| File name: | client |
| Full analysis: | https://app.any.run/tasks/05a71047-77f8-43cd-83d9-79cd27b01814 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | August 18, 2018, 19:26:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 488A5223BE4031E34778F28AA7AEFCBF |
| SHA1: | D08B42278D1A472280114C3FBD860C27B8F32086 |
| SHA256: | 055D4B6E6D189FF1F89BEDF51E83A74C6F0A83DA629C27DA7A4570F142D2AAD3 |
| SSDEEP: | 12288:GbdMET5piVslVNOzTkSCUsmc4p90IeSCBlgEy2sNvCY:GbSkmslVNhmNb0vHsNn |
MALICIOUS
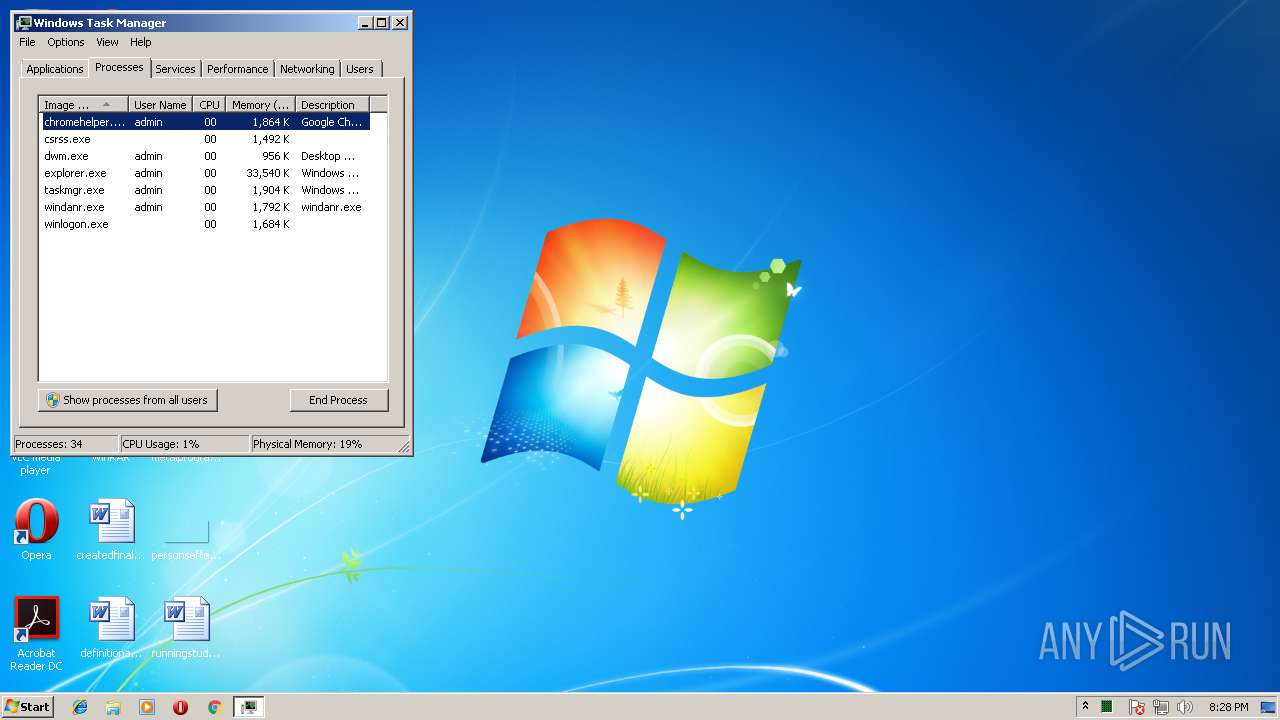
Loads dropped or rewritten executable
- chromehelper.exe (PID: 2504)
- explorer.exe (PID: 1380)
- taskmgr.exe (PID: 3012)
- conhost.exe (PID: 592)
- schtasks.exe (PID: 3952)
- conhost.exe (PID: 2764)
- schtasks.exe (PID: 620)
- conhost.exe (PID: 4088)
- conhost.exe (PID: 3184)
- explorer.exe (PID: 3696)
- explorer.exe (PID: 3728)
Changes the autorun value in the registry
- chromehelper.exe (PID: 2504)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3952)
- schtasks.exe (PID: 620)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2672)
- cmd.exe (PID: 3652)
Application was dropped or rewritten from another process
- atiservice.exe (PID: 592)
Connects to CnC server
- atiservice.exe (PID: 592)
SUSPICIOUS
Executable content was dropped or overwritten
- client.scr (PID: 2312)
- chromehelper.exe (PID: 2504)
Starts itself from another location
- client.scr (PID: 2312)
Starts application with an unusual extension
- explorer.exe (PID: 1380)
Starts CMD.EXE for commands execution
- chromehelper.exe (PID: 2504)
Connects to unusual port
- atiservice.exe (PID: 592)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (46.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (23.3) |
| .exe | | | Win32 Executable (generic) (15.9) |
| .exe | | | Generic Win/DOS Executable (7) |
| .exe | | | DOS Executable Generic (7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 512000 |
| InitializedDataSize: | 203264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7de60 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.4 |
| ProductVersionNumber: | 1.0.0.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Turkish |
| CharacterSet: | Windows, Turkish |
| CompanyName: | Google Inc |
| FileDescription: | Google Chrome Crash Helper |
| FileVersion: | 1.0.0.4 |
| InternalName: | - |
| LegalCopyright: | Copyright 2017 Google Inc. All Right reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | chromehelper.exe |
