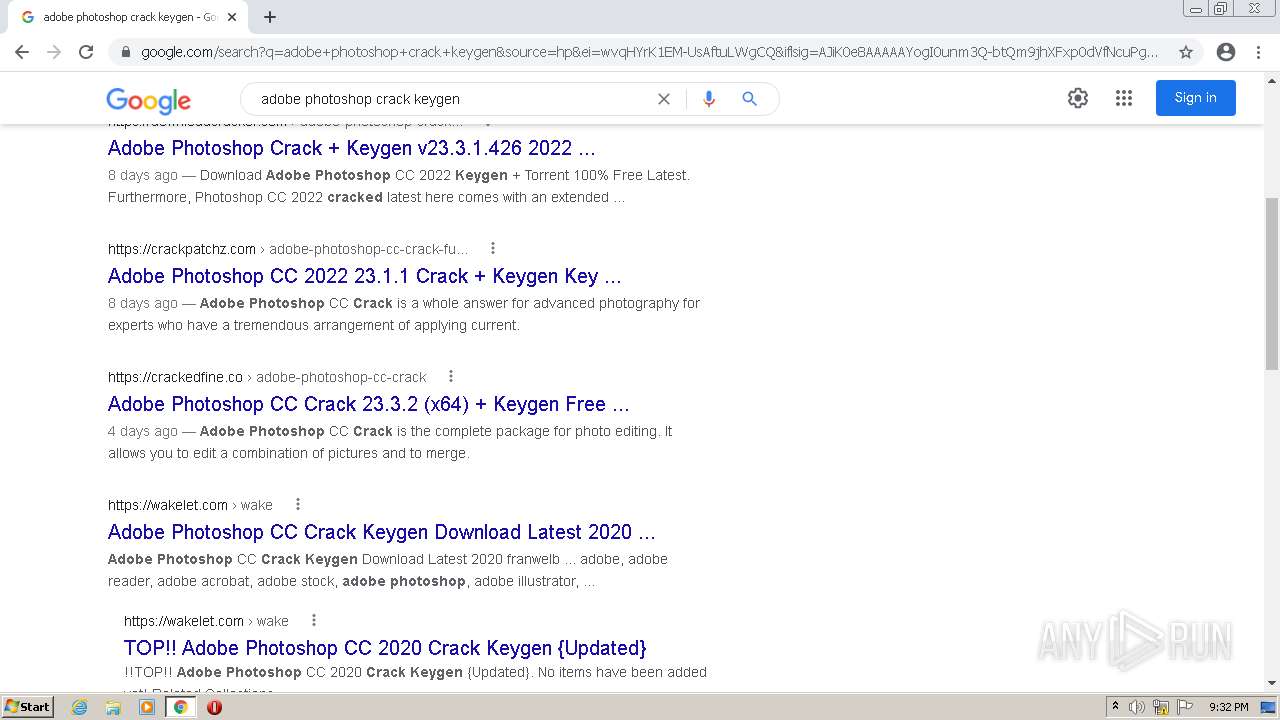
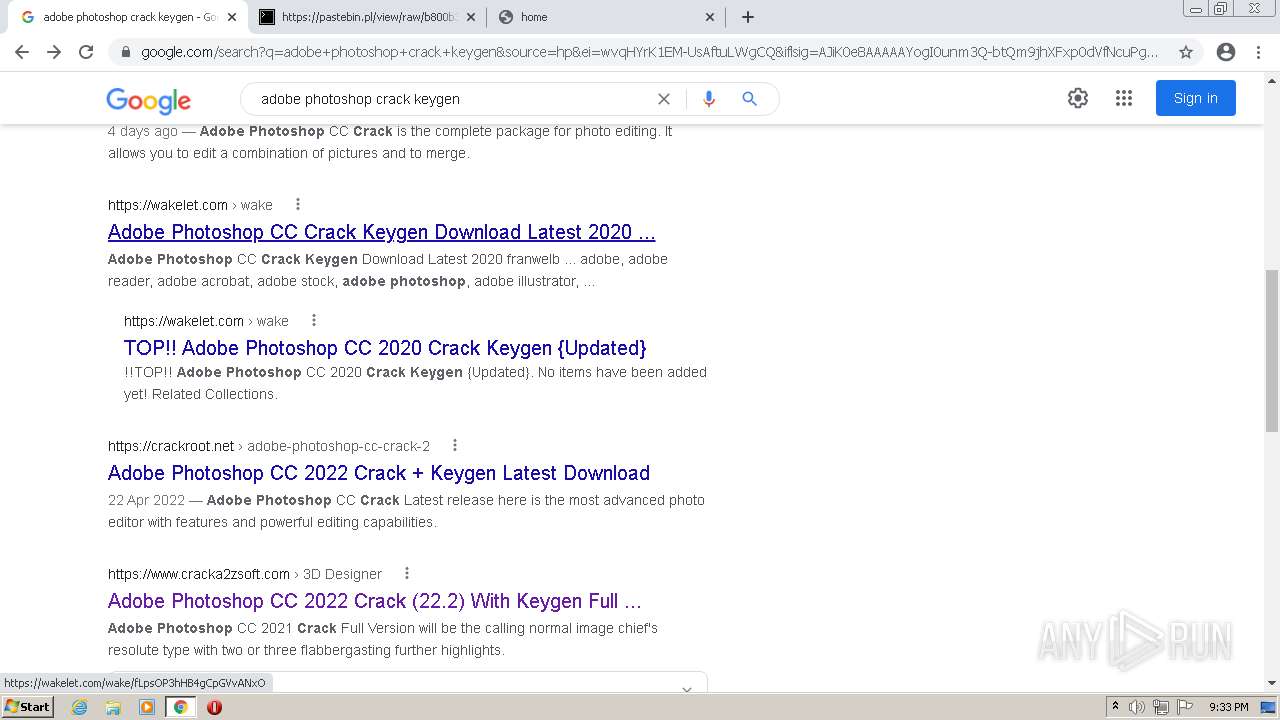
| URL: | https://google.com |
| Full analysis: | https://app.any.run/tasks/8920c2c2-dc6c-4385-9c0d-191b8c11600e |
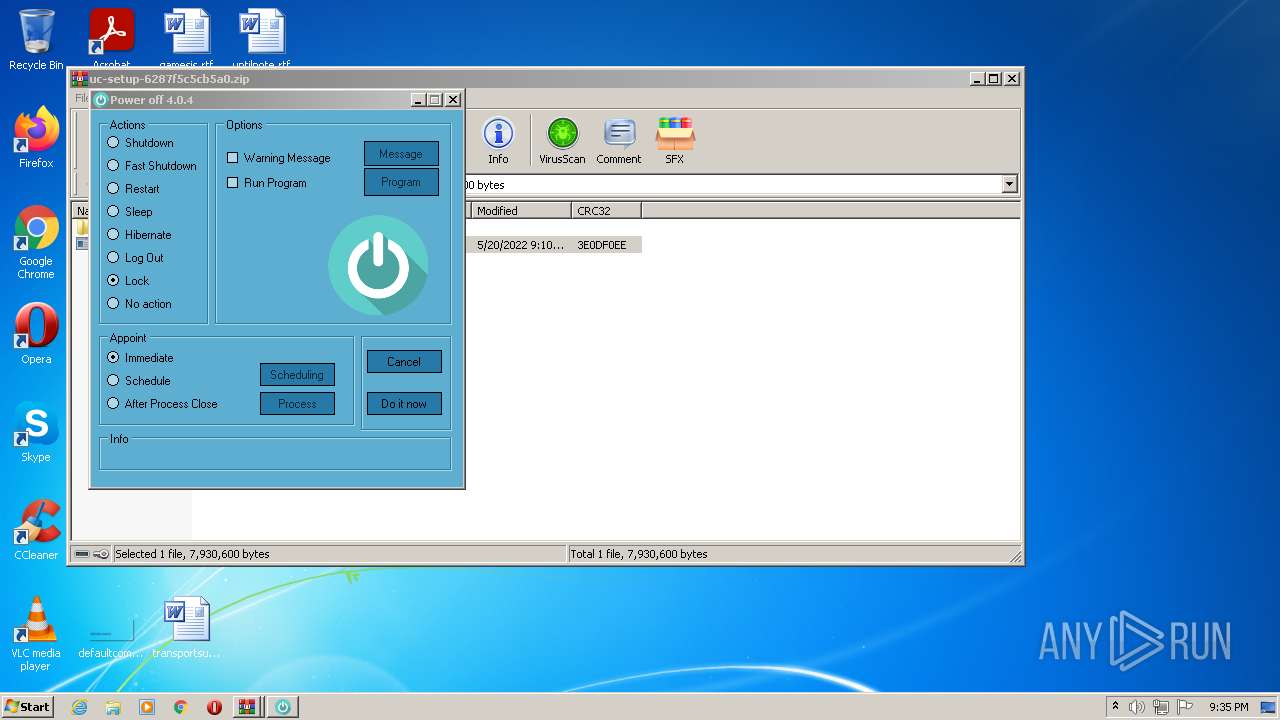
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | May 20, 2022, 20:31:54 |
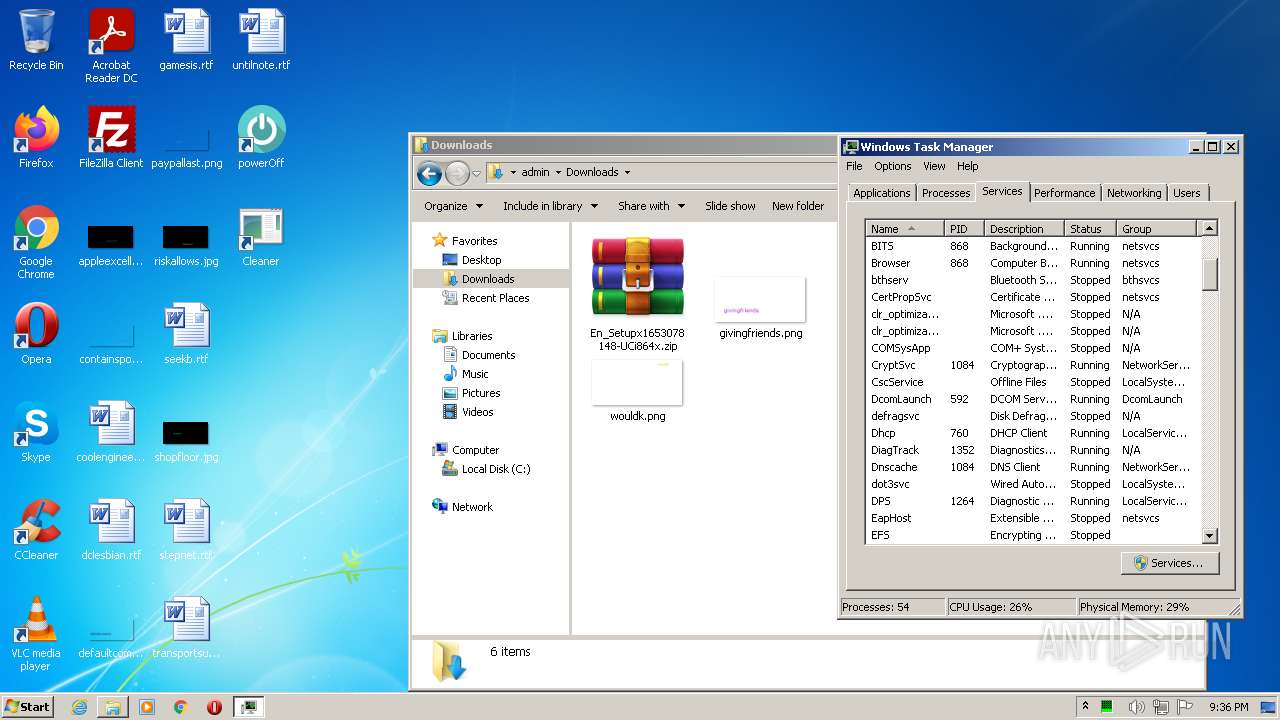
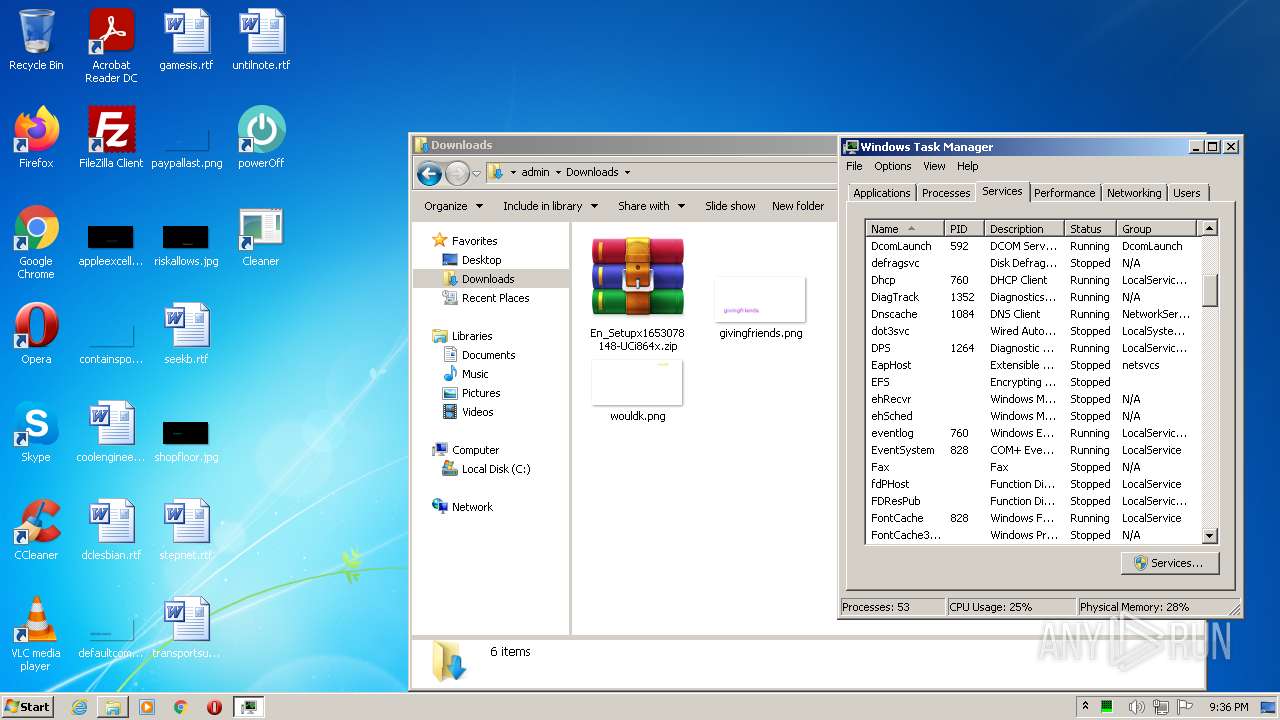
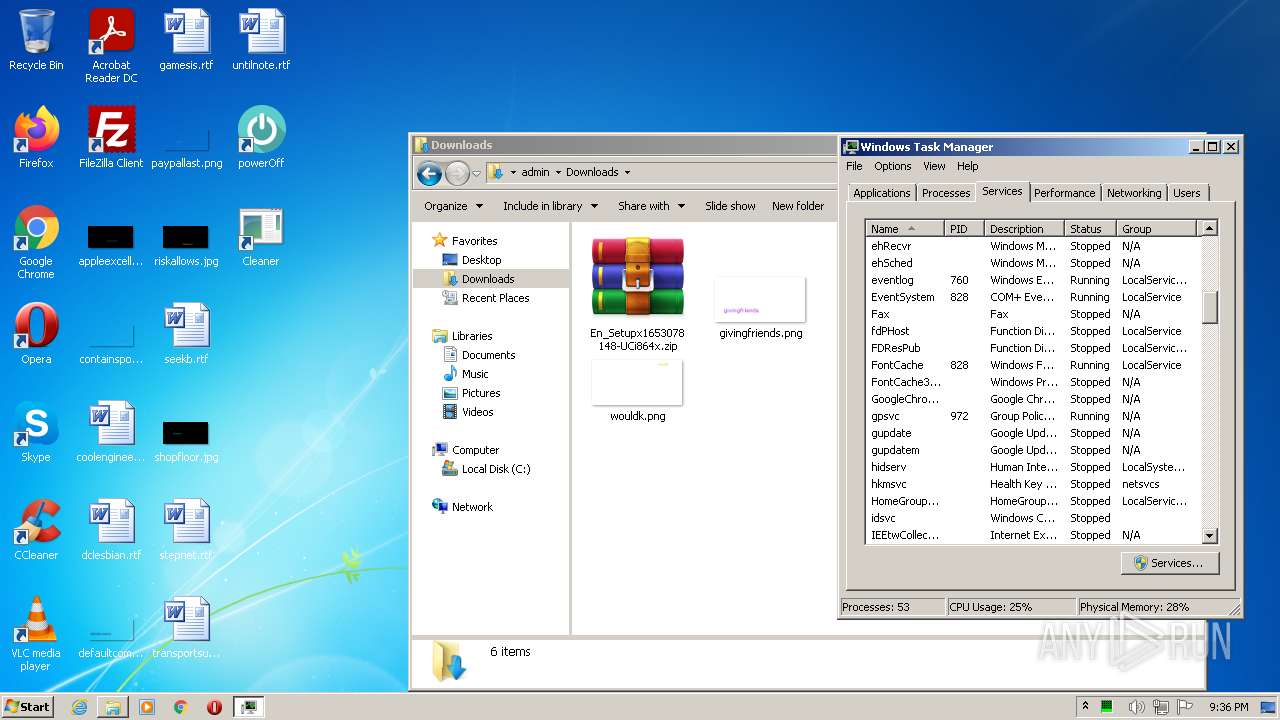
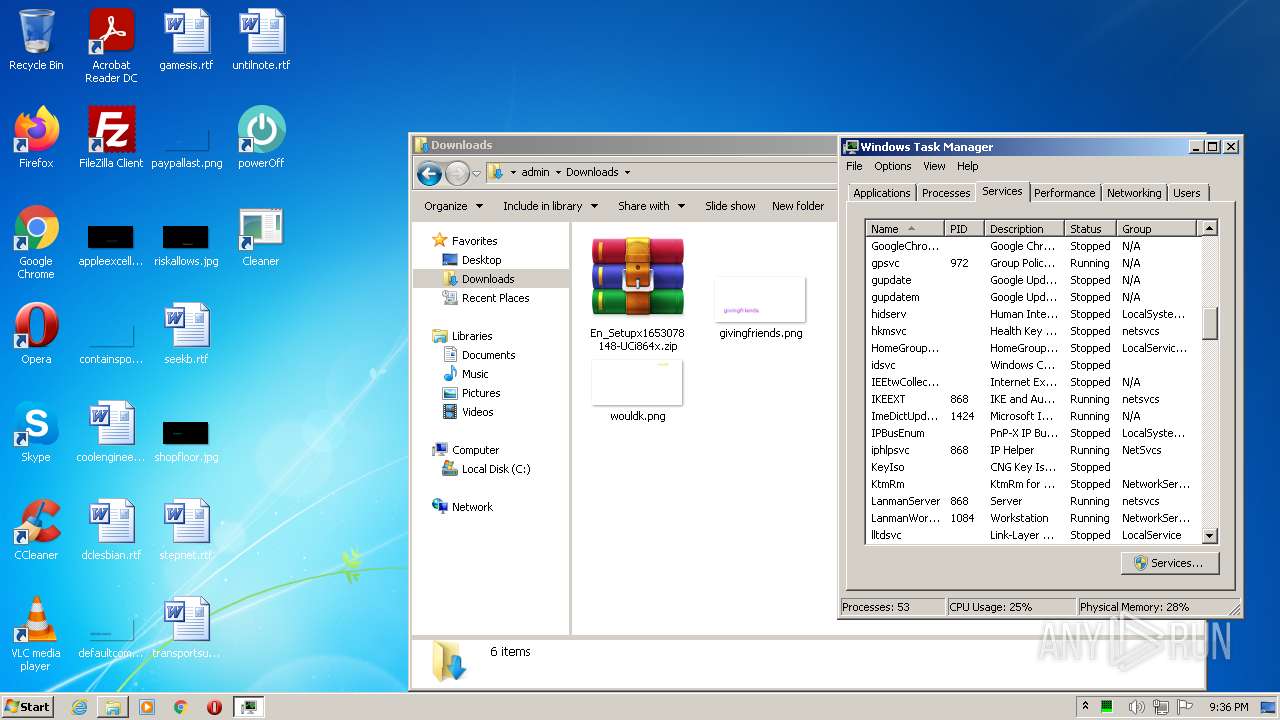
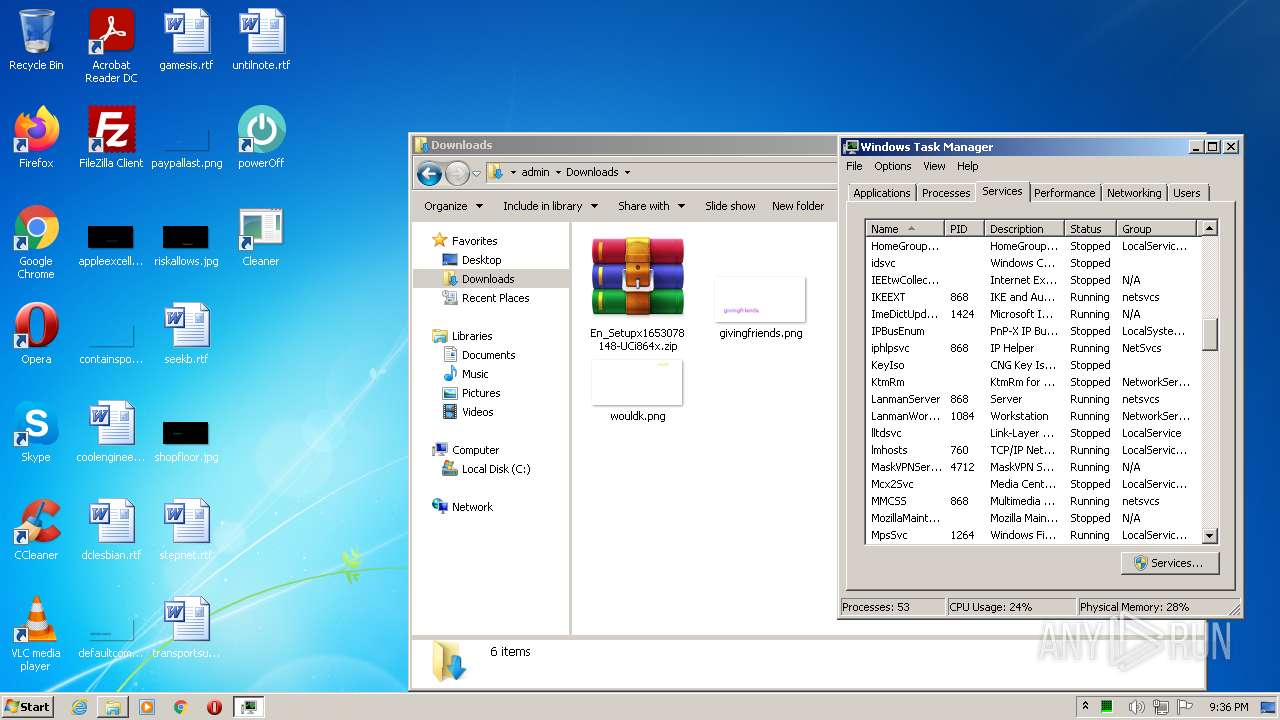
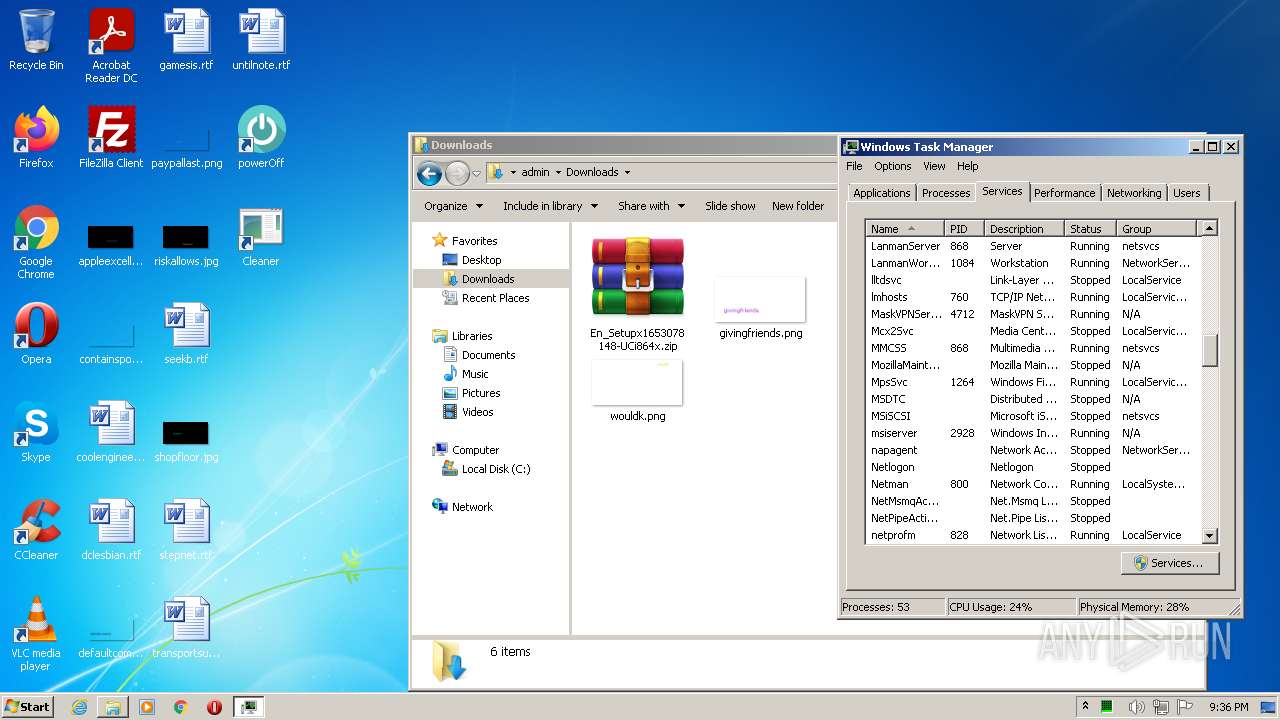
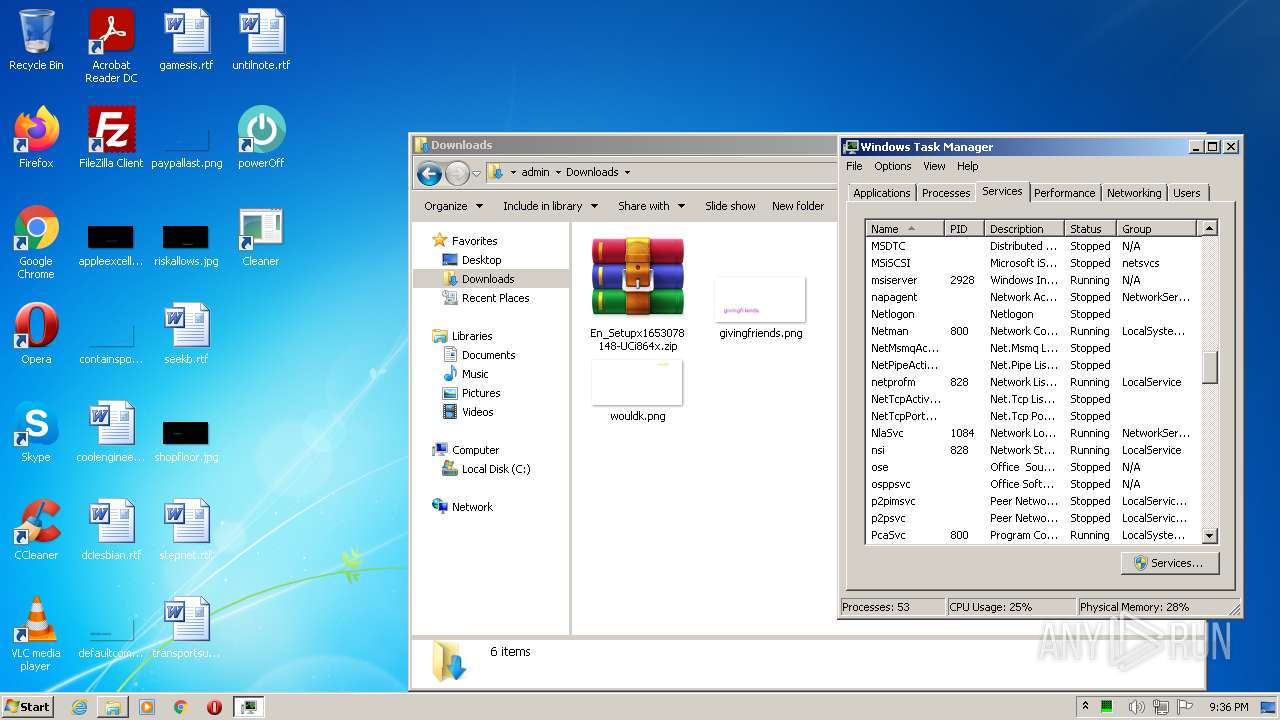
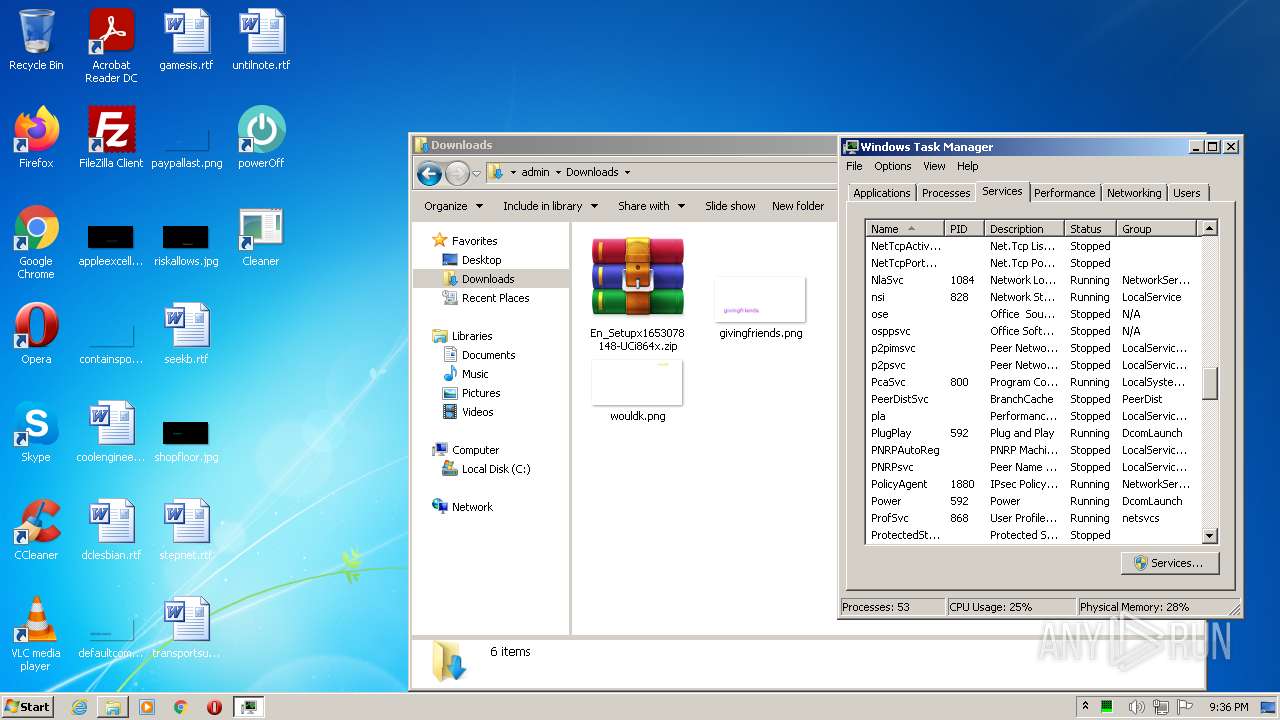
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 99999EBCFDB78DF077AD2727FD00969F |
| SHA1: | 72FE95C5576EC634E214814A32AB785568EDA76A |
| SHA256: | 05046F26C83E8C88B3DDAB2EAB63D0D16224AC1E564535FC75CDCEEE47A0938D |
| SSDEEP: | 3:N8r3uK:2LuK |
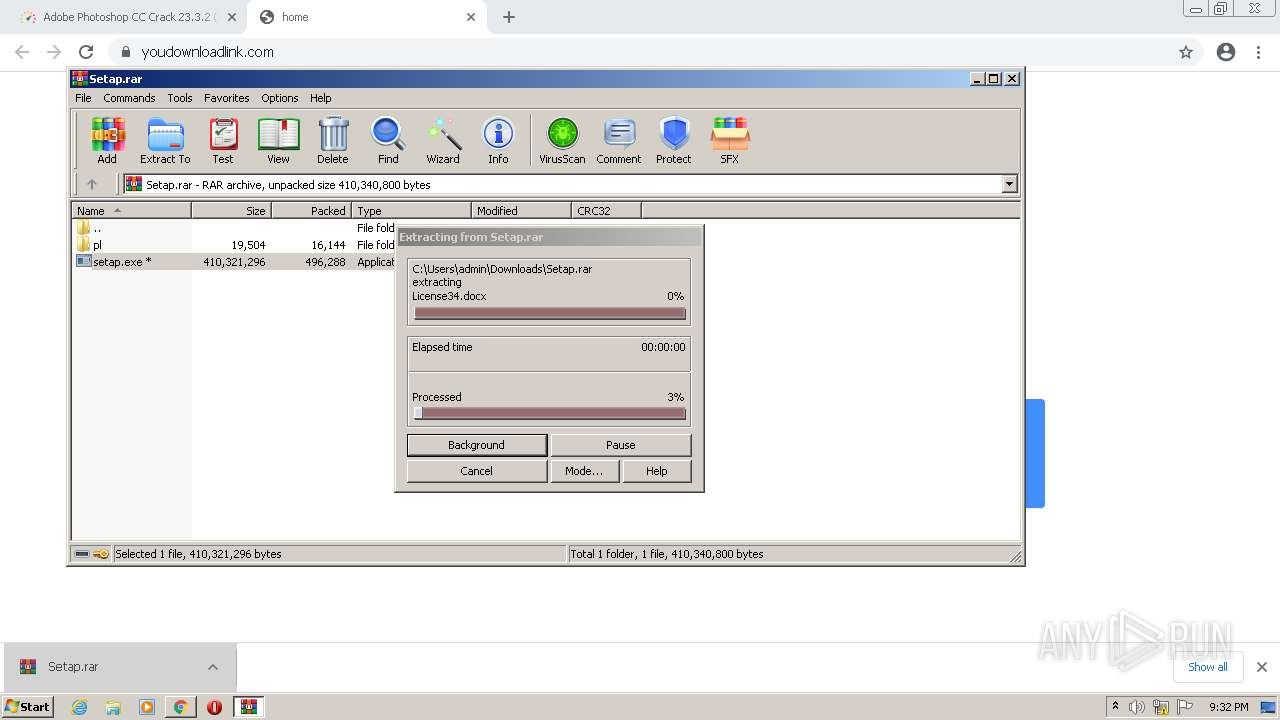
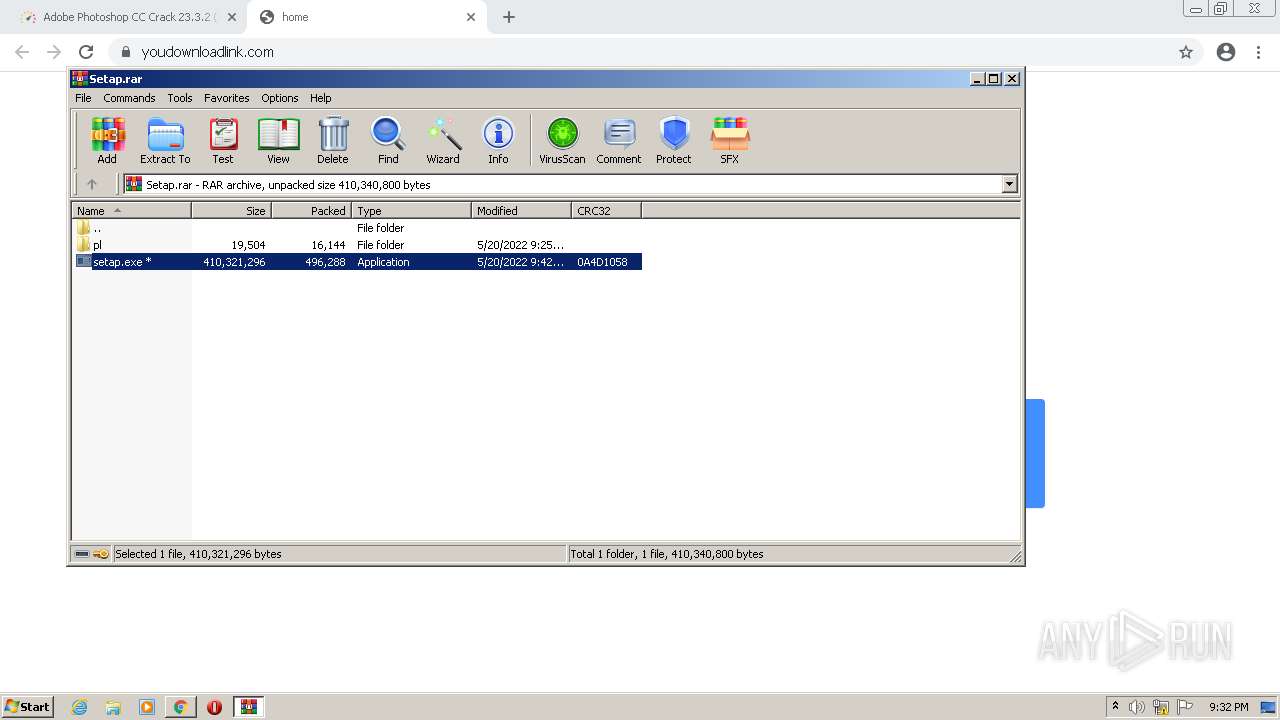
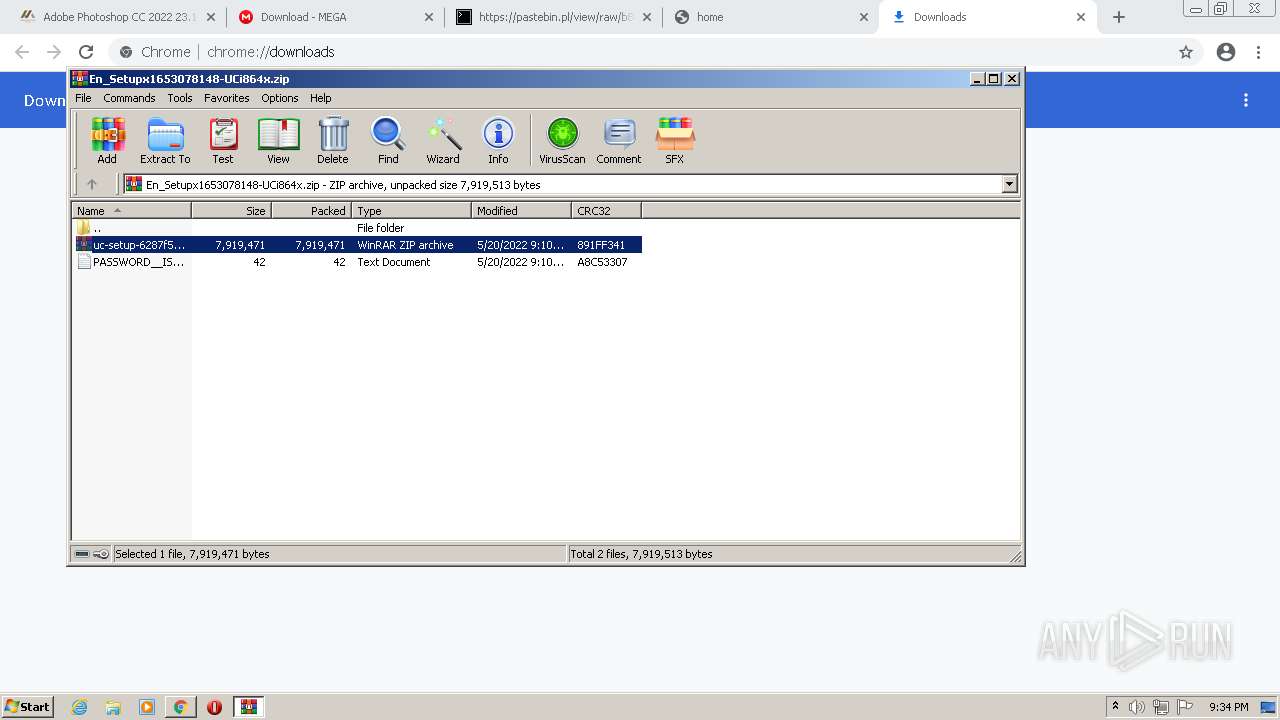
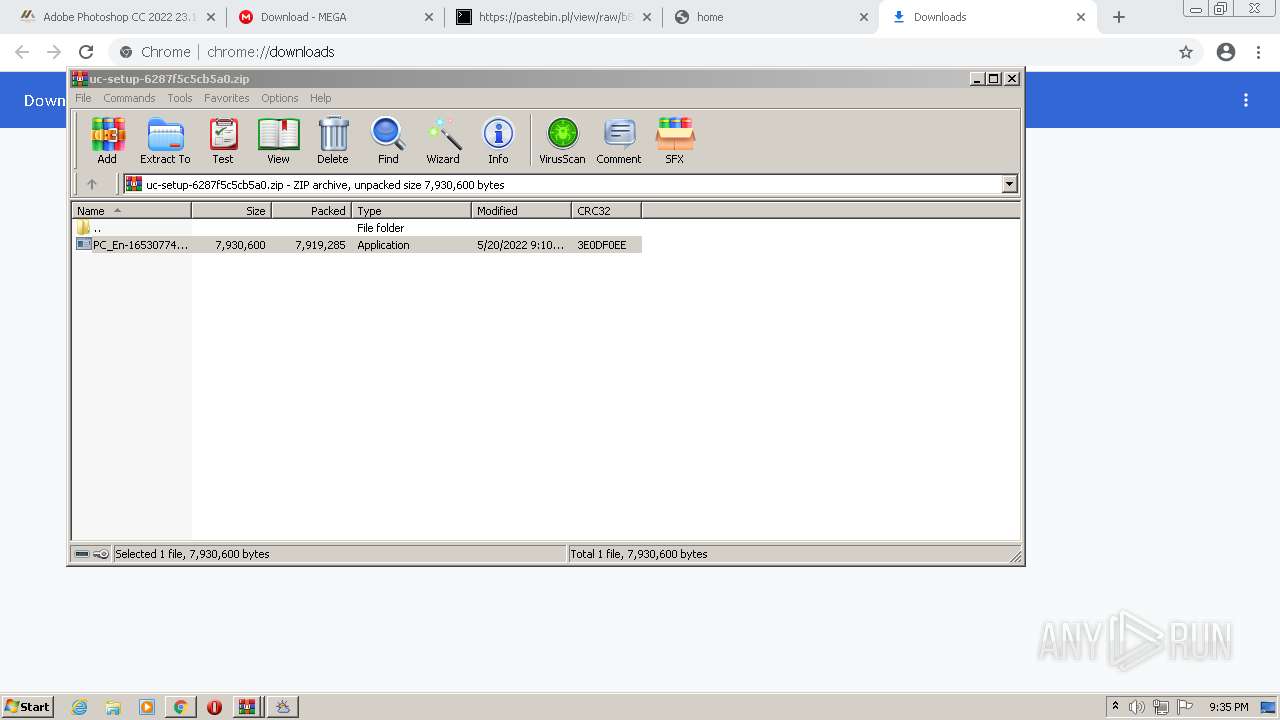
MALICIOUS
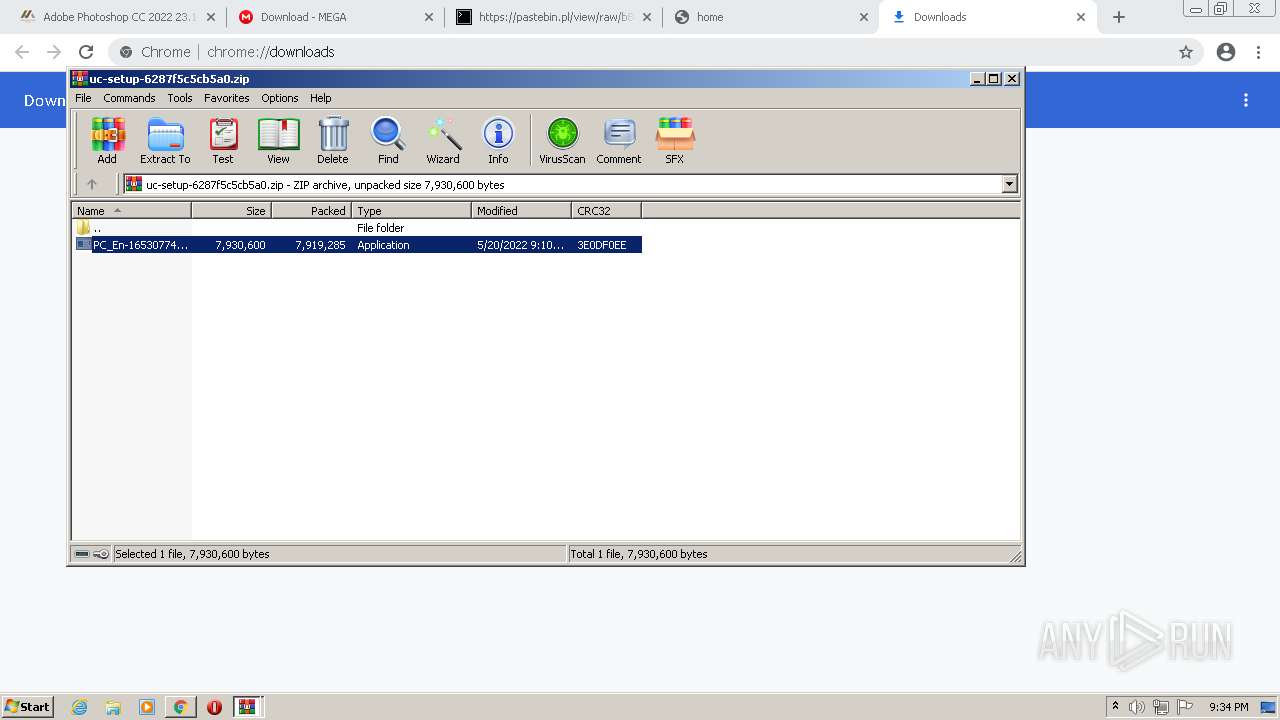
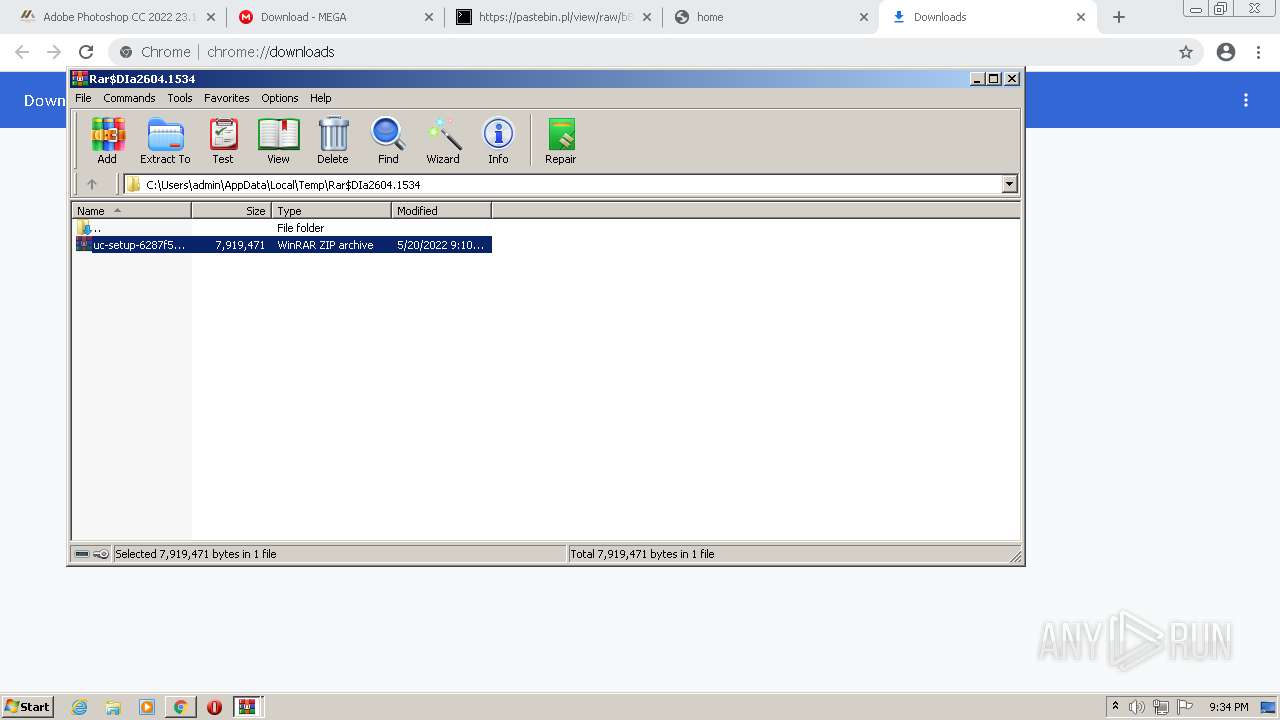
Drops executable file immediately after starts
- chrome.exe (PID: 3224)
- setup_installer.exe (PID: 1040)
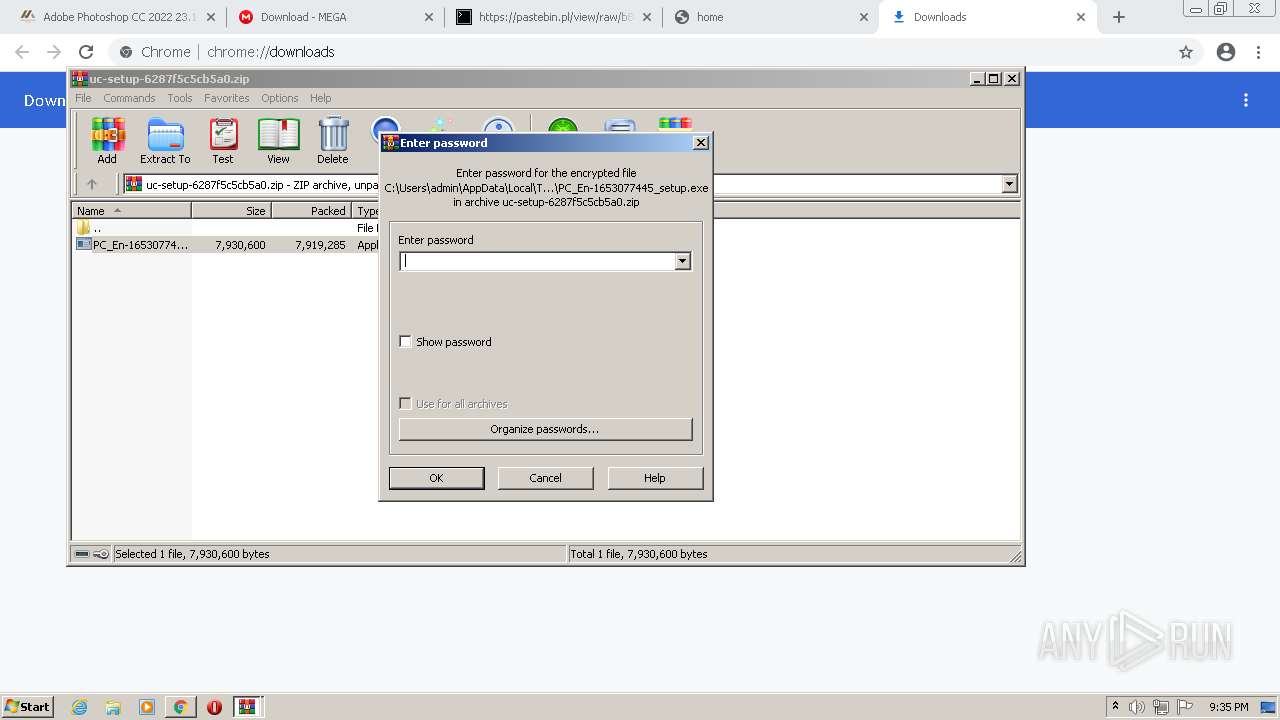
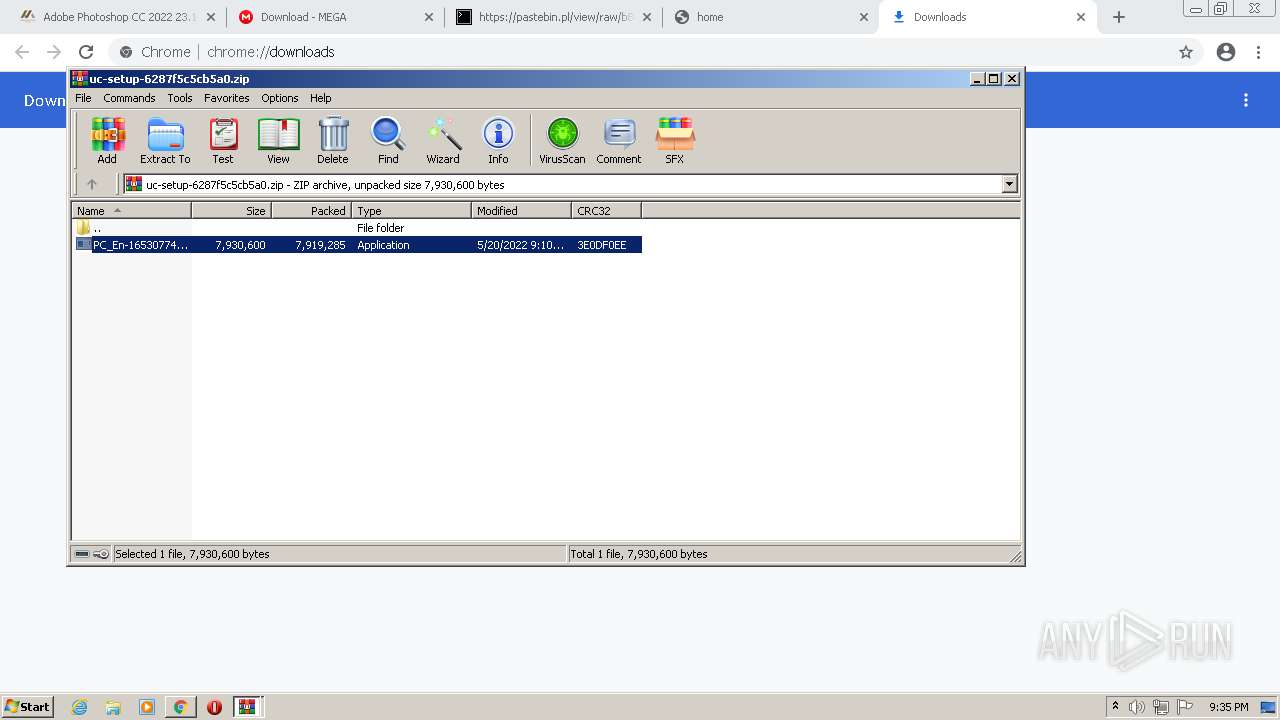
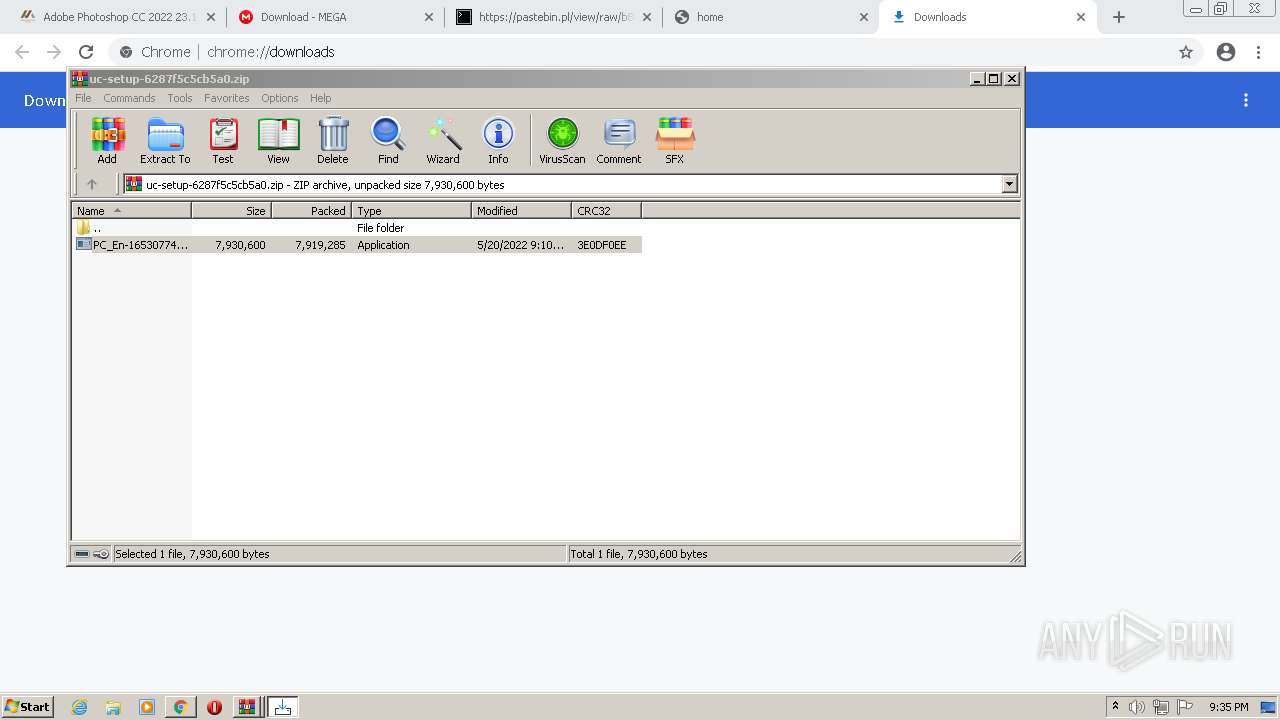
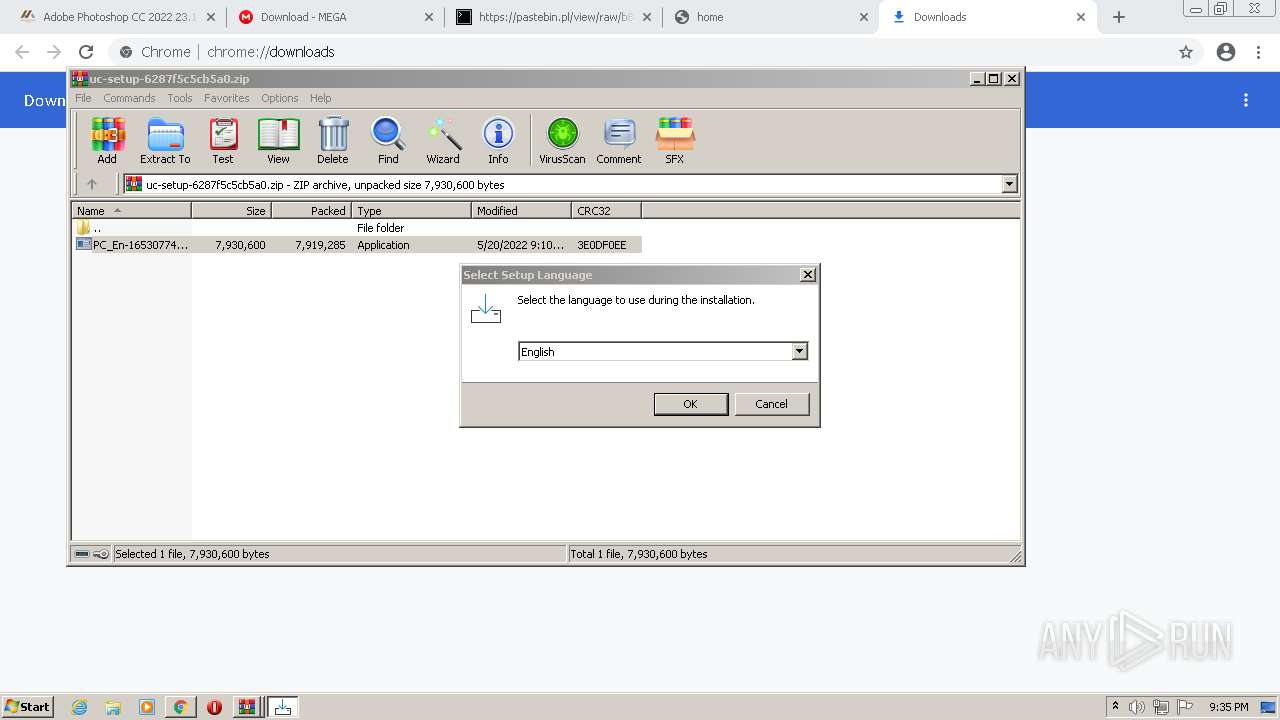
- PC_En-1653077445_setup.exe (PID: 2380)
- WinRAR.exe (PID: 2760)
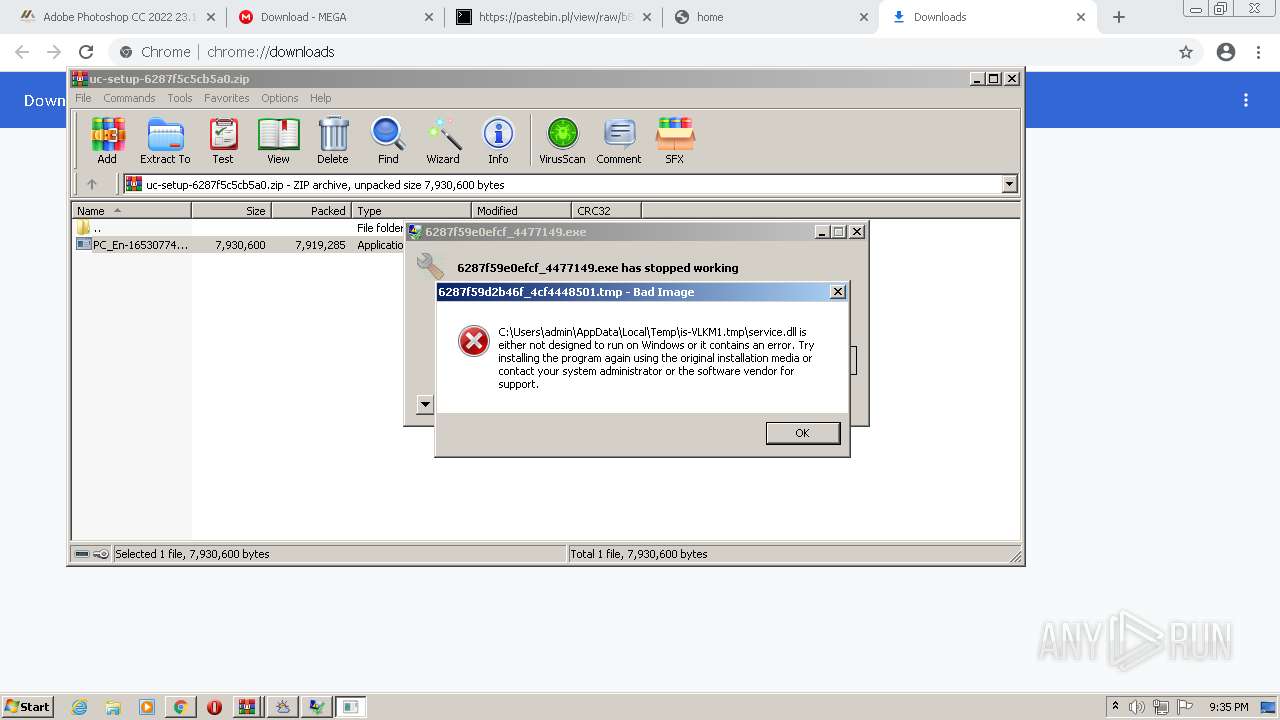
- 6287f59d2b46f_4cf4448501.exe (PID: 3920)
- 6287f5bd026e4_7412125.exe (PID: 3296)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- 6287f59d2b46f_4cf4448501.exe (PID: 3624)
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- 6287f5bbde3df_8d6393c.exe (PID: 3436)
- lBo5.exe (PID: 2704)
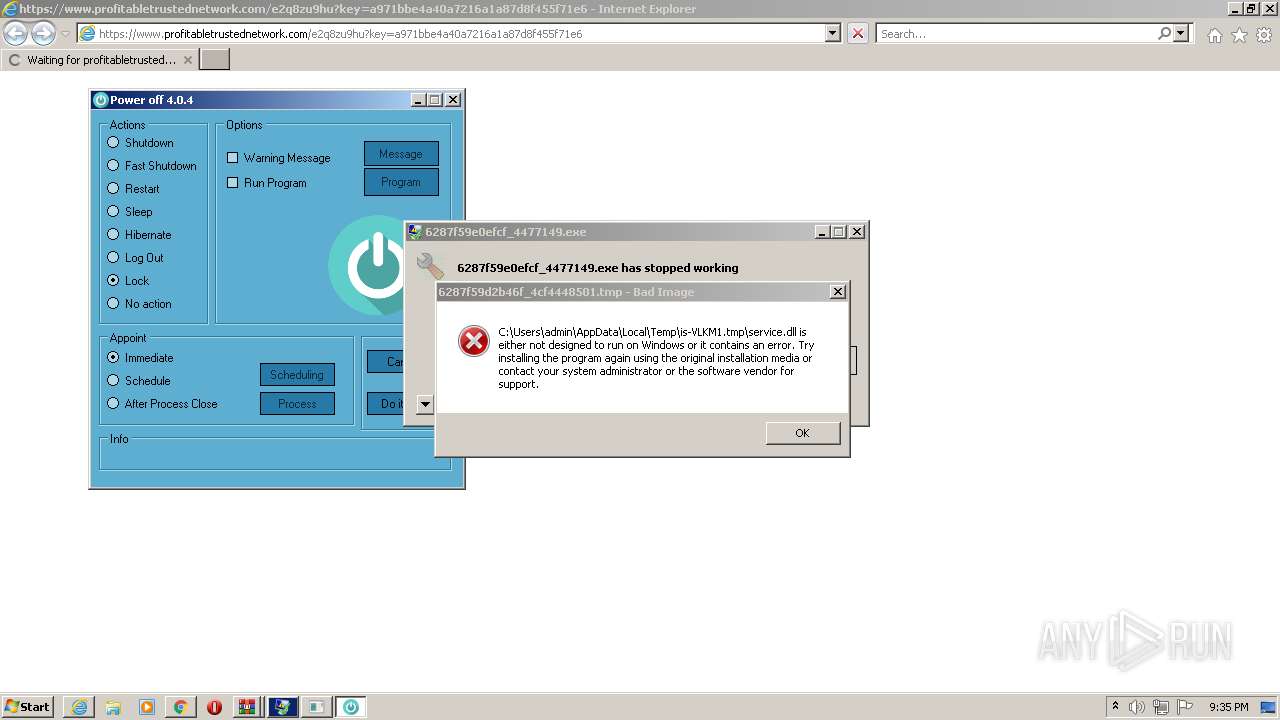
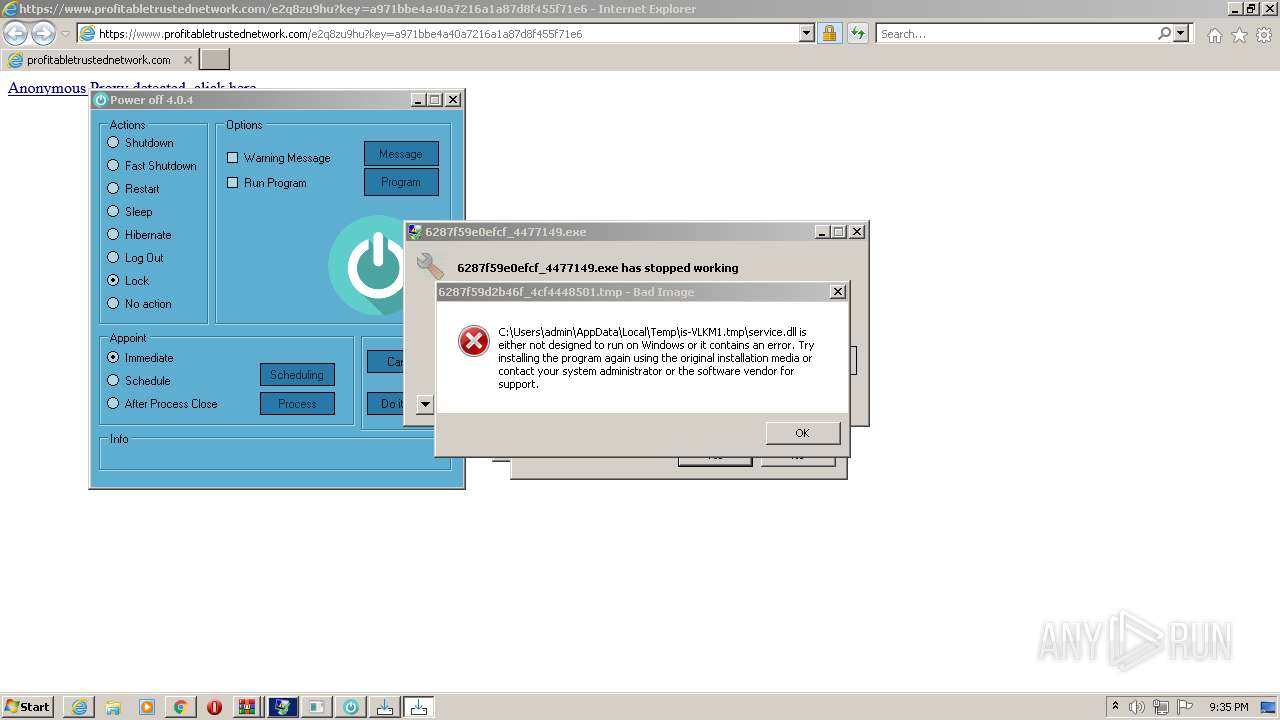
- poweroff.exe (PID: 1164)
- poweroff.tmp (PID: 2024)
- Vaeshaelomuve.exe (PID: 3124)
- N5KMZ9Gsim.exe (PID: 3484)
- BEXAe3Mo0P.exe (PID: 768)
- 6287f5a3051ac_4c9035c4.exe (PID: 1396)
- 161.exe (PID: 3892)
- 161.tmp (PID: 680)
- installer.exe (PID: 1992)
- tapinstall.exe (PID: 2040)
- DrvInst.exe (PID: 2116)
- msiexec.exe (PID: 2928)
- yNMGD.exe (PID: 3632)
- chrome.exe (PID: 2400)
Application was dropped or rewritten from another process
- PC_En-1653077445_setup.exe (PID: 3356)
- PC_En-1653077445_setup.exe (PID: 2380)
- setup_installer.exe (PID: 1040)
- 6287f5bbde3df_8d6393c.exe (PID: 3436)
- setup_install.exe (PID: 920)
- 6287f5bd026e4_7412125.exe (PID: 3296)
- 6287f5a3051ac_4c9035c4.exe (PID: 1396)
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- 6287f5a5bc5c5_3b0454.exe (PID: 3768)
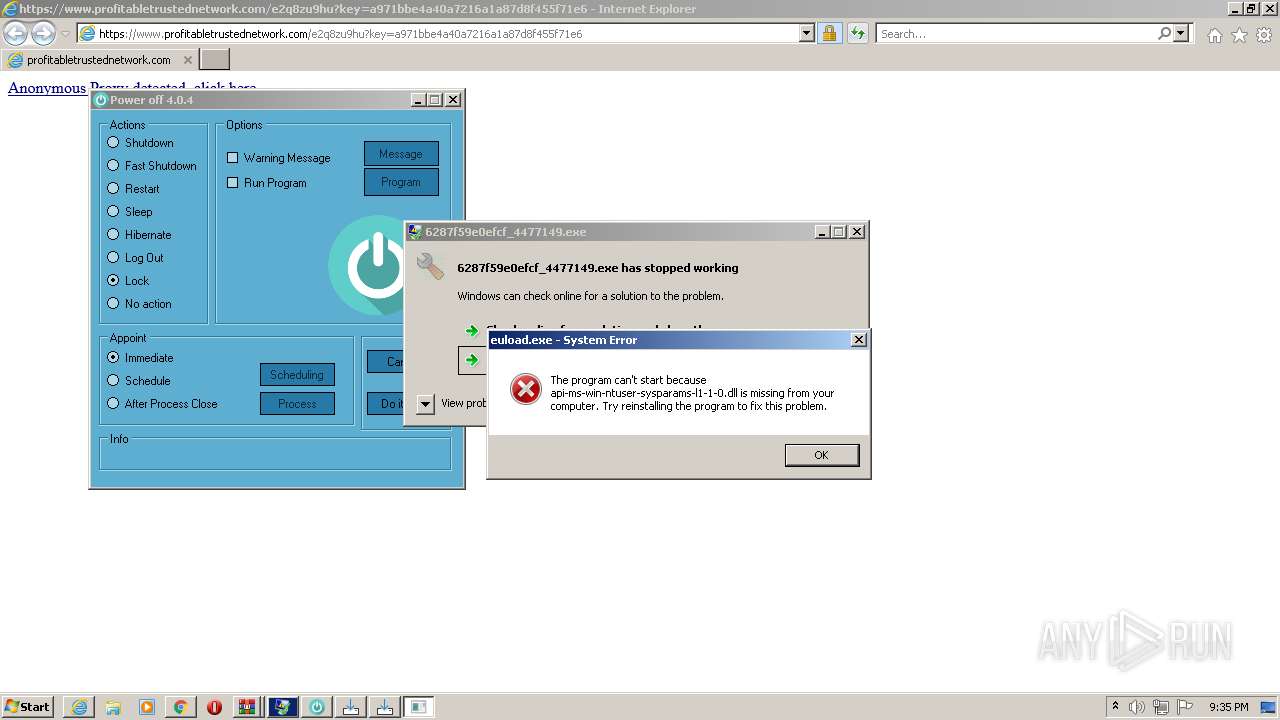
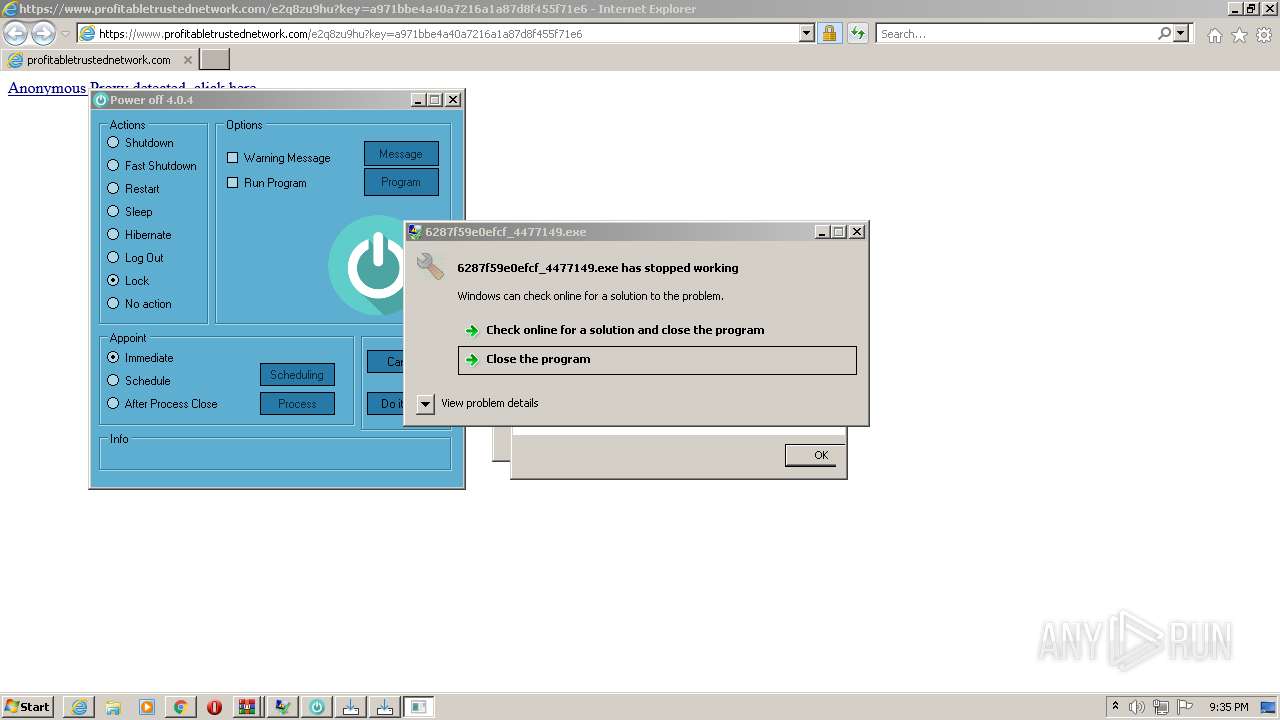
- 6287f59e0efcf_4477149.exe (PID: 3744)
- 6287f59b040e8_1fe17aaeae.exe (PID: 3264)
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- 6287f59bb75e4_d750e42fc1.exe (PID: 348)
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- 6287f5a19fe91_40ddf90.exe (PID: 3188)
- 6287f59d2b46f_4cf4448501.exe (PID: 3920)
- 6287f59d2b46f_4cf4448501.exe (PID: 3624)
- 6287f5a5bc5c5_3b0454.exe (PID: 2384)
- yNMGD.exe (PID: 3632)
- N5KMZ9Gsim.exe (PID: 3484)
- Tabadekuhi.exe (PID: 3904)
- Vaeshaelomuve.exe (PID: 3124)
- poweroff.exe (PID: 1164)
- 5927335832.exe (PID: 1972)
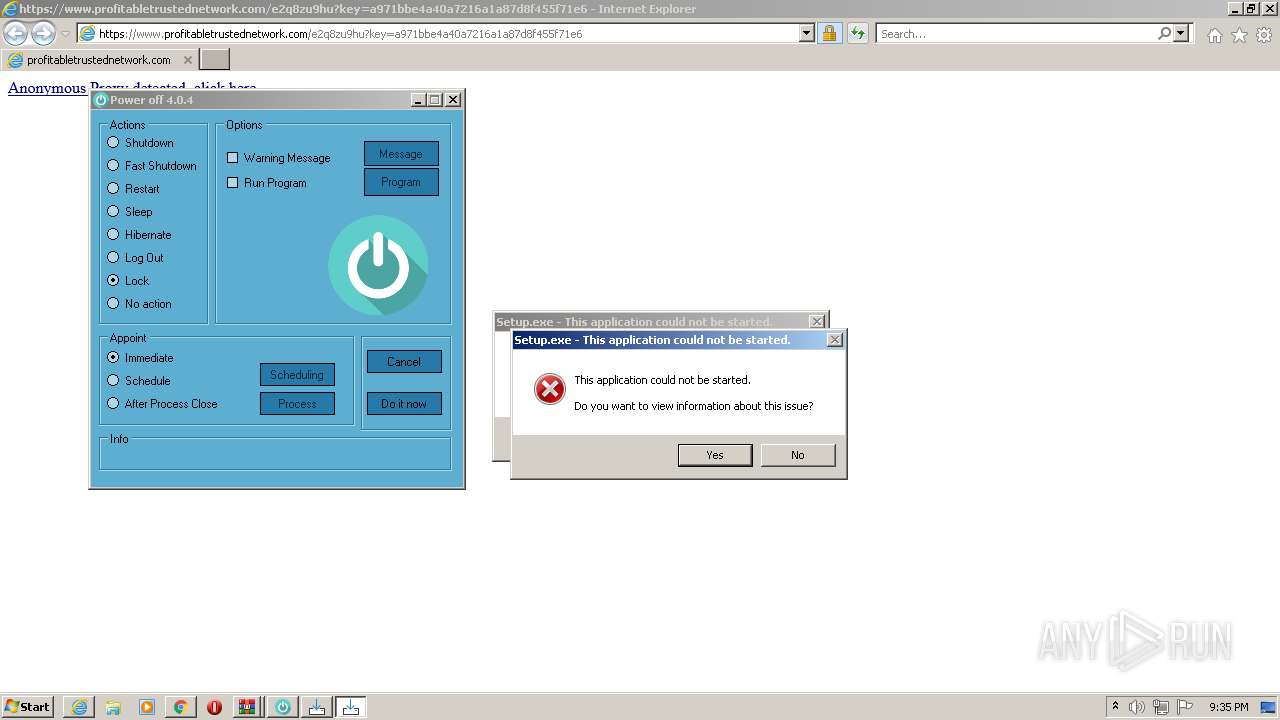
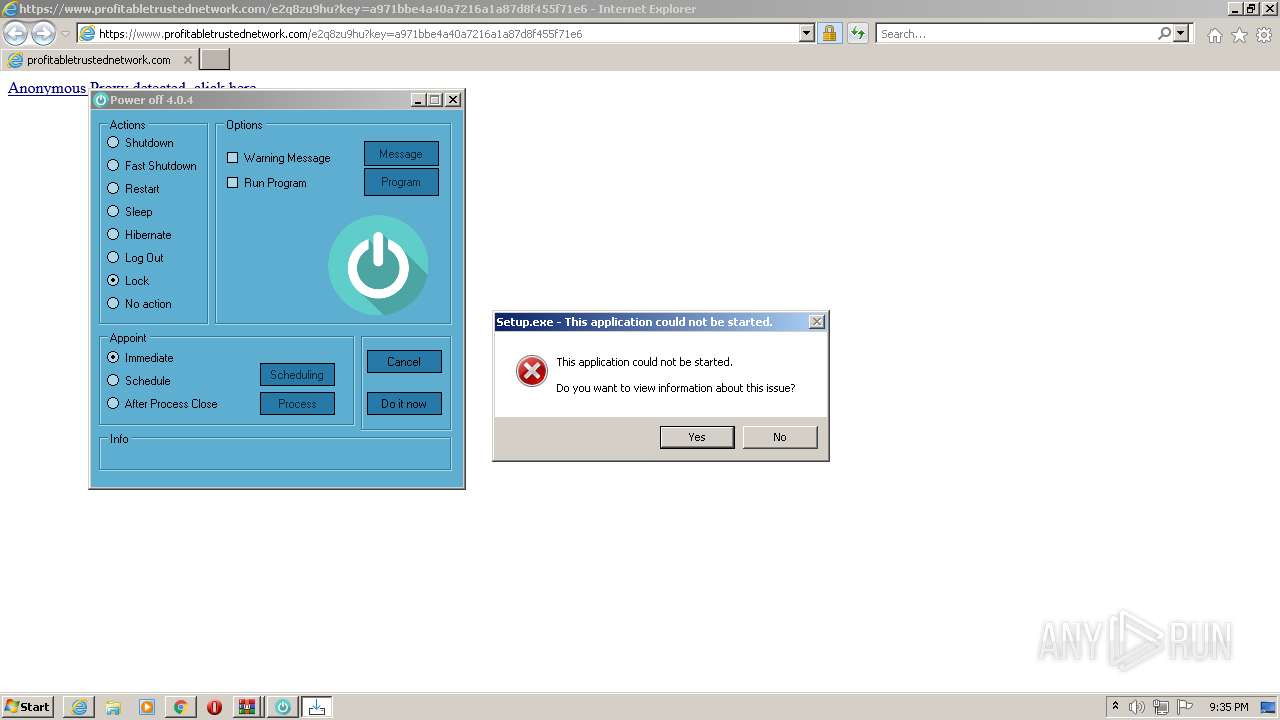
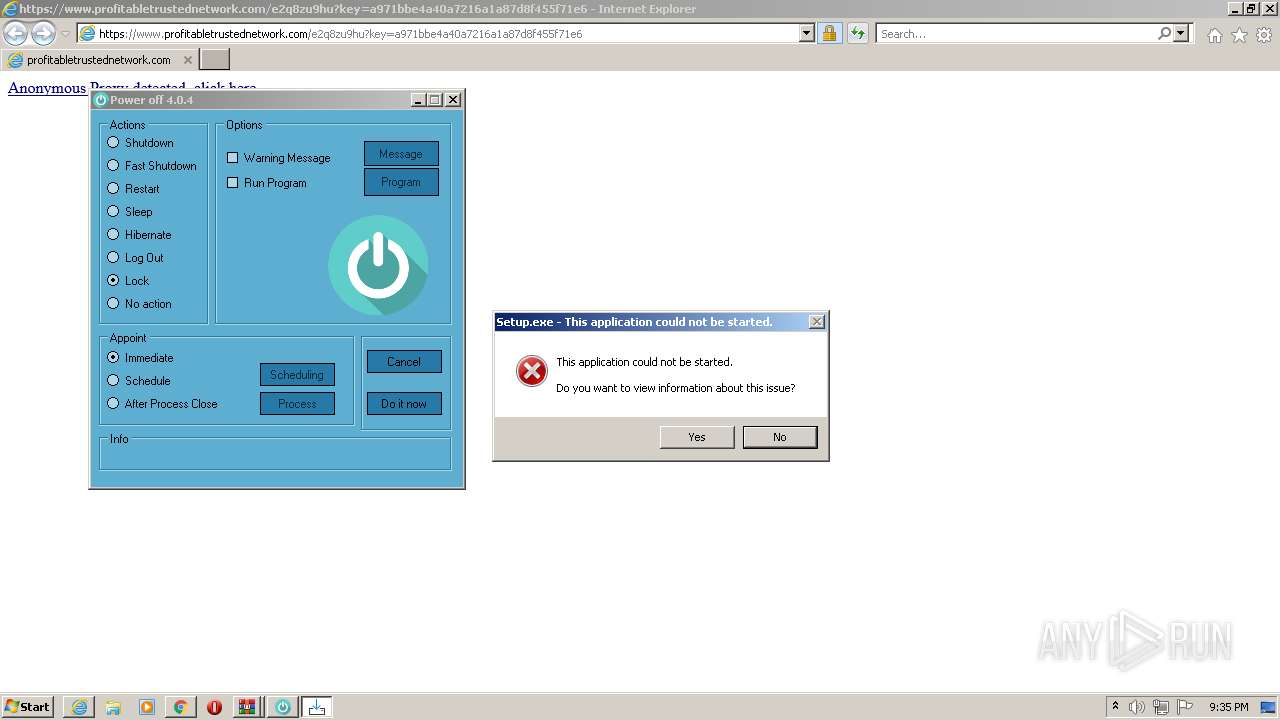
- Setup.exe (PID: 1820)
