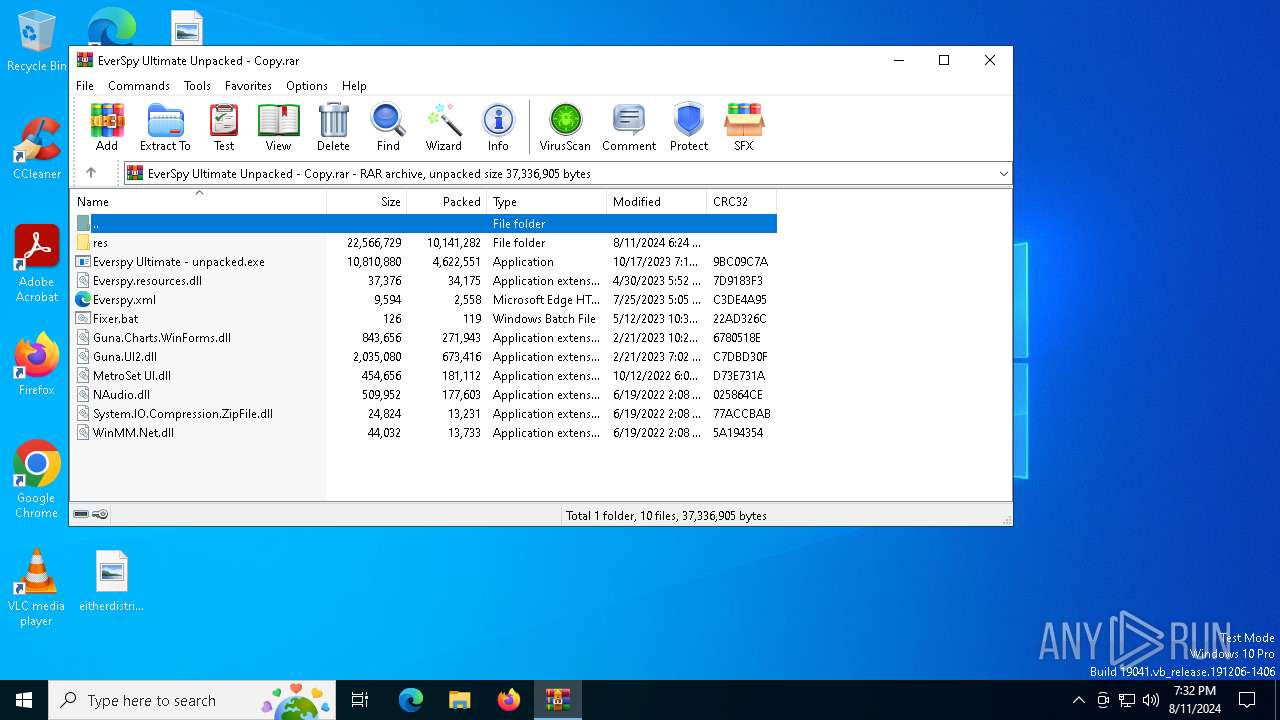
| File name: | EverSpy Ultimate Unpacked - Copy.rar |
| Full analysis: | https://app.any.run/tasks/6130b71b-5608-447d-a338-0bce6aca9466 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | August 11, 2024, 19:32:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7CEA74158FFA610149B5B76B9CE29E5D |
| SHA1: | BD5BBD55F354B271015BE7B971DD3510064EE709 |
| SHA256: | 04D5C7486CF4962F52AC9173987C4AE53084A9329797F9E872D701943AF4A022 |
| SSDEEP: | 98304:/Ynz1/Hgu+4BNfWxWLFDou3biToRnoJF5j4GcvIhXWHhC320BIwXx3dyu4SJwbsk:DcFS50oBk3JJ7Rs63kuf2fN8 |
MALICIOUS
Actions looks like stealing of personal data
- Evolution X Loader.exe (PID: 6992)
Steals credentials from Web Browsers
- Evolution X Loader.exe (PID: 6992)
STORMKITTY has been detected (YARA)
- Evolution X Loader.exe (PID: 6992)
Stealers network behavior
- Evolution X Loader.exe (PID: 6992)
Attempting to use instant messaging service
- Evolution X Loader.exe (PID: 6992)
ASYNCRAT has been detected (MUTEX)
- Evolution X Loader.exe (PID: 6992)
SUSPICIOUS
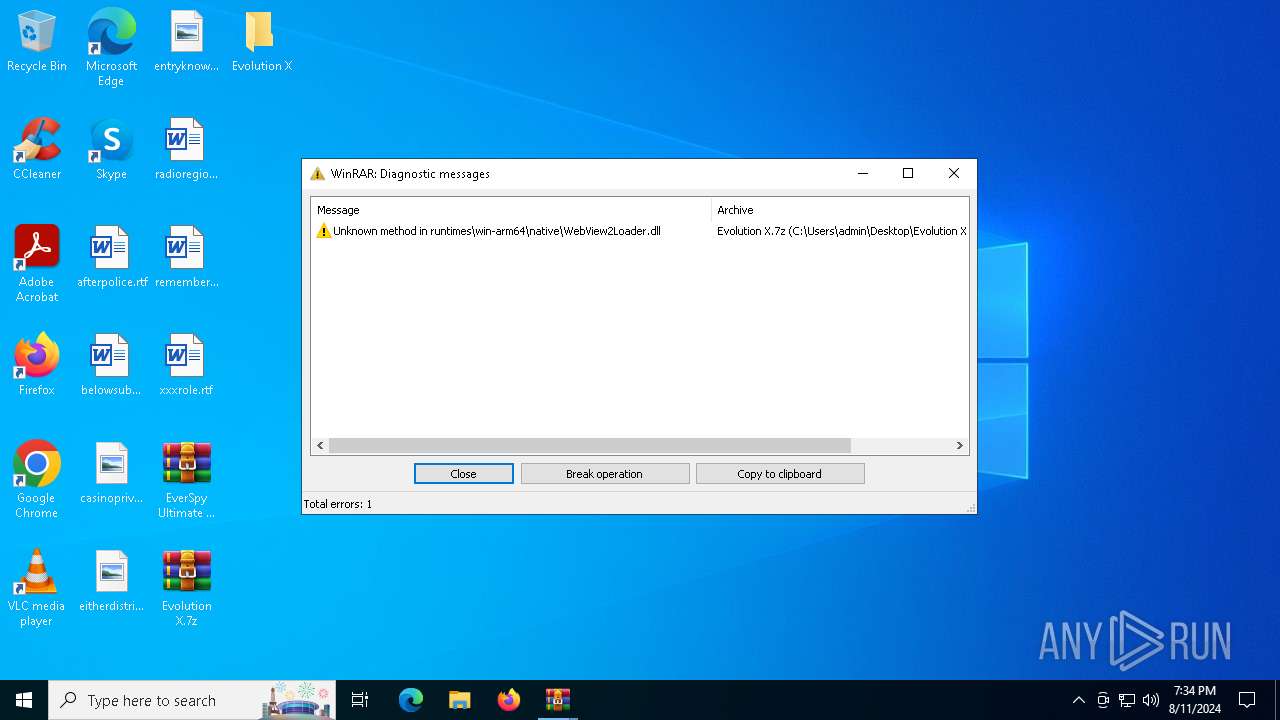
Process drops legitimate windows executable
- WinRAR.exe (PID: 2464)
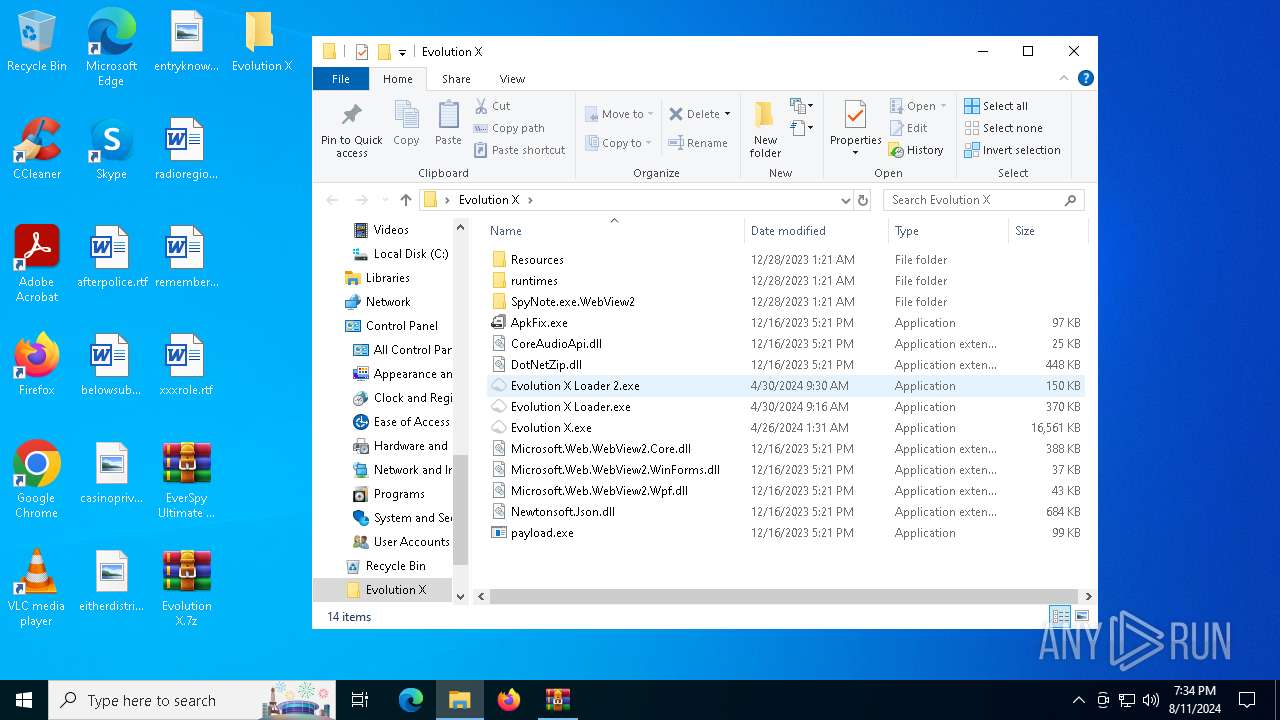
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Evolution X Loader 2.exe (PID: 4708)
- Evolution X Loader.exe (PID: 6992)
Write to the desktop.ini file (may be used to cloak folders)
- Evolution X Loader.exe (PID: 6992)
Starts application with an unusual extension
- cmd.exe (PID: 3360)
- cmd.exe (PID: 6304)
Starts CMD.EXE for commands execution
- Evolution X Loader.exe (PID: 6992)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 3360)