| ProductName: | Google Chrome |
| ProductVersion: | 66.0.3359.1 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Google Inc |
| FileDescription: | Google Chrome Crash Helper |
| FileVersion: | 1.0.0.4 |
| InternalName: | - |
| LegalCopyright: | Copyright 2017 Google Inc. All Right reserved. |
| LegalTrademarks: | - |
| OriginalFilename: | chromehelper.exe |
| ProductName: | Google Chrome |
| ProductVersion: | 66.0.3359.1 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0007D000 | 0x0007D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57236 |
DATA | 0x0007E000 | 0x0000216C | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.78531 |
BSS | 0x00081000 | 0x00001111 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00083000 | 0x00002932 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.90009 |
.tls | 0x00086000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00087000 | 0x00000033 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.678483 |
.reloc | 0x00088000 | 0x00007A88 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00090000 | 0x0002CA7C | 0x0002CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.9882 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.33781 | 856 | Latin 1 / Western European | Turkish - Turkey | RT_VERSION |
2 | 4.20404 | 21640 | Latin 1 / Western European | Turkish - Turkey | RT_ICON |
3 | 3.92354 | 16936 | Latin 1 / Western European | Turkish - Turkey | RT_ICON |
4 | 4.535 | 9640 | Latin 1 / Western European | Turkish - Turkey | RT_ICON |
5 | 4.5716 | 4264 | Latin 1 / Western European | Turkish - Turkey | RT_ICON |
6 | 5.0081 | 2440 | Latin 1 / Western European | Turkish - Turkey | RT_ICON |
7 | 5.09547 | 1128 | Latin 1 / Western European | Turkish - Turkey | RT_ICON |
PREVIEWGLYPH | 2.85172 | 232 | Latin 1 / Western European | Turkish - Turkey | RT_BITMAP |
EX | 5.9985 | 24707 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
KD | 5.9981 | 25259 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
wininet.dll |
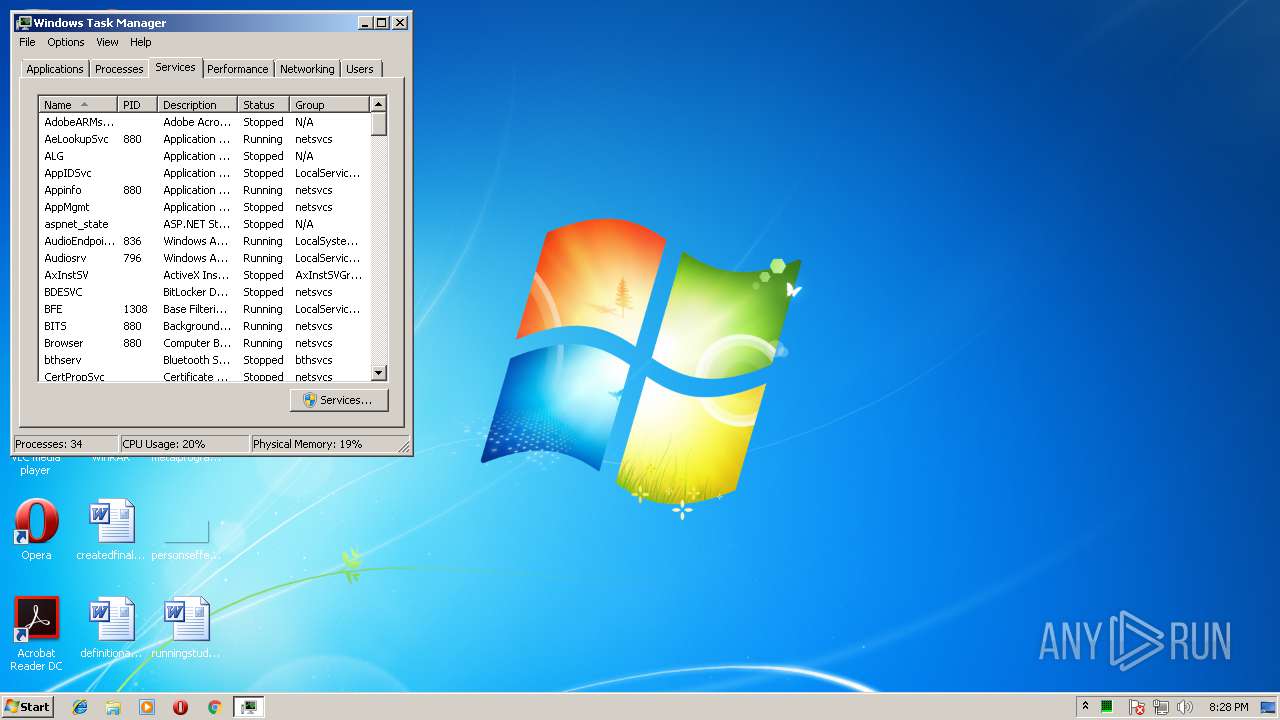
Total processes
50
Monitored processes
16
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
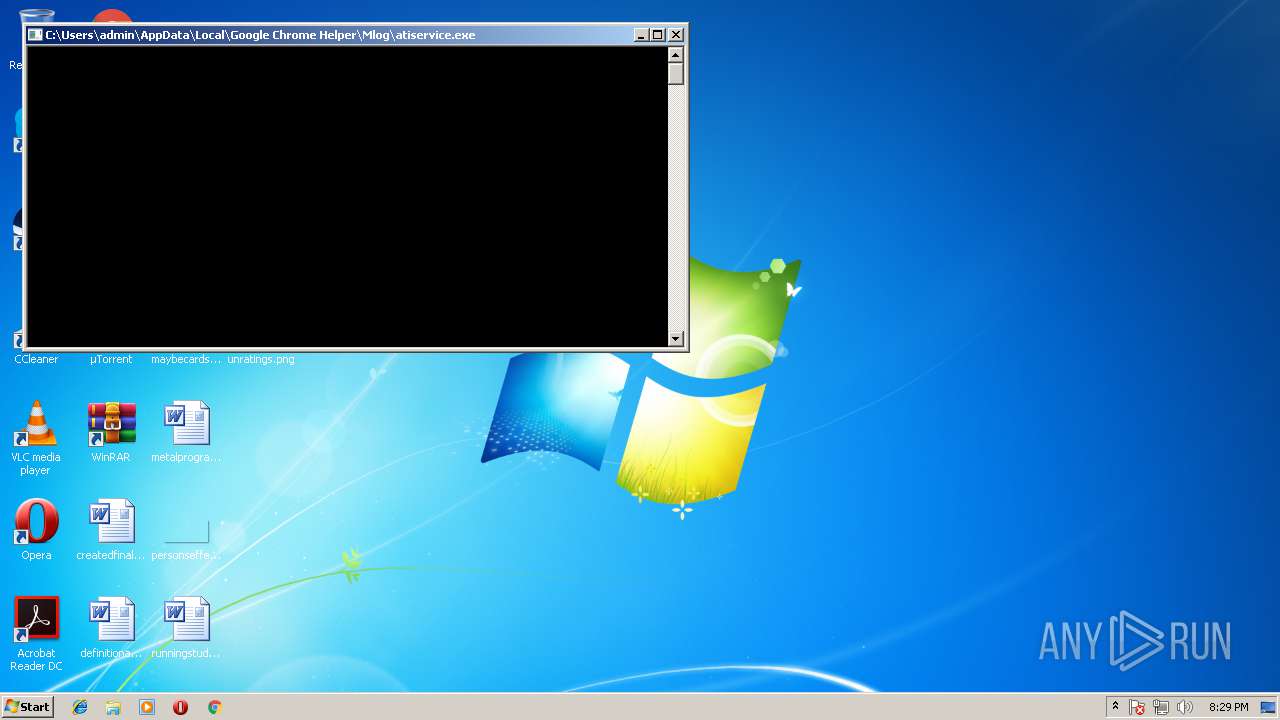
| 592 | "C:\Users\admin\AppData\Local\Google Chrome Helper\Mlog\atiservice.exe" | C:\Users\admin\AppData\Local\Google Chrome Helper\Mlog\atiservice.exe | explorer.exe | ||||||||||||
User: admin Company: ATI Corp Integrity Level: MEDIUM Description: ATI Graphics Controlller Update Service Exit code: 0 Version: 2.6.2 Modules
