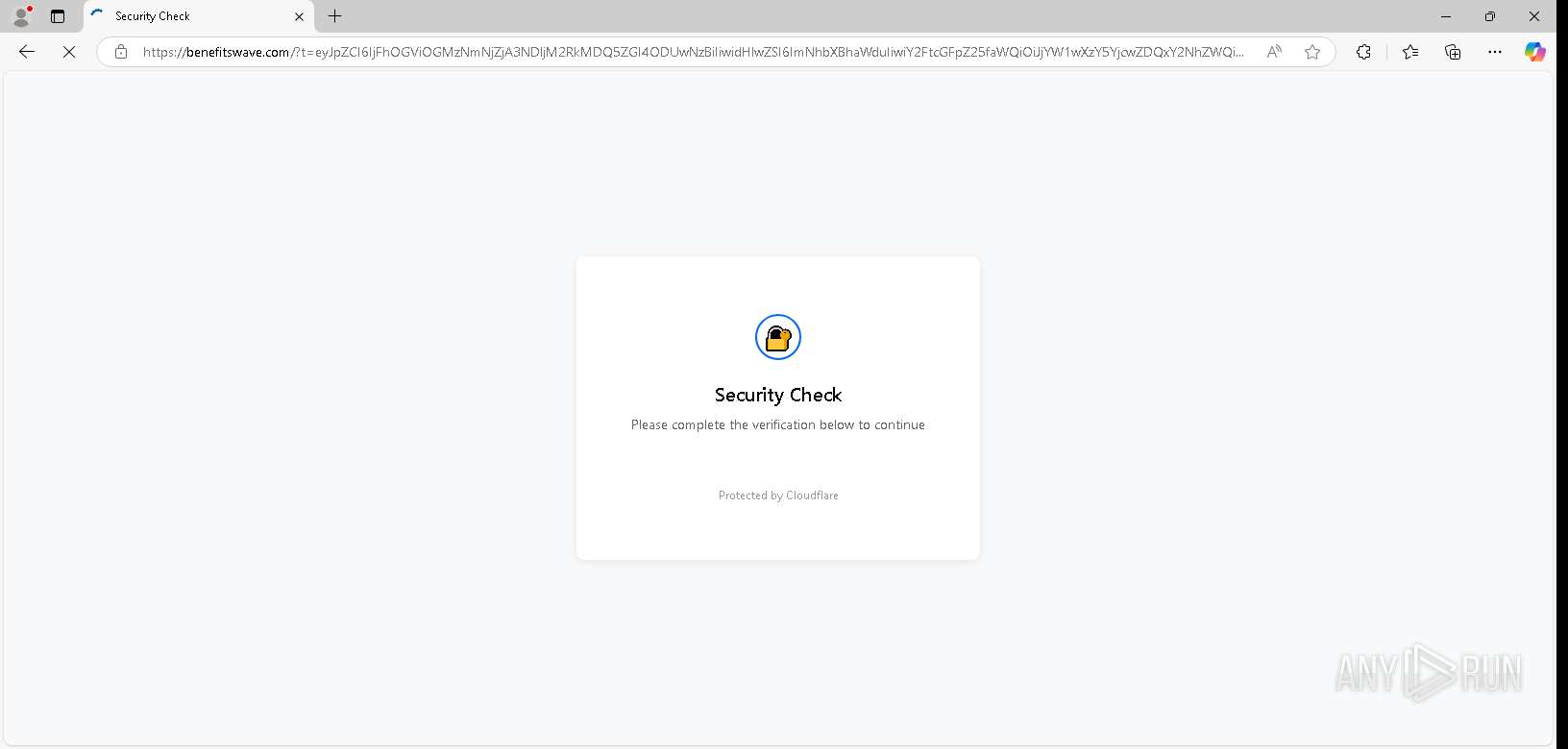
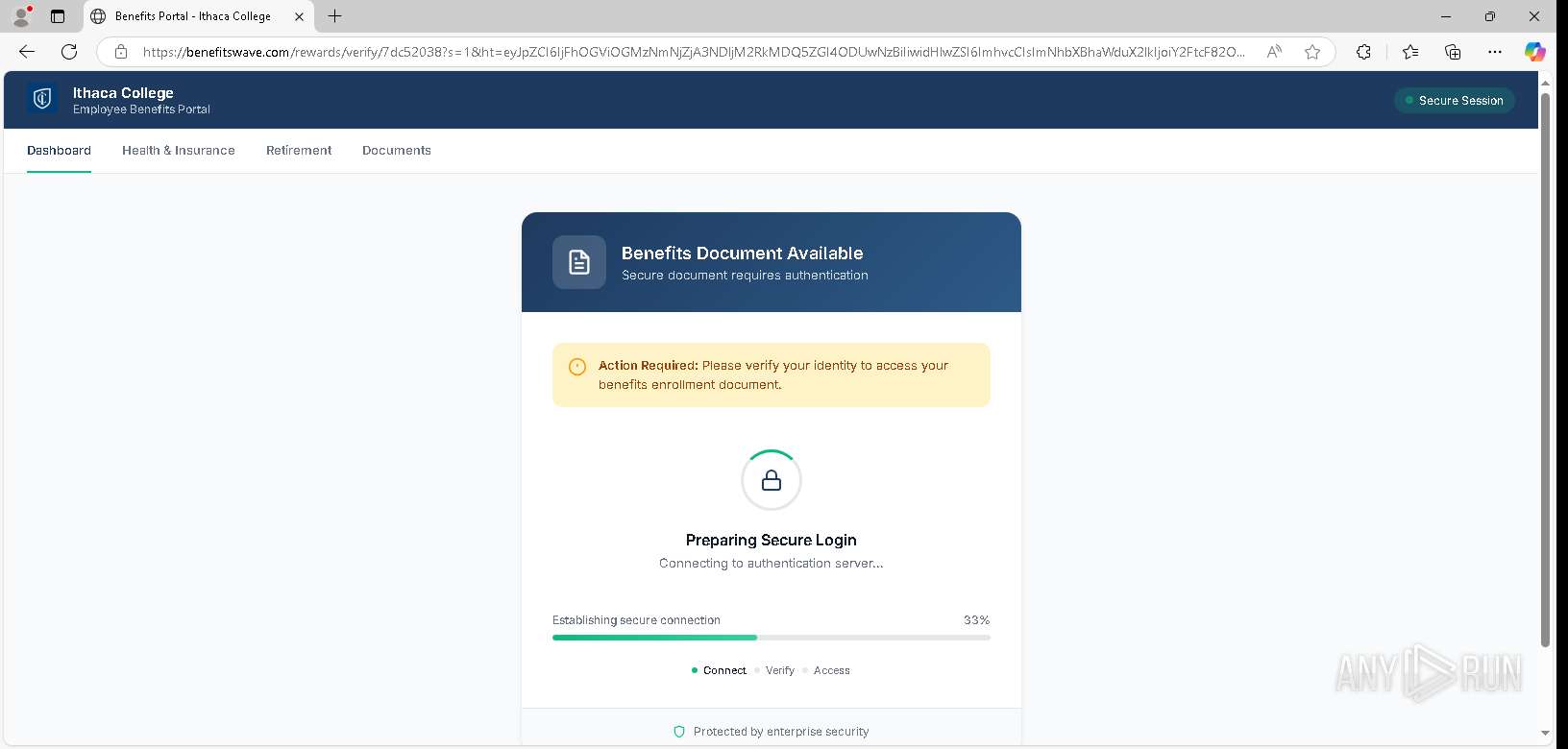
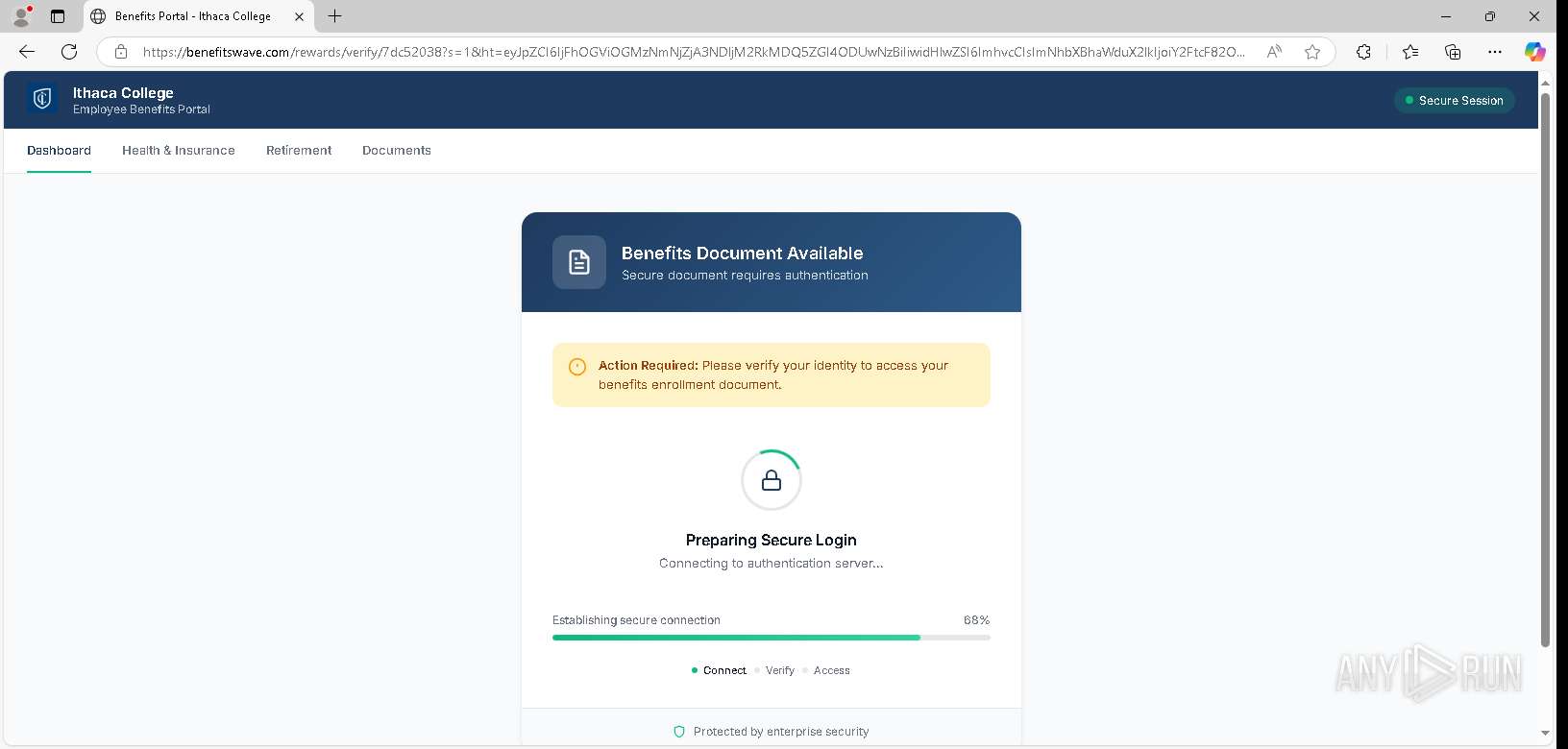
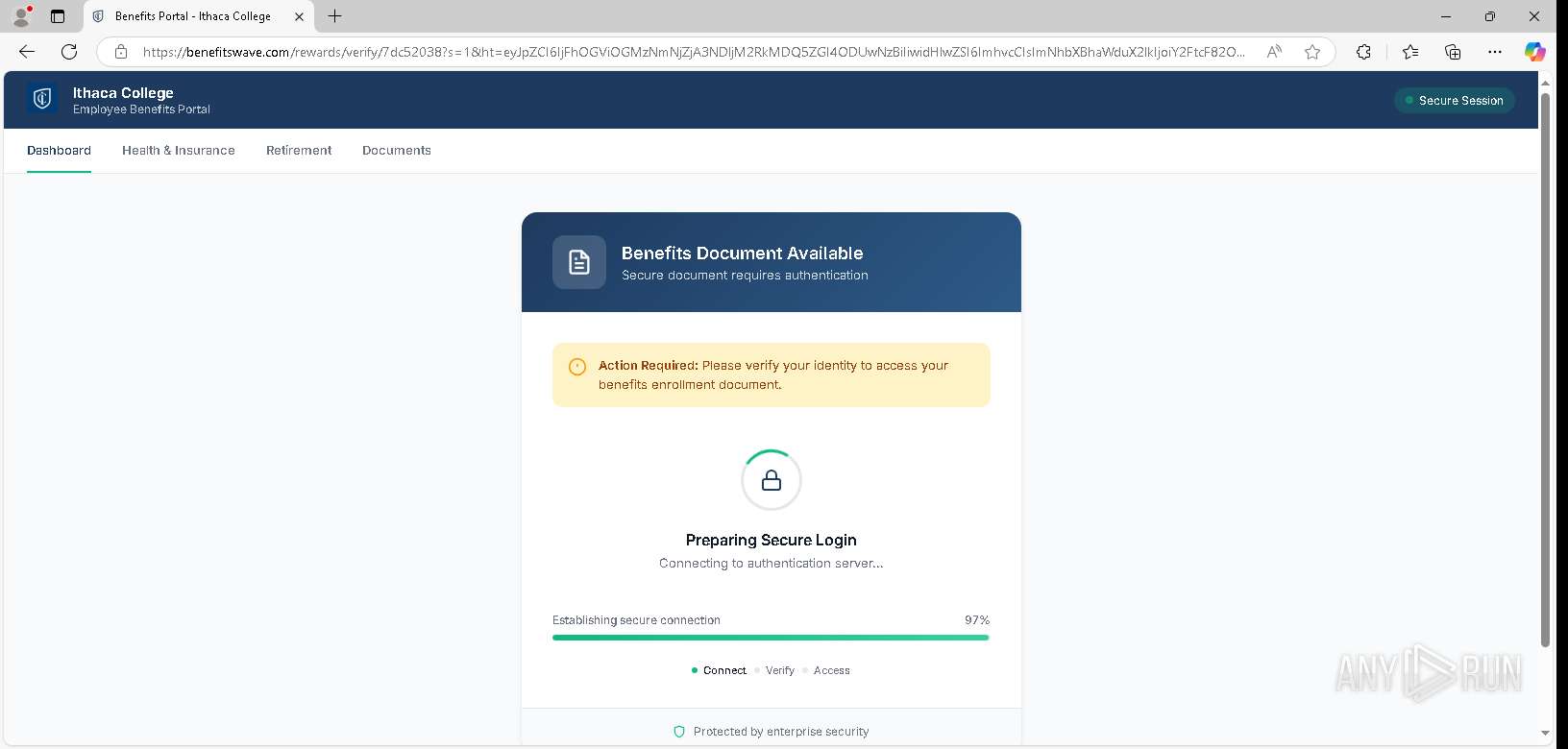
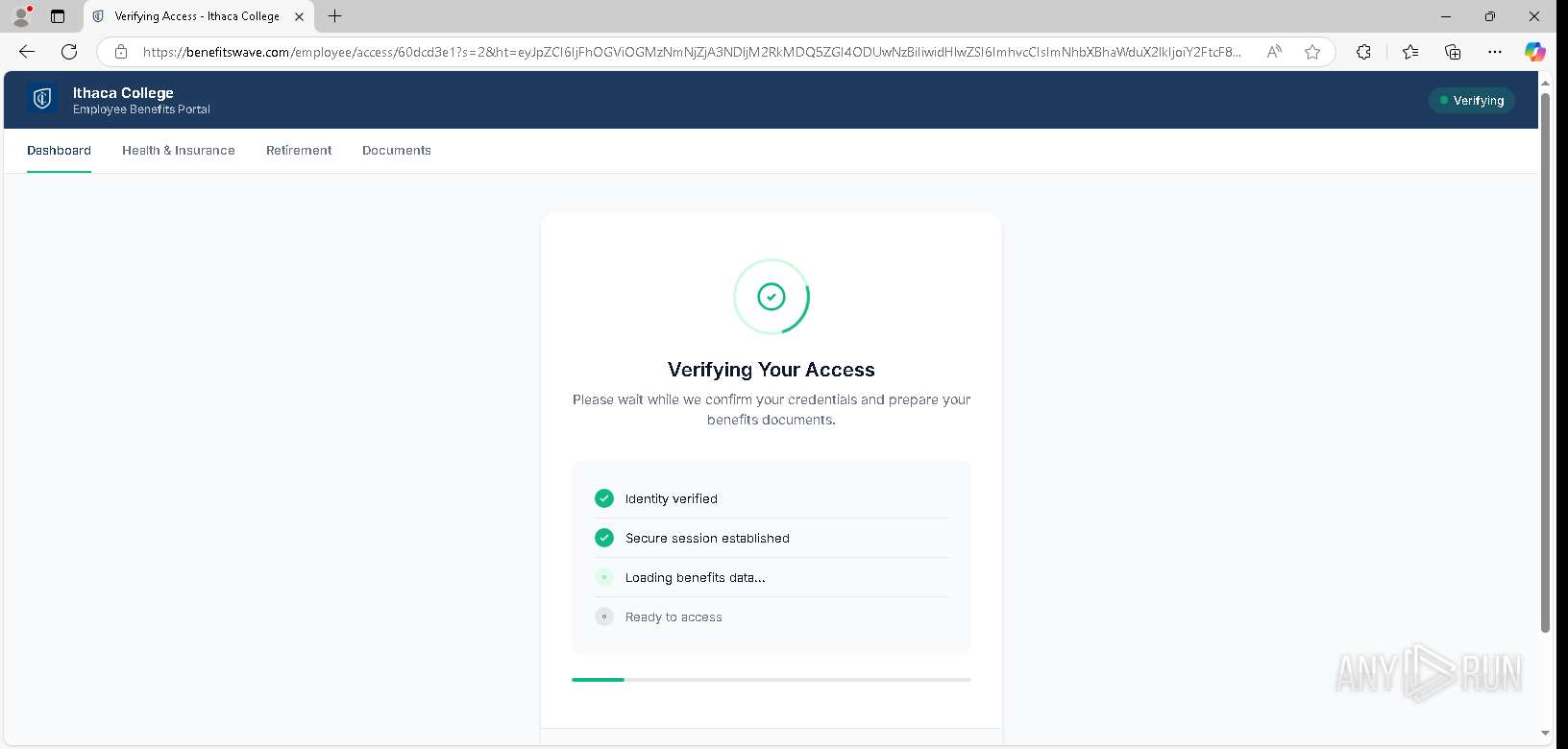
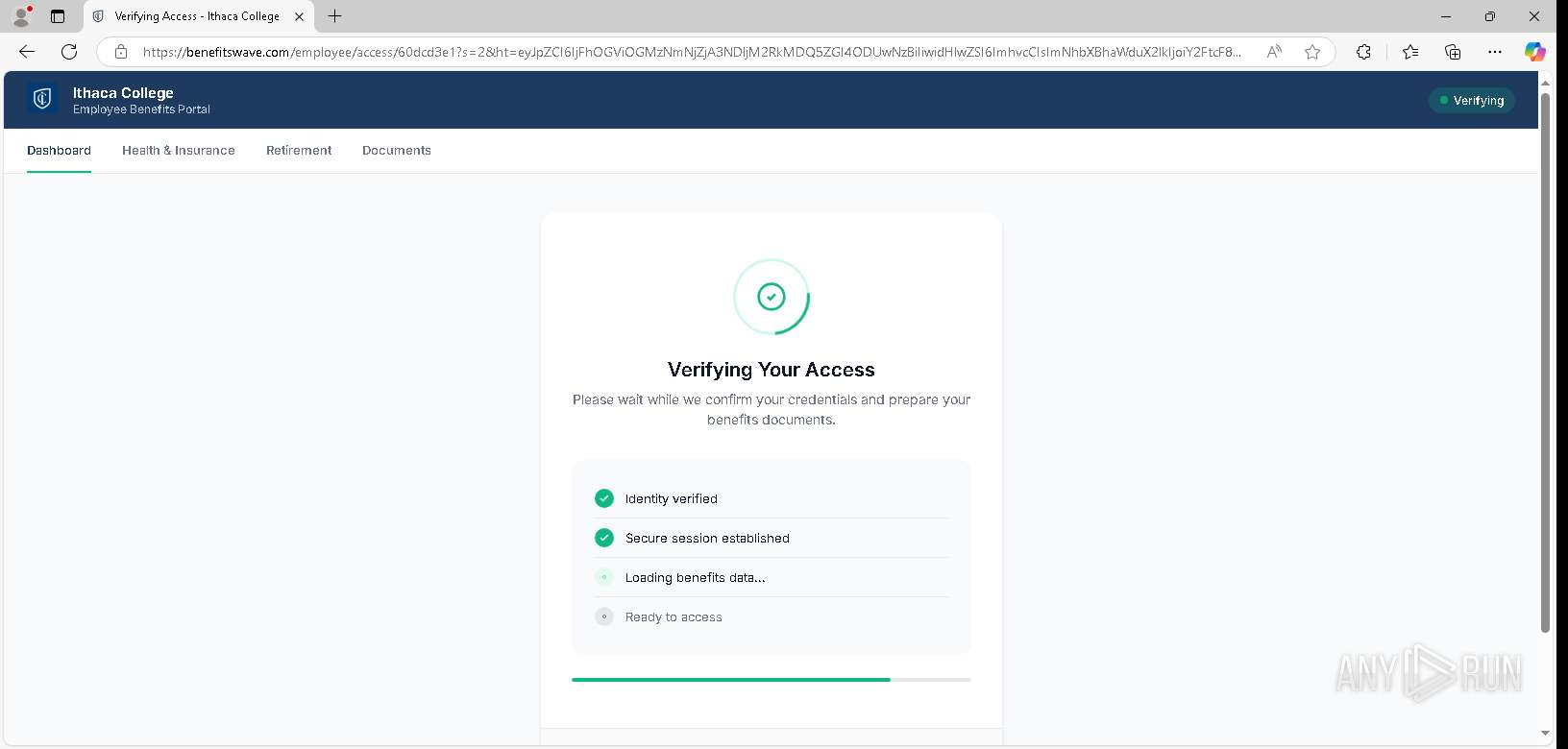
| URL: | https://tracking.kvo1.io/uHfVbF |
| Full analysis: | https://app.any.run/tasks/0c1b1aa8-d20e-465a-a274-9e68b208bdde |
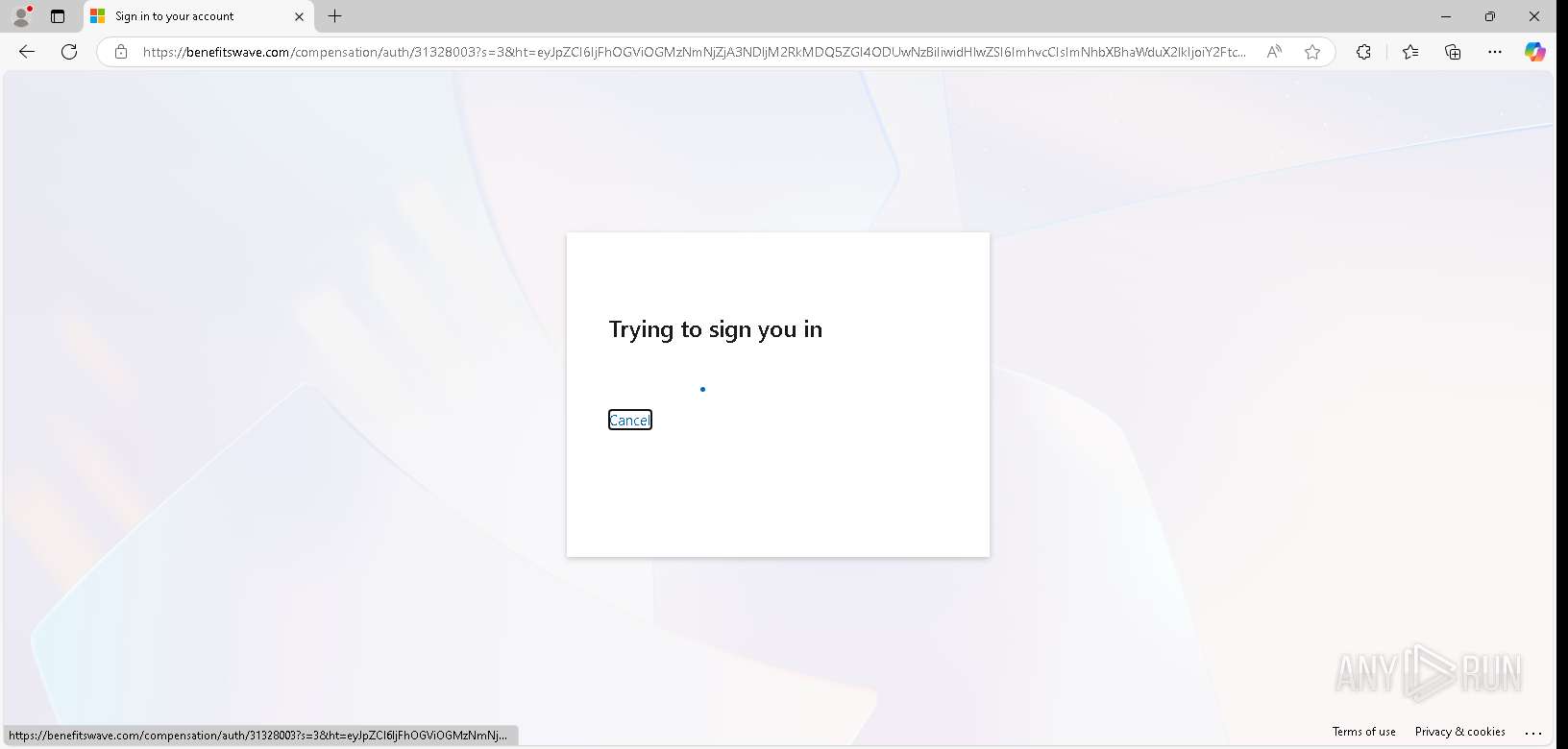
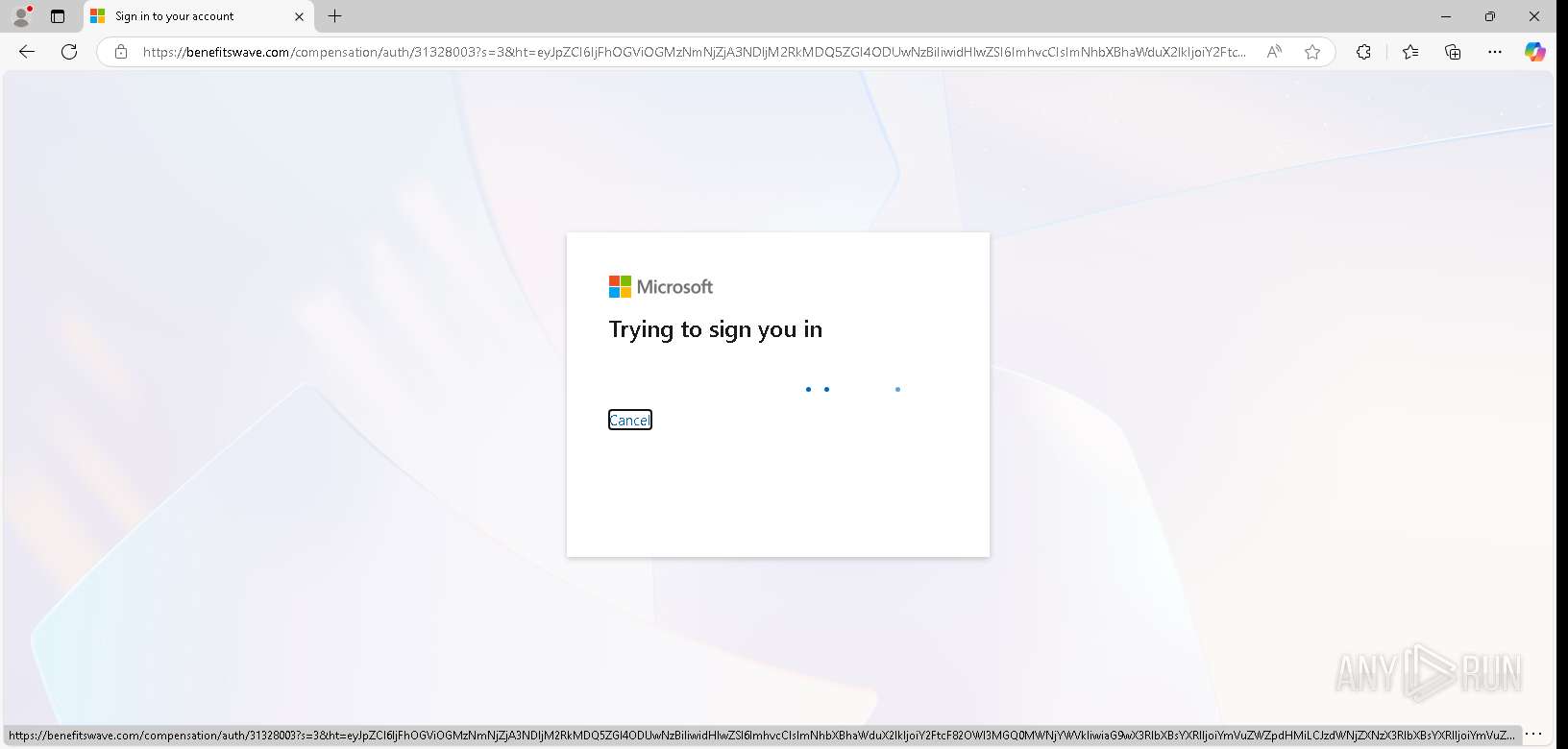
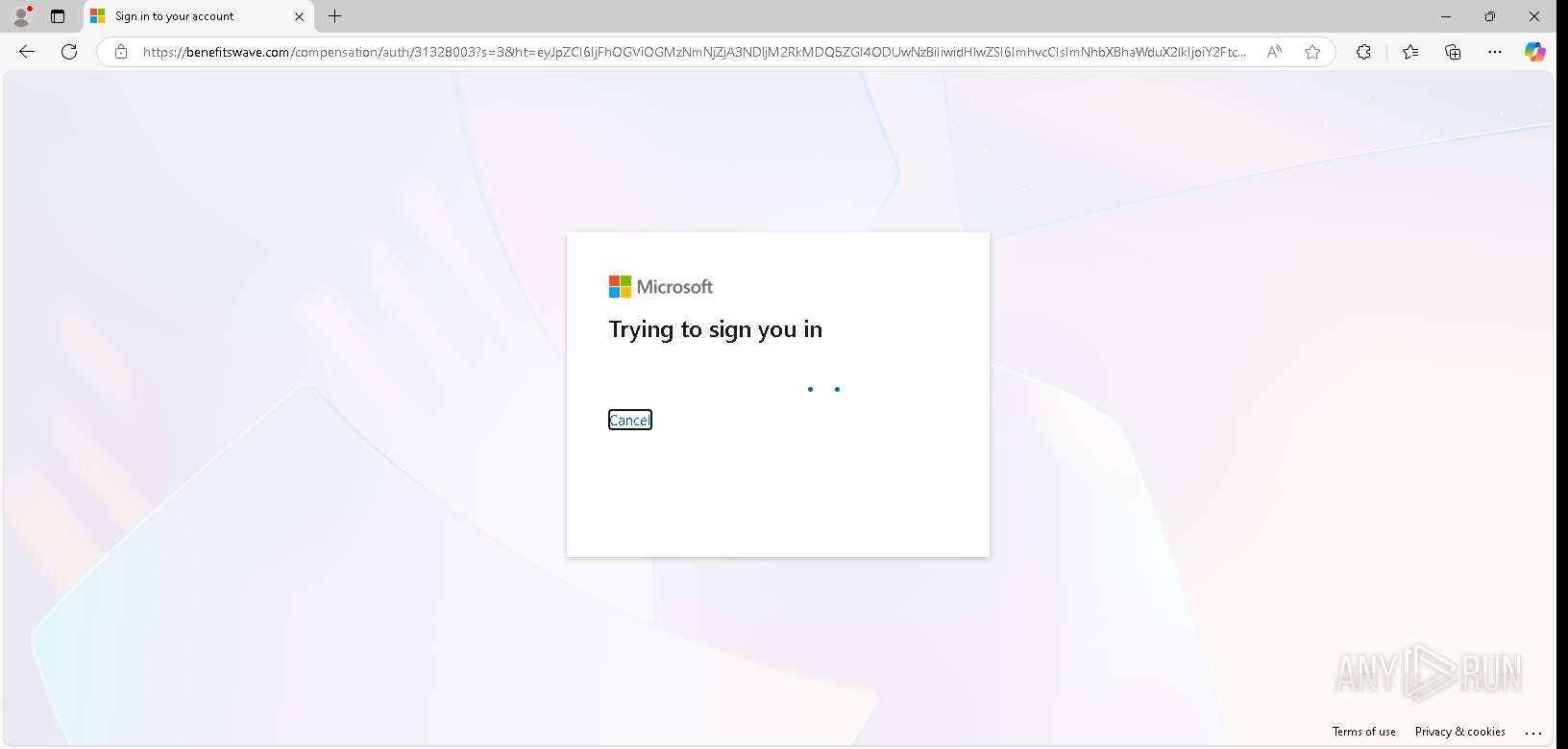
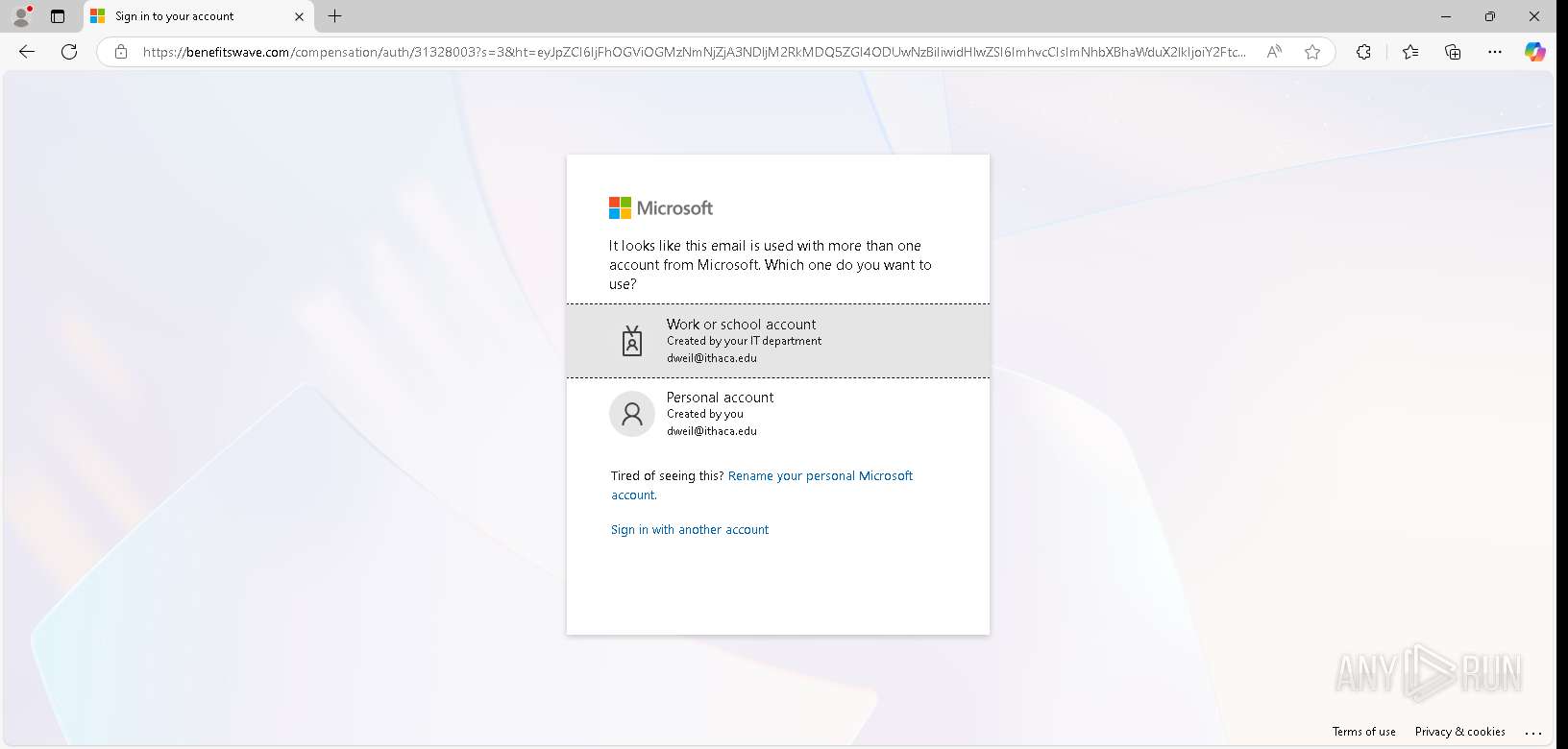
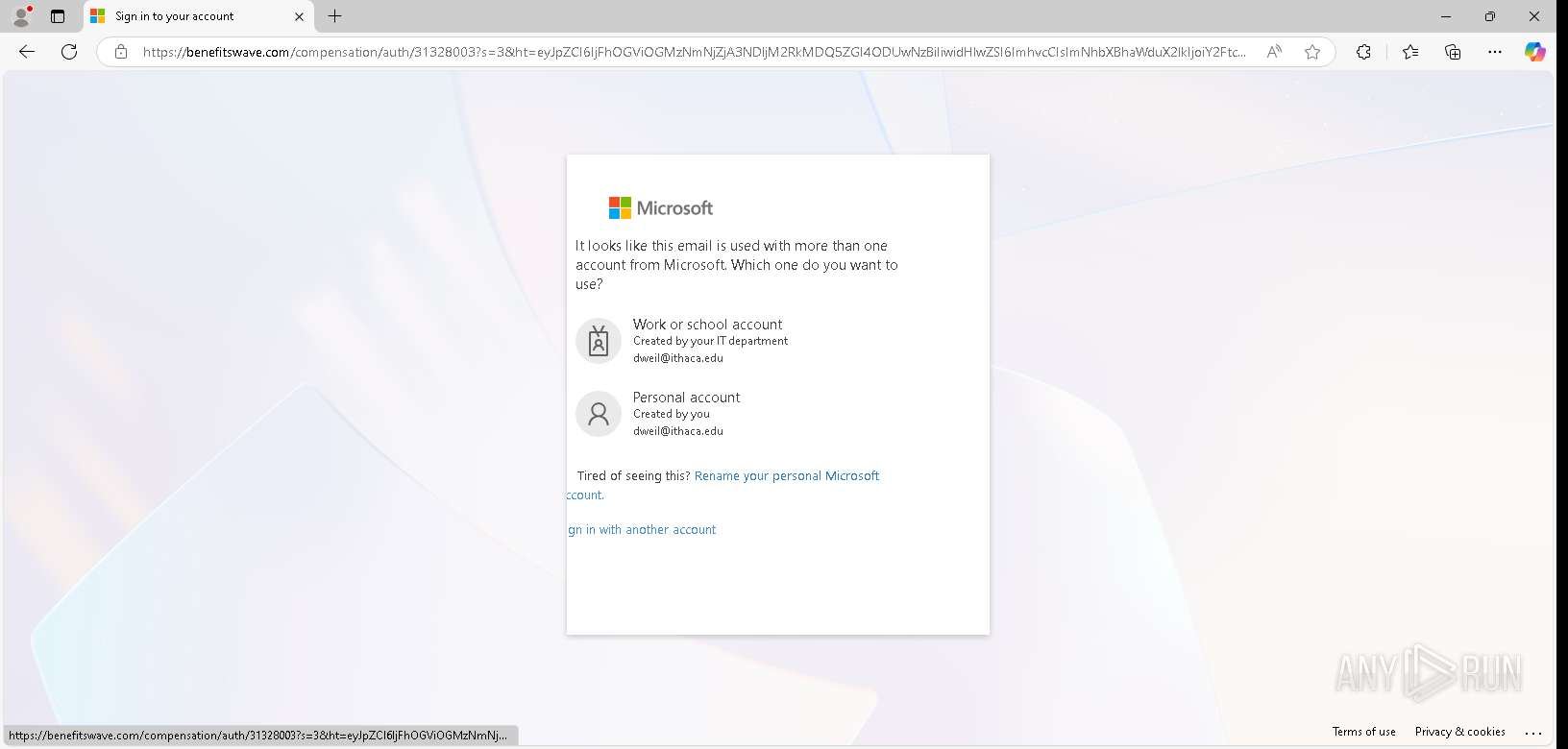
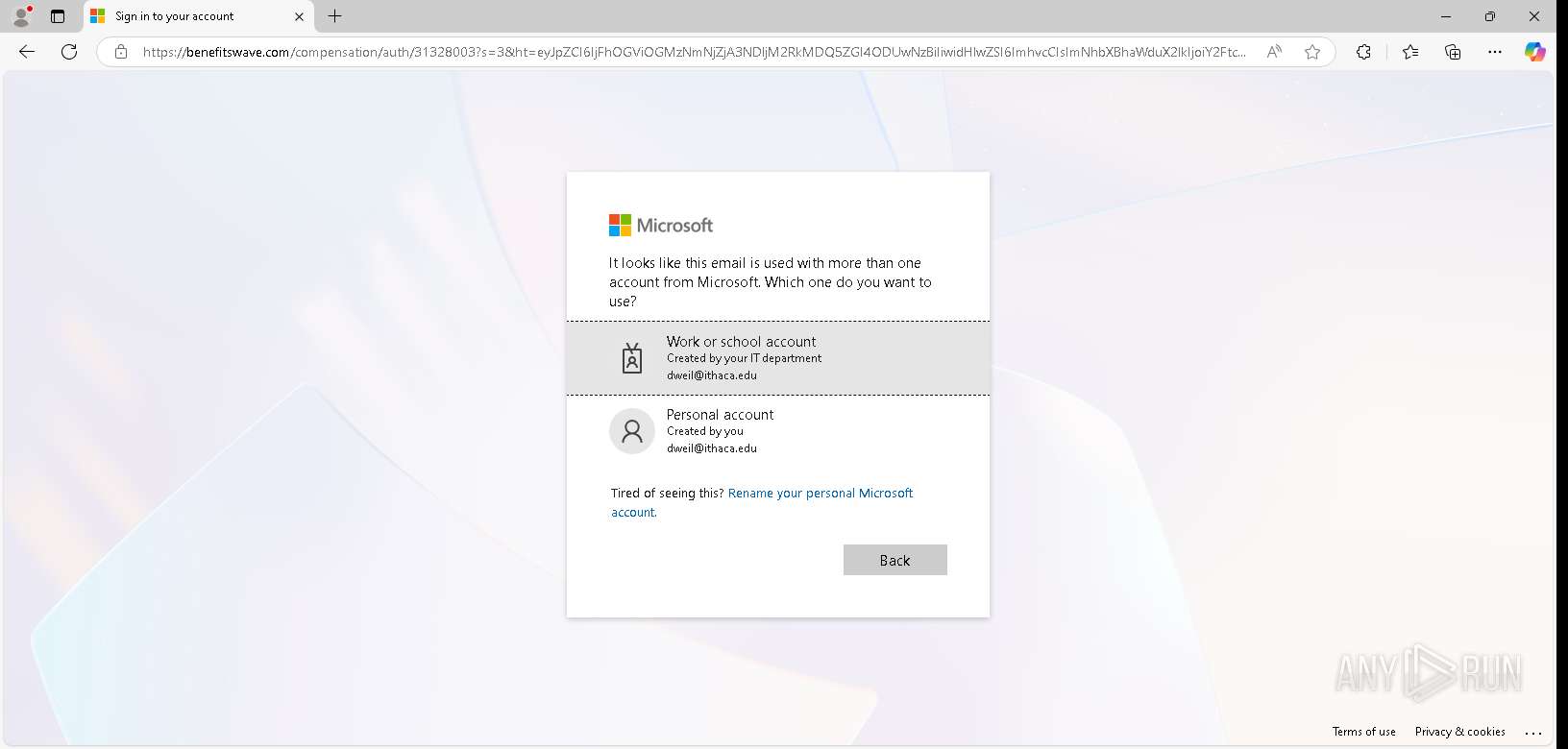
| Verdict: | Malicious activity |
| Threats: | EvilProxy is a phishing-as-a-service (PhaaS) platform that enables cybercriminals to bypass multi-factor authentication (MFA) and hijack user sessions. It leverages reverse proxy techniques to harvest credentials and session cookies, posing a serious threat to both individuals and enterprises. |