- cmd.exe (PID: 6304)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3360)
Checks for external IP
- svchost.exe (PID: 2256)
- Evolution X Loader.exe (PID: 6992)
The process connected to a server suspected of theft
- Evolution X Loader.exe (PID: 6992)
Executable content was dropped or overwritten
- RegAsm.exe (PID: 6440)
Drops the executable file immediately after the start
- RegAsm.exe (PID: 6440)
Potential Corporate Privacy Violation
- Evolution X Loader.exe (PID: 6992)
INFO
Dropped object may contain TOR URL's
- WinRAR.exe (PID: 2464)
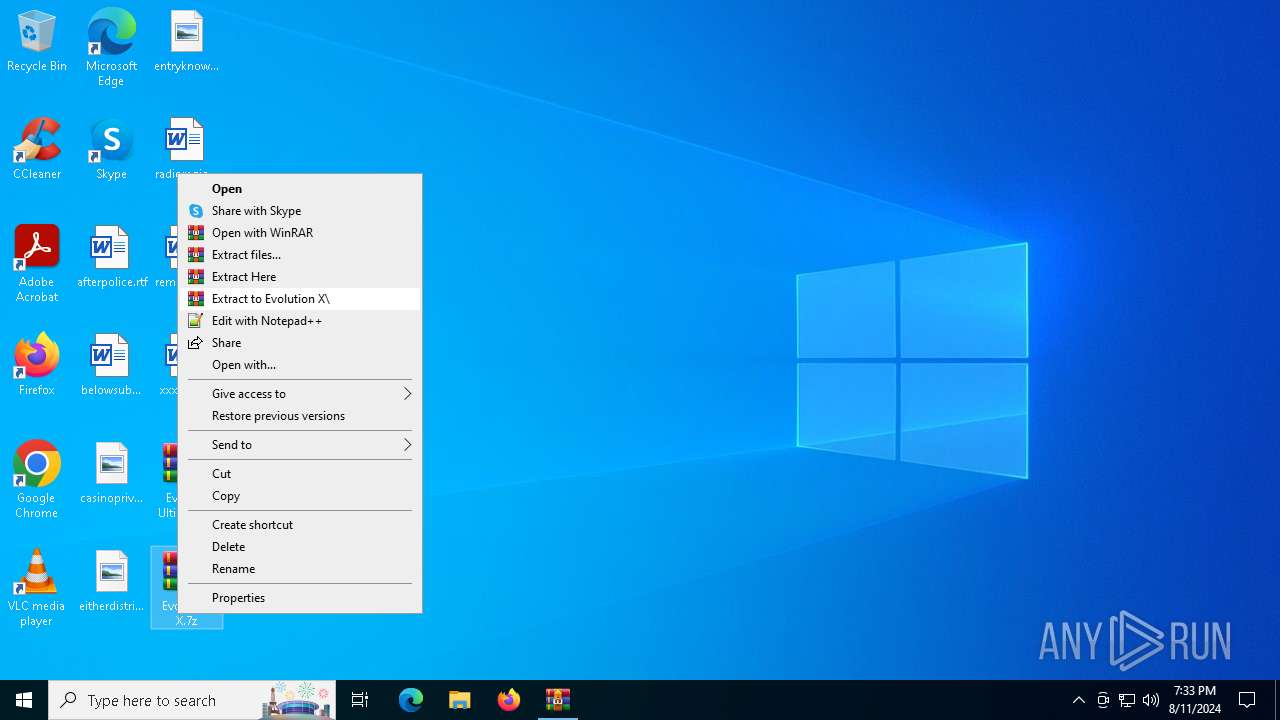
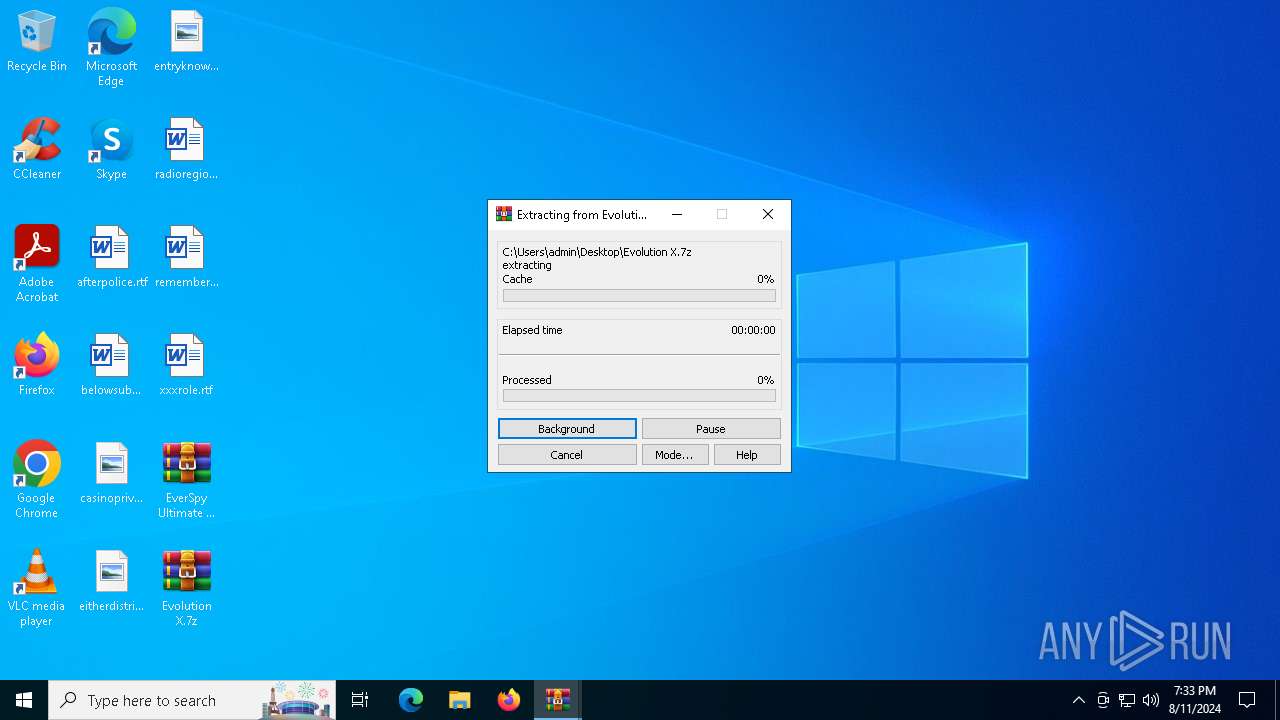
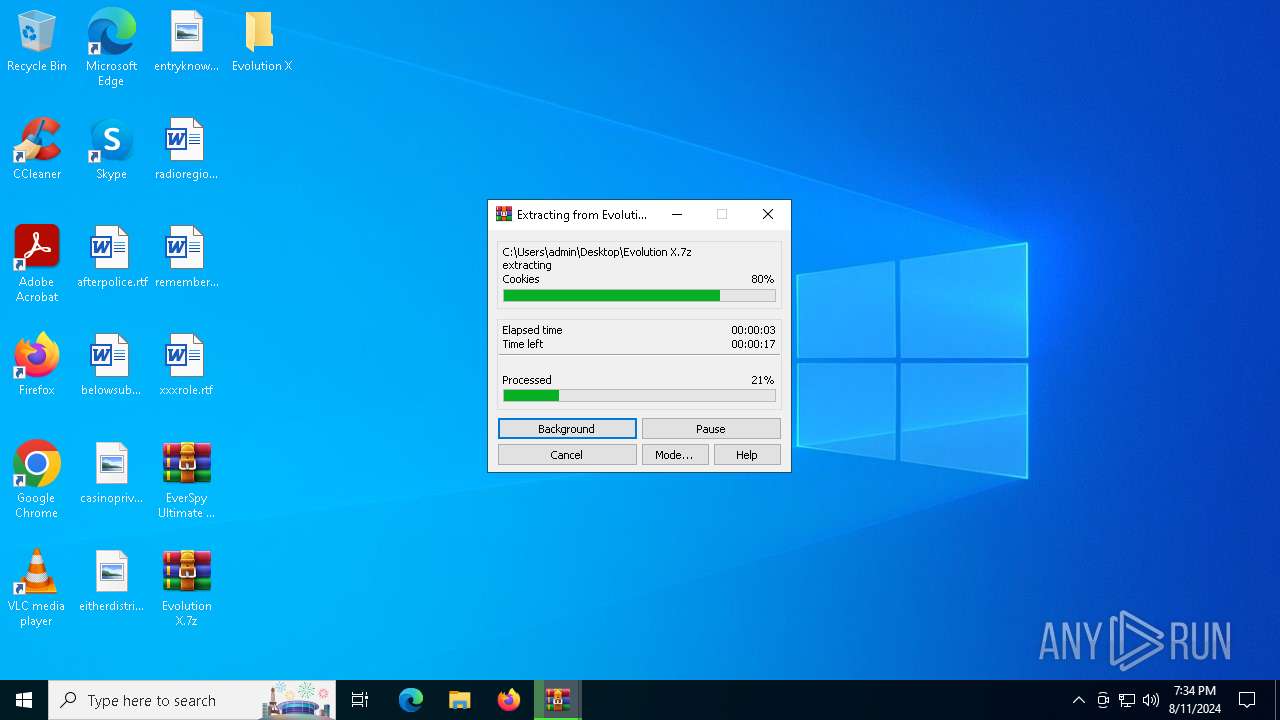
Manual execution by a user
- WinRAR.exe (PID: 2464)
- Evolution X Loader 2.exe (PID: 4708)
- Evolution X Loader.exe (PID: 6992)
- ApkFix.exe (PID: 1344)
- Evolution X.exe (PID: 2064)
- payload.exe (PID: 1224)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2464)
Reads the computer name
- Evolution X Loader 2.exe (PID: 4708)
- Evolution X Loader.exe (PID: 6992)
- ApkFix.exe (PID: 1344)
- Evolution X.exe (PID: 2064)
- RegAsm.exe (PID: 6440)
- payload.exe (PID: 1224)
Reads Environment values
- Evolution X Loader 2.exe (PID: 4708)
- Evolution X Loader.exe (PID: 6992)
Checks supported languages
- Evolution X Loader.exe (PID: 6992)
- ApkFix.exe (PID: 1344)
- Evolution X Loader 2.exe (PID: 4708)
- chcp.com (PID: 2132)
- chcp.com (PID: 4592)
- Evolution X.exe (PID: 2064)
- payload.exe (PID: 1224)
- RegAsm.exe (PID: 6440)
Attempting to use instant messaging service
- Evolution X Loader 2.exe (PID: 4708)