- Setup.exe (PID: 3704)
- 5927335832.exe (PID: 292)
- BEXAe3Mo0P.exe (PID: 768)
- euload.exe (PID: 3436)
- Power Off.exe (PID: 2528)
- strongix.exe (PID: 340)
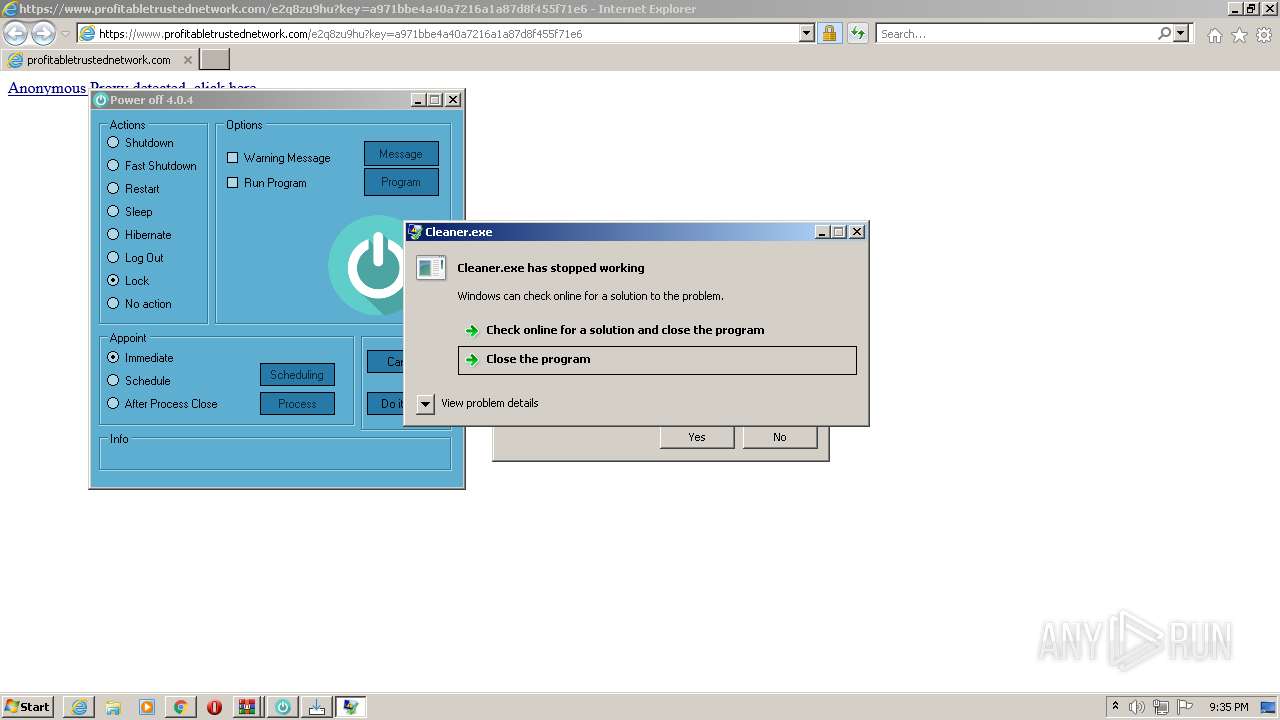
- Cleaner.exe (PID: 3248)
- 161.exe (PID: 3892)
- GcleanerEU.exe (PID: 2792)
- gcleaner.exe (PID: 1044)
- installer.exe (PID: 1992)
- random.exe (PID: 2920)
- random.exe (PID: 2872)
- Adamerax.exe (PID: 2572)
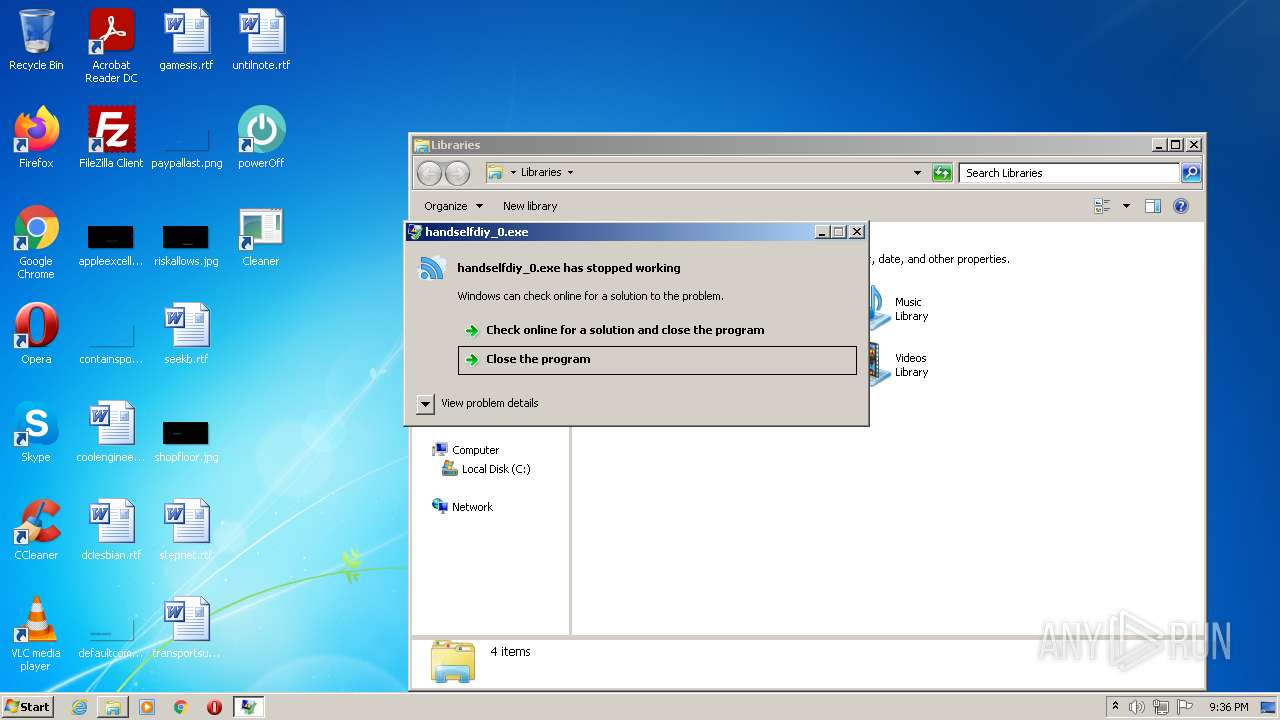
- handselfdiy_0.exe (PID: 3236)
- tapinstall.exe (PID: 3436)
- tapinstall.exe (PID: 2040)
- chrome.exe (PID: 2400)
- b123.exe (PID: 2920)
- mask_svc.exe (PID: 4620)
- installer.exe (PID: 340)
- mask_svc.exe (PID: 3744)
- mask_svc.exe (PID: 4712)
- Qadddgh25r.exe (PID: 5480)
Executes PowerShell scripts
- cmd.exe (PID: 3152)
Actions looks like stealing of personal data
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 1248)
- strongix.exe (PID: 340)
- b123.exe (PID: 2920)
- yNMGD.exe (PID: 3632)
Loads dropped or rewritten executable
- setup_install.exe (PID: 920)
- rundll32.exe (PID: 1636)
- Cleaner.exe (PID: 3248)
- installer.exe (PID: 1992)
- yNMGD.exe (PID: 3632)
- b123.exe (PID: 2920)
- mask_svc.exe (PID: 4712)
Stealing of credential data
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
Changes settings of System certificates
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- 161.tmp (PID: 680)
- installer.exe (PID: 1992)
- Vaeshaelomuve.exe (PID: 3124)
Steals credentials from Web Browsers
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- strongix.exe (PID: 340)
- yNMGD.exe (PID: 3632)
- b123.exe (PID: 2920)
Connects to CnC server
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- 6287f5bbde3df_8d6393c.exe (PID: 3436)
- strongix.exe (PID: 340)
- yNMGD.exe (PID: 3632)
REDLINE detected by memory dumps
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
REDLINE was detected
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- strongix.exe (PID: 340)
Runs injected code in another process
- rundll32.exe (PID: 1636)
- rundll32.exe (PID: 452)
Application was injected by another process
- svchost.exe (PID: 868)
Changes the autorun value in the registry
- lBo5.exe (PID: 2704)
- DrvInst.exe (PID: 5600)
- chrome.exe (PID: 2400)
- svchost.exe (PID: 868)
Loads the Task Scheduler DLL interface
- 5927335832.exe (PID: 1972)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 268)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2040)
- MsiExec.exe (PID: 3384)
- installer.exe (PID: 1992)
SYSTEMBC detected by memory dumps
- 5927335832.exe (PID: 1972)
- 5927335832.exe (PID: 292)
ARKEI was detected
- yNMGD.exe (PID: 3632)
SUSPICIOUS
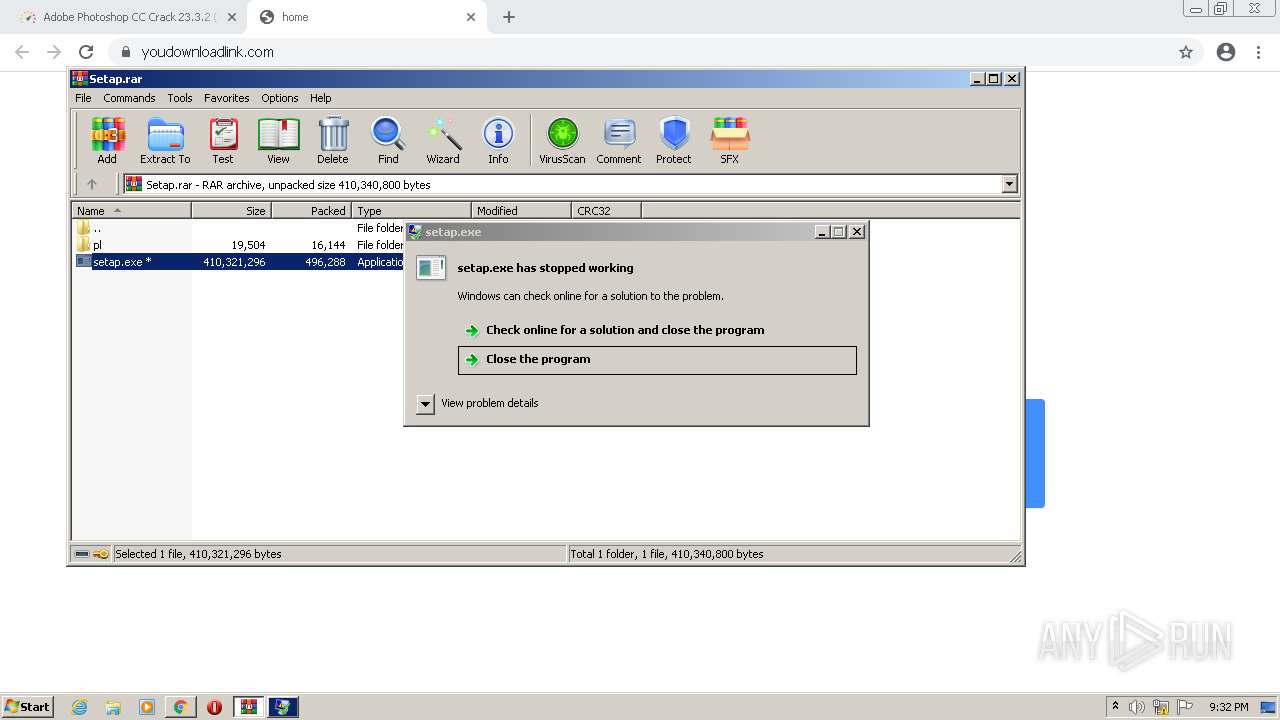
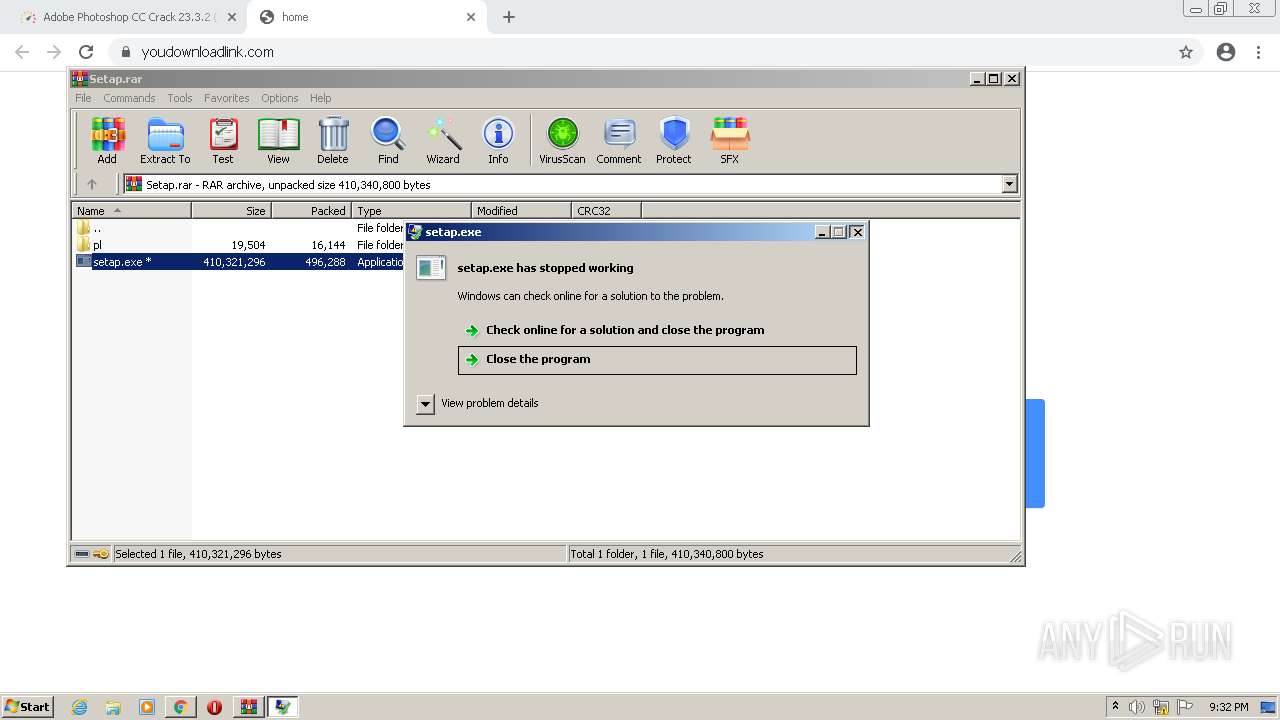
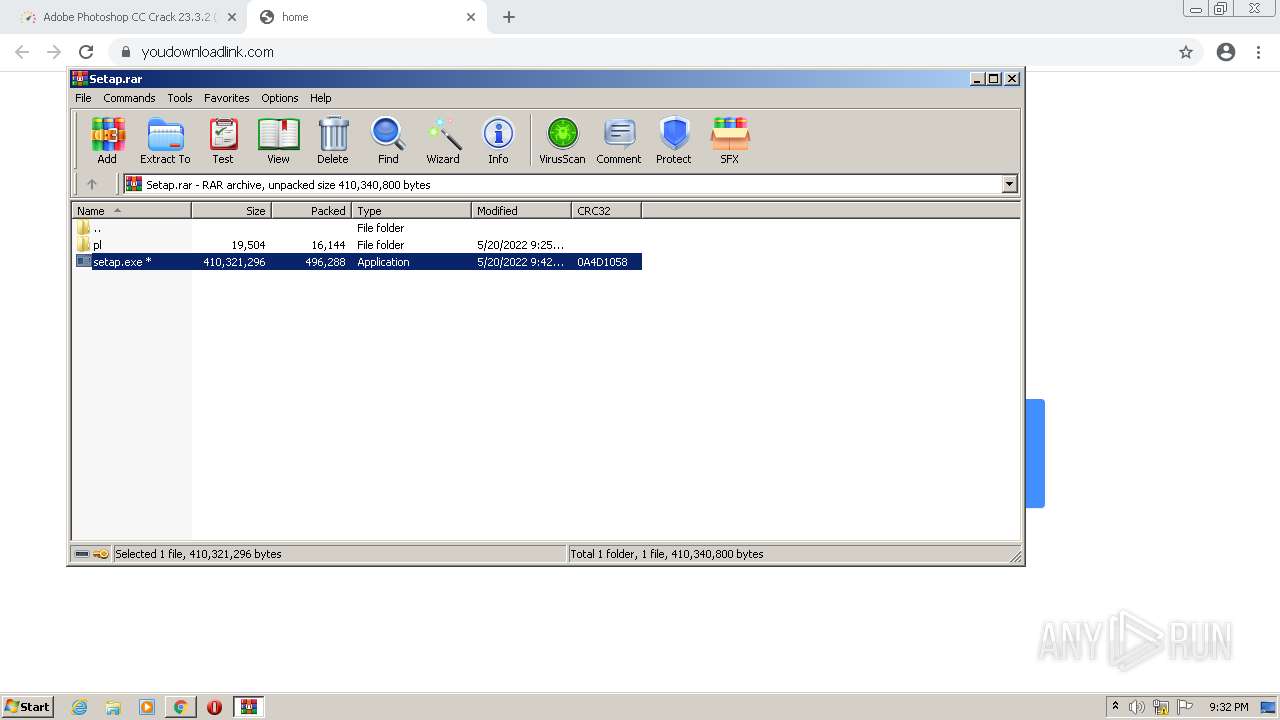
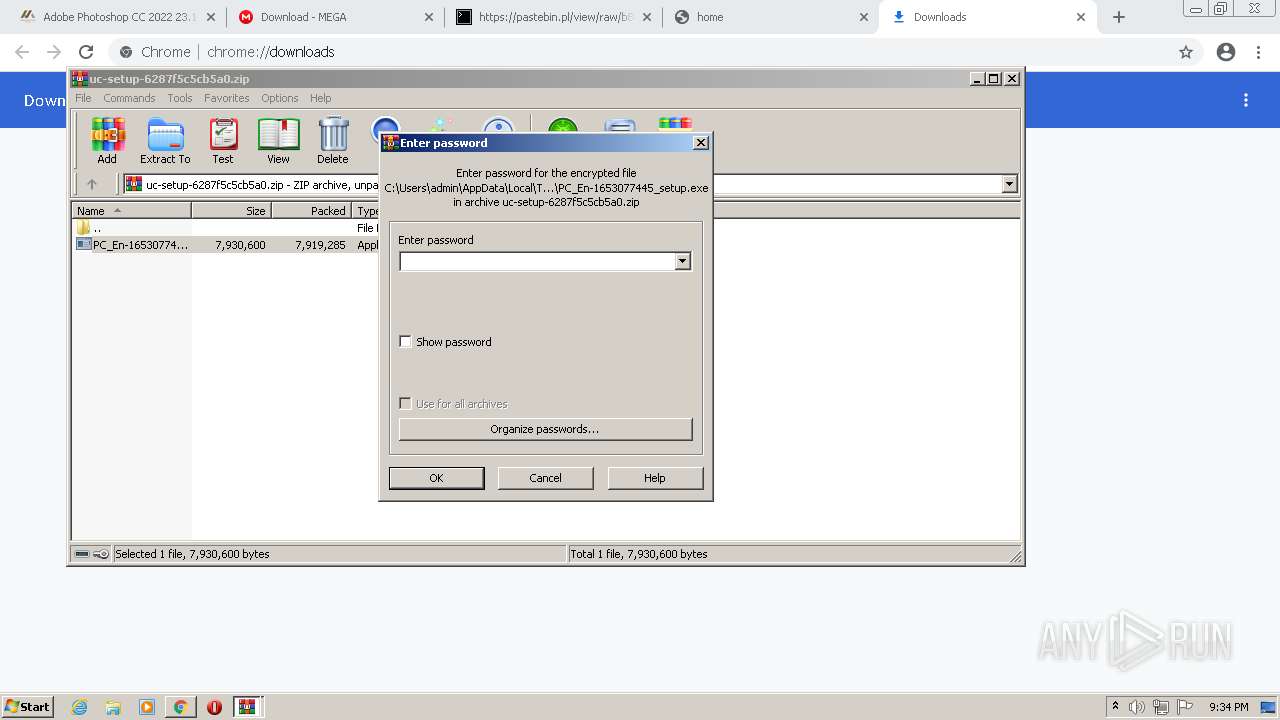
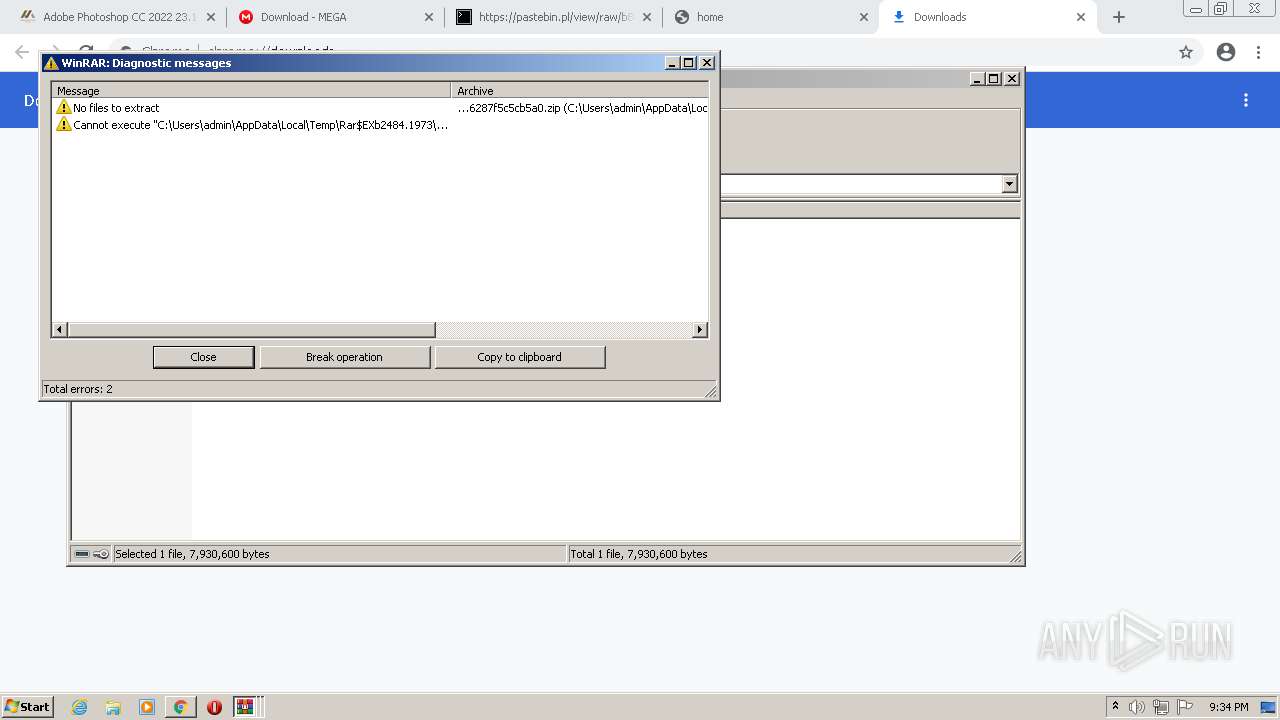
Checks supported languages
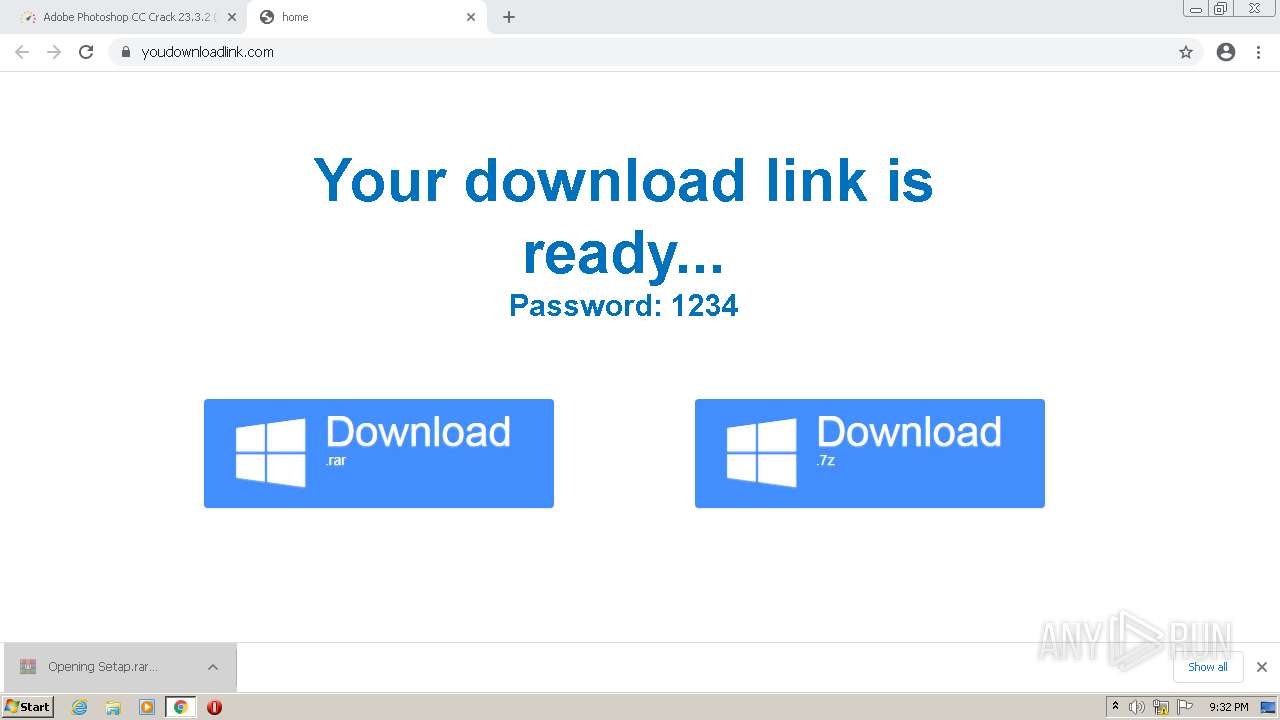
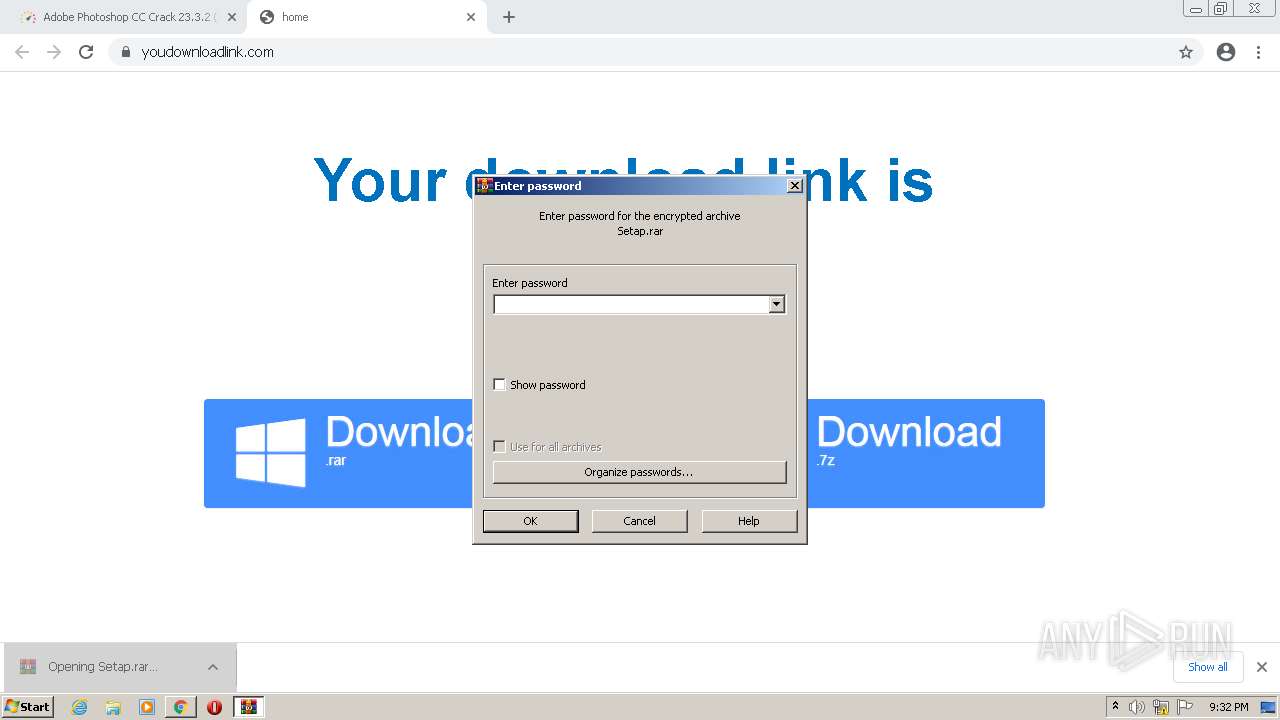
- WinRAR.exe (PID: 2864)
- setap.exe (PID: 3744)
- WinRAR.exe (PID: 2484)
- WinRAR.exe (PID: 2604)
- WinRAR.exe (PID: 2760)
- PC_En-1653077445_setup.exe (PID: 2380)
- setup_installer.exe (PID: 1040)
- setup_install.exe (PID: 920)
- cmd.exe (PID: 1440)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 3152)
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- cmd.exe (PID: 3980)
- powershell.exe (PID: 2068)
- 6287f59bb75e4_d750e42fc1.exe (PID: 348)
- 6287f59b040e8_1fe17aaeae.exe (PID: 3264)
- cmd.exe (PID: 680)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- cmd.exe (PID: 3892)