| Analysis date: | March 15, 2026, 21:35:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6F07E02C7787A1DE44B8874192646334 |
| SHA1: | 074D0E9D1739149551A319823A660095703A0653 |
| SHA256: | 057F4EB7469BD11A636DEB077D14684C714CB93634204CBF4DA0340F684F79C3 |
| SSDEEP: | 3:N8fvjDdrj:2nBj |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 6612)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
150
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 6612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --webtransport-developer-mode --string-annotations --always-read-main-dll --field-trial-handle=2268,i,4483529040041015744,4079588458005810556,262144 --variations-seed-version --mojo-platform-channel-handle=2612 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
15
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b6 | binary | |
MD5:21AD0BDC35C8AEC1364003FDB4FEE011 | SHA256:ABCC6EA2A48809CDDD125CD93C43F7352CC910B527CC2EE0B50FE4864B039ECC | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c1 | compressed | |
MD5:F911486951B62AFDFF95E0B60A7B6C34 | SHA256:811A9EA100FBDD669C13CADF36B5FB93E2EB953AC8ACF63B50865D81BAB7193F | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bd | compressed | |
MD5:E6F9C2D5A74A3E5D1F4EC8A81C969438 | SHA256:0BEB2B49EB3C530408AB26D852F699CFB133F7C45E5DDFAB26BE9F506C30D552 | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\15e5fa07-74af-4571-878d-d74c914821c6.tmp | text | |
MD5:F054A7D6E382DF24018FE84986B710A2 | SHA256:4E5235C6B40BCE6C5FD0554D554FCDB38E8016DCDDFA9CAB63103407CAF8DAEB | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF13a924.TMP | text | |
MD5:8CA6AC4CD0D4F8B2EA5A9FC6FD4311D7 | SHA256:EE810A451AEA499C3D6F89EDB840ED025DF0937874485A211A3BB39F915F4EA0 | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bf | compressed | |
