDH3YP3tOnsVmJoQQ2Dlld3wPDOYaTLKBMBVXZJHGEjAN0XgIJ2UmOuG_WGQuzRa-FxgFPmWANTv7rnMdwUQoamQvmnSBxHrlokqW6kpUBIeLcnv42ZtdORqMTzZhQ=&c=H2wz9bsRla-h55aHwPe5vB-B0yjwFSlAkZdsmP_AXj6T-OtZ8uEFyw==&ch=PxUHI4dUTwSfdJKhg4HRC_sU0fD2sObARf3uItsukJwp38SyiTMV-g== |
| Full analysis: | https://app.any.run/tasks/8802357e-a7ca-44e9-836e-52a6c550a42e |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | January 17, 2020, 16:00:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F29CE92BC8738230EF3AE98D5F548C49 |
| SHA1: | 714FCC838B605E84C1EA6D3AC4B735586C097235 |
| SHA256: | 05ED8C49A5AD404E41108E14C2B201EA1F711AD9F3D10B7660766DFDE2B04F8F |
| SSDEEP: | 12:ZFBqvdW4oJXnIVoVWgHQZgTq/ryHEFPG8N:7BqvTodjVWfJDyHI |
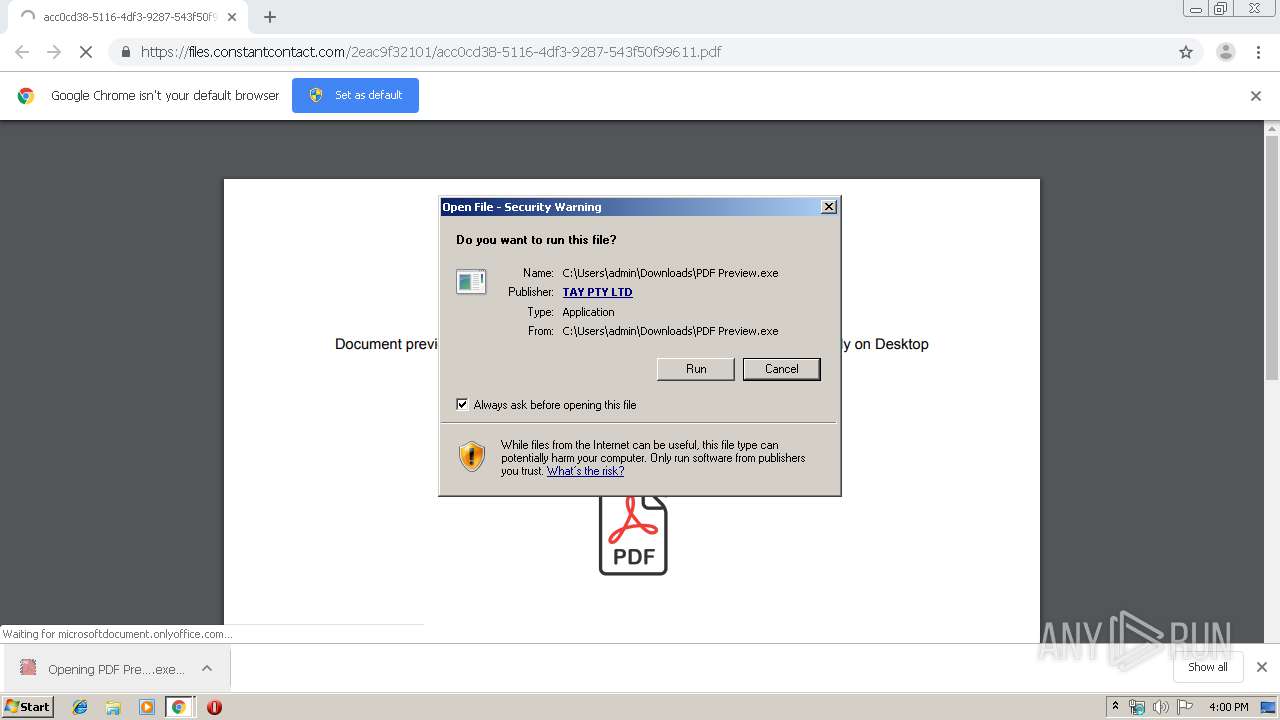
MALICIOUS
Changes settings of System certificates
- PDF Preview.exe (PID: 2828)
- PDF Preview (1).exe (PID: 3672)
Application was dropped or rewritten from another process
- PDF Preview.exe (PID: 2828)
- _æd7DFF.exe (PID: 496)
- _æd7DFF.exe (PID: 2644)
- PDF Preview (1).exe (PID: 3672)
- _ædA33C.exe (PID: 3088)
- _ædA53E.exe (PID: 3516)
- _ædA53E.exe (PID: 2884)
Known privilege escalation attack
- DllHost.exe (PID: 1972)
- DllHost.exe (PID: 2188)
TRICKBOT was detected
- _æd7DFF.exe (PID: 2644)
- _ædA33C.exe (PID: 3088)
- _ædA53E.exe (PID: 2884)
Loads the Task Scheduler COM API
- _æd7DFF.exe (PID: 2644)
- _ædA53E.exe (PID: 2884)
- _ædA33C.exe (PID: 3088)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2504)
Executable content was dropped or overwritten
- chrome.exe (PID: 2504)
- PDF Preview.exe (PID: 2828)
- _æd7DFF.exe (PID: 2644)
- chrome.exe (PID: 1784)
- PDF Preview (1).exe (PID: 3672)
- _ædA53E.exe (PID: 2884)
Adds / modifies Windows certificates
- PDF Preview.exe (PID: 2828)
- PDF Preview (1).exe (PID: 3672)
Executed via COM
- DllHost.exe (PID: 1972)
- DllHost.exe (PID: 2188)
Creates files in the user directory
- _æd7DFF.exe (PID: 2644)
- _ædA53E.exe (PID: 2884)
- _ædA33C.exe (PID: 3088)
Executed via Task Scheduler
- _ædA33C.exe (PID: 3088)
INFO
Reads the hosts file
- chrome.exe (PID: 2504)
- chrome.exe (PID: 1784)
Application launched itself
- chrome.exe (PID: 2504)
Reads Internet Cache Settings
- chrome.exe (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
47
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16223505457511214608 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12354490901473591486 --mojo-platform-channel-handle=3848 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17922817031719414423 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 496 | C:\Users\admin\AppData\Local\Temp\_æd7DFF.exe | C:\Users\admin\AppData\Local\Temp\_æd7DFF.exe | — | PDF Preview.