- 6287f59d2b46f_4cf4448501.exe (PID: 3920)
- 6287f59e0efcf_4477149.exe (PID: 3744)
- 6287f5a19fe91_40ddf90.exe (PID: 3188)
- 6287f5a3051ac_4c9035c4.exe (PID: 1396)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 3880)
- 6287f5a5bc5c5_3b0454.exe (PID: 3768)
- 6287f5bd026e4_7412125.exe (PID: 3296)
- cmd.exe (PID: 2964)
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- cmd.exe (PID: 768)
- cmd.exe (PID: 2460)
- 6287f5bbde3df_8d6393c.exe (PID: 3436)
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.exe (PID: 3624)
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- lBo5.exe (PID: 2704)
- 6287f5a5bc5c5_3b0454.exe (PID: 2384)
- yNMGD.exe (PID: 3632)
- Tabadekuhi.exe (PID: 3904)
- Vaeshaelomuve.exe (PID: 3124)
- poweroff.exe (PID: 1164)
- poweroff.tmp (PID: 2024)
- Power Off.exe (PID: 2528)
- cmd.exe (PID: 3032)
- N5KMZ9Gsim.exe (PID: 3484)
- cmd.exe (PID: 3700)
- Setup.exe (PID: 3704)
- cmd.exe (PID: 696)
- 5927335832.exe (PID: 1972)
- cmd.exe (PID: 1248)
- Setup.exe (PID: 1820)
- BEXAe3Mo0P.exe (PID: 768)
- 5927335832.exe (PID: 292)
- cmd.exe (PID: 2580)
- cmd.exe (PID: 268)
- strongix.exe (PID: 340)
- cmd.exe (PID: 2448)
- Cleaner.exe (PID: 3248)
- cmd.exe (PID: 3472)
- 161.exe (PID: 3892)
- cmd.exe (PID: 2360)
- 161.tmp (PID: 680)
- cmd.exe (PID: 2496)
- installer.exe (PID: 1992)
- tapinstall.exe (PID: 3436)
- cmd.exe (PID: 3096)
- GcleanerEU.exe (PID: 2792)
- cmd.exe (PID: 2168)
- tapinstall.exe (PID: 2040)
- cmd.exe (PID: 768)
- gcleaner.exe (PID: 1044)
- msiexec.exe (PID: 2928)
- MsiExec.exe (PID: 2640)
- cmd.exe (PID: 2776)
- DrvInst.exe (PID: 2116)
- MsiExec.exe (PID: 4088)
- cmd.exe (PID: 2300)
- random.exe (PID: 2872)
- random.exe (PID: 2920)
- MsiExec.exe (PID: 3384)
- handselfdiy_0.exe (PID: 3236)
- Adamerax.exe (PID: 2572)
- cmd.exe (PID: 2704)
- chrome.exe (PID: 2400)
- cmd.exe (PID: 1440)
- cmd.exe (PID: 3916)
- b123.exe (PID: 2920)
- cmd.exe (PID: 4324)
- cmd.exe (PID: 4692)
- DrvInst.exe (PID: 5600)
- cmd.exe (PID: 2472)
- cmd.exe (PID: 4520)
- installer.exe (PID: 340)
- cmd.exe (PID: 5152)
- mask_svc.exe (PID: 4620)
- mask_svc.exe (PID: 3744)
- mask_svc.exe (PID: 4712)
- Qadddgh25r.exe (PID: 5480)
- InstallUtil.exe (PID: 4640)
Reads the computer name
- WinRAR.exe (PID: 2864)
- setap.exe (PID: 3744)
- WinRAR.exe (PID: 2604)
- WinRAR.exe (PID: 2484)
- PC_En-1653077445_setup.exe (PID: 2380)
- WinRAR.exe (PID: 2760)
- setup_installer.exe (PID: 1040)
- powershell.exe (PID: 2068)
- 6287f59b040e8_1fe17aaeae.exe (PID: 3264)
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- 6287f59bb75e4_d750e42fc1.exe (PID: 348)
- 6287f5a19fe91_40ddf90.exe (PID: 3188)
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- 6287f5a3051ac_4c9035c4.exe (PID: 1396)
- 6287f5bbde3df_8d6393c.exe (PID: 3436)
- lBo5.exe (PID: 2704)
- Tabadekuhi.exe (PID: 3904)
- Vaeshaelomuve.exe (PID: 3124)
- poweroff.tmp (PID: 2024)
- 5927335832.exe (PID: 1972)
- Setup.exe (PID: 3704)
- Setup.exe (PID: 1820)
- 5927335832.exe (PID: 292)
- N5KMZ9Gsim.exe (PID: 3484)
- BEXAe3Mo0P.exe (PID: 768)
- Cleaner.exe (PID: 3248)
- 161.tmp (PID: 680)
- installer.exe (PID: 1992)
- strongix.exe (PID: 340)
- tapinstall.exe (PID: 3436)
- msiexec.exe (PID: 2928)
- tapinstall.exe (PID: 2040)
- MsiExec.exe (PID: 2640)
- DrvInst.exe (PID: 2116)
- MsiExec.exe (PID: 4088)
- random.exe (PID: 2872)
- random.exe (PID: 2920)
- Power Off.exe (PID: 2528)
- MsiExec.exe (PID: 3384)
- handselfdiy_0.exe (PID: 3236)
- yNMGD.exe (PID: 3632)