- svchost.exe (PID: 2256)
- Evolution X Loader.exe (PID: 6992)
Reads the machine GUID from the registry
- Evolution X Loader.exe (PID: 6992)
- ApkFix.exe (PID: 1344)
- Evolution X Loader 2.exe (PID: 4708)
- Evolution X.exe (PID: 2064)
- payload.exe (PID: 1224)
Disables trace logs
- Evolution X Loader 2.exe (PID: 4708)
- Evolution X Loader.exe (PID: 6992)
Checks proxy server information
- Evolution X Loader 2.exe (PID: 4708)
- Evolution X Loader.exe (PID: 6992)
Reads the software policy settings
- Evolution X Loader 2.exe (PID: 4708)
- Evolution X Loader.exe (PID: 6992)
Creates files or folders in the user directory
- Evolution X Loader.exe (PID: 6992)
Create files in a temporary directory
- Evolution X Loader.exe (PID: 6992)
- RegAsm.exe (PID: 6440)
Changes the display of characters in the console
- chcp.com (PID: 2132)
- chcp.com (PID: 4592)
Reads CPU info
- Evolution X Loader.exe (PID: 6992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
StormKitty
(PID) Process(6992) Evolution X Loader.exe
C2 (1)127.0.0.1
Ports (3)6606
7707
8808
Credentials
Protocoltelegram
URLhttps://api.telegram.org/bot1119746739:AAGMhvpUjXI4CzIfizRC--VXilxnkJlhaf8/send
Token6136383697:AAGfsDaDLMnRmxp7pg4J5BoUuPDhvYm_M10
ChatId1863892139
Version
BotnetDefault
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE9jCCAt6gAwIBAgIQAKQXqY8ZdB/modqi69mWGTANBgkqhkiG9w0BAQ0FADAcMRowGAYDVQQDDBFXb3JsZFdpbmQgU3RlYWxlcjAgFw0yMTA3MTMwNDUxMDZaGA85OTk5MTIzMTIzNTk1OVowHDEaMBgGA1UEAwwRV29ybGRXaW5kIFN0ZWFsZXIwggIiMA0GCSqGSIb3DQEBAQUAA4ICDwAwggIKAoICAQCnRXYoxuLqqgXdcvIAYWb9DuVRl5ZpdpPfoIgmb7Y9A9AuiddKNm4is8EvIlEh98bQD4OB...