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ZoomPerspective MFC Application Exit code: 0 Version: 1, 0, 2, 773 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8992684838680355132 --mojo-platform-channel-handle=4180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9126797025090488998 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16296555786032994763 --mojo-platform-channel-handle=3684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3404024684740692671 --mojo-platform-channel-handle=4880 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5155798917266614928 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11539752996789528072 --mojo-platform-channel-handle=5144 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 874
Read events
1 691
Write events
176
Delete events
7
Modification events
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2504-13223750421158750 |
Value: 259 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
12
Suspicious files
23
Text files
284
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a9a8.TMP | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b318ef6d-6d26-4d31-8c98-cd6d92bb43c6.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a93b.TMP | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a969.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
43
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1784 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
1784 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
1784 | chrome.exe | GET | 200 | 172.217.132.71:80 | http://r2---sn-5hne6nsr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=84.17.36.75&mm=28&mn=sn-5hne6nsr&ms=nvh&mt=1579276755&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
1784 | chrome.exe | GET | 200 | 74.125.100.183:80 | http://r1---sn-5hnedn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=84.17.36.75&mm=28&mn=sn-5hnedn7z&ms=nvh&mt=1579276755&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1784 | chrome.exe | 74.125.100.183:80 | r1---sn-5hnedn7z.gvt1.com | Google Inc. | US | whitelisted |
1784 | chrome.exe | 172.217.21.238:443 | docs.google.com | Google Inc. | US | whitelisted |
1784 | chrome.exe | 172.217.132.71:80 | r2---sn-5hne6nsr.gvt1.com | Google Inc. | US | whitelisted |
1784 | chrome.exe | 54.191.34.90:443 | microsoftdocument.onlyoffice.com | Amazon.com, Inc. | US | unknown |
1784 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2828 | PDF Preview.exe | 216.239.32.21:443 | myexternalip.com | Google Inc. | US | whitelisted |
1784 | chrome.exe | 216.58.207.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1784 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2828 | PDF Preview.exe | 192.185.129.7:80 | mappingskills.com | CyrusOne LLC | US | suspicious |
3672 | PDF Preview (1).exe | 216.239.32.21:443 | myexternalip.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
r20.rs6.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
files.constantcontact.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-5hnedn7z.gvt1.com |
| whitelisted |
r2---sn-5hne6nsr.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2828 | PDF Preview.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] Encrypted PE EXE or DLL Windows file download Key = 6e |