- chrome.exe (PID: 2400)
- b123.exe (PID: 2920)
- GcleanerEU.exe (PID: 2792)
- DrvInst.exe (PID: 5600)
- gcleaner.exe (PID: 1044)
- installer.exe (PID: 340)
- mask_svc.exe (PID: 4620)
- mask_svc.exe (PID: 3744)
- mask_svc.exe (PID: 4712)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3288)
Executable content was dropped or overwritten
- chrome.exe (PID: 3224)
- WinRAR.exe (PID: 2760)
- PC_En-1653077445_setup.exe (PID: 2380)
- setup_installer.exe (PID: 1040)
- 6287f59d2b46f_4cf4448501.exe (PID: 3920)
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- 6287f59d2b46f_4cf4448501.exe (PID: 3624)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- 6287f5a3051ac_4c9035c4.exe (PID: 1396)
- lBo5.exe (PID: 2704)
- 6287f5bbde3df_8d6393c.exe (PID: 3436)
- 6287f5bd026e4_7412125.exe (PID: 3296)
- poweroff.exe (PID: 1164)
- poweroff.tmp (PID: 2024)
- Vaeshaelomuve.exe (PID: 3124)
- N5KMZ9Gsim.exe (PID: 3484)
- BEXAe3Mo0P.exe (PID: 768)
- 161.exe (PID: 3892)
- 161.tmp (PID: 680)
- installer.exe (PID: 1992)
- tapinstall.exe (PID: 2040)
- DrvInst.exe (PID: 2116)
- yNMGD.exe (PID: 3632)
- chrome.exe (PID: 2400)
- msiexec.exe (PID: 2928)
Drops a file with a compile date too recent
- chrome.exe (PID: 3224)
- WinRAR.exe (PID: 2760)
- PC_En-1653077445_setup.exe (PID: 2380)
- setup_installer.exe (PID: 1040)
- 6287f59d2b46f_4cf4448501.exe (PID: 3920)
- 6287f5bd026e4_7412125.exe (PID: 3296)
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- 6287f59d2b46f_4cf4448501.exe (PID: 3624)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- 6287f5bbde3df_8d6393c.exe (PID: 3436)
- lBo5.exe (PID: 2704)
- poweroff.exe (PID: 1164)
- poweroff.tmp (PID: 2024)
- Vaeshaelomuve.exe (PID: 3124)
- N5KMZ9Gsim.exe (PID: 3484)
- BEXAe3Mo0P.exe (PID: 768)
- 6287f5a3051ac_4c9035c4.exe (PID: 1396)
- 161.exe (PID: 3892)
- 161.tmp (PID: 680)
- installer.exe (PID: 1992)
- tapinstall.exe (PID: 2040)
- DrvInst.exe (PID: 2116)
- msiexec.exe (PID: 2928)
- yNMGD.exe (PID: 3632)
- chrome.exe (PID: 2400)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 1852)
- iexplore.exe (PID: 2968)
Application launched itself
- WinRAR.exe (PID: 2604)
- 6287f59b040e8_1fe17aaeae.exe (PID: 3264)
- 6287f59bb75e4_d750e42fc1.exe (PID: 348)
- 6287f5a5bc5c5_3b0454.exe (PID: 3768)
- random.exe (PID: 2872)
Starts CMD.EXE for commands execution
- setup_install.exe (PID: 920)
- Vaeshaelomuve.exe (PID: 3124)
- 6287f5bbde3df_8d6393c.exe (PID: 3436)
- BEXAe3Mo0P.exe (PID: 768)
- 6287f5a3051ac_4c9035c4.exe (PID: 1396)
- 161.tmp (PID: 680)
- chrome.exe (PID: 2400)
- GcleanerEU.exe (PID: 2792)
- gcleaner.exe (PID: 1044)
Reads Windows owner or organization settings
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- poweroff.tmp (PID: 2024)
- 161.tmp (PID: 680)
- installer.exe (PID: 1992)
- msiexec.exe (PID: 2928)
Reads the Windows organization settings
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- poweroff.tmp (PID: 2024)
- 161.tmp (PID: 680)
- installer.exe (PID: 1992)
- msiexec.exe (PID: 2928)
Loads DLL from Mozilla Firefox
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
Adds / modifies Windows certificates
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- installer.exe (PID: 1992)
- Vaeshaelomuve.exe (PID: 3124)
Executed via WMI
- rundll32.exe (PID: 1636)
- rundll32.exe (PID: 452)
Reads Environment values
- lBo5.exe (PID: 2704)
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- Tabadekuhi.exe (PID: 3904)
- Vaeshaelomuve.exe (PID: 3124)
- N5KMZ9Gsim.exe (PID: 3484)