MD5:1C0D6AB57F7F9489916221BE190ACF48 | SHA256:D558E9CC4B05F7F83F124570D2E026CE8FA24F85E0830AFAA152C1B0634CF900 | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bc | compressed | |
MD5:49A8628B8B6FBEF442B625D83BEE7B93 | SHA256:6915BA8D1C5F77F7851BF5149A5A5B496B6D795831E2413CF78A46EF0D614764 | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c0 | compressed | |
MD5:E6F9C2D5A74A3E5D1F4EC8A81C969438 | SHA256:0BEB2B49EB3C530408AB26D852F699CFB133F7C45E5DDFAB26BE9F506C30D552 | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000be | compressed | |
MD5:49A8628B8B6FBEF442B625D83BEE7B93 | SHA256:6915BA8D1C5F77F7851BF5149A5A5B496B6D795831E2413CF78A46EF0D614764 | |||
| 6612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c2 | compressed | |
MD5:F911486951B62AFDFF95E0B60A7B6C34 | SHA256:811A9EA100FBDD669C13CADF36B5FB93E2EB953AC8ACF63B50865D81BAB7193F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
83
TCP/UDP connections
68
DNS requests
60
Threats
34
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6244 | svchost.exe | HEAD | 200 | 104.102.63.189:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | whitelisted |
7648 | RUXIMICS.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/RUXIM?os=Windows&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3623&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&FlightRing=Retail&AttrDataVer=188&App=RUXIM&AppVer=&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
5336 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3593&FlightIds=&UpdateOfferedDays=344&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%206%20Model%2014%20Stepping%203&sku=48&ActivationChannel=Retail&AttrDataVer=188&IsMDMEnrolled=0&ProcessorCores=4&ProcessorModel=Intel%28R%29%20Core%28TM%29%20i5-6400%20CPU%20%40%202.70GHz&TotalPhysicalRAM=4096&