| |||||||||||||||
| 592 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 620 | schtasks /DELETE /F /TN "Ati Update Service" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | cmd.exe /C explorer "C:\Users\admin\AppData\Local\Google Chrome Helper\Mlog\atiservice.exe" | C:\Windows\system32\cmd.exe | — | chromehelper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\AppData\Local\Temp\client.scr" /S | C:\Users\admin\AppData\Local\Temp\client.scr | explorer.exe | ||||||||||||
User: admin Company: Google Inc Integrity Level: MEDIUM Description: Google Chrome Crash Helper Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\AppData\Local\Google Chrome Helper\chromehelper.exe" /S | C:\Users\admin\AppData\Local\Google Chrome Helper\chromehelper.exe | client.scr | ||||||||||||
User: admin Company: Google Inc Integrity Level: MEDIUM Description: Google Chrome Crash Helper Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 2672 | cmd.exe /C schtasks /END /TN "Ati Update Service" | C:\Windows\system32\cmd.exe | — | chromehelper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2764 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
565
Read events
530
Write events
35
Delete events
0
Modification events
| (PID) Process: | (2312) client.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2312) client.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2504) chromehelper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Google Chrome Helper |
Value: C:\Users\admin\AppData\Local\Google Chrome Helper\chromehelper.exe | |||
| (PID) Process: | (3012) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (3012) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000000A0000000A0000009E010000C90100000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005A0000004000000021000000460000004A000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000001000000020000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\gnfxzte.rkr |
Value: 00000000000000000B000000D96B0300000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004E00000071000000428219000A00000009000000B64206007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C0072006500670065006400690074002E0065007800650000004D00D8674D003076B90618AB4E000100000068E9E101F0E9E101FCEFE101EDE00B77347B1800FEFFFFFFE72F0F77822E0F770000000004EBE1010000000078EAE1010000000078EAE1017800000030EAE101FE720F773CEBE10160EDE101780000001800