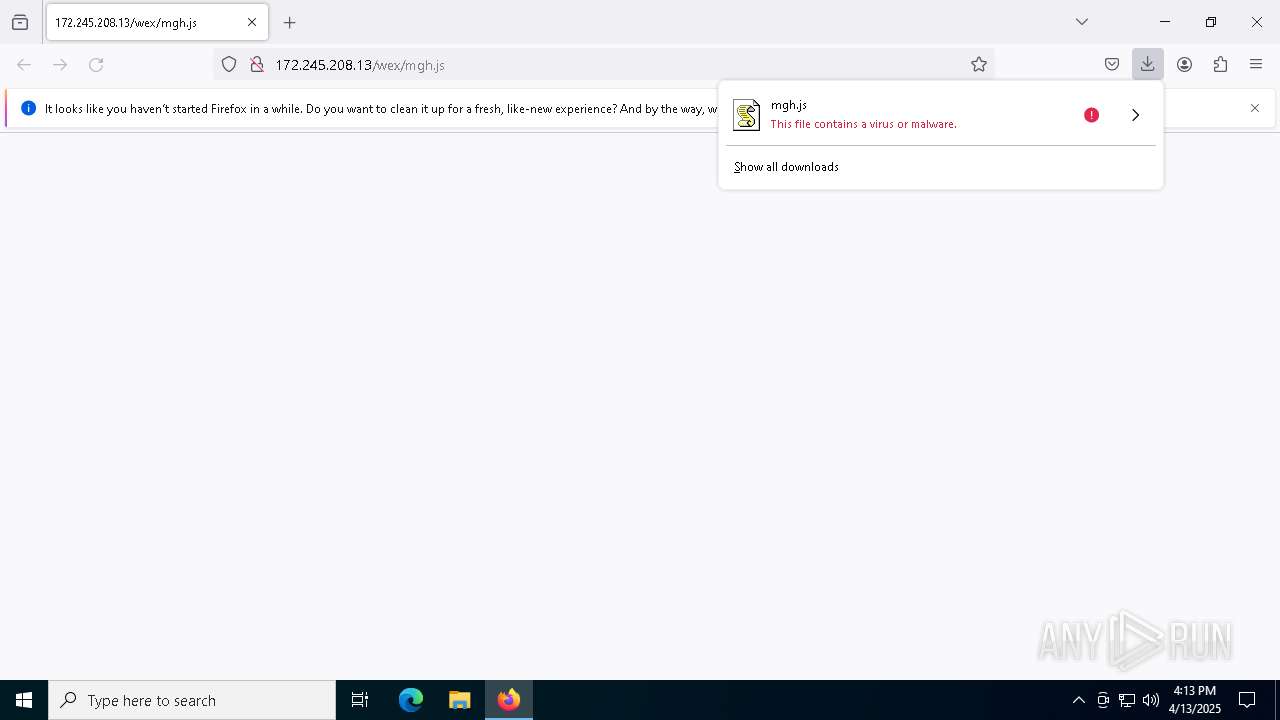
| URL: | http://172.245.208.13/wex/mgh.js |
| Full analysis: | https://app.any.run/tasks/f4e55d26-64c4-4079-a15b-c456a0c7e265 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | April 13, 2025, 16:13:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9CCB44B3C34AF63D426CF98FC35C9DCA |
| SHA1: | A26CFDABA9E4B8C08CF531A5D8408A897C7F8373 |
| SHA256: | 05703A7D557F5244A307869B7FE31DC83DEE3F0EF536BE1F68F9DA9C0B5FFAA0 |
| SSDEEP: | 3:N1KqXL8guNLPW:CqYguNLu |
MALICIOUS
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 4268)
- wscript.exe (PID: 6516)
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 6516)
Detects the decoding of a binary file from Base64 (SCRIPT)
- wscript.exe (PID: 6516)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 4268)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 4268)
Gets startup folder path (SCRIPT)
- wscript.exe (PID: 4268)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 4268)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 4268)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 4268)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 4268)
Modifies registry startup key (SCRIPT)
- wscript.exe (PID: 4268)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 4268)
Opens a text file (SCRIPT)
- wscript.exe (PID: 4268)
Create files in the Startup directory
- wscript.exe (PID: 4268)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 4268)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 4268)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 4268)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 4268)
WSHRAT has been detected (SURICATA)
- wscript.exe (PID: 4268)
Connects to the CnC server
- wscript.exe (PID: 4268)
Gets username (SCRIPT)
- wscript.exe (PID: 4268)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 4268)
SUSPICIOUS
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 6516)
Script creates XML DOM node (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 6516)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 4268)
- wscript.exe (PID: 6516)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 6516)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 6516)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 6516)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 6516)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 6516)
The process executes JS scripts
- wscript.exe (PID: 5392)
Application launched itself
- wscript.exe (PID: 5392)
Executable content was dropped or overwritten
- wscript.exe (PID: 6516)
Gets the drive type (SCRIPT)
- wscript.exe (PID: 4268)
Gets disk free space (SCRIPT)
- wscript.exe (PID: 4268)
Accesses local storage devices (Win32_LogicalDisk) via WMI (SCRIPT)
- wscript.exe (PID: 4268)
Gets a collection of all available drive names (SCRIPT)
- wscript.exe (PID: 4268)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 4268)
Checks whether the drive is ready (SCRIPT)
- wscript.exe (PID: 4268)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 4268)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 4268)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 4268)
Gets computer name (SCRIPT)