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260246&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.212.222.21:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | — |
— | — | GET | 301 | 104.17.94.1:443 | https://tracking.kvo1.io/uHfVbF | unknown | text | 136 b | unknown |
6612 | msedge.exe | GET | 403 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1757972498&P2=404&P3=2&P4=SosfgGvPP%2bqG%2fKPFOnStRp0ebgR4wibSifLIFAVozbIX%2fohzlu3OKFqIl2l0qzX%2bohjhEGOVS0QtuGPmE2Wd%2bQ%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.212.222.21:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | text | 55 b | whitelisted |
— | — | POST | 200 | 150.171.28.11:443 | https://edge.microsoft.com/componentupdater/api/v1/update | unknown | text | 1.57 Kb | whitelisted |
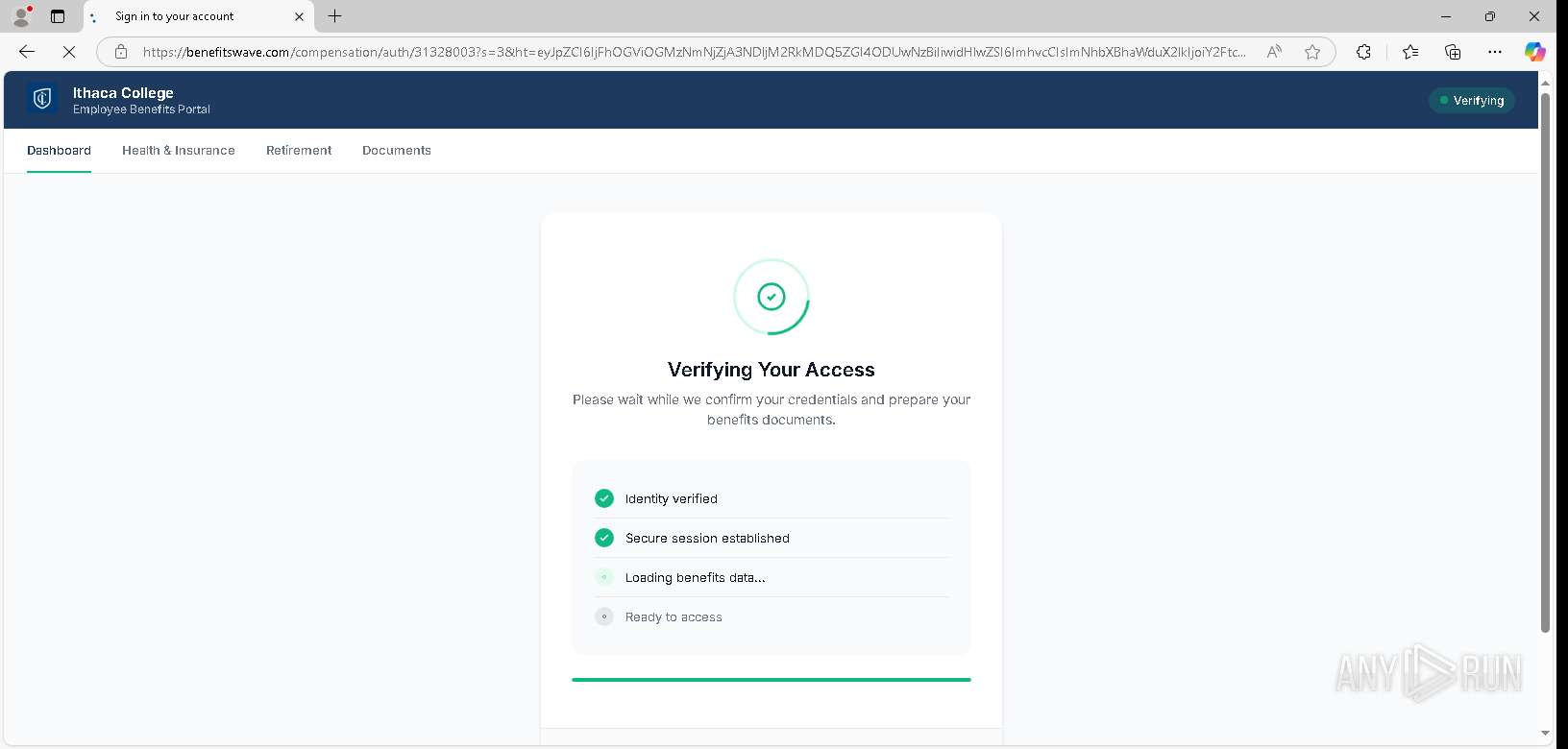
— | — | GET | 301 | 144.172.89.223:443 | https://fastx.to/5O35ck2i?_kx=pUzjHJ__7ZoTpO2Mf627kfKz9Jsl2xi6gjL8F776VUd2cnzfYXZhhwbPFnqGeusN.WJUgwU | unknown | — | — | — |