000078EAE101000000004CEAE10151EE0F77F48EF6760000000004EBE1011E00000070EAE10120EF0F773076B9060AA50E771E0000000000000004EBE10100000000F88EF676F0EAE101D6A810778CEAE101A4EAE101000000000000000000004D003076B9065A008A004E76B9060A001900011B8A11A4EAE10100000000010500001876B90611000000A045500098455000E82C0F7754EBE1011000000034EB0000A2F8B40EE4EAE1018291597534EBE101049300008EF8B40EF8EAE101B69C597508934D025C0000000401000098F5E10158F5E10111000000A04550009845500098F5E101785BE203FA4FEE730000000088EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101090000002B000000334F04007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000070EAE101FFFFFFFFE0B55100FFFFFFFF90492B7500000000000000000CEAE101D5742775000400000000000070EAE101FFFFFFFFE0B55100FFFFFFFFD0155200D4165200D8B551003CEAE1012FB1587580B08B757CF7E101381E597514635975A016500070EAE101308351007000000052F8B40E50EAE101BE6A5975A016500070EAE101000000007CECE1016F625975A016500070EAE10100000400000000807C625975A016500063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630011000000A0455000984550002000700069006E006E00650064005C0088EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101090000002B000000334F04007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000070EAE101FFFFFFFFE0B55100FFFFFFFF90492B7500000000000000000CEAE101D5742775000400000000000070EAE101FFFFFFFFE0B55100FFFFFFFFD0155200D4165200D8B551003CEAE1012FB1587580B08B757CF7E101381E597514635975A016500070EAE101308351007000000052F8B40E50EAE101BE6A5975A016500070EAE101000000007CECE1016F625975A016500070EAE10100000400000000807C625975A016500063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630011000000A0455000984550002000700069006E006E00650064005C0088EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101 | |||
| (PID) Process: | (2504) chromehelper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chromehelper_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2504) chromehelper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chromehelper_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2504) chromehelper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chromehelper_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
5
Suspicious files
0