- BEXAe3Mo0P.exe (PID: 768)
- Cleaner.exe (PID: 3248)
- strongix.exe (PID: 340)
- installer.exe (PID: 1992)
- MsiExec.exe (PID: 2640)
- MsiExec.exe (PID: 4088)
- vssvc.exe (PID: 3168)
- chrome.exe (PID: 2400)
- yNMGD.exe (PID: 3632)
- b123.exe (PID: 2920)
- DrvInst.exe (PID: 5600)
- 161.tmp (PID: 680)
Reads CPU info
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- N5KMZ9Gsim.exe (PID: 3484)
- BEXAe3Mo0P.exe (PID: 768)
- yNMGD.exe (PID: 3632)
- b123.exe (PID: 2920)
Reads the cookies of Mozilla Firefox
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- strongix.exe (PID: 340)
Creates files in the user directory
- 6287f5a3051ac_4c9035c4.exe (PID: 1396)
- N5KMZ9Gsim.exe (PID: 3484)
- BEXAe3Mo0P.exe (PID: 768)
- installer.exe (PID: 1992)
- b123.exe (PID: 2920)
- yNMGD.exe (PID: 3632)
- chrome.exe (PID: 2400)
Searches for installed software
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- 6287f59b040e8_1fe17aaeae.exe (PID: 2992)
- BEXAe3Mo0P.exe (PID: 768)
- strongix.exe (PID: 340)
- b123.exe (PID: 2920)
- yNMGD.exe (PID: 3632)
Starts Internet Explorer
- Tabadekuhi.exe (PID: 3904)
Creates a directory in Program Files
- lBo5.exe (PID: 2704)
- poweroff.tmp (PID: 2024)
- 161.tmp (PID: 680)
- msiexec.exe (PID: 2928)
Creates files in the Windows directory
- 5927335832.exe (PID: 1972)
- svchost.exe (PID: 868)
- DrvInst.exe (PID: 2116)
- DrvInst.exe (PID: 5600)
- Vaeshaelomuve.exe (PID: 3124)
Creates files in the program directory
- svchost.exe (PID: 868)
- yNMGD.exe (PID: 3632)
- b123.exe (PID: 2920)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 696)
- cmd.exe (PID: 3472)
- MsiExec.exe (PID: 4088)
- cmd.exe (PID: 2472)
- cmd.exe (PID: 5152)
Executed via Task Scheduler
- 5927335832.exe (PID: 292)
- Adamerax.exe (PID: 2572)
Executed via COM
- DrvInst.exe (PID: 2116)
- DrvInst.exe (PID: 5600)
Check for Java to be installed
- MsiExec.exe (PID: 2640)
- MsiExec.exe (PID: 4088)
Creates files in the driver directory
- DrvInst.exe (PID: 2116)
- DrvInst.exe (PID: 5600)
Removes files from Windows directory
- DrvInst.exe (PID: 2116)
- DrvInst.exe (PID: 5600)
Executed as Windows Service
- vssvc.exe (PID: 3168)
- mask_svc.exe (PID: 4712)
Starts Microsoft Installer
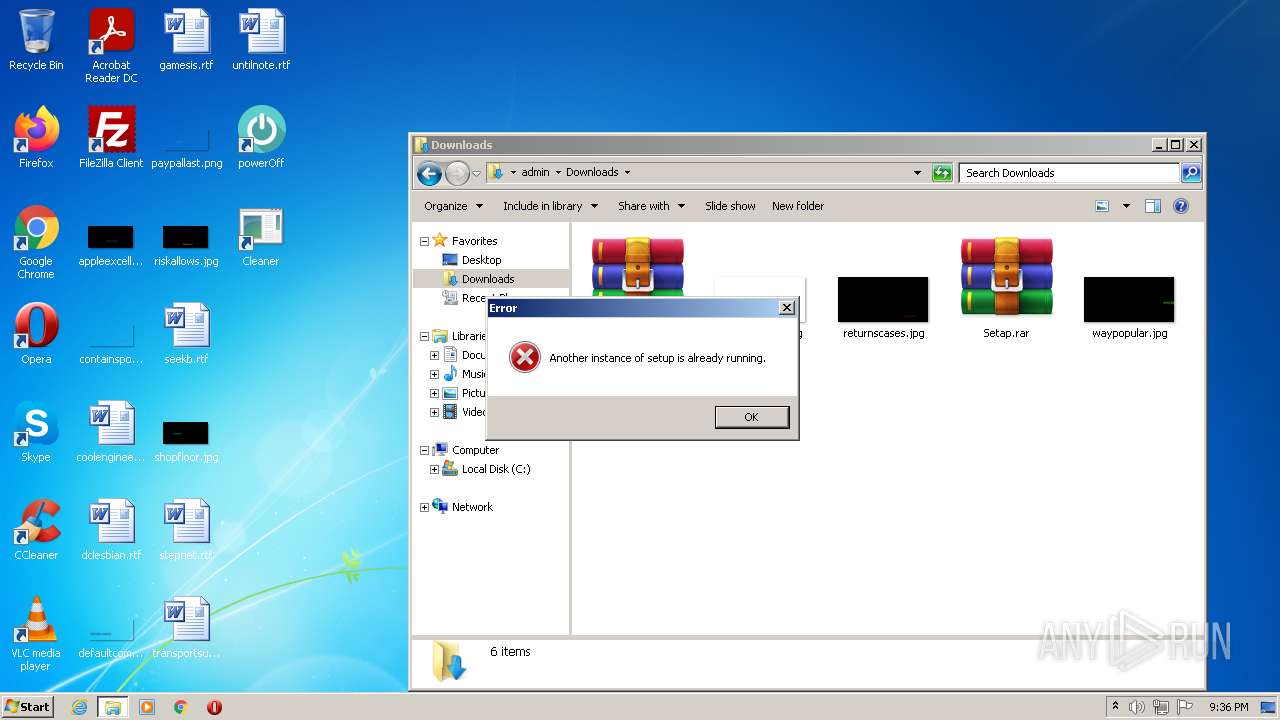
- installer.exe (PID: 1992)
Reads mouse settings
- Adamerax.exe (PID: 2572)
INFO
Checks supported languages
- chrome.exe (PID: 3288)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 1840)
- chrome.exe (PID: 3844)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 1624)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 1612)
- chrome.exe (PID: 3344)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 404)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 1840)
- chrome.exe (PID: 2344)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3916)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 2264)
- svchost.exe (PID: 868)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 1300)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 1852)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 2940)
- NOTEPAD.EXE (PID: 2476)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3724)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3936)
- msiexec.exe (PID: 1280)
- rundll32.exe (PID: 1636)
- chrome.exe (PID: 2268)
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 2968)
- taskkill.exe (PID: 1556)
- chrome.exe (PID: 2680)
- schtasks.exe (PID: 2040)
- taskkill.exe (PID: 3132)
- msiexec.exe (PID: 1768)
- taskkill.exe (PID: 3688)