- wscript.exe (PID: 4268)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 4268)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 4268)
Accesses WMI object caption (SCRIPT)
- wscript.exe (PID: 4268)
Accesses operating system name via WMI (SCRIPT)
- wscript.exe (PID: 4268)
Connects to unusual port
- wscript.exe (PID: 4268)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 4268)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 4268)
Contacting a server suspected of hosting an CnC
- wscript.exe (PID: 4268)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 4268)
Gets name of the script (SCRIPT)
- wscript.exe (PID: 4268)
INFO
Application launched itself
- firefox.exe (PID: 7396)
- firefox.exe (PID: 7300)
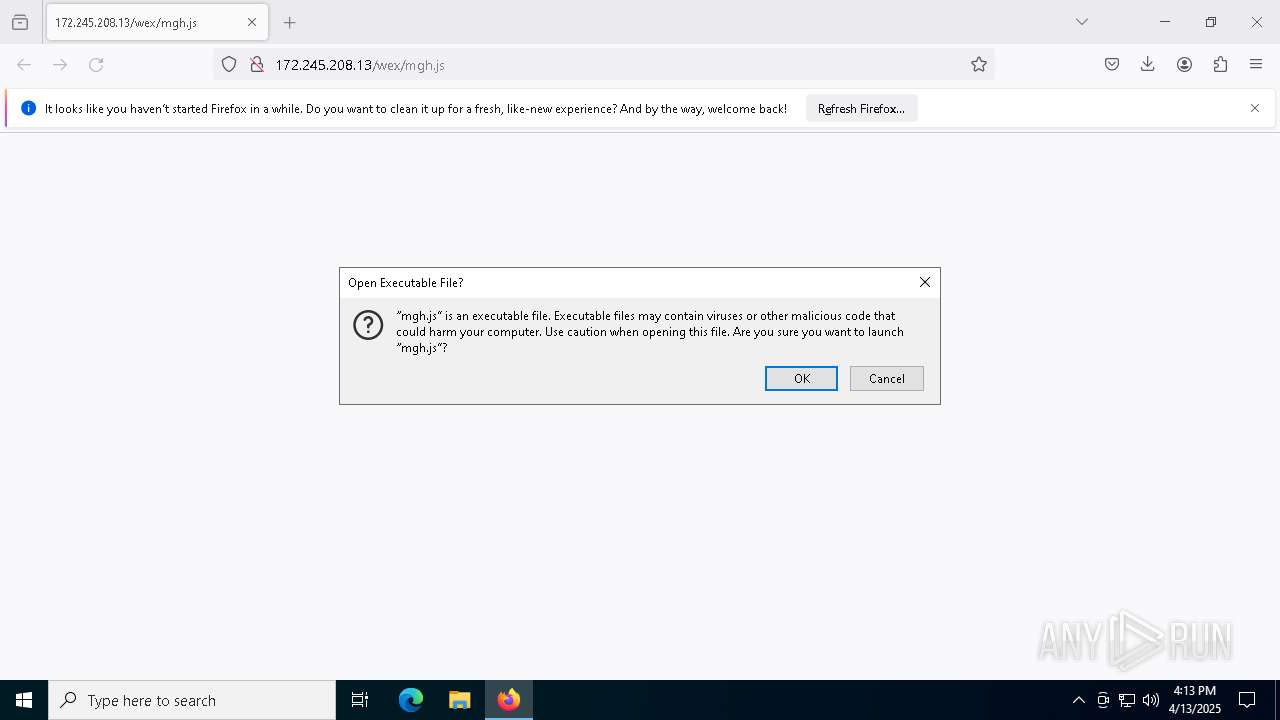
Autorun file from Downloads
- firefox.exe (PID: 7396)
Manual execution by a user
- wscript.exe (PID: 5392)
Checks supported languages
- iWFu.exe (PID: 1300)
Checks proxy server information
- wscript.exe (PID: 4268)
Reads the software policy settings
- slui.exe (PID: 2316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
146
Monitored processes
19
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1300 | "C:\Users\admin\AppData\Local\Temp\iWFu.exe" | C:\Users\admin\AppData\Local\Temp\iWFu.exe | — | wscript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2152 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2316 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4268 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\adobe.js" | C:\Windows\System32\wscript.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4488 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5544 -childID 6 -isForBrowser -prefsHandle 5536 -prefMapHandle 5532 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1284 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {8314e4d0-9a9a-4b61-a579-52874d50f442} 7396 "\\.\pipe\gecko-crash-server-pipe.7396" 1b0e6358690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5164 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5076 -childID 4 -isForBrowser -prefsHandle 5308 -prefMapHandle 5304 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1284 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {123571a7-4847-4aa8-8fa5-63dee1adf2ff} 7396 "\\.\pipe\gecko-crash-server-pipe.7396" 1b0e6358310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5392 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\mgh.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5936 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6476 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5448 -childID 5 -isForBrowser -prefsHandle 5368 -prefMapHandle 5372 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1284 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {bacec672-6aa4-4a2b-a631-a368accdb91f} 7396 "\\.\pipe\gecko-crash-server-pipe.7396" 1b0e63584d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
16 682
Read events
16 669
Write events
13
Delete events
0
Modification events
| (PID) Process: | (7396) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5392) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.js\OpenWithProgids |
| Operation: | write | Name: | JSFile |
Value: | |||
| (PID) Process: | (5392) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: D454110000000000 | |||