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Temp\etlN7a.exe | — | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Temp\RCX3B7E.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Temp\etlN7a.ico | — | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Temp\RCX3B8E.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Temp\RCX3B9F.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Google Chrome Helper\update.ini | — | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Google Chrome Helper\config.dat | text | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Google Chrome Helper\Mlog\_cache | res | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Google Chrome Helper\Mlog\atiservice64.exe | executable | |
MD5:— | SHA256:— | |||
| 2504 | chromehelper.exe | C:\Users\admin\AppData\Local\Google Chrome Helper\Mlog\config.json | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
2
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2504 | chromehelper.exe | GET | 301 | 69.197.18.180:80 | http://xredini.mooo.com/ | US | — | — | suspicious |
2504 | chromehelper.exe | GET | 200 | 45.76.3.86:80 | http://45.76.3.86/min | US | res | 1.64 Mb | suspicious |
2504 | chromehelper.exe | GET | 200 | 45.76.3.86:80 | http://45.76.3.86/config | US | text | 3.65 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2504 | chromehelper.exe | 69.197.18.180:80 | xredini.mooo.com | Staminus Communications | US | suspicious |
2504 | chromehelper.exe | 45.76.3.86:80 | — | Choopa, LLC | US | suspicious |
592 | atiservice.exe | 51.15.58.224:14444 | xmr-eu1.nanopool.org | Online S.a.s. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xredini.mooo.com |
| suspicious |
xmr-eu1.nanopool.org |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1092 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to Abused Domain *.mooo.com |
2504 | chromehelper.exe | A Network Trojan was detected | ET POLICY Suspicious User-Agent Containing .exe |
2504 | chromehelper.exe | A Network Trojan was detected | ET POLICY Suspicious User-Agent Containing .exe |
2504 | chromehelper.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to Abused Domain *.mooo.com |
2504 | chromehelper.exe | A Network Trojan was detected | ET POLICY Suspicious User-Agent Containing .exe |
592 | atiservice.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
592 | atiservice.exe | Misc activity | SUSPICIOUS [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
592 | atiservice.exe | Misc activity | SUSPICIOUS [PTsecurity] Risktool.W32.coinminer!c |
592 | atiservice.exe | Misc activity | SUSPICIOUS [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
592 | atiservice.exe | Misc activity | SUSPICIOUS [PTsecurity] Risktool.W32.coinminer!c |