- vssvc.exe (PID: 3168)
- explorer.exe (PID: 392)
- rundll32.exe (PID: 452)
- timeout.exe (PID: 4488)
- taskkill.exe (PID: 3652)
- taskkill.exe (PID: 5312)
- taskmgr.exe (PID: 2300)
Reads the computer name
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 2344)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 1852)
- rundll32.exe (PID: 1636)
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 2968)
- taskkill.exe (PID: 1556)
- schtasks.exe (PID: 2040)
- taskkill.exe (PID: 3132)
- msiexec.exe (PID: 1768)
- vssvc.exe (PID: 3168)
- taskkill.exe (PID: 3688)
- explorer.exe (PID: 392)
- rundll32.exe (PID: 452)
- taskkill.exe (PID: 3652)
- taskkill.exe (PID: 5312)
- taskmgr.exe (PID: 2300)
Reads the hosts file
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2452)
Application launched itself
- chrome.exe (PID: 3288)
- iexplore.exe (PID: 2464)
- msiexec.exe (PID: 2928)
Reads settings of System Certificates
- chrome.exe (PID: 2452)
- 6287f59bb75e4_d750e42fc1.exe (PID: 1996)
- powershell.exe (PID: 2068)
- lBo5.exe (PID: 2704)
- Tabadekuhi.exe (PID: 3904)
- Vaeshaelomuve.exe (PID: 3124)
- iexplore.exe (PID: 2968)
- 6287f59a5424c_555ba6edf.exe (PID: 1924)
- iexplore.exe (PID: 2464)
- installer.exe (PID: 1992)
- 161.tmp (PID: 680)
- tapinstall.exe (PID: 2040)
- DrvInst.exe (PID: 2116)
- msiexec.exe (PID: 2928)
- random.exe (PID: 2920)
- MsiExec.exe (PID: 4088)
- handselfdiy_0.exe (PID: 3236)
- b123.exe (PID: 2920)
- chrome.exe (PID: 2400)
- DrvInst.exe (PID: 5600)
Reads the date of Windows installation
- chrome.exe (PID: 2344)
- iexplore.exe (PID: 2464)
Checks Windows Trust Settings
- powershell.exe (PID: 2068)
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 2464)
- installer.exe (PID: 1992)
- tapinstall.exe (PID: 2040)
- DrvInst.exe (PID: 2116)
- msiexec.exe (PID: 2928)
- MsiExec.exe (PID: 4088)
- handselfdiy_0.exe (PID: 3236)
- b123.exe (PID: 2920)
- DrvInst.exe (PID: 5600)
Application was dropped or rewritten from another process
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- lBo5.exe (PID: 2704)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- poweroff.tmp (PID: 2024)
- 161.tmp (PID: 680)
Loads dropped or rewritten executable
- 6287f5bd026e4_7412125.tmp (PID: 3304)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3468)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- poweroff.tmp (PID: 2024)
- 161.tmp (PID: 680)
- MsiExec.exe (PID: 3384)
- MsiExec.exe (PID: 4088)
- MsiExec.exe (PID: 2640)
Creates files in the program directory
- lBo5.exe (PID: 2704)
- poweroff.tmp (PID: 2024)
- 161.tmp (PID: 680)
- msiexec.exe (PID: 2928)
Changes internet zones settings
- iexplore.exe (PID: 2464)
Creates a software uninstall entry
- poweroff.tmp (PID: 2024)
- 6287f59d2b46f_4cf4448501.tmp (PID: 3268)
- 161.tmp (PID: 680)
- msiexec.exe (PID: 2928)
Creates files in the user directory
- iexplore.exe (PID: 2968)
Reads internet explorer settings
- iexplore.exe (PID: 2968)
Reads Microsoft Office registry keys
- MsiExec.exe (PID: 2640)
- MsiExec.exe (PID: 4088)
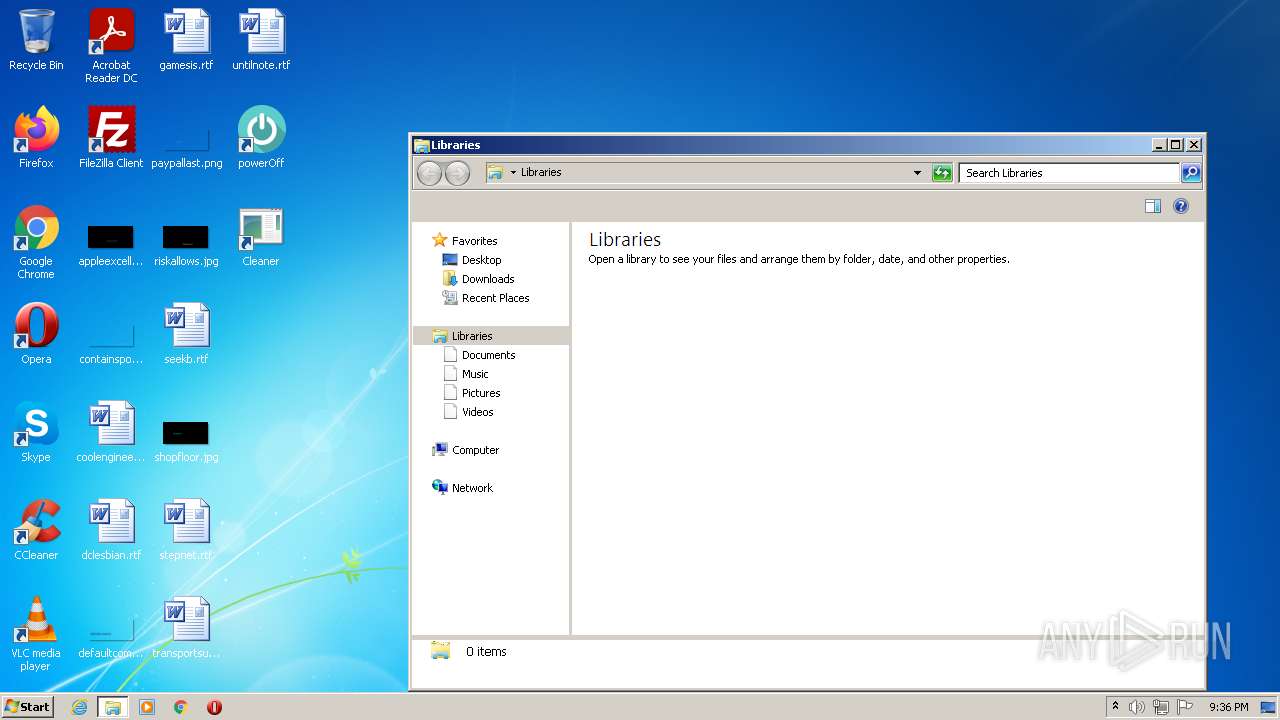
Manual execution by user
- explorer.exe (PID: 392)
- taskmgr.exe (PID: 2300)
Searches for installed software
- DrvInst.exe (PID: 2116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(2992) 6287f59b040e8_1fe17aaeae.exe
C2 (1)141.95.211.151:34846
Botnetbernard03
Err_msg
Auth_value79ef71b2b79b4bbfc450d11fa1720cea
US (165)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Host
Port
:
User
Pass
cookies.sqlite
%USEDisposeRPROFILE%\AppDaDisposeta\LDisposeocal