Server_SignatureB/V3BUeYu10HTiTPmCXLqLTBnmwYEOinSL5L9EBUMNAAIaqtzGNvo5uy0BFrbrRaukmCUaas84RekvOxu9rDTharx8OjwxzGo6OoNNC5TemoZGE6G7LVXg181LlExXduQqKwNczYs6PK8C/1UfRZf0l1I3ZYE5vUXuPWxl5MZhuHBK663w6tpzni0Z9/061Ckbt5xqOXPiKlLCTyLwsLWnXwga9DlwjRpzNZwUlVVkj+YJay96Bssoh/Lw59N++3BeGJMqN/apXhLm4HCjOTKPj8cQRb2eNlBrLeKz2YO+3l...
Keys
AES33baad7fc5ff88a90432d49306410cd4ccf076637b30c5e986f32500f077b9b6
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
149
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
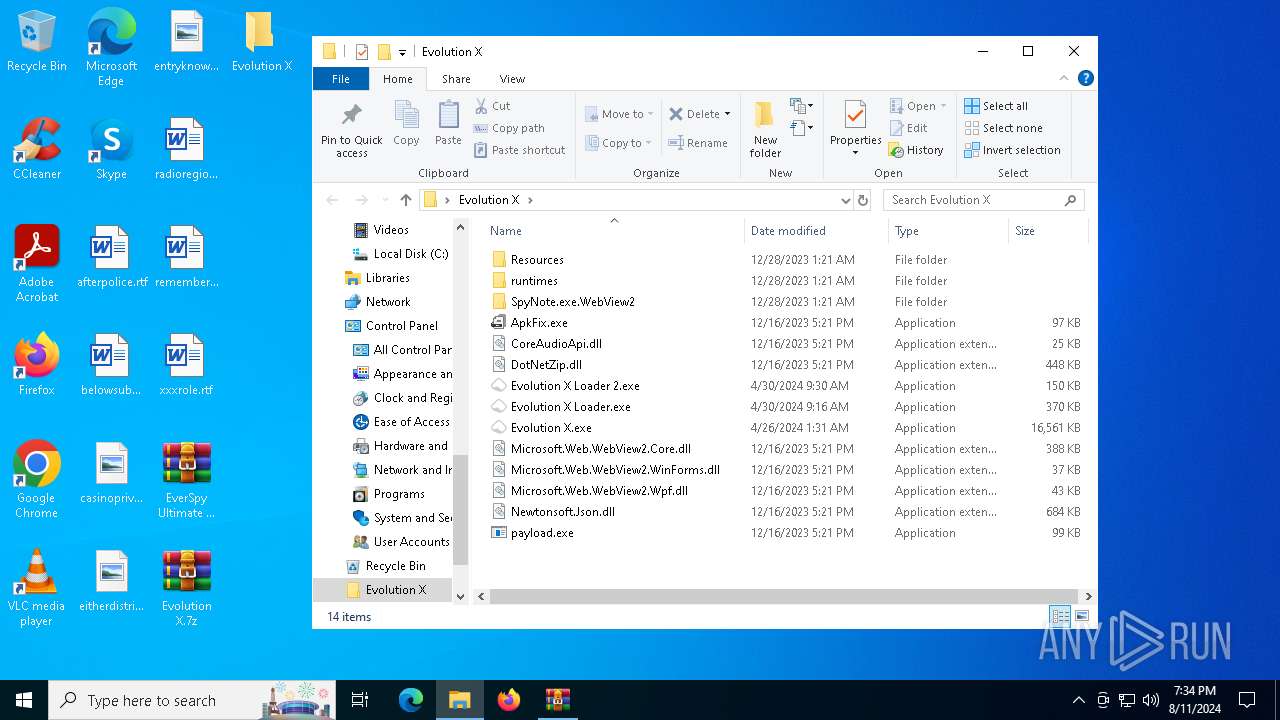
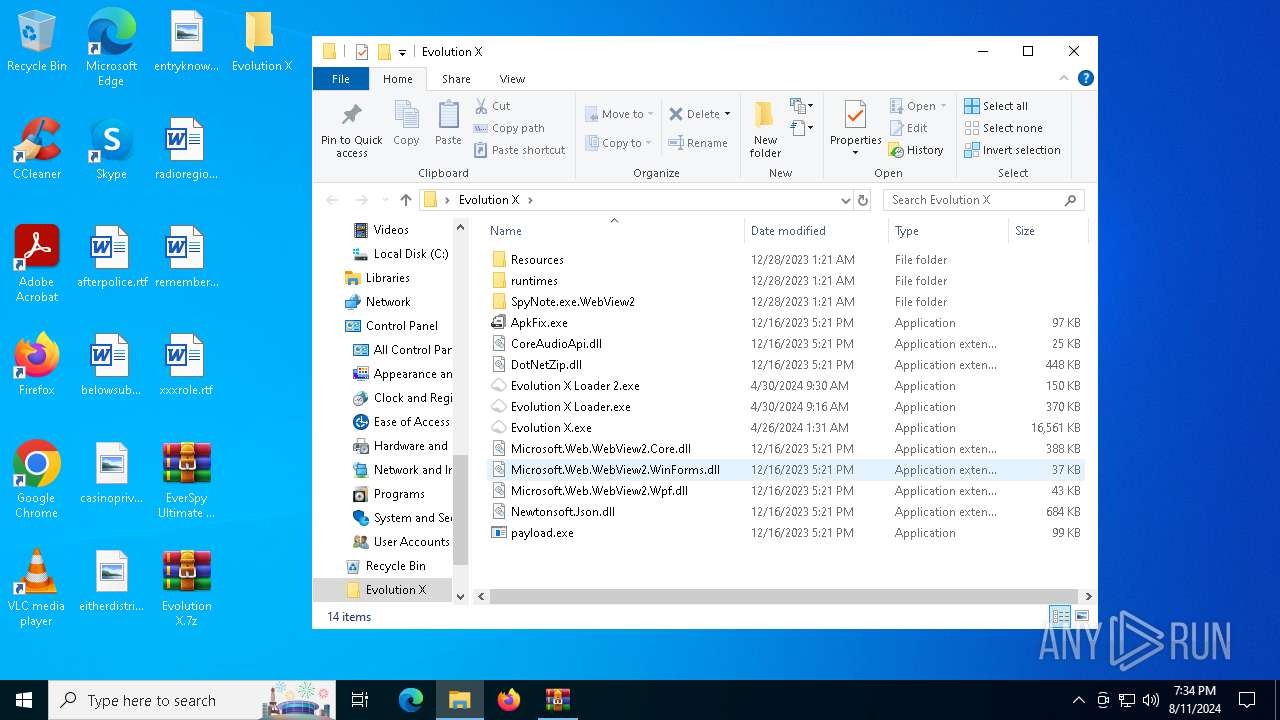
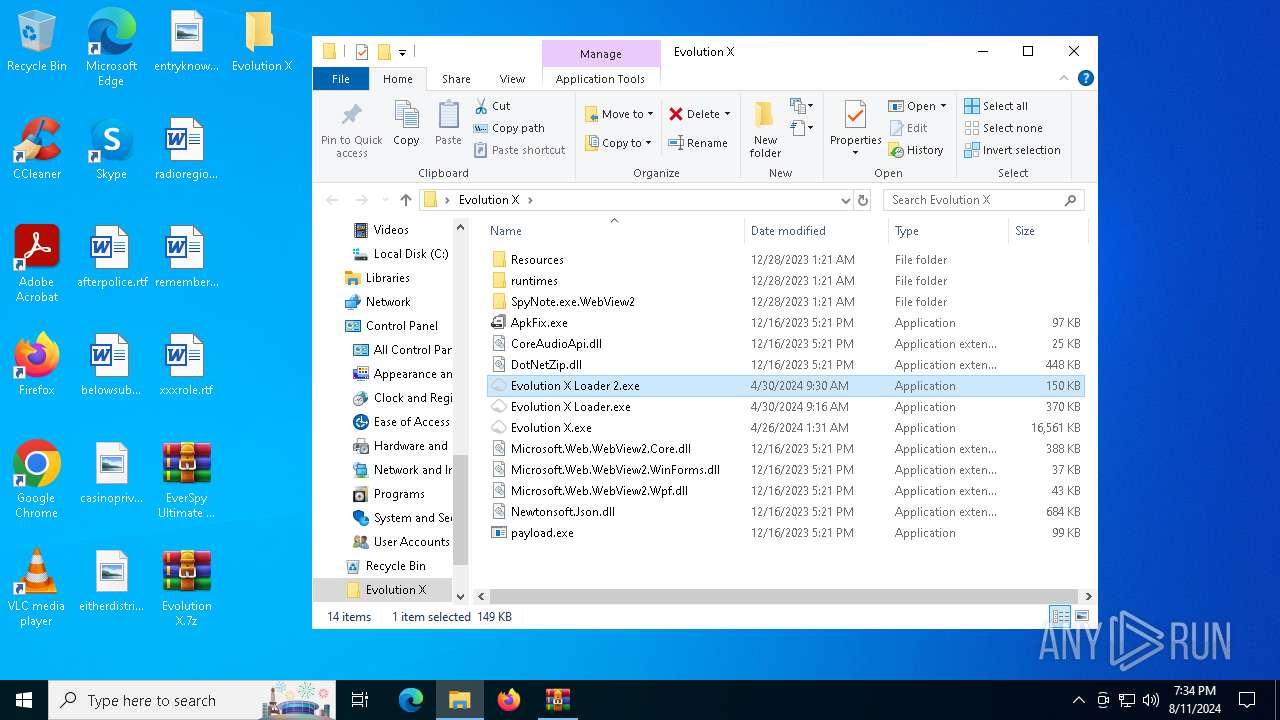
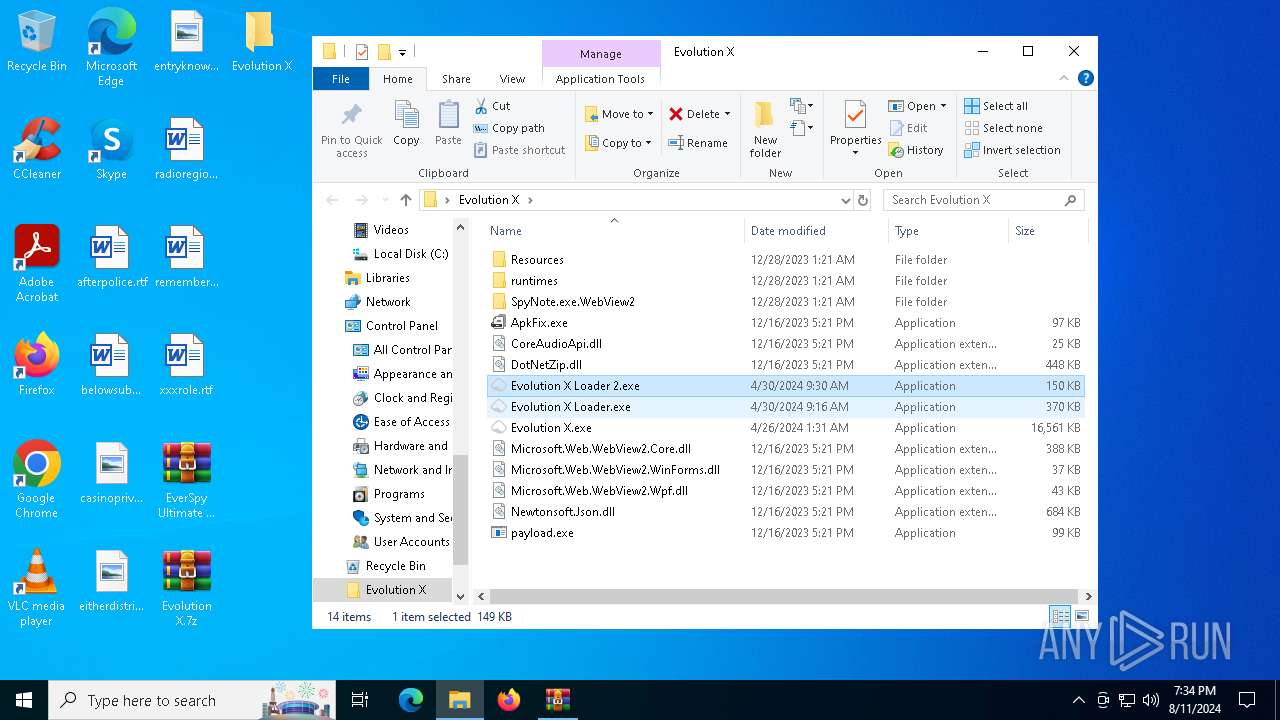
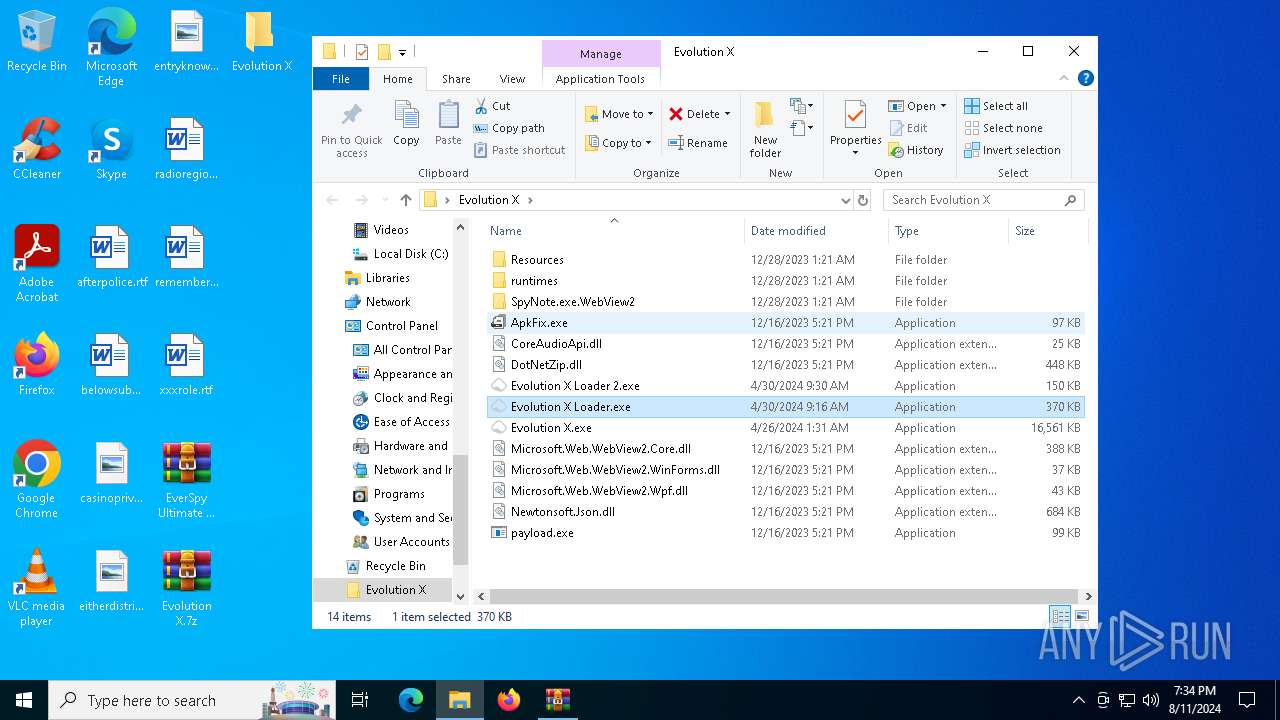
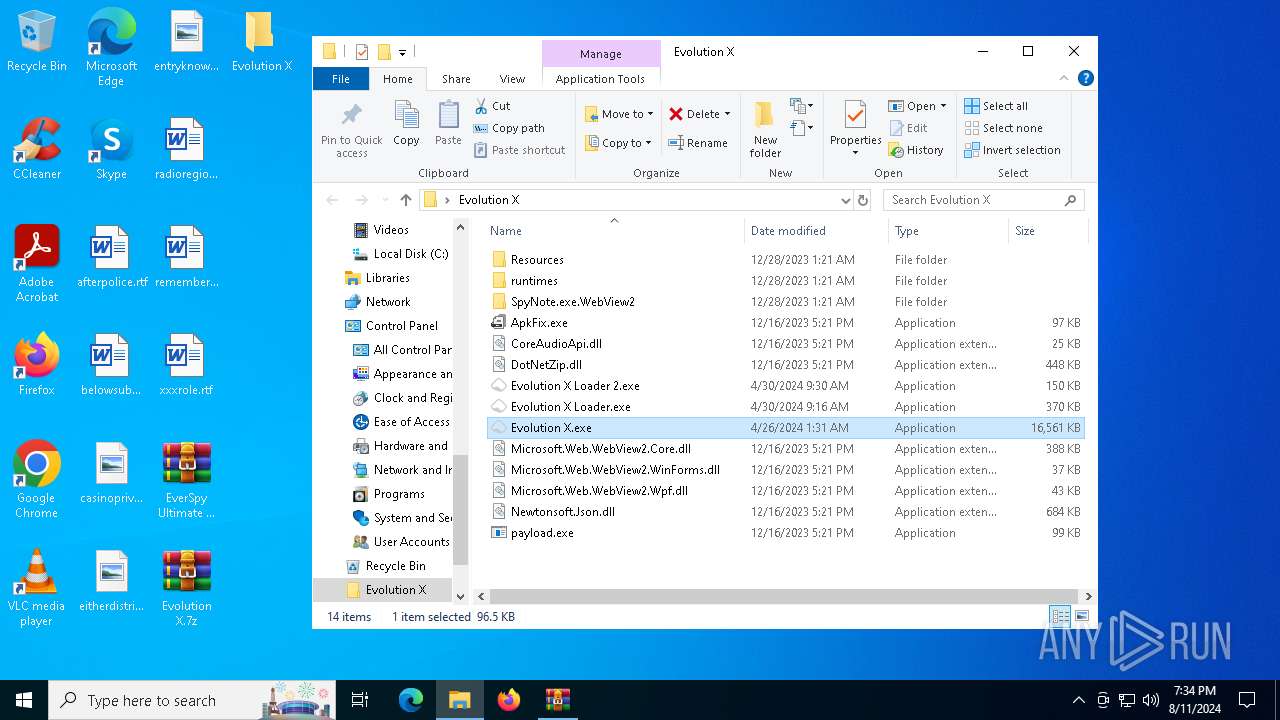
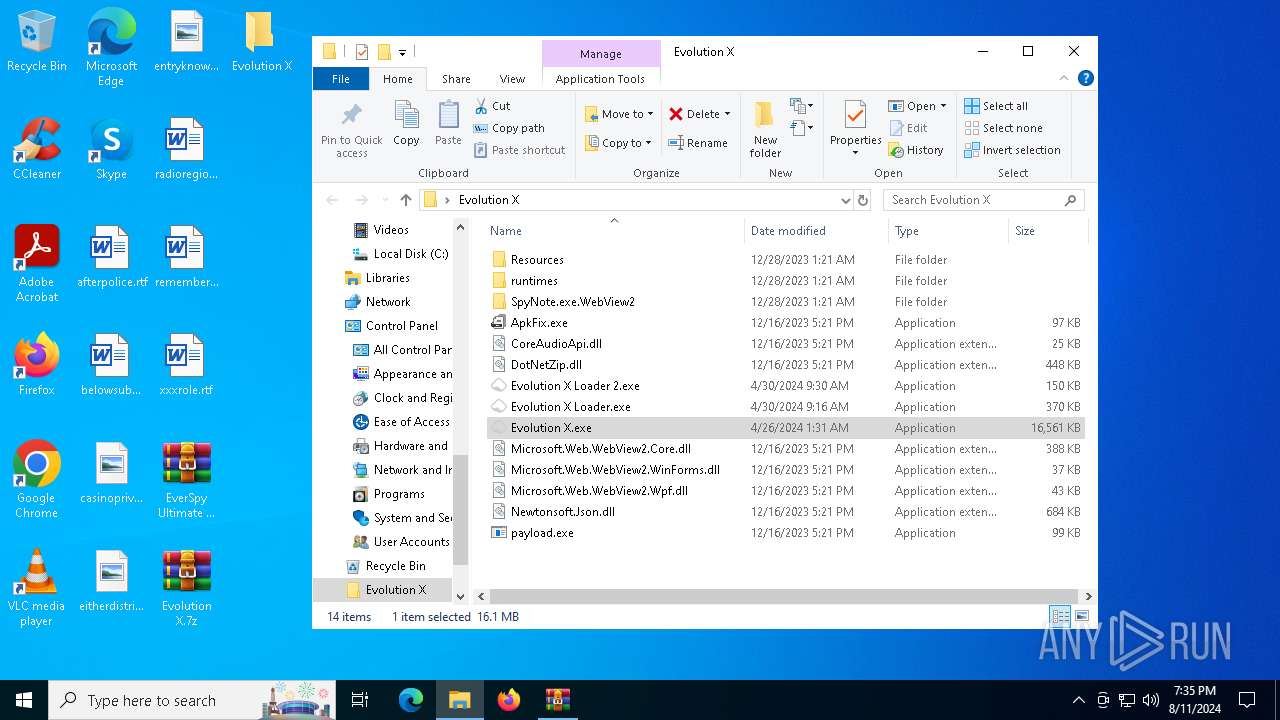
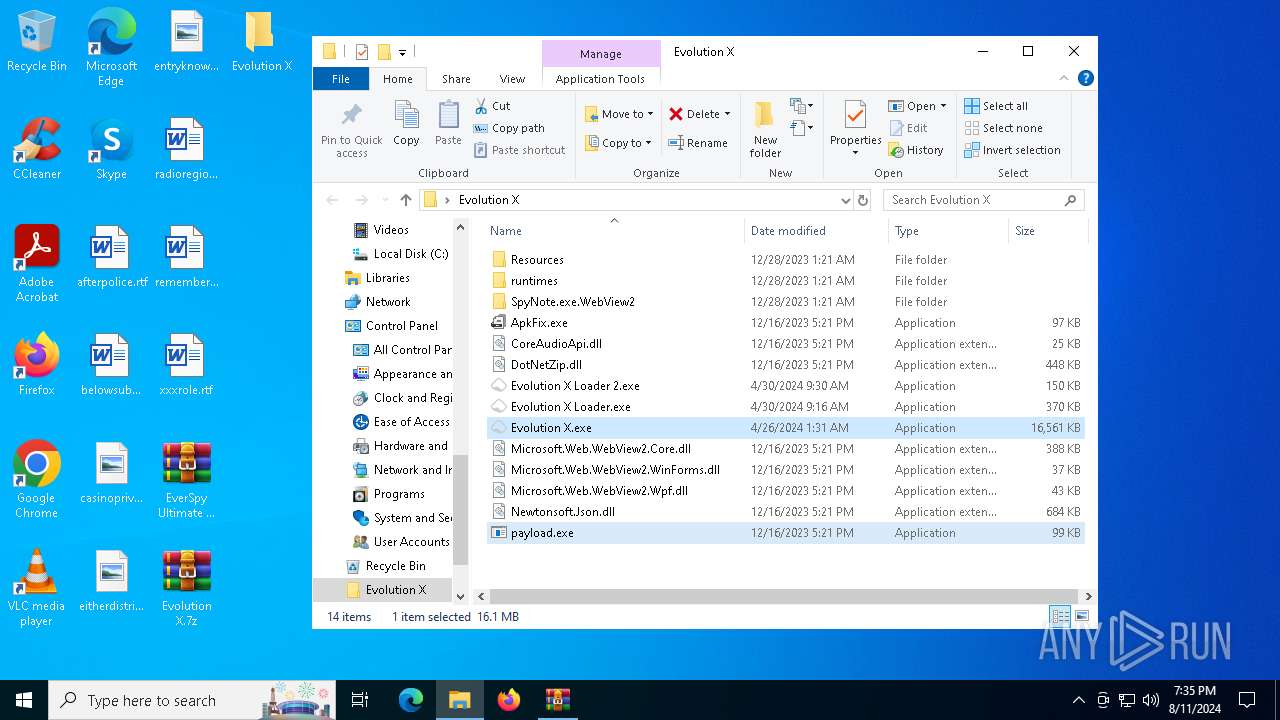
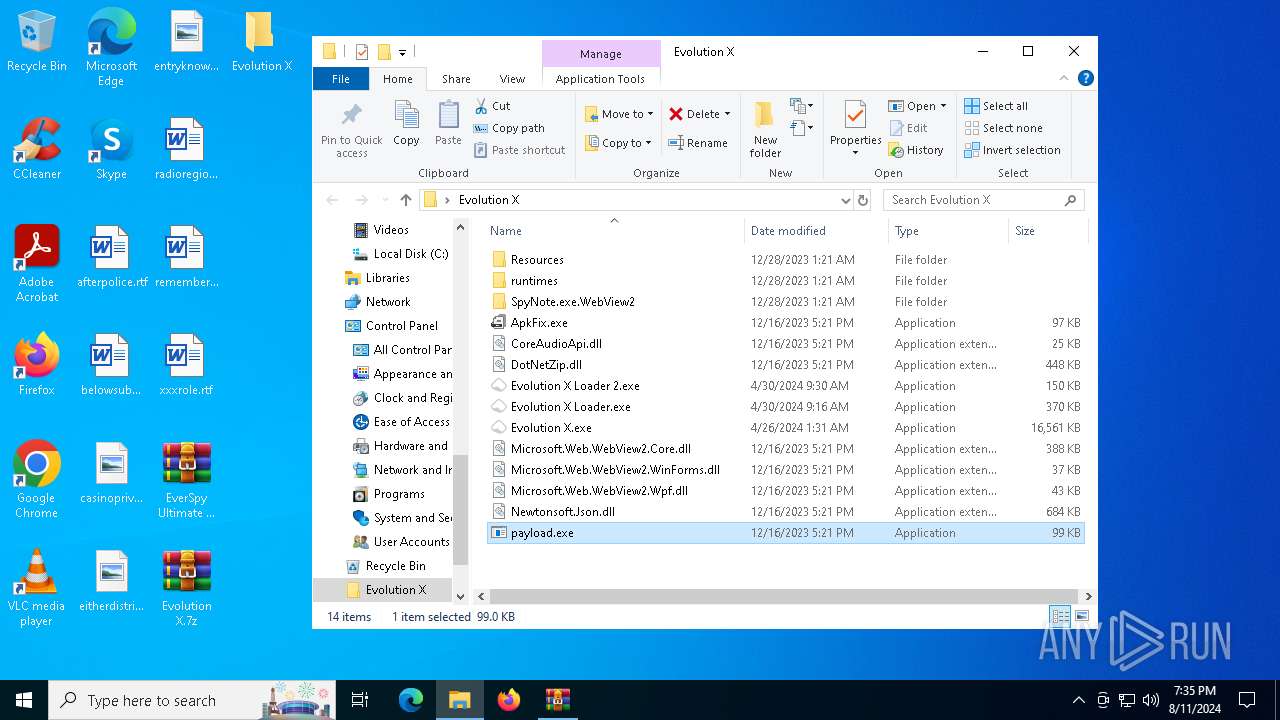
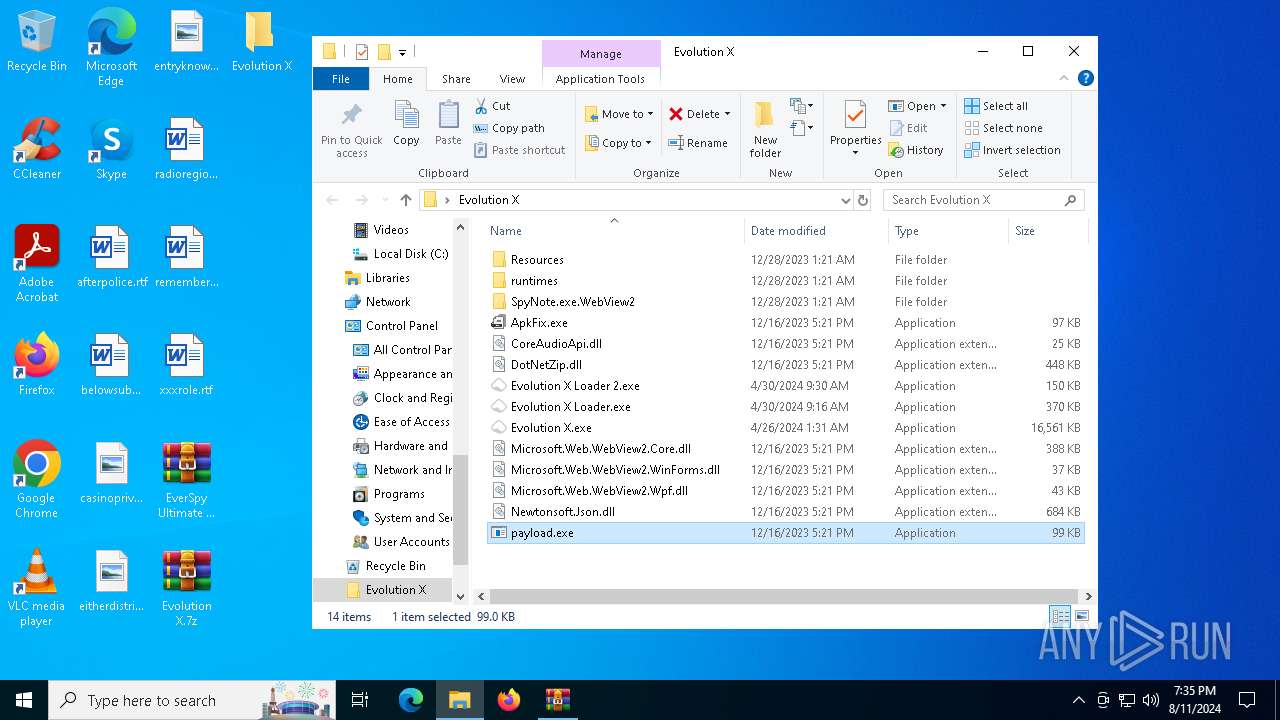
| 1224 | "C:\Users\admin\Desktop\Evolution X\payload.exe" | C:\Users\admin\Desktop\Evolution X\payload.exe | — | explorer.exe | |||||||||||
User: admin Company: spynote.us Integrity Level: MEDIUM Description: Payload Exit code: 0 Version: 7.0.1.1 Modules
| |||||||||||||||