7568 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7568 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
440 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7648 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5336 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | whitelisted |
6612 | msedge.exe | 199.232.210.172:80 | msedge.b.tlu.dl.delivery.mp.microsoft.com | FASTLY | US | whitelisted |
6244 | svchost.exe | 104.102.63.189:443 | fs.microsoft.com | AKAMAI-AS | US | whitelisted |
6612 | msedge.exe | 104.17.93.1:443 | tracking.kvo1.io | CLOUDFLARENET | US | whitelisted |
6612 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6612 | msedge.exe | 144.172.89.223:443 | fastx.to | ROUTERHOSTING | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
msedge.b.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
tracking.kvo1.io |
| unknown |
edge.microsoft.com |
| whitelisted |
fastx.to |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
benefitswave.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7648 | RUXIMICS.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Misc activity | ET HUNTING HTTP Permissions-Policy Geolocation Directive Misconfiguration |
6612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
— | — | Misc activity | ET HUNTING HTTP Permissions-Policy Geolocation Directive Misconfiguration |
— | — | Misc activity | ET HUNTING HTTP Permissions-Policy Geolocation Directive Misconfiguration |
— | — | Misc activity | ET HUNTING HTTP Permissions-Policy Geolocation Directive Misconfiguration |
— | — | Misc activity | ET HUNTING HTTP Permissions-Policy Geolocation Directive Misconfiguration |
— | — | Misc activity | ET HUNTING HTTP Permissions-Policy Geolocation Directive Misconfiguration |