Dispose
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrbyte[]yptDesbyte[]troyKbyte[]ey
byte[]
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
79ef71b2b79b4bbfc450d11fa1720cea
Authorization
ns1
UNKNWON
AzsrAiAPJV42ECUdAzxOAiIxC1k3AD1RACsjRw==
FwIsAw4ICBYgPi0f
Nozzle
Yandex\YaAddon
ToString
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
Network\
String
Replace
80
81
0.0.0.0
SystemBC
(PID) Process(1972) 5927335832.exe
C2 (2)135.125.248.50:443
146.70.53.169:443
(PID) Process(292) 5927335832.exe
C2 (2)135.125.248.50:443
146.70.53.169:443
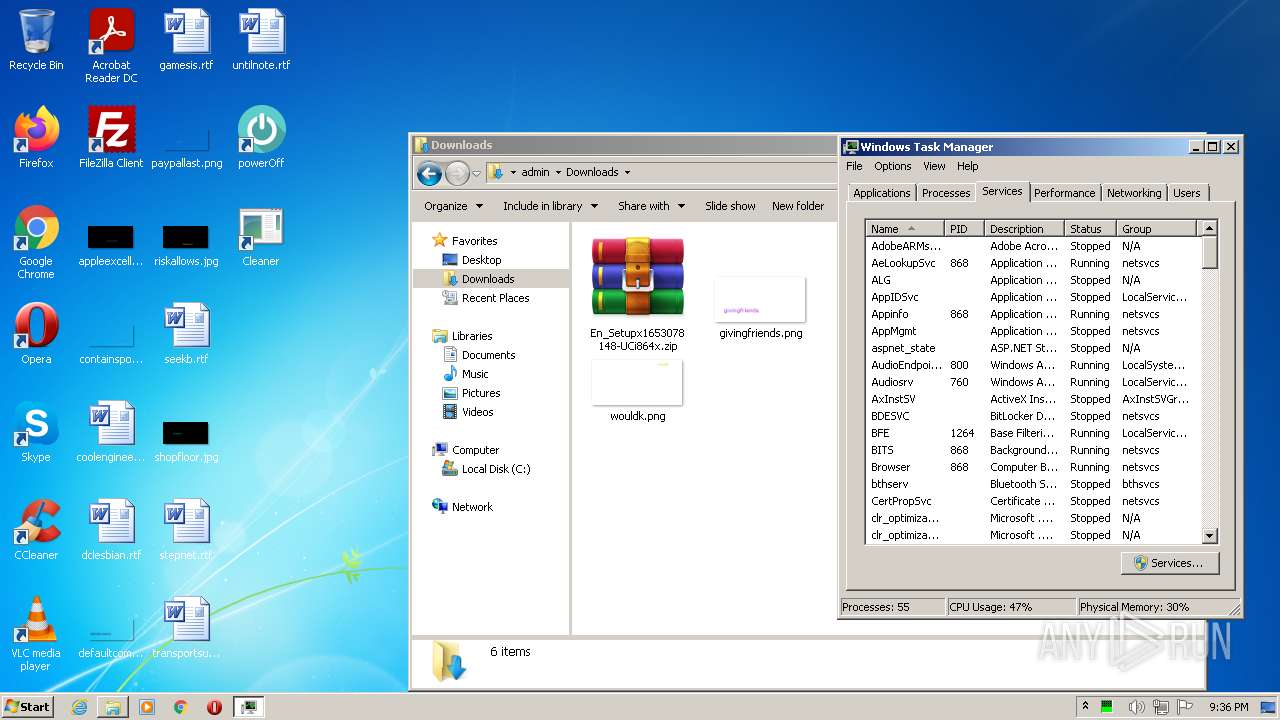
Total processes
255
Monitored processes
169
Malicious processes
59
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Windows\system32\cmd.exe" /c schtasks /create /tn \Service\Diagnostic /tr """"C:\Users\admin\AppData\Roaming\ServiceGet\Adamerax.exe""" """C:\Users\admin\AppData\Roaming\ServiceGet\Adamerax.dat"""" /st 00:01 /du 9700:49 /sc once /ri 1 /f | C:\Windows\system32\cmd.exe | — | BEXAe3Mo0P.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 292 | C:\Users\admin\AppData\Local\Temp\5927335832.exe start | C:\Users\admin\AppData\Local\Temp\5927335832.exe | taskeng.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
SystemBC(PID) Process(292) 5927335832.exe C2 (2)135.125.248.50:443 146.70.53.169:443 | |||||||||||||||
| 340 | strongix.exe | C:\Users\admin\AppData\Roaming\shftool\strongix.exe | N5KMZ9Gsim.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 340 | C:\Users\admin\AppData\Local\Temp\lb2vuwuu.qwe\installer.exe /qn CAMPAIGN=654 | C:\Users\admin\AppData\Local\Temp\lb2vuwuu.qwe\installer.exe | — | cmd.exe | |||||||||||
User: admin Company: AW Manager Integrity Level: HIGH Description: Windows Manager Installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 348 | 6287f59bb75e4_d750e42fc1.exe | C:\Users\admin\AppData\Local\Temp\7zS0140E5A2\6287f59bb75e4_d750e42fc1.exe | — | cmd.exe | |||||||||||
User: admin Company: TODO: <Company name> Integrity Level: HIGH Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 392 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=836,11507321809954503784,17252226450444471852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 452 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\db.dll",global | C:\Windows\system32\rundll32.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | C:\Windows\system32\cmd.exe /c 6287f5a19fe91_40ddf90.exe | C:\Windows\system32\cmd.exe | — | setup_install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147944514 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 680 | "C:\Users\admin\AppData\Local\Temp\is-JASPV.tmp\161.tmp" /SL5="$3023E,15170975,270336,C:\Users\admin\AppData\Local\Temp\scq43b1u.24f\161.exe" /silent /subid=798 | C:\Users\admin\AppData\Local\Temp\is-JASPV.tmp\161.tmp | 161.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
126 845
Read events
124 459
Write events
2 240
Delete events
146
Modification events
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
151
Suspicious files
150
Text files
269
Unknown types
85
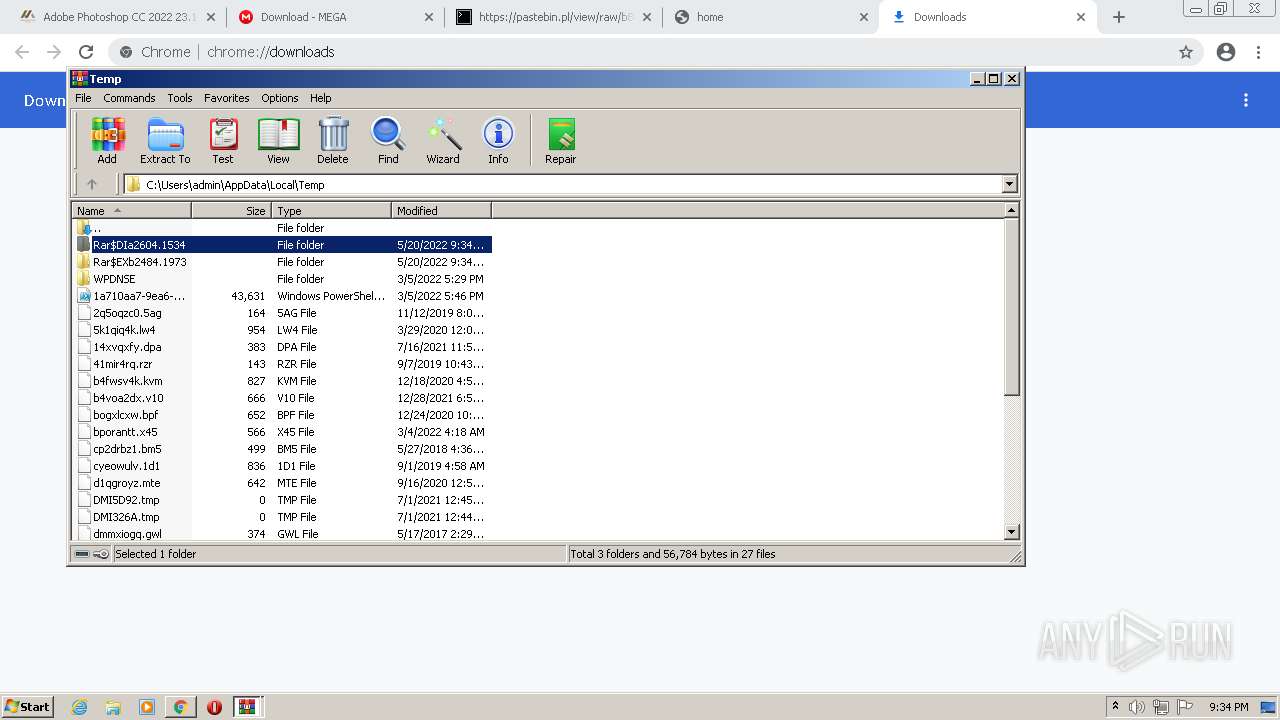
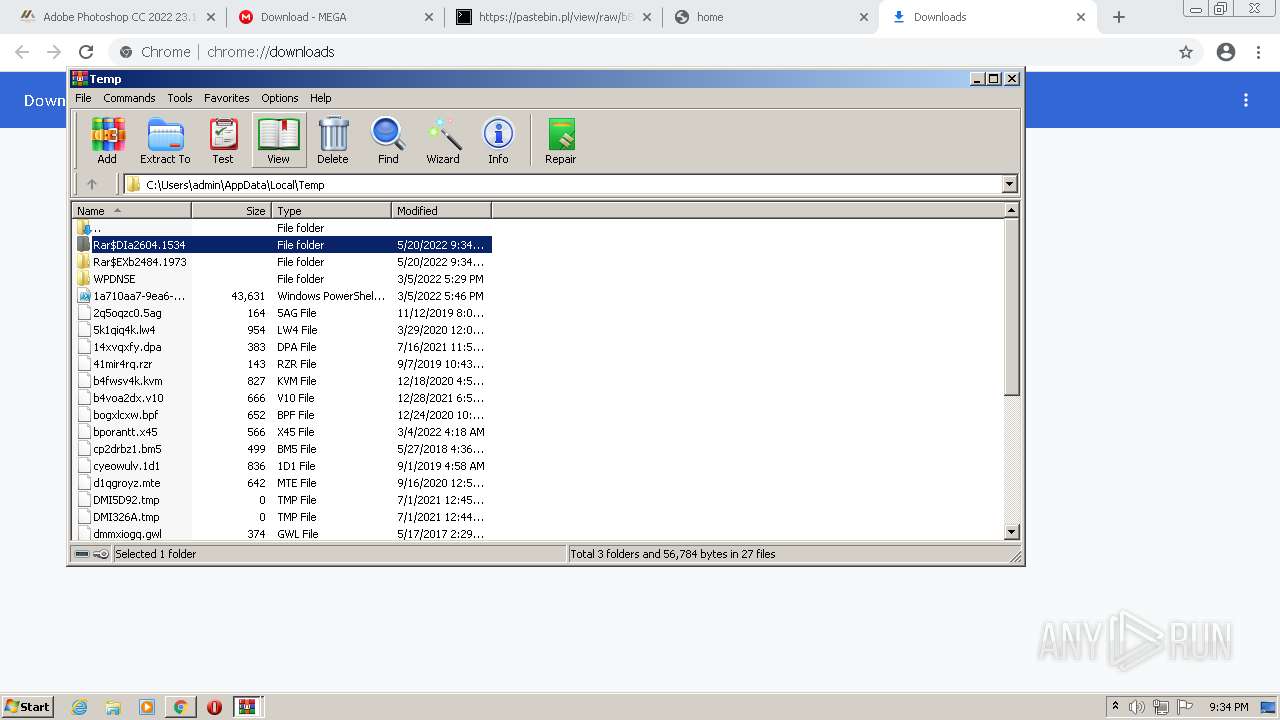
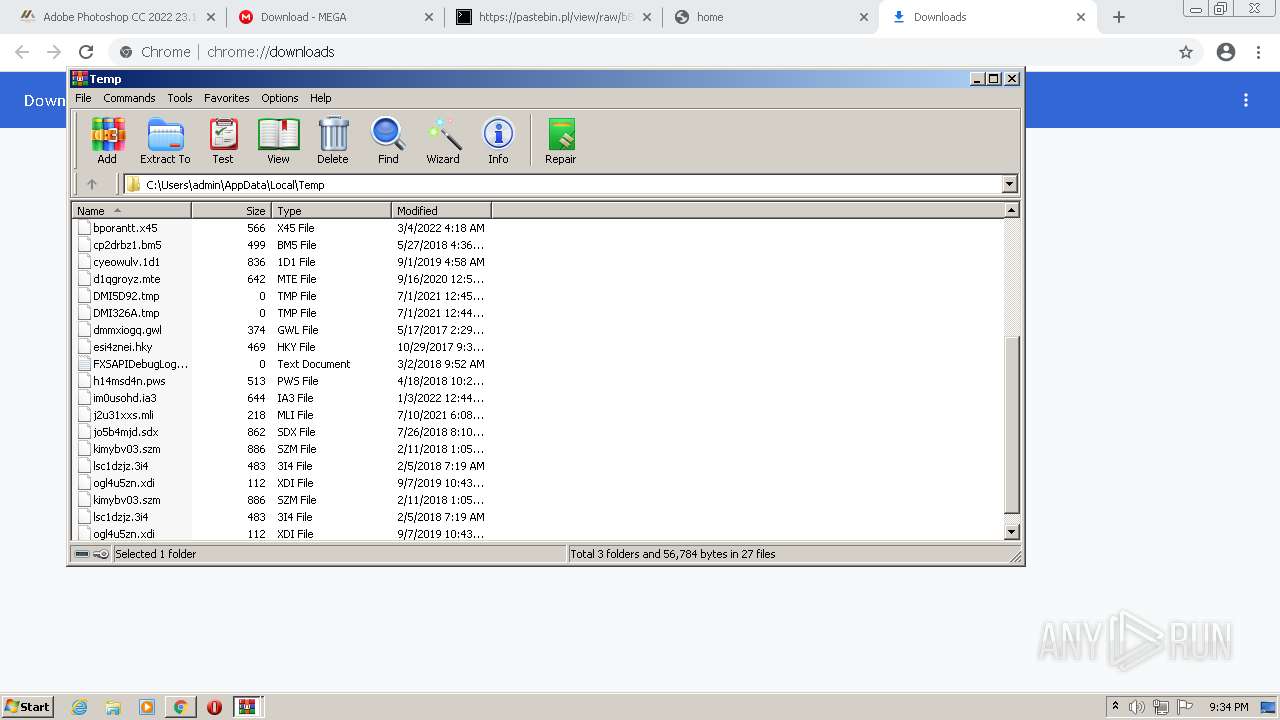
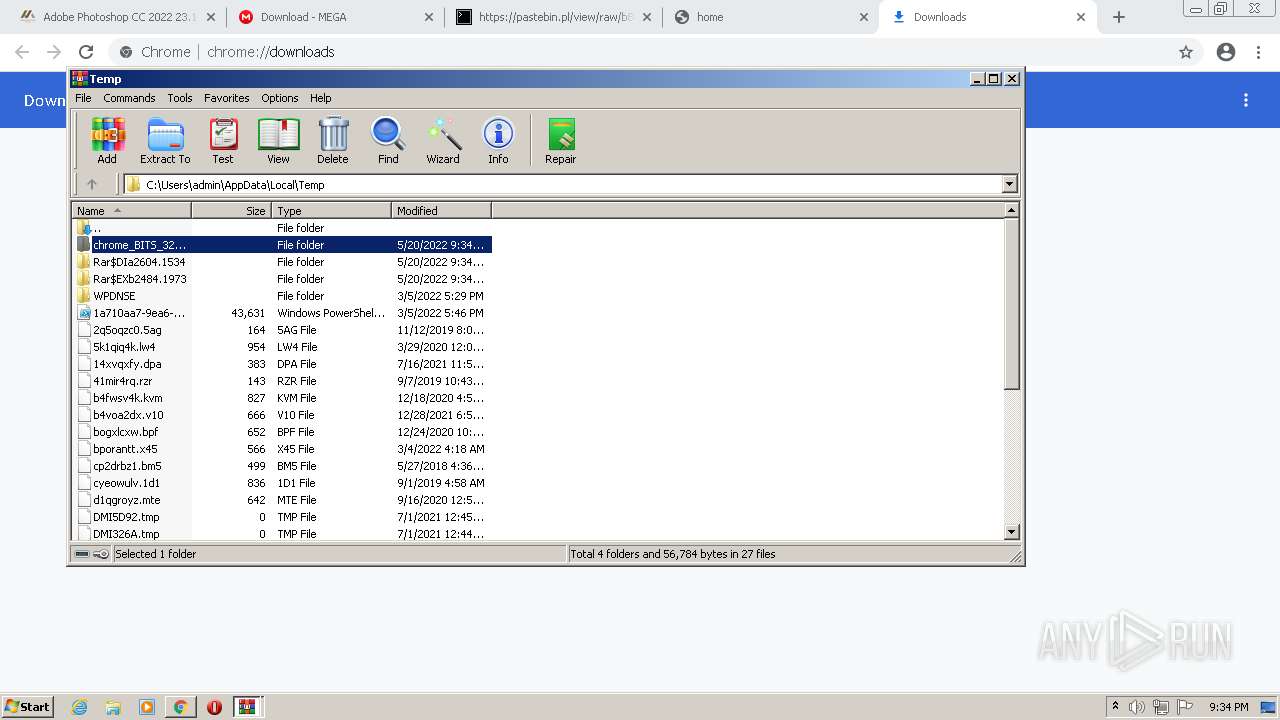
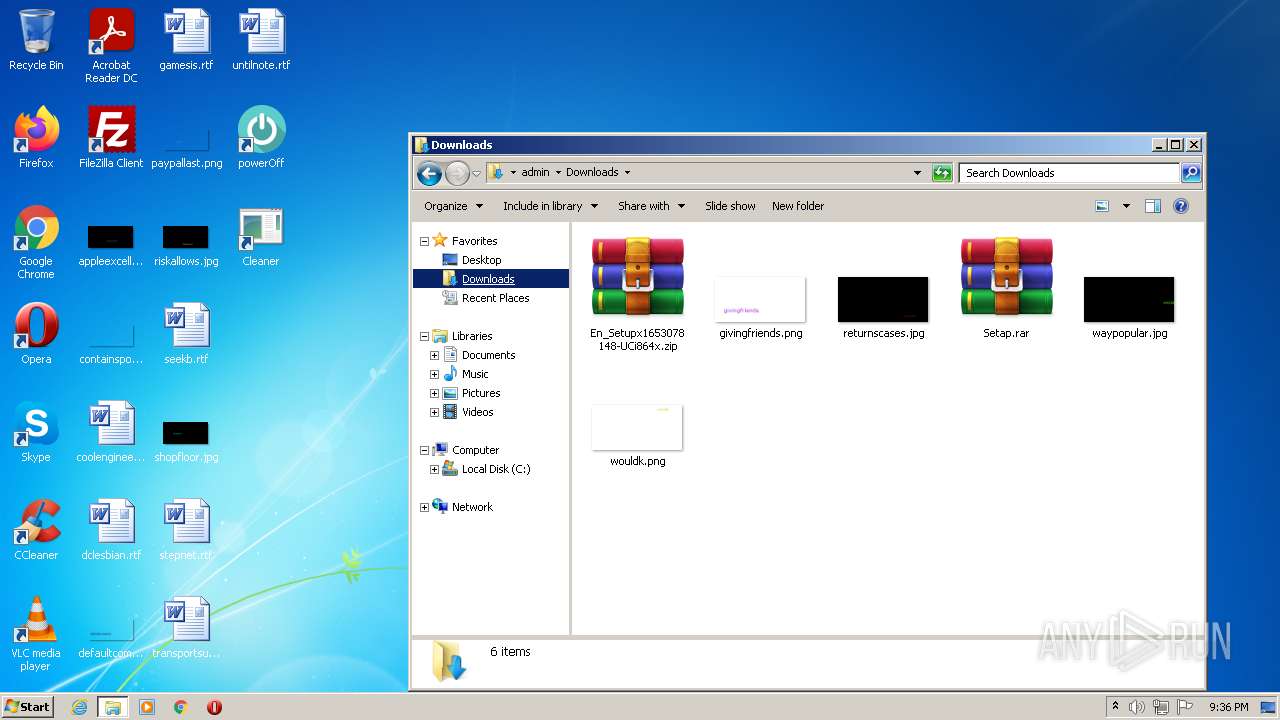
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6287FABE-CD8.pma | — | |
MD5:— | SHA256:— | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\26aff75d-e019-4ca3-b760-44ced79ebac9.tmp | text | |