| 1344 | "C:\Users\admin\Desktop\Evolution X\ApkFix.exe" | C:\Users\admin\Desktop\Evolution X\ApkFix.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ApkFix Exit code: 0 Version: 7.0.1.1 Modules
| |||||||||||||||
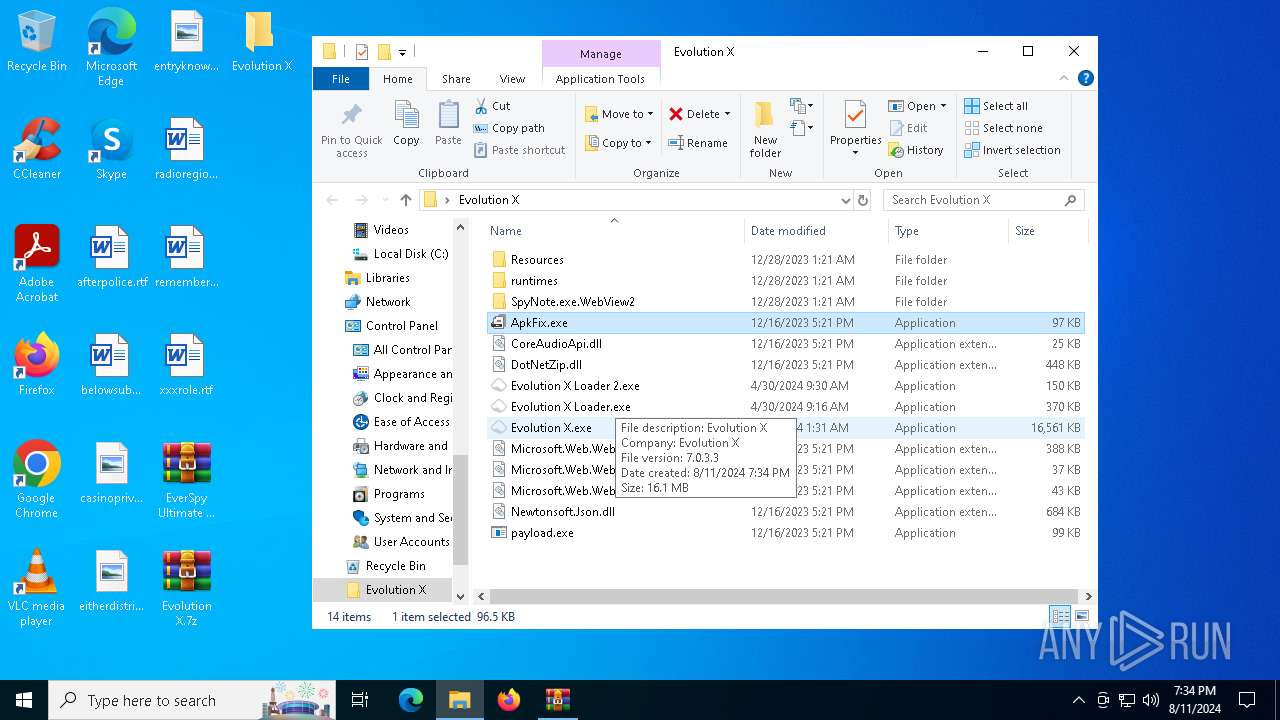
| 2064 | "C:\Users\admin\Desktop\Evolution X\Evolution X.exe" | C:\Users\admin\Desktop\Evolution X\Evolution X.exe | — | explorer.exe | |||||||||||
User: admin Company: Evolution X Integrity Level: MEDIUM Description: Evolution X Exit code: 0 Version: 7.0.3.3 Modules
| |||||||||||||||
| 2132 | chcp 65001 | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2388 | netsh wlan show profile | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Evolution X.7z" "C:\Users\admin\Desktop\Evolution X\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 2 Version: 5.91.0 Modules
| |||||||||||||||
| 3360 | "cmd.exe" /C chcp 65001 && netsh wlan show profile | findstr All | C:\Windows\SysWOW64\cmd.exe | — | Evolution X Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4592 | chcp 65001 | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 286
Read events
11 242
Write events
44
Delete events
0
Modification events
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\EverSpy Ultimate Unpacked - Copy.rar | |||