| (PID) Process: | (4268) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | adobe |
Value: wscript.exe //B "C:\Users\admin\AppData\Local\Temp\adobe.js" | |||
Executable files
1
Suspicious files
147
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7396 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7396 | firefox.exe | C:\Users\admin\Downloads\mgh.Cp9BcQSE.js.part | — | |
MD5:— | SHA256:— | |||
| 7396 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7396 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7396 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7396 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7396 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7396 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:45A4A90879D7426CCB61574F4DF8F9FA | SHA256:39909D531C097BCFF51AD89559901B72887DAB2EB1B20B3D9E8F270B3EFDE87D | |||
| 7396 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7396 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:AADE8C264BC2949C09F23251F94F0F7D | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
74
DNS requests
105
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7396 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7396 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7396 | firefox.exe | GET | — | 172.245.208.13:80 | http://172.245.208.13/wex/mgh.js | unknown | — | — | malicious |
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7396 | firefox.exe | POST | 200 | 184.24.77.59:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7396 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
7396 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7396 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7396 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7396 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7396 | firefox.exe | 172.245.208.13:80 | — | AS-COLOCROSSING | US | malicious |
7396 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7396 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
7396 | firefox.exe | 142.250.185.234:443 | safebrowsing.googleapis.com | — | — | whitelisted |
7396 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | whitelisted |
7396 | firefox.exe | 34.36.54.80:443 | ads-img.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.kozow .com Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.kozow .com Domain |
4268 | wscript.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.kozow .com Domain |
4268 | wscript.exe | Malware Command and Control Activity Detected | ET MALWARE Worm.VBS Dunihi/Houdini/H-Worm/WSHRAT Checkin 1 |
4268 | wscript.exe | Malware Command and Control Activity Detected | ET MALWARE WSHRAT CnC Checkin |
4268 | wscript.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.kozow .com Domain |
4268 | wscript.exe | Malware Command and Control Activity Detected | ET MALWARE Worm.VBS Dunihi/Houdini/H-Worm/WSHRAT Checkin 1 |
4268 | wscript.exe | Malware Command and Control Activity Detected | ET MALWARE WSHRAT CnC Checkin |
4268 | wscript.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.kozow .com Domain |
4268 | wscript.exe | Malware Command and Control Activity Detected | ET MALWARE Worm.VBS Dunihi/Houdini/H-Worm/WSHRAT Checkin 1 |