MD5:— | SHA256:— | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7e326524-6f63-47ac-ba6c-694c383c2411.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf96d8.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
124
TCP/UDP connections
243
DNS requests
118
Threats
141
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
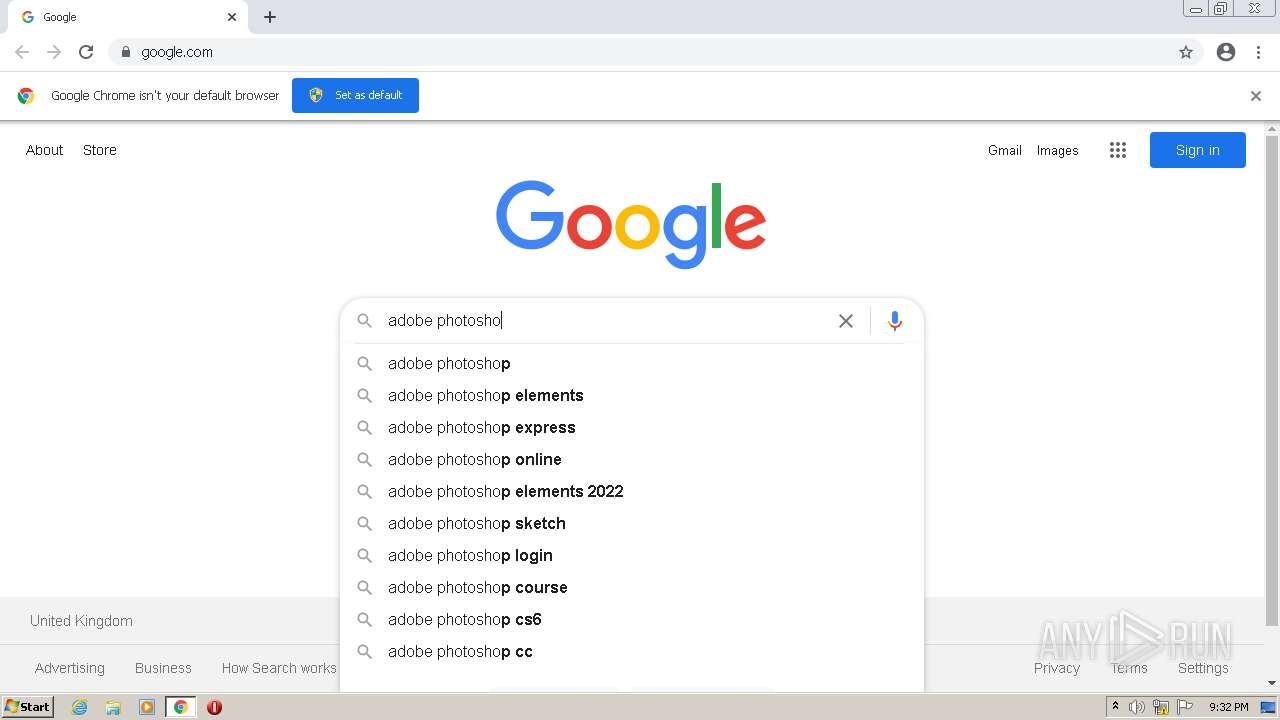
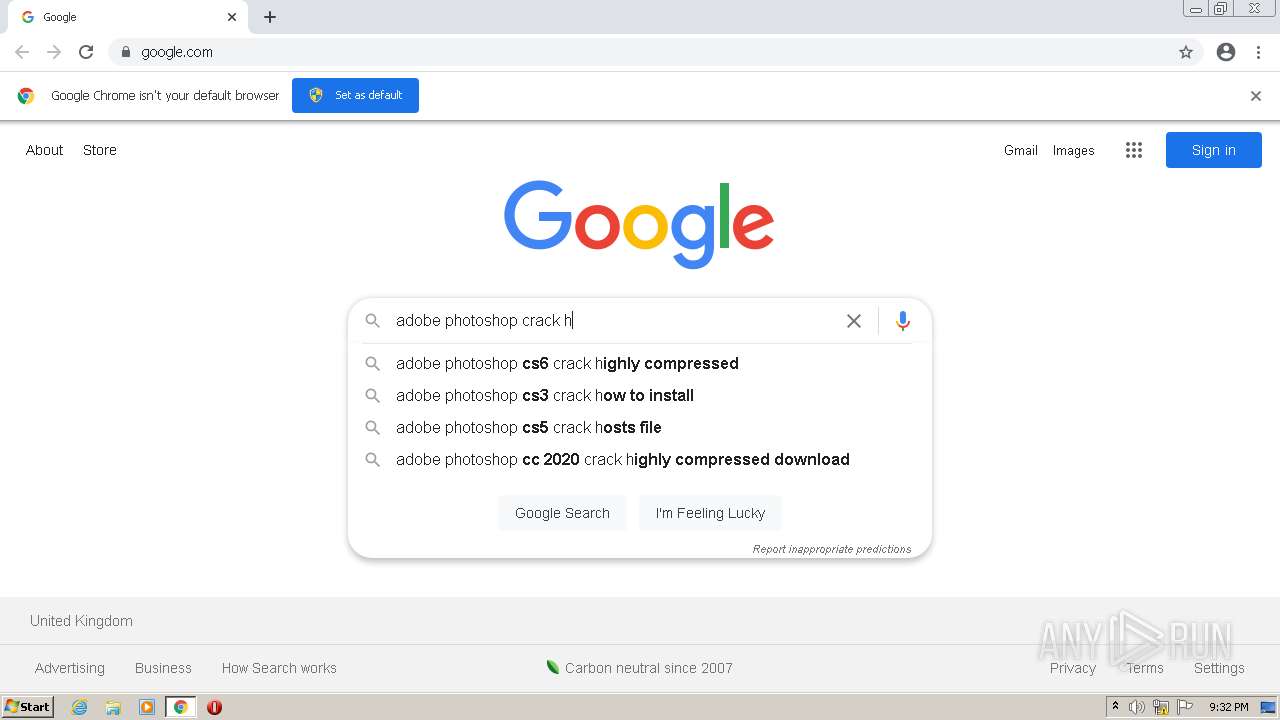
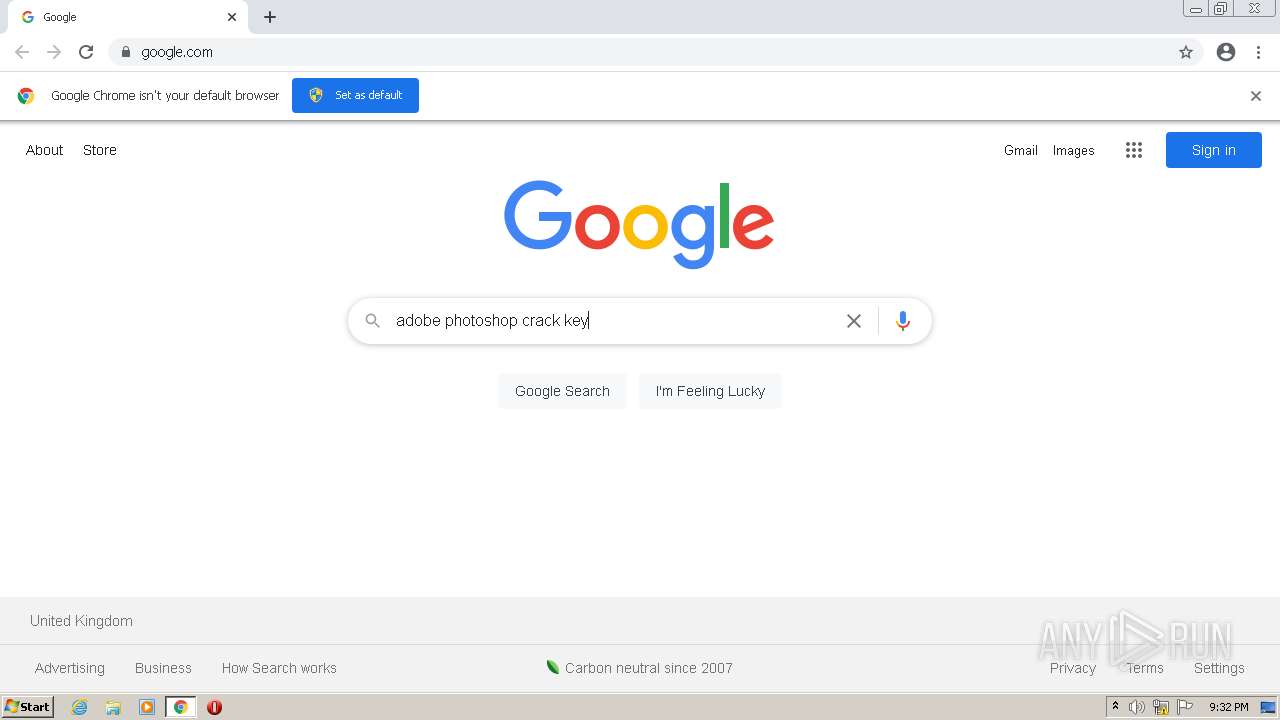
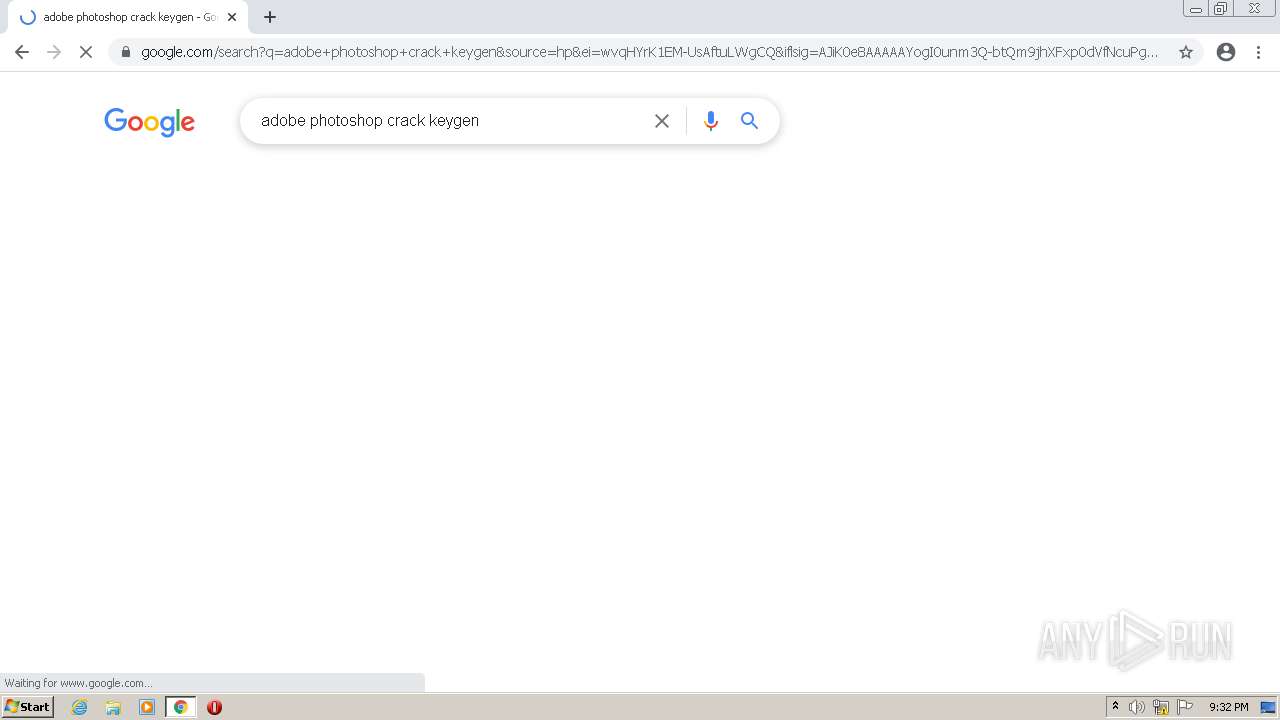
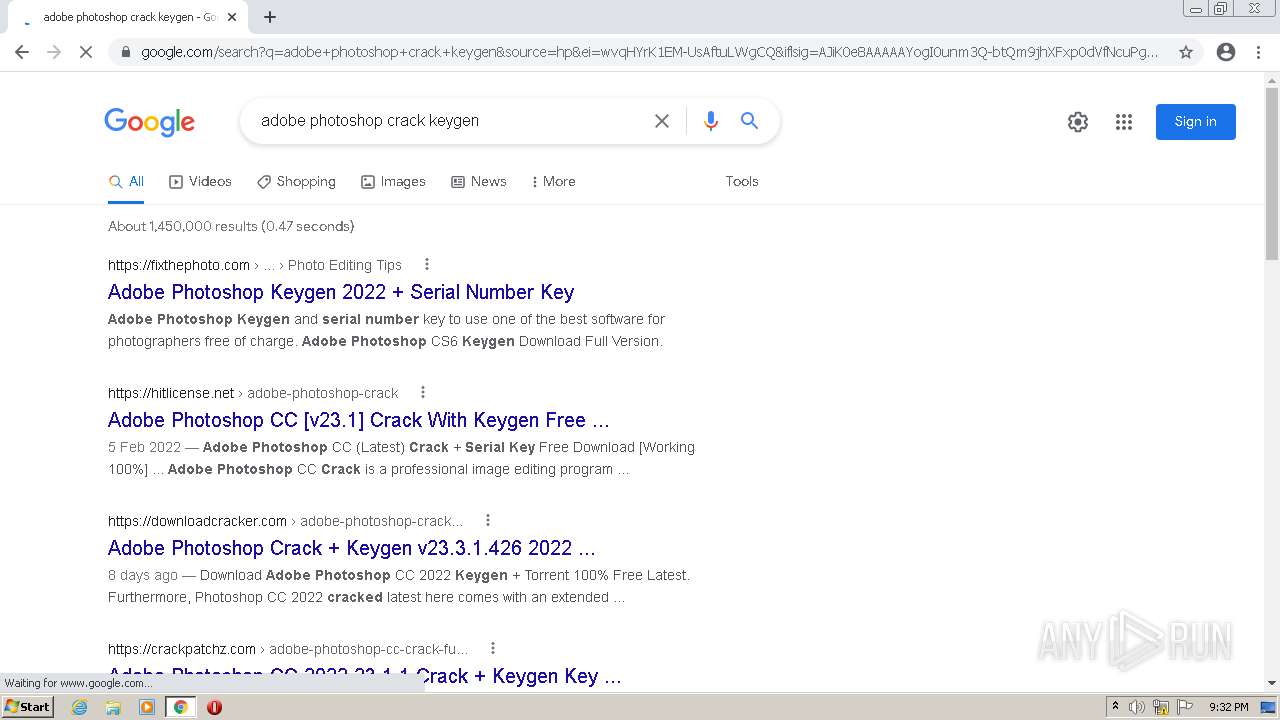
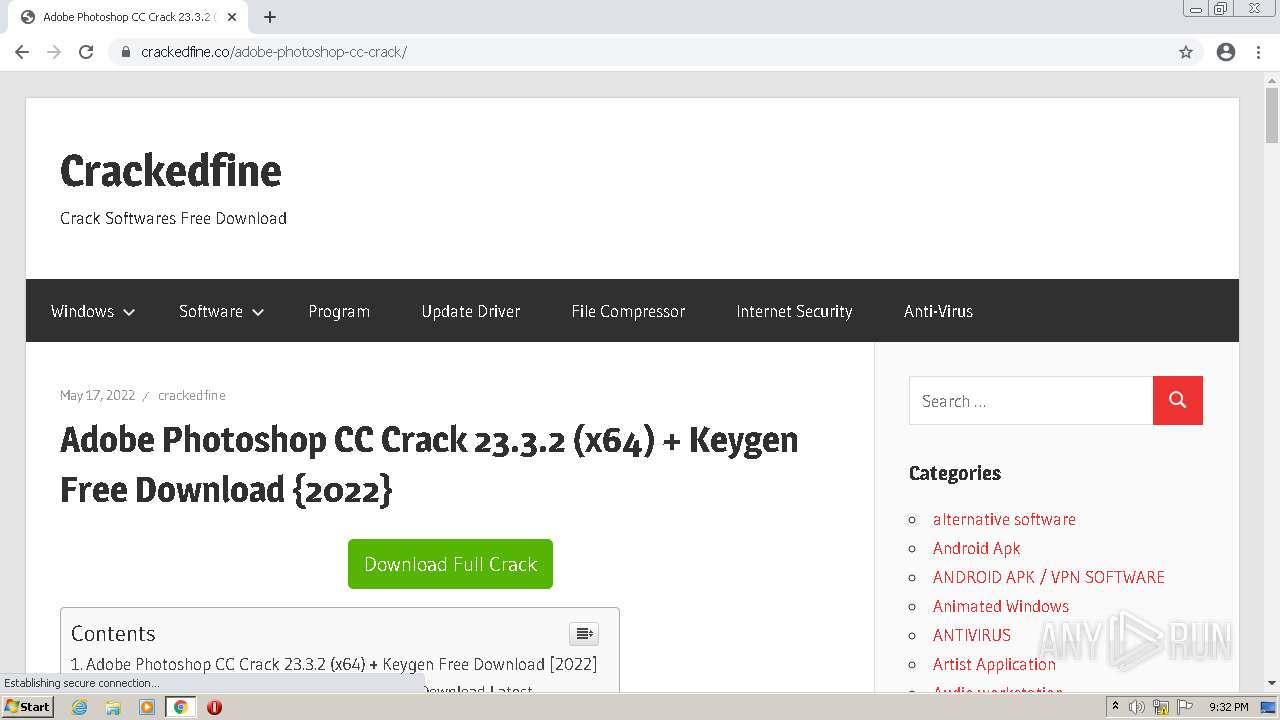
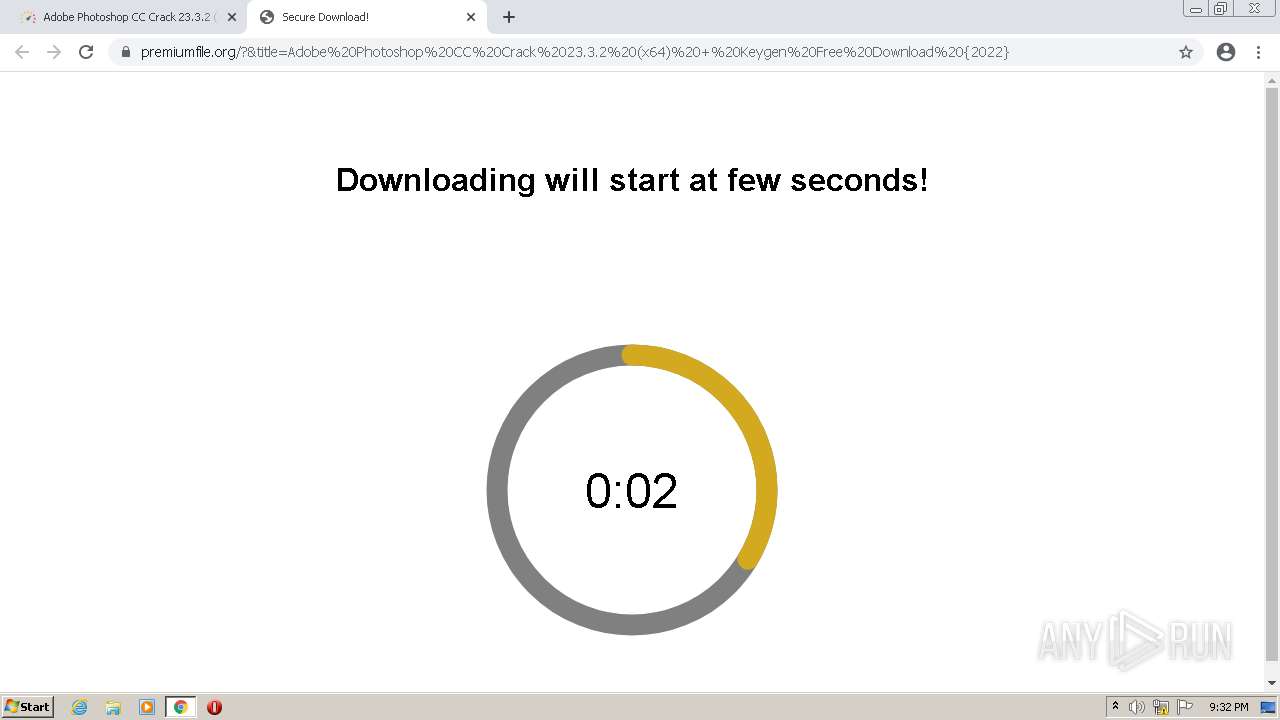
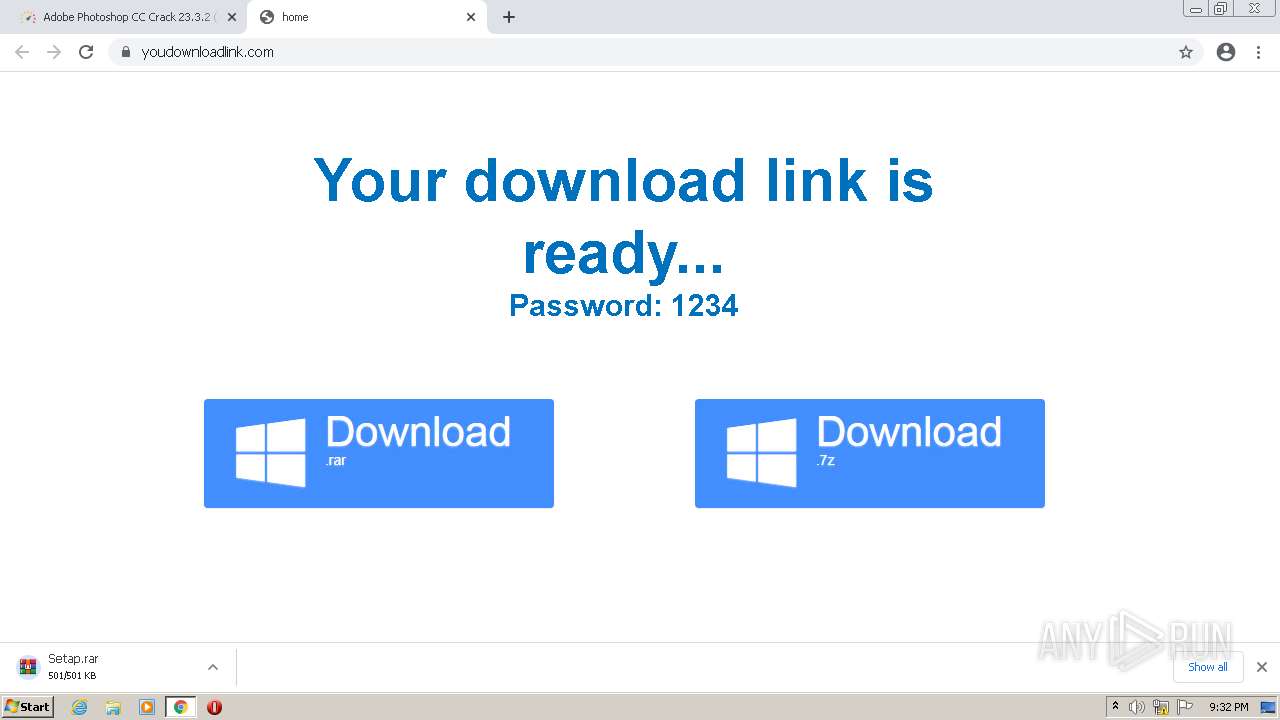
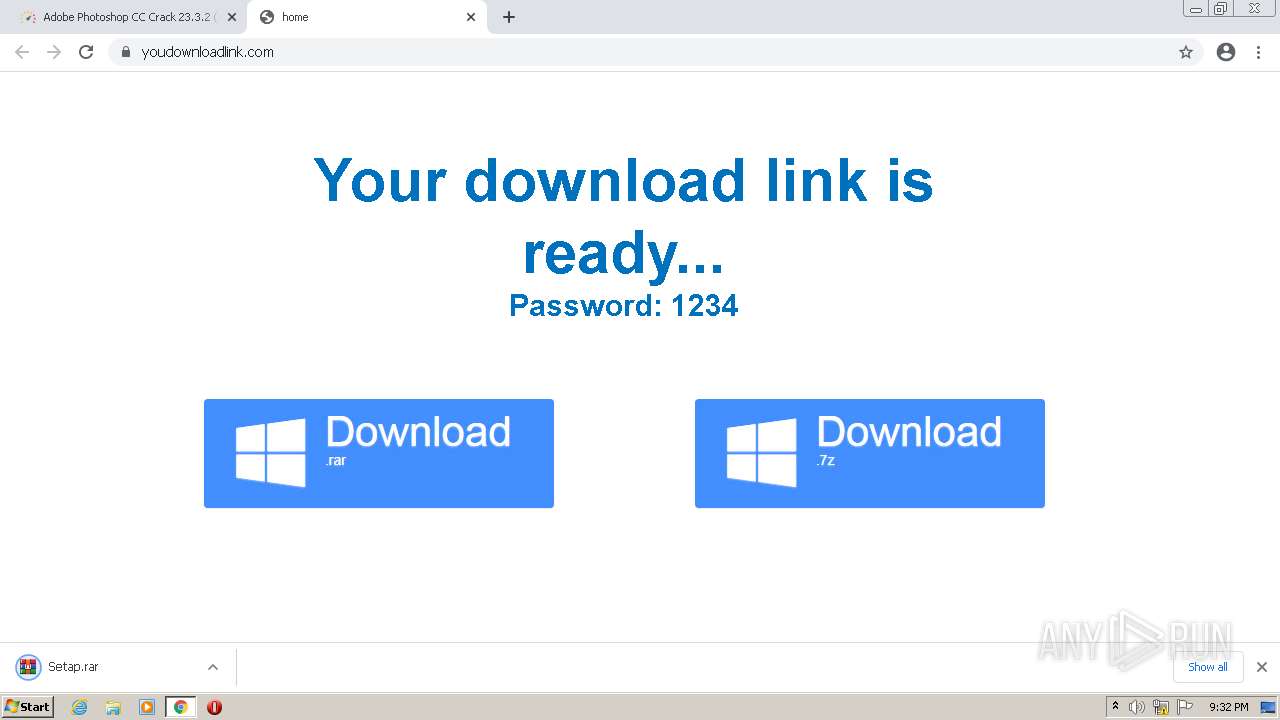
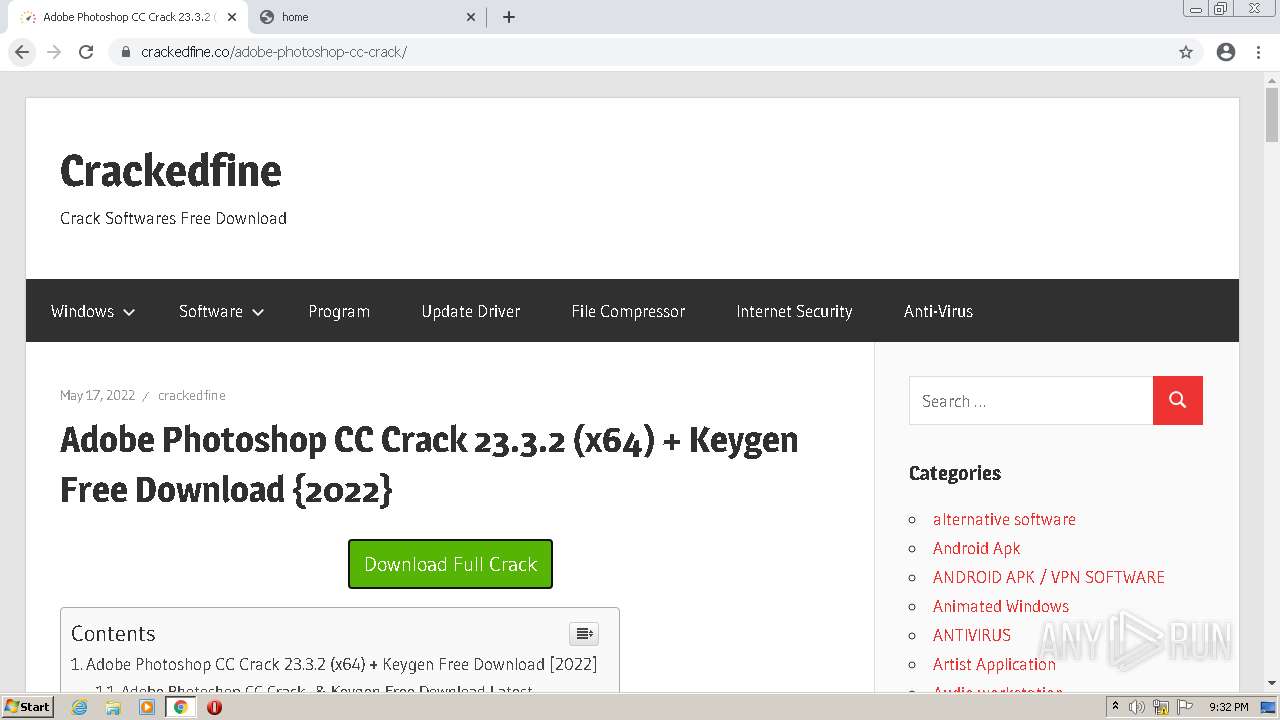
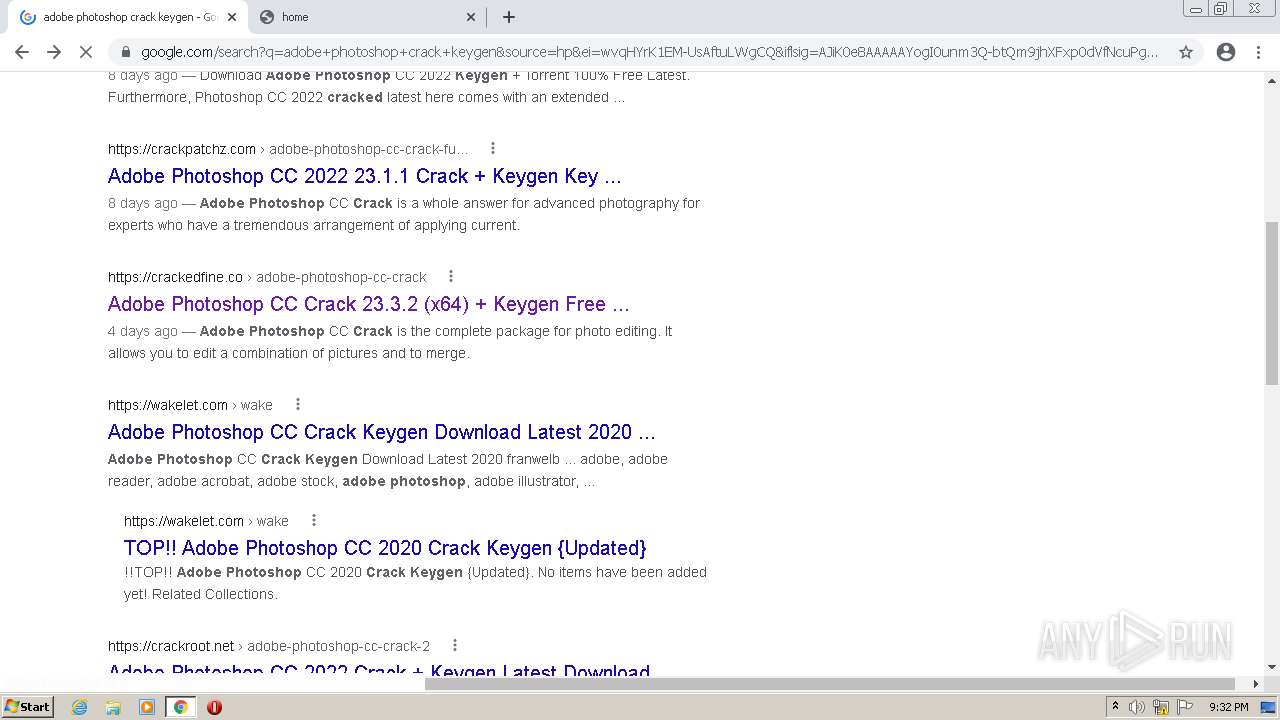
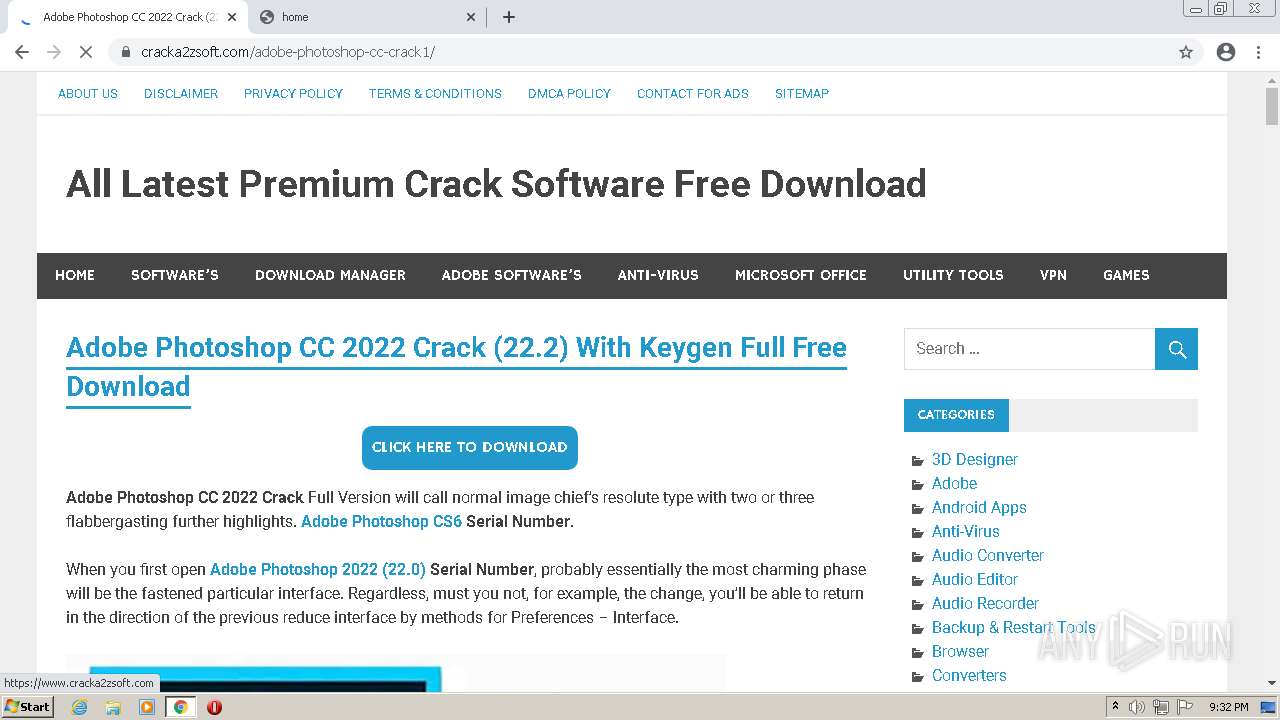
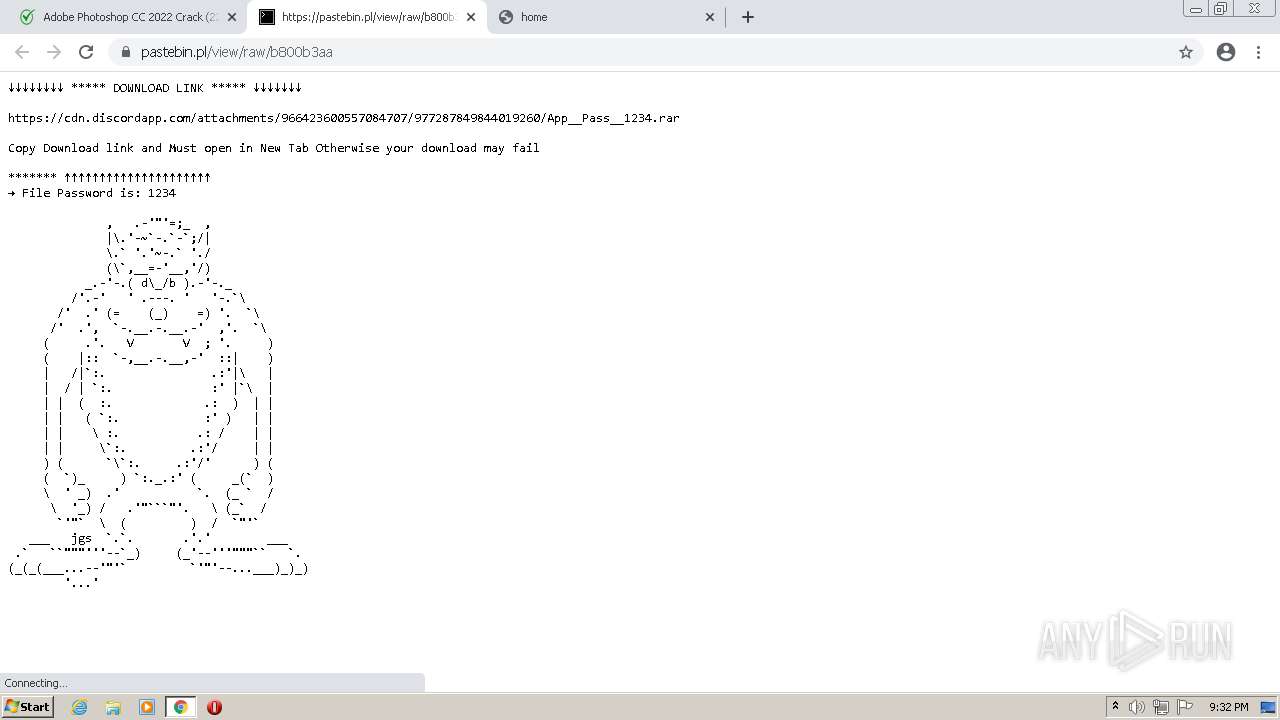
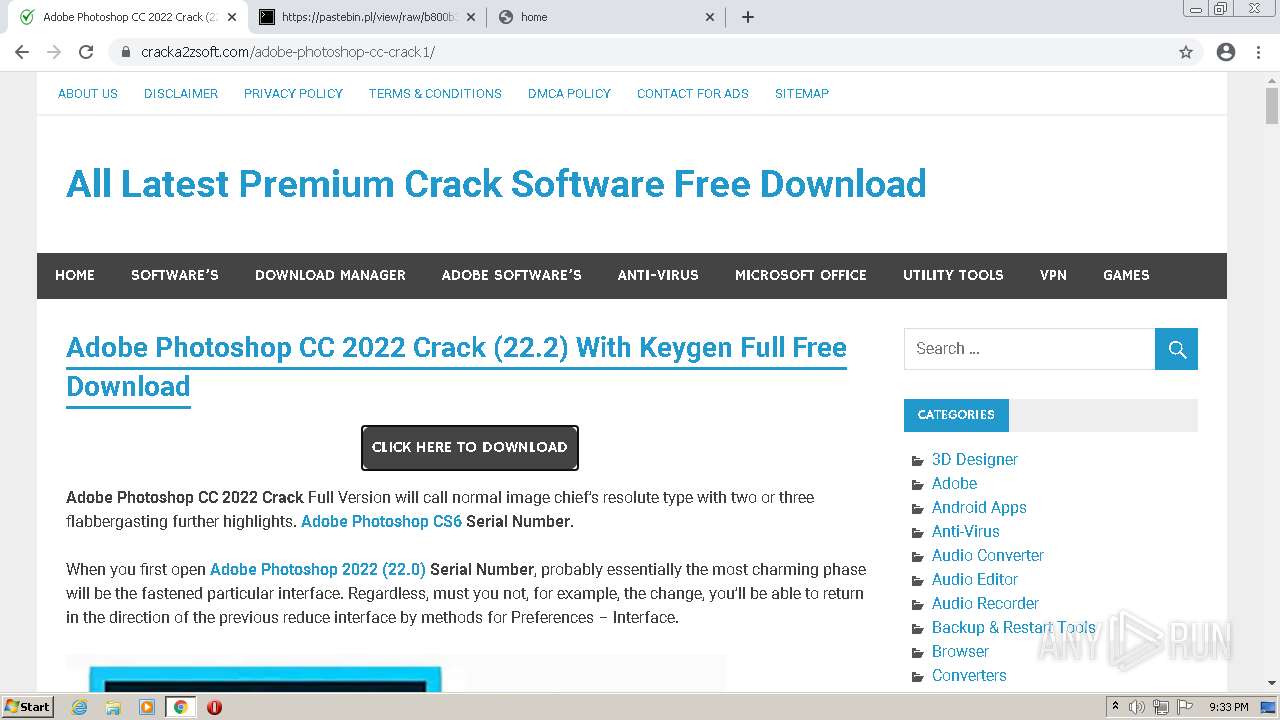
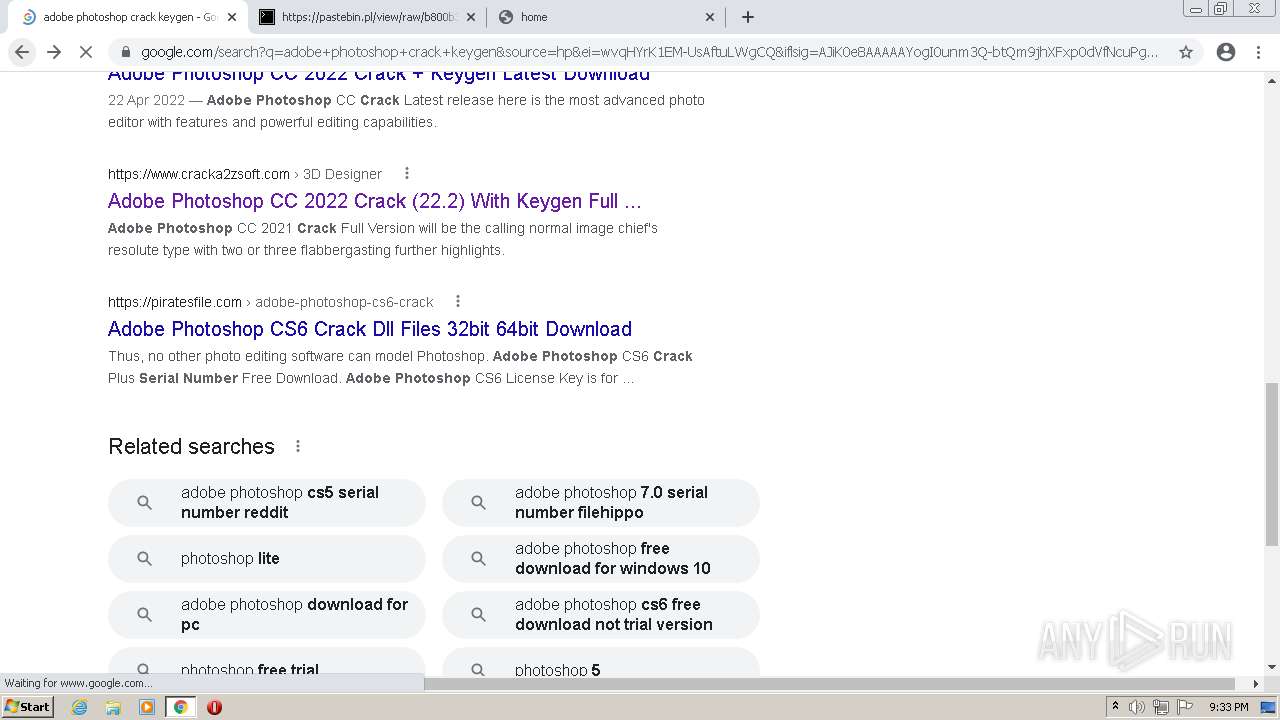
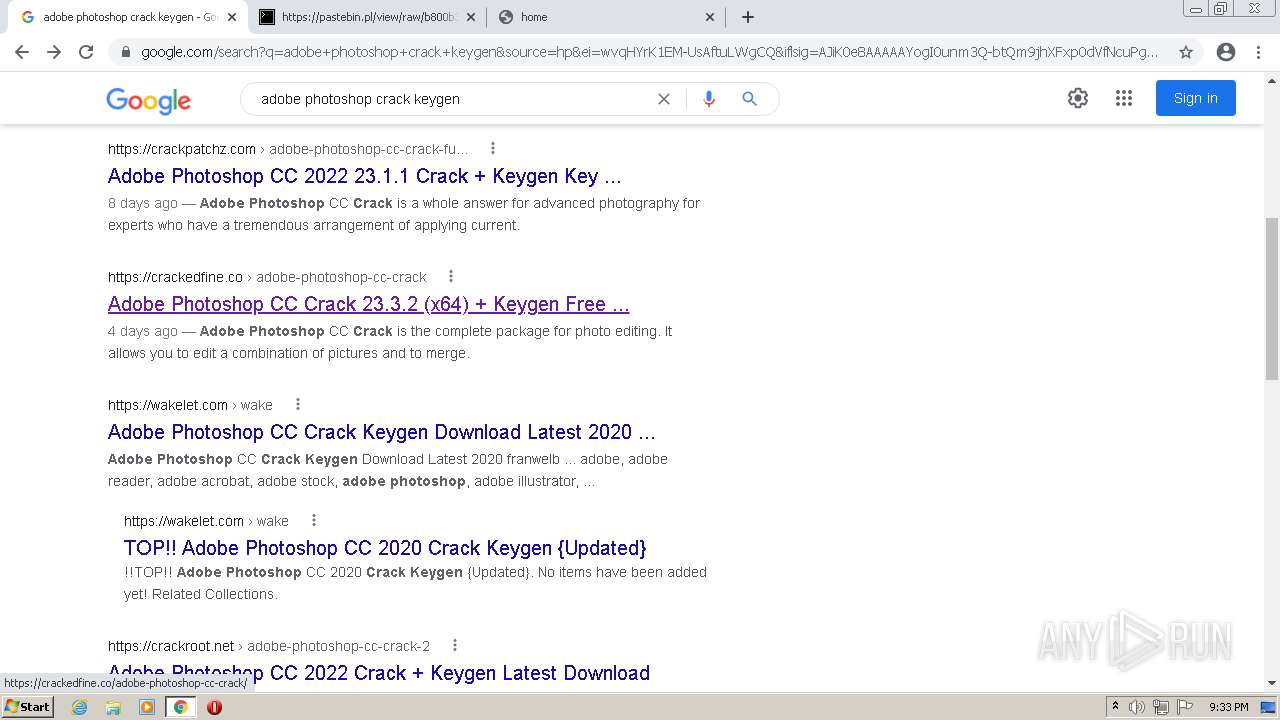
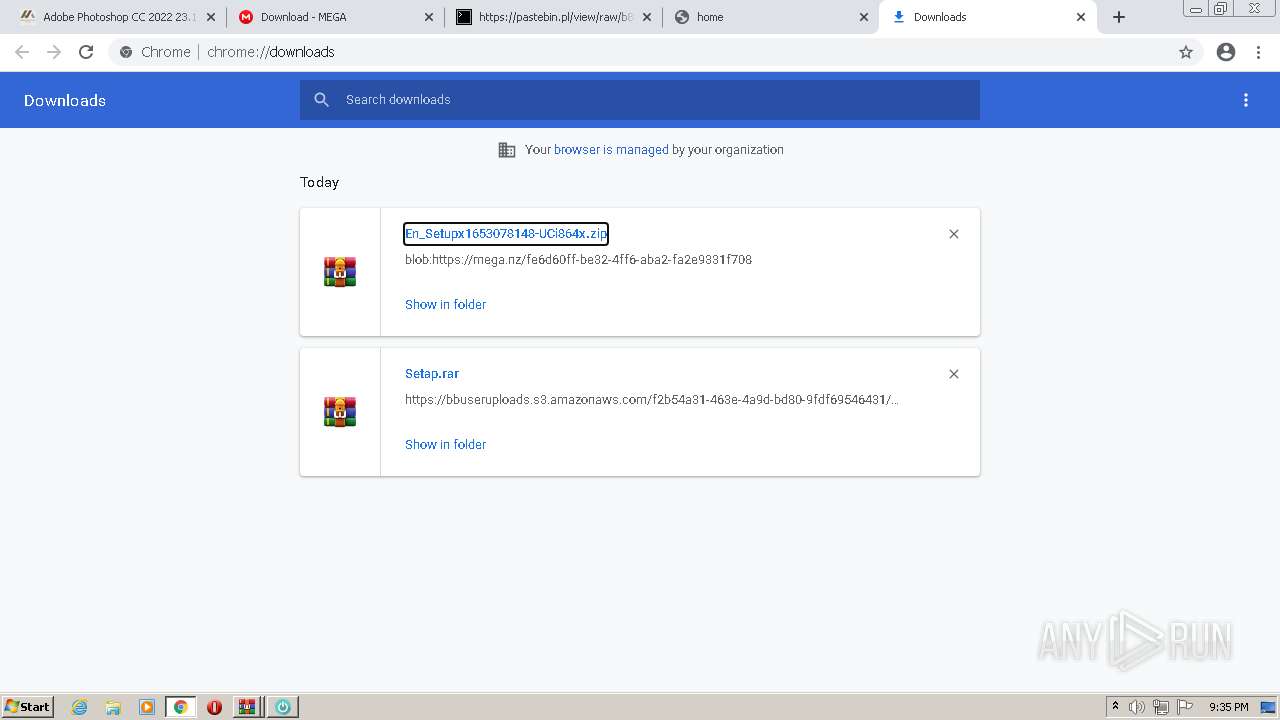
2452 | chrome.exe | GET | 200 | 188.166.138.48:80 | http://188.166.138.48/?http://138.197.130.160/?rip=5b545495601c7f0f7b3774563480f0ee&ikdp=2749&content=1_adobe-photoshop-cc-2022-crack-22-2-with-keygen-full-free-download&gkss=1594 | GB | html | 154 b | unknown |
2452 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 43.6 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | fli | 21.1 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 1.10 Mb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.90 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.90 Kb | whitelisted |
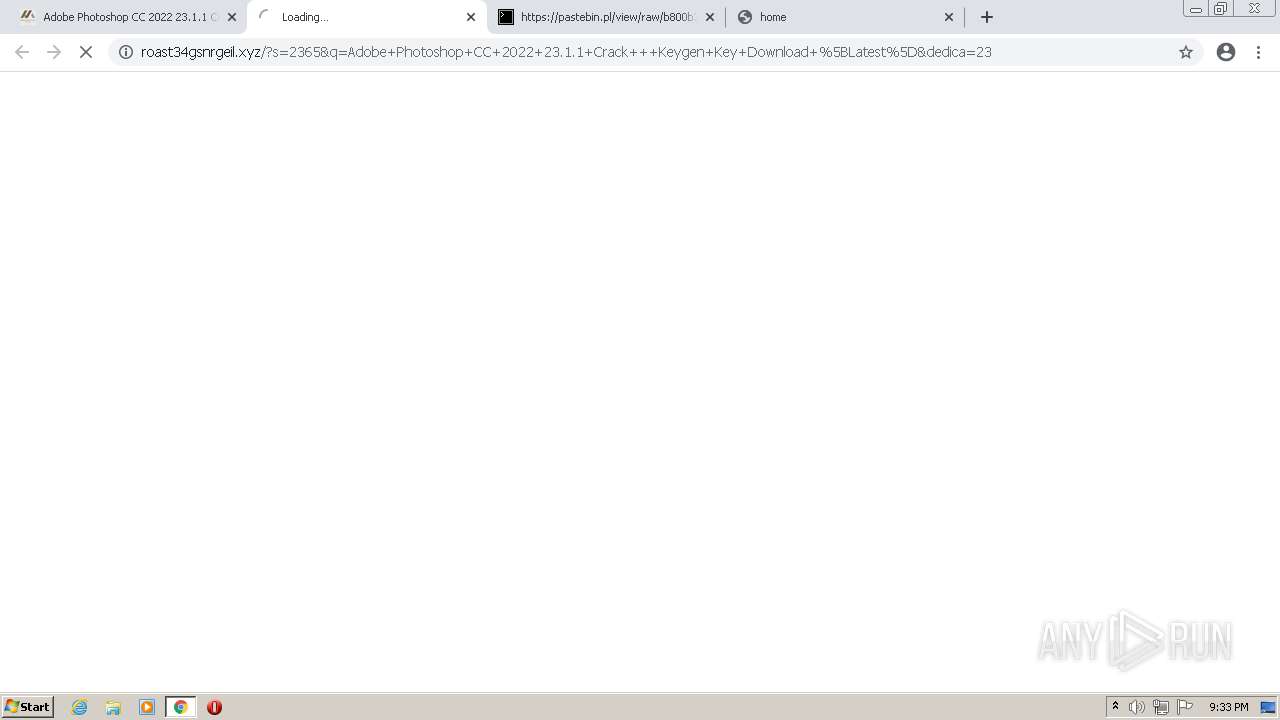
2452 | chrome.exe | GET | 200 | 188.114.96.10:80 | http://roast34gsnrgeil.xyz/?s=2365&q=Adobe+Photoshop+CC+2022+23.1.1+Crack+++Keygen+Key+Download+%5BLatest%5D&dedica=23 | US | html | 177 b | malicious |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 5.78 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2452 | chrome.exe | 142.250.185.164:443 | www.google.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 142.250.185.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 216.58.212.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2452 | chrome.exe | 142.250.186.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.18.110:443 | consent.youtube.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 142.251.36.98:443 | adservice.google.com | Google Inc. | US | suspicious |
2452 | chrome.exe | 142.250.185.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 142.250.185.168:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
consent.google.com |
| shared |
consent.google.co.uk |
| whitelisted |
play.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2452 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3304 | 6287f5bd026e4_7412125.tmp | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
3304 | 6287f5bd026e4_7412125.tmp | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
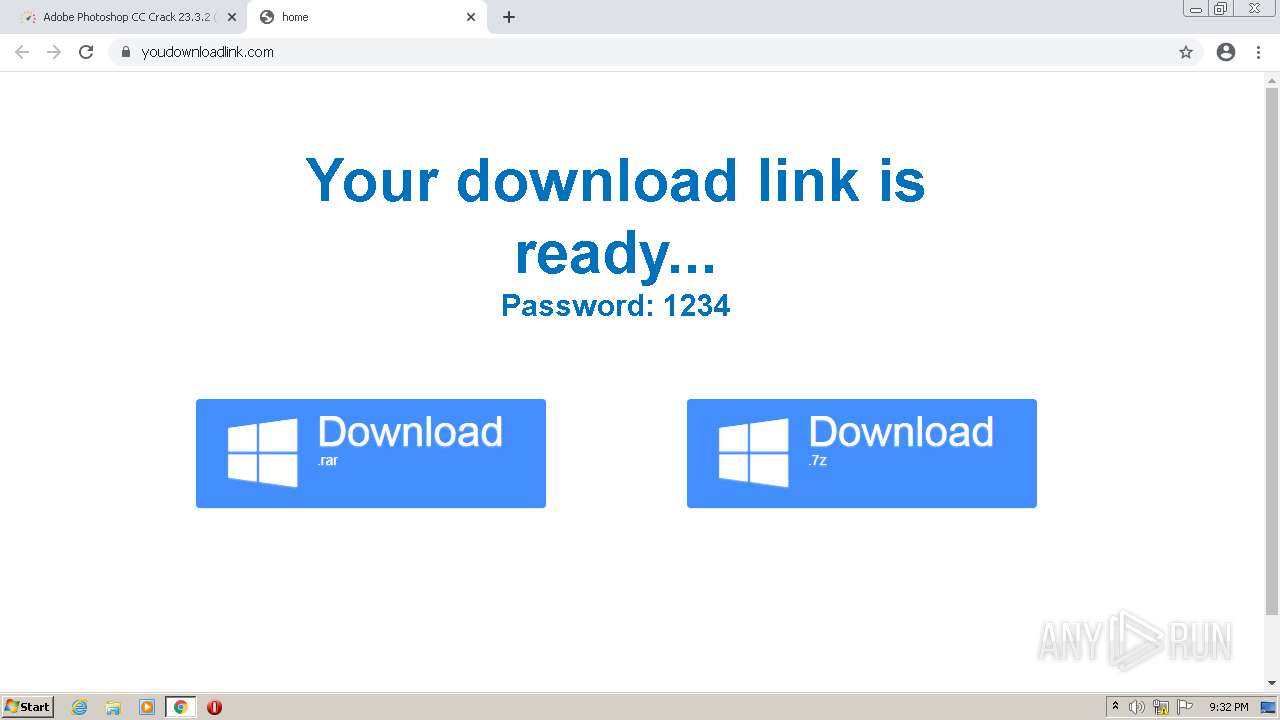
3304 | 6287f5bd026e4_7412125.tmp | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3268 | 6287f59d2b46f_4cf4448501.tmp | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3268 | 6287f59d2b46f_4cf4448501.tmp | Misc activity | ET INFO EXE - Served Attached HTTP |
3436 | 6287f5bbde3df_8d6393c.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3436 | 6287f5bbde3df_8d6393c.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
49 ETPRO signatures available at the full report