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6544) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
Executable files
20
Suspicious files
195
Text files
467
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\CutiveMono.ttf | ttf | |
MD5:2873A2747ABEDF74A31909E1BE5E23F9 | SHA256:AE8AD180A0166369407284E62D02D8DAF6A5BD28D4064F0008023A84458840B9 | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\Hurme Geometric Sans 4 W00 Lt.ttf | binary | |
MD5:8C7C5CEDB3DD34C518D04AB514DDFB92 | SHA256:62AFE2D0F5627146C225957A0F91D649ED1893D33BE813D2AC7C5110B4F3EF29 | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\FiraCode-Light.ttf | binary | |
MD5:A85EBFC3913AB6BC6A7B817FA627B904 | SHA256:DBAEA44B044C9F6552D3ABFB4EB936F51A6871DC5421EF2BDE80730C82DBA442 | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\DroidSansMonoSlashed.ttf | binary | |
MD5:D5540FAA206983C791843A3A55E3CB98 | SHA256:01550D67B4C7A8C113DA222A26F0E77F39D9FE2264369C7CC2D8F6962682BE35 | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\HurmeGeometricSans4Hairline.otf | otf | |
MD5:24195D22CC0D7904FADCA0E9394B48EC | SHA256:2AACB9E73E9791FD028B2B860F6C8CFB4D0317CD19987C539EB53BA2D9F9B7AD | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\Hurme Geometric Sans 3 W03 Thin.ttf | binary | |
MD5:8FE5F2D2FE1A3E8C6945040581835A2E | SHA256:07C47AC95F8769E11471C6742AC9A903A45DFB557B5EEA60A48A78CB20A353C4 | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\Hurme Geometric Sans 4 W00 Obl.ttf | binary | |
MD5:D4ED7B2A4E107926E104E6EEC0295987 | SHA256:21E3D6B731A4EBF89FA2171500D97EEB1208B32AD6DA81281C82A97E8D807F0F | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\HurmeGeometricSans4 SemiBold.otf | otf | |
MD5:509442DEB9016B1293D9C9CE3AD3200E | SHA256:507206159EDAB0BA7A0755E96AF5103934ACB41FCA5B3A64BEE09D43280C4742 | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\Hurme Geometric Sans 4 W00 Thin.ttf | binary | |
MD5:ED24E555A430285DAD7079CBFBC81C92 | SHA256:752AA90B1CC95E627268A10A7DEFA463DE14ADE1CFCF759C768EF76B5A40D0F7 | |||
| 2464 | WinRAR.exe | C:\Users\admin\Desktop\Evolution X\Resources\fonts\Hurme Geometric Sans 3 W03 Rg.ttf | binary | |
MD5:BAA223CE70692D6C7C620EDE6F841F29 | SHA256:A71439EB2A02A713A07FC59C964A39EDE2DAF6EDFAFC3E440AF8AB0D691C207B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
45
DNS requests
21
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6880 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2068 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6928 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6992 | Evolution X Loader.exe | GET | 200 | 104.16.184.241:80 | http://icanhazip.com/ | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1128 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5040 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2068 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2068 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
4708 | Evolution X Loader 2.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
4708 | Evolution X Loader 2.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
6992 | Evolution X Loader.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
6992 | Evolution X Loader.exe | Potential Corporate Privacy Violation | ET POLICY Observed Wifi Geolocation Domain (api .mylnikov .org in TLS SNI) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
6992 | Evolution X Loader.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
6992 | Evolution X Loader.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
6992 | Evolution X Loader.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
6992 | Evolution X Loader.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |